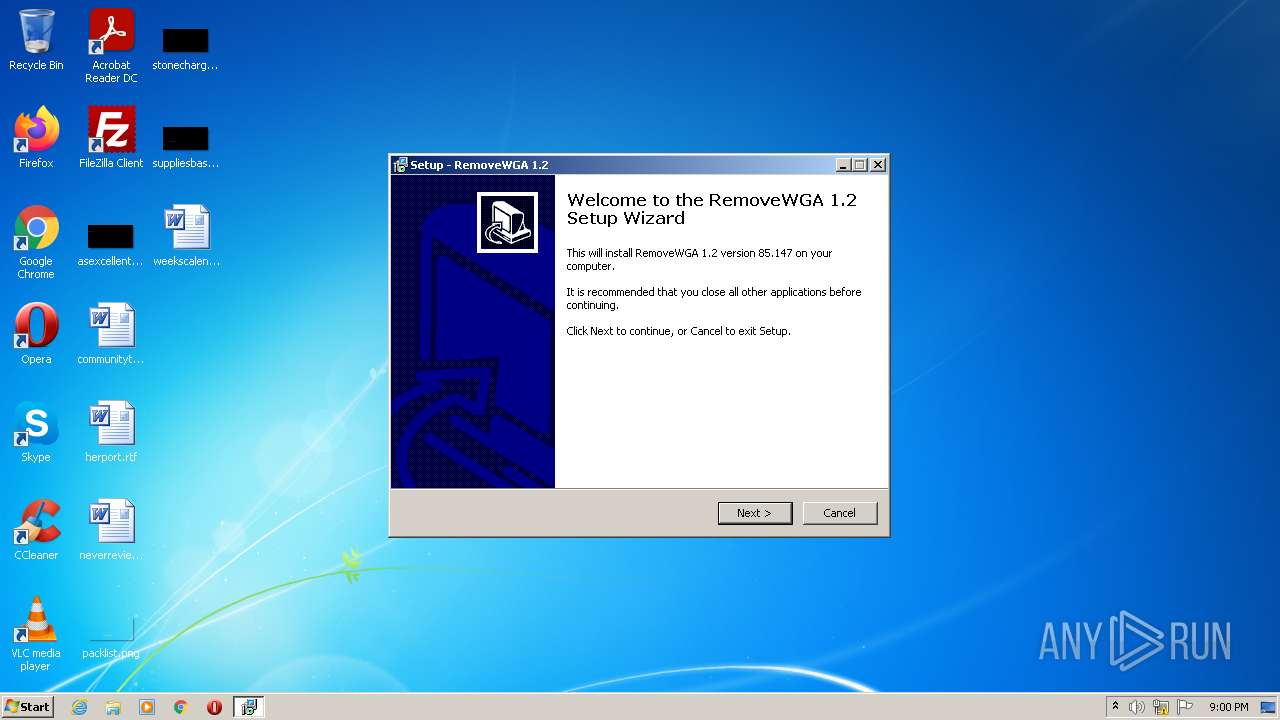
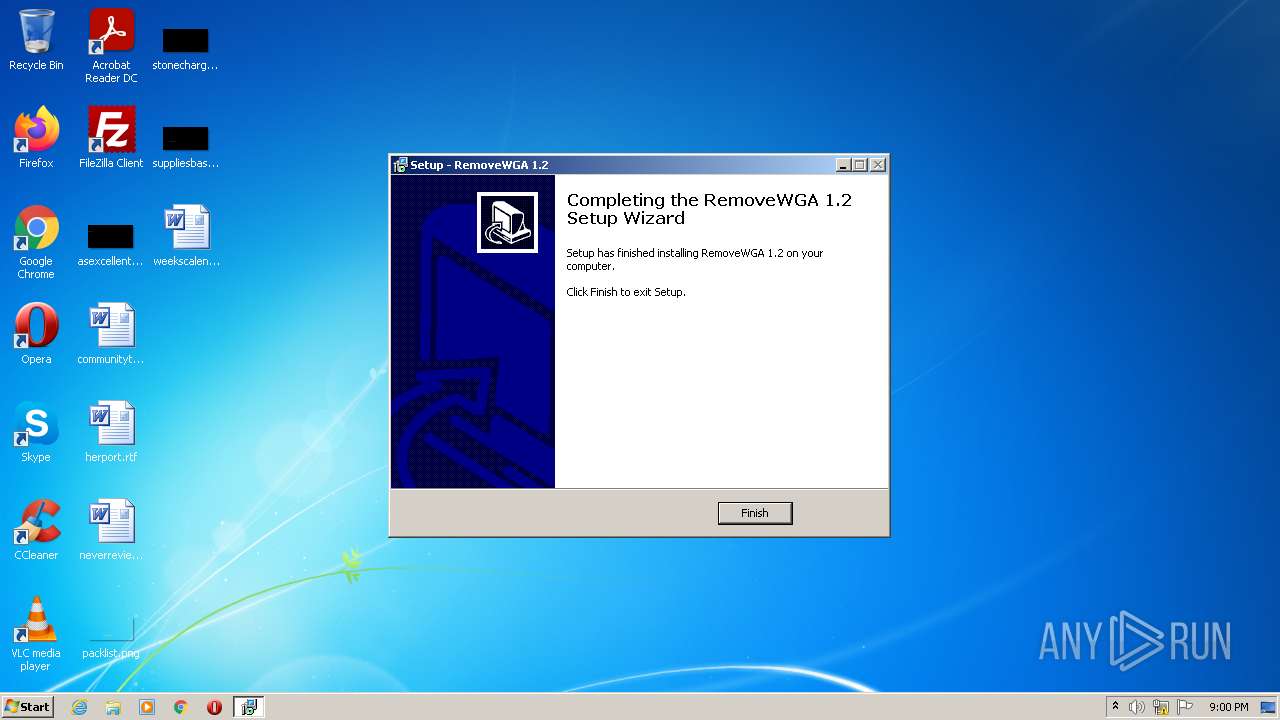
| File name: | RemoveWGA 1.2.ll |
| Full analysis: | https://app.any.run/tasks/e78a5e95-ad1c-4936-b33d-4966f3449edb |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2022, 21:00:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AA7868895754263BDD1A920451B30052 |
| SHA1: | 63A043953A0DD9D8791CC08D125D7541B0932BC1 |
| SHA256: | D7F2C9E3231BA0B3534E8475FDF87BA1A8434E23A4426533449E3CD1FDB7DE43 |
| SSDEEP: | 12288:uaHc64b888888888888W88888888888mjscV7TdjL47zdU5imJ1PXgQW33rD+zG5:F86nIW7uvmQq1PoezG/aYFkJR30F6rpM |
MALICIOUS
Drops executable file immediately after starts
- RemoveWGA 1.2.ll.exe (PID: 1248)
- 7za.exe (PID: 3284)
- RemoveWGA 1.2.ll.exe (PID: 548)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 484)
- schtasks.exe (PID: 3388)
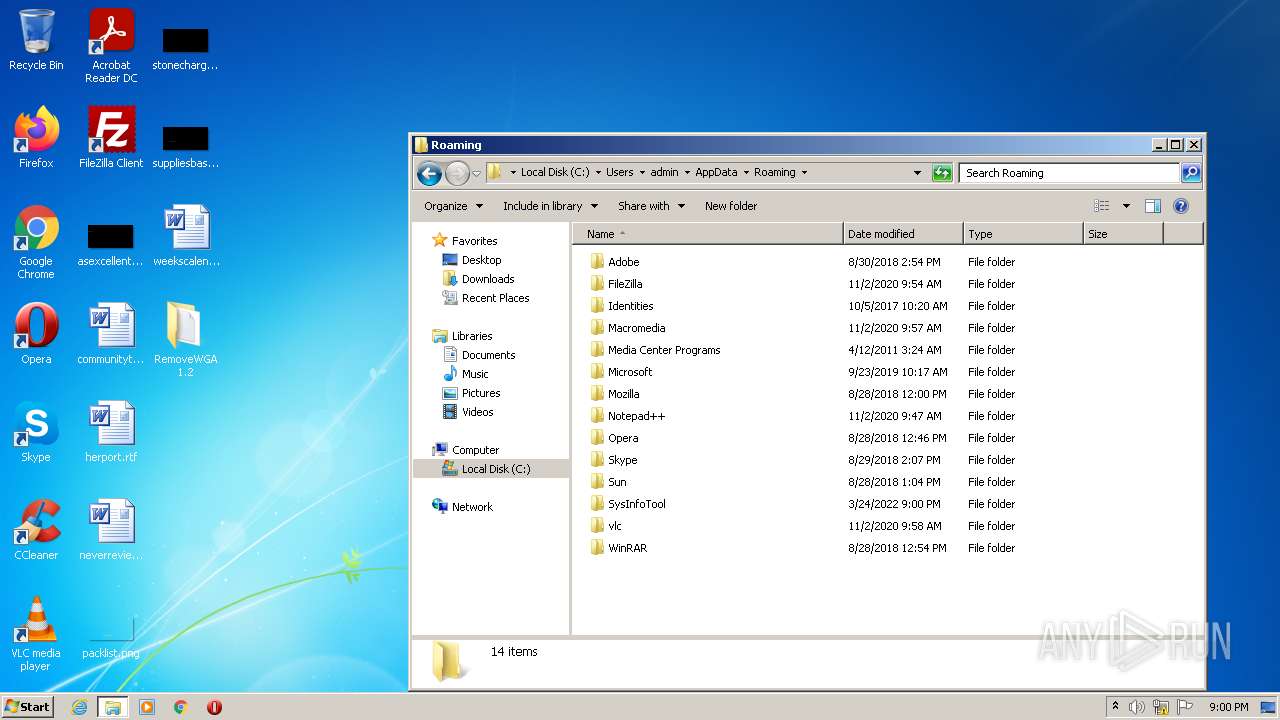
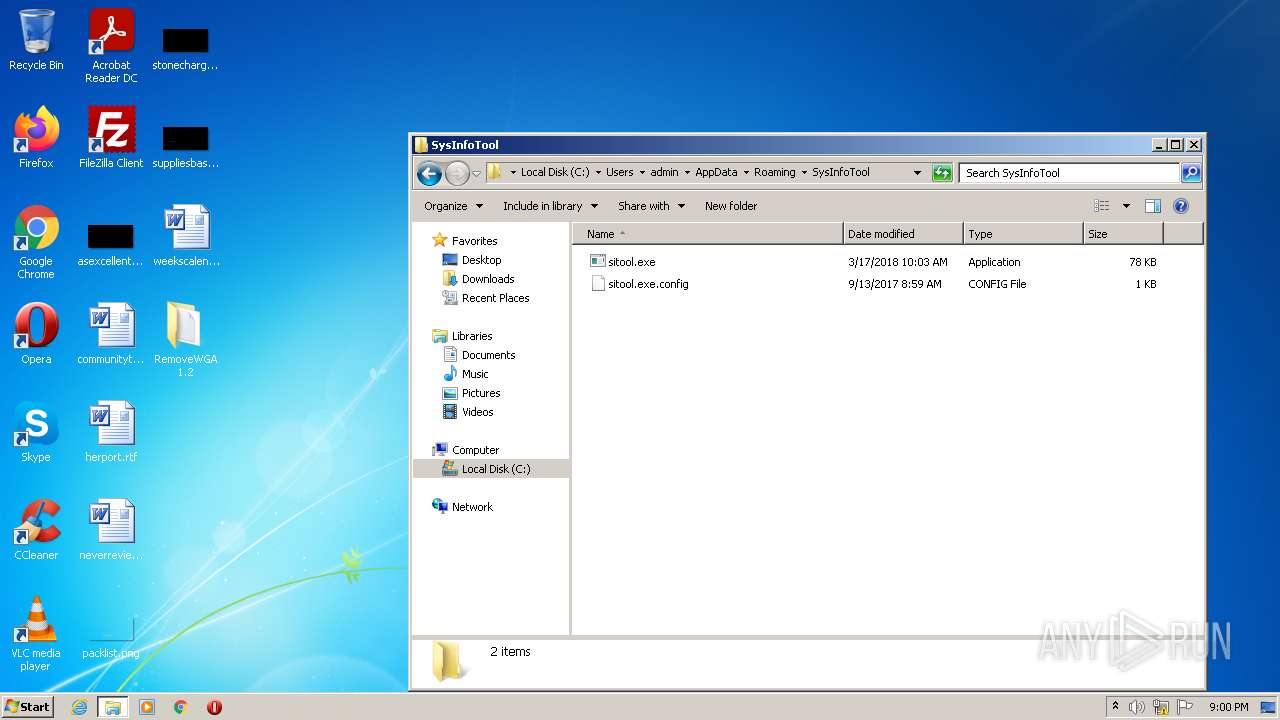
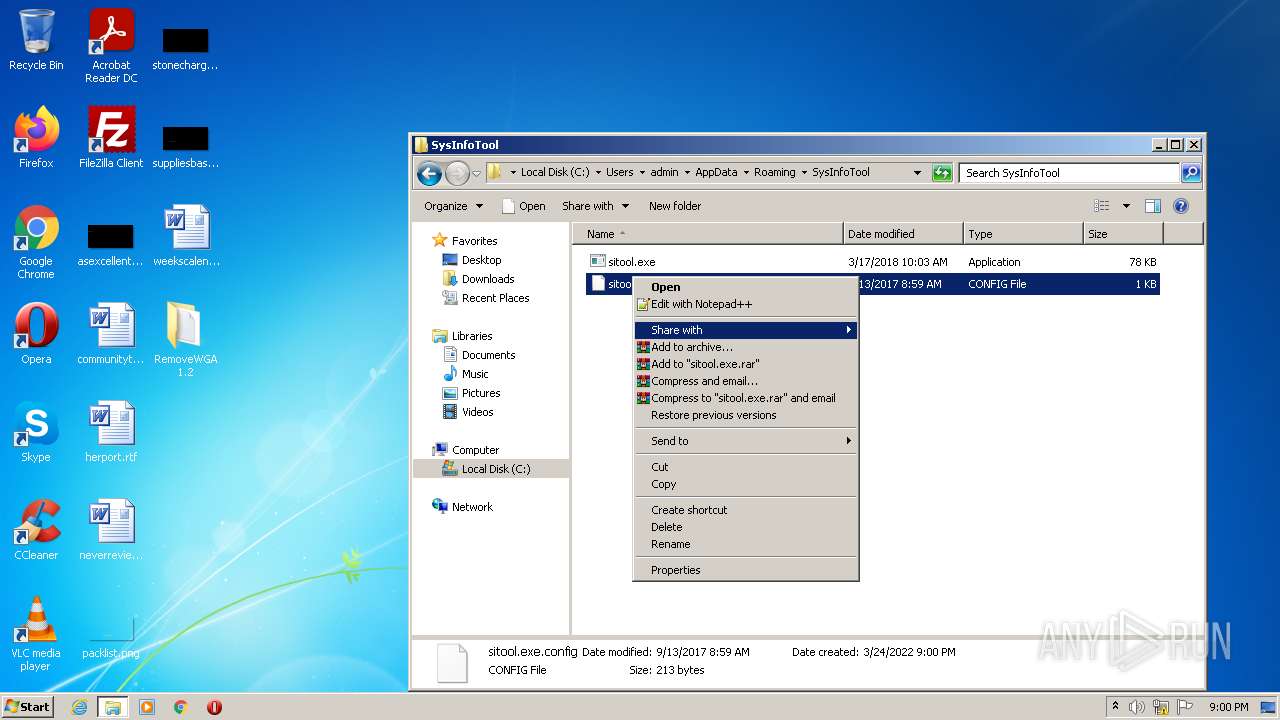
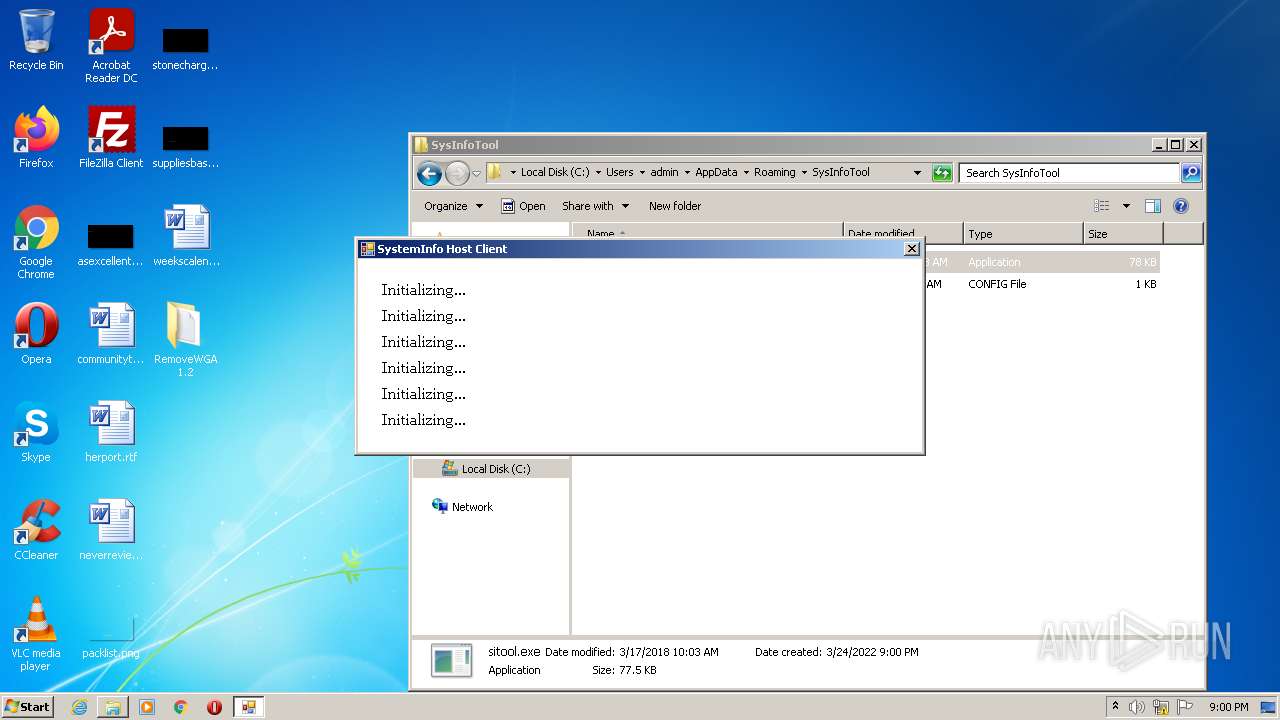
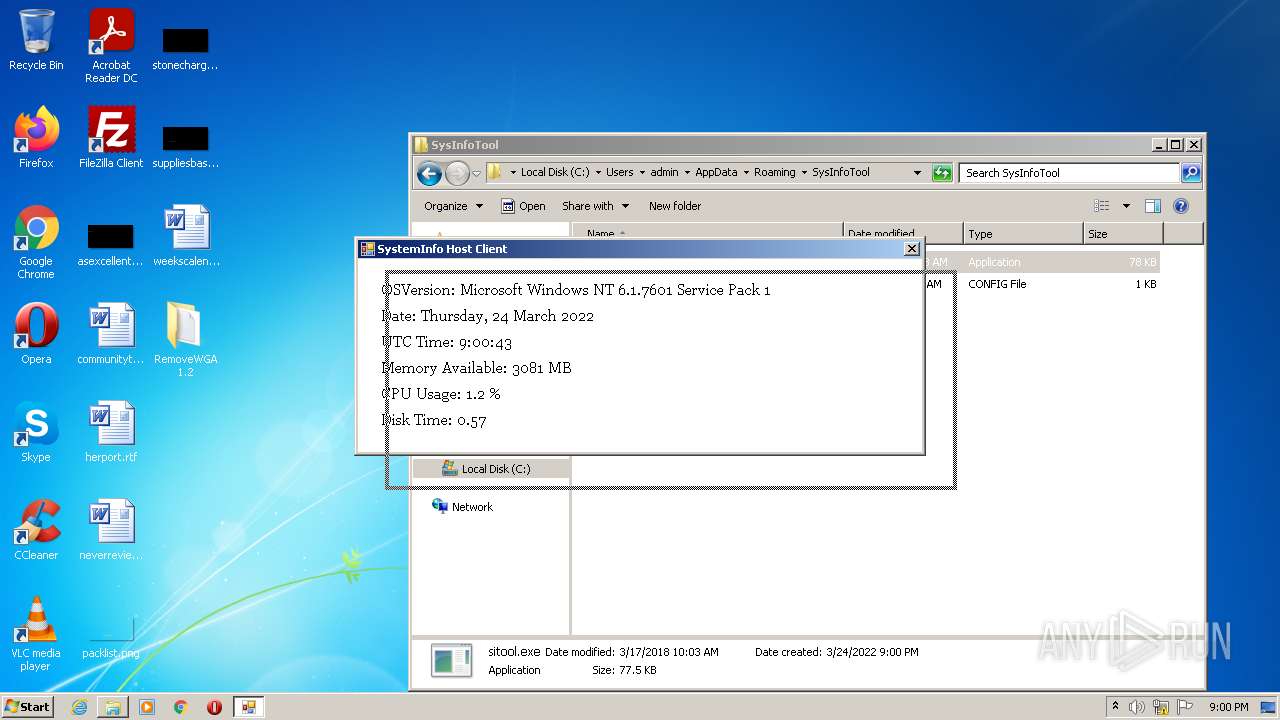
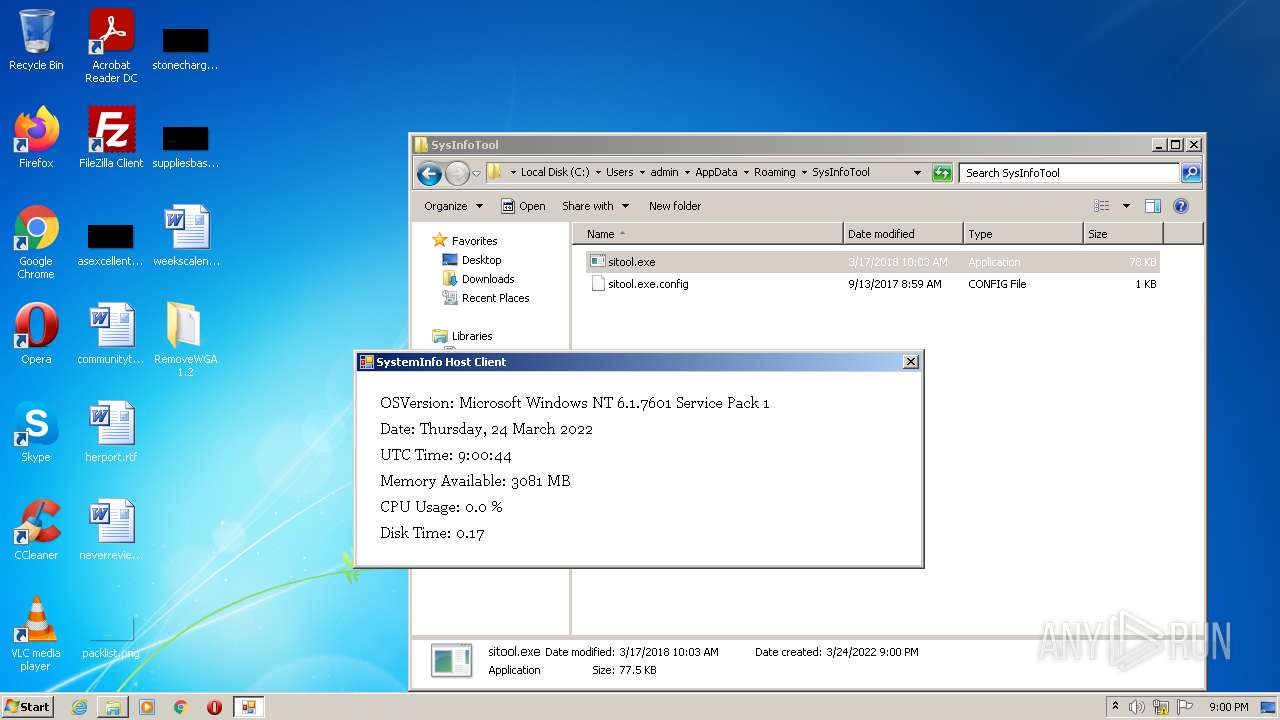
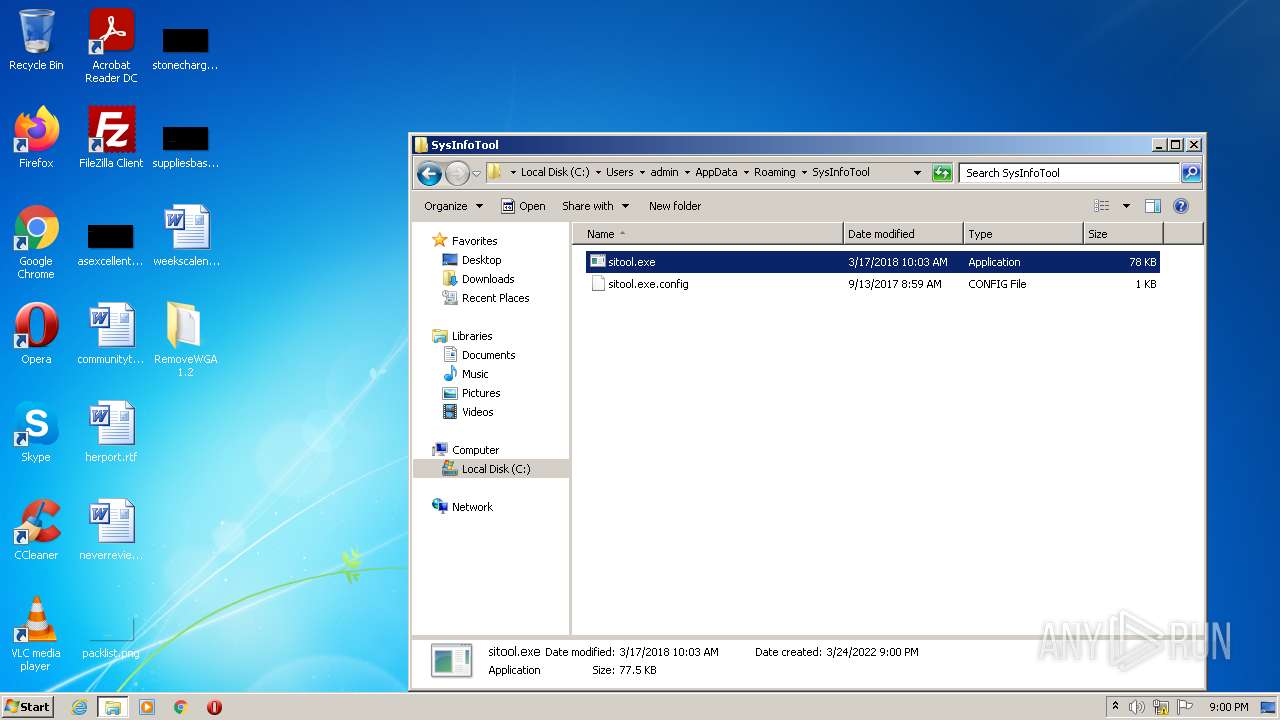
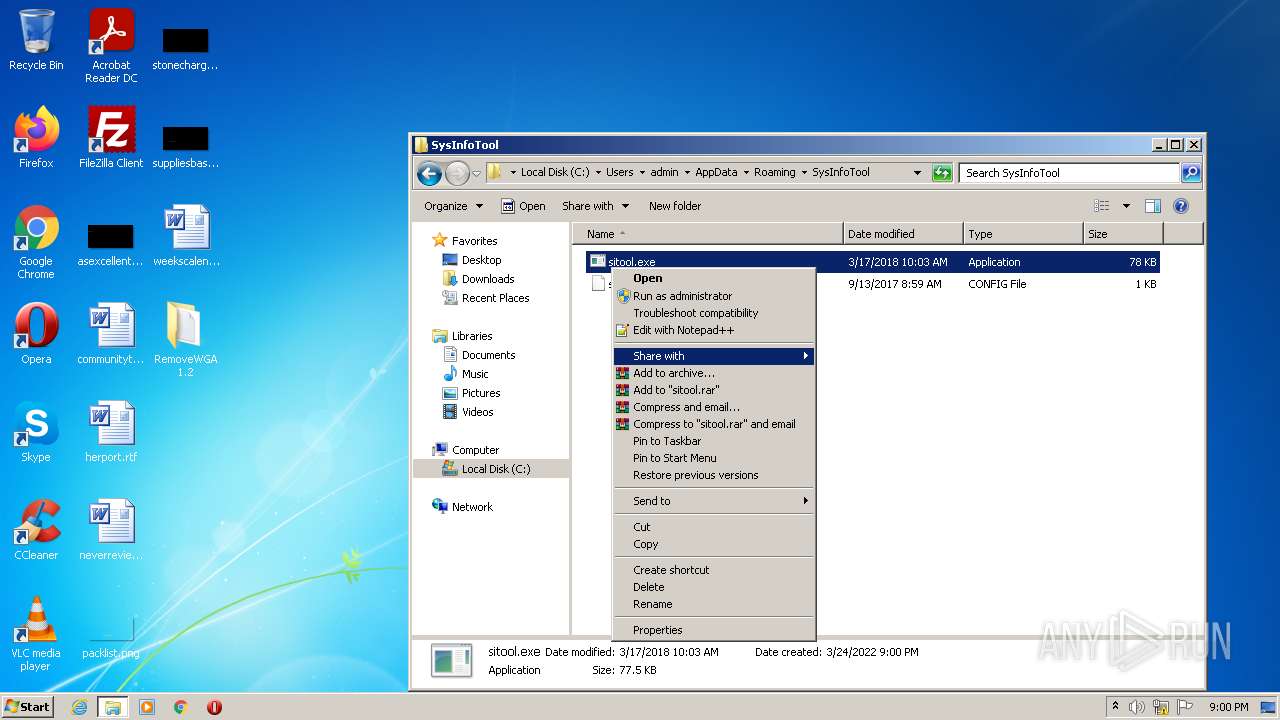
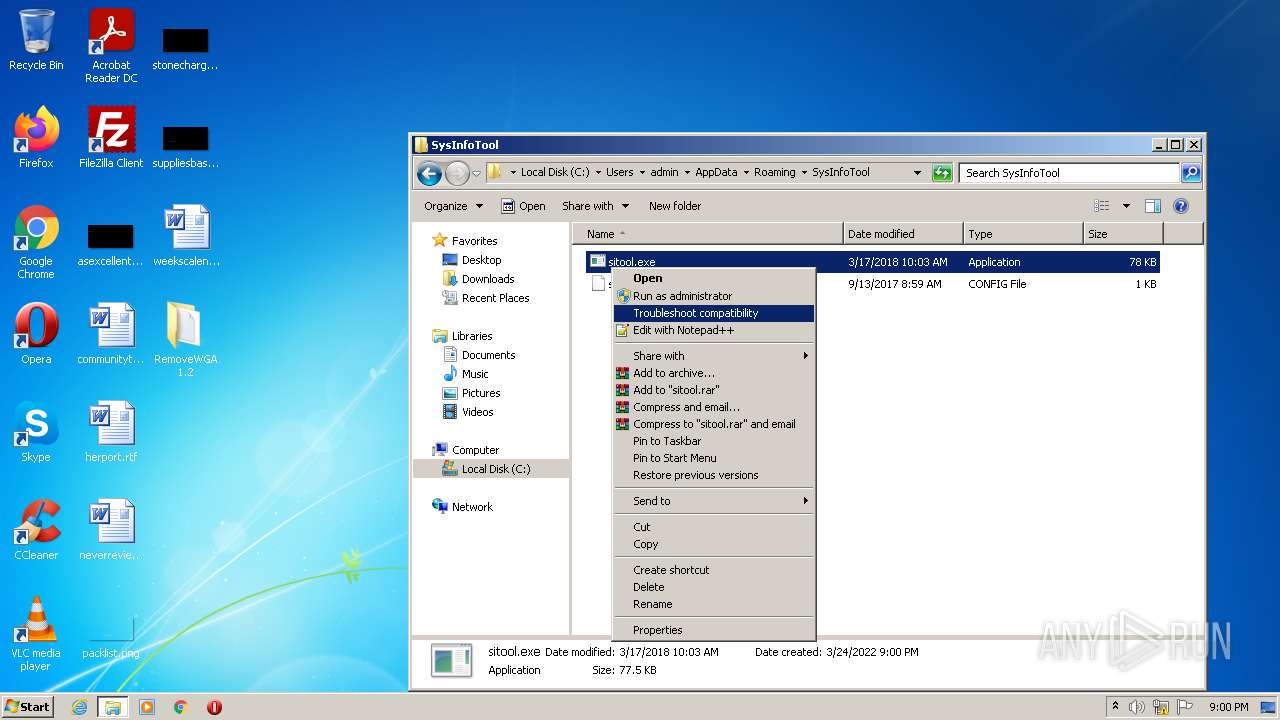
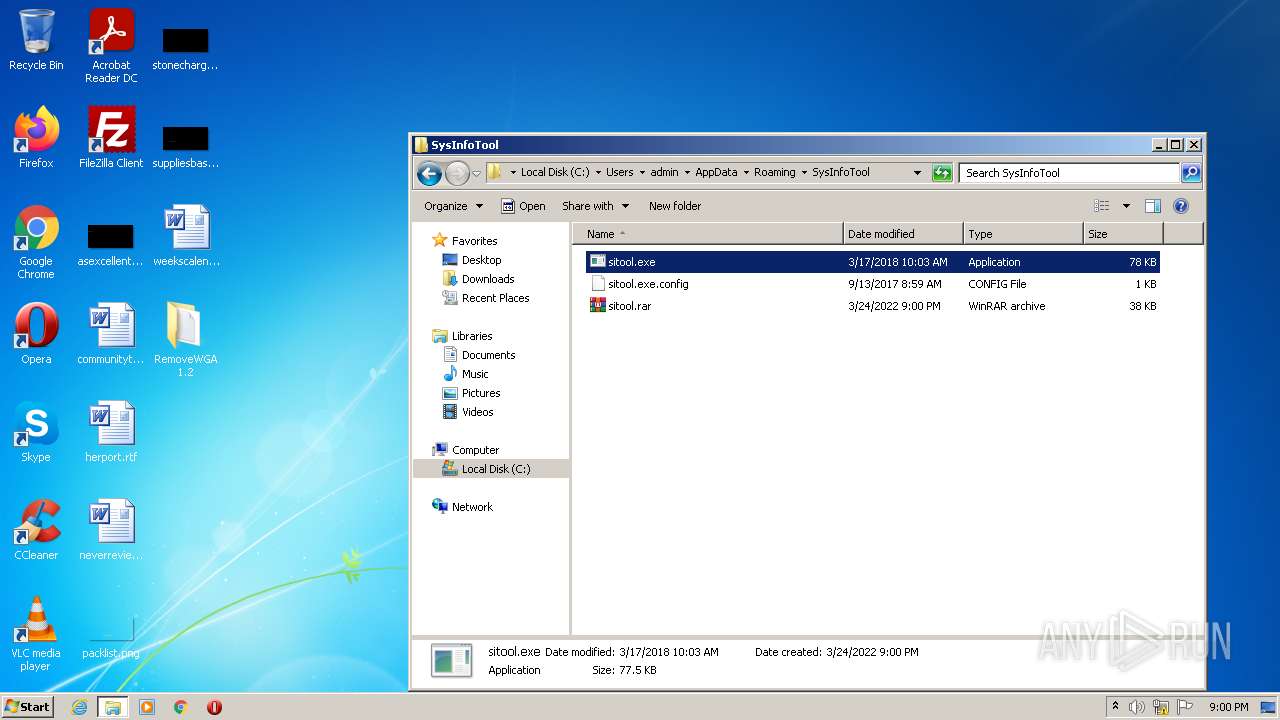
Application was dropped or rewritten from another process
- sitool.exe (PID: 3892)
- sitool.exe (PID: 3584)
Uses Task Scheduler to run other applications
- sitool.exe (PID: 3892)
SUSPICIOUS
Reads the computer name
- RemoveWGA 1.2.ll.tmp (PID: 3660)
