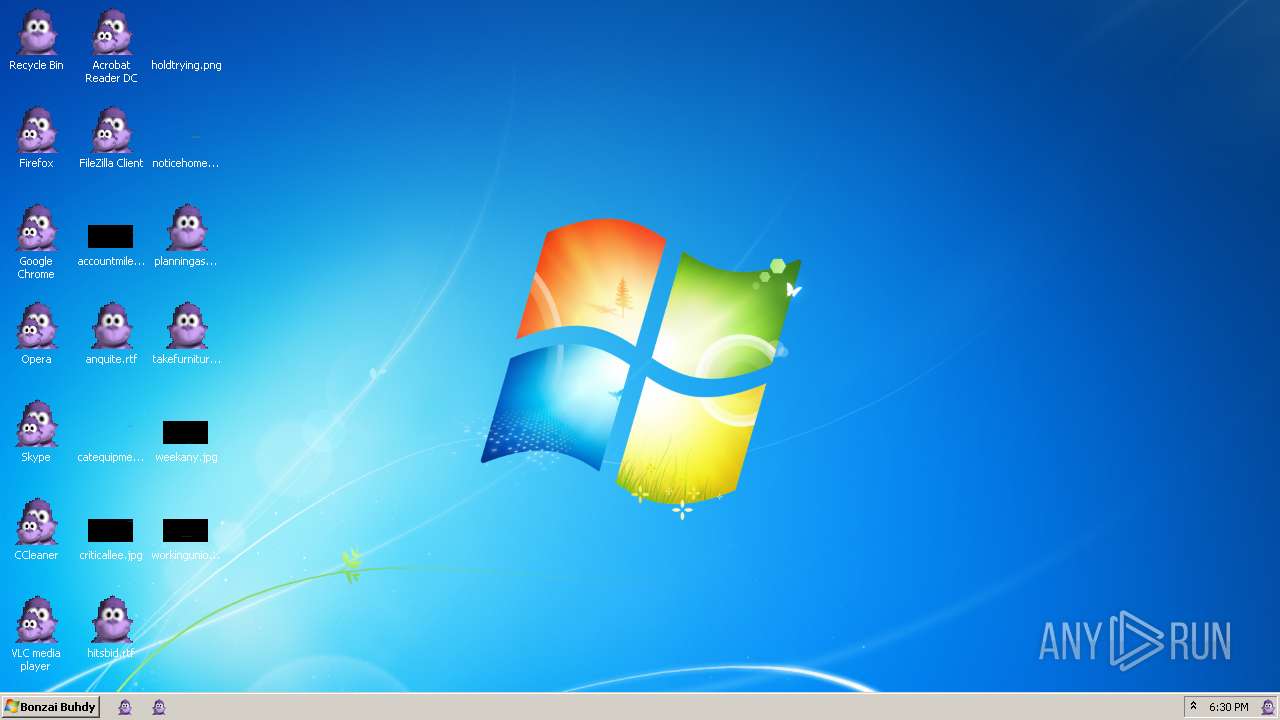
| download: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/172a52fb-67ef-4449-873d-0883f5bcfe68 |
| Verdict: | Malicious activity |
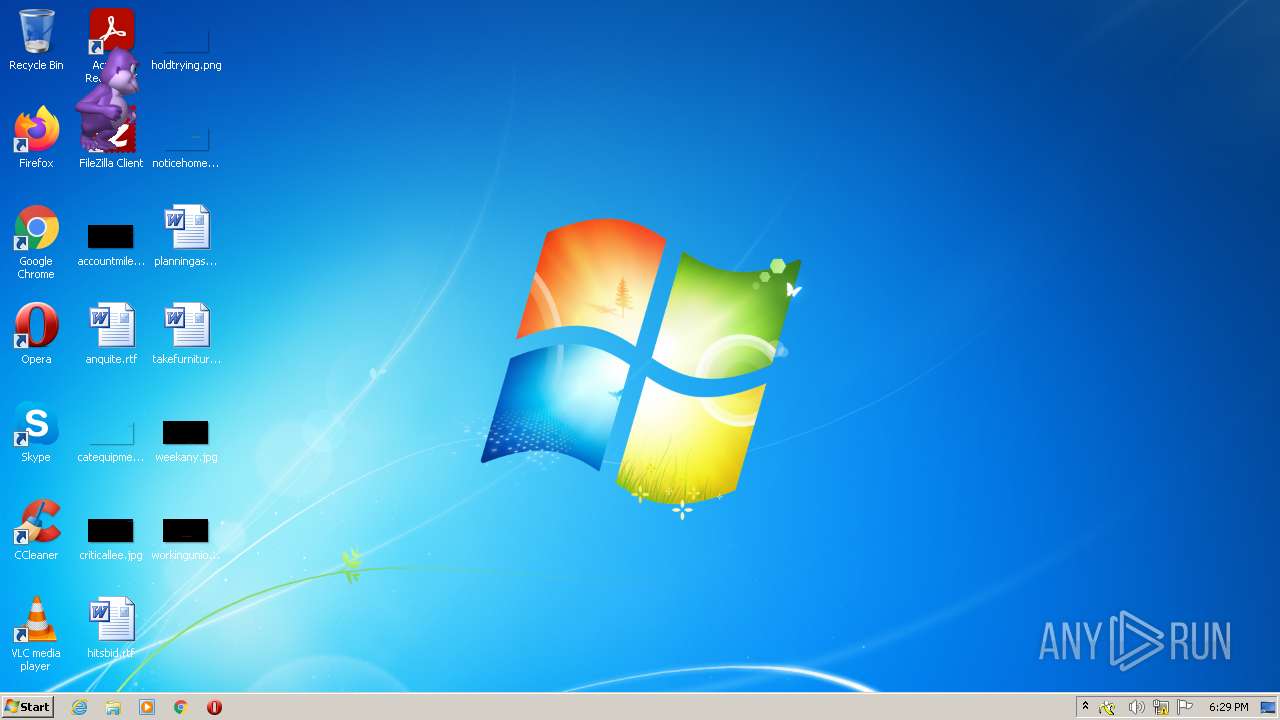
| Analysis date: | January 03, 2022, 18:29:35 |
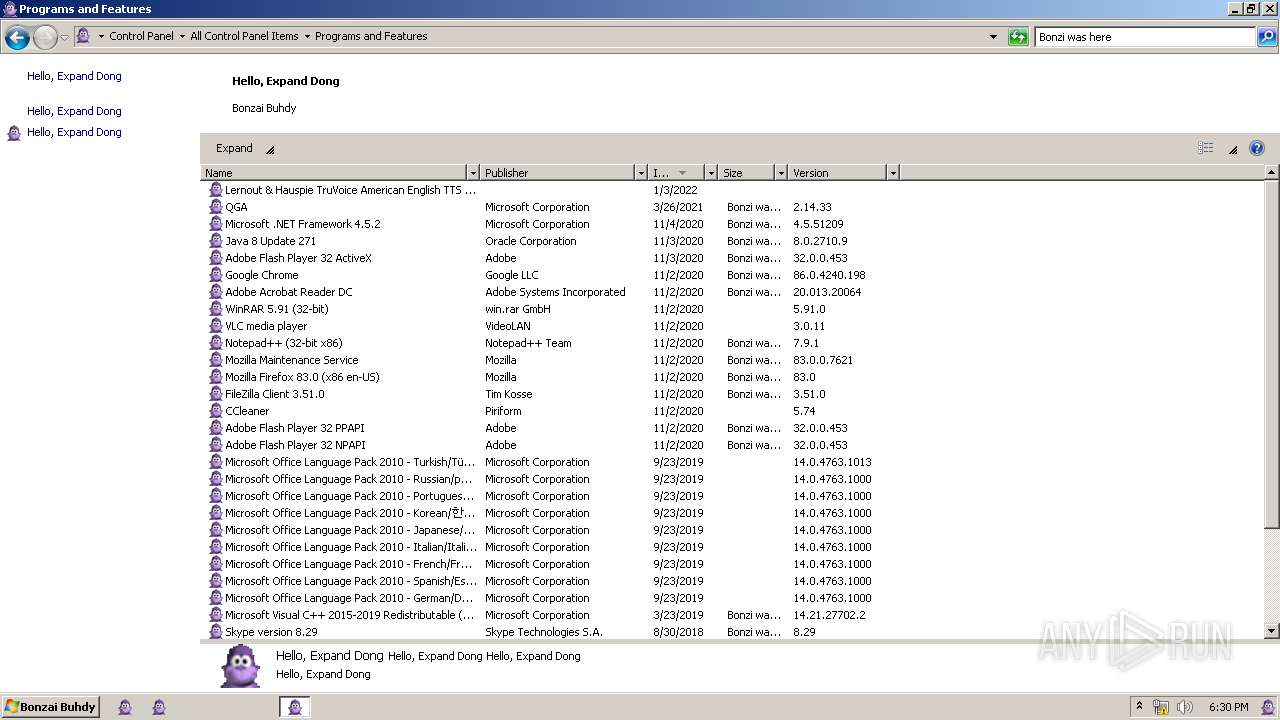
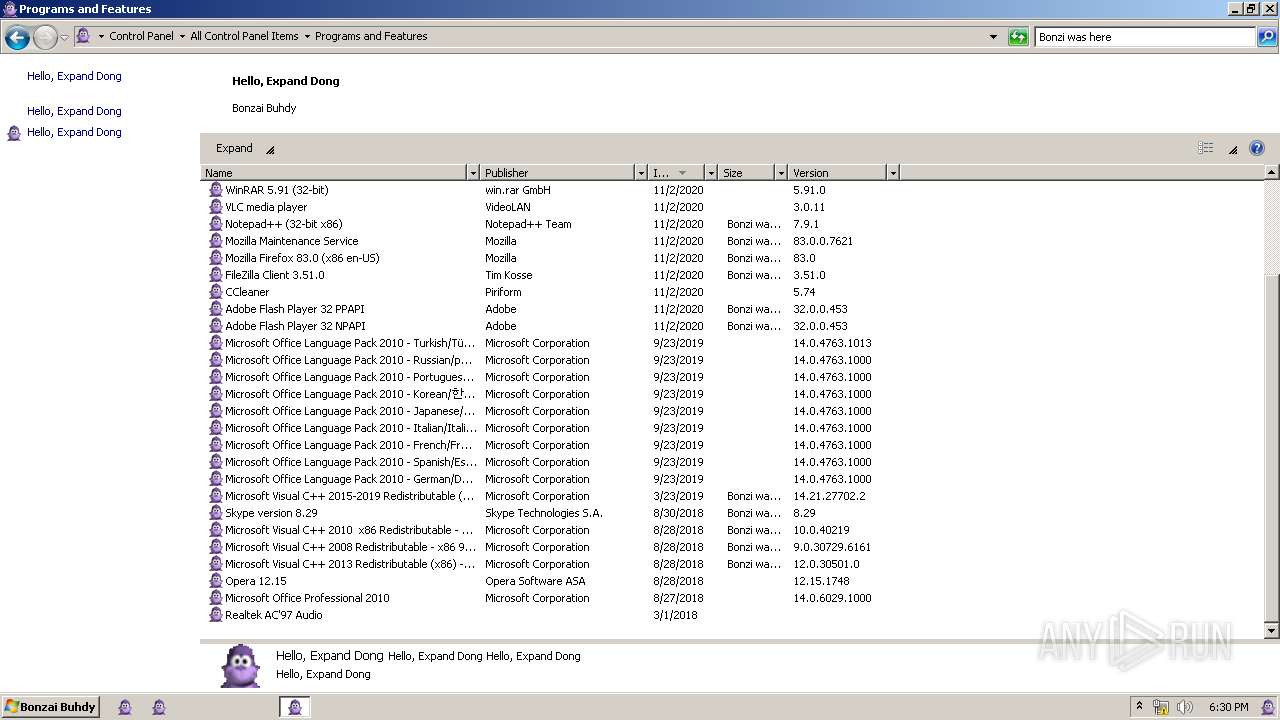
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9C352D2CE0C0BDC40C72F52CE3480577 |
| SHA1: | BD4C956186F33C92EB4469F7E5675510D0790E99 |
| SHA256: | D7E6580054525D3F21F86EDFC9F30B7A75FFA829A1EB67EE3CAB33F0040DBA4E |
| SSDEEP: | 196608:/dAMaWetTeAkLIdx751qFTkub//73lc6u7b5VJ2Yx5xIdk3o:naWedh+Idx75QYub//73lc6u7bLMYxDo |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 2228)
- SearchProtocolHost.exe (PID: 668)
- DllHost.exe (PID: 592)
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 3360)
- INSTALLER.exe (PID: 3616)
Application was dropped or rewritten from another process
- INSTALLER.exe (PID: 3616)
- INSTALLER.exe (PID: 3360)
SUSPICIOUS
Creates files in the Windows directory
- Bonzify.exe (PID: 1320)
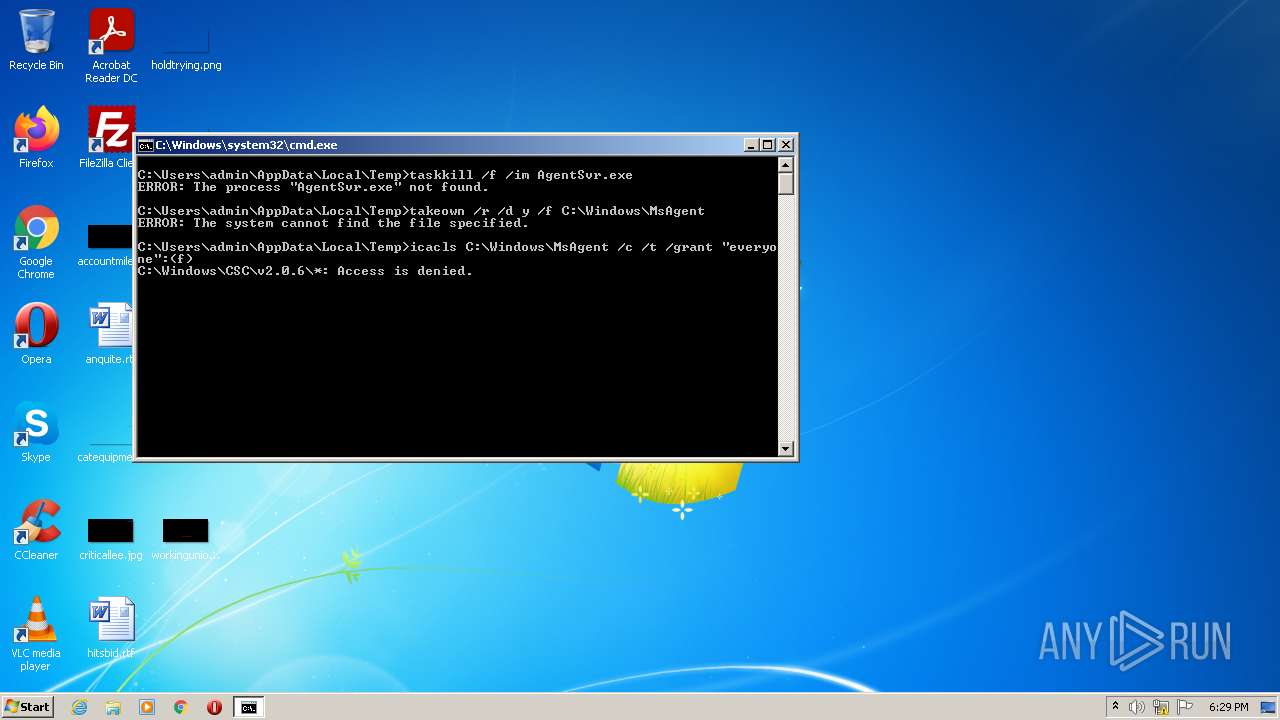
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 1320)
Checks supported languages
- Bonzify.exe (PID: 1320)
- cmd.exe (PID: 756)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 756)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 756)
Drops a file with too old compile date
- Bonzify.exe (PID: 1320)
Drops a file that was compiled in debug mode
- Bonzify.exe (PID: 1320)
Executable content was dropped or overwritten
- Bonzify.exe (PID: 1320)
Executed via COM
- AgentSvr.exe (PID: 3128)
INFO
Reads the computer name
- taskkill.exe (PID: 1808)
- takeown.exe (PID: 2120)
- icacls.exe (PID: 2576)
Checks supported languages
- taskkill.exe (PID: 1808)
- takeown.exe (PID: 2120)
- icacls.exe (PID: 2576)
Dropped object may contain Bitcoin addresses
- Bonzify.exe (PID: 1320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (86.7) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.8) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Generic Win/DOS Executable (0.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x16b0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 6697472 |
| CodeSize: | 4096 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2019:03:04 15:58:11+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Mar-2019 14:58:11 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Mar-2019 14:58:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000F88 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.51622 |
.rdata | 0x00002000 | 0x0000109C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13419 |
.data | 0x00004000 | 0x00000020 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00005000 | 0x00661BD8 | 0x00661C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.84962 |
.reloc | 0x00667000 | 0x000001C4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.08408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.01704 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
100 | 7.82633 | 5249795 | UNKNOWN | UNKNOWN | DATA |
101 | 7.78087 | 400536 | UNKNOWN | UNKNOWN | DATA |
102 | 7.93147 | 1021232 | UNKNOWN | UNKNOWN | DATA |
103 | 4.90328 | 161 | UNKNOWN | UNKNOWN | DATA |
104 | 4.49923 | 46 | UNKNOWN | UNKNOWN | DATA |
110 | 5.36458 | 15360 | UNKNOWN | UNKNOWN | DATA |
IDI_BONZI | 2.32824 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
62
Monitored processes
24
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10003_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10003 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 756 | C:\Windows\system32\cmd.exe /c "C:\Users\admin\AppData\Local\Temp\KillAgent.bat" | C:\Windows\system32\cmd.exe | — | Bonzify.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 908 | regsvr32 /s "C:\Windows\msagent\mslwvtts.dll" | C:\Windows\system32\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1320 | "C:\Users\admin\AppData\Local\Temp\Bonzify.exe" | C:\Users\admin\AppData\Local\Temp\Bonzify.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1808 | taskkill /f /im AgentSvr.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | regsvr32 /s "C:\Windows\msagent\AgentMPx.dll" | C:\Windows\system32\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1968 | regsvr32 /s C:\Windows\lhsp\tv\tv_enua.dll | C:\Windows\system32\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | regsvr32 /s "C:\Windows\msagent\AgentCtl.dll" | C:\Windows\system32\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | takeown /r /d y /f C:\Windows\MsAgent | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
16 386
Read events
15 389
Write events
979
Delete events
18
Modification events
| (PID) Process: | (3616) INSTALLER.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1 |
| Operation: | write | Name: | (default) |
Value: Microsoft Agent Control 1.5 | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1\CLSID |
| Operation: | write | Name: | (default) |
Value: {F5BE8BD2-7DE6-11D0-91FE-00C04FD701A5} | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2 |
| Operation: | write | Name: | (default) |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2\CLSID |
| Operation: | write | Name: | (default) |
Value: {D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control |
| Operation: | write | Name: | (default) |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control\CurVer |
| Operation: | write | Name: | (default) |
Value: Agent.Control.2 | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} |
| Operation: | write | Name: | (default) |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\ProgID |
| Operation: | write | Name: | (default) |
Value: Agent.Control.2 | |||
| (PID) Process: | (2068) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\VersionIndependentProgID |
| Operation: | write | Name: | (default) |
Value: Agent.Control | |||
Executable files
3
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1320 | Bonzify.exe | C:\Windows\msagent\chars\Bonzi.acs | — | |
MD5:— | SHA256:— | |||
| 1320 | Bonzify.exe | C:\Windows\executables.bin | binary | |
MD5:1937DF7C6CD286FBFA5556DC2DC55B6E | SHA256:86456B35103FD33097E40ECD4C34A5082471C86F7EE8FDC8AABDD0A72A6DE652 | |||
| 1320 | Bonzify.exe | C:\HookDLL.dll | executable | |
MD5:999225434CDBB7BD18F35A1CC588AAE7 | SHA256:FAB2F350FADC87C2D4E3F826E0D5B237A2E07BE768104A19BCDF32F77FF360BA | |||
| 1320 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\KillAgent.bat | text | |
MD5:EA7DF060B402326B4305241F21F39736 | SHA256:E4EDC2CB6317AB19EE1A6327993E9332AF35CFBEBAFF2AC7C3F71D43CFCBE793 | |||
| 1320 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\TakeOwn.bat | text | |
MD5:F80E36CD406022944558D8A099DB0FA7 | SHA256:7B41E5A6C2DD92F60C38CB4FE09DCBE378C3E99443F7BAF079ECE3608497BDC7 | |||
| 1320 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\INSTALLER.exe | executable | |
MD5:66996A076065EBDCDAC85FF9637CEAE0 | SHA256:16CA09AD70561F413376AD72550AE5664C89C6A76C85C872FFE2CB1E7F49E2AA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | UnclaimOutput
|