| File name: | lombok.jar |
| Full analysis: | https://app.any.run/tasks/42500b6f-408a-41c6-bf4f-9dde0e2c4fac |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2023, 12:57:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | F9FF3A48FA4CC5AC7E0A426E2F5C30B2 |
| SHA1: | 6EF15599B55A90D2704A1A9F3FE04C12BB58081C |
| SHA256: | D7EE122EEE1EAEEB45182A89FF36FC2DD086858D1B2F54B615C6FEF7BA1D6012 |
| SSDEEP: | 98304:HUs9+EPHydwcnNA6WjbLpaIqEmRIkaqDpeGemHv+Ijs7ZY14GHVRGFWMVr5flxIM:RlB1uFq |
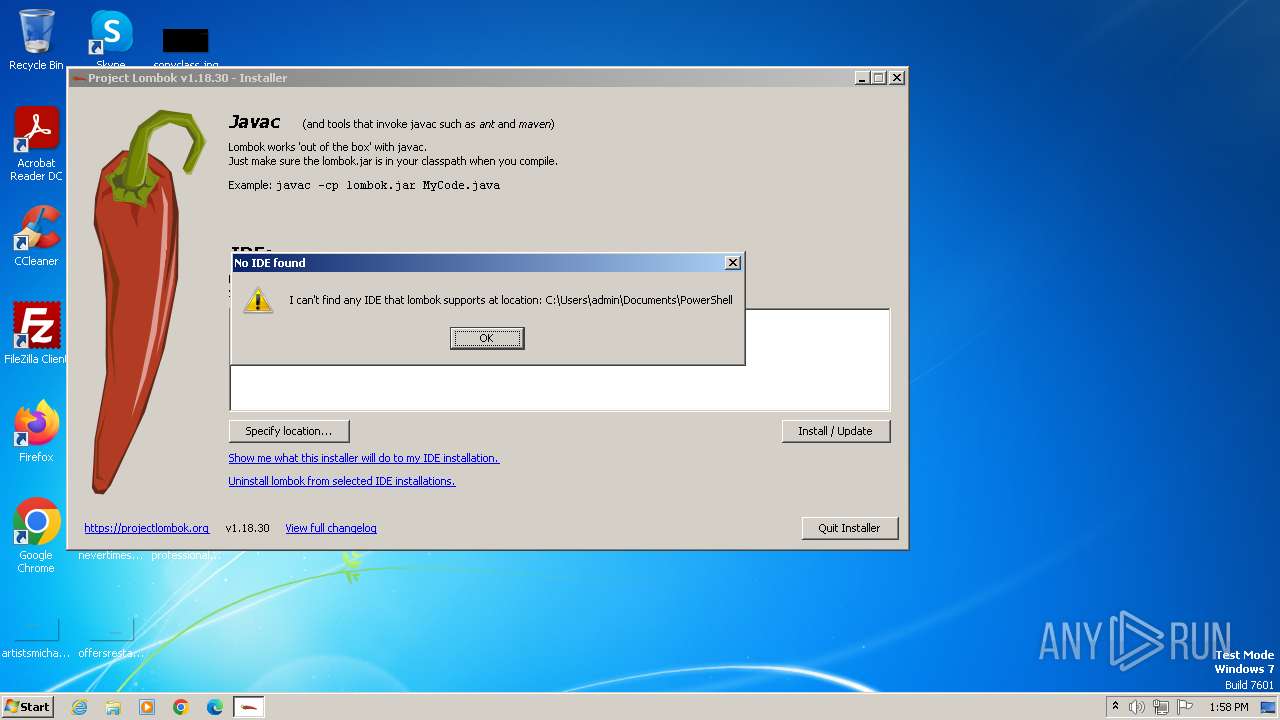
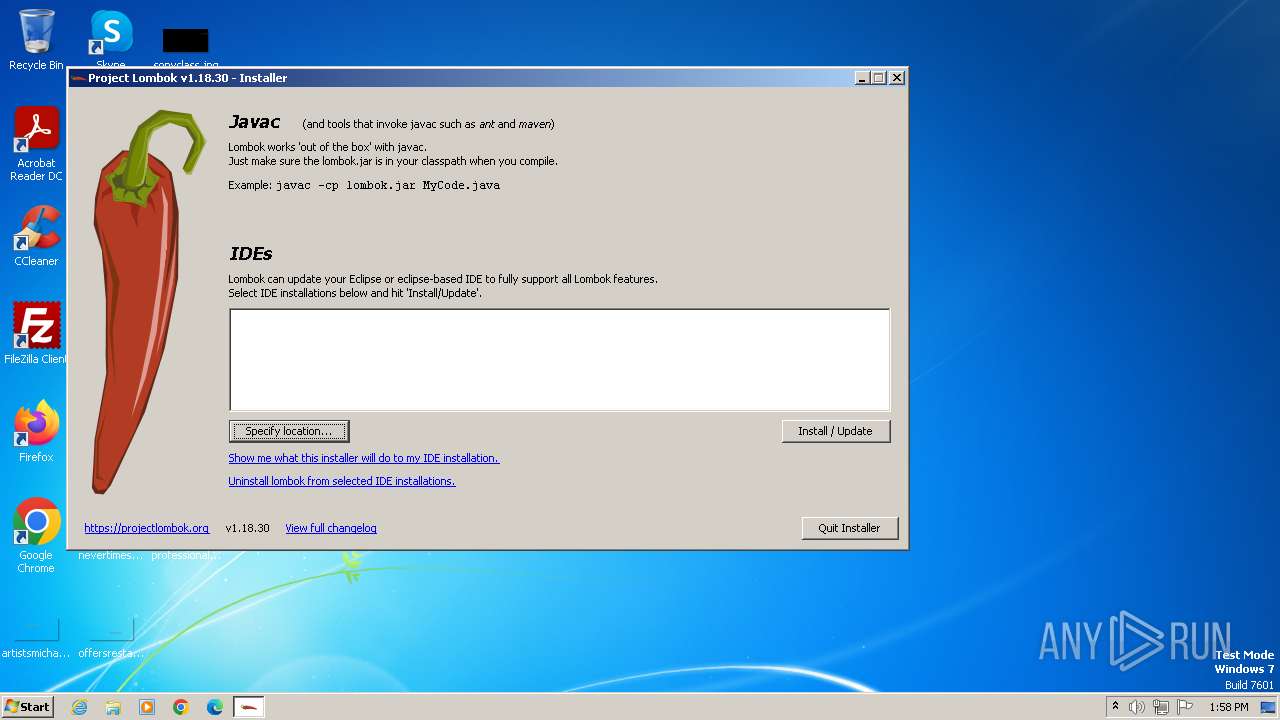
MALICIOUS
Drops the executable file immediately after the start
- javaw.exe (PID: 372)
Loads dropped or rewritten executable
- javaw.exe (PID: 372)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- javaw.exe (PID: 372)
Reads the computer name
- javaw.exe (PID: 372)
Creates files in the program directory
- javaw.exe (PID: 372)
Reads the machine GUID from the registry
- javaw.exe (PID: 372)
Create files in a temporary directory
- javaw.exe (PID: 372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2023:09:20 04:39:50 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/ |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\lombok.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3452 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 228
Read events
1 223
Write events
5
Delete events
0
Modification events
| (PID) Process: | (372) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (372) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:AB6810CBA0AC0CD919F989DE85631A92 | SHA256:CA278514578D11DF1EB4009747CF8E7191F45605142BE090FDE1112F8E4D90AC | |||
| 372 | javaw.exe | C:\Users\admin\AppData\Local\Temp\lombok-1.18.30-WindowsDriveInfo-i386.dll | executable | |
MD5:C4D7064E400A22CC9A59D2D97382B5B8 | SHA256:F210056BA0DFD996646B91E92F4665399B33BF4DA651DEA26B4888F87215EC29 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |