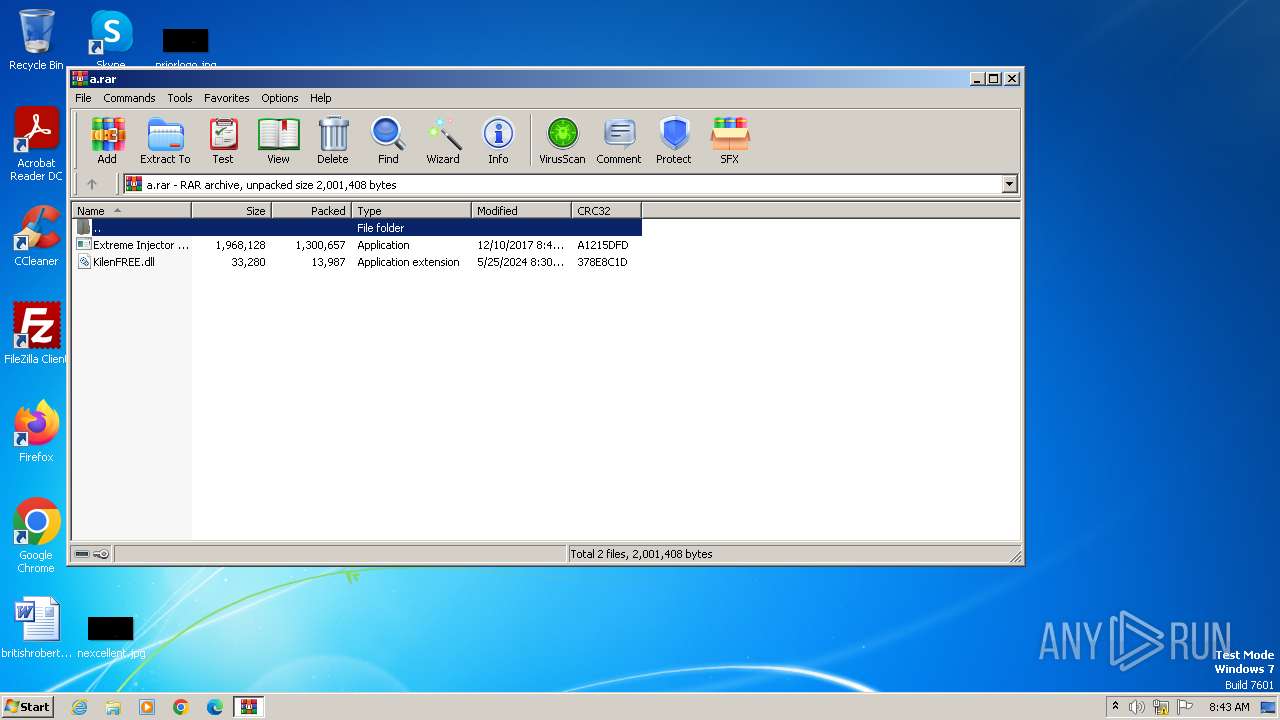
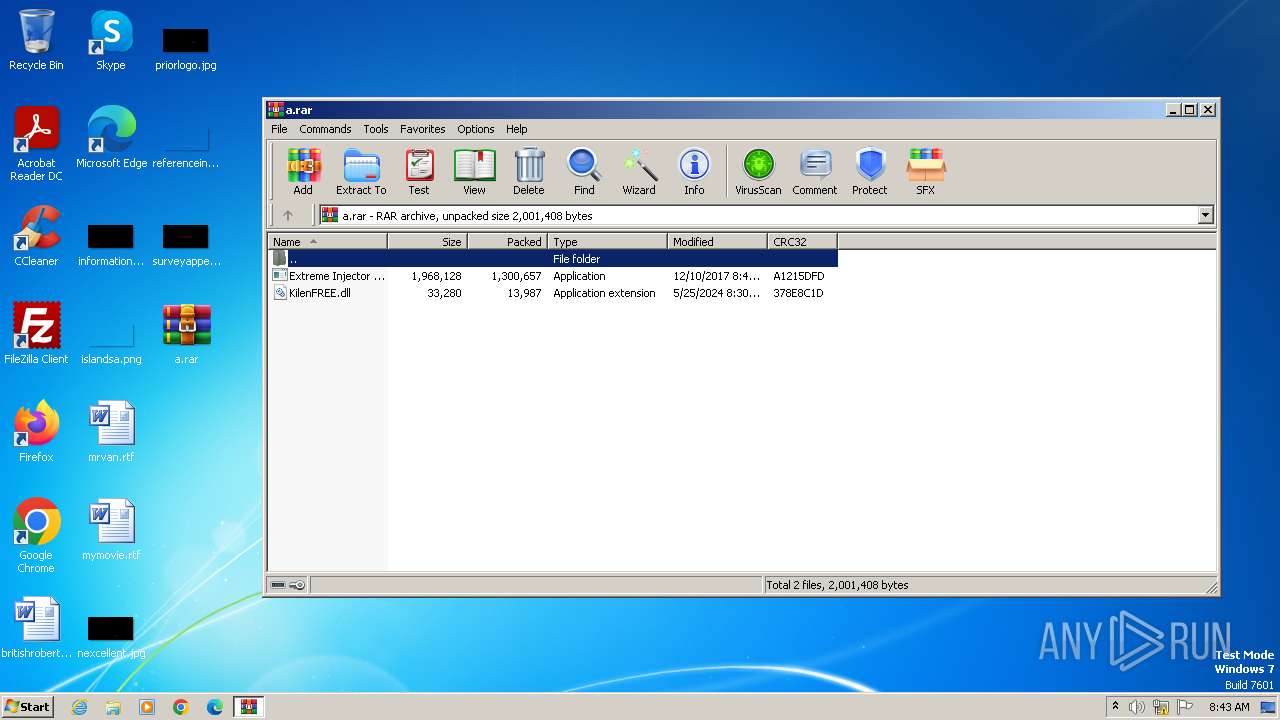
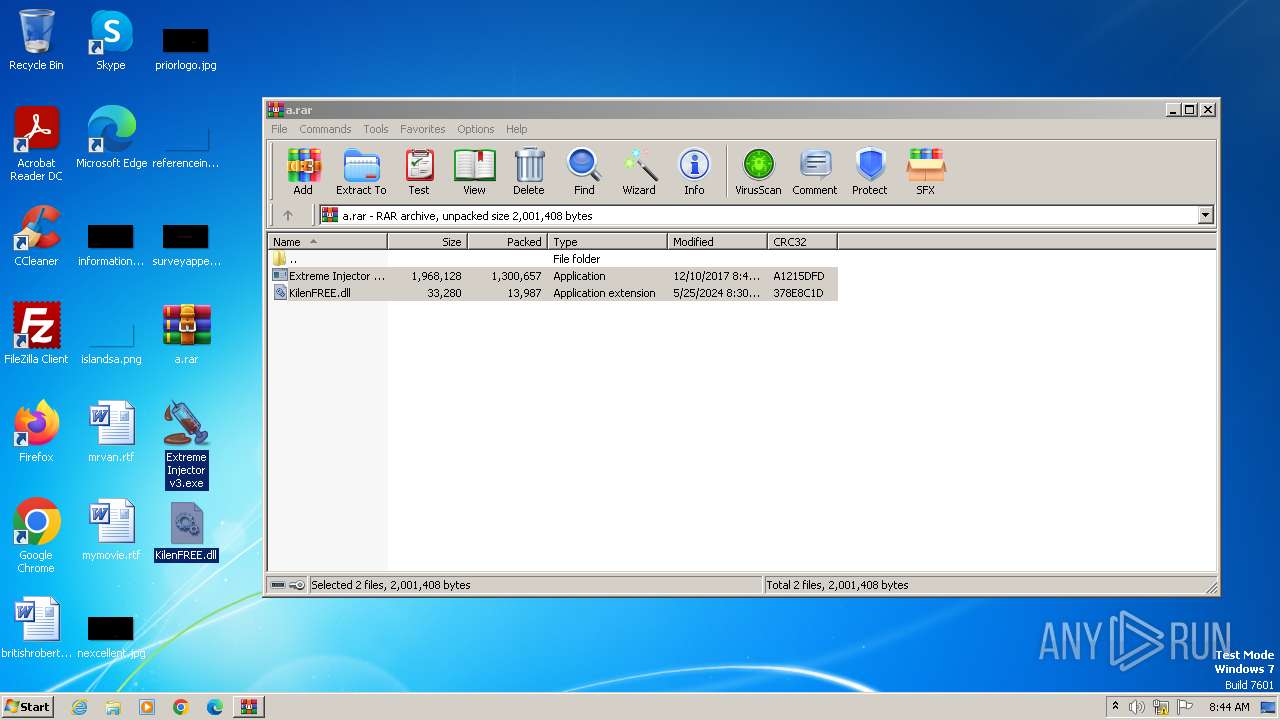
| File name: | a.rar |
| Full analysis: | https://app.any.run/tasks/8347b90f-f7f9-4189-a30e-b123b58f1d0b |
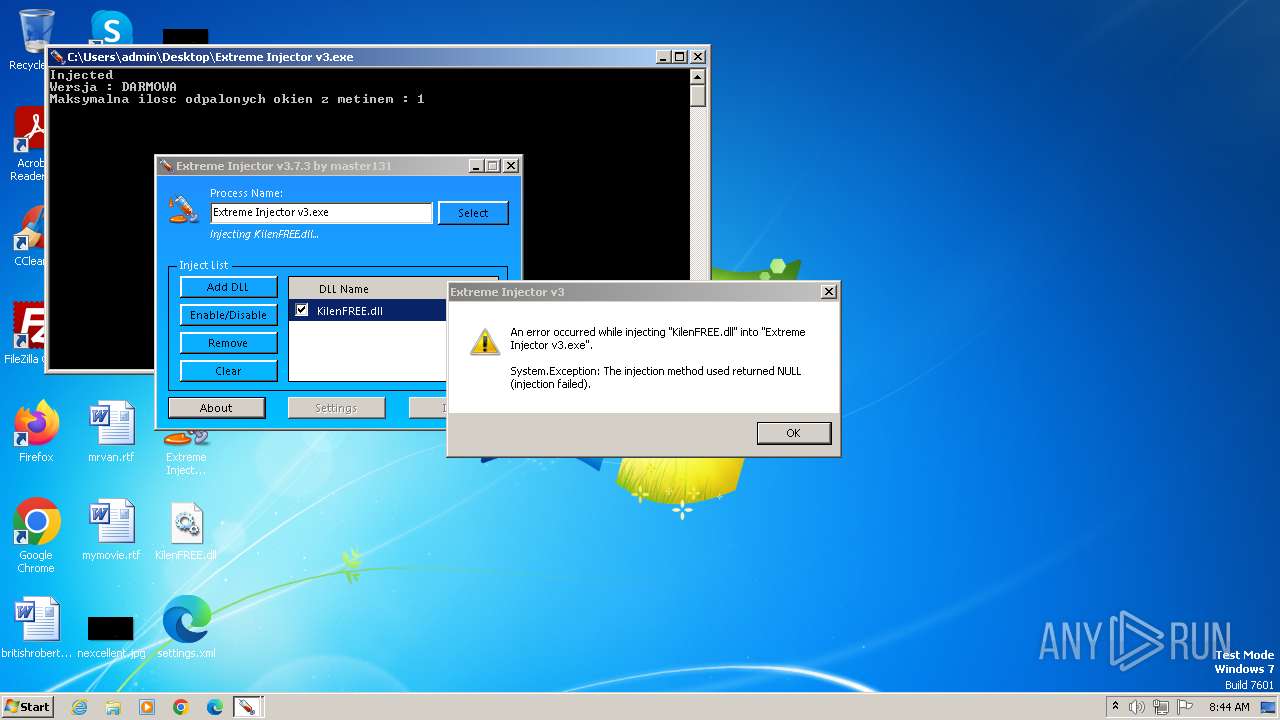
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2024, 07:43:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AFFE40B4B16FC22E060F0EC3FC3703A4 |
| SHA1: | E01C77FE0B4DAC75389F7ABC3D488FC99DAAD0D2 |
| SHA256: | D804A7396146645144B070CF6F70B9FB7A0CE3F7E03FB8B5B2EE4220E1DD1BA5 |
| SSDEEP: | 49152:cyjrvYehC9xVRGoeyQi6GVgHfwKl4fFOIg90vzdoXmp71K3NlZKZRMJCr8Sh79TV:cYrvYU4xflgi7VgHifFOIg90vzE0K9lm |
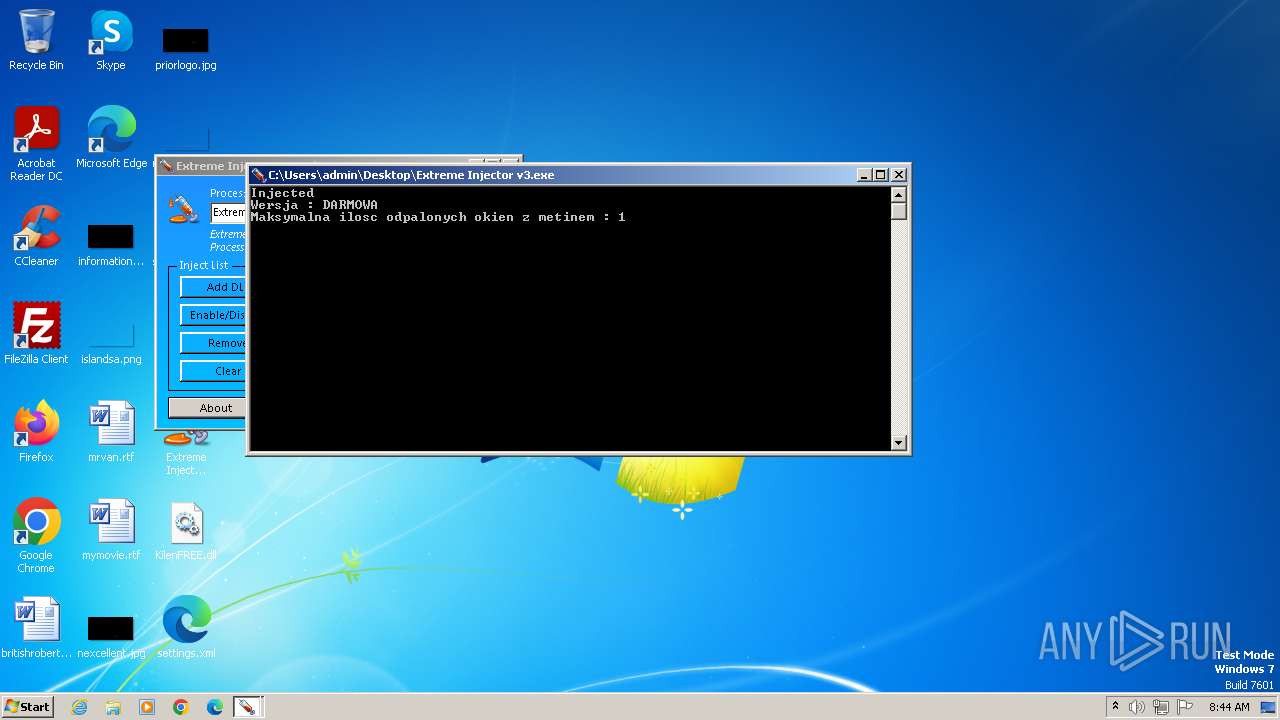
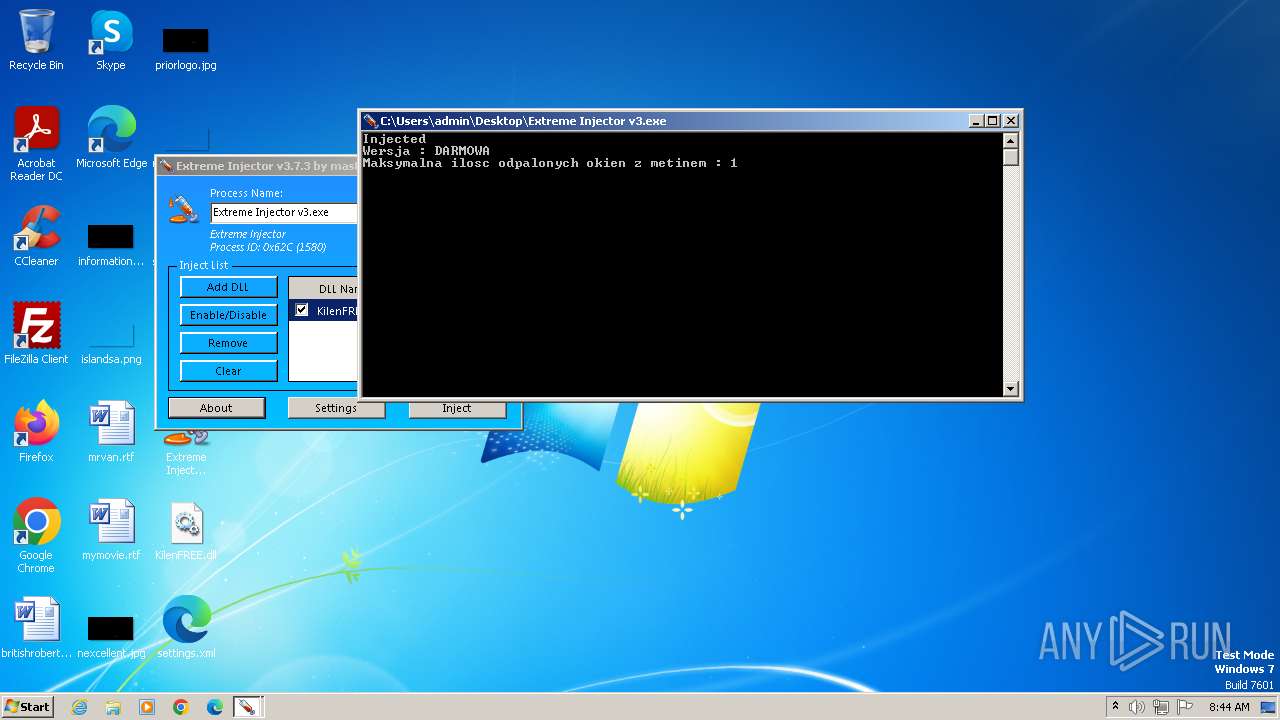
MALICIOUS
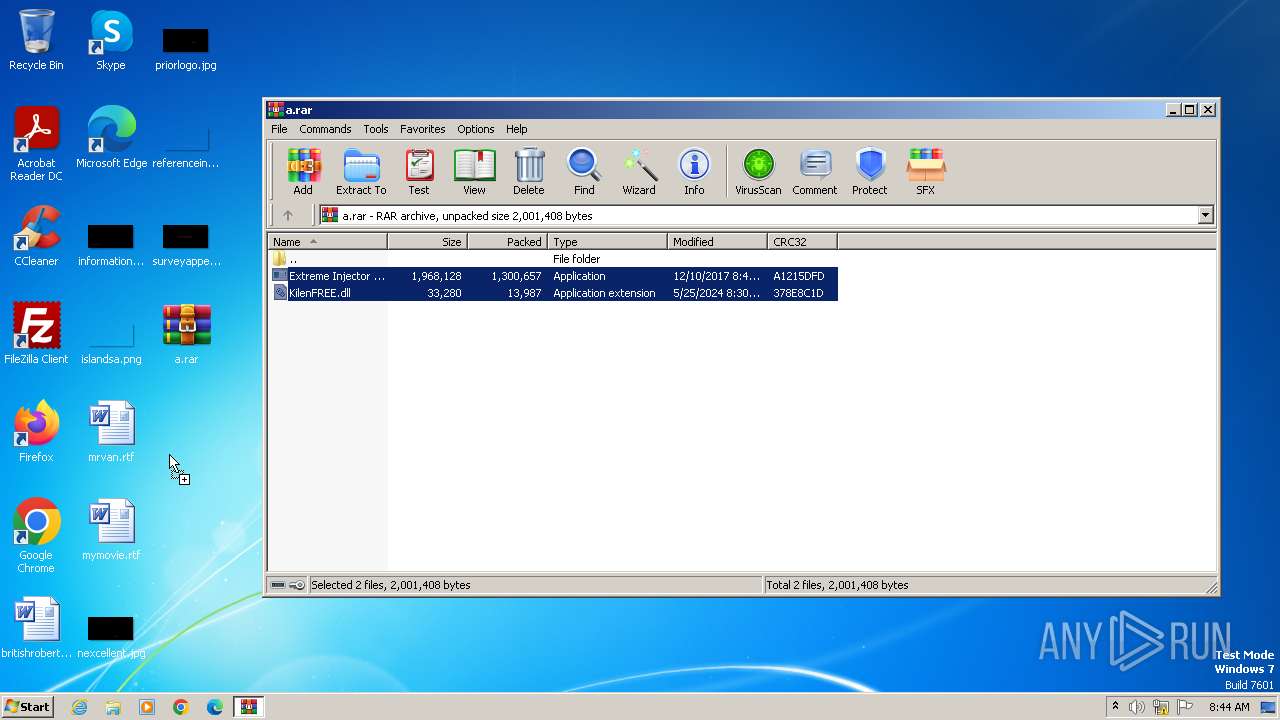
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3980)
SUSPICIOUS
Reads security settings of Internet Explorer
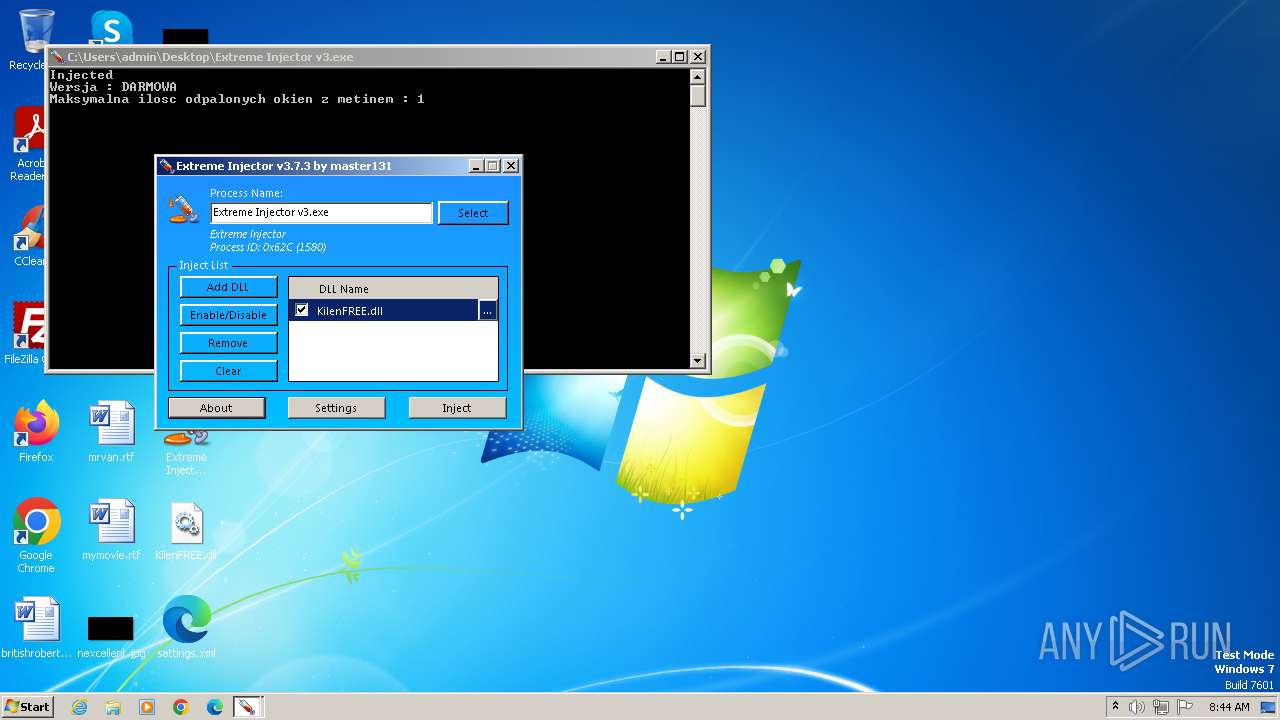
- Extreme Injector v3.exe (PID: 1064)
Reads the Internet Settings
- Extreme Injector v3.exe (PID: 1064)
- Extreme Injector v3.exe (PID: 1580)
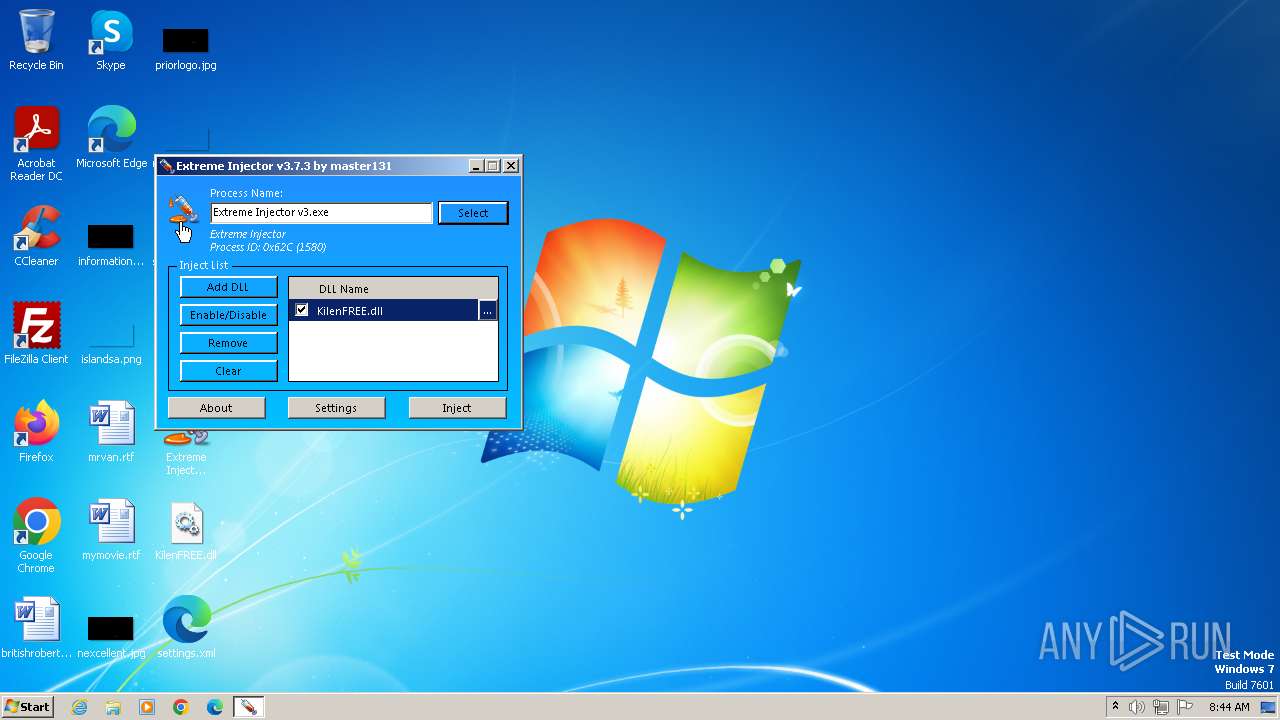
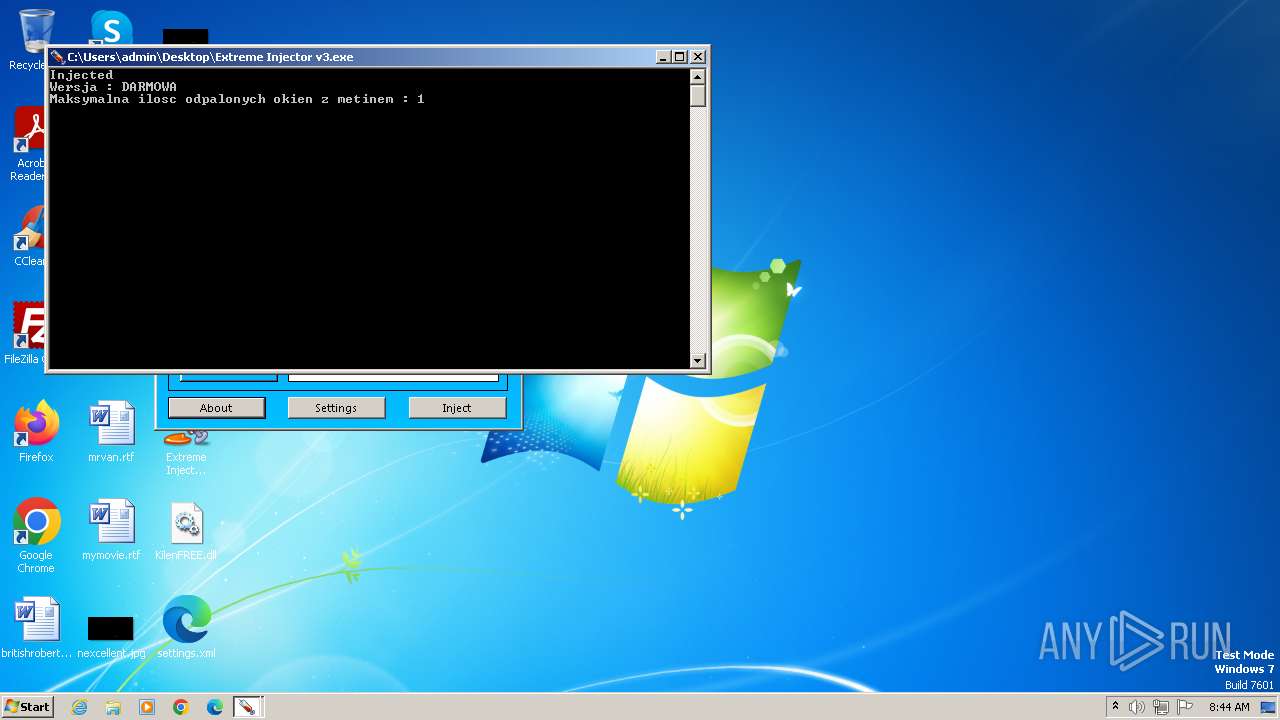
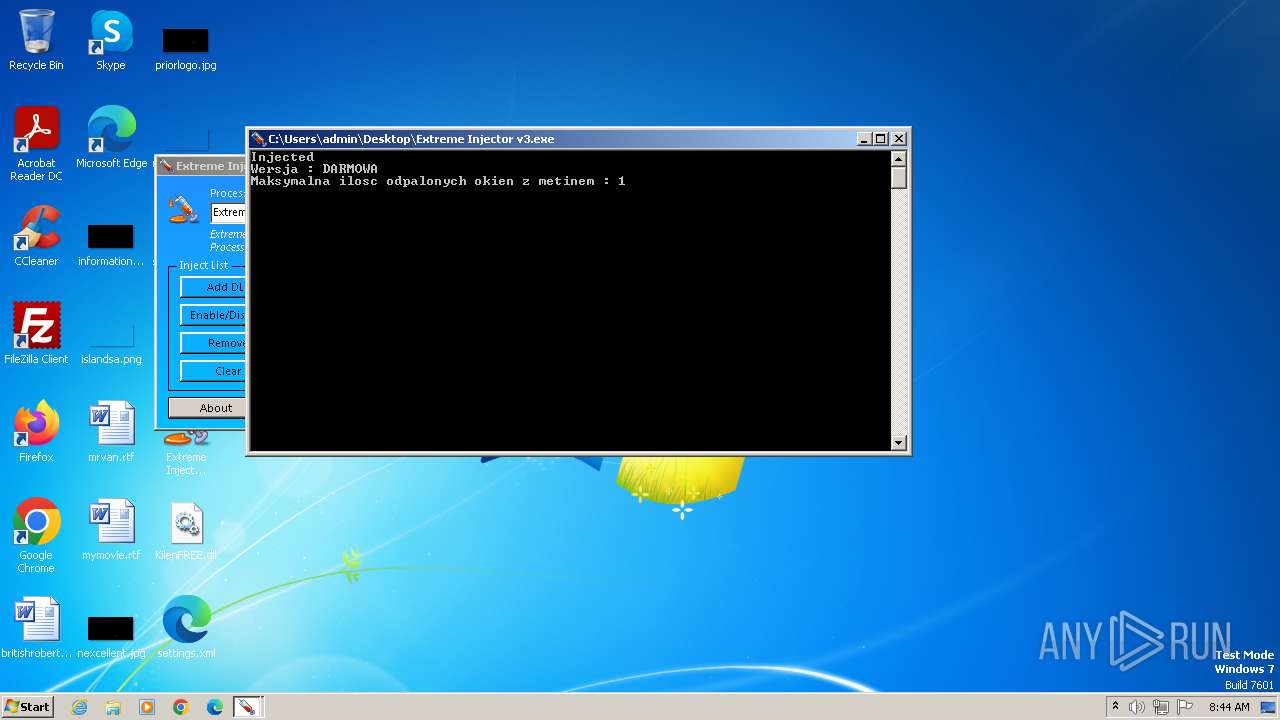
Application launched itself
- Extreme Injector v3.exe (PID: 1064)
Reads settings of System Certificates
- Extreme Injector v3.exe (PID: 1580)
INFO
Checks supported languages
- Extreme Injector v3.exe (PID: 1064)
- Extreme Injector v3.exe (PID: 1580)
- wmpnscfg.exe (PID: 2052)
Reads the computer name
- Extreme Injector v3.exe (PID: 1064)
- Extreme Injector v3.exe (PID: 1580)
- wmpnscfg.exe (PID: 2052)
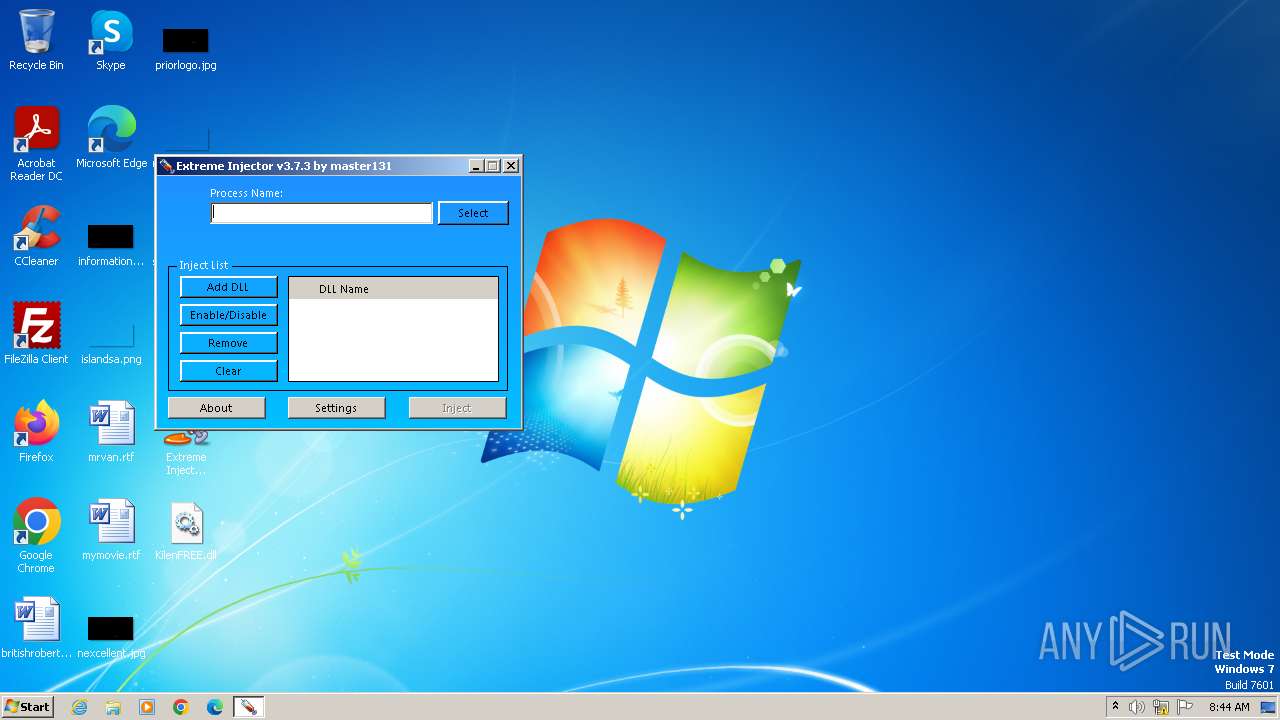
Manual execution by a user
- Extreme Injector v3.exe (PID: 1064)
- wmpnscfg.exe (PID: 2052)
Reads the machine GUID from the registry
- Extreme Injector v3.exe (PID: 1064)
- Extreme Injector v3.exe (PID: 1580)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3980)
Reads Environment values
- Extreme Injector v3.exe (PID: 1580)
Disables trace logs
- Extreme Injector v3.exe (PID: 1580)
Reads the software policy settings
- Extreme Injector v3.exe (PID: 1580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
44
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | "C:\Users\admin\Desktop\Extreme Injector v3.exe" | C:\Users\admin\Desktop\Extreme Injector v3.exe | — | explorer.exe | |||||||||||
User: admin Company: master131 Integrity Level: MEDIUM Description: Extreme Injector Exit code: 0 Version: 3.7.3.0 Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\Desktop\Extreme Injector v3.exe" | C:\Users\admin\Desktop\Extreme Injector v3.exe | Extreme Injector v3.exe | ||||||||||||
User: admin Company: master131 Integrity Level: HIGH Description: Extreme Injector Version: 3.7.3.0 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\a.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
7 857
Read events
7 795
Write events
59
Delete events
3
Modification events
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\a.rar | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3980.35103\KilenFREE.dll | executable | |
MD5:7F364C59732069B3C141079AD6995AE0 | SHA256:BA4369C2F1AE2F90EA438C3D0CEA6B8F9BCD78781CC89D1A7D1E276A7811E47C | |||
| 1580 | Extreme Injector v3.exe | C:\Users\admin\Desktop\settings.xml | xml | |
MD5:28AD2E88883024E7BFCC00817754A783 | SHA256:5F4E888E062EFA0D64E818CA1EE67189615A9B0FEC4DD386D108C0972CFC6DF2 | |||
| 3980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3980.35103\Extreme Injector v3.exe | executable | |
MD5:EC801A7D4B72A288EC6C207BB9FF0131 | SHA256:B65F40618F584303CA0BCF9B5F88C233CC4237699C0C4BF40BA8FACBE8195A46 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1580 | Extreme Injector v3.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |