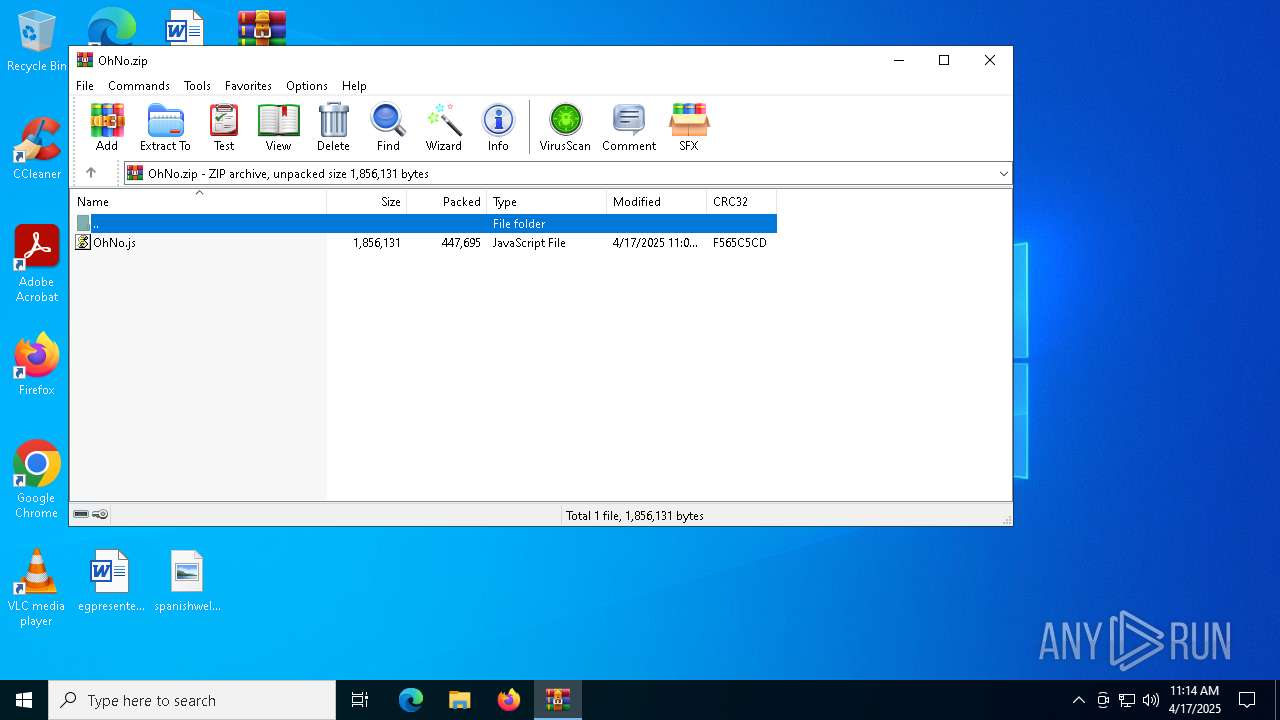
| File name: | OhNo.zip |
| Full analysis: | https://app.any.run/tasks/e80f9084-fb37-4bc5-85a0-8efa700fe882 |
| Verdict: | Malicious activity |
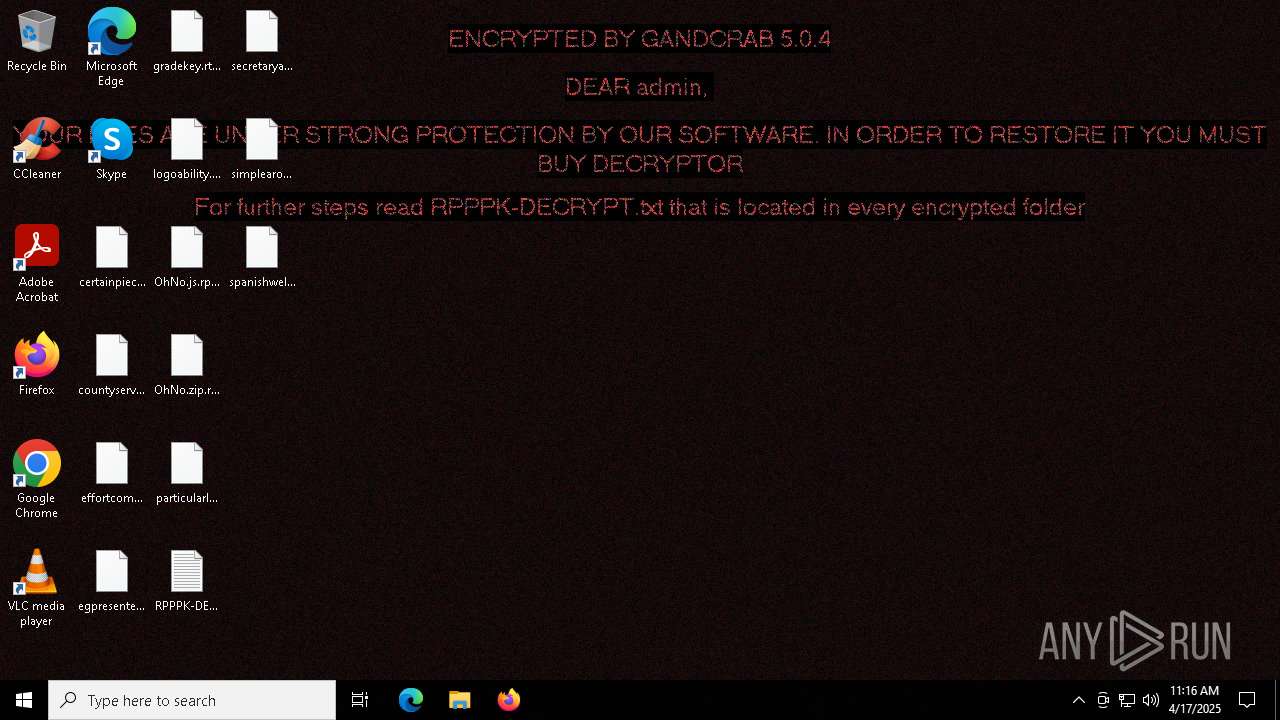
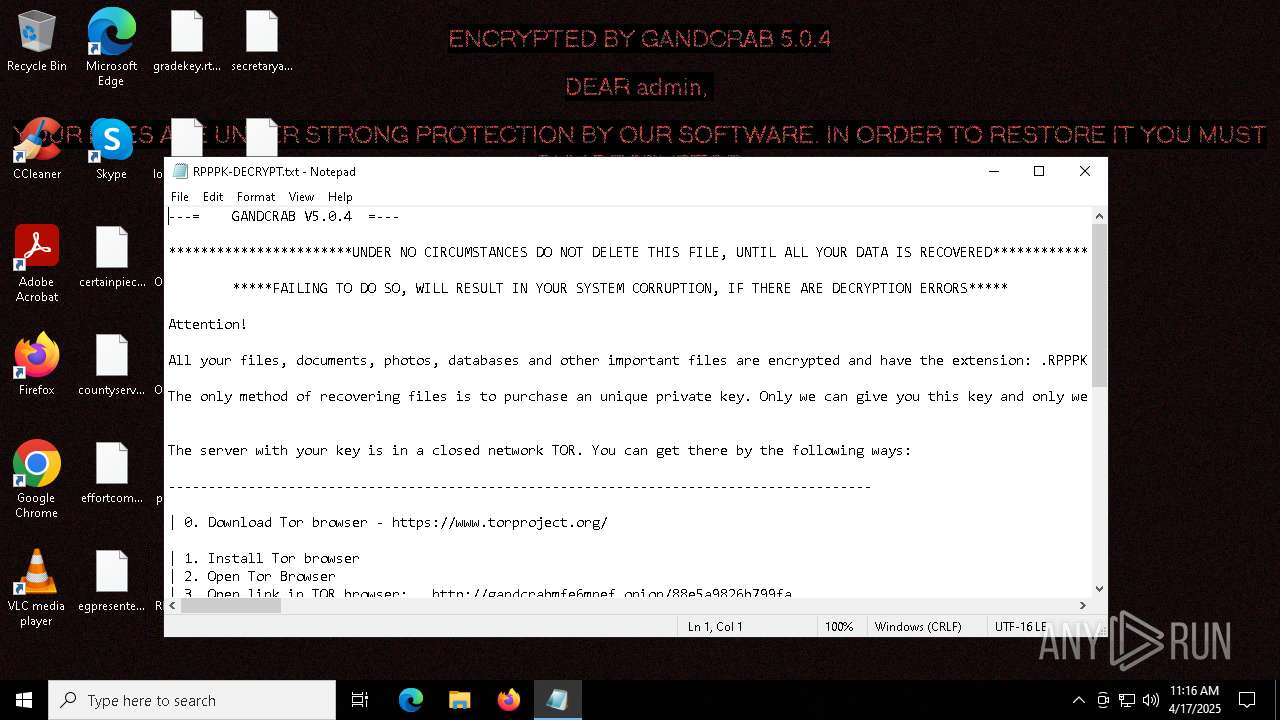
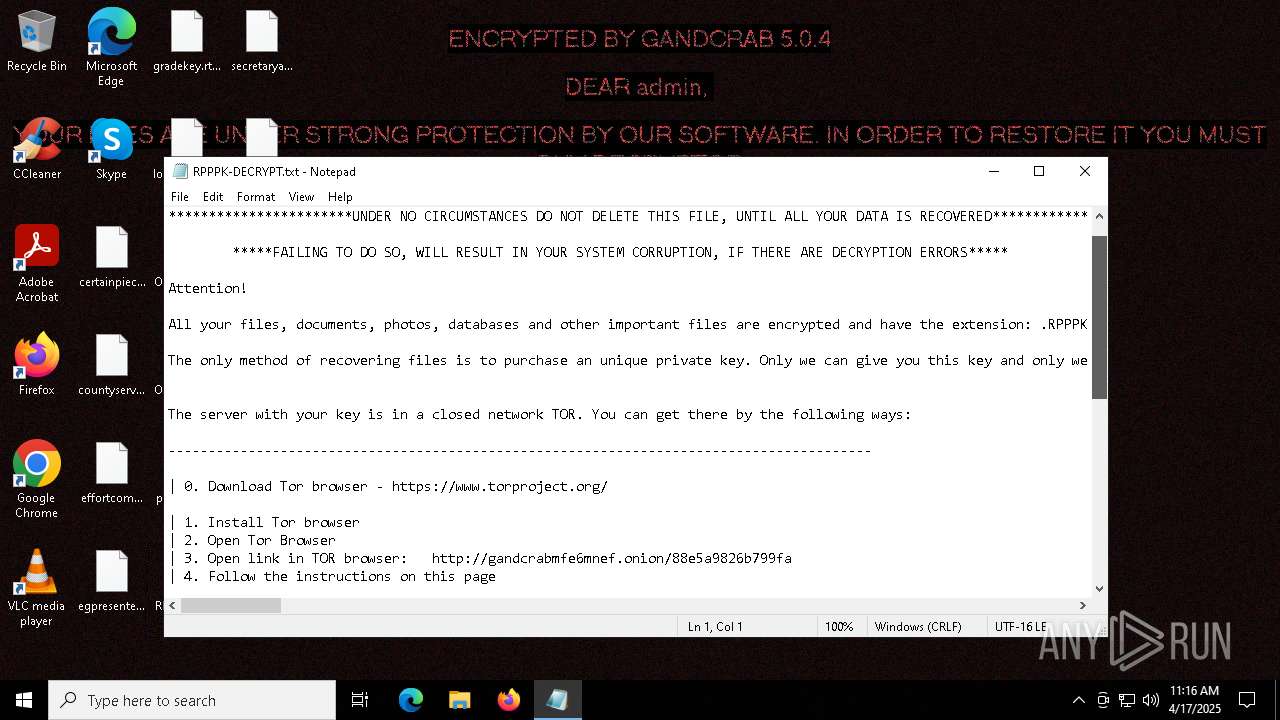
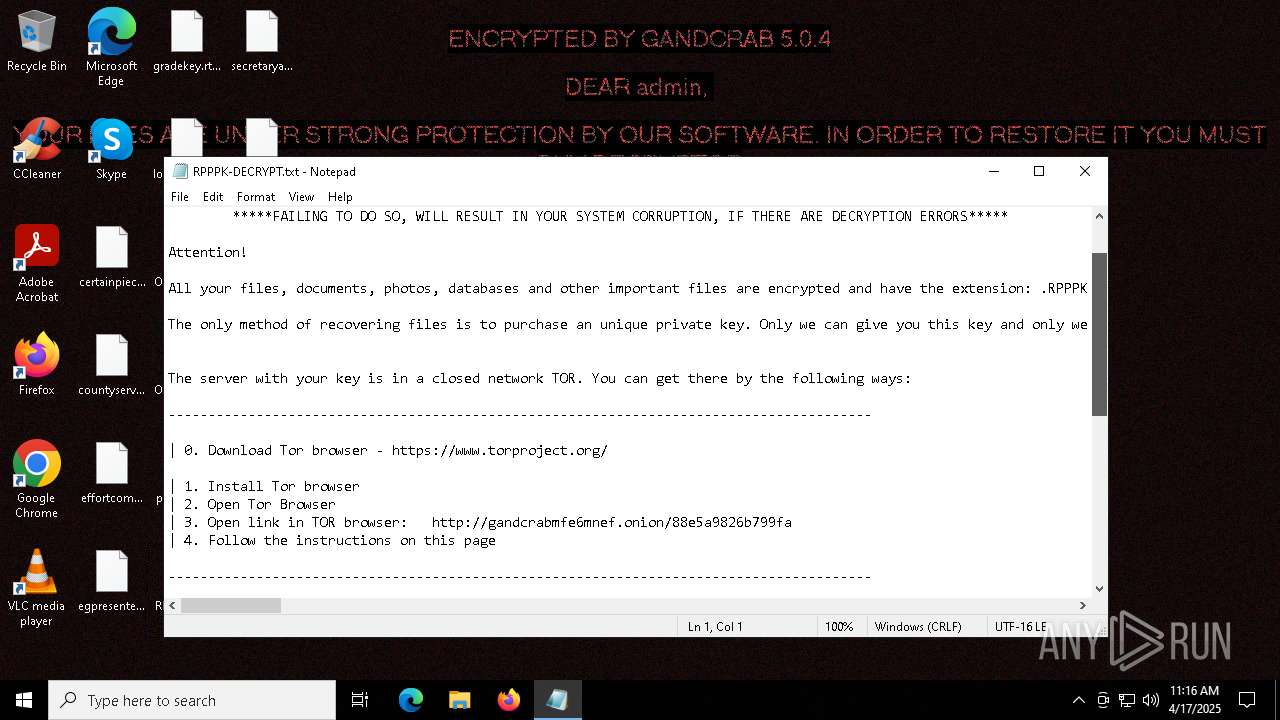
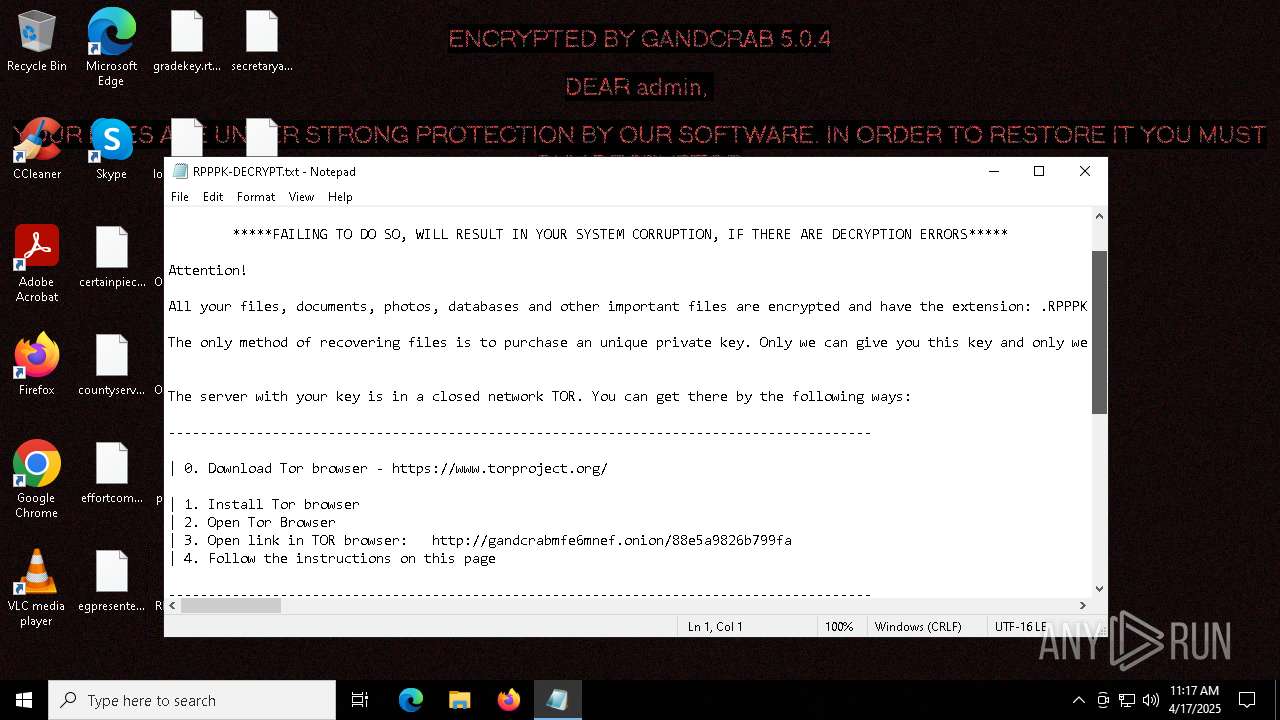
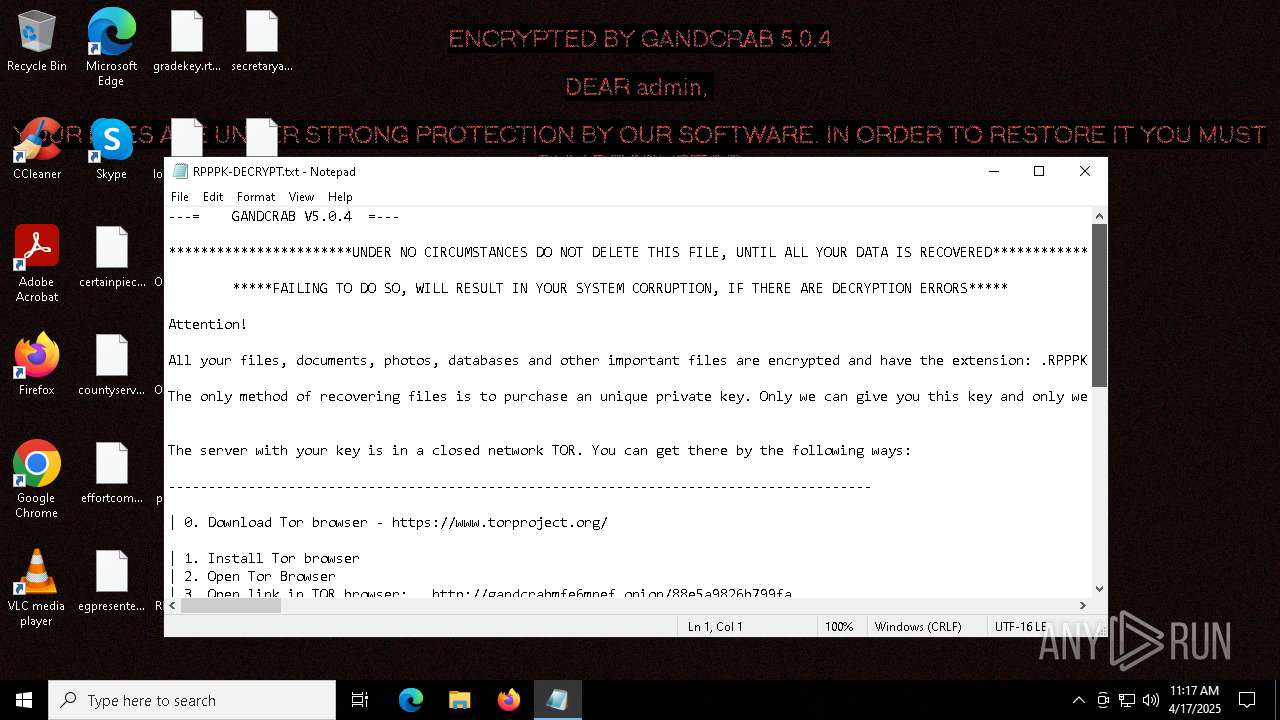
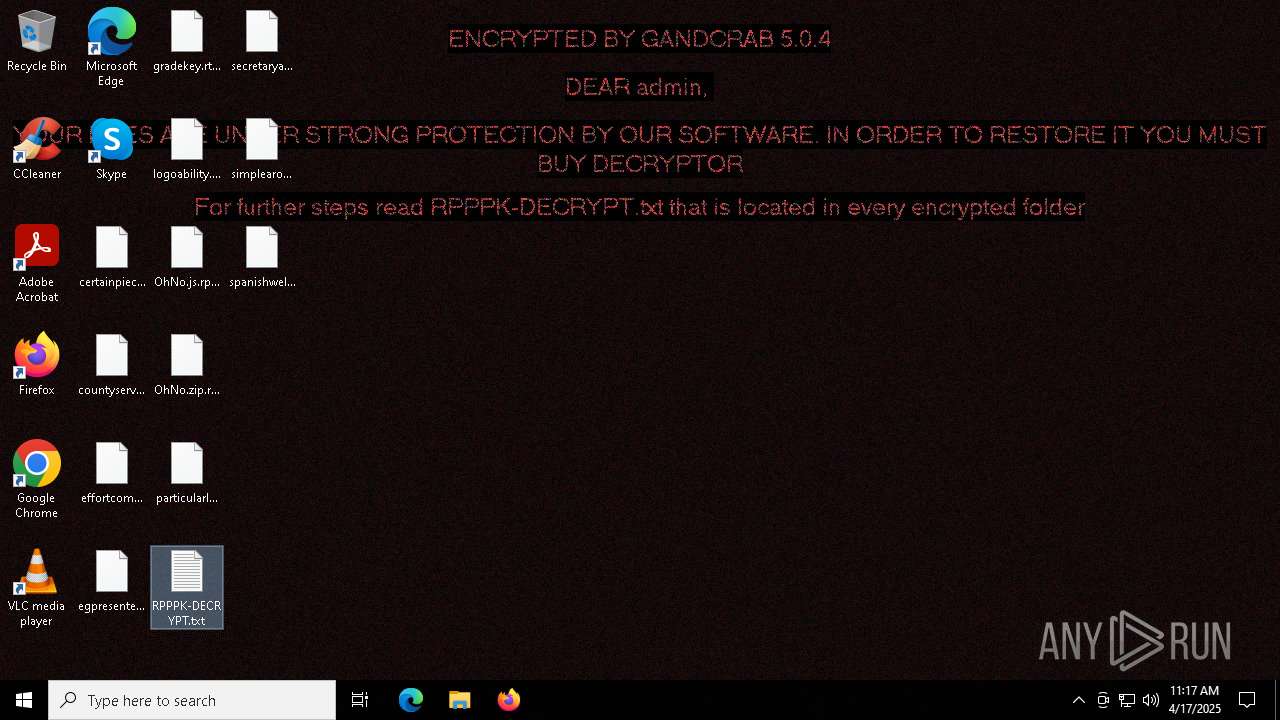
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | April 17, 2025, 11:14:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 72F9CE6E9A0842E87D7511D9843B495C |
| SHA1: | 60B18124990CC747F841C2AFB21A3AABE1214001 |
| SHA256: | D7F5A5343A2278D07CA9F656AADC93AB9B218026E11869FE7B72D122A7FC0F2D |
| SSDEEP: | 12288:ps2Plz+HSajsQlNcYk/xbLQ7YXEJJXFv5O0KqF:pdPlz+HSajVfnk/xbEMX4VBO0KqF |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2284)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 6032)
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 6032)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 6032)
Bypass execution policy to execute commands
- powershell.exe (PID: 2092)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 6032)
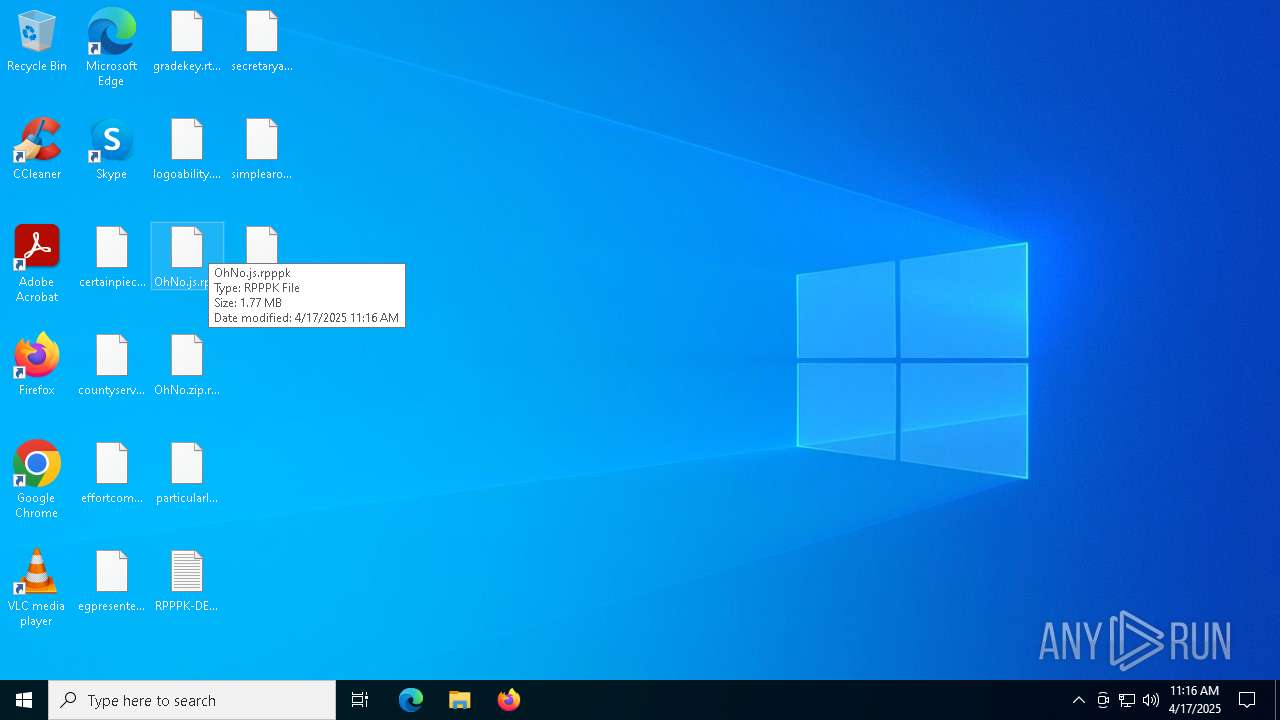
Renames files like ransomware
- powershell.exe (PID: 2092)
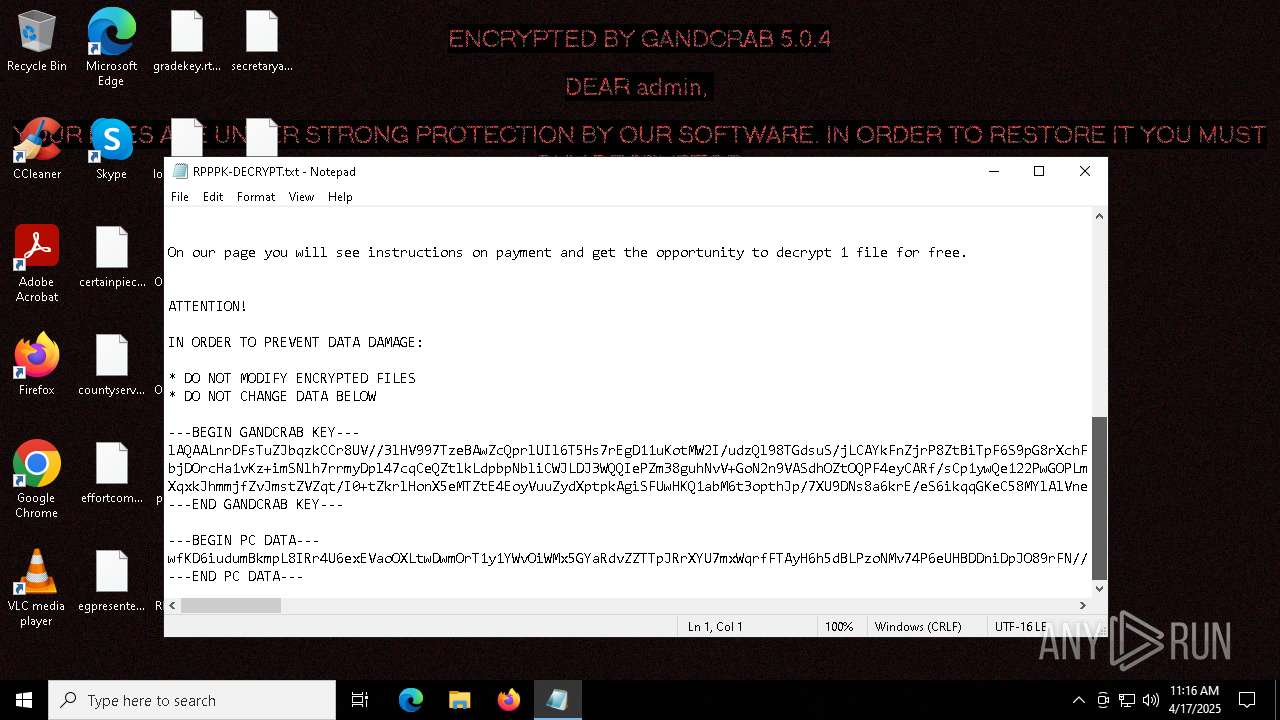
GandCrab keys are found
- powershell.exe (PID: 2092)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2092)
RANSOMWARE has been detected
- powershell.exe (PID: 2092)
Writes a file to the Word startup folder
- powershell.exe (PID: 2092)
Deletes shadow copies
- powershell.exe (PID: 2092)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6032)
Changes charset (SCRIPT)
- wscript.exe (PID: 6032)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 6032)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 6032)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 6032)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 6032)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 6032)
Converts TXT file into a string
- powershell.exe (PID: 2092)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 6032)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6032)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2092)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6032)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2092)
Creates file in the systems drive root
- powershell.exe (PID: 2092)
INFO
Manual execution by a user
- wscript.exe (PID: 6032)
- notepad.exe (PID: 2392)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2092)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 2092)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 2092)
Found Base64 encoded compression PowerShell classes (YARA)
- powershell.exe (PID: 2092)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 2092)
Reads the software policy settings
- slui.exe (PID: 6040)
- slui.exe (PID: 5400)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 2092)
Reads CPU info
- powershell.exe (PID: 2092)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2392)
- WMIC.exe (PID: 2140)
Checks proxy server information
- powershell.exe (PID: 2092)
- slui.exe (PID: 5400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:17 04:05:16 |
| ZipCRC: | 0xf565c5cd |
| ZipCompressedSize: | 447695 |
| ZipUncompressedSize: | 1856131 |
| ZipFileName: | OhNo.js |
Total processes
140
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1276 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -Command "IEX (([System.IO.File]::ReadAllText('C:\Users\admin\AppData\Roaming\buippdgrgk.log')).Replace('?',''));" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | "C:\WINDOWS\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\SysWOW64\wbem\WMIC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
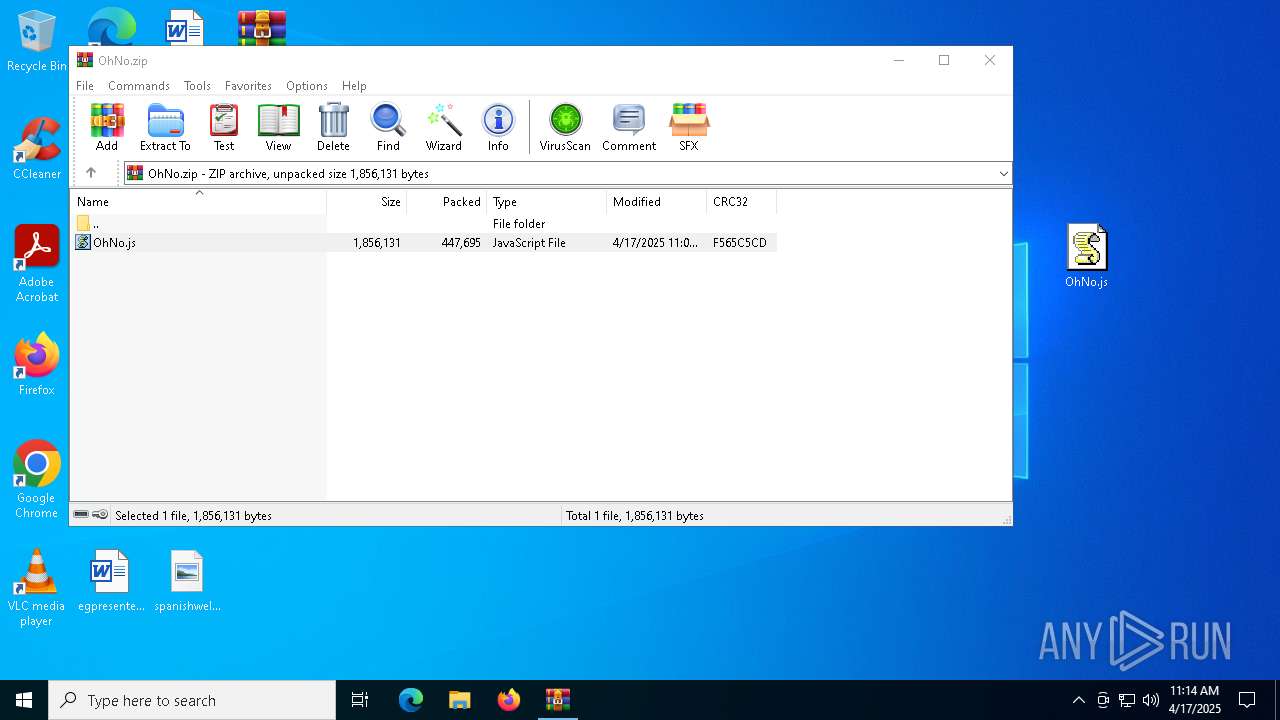
| 2284 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\OhNo.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
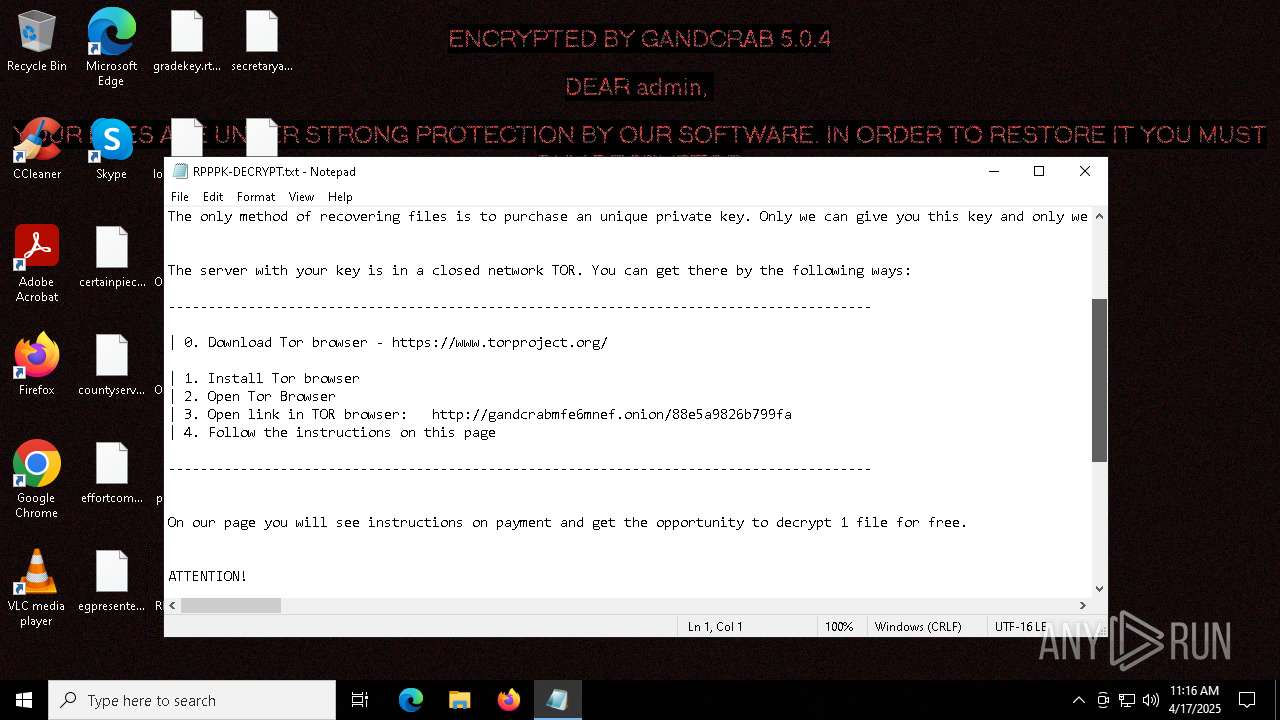
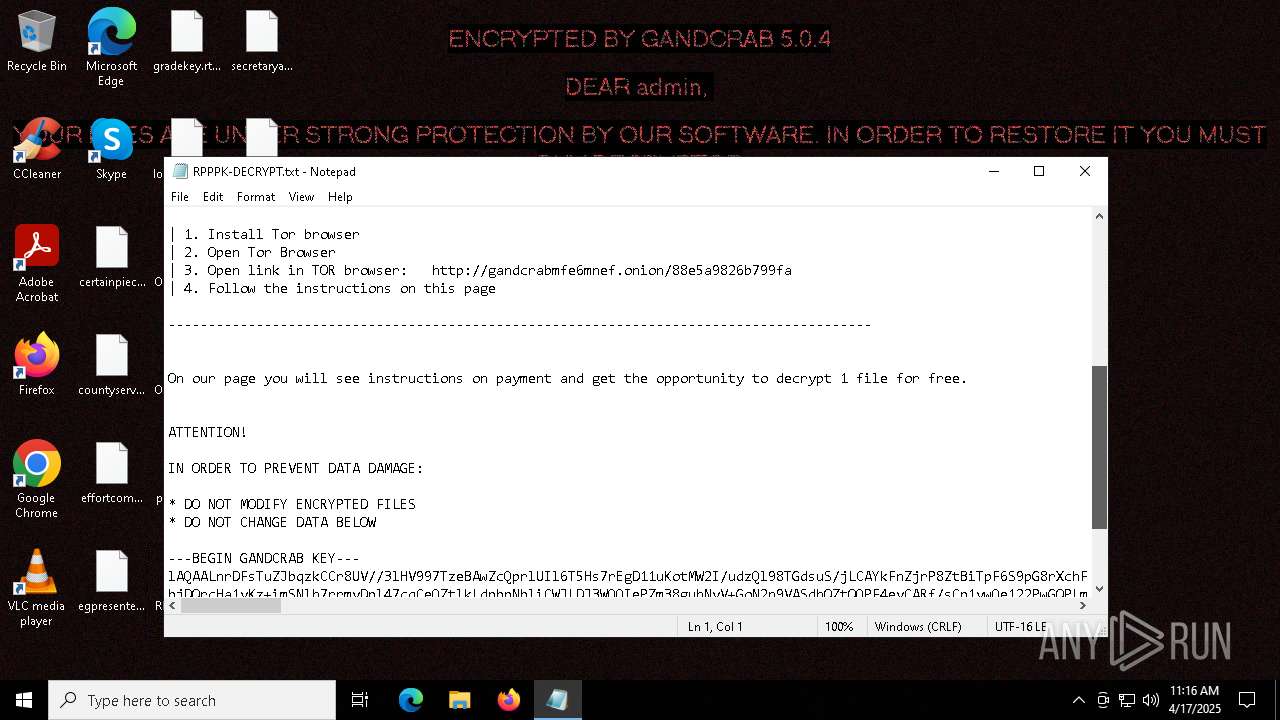
| 2392 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\RPPPK-DECRYPT.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\OhNo.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
24 138
Read events
24 113
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\OhNo.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
0
Suspicious files
1 026
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2092 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dsct43yz.zz3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6032 | wscript.exe | C:\Users\admin\AppData\Roaming\buippdgrgk.log | text | |
MD5:F82FA95AF7C7711B7EB03038A3D7B92F | SHA256:E8A87BB31665AADBEDAAE5C3A0B3DB6346ABFEF5DE8ED8C9E9A04F708D398E61 | |||
| 2092 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\RPPPK-DECRYPT.txt | binary | |
MD5:D954F50AB6DDBCA66F9039A26FCFAB17 | SHA256:5446C5473AE71B95EFF3E7693517B6125493923EE38A36362FF7EEE39F389D6B | |||
| 2092 | powershell.exe | C:\bootTel.dat | binary | |
MD5:23155C5554230E5E73DE8C6A003F0FEE | SHA256:AE1E56343EC1E1C744E1045235408596DD5ED942C5F1C435639024A00A1EA6AE | |||
| 2284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2284.29426\OhNo.js | text | |
MD5:16C8B6CED2E5A69F50ED0CEDD893D197 | SHA256:39D4EF8A68D2427D6EB1D26574F0A0927C846047095225F993C3A13A292CD3D5 | |||
| 2092 | powershell.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\RPPPK-DECRYPT.txt | binary | |
MD5:D954F50AB6DDBCA66F9039A26FCFAB17 | SHA256:5446C5473AE71B95EFF3E7693517B6125493923EE38A36362FF7EEE39F389D6B | |||
| 2092 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8B8A832FCE2174C8FEE26B70F2483FBB | SHA256:0FBA3A37EF443507F533A7C3F31C0B5826EA416B95FDE43479E02D4E0C29400B | |||
| 2092 | powershell.exe | C:\Users\admin\RPPPK-DECRYPT.txt | binary | |
MD5:D954F50AB6DDBCA66F9039A26FCFAB17 | SHA256:5446C5473AE71B95EFF3E7693517B6125493923EE38A36362FF7EEE39F389D6B | |||
| 2092 | powershell.exe | C:\Users\admin\AppData\RPPPK-DECRYPT.txt | binary | |
MD5:D954F50AB6DDBCA66F9039A26FCFAB17 | SHA256:5446C5473AE71B95EFF3E7693517B6125493923EE38A36362FF7EEE39F389D6B | |||
| 2092 | powershell.exe | C:\Users\admin\3D Objects\RPPPK-DECRYPT.txt | binary | |
MD5:D954F50AB6DDBCA66F9039A26FCFAB17 | SHA256:5446C5473AE71B95EFF3E7693517B6125493923EE38A36362FF7EEE39F389D6B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
42
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2092 | powershell.exe | GET | — | 217.26.63.20:80 | http://www.haargenau.biz/ | unknown | — | — | malicious |
2092 | powershell.exe | GET | 301 | 77.75.249.22:80 | http://www.2mmotorsport.biz/ | unknown | — | — | malicious |
2092 | powershell.exe | GET | 200 | 184.24.77.61:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgPPnKbhreEUZwelNITCg9lyfQ%3D%3D | unknown | — | — | whitelisted |
2092 | powershell.exe | GET | 301 | 18.197.248.23:80 | http://www.holzbock.biz/ | unknown | — | — | malicious |
2092 | powershell.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2092 | powershell.exe | GET | 302 | 185.177.62.27:80 | http://www.pizcam.com/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3240 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3240 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |