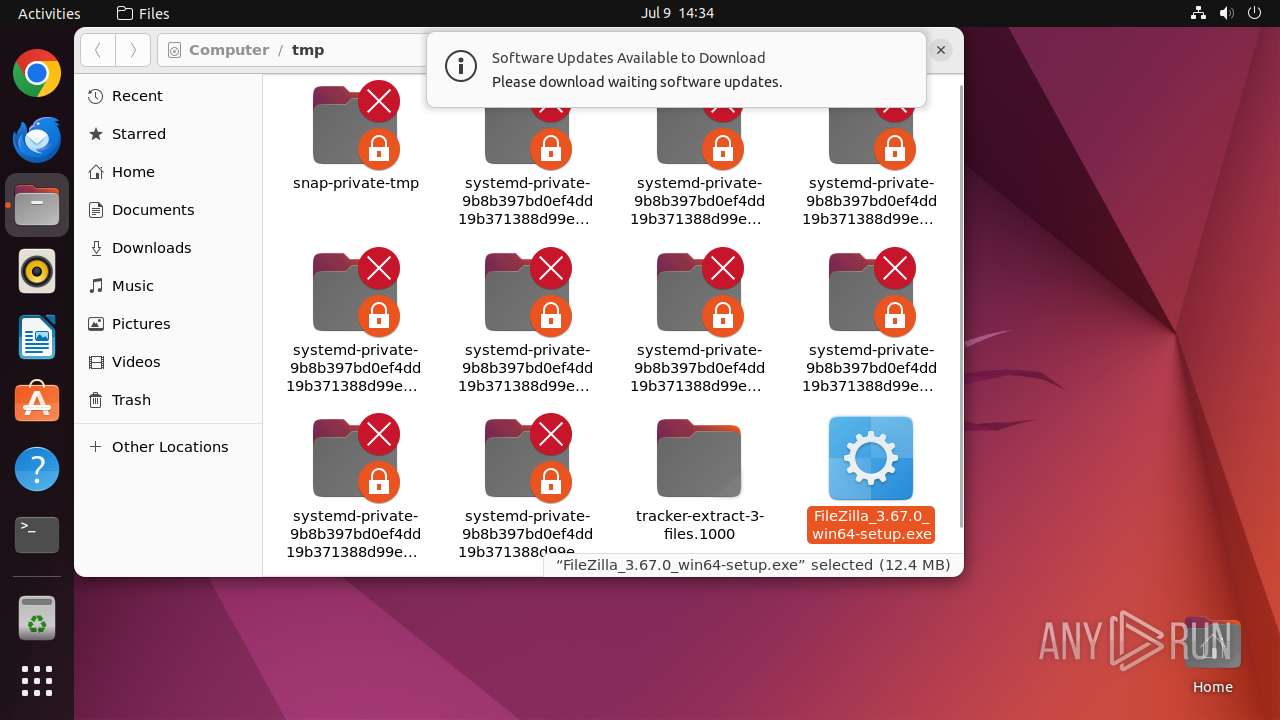
| File name: | FileZilla_3.67.0_win64-setup.exe |
| Full analysis: | https://app.any.run/tasks/a858b3c5-e462-4fee-a660-94156d302040 |
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2024, 13:34:35 |
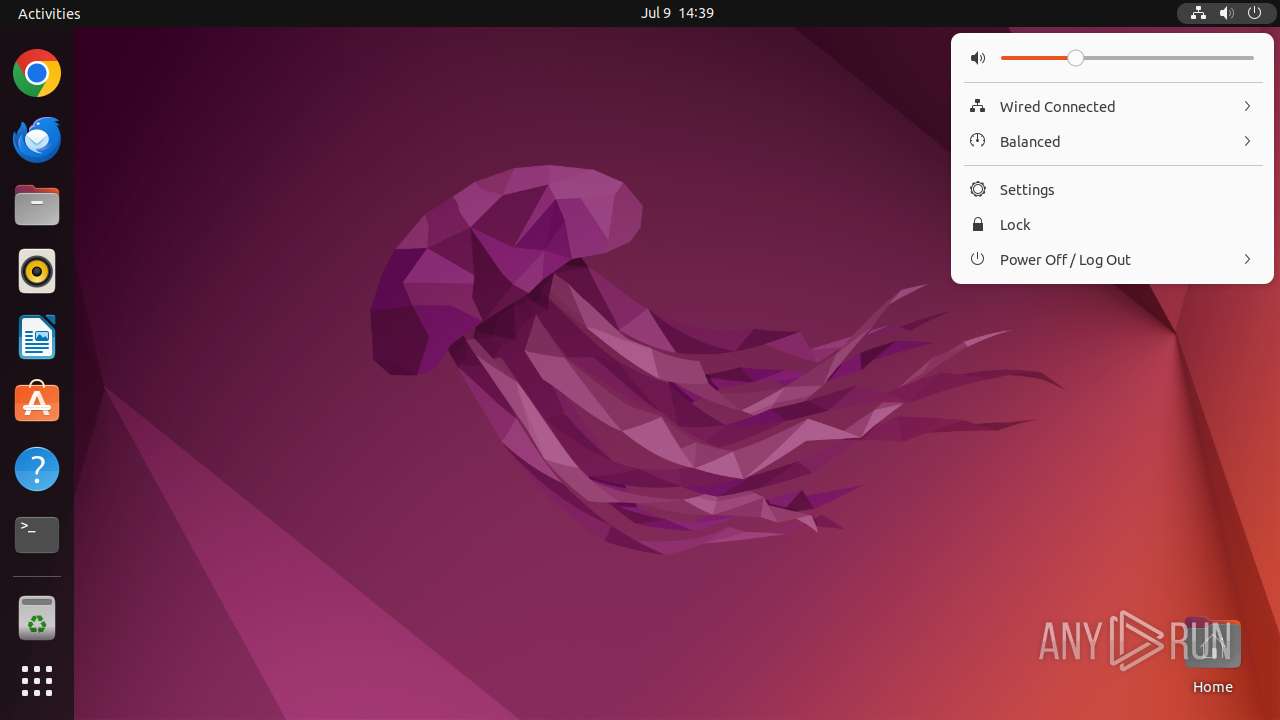
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D24255FA5F117A2506045143856B6336 |
| SHA1: | 8EA2BF726044E98479076D0E64327F7AE7A6E5F2 |
| SHA256: | D7E11B178FCC3D1EE7F6AD3DCE6DA2EA043DE64D521CF3578FB09031CBDB0AE2 |
| SSDEEP: | 98304:HMyWOAfu/ycn2A237vF402BeCkdLddmK2bKg9eR5S2UjaVWxnHs5sleLWmArq0zM:8lzP5chUclFe0OHEcKswjajKqUn4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 12954)
Executes commands using command-line interpreter
- update-notifier (PID: 13375)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13377)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:43+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3645 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.67.0.0 |
| ProductVersionNumber: | 3.67.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Tim Kosse |
| FileDescription: | FileZilla FTP Client |
| FileVersion: | 3.67.0 |
| LegalCopyright: | Tim Kosse |
| OriginalFileName: | FileZilla_3.67.0_win32-setup.exe |
| ProductName: | FileZilla |
| ProductVersion: | 3.67.0 |
Total processes
349
Monitored processes
134
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12928 | sh -c "file --mime-type /tmp/FileZilla_3\.67\.0_win64-setup\.exe" | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12929 | file --mime-type /tmp/FileZilla_3.67.0_win64-setup.exe | /usr/bin/file | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12930 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /tmp/FileZilla_3\.67\.0_win64-setup\.exe " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 480 | ||||
| 12931 | sudo -iu user nautilus /tmp/FileZilla_3.67.0_win64-setup.exe | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 418 | ||||
| 12932 | nautilus /tmp/FileZilla_3.67.0_win64-setup.exe | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 13432 | ||||
| 12933 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12954 | /lib/systemd/systemd-hostnamed | /lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 12970 | ||||
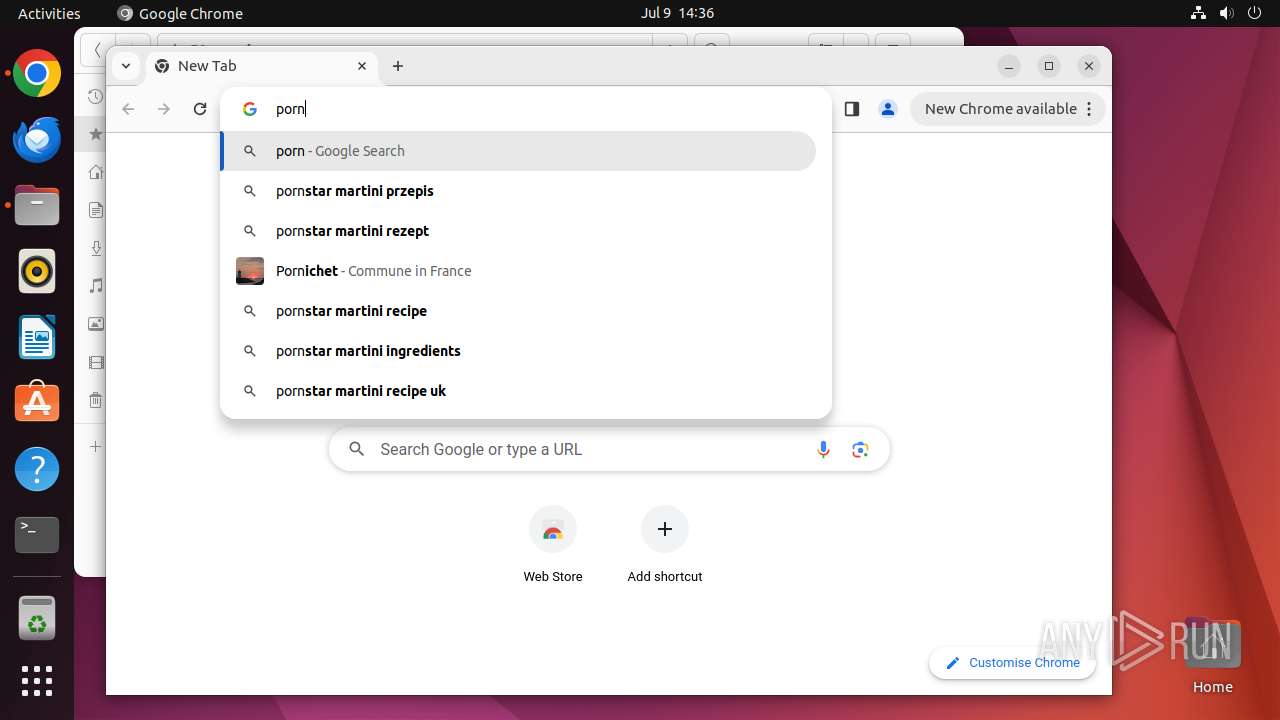
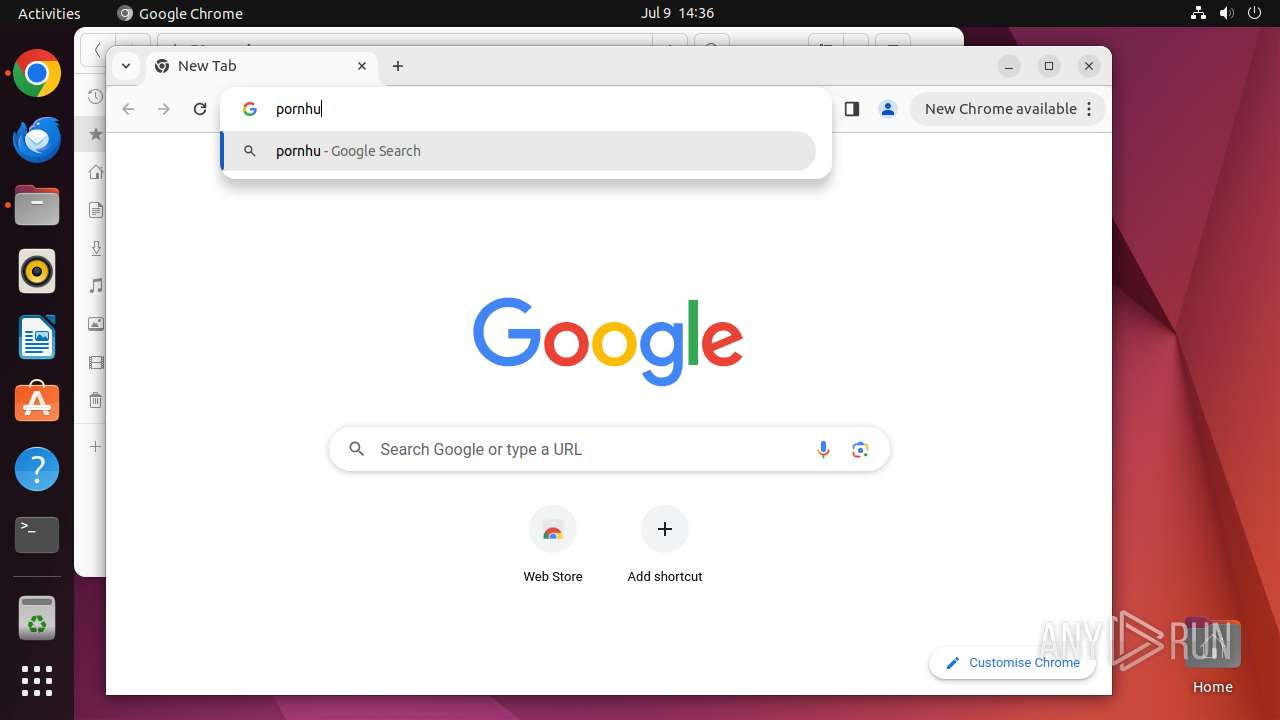
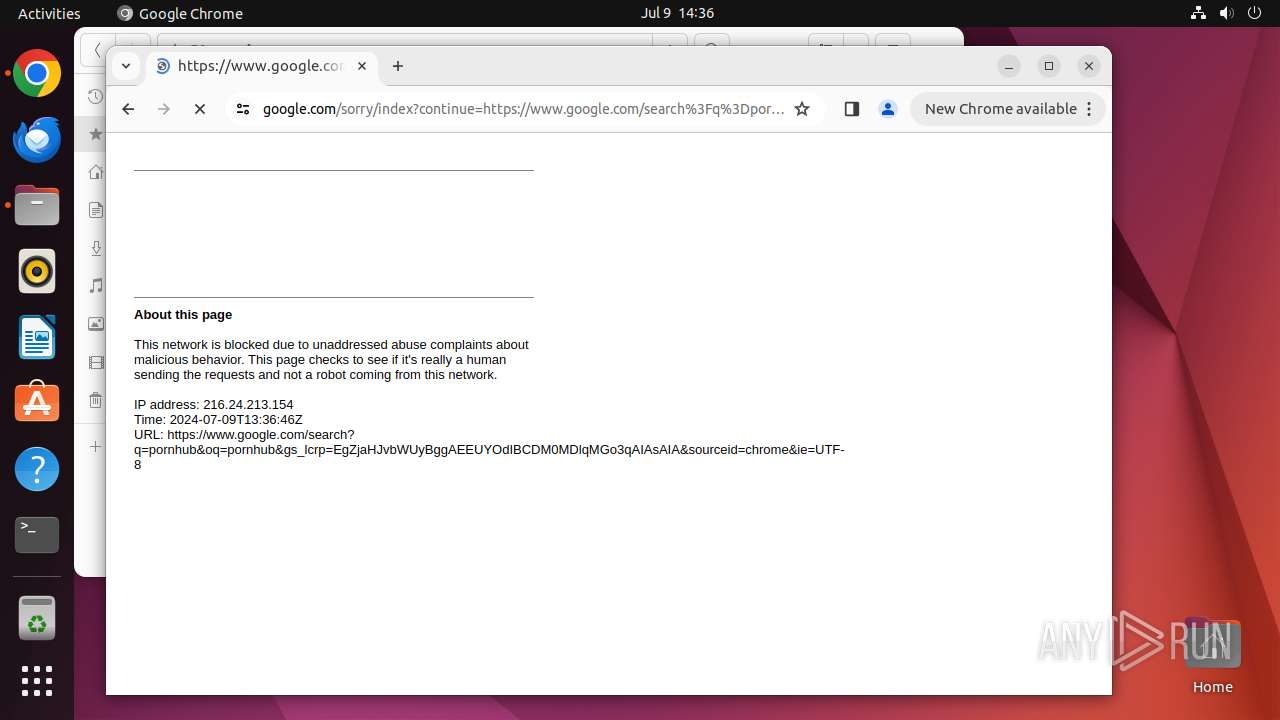
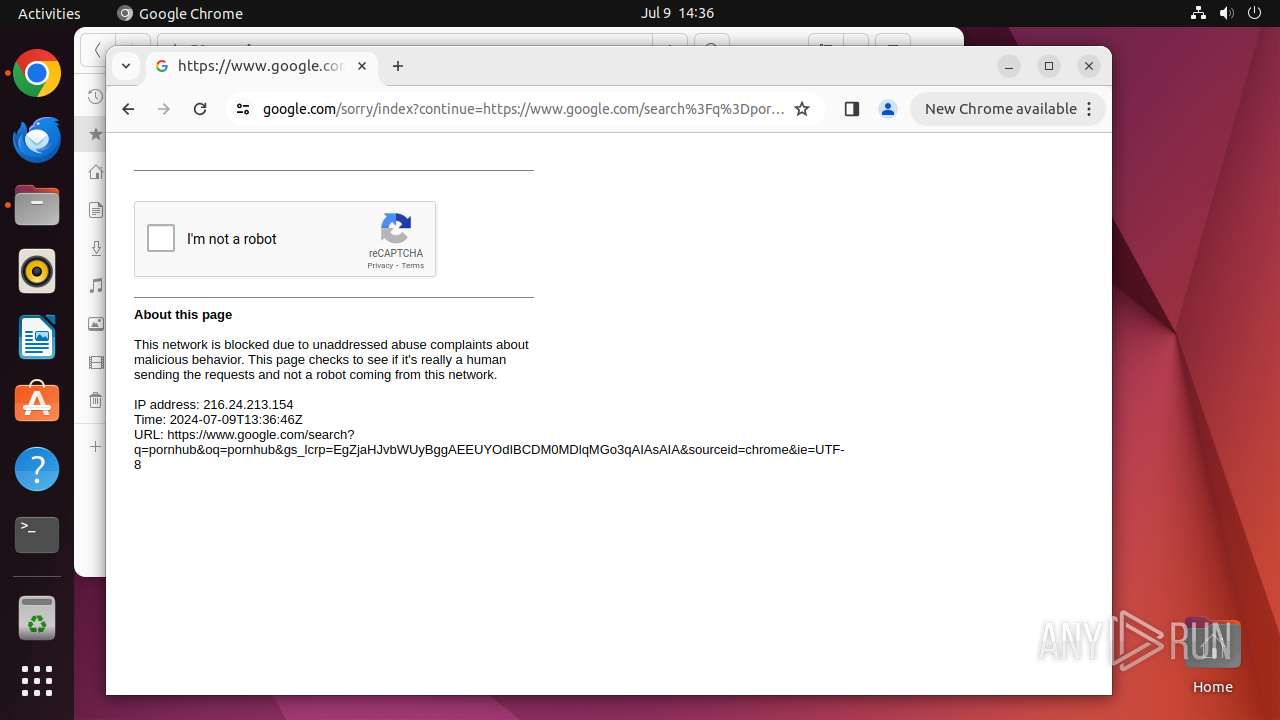
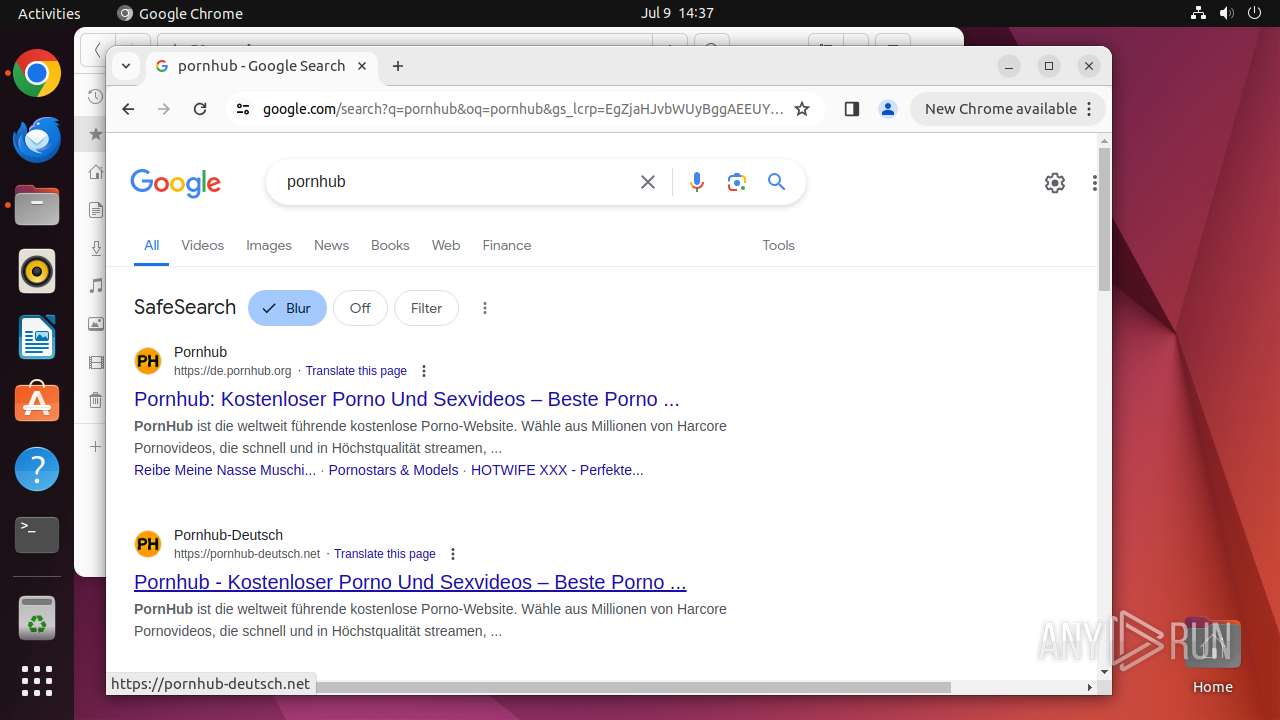
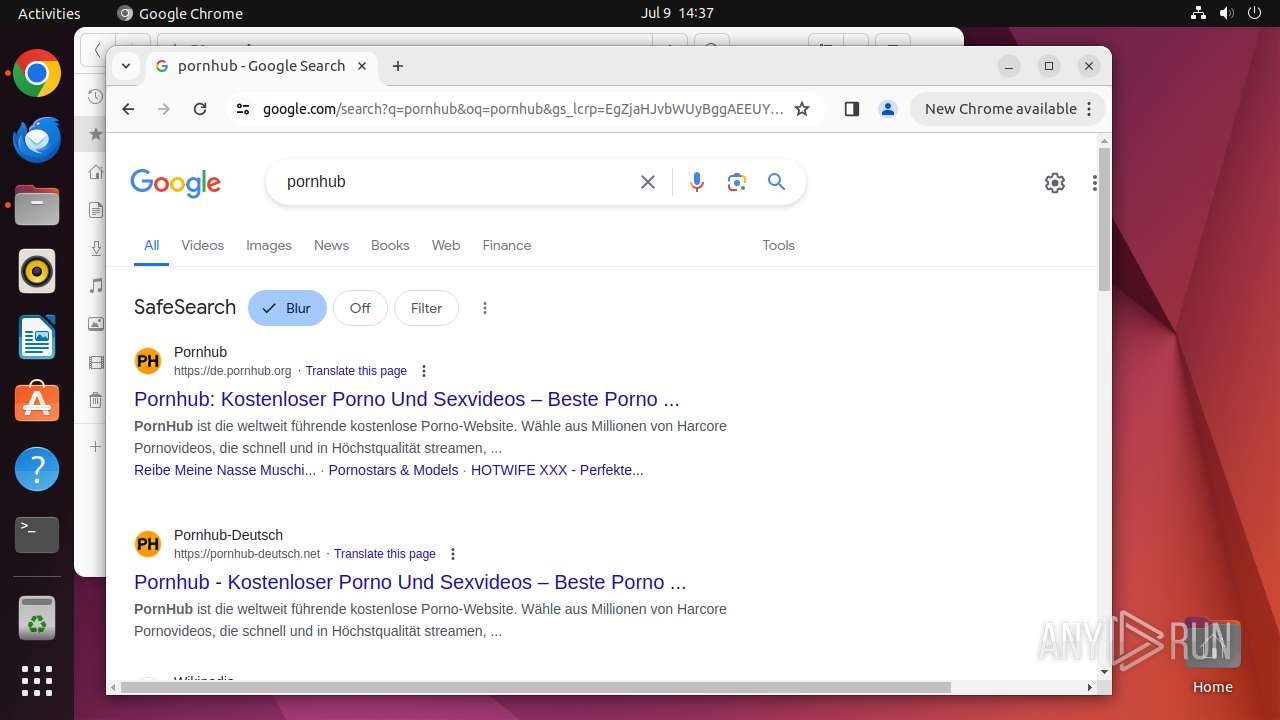
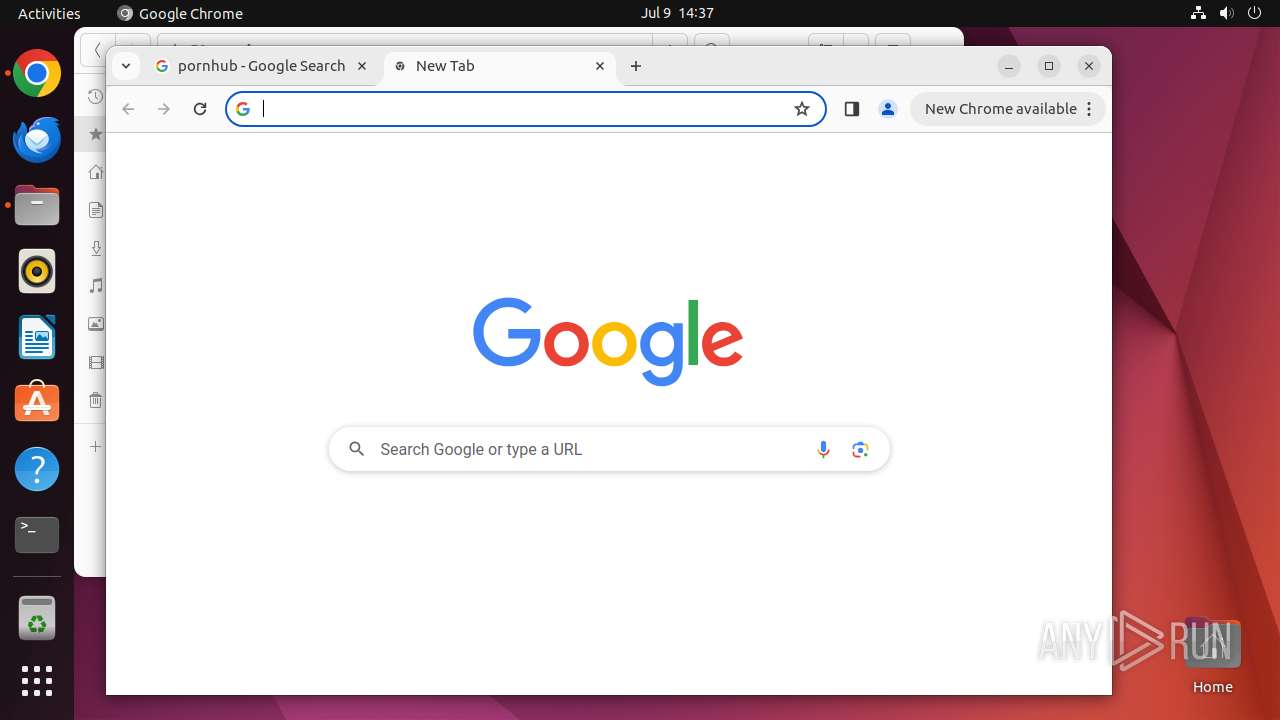
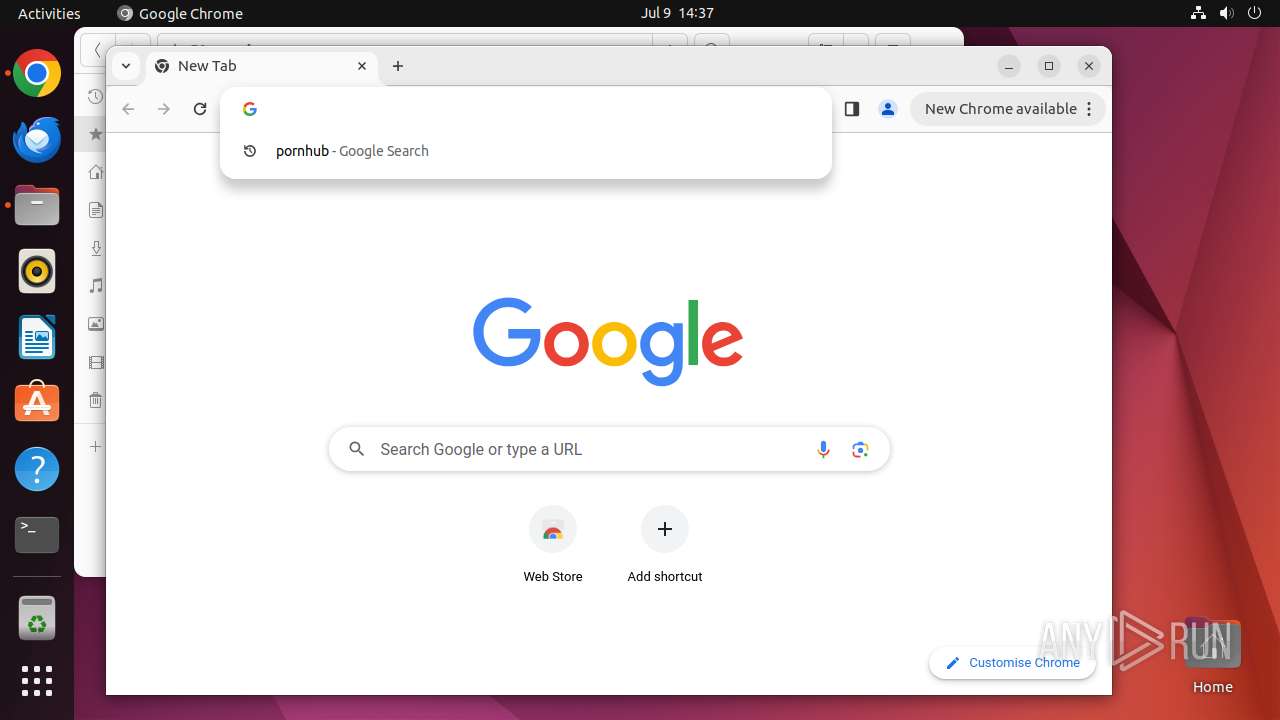
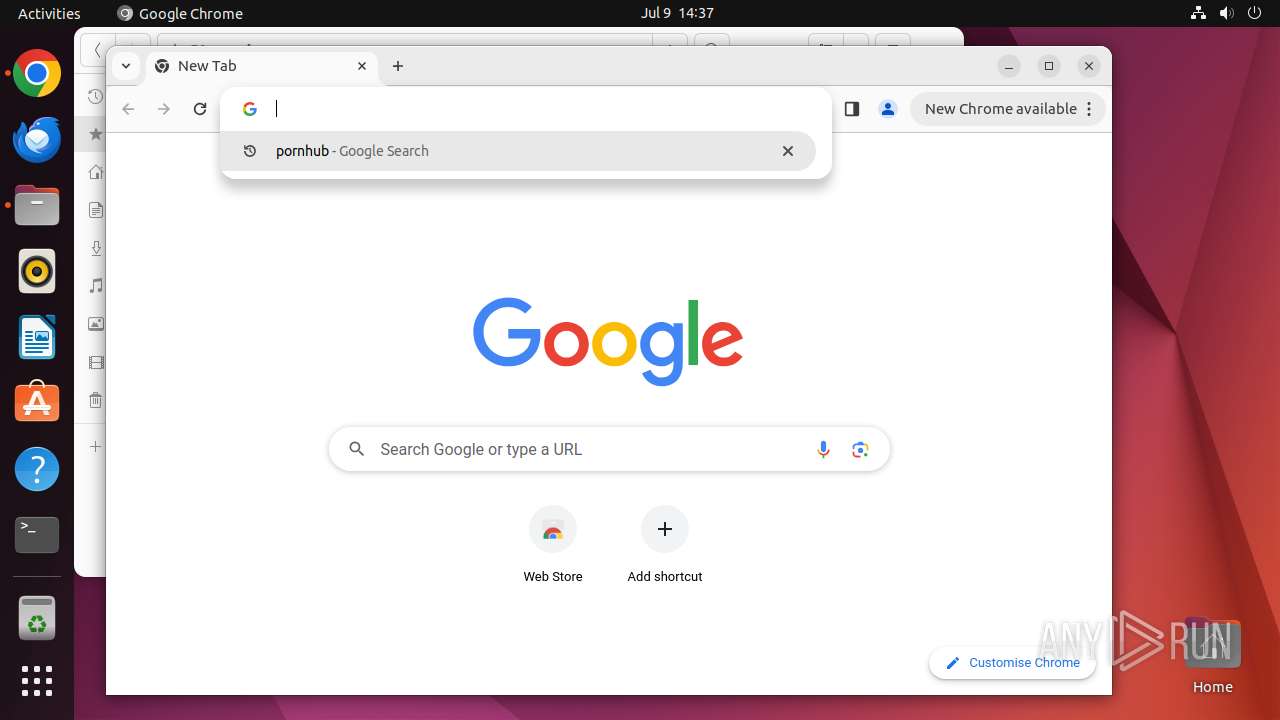
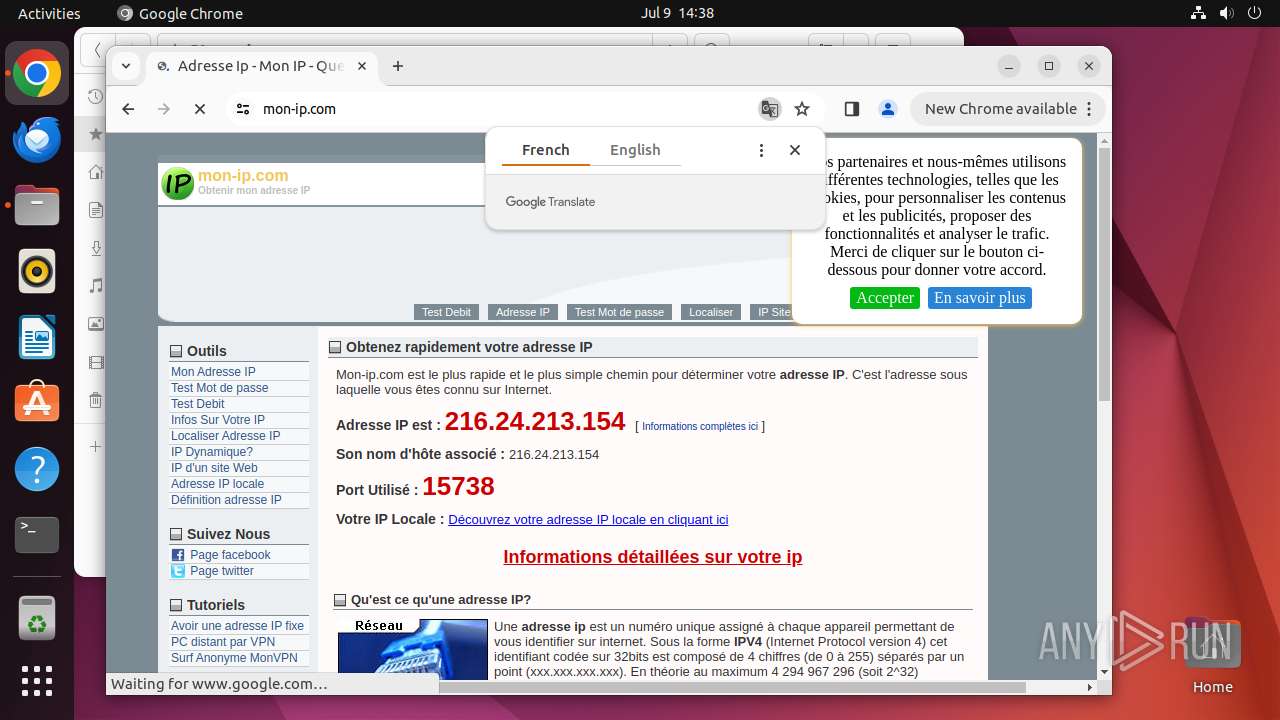
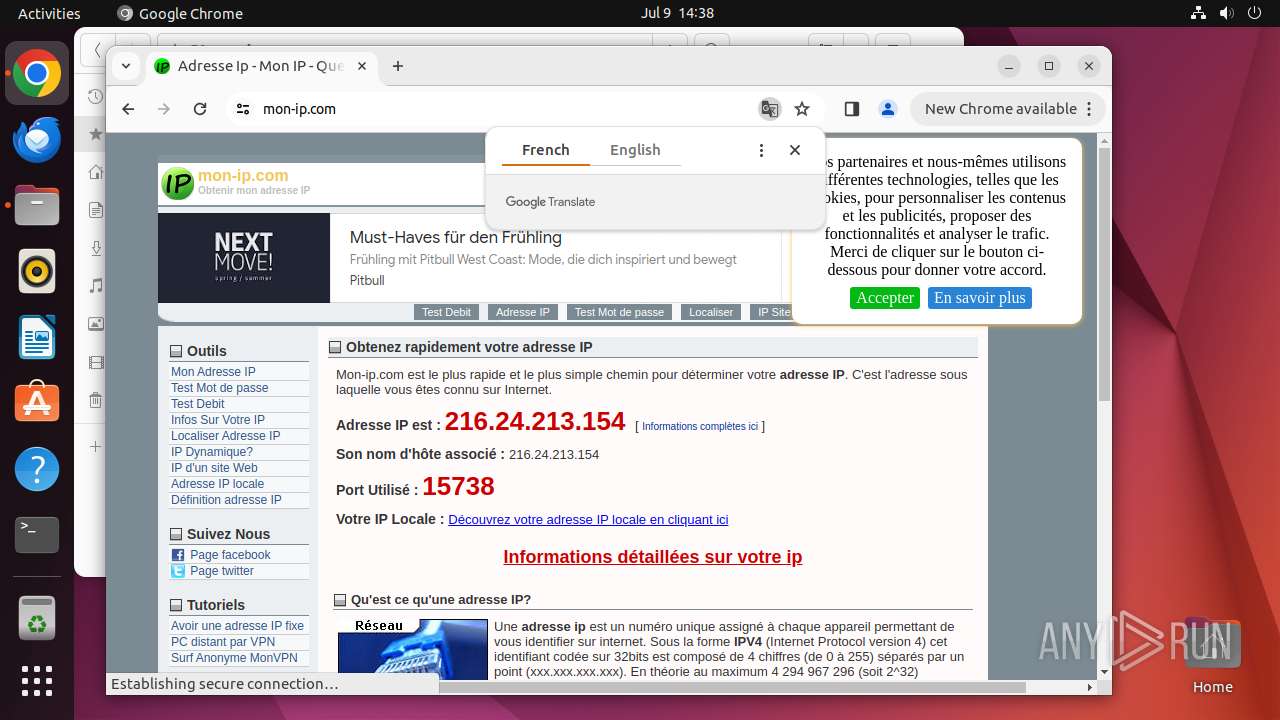
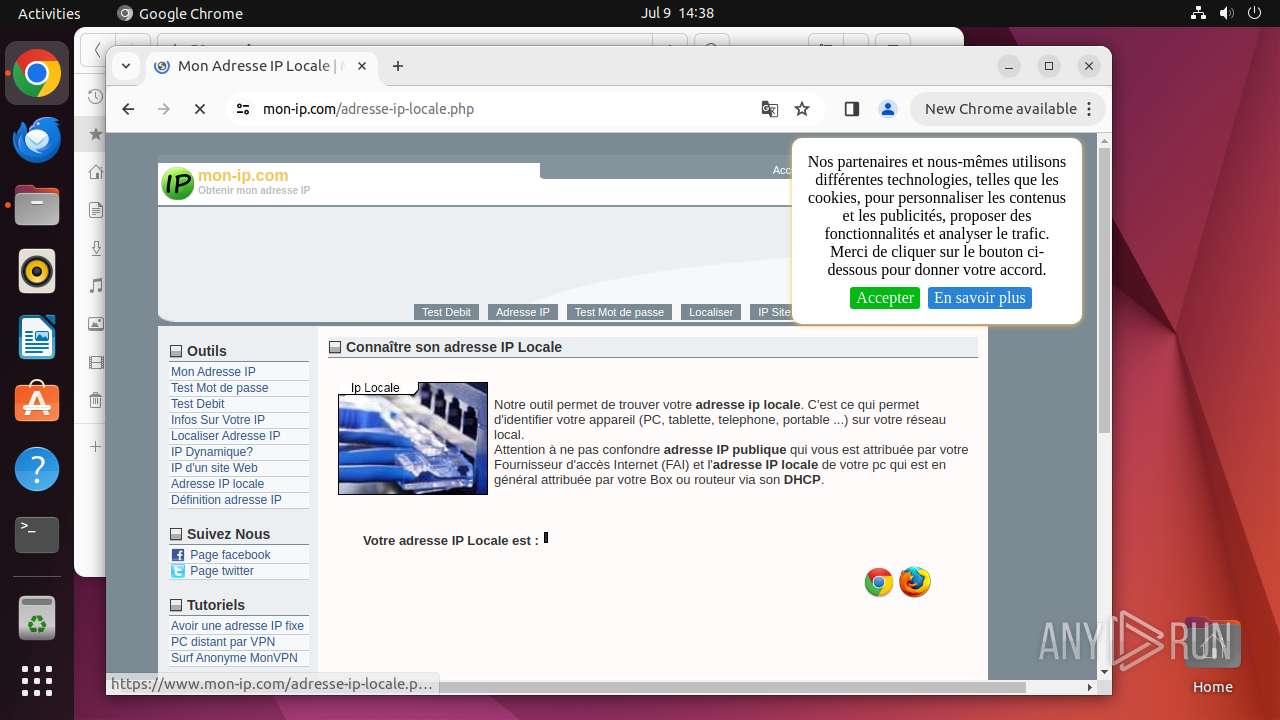
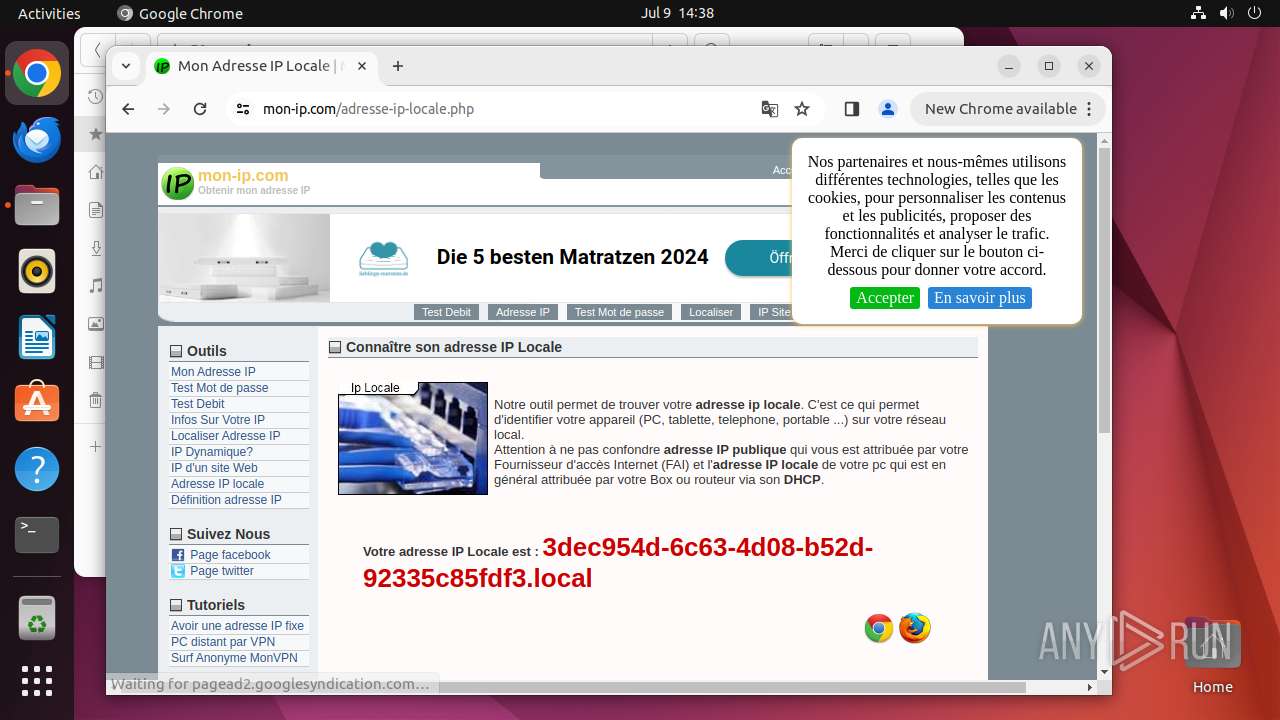
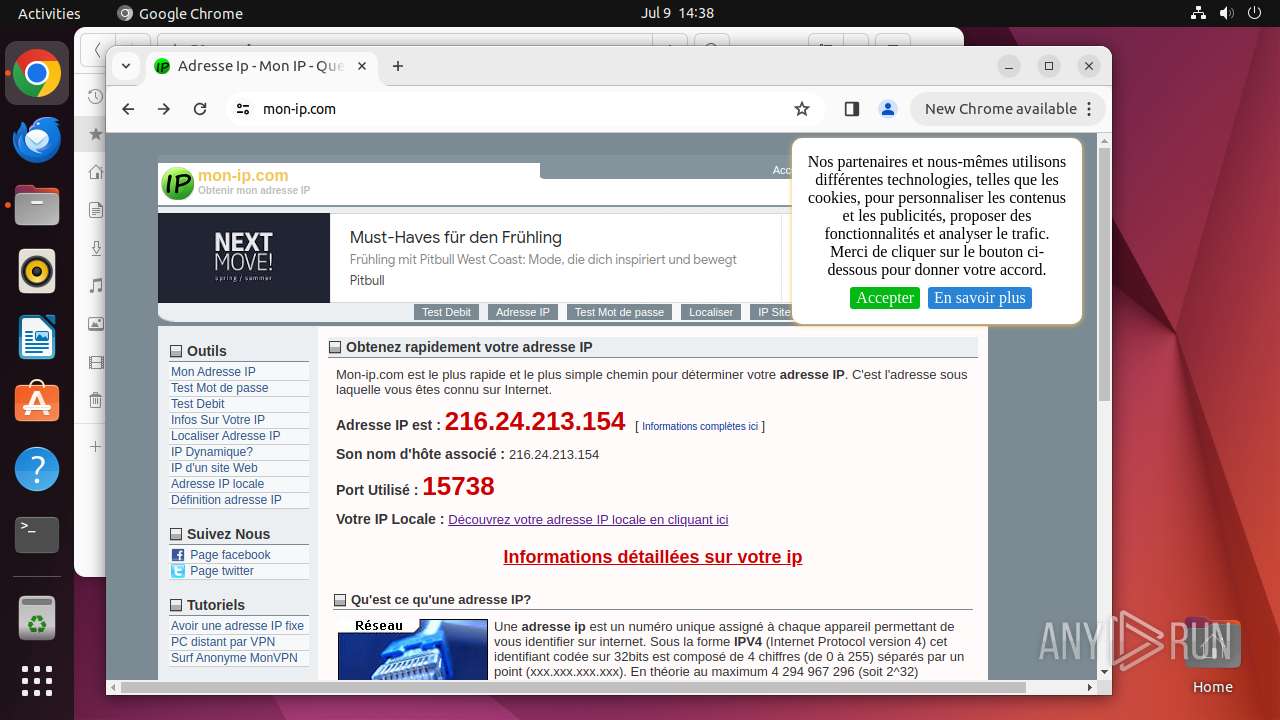
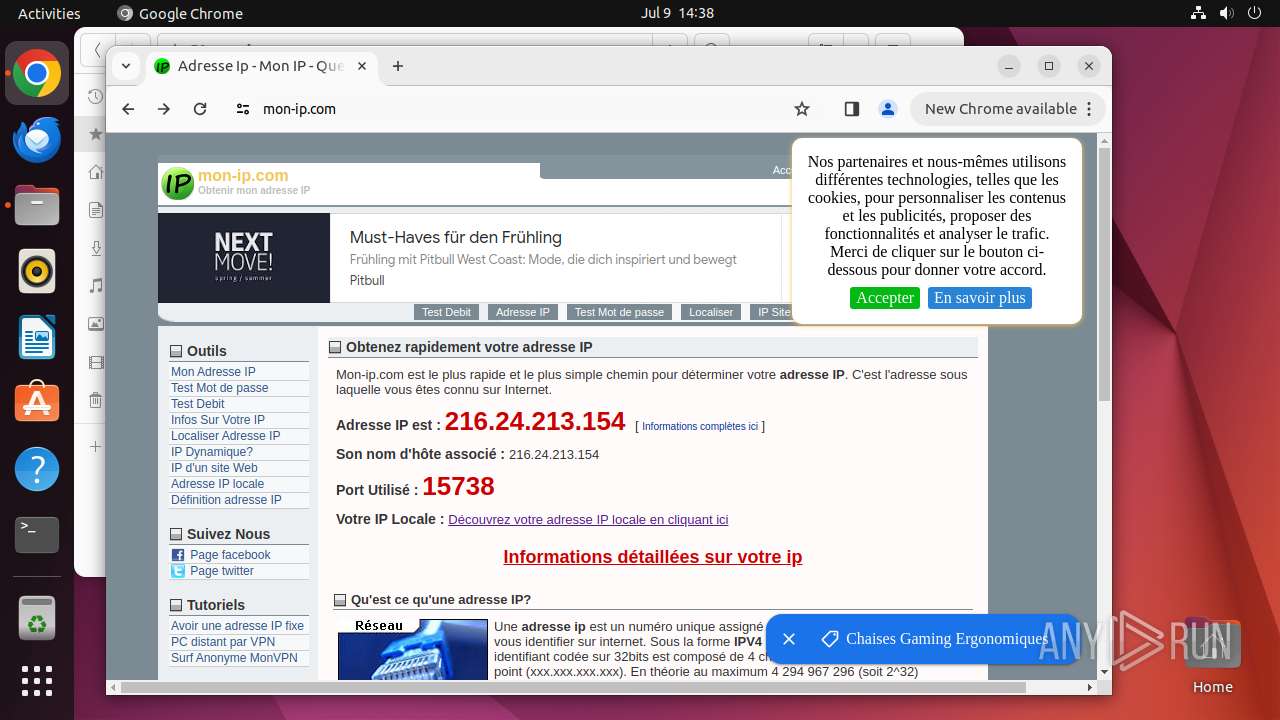
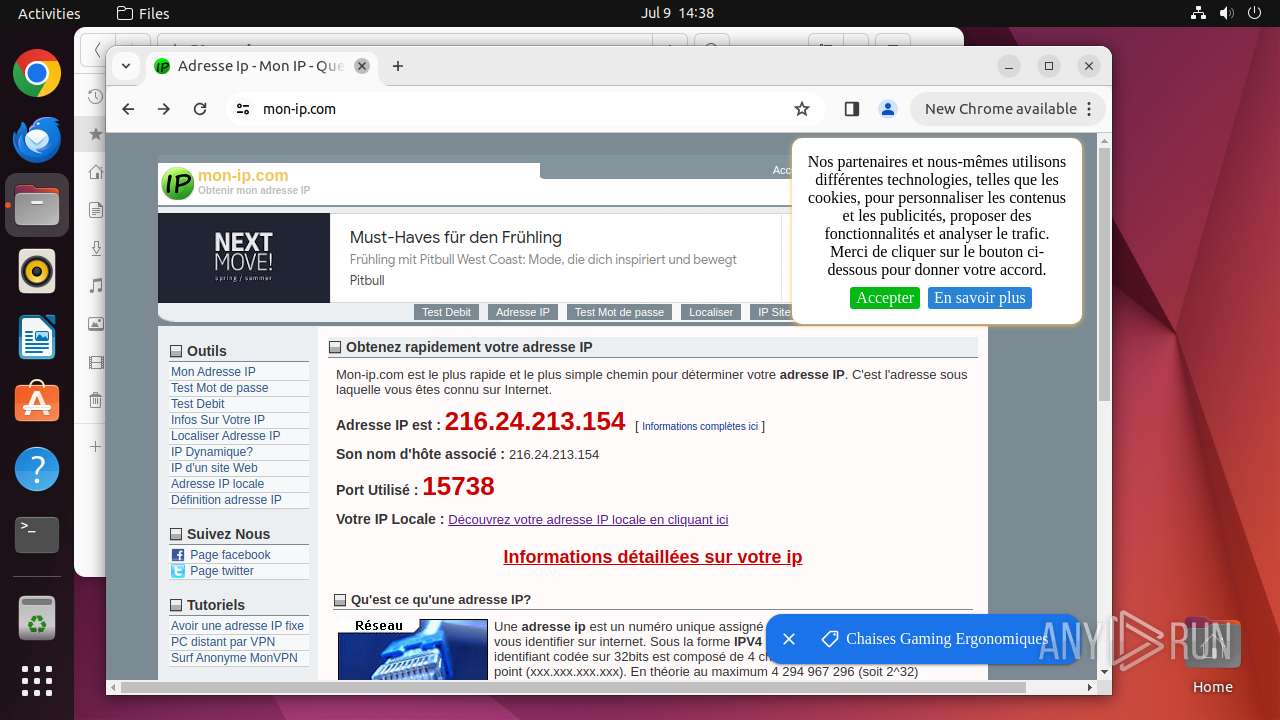
| 12970 | /usr/bin/google-chrome-stable | /opt/google/chrome/chrome | gnome-shell | |
User: user Integrity Level: UNKNOWN Exit code: 13026 | ||||
| 12973 | readlink -f /usr/bin/google-chrome-stable | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12974 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 482 | ||||
Executable files
7
Suspicious files
712
Text files
48
Unknown types
89
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12932 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | binary | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/Default/Extension State/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12970 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
82
DNS requests
99
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/niikhdgajlphfehepabhhblakbdgeefj/1.7e329996ac41ced208e9d13f023bb152b55bd2c4d158f9482a7dd65d6eb1b03b/1.1dbb3990e16ba546e7367ef84c38441173fbb5a7b570bb9b183d3b6faaeb622d/88ff621e99681d7d7370a35f49475234b599bc668125fe32f68ff670acb0dfc1.puff | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gp5sujfha3uuuceulcjdrip7ga_20240628.649506826.14/obedbbhbpmojnkanicioggnmelmoomoc_20240628.649506826.14_all_ENGB500000_adhq4rfezapaqpsy653jepwymmeq.crx3 | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lvx4ng4qhhp4kpddwmwjgzrumu_2024.6.5.140657/eeigpngbgcognadeebkilcpcaedhellh_2024.06.05.140657_all_ccj7nw5iotmqmvpbhiiji4wfca.crx3 | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/kiabhabjdbkjdpjbpigfodbdjmbglcoo/1.f6cc30e6a2d15e778f6701074d1f4b4505db1f516e06c9969160e0d6c62c5837/1.153e9301be7e862a33e2cab936a0a97e2f8bdf2dae1be516d6fe8a5f184ce028/abe599c5e7c450e0e3bfebef2d768b2903a8f50780214f1b81006d26589c3fc9.puff | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.900410b03a2b6d9b98abb85833bbb2a557cbda8fe7df65fb688a9ca04a3f6d40/1.ff0e88cc4f10c87e09be229b861a5ce2909b22d830b3634c51e29b150342eee0/427368a661ed32d5b6002fd830e70c8056dcd40649a6bf5666360d93073e0362.puff | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.2e871143703b862fcdf558b45cfe02a93a2cb74518b30f4c1e0f07753b0823b8/1.888ebbd183d017421d0f23a0a1ea9eaedffefd772878d86c67536c138ef62ada/9d1d7c69912e231efc605fa136885de4703daed3755e6a972a7dd67b6cc15b0b.puff | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.a9dcdb84b51dfb80ecd937f7775193f7c50fab755f256202e382db7a49207190/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/cf7a3395d1c87e8889d87c7cfe0924969f2dfcdb282fd8d974db8069017ee67d.puff | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac3ovrbpjgoenwowvckrpmdglcha_455/lmelglejhemejginpboagddgdfbepgmp_455_all_ZZ_cwlealxyci4dby37uu5pwx3ljq.crx3 | unknown | — | — | unknown |
13026 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acfa6xneni6qrevfefhktmfe36qq_8919/hfnkpimlhhgieaddgfemjhofmfblmnib_8919_all_jz2stbm7pdyhcevlboqo7cfa3a.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | malicious |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
13026 | chrome | 142.250.186.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
12970 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
13026 | chrome | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
13026 | chrome | 216.58.206.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
13026 | chrome | 142.250.184.228:443 | www.google.com | — | — | whitelisted |
13026 | chrome | 142.250.186.99:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
186.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| unknown |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |