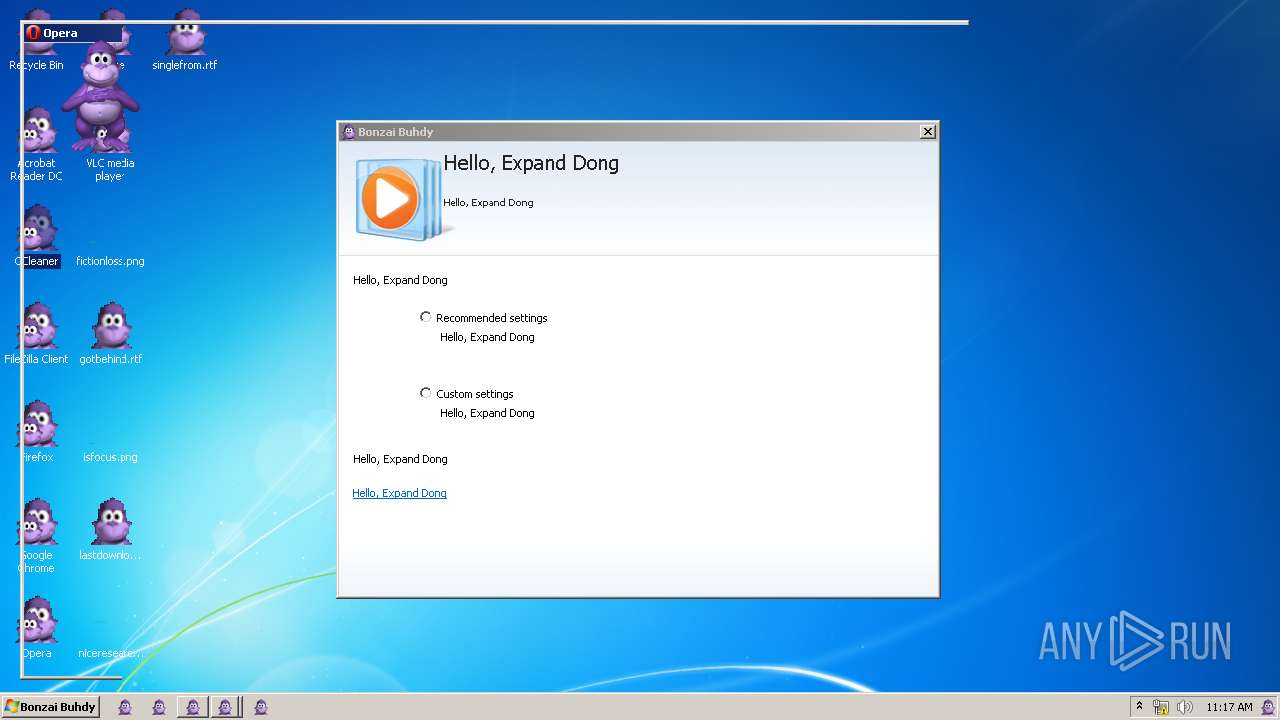
| File name: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/497ee480-ed1d-4ab7-b17f-9c04516ea270 |
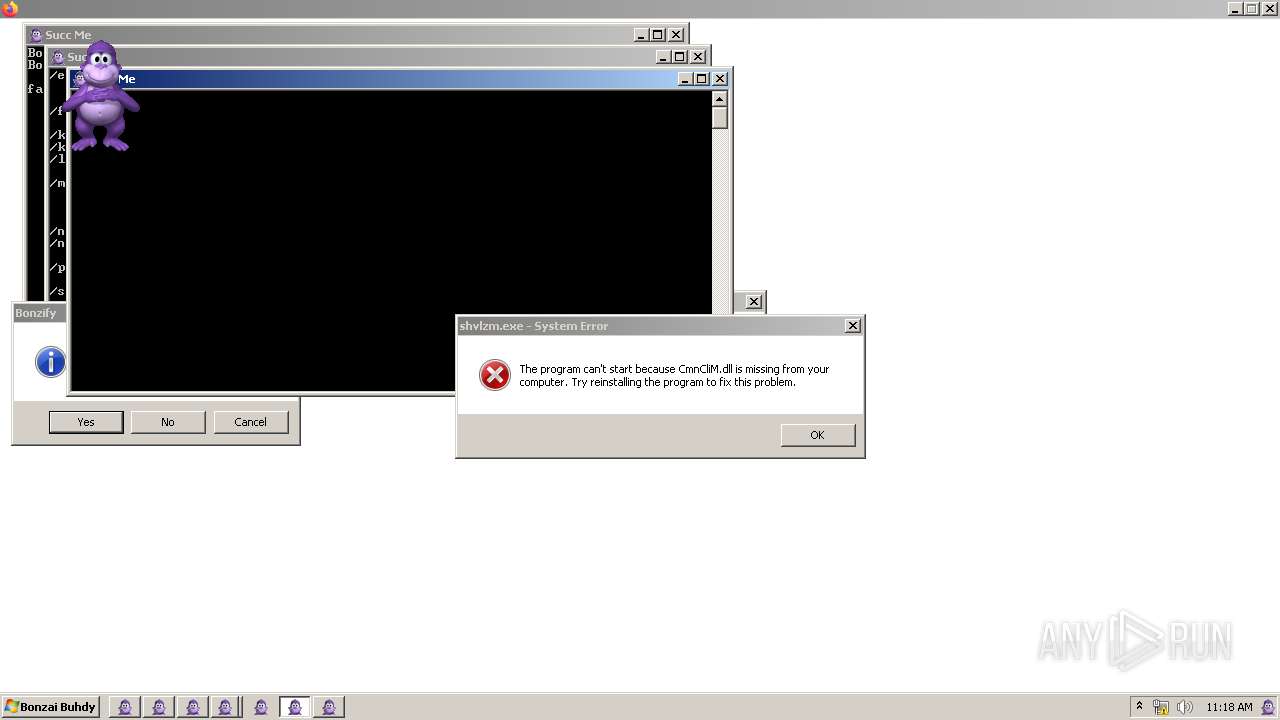
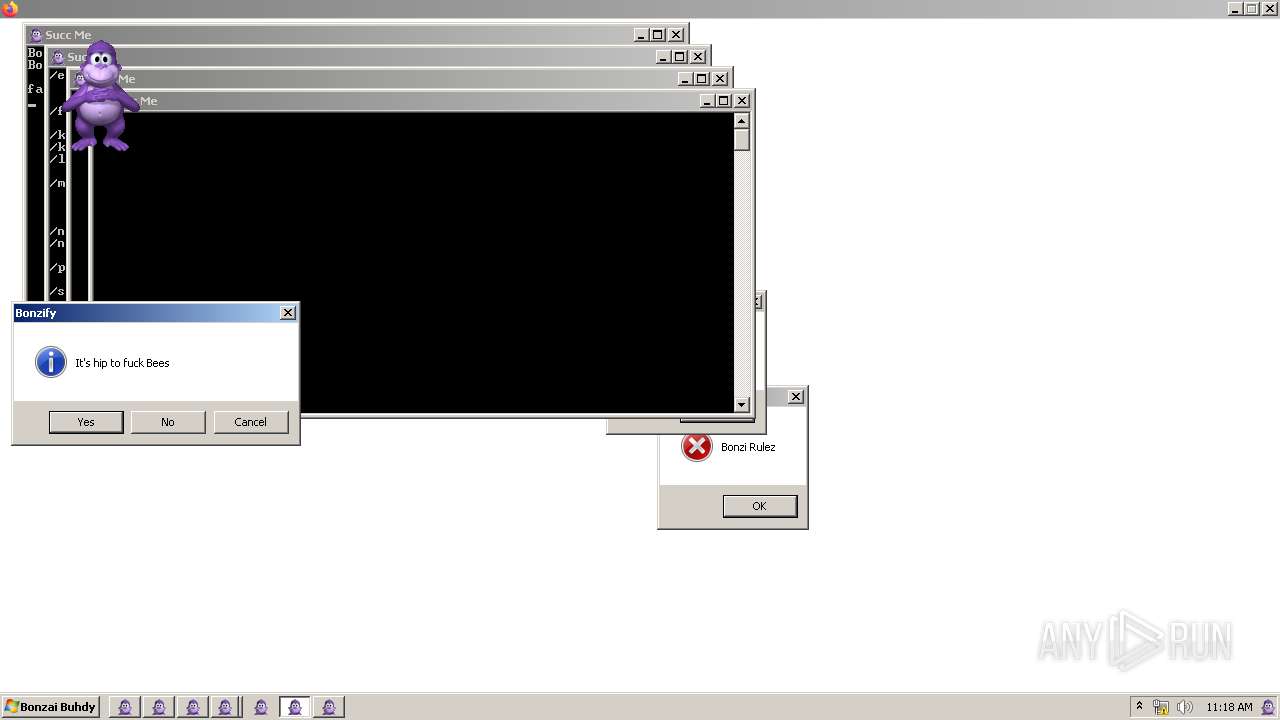
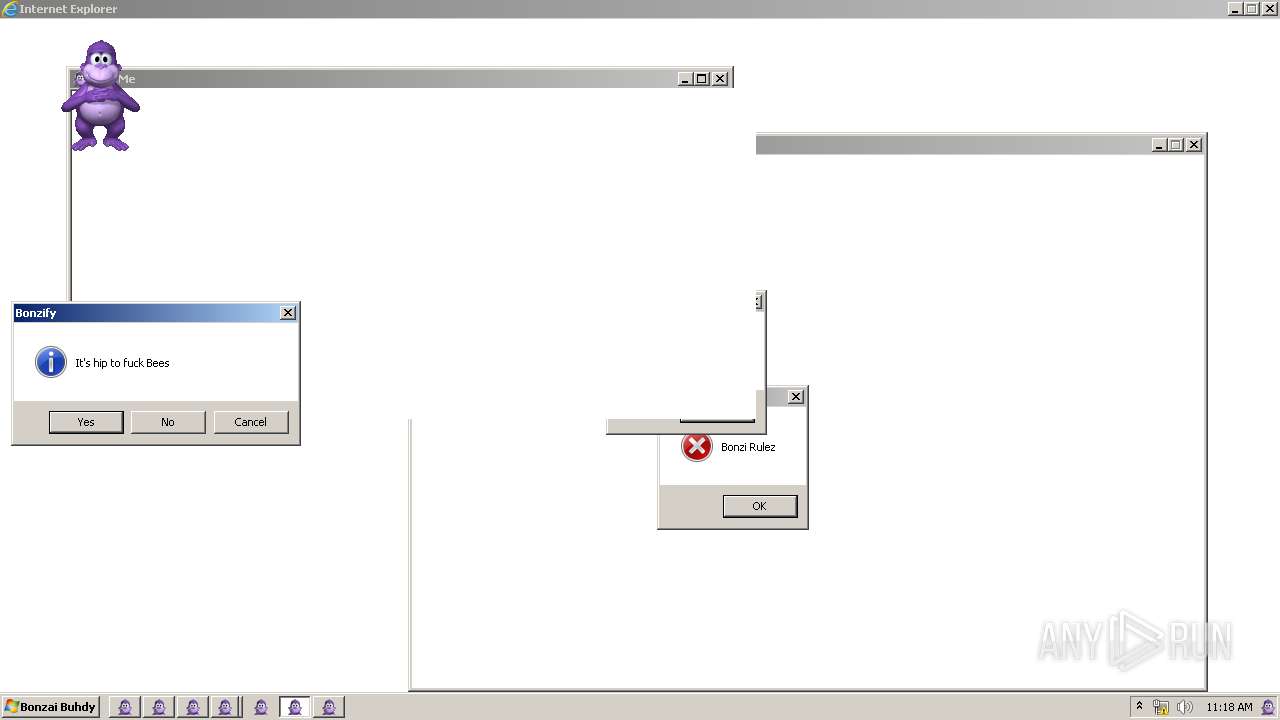
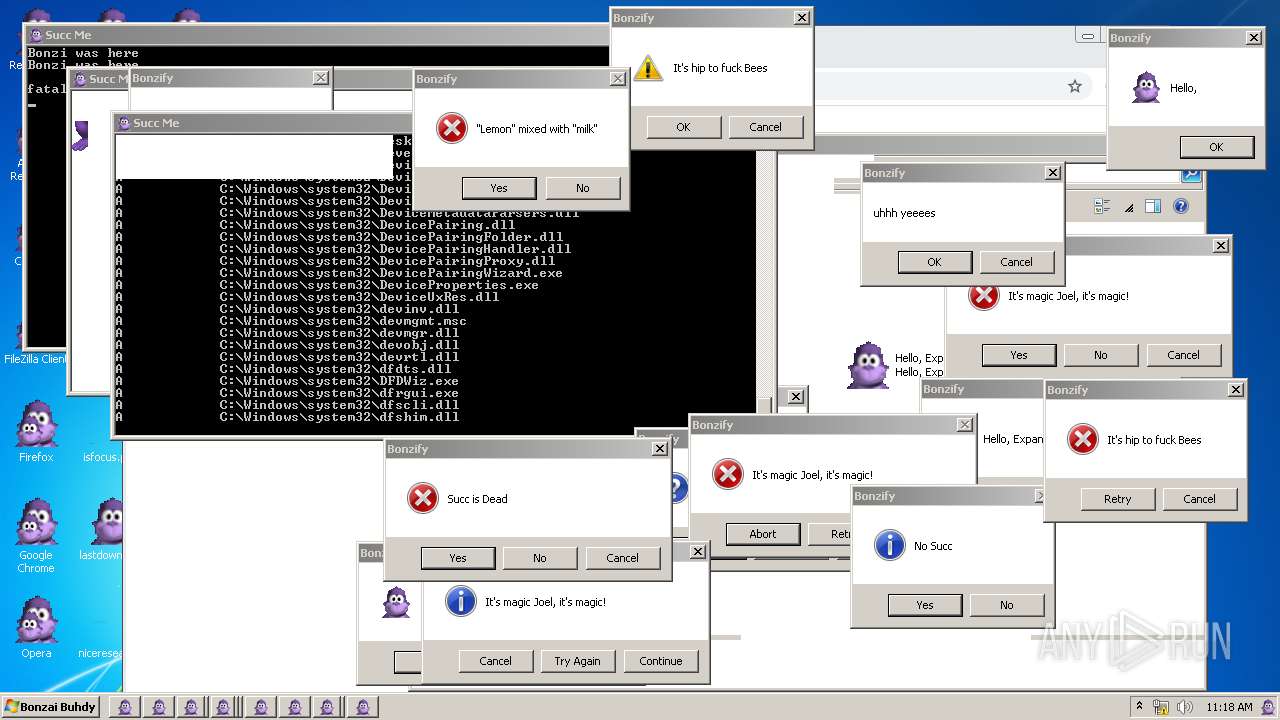
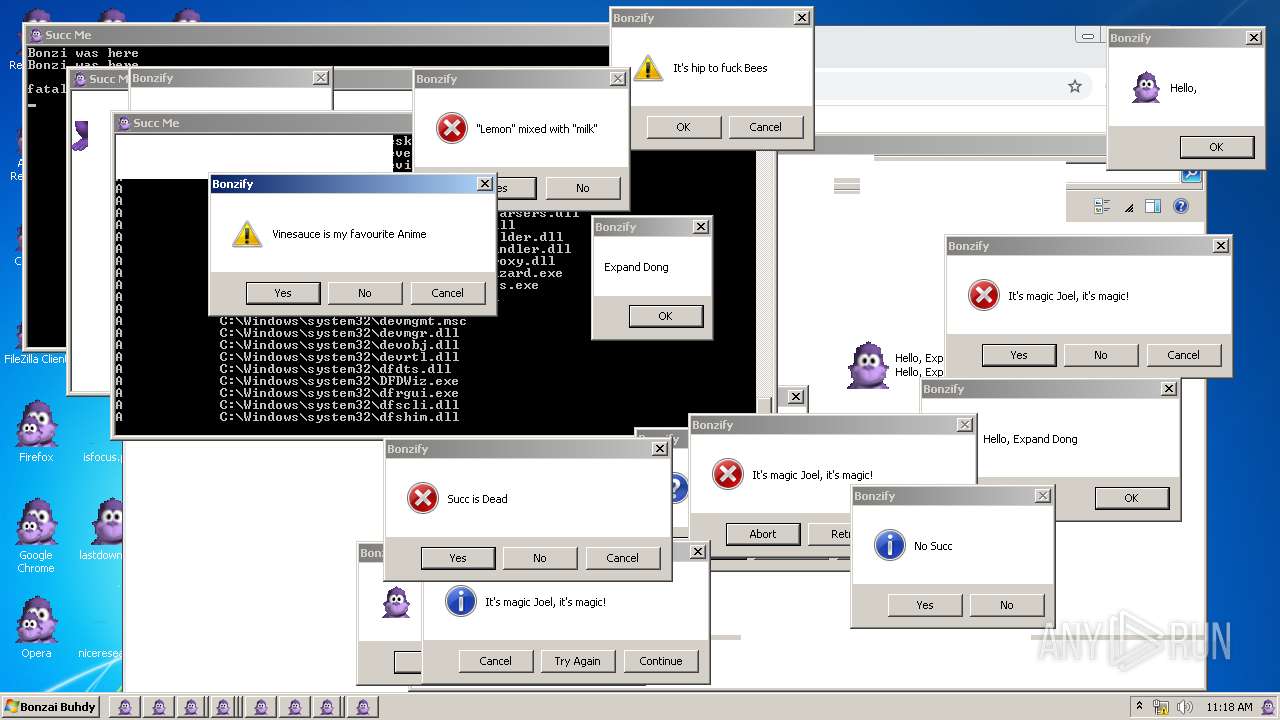
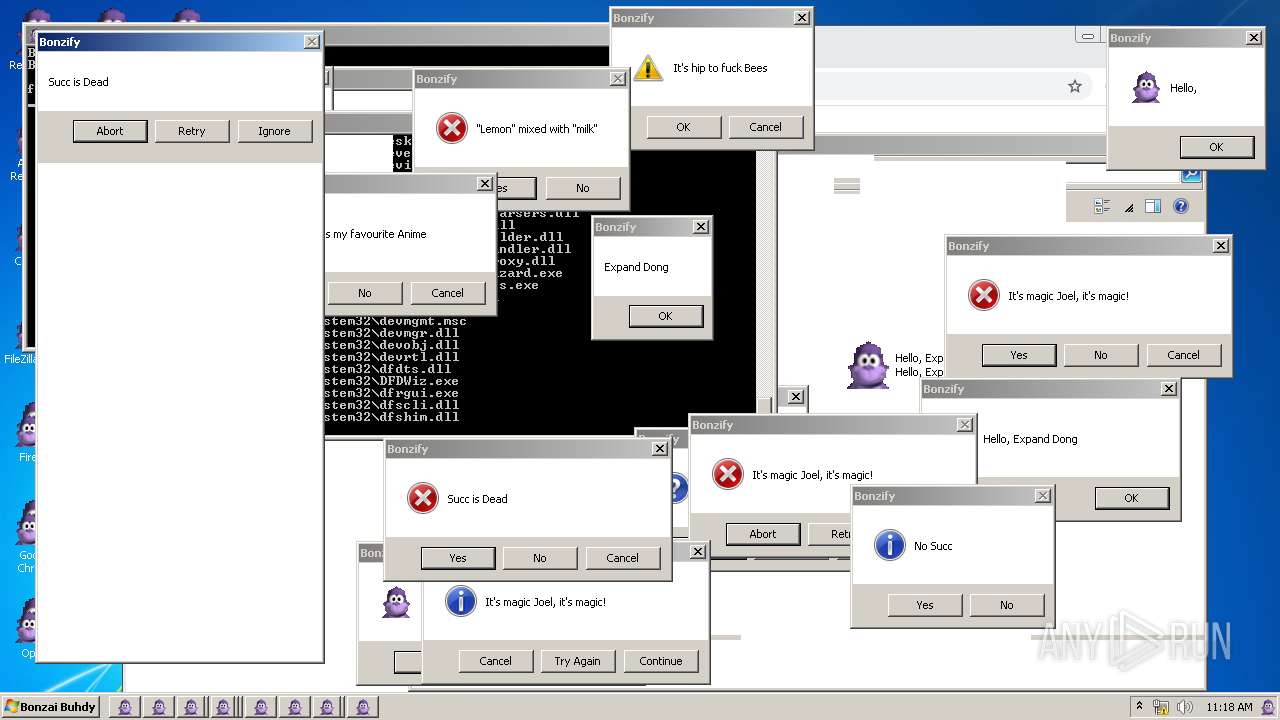
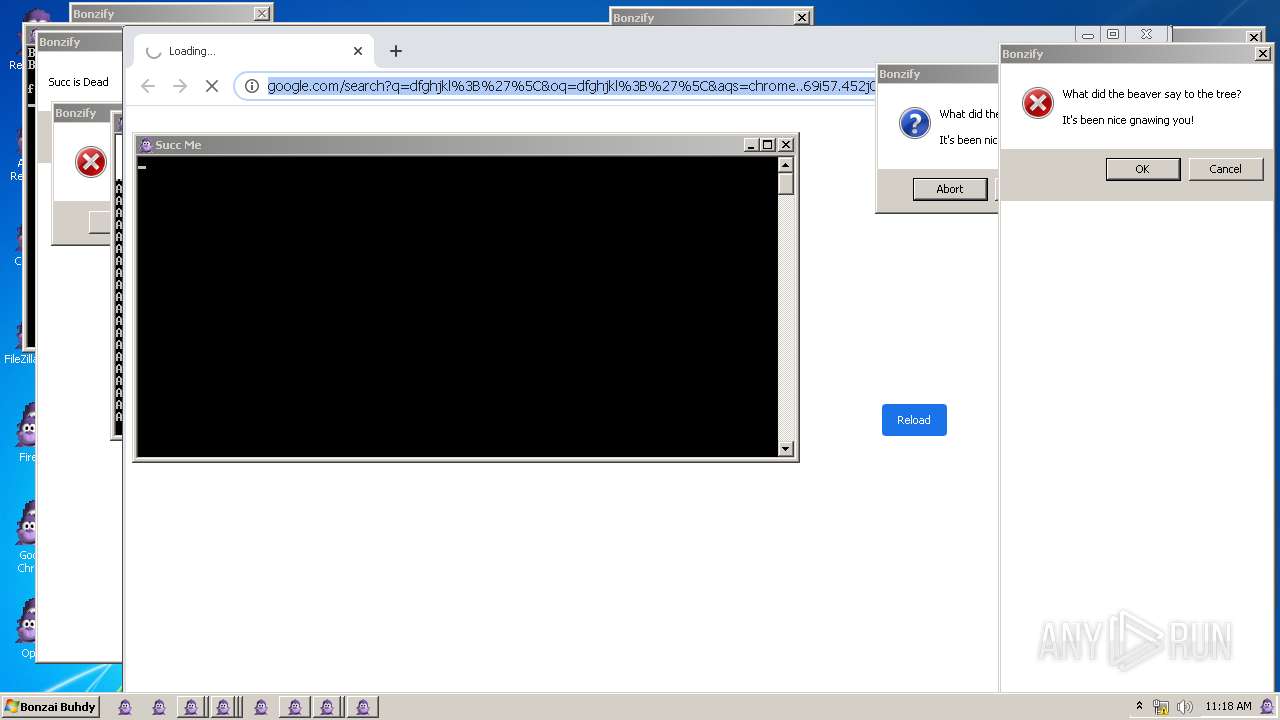
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2023, 10:16:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9C352D2CE0C0BDC40C72F52CE3480577 |
| SHA1: | BD4C956186F33C92EB4469F7E5675510D0790E99 |
| SHA256: | D7E6580054525D3F21F86EDFC9F30B7A75FFA829A1EB67EE3CAB33F0040DBA4E |
| SSDEEP: | 196608:/dAMaWetTeAkLIdx751qFTkub//73lc6u7b5VJ2Yx5xIdk3:naWedh+Idx75QYub//73lc6u7bLMYxD |
MALICIOUS
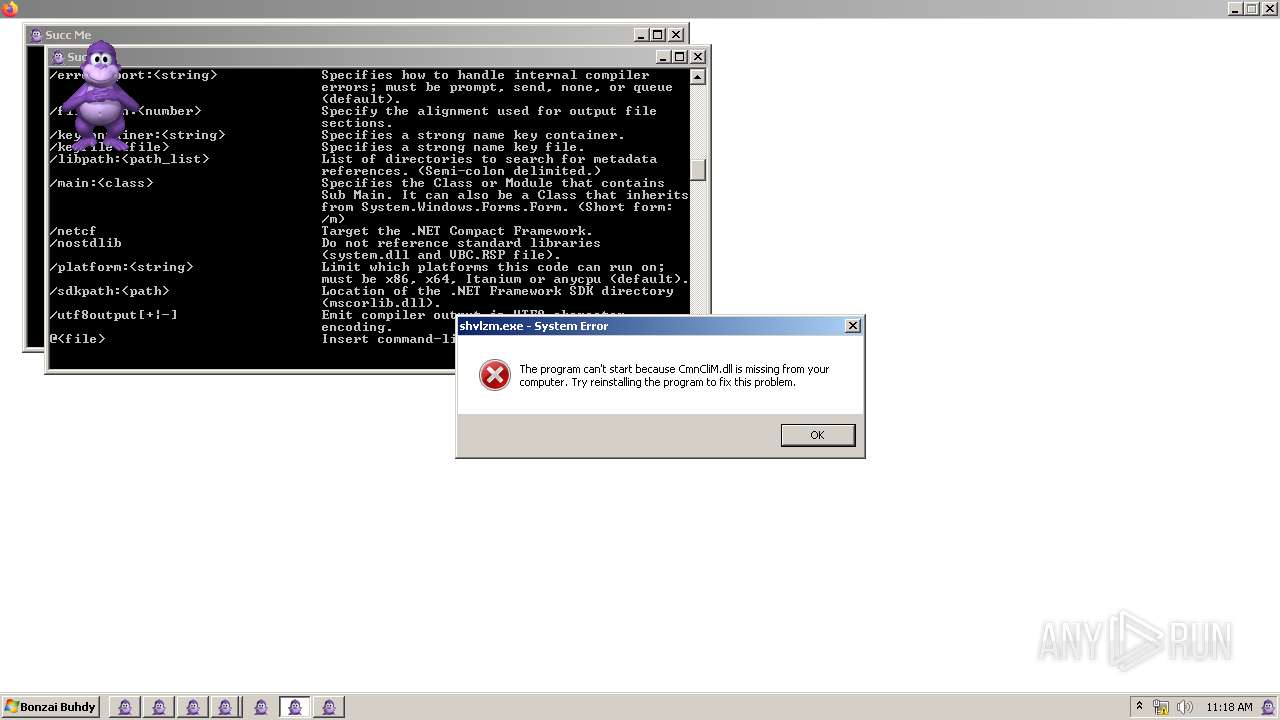
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 1276)
- INSTALLER.exe (PID: 2600)
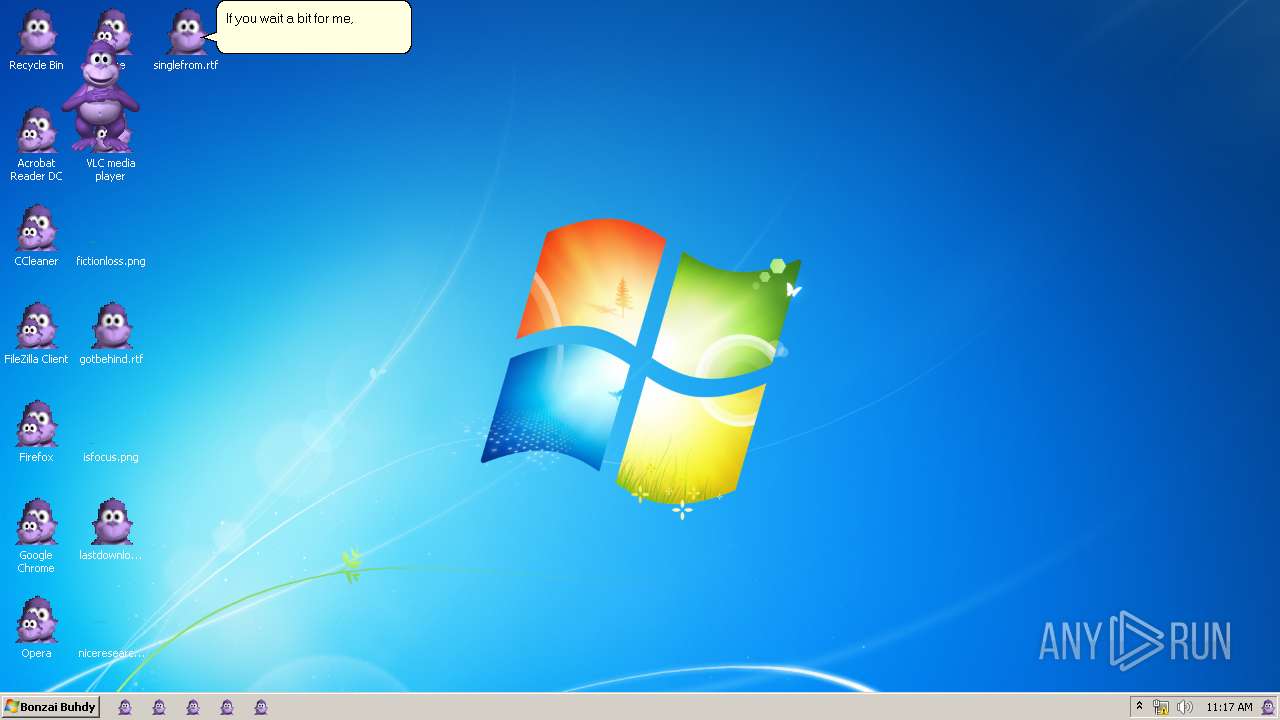
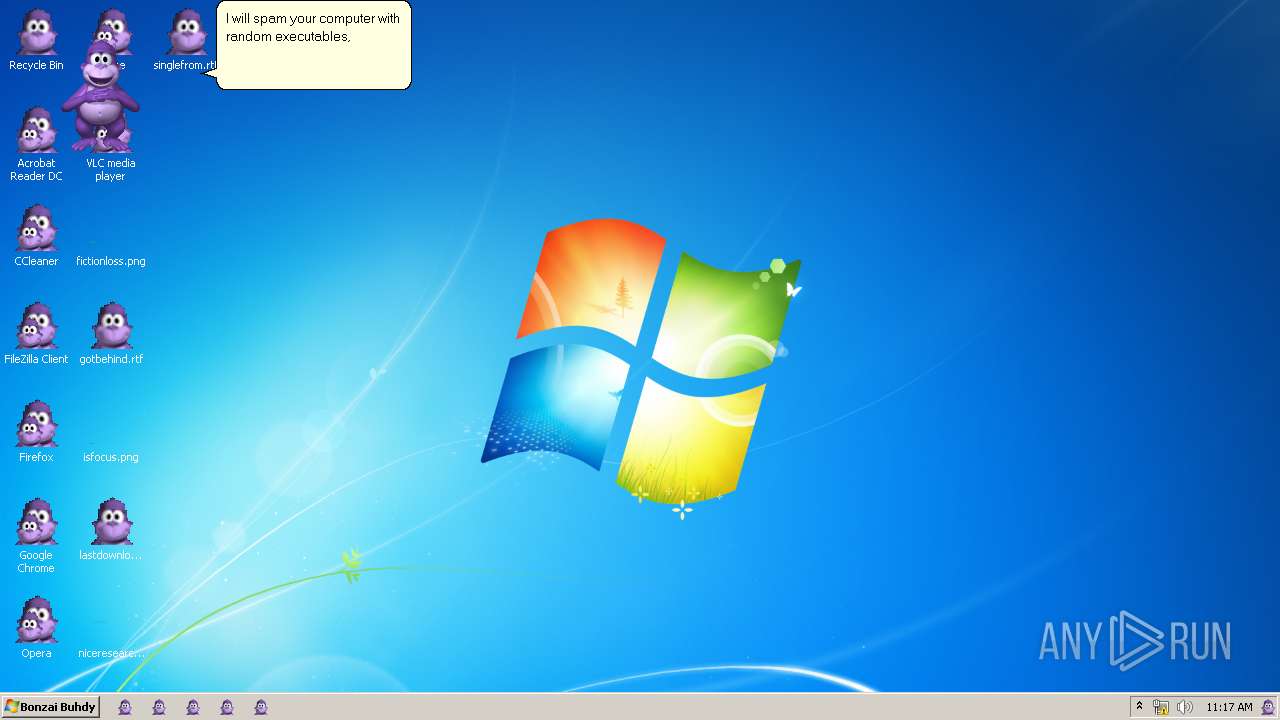
Application was dropped or rewritten from another process
- INSTALLER.exe (PID: 1276)
- INSTALLER.exe (PID: 2600)
- AgentSvr.exe (PID: 3508)
- AgentSvr.exe (PID: 2280)
Creates a writable file the system directory
- INSTALLER.exe (PID: 2600)
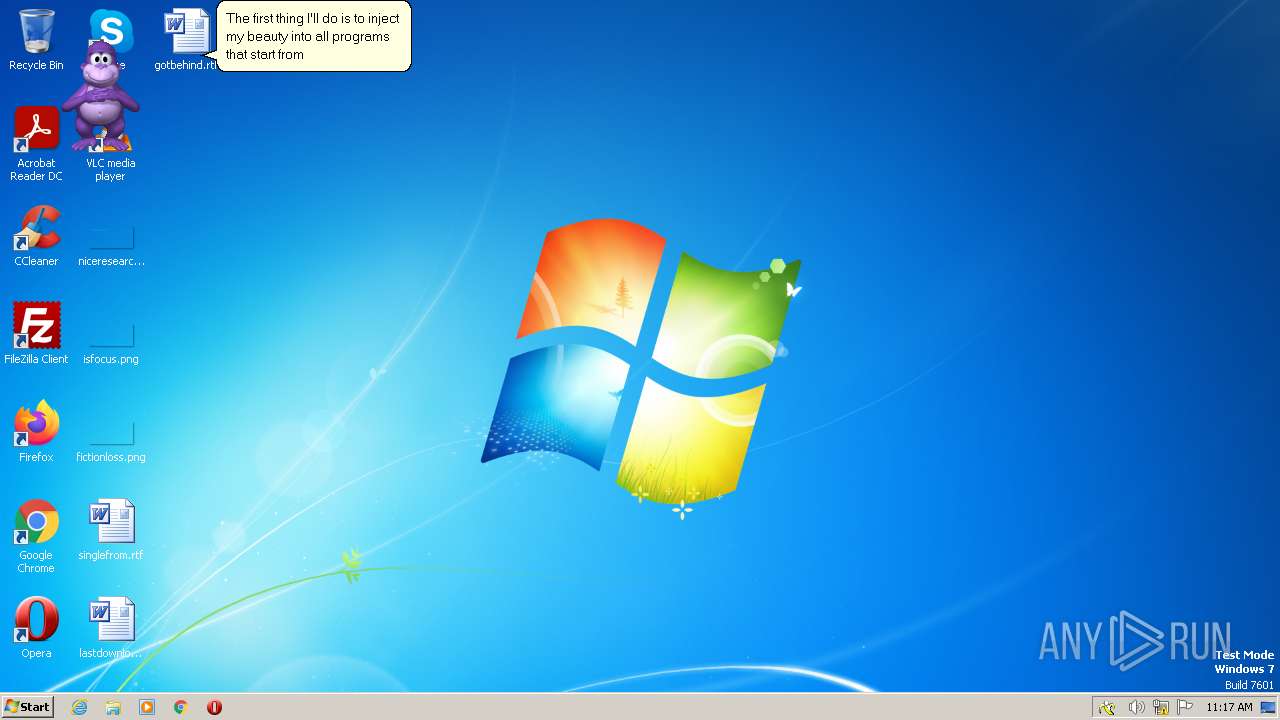
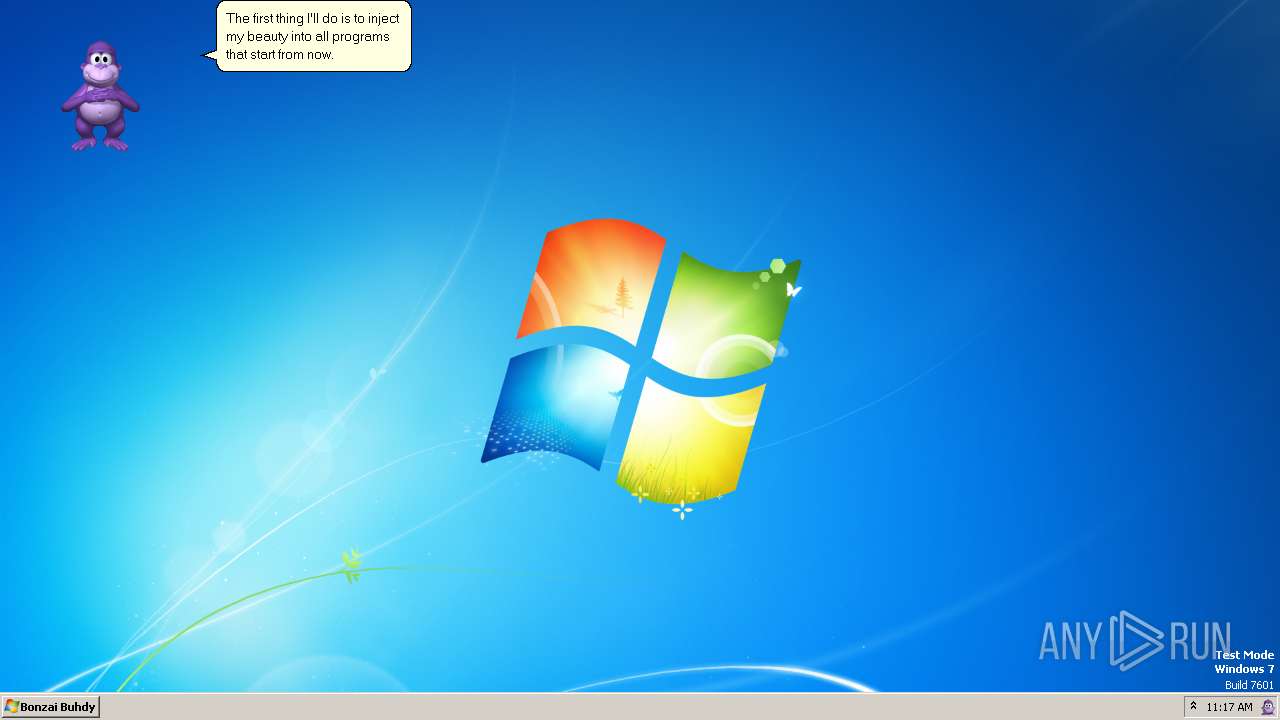
Changes the AppInit_DLLs value (autorun option)
- Bonzify.exe (PID: 2748)
SUSPICIOUS
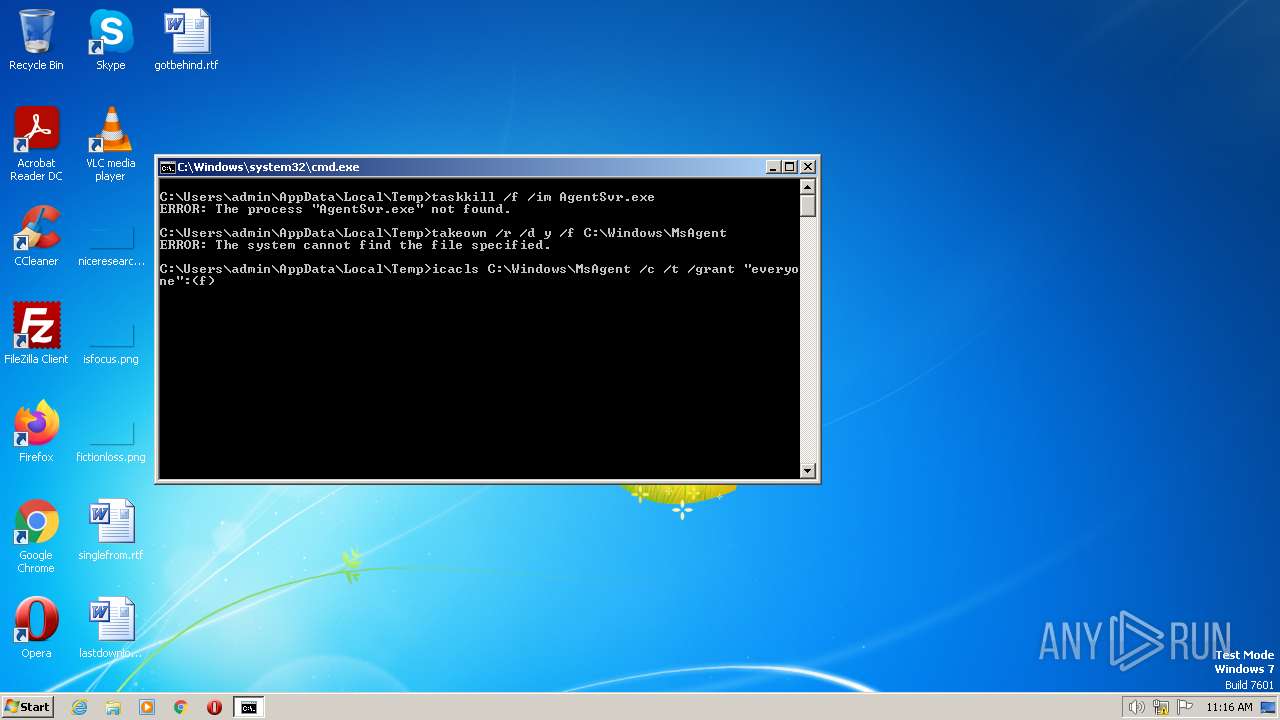
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2912)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2912)
Starts CMD.EXE for commands execution
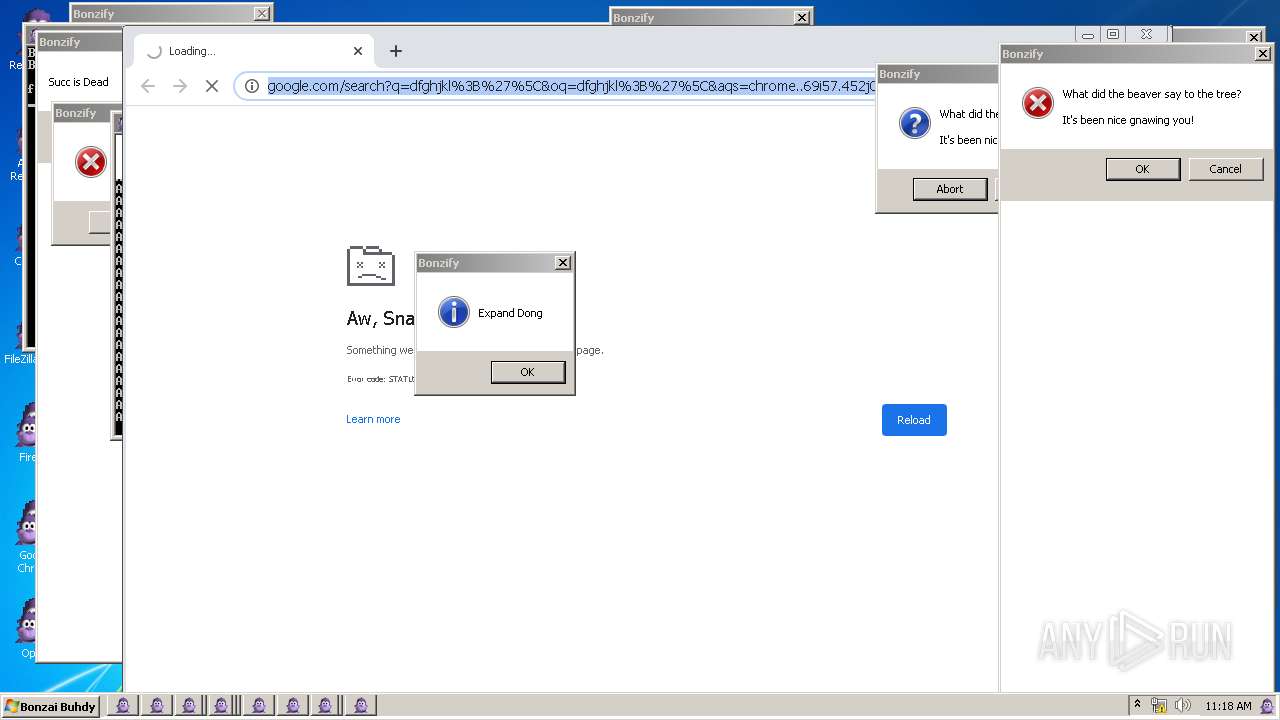
- Bonzify.exe (PID: 2748)
Executing commands from a ".bat" file
- Bonzify.exe (PID: 2748)
Executable content was dropped or overwritten
- INSTALLER.exe (PID: 1276)
- INSTALLER.exe (PID: 2600)
- Bonzify.exe (PID: 2748)
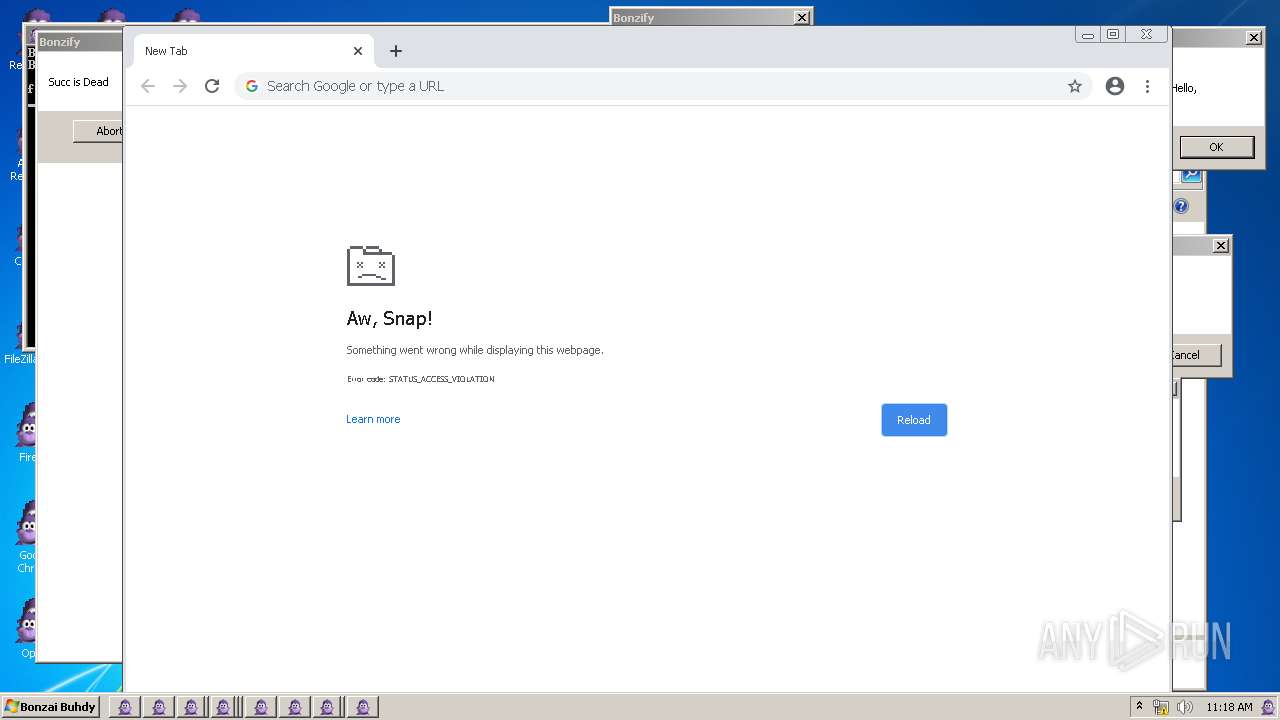
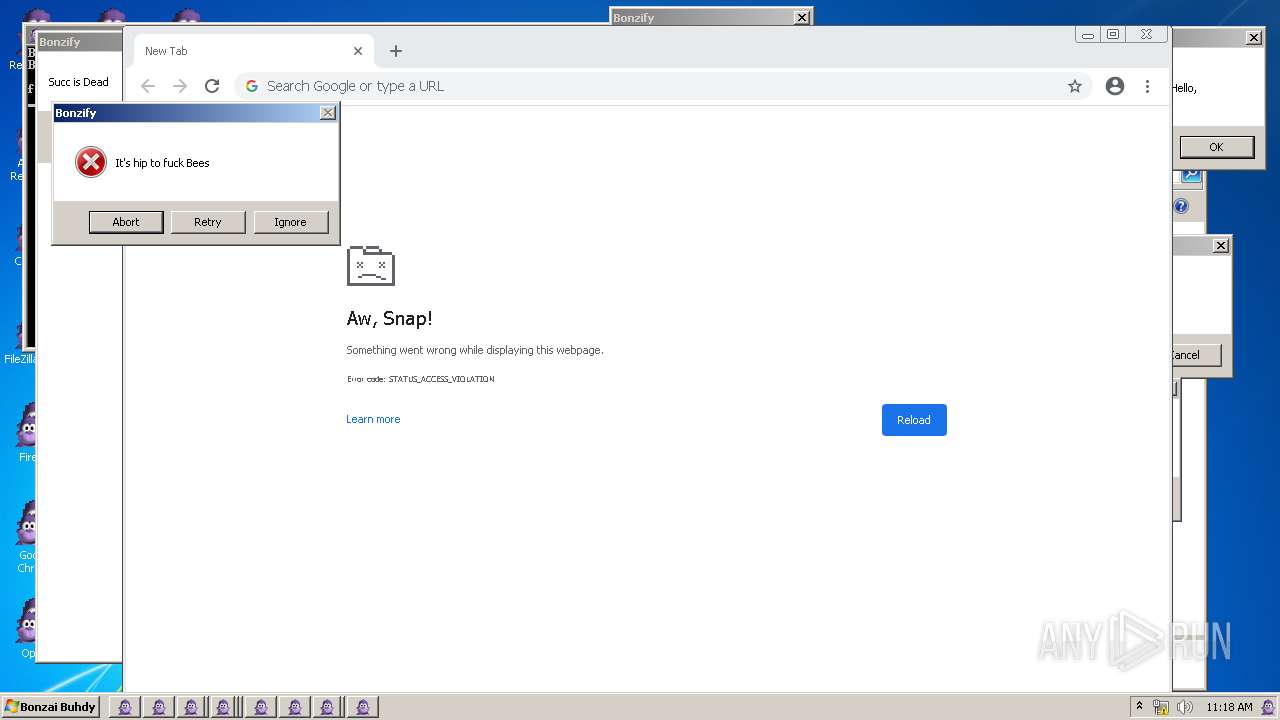
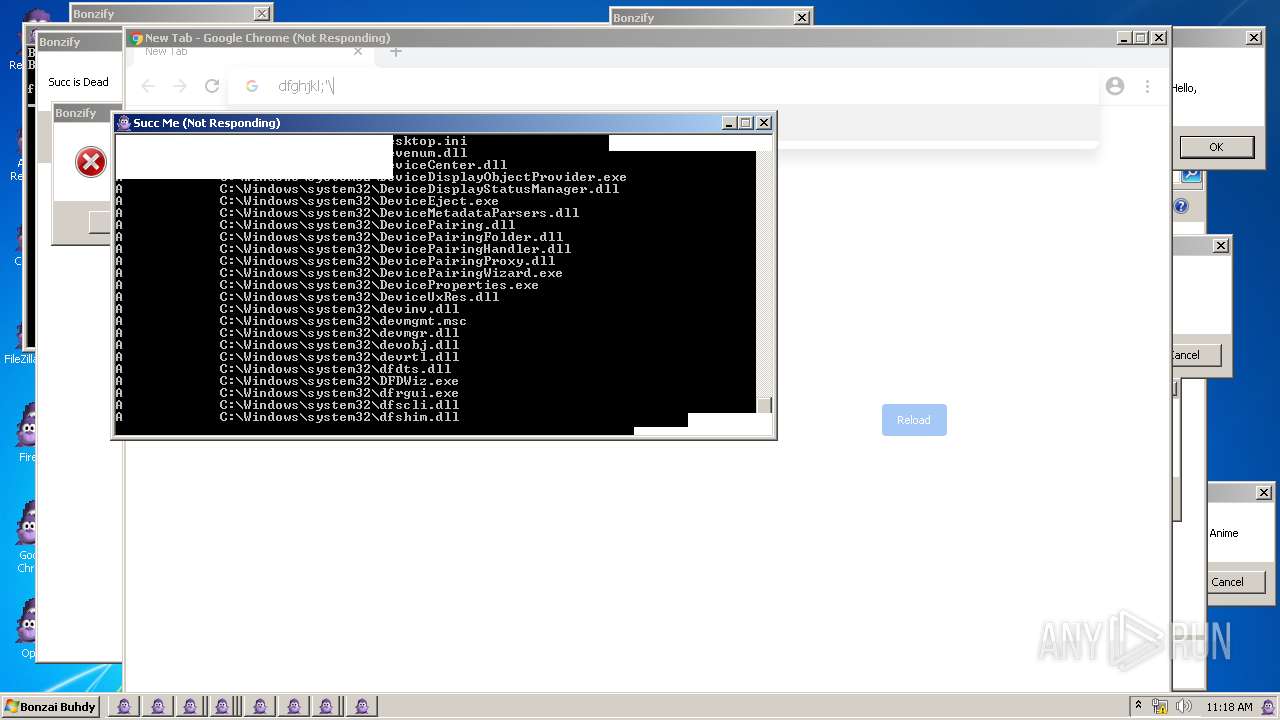
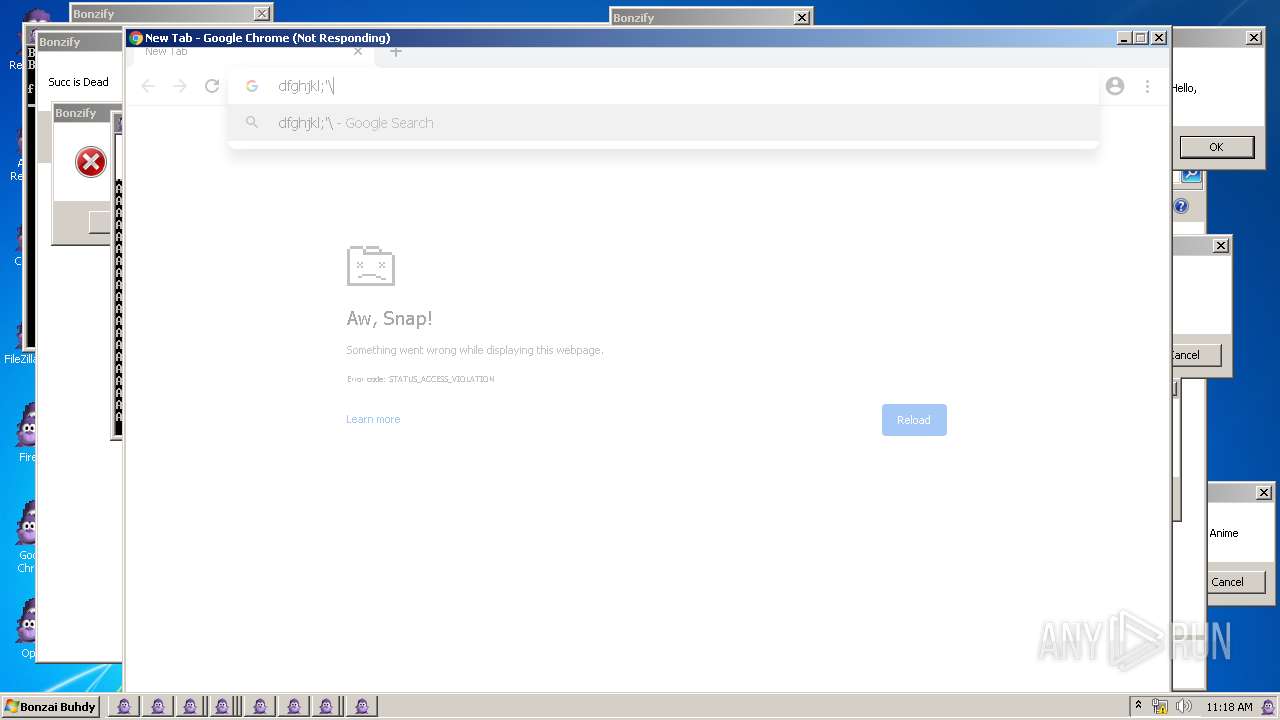
Executes application which crashes
- svchost.exe (PID: 3492)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2060)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 1824)
- Bonzify.exe (PID: 2748)
- AgentSvr.exe (PID: 2280)
- INSTALLER.exe (PID: 2600)
- AgentSvr.exe (PID: 3508)
- INSTALLER.exe (PID: 1276)
The process checks LSA protection
- wmpnscfg.exe (PID: 1824)
- taskkill.exe (PID: 2788)
- Bonzify.exe (PID: 2748)
- AgentSvr.exe (PID: 3508)
- explorer.exe (PID: 4012)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1824)
- Bonzify.exe (PID: 2748)
- AgentSvr.exe (PID: 3508)
Reads the computer name
- wmpnscfg.exe (PID: 1824)
- INSTALLER.exe (PID: 1276)
- INSTALLER.exe (PID: 2600)
- AgentSvr.exe (PID: 3508)
- Bonzify.exe (PID: 2748)
Create files in a temporary directory
- INSTALLER.exe (PID: 1276)
- Bonzify.exe (PID: 2748)
- INSTALLER.exe (PID: 2600)
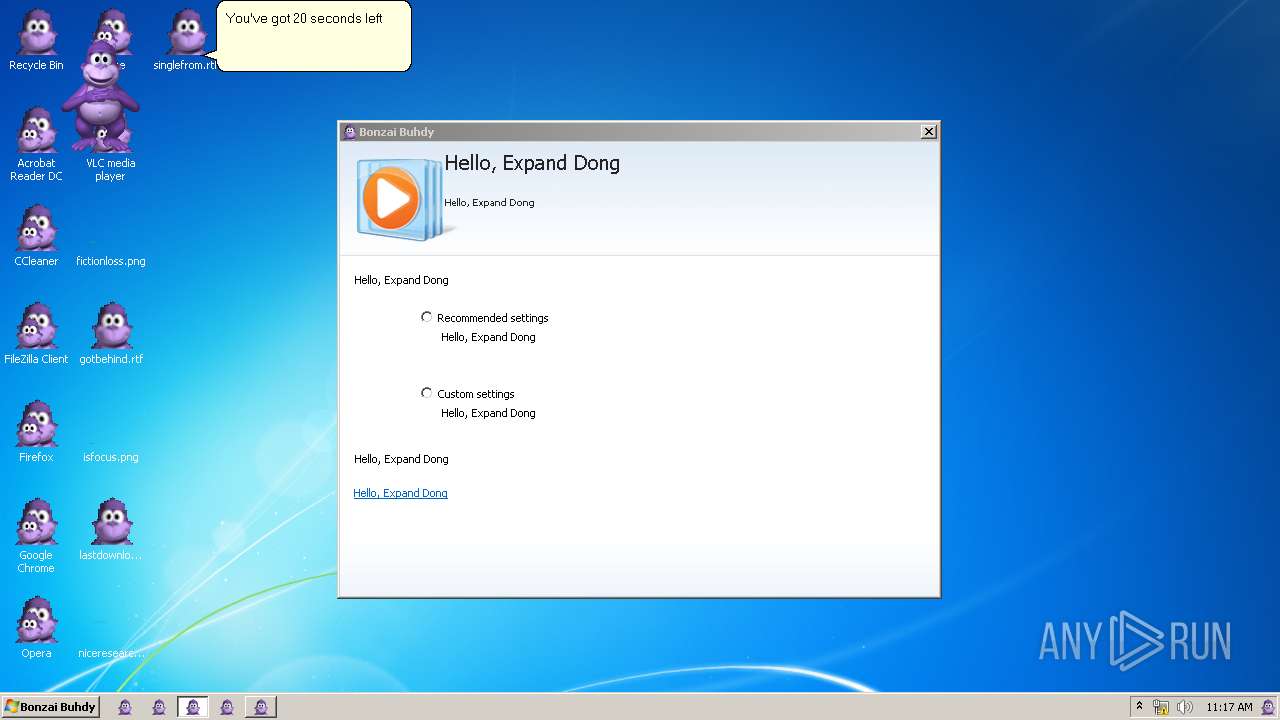
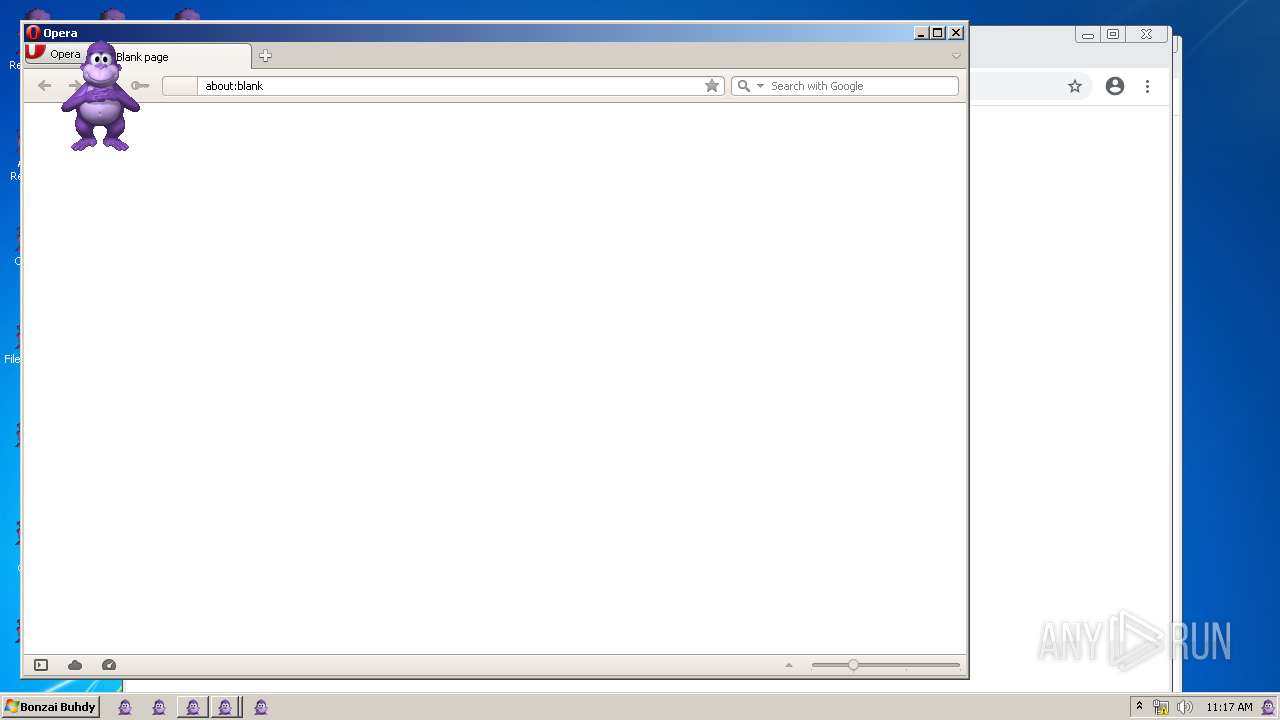
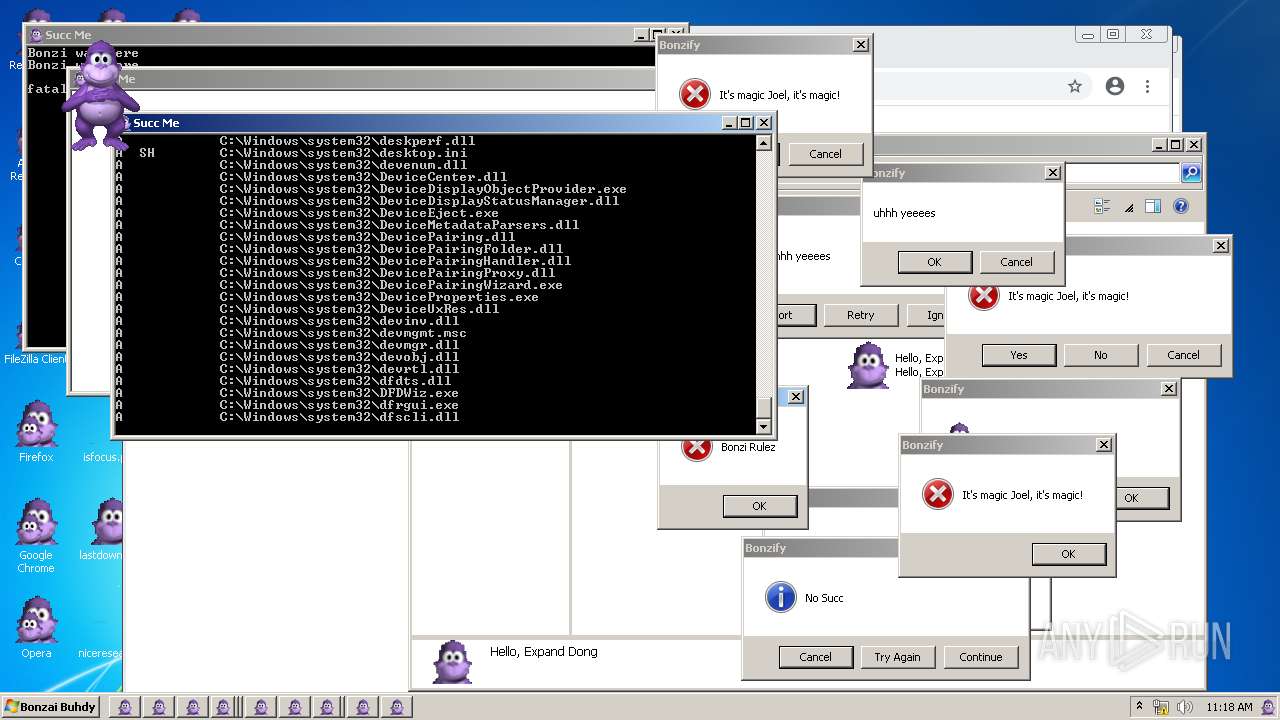
Manual execution by a user
- wmpnscfg.exe (PID: 1592)
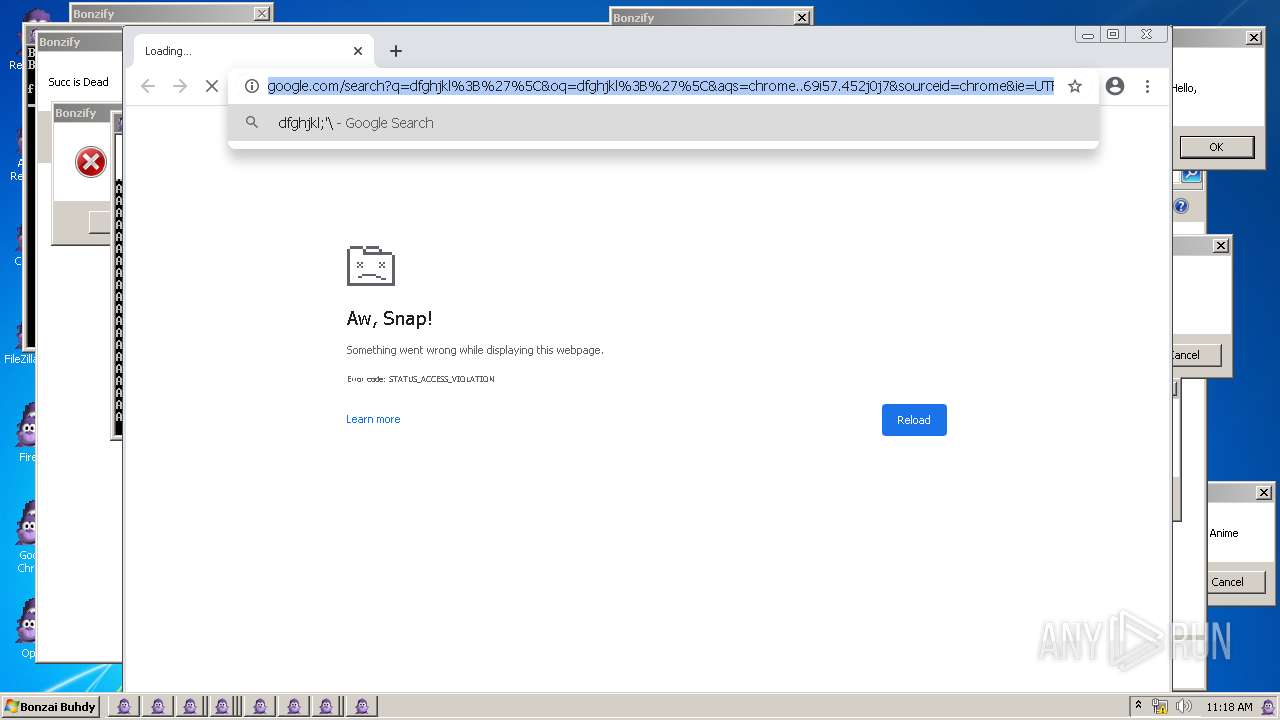
- chrome.exe (PID: 268)
- wmplayer.exe (PID: 3988)
- WINWORD.EXE (PID: 1368)
- chrome.exe (PID: 1352)
- opera.exe (PID: 1300)
- explorer.exe (PID: 3552)
- firefox.exe (PID: 4044)
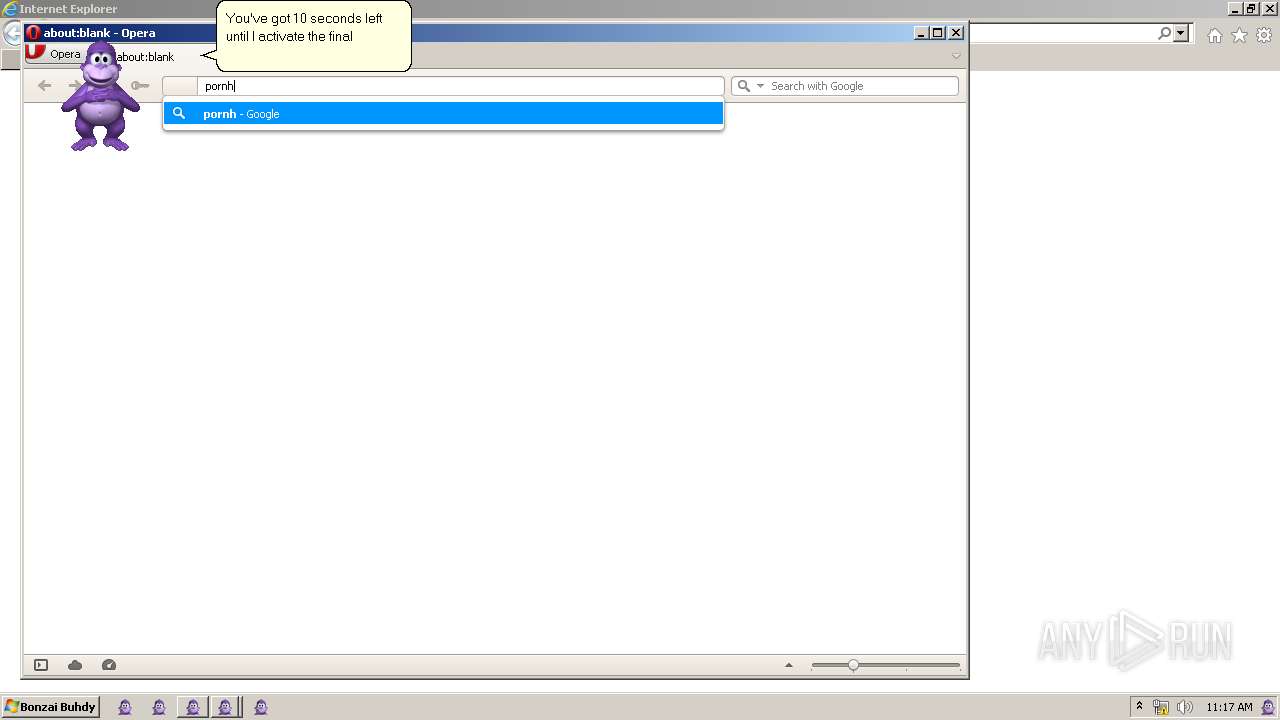
- iexplore.exe (PID: 3852)
- filezilla.exe (PID: 1944)
- CCleaner.exe (PID: 3824)
- wmpnscfg.exe (PID: 2800)
Application launched itself
- chrome.exe (PID: 268)
- chrome.exe (PID: 1352)
- firefox.exe (PID: 4044)
- iexplore.exe (PID: 3852)
- firefox.exe (PID: 1420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (86.7) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.8) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Generic Win/DOS Executable (0.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x16b0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 6697472 |
| CodeSize: | 4096 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2019:03:04 14:58:11+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Mar-2019 14:58:11 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Mar-2019 14:58:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000F88 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.51622 |
.rdata | 0x00002000 | 0x0000109C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13419 |
.data | 0x00004000 | 0x00000020 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00005000 | 0x00661BD8 | 0x00661C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.84962 |
.reloc | 0x00667000 | 0x000001C4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.08408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.01704 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
100 | 7.82633 | 5249795 | UNKNOWN | UNKNOWN | DATA |
101 | 7.78087 | 400536 | UNKNOWN | UNKNOWN | DATA |
102 | 7.93147 | 1021232 | UNKNOWN | UNKNOWN | DATA |
103 | 4.90328 | 161 | UNKNOWN | UNKNOWN | DATA |
104 | 4.49923 | 46 | UNKNOWN | UNKNOWN | DATA |
110 | 5.36458 | 15360 | UNKNOWN | UNKNOWN | DATA |
IDI_BONZI | 2.32824 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
94
Monitored processes
53
Malicious processes
5
Suspicious processes
0
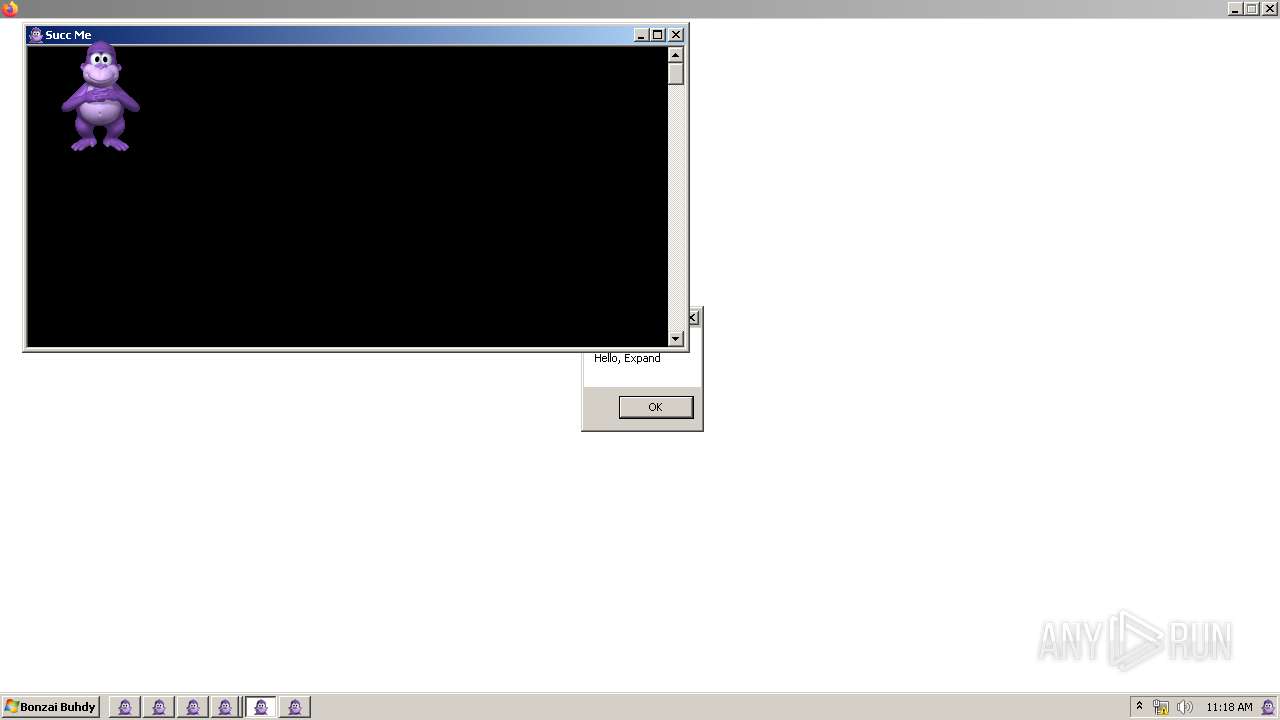
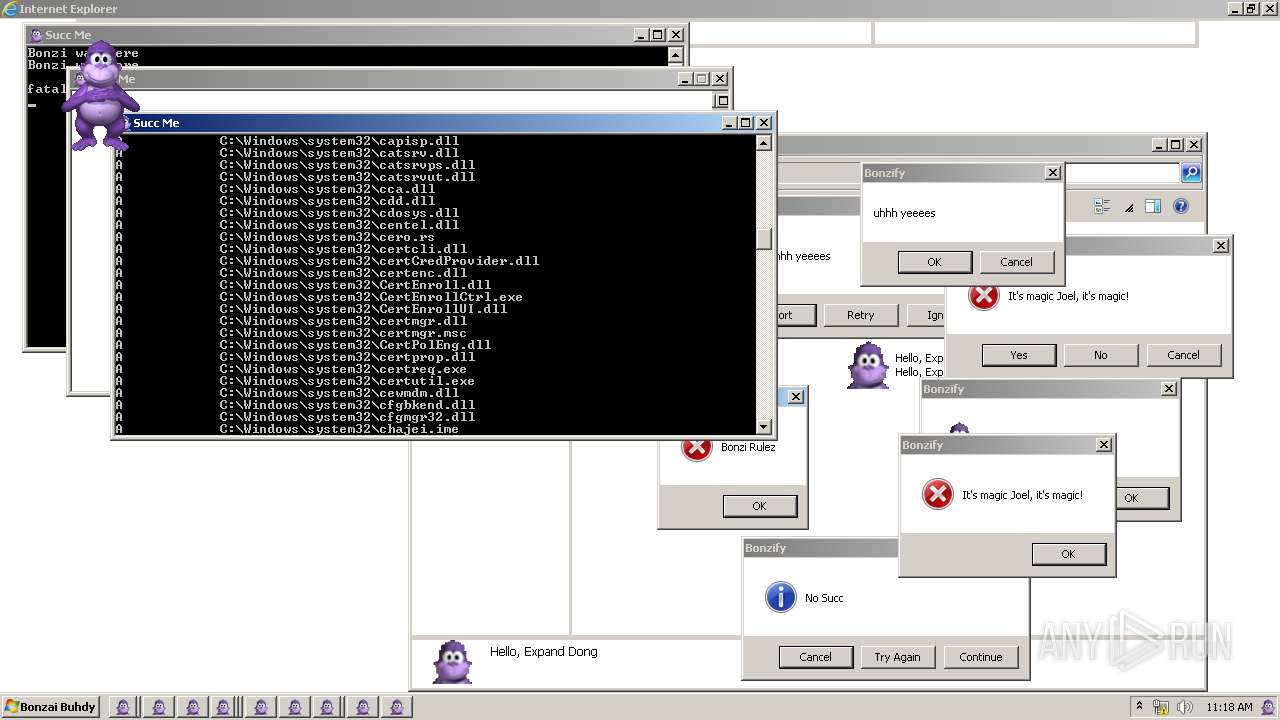
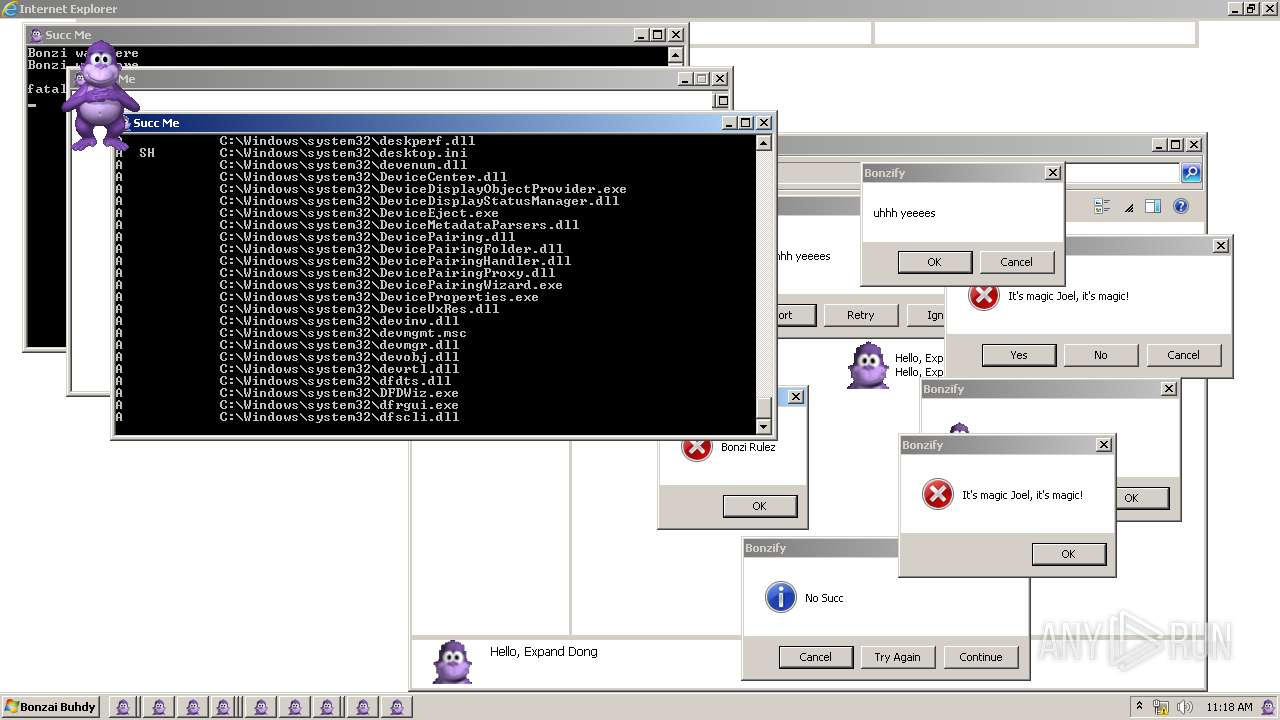
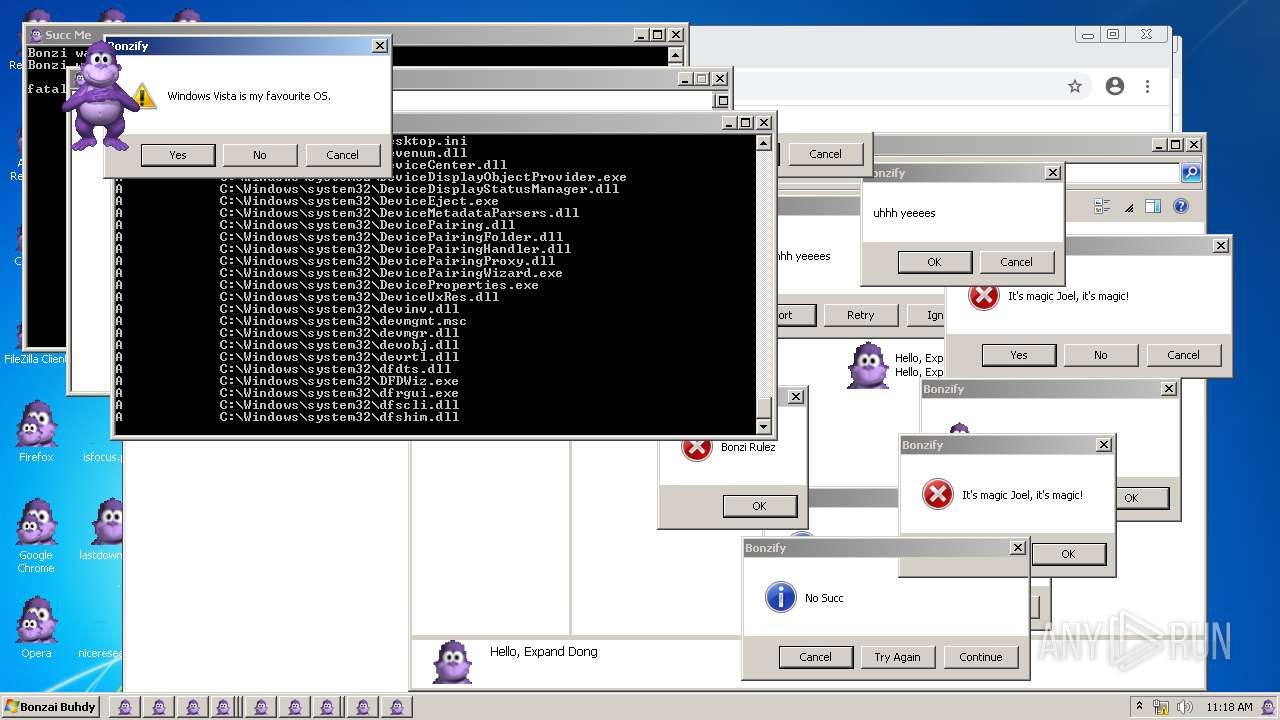
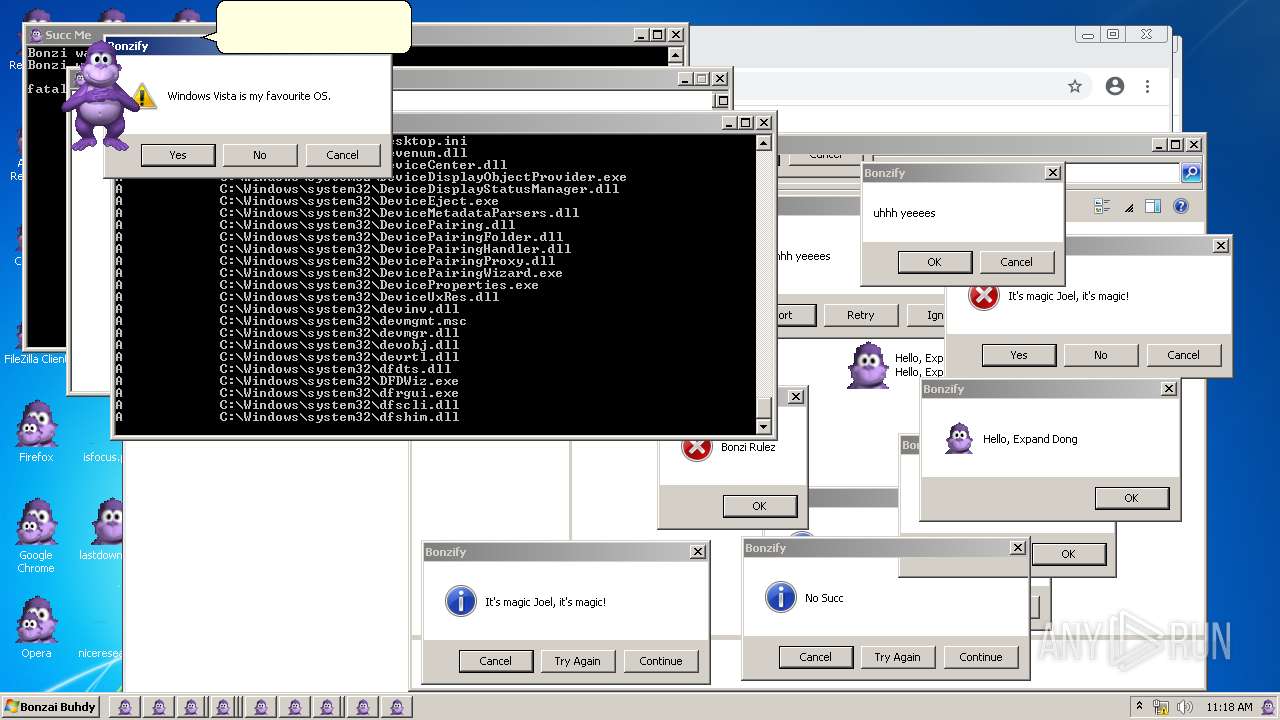
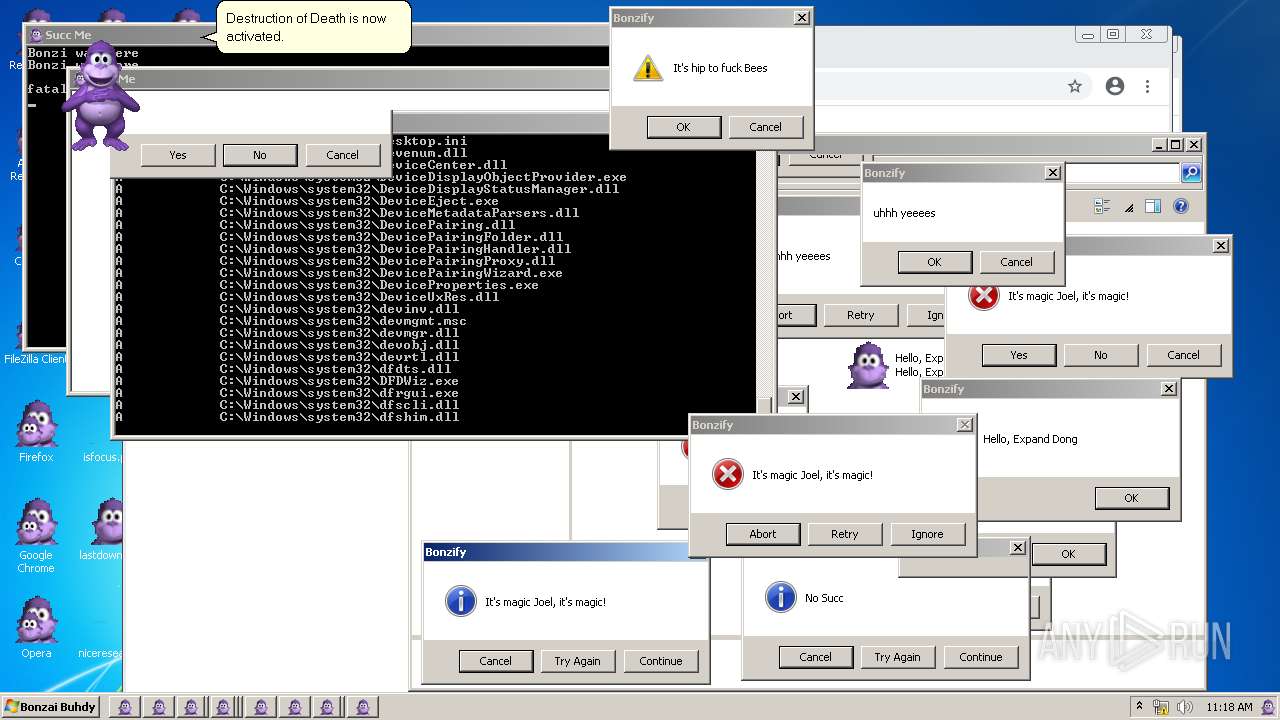
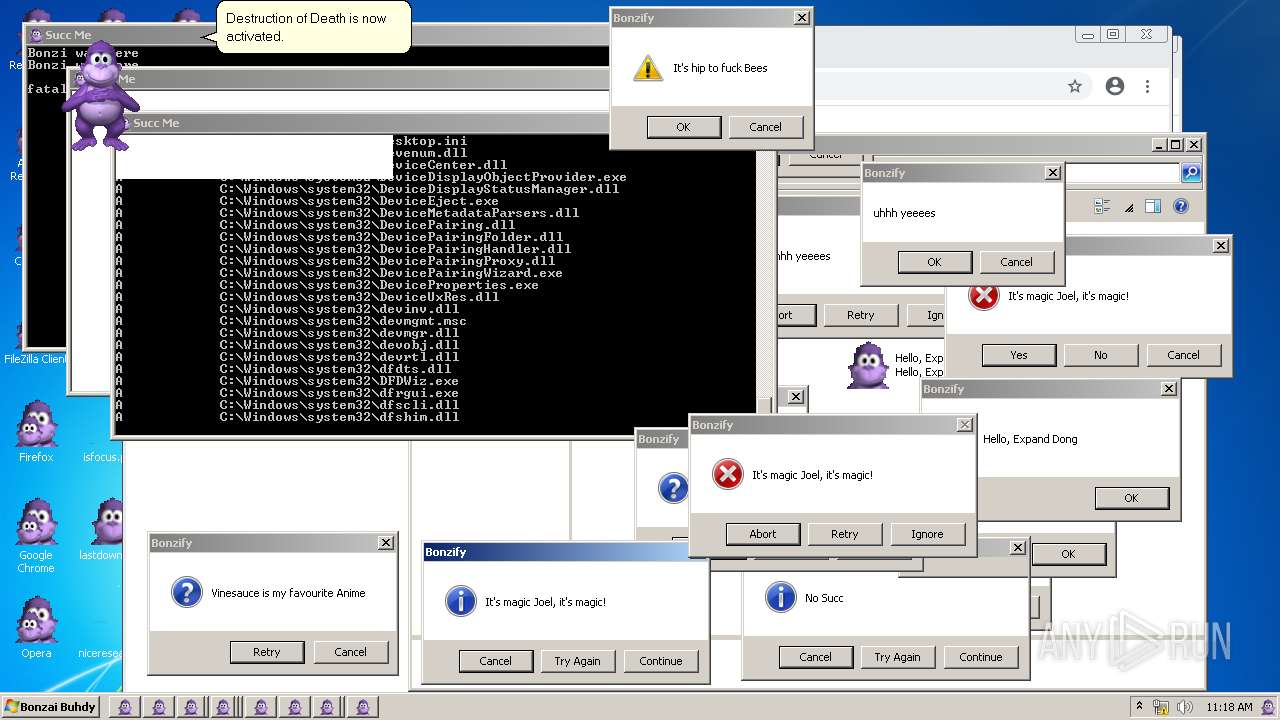
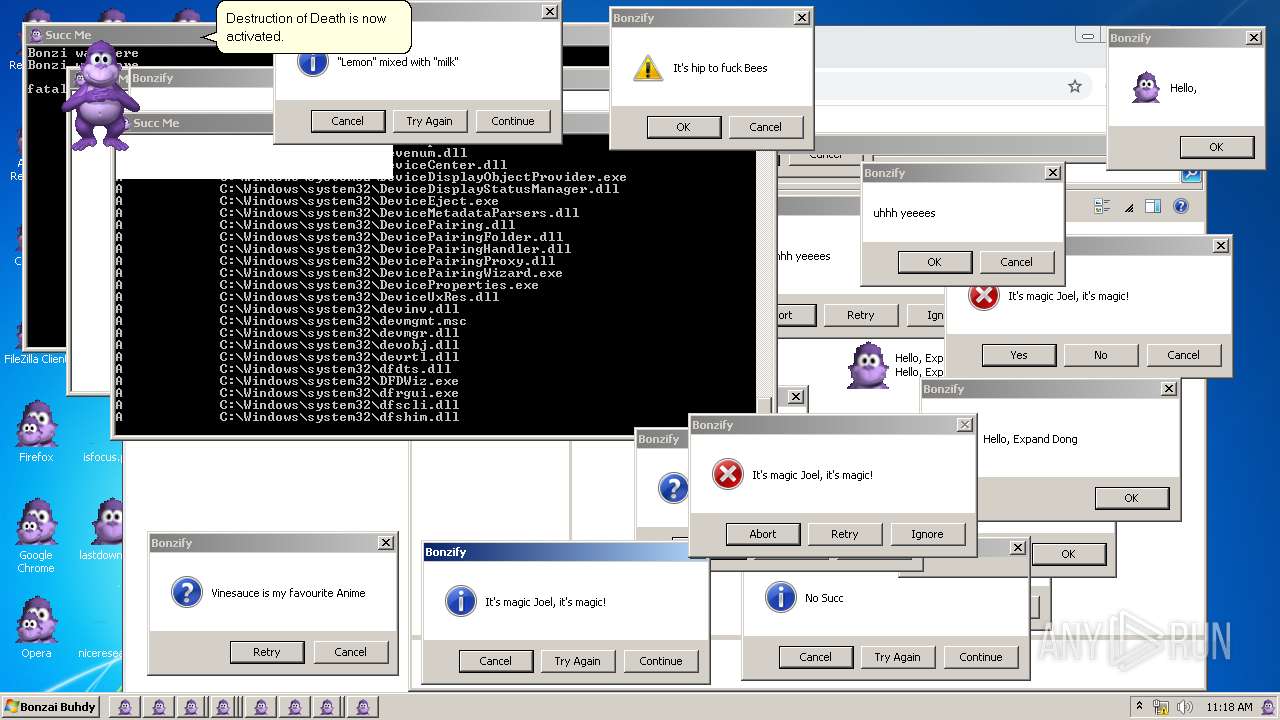
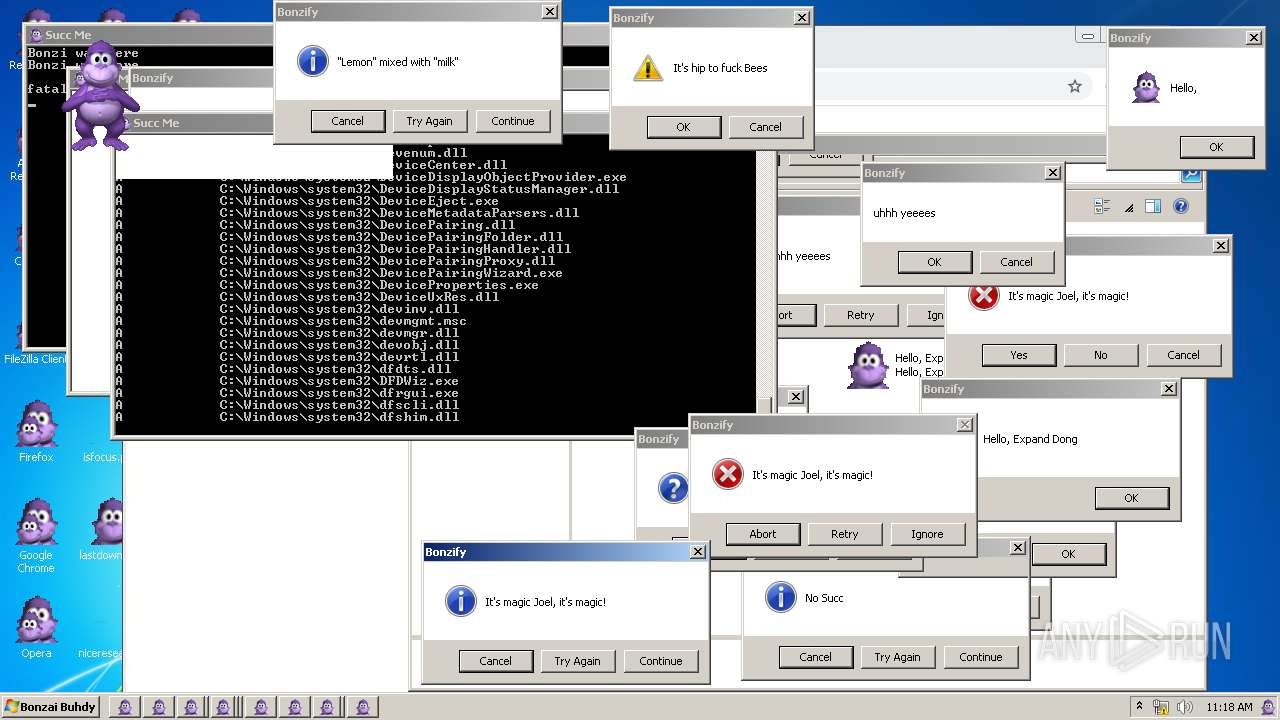
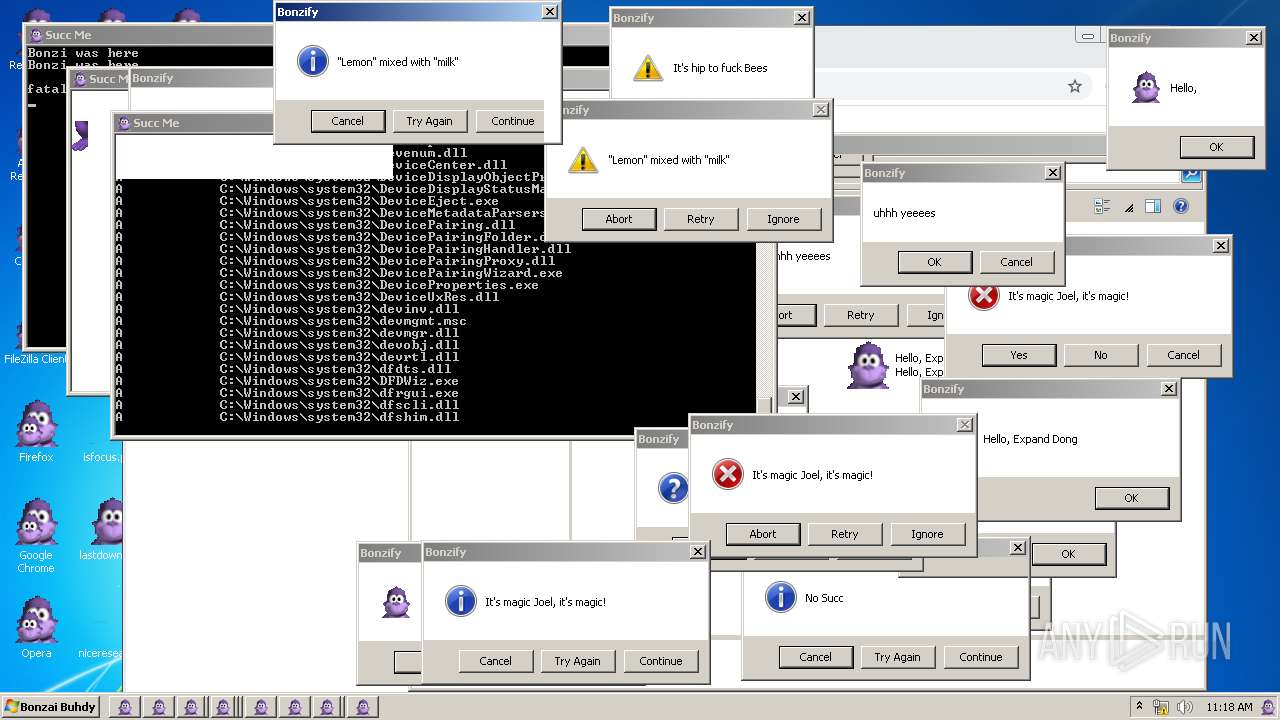
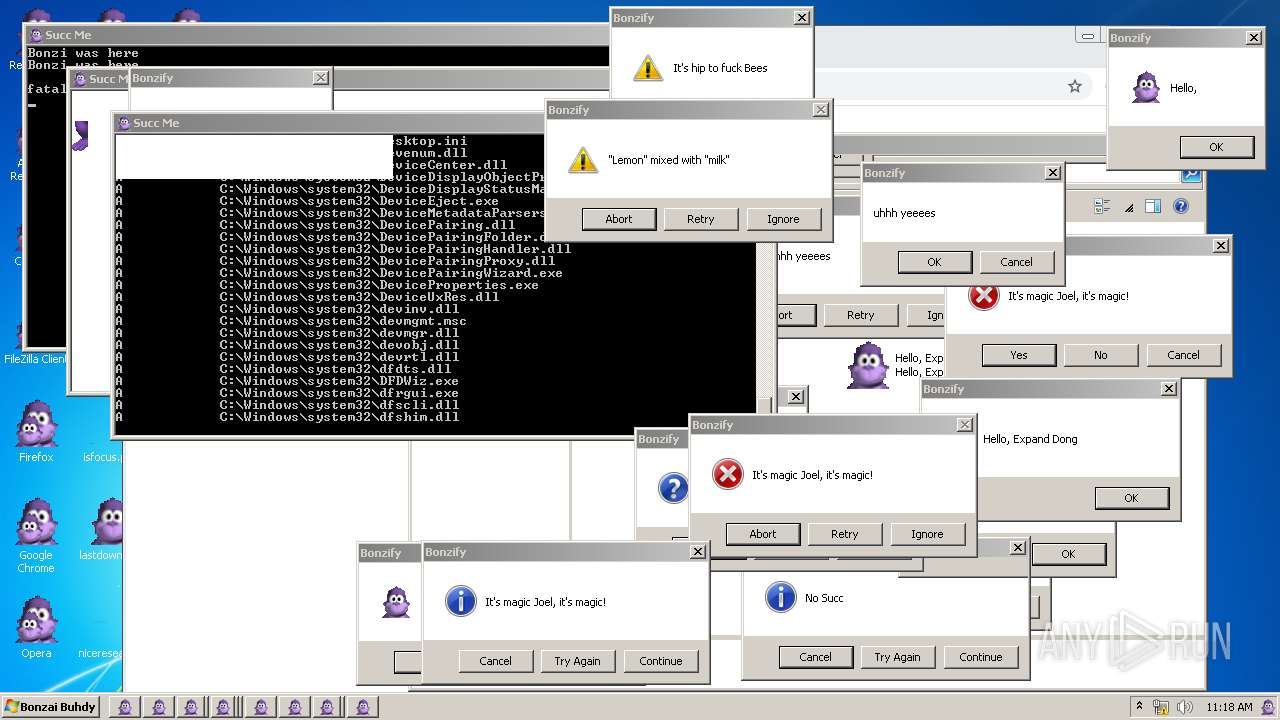
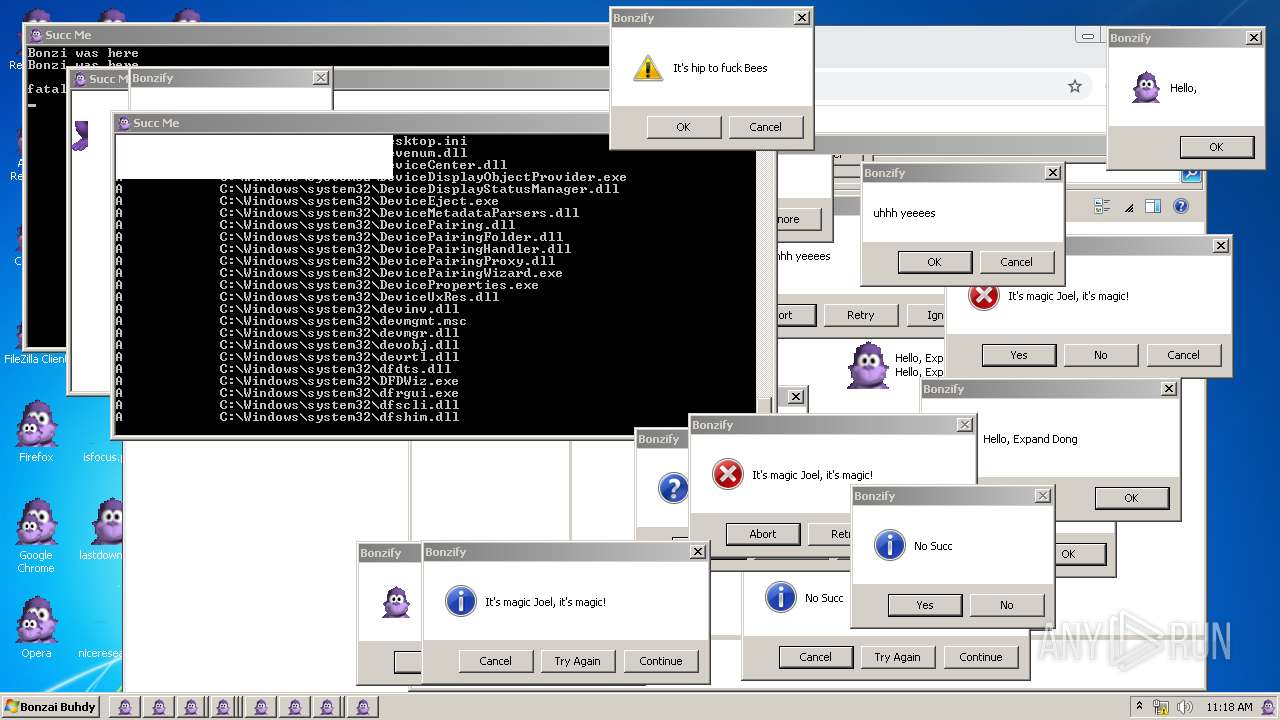
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 660 | regsvr32 /s "C:\Windows\msagent\AgentDPv.dll" | C:\Windows\System32\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1108,13554547360355823008,7392132722769724067,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2372 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1108,13554547360355823008,7392132722769724067,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 1 Version: 86.0.4240.198 | |||||||||||||||
| 1092 | grpconv.exe -o | C:\Windows\System32\grpconv.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1276 | INSTALLER.exe /q | C:\Users\admin\AppData\Local\Temp\INSTALLER.exe | Bonzify.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | — | explorer.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 | |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 1368 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\lastdownloads.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | |||||||||||||||
| 1420 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 | |||||||||||||||
Total events
3 515
Read events
3 405
Write events
83
Delete events
27
Modification events
| (PID) Process: | (1824) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{3626477B-5990-463E-B909-AE79D221C5F6}\{E8D89F32-6ED1-4DC6-844F-44585135AA1A} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1824) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{3626477B-5990-463E-B909-AE79D221C5F6} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1824) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{BF001409-272B-4CC4-AF81-812450177E52} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2060) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\Control |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2060) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\InprocServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2060) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\MiscStatus\1 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2060) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\MiscStatus |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2060) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\ProgID |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2060) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\Programmable |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2060) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\ToolboxBitmap32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
54
Suspicious files
42
Text files
44
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\KillAgent.bat | text | |
MD5:EA7DF060B402326B4305241F21F39736 | SHA256:E4EDC2CB6317AB19EE1A6327993E9332AF35CFBEBAFF2AC7C3F71D43CFCBE793 | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTDPV.DLL | executable | |
MD5:7C5AEFB11E797129C9E90F279FBDF71B | SHA256:394A17150B8774E507B8F368C2C248C10FCE50FC43184B744E771F0E79ECAFED | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTDP2.DLL | executable | |
MD5:A334BBF5F5A19B3BDB5B7F1703363981 | SHA256:C33BEABA130F8B740DDDB9980FE9012F9322AC6E94F36A6AA6086851C51B98DE | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTSR.DLL | executable | |
MD5:9FAFB9D0591F2BE4C2A846F63D82D301 | SHA256:E78E74C24D468284639FAF9DCFDBA855F3E4F00B2F26DB6B2C491FA51DA8916D | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTANM.DLL | executable | |
MD5:48C00A7493B28139CBF197CCC8D1F9ED | SHA256:905CB1A15ECCAA9B79926EE7CFE3629A6F1C6B24BDD6CEA9CCB9EBC9EAA92FF7 | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTPSH.DLL | executable | |
MD5:B4AC608EBF5A8FDEFA2D635E83B7C0E8 | SHA256:8414DFE399813B7426C235BA1E625BD2B5635C8140DA0D0CFC947F6565FE415F | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGT0409.DLL | executable | |
MD5:0CBF0F4C9E54D12D34CD1A772BA799E1 | SHA256:6B0B57E5B27D901F4F106B236C58D0B2551B384531A8F3DAD6C06ED4261424B1 | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGT0409.HLP | binary | |
MD5:466D35E6A22924DD846A043BC7DD94B8 | SHA256:E4CCF06706E68621BB69ADD3DD88FED82D30AD8778A55907D33F6D093AC16801 | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGT20.INF | binary | |
MD5:E4A499B9E1FE33991DBCFB4E926C8821 | SHA256:49E6B848F5A708D161F795157333D7E1C7103455A2F47F50895683EF6A1ABE4D | |||
| 1276 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGTCTL15.TLB | executable | |
MD5:F1656B80EAAE5E5201DCBFBCD3523691 | SHA256:3F8ADC1E332DD5C252BBCF92BF6079B38A74D360D94979169206DB34E6A24CD2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
107
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
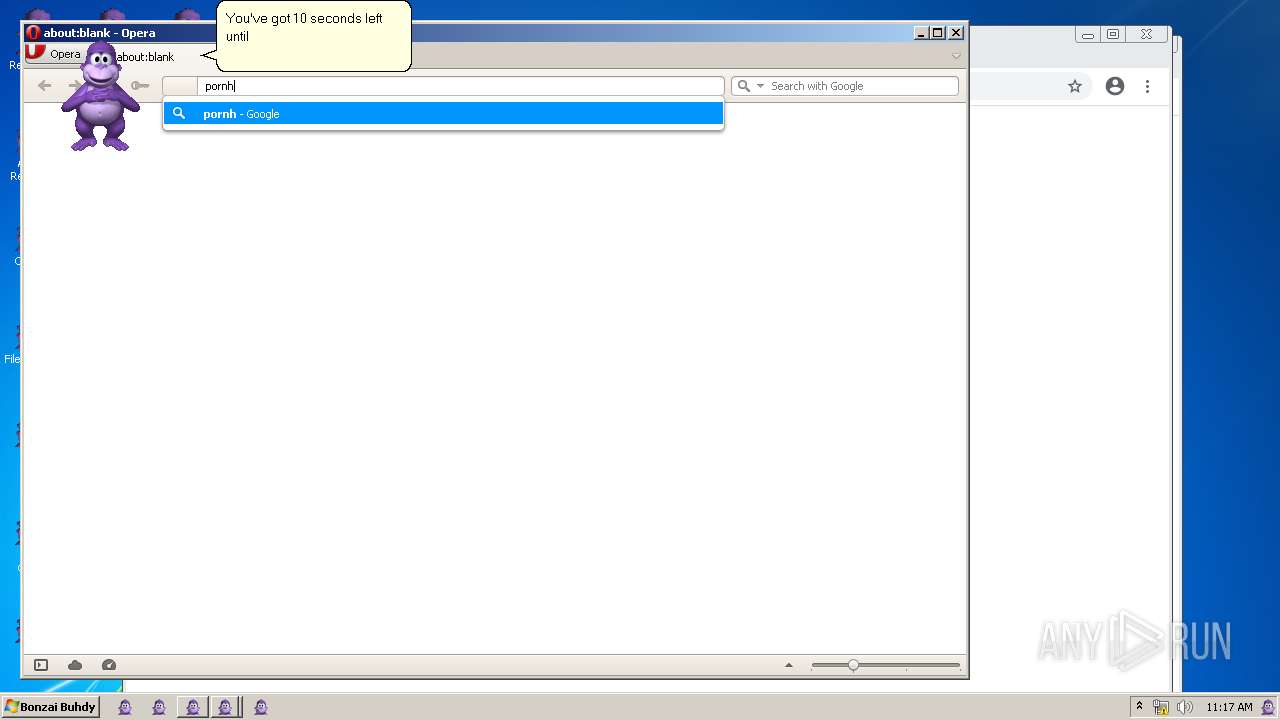
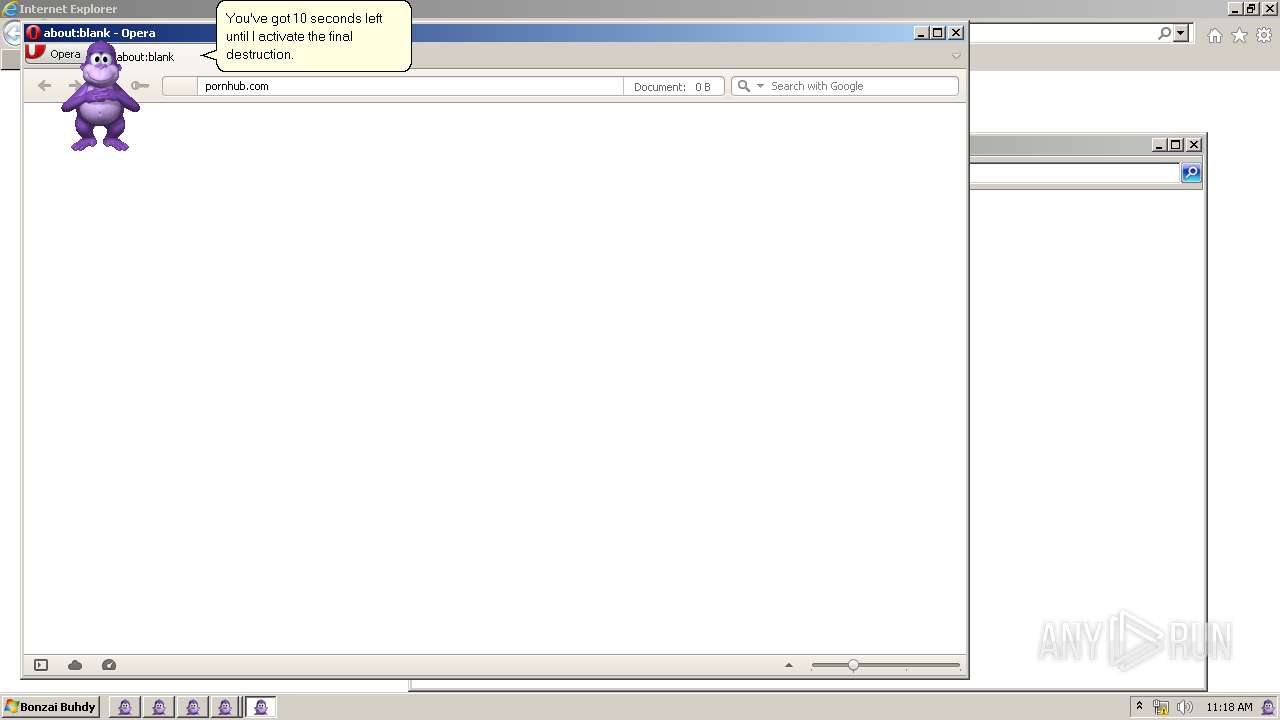
— | — | GET | 404 | 66.254.114.41:80 | http://pornhub.com/favicon.ico | US | xml | 341 b | whitelisted |
— | — | GET | 404 | 82.145.216.16:80 | http://sitecheck2.opera.com/?host=pornhub.com&hdn=x2AhXBMNx3Ym30F/CBR%2BHA== | unknown | xml | 341 b | whitelisted |
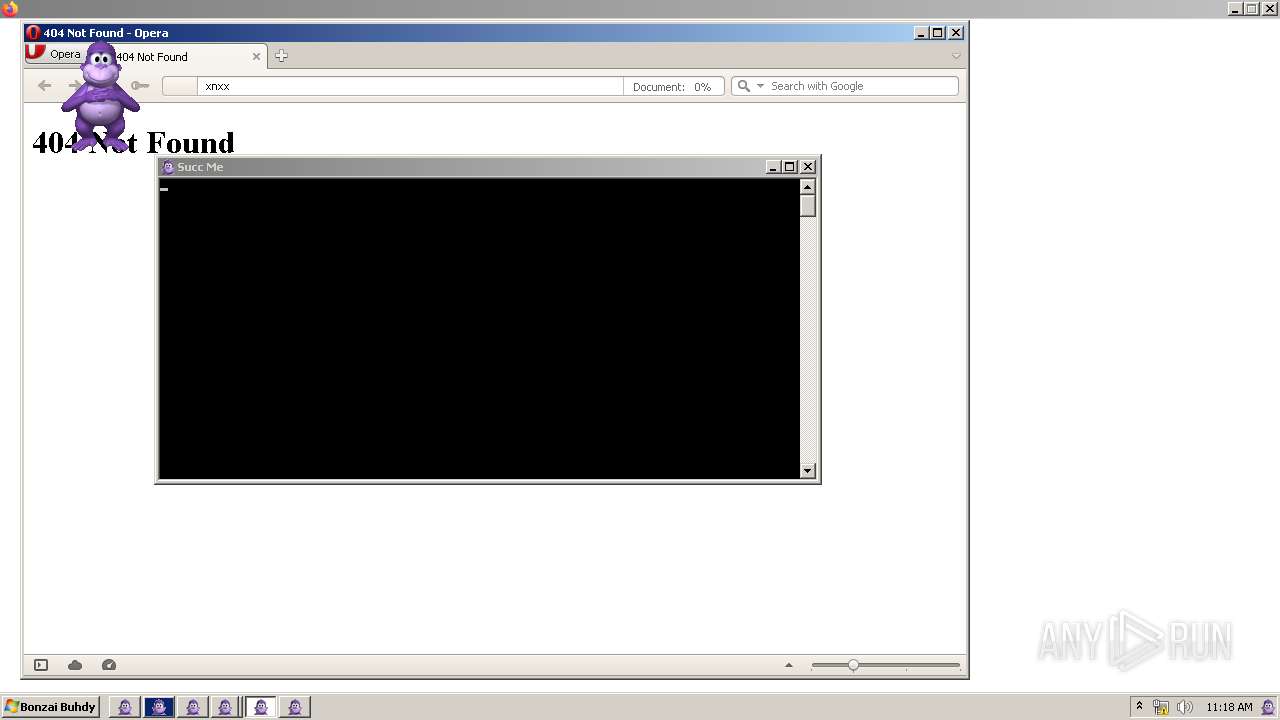
— | — | GET | 404 | 142.250.185.142:80 | http://clients1.google.com/complete/search?q=xnx&client=opera-suggest-omnibox&hl=de | US | xml | 341 b | whitelisted |
— | — | GET | 404 | 66.254.114.41:80 | http://pornhub.com/ | US | xml | 341 b | whitelisted |
— | — | GET | 404 | 142.250.185.195:80 | http://www.google.com.ua/search?q=xnxx&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | xml | 341 b | whitelisted |
— | — | GET | 404 | 142.250.185.195:80 | http://www.google.com.ua/favicon.ico | US | xml | 341 b | whitelisted |
— | — | GET | 404 | 142.250.185.142:80 | http://clients1.google.com/complete/search?q=pornhi&client=opera-suggest-omnibox&hl=de | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1464 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
1464 | chrome.exe | 142.250.185.227:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1464 | chrome.exe | 142.250.185.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
1464 | chrome.exe | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | suspicious |
— | — | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
certs.opera.com |
| whitelisted |
clients1.google.com |
| whitelisted |
pornhub.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
Threats
1 ETPRO signatures available at the full report
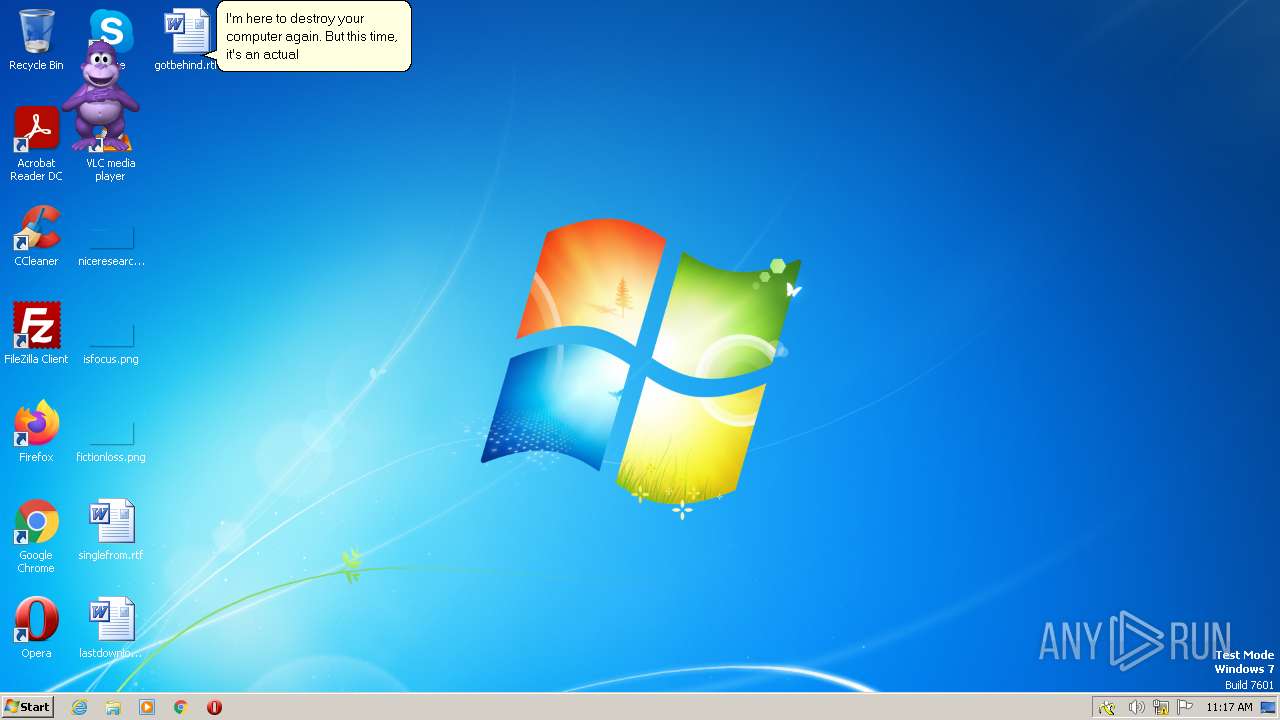
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|