- RemoveWGA 1.2.ll.tmp (PID: 1392)
- sitool.exe (PID: 3892)
- sitool.exe (PID: 3584)
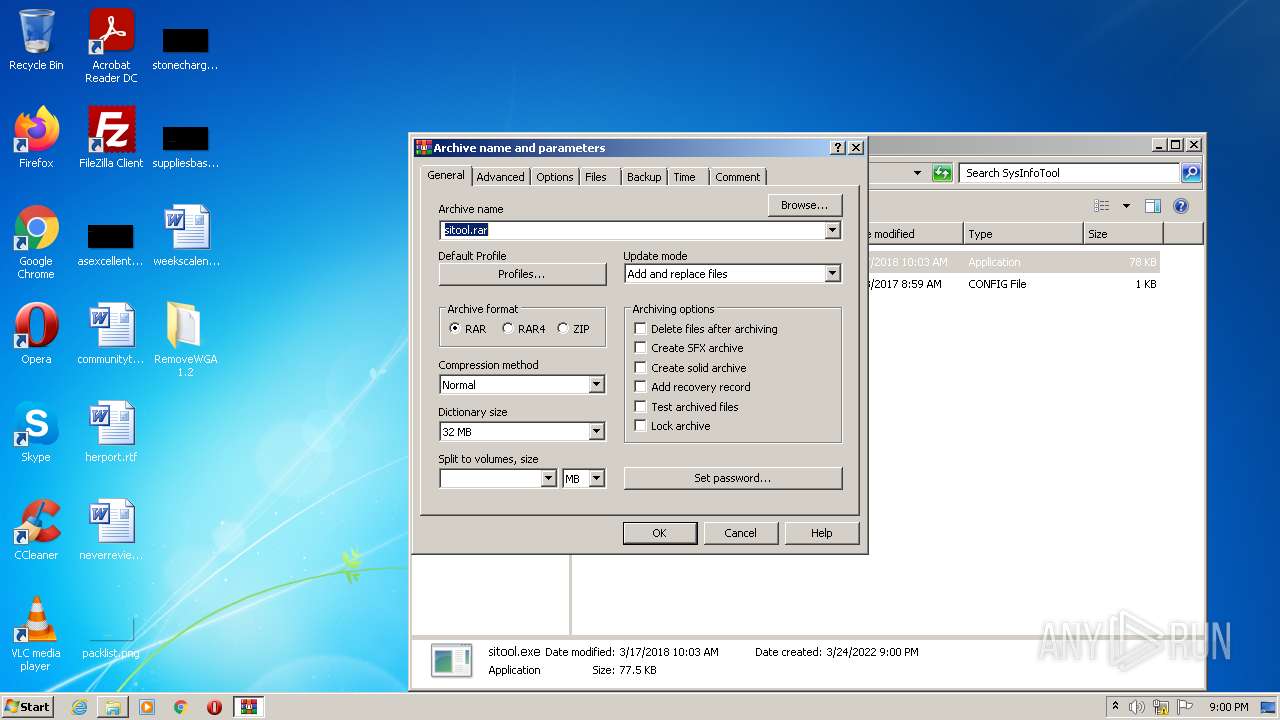
- WinRAR.exe (PID: 3944)
Executable content was dropped or overwritten
- RemoveWGA 1.2.ll.exe (PID: 548)
- RemoveWGA 1.2.ll.exe (PID: 1248)
- RemoveWGA 1.2.ll.tmp (PID: 1392)
- 7za.exe (PID: 3284)
Reads Windows owner or organization settings
- RemoveWGA 1.2.ll.tmp (PID: 1392)
Checks supported languages
- RemoveWGA 1.2.ll.tmp (PID: 3660)
- RemoveWGA 1.2.ll.exe (PID: 548)
- RemoveWGA 1.2.ll.tmp (PID: 1392)
- 7za.exe (PID: 1876)
- RemoveWGA 1.2.ll.exe (PID: 1248)
- 7za.exe (PID: 3284)
- sitool.exe (PID: 3892)
- notepad++.exe (PID: 2976)
- sitool.exe (PID: 3584)
- WinRAR.exe (PID: 3944)
- 7za.exe (PID: 3316)
Reads the Windows organization settings
- RemoveWGA 1.2.ll.tmp (PID: 1392)
Drops a file with too old compile date
- RemoveWGA 1.2.ll.tmp (PID: 1392)
Drops a file with a compile date too recent
- 7za.exe (PID: 3284)
- RemoveWGA 1.2.ll.tmp (PID: 1392)
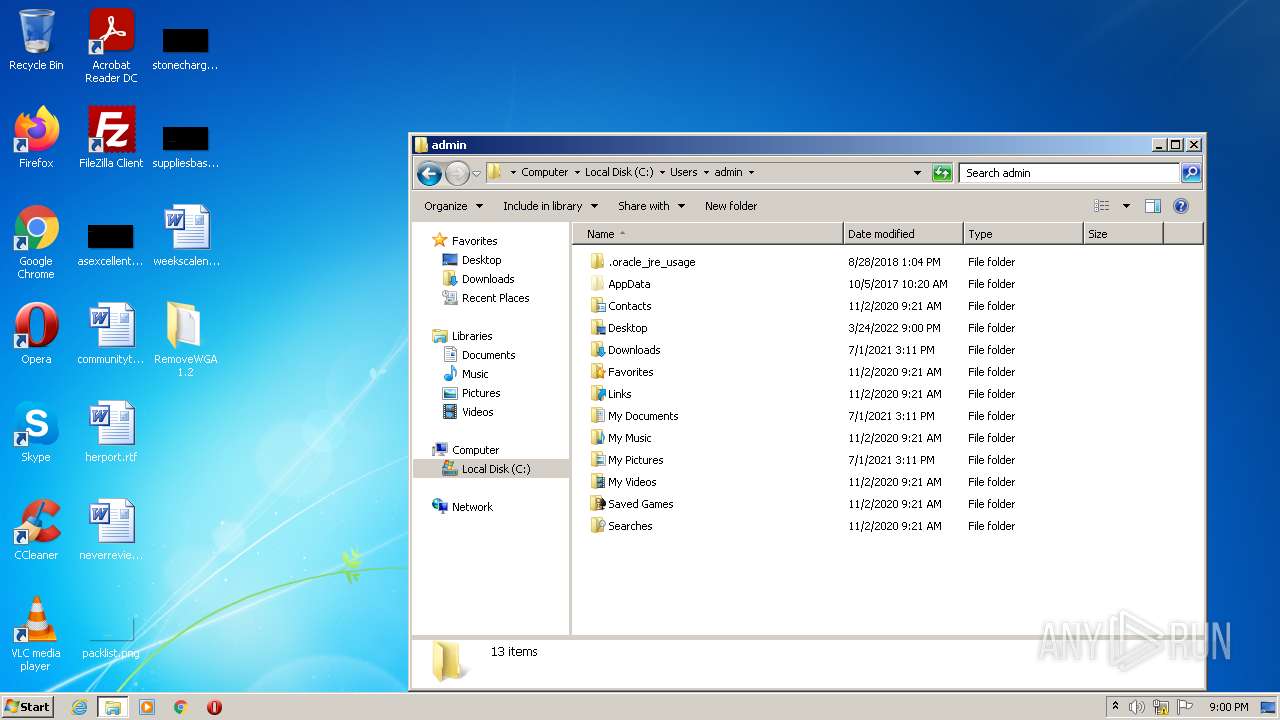
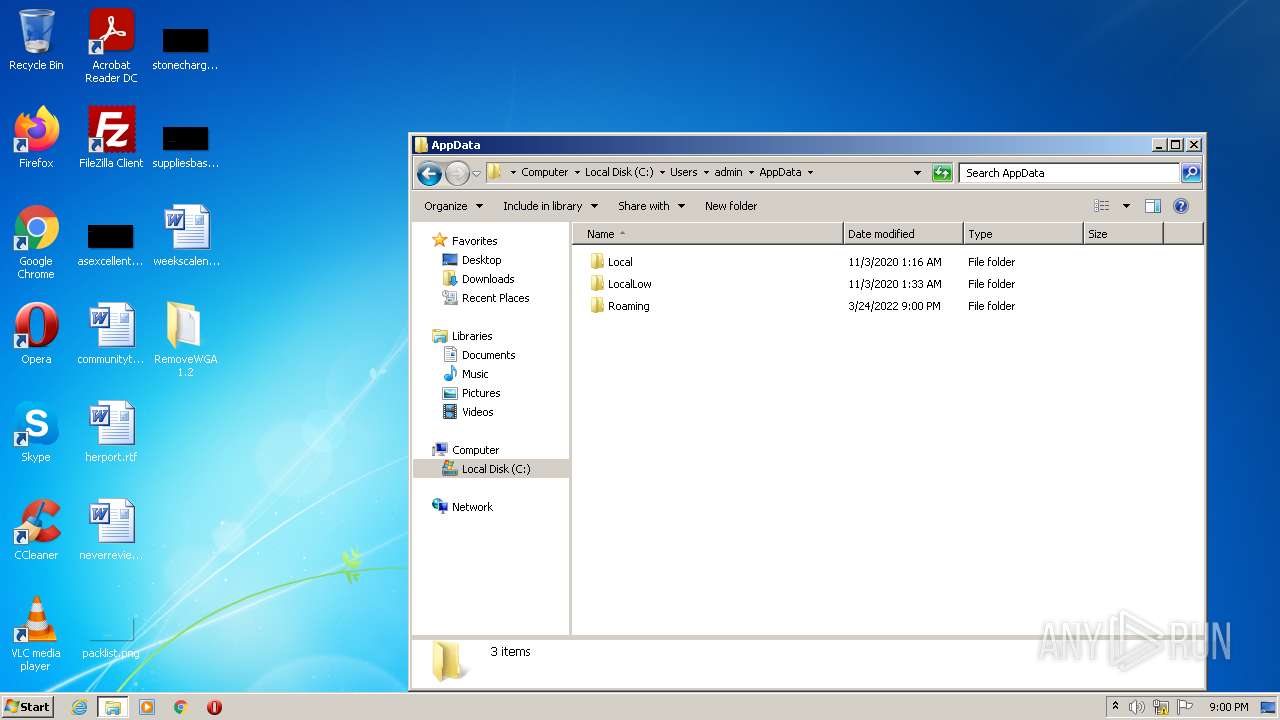
Creates files in the user directory
- RemoveWGA 1.2.ll.tmp (PID: 1392)
- WinRAR.exe (PID: 3944)
- sitool.exe (PID: 3892)
Executed via COM
- explorer.exe (PID: 2372)
Reads the date of Windows installation
- explorer.exe (PID: 2372)
Reads Environment values
- sitool.exe (PID: 3584)
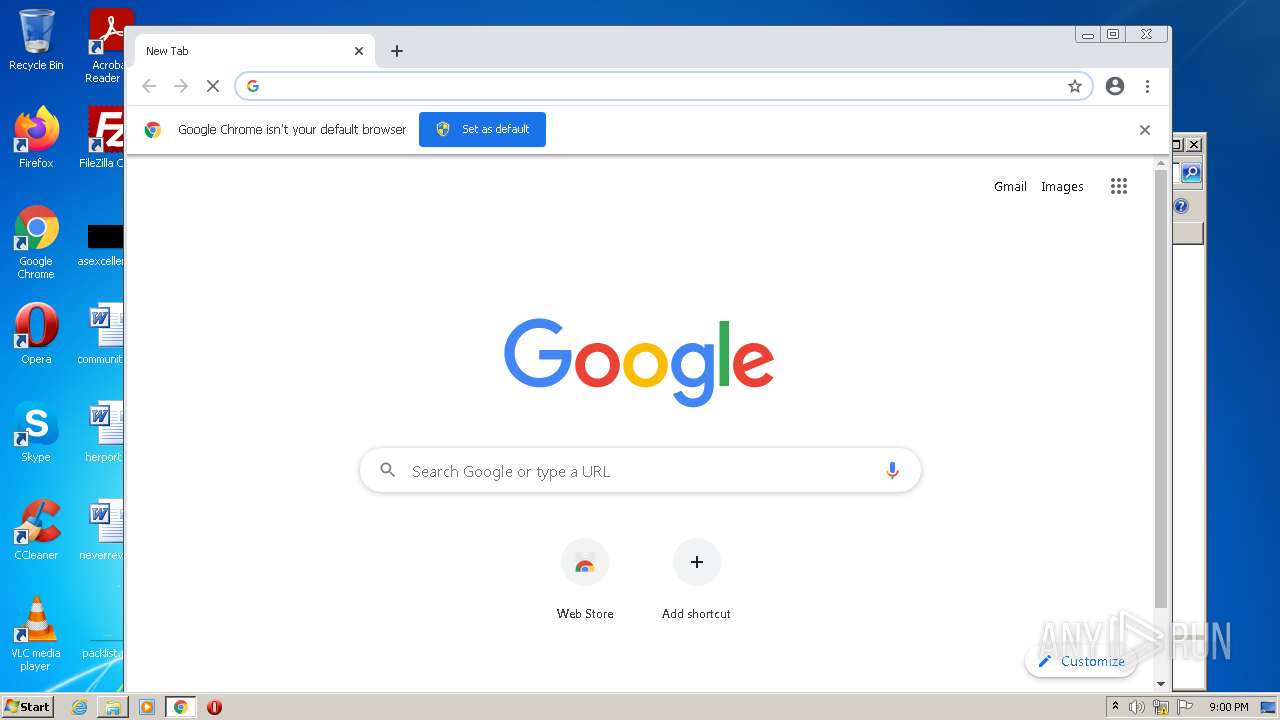
Modifies files in Chrome extension folder
- chrome.exe (PID: 3352)
INFO
Application was dropped or rewritten from another process
- RemoveWGA 1.2.ll.tmp (PID: 3660)
- RemoveWGA 1.2.ll.tmp (PID: 1392)
- 7za.exe (PID: 1876)
- 7za.exe (PID: 3284)
- 7za.exe (PID: 3316)
Checks supported languages
- schtasks.exe (PID: 484)
- schtasks.exe (PID: 3388)
- explorer.exe (PID: 2372)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 1700)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 1792)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 3628)
- explorer.exe (PID: 2736)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 1240)
Reads the computer name
- explorer.exe (PID: 2736)
- schtasks.exe (PID: 3388)
- explorer.exe (PID: 2372)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 1700)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 3628)
- schtasks.exe (PID: 484)
Reads CPU info
- explorer.exe (PID: 2372)
Manual execution by user
- chrome.exe (PID: 3352)
Reads the hosts file
- chrome.exe (PID: 3352)
- chrome.exe (PID: 1700)
Application launched itself
- chrome.exe (PID: 3352)
Reads settings of System Certificates
- chrome.exe (PID: 1700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| ProductVersion: | 85.147 |
|---|---|
| ProductName: | |
| LegalCopyright: | |
| FileVersion: | 85.147 |
| FileDescription: | |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 85.147.0.0 |
| FileVersionNumber: | 85.147.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x1181c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 53760 |
| CodeSize: | 66560 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 85.147 |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | 85.147 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.139 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
85
Monitored processes
41
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 484 | "C:\Windows\system32\schtasks.exe" /Delete /tn "Microsoft\Windows\Windows Error Reporting\ToolSystemInfo" /f | C:\Windows\system32\schtasks.exe | — | sitool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | "C:\Users\admin\AppData\Local\Temp\RemoveWGA 1.2.ll.exe" /SPAWNWND=$1013E /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\RemoveWGA 1.2.ll.exe | RemoveWGA 1.2.ll.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: 85.147 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12558703927954575999,13975313832356143229,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1248 | "C:\Users\admin\AppData\Local\Temp\RemoveWGA 1.2.ll.exe" | C:\Users\admin\AppData\Local\Temp\RemoveWGA 1.2.ll.exe | Explorer.EXE | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 0 Version: 85.147 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,12558703927954575999,13975313832356143229,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2988 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\AppData\Local\Temp\is-80R3Q.tmp\RemoveWGA 1.2.ll.tmp" /SL5="$20140,373962,121344,C:\Users\admin\AppData\Local\Temp\RemoveWGA 1.2.ll.exe" /SPAWNWND=$1013E /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-80R3Q.tmp\RemoveWGA 1.2.ll.tmp | RemoveWGA 1.2.ll.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,12558703927954575999,13975313832356143229,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12558703927954575999,13975313832356143229,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,12558703927954575999,13975313832356143229,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1344 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,12558703927954575999,13975313832356143229,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2696 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
20 323
Read events
19 851
Write events
468
Delete events
4
Modification events
| (PID) Process: | (1392) RemoveWGA 1.2.ll.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 7005000066A5FD29C23FD801 | |||
| (PID) Process: | (1392) RemoveWGA 1.2.ll.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 05C9B2AAA355A6DF51E6B1848ABF4EEEC390969512B38ED69B6EBD36820ED405 | |||
| (PID) Process: | (1392) RemoveWGA 1.2.ll.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1392) RemoveWGA 1.2.ll.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1392) RemoveWGA 1.2.ll.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 05C9B2AAA355A6DF51E6B1848ABF4EEEC390969512B38ED69B6EBD36820ED405 | |||
| (PID) Process: | (1392) RemoveWGA 1.2.ll.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 7005000066A5FD29C23FD801 | |||
| (PID) Process: | (1392) RemoveWGA 1.2.ll.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\0\0 |
| Operation: | write | Name: | 2 |
Value: 7A0031000000000078540AA811004465736B746F7000640008000400EFBE454B814A78540AA82A0000007B0100000000020000000000000000003A00000000004400650073006B0074006F007000000040007300680065006C006C00330032002E0064006C006C002C002D0032003100370036003900000016000000 | |||
Executable files
5
Suspicious files
116
Text files
85
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | RemoveWGA 1.2.ll.tmp | C:\Users\admin\AppData\Local\Temp\{21987150-1D56-430E-8A7C-1036F3EB38F3}\is-UL7DI.tmp | — | |
MD5:— | SHA256:— | |||
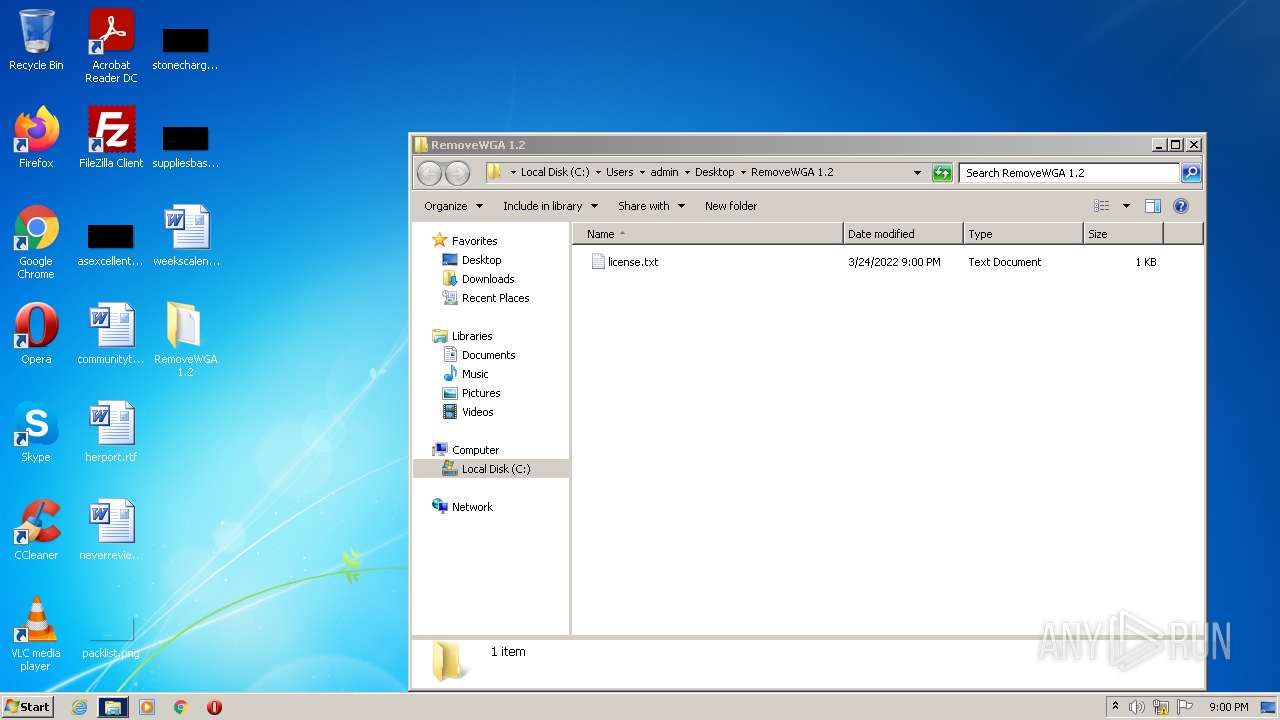
| 1392 | RemoveWGA 1.2.ll.tmp | C:\Users\admin\AppData\Local\Temp\{21987150-1D56-430E-8A7C-1036F3EB38F3}\license.txt | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-623CDC08-D18.pma | — | |
MD5:— | SHA256:— | |||
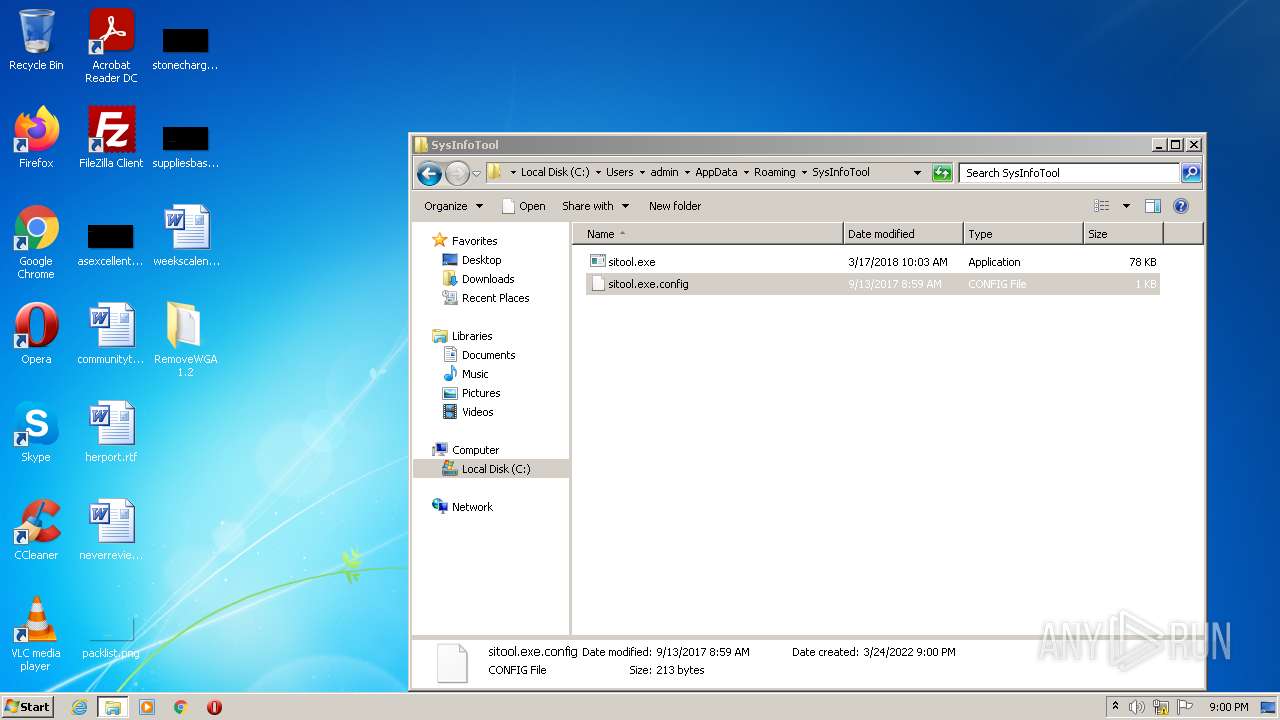
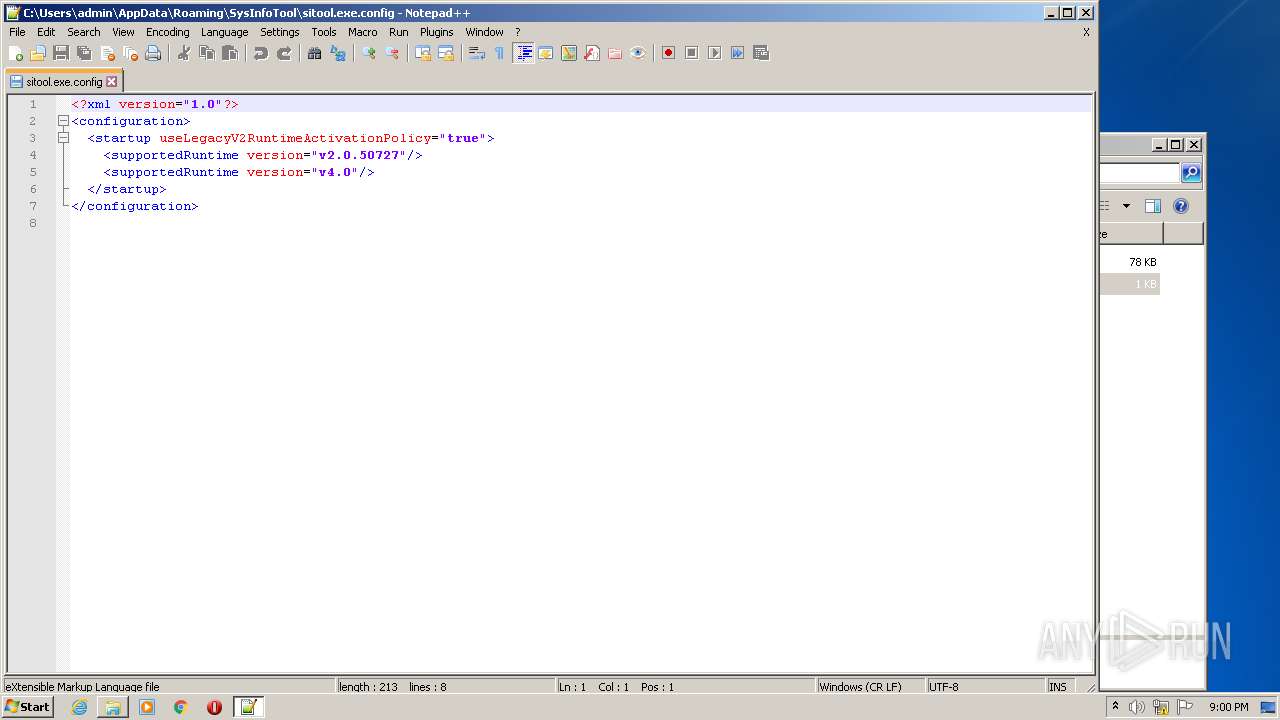
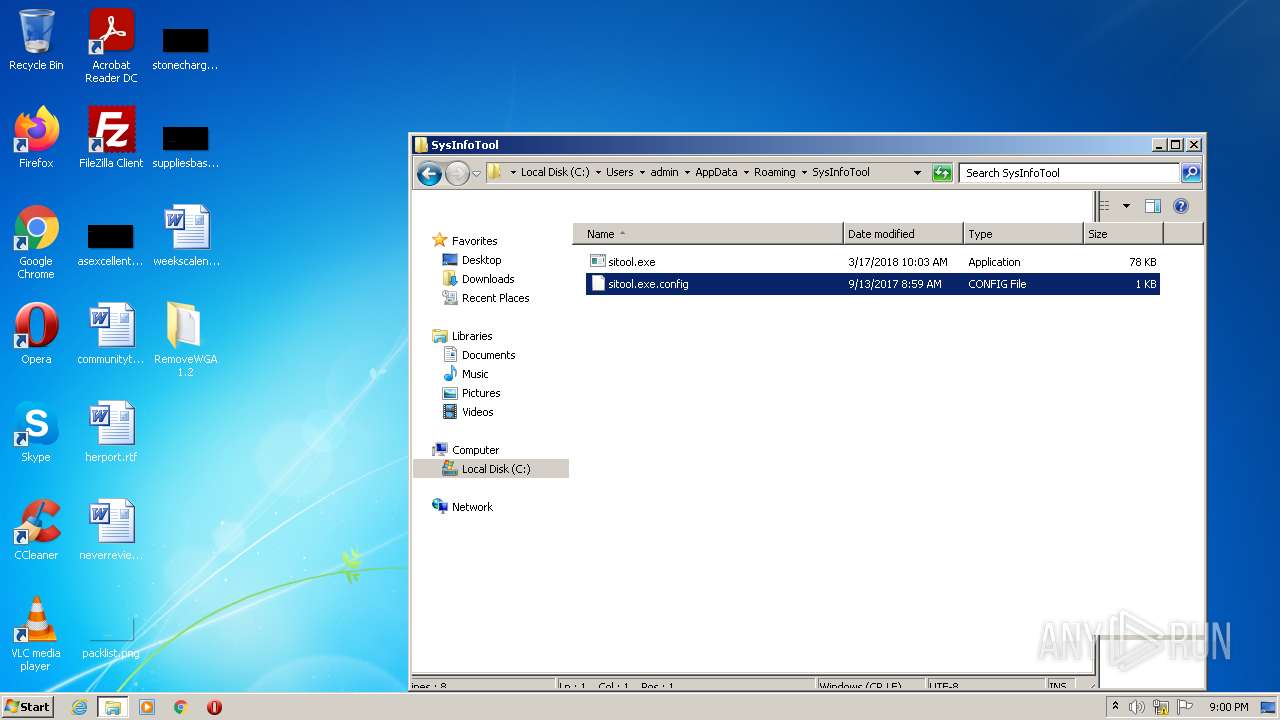
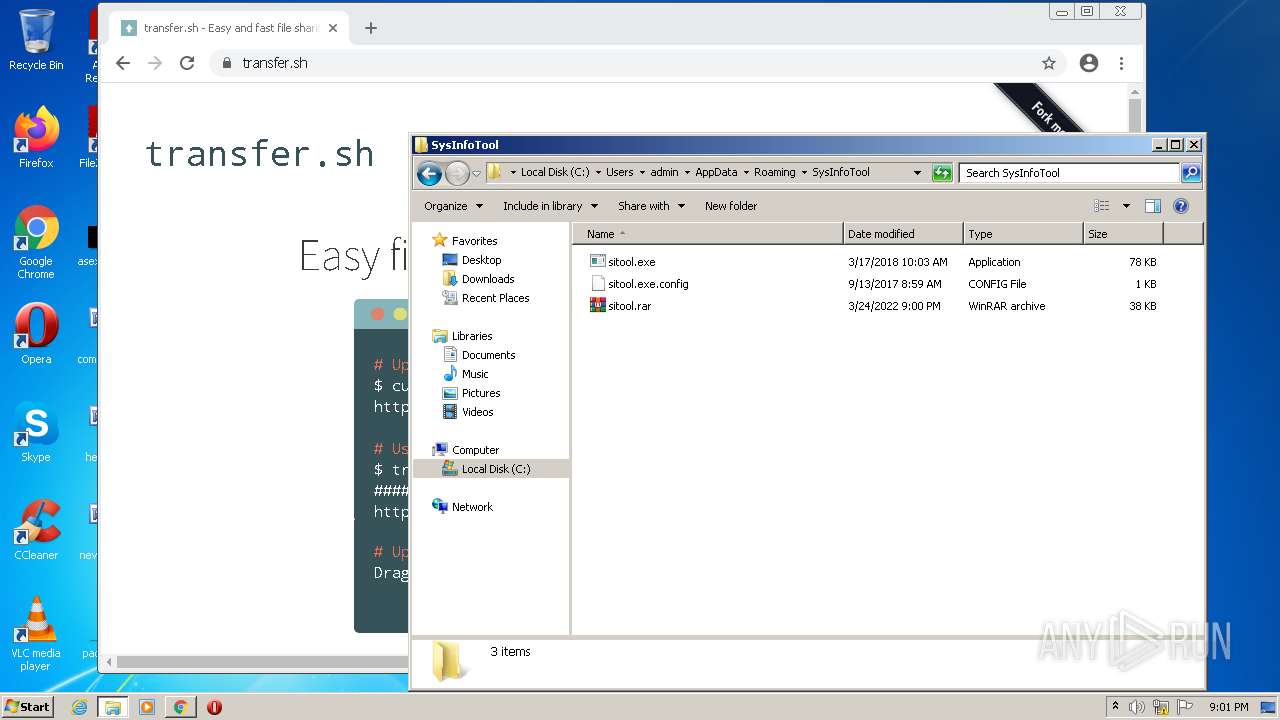
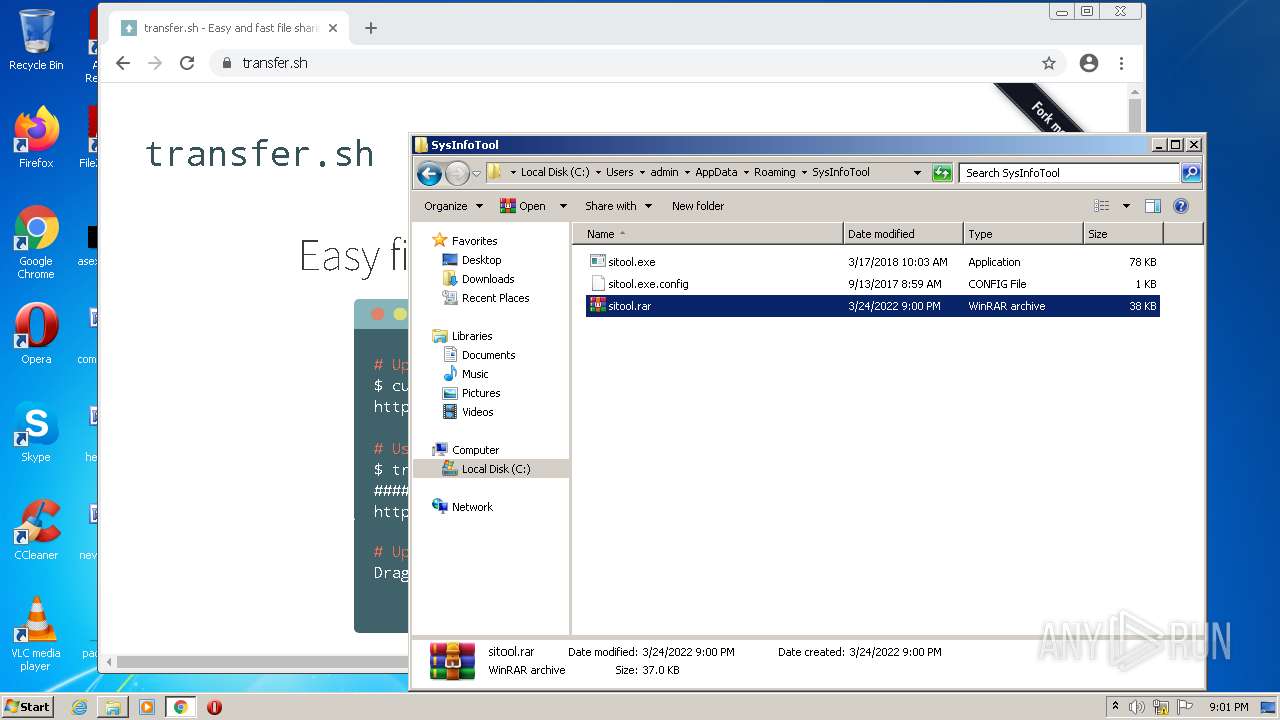
| 1392 | RemoveWGA 1.2.ll.tmp | C:\Users\admin\AppData\Roaming\SysInfoTool\sitool.exe | executable | |
MD5:2E827FD3CFC35BFA6E9351C7C267E4DF | SHA256:80B4D2C8FB391BD051E5786E31E10A679E8BBB15E695C2C9F3BF2893921C7B9A | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Roaming\SysInfoTool\sitool.rar | compressed | |
MD5:— | SHA256:— | |||
| 1392 | RemoveWGA 1.2.ll.tmp | C:\Users\admin\Desktop\RemoveWGA 1.2\license.txt | text | |
MD5:— | SHA256:— | |||
| 1392 | RemoveWGA 1.2.ll.tmp | C:\Users\admin\AppData\Local\Temp\is-IVNGG.tmp\misc.res | compressed | |
MD5:E2FBB5DC7CD1E6D0BE984B2BEAE313E2 | SHA256:27C8A7BE79A7B7D658CF90B6B8BA134DC9AB26A29FB1FAACD261F69433B83FEC | |||
| 3892 | sitool.exe | C:\Users\admin\AppData\Roaming\SysInfoTool\data.xml | xml | |
MD5:— | SHA256:— | |||
| 1392 | RemoveWGA 1.2.ll.tmp | C:\Users\admin\AppData\Local\Temp\is-IVNGG.tmp\form.res | compressed | |
MD5:A81E23F6523394DEB32F410ABFF37BBC | SHA256:C76589A829EF2992375C46BC17E6C4D6CA62FA30580FF25FCA11927AE1AC4857 | |||
| 1876 | 7za.exe | C:\Users\admin\AppData\Local\Temp\is-IVNGG.tmp\sub.xml | xml | |
MD5:C047508A4A1F583B7ED31EC7B0DF9695 | SHA256:CD999BAA036D44D442FE43A541D69F04BA206C58938F3C22EC0F226493C63E35 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
32
DNS requests
19
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1700 | chrome.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?cd60e6ddf7c24168 | US | compressed | 59.5 Kb | whitelisted |
1700 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
1392 | RemoveWGA 1.2.ll.tmp | POST | 200 | 142.250.185.174:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
1392 | RemoveWGA 1.2.ll.tmp | GET | 200 | 188.114.96.7:80 | http://avkit.org/home/getchannel | US | binary | 1 b | malicious |
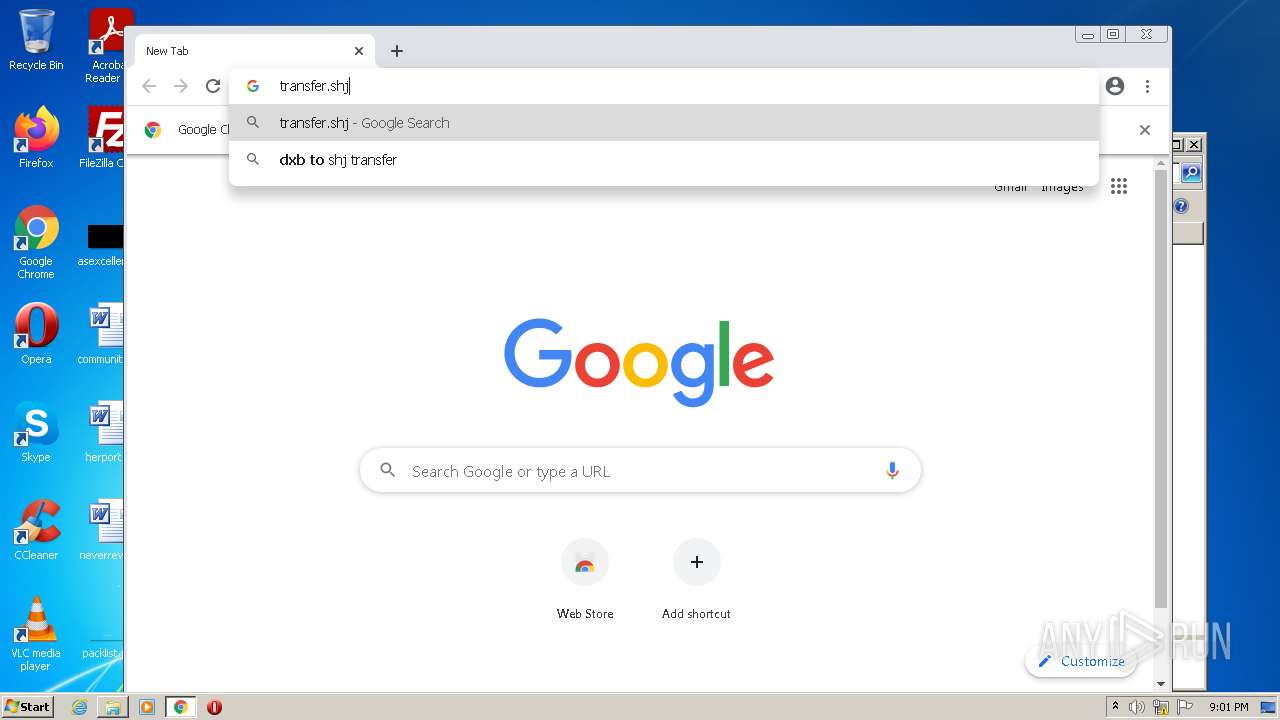
1700 | chrome.exe | GET | 301 | 144.76.136.153:80 | http://transfer.sh/ | DE | html | 185 b | whitelisted |
1392 | RemoveWGA 1.2.ll.tmp | POST | 200 | 142.250.185.174:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1392 | RemoveWGA 1.2.ll.tmp | 142.250.185.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 142.250.186.164:443 | www.google.com | Google Inc. | US | whitelisted |
1392 | RemoveWGA 1.2.ll.tmp | 188.114.96.7:80 | avkit.org | Cloudflare Inc | US | malicious |
1700 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 142.250.185.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
1700 | chrome.exe | 142.250.185.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 142.250.186.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 142.250.184.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
avkit.org |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1392 | RemoveWGA 1.2.ll.tmp | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
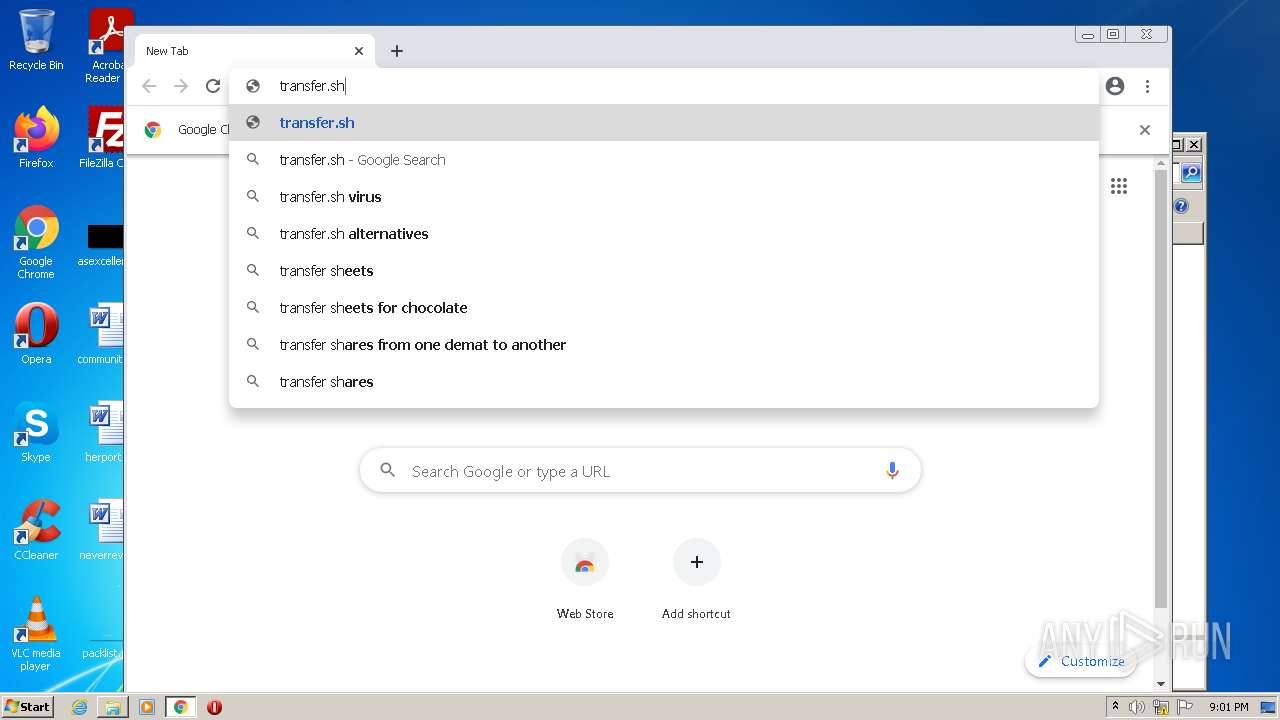
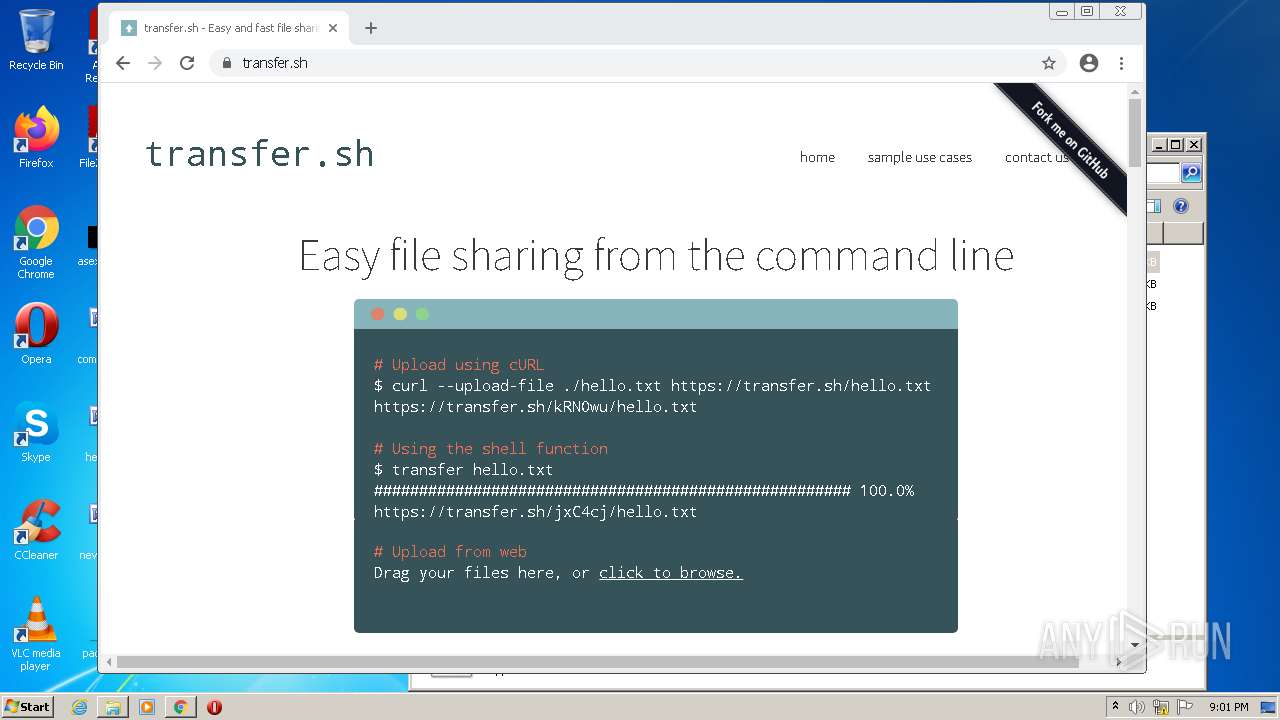
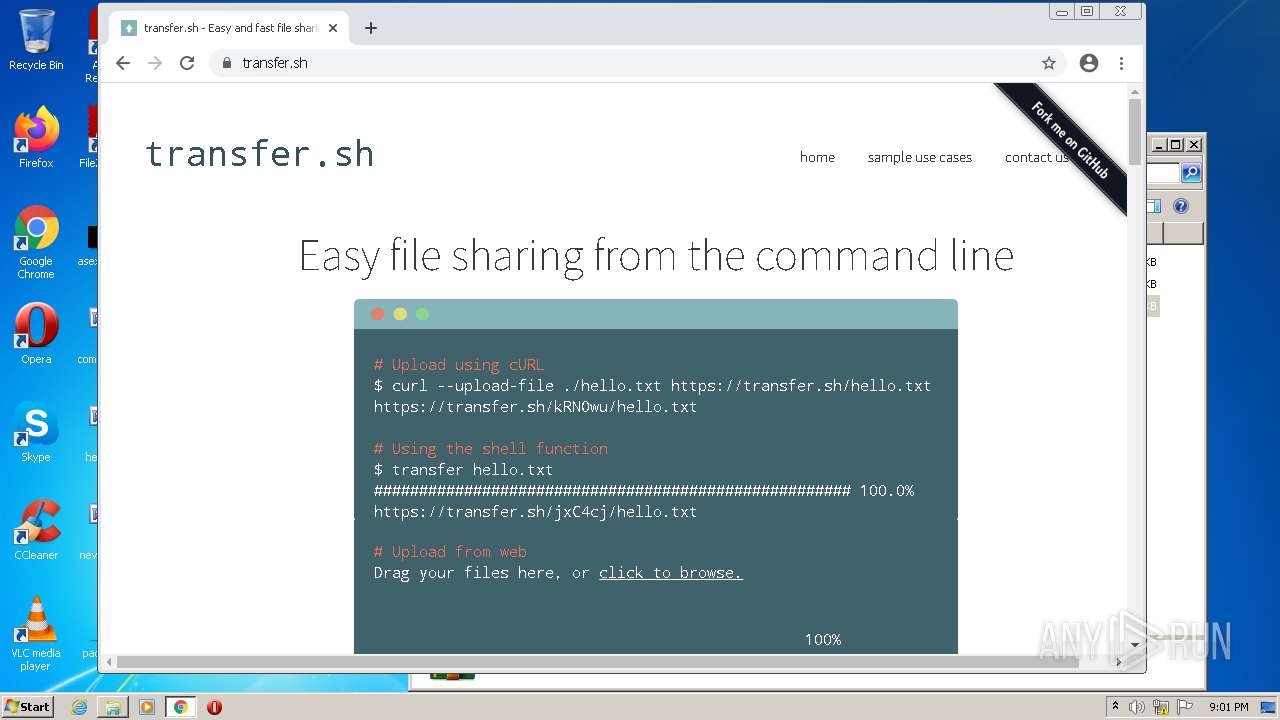
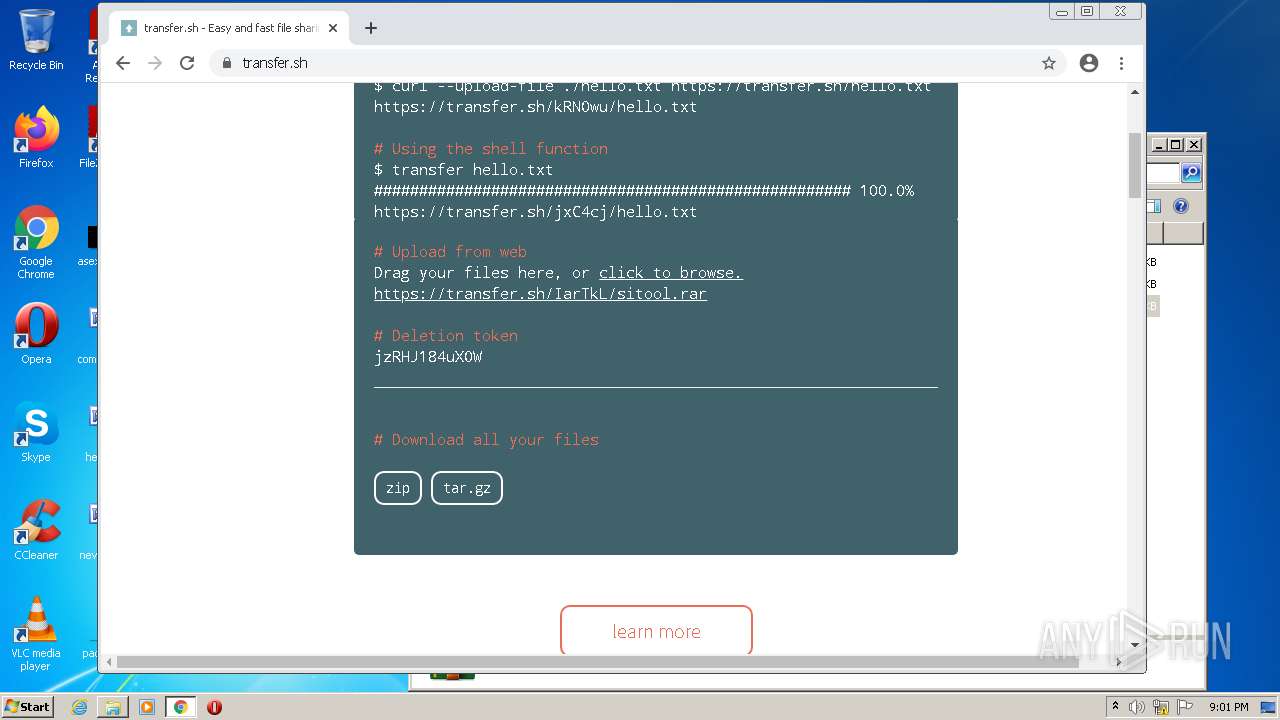
— | — | Potentially Bad Traffic | ET POLICY Observed DNS Query to File Transfer Service Domain (transfer .sh) |
— | — | Misc activity | ET INFO Commonly Abused File Sharing Site Domain Observed (transfer .sh in DNS Lookup) |
1700 | chrome.exe | Misc activity | ET INFO Commonly Abused File Sharing Site Domain Observed (transfer .sh in TLS SNI) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|