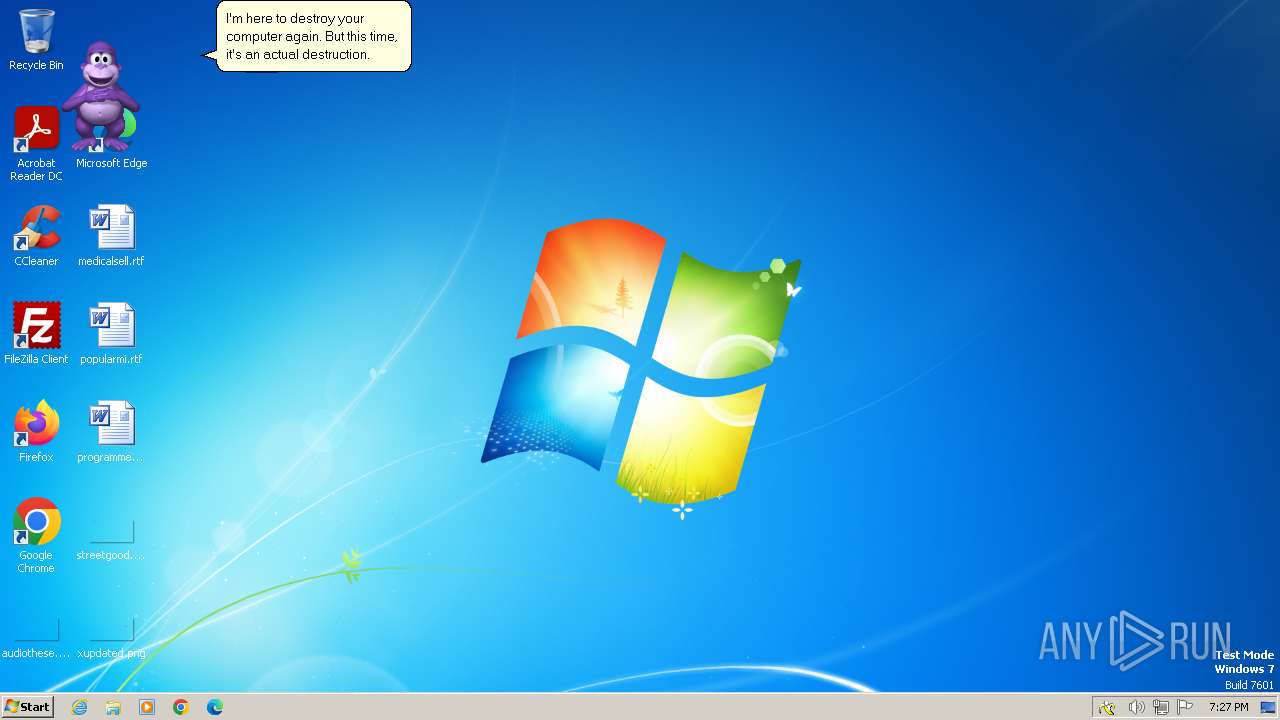
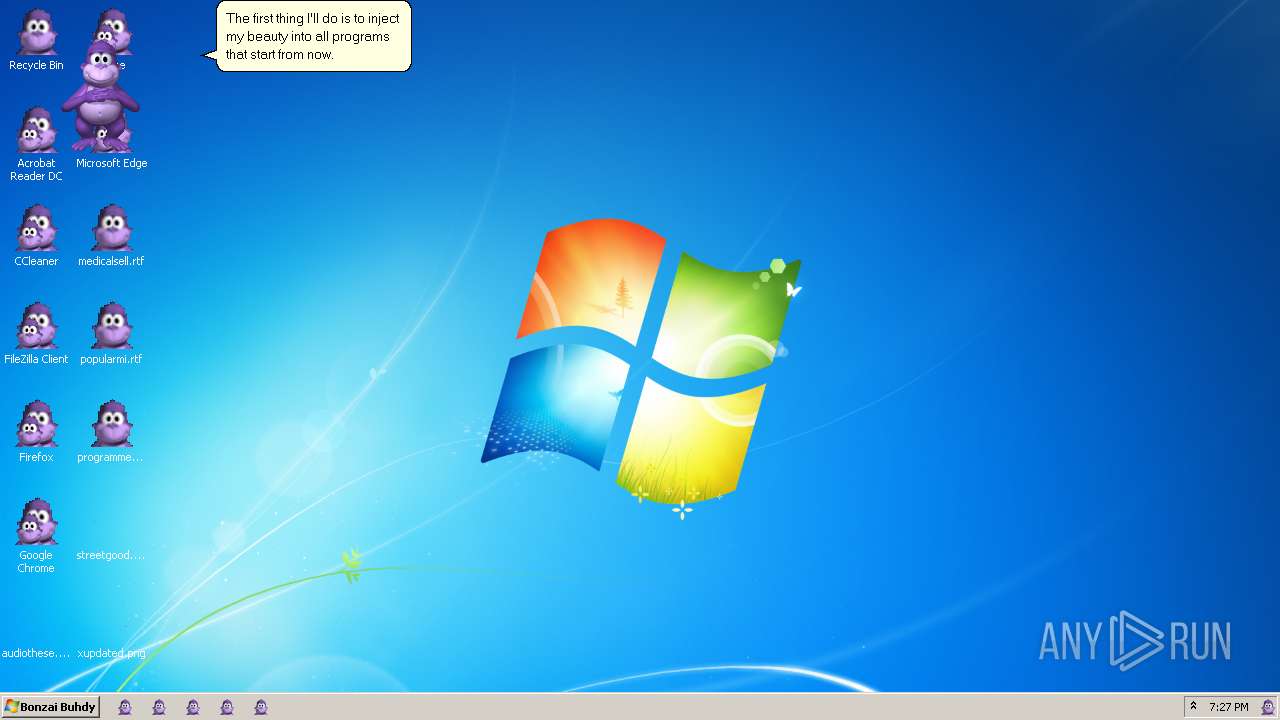
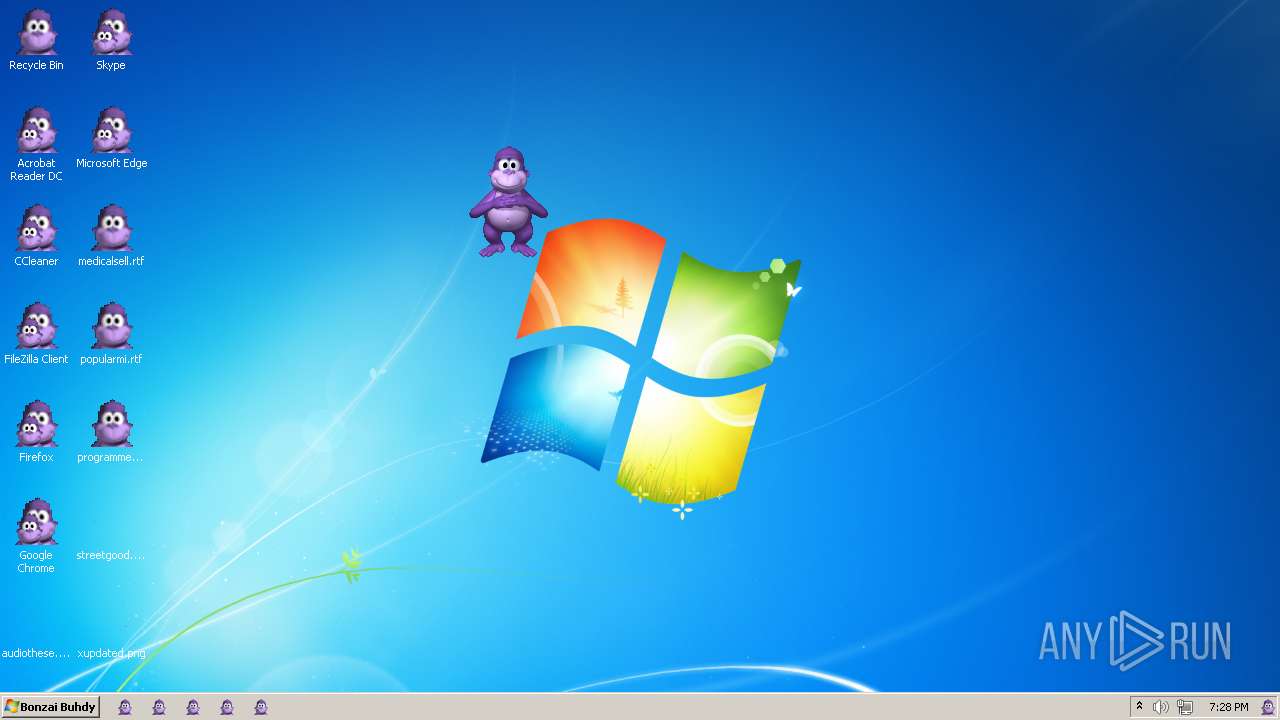
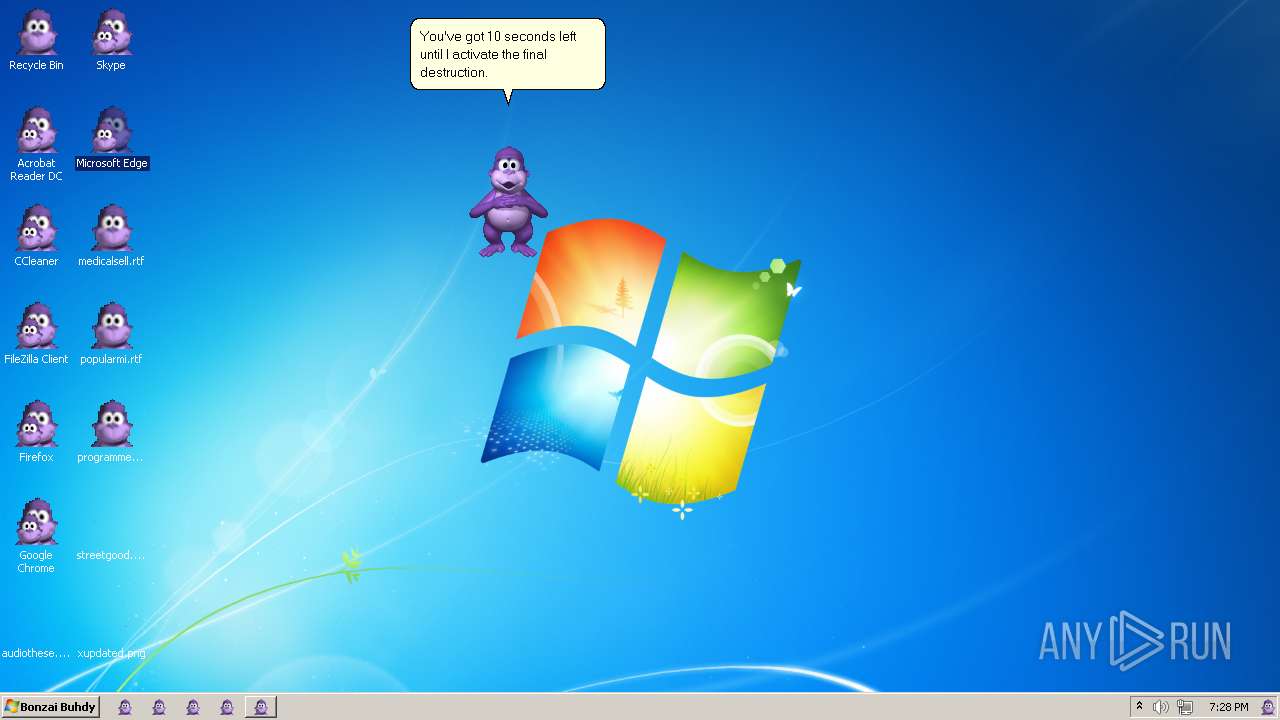
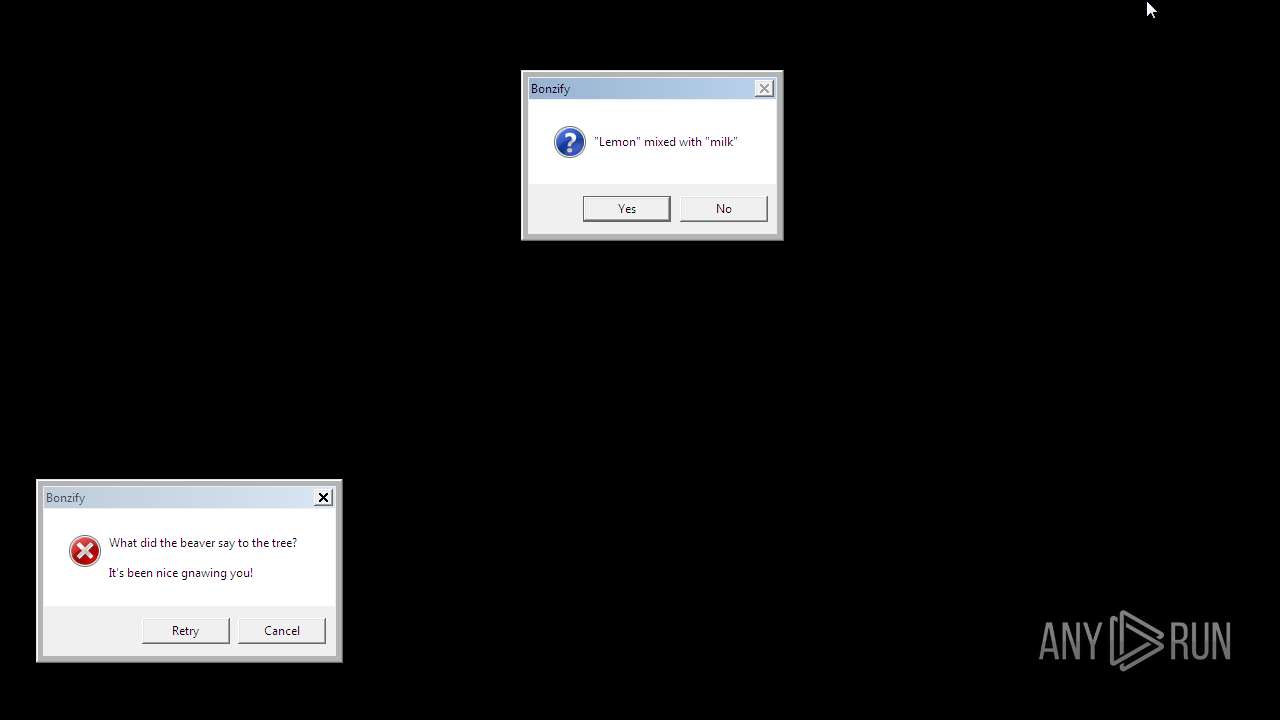
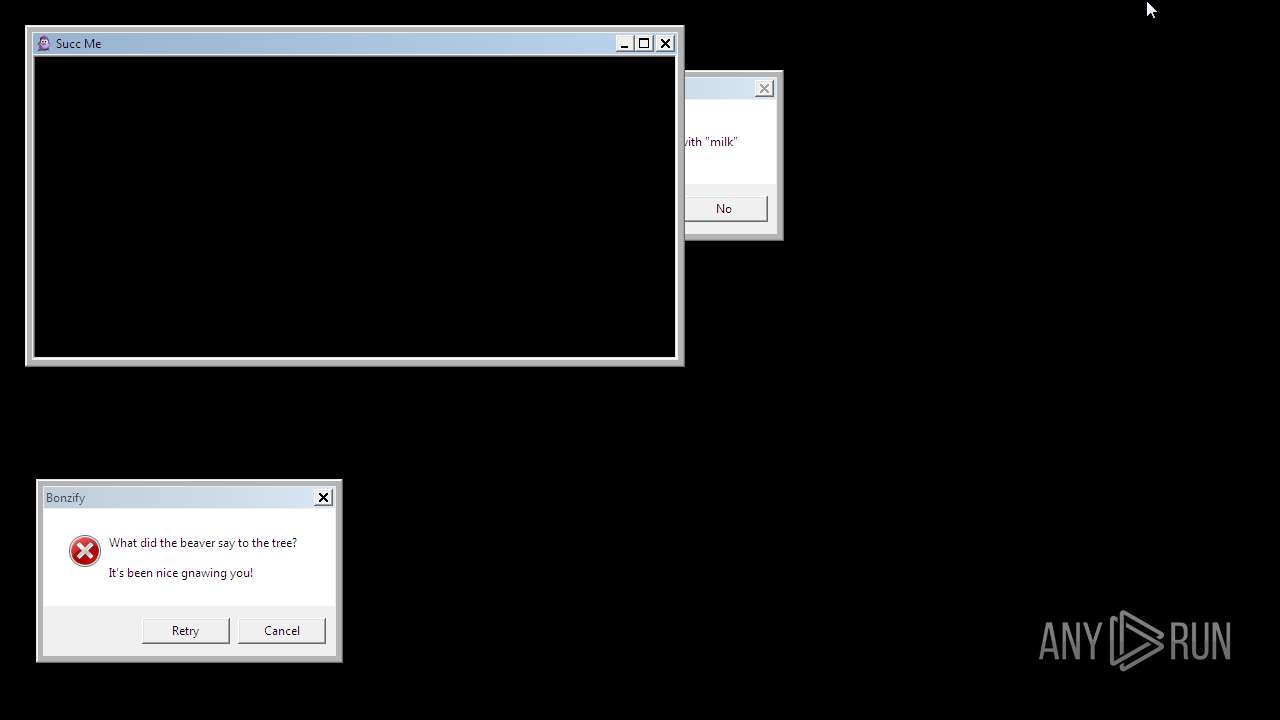
| File name: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/6de9cefb-57c1-4c1f-9aa7-685d3ed3426f |
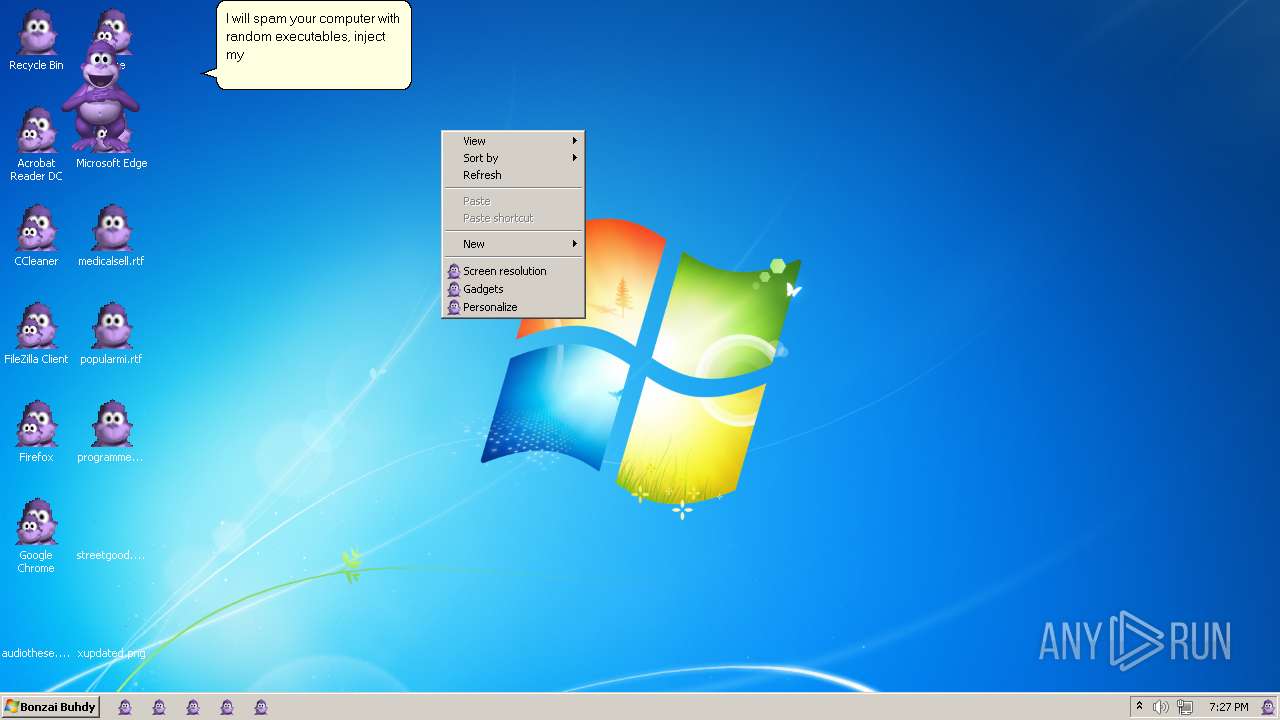
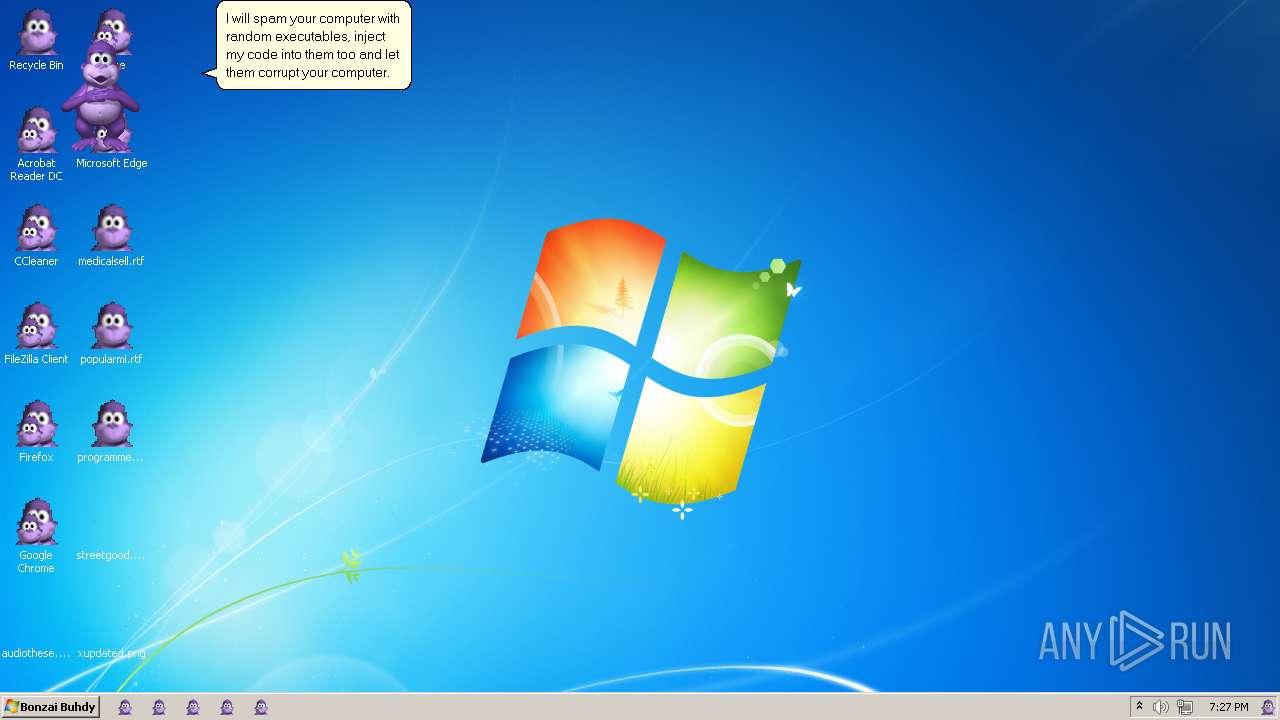
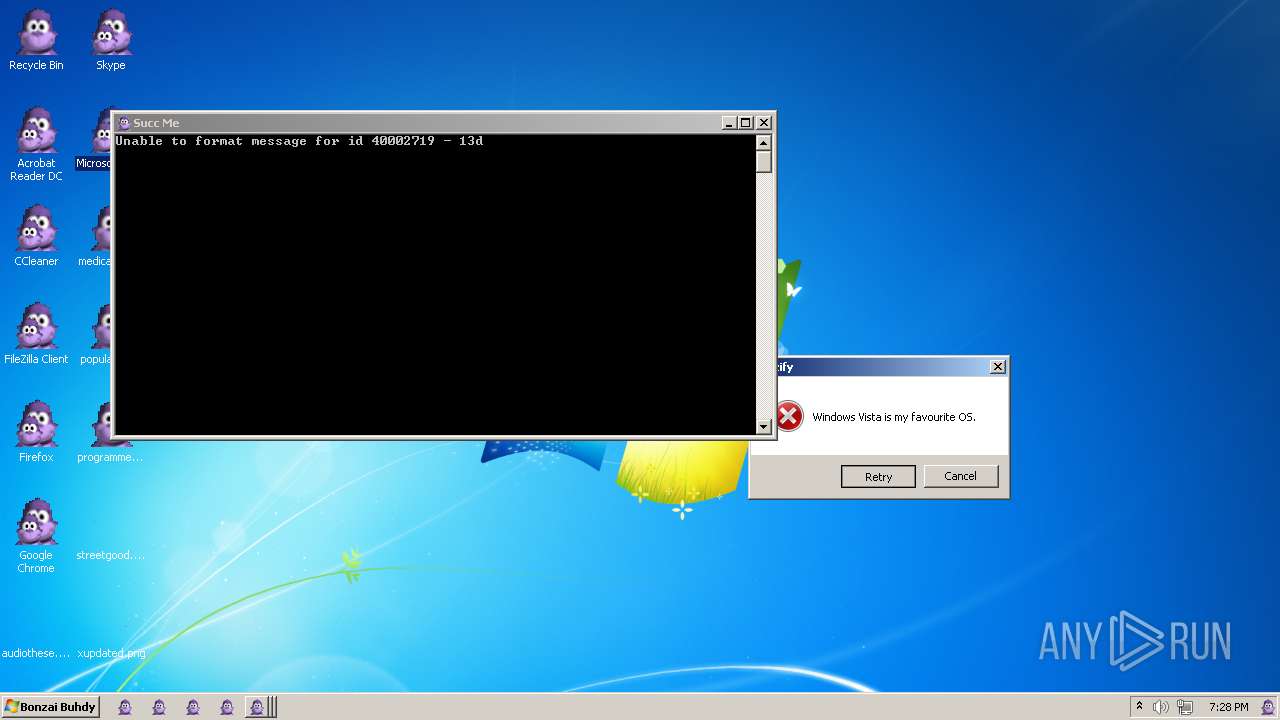
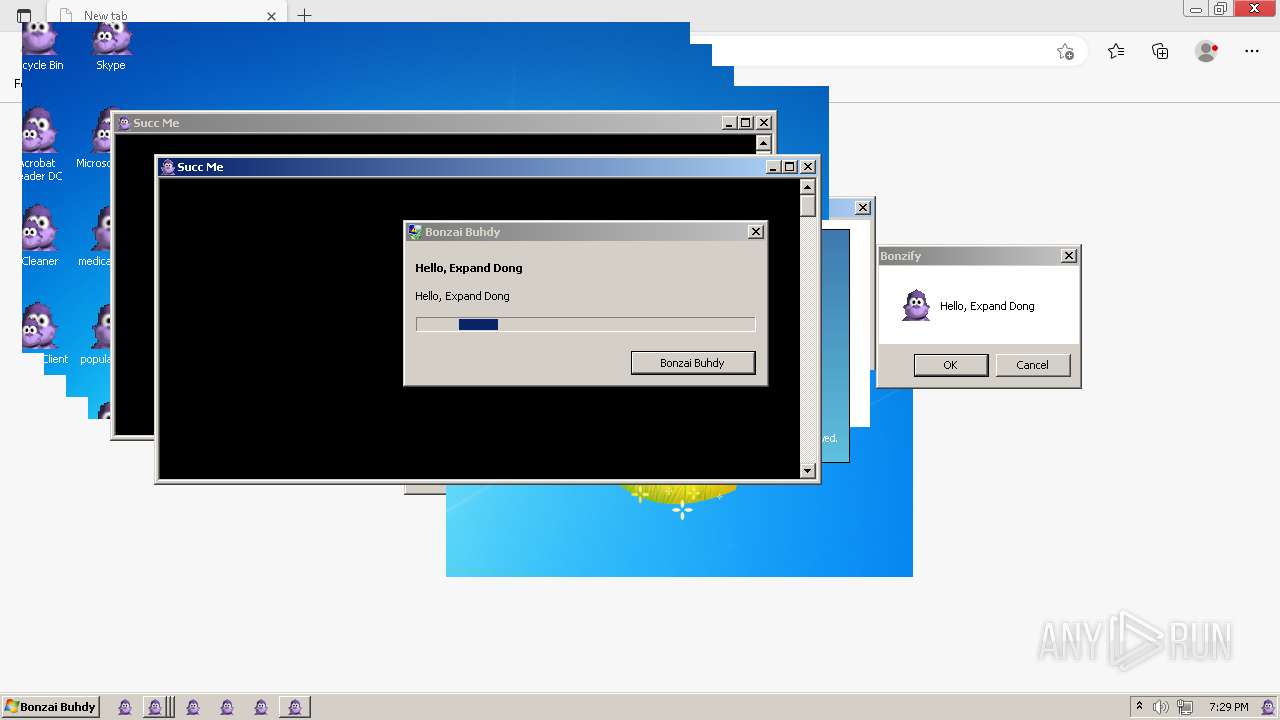
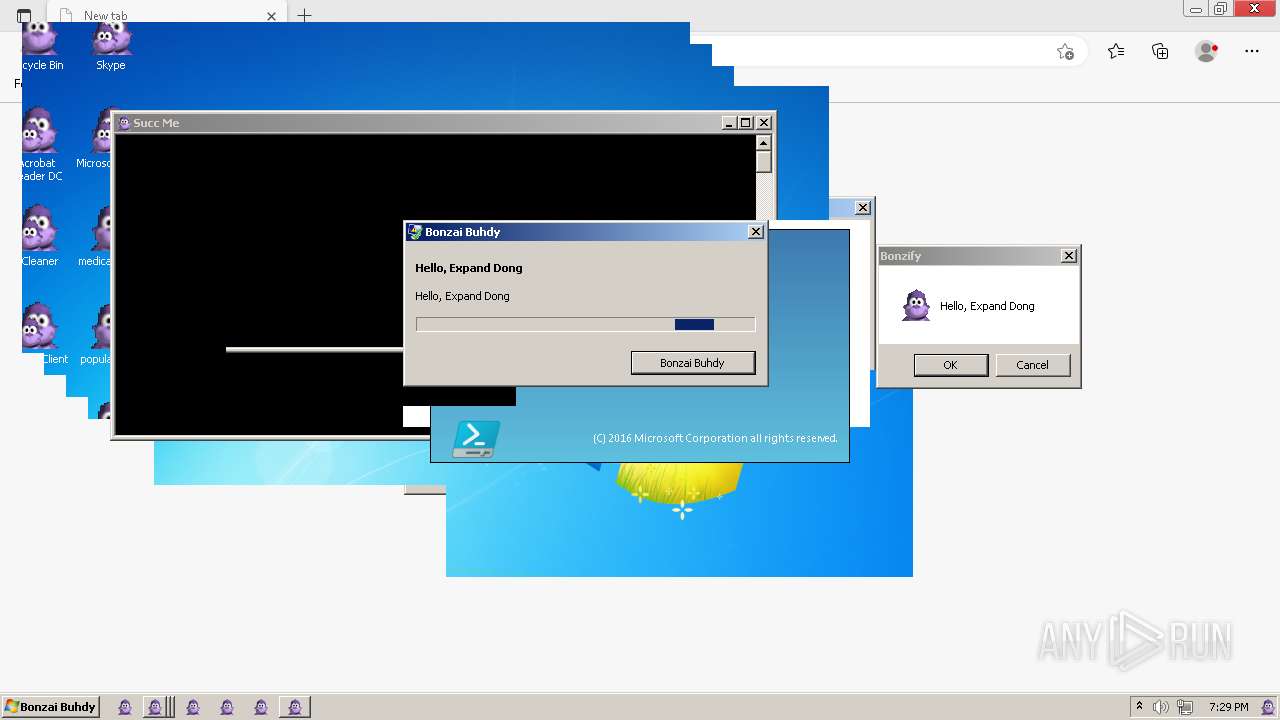
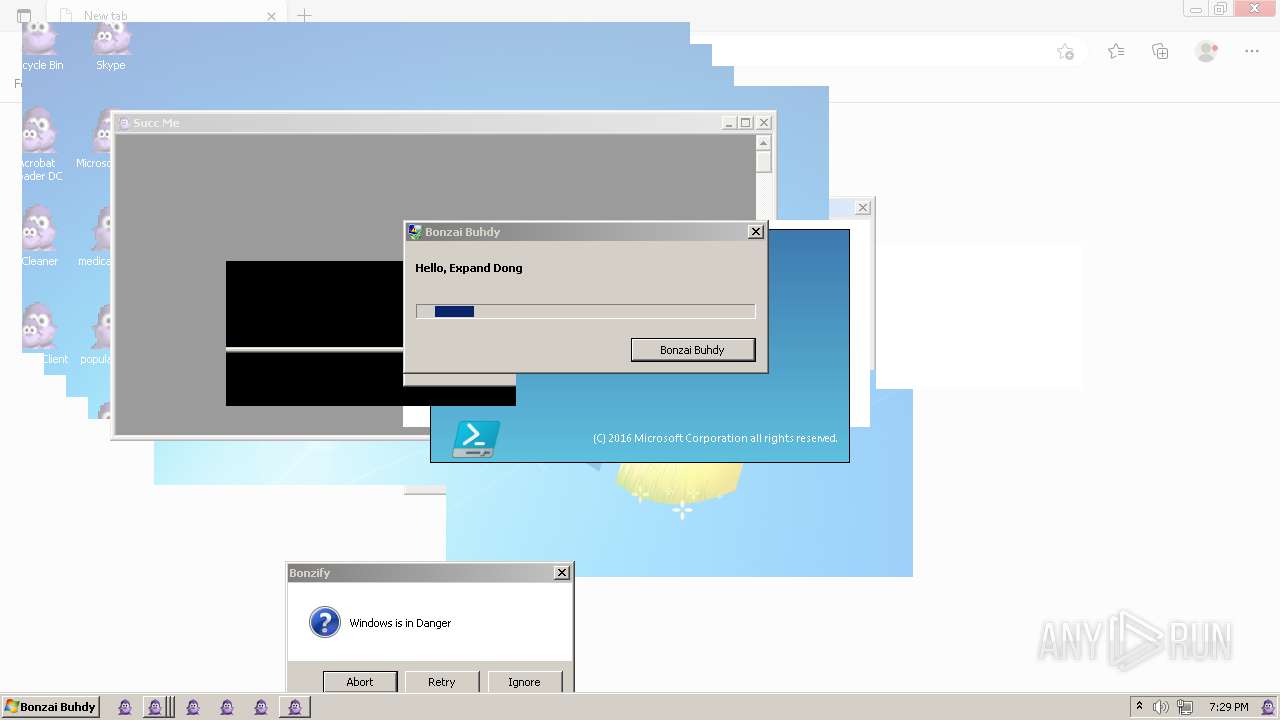
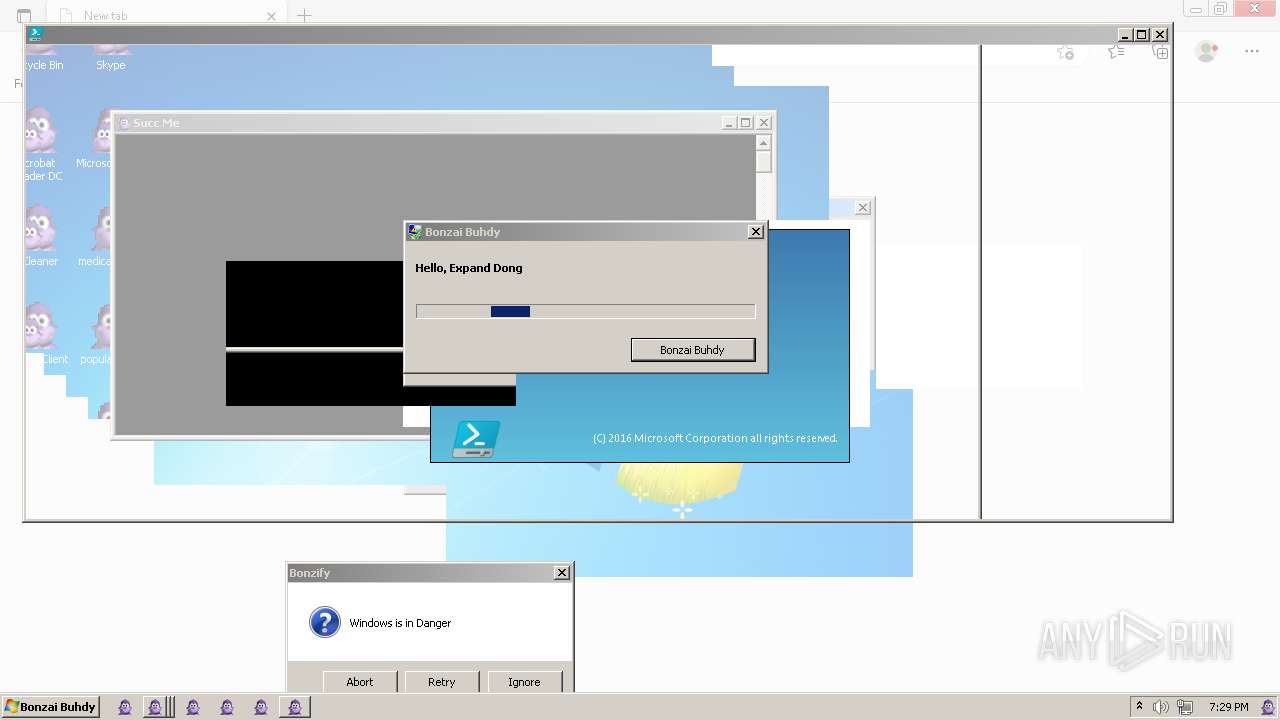
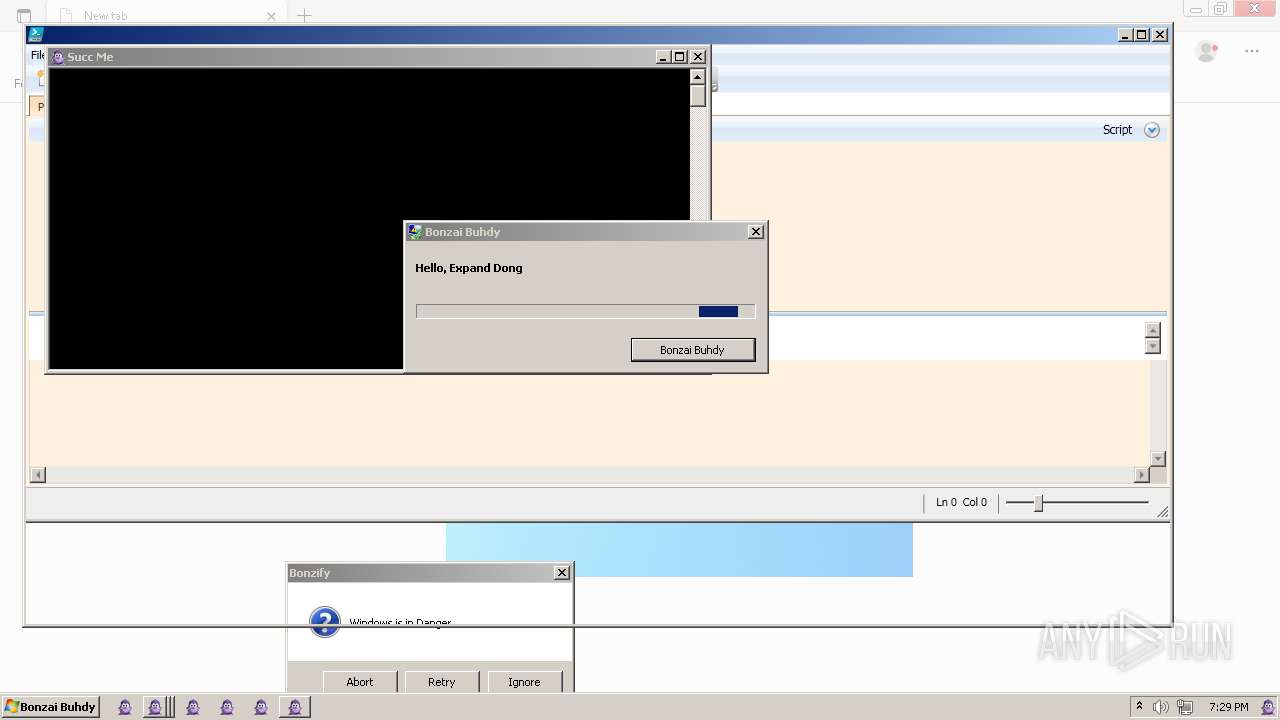
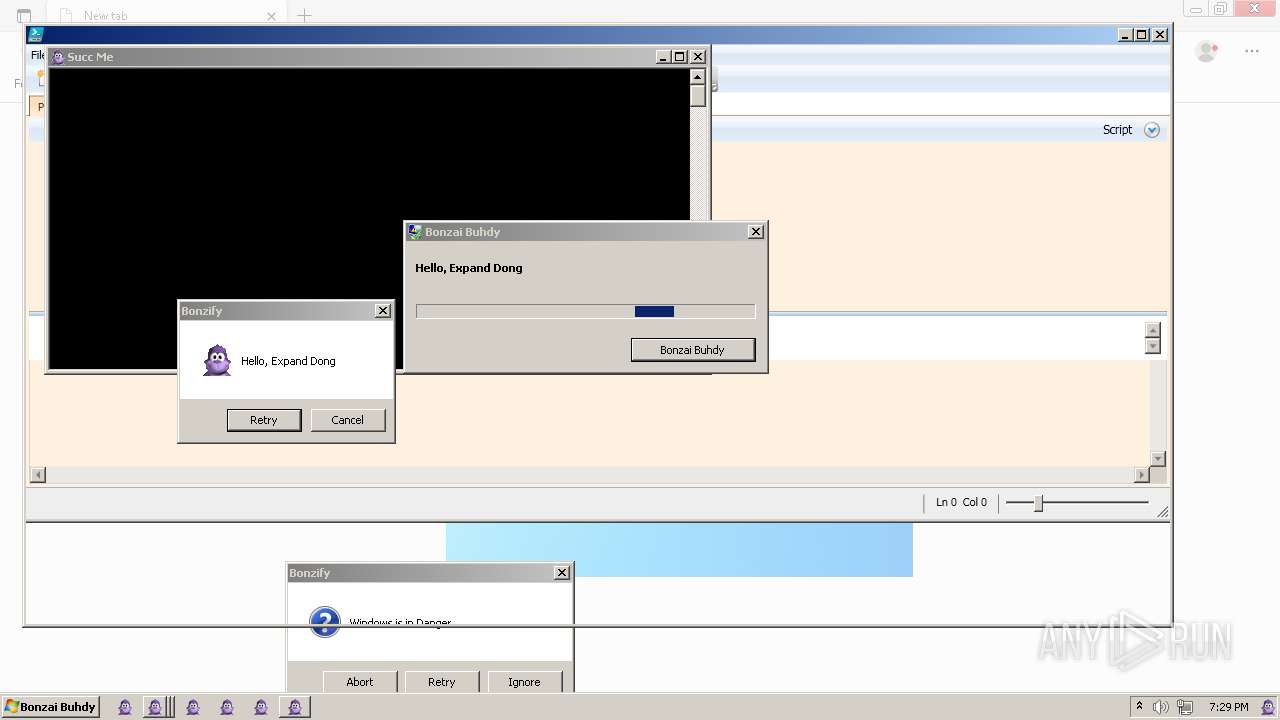
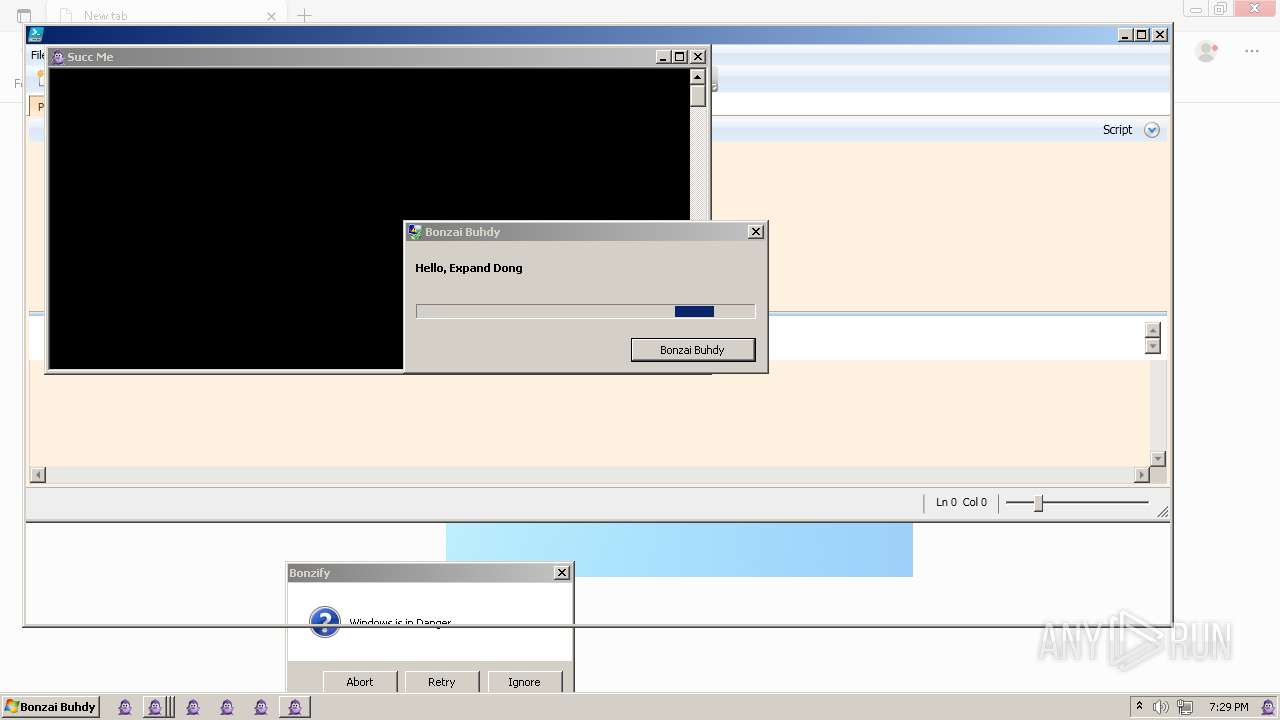
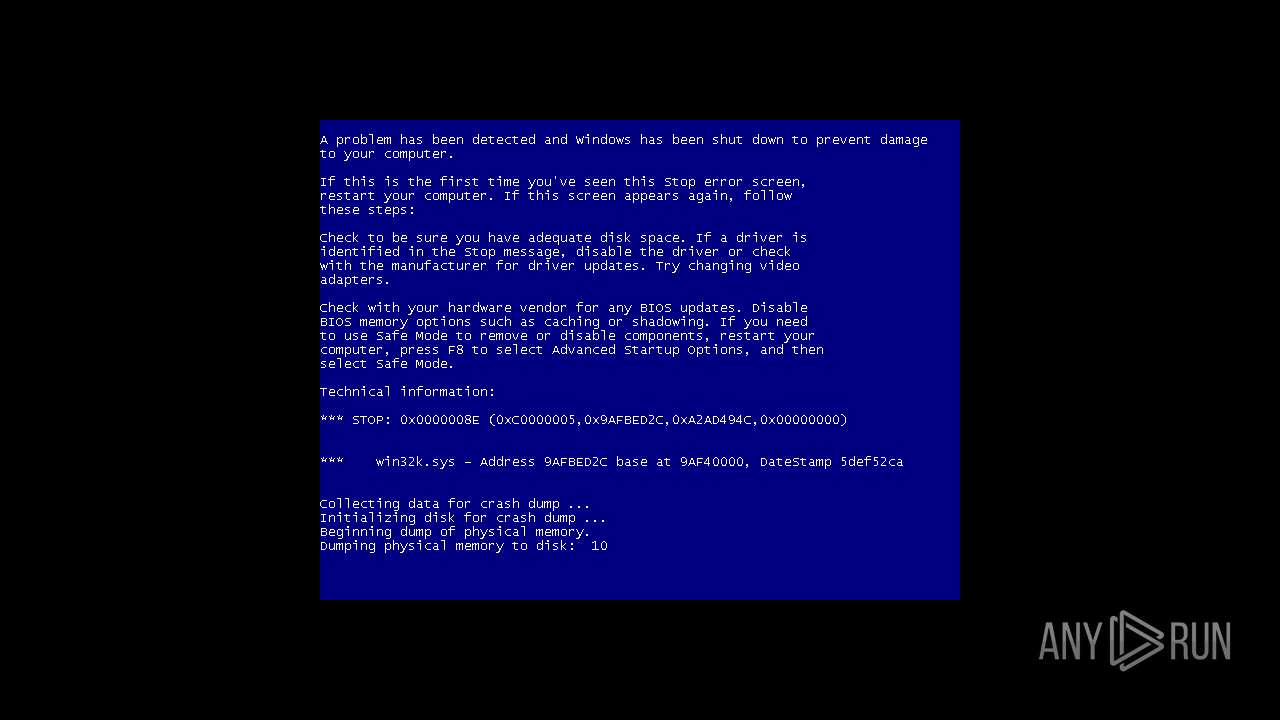
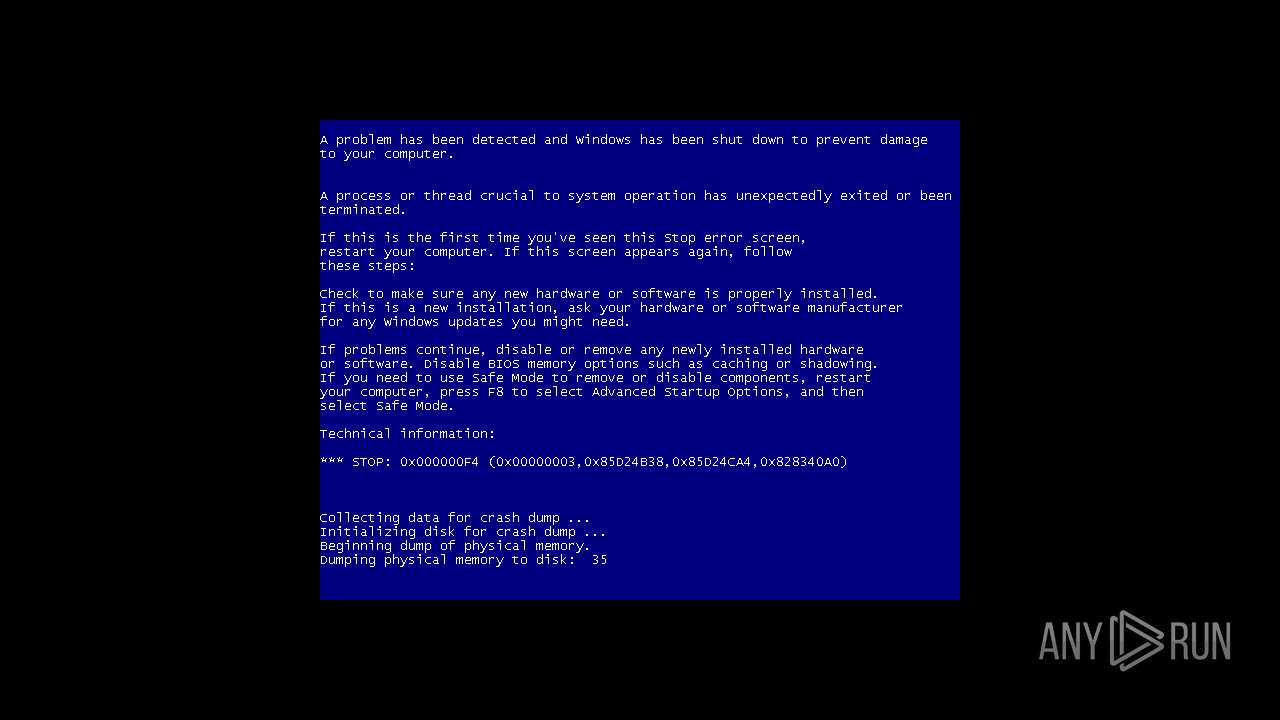
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2024, 19:26:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9C352D2CE0C0BDC40C72F52CE3480577 |
| SHA1: | BD4C956186F33C92EB4469F7E5675510D0790E99 |
| SHA256: | D7E6580054525D3F21F86EDFC9F30B7A75FFA829A1EB67EE3CAB33F0040DBA4E |
| SSDEEP: | 196608:/dAMaWetTeAkLIdx751qFTkub//73lc6u7b5VJ2Yx5xIdk3o:naWedh+Idx75QYub//73lc6u7bLMYxDo |
MALICIOUS
Drops the executable file immediately after the start
- Bonzify.exe (PID: 2840)
- INSTALLER.exe (PID: 2960)
- INSTALLER.exe (PID: 2572)
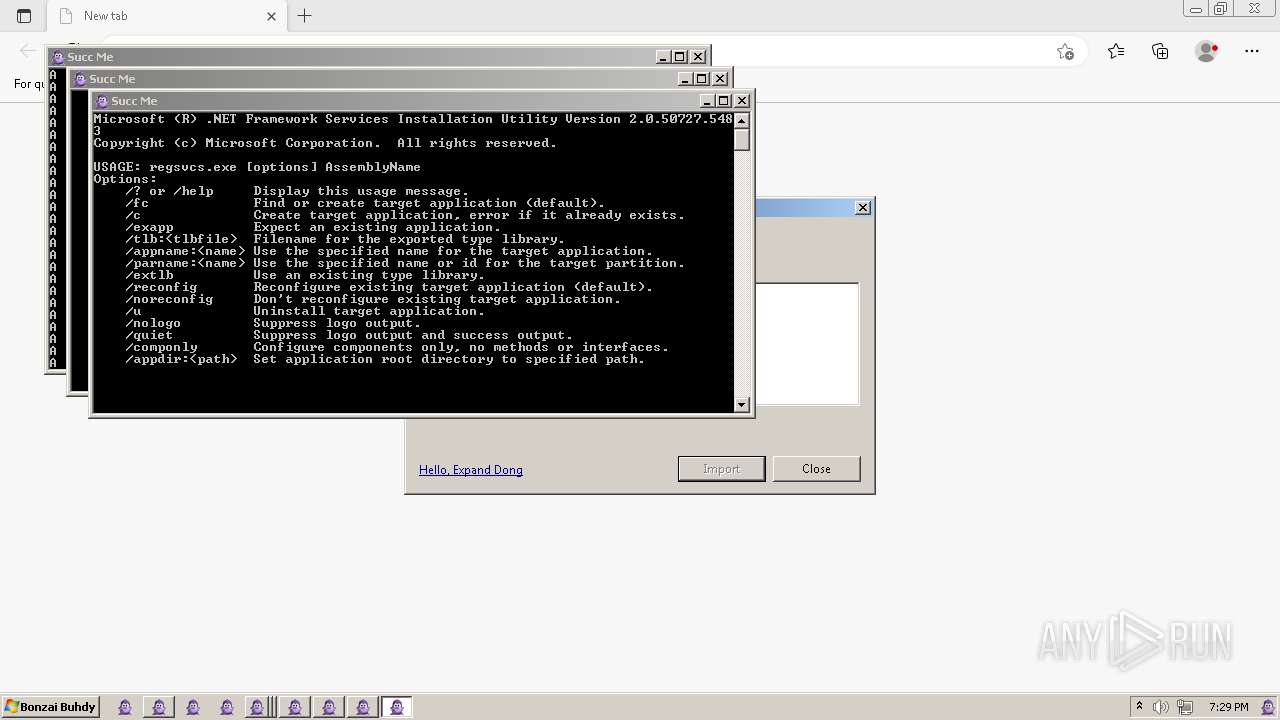
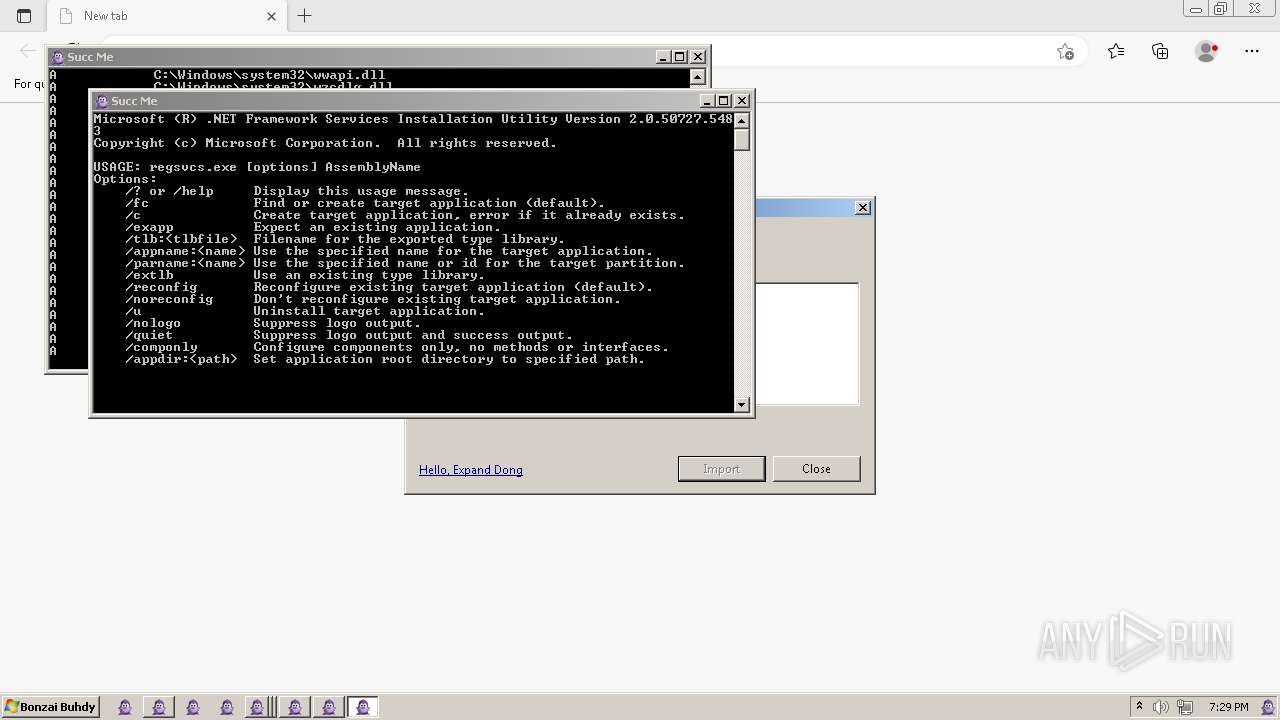
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 2572)
- INSTALLER.exe (PID: 2960)
Creates a writable file in the system directory
- INSTALLER.exe (PID: 2960)
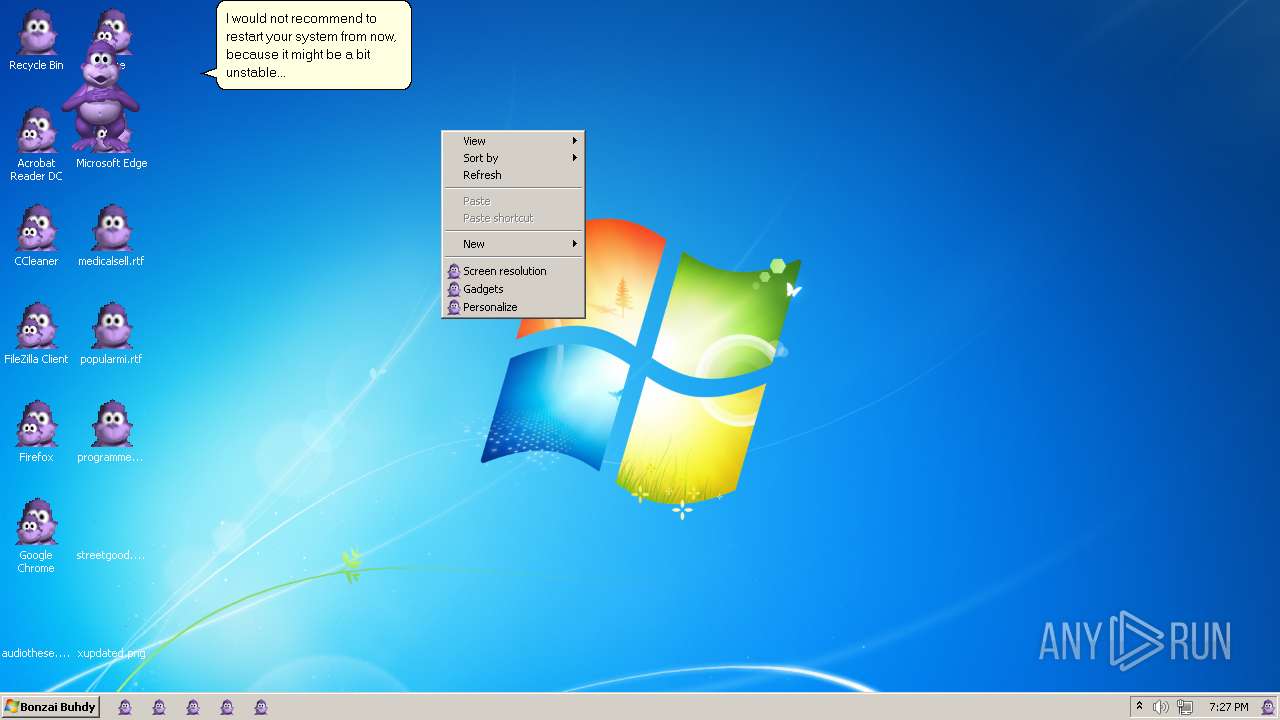
Changes the autorun value in the registry
- INSTALLER.exe (PID: 2960)
- wabmig.exe (PID: 2484)
- windeploy.exe (PID: 3592)
- DeviceDisplayObjectProvider.exe (PID: 2364)
- dplaysvr.exe (PID: 2896)
- dllhost.exe (PID: 2312)
- SETUP.EXE (PID: 3576)
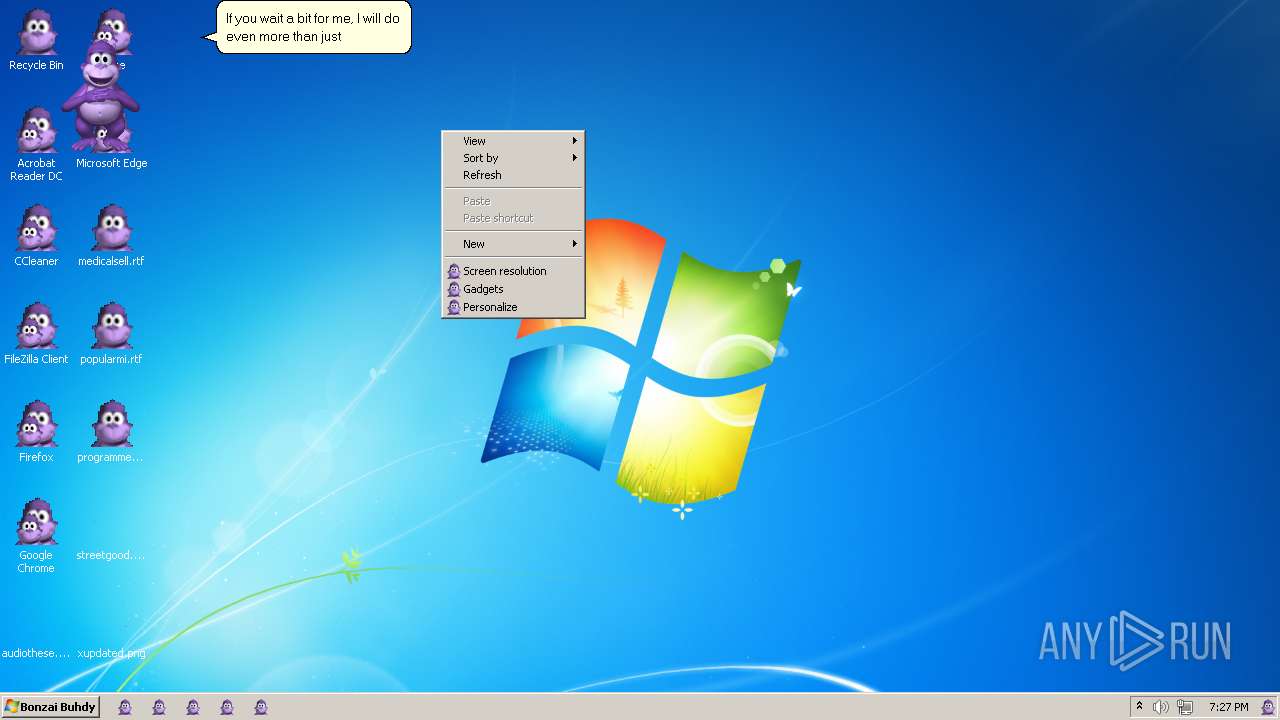
Changes the AppInit_DLLs value (autorun option)
- Bonzify.exe (PID: 2840)
SUSPICIOUS
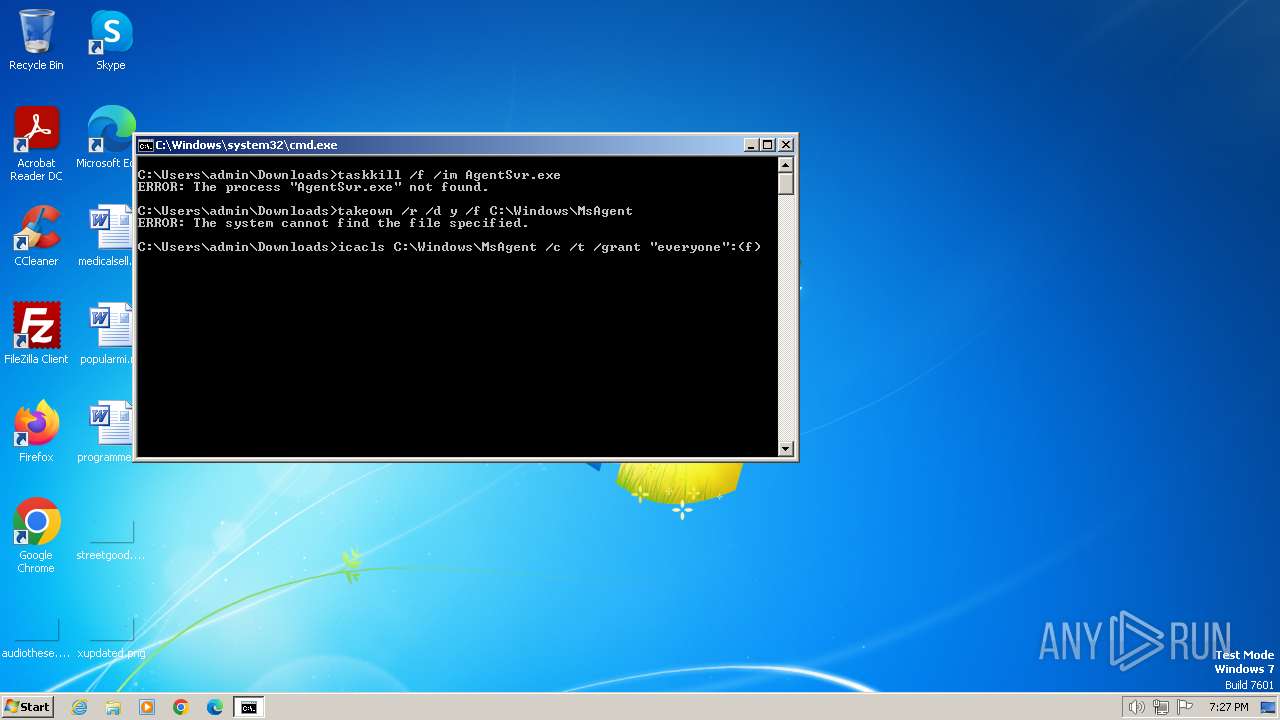
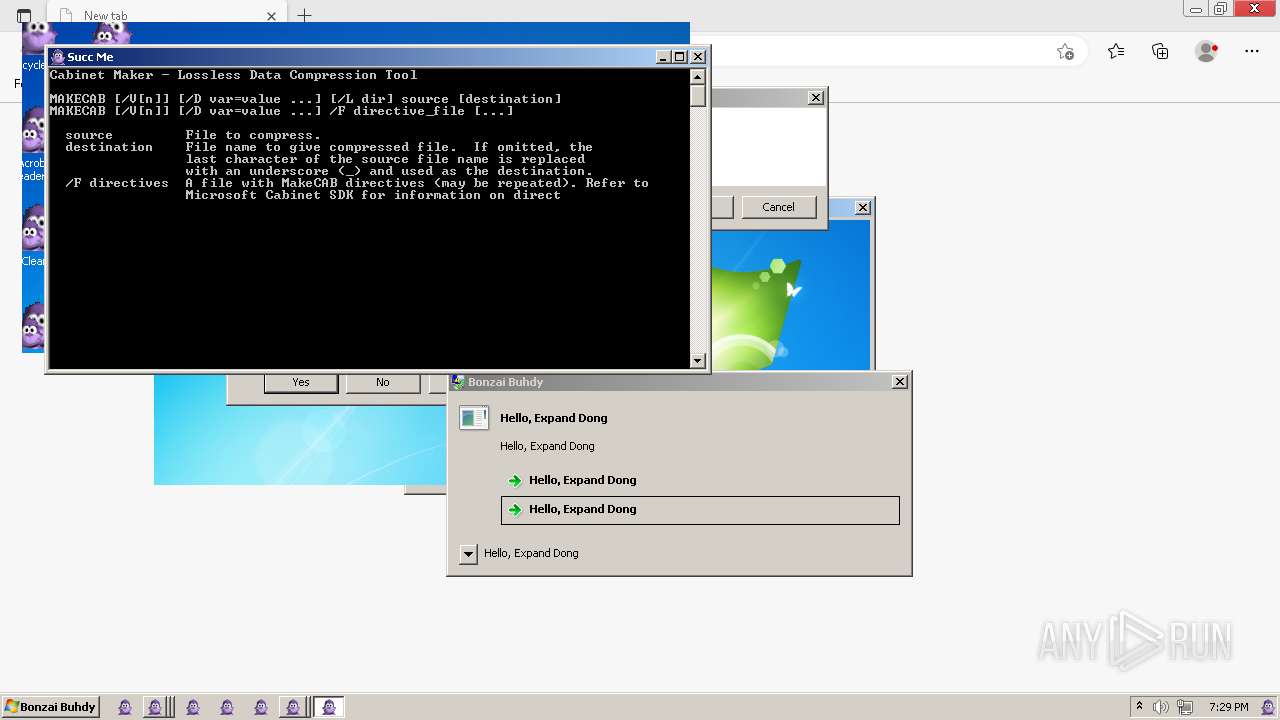
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 2840)
Executing commands from a ".bat" file
- Bonzify.exe (PID: 2840)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3848)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 3848)
Starts a Microsoft application from unusual location
- INSTALLER.exe (PID: 2572)
- INSTALLER.exe (PID: 2960)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3848)
Executable content was dropped or overwritten
- Bonzify.exe (PID: 2840)
- INSTALLER.exe (PID: 2572)
- INSTALLER.exe (PID: 2960)
Process drops legitimate windows executable
- Bonzify.exe (PID: 2840)
- INSTALLER.exe (PID: 2572)
- INSTALLER.exe (PID: 2960)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 4044)
- regsvr32.exe (PID: 2892)
- regsvr32.exe (PID: 956)
- regsvr32.exe (PID: 2896)
- regsvr32.exe (PID: 2756)
- regsvr32.exe (PID: 2792)
- regsvr32.exe (PID: 1740)
- regsvr32.exe (PID: 796)
- regsvr32.exe (PID: 4004)
- msedge.exe (PID: 2820)
- msedge.exe (PID: 3080)
- wabmig.exe (PID: 2484)
- DeviceDisplayObjectProvider.exe (PID: 2364)
- dllhost.exe (PID: 2312)
Creates a software uninstall entry
- INSTALLER.exe (PID: 2960)
- wabmig.exe (PID: 2484)
- dllhost.exe (PID: 2312)
Changes internet zones settings
- dpnsvr.exe (PID: 2548)
- wabmig.exe (PID: 2484)
- dllhost.exe (PID: 2312)
- aspnet_compiler.exe (PID: 1188)
- DeviceDisplayObjectProvider.exe (PID: 2364)
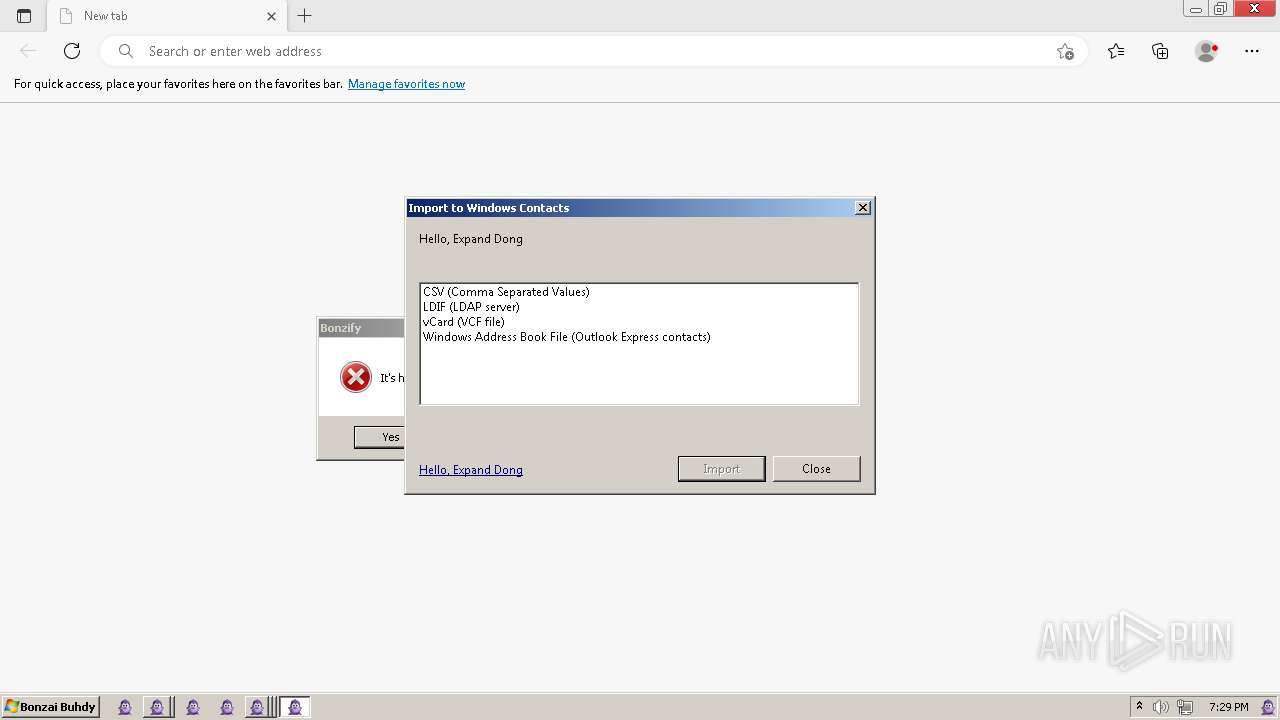
Changes default file association
- wabmig.exe (PID: 2484)
Adds/modifies Windows certificates
- wabmig.exe (PID: 2484)
Executes as Windows Service
- dllhost.exe (PID: 2312)
Changes the title of the Internet Explorer window
- dllhost.exe (PID: 2312)
Changes the Home page of Internet Explorer
- dllhost.exe (PID: 2312)
Checks Windows Trust Settings
- SETUP.EXE (PID: 3576)
Disables SEHOP
- wabmig.exe (PID: 2484)
INFO
Create files in a temporary directory
- Bonzify.exe (PID: 2840)
- INSTALLER.exe (PID: 2572)
- INSTALLER.exe (PID: 2960)
Checks supported languages
- Bonzify.exe (PID: 2840)
- INSTALLER.exe (PID: 2572)
- INSTALLER.exe (PID: 2960)
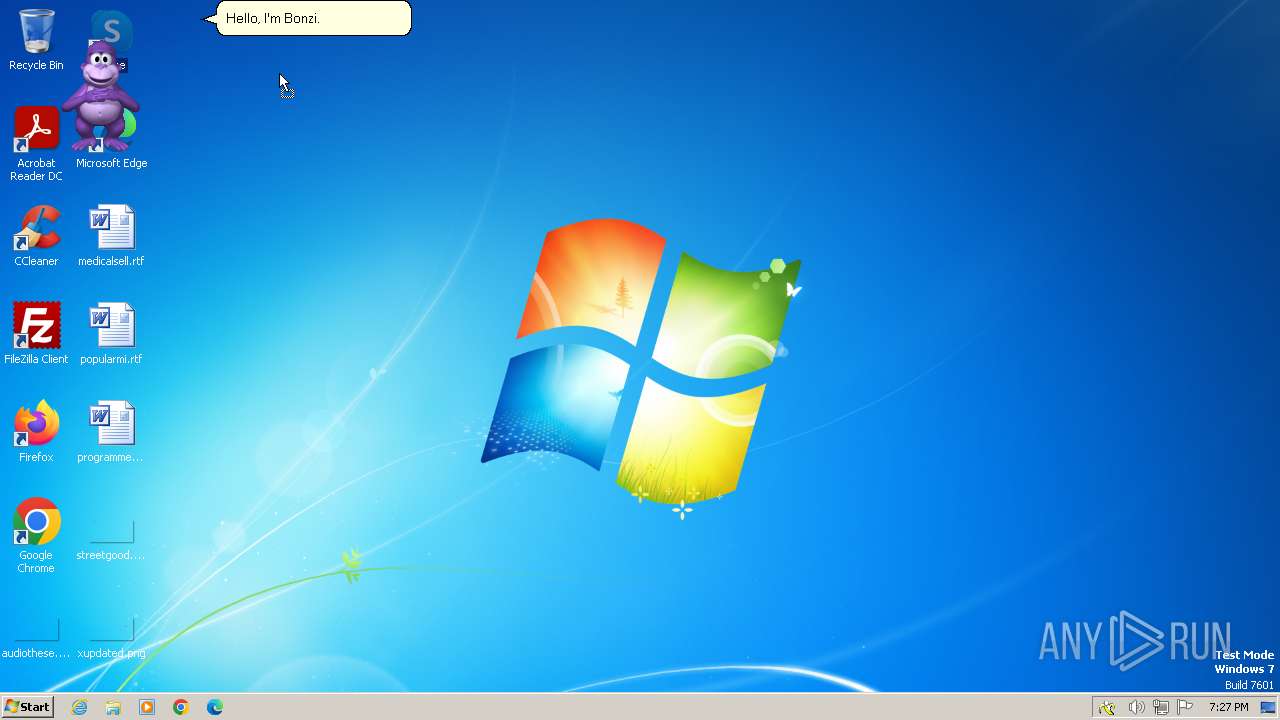
- AgentSvr.exe (PID: 2064)
- AgentSvr.exe (PID: 2148)
- wmpnscfg.exe (PID: 3140)
- wmpnscfg.exe (PID: 3132)
- TSWbPrxy.exe (PID: 2876)
- credwiz.exe (PID: 3052)
- notepad.exe (PID: 3504)
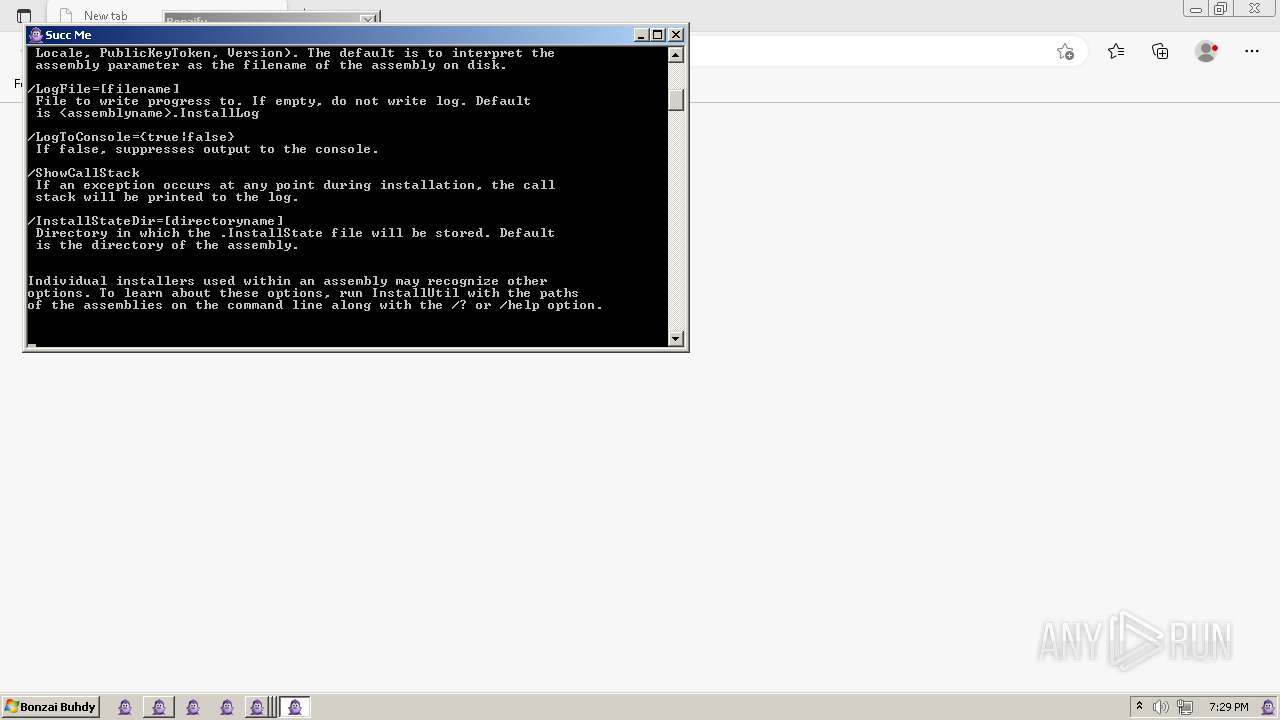
- InstallUtil.exe (PID: 2100)
- msdtc.exe (PID: 1236)
- wabmig.exe (PID: 2484)
- attrib.exe (PID: 1976)
- calc.exe (PID: 908)
- pcawrk.exe (PID: 1072)
- reg.exe (PID: 3284)
- diantz.exe (PID: 4064)
- taskeng.exe (PID: 3692)
- BrmfRsmg.exe (PID: 3332)
- lsass.exe (PID: 1308)
- DeviceEject.exe (PID: 2968)
- invalidateFntcache.exe (PID: 3380)
- SoundRecorder.exe (PID: 3540)
- ServiceModelReg.exe (PID: 3136)
- SETUP.EXE (PID: 3576)
- aspnet_compiler.exe (PID: 1188)
- MSTORDB.EXE (PID: 2248)
- wmpconfig.exe (PID: 4304)
- notepad.exe (PID: 4632)
- unsecapp.exe (PID: 5344)
- upnpcont.exe (PID: 3136)
- lsass.exe (PID: 124)
Reads the computer name
- INSTALLER.exe (PID: 2572)
- INSTALLER.exe (PID: 2960)
- Bonzify.exe (PID: 2840)
- AgentSvr.exe (PID: 2148)
- wmpnscfg.exe (PID: 3140)
- wmpnscfg.exe (PID: 3132)
- TSWbPrxy.exe (PID: 2876)
- msdtc.exe (PID: 1236)
- upnpcont.exe (PID: 3136)
- BrmfRsmg.exe (PID: 3332)
- wabmig.exe (PID: 2484)
- SoundRecorder.exe (PID: 3540)
- MSTORDB.EXE (PID: 2248)
Reads the machine GUID from the registry
- Bonzify.exe (PID: 2840)
- AgentSvr.exe (PID: 2148)
- TSWbPrxy.exe (PID: 2876)
- credwiz.exe (PID: 3052)
- InstallUtil.exe (PID: 2100)
- msdtc.exe (PID: 1236)
- wabmig.exe (PID: 2484)
- attrib.exe (PID: 1976)
- calc.exe (PID: 908)
- upnpcont.exe (PID: 3136)
- BrmfRsmg.exe (PID: 3332)
- SoundRecorder.exe (PID: 3540)
- SETUP.EXE (PID: 3576)
- aspnet_compiler.exe (PID: 1188)
- diantz.exe (PID: 4064)
Manual execution by a user
- wmpnscfg.exe (PID: 3140)
- msedge.exe (PID: 3080)
- wmpnscfg.exe (PID: 3132)
- msedge.exe (PID: 3464)
- msedge.exe (PID: 2792)
- msedge.exe (PID: 2904)
- mpnotify.exe (PID: 2480)
- qappsrv.exe (PID: 3632)
- mtstocom.exe (PID: 2780)
- attrib.exe (PID: 1976)
- SystemPropertiesDataExecutionPrevention.exe (PID: 1632)
- winload.exe (PID: 2496)
- windeploy.exe (PID: 3592)
- diantz.exe (PID: 4064)
- mcbuilder.exe (PID: 3536)
- msedge.exe (PID: 1576)
- msedge.exe (PID: 2564)
Application launched itself
- msedge.exe (PID: 3080)
- msedge.exe (PID: 3464)
- msedge.exe (PID: 2792)
- msedge.exe (PID: 1576)
- msedge.exe (PID: 2564)
- msedge.exe (PID: 2820)
- msedge.exe (PID: 2904)
Checks transactions between databases Windows and Oracle
- dllhost.exe (PID: 2312)
Reads Microsoft Office registry keys
- SETUP.EXE (PID: 3576)
Reads the software policy settings
- SETUP.EXE (PID: 3576)
Reads Environment values
- MSTORDB.EXE (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (86.7) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.8) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Generic Win/DOS Executable (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:04 14:58:11+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 4096 |
| InitializedDataSize: | 6697472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
298
Monitored processes
108
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Windows\winsxs\x86_microsoft-windows-lsa_31bf3856ad364e35_6.1.7601.17940_none_a82d8b59bb293454\lsass.exe" | C:\Windows\winsxs\x86_microsoft-windows-lsa_31bf3856ad364e35_6.1.7601.17940_none_a82d8b59bb293454\lsass.exe | — | wabmig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Local Security Authority Process Exit code: 3221225569 Version: 6.1.7601.17725 (win7sp1_gdr.111116-1503) Modules
| |||||||||||||||
| 240 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xcc,0xd0,0xd4,0xa0,0x100,0x6dcbf598,0x6dcbf5a8,0x6dcbf5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 696 | grpconv.exe -o | C:\Windows\System32\grpconv.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2980 --field-trial-handle=1192,i,8677368232141941115,1975439526682163907,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 796 | regsvr32 /s C:\Windows\lhsp\tv\tv_enua.dll | C:\Windows\System32\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Windows\winsxs\x86_microsoft-windows-calc_31bf3856ad364e35_6.1.7601.17514_none_abc56b2678fe1108\calc.exe" | C:\Windows\winsxs\x86_microsoft-windows-calc_31bf3856ad364e35_6.1.7601.17514_none_abc56b2678fe1108\calc.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 3221225477 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | regsvr32 /s "C:\Windows\msagent\AgentSR.dll" | C:\Windows\System32\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Windows\winsxs\x86_microsoft-windows-a..atibility-assistant_31bf3856ad364e35_6.1.7600.16385_none_339cdc37847a979b\pcawrk.exe" | C:\Windows\winsxs\x86_microsoft-windows-a..atibility-assistant_31bf3856ad364e35_6.1.7600.16385_none_339cdc37847a979b\pcawrk.exe | — | wabmig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Assistant Helper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1188 | "C:\Windows\winsxs\x86_aspnet_compiler_b03f5f7f11d50a3a_6.1.7601.22617_none_d65590612edbd344\aspnet_compiler.exe" | C:\Windows\winsxs\x86_aspnet_compiler_b03f5f7f11d50a3a_6.1.7601.22617_none_d65590612edbd344\aspnet_compiler.exe | — | dllhost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: aspnet_compiler.exe Exit code: 1 Version: 2.0.50727.7057 (QFE.050727-7000) Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3252 --field-trial-handle=1192,i,8677368232141941115,1975439526682163907,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
15 295
Read events
12 472
Write events
2 803
Delete events
20
Modification events
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F5BE8BD2-7DE6-11D0-91FE-00C04FD701A5}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\Control |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\InprocServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\MiscStatus\1 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\MiscStatus |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\ProgID |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\Programmable |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\ToolboxBitmap32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4004) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\TypeLib |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
53
Suspicious files
27
Text files
36
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTDPV.DLL | executable | |
MD5:7C5AEFB11E797129C9E90F279FBDF71B | SHA256:394A17150B8774E507B8F368C2C248C10FCE50FC43184B744E771F0E79ECAFED | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTSVR.EXE | executable | |
MD5:5C91BF20FE3594B81052D131DB798575 | SHA256:E8CE546196B6878A8C34DA863A6C8A7E34AF18FB9B509D4D36763734EFA2D175 | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTDP2.DLL | executable | |
MD5:A334BBF5F5A19B3BDB5B7F1703363981 | SHA256:C33BEABA130F8B740DDDB9980FE9012F9322AC6E94F36A6AA6086851C51B98DE | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGT0409.DLL | executable | |
MD5:0CBF0F4C9E54D12D34CD1A772BA799E1 | SHA256:6B0B57E5B27D901F4F106B236C58D0B2551B384531A8F3DAD6C06ED4261424B1 | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGT0409.HLP | hlp | |
MD5:466D35E6A22924DD846A043BC7DD94B8 | SHA256:E4CCF06706E68621BB69ADD3DD88FED82D30AD8778A55907D33F6D093AC16801 | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\MSLWVTTS.DLL | executable | |
MD5:316999655FEF30C52C3854751C663996 | SHA256:EA4CA740CD60D2C88280FF8115BF354876478EF27E9E676D8B66601B4E900BA0 | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGTEULA.TXT | text | |
MD5:7070B77ED401307D2E9A0F8EAAAA543B | SHA256:225D227ABBD45BF54D01DFC9FA6E54208BF5AE452A32CC75B15D86456A669712 | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTSR.DLL | executable | |
MD5:9FAFB9D0591F2BE4C2A846F63D82D301 | SHA256:E78E74C24D468284639FAF9DCFDBA855F3E4F00B2F26DB6B2C491FA51DA8916D | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ADVPACK.DLL | executable | |
MD5:81E5C8596A7E4E98117F5C5143293020 | SHA256:7D126ED85DF9705EC4F38BD52A73B621CF64DD87A3E8F9429A569F3F82F74004 | |||
| 2572 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGTINST.INF | binary | |
MD5:B127D9187C6DBB1B948053C7C9A6811F | SHA256:BD1295D19D010D4866C9D6D87877913EEE69E279D4D089E5756BA285F3424E00 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
34
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
2820 | msedge.exe | 20.189.173.21:443 | nw-umwatson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3080 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2896 | dplaysvr.exe | 192.168.100.2:1900 | — | — | — | whitelisted |
3080 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nw-umwatson.events.data.microsoft.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
watson.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|