| File name: | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader |
| Full analysis: | https://app.any.run/tasks/43141460-c8d9-479b-933b-c658be65b842 |
| Verdict: | Malicious activity |
| Analysis date: | April 20, 2025, 08:16:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 20B82BBBDB93A69F62160F11333D4F2F |
| SHA1: | 1AF4201925E99C7C5EE2B484DC6A4CA4D9826BC1 |
| SHA256: | D7BF6DBCFD064E7B586EDDF131CC23B3DC6024650F4E40FC6F082C73E5048BBB |
| SSDEEP: | 98304:iefUuZuKAuf5jTFhkOefUuZuKAuf5jTFrkHVrGDYwOwjefUuZuKAuf5jTFPkOef3:Mz |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7648)
Starts NET.EXE for service management
- cmd.exe (PID: 7832)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7856)
- net.exe (PID: 4040)
- net.exe (PID: 3240)
- net.exe (PID: 6872)
- net.exe (PID: 6240)
- net.exe (PID: 5728)
Uses NET.EXE to stop Windows Security Center service
- cmd.exe (PID: 7856)
- net.exe (PID: 3240)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 7840)
- net.exe (PID: 6872)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 7924)
- net.exe (PID: 1164)
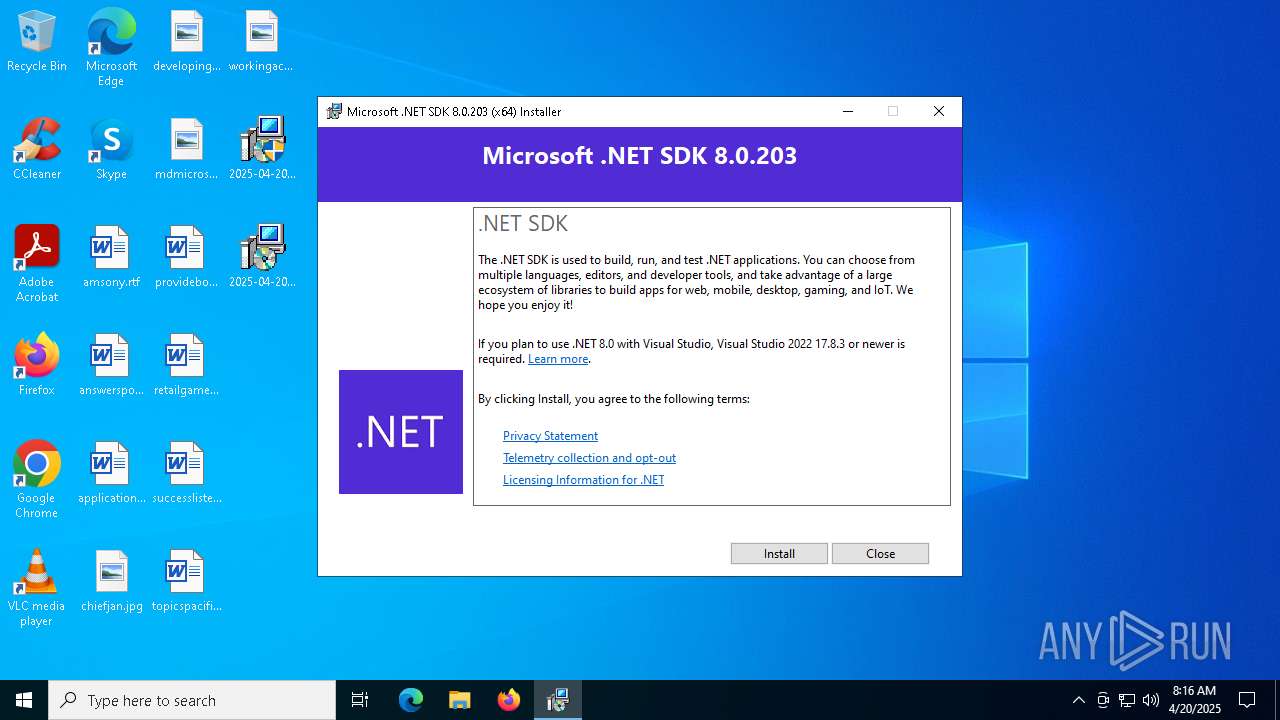
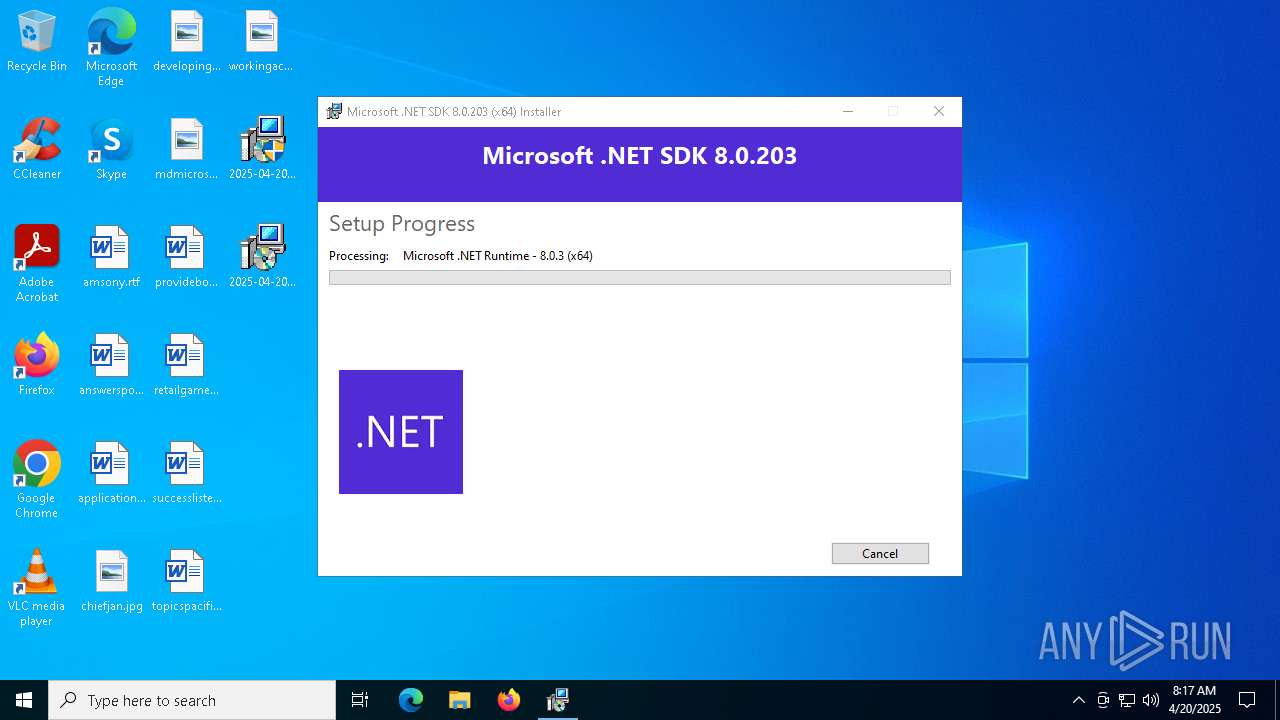
Changes the autorun value in the registry
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
Starts NET.EXE to view/change users localgroup
- net.exe (PID: 4120)
- cmd.exe (PID: 7940)
SUSPICIOUS
Process drops legitimate windows executable
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- UpdatAuto.exe (PID: 7580)
Executing commands from a ".bat" file
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- UpdatAuto.exe (PID: 7580)
Starts itself from another location
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7648)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
Starts CMD.EXE for commands execution
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- UpdatAuto.exe (PID: 7580)
Starts a Microsoft application from unusual location
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7344)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7648)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
Creates file in the systems drive root
- UpdatAuto.exe (PID: 7580)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
Executable content was dropped or overwritten
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7648)
- UpdatAuto.exe (PID: 7580)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
Searches for installed software
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
Reads security settings of Internet Explorer
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
Creates a software uninstall entry
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
Windows service management via SC.EXE
- sc.exe (PID: 8008)
- sc.exe (PID: 7964)
- sc.exe (PID: 8020)
- sc.exe (PID: 8036)
- sc.exe (PID: 8044)
INFO
The sample compiled with chinese language support
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- UpdatAuto.exe (PID: 7580)
Create files in a temporary directory
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- UpdatAuto.exe (PID: 7580)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
Checks supported languages
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
- UpdatAuto.exe (PID: 7580)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7648)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
The sample compiled with english language support
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
Reads the computer name
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
- UpdatAuto.exe (PID: 7580)
Creates files in the program directory
- UpdatAuto.exe (PID: 7580)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 7452)
Process checks computer location settings
- 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 7668)
Auto-launch of the file from Registry key
- dotnet-sdk-8.0.203-win-x64.exe (PID: 7732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (47.8) |
|---|---|---|
| .exe | | | InstallShield setup (25.1) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (18.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:12 04:30:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 102400 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27dc |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.0 |
| ProductVersionNumber: | 6.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Windows Update Manager for NT |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Update Manager for NT |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1981-1999 |
| ProductName: | Microsoft(R) Windows (R) 2000 Operating System |
| FileVersion: | 6.01 |
| ProductVersion: | 6.01 |
| InternalName: | INCUBUS |
| OriginalFileName: | INCUBUS.exe |
Total processes
176
Monitored processes
49
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | C:\WINDOWS\system32\net1 stop wuauserv | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | C:\WINDOWS\system32\net1 localgroup administrators helpassistant /add | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | net user helpassistant 123456 | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\net1 stop wscsvc | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | C:\WINDOWS\system32\net1 stop sharedaccess | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | net stop wscsvc | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | net stop srservice | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | net localgroup administrators helpassistant /add | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | C:\WINDOWS\system32\net1 stop srservice | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4976 | C:\WINDOWS\system32\net1 user helpassistant 123456 | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 041
Read events
1 008
Write events
26
Delete events
7
Modification events
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | EstimatedSize |
Value: 991425 | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | Version |
Value: 8.2.324.15524 | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | DisplayName |
Value: Microsoft .NET SDK 8.0.203 (x64) | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | Resume |
Value: 1 | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | {1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
Value: "C:\ProgramData\Package Cache\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9}\dotnet-sdk-8.0.203-win-x64.exe" /burn.runonce | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleResumeCommandLine |
Value: /burn.log.append "C:\Users\admin\AppData\Local\Temp\Microsoft_.NET_SDK_8.0.203_(x64)_20250420081658.log" | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9}\Dependents\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | delete value | Name: | MinVersion |
Value: | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9}\Dependents\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | delete value | Name: | MaxVersion |
Value: | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\ProgramData\Package Cache\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9}\dotnet-sdk-8.0.203-win-x64.exe | |||
| (PID) Process: | (7732) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {2F768D97-5DB1-633B-DA88-37AFC81A605E} | |||
Executable files
16
Suspicious files
1
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7452 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\Option.bat | text | |
MD5:1D04ABF39E9DF55EED1D04430CC21EB8 | SHA256:0BC485263CF8A962E64DB0B88F156F2A9AF1B81ECFDB1CF9111D497E85DF70F3 | |||
| 7452 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\ntldr~6 | executable | |
MD5:671F1024D7A06AB53F4562BD9E71AFD3 | SHA256:06A1BCAB23AE79915403EFA2605BDBA78C6D59A0688D4904AFA0199FF5528E3C | |||
| 7668 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{D55A1C54-B99D-4317-BB4A-11CEDA9961B6}\.ba\thm.xml | xml | |
MD5:BC4C1B302D6C87C4026508120E167C95 | SHA256:C9E7E37D46601196E0DDA5D42FDF80C533DAB4CDF09D68E5A7C9A86C05795E00 | |||
| 7452 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\Users\admin\Desktop\2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | executable | |
MD5:4DA13A963E70EC892D0A70B3B052F5B9 | SHA256:1FA5D8CC5FB8FF5D877A9EC25D3744FF8FD25CEDB89C7018EE34D974A6A93A8A | |||
| 7668 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{D55A1C54-B99D-4317-BB4A-11CEDA9961B6}\.ba\1040\thm.wxl | xml | |
MD5:29AECDE585E557A812B86141F0656043 | SHA256:04FAD78A493E7123CABCFD4E0A405AF3FD2175CF24AD4CE93B30539029FEC5C3 | |||
| 7648 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A891825C-5B50-4B34-B565-4F1C356C773F}\.cr\2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | executable | |
MD5:D5A4A8FEF54BF3C2D09D14E7CFEAAA88 | SHA256:B791DC8ACE5E60989D47DBE0BE982F7623C1FAE5EEED569A2AF9D17BD9A941A2 | |||
| 7668 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{D55A1C54-B99D-4317-BB4A-11CEDA9961B6}\.ba\1031\thm.wxl | xml | |
MD5:D9F3E60B1262A4140991C47BC9D2E37F | SHA256:6B37D837535CA6AB6D46703EADF9CD87965DE6DA66F034F0053F52971150FC43 | |||
| 7668 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{D55A1C54-B99D-4317-BB4A-11CEDA9961B6}\.ba\thm.wxl | xml | |
MD5:4479C9AAAAE17F8009392786F0910789 | SHA256:34919F9197533A6BA636941A91E33E57338FB86A821FA02BF586CB80E9EEBDB2 | |||
| 7668 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{D55A1C54-B99D-4317-BB4A-11CEDA9961B6}\.ba\1028\thm.wxl | xml | |
MD5:9FE46D49770E77244310F4792D3D80E3 | SHA256:E223393A3CD462D725D56D687DFB2EB3CC1C380D7CCFAD12329547F6816979ED | |||
| 7668 | 2025-04-20_20b82bbbdb93a69f62160f11333d4f2f_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{D55A1C54-B99D-4317-BB4A-11CEDA9961B6}\.ba\1033\thm.wxl | xml | |
MD5:4479C9AAAAE17F8009392786F0910789 | SHA256:34919F9197533A6BA636941A91E33E57338FB86A821FA02BF586CB80E9EEBDB2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
41
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 172.202.163.200:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 172.202.163.200:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
7448 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7448 | SIHClient.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7448 | SIHClient.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
7448 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7448 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7448 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7448 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
7448 | SIHClient.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |