| File name: | VolcanoUpdater.exe |
| Full analysis: | https://app.any.run/tasks/4d02b7fd-0221-4949-8877-27ef566c2591 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2025, 21:02:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 14 sections |
| MD5: | 690B0BE88351C438FF24DBC67E50AE96 |
| SHA1: | 562C1AE7E92574FE1E73B1A9734ABF9F2CEF866B |
| SHA256: | D7907E93B9EE8ED2AC0B4C4F5C20A961A1A0BEE0000FBBD3A57E87ECBC846899 |
| SSDEEP: | 98304:Y5dEtqUtUK7HfktQ62o7fa3/q4lODvNn2deEUdnf+XCNlmKSyF/JylQZcvBL4j+5:RjRa4O92lbK/iF |
MALICIOUS
XORed URL has been found (YARA)
- VolcanoUI.exe (PID: 5708)
SUSPICIOUS
Reads the BIOS version
- VolcanoUpdater.exe (PID: 1816)
- VolcanoUI.exe (PID: 5708)
Reads the date of Windows installation
- VolcanoUpdater.exe (PID: 1816)
Reads security settings of Internet Explorer
- VolcanoUpdater.exe (PID: 1816)
Process drops legitimate windows executable
- VolcanoUI.exe (PID: 5708)
Executable content was dropped or overwritten
- VolcanoUI.exe (PID: 5708)
- VolcanoUpdater.exe (PID: 1816)
INFO
Create files in a temporary directory
- VolcanoUpdater.exe (PID: 1816)
- VolcanoUI.exe (PID: 5708)
Checks supported languages
- VolcanoUpdater.exe (PID: 1816)
- VolcanoUI.exe (PID: 5708)
Reads the computer name
- VolcanoUpdater.exe (PID: 1816)
- VolcanoUI.exe (PID: 5708)
The sample compiled with english language support
- VolcanoUI.exe (PID: 5708)
Process checks computer location settings
- VolcanoUpdater.exe (PID: 1816)
Themida protector has been detected
- VolcanoUI.exe (PID: 5708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(5708) VolcanoUI.exe
Decrypted-URLs (2)https://file.volcano.wtf/versioR
https://key.vol2
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:09 16:37:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 801280 |
| InitializedDataSize: | 262656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7e3058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
139
Monitored processes
3
Malicious processes
2
Suspicious processes
0
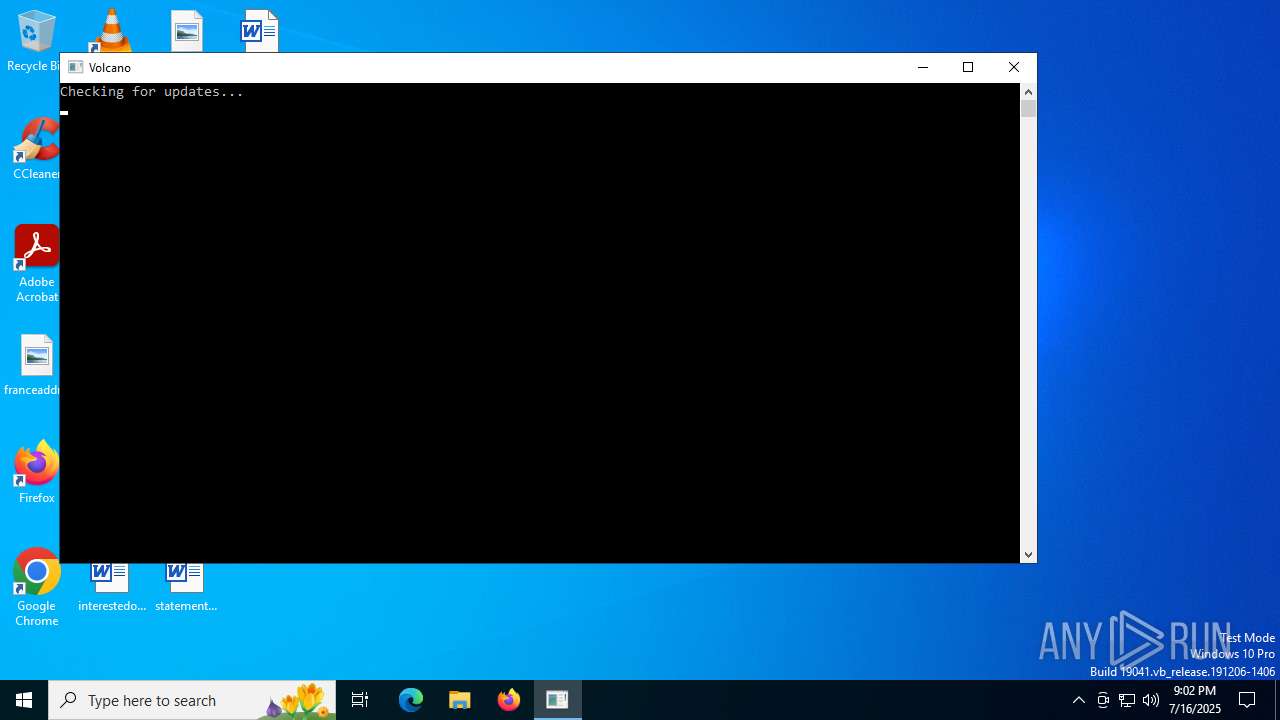
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | "C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | VolcanoUpdater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5708 | "C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe | VolcanoUpdater.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
xor-url(PID) Process(5708) VolcanoUI.exe Decrypted-URLs (2)https://file.volcano.wtf/versioR https://key.vol2 | |||||||||||||||
Total events
1 293
Read events
1 293
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
16
Text files
74
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\temp | compressed | |
MD5:7F26379D67C5F33058026AF16442D593 | SHA256:C73B7E3F20992EA135D332334BB70F7C3EBF94A64F6E26E3504072F84EE32995 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\abap-BrgZPUOV.js | text | |
MD5:5E0865606680E6D5AB5FAAE672097932 | SHA256:A3E2A241DA83C7AA80836ACE9FB3B2A242F458FF917DF9F19363F2E6430DD059 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\clojure-DTECt2xU.js | text | |
MD5:CBE50C2D87AFFE61EE11FAADF2F57252 | SHA256:C897D061A0F39FABC5B9204E0EA8F78FA12C37C4BE45A2749BD1119D2CBCBF68 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\luau-lifter.exe | executable | |
MD5:F1246A49C8183FCFAC4D7669A6C50881 | SHA256:F5AD37B2293814CE33149CA8D8BF1D673AE0C8F3CB025D7B83954EB0E68E631D | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\cpp-CLLBncYj.js | text | |
MD5:0F3FCC7CA8691D6CF4FF68B8347D18DD | SHA256:A5FB8F0E4EBFC61B3865C092BD6434A36D24EE6E62477D4ADD55A1D796CD88B4 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\apex-DyP6w7ZV.js | text | |
MD5:EEA817DCF104C3F416EB86054E4AB065 | SHA256:9E6D5B433394FC90B3A7C58514AB58C6BB49E740EF03E146928A3FD0095AEB68 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\cameligo-BFG1Mk7z.js | text | |
MD5:E9D40B956B6BEC8A5BFFD0D94552B2F8 | SHA256:CC50FE6B6738380FDC2D31D1A2FE210EA67CB19A5F6ABBF91E0AD3A08491A1E5 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\css-D3h14YRZ.js | text | |
MD5:387BF345843B2BE9BA90A6FBA1DE584E | SHA256:55CD0C924635240191C8189F4A500720E61EEE267EB2093474BF686AE5820EA6 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\bat-CFOPXBzS.js | text | |
MD5:4133D4FC714DDF40B53FB1F2F3B15579 | SHA256:471438AB5BC0B324A6B828AC8FA79CD86214FC4C84F4C2E9AAF55CAF56043D92 | |||
| 1816 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\bicep-BfEKNvv3.js | text | |
MD5:D57E65CA5EB6CAF649C5393DC167CB6D | SHA256:9DE9B6AD69CBF4B0D3DA56D87E5F33BF0DD5ECBB1DA2B3DEC999F6AEDA197246 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
764 | lsass.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6756 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
512 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
512 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4916 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1816 | VolcanoUpdater.exe | 104.21.56.14:443 | file.volcano.wtf | CLOUDFLARENET | — | malicious |
764 | lsass.exe | 142.250.181.227:80 | c.pki.goog | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5708 | VolcanoUI.exe | 104.21.56.14:443 | file.volcano.wtf | CLOUDFLARENET | — | malicious |
6756 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6756 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
file.volcano.wtf |
| malicious |
c.pki.goog |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
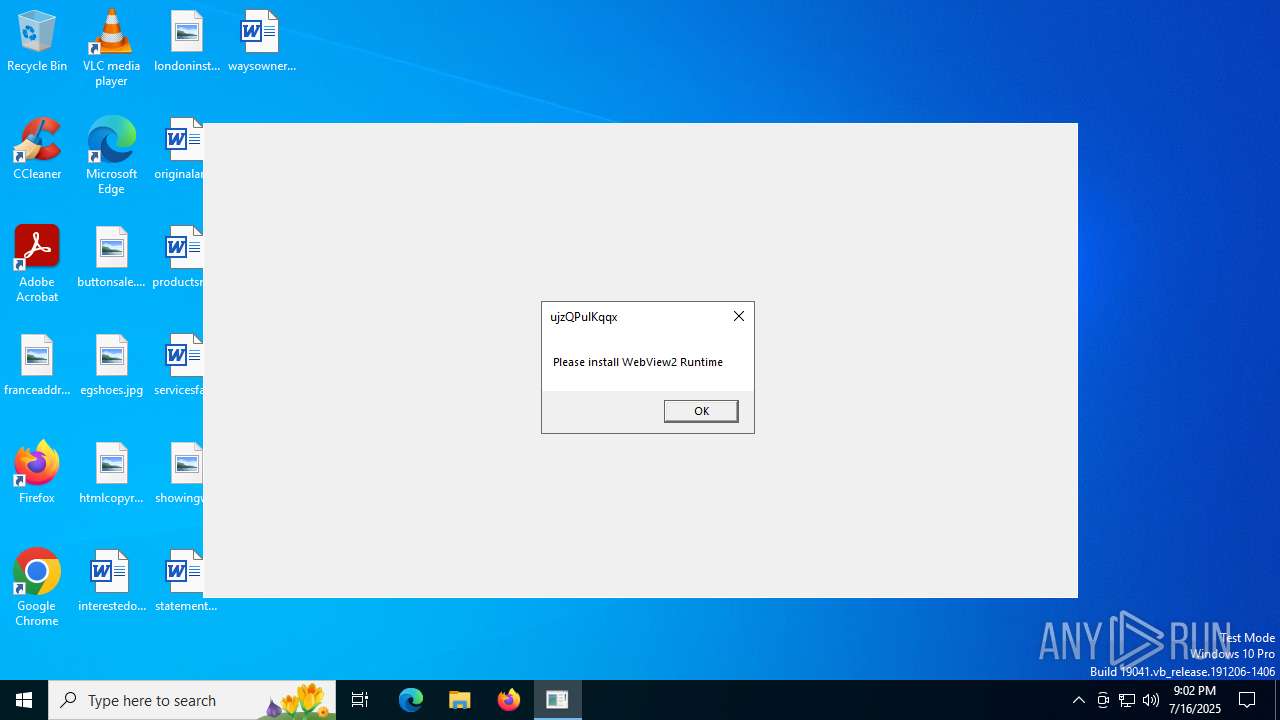
Threats
Process | Message |
|---|---|
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|