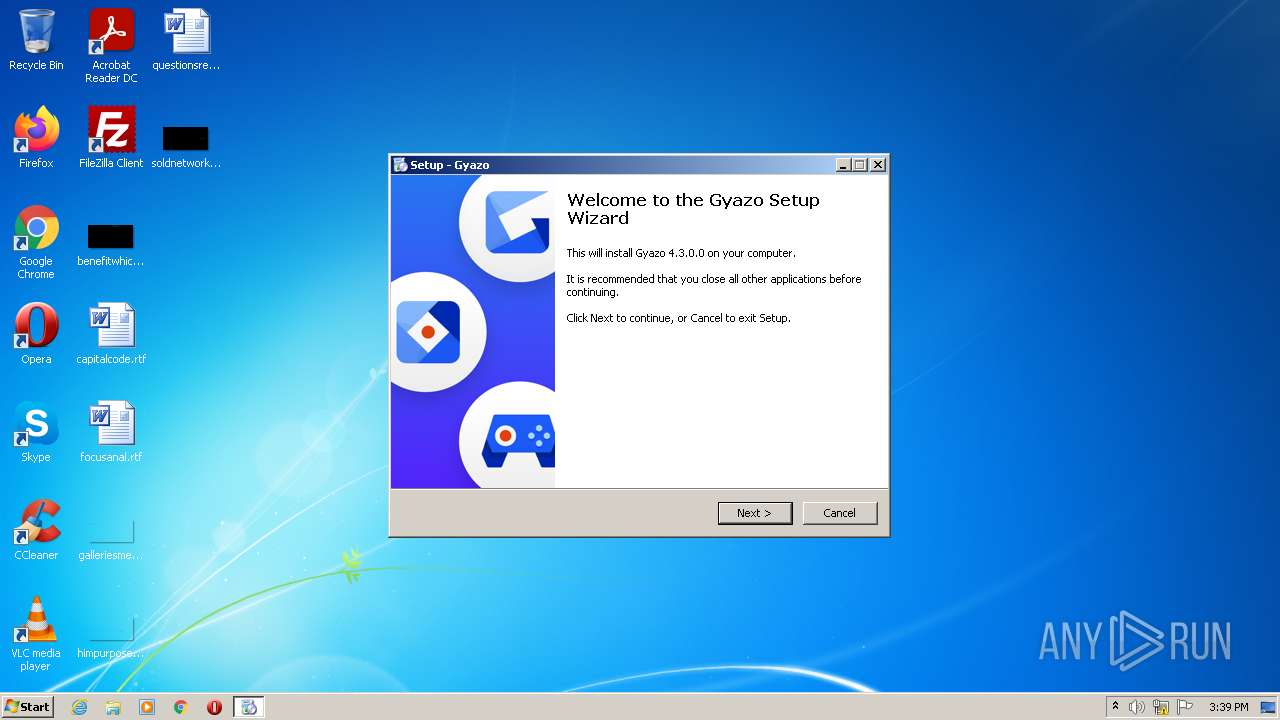
| File name: | Gyazo-4.3.exe |
| Full analysis: | https://app.any.run/tasks/c12d6269-b060-46b6-bf49-b2a15f51276b |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2022, 14:39:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8F3D850A779138D2A07674DEB0462109 |
| SHA1: | 7306E5D8E210B3F5E70E76DD5F224D877D601B20 |
| SHA256: | D83E5D588BD8D7B168614559225D88CC70F57667940A655A9F7867FBDA66B6AB |
| SSDEEP: | 196608:BctRk3FvO05PrevlIgWS1lBVMeEe9lFyAscZ2pGw0l50+OFobOOoZFSCutNeONp+:BSRwevlINSVVrn7kw5TOOQFSOu8 |
MALICIOUS
Drops executable file immediately after starts
- Gyazo-4.3.exe (PID: 2072)
- Gyazo-4.3.exe (PID: 2656)
- Gyazo-4.3.tmp (PID: 1464)
Application was dropped or rewritten from another process
- GyStation.exe (PID: 3576)
- GyStation.exe (PID: 860)
- Gyazowin.exe (PID: 2344)
- GyOnboarding.exe (PID: 3296)
- Gyazowin.exe (PID: 1080)
- GyStation.exe (PID: 2968)
Uses Task Scheduler to run other applications
- Gyazo-4.3.tmp (PID: 1464)
- Gyazo-4.3.tmp (PID: 1464)
Changes the autorun value in the registry
- Gyazo-4.3.tmp (PID: 1464)
- GyStation.exe (PID: 860)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3740)
- schtasks.exe (PID: 4008)
Loads dropped or rewritten executable
- GyStation.exe (PID: 3576)
- GyStation.exe (PID: 2968)
- GyStation.exe (PID: 860)
- Gyazowin.exe (PID: 1080)
- Gyazowin.exe (PID: 2344)
SUSPICIOUS
Checks supported languages
- Gyazo-4.3.exe (PID: 2072)
- Gyazo-4.3.tmp (PID: 3412)
- Gyazo-4.3.exe (PID: 2656)
- Gyazo-4.3.tmp (PID: 1464)
- GyStation.exe (PID: 3576)
- GyStation.exe (PID: 860)
- GyStation.exe (PID: 2968)
- Gyazowin.exe (PID: 2344)
- GyOnboarding.exe (PID: 3296)
- Gyazowin.exe (PID: 1080)
Reads the computer name
- Gyazo-4.3.tmp (PID: 3412)
- Gyazo-4.3.tmp (PID: 1464)
- GyStation.exe (PID: 860)
- GyStation.exe (PID: 2968)
- GyStation.exe (PID: 3576)
- GyOnboarding.exe (PID: 3296)
- Gyazowin.exe (PID: 2344)
- Gyazowin.exe (PID: 1080)
Drops a file with a compile date too recent
- Gyazo-4.3.exe (PID: 2072)
- Gyazo-4.3.exe (PID: 2656)
- Gyazo-4.3.tmp (PID: 1464)
Executable content was dropped or overwritten
- Gyazo-4.3.exe (PID: 2072)
- Gyazo-4.3.exe (PID: 2656)
- Gyazo-4.3.tmp (PID: 1464)
Reads Windows owner or organization settings
- Gyazo-4.3.tmp (PID: 1464)
Reads the Windows organization settings
- Gyazo-4.3.tmp (PID: 1464)
Creates a directory in Program Files
- Gyazo-4.3.tmp (PID: 1464)
Creates files in the user directory
- Gyazo-4.3.tmp (PID: 1464)
- GyOnboarding.exe (PID: 3296)
- Gyazowin.exe (PID: 1080)
- Gyazowin.exe (PID: 2344)
Changes default file association
- GyStation.exe (PID: 3576)
Reads Environment values
- GyStation.exe (PID: 860)
- GyOnboarding.exe (PID: 3296)
Changes IE settings (feature browser emulation)
- GyOnboarding.exe (PID: 3296)
Reads Microsoft Outlook installation path
- GyOnboarding.exe (PID: 3296)
- iexplore.exe (PID: 3796)
Reads internet explorer settings
- GyOnboarding.exe (PID: 3296)
Reads the date of Windows installation
- Gyazowin.exe (PID: 1080)
- Gyazowin.exe (PID: 2344)
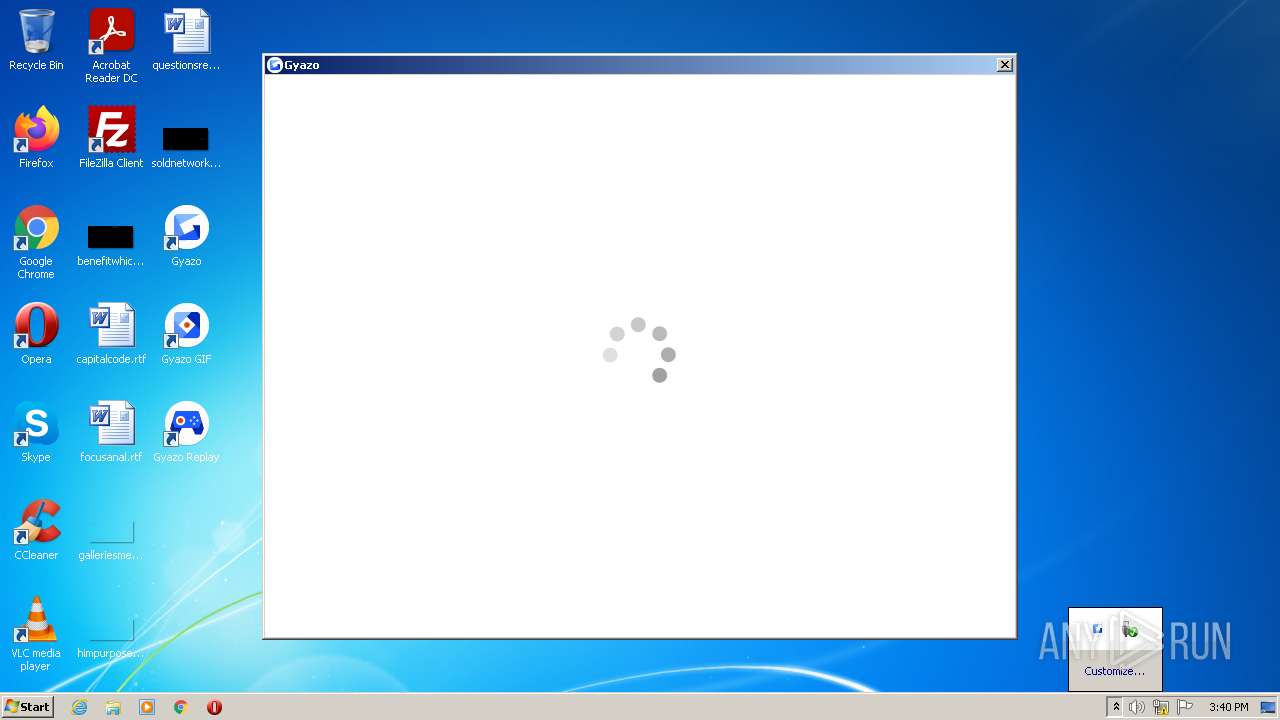
Starts Internet Explorer
- Gyazowin.exe (PID: 1080)
INFO
Application was dropped or rewritten from another process
- Gyazo-4.3.tmp (PID: 1464)
- Gyazo-4.3.tmp (PID: 3412)
Creates files in the program directory
- Gyazo-4.3.tmp (PID: 1464)
Dropped object may contain Bitcoin addresses
- Gyazo-4.3.tmp (PID: 1464)
Checks supported languages
- schtasks.exe (PID: 3740)
- schtasks.exe (PID: 4008)
- WISPTIS.EXE (PID: 604)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 3796)
Creates a software uninstall entry
- Gyazo-4.3.tmp (PID: 1464)
Reads the computer name
- schtasks.exe (PID: 3740)
- schtasks.exe (PID: 4008)
- WISPTIS.EXE (PID: 604)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 3796)
Reads settings of System Certificates
- GyStation.exe (PID: 860)
- GyOnboarding.exe (PID: 3296)
- Gyazowin.exe (PID: 1080)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 3796)
Manual execution by user
- Gyazowin.exe (PID: 1080)
Checks Windows Trust Settings
- GyOnboarding.exe (PID: 3296)
- Gyazowin.exe (PID: 1080)
- iexplore.exe (PID: 3796)
- iexplore.exe (PID: 2460)
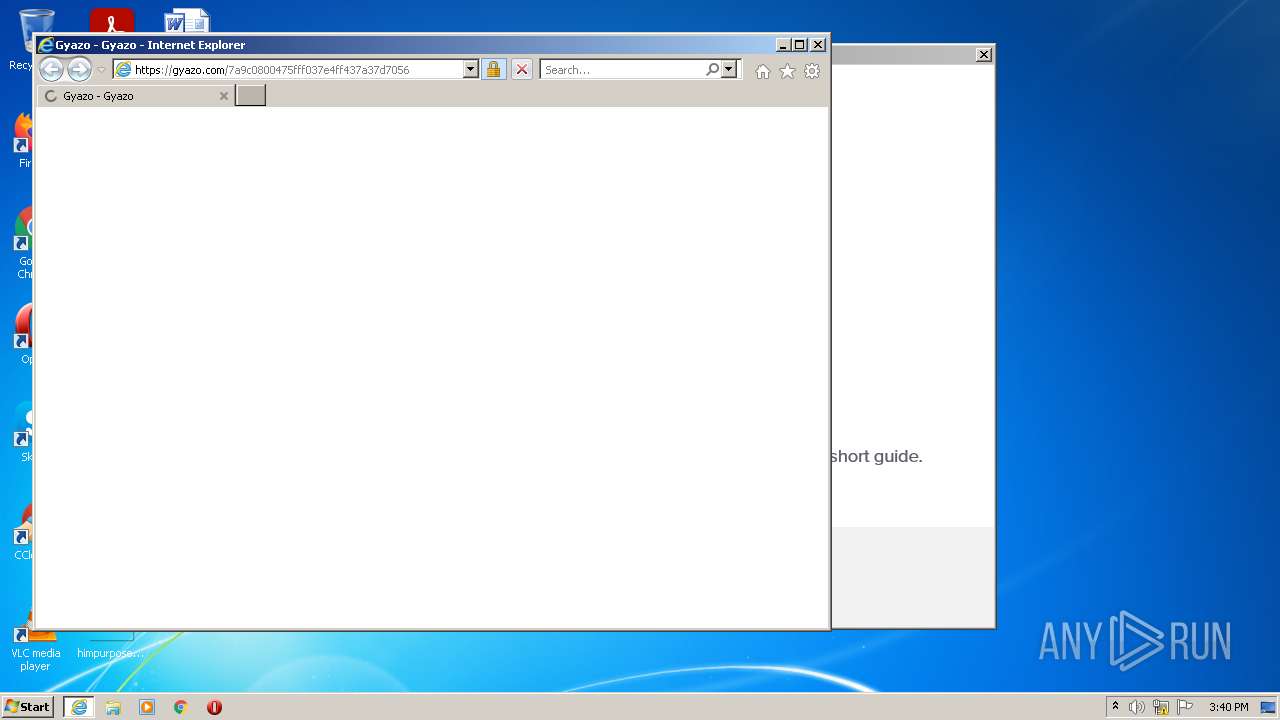
Application launched itself
- iexplore.exe (PID: 2460)
Creates files in the user directory
- iexplore.exe (PID: 3796)
Reads internet explorer settings
- iexplore.exe (PID: 3796)
Reads the date of Windows installation
- iexplore.exe (PID: 2460)
Changes internet zones settings
- iexplore.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| ProductVersion: | 4.3.0.0 |
|---|---|
| ProductName: | Gyazo |
| LegalCopyright: | (c) Nota Inc. All rights reserved. |
| FileVersion: | 4.3.0.0 |
| FileDescription: | Gyazo Setup |
| CompanyName: | Nota Inc. |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.3.0.0 |
| FileVersionNumber: | 4.3.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x1181c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 74240 |
| CodeSize: | 66560 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Nota Inc. |
| FileDescription: | Gyazo Setup |
| FileVersion: | 4.3.0.0 |
| LegalCopyright: | (c) Nota Inc. All rights reserved. |
| ProductName: | Gyazo |
| ProductVersion: | 4.3.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00010178 | 0x00010200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15111 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.88101 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.13606 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.6097 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.72198 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.4516 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.16878 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.61929 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.08044 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
61
Monitored processes
16
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | GyStation.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | "C:\Program Files\Gyazo\GyStation.exe" /start_resident | C:\Program Files\Gyazo\GyStation.exe | Gyazo-4.3.tmp | ||||||||||||
User: admin Company: Nota Inc. Integrity Level: MEDIUM Description: GyStation Exit code: 0 Version: 4.3.0.0 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Gyazo\Gyazowin.exe" | C:\Program Files\Gyazo\Gyazowin.exe | Explorer.EXE | ||||||||||||
User: admin Company: Nota Inc. Integrity Level: MEDIUM Description: Gyazo: Screen Uploader Exit code: 0 Version: 4.3.0.0 Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\AppData\Local\Temp\is-OA30H.tmp\Gyazo-4.3.tmp" /SL5="$2013A,10972952,141824,C:\Users\admin\AppData\Local\Temp\Gyazo-4.3.exe" /SPAWNWND=$20130 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-OA30H.tmp\Gyazo-4.3.tmp | Gyazo-4.3.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1584 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | GyStation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\Gyazo-4.3.exe" | C:\Users\admin\AppData\Local\Temp\Gyazo-4.3.exe | Explorer.EXE | ||||||||||||
User: admin Company: Nota Inc. Integrity Level: MEDIUM Description: Gyazo Setup Exit code: 0 Version: 4.3.0.0 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Gyazo\Gyazowin.exe" /ltt | C:\Program Files\Gyazo\Gyazowin.exe | — | GyStation.exe | |||||||||||
User: admin Company: Nota Inc. Integrity Level: MEDIUM Description: Gyazo: Screen Uploader Exit code: 0 Version: 4.3.0.0 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Internet Explorer\iexplore.exe" https://gyazo.com/7a9c0800475fff037e4ff437a37d7056?token=e4f5a891fabc8a680b1d74be90c213e8 | C:\Program Files\Internet Explorer\iexplore.exe | Gyazowin.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2656 | "C:\Users\admin\AppData\Local\Temp\Gyazo-4.3.exe" /SPAWNWND=$20130 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\Gyazo-4.3.exe | Gyazo-4.3.tmp | ||||||||||||
User: admin Company: Nota Inc. Integrity Level: HIGH Description: Gyazo Setup Exit code: 0 Version: 4.3.0.0 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Gyazo\GyStation.exe" /balloon "Welcome to Gyazo!@Left click the icon then drag to capture, right click for settings." | C:\Program Files\Gyazo\GyStation.exe | — | Gyazo-4.3.tmp | |||||||||||
User: admin Company: Nota Inc. Integrity Level: MEDIUM Description: GyStation Exit code: 0 Version: 4.3.0.0 Modules
| |||||||||||||||
Total events
29 923
Read events
29 418
Write events
497
Delete events
8
Modification events
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B80500008218C2D79F51D801 | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 966609508CCCC6A106B0BC522E2747E2670D5B4CA61E04A6F34989804598D45B | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Gyazo\Gyazowin.exe | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 00D9FB19A4789D1496031633EE5C5B68850603F68325DCD949FE02BD25BB539C | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Gyazo |
Value: | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{6DB8C365-E719-4BA5-9594-10DFC244D3FD}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{6DB8C365-E719-4BA5-9594-10DFC244D3FD}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Gyazo | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{6DB8C365-E719-4BA5-9594-10DFC244D3FD}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Gyazo\ | |||
| (PID) Process: | (1464) Gyazo-4.3.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{6DB8C365-E719-4BA5-9594-10DFC244D3FD}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Gyazo | |||
Executable files
112
Suspicious files
31
Text files
87
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2072 | Gyazo-4.3.exe | C:\Users\admin\AppData\Local\Temp\is-O164P.tmp\Gyazo-4.3.tmp | executable | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\Gyazowin.exe | executable | |
MD5:— | SHA256:— | |||
| 2656 | Gyazo-4.3.exe | C:\Users\admin\AppData\Local\Temp\is-OA30H.tmp\Gyazo-4.3.tmp | executable | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\is-UQTDU.tmp | executable | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\is-PIUME.tmp | executable | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\GyazoGIF.exe | executable | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\GyazoReplay.exe.config | xml | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\is-LPTEK.tmp | xml | |
MD5:— | SHA256:— | |||
| 1464 | Gyazo-4.3.tmp | C:\Program Files\Gyazo\is-DVCSQ.tmp | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
72
DNS requests
28
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3296 | GyOnboarding.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAwIlmU1uUKpc1Jl5Pl1QLw%3D | US | der | 471 b | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgSiyNv5x8fBIAAAAABooL | US | der | 472 b | whitelisted |
2460 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTubeiRal9hlMRbT70r8I4mClph2gQUEsmImy%2FJRHp9EvHfQANCmJLHJNYCEArazY9HXCOq19XmaUmN1Gg%3D | US | der | 471 b | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3296 | GyOnboarding.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
860 | GyStation.exe | 142.250.186.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3296 | GyOnboarding.exe | 35.186.213.112:443 | gyazo.com | Google Inc. | US | suspicious |
3296 | GyOnboarding.exe | 92.123.194.121:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | malicious |
3296 | GyOnboarding.exe | 142.250.185.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3296 | GyOnboarding.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
3296 | GyOnboarding.exe | 69.16.175.10:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
— | — | 104.244.42.3:443 | analytics.twitter.com | Twitter Inc. | US | suspicious |
3296 | GyOnboarding.exe | 104.244.42.133:443 | t.co | Twitter Inc. | US | suspicious |
3296 | GyOnboarding.exe | 92.123.225.18:443 | use.typekit.net | Akamai International B.V. | — | malicious |
3296 | GyOnboarding.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
gyazo.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
assets2.gyazo.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
code.jquery.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
cdn.mxpnl.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3296 | GyOnboarding.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |