| File name: | wsock32.dll |
| Full analysis: | https://app.any.run/tasks/c6d827e0-0e21-430b-b044-c023fc9db8f8 |
| Verdict: | Suspicious activity |
| Analysis date: | January 21, 2020, 13:19:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | A094EFFBB91BA2002F815340EDA30890 |
| SHA1: | 968DA067C976004DE73087E641217C204B20AB3F |
| SHA256: | D7D35019CE0C03D97C32AB25A145371806CA2D1572AF1E5146EA886D41818850 |
| SSDEEP: | 384:ei3aNu94p4kfzjrl/sY8PUm11blufoUx/KULigYBktIFU8xTiUfXDe:f3aawD7fmHk90RCIVxiuXDe |
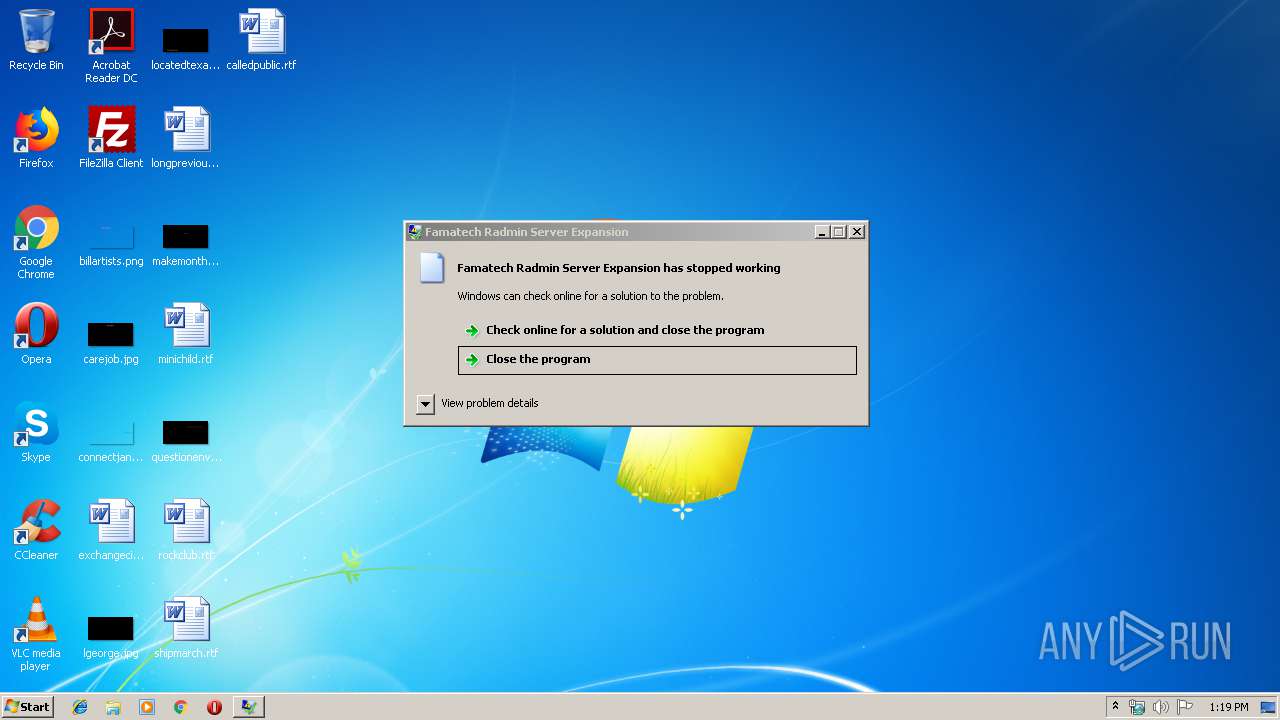
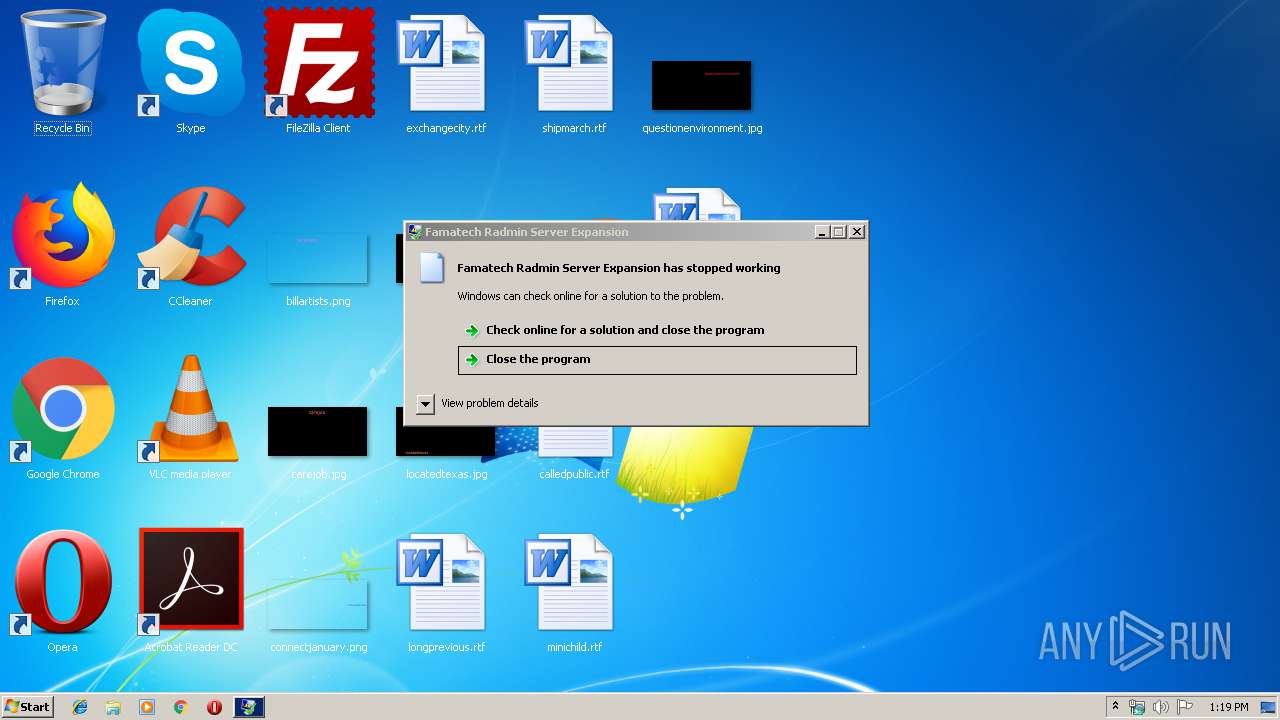
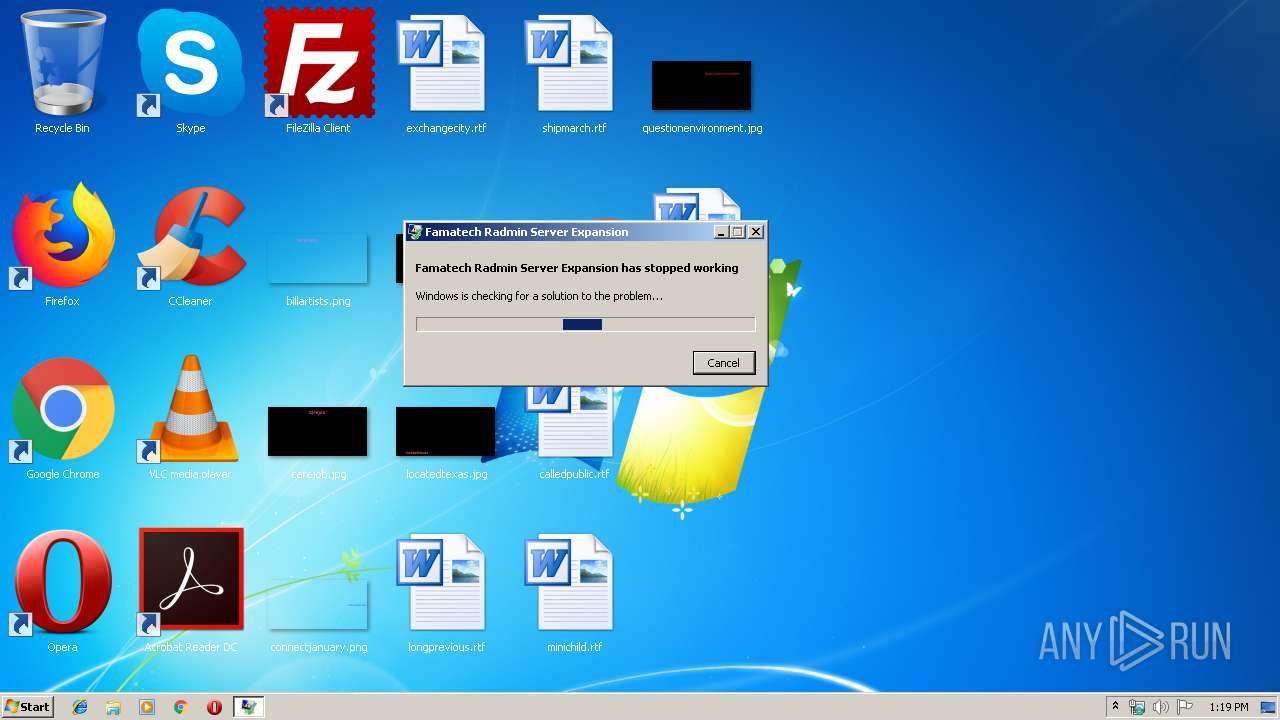
MALICIOUS
Loads dropped or rewritten executable
- WerFault.exe (PID: 1724)
SUSPICIOUS
No suspicious indicators.INFO
Loads main object executable
- rundll32.exe (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 21504 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5bf4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.0.0 |
| ProductVersionNumber: | 2.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Famatech Fan Club |
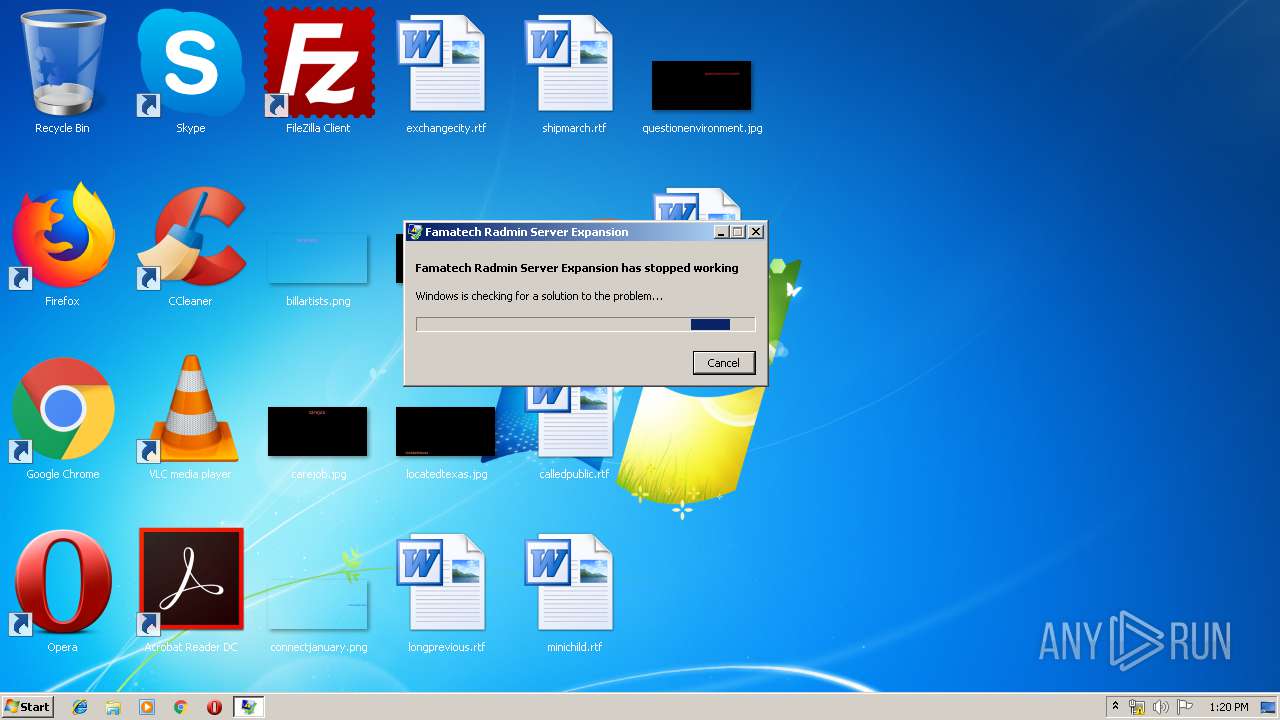
| FileDescription: | Famatech Radmin Server Expansion |
| FileVersion: | 2.3.0.0 |
| LegalCopyright: | © 2007-2010 Famatech Fan Club |
| ProductName: | NTS |
| ProductVersion: | 2.3.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Famatech Fan Club |
| FileDescription: | Famatech Radmin Server Expansion |
| FileVersion: | 2.3.0.0 |
| LegalCopyright: | © 2007-2010 Famatech Fan Club |
| ProductName: | NTS |
| ProductVersion: | 2.3.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000052B4 | 0x00005400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32359 |
DATA | 0x00007000 | 0x000000BC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.70325 |
BSS | 0x00008000 | 0x00000B35 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00009000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.30346 |
.edata | 0x0000A000 | 0x0000059B | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.0653 |
.reloc | 0x0000B000 | 0x00000634 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.78703 |
.rsrc | 0x0000C000 | 0x000002D8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 2.52848 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.36272 | 632 | UNKNOWN | UNKNOWN | RT_VERSION |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
ntdll.dll |
oleaut32.dll |
user32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
accept | 1 | 0x000059F4 |
bind | 2 | 0x000059FC |
closesocket | 3 | 0x00005A04 |
connect | 4 | 0x00005A0C |
getpeername | 5 | 0x00005A14 |
getsockname | 6 | 0x00005A1C |
getsockopt | 7 | 0x00005A24 |
htonl | 8 | 0x00005A2C |
htons | 9 | 0x00005A34 |
inet_addr | 10 | 0x00005A3C |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1724 | C:\Windows\system32\WerFault.exe -u -p 2480 -s 180 | C:\Windows\system32\WerFault.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\wsock32.dll", accept | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30
Read events
30
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER8505.tmp.appcompat.txt | — | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER8535.tmp.hdmp | — | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER85C3.tmp.mdmp | — | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER7F5.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_wso_a811f879c598d81d23a622277fff703935f38f_cab_0686861d\WER8535.tmp.hdmp | dmp | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_wso_a811f879c598d81d23a622277fff703935f38f_cab_0686861d\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rundll32.exe.2480.dmp | dmp | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_wso_a811f879c598d81d23a622277fff703935f38f_cab_0686861d\WER85C3.tmp.mdmp | dmp | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_wso_a811f879c598d81d23a622277fff703935f38f_cab_0686861d\WER7F5.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 1724 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_wso_a811f879c598d81d23a622277fff703935f38f_cab_0686861d\WER8505.tmp.appcompat.txt | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1724 | WerFault.exe | GET | — | 52.158.209.219:80 | http://watson.microsoft.com/StageOne/Generic/BEX/rundll32_exe_wsock32_dll/6_1_7600_16385/4a5bc637/StackHash_0a9e/0_0_0_0/00000000/00000000/c0000005/00000008.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1724 | WerFault.exe | 52.158.209.219:80 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1724 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
1724 | WerFault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |