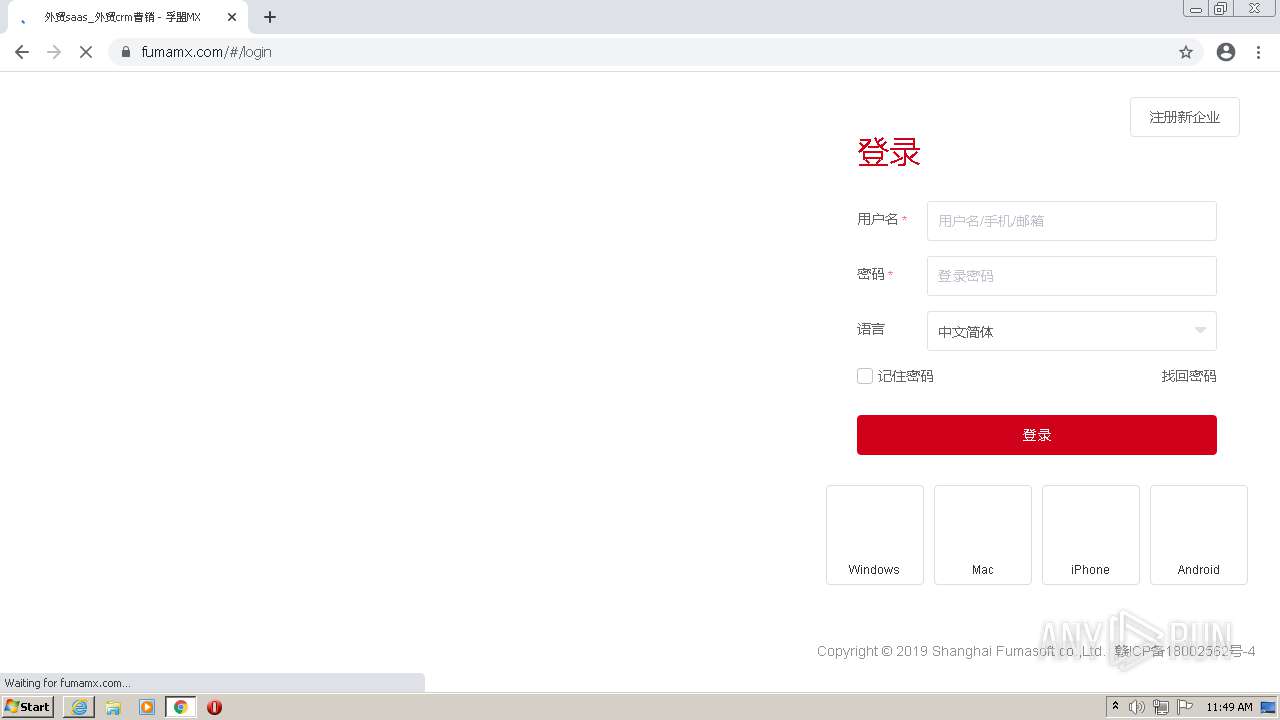
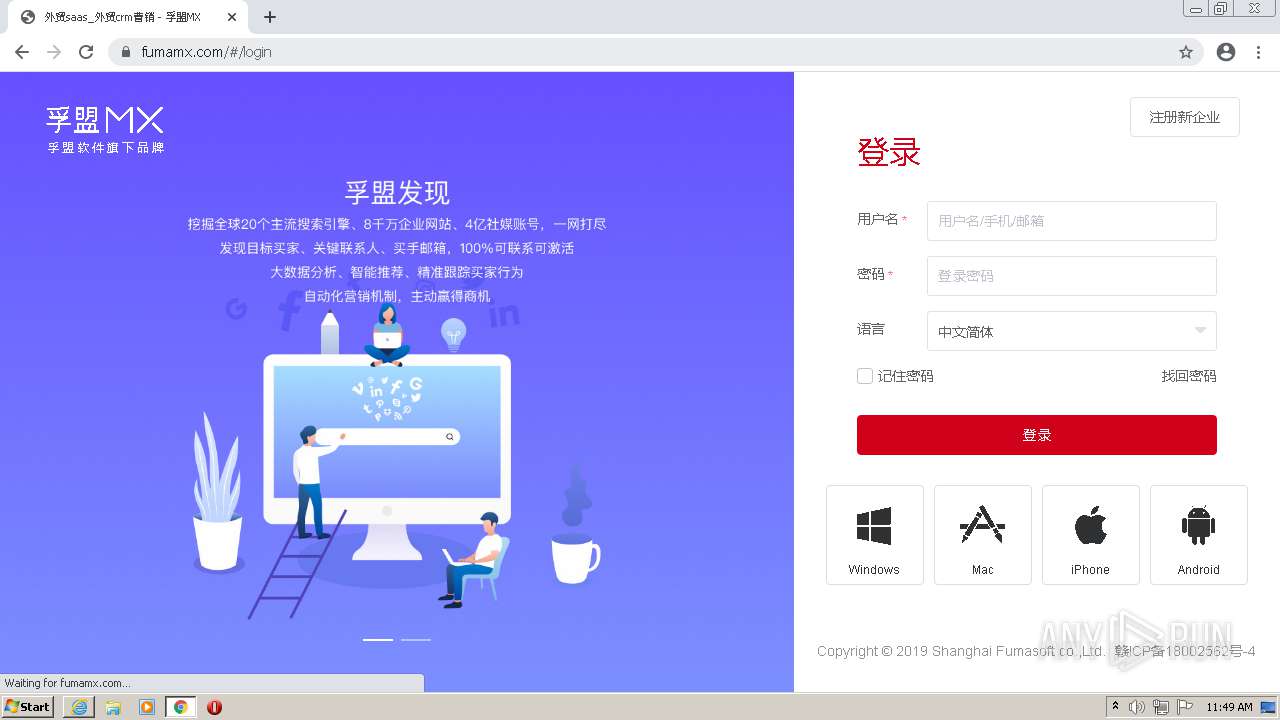
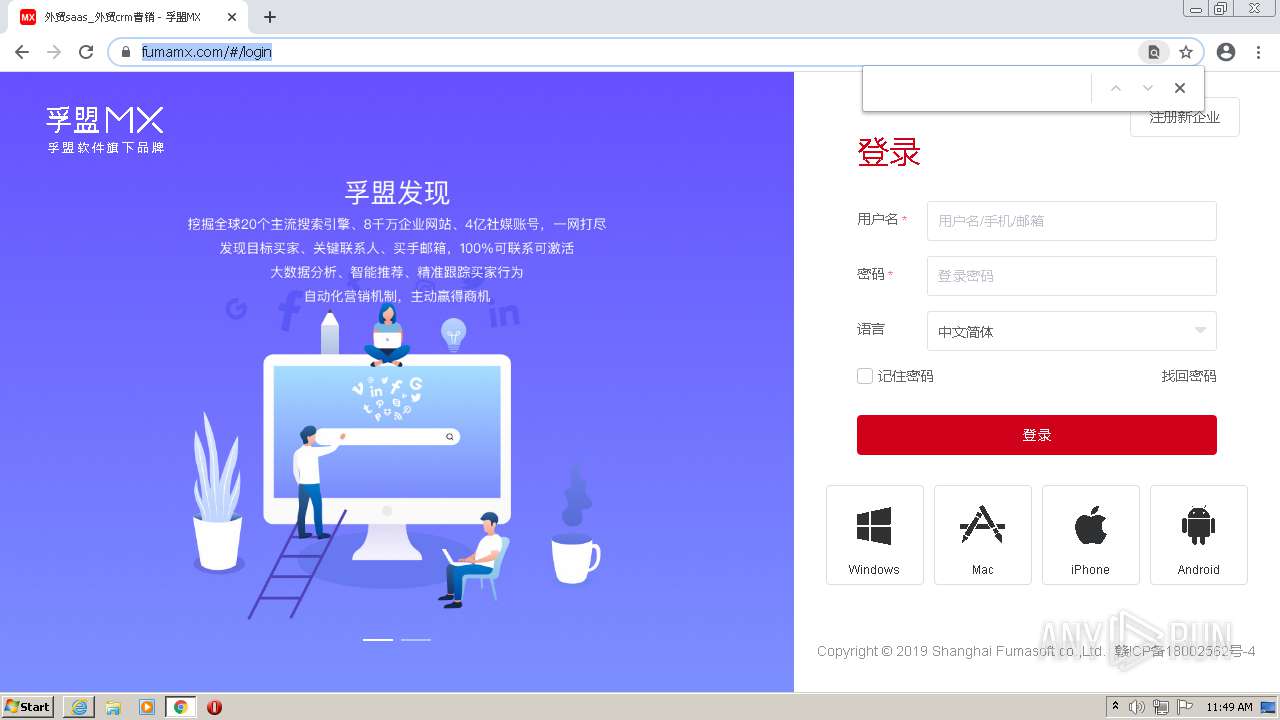
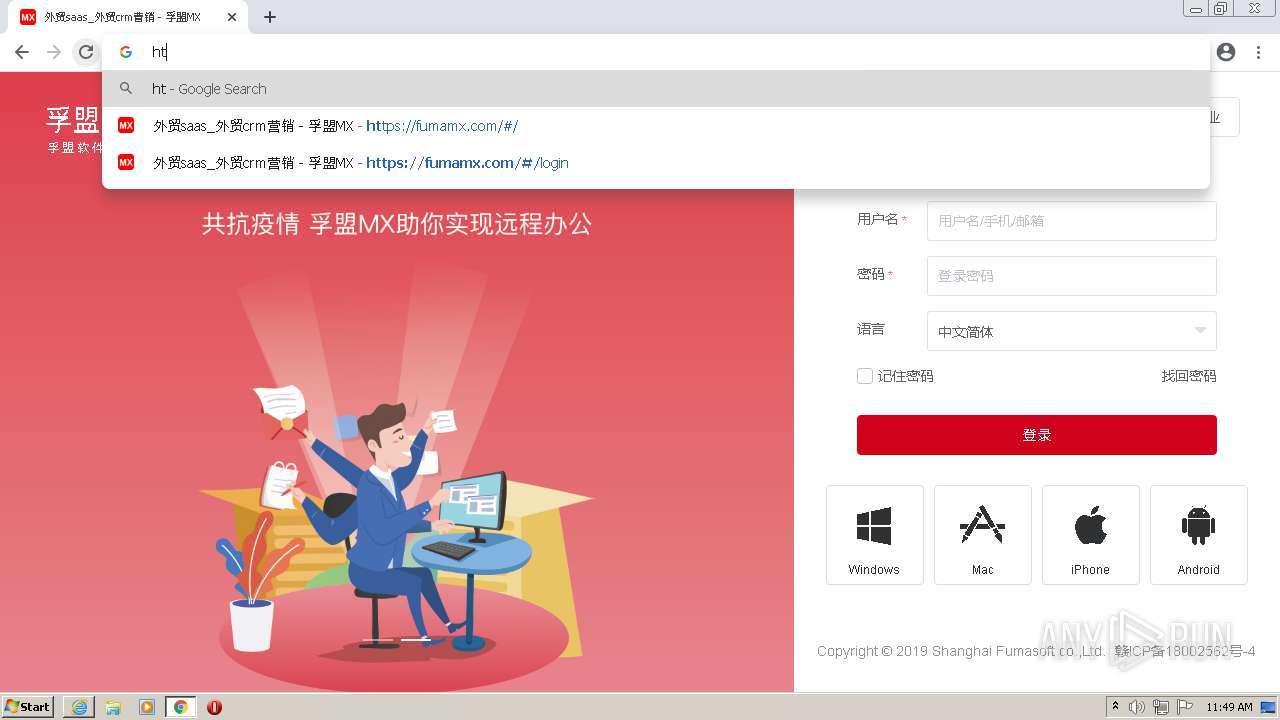
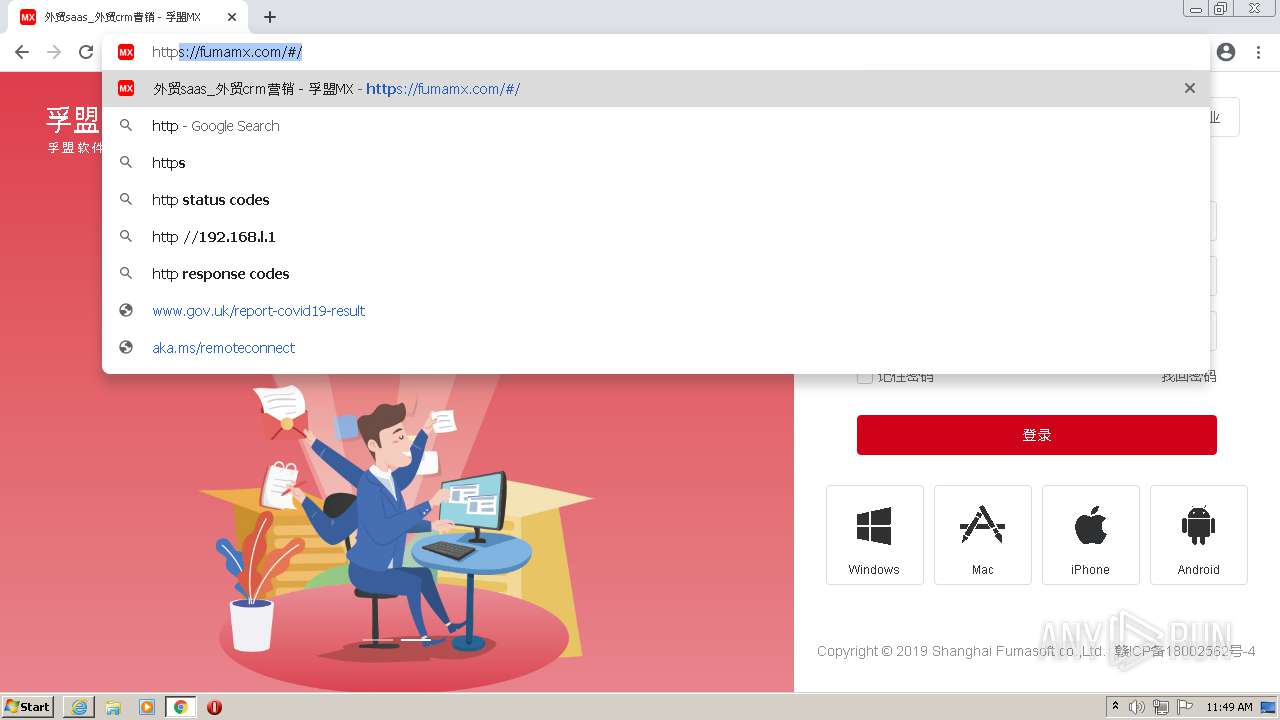
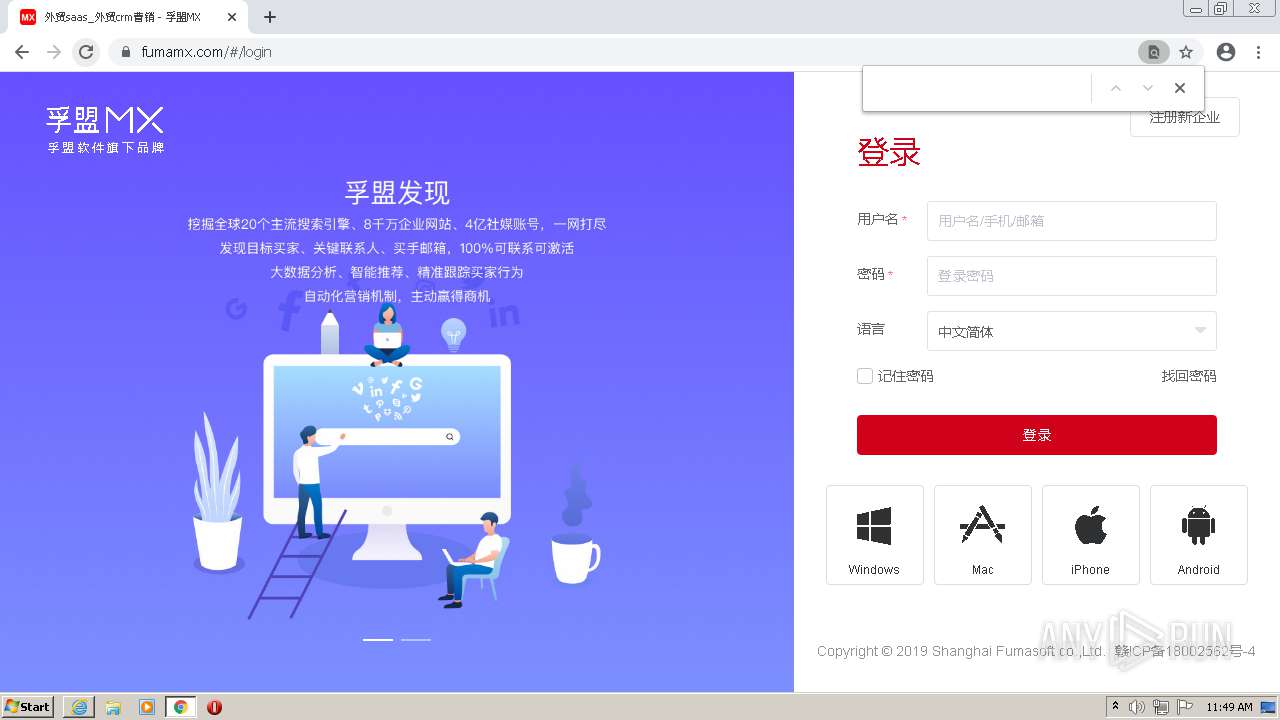
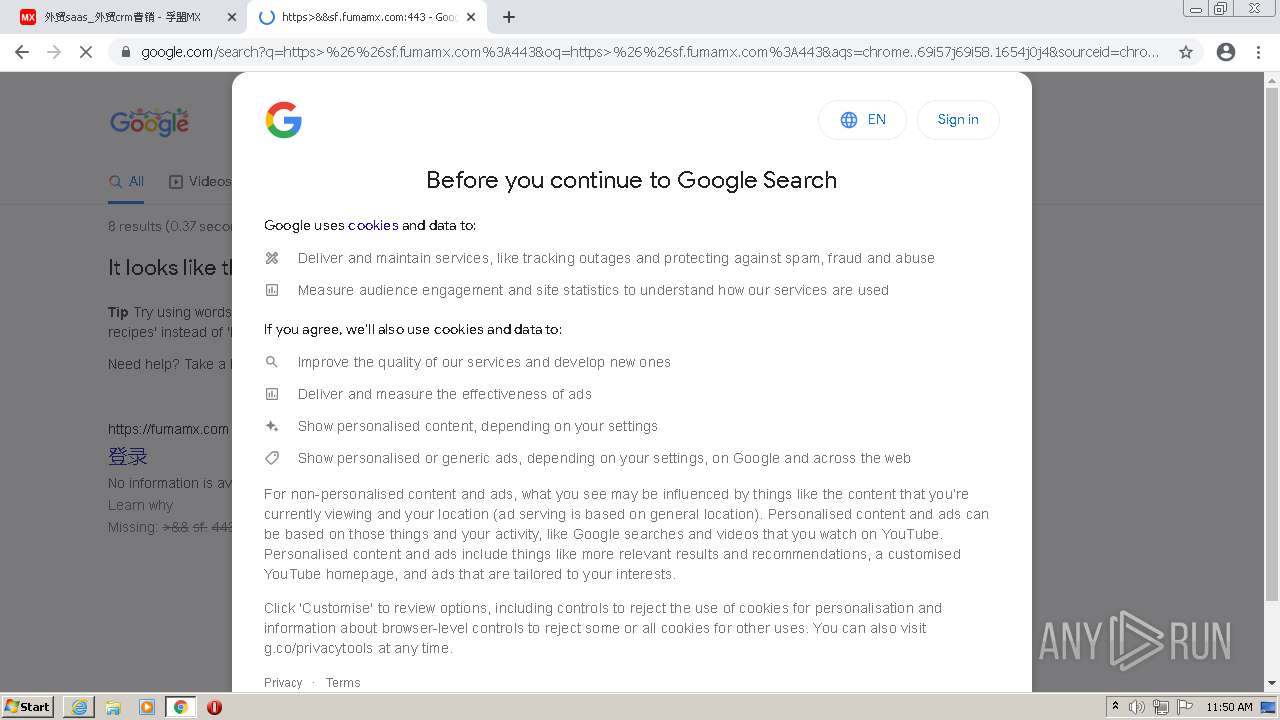
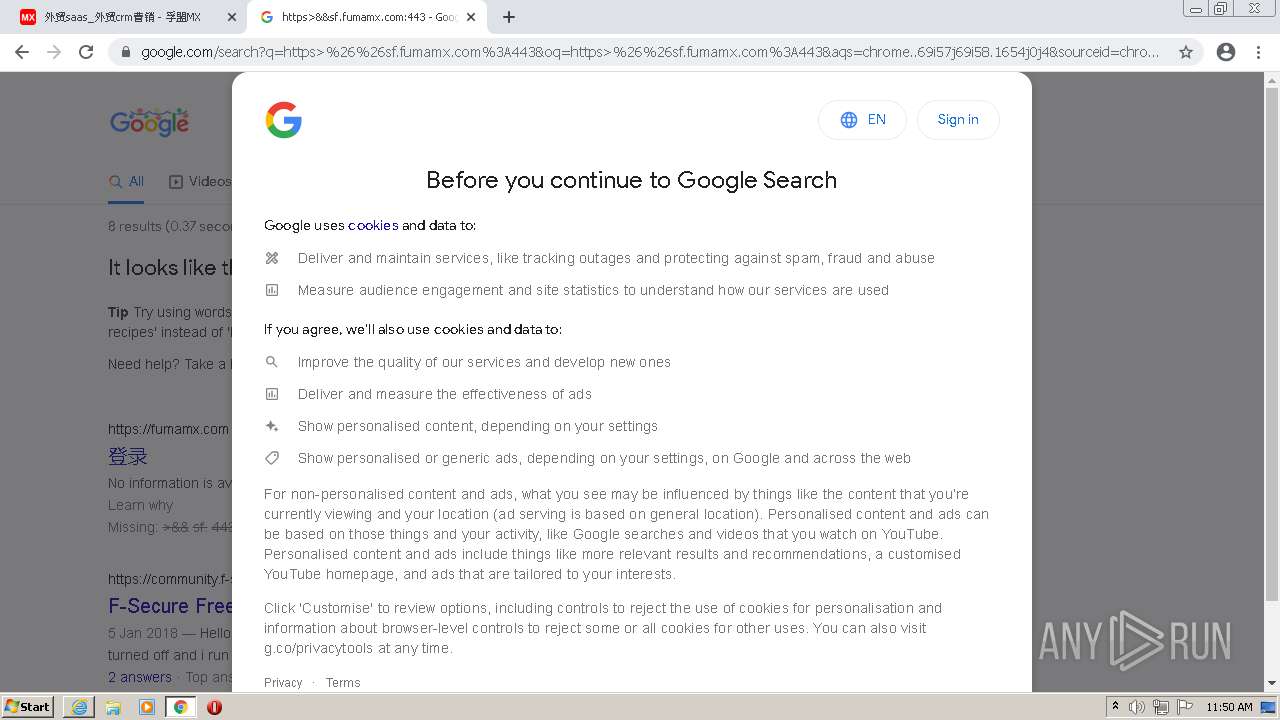
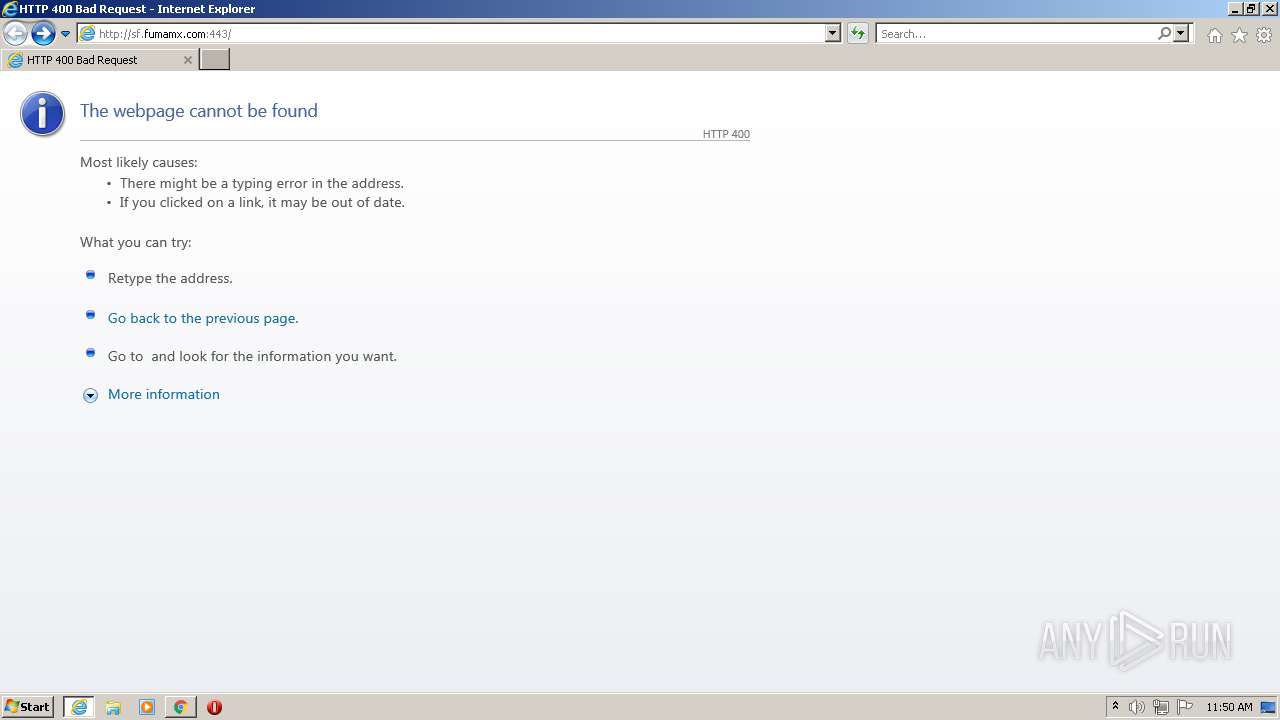
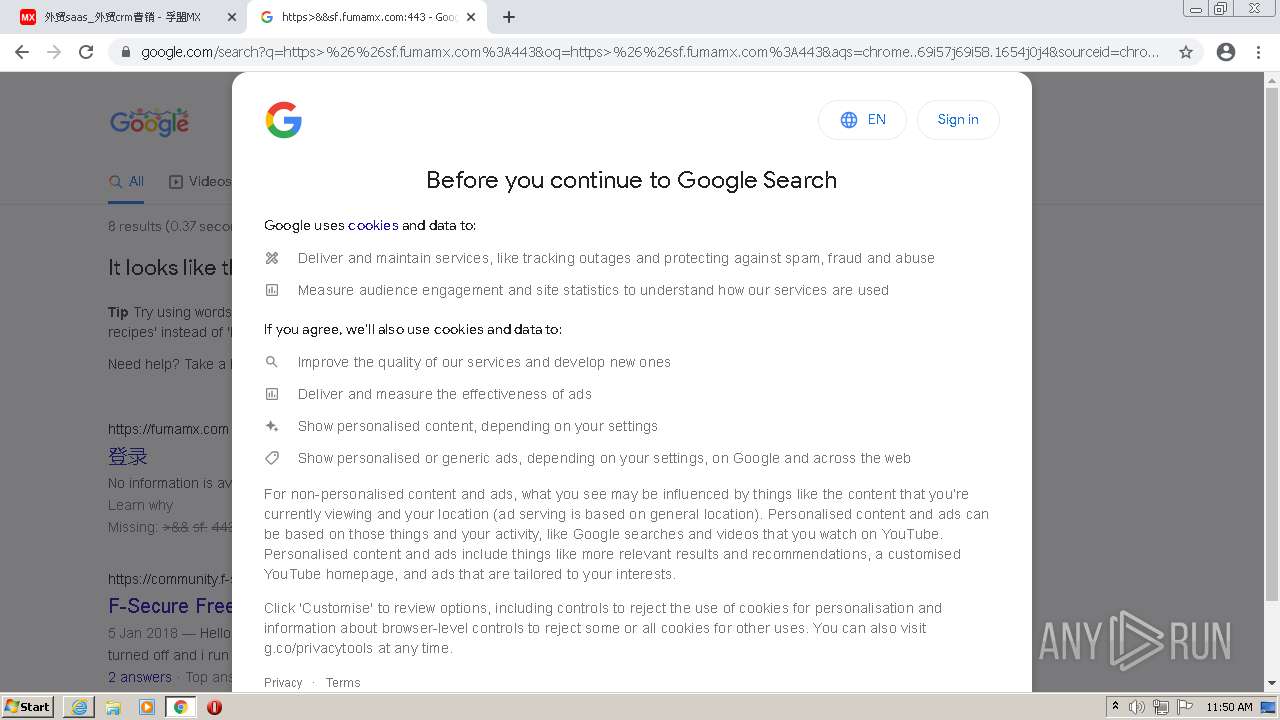
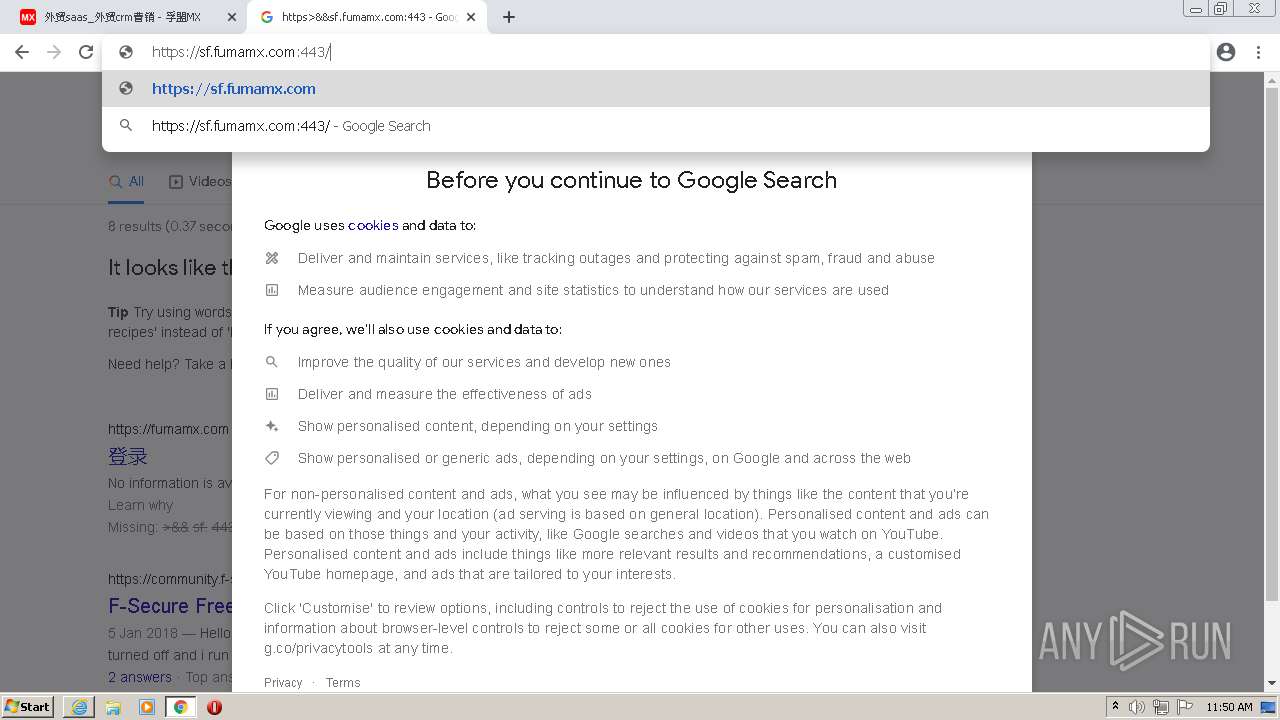
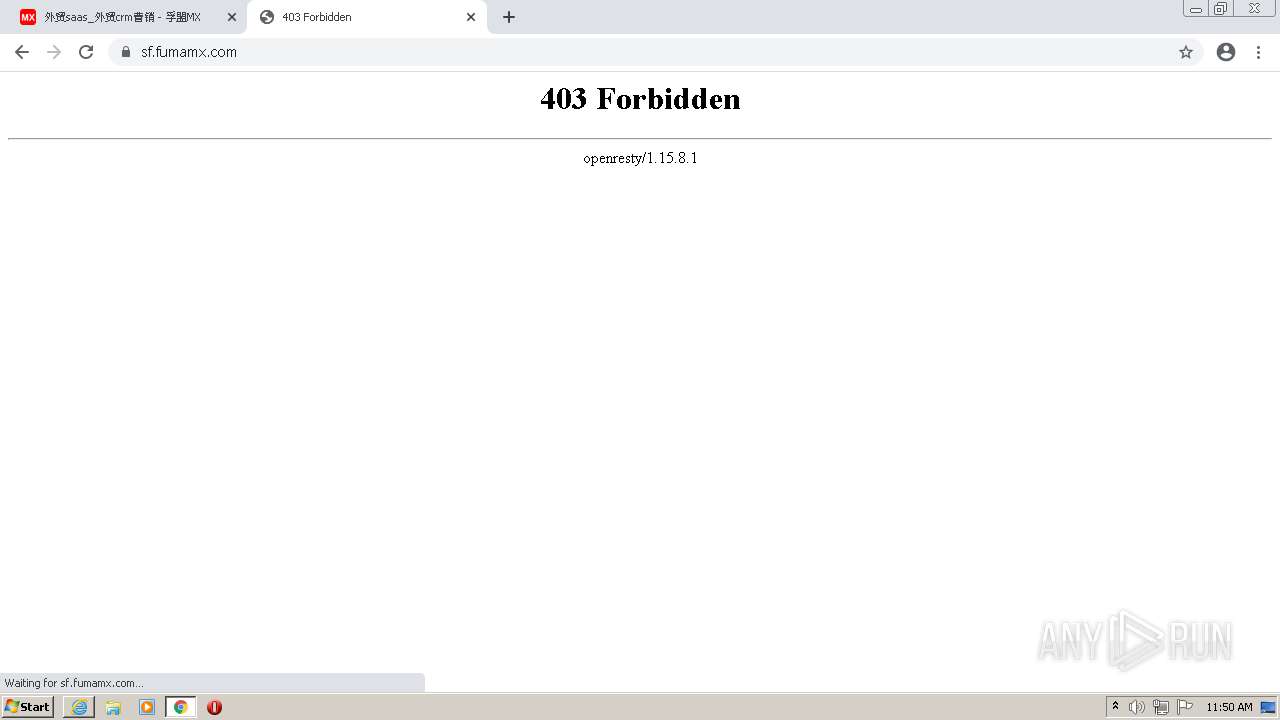
| URL: | http://sf.fumamx.com:443 |
| Full analysis: | https://app.any.run/tasks/781631d5-41e5-464d-91b7-034bf03cdd97 |
| Verdict: | Malicious activity |
| Analysis date: | December 16, 2021, 11:48:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DFB1317BFD38565935B87191F95848B7 |
| SHA1: | DF499B0817DD8AC7229DFD7EA2462308E5F95185 |
| SHA256: | D807E95E686C54FB01021533A945F990AF802FC4B747534A2A82DA24066C6E16 |
| SSDEEP: | 3:N1KNDRdywn:Ctyw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2604)
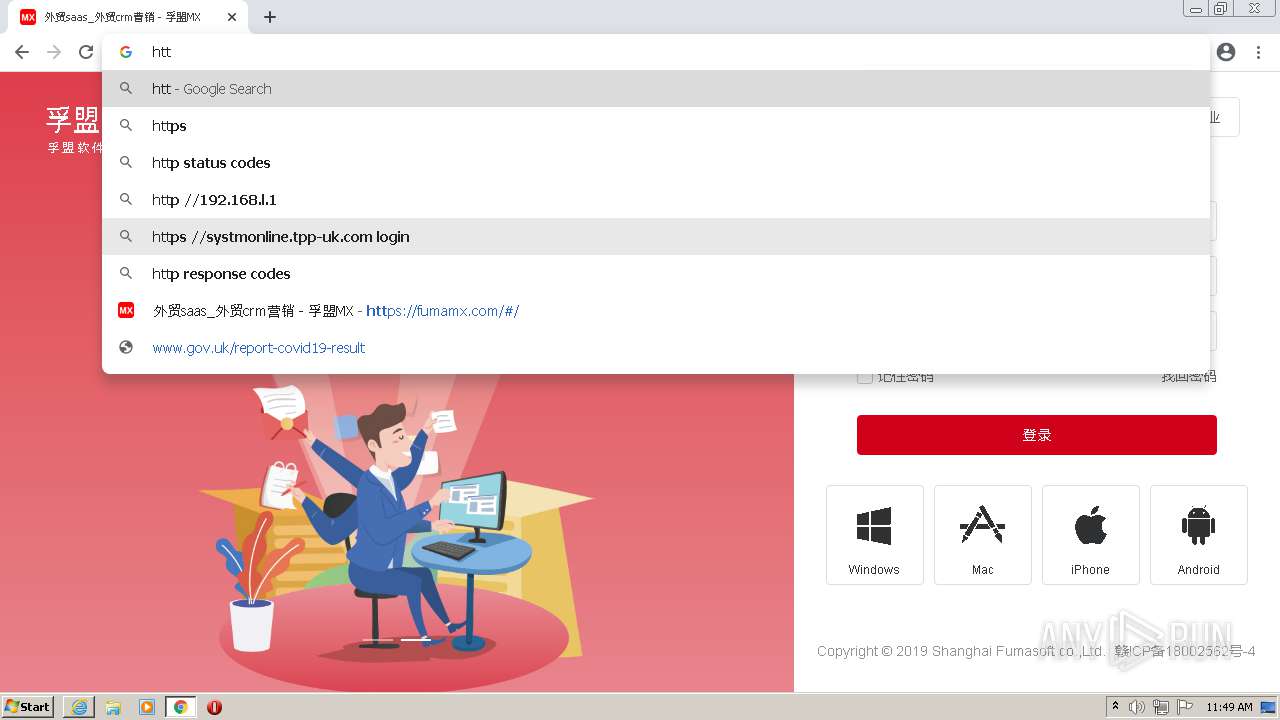
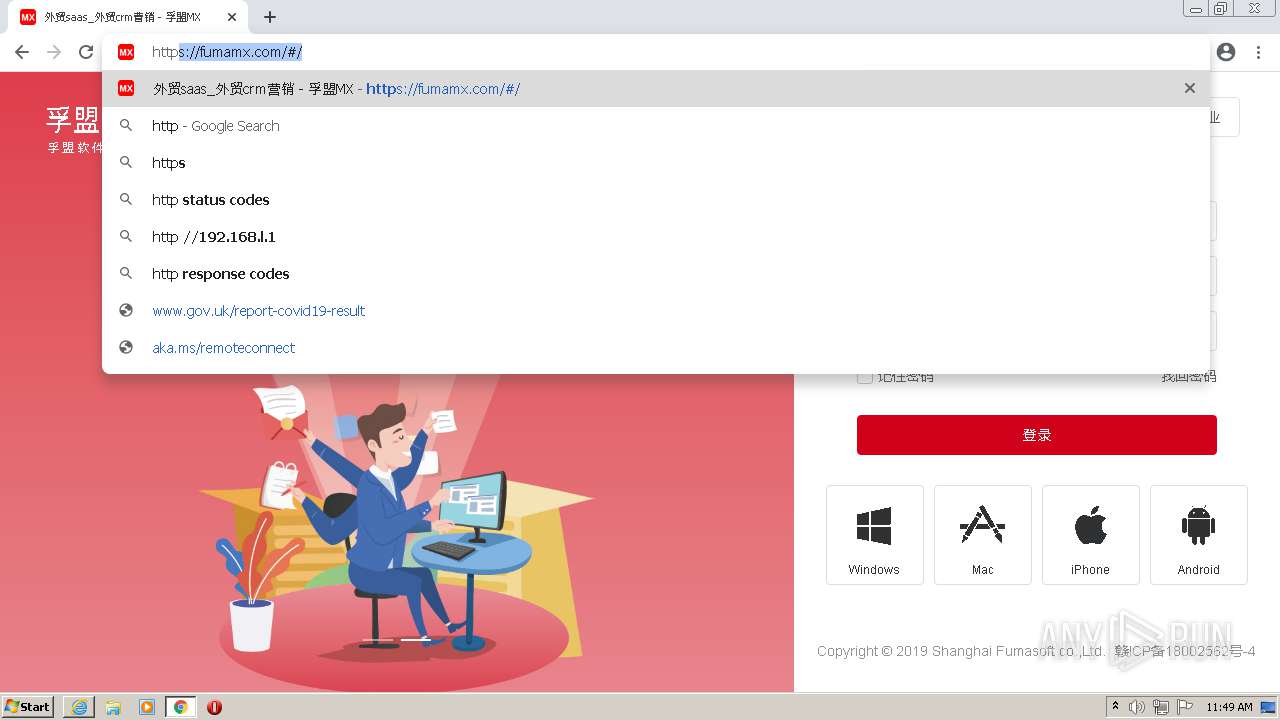
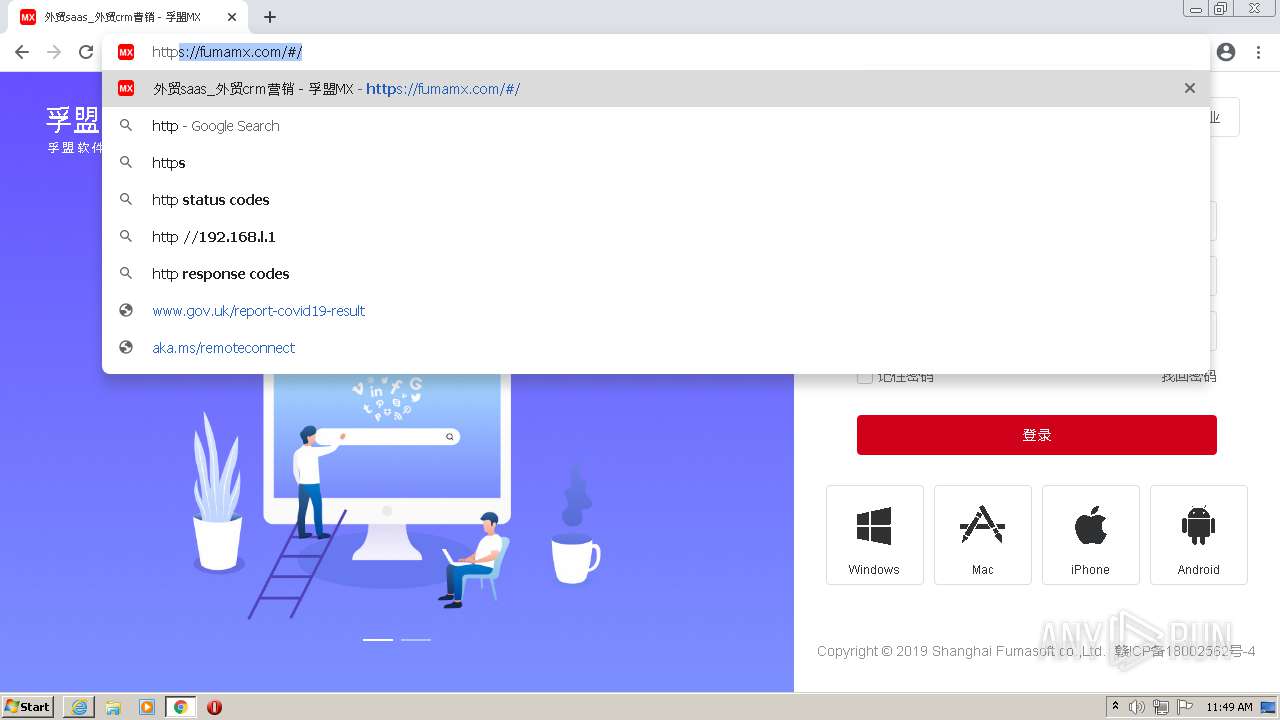
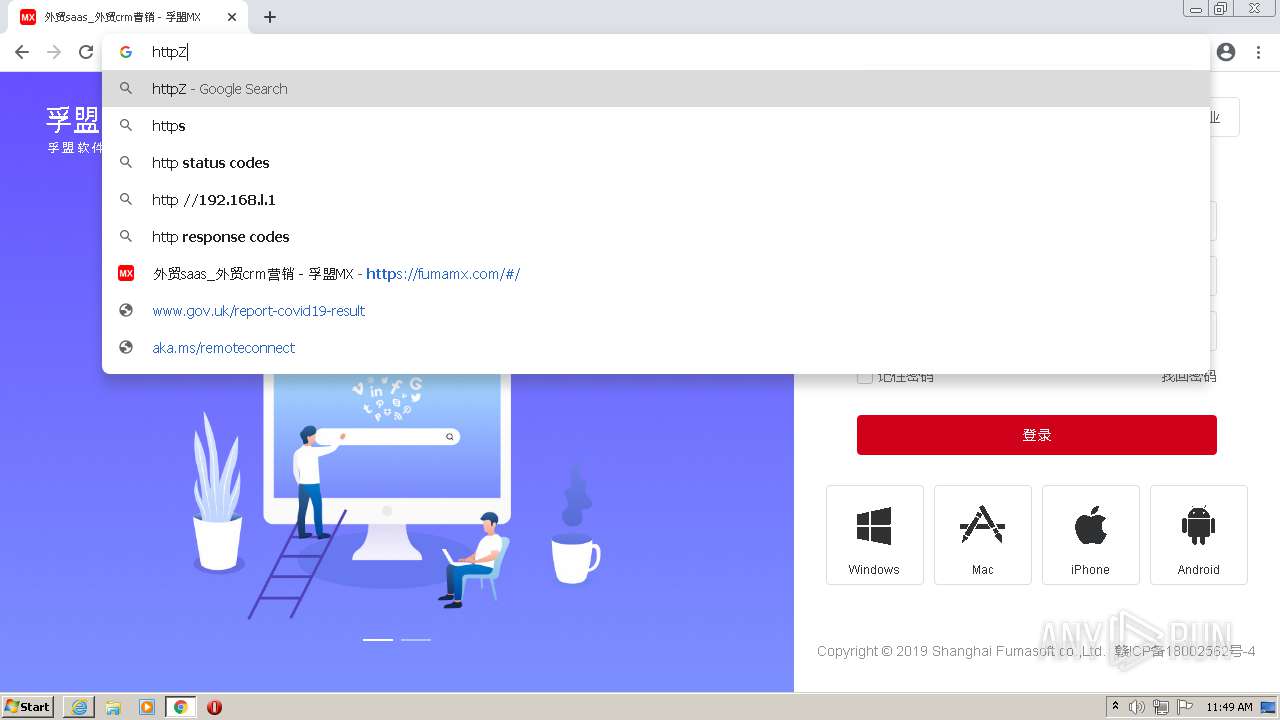
Modifies files in Chrome extension folder
- chrome.exe (PID: 3668)
INFO
Checks supported languages
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 1968)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 1760)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 872)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 688)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 960)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 2088)
- chrome.exe (PID: 2148)
Reads the computer name
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 1968)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 1760)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3856)
Changes internet zones settings
- iexplore.exe (PID: 1968)
Checks Windows Trust Settings
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 1968)
Reads internet explorer settings
- iexplore.exe (PID: 2604)
Reads settings of System Certificates
- iexplore.exe (PID: 1968)
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 2688)
Creates files in the user directory
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 1968)
Changes settings of System certificates
- iexplore.exe (PID: 1968)
Application launched itself
- chrome.exe (PID: 3668)
- iexplore.exe (PID: 1968)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1968)
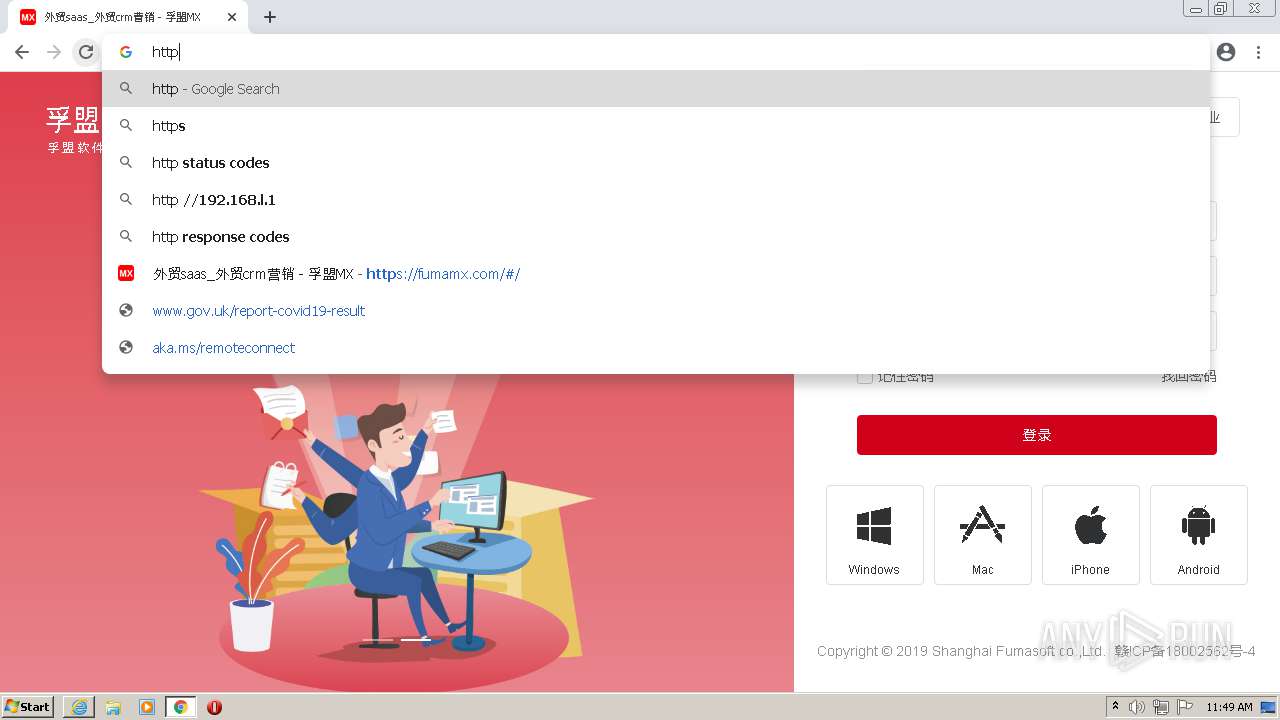
Manual execution by user
- chrome.exe (PID: 3668)
Reads the hosts file
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2688)
Reads the date of Windows installation
- chrome.exe (PID: 3884)
- iexplore.exe (PID: 1968)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2384 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2708 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=2952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1304 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2944 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
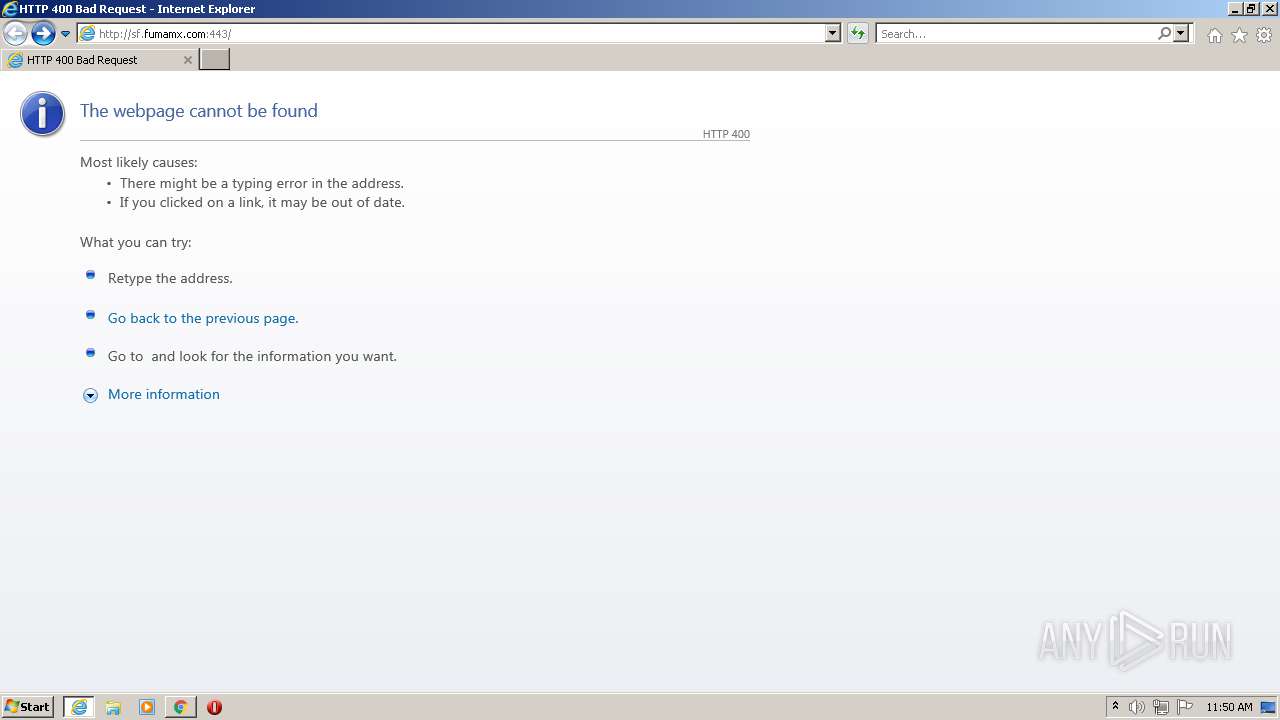
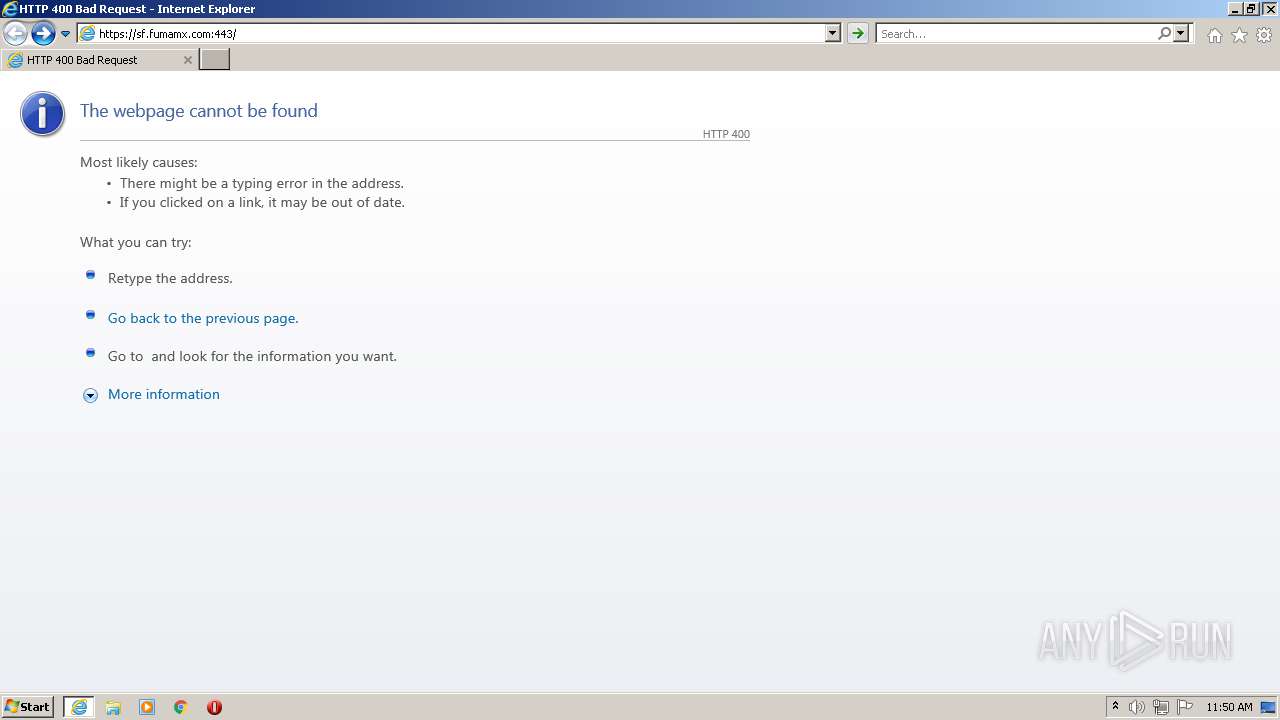
| 1968 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://sf.fumamx.com:443" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
33 518
Read events
33 142
Write events
361
Delete events
15
Modification events
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30929522 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30929522 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
234
Text files
274
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 1968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RQ9S7RGC.txt | text | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\NMX8XONJ.txt | text | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YIYEAKCX.txt | text | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\UKC1JJML.txt | text | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YLD1DUIP.txt | text | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].htm | xml | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
129
DNS requests
72
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
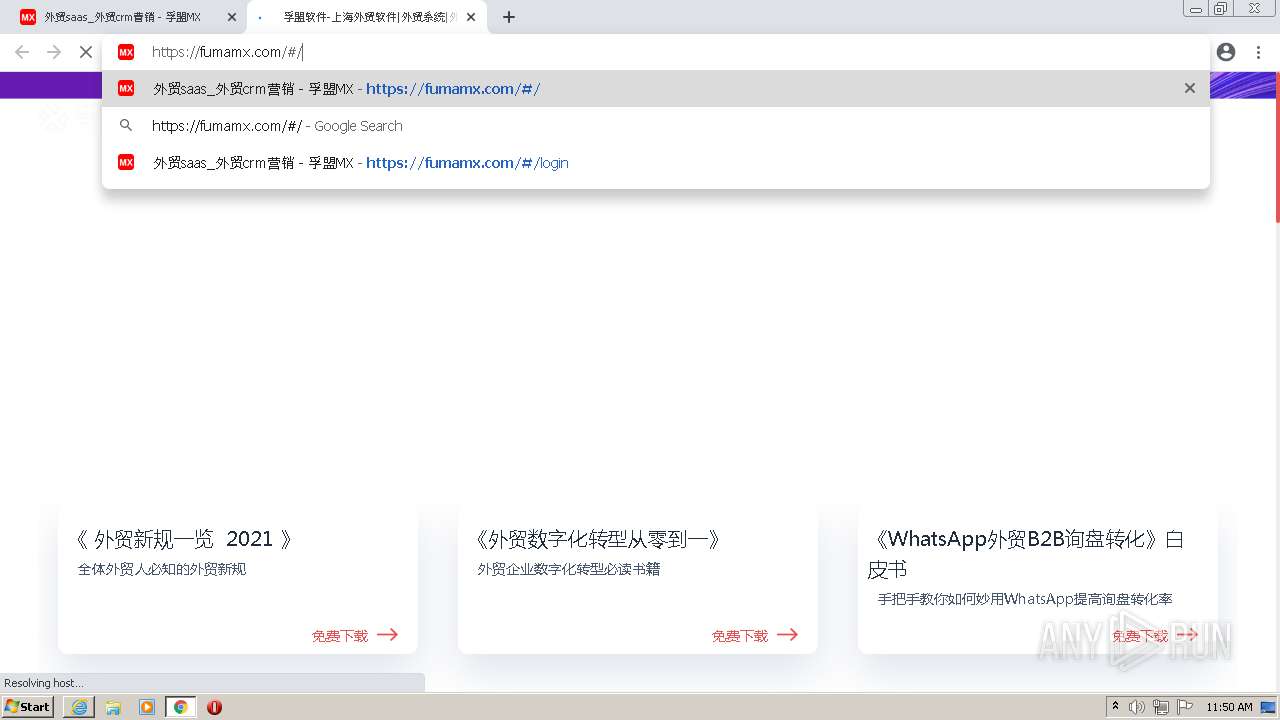
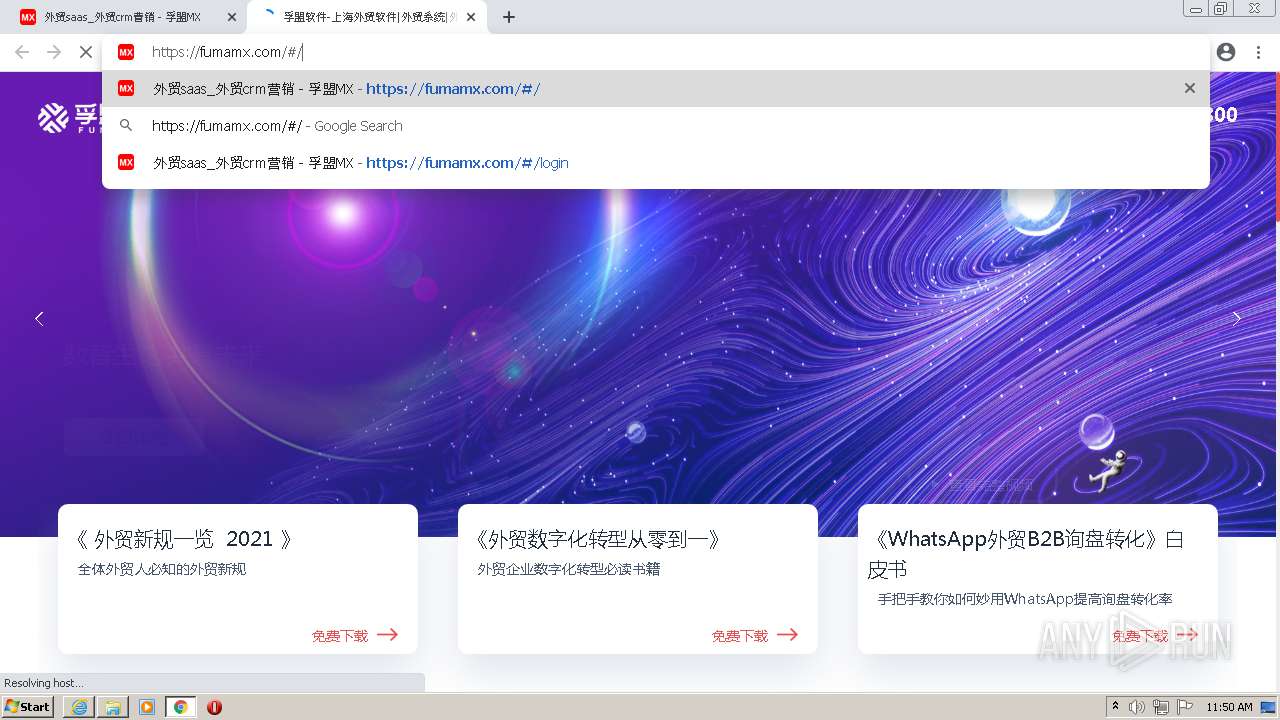
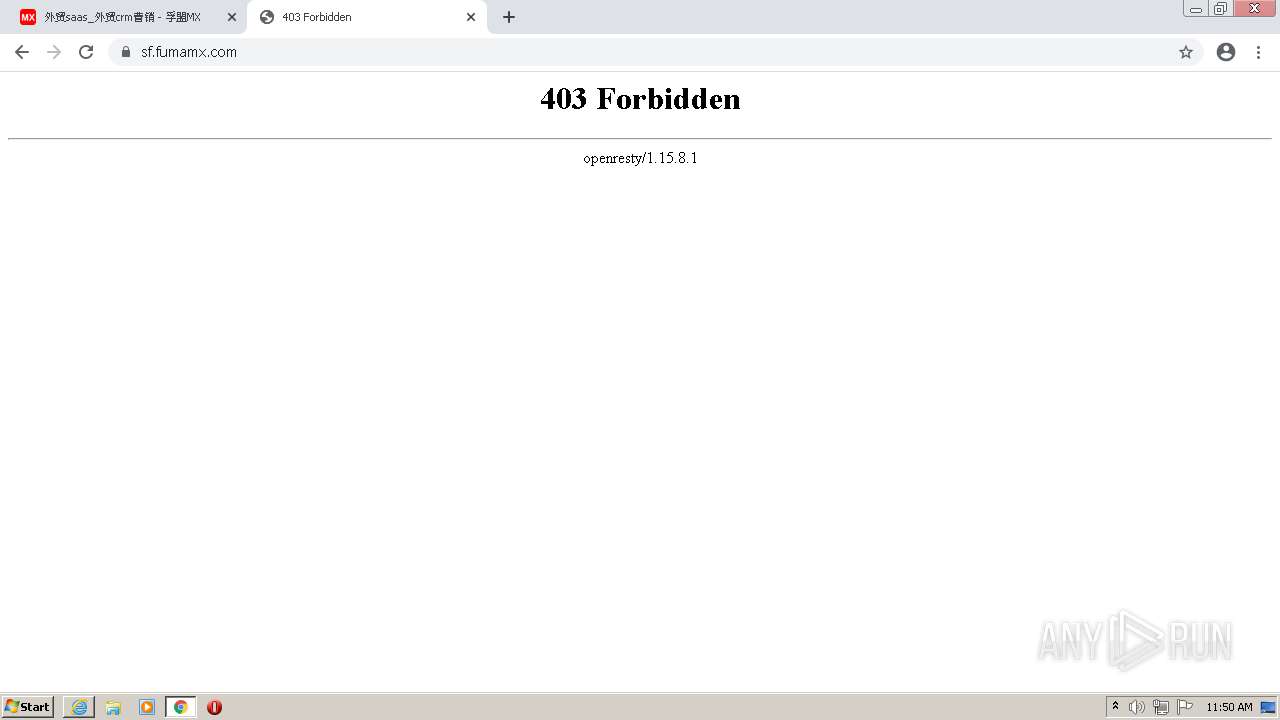
2604 | iexplore.exe | GET | 400 | 47.96.74.122:443 | http://sf.fumamx.com:443/ | CN | html | 261 b | suspicious |
1968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2604 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR0tOcjGcdlkhVARHvHzj6Qwhh26wQUpI3lvnx55HAjbS4pNK0jWNz1MX8CEAfKSFrISzBibb%2BrstOrsQk%3D | US | der | 471 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR0tOcjGcdlkhVARHvHzj6Qwhh26wQUpI3lvnx55HAjbS4pNK0jWNz1MX8CEA1io09Q7vBDLsfkfE24YzU%3D | US | der | 471 b | whitelisted |
1968 | iexplore.exe | GET | 400 | 47.96.74.122:443 | http://sf.fumamx.com:443/favicon.ico | CN | html | 261 b | suspicious |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 5.63 Kb | whitelisted |
1968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1968 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2604 | iexplore.exe | 47.96.74.122:443 | sf.fumamx.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
1968 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
2604 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
1968 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2604 | iexplore.exe | 114.215.217.142:80 | fumamx.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
2604 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2604 | iexplore.exe | 114.215.217.142:443 | fumamx.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
2604 | iexplore.exe | 163.171.128.148:443 | s1.pstatp.com | — | US | malicious |
1968 | iexplore.exe | 114.80.187.100:443 | file.fumamx.com | China Telecom (Group) | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sf.fumamx.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fumamx.com |
| suspicious |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
zerossl.ocsp.sectigo.com |
| whitelisted |
s0.pstatp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2604 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1968 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1968 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |