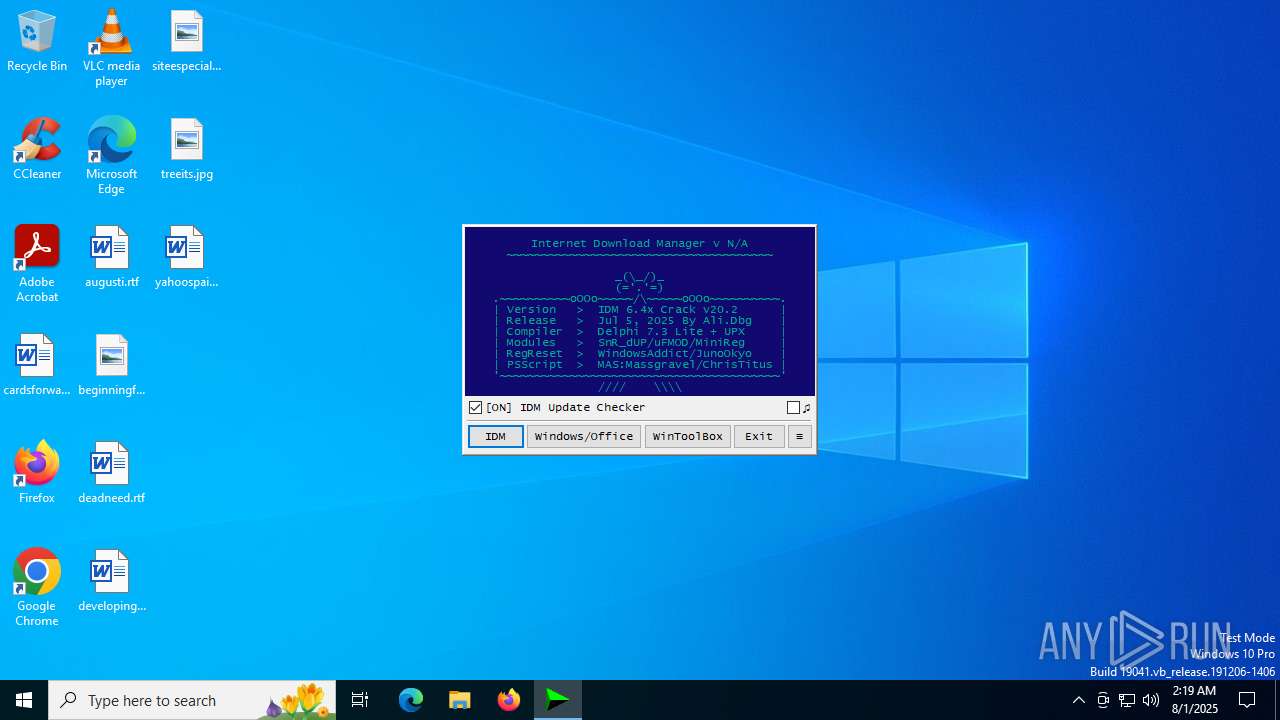
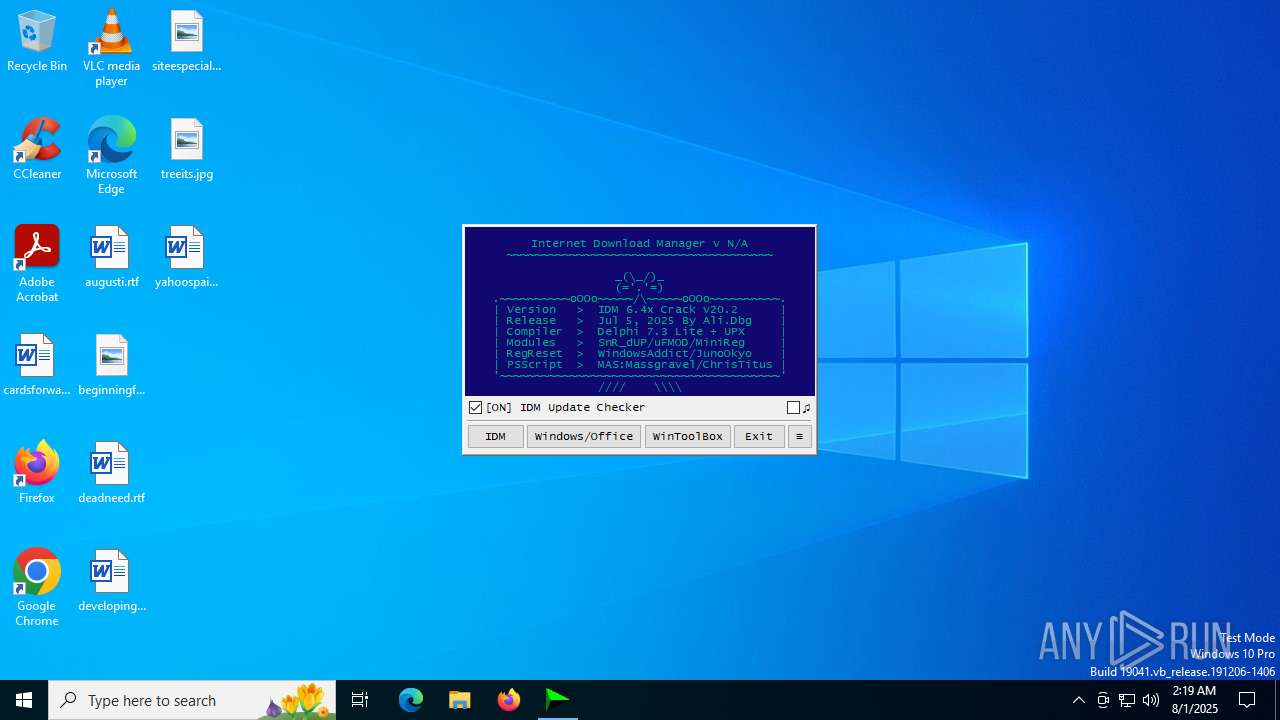
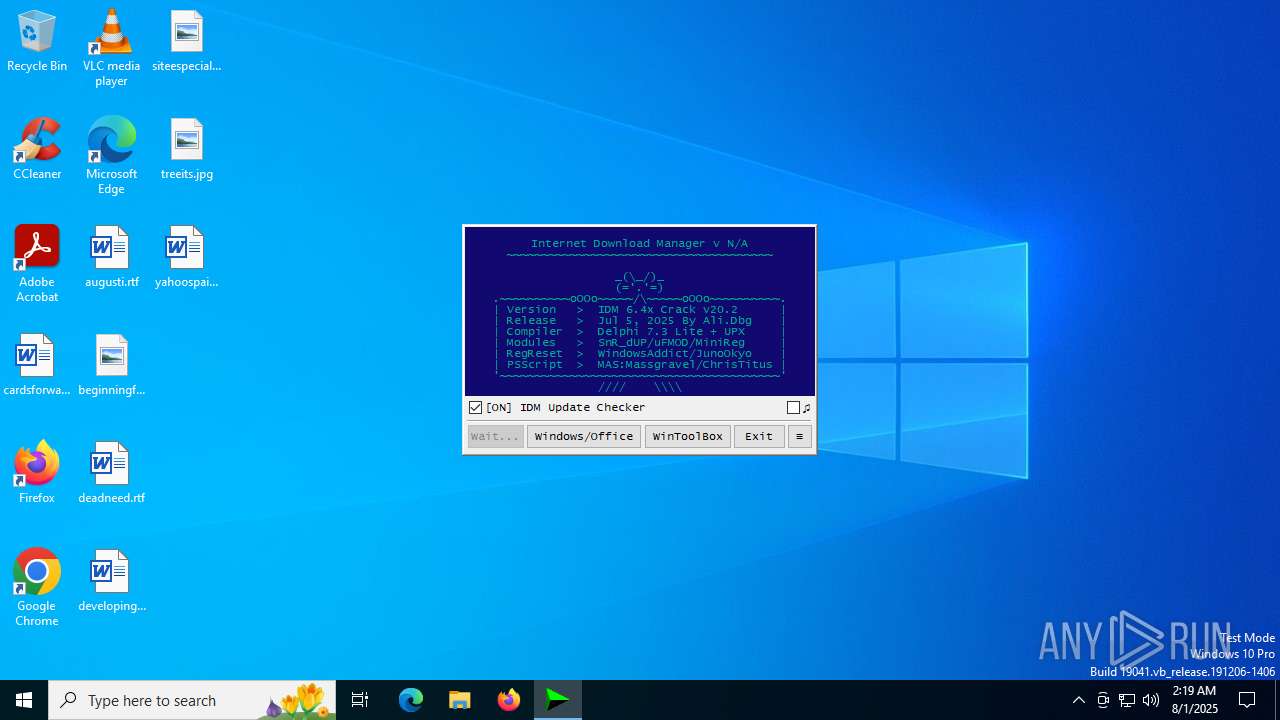
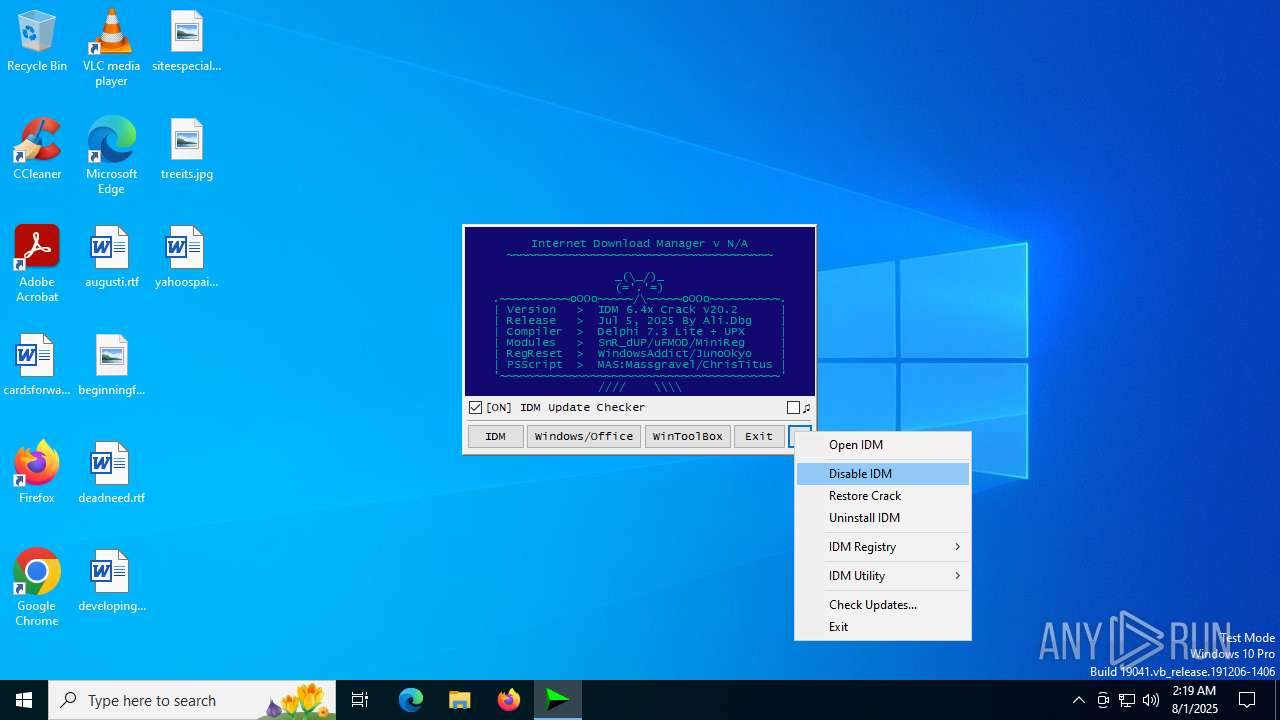
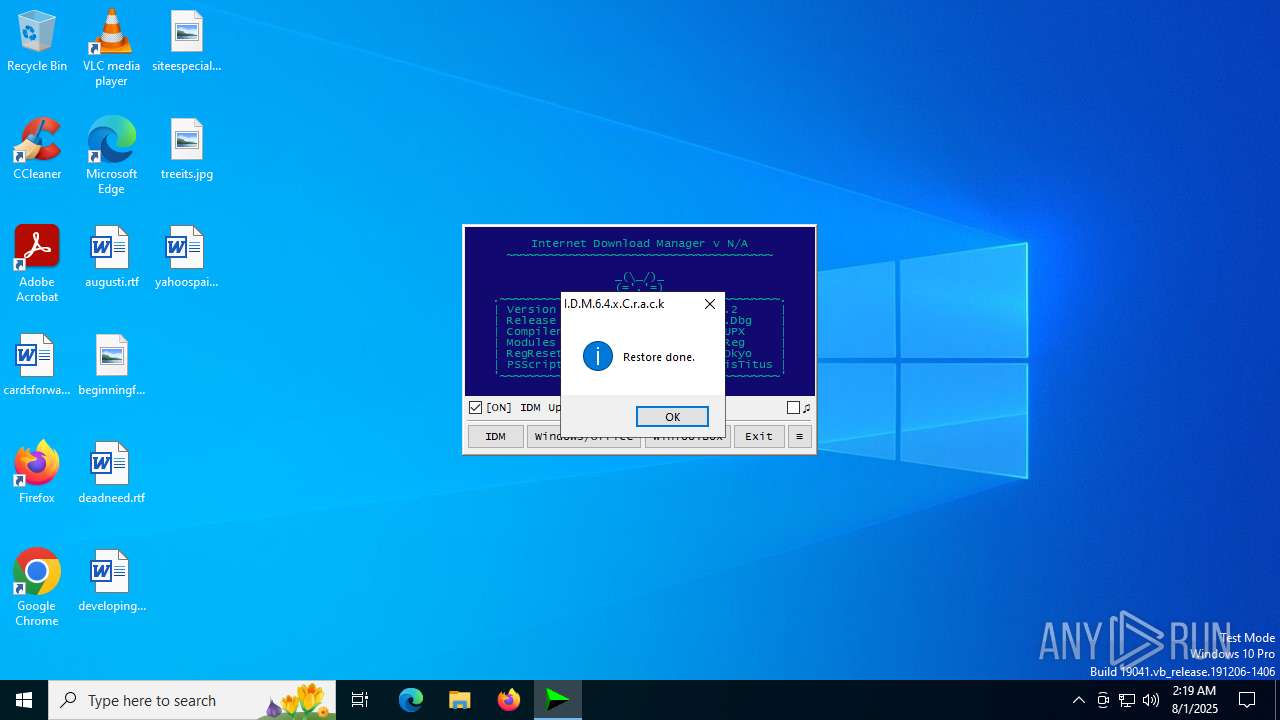
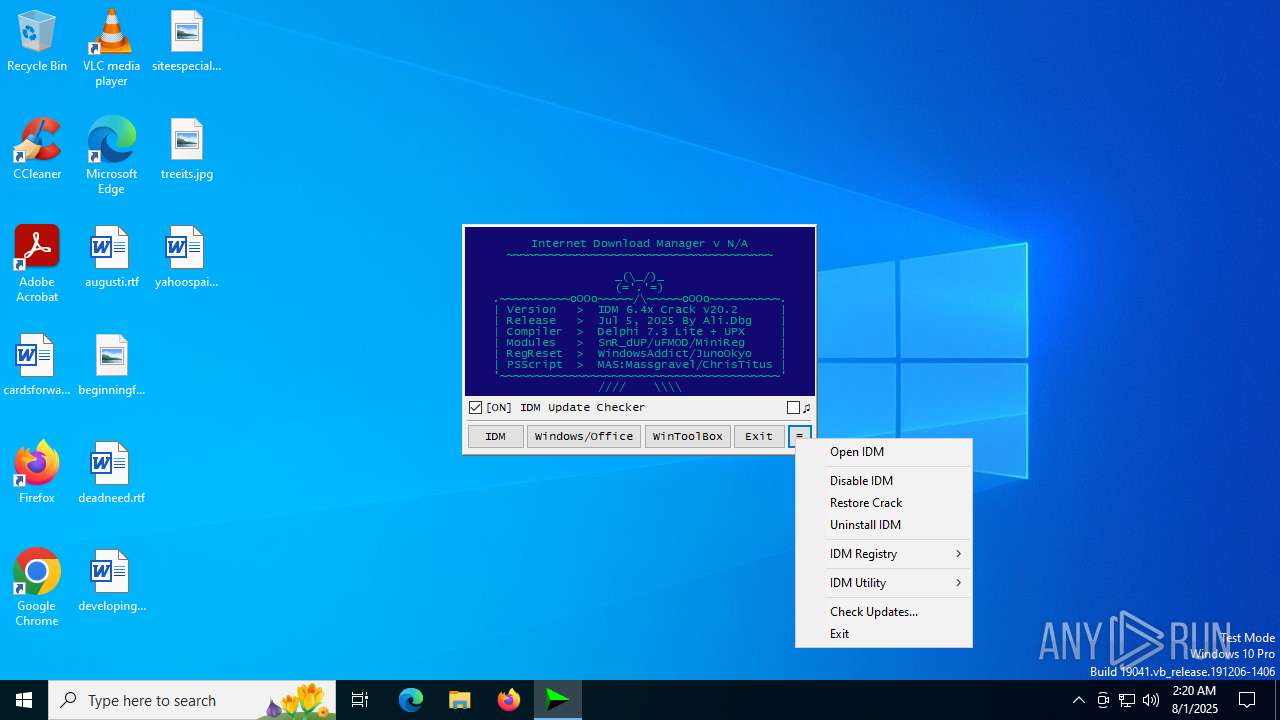
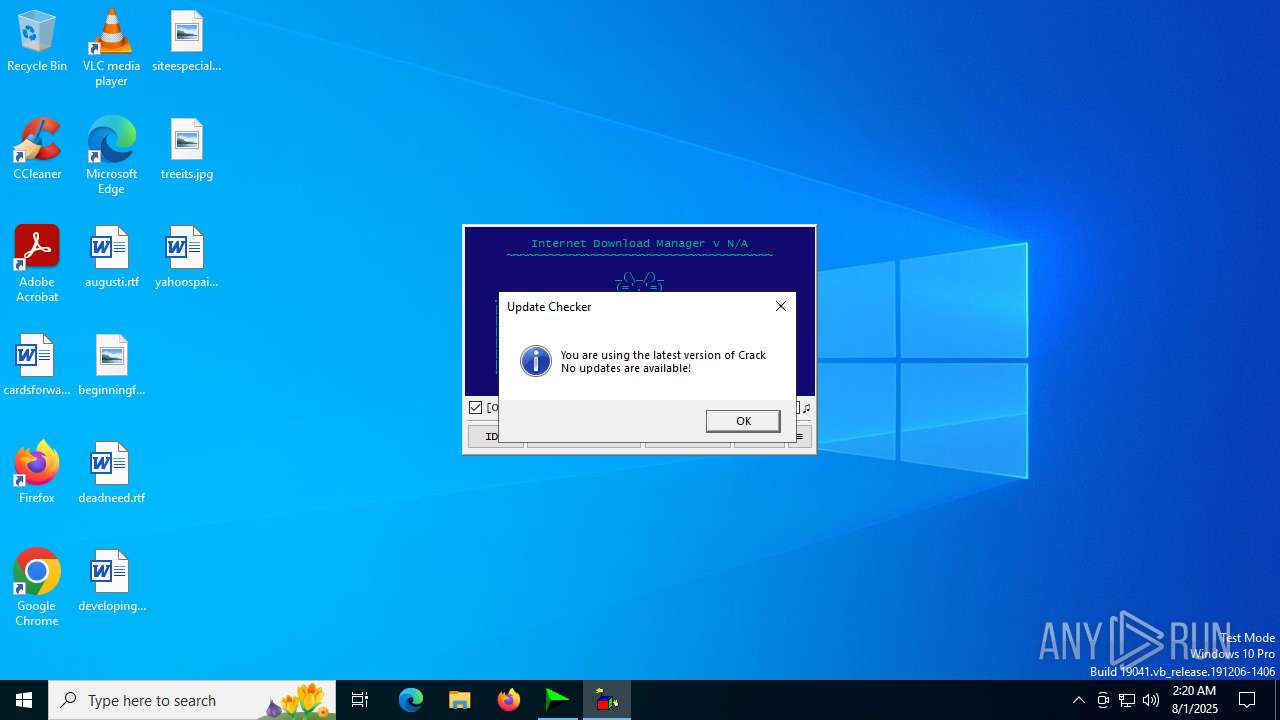
| File name: | IDM_6.4x_Crack_v20.2.exe |
| Full analysis: | https://app.any.run/tasks/399ac21e-f303-4ece-85b4-5d44c5db63e6 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 02:19:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 689F245046CA30CE27203DE3EDEC8327 |
| SHA1: | C03DCA393288C88ABDB9EF48B52CD92FC28B9F2C |
| SHA256: | D80B7BD24276190D25B7FEE3A09530C5A9736306DA83842D37A4D52D92BBA897 |
| SSDEEP: | 1536:1e+j44X5OjRutV4N8YLekTVrfg1JlCI0ZeKZMvrOAV:1e+04XNtVZi5fyJlL0ZfGDOAV |
MALICIOUS
Changes powershell execution policy (Bypass)
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5716)
- wscript.exe (PID: 5188)
Bypass execution policy to execute commands
- powershell.exe (PID: 3112)
Starts Visual C# compiler
- powershell.exe (PID: 3112)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 3112)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5188)
- wscript.exe (PID: 5716)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5188)
- wscript.exe (PID: 5716)
Deletes a file (SCRIPT)
- wscript.exe (PID: 5188)
- wscript.exe (PID: 5716)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 5716)
- wscript.exe (PID: 5188)
The process hides Powershell's copyright startup banner
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
Reads security settings of Internet Explorer
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
The process bypasses the loading of PowerShell profile settings
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
Starts POWERSHELL.EXE for commands execution
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 3000)
The process executes VB scripts
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 5716)
- wscript.exe (PID: 5188)
Possibly malicious use of IEX has been detected
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
- cmd.exe (PID: 5244)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 3112)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 3112)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 3112)
Uses .NET C# to load dll
- powershell.exe (PID: 3112)
CSC.EXE is used to compile C# code
- csc.exe (PID: 5708)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 2112)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
- cmd.exe (PID: 5244)
Application launched itself
- cmd.exe (PID: 5244)
- cmd.exe (PID: 4580)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
- cmd.exe (PID: 4580)
- cmd.exe (PID: 5244)
Executable content was dropped or overwritten
- csc.exe (PID: 5708)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5244)
Hides command output
- cmd.exe (PID: 5744)
- cmd.exe (PID: 2112)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 5188)
- wscript.exe (PID: 5716)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 5716)
- wscript.exe (PID: 5188)
Starts application with an unusual extension
- cmd.exe (PID: 5244)
INFO
Reads the computer name
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
Checks supported languages
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
- csc.exe (PID: 5708)
- cvtres.exe (PID: 1036)
- chcp.com (PID: 5876)
Process checks computer location settings
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
Creates files or folders in the user directory
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
Create files in a temporary directory
- IDM_6.4x_Crack_v20.2.exe (PID: 4648)
- cvtres.exe (PID: 1036)
- csc.exe (PID: 5708)
- reg.exe (PID: 2716)
Disables trace logs
- powershell.exe (PID: 3112)
Checks proxy server information
- powershell.exe (PID: 3112)
- wscript.exe (PID: 5188)
- wscript.exe (PID: 5716)
Reads the machine GUID from the registry
- csc.exe (PID: 5708)
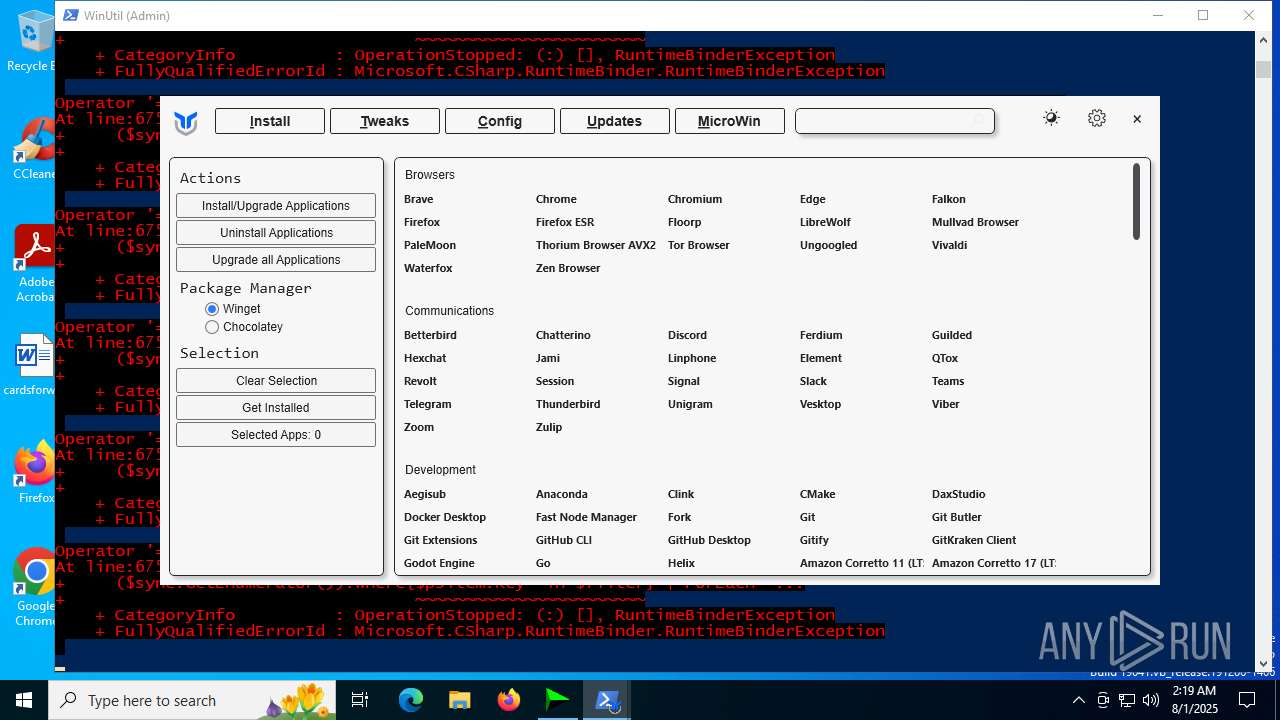
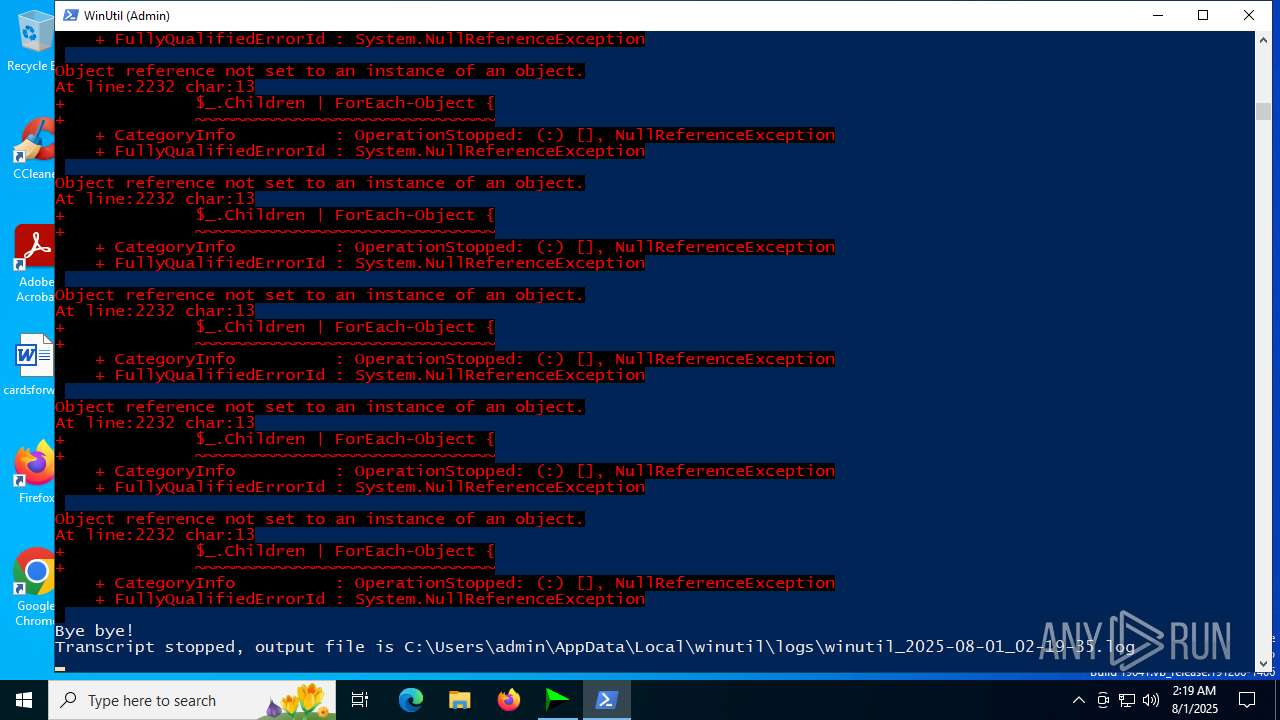
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3112)
Reads mouse settings
- powershell.exe (PID: 3112)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3112)
Checks operating system version
- cmd.exe (PID: 5244)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3628)
- powershell.exe (PID: 6656)
Changes the display of characters in the console
- cmd.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 61440 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 188416 |
| EntryPoint: | 0x3d220 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
200
Monitored processes
63
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | reg query HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESB50.tmp" "c:\Users\admin\AppData\Local\Temp\f2wiej4x\CSC9EF56DADFAD43D685466410B4F58A3E.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1040 | reg query "HKCU\Software\DownloadManager" "/v" "Serial" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | reg query HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1560 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo "C:\Users\admin\AppData\Local\Temp\BATCLEN.bat" " | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1632 | reg add HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1808 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | find /i "computersystem" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 550
Read events
42 489
Write events
46
Delete events
15
Modification events
| (PID) Process: | (5716) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5716) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5716) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4648) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (4648) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (4648) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (4648) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (4648) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (4648) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (4648) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
Executable files
1
Suspicious files
6
Text files
29
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5716 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | der | |
MD5:CA8A9BDCA7AD59F5C8B7E1AA63160039 | SHA256:81B7FA53B692B4D26E2E8943F2DDA2F9563CFCB0E11F48679EB2BE4F8C375B90 | |||
| 4648 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Roaming\WinRAR\rarreg.key | text | |
MD5:CC72935D4E4BD54DB0ED6BF4701FDC9E | SHA256:2ABE74BB821BA46762AFDB23EAC95454EC7155D5379E3CD56385D900C34CB1BF | |||
| 5716 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:3B3C98A8C62FD313D25D9942A143A9F4 | SHA256:EA5E075FC009831A072D2CE85321E39C26FDDF06D0D673F5540546D92A719239 | |||
| 5716 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | der | |
MD5:1FBB37F79B317A9A248E7C4CE4F5BAC5 | SHA256:9BF639C595FE335B6F694EE35990BEFD2123F5E07FD1973FF619E3FC88F5F49F | |||
| 4648 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Local\Temp\CRK_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 4648 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Local\Temp\IDM_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 5708 | csc.exe | C:\Users\admin\AppData\Local\Temp\f2wiej4x\CSC9EF56DADFAD43D685466410B4F58A3E.TMP | res | |
MD5:619189DCACA68BB619185F2EB364E430 | SHA256:172B509EAE7E171C2C23DE7F7A194E1669736216619AF186D53DFCDDC47CF22A | |||
| 3112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_52zoakeh.hjd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3112 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:910064FB755AF93275E1851EDB9D432D | SHA256:4115FE9462AF1F0FBC8558D31E98D7CD1E25CF15BA4806A414440C5B03E4F819 | |||
| 5716 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:C911742595DEAAE30FA6F14526907932 | SHA256:049B163DF13C49678194D772D16712C95B86C9014CF9139251FCE92739DF1E2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5716 | wscript.exe | GET | 200 | 142.250.185.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5716 | wscript.exe | GET | 200 | 142.250.185.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6356 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6356 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5716 | wscript.exe | 188.114.96.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
5716 | wscript.exe | 142.250.185.163:80 | c.pki.goog | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6216 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6216 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
idm.0dy.ir |
| unknown |
c.pki.goog |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
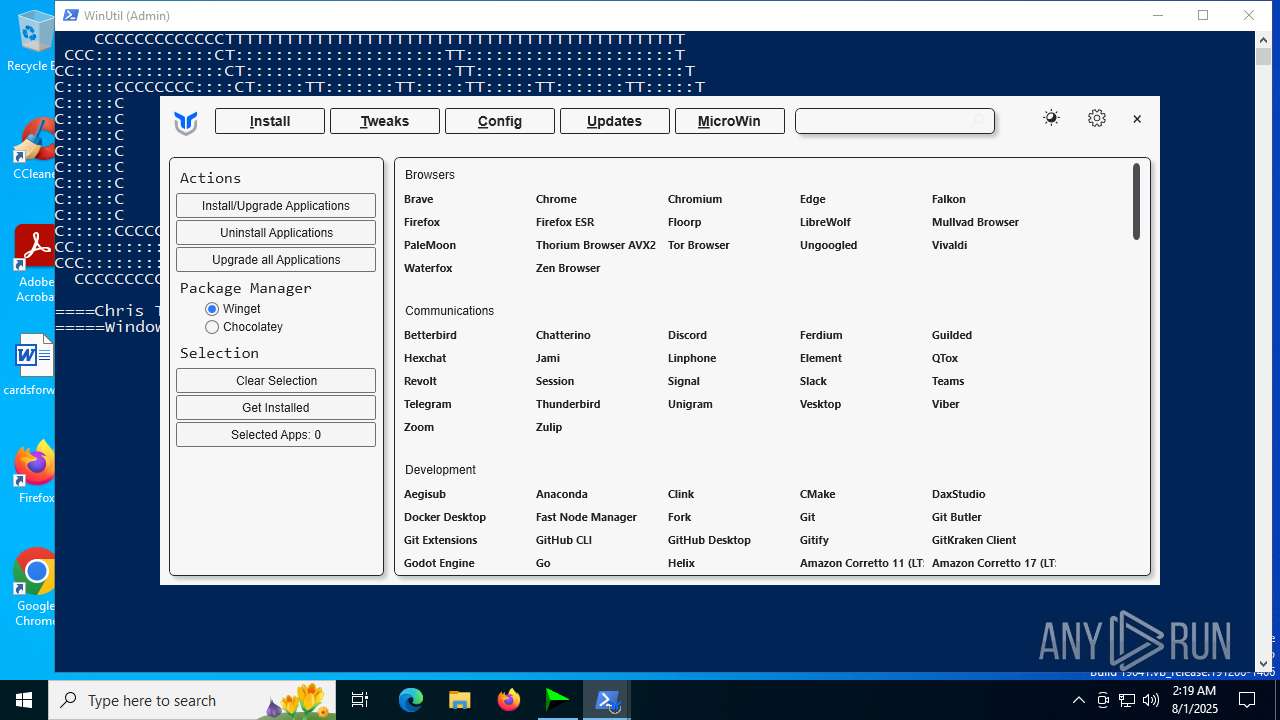
christitus.com |
| malicious |
github.com |
| whitelisted |