| File name: | invoice_898527.doc |
| Full analysis: | https://app.any.run/tasks/59388311-7ae1-44f0-bb70-d967bd814274 |
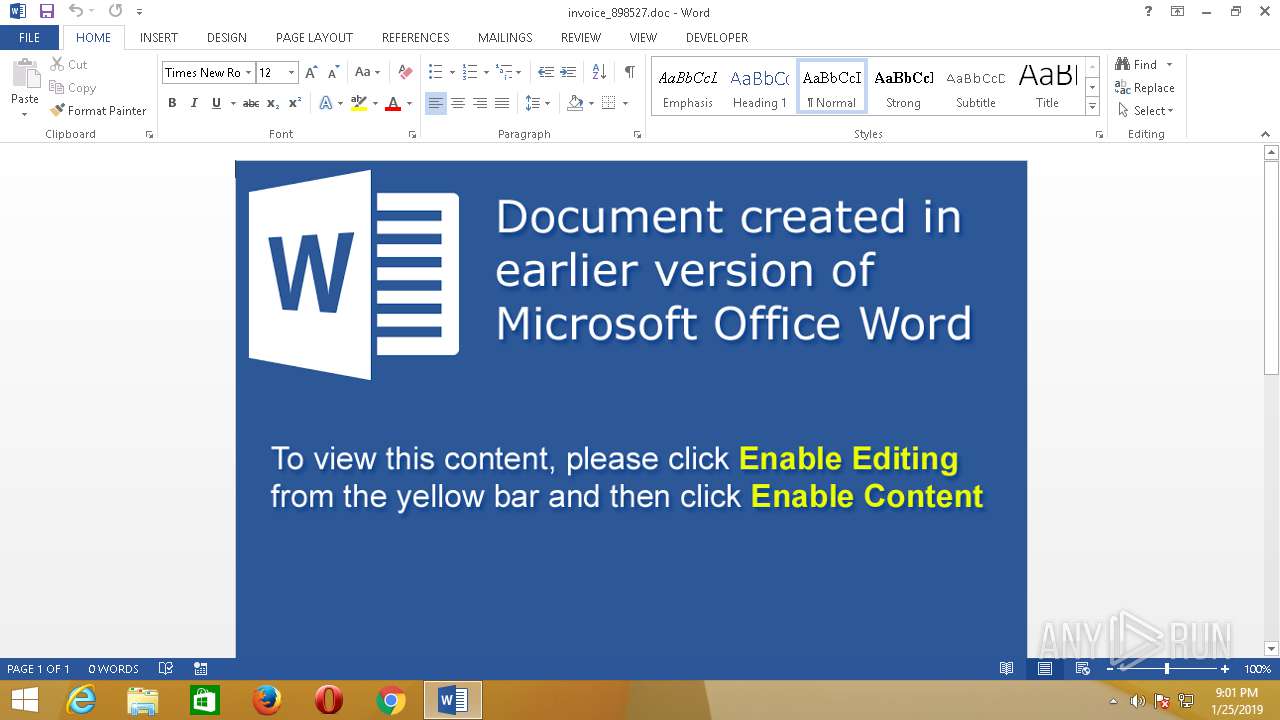
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2019, 05:00:46 |
| OS: | Windows 8.1 Professional (build: 9600, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | AB1A784D214F4DEB478796E8D7B93C29 |
| SHA1: | A574D159BA6BDB58D2FB7364E5DF5370B380424B |
| SHA256: | D7C29905B5A0DAD34210995D488EDBF9B5BC2F8BAA68D8A54EEA05E0FEB8C945 |
| SSDEEP: | 1536:j4n5WAp56LromUsO5ucuqIljPOs+jH8VuVY0n:jaOrXU55ucglqs28Yy0n |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
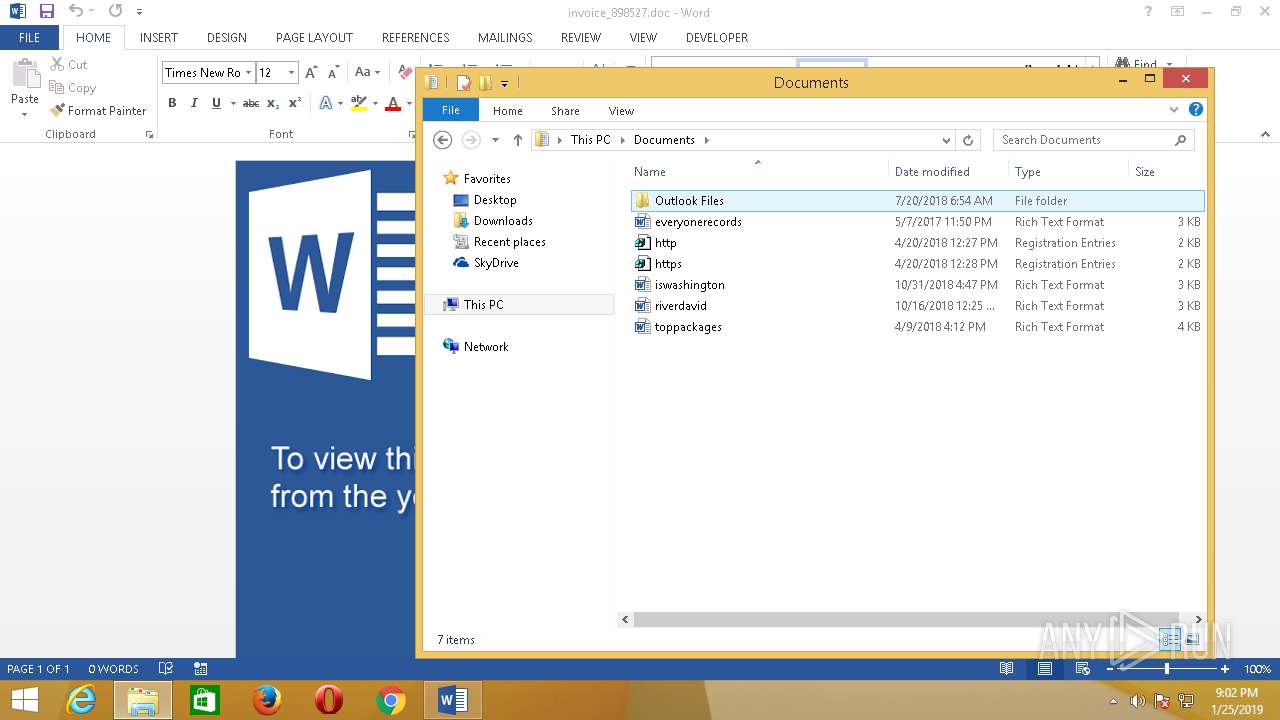
Creates files in the user directory
- WINWORD.EXE (PID: 2860)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x3f450766 |
| ZipCompressedSize: | 399 |
| ZipUncompressedSize: | 1503 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Manager: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Admin |
| RevisionNumber: | 2 |
| CreateDate: | 2019:01:14 14:59:00Z |
| ModifyDate: | 2019:01:14 14:59:00Z |
| Category: | - |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | - |
| Description: | - |
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2860 | "C:\Program Files\Microsoft Office 15\Root\Office15\WINWORD.EXE" /n "C:\Users\admin\Desktop\invoice_898527.doc.docm" /o "" | C:\Program Files\Microsoft Office 15\Root\Office15\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 15.0.4433.1506 Modules
| |||||||||||||||
Total events
907
Read events
482
Write events
416
Delete events
9
Modification events
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n3) |
Value: 6E3329002C0B000001000000000000007493EB2C34B5D40100000000 | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word |
| Operation: | write | Name: | MTTT |
Value: 2C0B0000BA15662C34B5D40100000000 | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 16) |
Value: 313629002C0B00000400000000000000FC063F2D34B5D4018C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 16) |
Value: 313629002C0B00000400000000000000FC063F2D34B5D4018C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\Roaming |
| Operation: | write | Name: | RoamingConfigurableSettings |
Value: B800000000000000803A0900E307010006001A000500010014009201000000000000000000000000201C0000201C00008051010080510100805101008051010080F4030080F4030080F403002C01000084030000805101000000000084030000805101000A0000001E0000001E000000000000000000000080510100010000000100000000000000000000000000000000000000008D2700008D2700008D2700010000000A00000080510100000030000000300000003000 | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\Roaming |
| Operation: | write | Name: | RoamingLastSyncTime |
Value: E307010006001A000500010014009201 | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\Roaming |
| Operation: | write | Name: | RoamingLastWriteTime |
Value: E307010006001A000500010014009201 | |||
| (PID) Process: | (2860) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRCFDE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF471013BB2D67841A.TMP | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF317C58C248A28063.TMP | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{96812D68-A988-482E-97F9-316BA1F172F5}.tmp | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\6073BA20.png | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{0C4F40F7-3201-4F64-88F8-2AEE4671B66C}.tmp | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF691252BD42959ABB.TMP | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRF{563C74CC-ACDC-4075-951D-8ADDFB954AD3}.tmp | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\Desktop\~$voice_898527.doc.docm | pgc | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\invoice_898527.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2860 | WINWORD.EXE | 198.54.120.132:443 | globalstateway.club | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
globalstateway.club |
| malicious |
Threats
Process | Message |
|---|---|
WINWORD.EXE | SHIMVIEW: ShimInfo(Complete)
|