| File name: | VolcanoUpdater.exe |
| Full analysis: | https://app.any.run/tasks/2f19d135-2489-48c8-9ace-c22a1fa2d6a7 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2026, 16:24:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 14 sections |
| MD5: | 690B0BE88351C438FF24DBC67E50AE96 |
| SHA1: | 562C1AE7E92574FE1E73B1A9734ABF9F2CEF866B |
| SHA256: | D7907E93B9EE8ED2AC0B4C4F5C20A961A1A0BEE0000FBBD3A57E87ECBC846899 |
| SSDEEP: | 98304:Y5dEtqUtUK7HfktQ62o7fa3/q4lODvNn2deEUdnf+XCNlmKSyF/JylQZcvBL4j+5:RjRa4O92lbK/iF |
MALICIOUS
GENERIC has been found (auto)
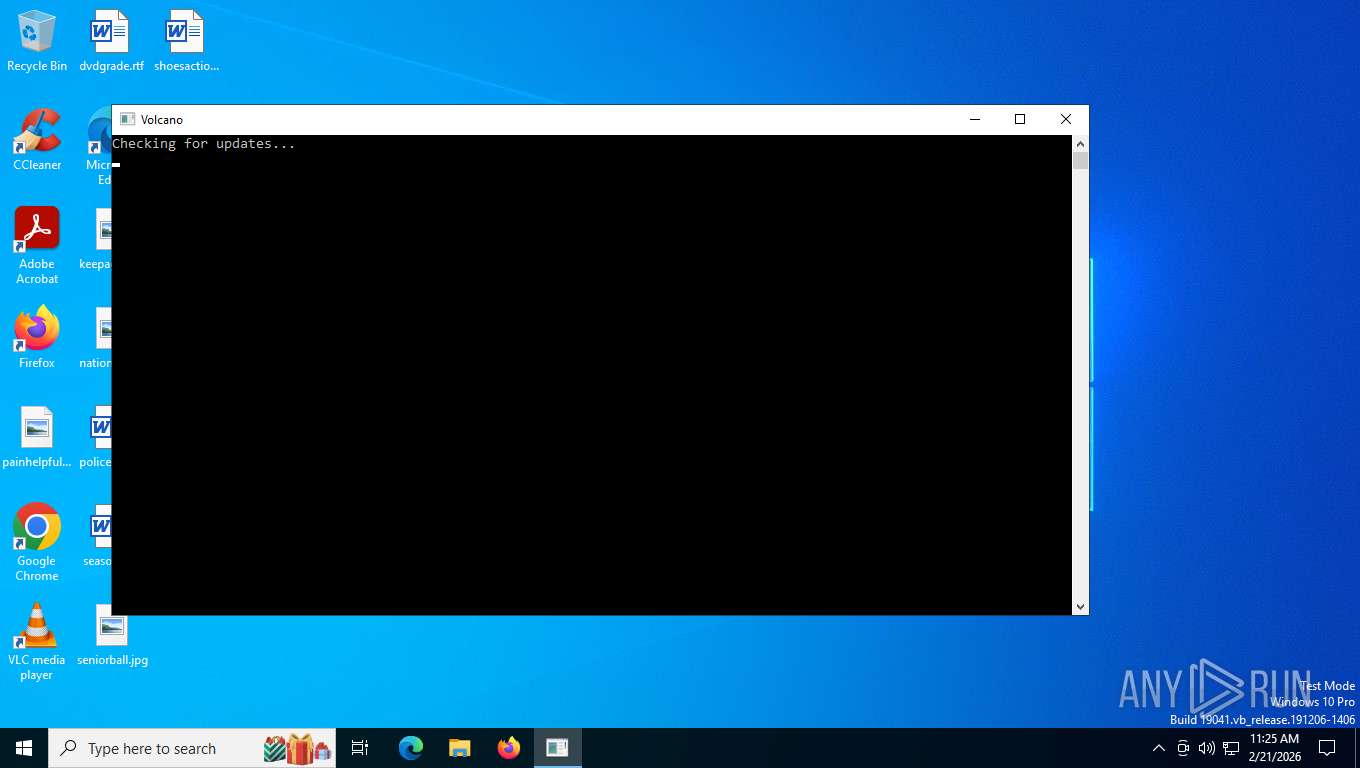
- VolcanoUpdater.exe (PID: 3652)
SUSPICIOUS
Reads the BIOS version
- VolcanoUpdater.exe (PID: 3652)
- VolcanoUI.exe (PID: 6584)
Reads the date of Windows installation
- VolcanoUpdater.exe (PID: 3652)
INFO
Create files in a temporary directory
- VolcanoUpdater.exe (PID: 3652)
- VolcanoUI.exe (PID: 6584)
Reads the computer name
- VolcanoUpdater.exe (PID: 3652)
- VolcanoUI.exe (PID: 6584)
Process checks whether UAC notifications are on
- VolcanoUI.exe (PID: 6584)
Checks supported languages
- VolcanoUI.exe (PID: 6584)
- VolcanoUpdater.exe (PID: 3652)
Process checks computer location settings
- VolcanoUpdater.exe (PID: 3652)
ROBLOX mutex has been found
- VolcanoUI.exe (PID: 6584)
Reads security settings of Internet Explorer
- VolcanoUpdater.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:09 16:37:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 801280 |
| InitializedDataSize: | 262656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7e3058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
151
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1932 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
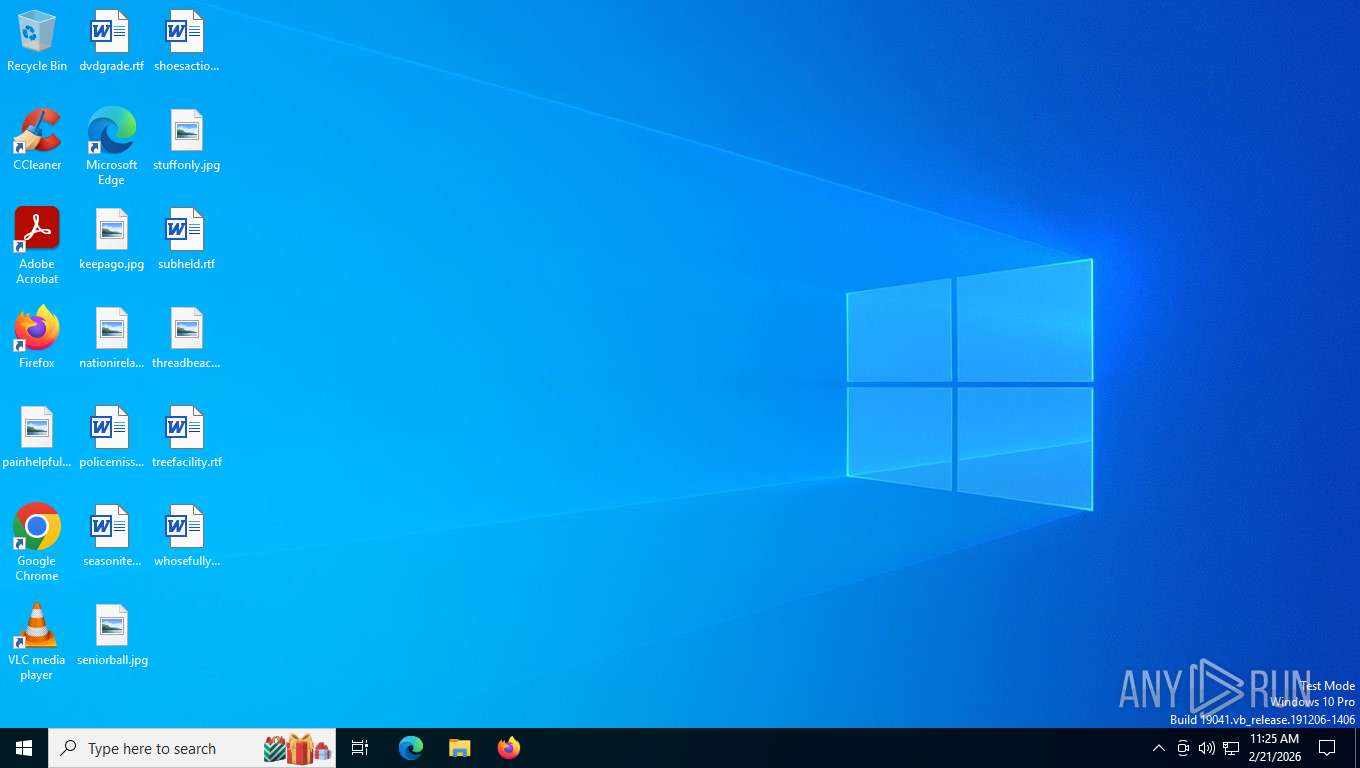
| 5048 | "C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe | — | VolcanoUpdater.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6584 | "C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe | VolcanoUpdater.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 8108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | VolcanoUpdater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 413
Read events
1 413
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\version.txt | binary | |
MD5:AF4A9179412B58188AA53E16B6D3D2BC | SHA256:6E8BFE77D24B44FE4301AD89F67B58D505750D410A4314BF641189E6815C2B7E | |||
| 3652 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\temp | binary | |
MD5:7FDB31393F5A26CA12992F152C5D21F6 | SHA256:7334258B8909C51A57588A07B8C2BA6AD171D8C304EEF11934728A149F9F237B | |||
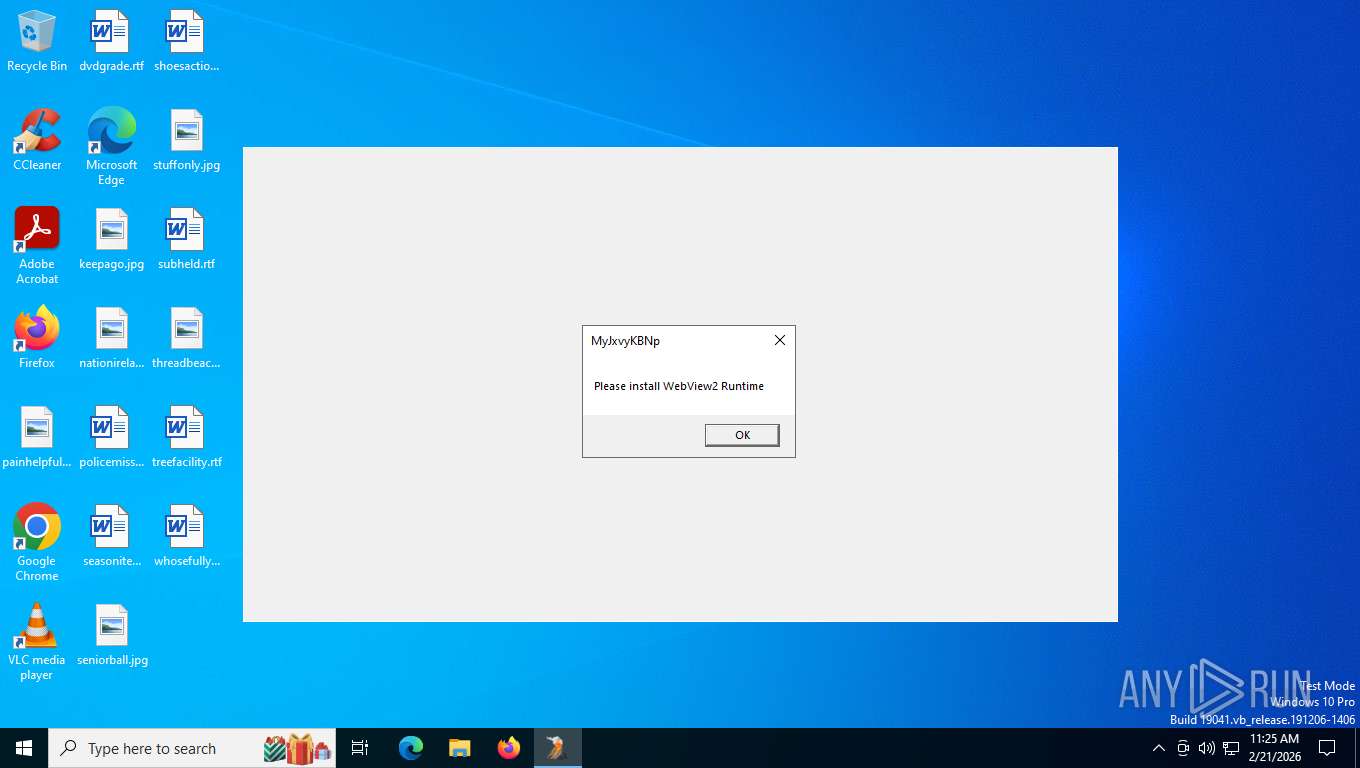
| 6584 | VolcanoUI.exe | C:\Users\admin\AppData\Local\Temp\WebView2Loader.dll | binary | |
MD5:E2F9D2EF3446E70B50DE50F577C6939E | SHA256:A8A6CD8D6DF1F913671BCD96B6298B6F53FD066A84AE891E4D865BC1B8E8E9E4 | |||
| 3652 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\luau-lifter.exe | binary | |
MD5:F1246A49C8183FCFAC4D7669A6C50881 | SHA256:F5AD37B2293814CE33149CA8D8BF1D673AE0C8F3CB025D7B83954EB0E68E631D | |||
| 3652 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe | binary | |
MD5:A5673669BD52F444796FE7DA77B295CB | SHA256:56C4476F29070418656B1A60C4C60CB615F39384EC552AC9F4D2DACC522DB3FC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
36
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 200 | 135.232.92.97:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
8400 | svchost.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
804 | lsass.exe | GET | 200 | 192.178.202.94:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 960 b | whitelisted |
804 | lsass.exe | GET | 200 | 192.178.202.94:80 | http://c.pki.goog/r/r4.crl | US | binary | 528 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8400 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5780 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.19:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 92.123.104.64:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 92.123.104.64:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
file.volcano.wtf |
| unknown |
c.pki.goog |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8400 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|