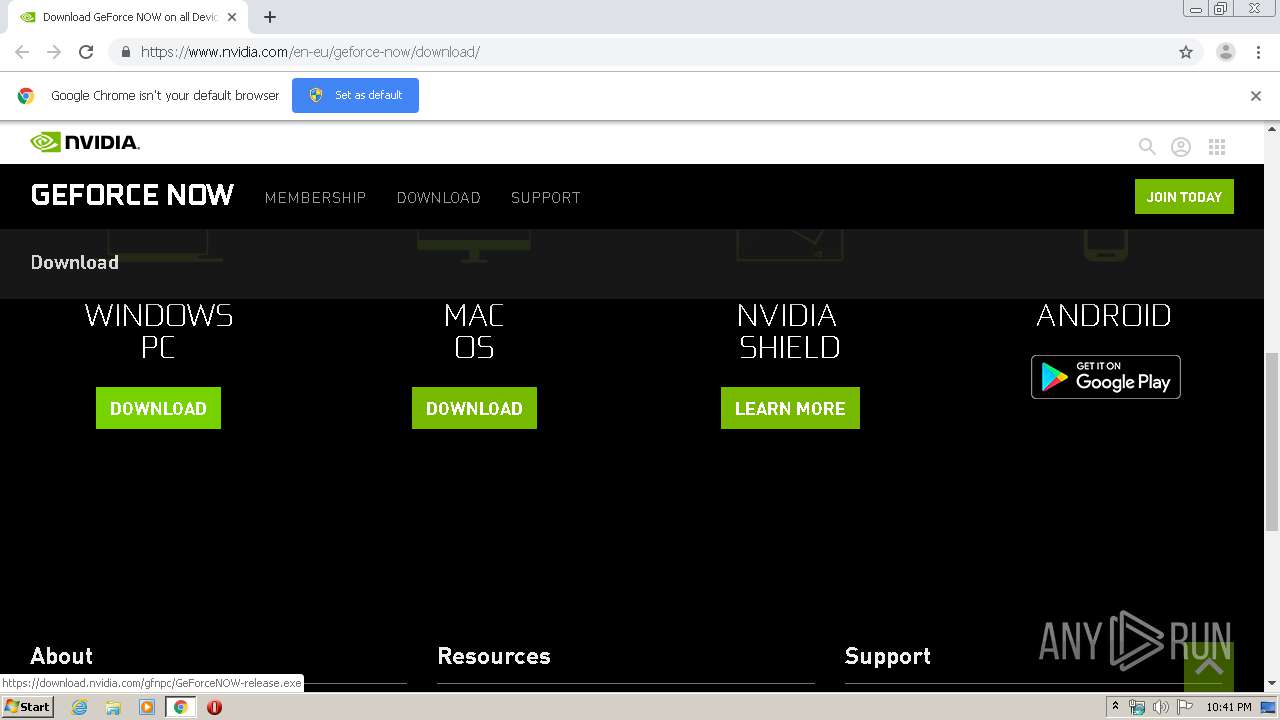
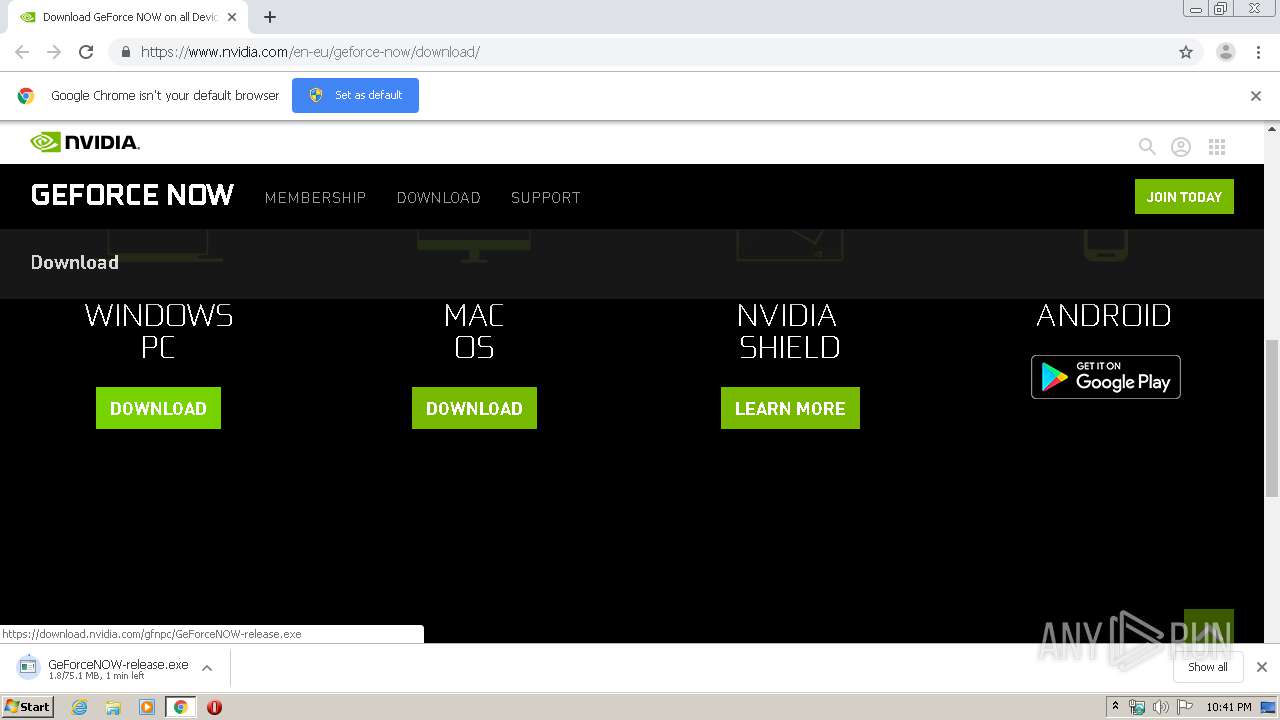
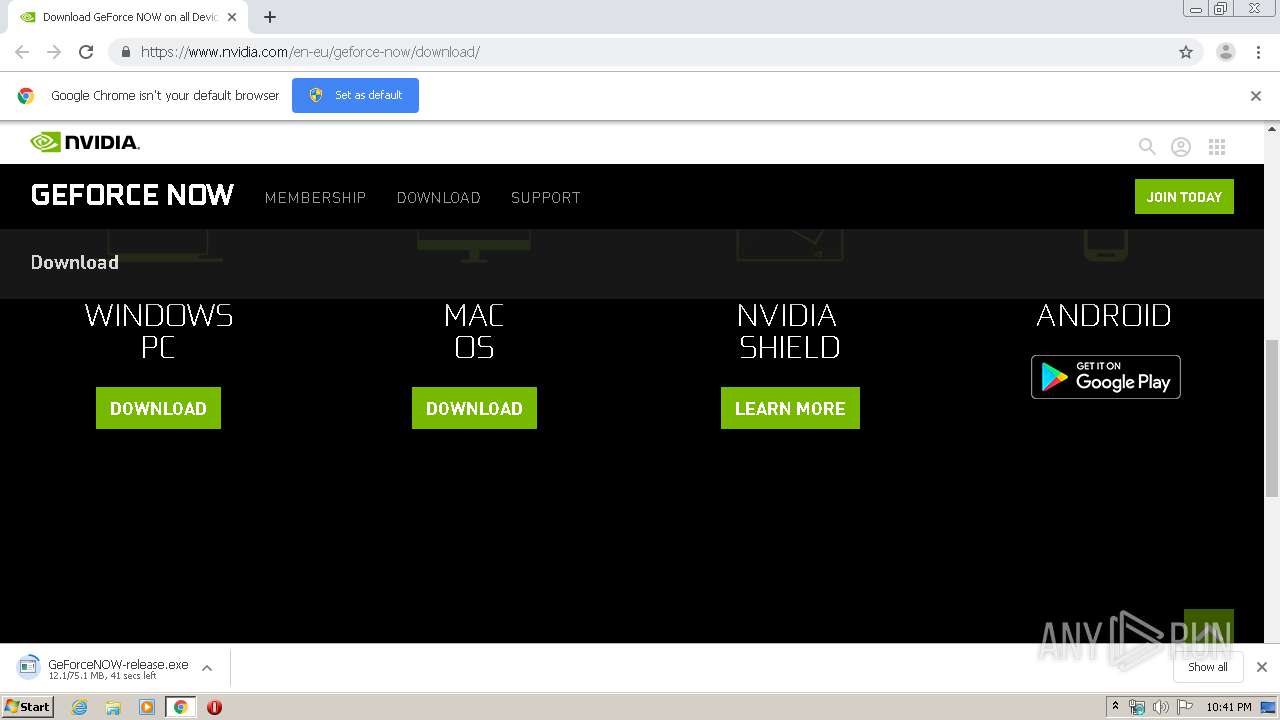
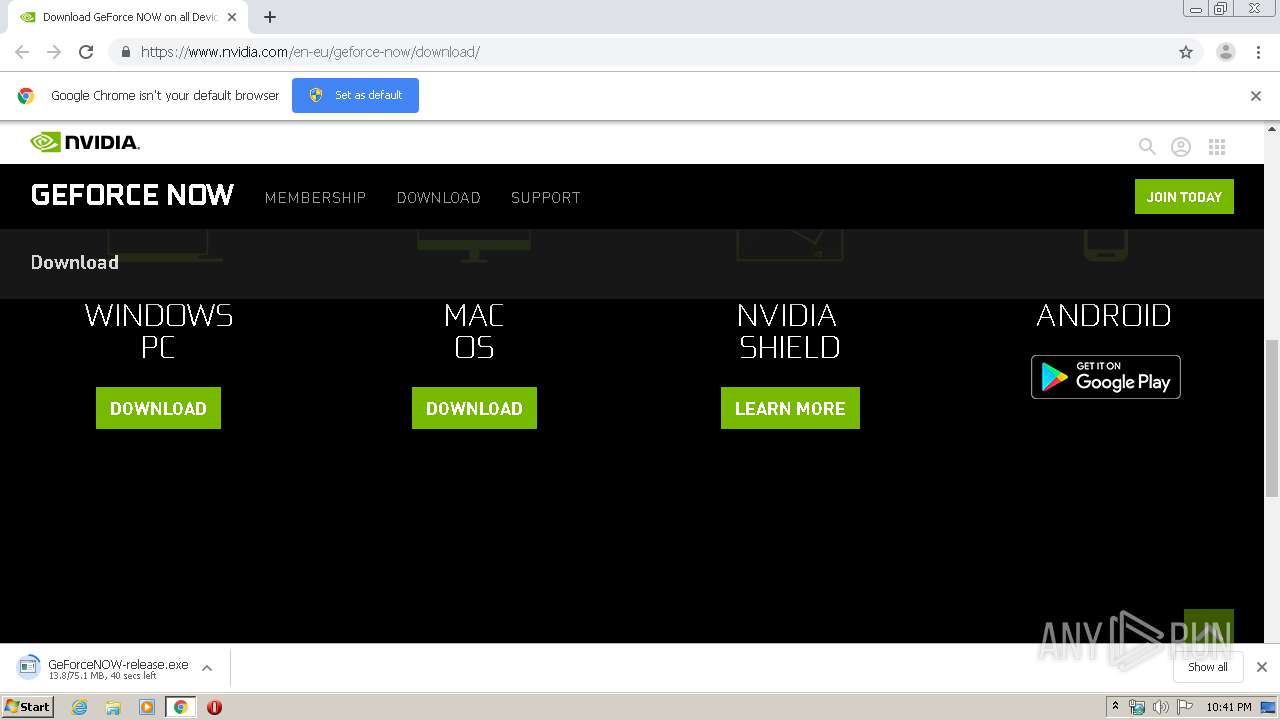
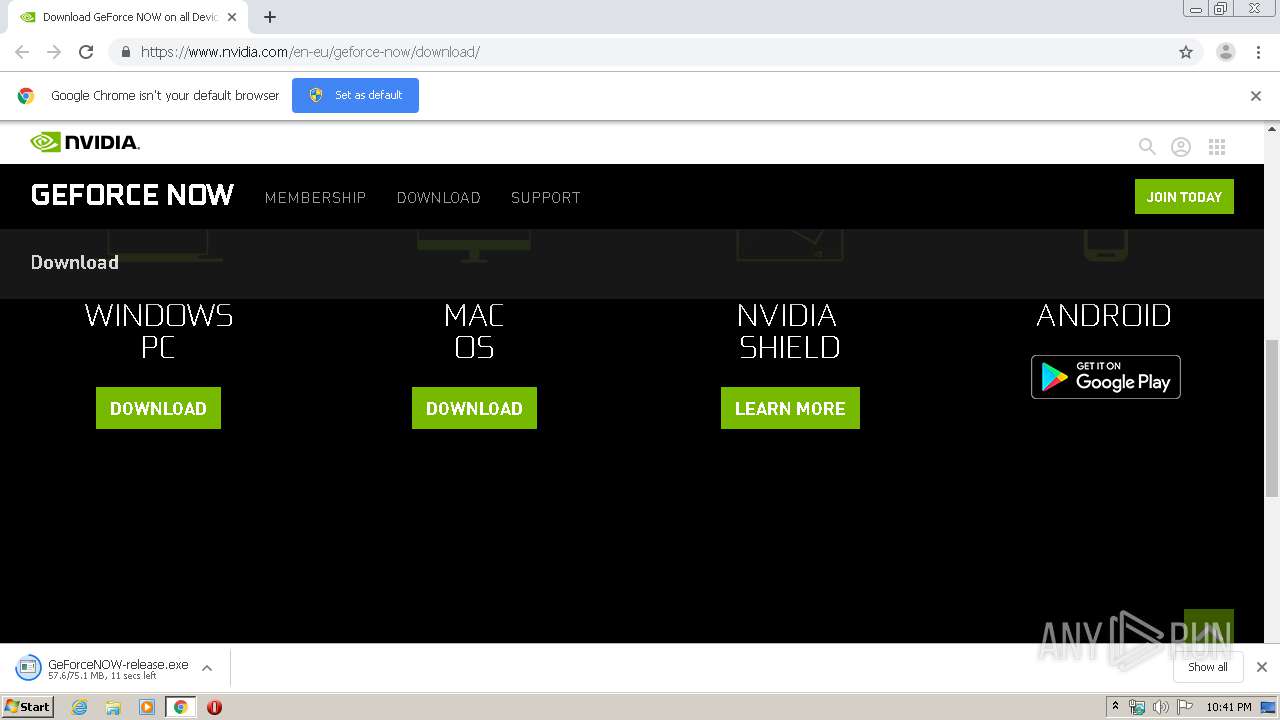
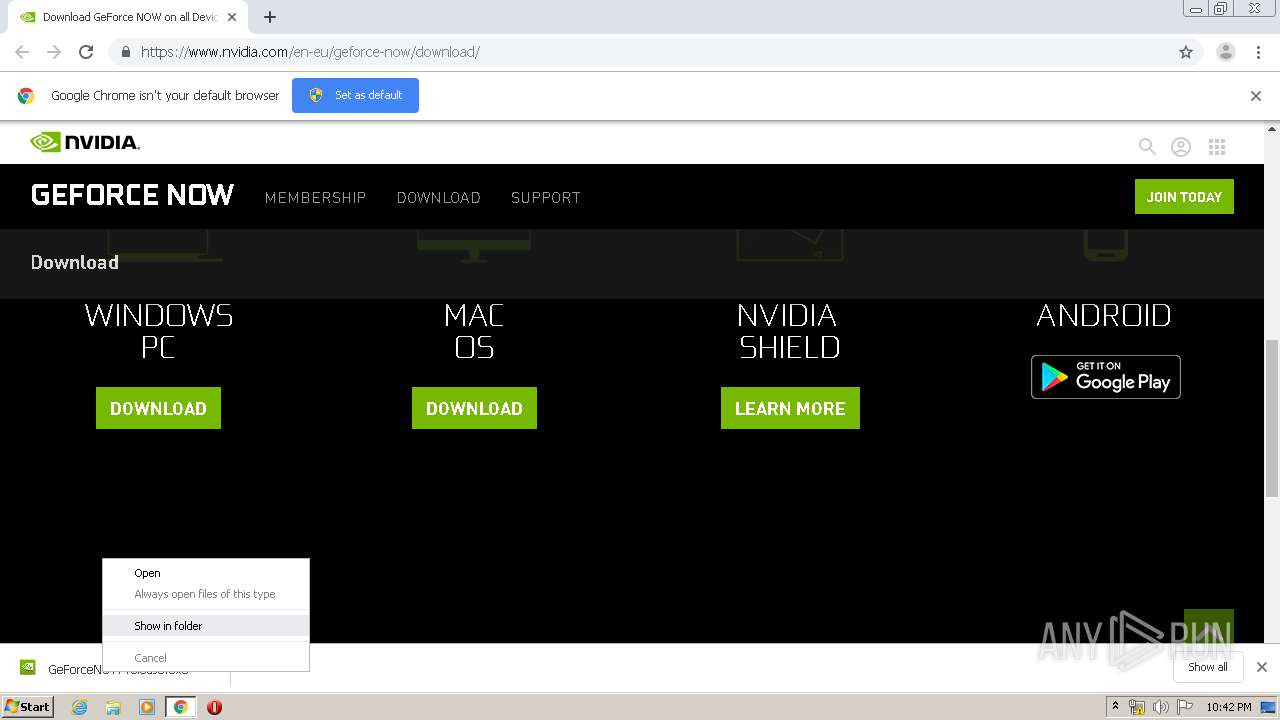
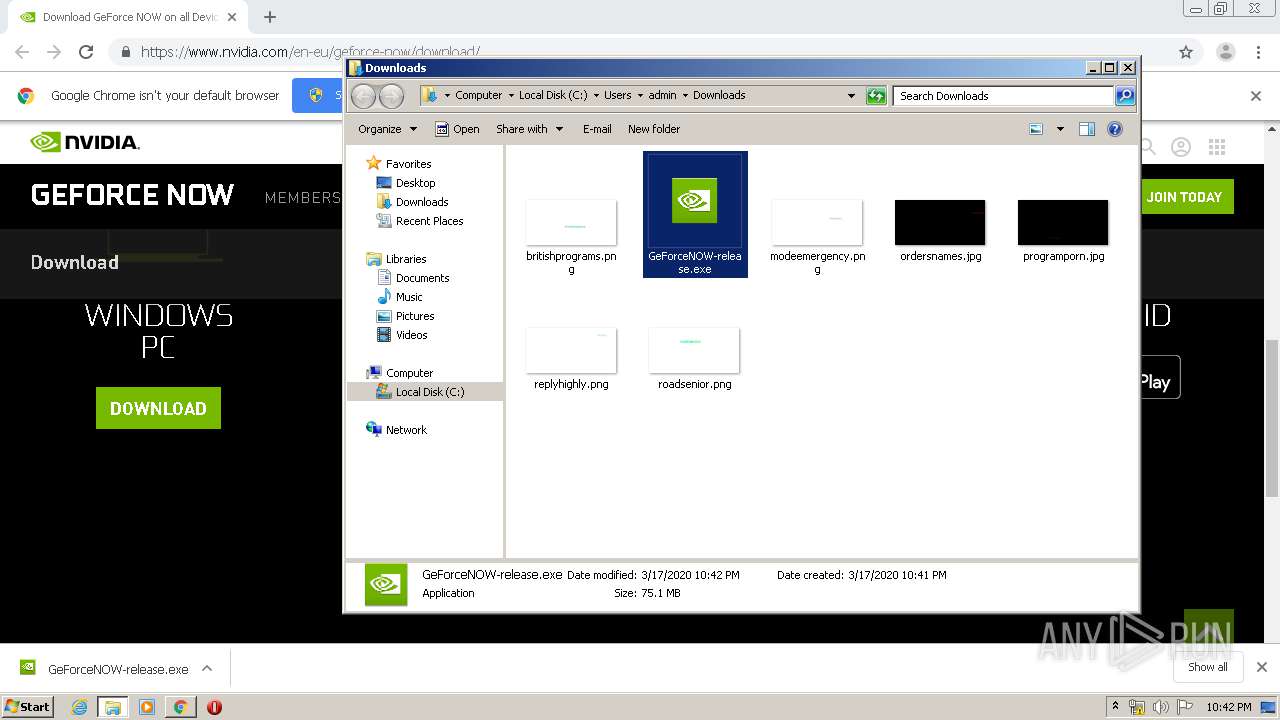
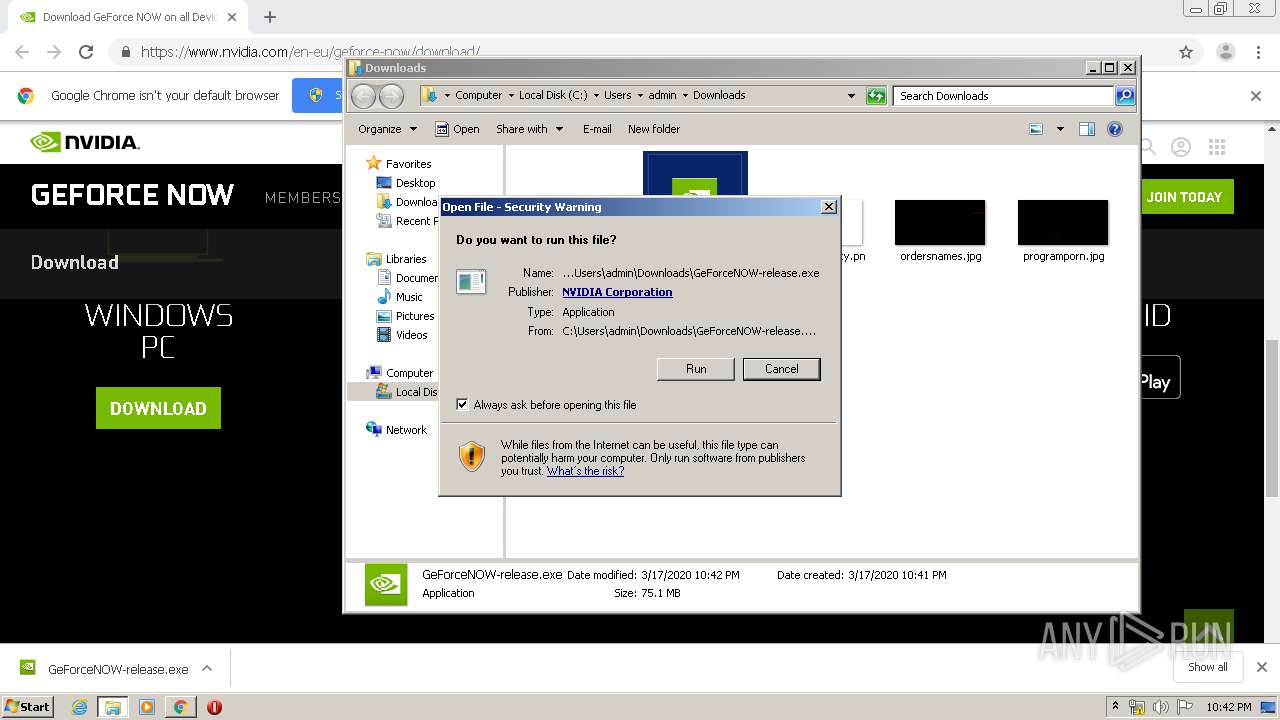
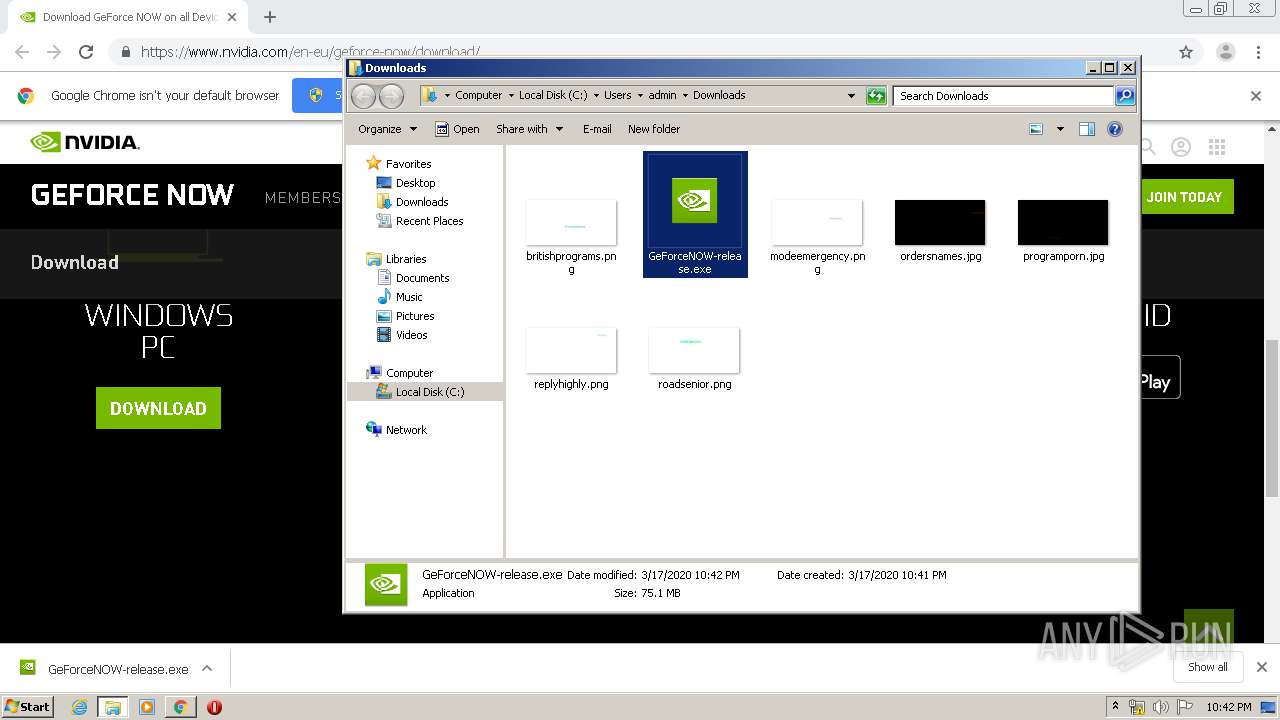
| URL: | https://www.nvidia.com/en-eu/geforce-now/download/ |
| Full analysis: | https://app.any.run/tasks/7e5fd7c3-ed04-4833-94a7-4827959962c4 |
| Verdict: | Malicious activity |
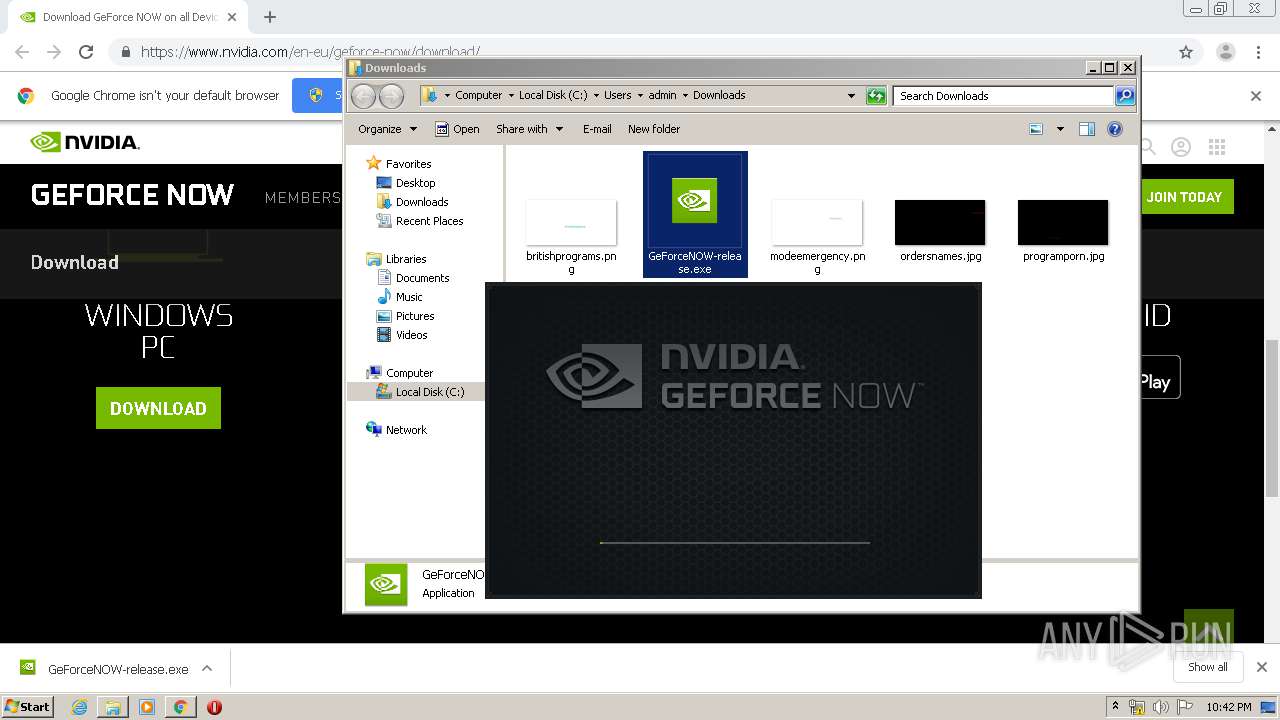
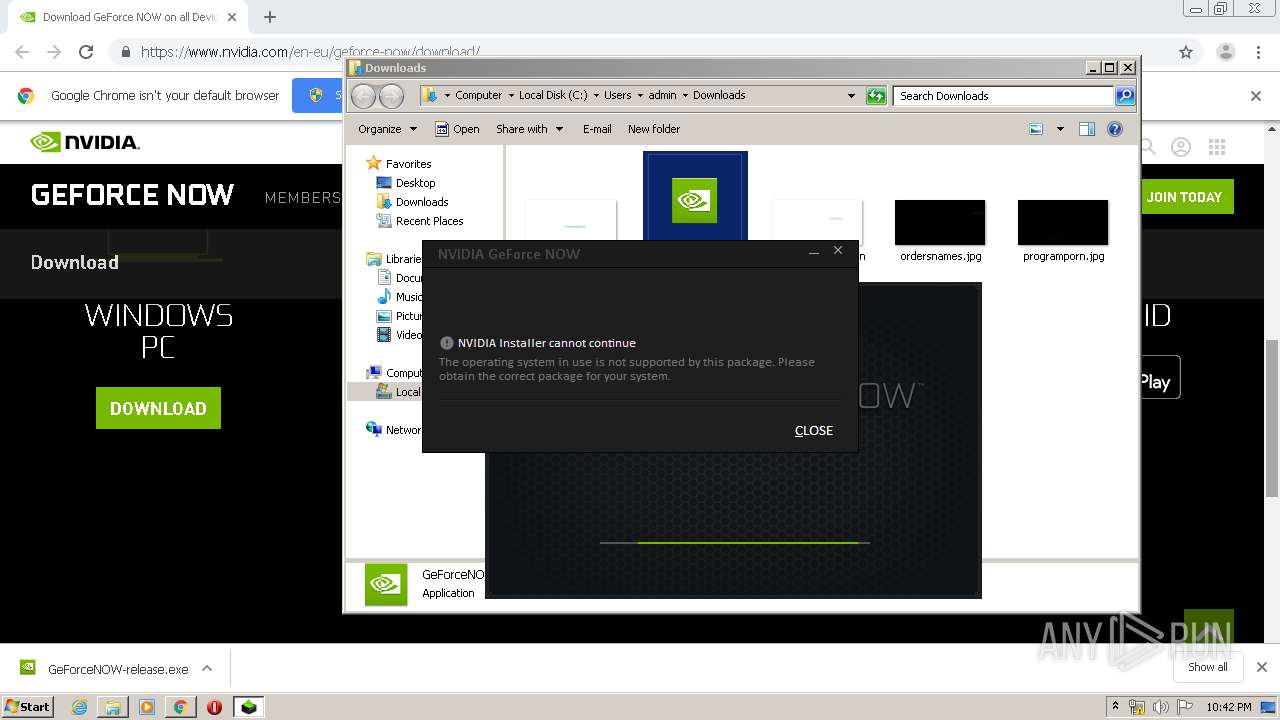
| Analysis date: | March 17, 2020, 22:41:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8F18DE9367D5E3FD0682D550A1A084B4 |
| SHA1: | 97E0B48656202116BFB3863C637C7049D3874541 |
| SHA256: | D79ECC36E52FFCBC615F170D3CC0DB07A62FDEF607CAFA583F3047632ED9F042 |
| SSDEEP: | 3:N8DSLnM6EZ3ADKXmoFJkn:2OLpEZ3mKXmo4 |
MALICIOUS
Application was dropped or rewritten from another process
- GeForceNOW-release.exe (PID: 3300)
Loads dropped or rewritten executable
- setup.exe (PID: 3800)
- RunDll32.EXE (PID: 2220)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2192)
- RunDll32.EXE (PID: 2220)
- setup.exe (PID: 3800)
- GeForceNOW-release.exe (PID: 3300)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2192)
Reads Environment values
- setup.exe (PID: 3800)
Uses RUNDLL32.EXE to load library
- setup.exe (PID: 3800)
INFO
Reads the hosts file
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2192)
Reads Internet Cache Settings
- chrome.exe (PID: 2192)
Application launched itself
- chrome.exe (PID: 2192)
Reads settings of System Certificates
- chrome.exe (PID: 3248)
- explorer.exe (PID: 372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
31
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13115994443624904742,17275933693979706315,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2482260032709554699 --mojo-platform-channel-handle=3680 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13115994443624904742,17275933693979706315,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12511087581236764900 --mojo-platform-channel-handle=3684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,13115994443624904742,17275933693979706315,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13438446587539138862 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=660 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13115994443624904742,17275933693979706315,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15865633512963054853 --mojo-platform-channel-handle=4260 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13115994443624904742,17275933693979706315,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6578579358466373047 --mojo-platform-channel-handle=4048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13115994443624904742,17275933693979706315,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2576450945056971281 --mojo-platform-channel-handle=4536 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13115994443624904742,17275933693979706315,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7704432479937539116 --mojo-platform-channel-handle=3004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 819
Read events
1 501
Write events
299
Delete events
19
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2192-13228958475943750 |
Value: 259 | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2192) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
Executable files
36
Suspicious files
60
Text files
280
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E71520C-890.pma | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a9094c41-d460-4d3c-8bec-f09cb3d4b5c8.tmp | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66c3f.TMP | text | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d87.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
42
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
372 | explorer.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.7 Kb | whitelisted |
3248 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
3248 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
3248 | chrome.exe | GET | 200 | 172.217.130.74:80 | http://r5---sn-2gb7sn7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=84.17.36.70&mm=28&mn=sn-2gb7sn7r&ms=nvh&mt=1584484821&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3248 | chrome.exe | GET | 200 | 173.194.150.236:80 | http://r6---sn-2gb7sn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=84.17.36.70&mm=28&mn=sn-2gb7sn7s&ms=nvh&mt=1584484821&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
372 | explorer.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3248 | chrome.exe | 52.57.44.100:443 | epsilon.6sense.com | Amazon.com, Inc. | DE | unknown |
3248 | chrome.exe | 172.217.23.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 23.201.175.211:443 | munchkin.marketo.net | Akamai Technologies, Inc. | NL | unknown |
3248 | chrome.exe | 192.28.147.68:443 | 156-ofn-742.mktoresp.com | MARKETO | US | suspicious |
3248 | chrome.exe | 143.204.97.56:443 | t.contentsquare.net | — | US | unknown |
3248 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3248 | chrome.exe | 104.92.75.207:443 | j.6sc.co | Akamai Technologies, Inc. | NL | unknown |
3248 | chrome.exe | 216.58.205.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
3248 | chrome.exe | 172.217.16.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.nvidia.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
assets.adobedtm.com |
| whitelisted |
smetrics.nvidia.com |
| whitelisted |
epsilon.6sense.com |
| shared |
clients1.google.com |
| whitelisted |
munchkin.marketo.net |
| whitelisted |
156-ofn-742.mktoresp.com |
| suspicious |
api.nvidia.com |
| whitelisted |
Threats
Process | Message |
|---|---|
setup.exe | 0.495 | INFO: [NVI2.NVInstaller] 363@CNVInstaller::HandleDeferredCleanupInstance : No deferred cleanup instance found running.
|
setup.exe | 0.495 | INFO: [NVI2.NVInstaller] 363@CNVInstaller::HandleDeferredCleanupInstance : No deferred cleanup instance found running.
|
setup.exe | 0.506 | INFO: [NVI2.Config.ManifestParser] 2450@CConfigManifestParser::Parse : Entering Checkpoint: Loading Configuration Manifest.
|
setup.exe | 0.518 | INFO: [NVI2.Config.ManifestParser] 2450@CConfigManifestParser::Parse : Exiting Checkpoint: Loading Configuration Manifest ( 15 ms ).
|
setup.exe | 0.518 | INFO: [NVI2.ConfigConstraintParser] 25@CNVConfigConstraintsParser::Parse : Entering Checkpoint: Loading configuration file C:\Users\admin\AppData\Local\Temp\GeForceNOWInstallerTemp\setup.CFG.
|
setup.exe | 0.521 | INFO: [NVI2.ConfigConstraintParser] 25@CNVConfigConstraintsParser::Parse : Entering Checkpoint: Loading configuration file C:\Users\admin\AppData\Local\Temp\GeForceNOWInstallerTemp\setup.CFG.
|
setup.exe | 0.521 | INFO: [NVI2.ConfigConstraintParser] 25@CNVConfigConstraintsParser::Parse : Exiting Checkpoint: Loading configuration file C:\Users\admin\AppData\Local\Temp\GeForceNOWInstallerTemp\setup.CFG ( 0 ms ).
|
setup.exe | 0.528 | INFO: [NVI2.ConfigConstraintParser] 25@CNVConfigConstraintsParser::Parse : Exiting Checkpoint: Loading configuration file C:\Users\admin\AppData\Local\Temp\GeForceNOWInstallerTemp\setup.CFG ( 16 ms ).
|
setup.exe | 0.529 | DEBUG: [NVI2.CEngineCache] 1845@CEngineCache::RelocateEngine : This DLL: C:\Users\admin\AppData\Local\Temp\GeForceNOWInstallerTemp\NVI2\NVI2.DLL relative path: .\NVI2.
|
setup.exe | 0.528 | DEBUG: [NVI2.CEngineCache] 1826@CEngineCache::RelocateEngine : Location of active installer module configuration: C:\Users\admin\AppData\Local\Temp\GeForceNOWInstallerTemp\setup.CFG.
|