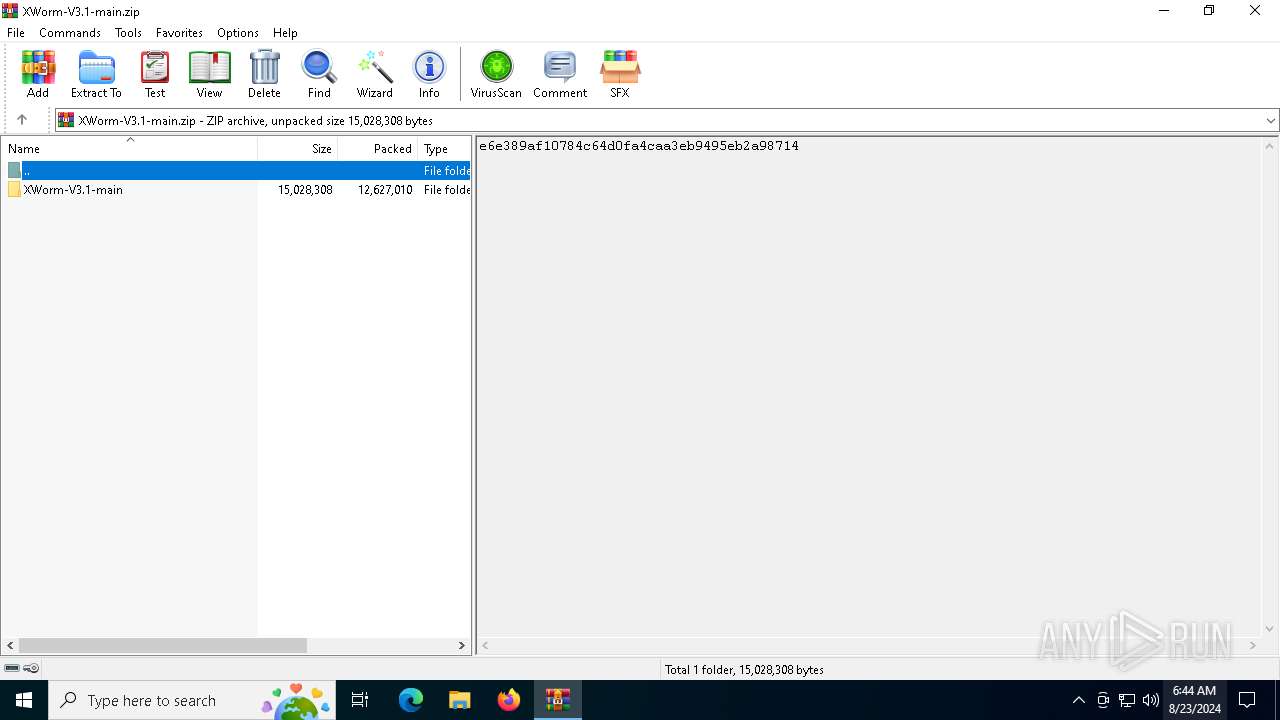
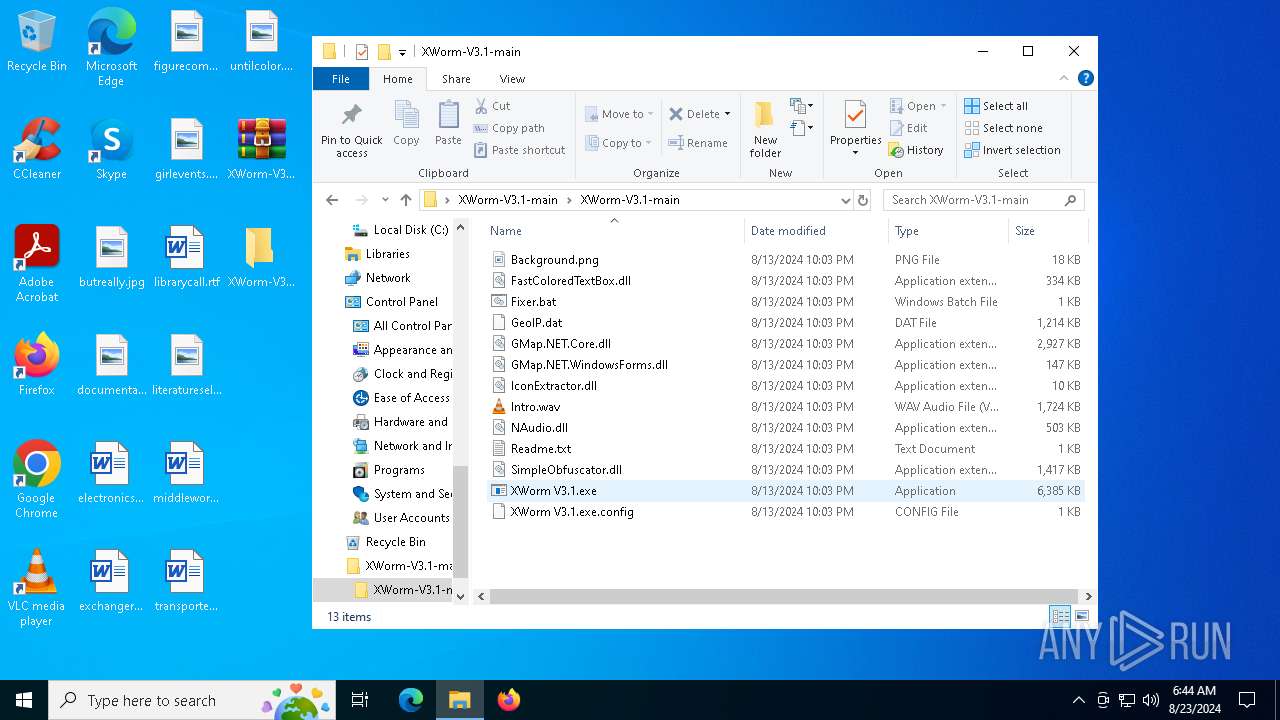
| File name: | XWorm-V3.1-main.zip |
| Full analysis: | https://app.any.run/tasks/164c50d8-7078-4a29-8657-dd84aede28cc |
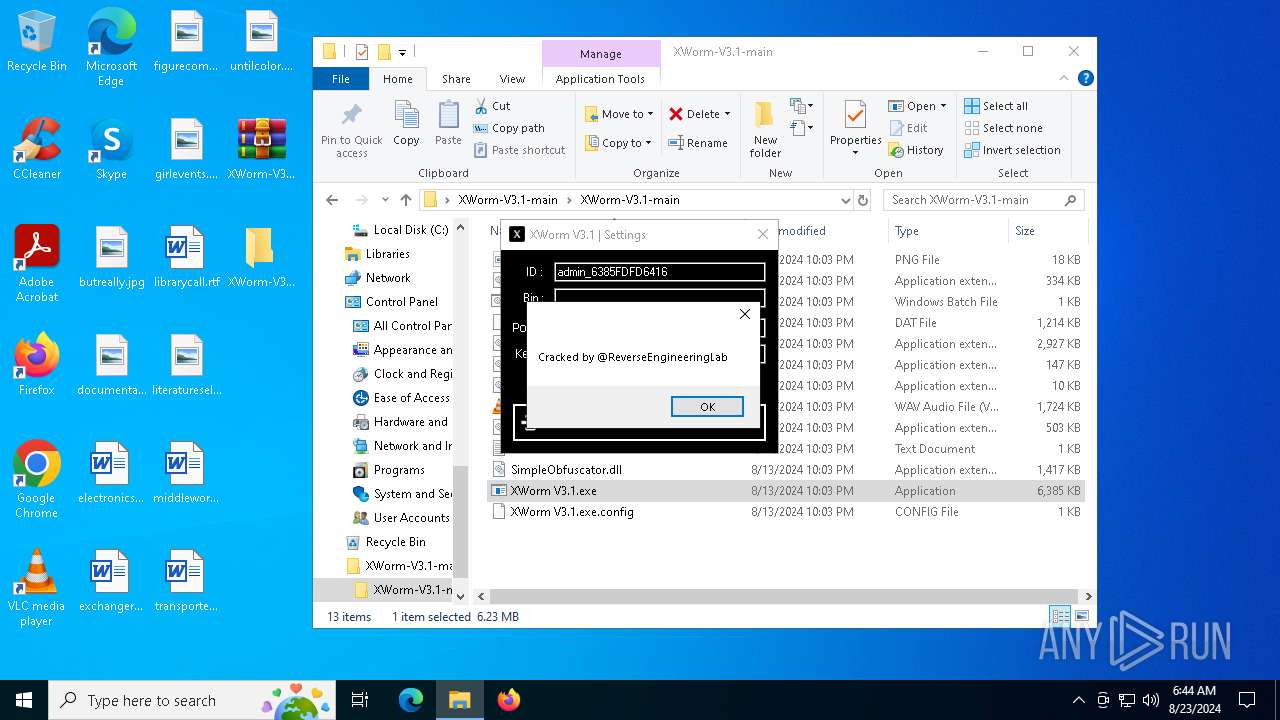
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2024, 06:44:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 61DCA6C636BE7E6866187BFB2971328F |
| SHA1: | 3B8CCF1944CC5861A72EC93AE9ED85A5ACFF46D0 |
| SHA256: | D7A30F8C998907FF7A08A1F437BD3A160209B51DBCD326CDB0C2AA2F9FF5FDD0 |
| SSDEEP: | 196608:VB/wF3dA5MO4/zr9inrSo7fJFRvhRJOg7V:vohS5MNLrEnrSAfFvfggh |
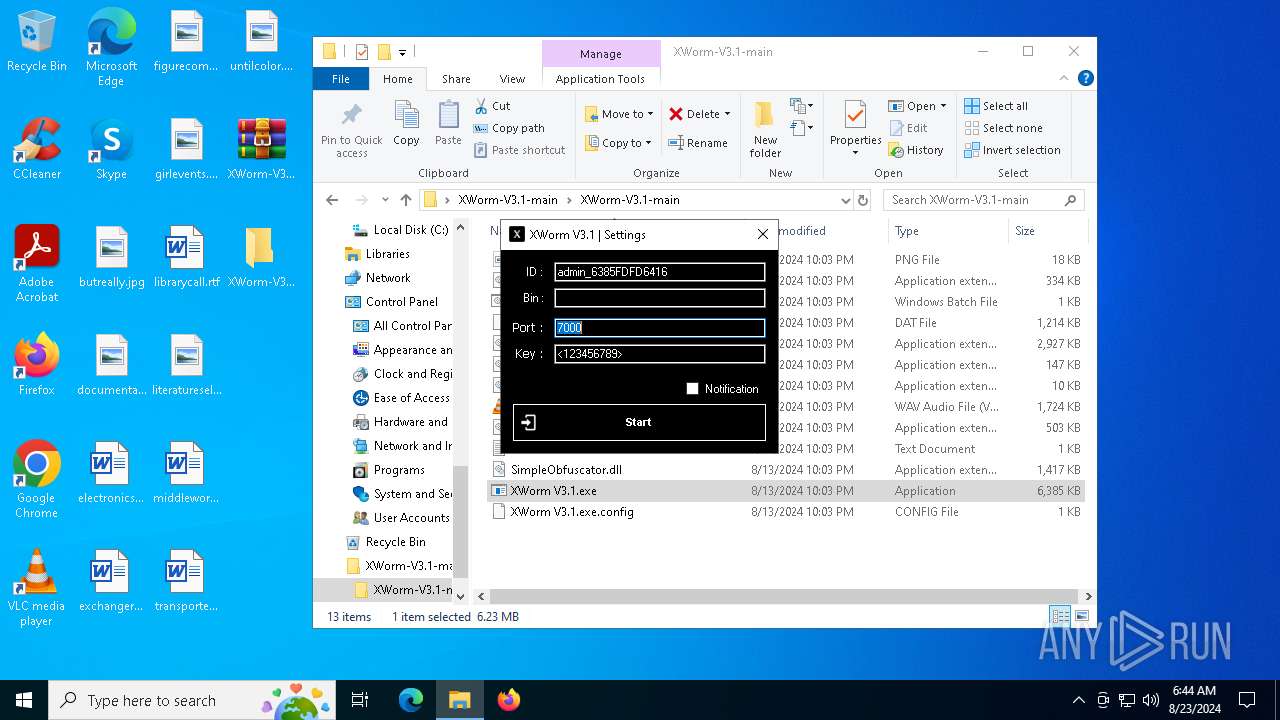
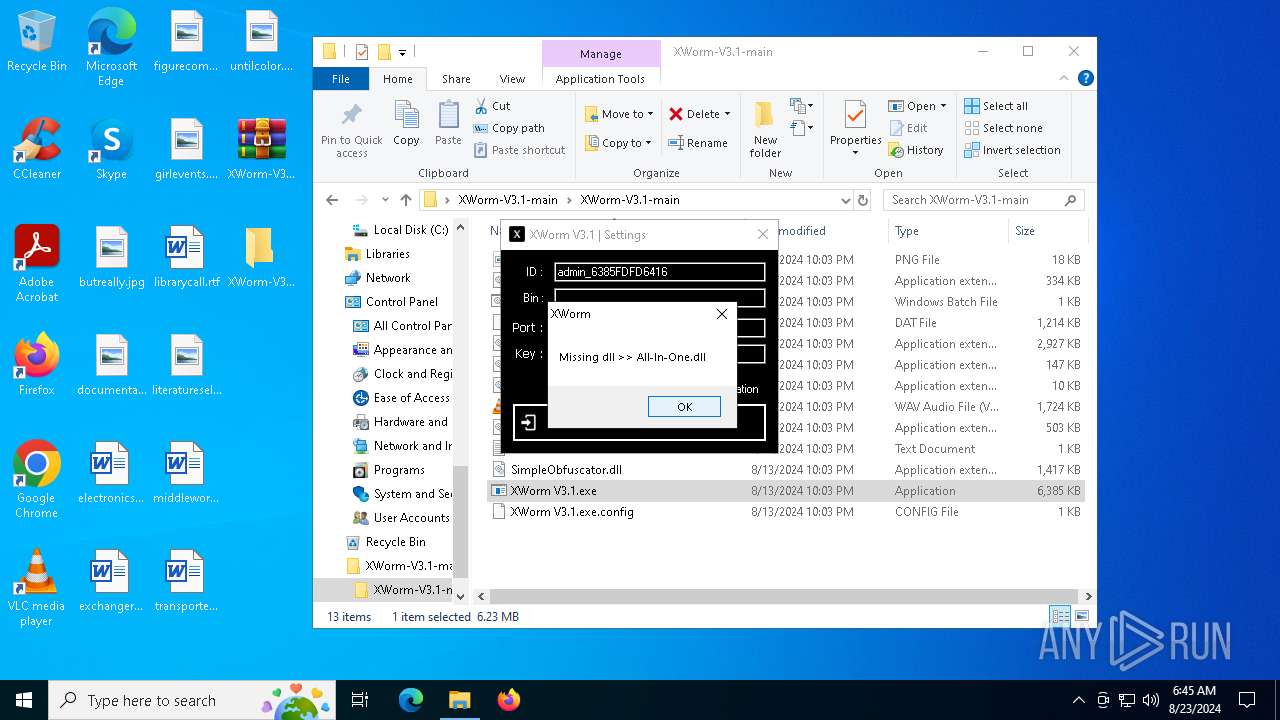
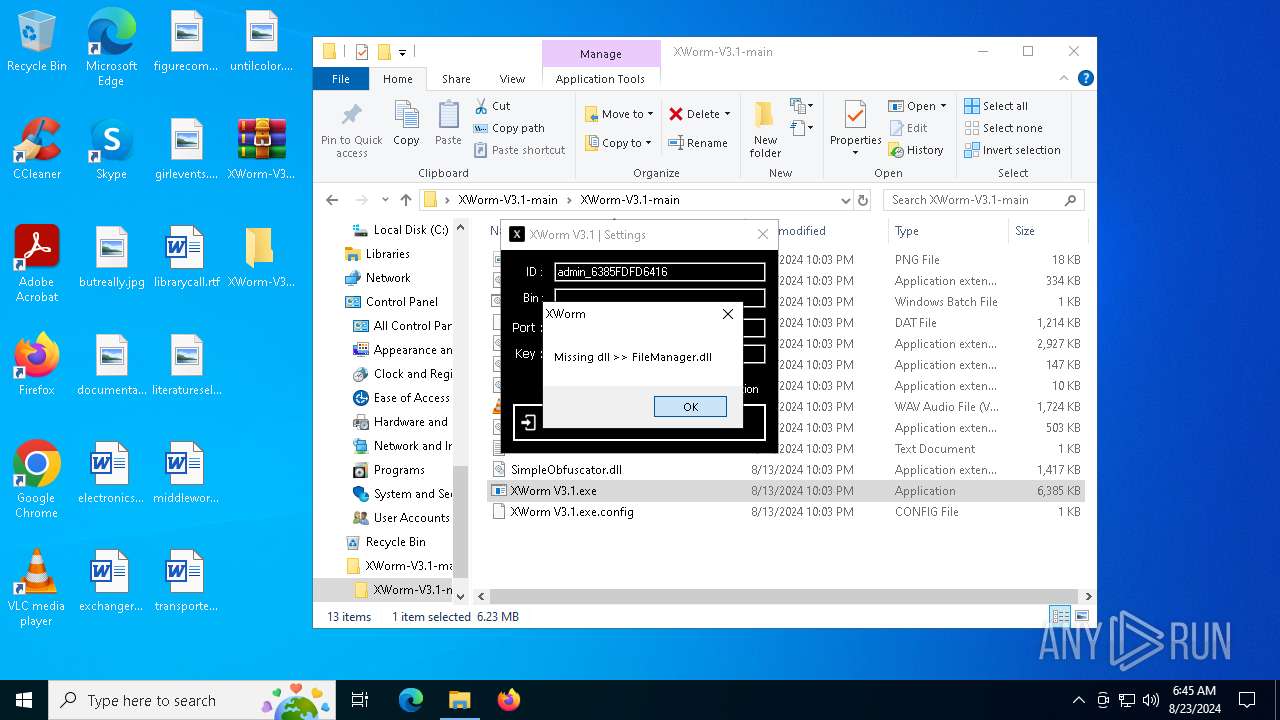
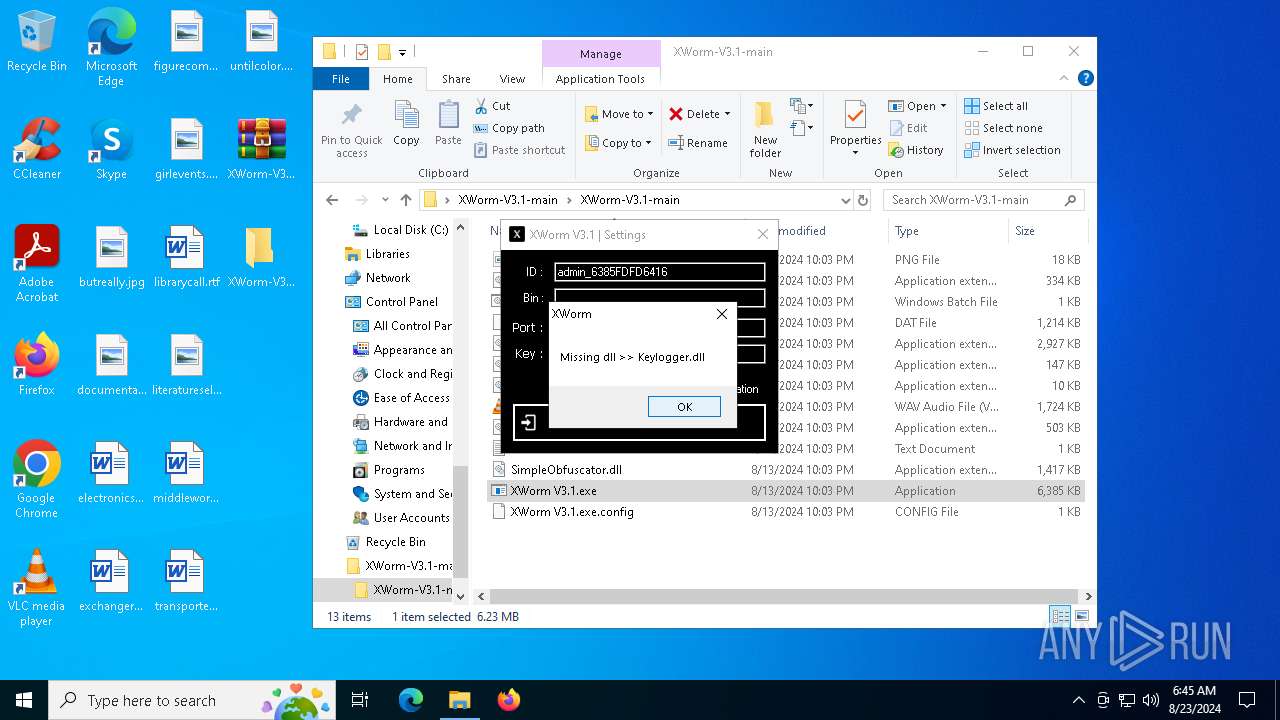
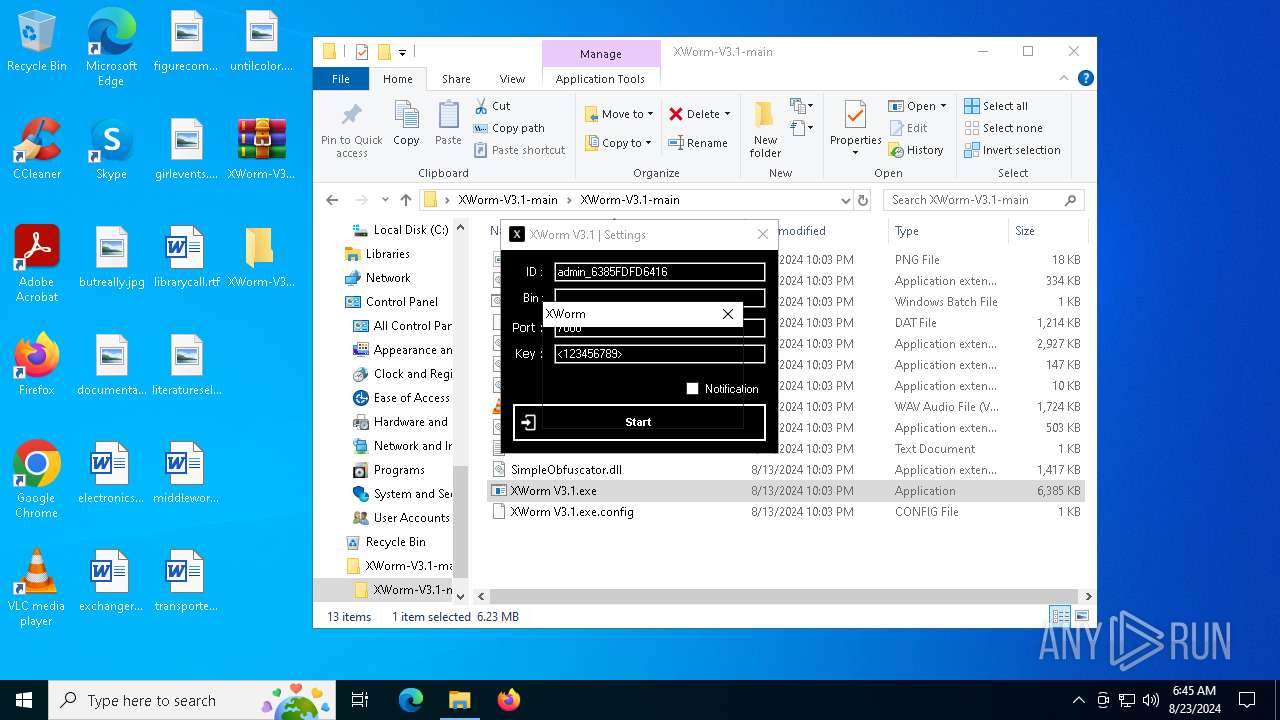
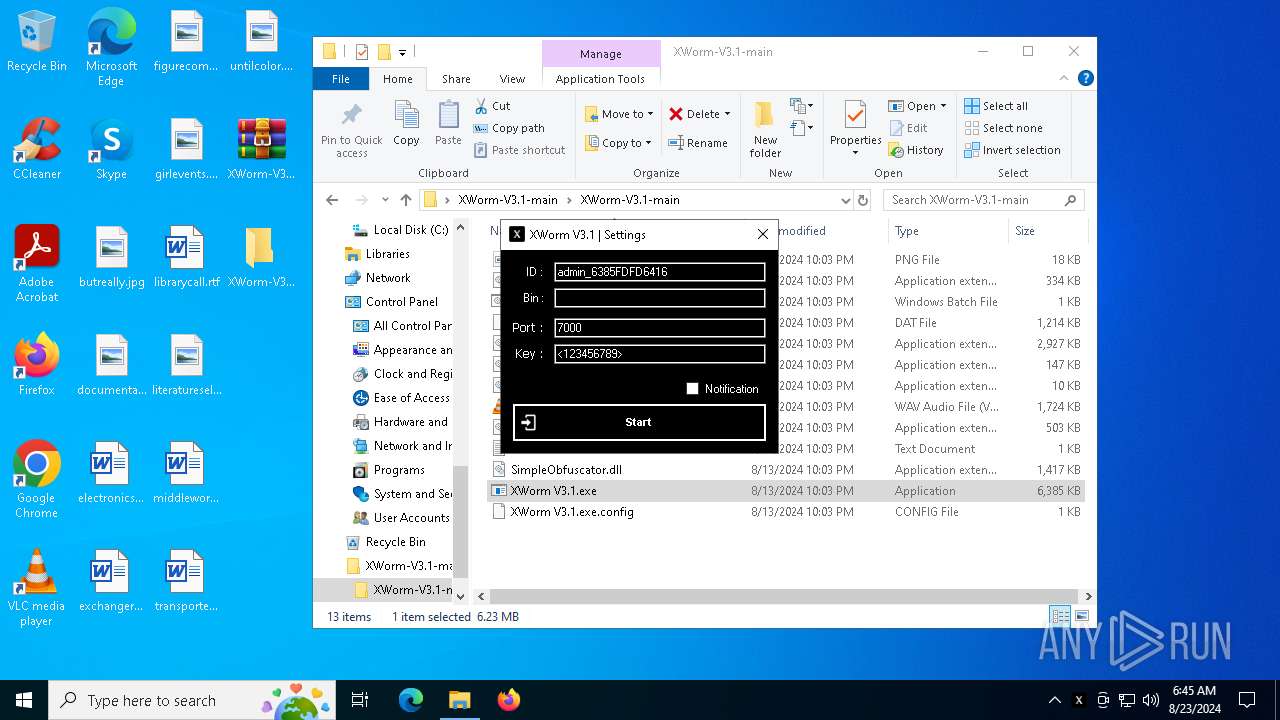
MALICIOUS
XORed URL has been found (YARA)
- XWorm V3.1.exe (PID: 6284)
SUSPICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6580)
- XWorm V3.1.exe (PID: 6216)
Executable content was dropped or overwritten
- XWorm V3.1.exe (PID: 6216)
Reads security settings of Internet Explorer
- XWorm V3.1.exe (PID: 6216)
Reads the date of Windows installation
- XWorm V3.1.exe (PID: 6216)
Found regular expressions for crypto-addresses (YARA)
- XWorm V3.1.exe (PID: 6284)
The process checks if it is being run in the virtual environment
- XWorm V3.1.exe (PID: 6284)
There is functionality for capture public ip (YARA)
- XWorm V3.1.exe (PID: 6284)
INFO
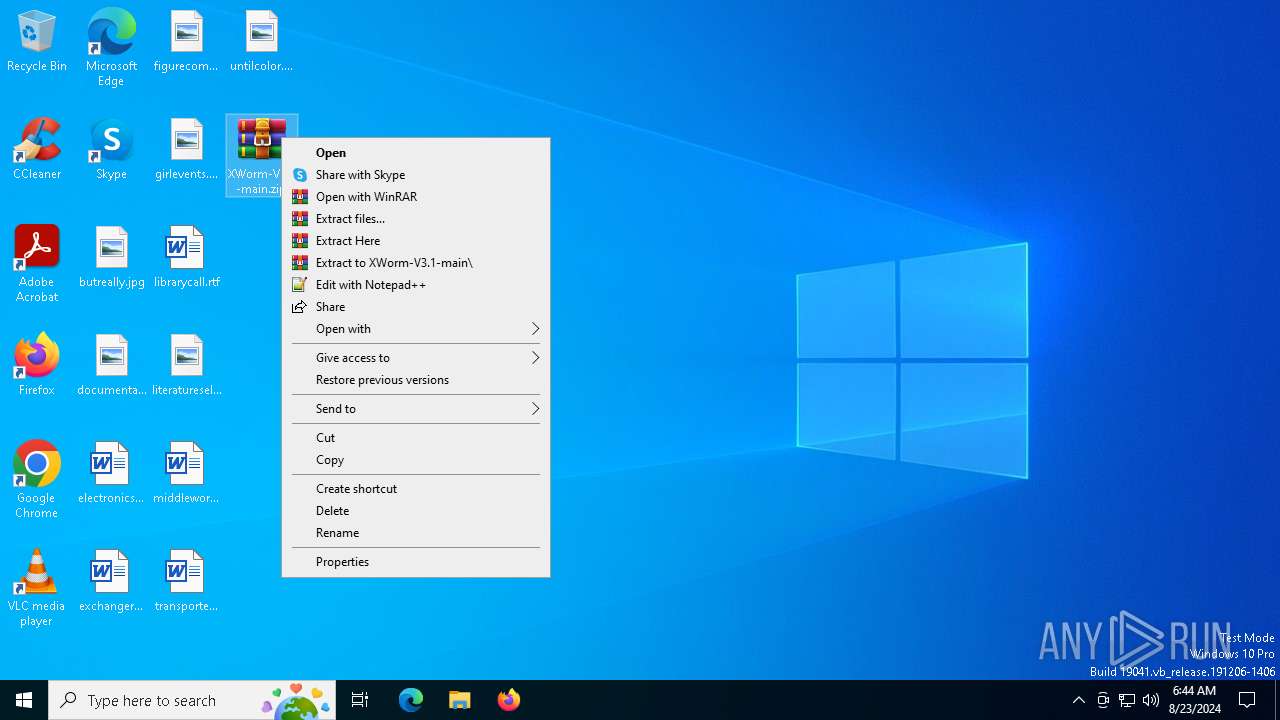
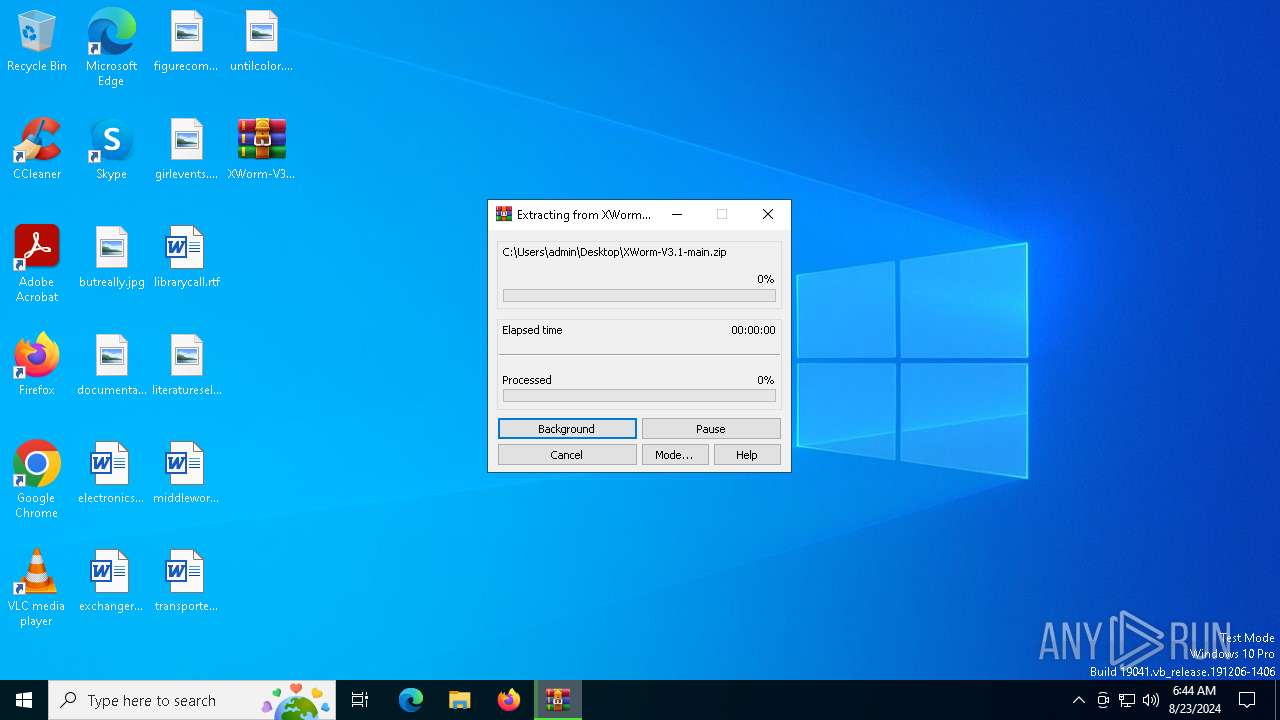
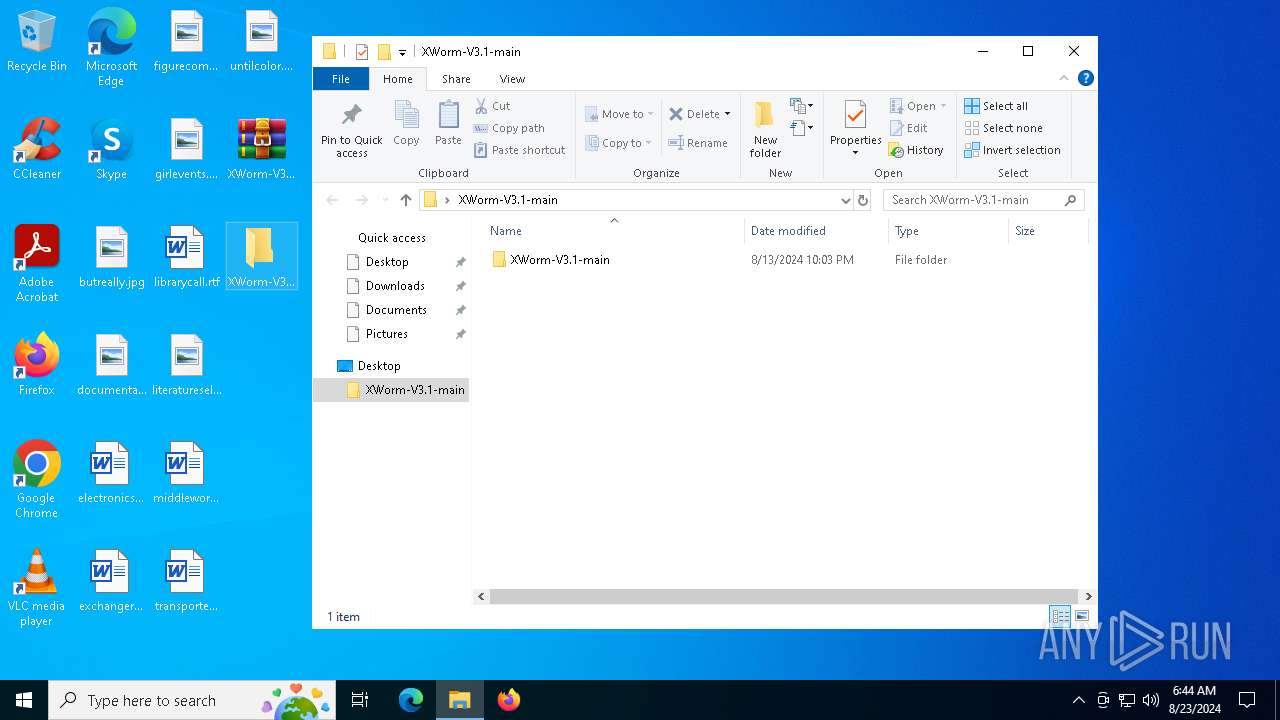
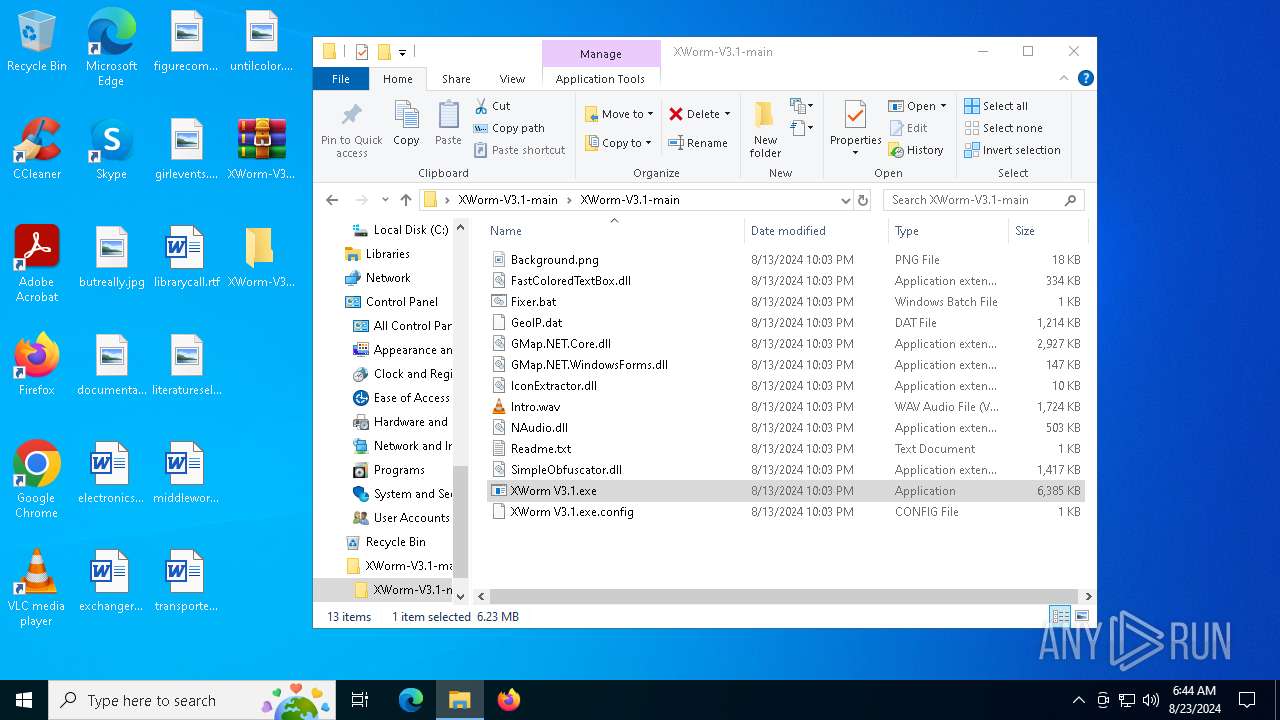
Manual execution by a user
- WinRAR.exe (PID: 6412)
- XWorm V3.1.exe (PID: 6216)
Reads the computer name
- XWorm V3.1.exe (PID: 6216)
- XWorm V3.1.exe (PID: 6284)
Reads the machine GUID from the registry
- XWorm V3.1.exe (PID: 6216)
- XWorm V3.1.exe (PID: 6284)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6412)
Checks supported languages
- XWorm V3.1.exe (PID: 6216)
- XWorm V3.1.exe (PID: 6284)
Create files in a temporary directory
- XWorm V3.1.exe (PID: 6216)
- XWorm V3.1.exe (PID: 6284)
Process checks computer location settings
- XWorm V3.1.exe (PID: 6216)
.NET Reactor protector has been detected
- XWorm V3.1.exe (PID: 6284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(6284) XWorm V3.1.exe
Decrypted-URLs (8)http://ip-api.com/csv/?fields=status,query#
http://www.example.com/File.exe!
http://www.example.com/File.exe)
http://www.example.com/XClient.exe*
https://pastebin.com/raw/H3wFXmEi+
https://t.me/XCoderGroup)
https://t.me/XCoderTools+
https://www.google.com/maps/place/$
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:08:13 15:03:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | XWorm-V3.1-main/ |
Total processes
134
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
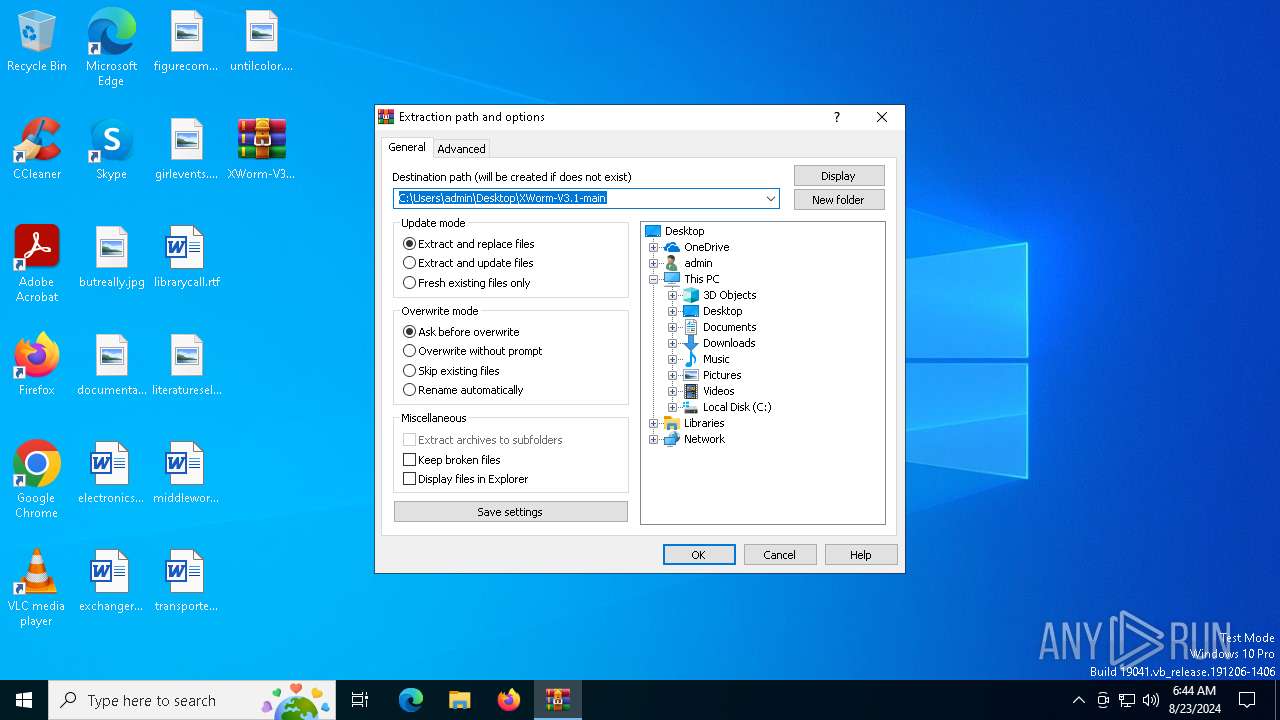
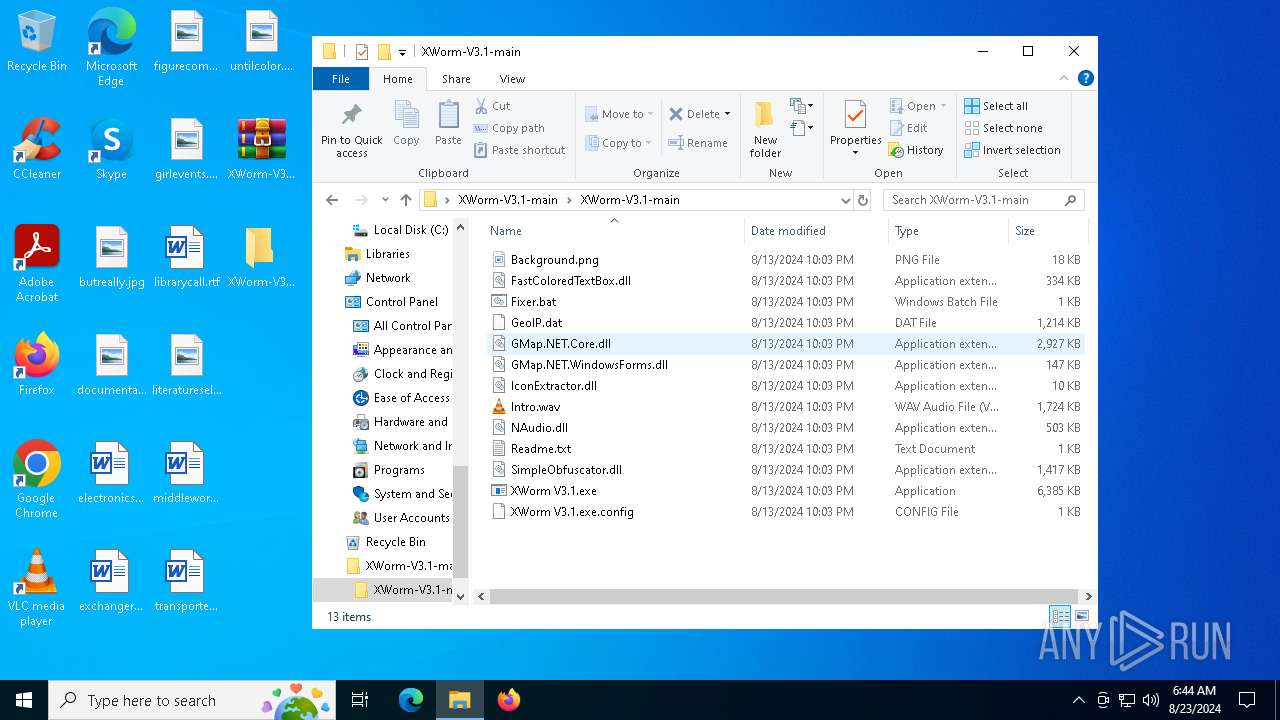
| 6216 | "C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\XWorm V3.1.exe" | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\XWorm V3.1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6284 | "C:\Users\admin\AppData\Local\Temp\XWorm V3.1.exe" | C:\Users\admin\AppData\Local\Temp\XWorm V3.1.exe | XWorm V3.1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
xor-url(PID) Process(6284) XWorm V3.1.exe Decrypted-URLs (8)http://ip-api.com/csv/?fields=status,query# http://www.example.com/File.exe! http://www.example.com/File.exe) http://www.example.com/XClient.exe* https://pastebin.com/raw/H3wFXmEi+ https://t.me/XCoderGroup) https://t.me/XCoderTools+ https://www.google.com/maps/place/$ | |||||||||||||||
| 6412 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\XWorm-V3.1-main.zip" "?\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6488 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6580 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\XWorm-V3.1-main.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
12 005
Read events
11 966
Write events
39
Delete events
0
Modification events
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\XWorm-V3.1-main.zip | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
8
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
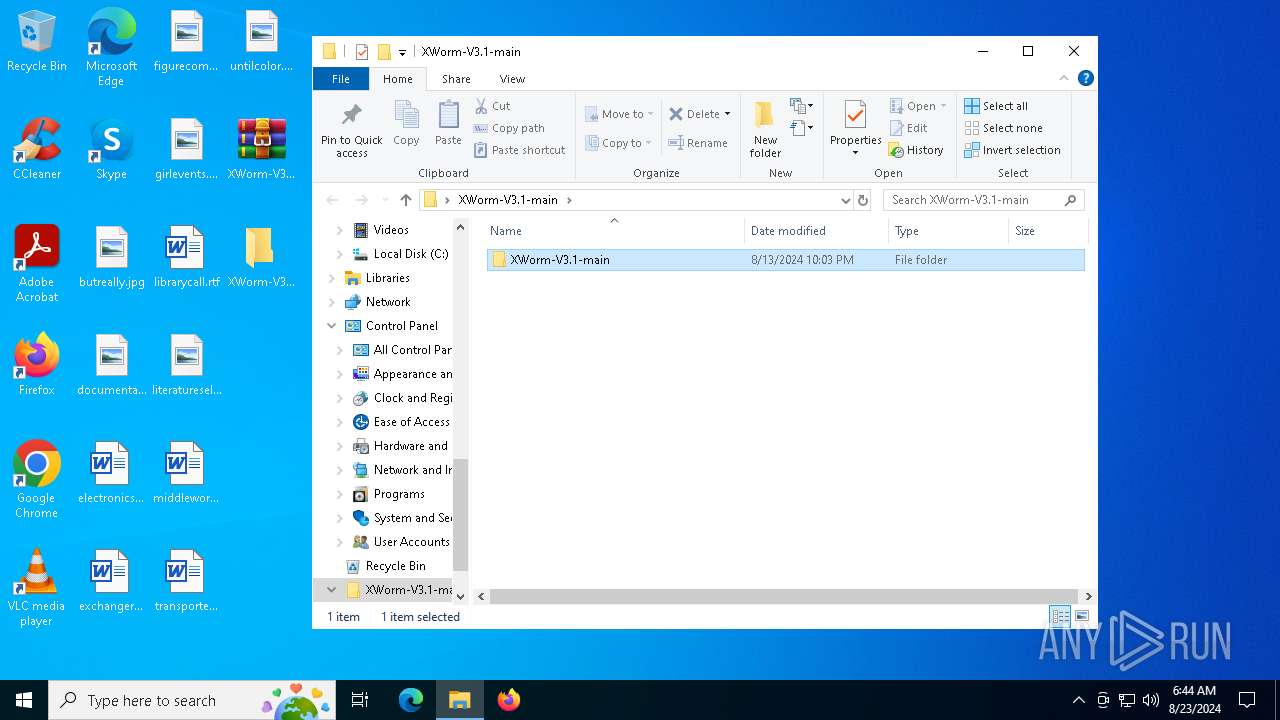
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\Background.png | image | |
MD5:A466FC11F42A6DE40E050C9813947612 | SHA256:5047DC90D705A1A50C325FC00B26D5290939C42D6AA727D09E8D21D0537CEC85 | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\IconExtractor.dll | executable | |
MD5:640D8FFA779C6DD5252A262E440C66C0 | SHA256:440912D85D2F98BB4F508AB82847067C18E1E15BE0D8ECDCFF0CC19327527FC2 | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\GMap.NET.WindowsForms.dll | executable | |
MD5:32A8742009FFDFD68B46FE8FD4794386 | SHA256:741E1A8F05863856A25D101BD35BF97CBA0B637F0C04ECB432C1D85A78EF1365 | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\GMap.NET.Core.dll | executable | |
MD5:819352EA9E832D24FC4CEBB2757A462B | SHA256:58C755FCFC65CDDEA561023D736E8991F0AD69DA5E1378DEA59E98C5DB901B86 | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\GeoIP.dat | binary | |
MD5:8EF41798DF108CE9BD41382C9721B1C9 | SHA256:BC07FF22D4EE0B6FAFCC12482ECF2981C172A672194C647CEDF9B4D215AD9740 | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\SimpleObfuscator.dll | executable | |
MD5:9043D712208178C33BA8E942834CE457 | SHA256:B7A6EEA19188B987DAD97B32D774107E9A1BEB4F461A654A00197D73F7FAD54C | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\Readme.txt | text | |
MD5:85122AD50370F9A829B6602384B1B644 | SHA256:444CBC7B57B4A6198EE1474FD9623E1AFCB8C7A0B180F05E961A822F4365499B | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\NAudio.dll | executable | |
MD5:3B87D1363A45CE9368E9BAEC32C69466 | SHA256:81B3F1DC3F1EAC9762B8A292751A44B64B87D0D4C3982DEBFDD2621012186451 | |||
| 6412 | WinRAR.exe | C:\Users\admin\Desktop\XWorm-V3.1-main\XWorm-V3.1-main\Intro.wav | binary | |
MD5:DC28D546B643C5A33C292AE32D7CF43B | SHA256:20DCC4F50EB47CAFDA7926735DF9EF8241598B83E233066EA495D4B8AA818851 | |||
| 6284 | XWorm V3.1.exe | C:\Users\admin\AppData\Local\Temp\Intro.wav | binary | |
MD5:DC28D546B643C5A33C292AE32D7CF43B | SHA256:20DCC4F50EB47CAFDA7926735DF9EF8241598B83E233066EA495D4B8AA818851 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
29
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6792 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6876 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2204 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2580 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3916 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2204 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2204 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6792 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
6792 | backgroundTaskHost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
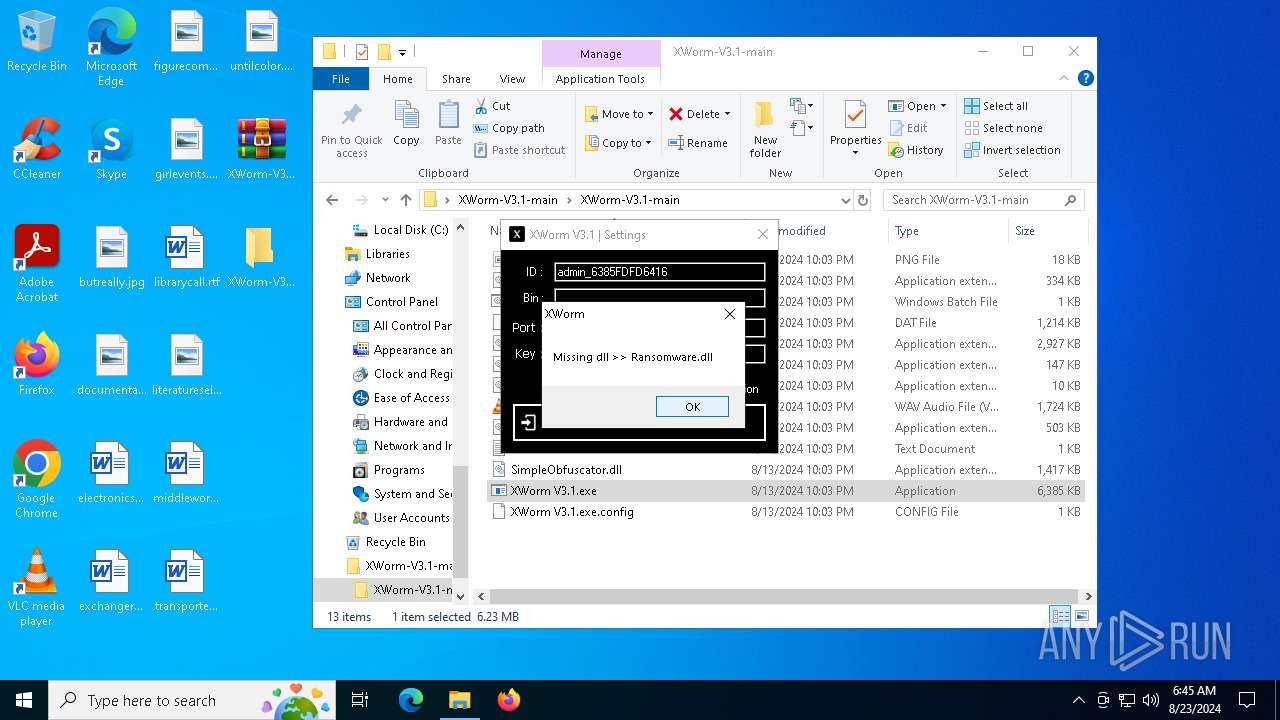
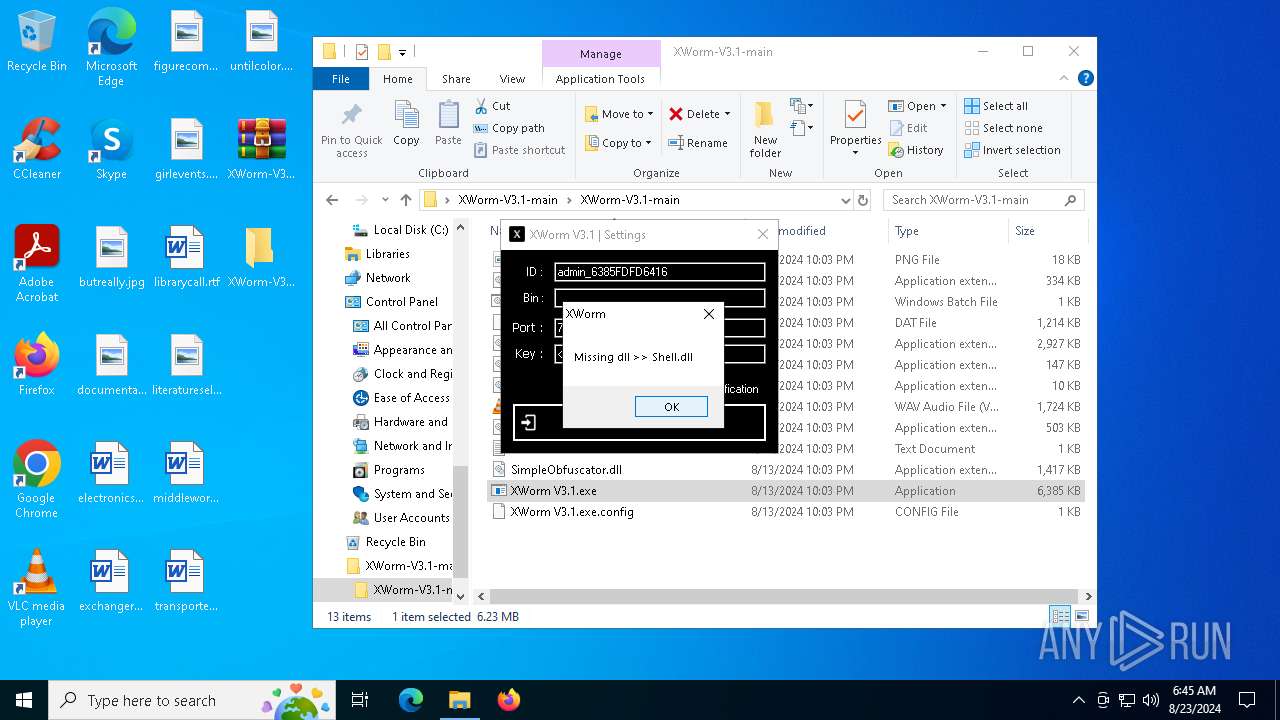
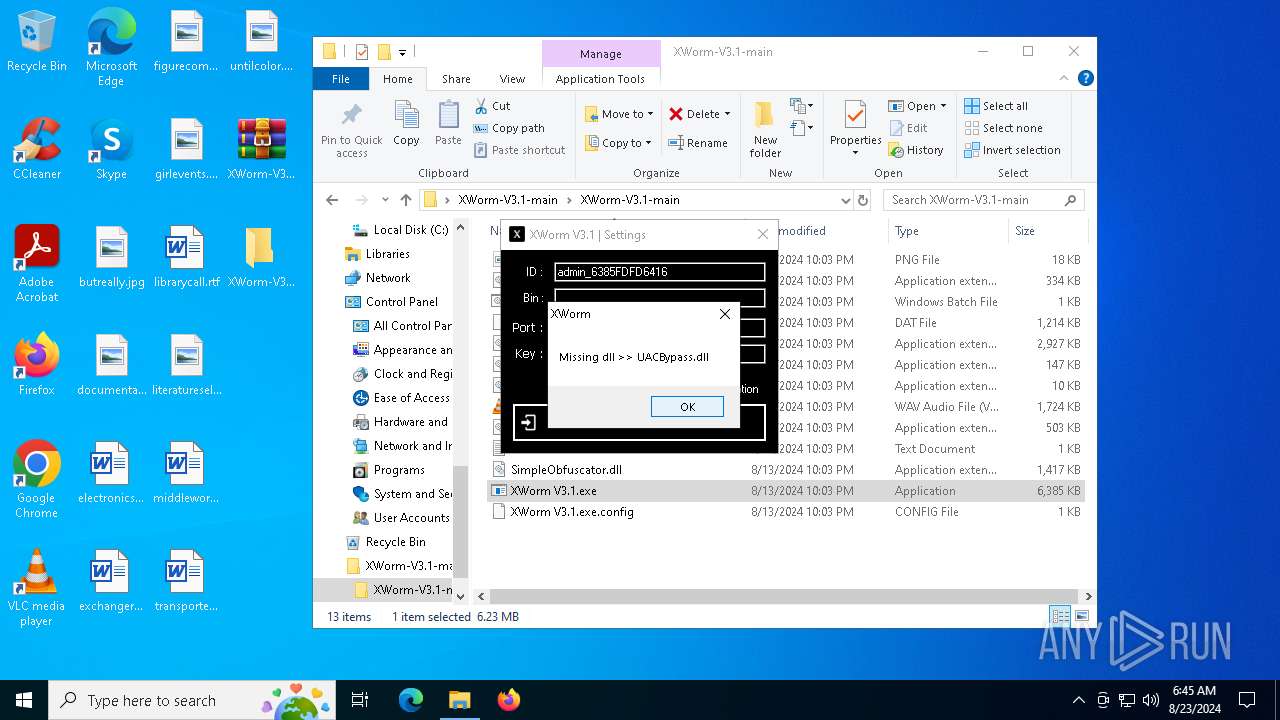
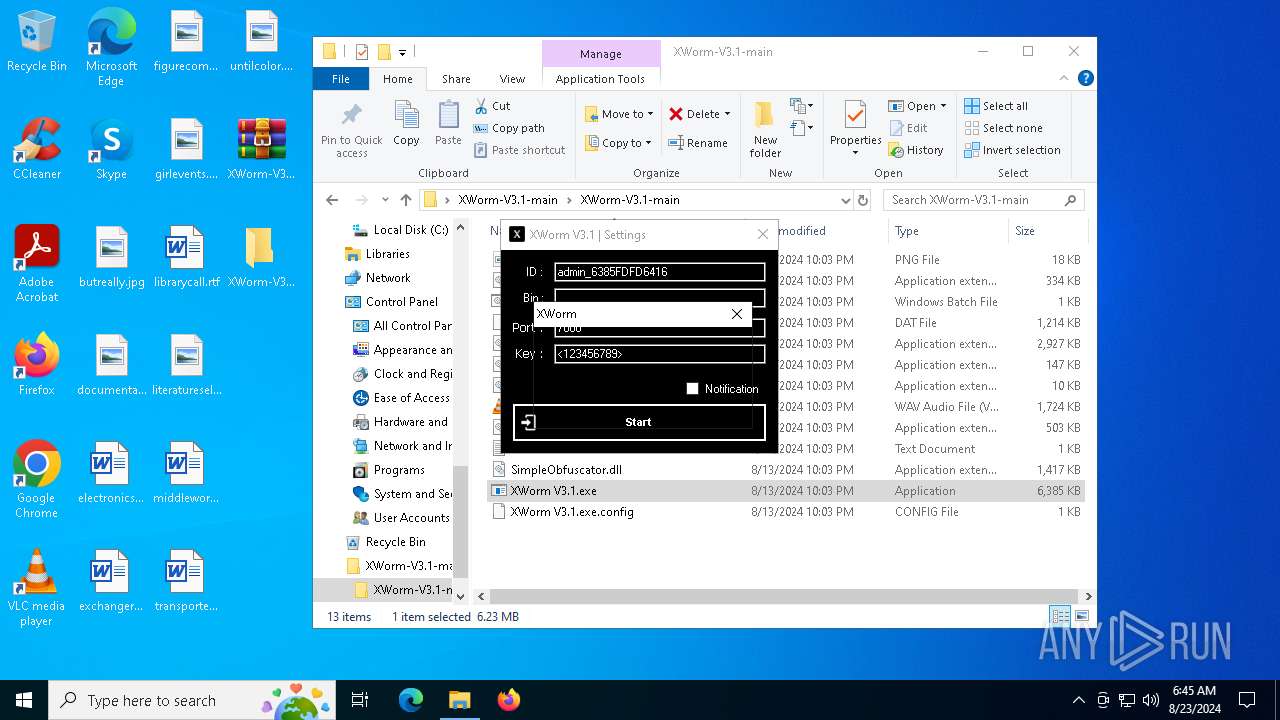
XWorm V3.1.exe | The type initializer for 'XWorm.Messages' threw an exception.
|