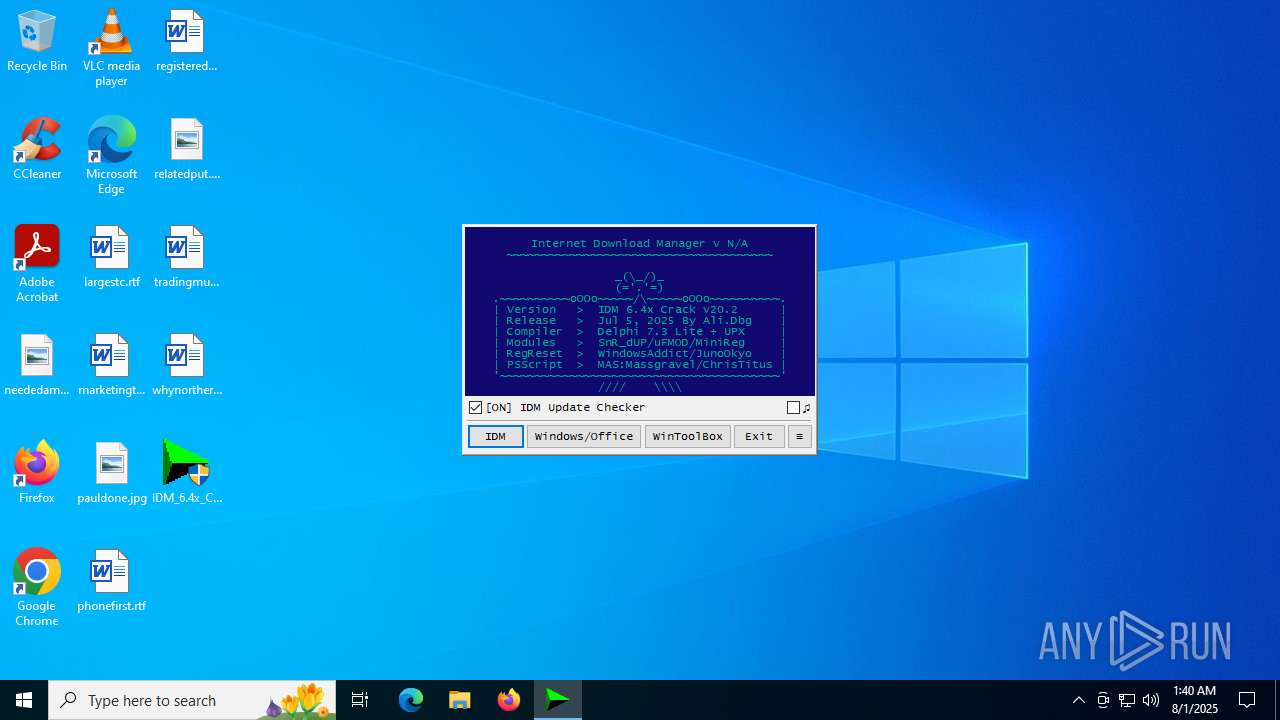
| File name: | IDM_6.4x_Crack_v20.2.exe |
| Full analysis: | https://app.any.run/tasks/a0962fbf-c7ce-4adc-a726-d701ab32a709 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 01:40:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 689F245046CA30CE27203DE3EDEC8327 |
| SHA1: | C03DCA393288C88ABDB9EF48B52CD92FC28B9F2C |
| SHA256: | D80B7BD24276190D25B7FEE3A09530C5A9736306DA83842D37A4D52D92BBA897 |
| SSDEEP: | 1536:1e+j44X5OjRutV4N8YLekTVrfg1JlCI0ZeKZMvrOAV:1e+04XNtVZi5fyJlL0ZfGDOAV |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5764)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5764)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5764)
Deletes a file (SCRIPT)
- wscript.exe (PID: 5764)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4264)
Bypass execution policy to execute commands
- powershell.exe (PID: 3608)
Run PowerShell with an invisible window
- powershell.exe (PID: 3608)
SUSPICIOUS
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 5764)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 5764)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 5764)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 5764)
The process executes VB scripts
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
Reads security settings of Internet Explorer
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
The process executes Powershell scripts
- cmd.exe (PID: 4264)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4264)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 3608)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 4264)
Removes files via Powershell
- powershell.exe (PID: 3608)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4264)
Manipulates environment variables
- powershell.exe (PID: 3608)
INFO
Checks supported languages
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
Reads the computer name
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
Creates files or folders in the user directory
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
Create files in a temporary directory
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
Checks proxy server information
- wscript.exe (PID: 5764)
- slui.exe (PID: 5504)
Process checks computer location settings
- IDM_6.4x_Crack_v20.2.exe (PID: 1232)
Reads the software policy settings
- slui.exe (PID: 5504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 61440 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 188416 |
| EntryPoint: | 0x3d220 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
139
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | "C:\Users\admin\Desktop\IDM_6.4x_Crack_v20.2.exe" | C:\Users\admin\Desktop\IDM_6.4x_Crack_v20.2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\Desktop\IDM_6.4x_Crack_v20.2.exe" | C:\Users\admin\Desktop\IDM_6.4x_Crack_v20.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3608 | powershell -ExecutionPolicy Bypass -NoProfile -NoLogo -WindowStyle Hidden -Command "Remove-Item -Path \"$env:TEMP\MAS*.ps1\",\"$env:TEMP\*UPDT.vbs\" -Force -ErrorAction SilentlyContinue" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4264 | "C:\Windows\System32\cmd.exe" /c powershell -ExecutionPolicy Bypass -NoProfile -NoLogo -WindowStyle Hidden -Command "Remove-Item -Path \"$env:TEMP\MAS*.ps1\",\"$env:TEMP\*UPDT.vbs\" -Force -ErrorAction SilentlyContinue" | C:\Windows\SysWOW64\cmd.exe | — | IDM_6.4x_Crack_v20.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5504 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5764 | wscript.exe "C:\Users\admin\AppData\Local\Temp\\CRK_UPDT.vbs" "https://idm.0dy.ir/" "Version" "Download_URL" "20.2" "Crack" "C:\Program Files\Google\Chrome\Application\chrome.exe" silent | C:\Windows\SysWOW64\wscript.exe | IDM_6.4x_Crack_v20.2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6796 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 457
Read events
11 442
Write events
15
Delete events
0
Modification events
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
| (PID) Process: | (1232) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\PowerShell\1\ShellIds\ScriptedDiagnostics |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1232 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Local\Temp\IDM_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 1232 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Local\Temp\CRK_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 1232 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Roaming\WinRAR\rarreg.key | text | |
MD5:CC72935D4E4BD54DB0ED6BF4701FDC9E | SHA256:2ABE74BB821BA46762AFDB23EAC95454EC7155D5379E3CD56385D900C34CB1BF | |||
| 5764 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\PO6FLYGP.xml | text | |
MD5:4578E6452BA4B6DB8F26638BEF27CD85 | SHA256:6F03D6B5FC6A2CA8F3B8683848C0F16A14ABF316156AECD7606D047A651CD3F6 | |||
| 3608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j1tywxz1.op5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gttuouax.cmw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3608 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:AE928522CBA46DB81647AC575B1C2C37 | SHA256:600F8548EB047C723613890FCC43DAEAFBD07111F61C322ECDDEF8190DD396B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
24
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
2216 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
2216 | RUXIMICS.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2216 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2216 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
idm.0dy.ir |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |