| File name: | 554200-108024V1Detallespdf.exe |
| Full analysis: | https://app.any.run/tasks/25b46f8c-0cdb-47ca-9973-1ca9f223d280 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 17:22:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2C040429AE3D91F1587F1A1E01F7CF1A |
| SHA1: | 92AC6C88D80EA8440DD22E3762DF550D207FDA16 |
| SHA256: | D7ACA0D03A0BB5F4BF7C6B67E985CFE02D3C0201A78D60BF1CC589182A850553 |
| SSDEEP: | 24576:5Jlh9bDN+ApFWTONIyCjeod84jYjno04bGpDoUpX4FNnnVQb1/WQF:5JGATWTEItZd8FnogpLBUNnGb1eQF |
MALICIOUS
Application was dropped or rewritten from another process
- hcs.exe (PID: 2496)
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 3032)
- hcs.exe (PID: 740)
- hcs.exe (PID: 3216)
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 1516)
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 2492)
Connects to CnC server
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 1516)
Loads dropped or rewritten executable
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 1516)
Changes settings of System certificates
- AdobeARM.exe (PID: 2644)
- AcroRd32.exe (PID: 2808)
SUSPICIOUS
Creates files in the program directory
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 1516)
- 554200-108024V1Detallespdf.exe (PID: 3924)
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 2492)
- AdobeARM.exe (PID: 2644)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 2808)
Application launched itself
- 554200-108024V1Detallespdf.exe (PID: 2728)
Executable content was dropped or overwritten
- 554200-108024V1Detallespdf.exe (PID: 3924)
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 2492)
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 1516)
Low-level read access rights to disk partition
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 1516)
Adds / modifies Windows certificates
- AdobeARM.exe (PID: 2644)
- AcroRd32.exe (PID: 2808)
Executed as Windows Service
- support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe (PID: 3032)
INFO
Application launched itself
- AcroRd32.exe (PID: 2808)
- RdrCEF.exe (PID: 3036)
Reads the hosts file
- RdrCEF.exe (PID: 3036)
Reads Internet Cache Settings
- AcroRd32.exe (PID: 2652)
- AcroRd32.exe (PID: 2808)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cab5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x0001B980 | 0x0001BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.53294 |
.reloc | 0x00076000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.8187 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 5.14816 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 4.37591 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 3.97928 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
51
Monitored processes
15
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 740 | "C:\ProgramData\Anyplace Control Support\hcs.exe" "/effects=onC:\ProgramData\Anyplace?Control?Support\apc-settings.ini" | C:\ProgramData\Anyplace Control Support\hcs.exe | — | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1516 | "" "/runsupportversion" | C:\Program Files\exa\support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 7.4.0.0 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\exa\support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe" | C:\Program Files\exa\support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | 554200-108024V1Detallespdf.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 7.4.0.0 Modules
| |||||||||||||||
| 2496 | "C:\ProgramData\Anyplace Control Support\hcs.exe" "/theme=onC:\ProgramData\Anyplace?Control?Support\apc-settings.ini" | C:\ProgramData\Anyplace Control Support\hcs.exe | — | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Program Files\exa\896554200-108024V1Detalles.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3036.0.786009772\1701403363" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\AppData\Local\Temp\554200-108024V1Detallespdf.exe" | C:\Users\admin\AppData\Local\Temp\554200-108024V1Detallespdf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Program Files\exa\896554200-108024V1Detalles.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | 554200-108024V1Detallespdf.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
1 863
Read events
628
Write events
1 234
Delete events
1
Modification events
| (PID) Process: | (2728) 554200-108024V1Detallespdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2728) 554200-108024V1Detallespdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3924) 554200-108024V1Detallespdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3924) 554200-108024V1Detallespdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2652) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2808) AcroRd32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Acrobatbrokerserverdispatchercpp789 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2652) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (2808) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 10001 | |||
| (PID) Process: | (2808) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | aFS |
Value: DOS | |||
| (PID) Process: | (2808) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tDIText |
Value: /C/Program Files/exa/896554200-108024V1Detalles.pdf | |||
Executable files
7
Suspicious files
5
Text files
43
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2652 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2652 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.2652 | — | |
MD5:— | SHA256:— | |||
| 2652 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.2652 | — | |
MD5:— | SHA256:— | |||
| 3924 | 554200-108024V1Detallespdf.exe | C:\Program Files\exa\support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | executable | |
MD5:— | SHA256:— | |||
| 1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | C:\ProgramData\Anyplace Control Support\apcErrorsLog.txt | text | |
MD5:— | SHA256:— | |||
| 2652 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R11rj3hg_nsqco5_21o.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1pr7dcv_nsqco4_21o.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1484nuu_nsqco3_21o.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R9tcsfh_nsqco2_21o.tmp | — | |
MD5:— | SHA256:— | |||
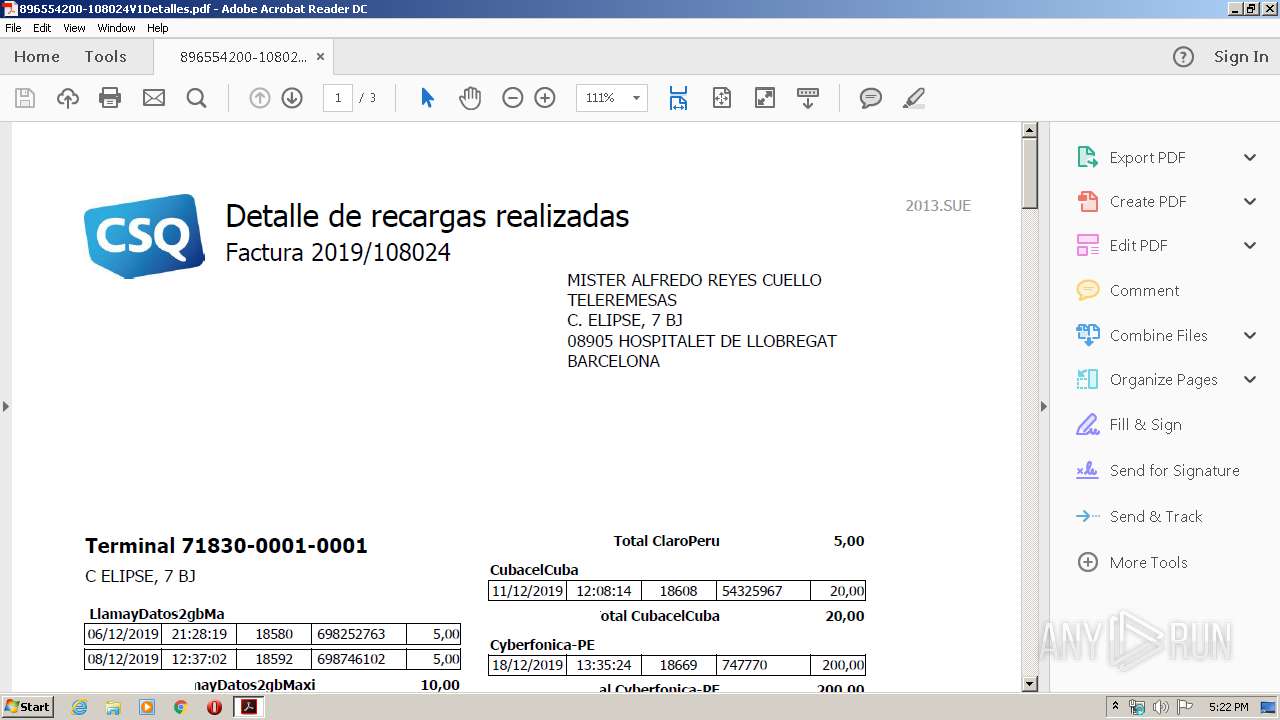
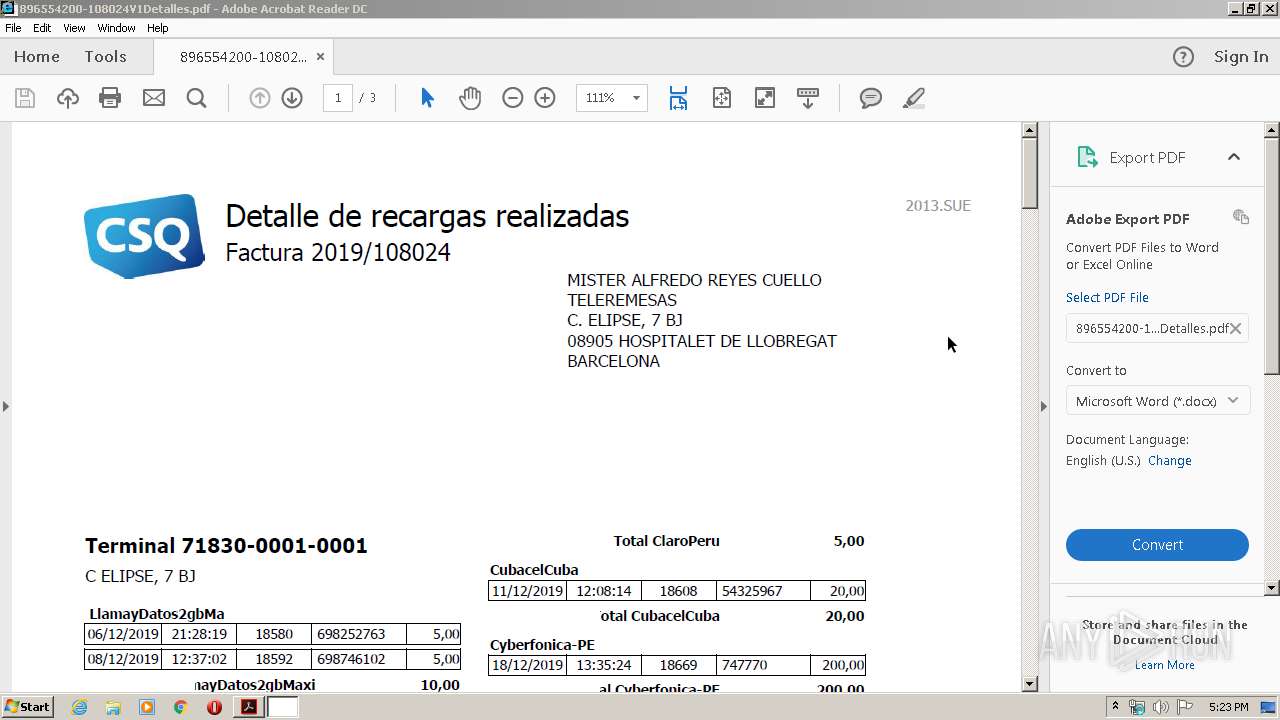
| 3924 | 554200-108024V1Detallespdf.exe | C:\Program Files\exa\896554200-108024V1Detalles.pdf | ||
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
8
DNS requests
6
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2808 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
2808 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2808 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2808 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2808 | AcroRd32.exe | GET | 200 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | compressed | 9.54 Kb | whitelisted |
2808 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | 76.72.163.161:443 | anyplace-gateway.info | Database by Design, LLC | US | malicious |
2808 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
2808 | AcroRd32.exe | 2.16.186.57:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
2808 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 23.58.217.61:443 | ardownload2.adobe.com | Akamai Technologies, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anyplace-gateway.info |
| malicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | ET INFO Anyplace Remote Access Initial Connection Attempt (005) |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | REMOTE [PTsecurity] AnyplaceControl.B |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | ET INFO Anyplace Remote Access Checkin (051) |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | REMOTE [PTsecurity] AnyplaceControl.B |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | ET INFO Anyplace Remote Access Initial Connection Attempt (005) |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | REMOTE [PTsecurity] AnyplaceControl.B |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | ET INFO Anyplace Remote Access Initial Connection Attempt (005) |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | A Network Trojan was detected | REMOTE [PTsecurity] AnyplaceControl.B |
1516 | support-Y3Jpc2dvbjg3QGdtYWlsLmNvbSAzODQ1MjMgNjM5NDU2MzY5Nzg5.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |