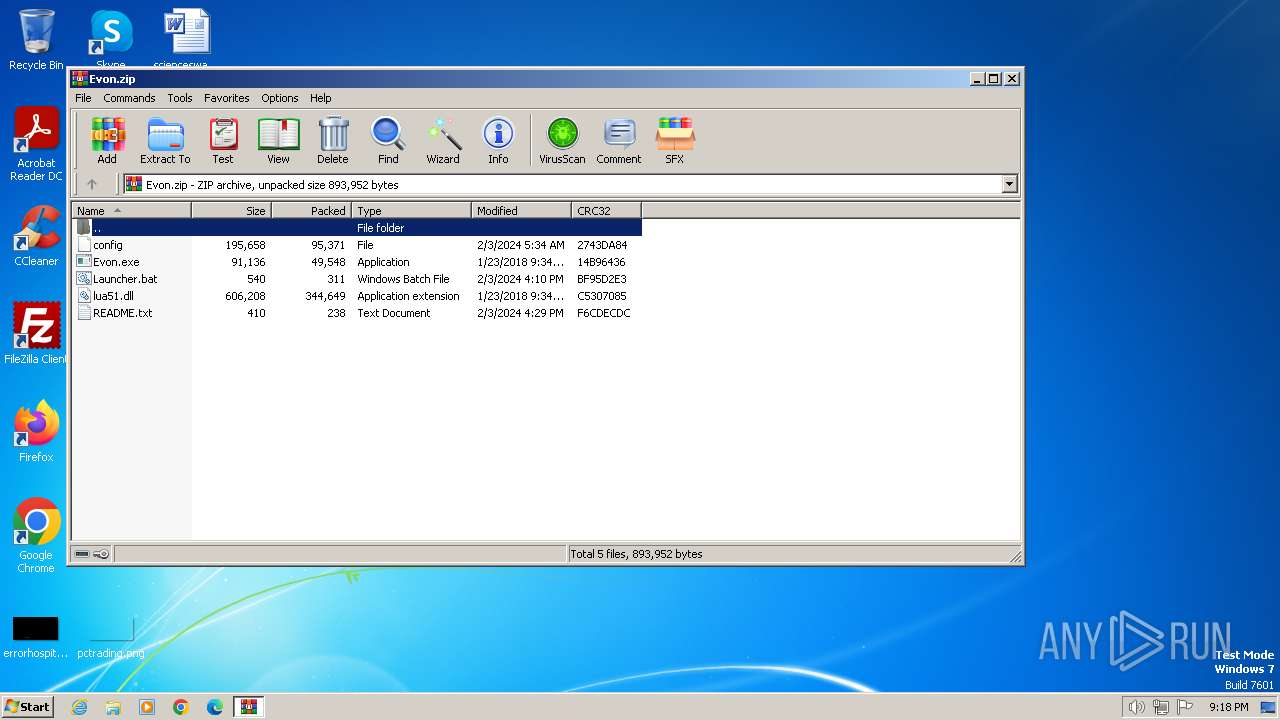
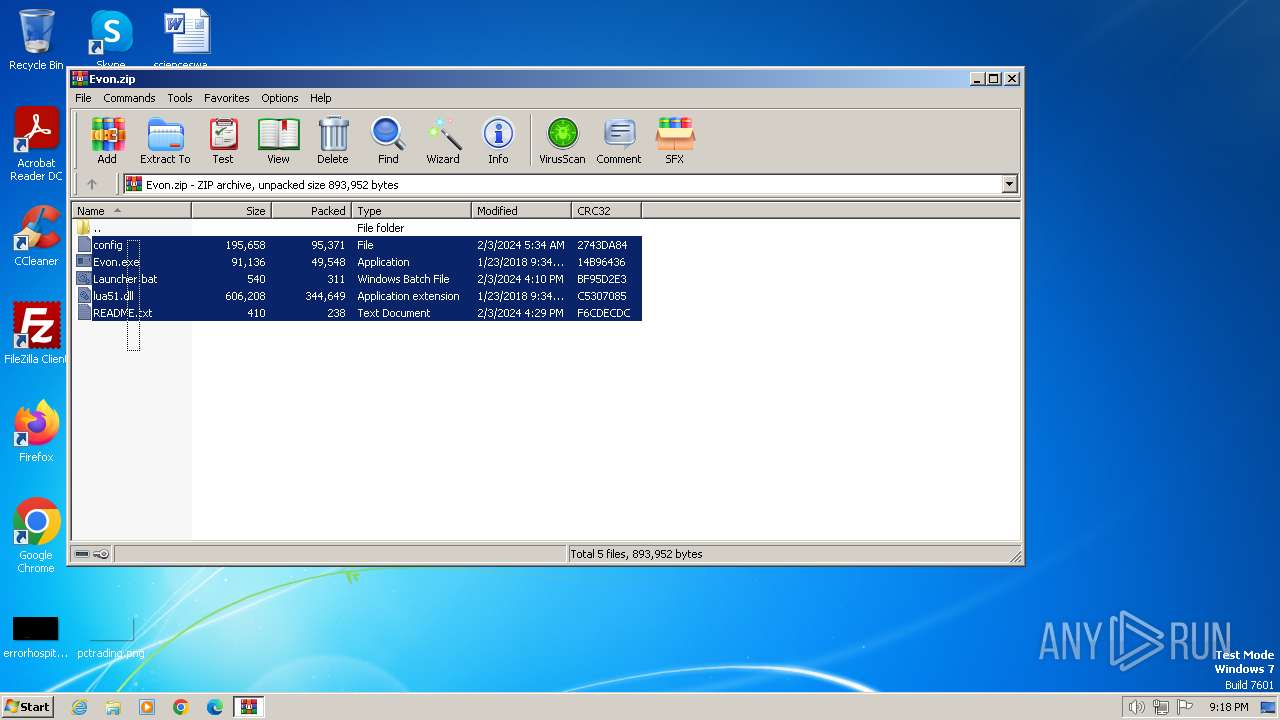
| File name: | Evon.zip |
| Full analysis: | https://app.any.run/tasks/1d111fa1-6095-483e-a667-b2810f8c75ee |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2024, 21:17:57 |
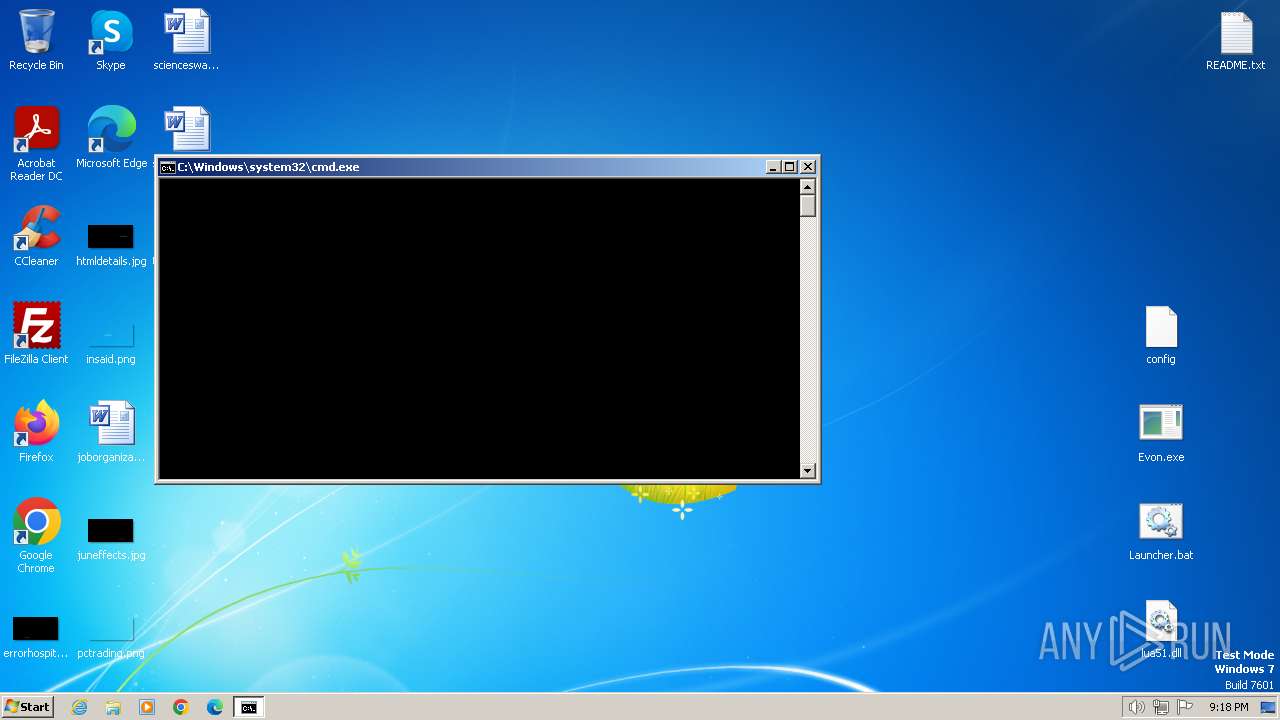
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 55421C59CBE012EA9FD6FFB058D5CB87 |
| SHA1: | 58A53602493596635DC4105C8D1912CEF6E0008A |
| SHA256: | D83482AF56DC082F48CE5AE70CE9E5DC8E7ADF66EC00492B78C5BAE4F8B20C00 |
| SSDEEP: | 24576:iF0RAA4XfalZoskVSSmGSJFN/qS7r78pTLDdhAgKE:iF0RAA4XylZoskVSWSJFN/qS7XeTLDdp |
MALICIOUS
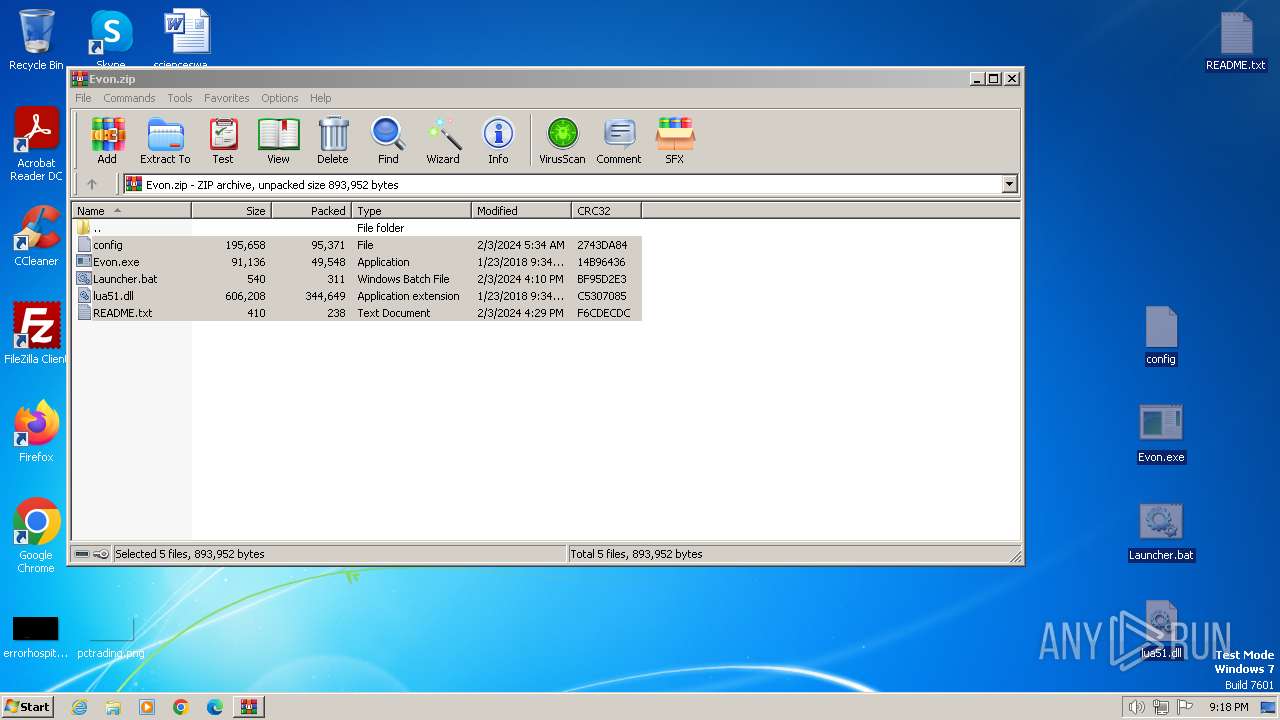
Drops the executable file immediately after the start
- WinRAR.exe (PID: 572)
- Evon.exe (PID: 3584)
SUSPICIOUS
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 1344)
- cmd.exe (PID: 2764)
The process executes VB scripts
- cmd.exe (PID: 1344)
Reads the Internet Settings
- cmd.exe (PID: 1344)
- wscript.exe (PID: 1408)
- Evon.exe (PID: 3584)
Executing commands from a ".bat" file
- wscript.exe (PID: 1408)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1408)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1408)
Executable content was dropped or overwritten
- Evon.exe (PID: 3584)
Connects to the server without a host name
- Evon.exe (PID: 3584)
Checks for external IP
- Evon.exe (PID: 3584)
Reads security settings of Internet Explorer
- Evon.exe (PID: 3584)
Reads settings of System Certificates
- Evon.exe (PID: 3584)
Checks Windows Trust Settings
- Evon.exe (PID: 3584)
INFO
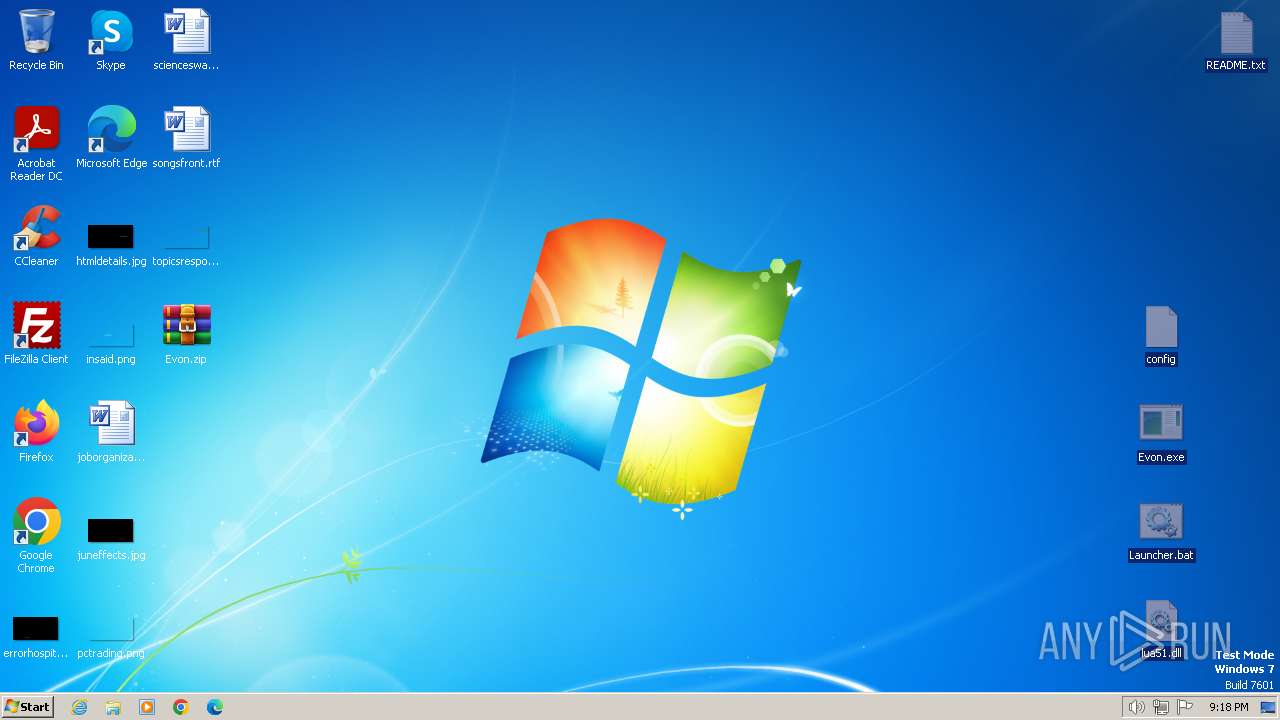
Manual execution by a user
- cmd.exe (PID: 1344)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 572)
Checks supported languages
- Evon.exe (PID: 3584)
Reads the computer name
- Evon.exe (PID: 3584)
Checks proxy server information
- Evon.exe (PID: 3584)
Creates files or folders in the user directory
- Evon.exe (PID: 3584)
Reads the machine GUID from the registry
- Evon.exe (PID: 3584)
Creates files in the program directory
- Evon.exe (PID: 3584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:02:03 08:34:20 |
| ZipCRC: | 0x2743da84 |
| ZipCompressedSize: | 95371 |
| ZipUncompressedSize: | 195658 |
| ZipFileName: | config |
Total processes
51
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Evon.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1344 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Launcher.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1408 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\getadmin.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2088 | "C:\Windows\system32\cacls.exe" "C:\Windows\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\Desktop\Launcher.bat | C:\Windows\System32\cmd.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3396 | "C:\Windows\system32\cacls.exe" "C:\Windows\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3584 | Evon.exe config | C:\Users\admin\Desktop\Evon.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3888 | schtasks /create /sc daily /st 13:27 /f /tn WindowsSetup /tr "C:/Windows/System32/oobe/Setup.exe" /rl highest | C:\Windows\System32\schtasks.exe | — | Evon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 009
Read events
4 942
Write events
67
Delete events
0
Modification events
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
4
Suspicious files
7
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 572 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa572.37286\lua51.dll | executable | |
MD5:3DFF7448B43FCFB4DC65E0040B0FFB88 | SHA256:FF976F6E965E3793E278FA9BF5E80B9B226A0B3932B9DA764BFFC8E41E6CDB60 | |||
| 1344 | cmd.exe | C:\Users\admin\AppData\Local\Temp\getadmin.vbs | text | |
MD5:D14A6C18536B08C2D91CC10129CEC2CA | SHA256:88F0E55BE41422957E8F4FEC8CAF0F9ED4E68D1F0290171BA8F4BD26C19FA17D | |||
| 3584 | Evon.exe | C:\ProgramData\OWYsN2YsN2YsYTAsOWUsODYsOGMsOTYsNjQsN2Ms\lua51.dll | executable | |
MD5:3DFF7448B43FCFB4DC65E0040B0FFB88 | SHA256:FF976F6E965E3793E278FA9BF5E80B9B226A0B3932B9DA764BFFC8E41E6CDB60 | |||
| 3584 | Evon.exe | C:\ProgramData\OWYsN2YsN2YsYTAsOWUsODYsOGMsOTYsNjQsN2Ms\config | binary | |
MD5:71FCF9D697616F36C76F7503ABFAFE48 | SHA256:C0826513F3AF80B1B21793B0D022263FF54E1F751B3F71D70B30CA35BFAF0CE2 | |||
| 3584 | Evon.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\json[1].json | binary | |
MD5:A45F35A8993AD7F42AE01DBCC40E61FE | SHA256:AAE2DEA15EF19DC5A25E4BAD9C2621BC61C6A56D08095209F9185390DACA0091 | |||
| 572 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa572.37286\Launcher.bat | text | |
MD5:8A73C96FF34B3781522DD9993F483E95 | SHA256:800B892D045AA373322D1A21F83A2616BAAE2A5C468096C502114F975B3C7271 | |||
| 3584 | Evon.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:A91E471FD4BB1839415D07E39E61BA1C | SHA256:ADB45670CDBB7AA6624529D978010E807A83D3ADF0F7526B948C7CD38DCE9419 | |||
| 572 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa572.37286\config | binary | |
MD5:71FCF9D697616F36C76F7503ABFAFE48 | SHA256:C0826513F3AF80B1B21793B0D022263FF54E1F751B3F71D70B30CA35BFAF0CE2 | |||
| 3584 | Evon.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EBC50DF58B54125747C49C76C05AD7F1 | SHA256:E622EC232A6755A34DC8603BEAF6CD6CE6B5FDF5B463A427CC3D1297BF19BBD4 | |||
| 3584 | Evon.exe | C:\Users\admin\Pictures\90059C37132041A4B58D2B75A9850D2F | binary | |
MD5:784FC1E238F54B7C339ABBB8E397F32F | SHA256:28E5EF9F1A67593F4FE9D5B2638111388549CAE31AFB55409A2D624B694B33A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
10
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3584 | Evon.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=query,status,countryCode,city,timezone | US | binary | 108 b | unknown |
— | — | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?346f4b31e5a38a22 | GB | — | — | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?89bca2e7018c82c0 | GB | compressed | 65.2 Kb | unknown |
3584 | Evon.exe | PUT | 200 | 185.103.100.158:80 | http://185.103.100.158/loader/screen/OWYsN2YsN2YsYTAsOWUsODYsOGMsOTYsNjQsN2Ms | RU | binary | 696 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3584 | Evon.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
3584 | Evon.exe | 88.221.125.143:443 | www.microsoft.com | AKAMAI-AS | DE | unknown |
3584 | Evon.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3584 | Evon.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3584 | Evon.exe | 185.103.100.158:80 | — | OOO FREEnet Group | RU | unknown |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
www.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3584 | Evon.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3584 | Evon.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |