| File name: | serve1r.exe |
| Full analysis: | https://app.any.run/tasks/35707c7e-36b1-4aa0-a22b-ce49958c0671 |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2021, 11:04:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 315ABD84D7A9CA3040456876E66C4BA9 |
| SHA1: | 93FD999DBE19AFB347418E2B318B9CBEE4EF6DEA |
| SHA256: | D84A0680C827FC7A543583902B600182773AE8DA78EEF943968E2A7978773789 |
| SSDEEP: | 196608:s9GElla5lWPQ2hQIGd6dC7ZhEXsUKpkbjccS2GVGmIYdsQsjUIazmp5nrUT/jgZ:s/+WYc6fZiXrKXcSpVzImH7zmQI |
MALICIOUS
Writes to a start menu file
- serve1r.exe (PID: 2884)
Drops executable file immediately after starts
- serve1r.exe (PID: 2884)
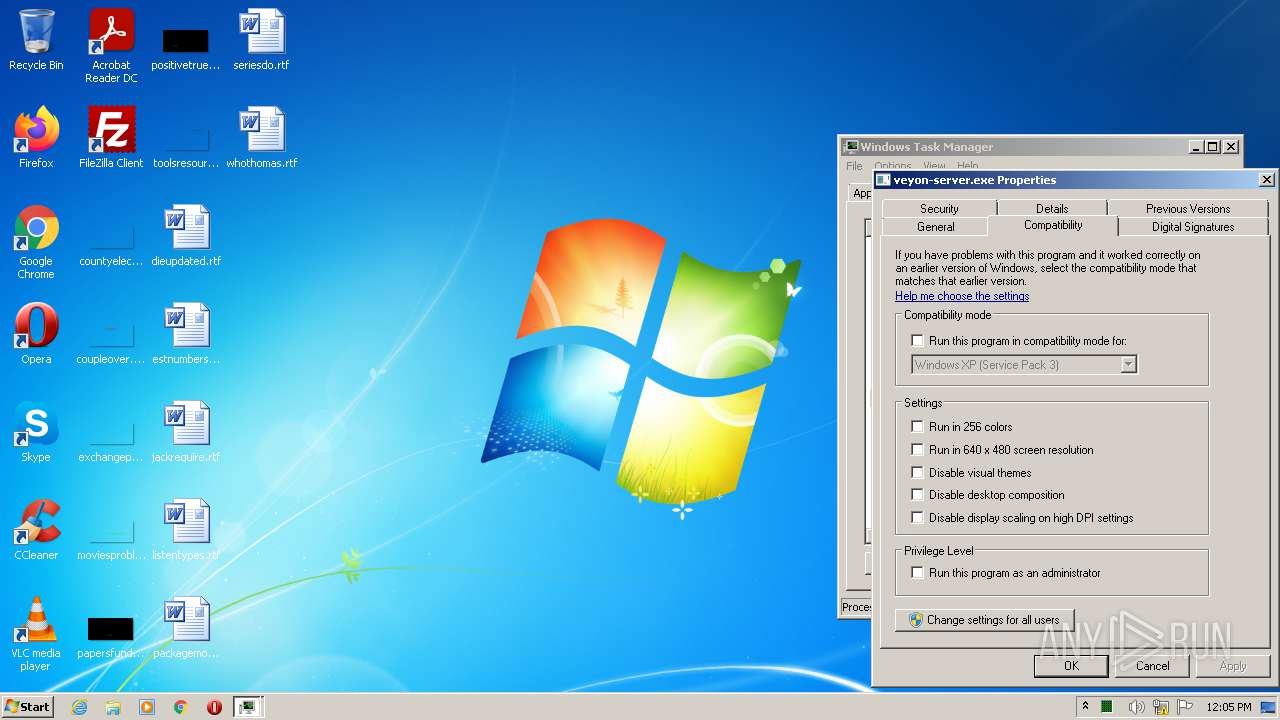
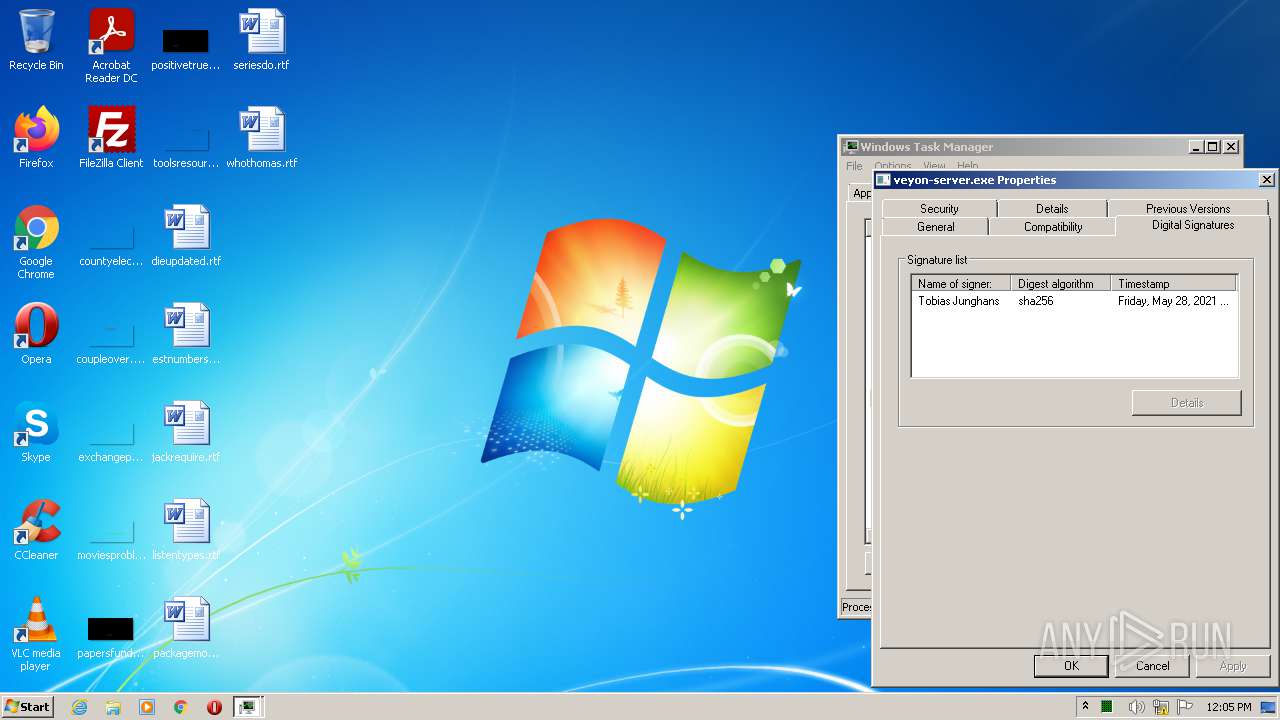
Loads dropped or rewritten executable
- veyon-server.exe (PID: 1528)
Application was dropped or rewritten from another process
- veyon-server.exe (PID: 1528)
SUSPICIOUS
Reads the computer name
- serve1r.exe (PID: 2884)
- WScript.exe (PID: 3360)
- veyon-server.exe (PID: 1528)
Removes files from Windows directory
- serve1r.exe (PID: 2884)
Checks supported languages
- serve1r.exe (PID: 2884)
- WScript.exe (PID: 3360)
- veyon-server.exe (PID: 1528)
- cmd.exe (PID: 3776)
Drops a file that was compiled in debug mode
- serve1r.exe (PID: 2884)
Creates files in the user directory
- serve1r.exe (PID: 2884)
Executes scripts
- serve1r.exe (PID: 2884)
Drops a file with too old compile date
- serve1r.exe (PID: 2884)
Creates files in the Windows directory
- serve1r.exe (PID: 2884)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3360)
Executable content was dropped or overwritten
- serve1r.exe (PID: 2884)
INFO
Dropped object may contain Bitcoin addresses
- serve1r.exe (PID: 2884)
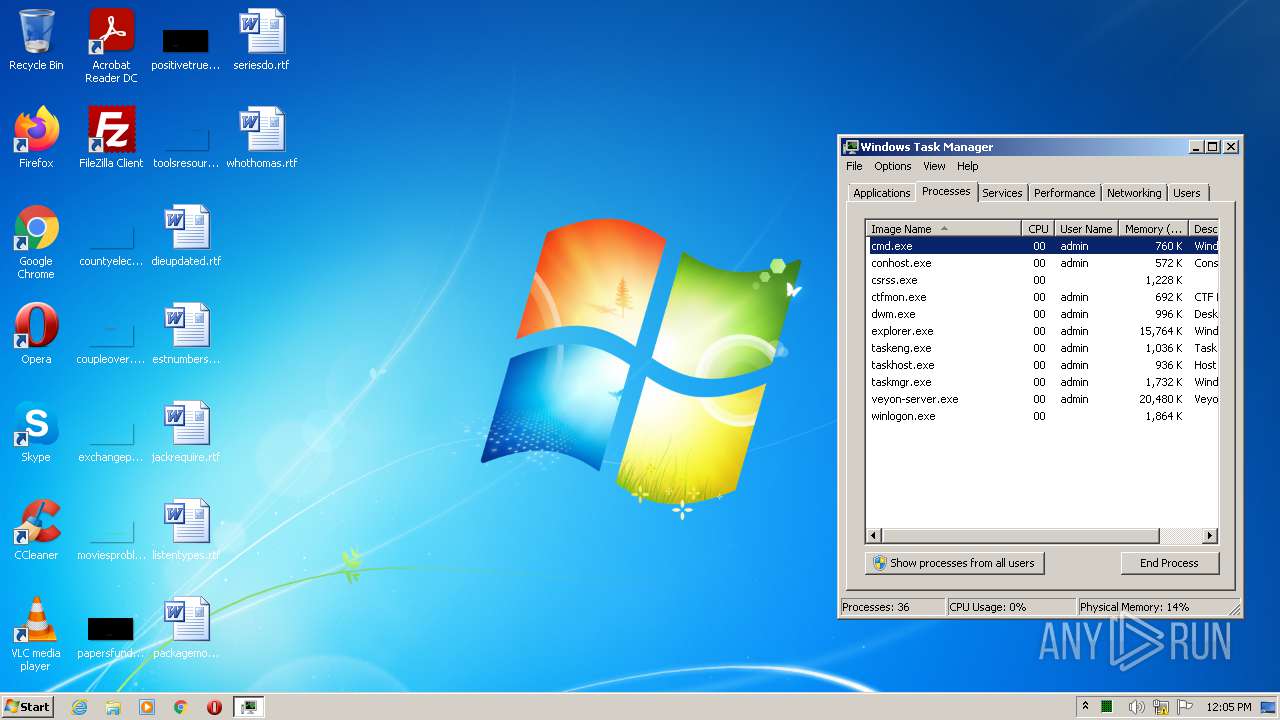
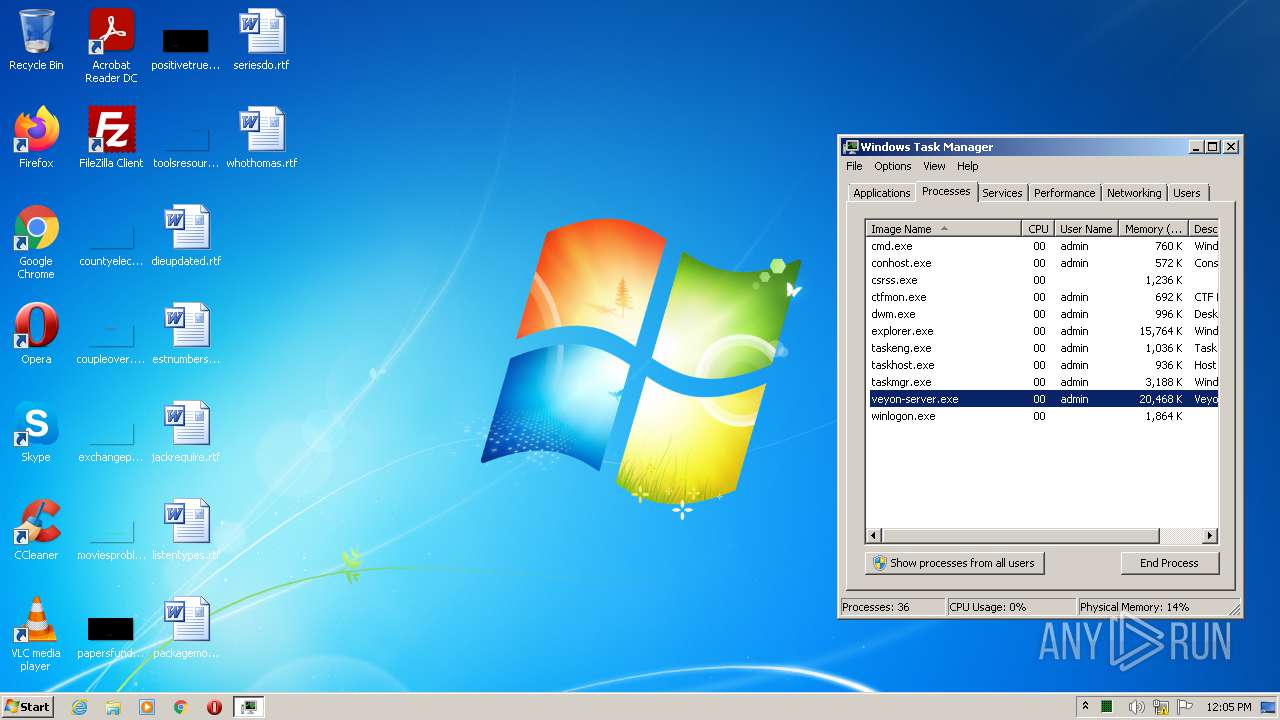
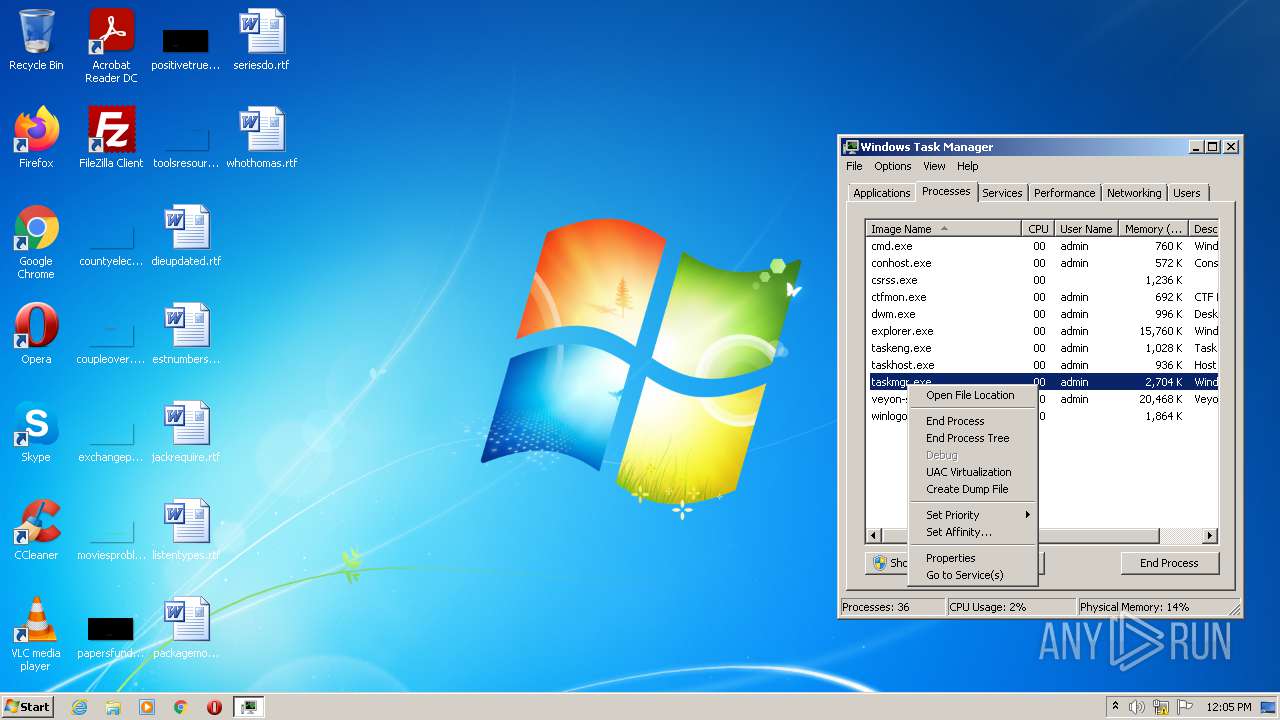
Manual execution by user
- taskmgr.exe (PID: 3412)
Checks supported languages
- taskmgr.exe (PID: 3412)
Checks Windows Trust Settings
- WScript.exe (PID: 3360)
Reads the computer name
- taskmgr.exe (PID: 3412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1cec9 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 69632 |
| CodeSize: | 188928 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2017:08:11 15:54:06+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Aug-2017 13:54:06 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Aug-2017 13:54:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E1CB | 0x0002E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69427 |
.rdata | 0x00030000 | 0x000098A0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12106 |
.data | 0x0003A000 | 0x0001F290 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23719 |
.gfids | 0x0005A000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.05507 |
.rsrc | 0x0005B000 | 0x00004714 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17395 |
.reloc | 0x00060000 | 0x00001F58 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62297 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.88998 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.12176 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.68705 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.74776 | 476 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11 | 3.90128 | 1128 | Latin 1 / Western European | UNKNOWN | RT_STRING |
12 | 3.68258 | 356 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
Total processes
42
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Users\admin\AppData\Local\Temp\serve1r.exe" | C:\Users\admin\AppData\Local\Temp\serve1r.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1528 | veyon-server.exe | C:\Windows\Systnet\veyon-server.exe | — | cmd.exe | |||||||||||
User: admin Company: Veyon Solutions Integrity Level: HIGH Description: Veyon Server Exit code: 0 Version: 4.5.6 Modules
| |||||||||||||||
| 2884 | "C:\Users\admin\AppData\Local\Temp\serve1r.exe" | C:\Users\admin\AppData\Local\Temp\serve1r.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3360 | "C:\Windows\System32\WScript.exe" "C:\Windows\Systnet\install.vbs" | C:\Windows\System32\WScript.exe | — | serve1r.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3412 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | C:\Windows\system32\cmd.exe /c ""C:\Windows\Systnet\install.bat" " | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 474
Read events
1 444
Write events
30
Delete events
0
Modification events
| (PID) Process: | (2884) serve1r.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2884) serve1r.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2884) serve1r.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2884) serve1r.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3360) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3360) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3360) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3360) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1528) veyon-server.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\Server |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\Systnet\veyon-server.exe | |||
| (PID) Process: | (1528) veyon-server.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\Server |
| Operation: | write | Name: | TypesSupported |
Value: 31 | |||
Executable files
81
Suspicious files
0
Text files
7
Unknown types
67
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | serve1r.exe | C:\Windows\Systnet\install.bat | text | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\veyon-master.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\veyon-wcli.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\veyon-configurator.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\plugins\authkeys (2).dll | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\veyon-service.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\veyon-worker.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\plugins\authkeys.dll | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\veyon-cli.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | serve1r.exe | C:\Windows\Systnet\veyon-server.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report