| File name: | Agent_Install.exe |
| Full analysis: | https://app.any.run/tasks/d623857c-17f1-4b2e-845a-03994e14c9bc |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2020, 11:24:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7E8384B6B80C8079F5A854DB7B72D849 |
| SHA1: | D5FD6F3CF1829144877897107F646B42E4E28C47 |
| SHA256: | D8311D9B80C758656686866AEC5FB656C394BBE88130D73D5CF24436464A218A |
| SSDEEP: | 98304:rsiIeqB3UL15suawUvnM+B6XnpiJCRIbat3H4GS9GiM0N+iNXtSwvnu7RF:rsi03Y8uafM+B63QJCMat3HpIGb0NRNK |
MALICIOUS
Loads dropped or rewritten executable
- Agent_Install.exe (PID: 3336)
- LTSvcMon.exe (PID: 4060)
- LTSVC.exe (PID: 3032)
- LabTechRemoteAgent.exe (PID: 1812)
- regsvr32.exe (PID: 1400)
- LTTray.exe (PID: 3860)
- LTSvcMon.exe (PID: 3540)
Application was dropped or rewritten from another process
- Agent_Install.exe (PID: 3336)
- LabTechRemoteAgent.exe (PID: 3664)
- LTSvcMon.exe (PID: 4060)
- LTSVC.exe (PID: 3032)
- LabTechRemoteAgent.exe (PID: 2056)
- LabTechRemoteAgent.exe (PID: 1812)
- LTTray.exe (PID: 3860)
- LTSvcMon.exe (PID: 3540)
Changes the autorun value in the registry
- LabTechRemoteAgent.exe (PID: 3664)
Starts NET.EXE for service management
- MsiExec.exe (PID: 3732)
- CMD.exe (PID: 2376)
Changes settings of System certificates
- LTSvcMon.exe (PID: 4060)
- LTSVC.exe (PID: 3032)
- LTSvcMon.exe (PID: 3540)
- msiexec.exe (PID: 2820)
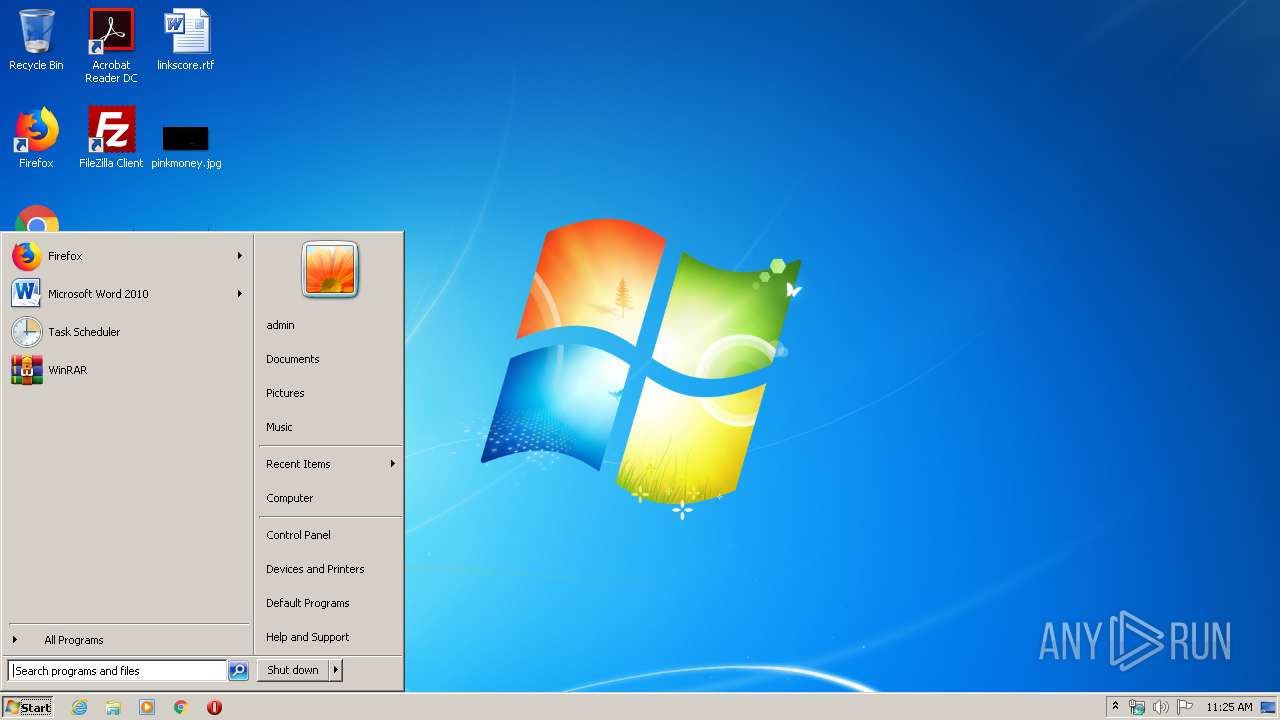
LABTECH was detected
- LTSVC.exe (PID: 3032)
Connects to CnC server
- LTSVC.exe (PID: 3032)
Registers / Runs the DLL via REGSVR32.EXE
- LTSVC.exe (PID: 3032)
SUSPICIOUS
Executable content was dropped or overwritten
- Agent_Install.exe (PID: 3680)
- Agent_Install.exe (PID: 3336)
- LabTechRemoteAgent.exe (PID: 3664)
- msiexec.exe (PID: 2820)
- LTSVC.exe (PID: 3032)
- LabTechRemoteAgent.exe (PID: 1812)
Starts itself from another location
- Agent_Install.exe (PID: 3336)
Executed as Windows Service
- vssvc.exe (PID: 536)
- LTSVC.exe (PID: 3032)
- LTSvcMon.exe (PID: 4060)
- LTSvcMon.exe (PID: 3540)
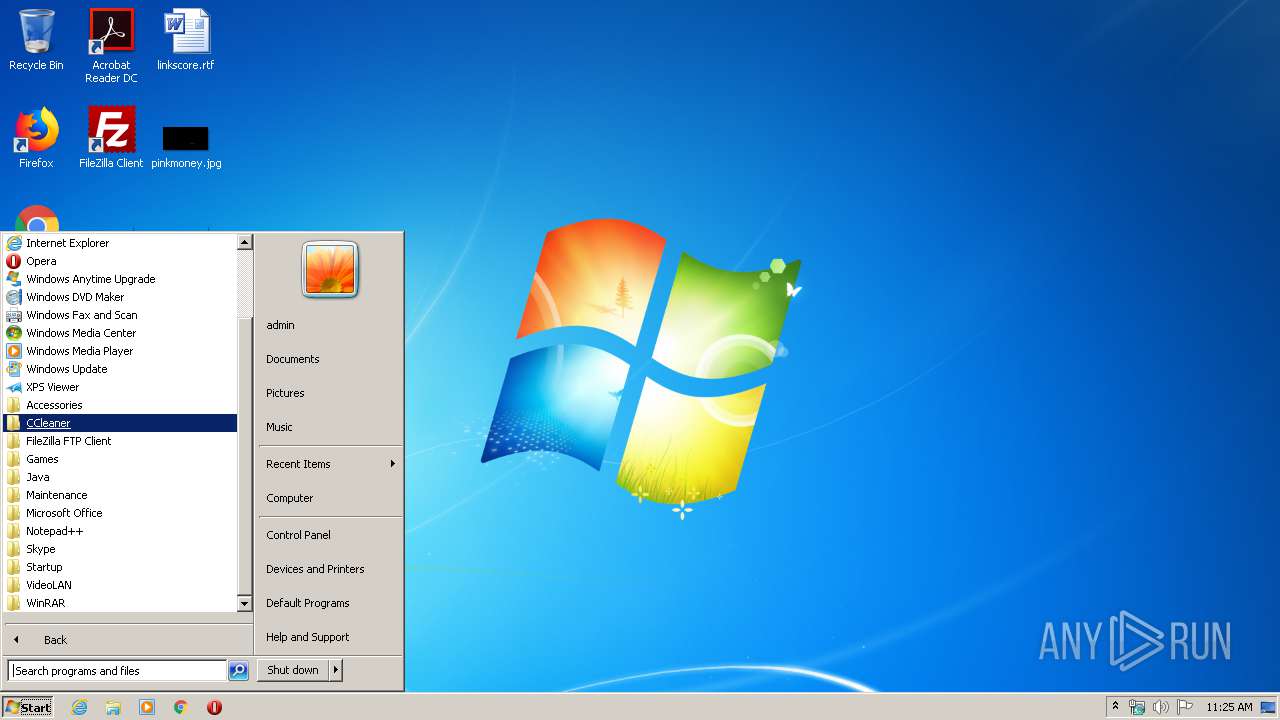
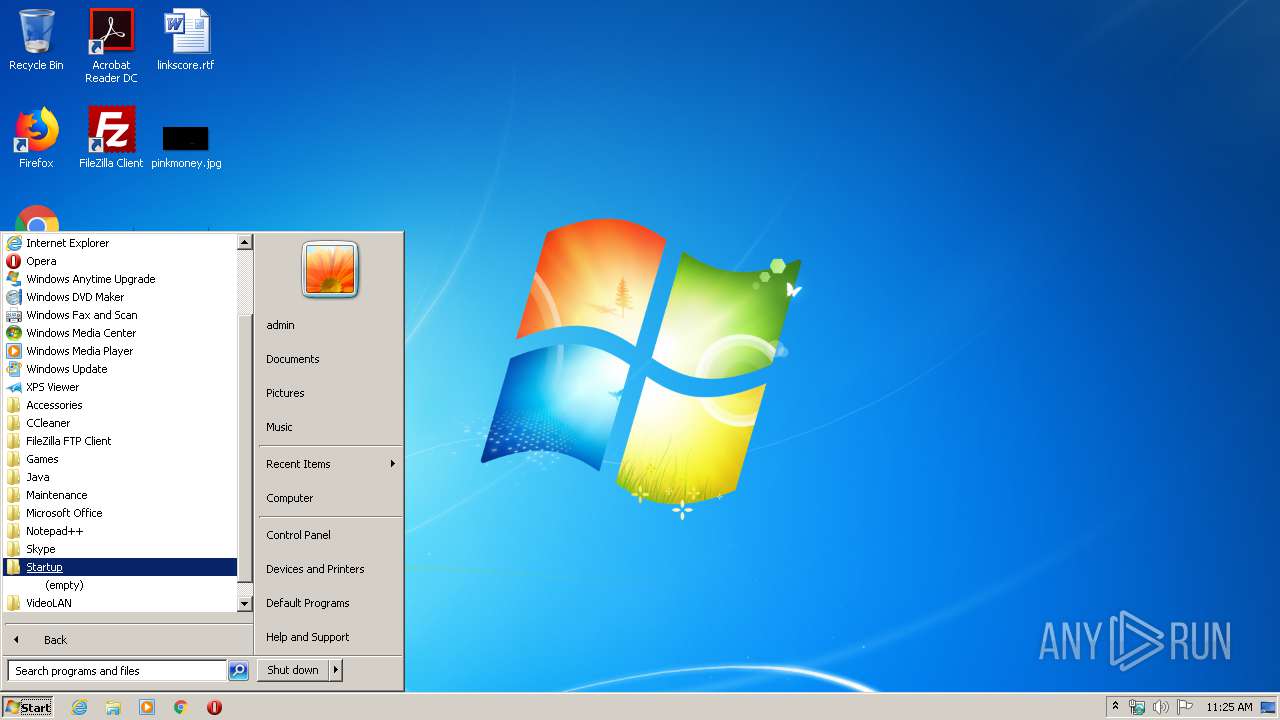
Searches for installed software
- LabTechRemoteAgent.exe (PID: 3664)
Creates files in the program directory
- LabTechRemoteAgent.exe (PID: 3664)
Creates a software uninstall entry
- LabTechRemoteAgent.exe (PID: 3664)
Creates files in the Windows directory
- msiexec.exe (PID: 2820)
- LTSVC.exe (PID: 3032)
- MsiExec.exe (PID: 3732)
- LTSvcMon.exe (PID: 3540)
Adds / modifies Windows certificates
- LTSVC.exe (PID: 3032)
- LTSvcMon.exe (PID: 4060)
- LTSvcMon.exe (PID: 3540)
- msiexec.exe (PID: 2820)
Removes files from Windows directory
- LTSVC.exe (PID: 3032)
Reads Environment values
- LTSVC.exe (PID: 3032)
- LTSvcMon.exe (PID: 3540)
Connects to server without host name
- LTSVC.exe (PID: 3032)
Starts CMD.EXE for commands execution
- LTSVC.exe (PID: 3032)
Application launched itself
- LabTechRemoteAgent.exe (PID: 2056)
Creates or modifies windows services
- LTSVC.exe (PID: 3032)
Creates COM task schedule object
- regsvr32.exe (PID: 1400)
Low-level read access rights to disk partition
- LTSVC.exe (PID: 3032)
Uses NETSH.EXE for network configuration
- CMD.exe (PID: 1448)
- CMD.exe (PID: 676)
- CMD.exe (PID: 2120)
- CMD.exe (PID: 2844)
- CMD.exe (PID: 3344)
- CMD.exe (PID: 3852)
- CMD.exe (PID: 3604)
- CMD.exe (PID: 3772)
- CMD.exe (PID: 1676)
- CMD.exe (PID: 2640)
- CMD.exe (PID: 3244)
- CMD.exe (PID: 3624)
- CMD.exe (PID: 2560)
- CMD.exe (PID: 3072)
- CMD.exe (PID: 3488)
- CMD.exe (PID: 3592)
- CMD.exe (PID: 1940)
- CMD.exe (PID: 2848)
- CMD.exe (PID: 2868)
- CMD.exe (PID: 4080)
- CMD.exe (PID: 3388)
- CMD.exe (PID: 3684)
- CMD.exe (PID: 3292)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 1500)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3976)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 740)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 536)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3732)
- MsiExec.exe (PID: 604)
Application launched itself
- msiexec.exe (PID: 2820)
Reads settings of System Certificates
- LTSVC.exe (PID: 3032)
Creates a software uninstall entry
- msiexec.exe (PID: 2820)
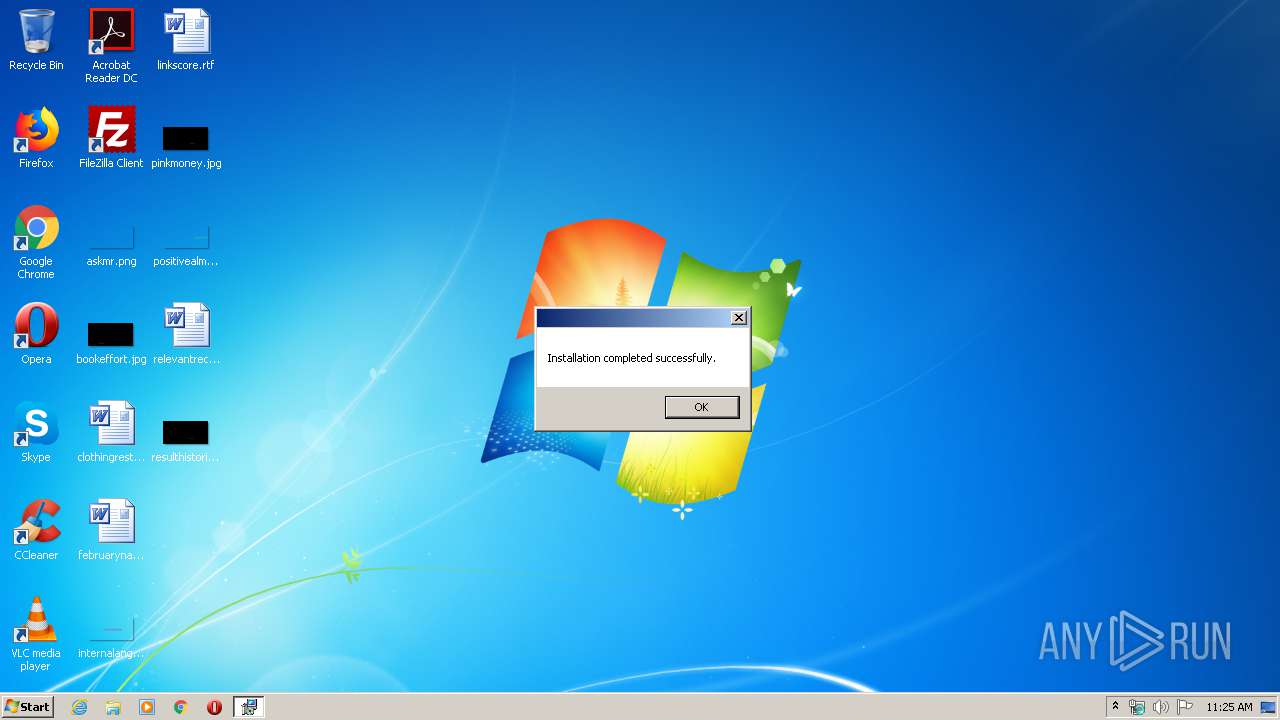
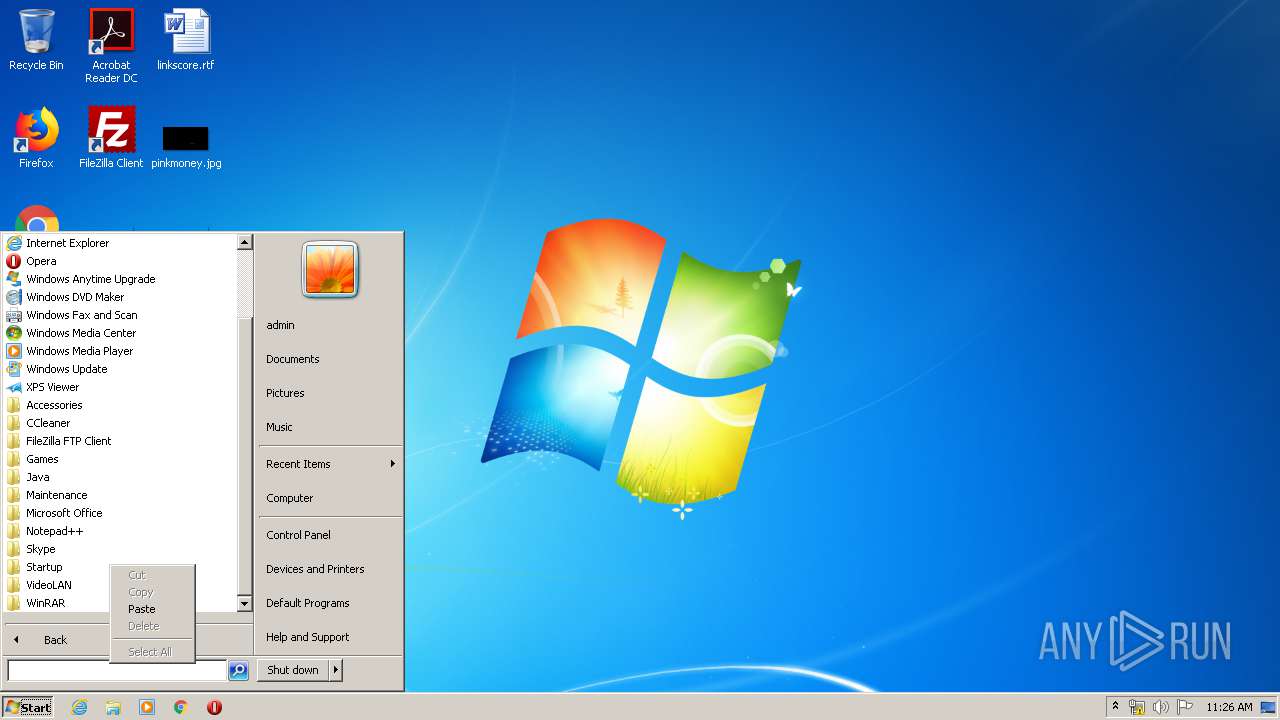
Manual execution by user
- verclsid.exe (PID: 840)
- LabTechRemoteAgent.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:28 19:25:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 301568 |
| InitializedDataSize: | 161280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e0c1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 20.0.81.0 |
| ProductVersionNumber: | 20.0.81.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ConnectWise, Inc. |
| FileDescription: | ConnectWise Automate Remote Agent |
| FileVersion: | 20.0.81 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ConnectWise, Inc.. All rights reserved. |
| OriginalFileName: | LabTechRemoteAgent.exe |
| ProductName: | ConnectWise Automate Remote Agent |
| ProductVersion: | 20.0.81 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Feb-2018 18:25:32 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ConnectWise, Inc. |
| FileDescription: | ConnectWise Automate Remote Agent |
| FileVersion: | 20.0.81 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ConnectWise, Inc.. All rights reserved. |
| OriginalFilename: | LabTechRemoteAgent.exe |
| ProductName: | ConnectWise Automate Remote Agent |
| ProductVersion: | 20.0.81 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 28-Feb-2018 18:25:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049827 | 0x00049A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55956 |
.rdata | 0x0004B000 | 0x0001EB34 | 0x0001EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11602 |
.data | 0x0006A000 | 0x00001740 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12305 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.742974 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.gfids | 0x0006E000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.01067 |
.rsrc | 0x0006F000 | 0x00003A78 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52973 |
.reloc | 0x00073000 | 0x00003D8C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.7698 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
183
Monitored processes
102
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | find /i "Listening" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | netstat -ano | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | C:\Windows\system32\MsiExec.exe -Embedding 5EDC763151BA8134DE0FCF26C1FC5DDA M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 676 | "CMD.exe" /c netsh advfirewall firewall Delete rule name="Allow Local VNC" | C:\Windows\system32\CMD.exe | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 740 | "cmd.exe" /C " netstat -ano | find "42000"| find /i "Listening" " | C:\Windows\system32\cmd.exe | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 840 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | C:\Windows\system32\net1 stop LTService | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1116 | "C:\Windows\System32\net.exe" stop LTService | C:\Windows\System32\net.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1116 | find /i "Listening" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 152
Read events
1 222
Write events
2 897
Delete events
33
Modification events
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3336) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
131
Suspicious files
16
Text files
243
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{B37EEC5F-529B-4ACB-BE05-00E22B10273C}\.cr\Agent_Install.exe | executable | |
MD5:— | SHA256:— | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\BootstrapperCore.dll | executable | |
MD5:— | SHA256:— | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\1028\mbapreq.wxl | xml | |
MD5:52D0DA3F25188F572B5F552C8EFB6F46 | SHA256:4BDE2A889BD1CA9C4EF83330BC4A3BCA6AED8BE570FB0654CC88A3DF65CE3135 | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\1035\mbapreq.wxl | xml | |
MD5:349706F77DF7CBB16E28BA520347734B | SHA256:7F416CE8D6CB33FD4F42F03062100F862A7561F87A5D93EDB0DB1DB60701BEF8 | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\mbapreq.wxl | xml | |
MD5:1D1E181B9DD086178F694E92E8E3D1FC | SHA256:3CABE8C4EB315967EABCC10795474B2838057E6320F723713C6DBE9F596826A7 | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\mbahost.dll | executable | |
MD5:4EA0CEC51846C3FAFA500925C55C827B | SHA256:19AA18857964BA91CDB7FD60566EF8CC026FAD27AE29E08305CC1016E5F5592A | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\mbapreq.thm | xml | |
MD5:360DB6C11D34BF83B92E736185338E2B | SHA256:F647445A1496B758D400B9AB5A0F4C6EBA86C5B7FEF4D047C4E98DA4A2D1F294 | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\mbapreq.dll | executable | |
MD5:93D3140599B9B4D21365E8B97D3FFDC6 | SHA256:362ABB424E424581113F5F04F4365A0957280453EB8C119ED3535DAB537D7498 | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\1030\mbapreq.wxl | xml | |
MD5:D9CB9B0C3953623300F2880798431B1B | SHA256:07855A13CBB7F2E2DD73663524478BE8F00605A66A9697A4A1342D4F84197A6B | |||
| 3336 | Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{32297C86-B152-4BA0-9EA5-4315BE9DBDF8}\.ba\1031\mbapreq.wxl | xml | |
MD5:0685B7B1ACB1BD573FA004CEA72F563C | SHA256:E6CF56E46ECC04D05877EF811074E67E18442CF42366DF513DDF51FF30D45342 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
37
DNS requests
3
Threats
88
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3032 | LTSVC.exe | GET | — | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.Aspx?DepCheck=1&DependancyID=14 | NZ | — | — | suspicious |
3032 | LTSVC.exe | GET | — | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.Aspx?DepCheck=1&DependancyID=107 | NZ | — | — | suspicious |
3032 | LTSVC.exe | GET | — | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.Aspx?DepCheck=1&DependancyID=-715 | NZ | — | — | suspicious |
3032 | LTSVC.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsextendcodesignsha2g3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQ3DAV9N6WelMGCzSTdNIqjdmfHiAQU3CxYLCpvNS2feZWoSF3EbT5Tv7kCDBWcvWHUaDWCegib0A%3D%3D | US | der | 1.55 Kb | whitelisted |
3032 | LTSVC.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDkgbagepQkweqv7zzfEP | US | der | 1.48 Kb | whitelisted |
3032 | LTSVC.exe | GET | 200 | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.Aspx?DepCheck=1&DependancyID=9 | NZ | image | 91.3 Kb | suspicious |
3032 | LTSVC.exe | GET | 200 | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.Aspx?DepCheck=1&DependancyID=106 | NZ | image | 316 Kb | suspicious |
3032 | LTSVC.exe | POST | 200 | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.aspx?DEPS | NZ | text | 1.72 Kb | suspicious |
3032 | LTSVC.exe | GET | 200 | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.Aspx?DepCheck=1&DependancyID=6 | NZ | image | 28.6 Kb | suspicious |
3032 | LTSVC.exe | GET | 200 | 58.84.239.94:80 | http://58.84.239.94/LabTech/Agent.Aspx?DepCheck=1&DependancyID=2 | NZ | image | 618 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | Agent_Install.exe | 58.84.239.94:80 | overwatch.itroom.co.nz | nzwireless LTD | NZ | suspicious |
3032 | LTSVC.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3032 | LTSVC.exe | 58.84.239.94:80 | overwatch.itroom.co.nz | nzwireless LTD | NZ | suspicious |
3032 | LTSVC.exe | 58.84.239.94:8040 | overwatch.itroom.co.nz | nzwireless LTD | NZ | suspicious |
3540 | LTSvcMon.exe | 58.84.239.94:443 | overwatch.itroom.co.nz | nzwireless LTD | NZ | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp2.globalsign.com |
| whitelisted |
overwatch.itroom.co.nz |
| suspicious |
connect.itroom.co.nz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] LabTech Remote Control |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] LabTech Remote Control |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] LabTech PC remote control session setup (BASE64 (Gzip)) |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] LabTech Remote Control Session Covert channel Activity |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] JPEG_File concatenate with Gzip (LabTech Remote Control Session Covert channel Activity) |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] LabTech Remote Control Session Covert channel Activity |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] JPEG_File concatenate with Gzip (LabTech Remote Control Session Covert channel Activity) |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] LabTech Remote Control Session Covert channel Activity |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] JPEG_File concatenate with Gzip (LabTech Remote Control Session Covert channel Activity) |
3032 | LTSVC.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] LabTech Remote Control Session Covert channel Activity |
37 ETPRO signatures available at the full report