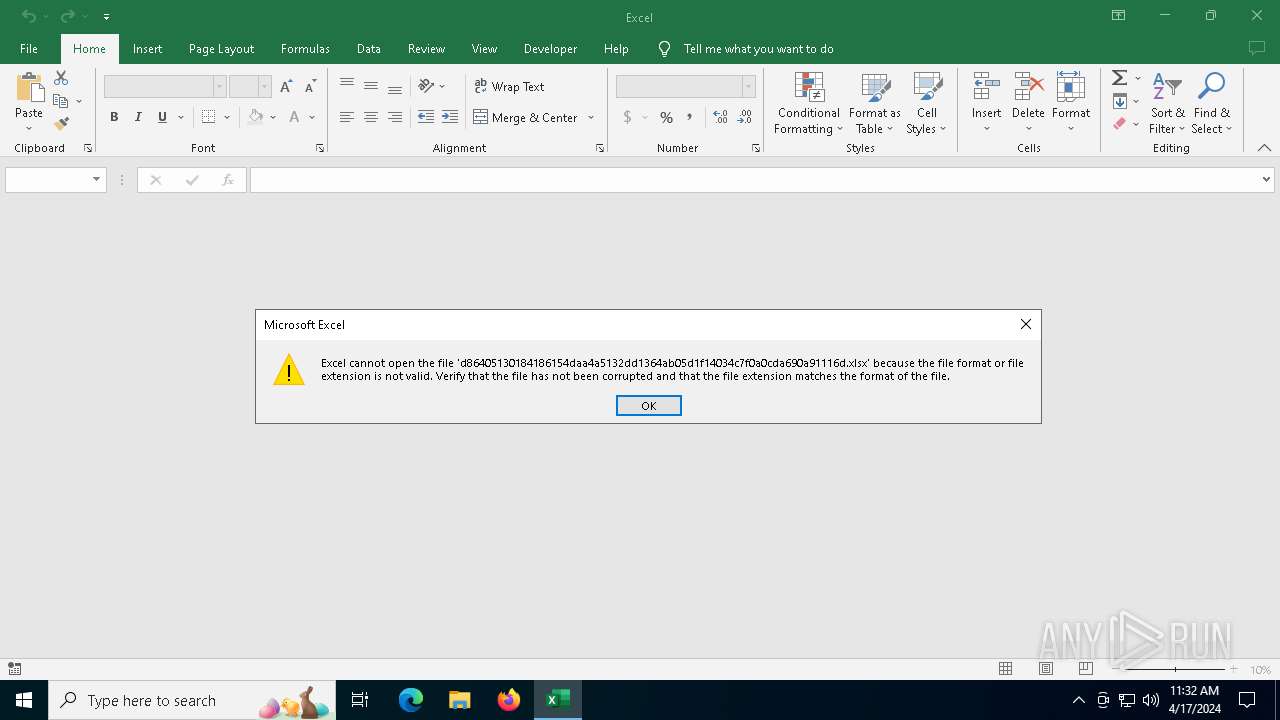
| File name: | d86405130184186154daa4a5132dd1364ab05d1f14034c7f0a0cda690a91116d.xlsx |
| Full analysis: | https://app.any.run/tasks/f4f986c8-cf19-464e-ab85-67b5bf0d342c |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2024, 11:32:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | E7C614F4EB6AA532C189C76D87A8862B |
| SHA1: | 191EDA0C539D284B29EFE556ABB05CD75A9077A0 |
| SHA256: | D86405130184186154DAA4A5132DD1364AB05D1F14034C7F0A0CDA690A91116D |
| SSDEEP: | 3072:jA/6Tx8Kj0B8MLpurjOXjvMdQ7xZvgHmLuYkVQGh9DZ:t8Kj0B8h3OjvM27xZNuxVQGh9DZ |
MALICIOUS
Drops known malicious document
- EXCEL.EXE (PID: 3068)
SUSPICIOUS
Sets XML DOM element text (SCRIPT)
- splwow64.exe (PID: 6208)
Non-standard symbols in registry
- EXCEL.EXE (PID: 3068)
INFO
Reads the software policy settings
- slui.exe (PID: 4460)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 6208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x8060f2d0 |
| ZipCompressedSize: | 442 |
| ZipUncompressedSize: | 1679 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 14.03 |
| LastModifiedBy: | - |
| CreateDate: | 2006:09:16 00:00:00Z |
| ModifyDate: | 2021:03:30 08:50:32Z |
XMP
| Creator: | - |
|---|
Total processes
135
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3068 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" C:\Users\admin\AppData\Local\Temp\d86405130184186154daa4a5132dd1364ab05d1f14034c7f0a0cda690a91116d.xlsx | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 4460 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4672 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6208 | C:\WINDOWS\splwow64.exe 8192 | C:\Windows\splwow64.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print driver host for applications Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6276 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 557
Read events
8 315
Write events
226
Delete events
16
Modification events
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\EXCEL\3068 |
| Operation: | write | Name: | 0 |
Value: 0B0E100EB279B82E87FA45B7FFF03BEDCCC46E2300468ECFF495AF97A4ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511FC17D2120965007800630065006C002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (3068) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
0
Suspicious files
4
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | — | |
MD5:— | SHA256:— | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\A35D2C9F-8B86-4BED-BF91-C40282F7A0FA | xml | |
MD5:C790F787C257D928E70B54CEB2E5D1F8 | SHA256:609394E6BF003A70208A4028B8FDDD1DDA551CF66391F5033027F05AA0FDBCDC | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:79778547B56A626D5AC1037F3C881533 | SHA256:AB879A0044A89B60D4069DE936E68CF0D5132F39E382D1DC4CD3FF021B7802E6 | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:81E121D0E72604FC0D2826F321341CD9 | SHA256:15234B584B68CEFA11D455EF6FF9A22CEDDF1DC888E88C94571C7AA28475BCCF | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\5475cb191e478c39370a215b2da98a37e9dc813d.tbres | binary | |
MD5:62B8C47C86C7DF6A8A84BF9BC9A20780 | SHA256:5368A09606B63A053D40F55D87558E2BA7EAE9D660451C684B257A4E8F7D83F8 | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~$d86405130184186154daa4a5132dd1364ab05d1f14034c7f0a0cda690a91116d.xlsx | binary | |
MD5:21E5D64E6DD2C94C577A61B0A25DE7A4 | SHA256:657F0604A7C1F6CFDC4E8A224F59BD6E1900A4A4DD8B3F61A20F67DEBE41F209 | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\SmartLookupCache\main_ssr.html | — | |
MD5:097A515809D45F83A3AC631E7716329C | SHA256:3AC2E64F913C481C26C7CEED2A9EB081FE790AF6024E38A2582EF53EAE0DB778 | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\SmartLookupCache\microsoft.office.smartlookup.ssr.js | — | |
MD5:BFB2AD1A74B14212AE90EC9EB700AE6A | SHA256:957AB82C0BEF888F8B0FFF4A1D0A06101F382D6755D3EE1869D16364F9C72F50 | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\SmartLookupCache\dictionary_words_bloom_filter.data | binary | |
MD5:A4AF96BCD3EE55F0CB99B37C806A82A5 | SHA256:1BE6D822C31EDC308903E04B986F13388B216DB44019E2BCC3C060284B480BA6 | |||
| 3068 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:904E3AB662DE47AEE248545EA96E2D34 | SHA256:D4EE41FB2DC2B804387D0BAAEAF908E416061486F6B98928905583F4ADDF02D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
52
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4808 | svchost.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
6416 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | unknown |
3068 | EXCEL.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
6040 | SIHClient.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6040 | SIHClient.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 2.19.45.226:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4008 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
4808 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5212 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5152 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4808 | svchost.exe | 2.19.45.226:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3068 | EXCEL.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
3068 | EXCEL.EXE | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3068 | EXCEL.EXE | 52.109.16.68:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3196 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |