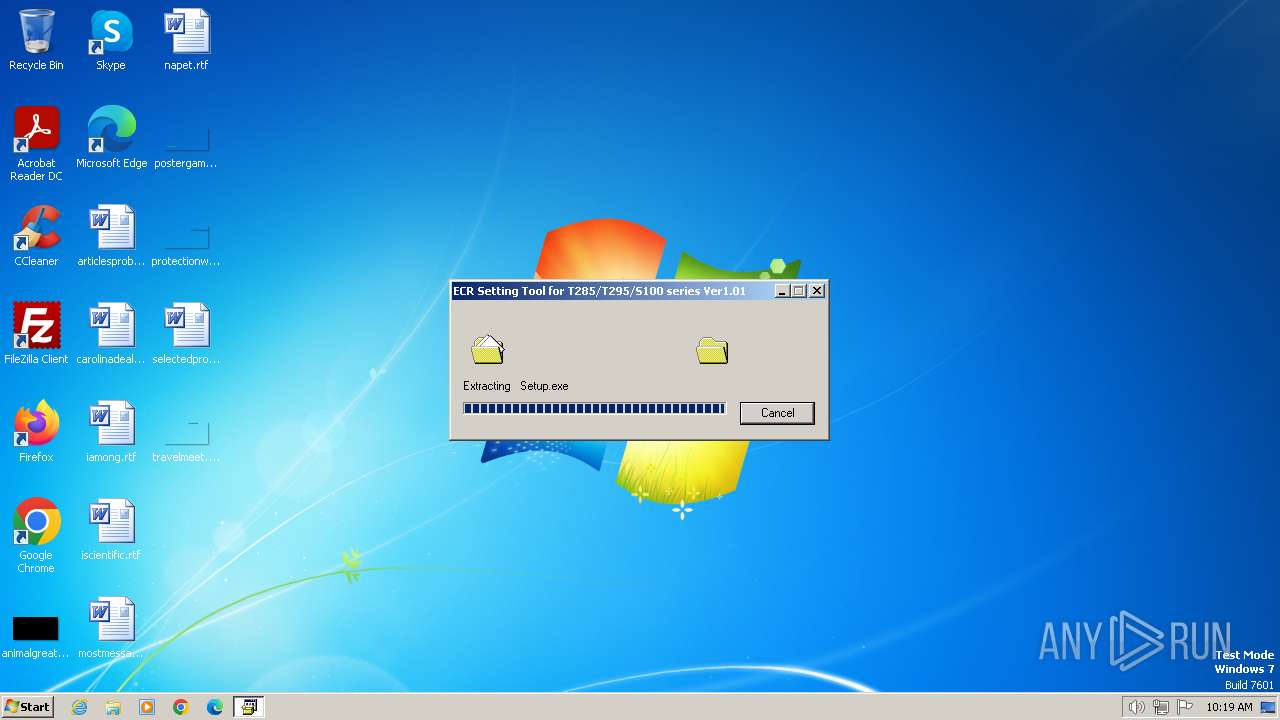
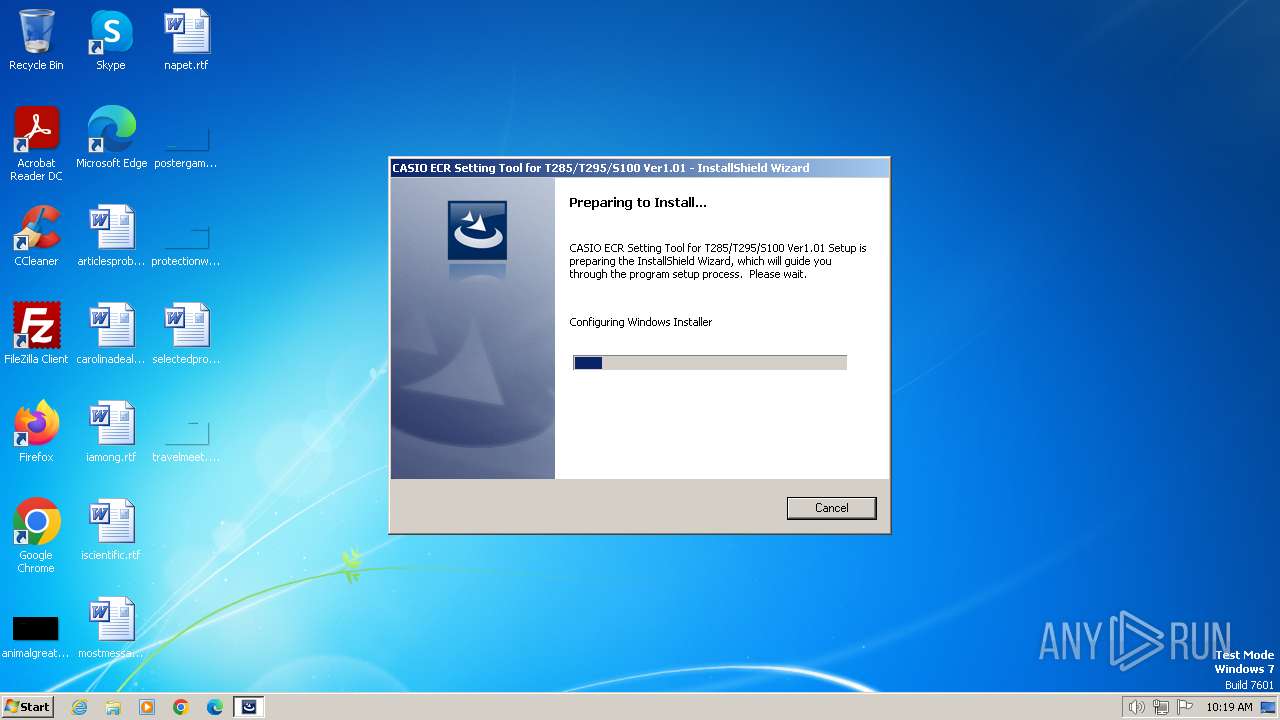
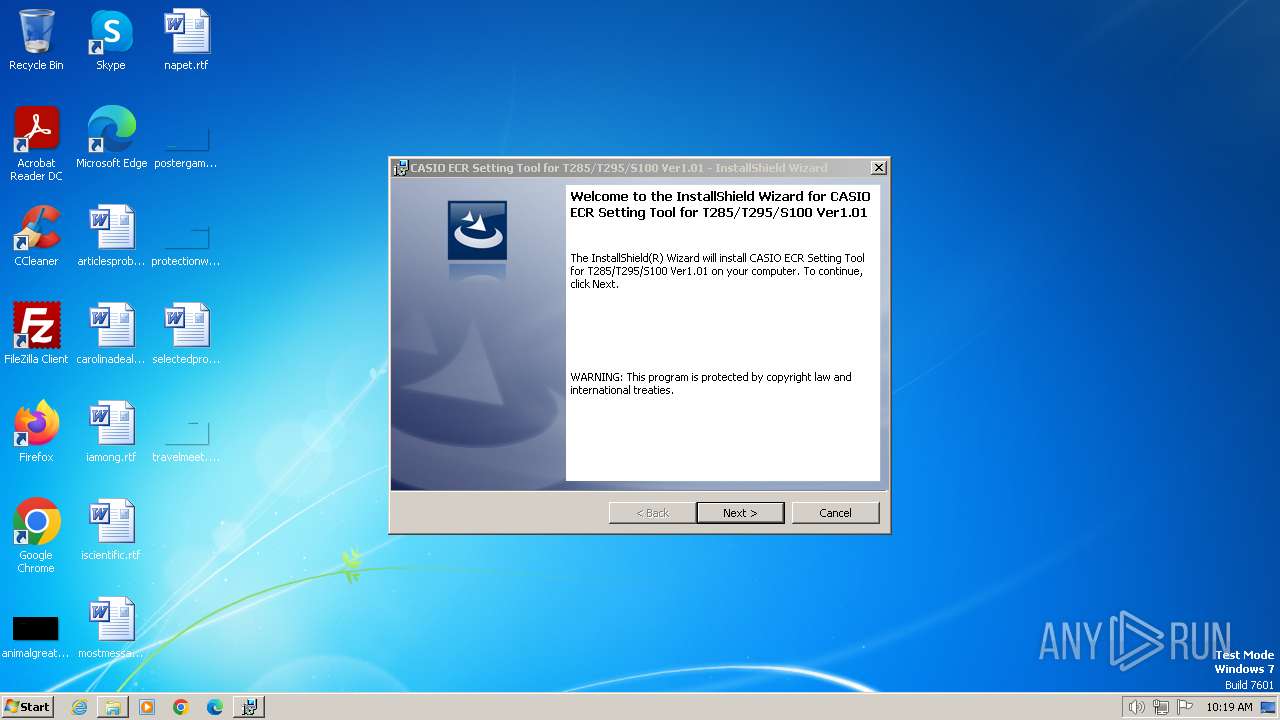
| File name: | EcrstSES100V1P01.EXE |
| Full analysis: | https://app.any.run/tasks/ff6c6164-fb5a-4e3f-b36b-b6d7255f14c3 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2024, 09:19:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 87BA64C8E8B5EFF12AE3EA662C8CA307 |
| SHA1: | E4EF305B832ADF1C60C705D67C08AB9AA13042D5 |
| SHA256: | D81DFD357953E2A0C1E925F0DE6F65FBCBCC5CAAE790A3F5041C31407E1671AA |
| SSDEEP: | 98304:eG264lCER93ukRWce7Qas5xpjqkaazhmNypVabGGF7tQ6I4kITiGBIHbIWHMF+48:Ym4vL/F/WMCudWRSHt |
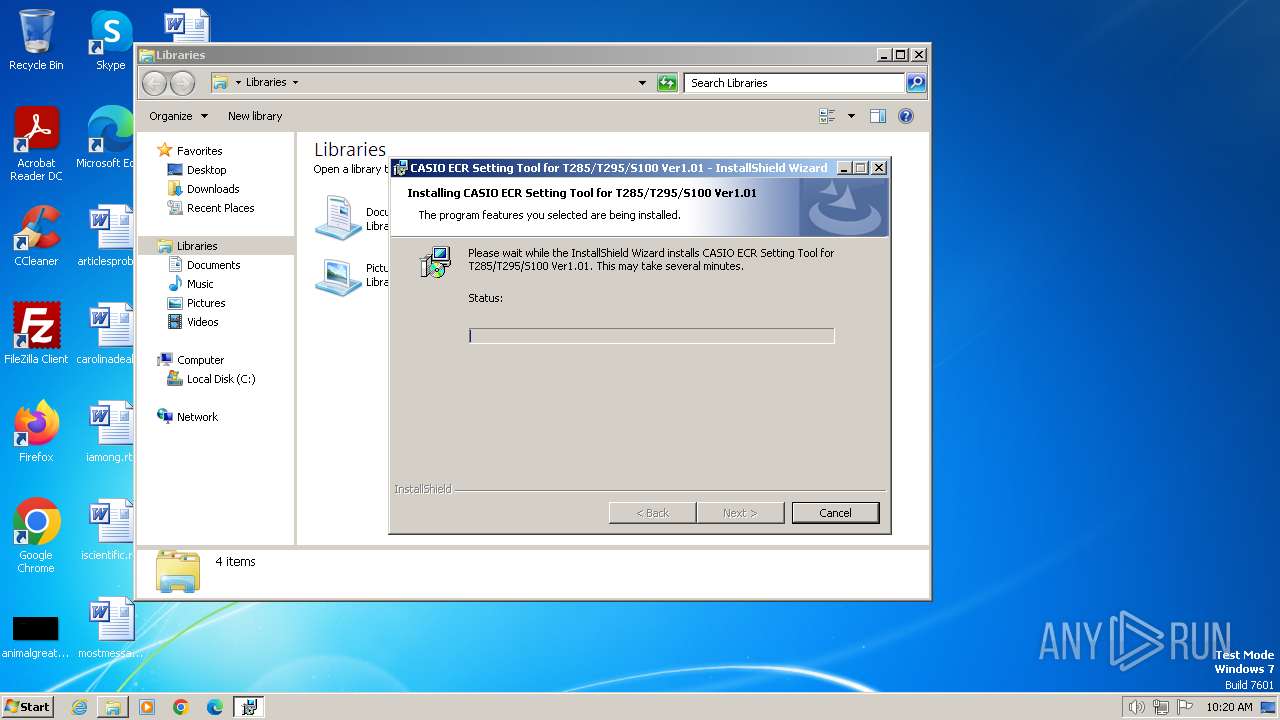
MALICIOUS
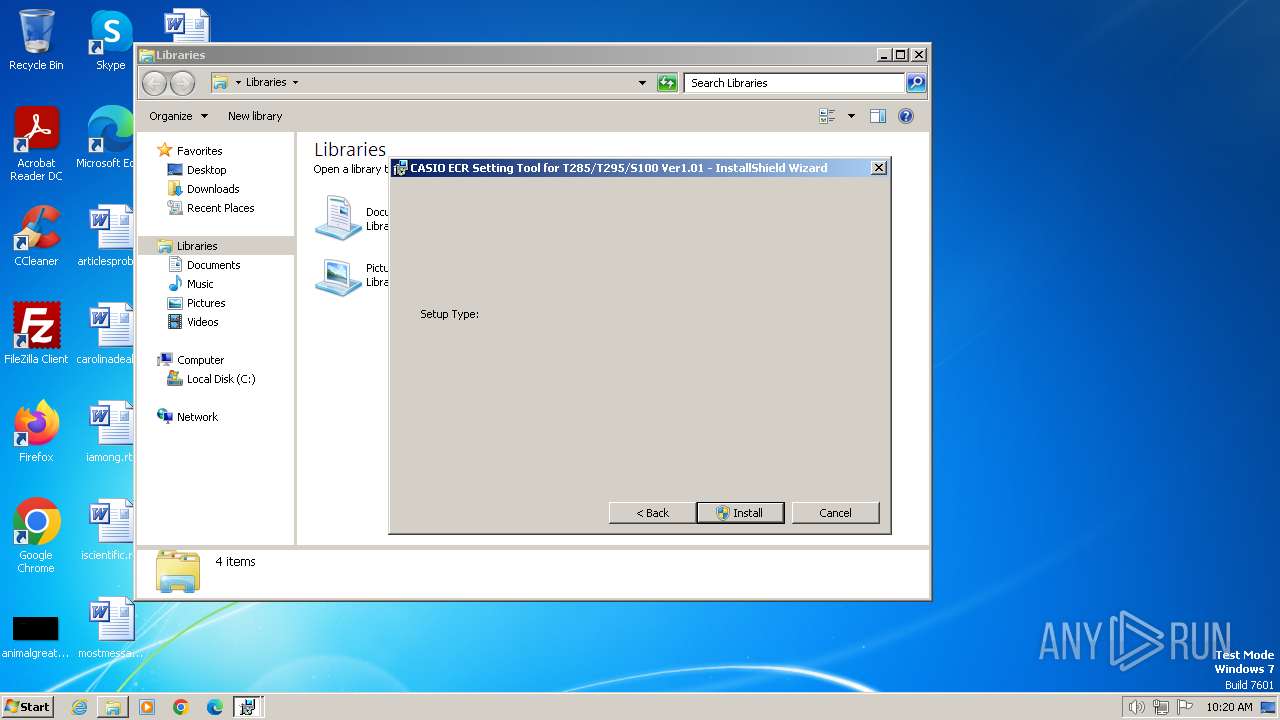
Drops the executable file immediately after the start
- EcrstSES100V1P01.EXE.exe (PID: 3384)
- msiexec.exe (PID: 3412)
Changes the autorun value in the registry
- EcrstSES100V1P01.EXE.exe (PID: 3384)
Creates a writable file in the system directory
- msiexec.exe (PID: 3412)
SUSPICIOUS
Process drops legitimate windows executable
- EcrstSES100V1P01.EXE.exe (PID: 3384)
- msiexec.exe (PID: 3412)
Starts a Microsoft application from unusual location
- EcrstSES100V1P01.EXE.exe (PID: 3384)
Executable content was dropped or overwritten
- EcrstSES100V1P01.EXE.exe (PID: 3384)
Executes as Windows Service
- VSSVC.exe (PID: 3164)
Checks Windows Trust Settings
- msiexec.exe (PID: 3412)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3412)
The process creates files with name similar to system file names
- msiexec.exe (PID: 3412)
INFO
Reads the computer name
- msiexec.exe (PID: 2748)
- Setup.exe (PID: 3332)
- msiexec.exe (PID: 3844)
- SE100ST.exe (PID: 3404)
- wmpnscfg.exe (PID: 2000)
- msiexec.exe (PID: 3412)
Checks supported languages
- msiexec.exe (PID: 2748)
- EcrstSES100V1P01.EXE.exe (PID: 3384)
- Setup.exe (PID: 3332)
- msiexec.exe (PID: 3412)
- msiexec.exe (PID: 3844)
- SE100IN.exe (PID: 4056)
- SE100ST.exe (PID: 3404)
- wmpnscfg.exe (PID: 2000)
Create files in a temporary directory
- Setup.exe (PID: 3332)
- EcrstSES100V1P01.EXE.exe (PID: 3384)
- msiexec.exe (PID: 3412)
- SE100ST.exe (PID: 3404)
Reads the software policy settings
- msiexec.exe (PID: 3568)
- msiexec.exe (PID: 3412)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2748)
- SE100ST.exe (PID: 3404)
- msiexec.exe (PID: 3844)
- msiexec.exe (PID: 3412)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3412)
- msiexec.exe (PID: 3568)
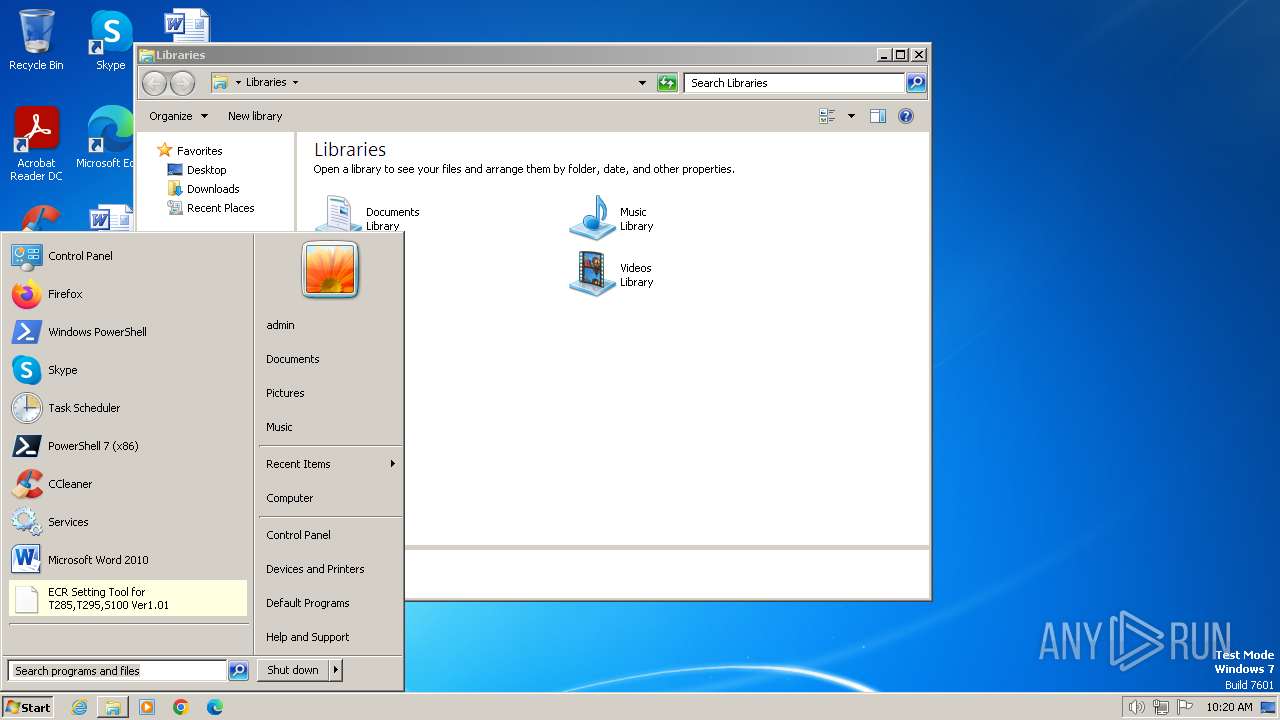
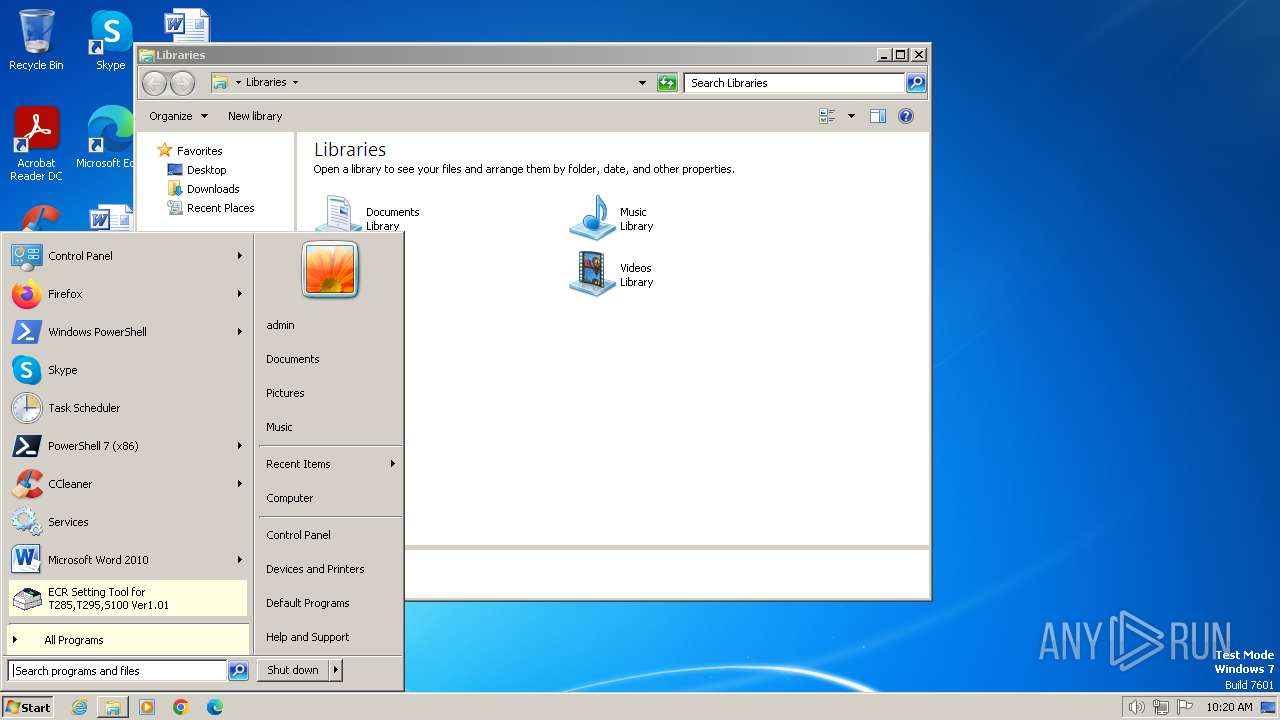
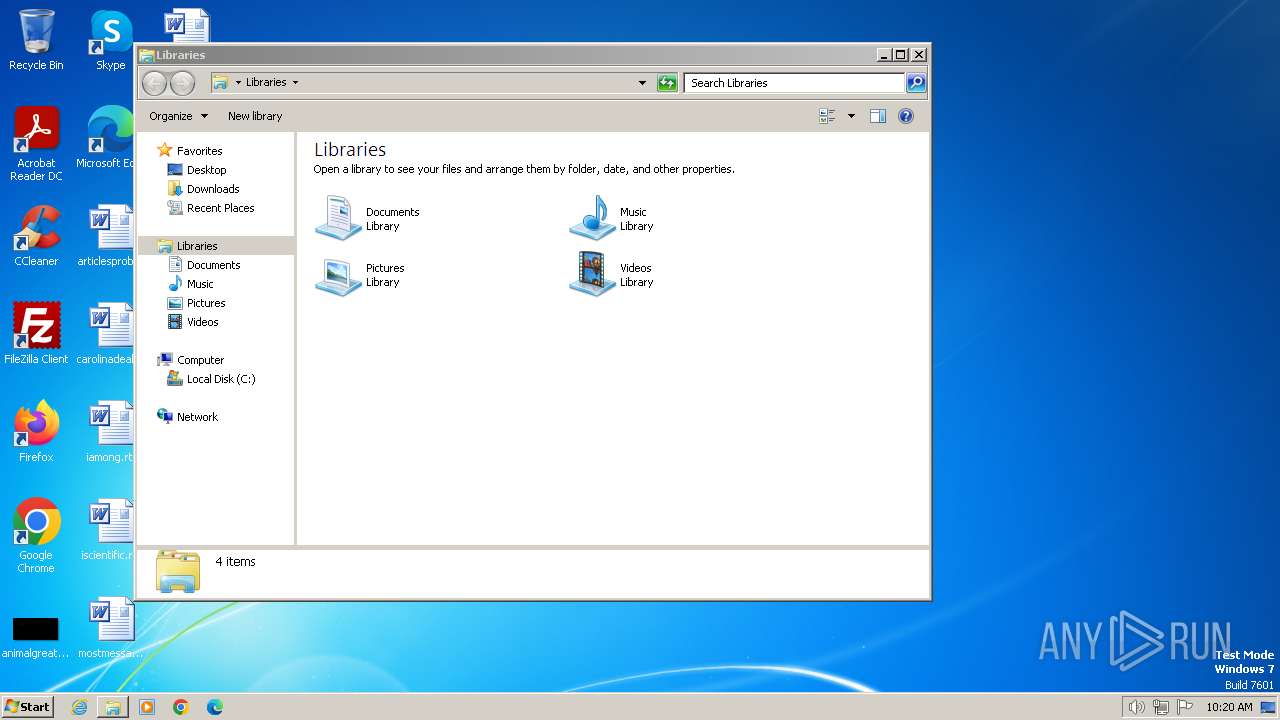
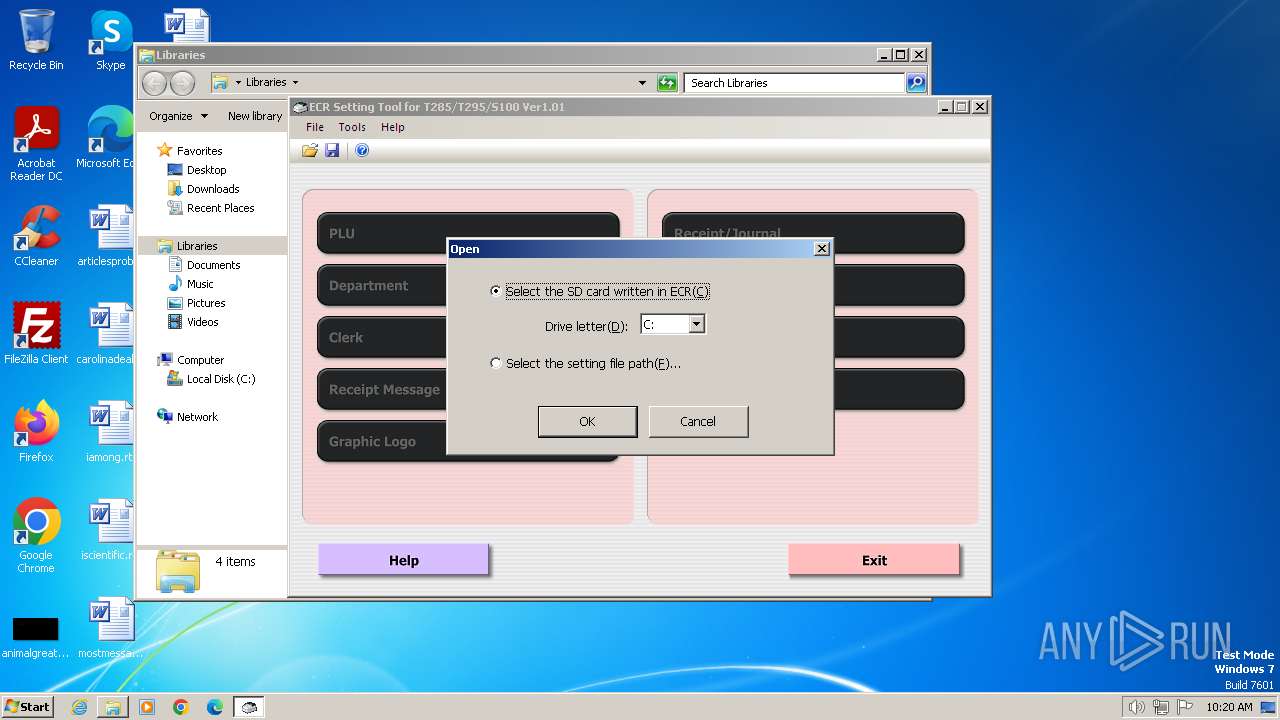
Manual execution by a user
- explorer.exe (PID: 540)
- wmpnscfg.exe (PID: 2000)
- SE100ST.exe (PID: 3404)
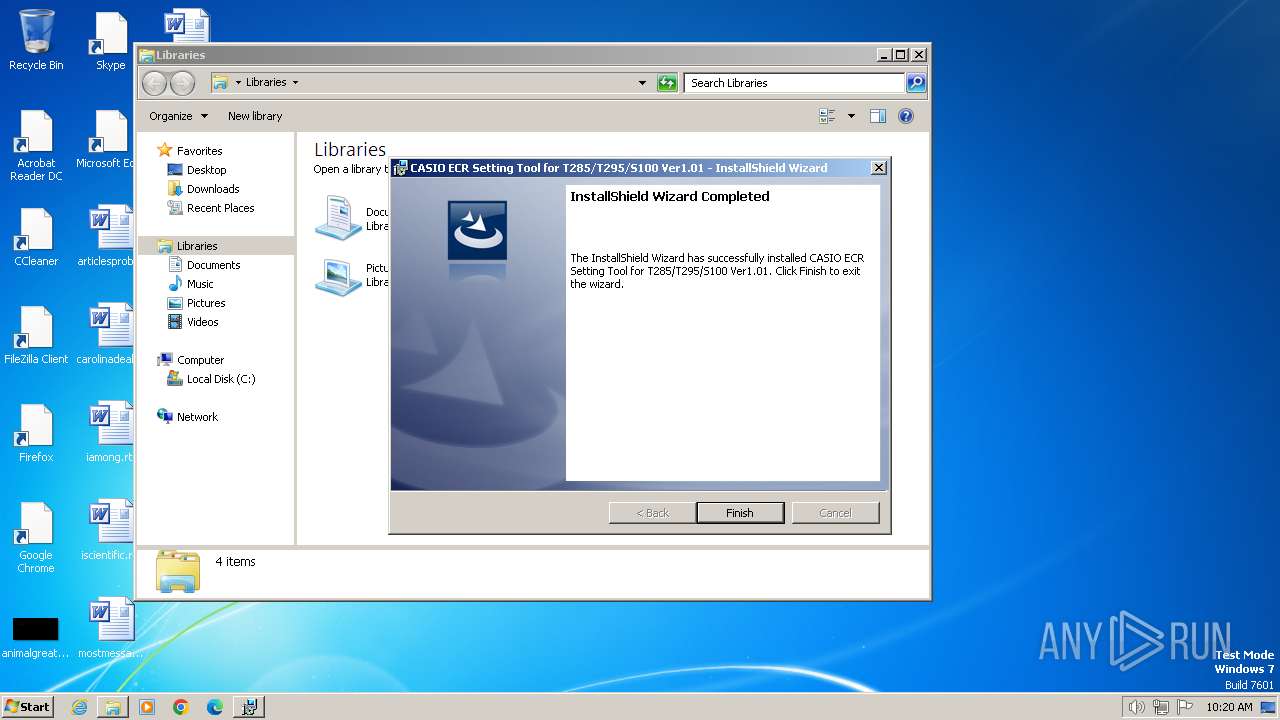
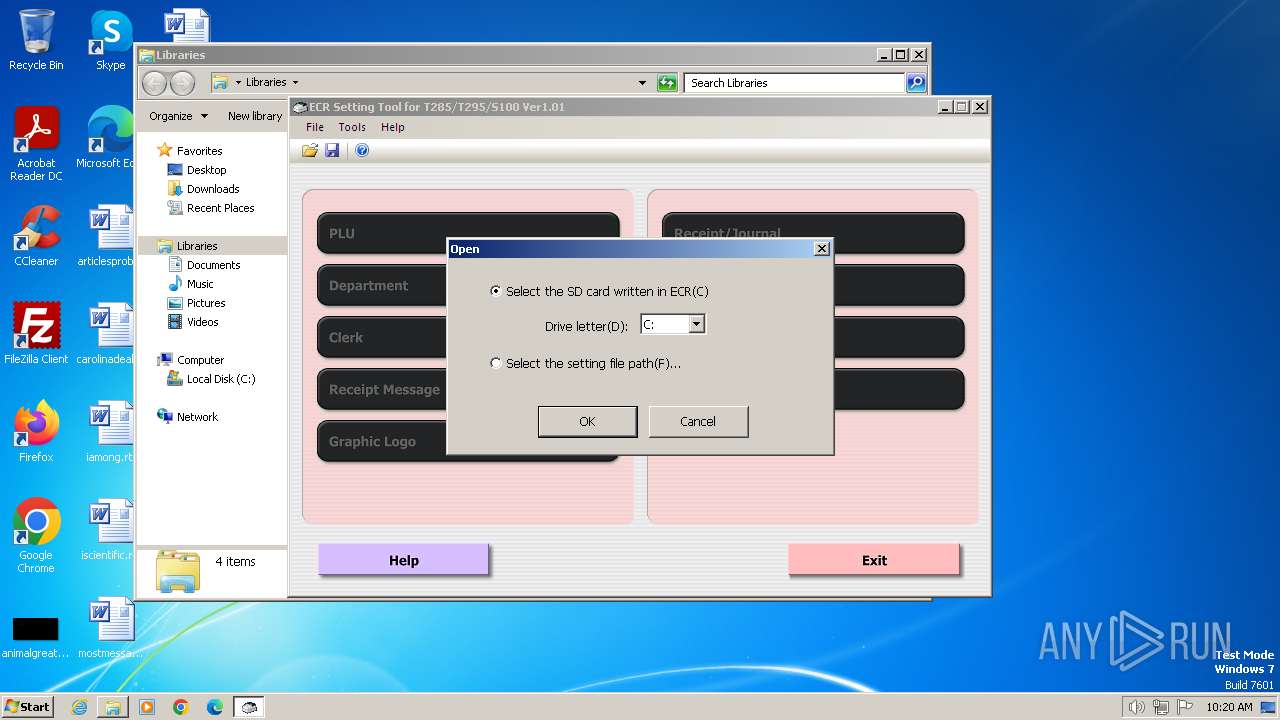
Creates a software uninstall entry
- msiexec.exe (PID: 3412)
Creates files or folders in the user directory
- SE100ST.exe (PID: 3404)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3568)
Application launched itself
- msiexec.exe (PID: 3412)
Drops the executable file immediately after the start
- msiexec.exe (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:04:13 18:32:45+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 39424 |
| InitializedDataSize: | 10260480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x645c |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.2900.5512 |
| ProductVersionNumber: | 6.0.2900.5512 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2900.5512 (xpsp.080413-2105) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.2900.5512 |
Total processes
49
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | C:\Windows\system32\MsiExec.exe -Embedding 5EA12422CE38C04E0303310FD0C9F424 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Setup.Exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Setup.exe | — | EcrstSES100V1P01.EXE.exe | |||||||||||
User: admin Company: CASIO COMPUTER CO.,LTD. Integrity Level: MEDIUM Description: Setup Launcher Unicode Exit code: 0 Version: 1.01.0001 Modules
| |||||||||||||||
| 3384 | "C:\Users\admin\AppData\Local\Temp\EcrstSES100V1P01.EXE.exe" | C:\Users\admin\AppData\Local\Temp\EcrstSES100V1P01.EXE.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 6.00.2900.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
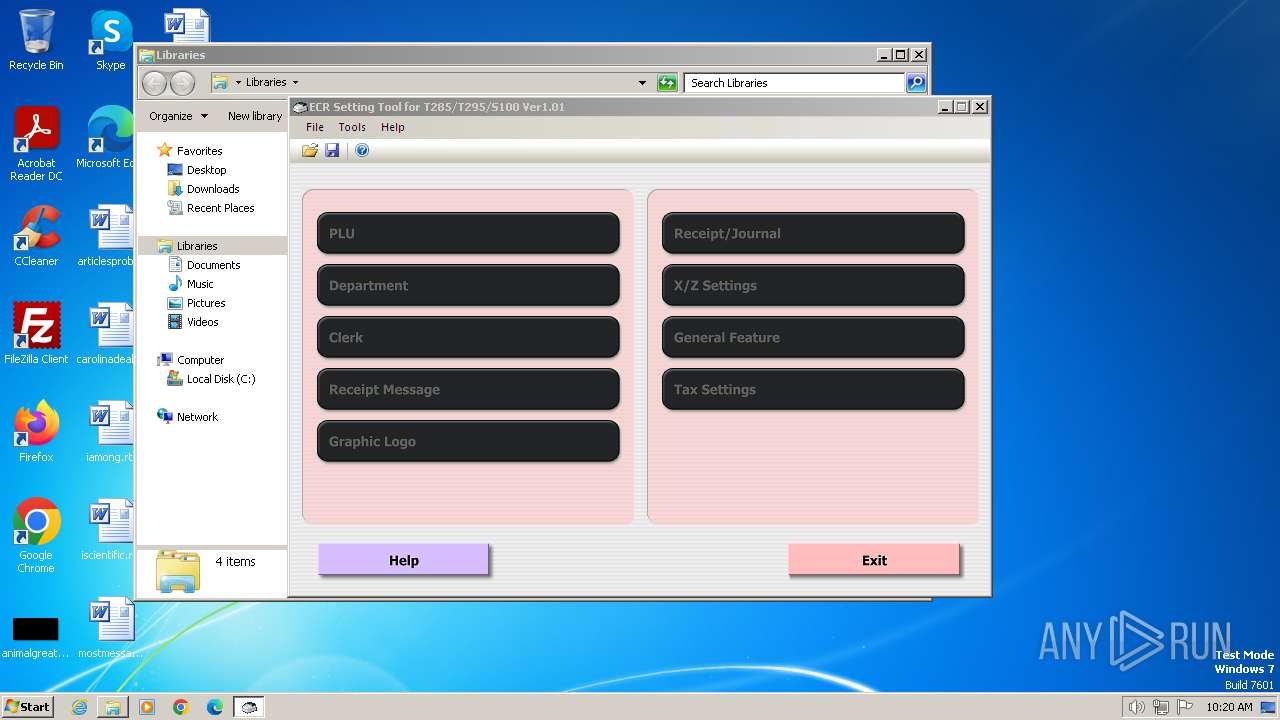
| 3404 | "C:\Program Files\CASIO\ECRSS100\SE100ST.exe" | C:\Program Files\CASIO\ECRSS100\SE100ST.exe | — | explorer.exe | |||||||||||
User: admin Company: CASIO COMPUTER CO., LTD. Integrity Level: MEDIUM Description: SE100ST application Version: 1.0.1.0 Modules
| |||||||||||||||
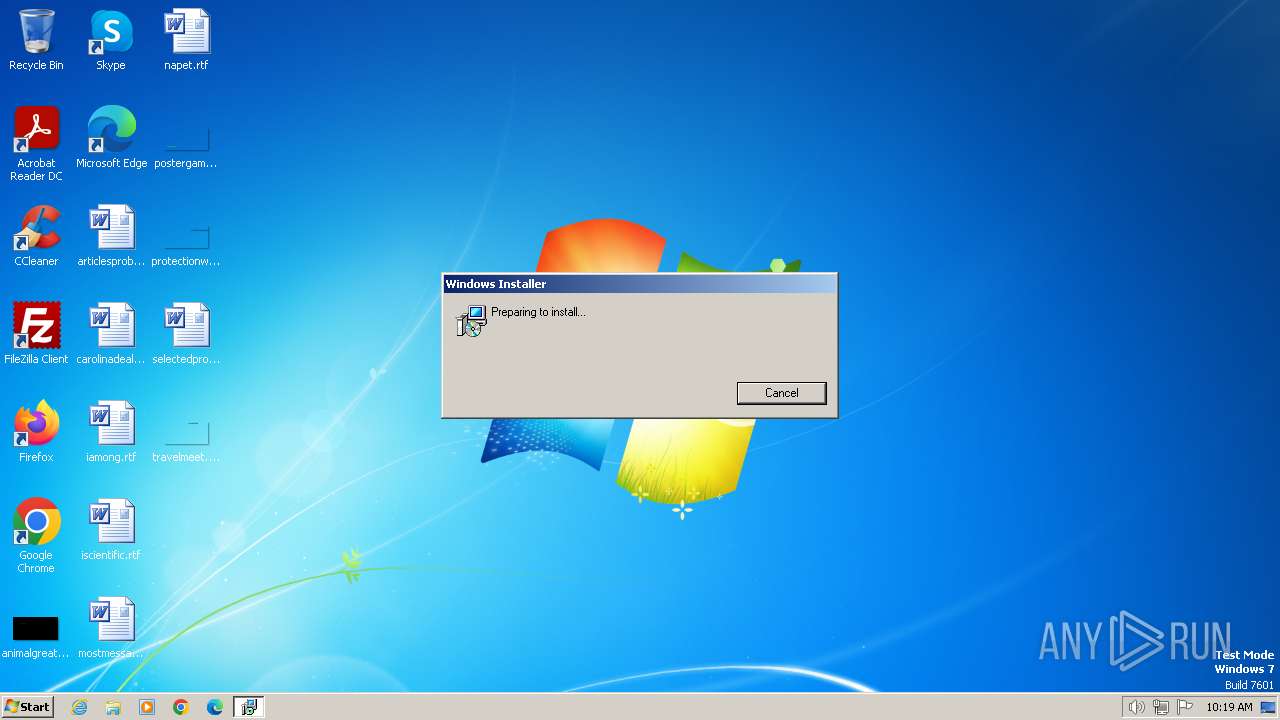
| 3412 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3568 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\EcrstSES100.msi" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\IXP000.TMP" SETUPEXENAME="Setup.Exe" | C:\Windows\System32\msiexec.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3844 | C:\Windows\system32\MsiExec.exe -Embedding D976D04D43C156A4DBC09699812027B6 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
12 834
Read events
12 420
Write events
401
Delete events
13
Modification events
| (PID) Process: | (3384) EcrstSES100V1P01.EXE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (3568) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3412) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000009C5DAADCE0C6DA01540D0000680C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3412) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009C5DAADCE0C6DA01540D0000680C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3412) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 75 | |||
| (PID) Process: | (3412) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000056C7B7DDE0C6DA01540D0000680C0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3412) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000A8CBCDDE0C6DA01540D0000300B0000E8030000010000000000000000000000B0A07B9D21FA8F43A36926CB5D0B6FC30000000000000000 | |||
| (PID) Process: | (3164) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000004228D9DDE0C6DA015C0C0000040E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3164) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000004228D9DDE0C6DA015C0C000020080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3164) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000004228D9DDE0C6DA015C0C0000940D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
63
Suspicious files
13
Text files
92
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | EcrstSES100V1P01.EXE.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Data1.cab | — | |
MD5:— | SHA256:— | |||
| 3412 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3384 | EcrstSES100V1P01.EXE.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Setup.exe | executable | |
MD5:942418C2DCAD76F2026F2E0D459397D6 | SHA256:B14D89D32B8AB0AC1B7E3BABAB85C0FD498AC89E8043CA8E22156A783D5FB756 | |||
| 3568 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1228.tmp | executable | |
MD5:778D0941FB9B969AB90B81C9B91086D7 | SHA256:3A2EB487237D36B6DA8CC21EB39AFDB890A84BF2E29FADF3182E44B1EF114FB8 | |||
| 3384 | EcrstSES100V1P01.EXE.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\0x0409.ini | text | |
MD5:BE345D0260AE12C5F2F337B17E07C217 | SHA256:E994689A13B9448C074F9B471EDEEC9B524890A0D82925E98AB90B658016D8F3 | |||
| 3384 | EcrstSES100V1P01.EXE.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Setup.Ini | text | |
MD5:9A731DEE0E2A7C34A875CA91ED6D869F | SHA256:F2F5740B10EFCDD05DEA1B633BD2917B534D20A0C523B1829B560260020C3E9B | |||
| 3412 | msiexec.exe | C:\Program Files\CASIO\ECRSS100\C_comw.dll | executable | |
MD5:60C876A9256F6A7F9FE2079521618AE3 | SHA256:884D77CFD6F807DAE2D345144BBB8E3904FECFD891519D1589E83BAD402B9D0F | |||
| 3412 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF18061E44C0210FA9.TMP | gmc | |
MD5:AD63A0AF20A778F394E410EB7946119D | SHA256:0BAA043017660F93F3ADF02B72DE793C84A7F240ED77DEE8437F67A98AD39072 | |||
| 3412 | msiexec.exe | C:\Windows\Installer\MSI6F0D.tmp | executable | |
MD5:FF43CABBA151DBA4C92800EEFCE66C37 | SHA256:78E2BDD0224D165D7021AE683946FB08865F3073B38F61F7F0D96D8E964DE249 | |||
| 3412 | msiexec.exe | C:\Program Files\CASIO\ECRSS100\CACReg.exe | executable | |
MD5:FEFC7FE9B7537ED329885A0B7A6C056B | SHA256:BD44A50C9D4C9225CF58B1C4CE7FA9FC098C661237BE6DBA51DEB91465D096F5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?11acddbe1ebd82b3 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:3702 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 95.101.54.128:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1372 | svchost.exe | 88.221.125.143:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 2.19.126.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |