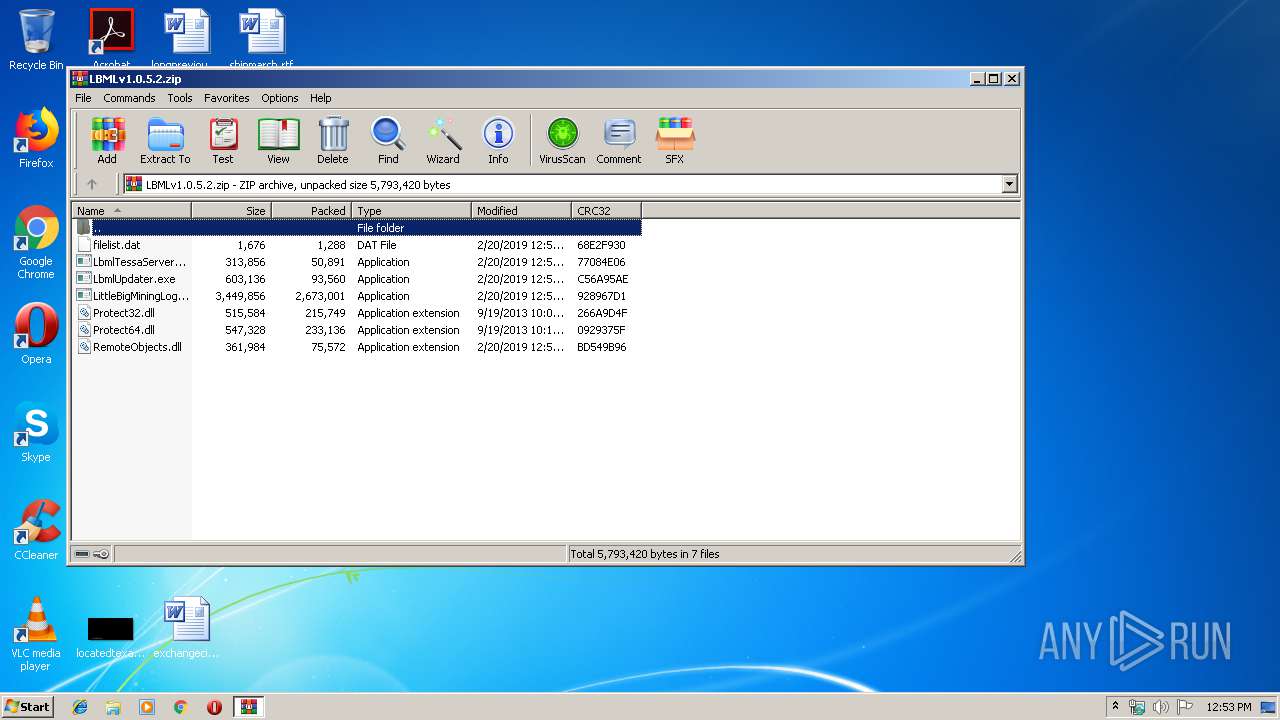
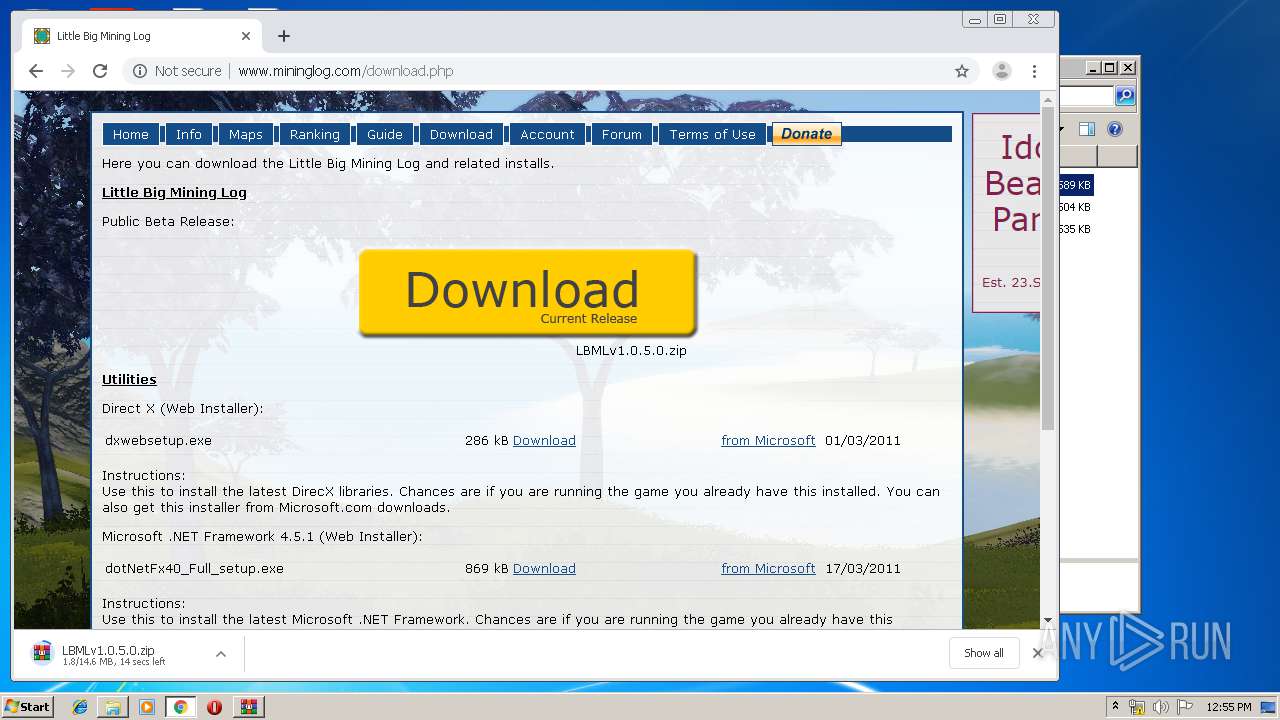
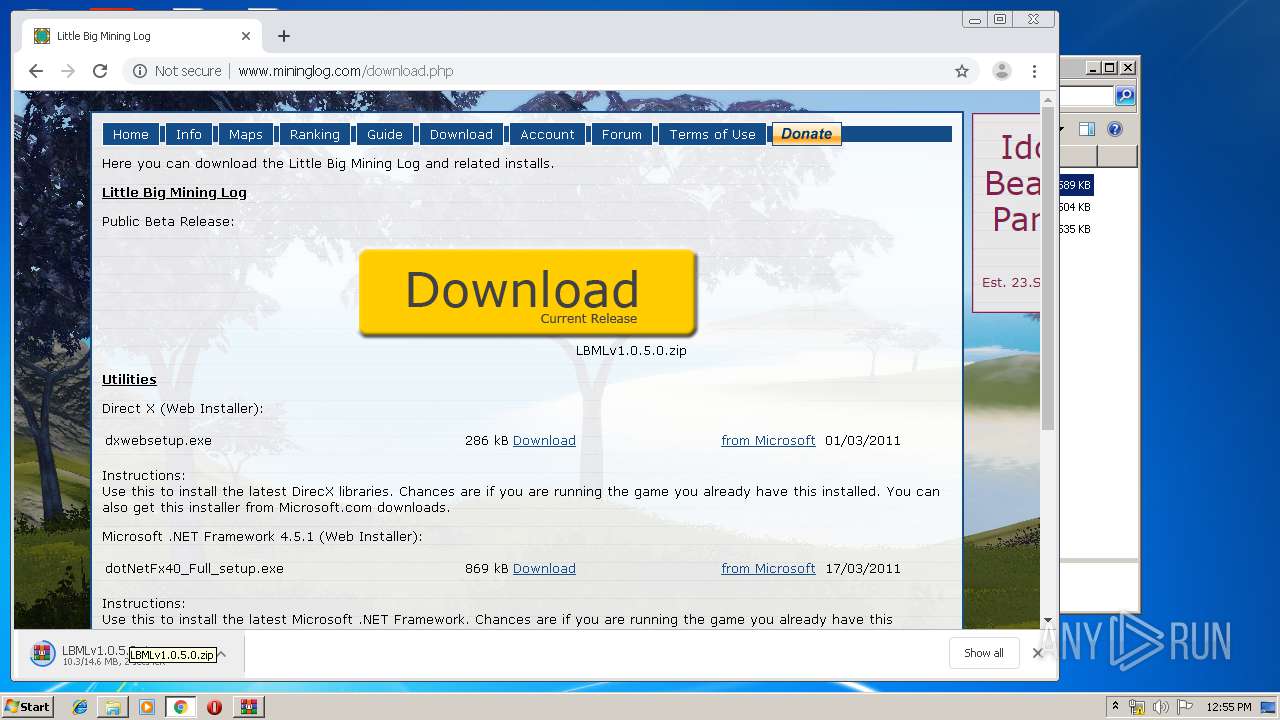
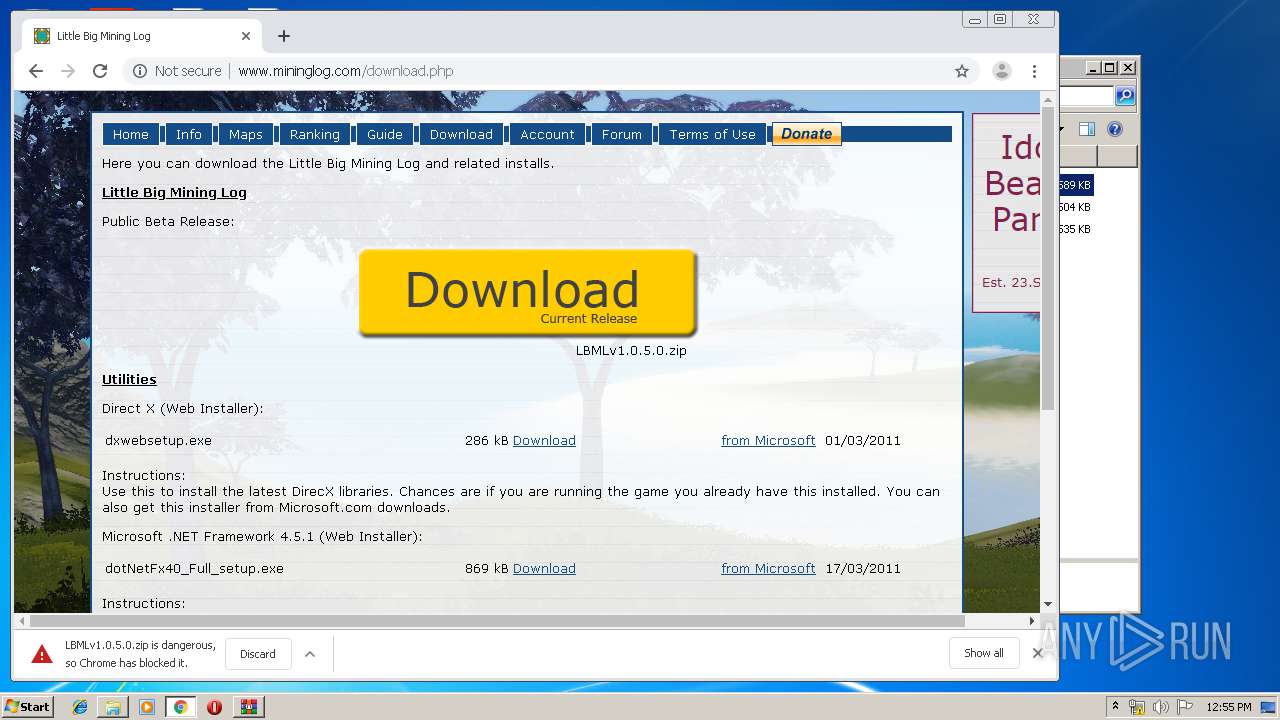
| File name: | http://www.mininglog.com/downloads/client2/LBMLv1.0.5.2.zip |
| Full analysis: | https://app.any.run/tasks/5d01b9f7-e109-4a69-8dda-721049b7336d |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 12:53:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2EB653E434BDDF81914DAB8CDB77042B |
| SHA1: | 0D1B5075ED0119D2535D009976F817AD5EE36DAE |
| SHA256: | D7C035CB10739D0E4F1CA1524245FB8AE949DEEB4DB84D1220864D6DB1957E4F |
| SSDEEP: | 49152:cZEQUNttJItgDNzysbzEeOzklZtFS9LIFc9YRtsW2K7BRWfUDlhxuYZxJD9YU5PE:USJ8g9weigZTE0Fx7sWxBRWyHpqjb2FC |
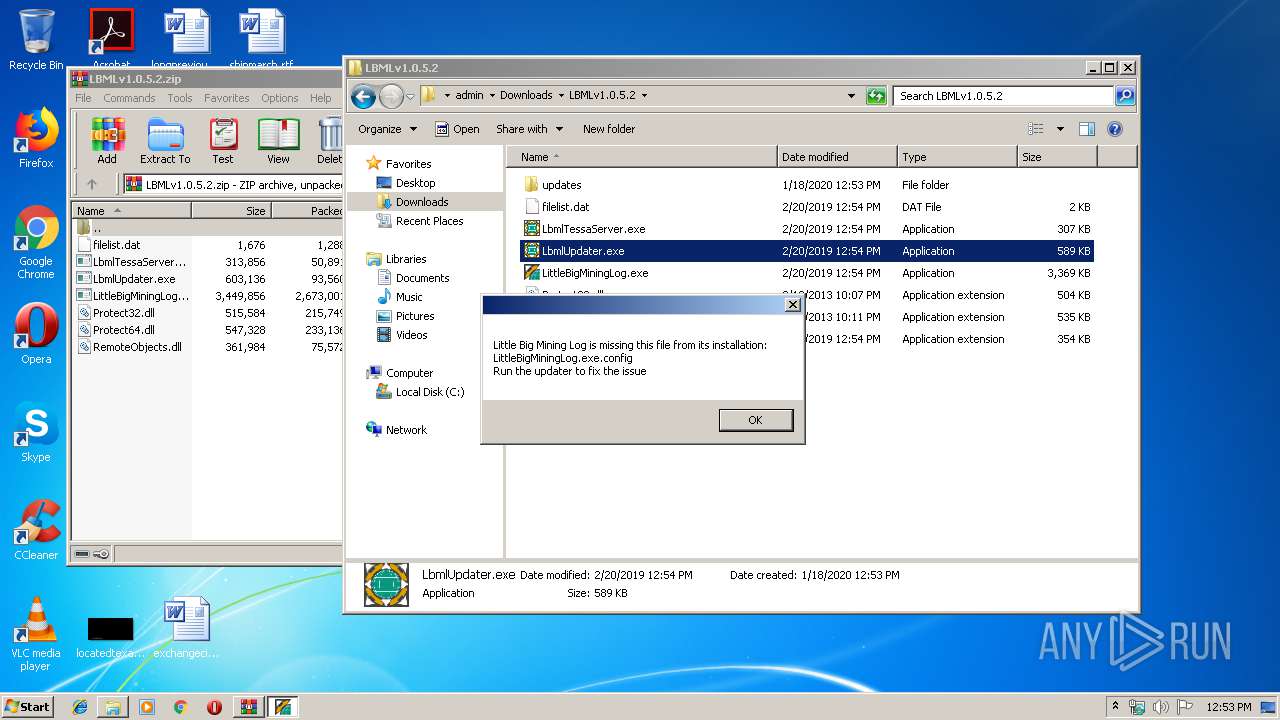
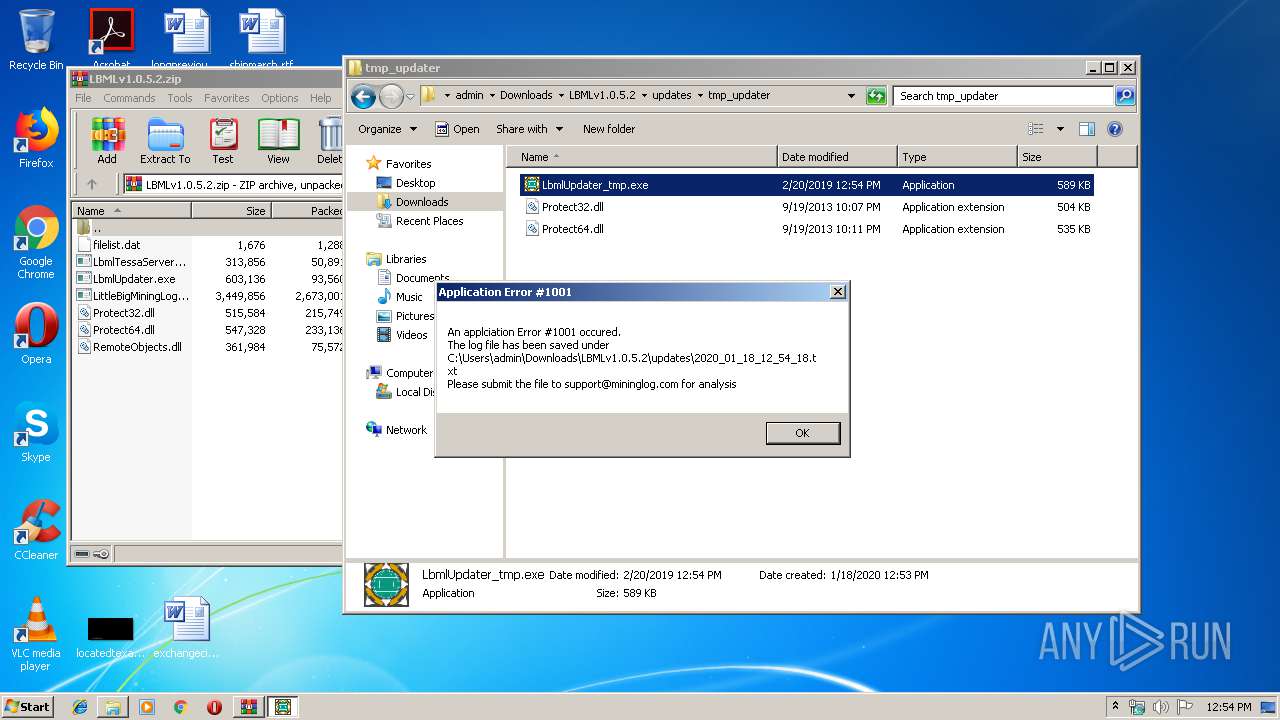
MALICIOUS
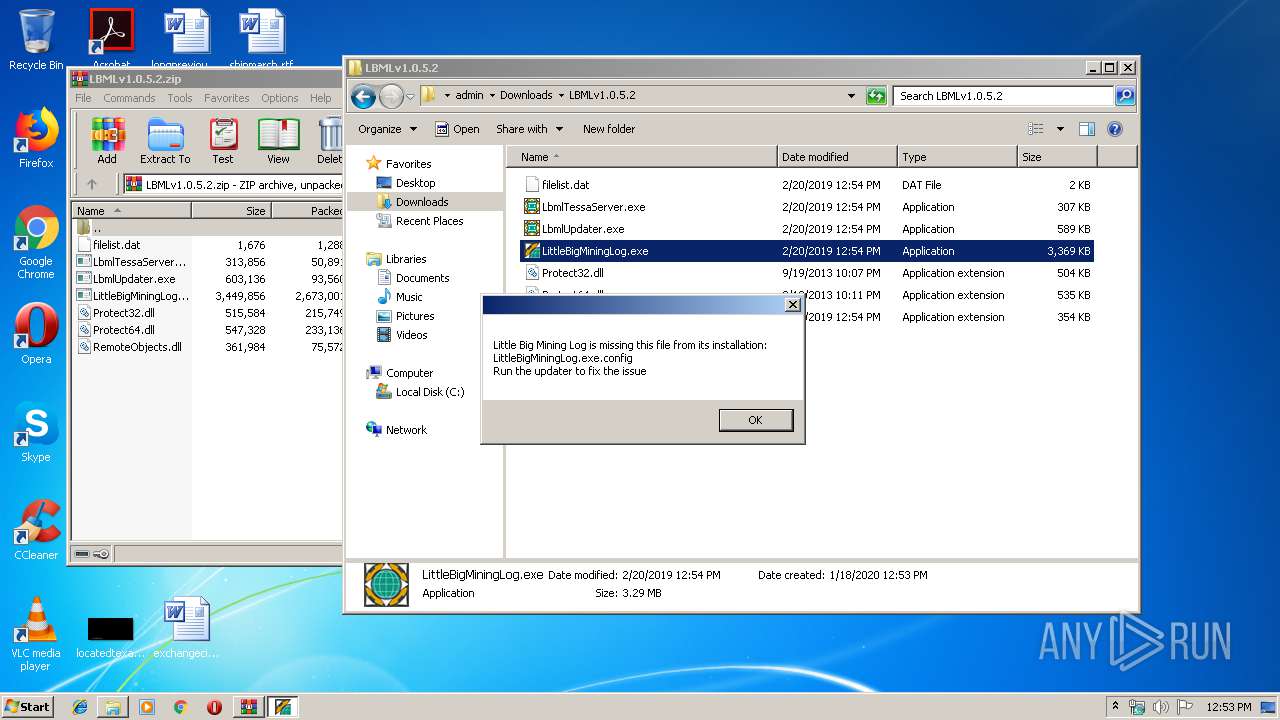
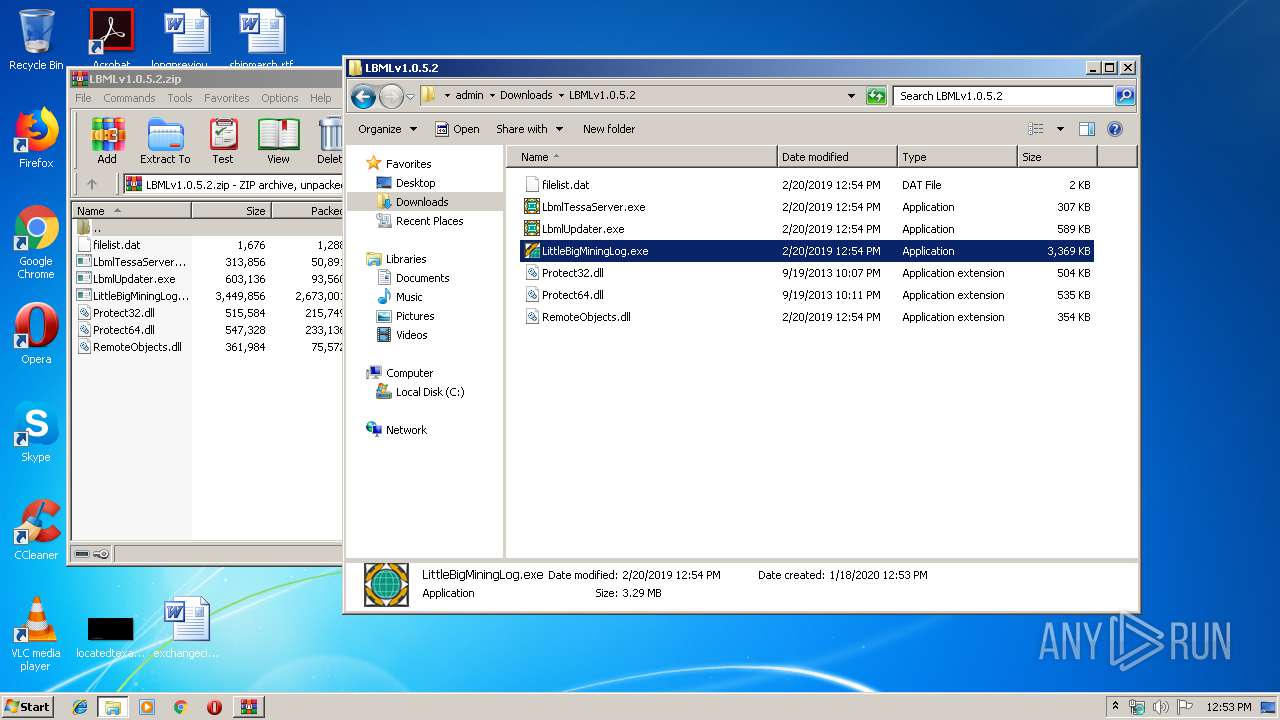
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3472)
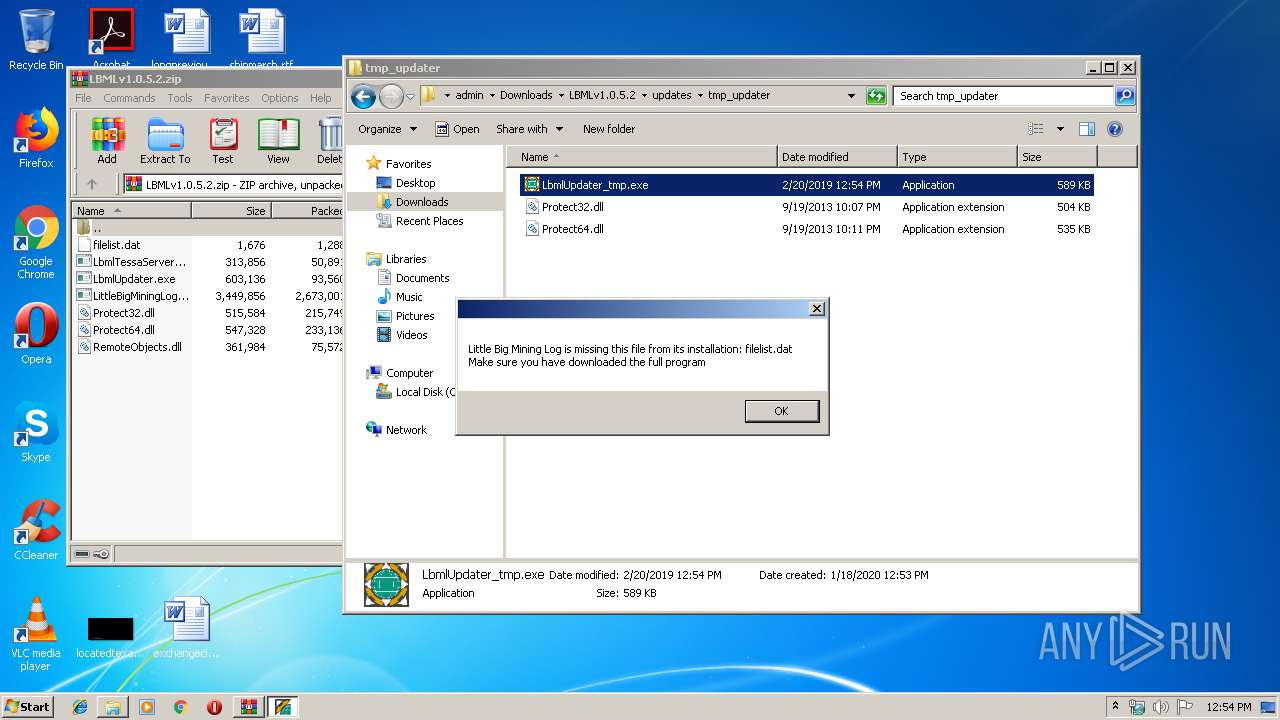
Application was dropped or rewritten from another process
- LittleBigMiningLog.exe (PID: 1536)
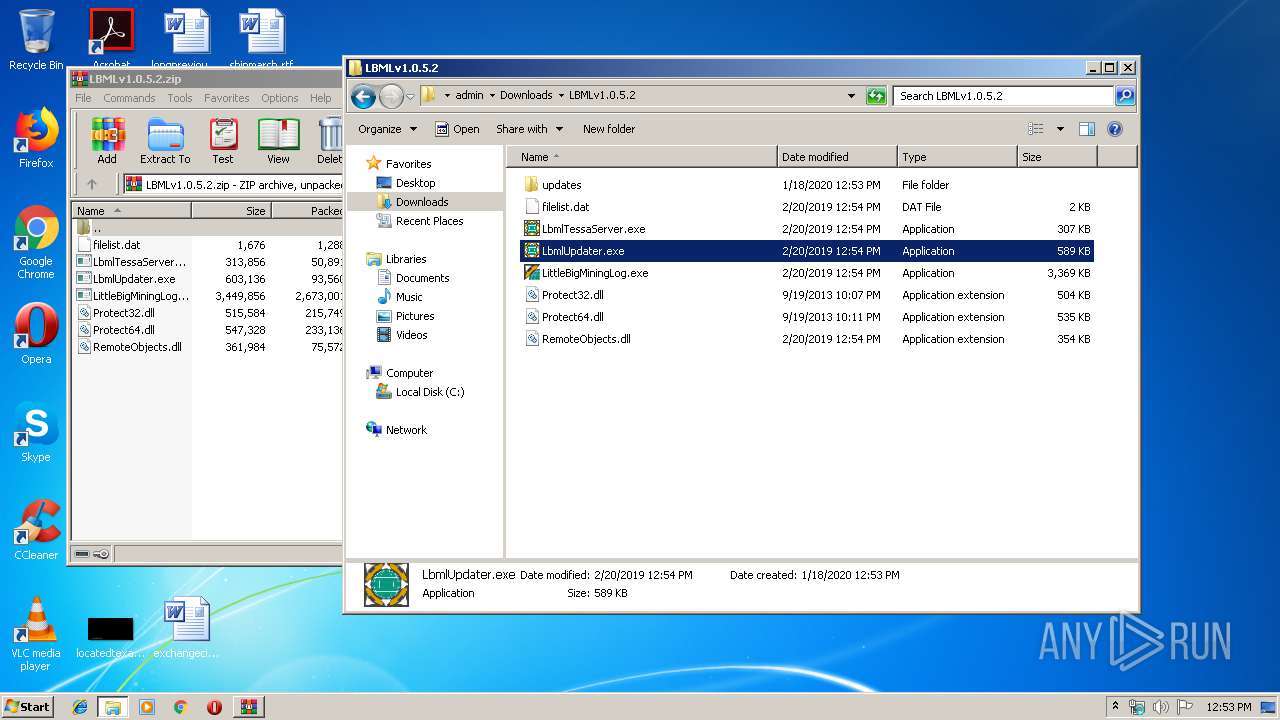
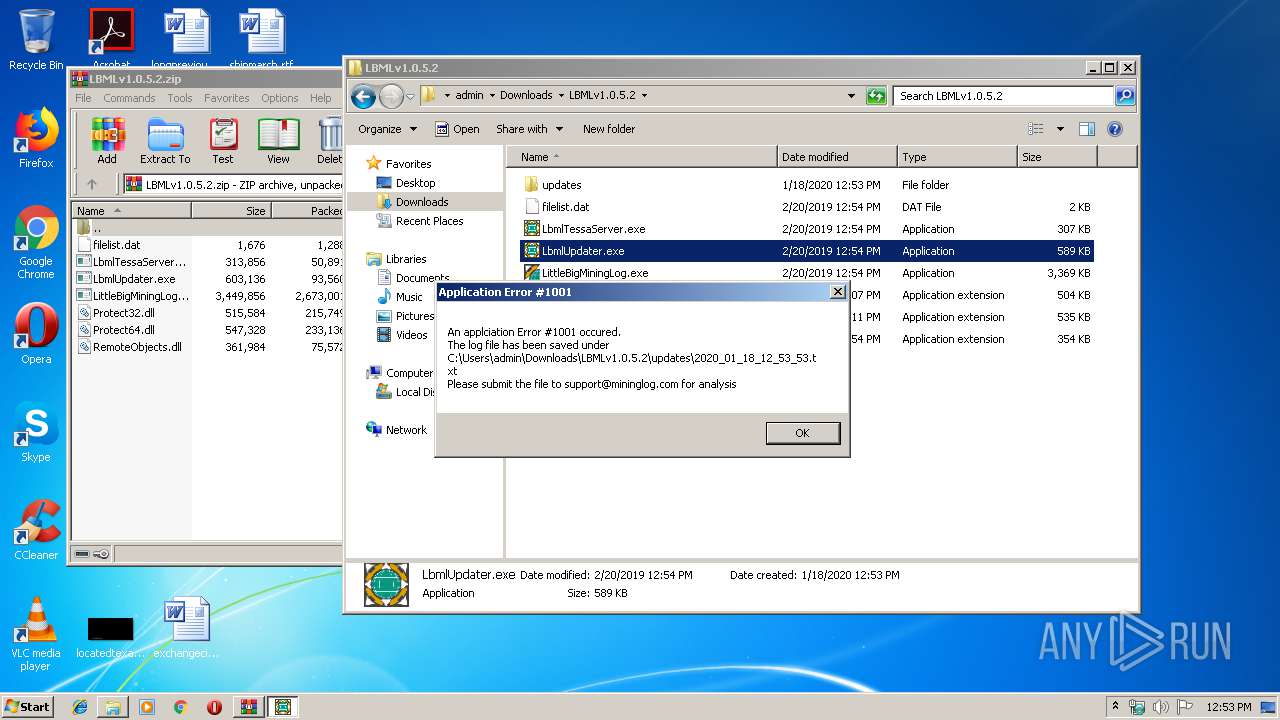
- LbmlUpdater.exe (PID: 2480)
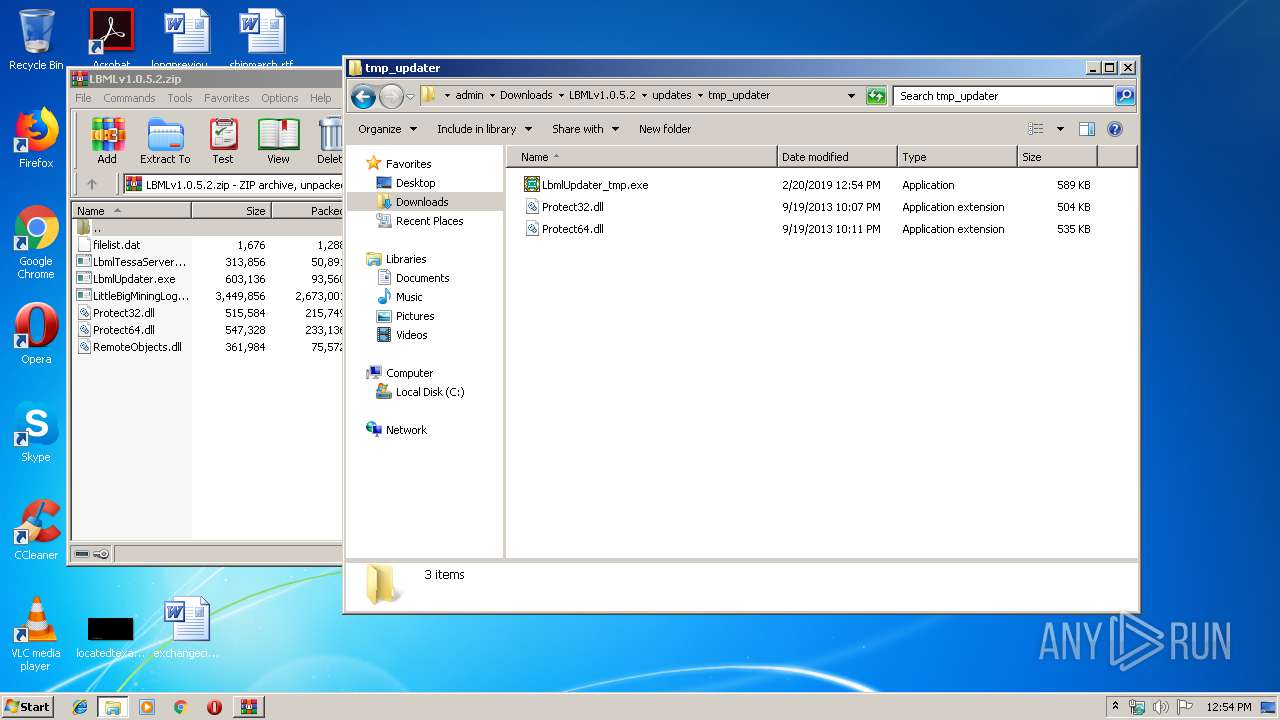
- LbmlUpdater_tmp.exe (PID: 2608)
- LbmlUpdater_tmp.exe (PID: 3708)
- LittleBigMiningLog.exe (PID: 2692)
- LittleBigMiningLog.exe (PID: 3172)
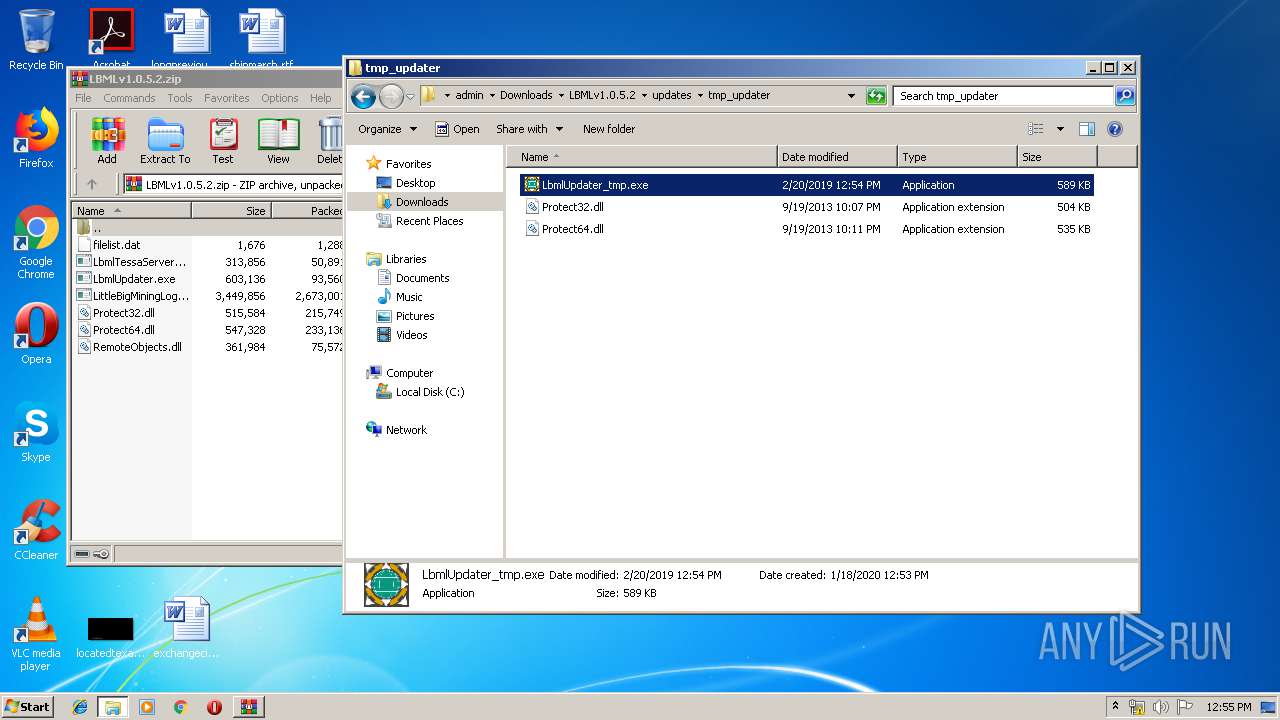
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1520)
- LbmlUpdater.exe (PID: 2480)
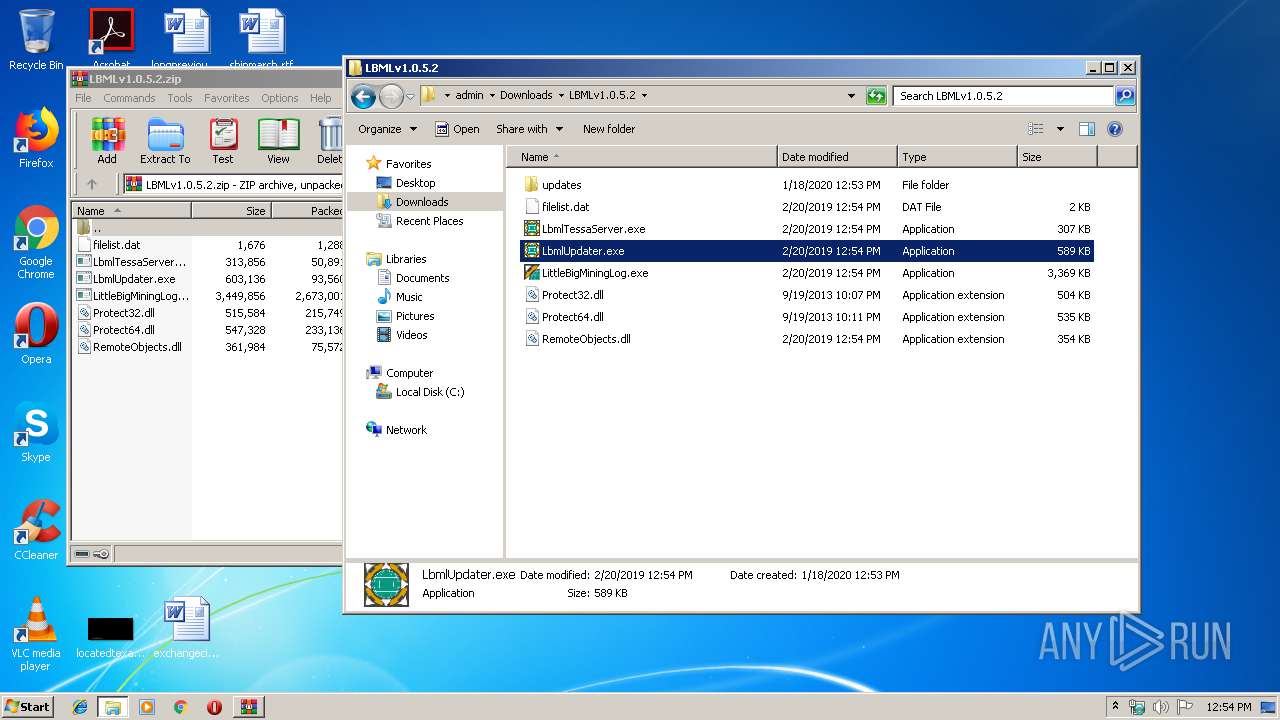
Starts itself from another location
- LbmlUpdater.exe (PID: 2480)
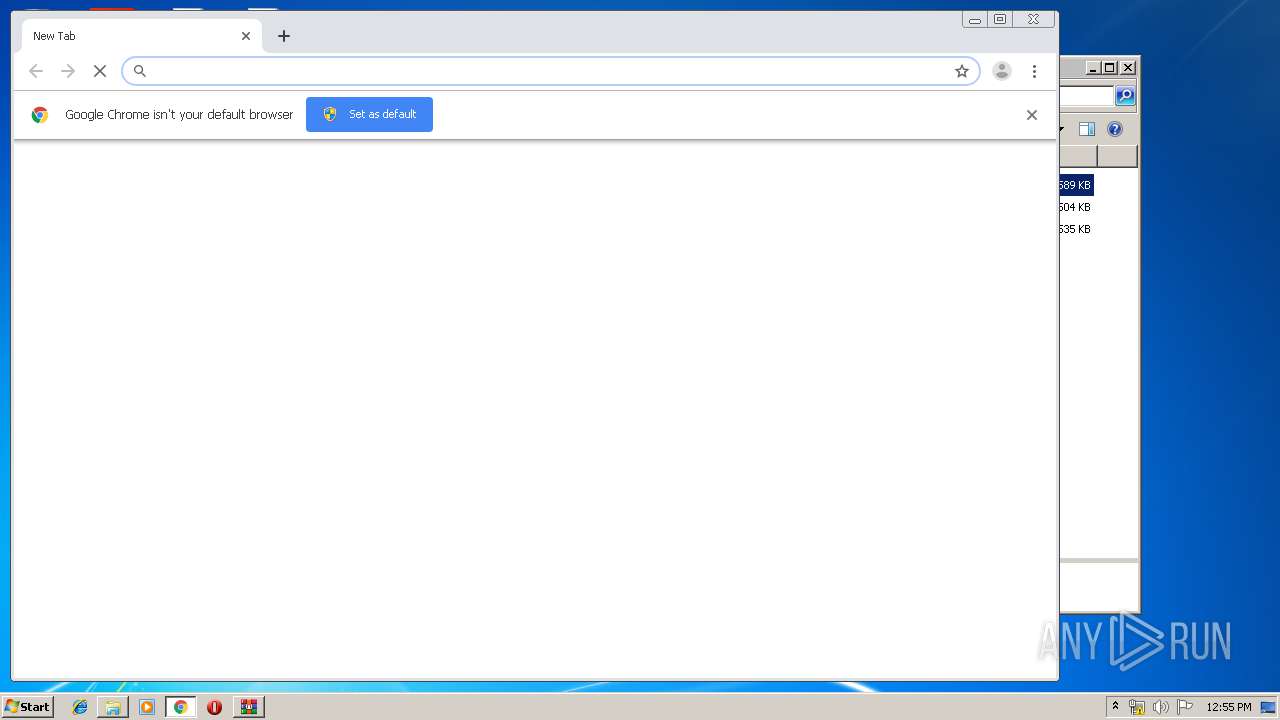
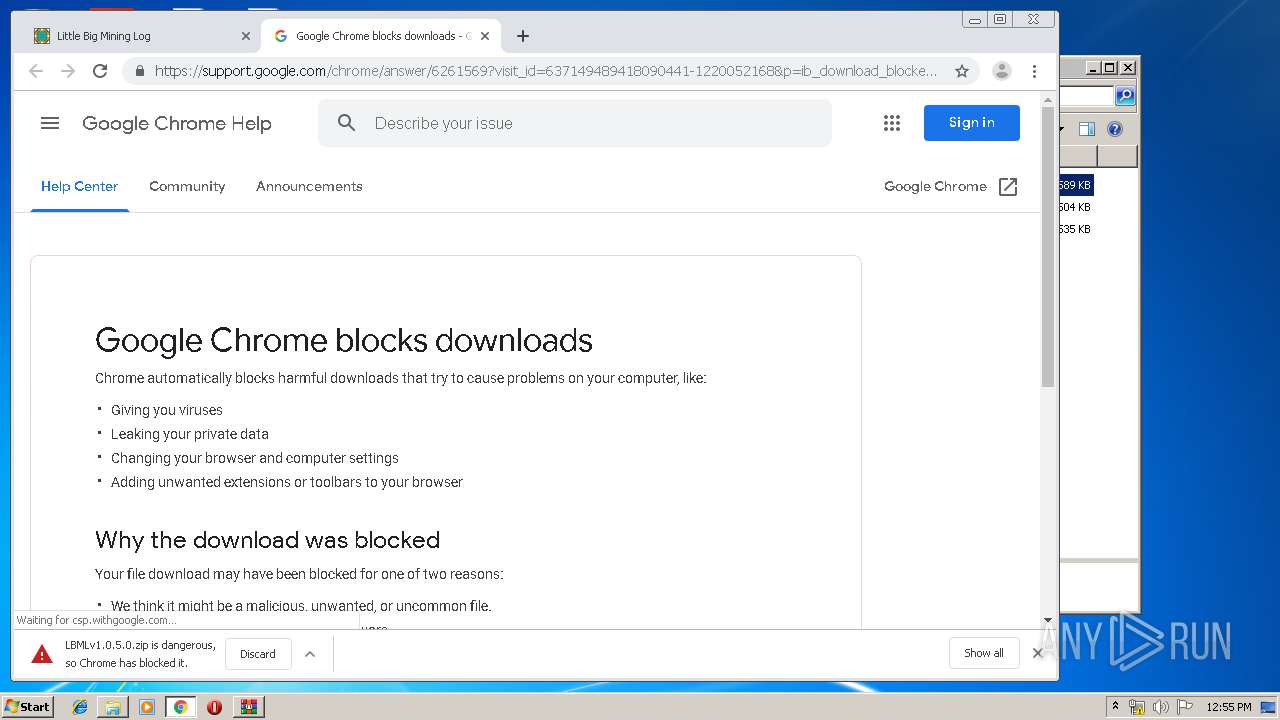
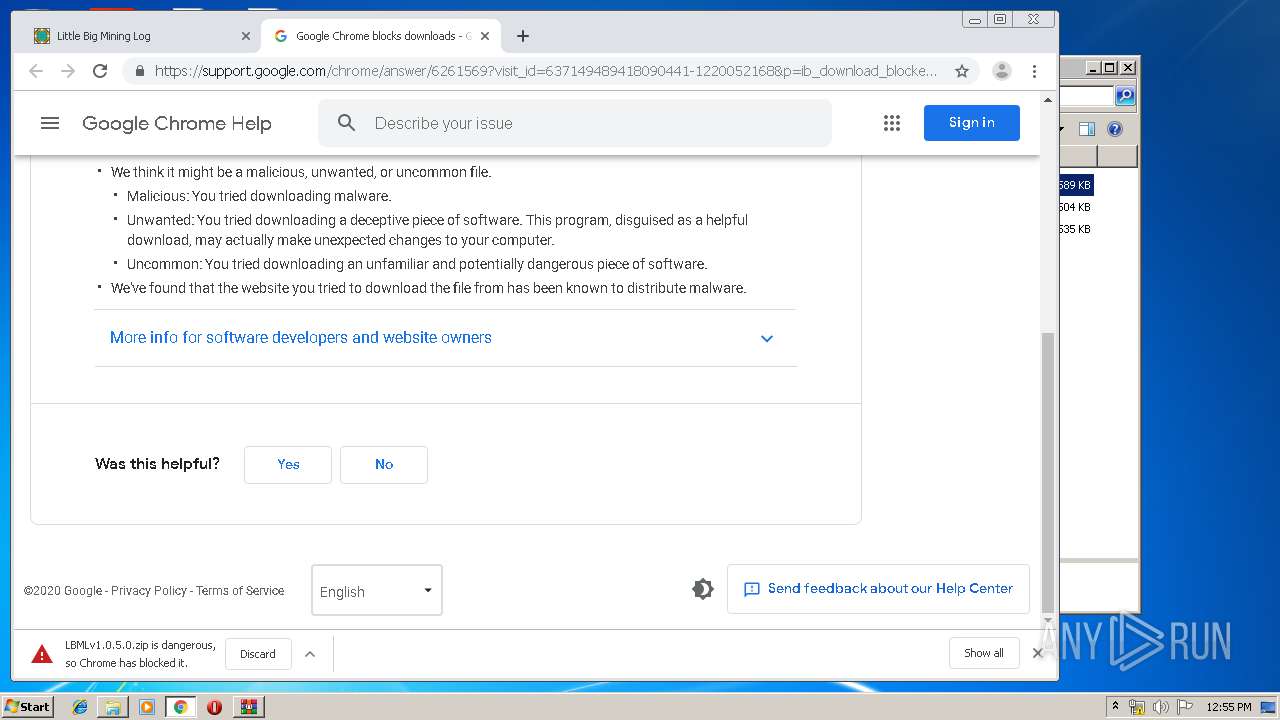
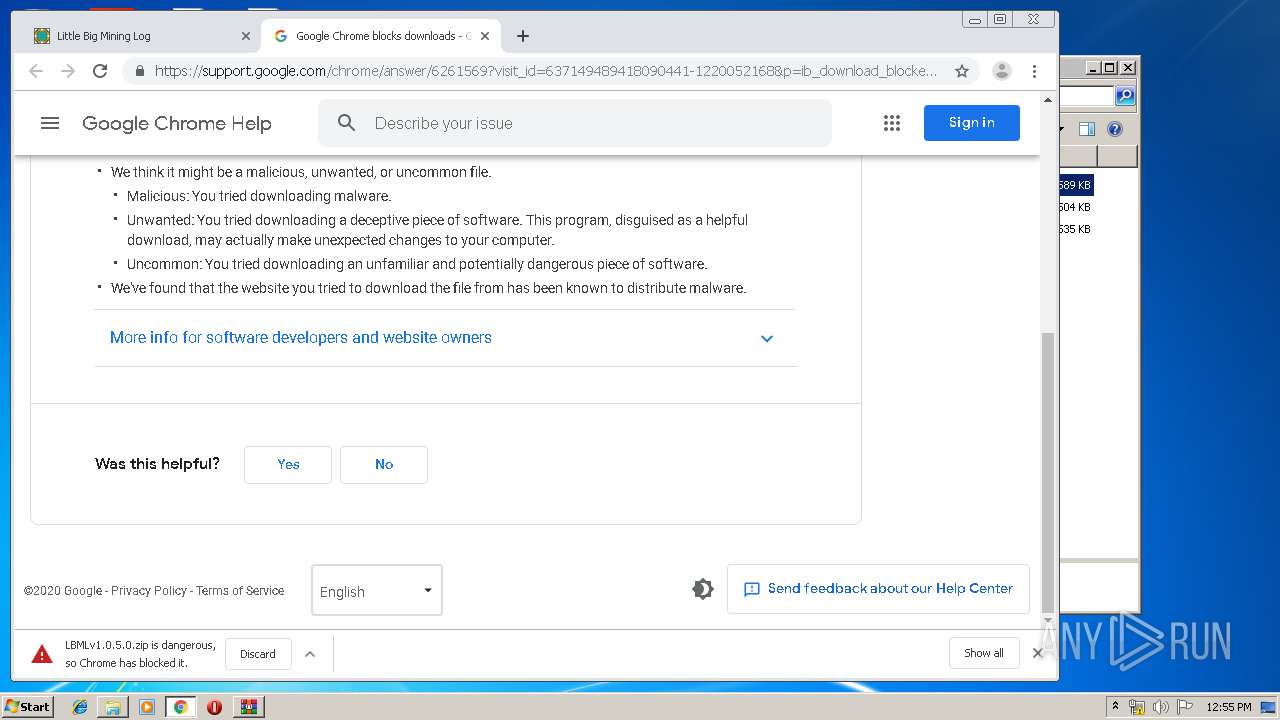
Modifies files in Chrome extension folder
- chrome.exe (PID: 2856)
INFO
Manual execution by user
- explorer.exe (PID: 2968)
- LittleBigMiningLog.exe (PID: 1536)
- LbmlUpdater.exe (PID: 2480)
- LbmlUpdater_tmp.exe (PID: 3708)
- NOTEPAD.EXE (PID: 388)
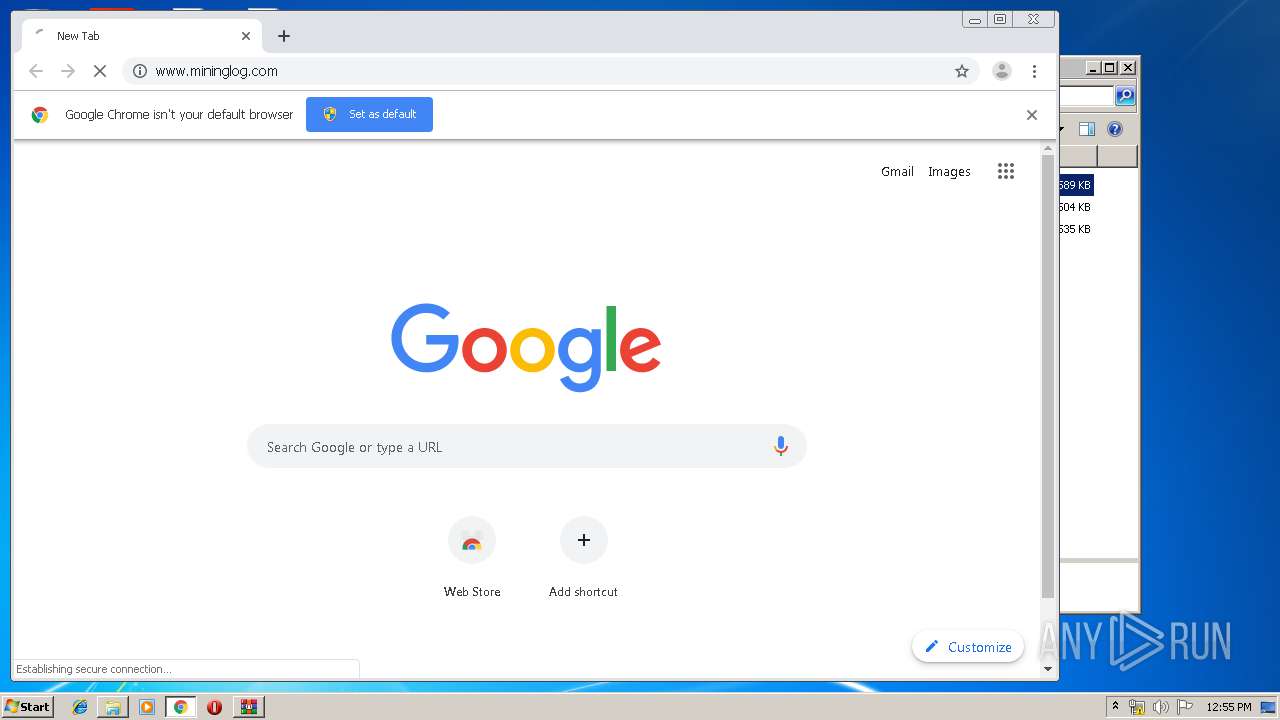
- chrome.exe (PID: 2856)
Reads the hosts file
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3392)
Reads settings of System Certificates
- chrome.exe (PID: 3392)
Application launched itself
- chrome.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:02:20 12:54:27 |
| ZipCRC: | 0x68e2f930 |
| ZipCompressedSize: | 1288 |
| ZipUncompressedSize: | 1676 |
| ZipFileName: | filelist.dat |
Total processes
90
Monitored processes
50
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
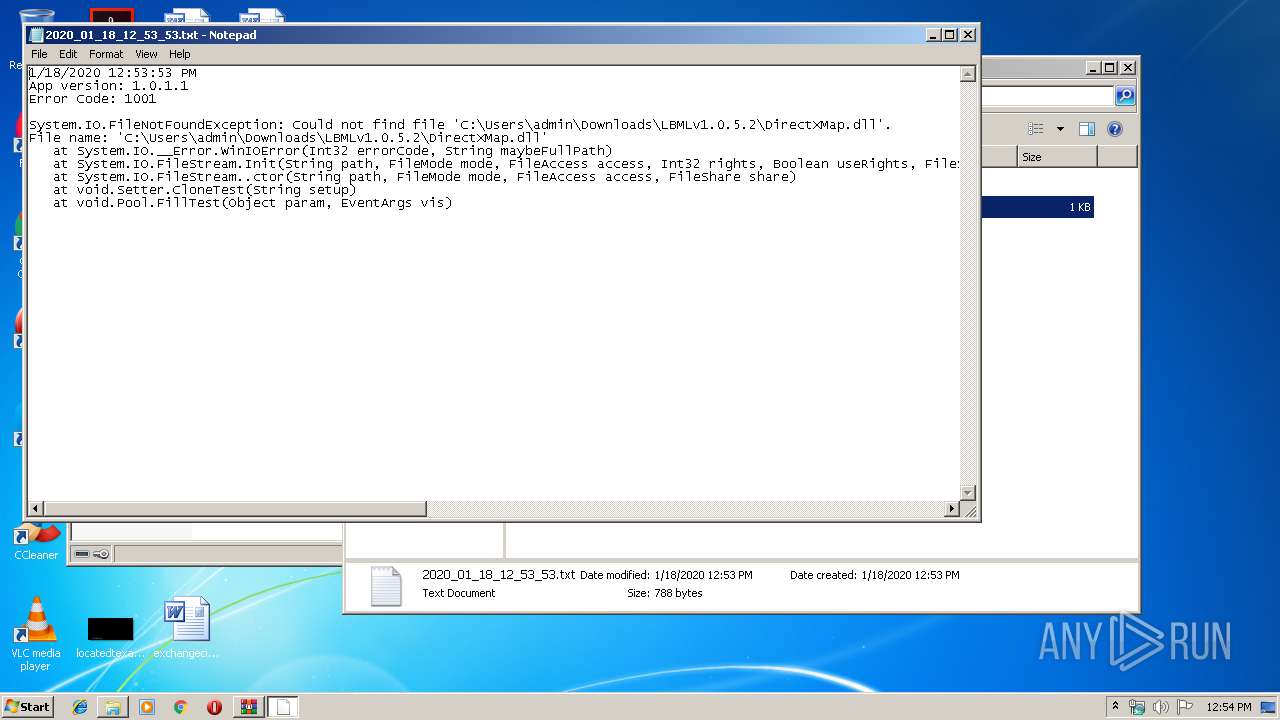
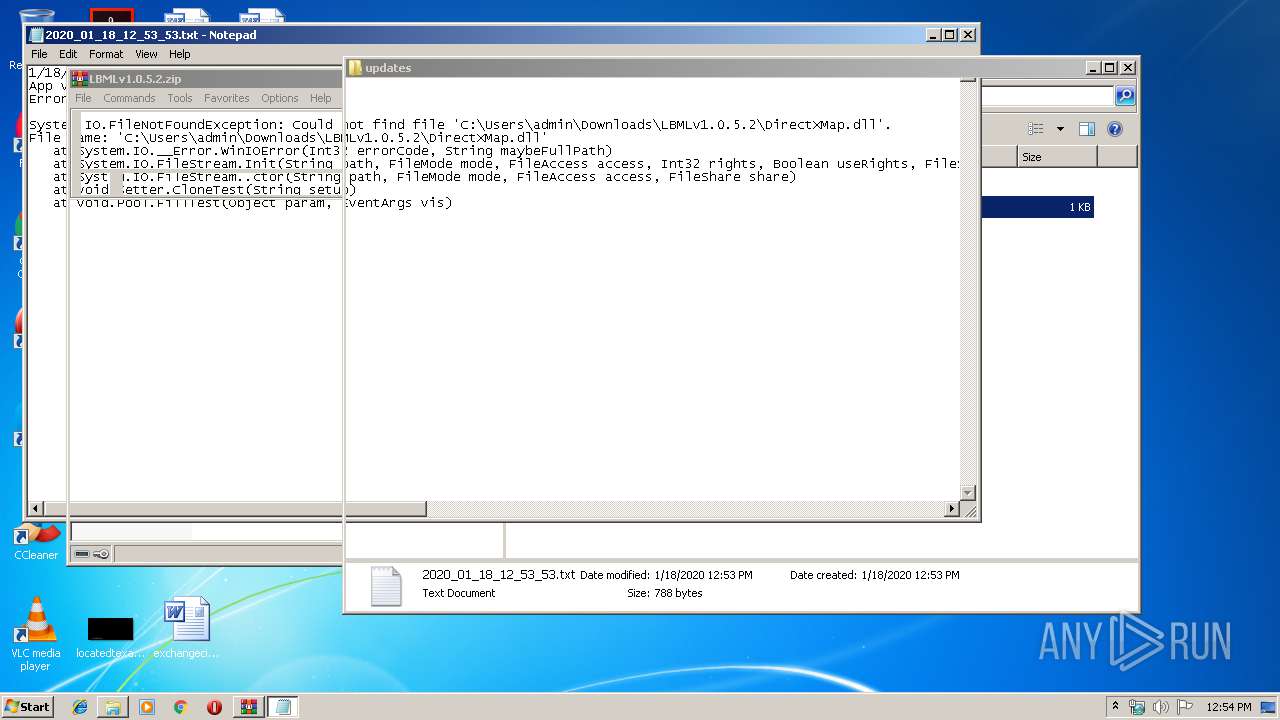
| 388 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\LBMLv1.0.5.2\updates\2020_01_18_12_53_53.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,3381848063875607774,14749563507199853667,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=384001740231813186 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,3381848063875607774,14749563507199853667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12827889630065966593 --mojo-platform-channel-handle=3904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,3381848063875607774,14749563507199853667,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=706447265546407393 --mojo-platform-channel-handle=4528 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,3381848063875607774,14749563507199853667,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2736336577467035208 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1820 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,3381848063875607774,14749563507199853667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8150463990870442135 --mojo-platform-channel-handle=4756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
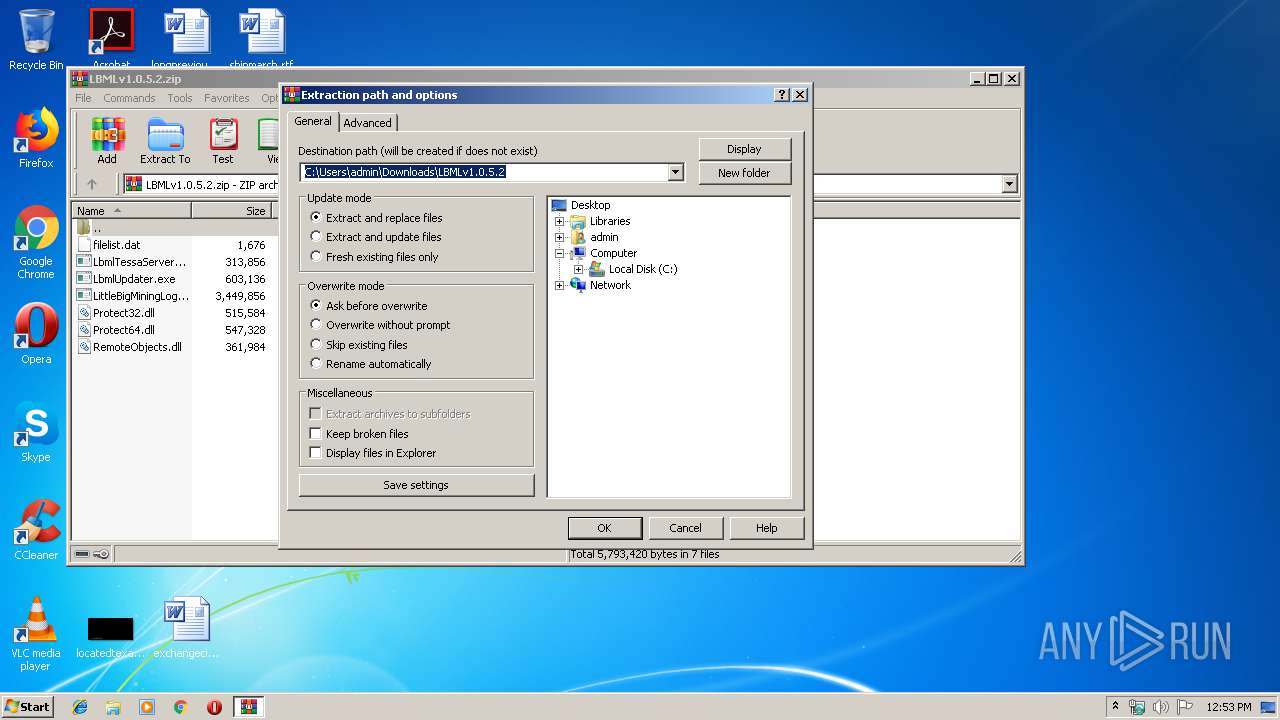
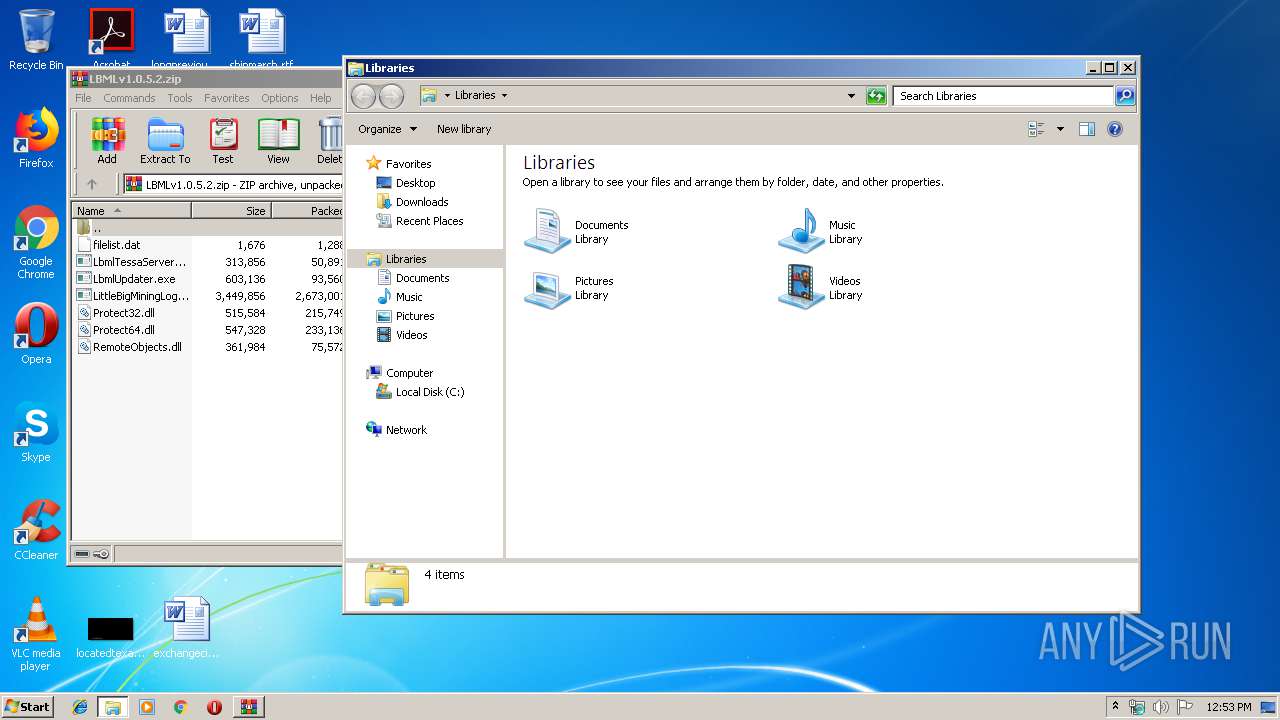
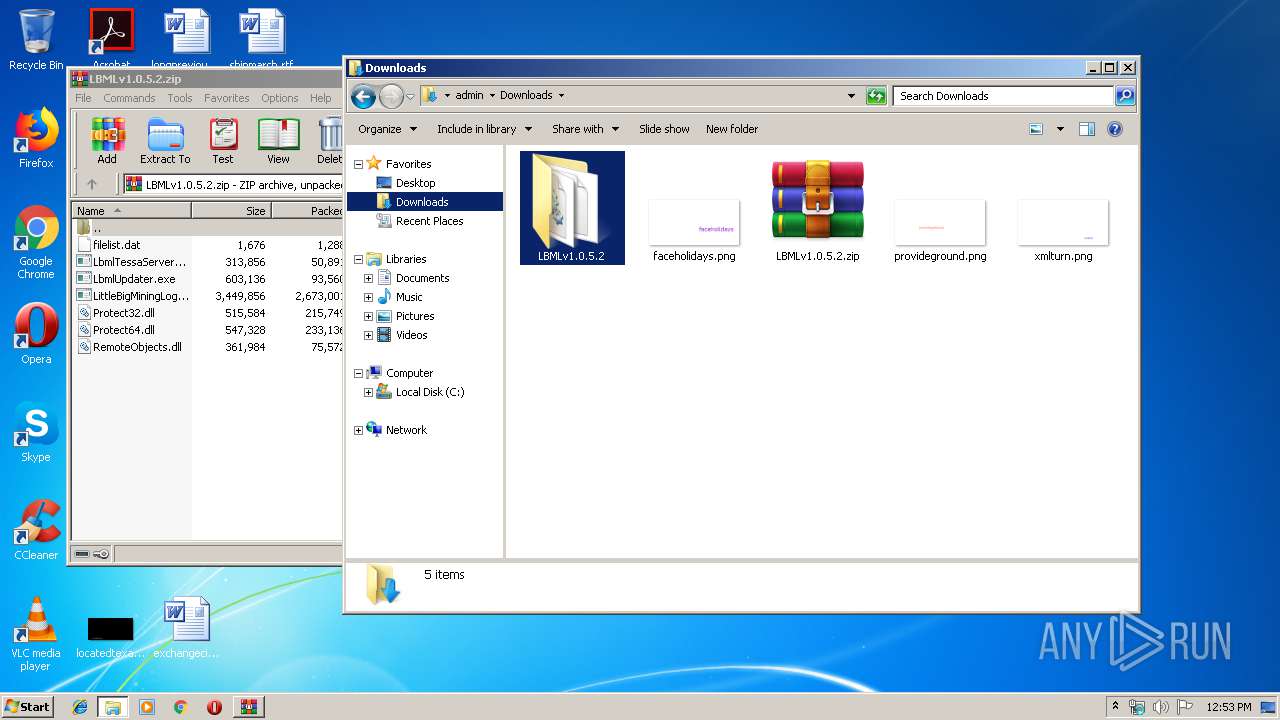
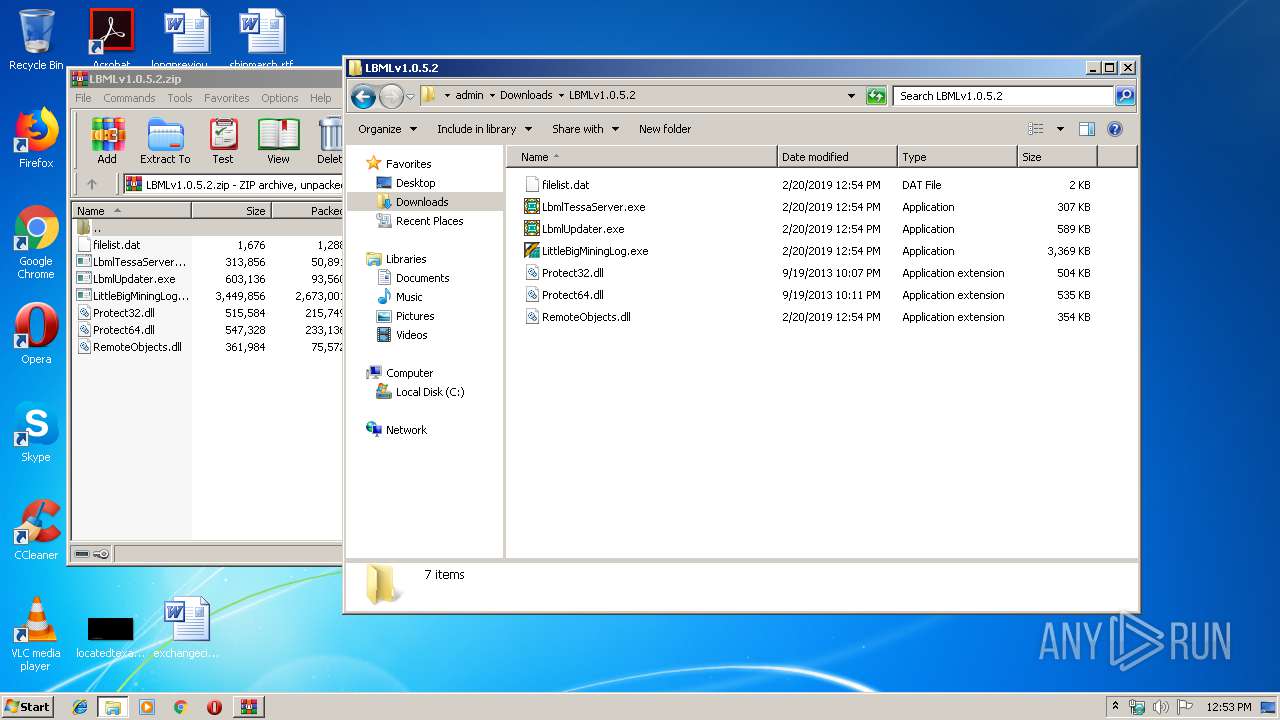
| 1520 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\LBMLv1.0.5.2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,3381848063875607774,14749563507199853667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2533260726095297951 --mojo-platform-channel-handle=4748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
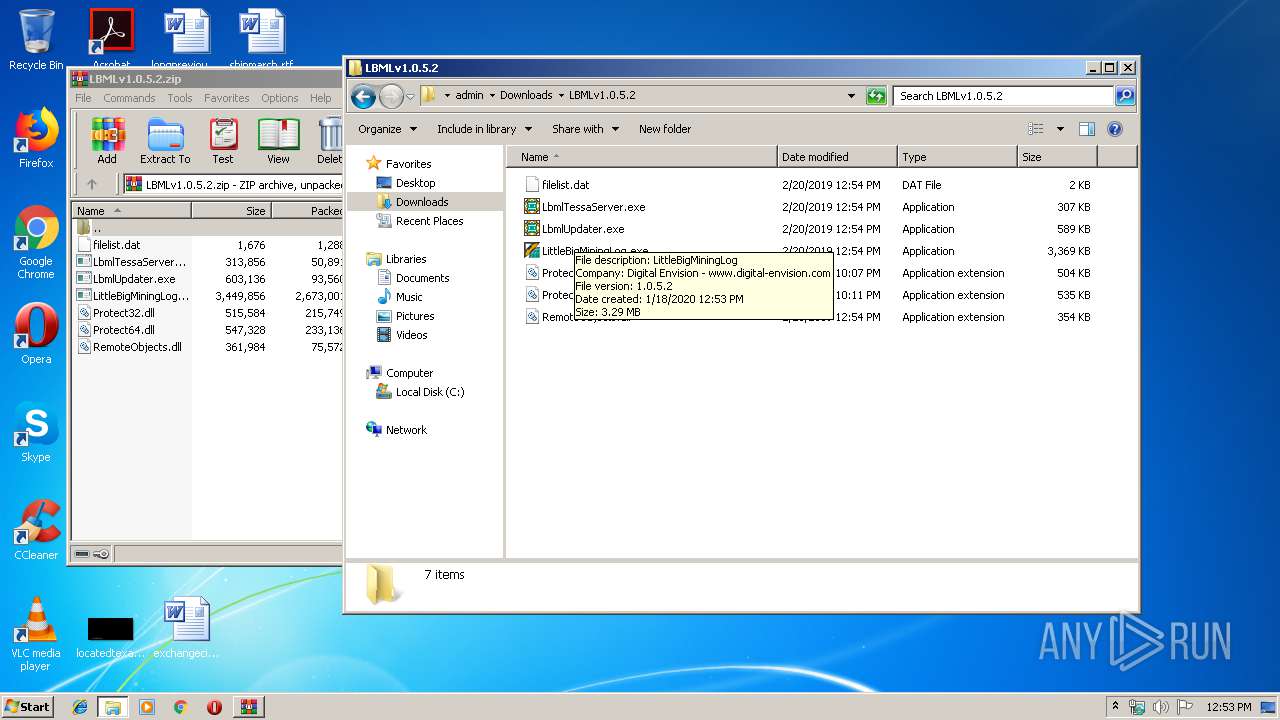
| 1536 | "C:\Users\admin\Downloads\LBMLv1.0.5.2\LittleBigMiningLog.exe" | C:\Users\admin\Downloads\LBMLv1.0.5.2\LittleBigMiningLog.exe | — | explorer.exe | |||||||||||
User: admin Company: Digital Envision - www.digital-envision.com Integrity Level: MEDIUM Description: LittleBigMiningLog Exit code: 0 Version: 1.0.5.2 Modules
| |||||||||||||||
Total events
2 527
Read events
2 397
Write events
125
Delete events
5
Modification events
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\LBMLv1.0.5.2.zip | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\LBMLv1.0.5.2 | |||
| (PID) Process: | (2480) LbmlUpdater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
9
Suspicious files
39
Text files
287
Unknown types
10
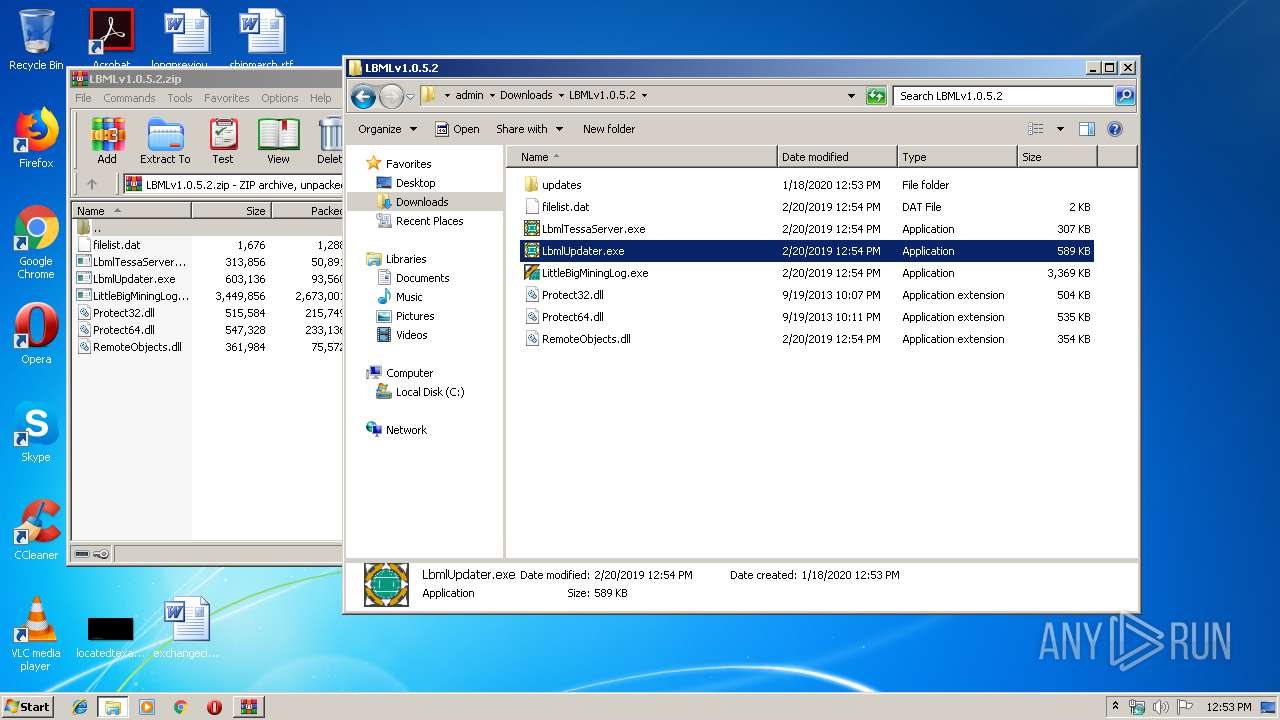
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
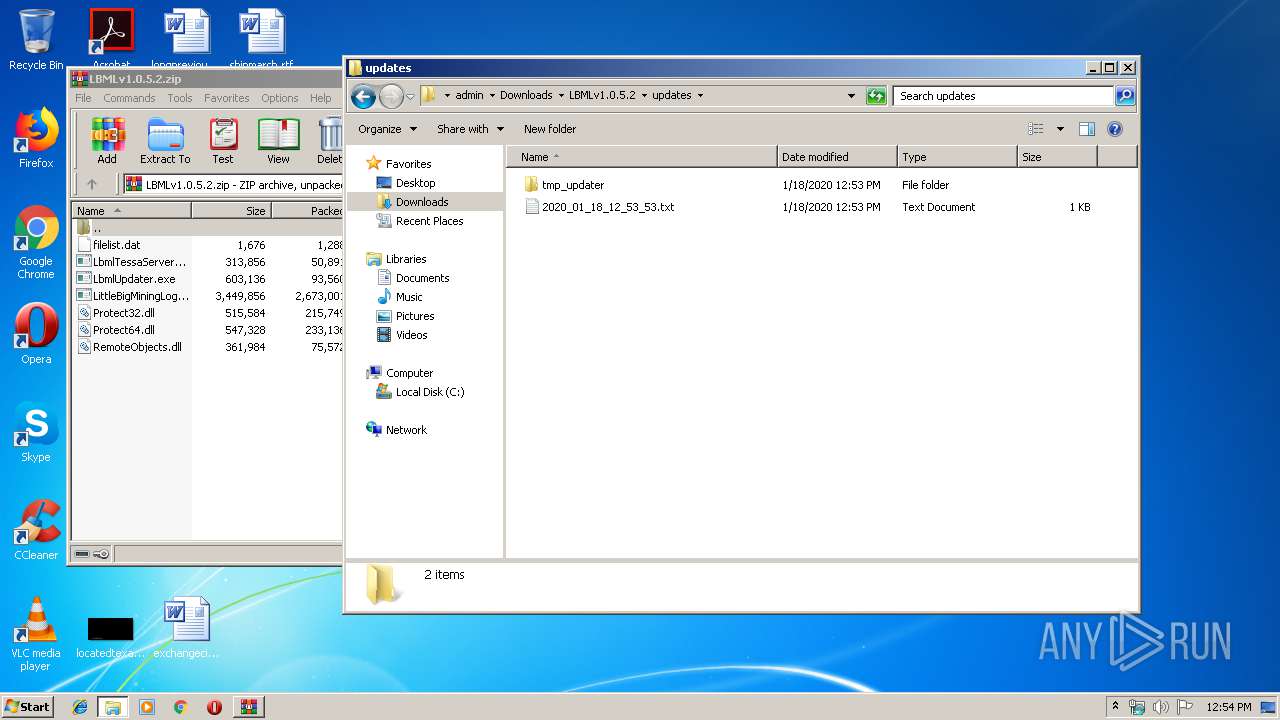
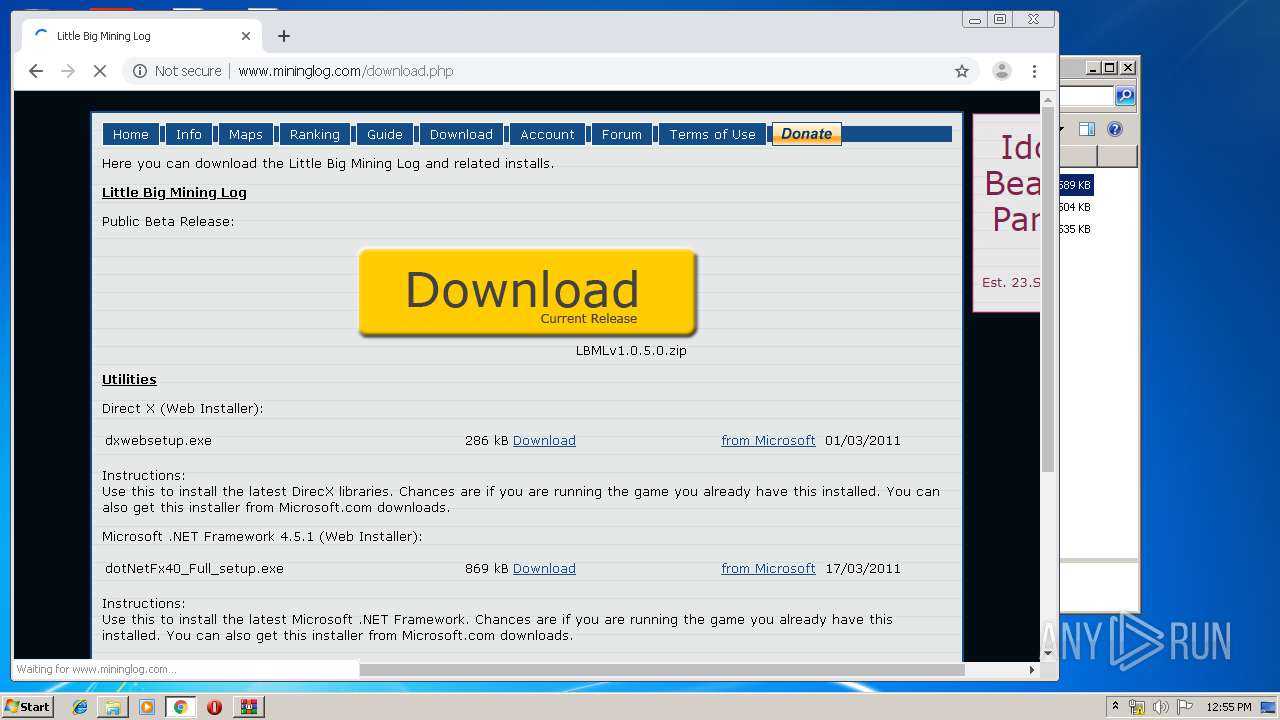
| 1520 | WinRAR.exe | C:\Users\admin\Downloads\LBMLv1.0.5.2\LittleBigMiningLog.exe | executable | |
MD5:— | SHA256:— | |||
| 1520 | WinRAR.exe | C:\Users\admin\Downloads\LBMLv1.0.5.2\LbmlUpdater.exe | executable | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF3b21e0.TMP | — | |
MD5:— | SHA256:— | |||
| 1520 | WinRAR.exe | C:\Users\admin\Downloads\LBMLv1.0.5.2\filelist.dat | text | |
MD5:— | SHA256:— | |||
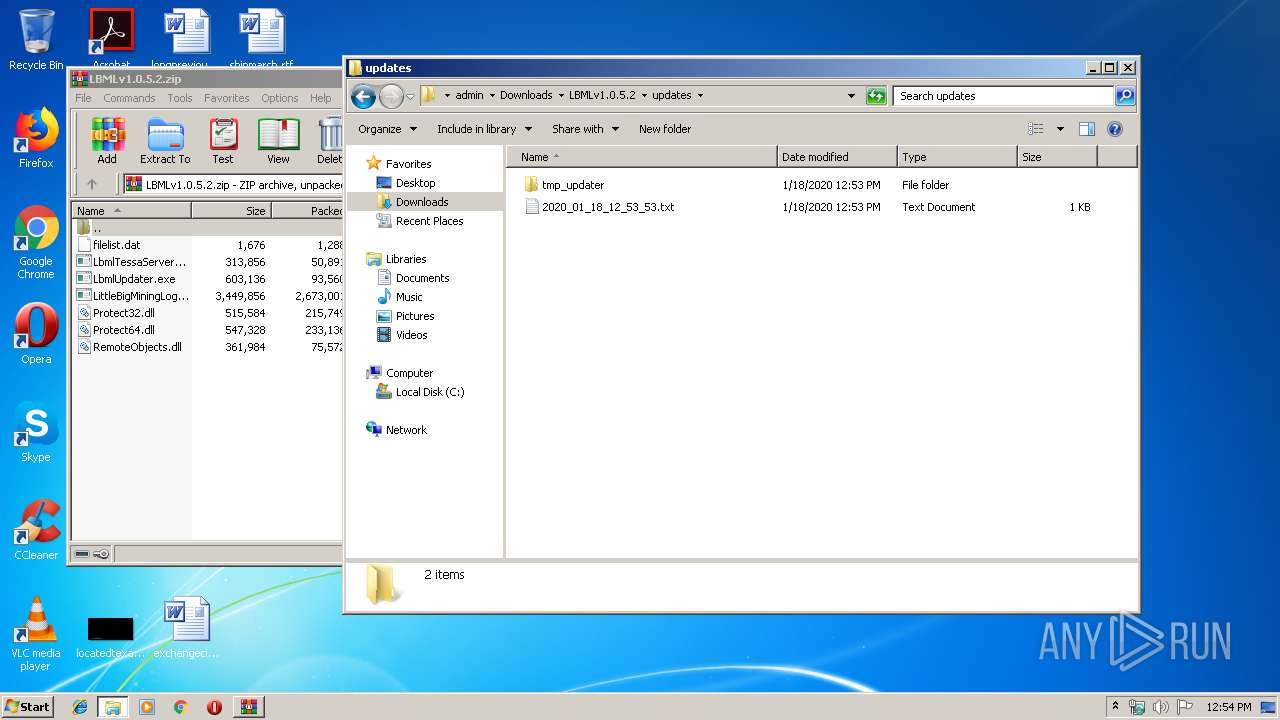
| 2608 | LbmlUpdater_tmp.exe | C:\Users\admin\Downloads\LBMLv1.0.5.2\updates\2020_01_18_12_53_53.txt | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0ba41f9d-844e-4a87-81e3-3bc90cacc1e4.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1520 | WinRAR.exe | C:\Users\admin\Downloads\LBMLv1.0.5.2\LbmlTessaServer.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
44
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
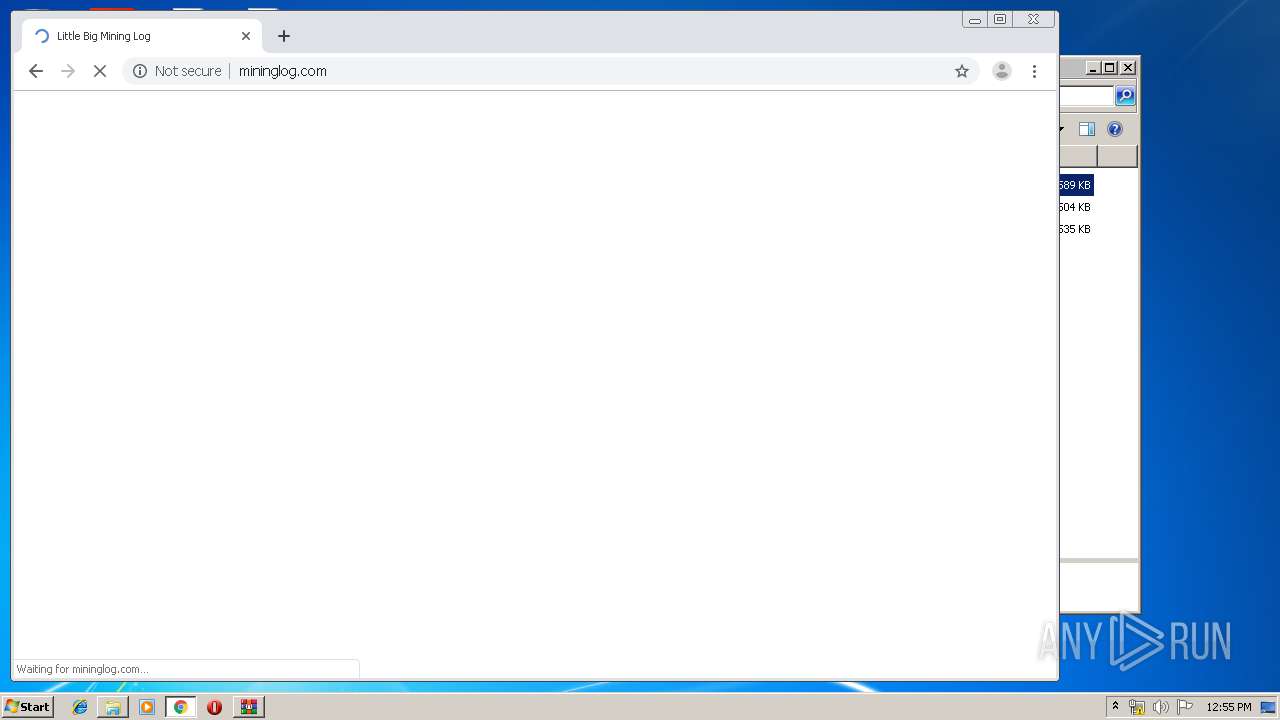
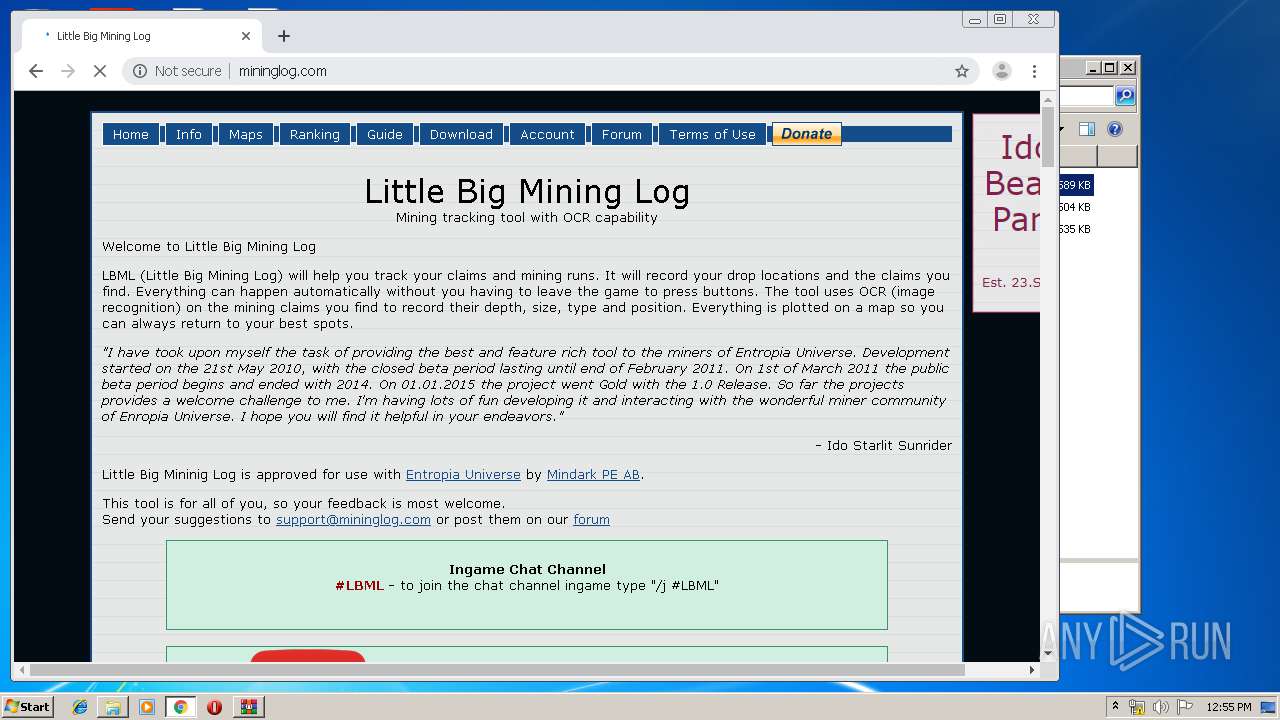
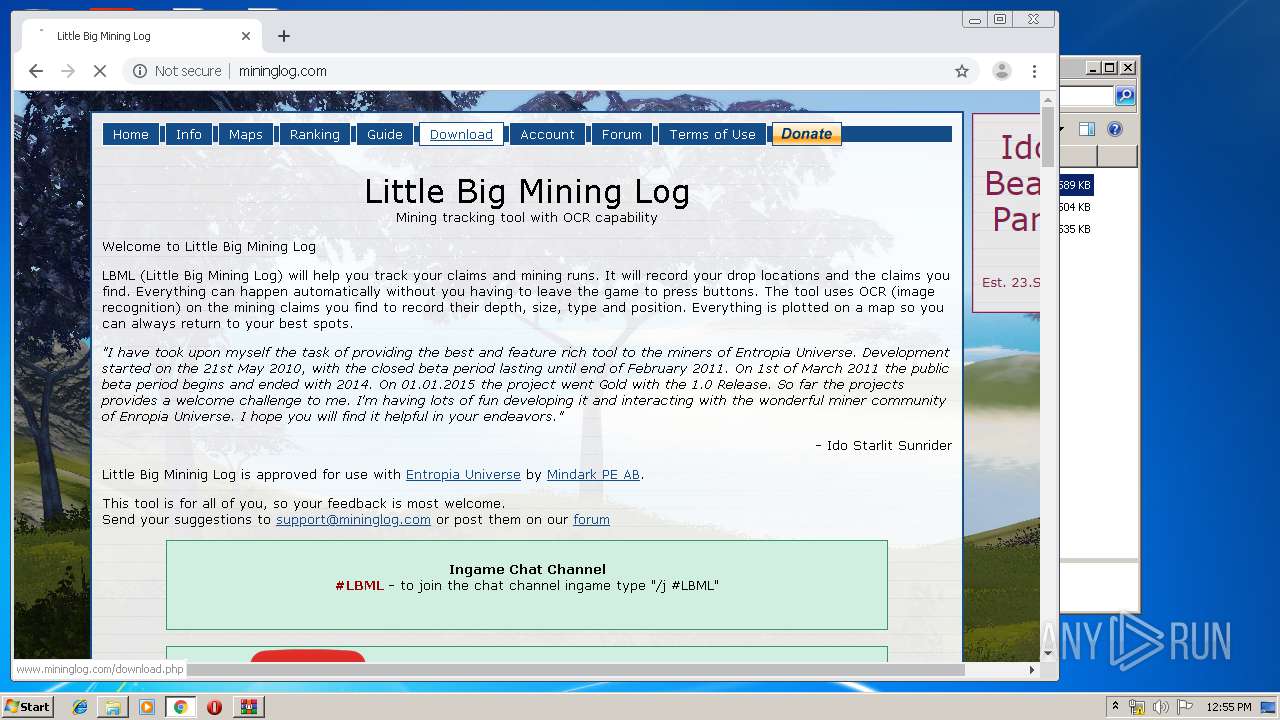
3392 | chrome.exe | GET | — | 132.148.61.1:80 | http://www.mininglog.com/ | US | — | — | suspicious |
2608 | LbmlUpdater_tmp.exe | GET | 200 | 132.148.61.1:80 | http://www.mininglog.com/downloads/version2.php | US | text | 242 b | suspicious |
3708 | LbmlUpdater_tmp.exe | GET | 200 | 132.148.61.1:80 | http://www.mininglog.com/downloads/version2.php | US | text | 242 b | suspicious |
3392 | chrome.exe | GET | 200 | 132.148.61.1:80 | http://www.mininglog.com/img/adds/ido.jpg | US | image | 40.8 Kb | suspicious |
3392 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3392 | chrome.exe | GET | 200 | 132.148.61.1:80 | http://www.mininglog.com/img/donate.jpg | US | image | 2.06 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 132.148.61.1:80 | http://mininglog.com/img/PeriodicTable_280.png | US | image | 71.9 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 132.148.61.1:80 | http://mininglog.com/ | US | html | 12.6 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 132.148.61.1:80 | http://mininglog.com/img/background.jpg | US | image | 512 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 132.148.61.1:80 | http://mininglog.com/img/transparent.png | US | image | 2.75 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3392 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 216.58.210.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3392 | chrome.exe | 216.58.205.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 216.58.205.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 74.125.4.166:80 | r1---sn-aigzrne7.gvt1.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 74.125.4.203:80 | r5---sn-aigzrner.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mininglog.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |