| File name: | EscapeFromTarkovStarter.exe |
| Full analysis: | https://app.any.run/tasks/0c02b3fe-5191-4ea9-9c54-a67845aededc |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 08:35:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 738B100522D537941DC74A2EB8323900 |
| SHA1: | 35197F603021E51D8610E87B99D0AFBDEC92BD89 |
| SHA256: | D7C80808C1951655513584A842789267BB42E5B65B9643BB3951545C13816B9D |
| SSDEEP: | 49152:Fx2w4VB8LiqjLzKe3QcOZSpVYeOvSBH7z5Qg18A/gc9Po4:Fxz4z4iSLVyY6Sz98fc9A4 |
MALICIOUS
Application was dropped or rewritten from another process
- EscapeFromTarkovLoader.exe (PID: 2656)
Changes settings of System certificates
- EscapeFromTarkovStarter.exe (PID: 1632)
SUSPICIOUS
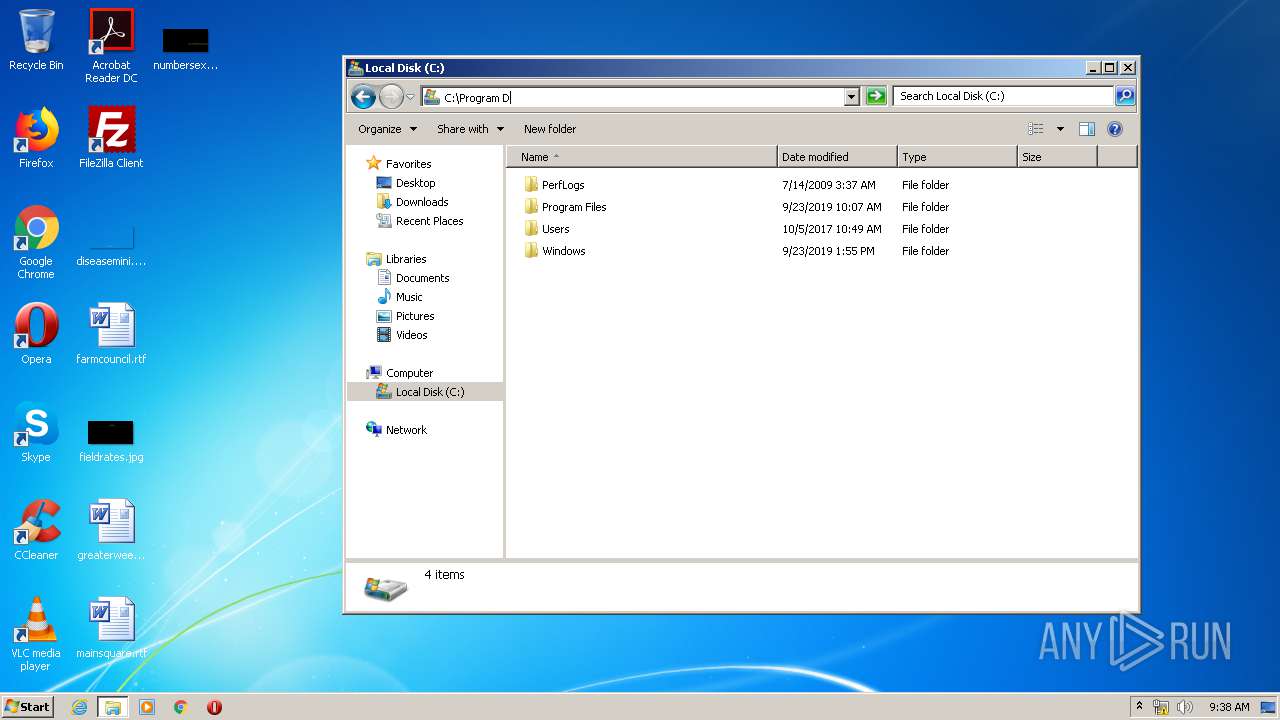
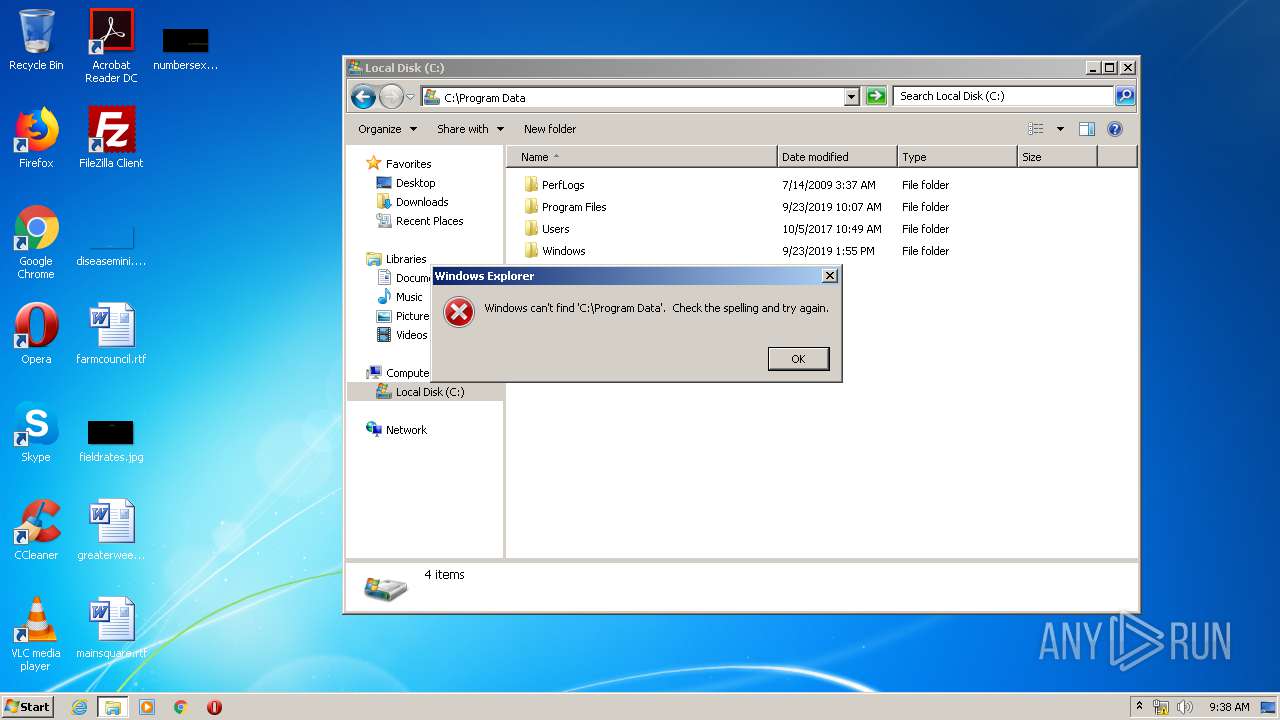
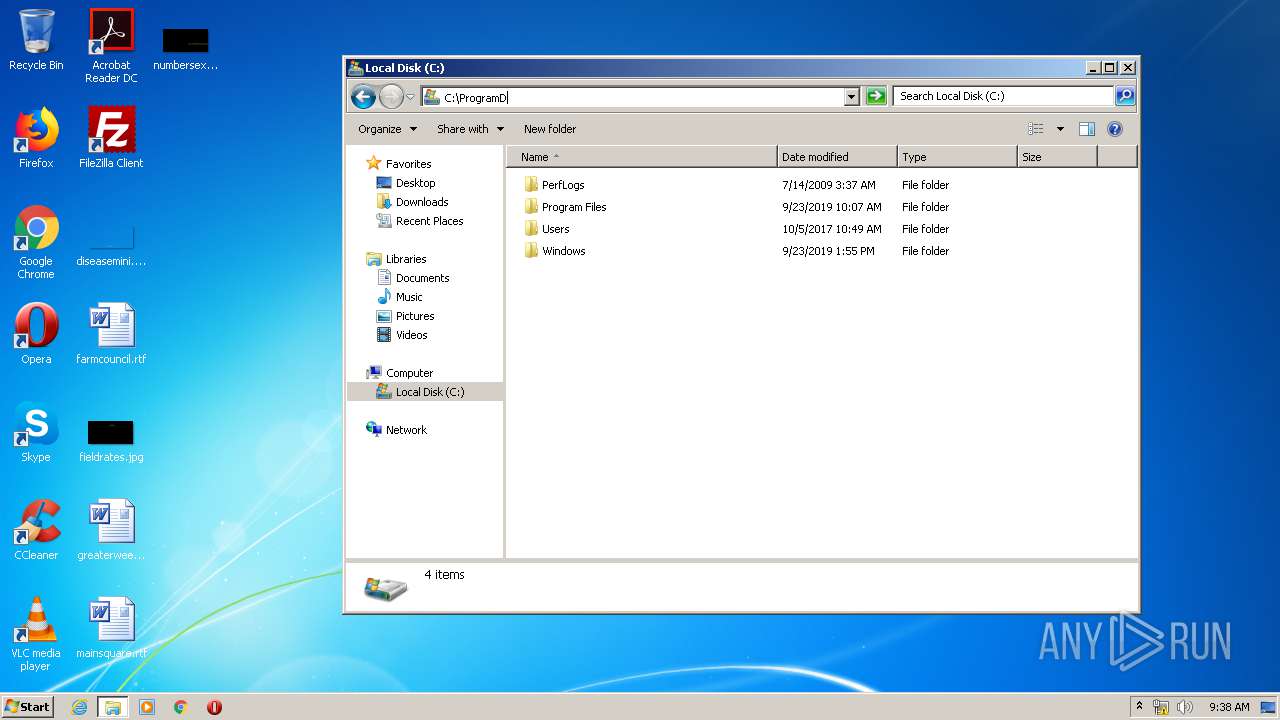
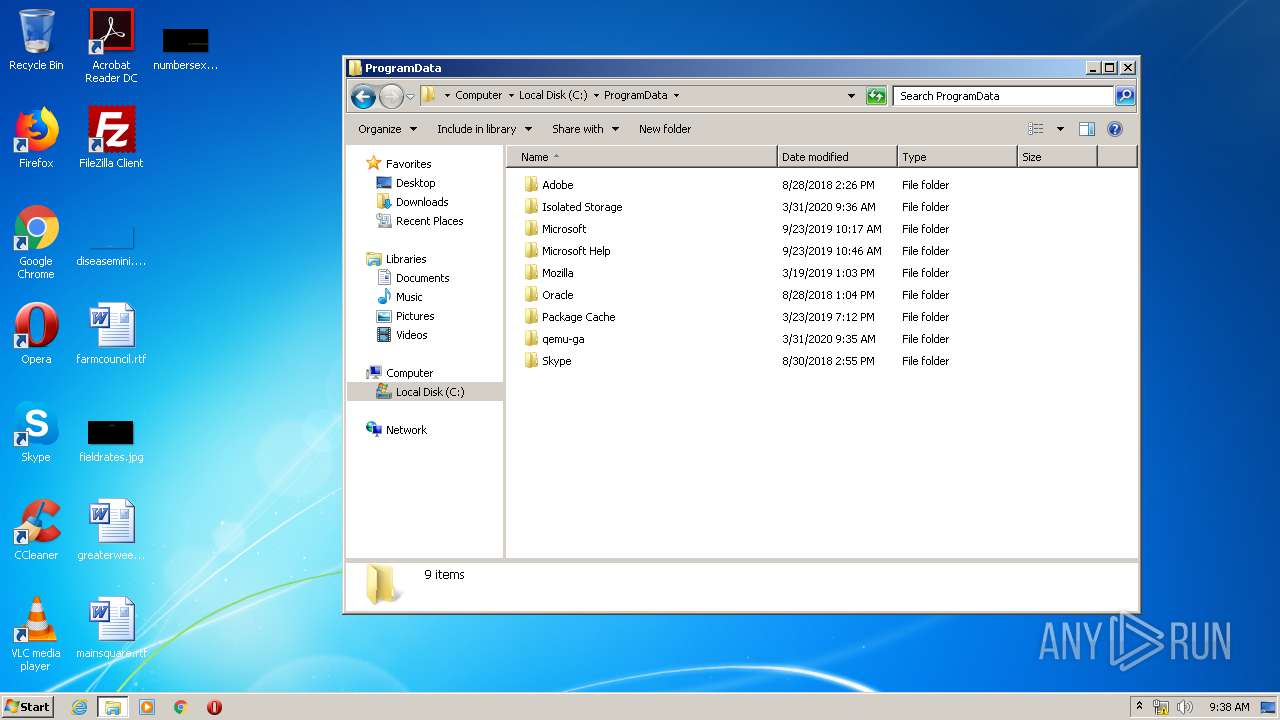
Creates files in the program directory
- EscapeFromTarkovStarter.exe (PID: 1632)
- EscapeFromTarkovLoader.exe (PID: 2656)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3120)
Reads Environment values
- EscapeFromTarkovStarter.exe (PID: 1632)
- EscapeFromTarkovLoader.exe (PID: 2656)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3120)
Executable content was dropped or overwritten
- EscapeFromTarkovStarter.exe (PID: 1632)
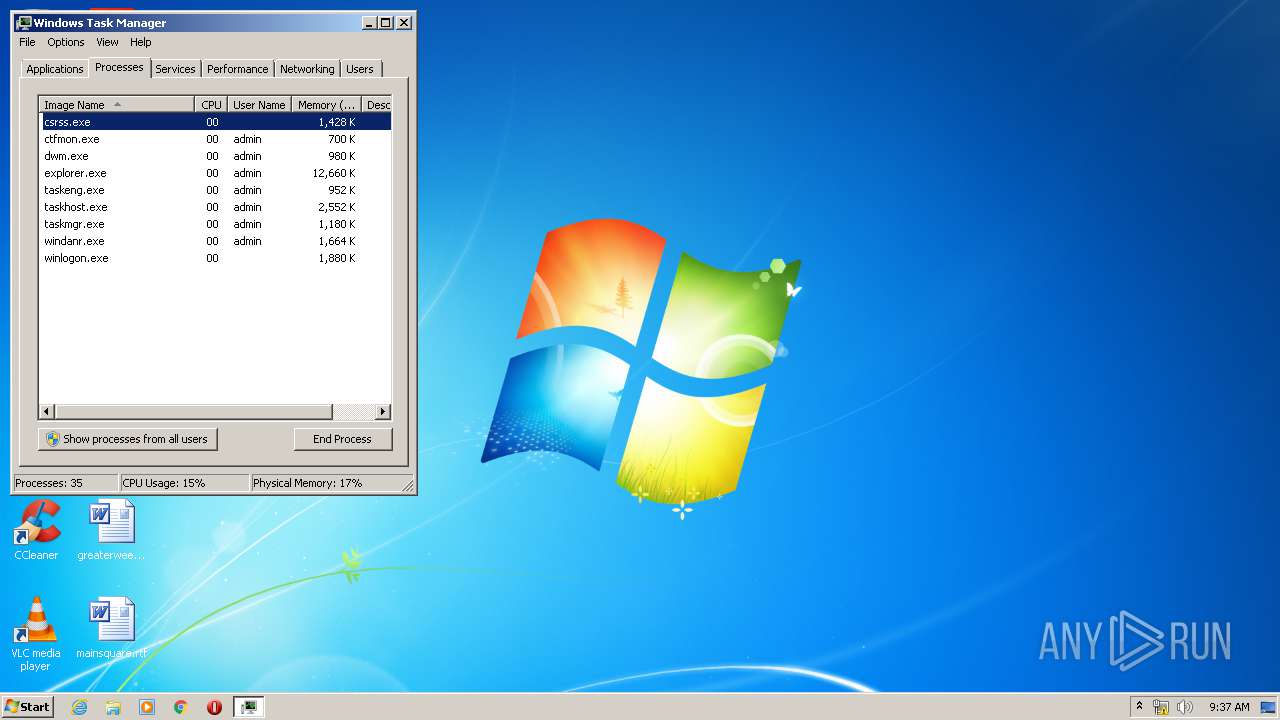
Uses TASKLIST.EXE to query information about running processes
- EscapeFromTarkovLoader.exe (PID: 2656)
Starts CMD.EXE for commands execution
- EscapeFromTarkovLoader.exe (PID: 2656)
Executed via COM
- DllHost.exe (PID: 340)
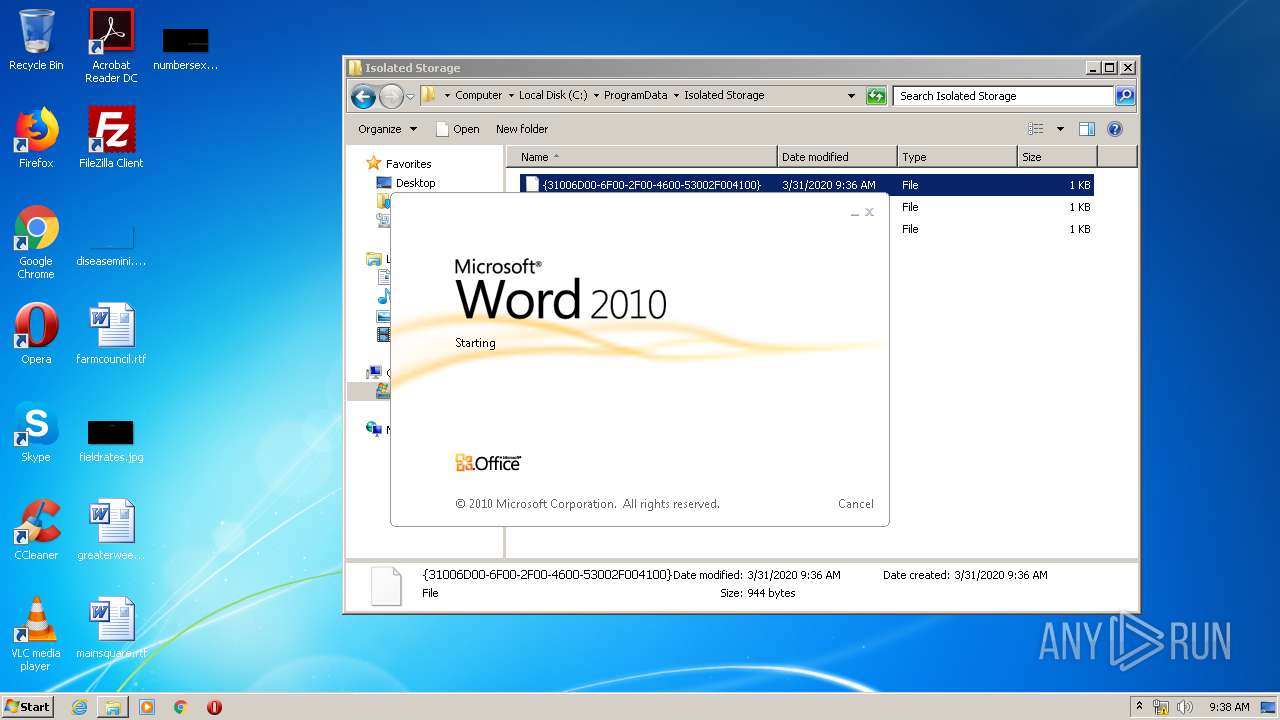
Starts Microsoft Office Application
- rundll32.exe (PID: 1140)
Adds / modifies Windows certificates
- EscapeFromTarkovStarter.exe (PID: 1632)
INFO
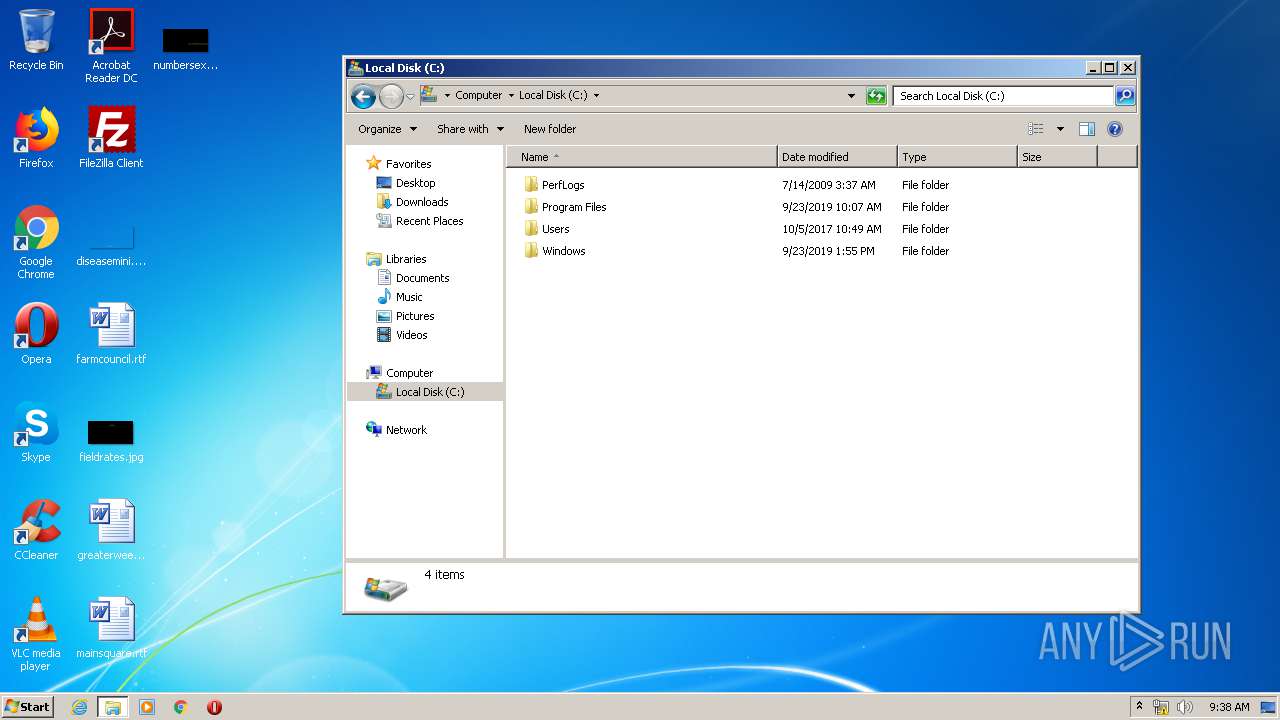
Manual execution by user
- explorer.exe (PID: 1740)
- taskmgr.exe (PID: 572)
- iexplore.exe (PID: 2868)
- rundll32.exe (PID: 1140)
- rundll32.exe (PID: 180)
Reads settings of System Certificates
- EscapeFromTarkovStarter.exe (PID: 1632)
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 2868)
Reads Internet Cache Settings
- iexplore.exe (PID: 2868)
- iexplore.exe (PID: 3108)
Changes internet zones settings
- iexplore.exe (PID: 2868)
Creates files in the user directory
- iexplore.exe (PID: 3108)
- WINWORD.EXE (PID: 1488)
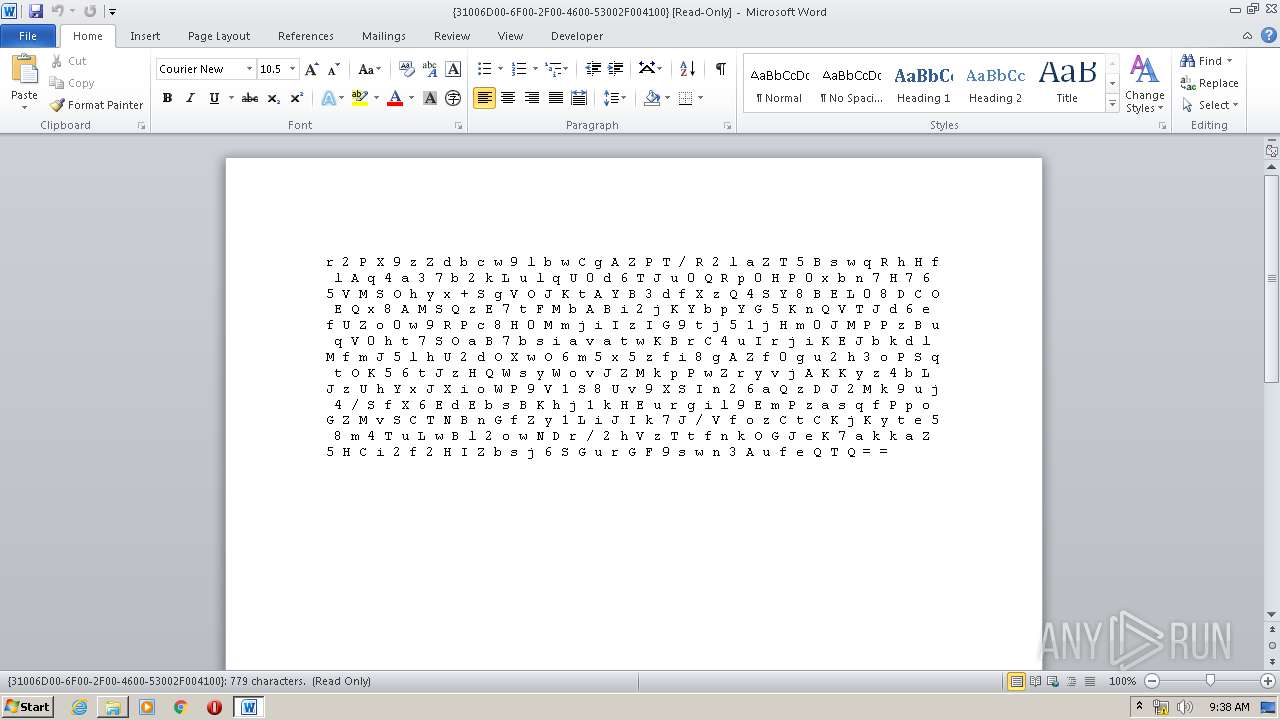
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3108)
Reads internet explorer settings
- iexplore.exe (PID: 3108)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2868)
Changes settings of System certificates
- iexplore.exe (PID: 2868)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2083:04:08 05:36:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 267264 |
| InitializedDataSize: | 5632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x67a000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | EscapeFromTarkovLoader |
| FileVersion: | 1.0.0.0 |
| InternalName: | EscapeFromTarkovStarter.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | EscapeFromTarkovStarter.exe |
| ProductName: | EscapeFromTarkovLoader |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 02-Mar-1947 21:08:34 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | EscapeFromTarkovLoader |
| FileVersion: | 1.0.0.0 |
| InternalName: | EscapeFromTarkovStarter.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | EscapeFromTarkovStarter.exe |
| ProductName: | EscapeFromTarkovLoader |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 02-Mar-1947 21:08:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00002000 | 0x00042000 | 0x0001F80D | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.98381 | |
b\x01 | 0x00044000 | 0x00000162 | 0x0000018C | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.3535 |
X\x11 | 0x00046000 | 0x00001158 | 0x0000075D | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.81818 |
\x0c | 0x00048000 | 0x0000000C | 0x0000000F | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.77356 |
.imports | 0x0004A000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.14864 |
.rsrc | 0x0004C000 | 0x00002000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00708 |
.themida | 0x0004E000 | 0x003E8000 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.boot | 0x00436000 | 0x00242600 | 0x00242600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96138 |
.taggant | 0x0067A000 | 0x00002200 | 0x00002014 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.82949 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06548 | 3372 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
kernel32.dll |
mscoree.dll |
Total processes
126
Monitored processes
49
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
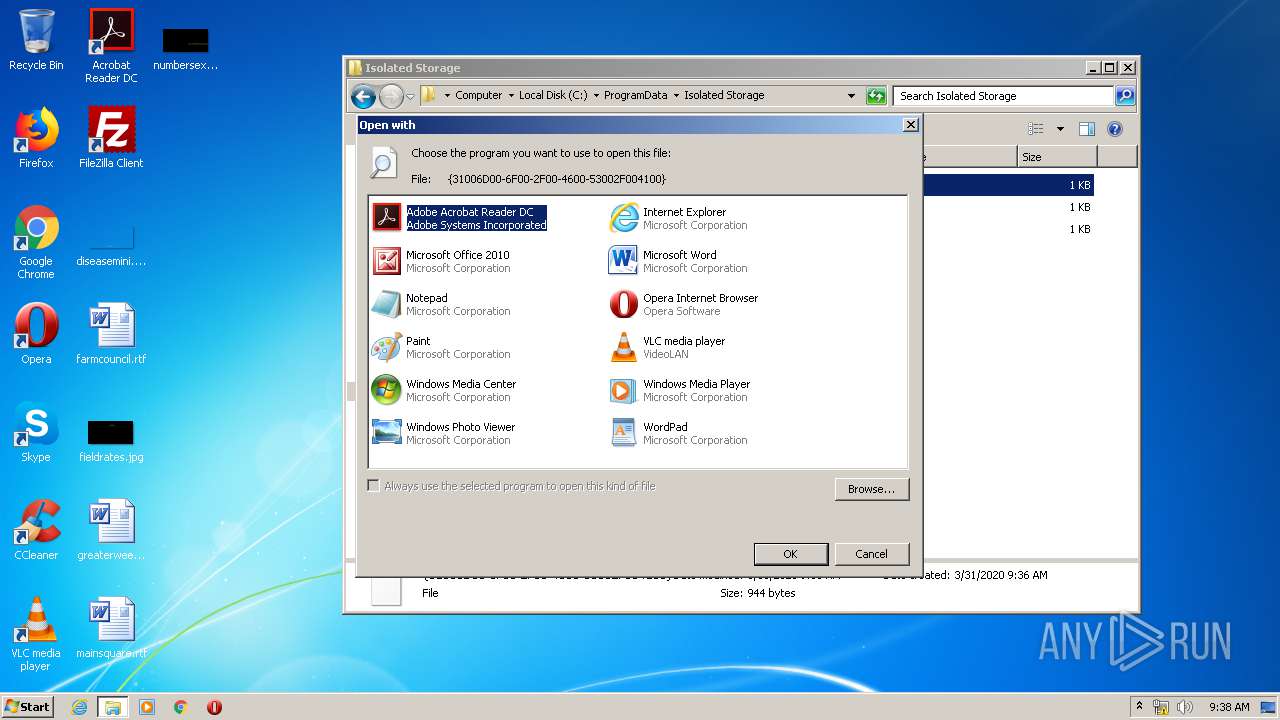
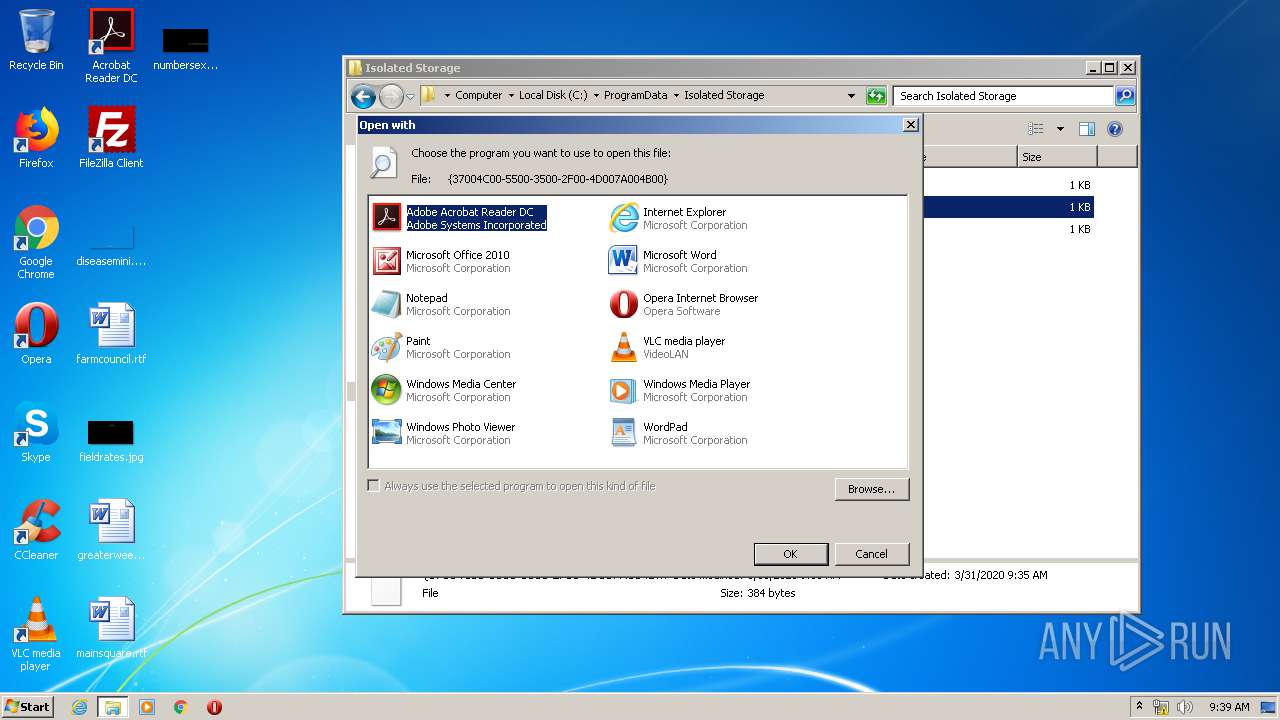
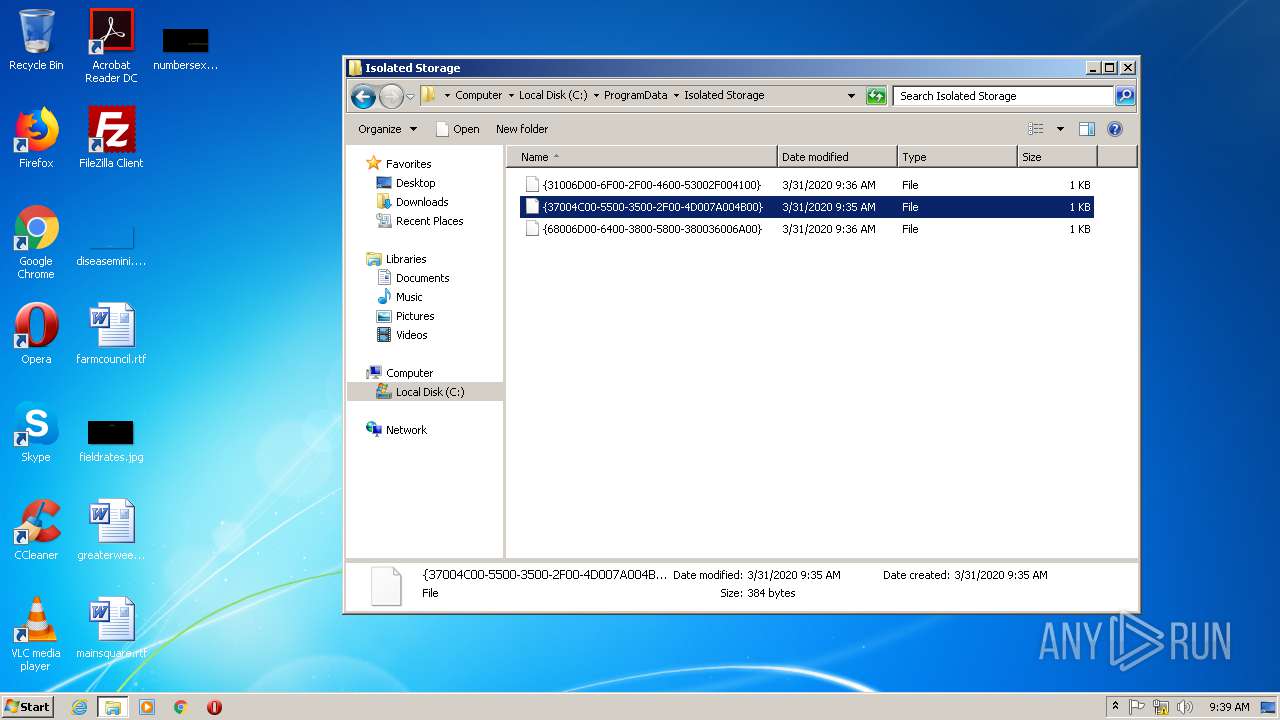
| 180 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\ProgramData\Isolated Storage\{37004C00-5500-3500-2F00-4D007A004B00} | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 340 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 488 | "tasklist" /V | C:\Windows\system32\tasklist.exe | — | EscapeFromTarkovLoader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | "tasklist" /V | C:\Windows\system32\tasklist.exe | — | EscapeFromTarkovLoader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | "tasklist" /V | C:\Windows\system32\tasklist.exe | — | EscapeFromTarkovLoader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
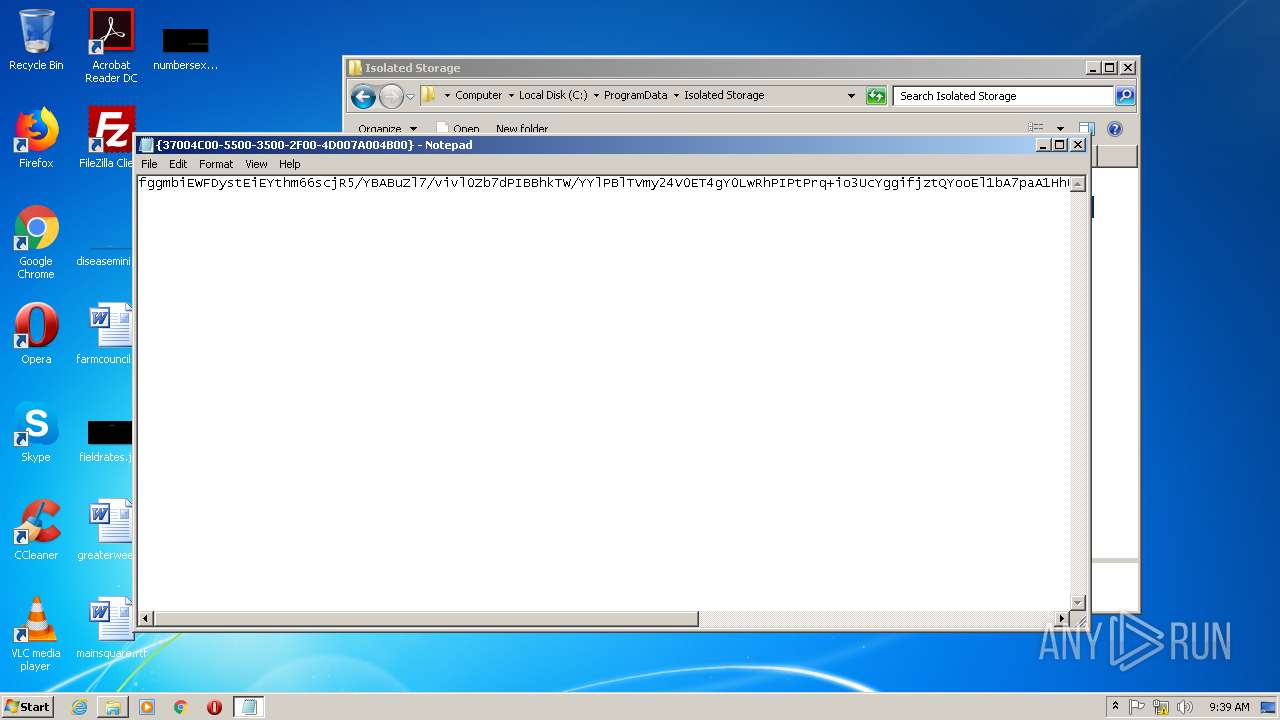
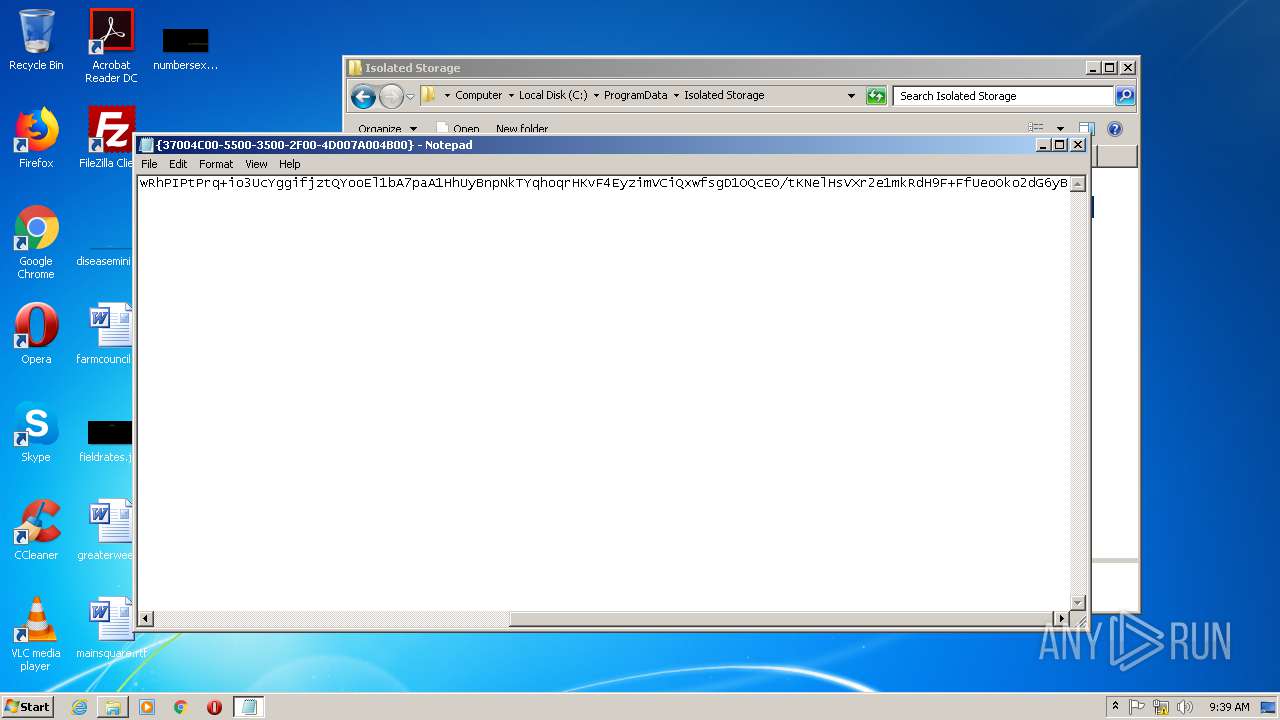
| 588 | "C:\Windows\system32\NOTEPAD.EXE" C:\ProgramData\Isolated Storage\{37004C00-5500-3500-2F00-4D007A004B00} | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "tasklist" /V | C:\Windows\system32\tasklist.exe | — | EscapeFromTarkovLoader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "tasklist" /V | C:\Windows\system32\tasklist.exe | — | EscapeFromTarkovLoader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
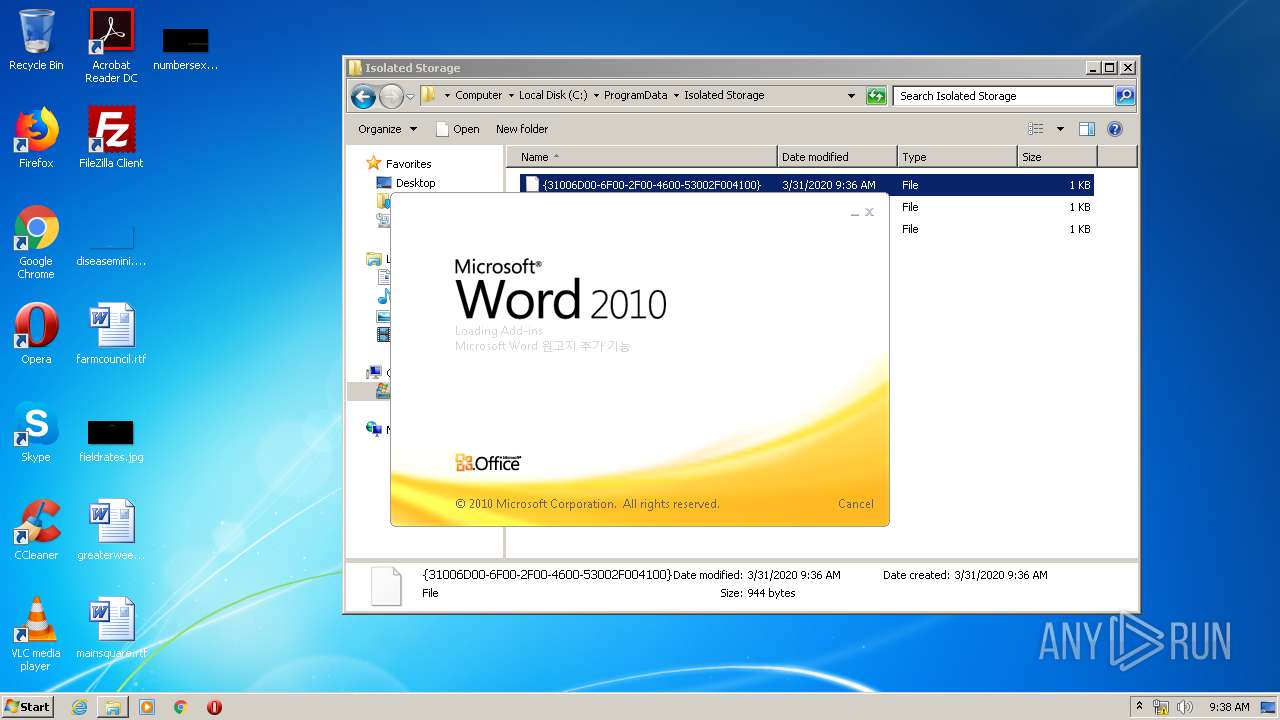
| 1140 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\ProgramData\Isolated Storage\{31006D00-6F00-2F00-4600-53002F004100} | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 842
Read events
3 076
Write events
1 623
Delete events
143
Modification events
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_CLASSES_ROOT\CID\{31005100-4F00-7300-4200-52002B003000} |
| Operation: | write | Name: | 1 |
Value: fggmbiEWFDystEiEYthm66scjR5/YBABuZl7/vivl0aJWFQnvAQYDJn8qSRw2kN/y1kUc802lgv3Wh3siEXFly/gvRI0pJLGysaEheGYHGBH9GgVkso2WK9cMoT9DofNMiQzoycA/F0olUh+LRgzsA/XhLN+EwP1Sb8zMSelzWfZ9QCsQgiS6rJHtK8uHb7fBVF2elGu4t770jkROKFyUSaeTQQfQkuydK6cu22ojduH9Ec8oVDx+uQTO65xbL3QeckAaYl8qST9msL/V49acqRYKPqJ/53/oLrsxFCL57scYcTBufSgeQXQF3Dl7ZUXxwydiMOtR35wpsYf8DjYYgbSE3jM/6/2HSS185Jz5l5mPLcFLKRbrOqwUMlfpIxZshw+JC/AExp3beURjEtgS5jVEvqq6PFj735WTNLW1NoEtK+E87RJExcAZJYW0W/l01j2TFm0auTLMtqvDnJ24w== | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_CLASSES_ROOT\CID\{37004C00-5500-3500-2F00-4D007A004B00} |
| Operation: | write | Name: | 1 |
Value: fggmbiEWFDystEiEYthm66scjR5/YBABuZl7/vivl0Zb7dPIBBhkTW/YYlPBlTVmy24V0ET4gY0LwRhPIPtPrq+io3UcYggifjztQYooEl1bA7paA1HhUyBnpNkTYqhoqrHKvF4EyzimVCiQxwfsgD1OQcEO/tKNelHsVXr2e1mkRdH9F+FfUeoOko2dG6yB | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1632) EscapeFromTarkovStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EscapeFromTarkovStarter_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
13
Text files
60
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\GA03X9CD.txt | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5F73BM3P.txt | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QBGJHKLQ.txt | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BVV0I7NU.txt | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\-nK5HAtc03YD_-fIE4Q-t8DnnZY[1].js | — | |
MD5:— | SHA256:— | |||
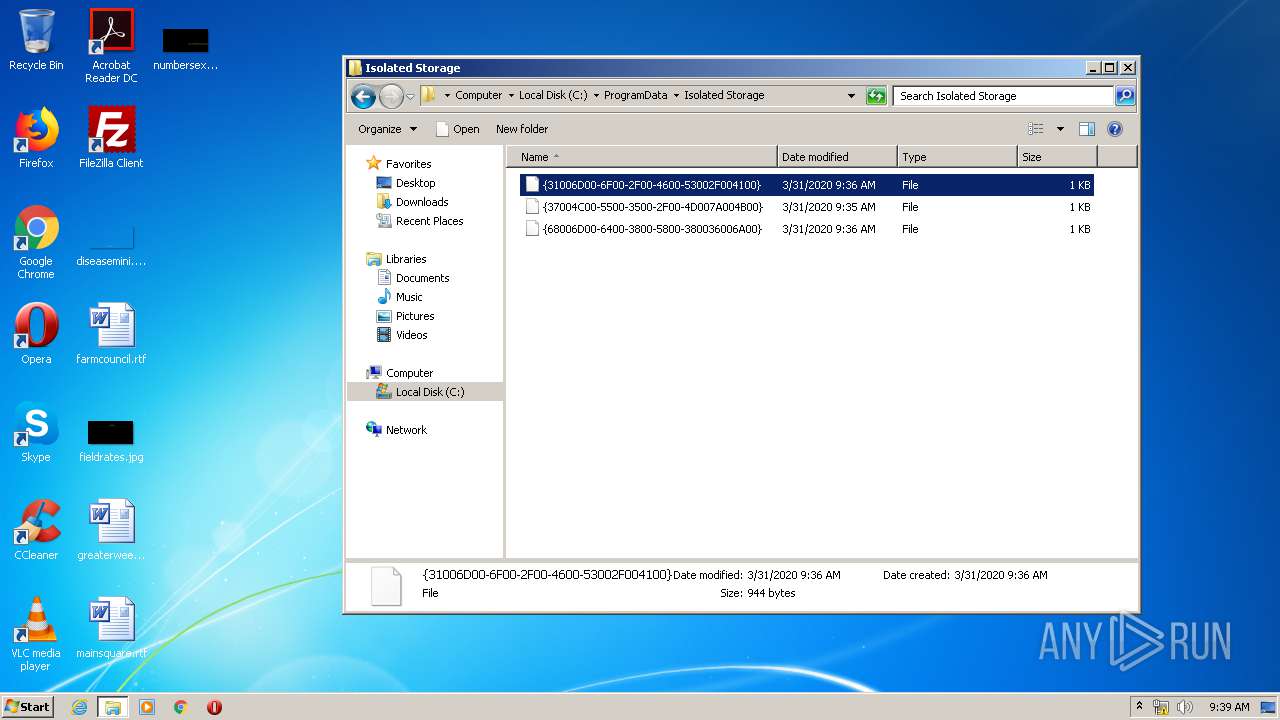
| 1632 | EscapeFromTarkovStarter.exe | C:\Users\admin\AppData\Local\Temp:{37004C00-5500-3500-2F00-4D007A004B00} | text | |
MD5:— | SHA256:— | |||
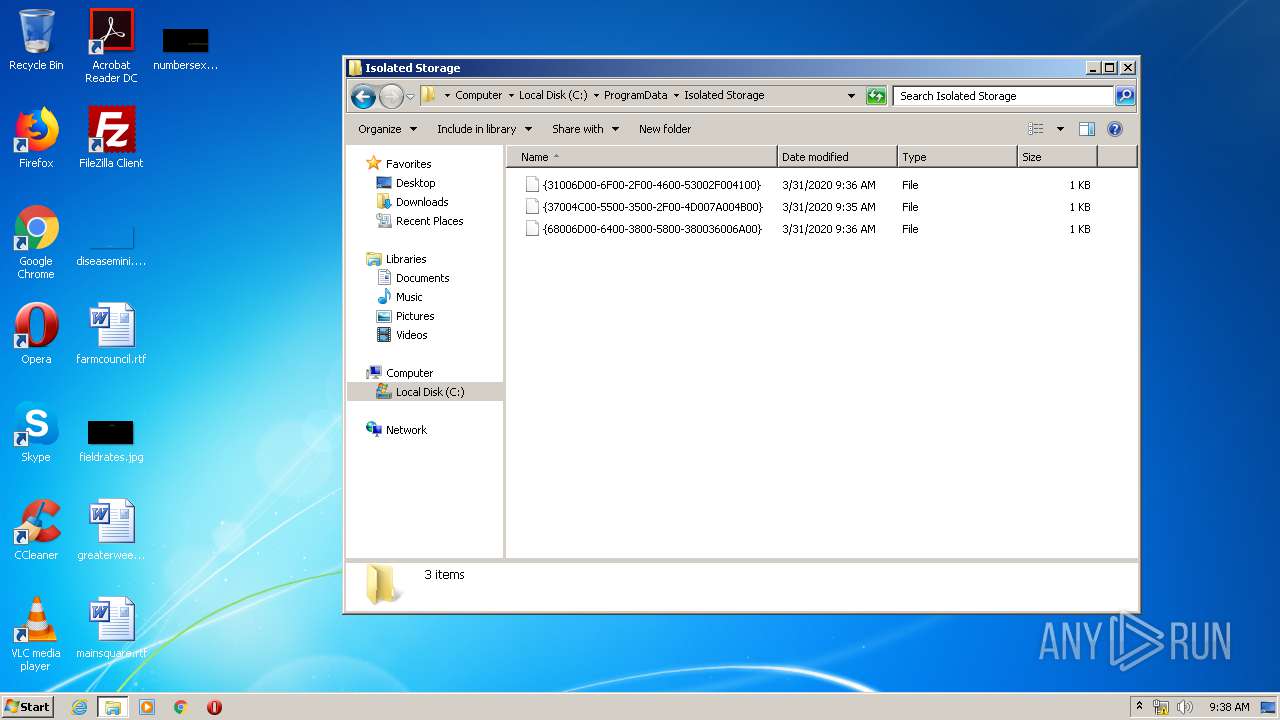
| 1632 | EscapeFromTarkovStarter.exe | C:\ProgramData\Isolated Storage\{37004C00-5500-3500-2F00-4D007A004B00} | binary | |
MD5:— | SHA256:— | |||
| 2656 | EscapeFromTarkovLoader.exe | C:\Users\admin\AppData\Local\Temp\EFT:{68006D00-6400-3800-5800-380036006A00} | text | |
MD5:— | SHA256:— | |||
| 2656 | EscapeFromTarkovLoader.exe | C:\ProgramData\Isolated Storage\{68006D00-6400-3800-5800-380036006A00} | binary | |
MD5:— | SHA256:— | |||
| 2656 | EscapeFromTarkovLoader.exe | C:\Users\admin\AppData\Local\Temp\EFT:{31006D00-6F00-2F00-4600-53002F004100} | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
20
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Z/2r/cj,nj/GTd5evTp2v9quFX_8_4U14MoprA.js | US | text | 816 b | whitelisted |
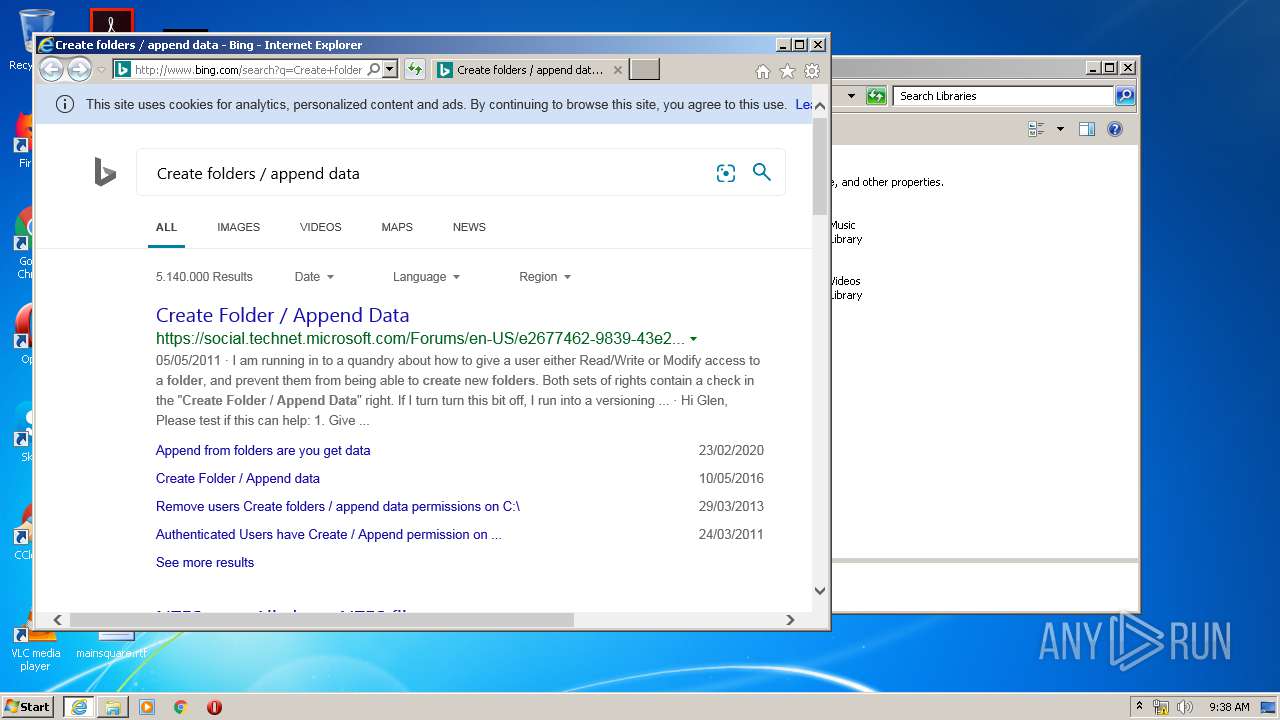
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=Create+folders+%2F+append+data&src=IE-TopResult&FORM=IE11TR&conversationid= | US | html | 44.6 Kb | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Z/2c/cj,nj/jkkMLrYXQVEFzxKwxLIvF320v4s.js | US | text | 773 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5g/cj,nj/D8nShhiaHwwY7S6Dowtg0f0NCMg.js?bu=EpMhqyHMINcgqQXrIO0guyHcIPYg-iClIakhnCH6H5gfmh-JIA | US | text | 5.38 Kb | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/3P/pq/cj,nj/lwQdVqXdJk4a1F5YBjGkU_5t-WY.js | US | text | 425 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=5BAC7008BDB5483F8E57F1E0DD9D87B7&CID=123DCDA47BDE667E2372C33A7AB567E8&Type=Event.CPT&DATA={"pp":{"S":"L","FC":70,"BC":239,"SE":-1,"TC":-1,"H":275,"BP":330,"CT":353,"IL":12},"ad":[-1,-1,776,528,1089,2352,1]}&P=SERP&DA=DUB02 | US | image | 609 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/4U/bO/cj,nj/Sk0R8mK1MeP5UBar_RwAJ9i5kf8.js | US | text | 651 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/4U/3K/cj,nj/iaYidzmUjFsGIP3s_5rfZiNv2uk.js | US | text | 529 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktop_ClearX_2x_030520.png?v=123 | US | image | 11.4 Kb | whitelisted |
3108 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/4U/bX/cj,nj/eHKUtiwjTlYrZ-E507QuFW2ZTLM.js | US | text | 665 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3108 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1632 | EscapeFromTarkovStarter.exe | 104.27.166.207:443 | escapefromtarkov.network | Cloudflare Inc | US | unknown |
2868 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3108 | iexplore.exe | 40.90.137.124:443 | login.live.com | Microsoft Corporation | US | unknown |
3108 | iexplore.exe | 40.126.1.142:443 | login.microsoftonline.com | Microsoft Corporation | US | unknown |
2868 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2868 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
escapefromtarkov.network |
| unknown |
www.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |