| File name: | krnl.exe |
| Full analysis: | https://app.any.run/tasks/5ae937e3-c6d1-48da-b4df-ab960ceba10d |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 16:05:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E2A9FEC47A88D70D0BB16160420418BA |
| SHA1: | 95B7634A88A21EE918576401F2A5FD40B8D919C9 |
| SHA256: | D7F152F22CE516AD72F5FA46148C045417F922A80B2D9869D3DAC328944C8B7F |
| SSDEEP: | 768:yU8+/s6nFkBywGNunzi+pCWg9PgRv52rpMIH+:NxyGNF+fg9oRvM1e |
MALICIOUS
Writes to a start menu file
- krnl.exe (PID: 2172)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 268)
Uses Task Scheduler to run other applications
- krnl.exe (PID: 2172)
Changes the autorun value in the registry
- krnl.exe (PID: 2172)
SUSPICIOUS
Checks supported languages
- krnl.exe (PID: 2172)
- krnl.exe (PID: 1820)
- krnl.exe (PID: 3624)
- krnl.exe (PID: 3148)
- krnl.exe (PID: 3656)
Reads the computer name
- krnl.exe (PID: 2172)
- krnl.exe (PID: 3624)
- krnl.exe (PID: 1820)
- krnl.exe (PID: 3656)
- krnl.exe (PID: 3148)
Reads Environment values
- krnl.exe (PID: 2172)
Creates files in the user directory
- krnl.exe (PID: 2172)
Drops a file with a compile date too recent
- krnl.exe (PID: 2172)
Executed via Task Scheduler
- krnl.exe (PID: 1820)
- krnl.exe (PID: 3624)
- krnl.exe (PID: 3148)
- krnl.exe (PID: 3656)
Executable content was dropped or overwritten
- krnl.exe (PID: 2172)
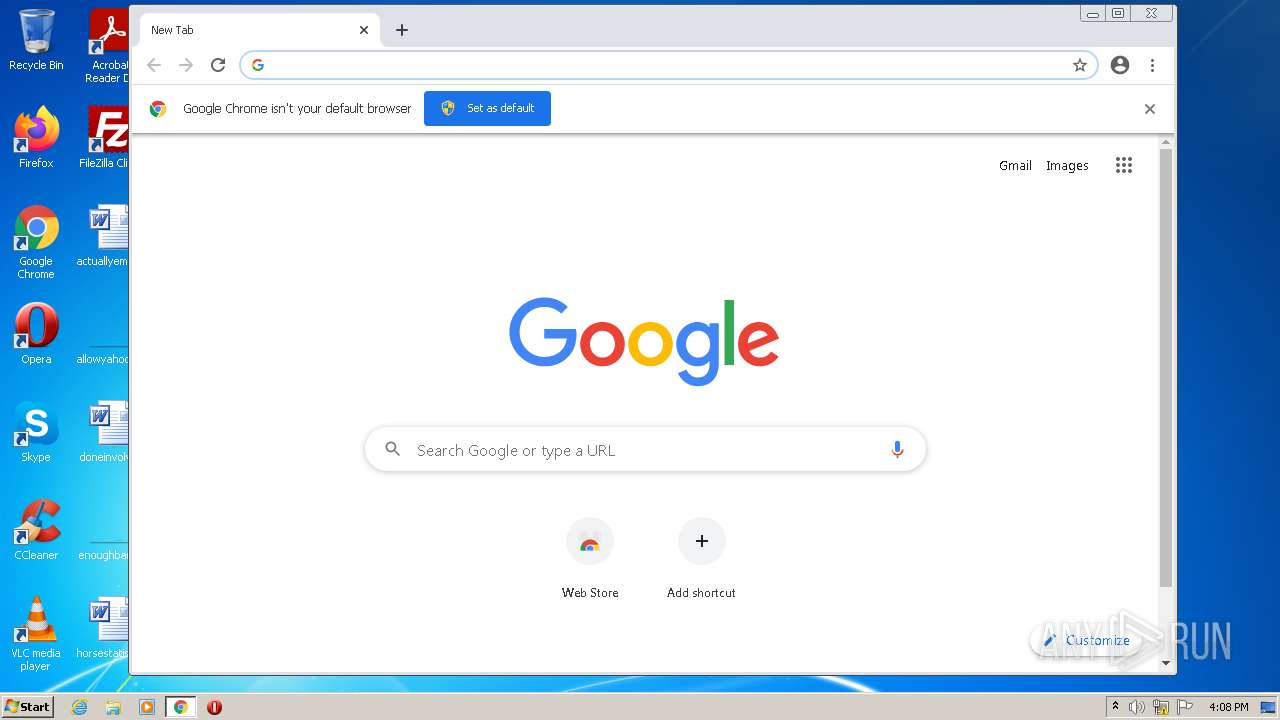
Modifies files in Chrome extension folder
- chrome.exe (PID: 2444)
INFO
Checks supported languages
- schtasks.exe (PID: 268)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 1972)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 1572)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 116)
- chrome.exe (PID: 4076)
Reads the computer name
- schtasks.exe (PID: 268)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 2928)
Reads settings of System Certificates
- krnl.exe (PID: 2172)
- chrome.exe (PID: 1076)
Manual execution by user
- chrome.exe (PID: 2444)
Reads the hosts file
- chrome.exe (PID: 2444)
- chrome.exe (PID: 1076)
Application launched itself
- chrome.exe (PID: 2444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 0.0.0.0 |
|---|---|
| ProductVersion: | 0.0.0.0 |
| OriginalFileName: | krnl.exe |
| LegalCopyright: | |
| InternalName: | krnl.exe |
| FileVersion: | 0.0.0.0 |
| FileDescription: | |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xc1ee |
| UninitializedDataSize: | - |
| InitializedDataSize: | 47616 |
| CodeSize: | 41472 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2022:01:24 16:45:40+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jan-2022 15:45:40 |
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | krnl.exe |
| LegalCopyright: | - |
| OriginalFilename: | krnl.exe |
| ProductVersion: | 0.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 24-Jan-2022 15:45:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000A1F4 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.70268 |
.rsrc | 0x0000E000 | 0x0000B784 | 0x0000B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.80797 |
.reloc | 0x0001A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.20769 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.18977 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.4226 | 6760 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.17064 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.39088 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.34639 | 1720 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 2.99605 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
56
Monitored processes
20
Malicious processes
1
Suspicious processes
0
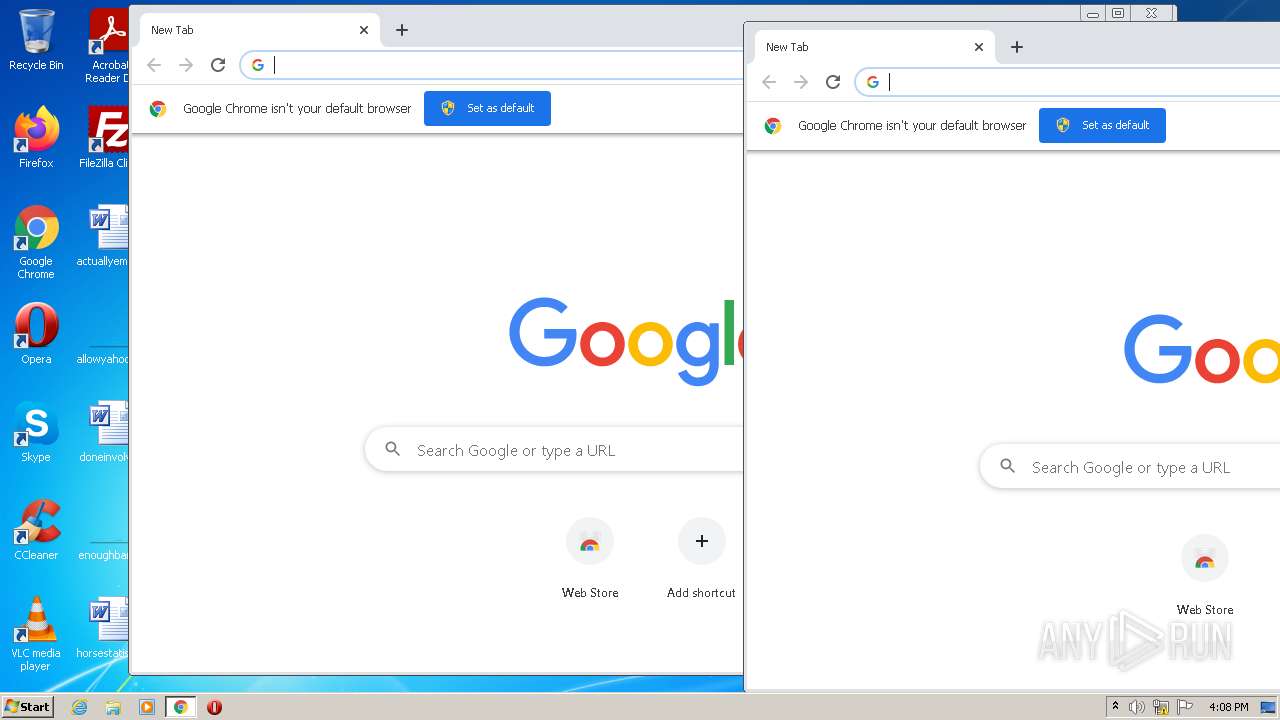
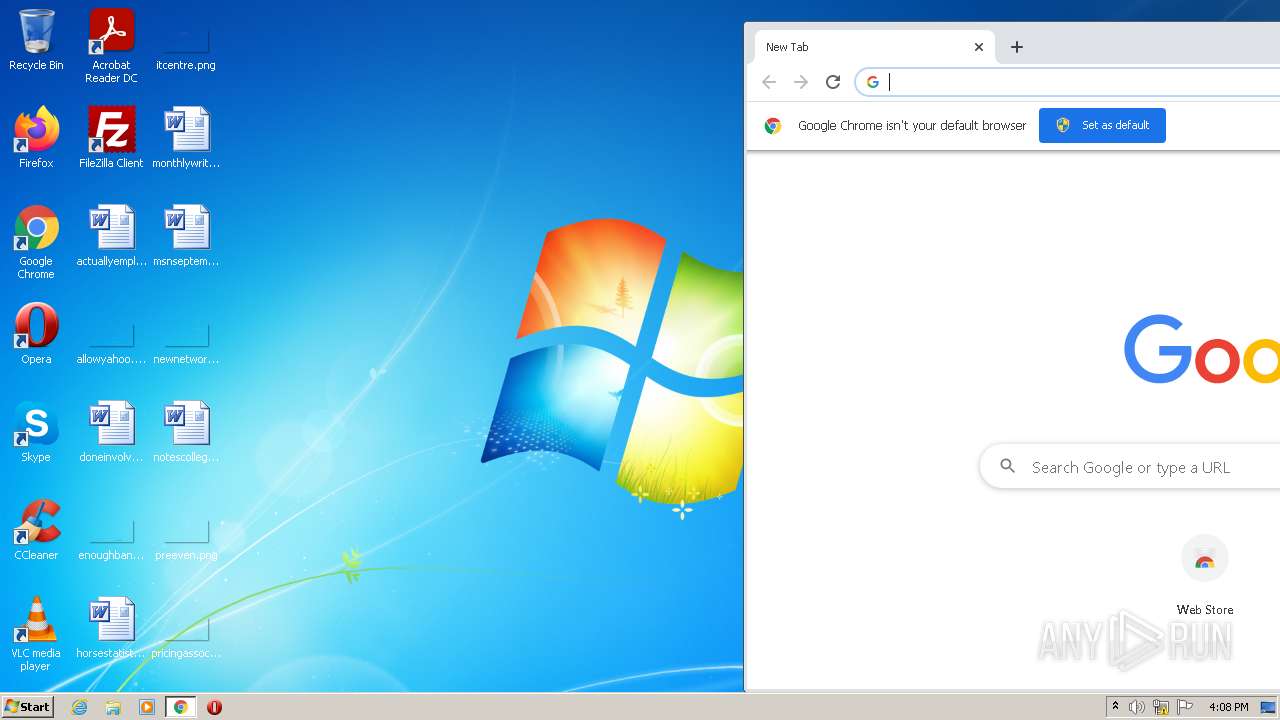
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,12116702548259864514,13120823525327746666,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3184 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 268 | "C:\Windows\System32\schtasks.exe" /create /sc minute /mo 1 /tn "krnl" /tr "C:\Users\admin\AppData\Roaming\krnl.exe" | C:\Windows\System32\schtasks.exe | — | krnl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1052,12116702548259864514,13120823525327746666,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1340 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,12116702548259864514,13120823525327746666,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1820 | C:\Users\admin\AppData\Roaming\krnl.exe | C:\Users\admin\AppData\Roaming\krnl.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e25d988,0x6e25d998,0x6e25d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,12116702548259864514,13120823525327746666,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3348 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2172 | "C:\Users\admin\AppData\Local\Temp\krnl.exe" | C:\Users\admin\AppData\Local\Temp\krnl.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,12116702548259864514,13120823525327746666,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2820 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 165
Read events
13 069
Write events
95
Delete events
1
Modification events
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2172) krnl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
2
Suspicious files
125
Text files
105
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EECEF8-98C.pma | — | |
MD5:— | SHA256:— | |||
| 2172 | krnl.exe | C:\Users\admin\AppData\Roaming\krnl.exe | executable | |
MD5:— | SHA256:— | |||
| 1076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2172 | krnl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\krnl.exe | executable | |
MD5:— | SHA256:— | |||
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a895b075-1852-4508-8906-99277c027445.tmp | text | |
MD5:— | SHA256:— | |||
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1383e9.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1383e9.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1384e3.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
15
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1076 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
1076 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
1076 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1076 | chrome.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1076 | chrome.exe | 142.250.74.195:443 | update.googleapis.com | Google Inc. | US | whitelisted |
1076 | chrome.exe | 142.250.186.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1076 | chrome.exe | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2172 | krnl.exe | 162.159.138.85:443 | sharetext.me | Cloudflare Inc | — | malicious |
1076 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1076 | chrome.exe | 142.250.181.238:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
sharetext.me |
| malicious |
6.tcp.ngrok.io |
| malicious |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |