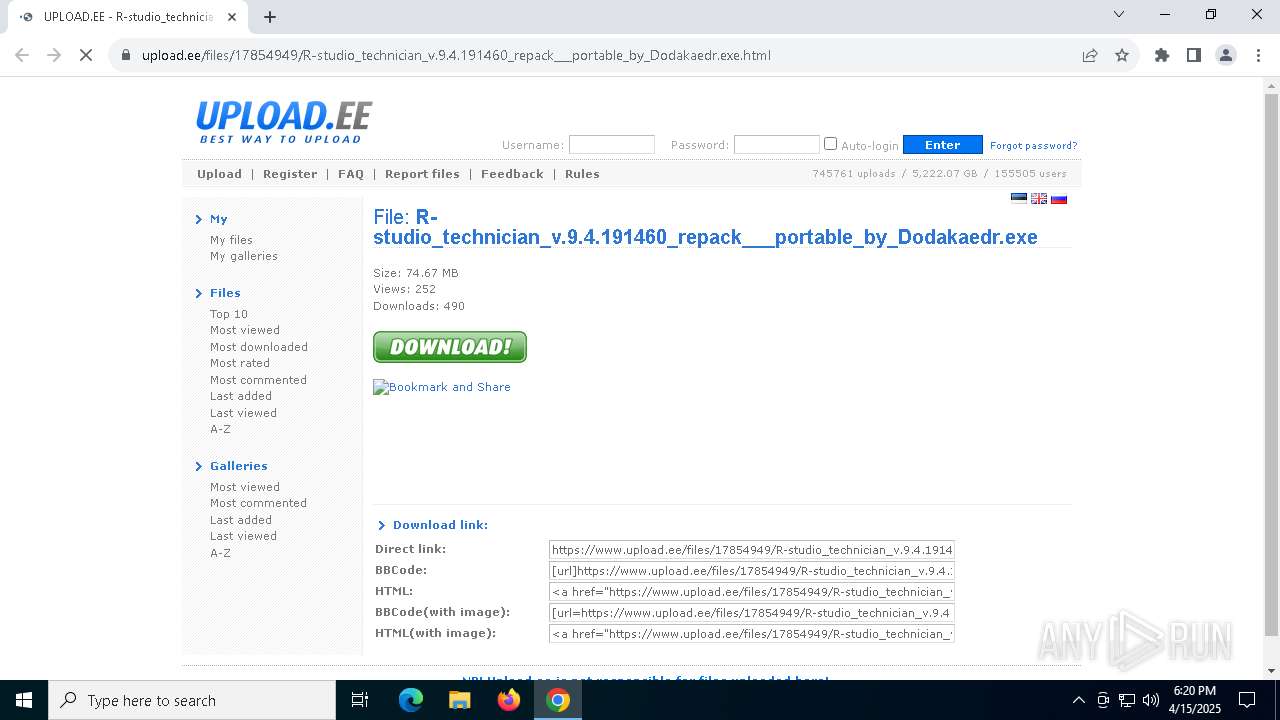
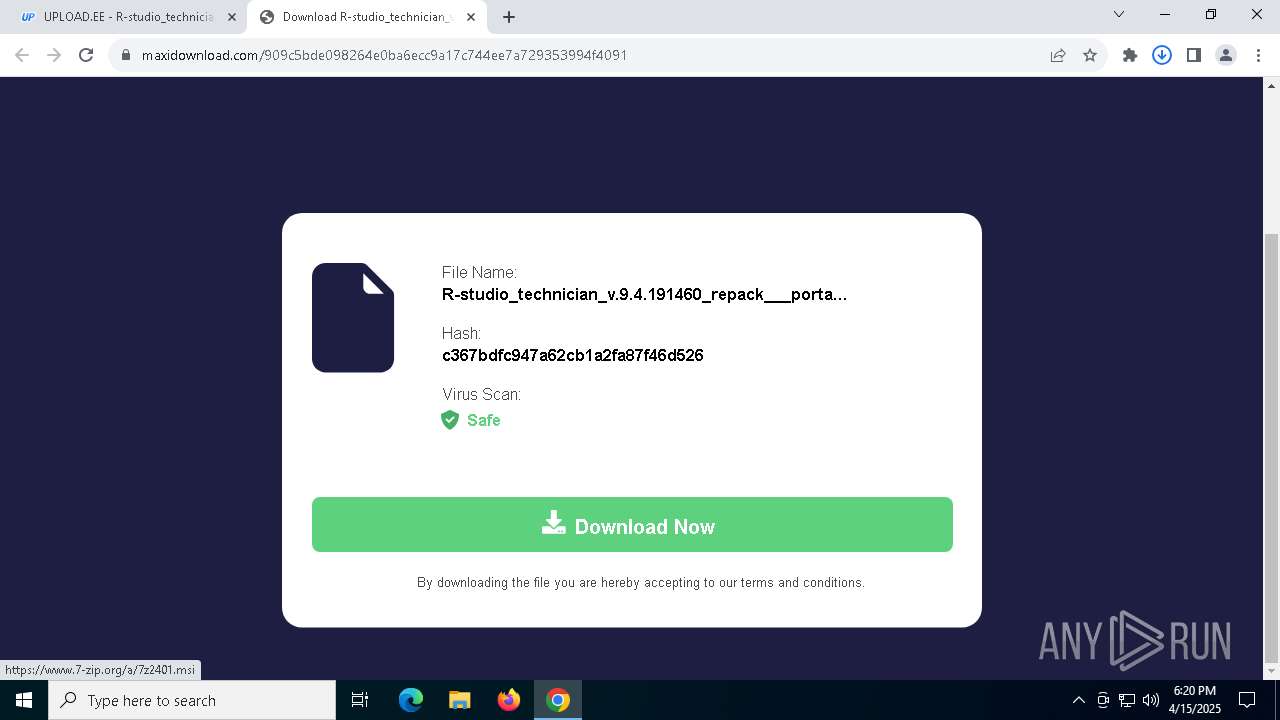
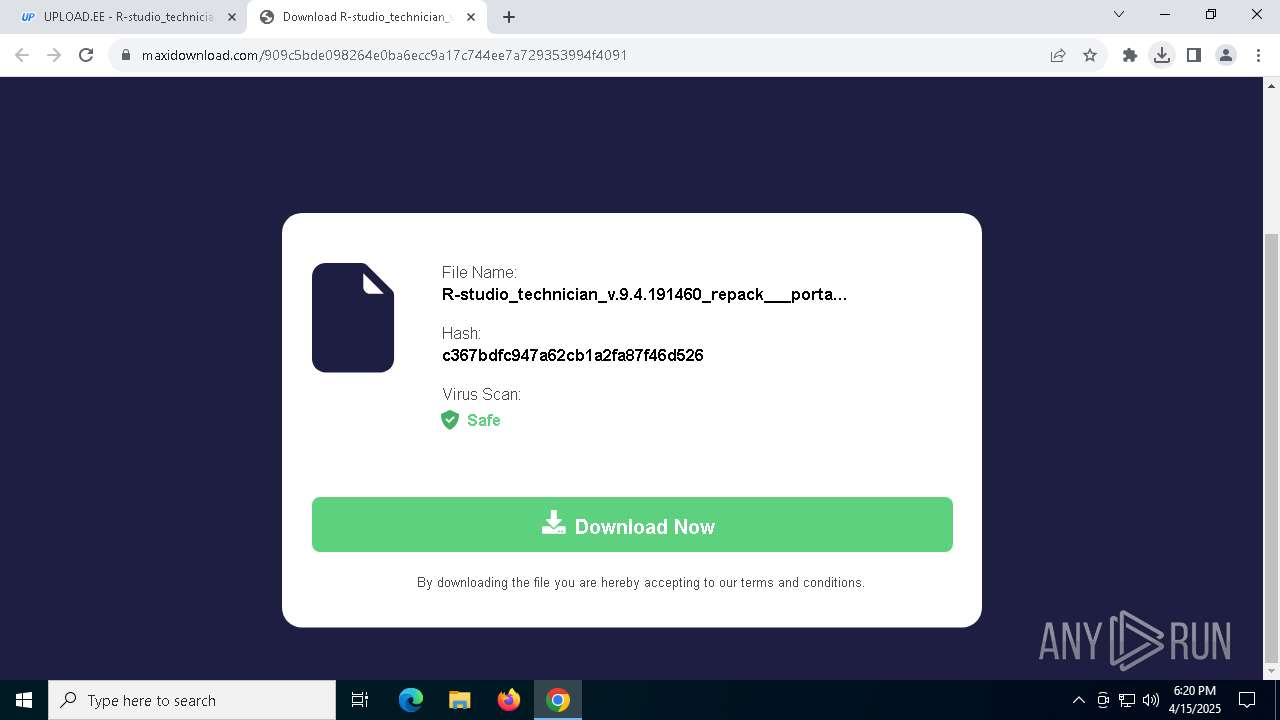
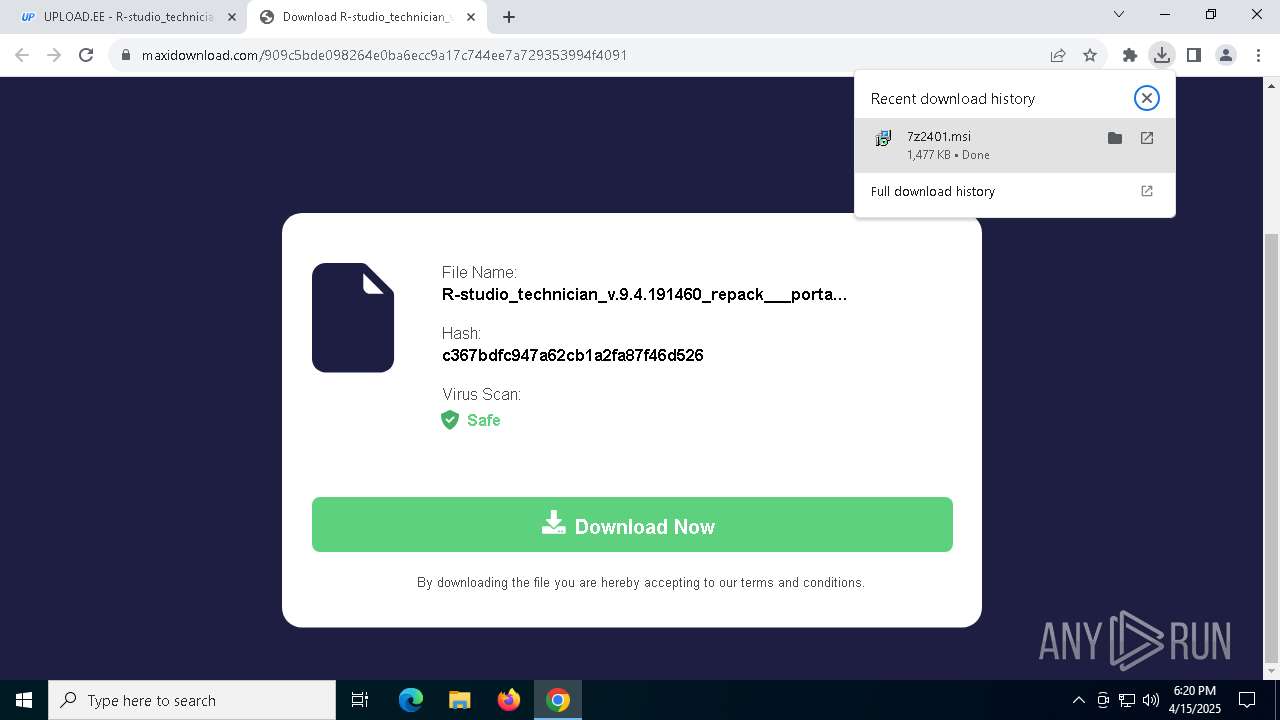
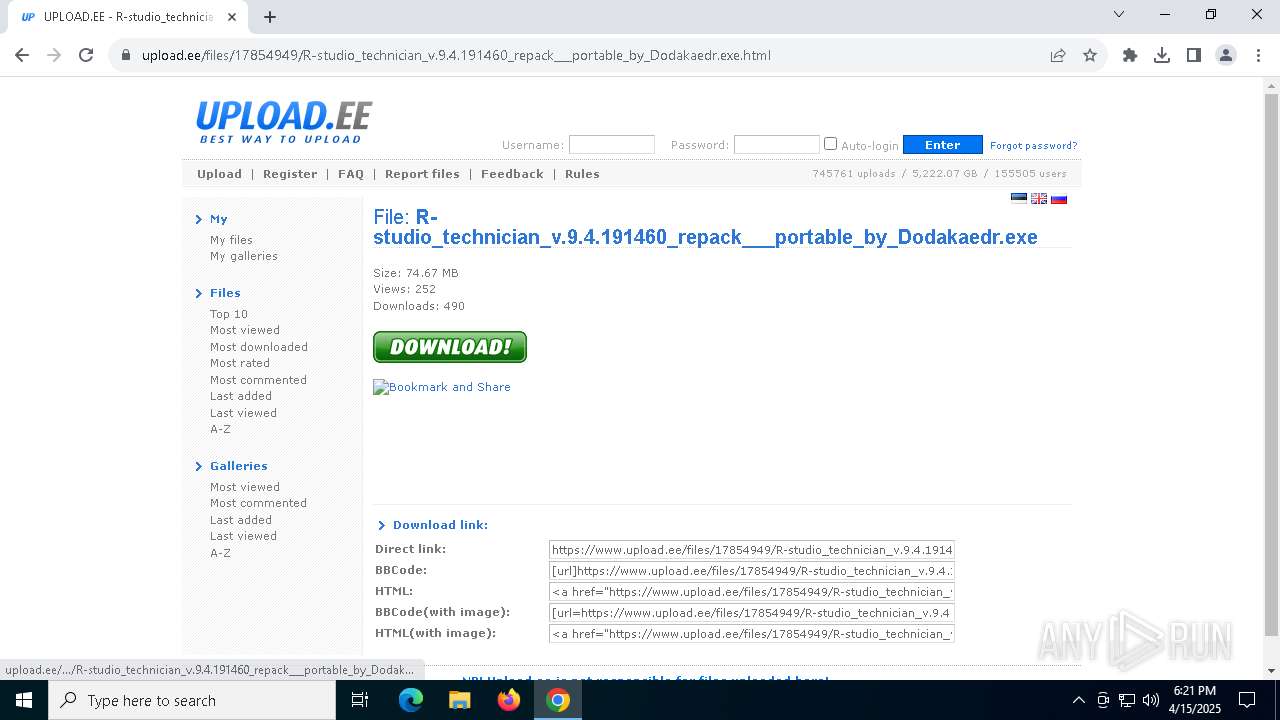
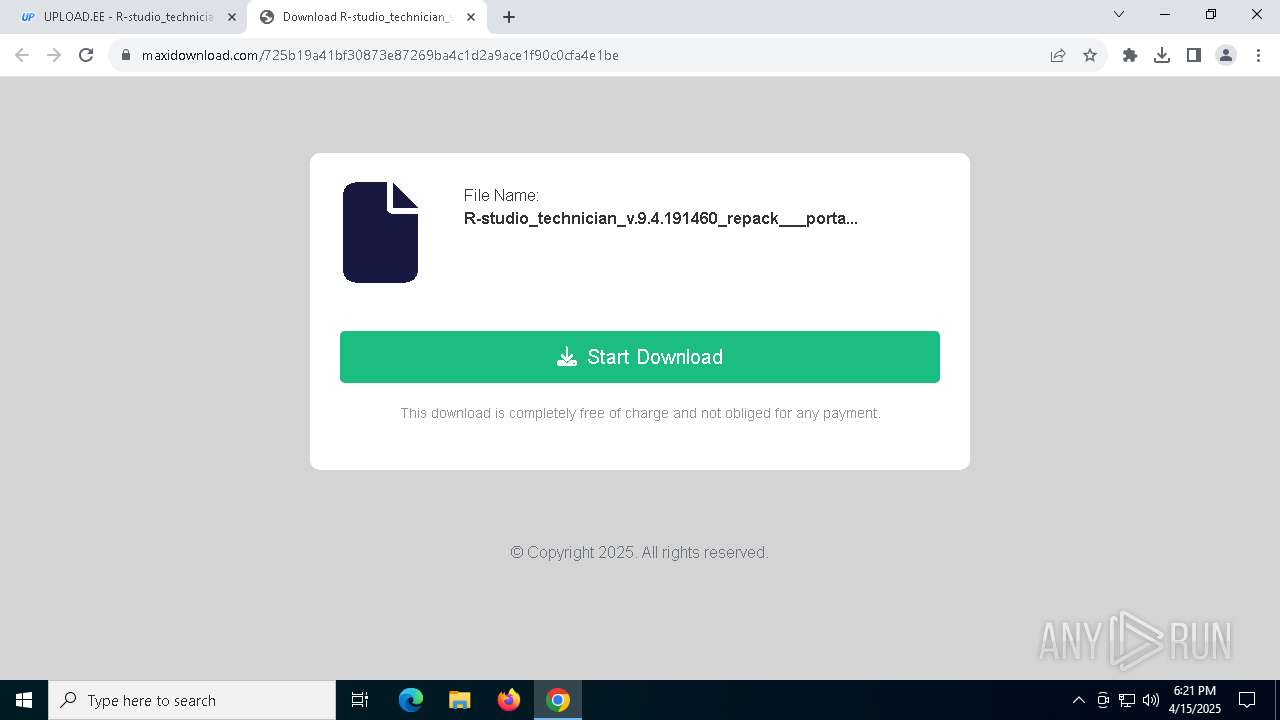
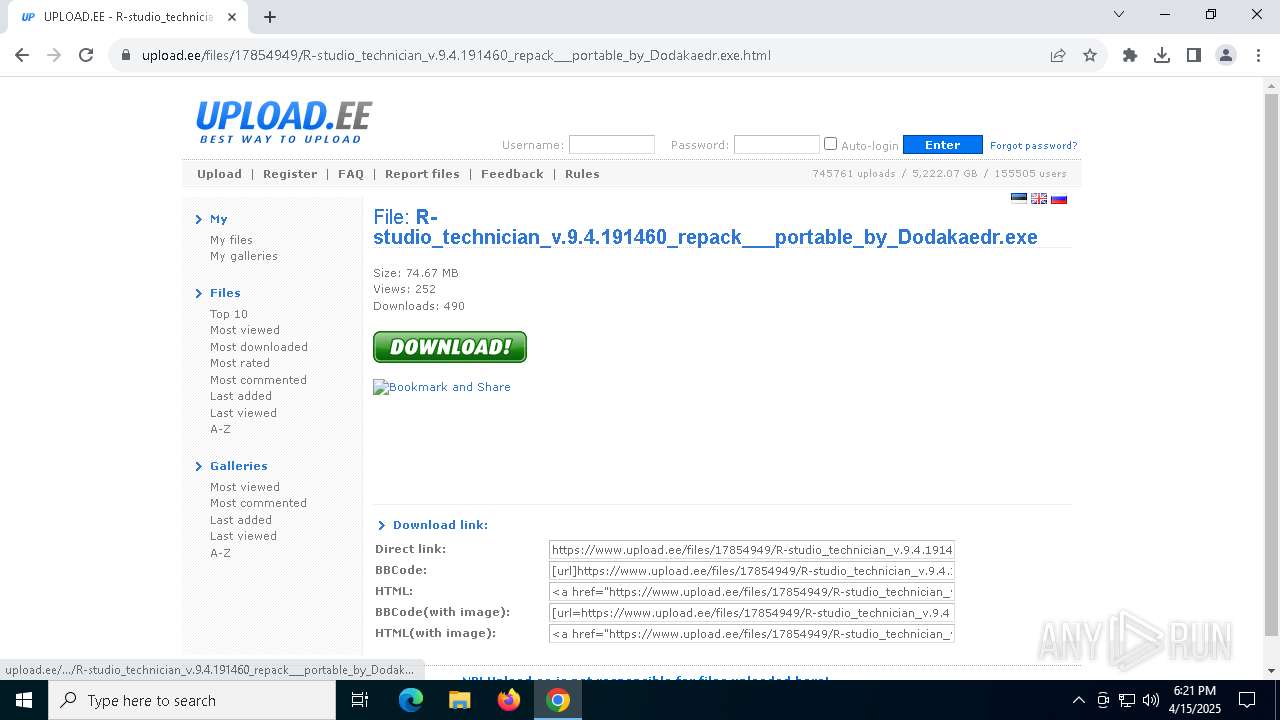
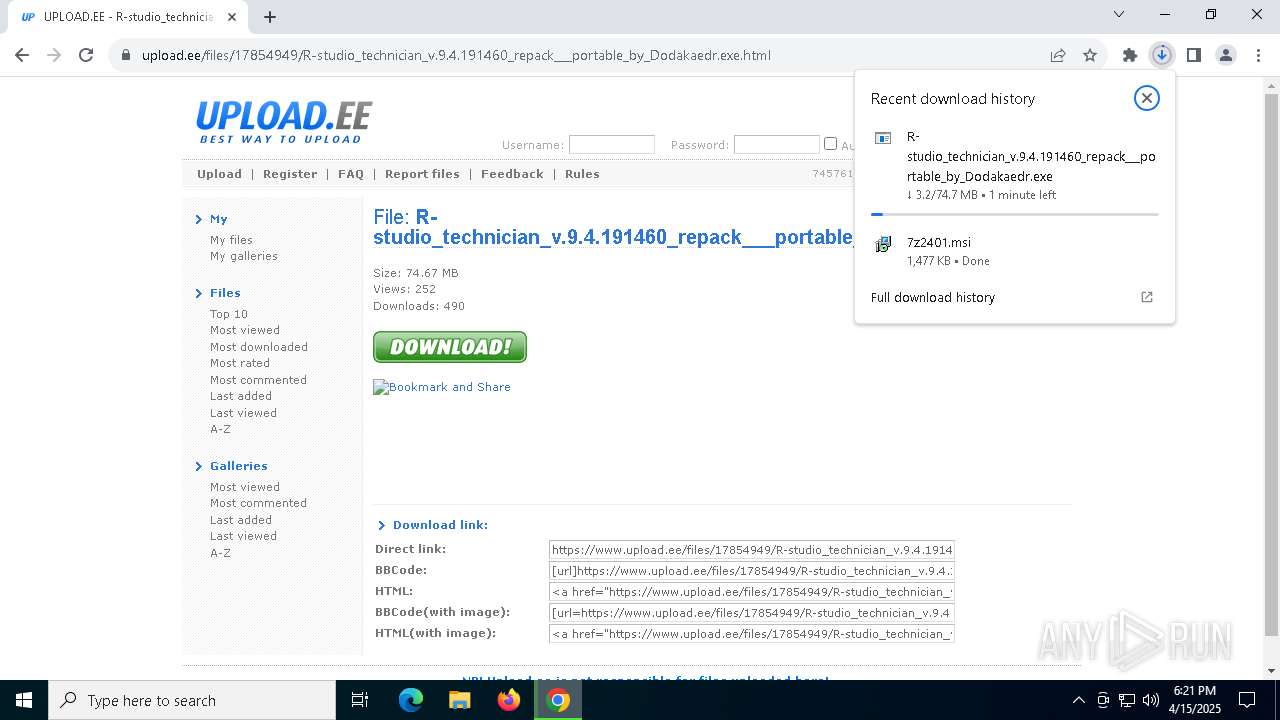
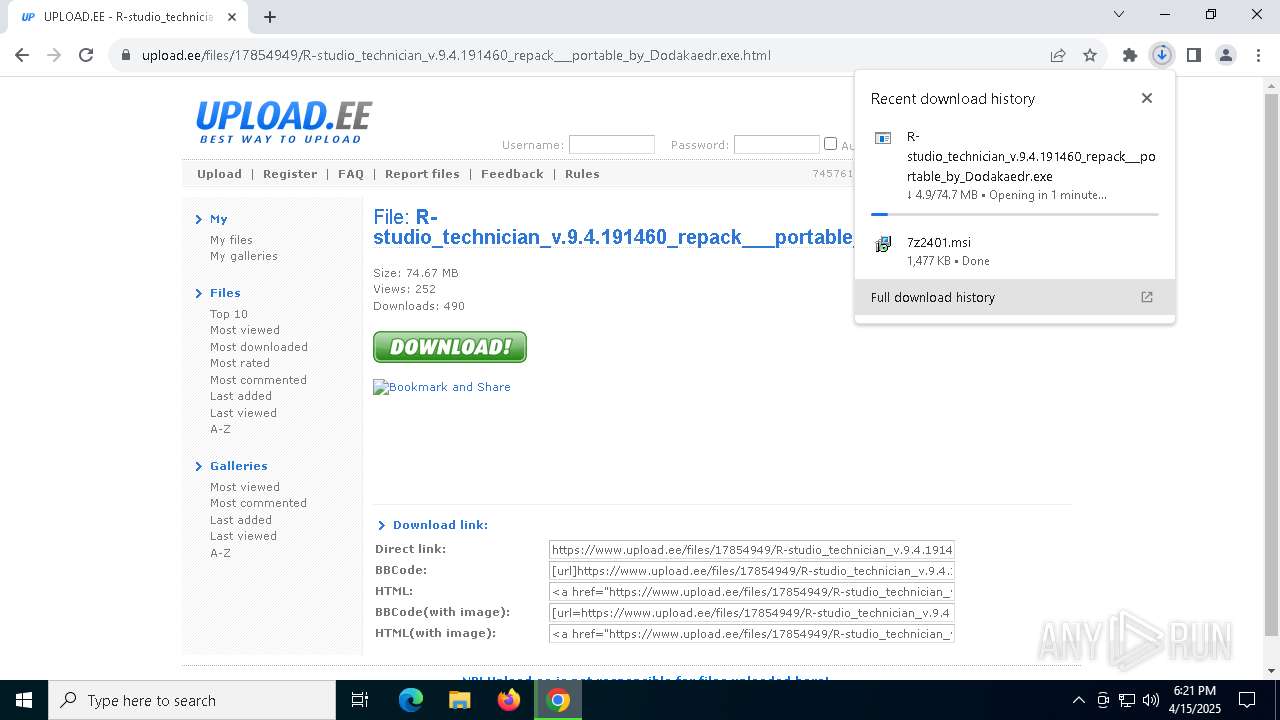
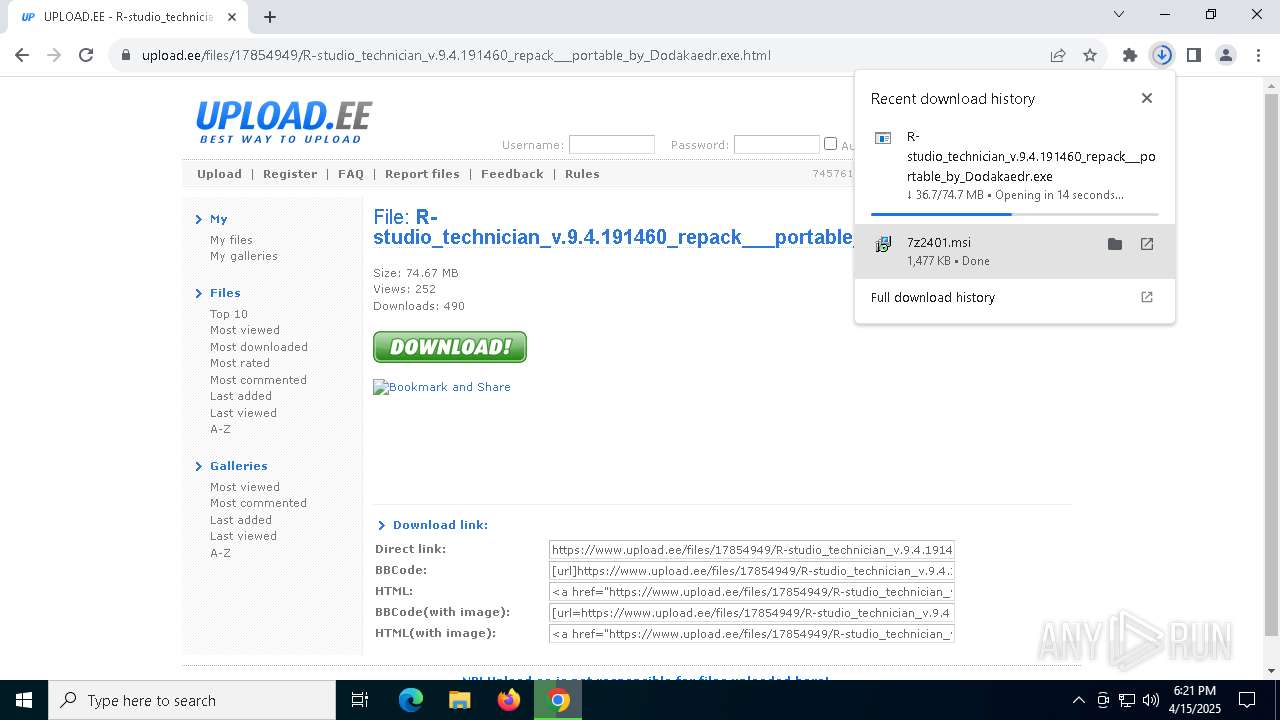
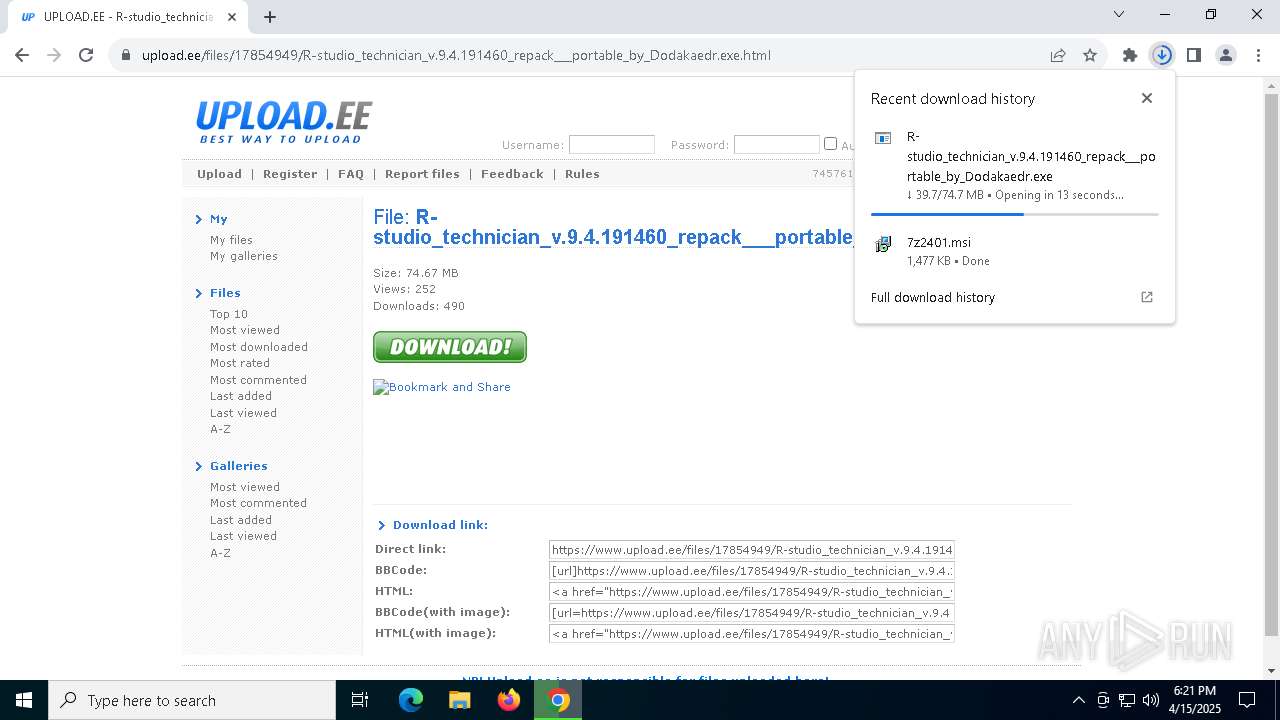
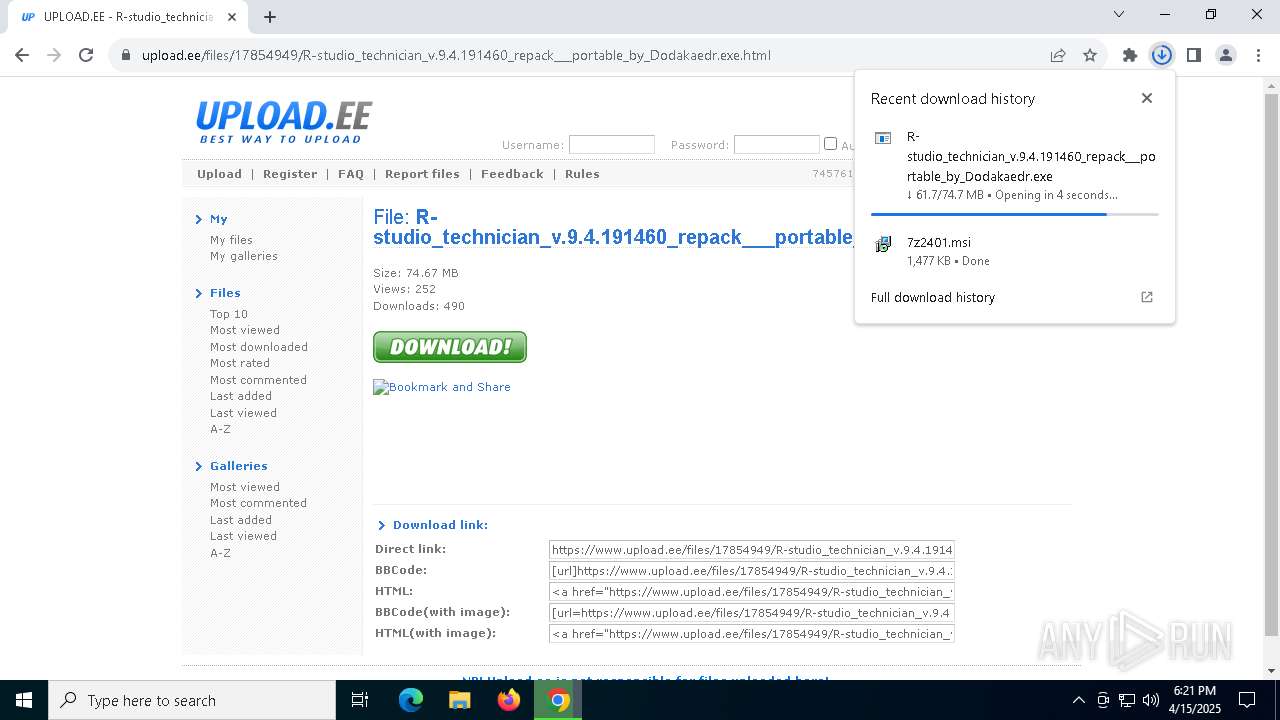
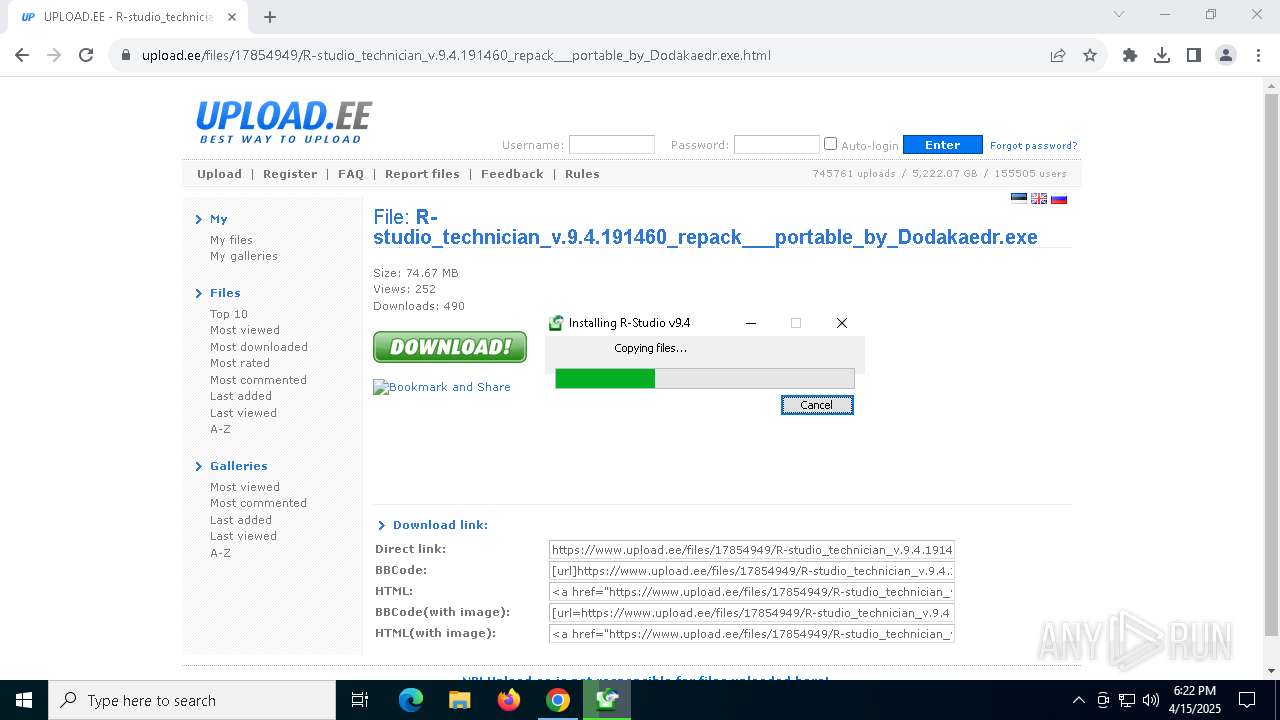
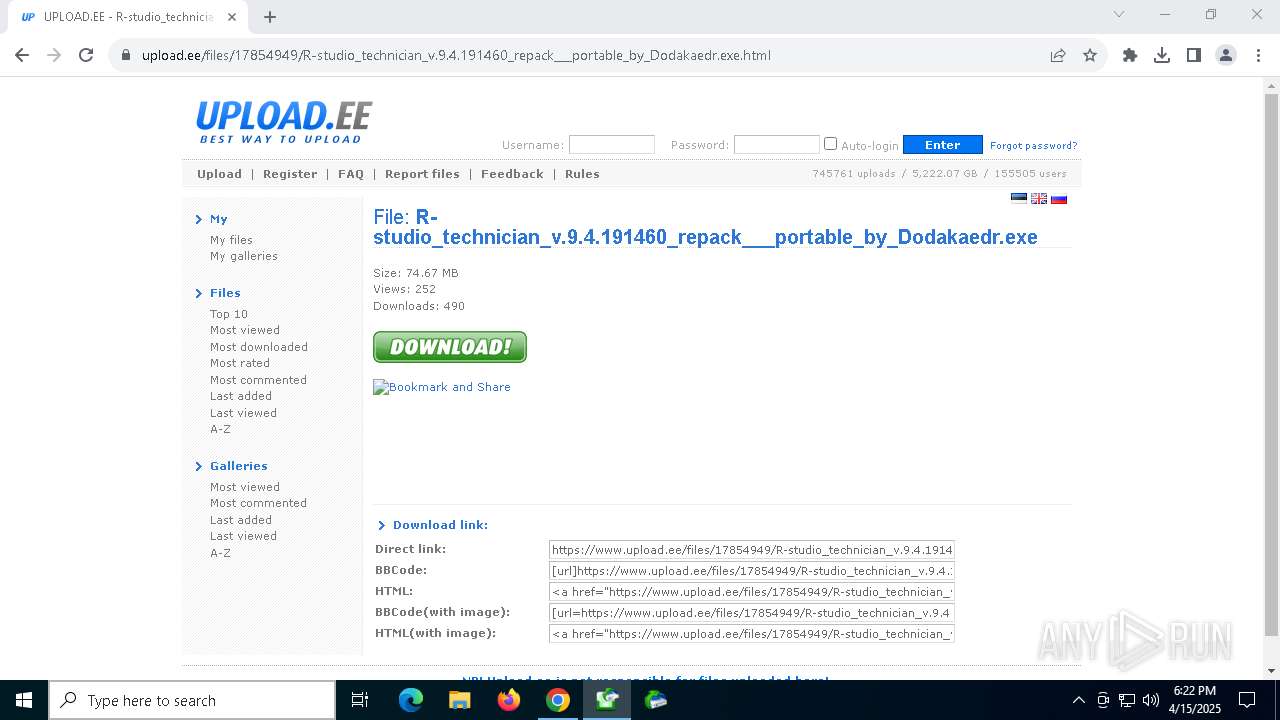
| URL: | https://www.upload.ee/files/17854949/R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe.html |
| Full analysis: | https://app.any.run/tasks/56cc85eb-bc79-465c-96c4-02933967d17e |
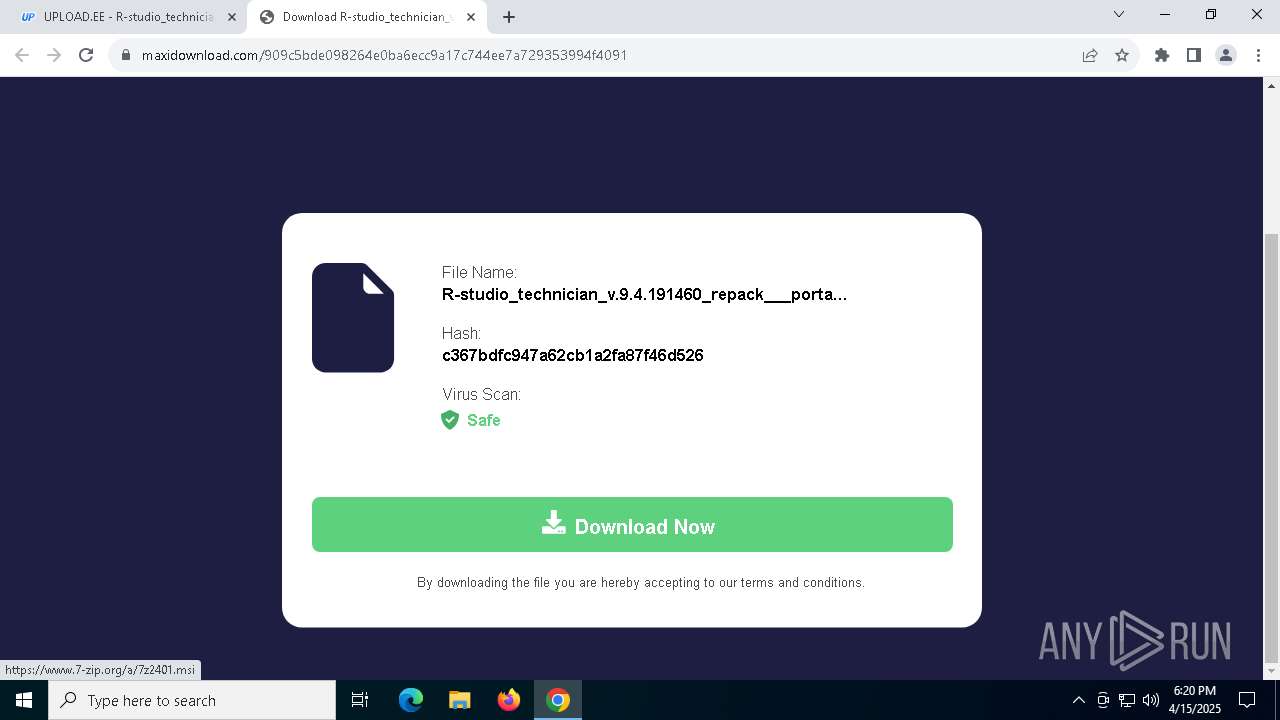
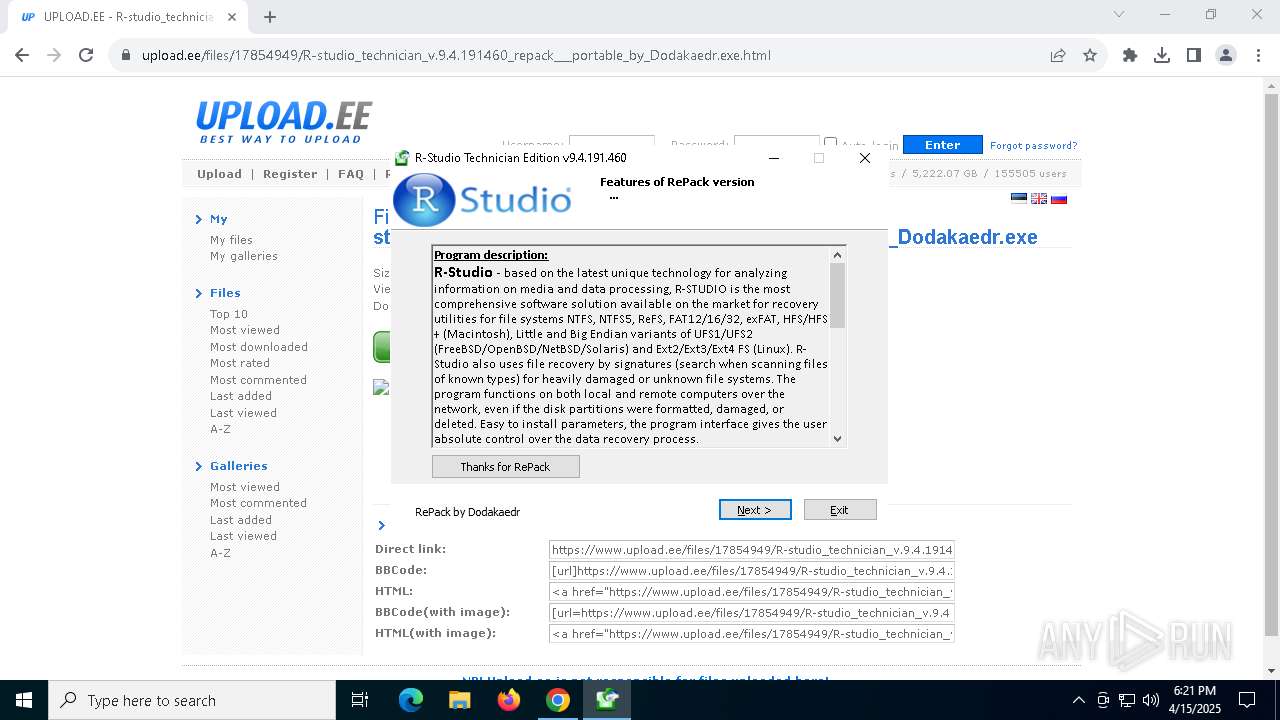
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 18:20:43 |
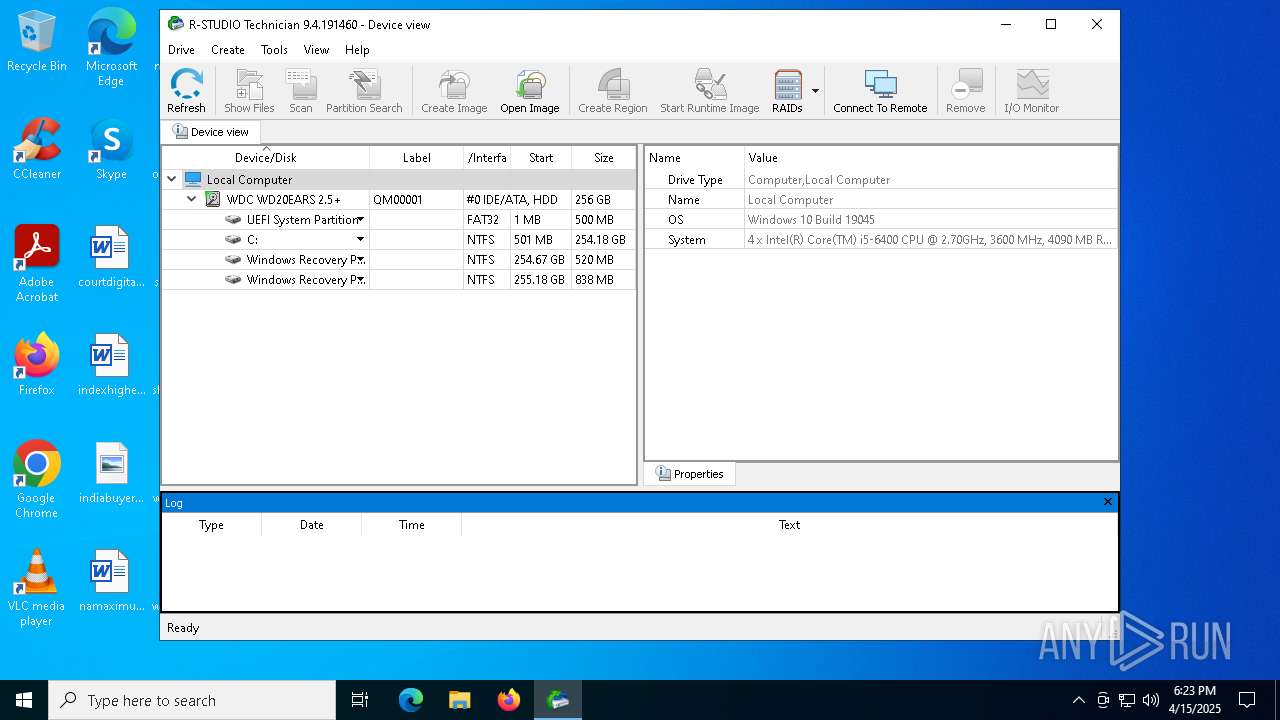
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
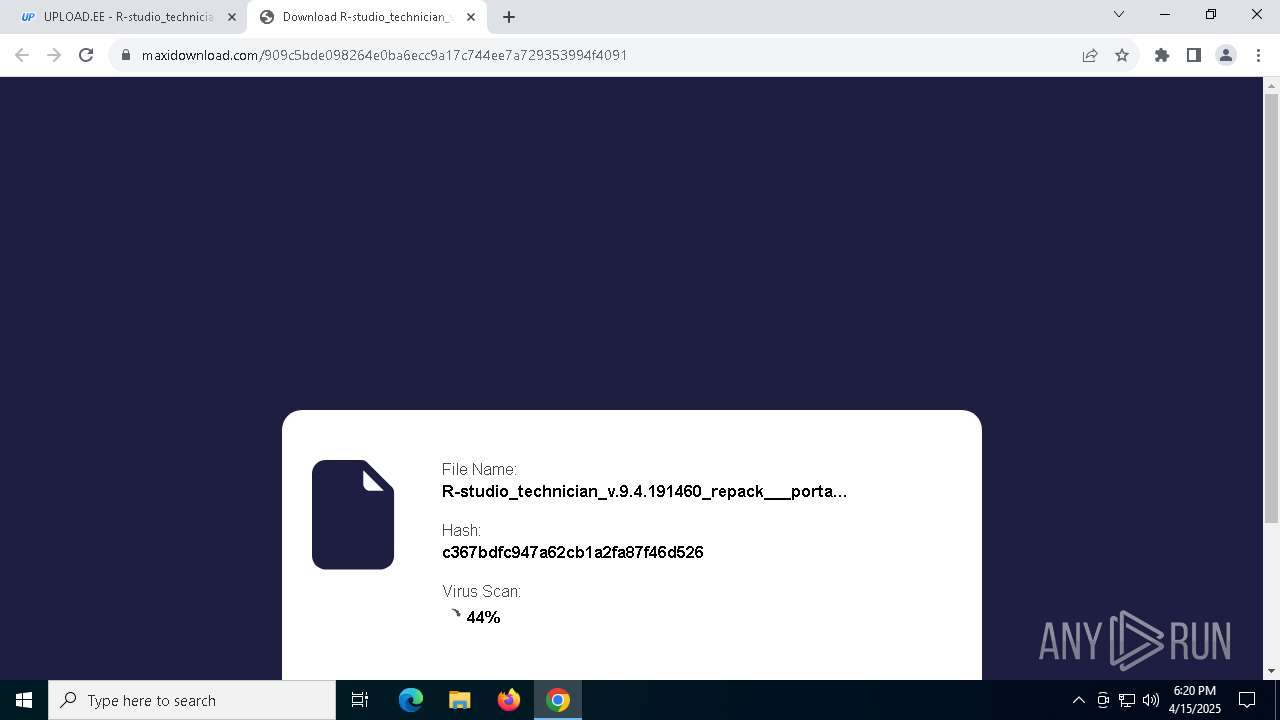
| MD5: | DD69CABB55579E4A49B6CF24DE1025E1 |
| SHA1: | 8F663C02E9CB70C275E170B91FBF2BC79F9F3662 |
| SHA256: | D78CB014C9C9C8EC0807AE02AE922FEDD189F45CE65EBC2D41D2AA2F8EEA9C83 |
| SSDEEP: | 3:N8DSLr7MJmUuQ66KbmMgAsEbtuRTCwXVMREHV8RRUCG:2OLr0SQ34eEbtMvMREHeU |
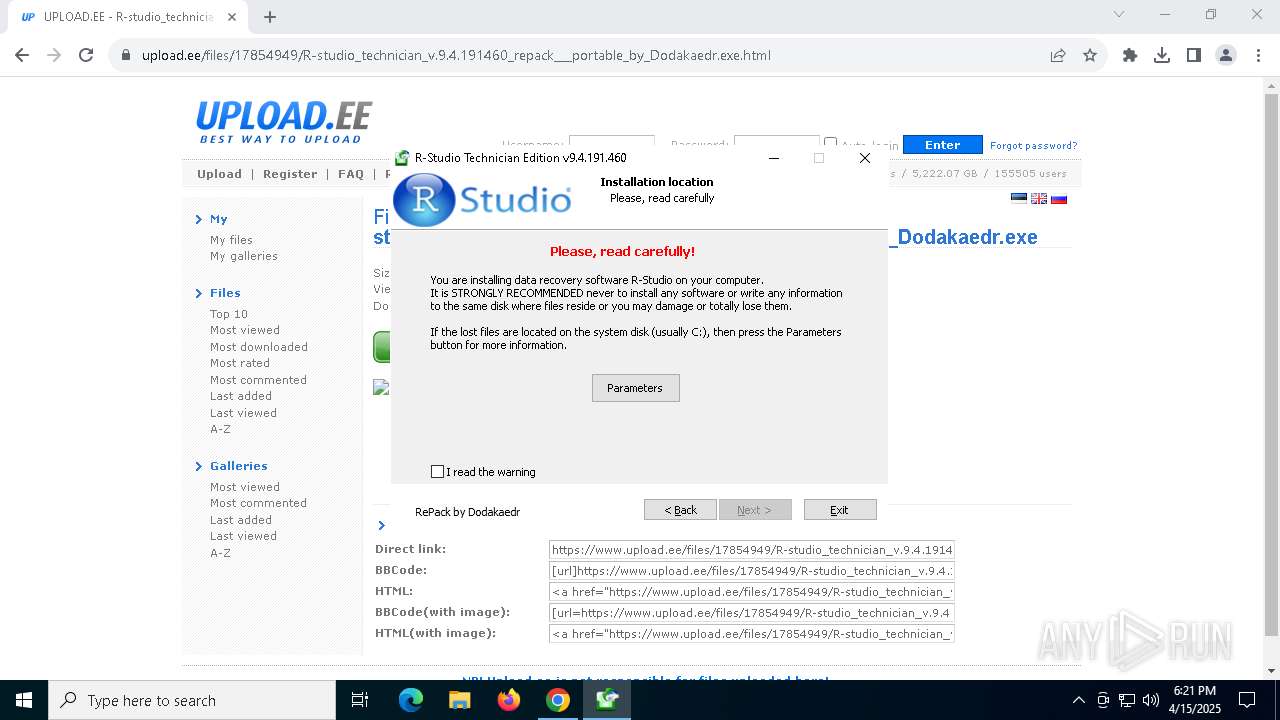
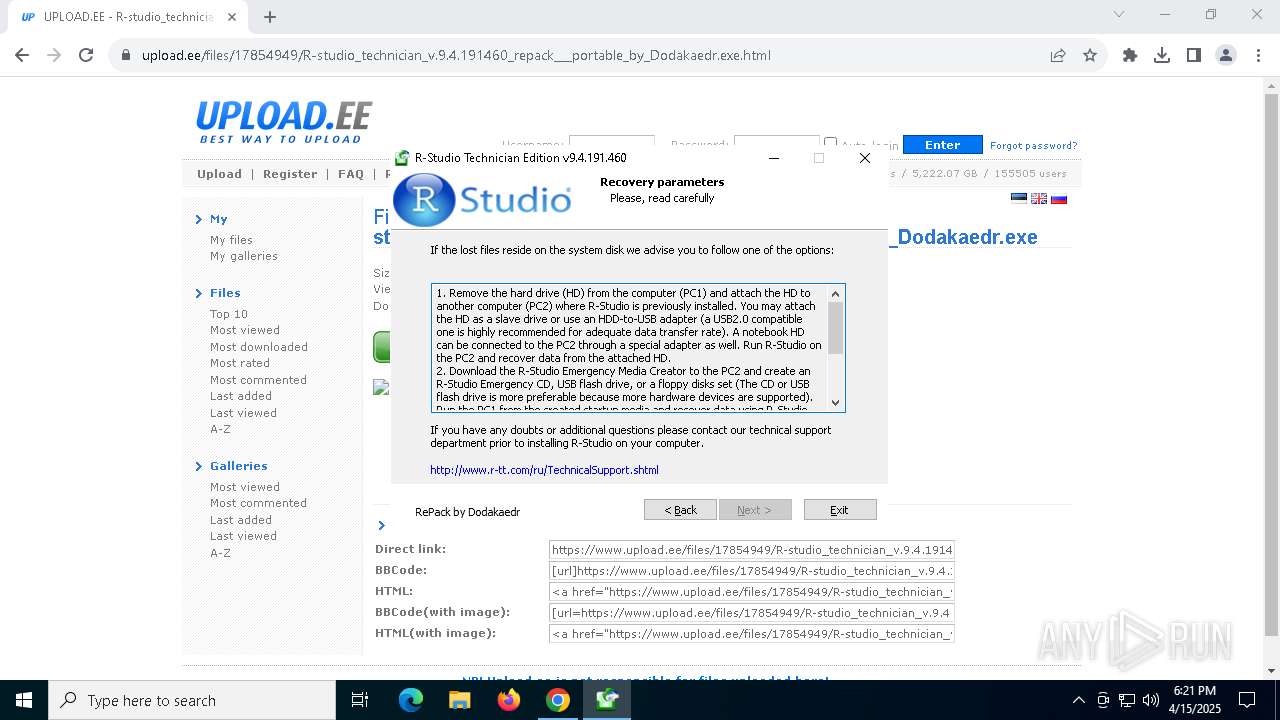
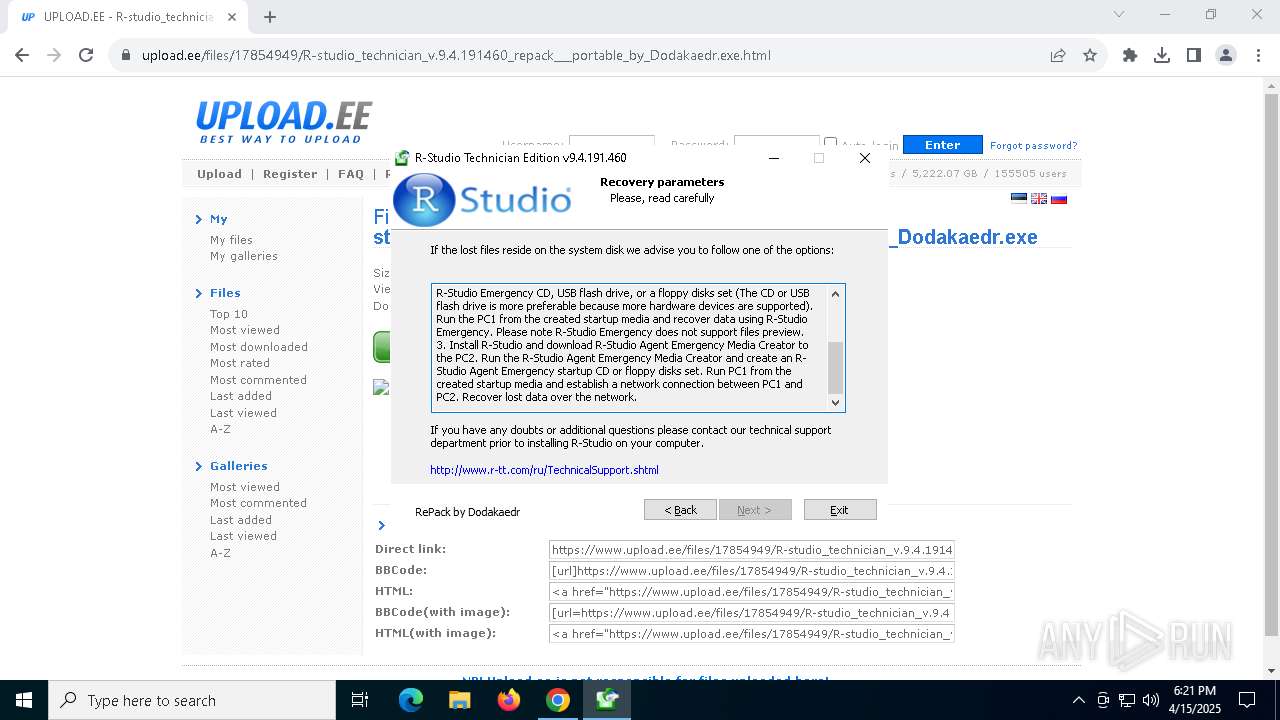
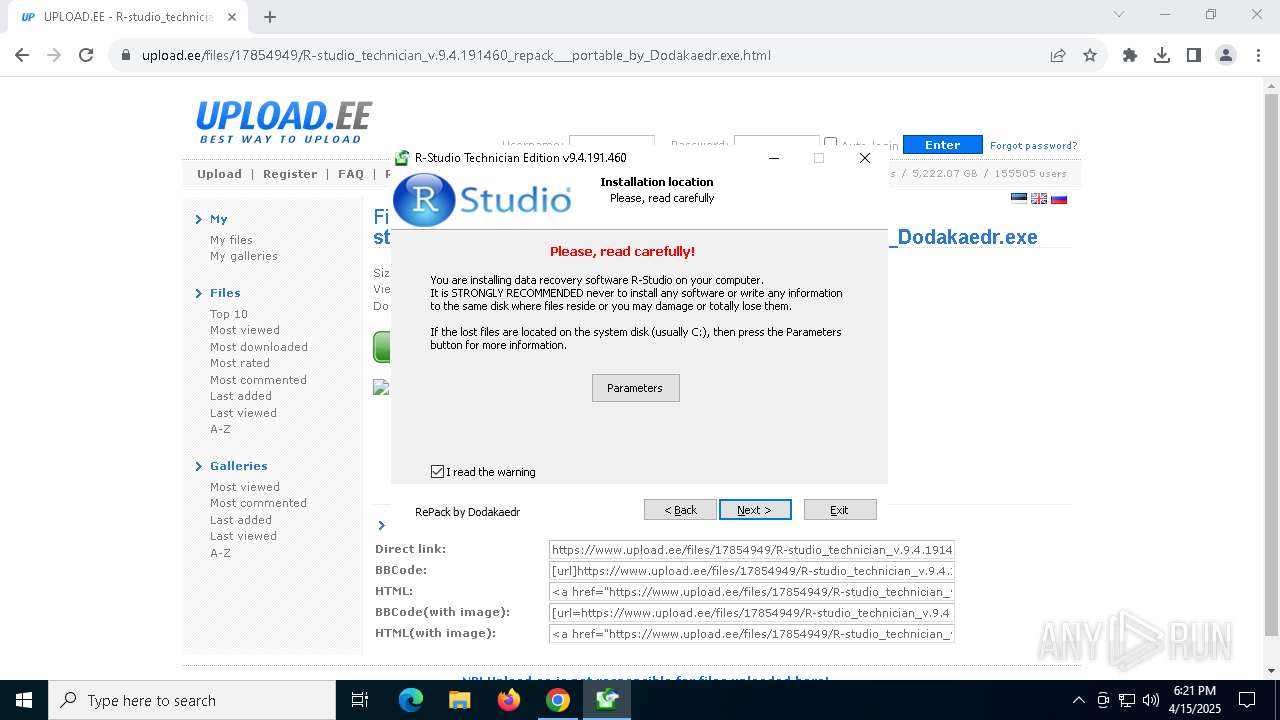
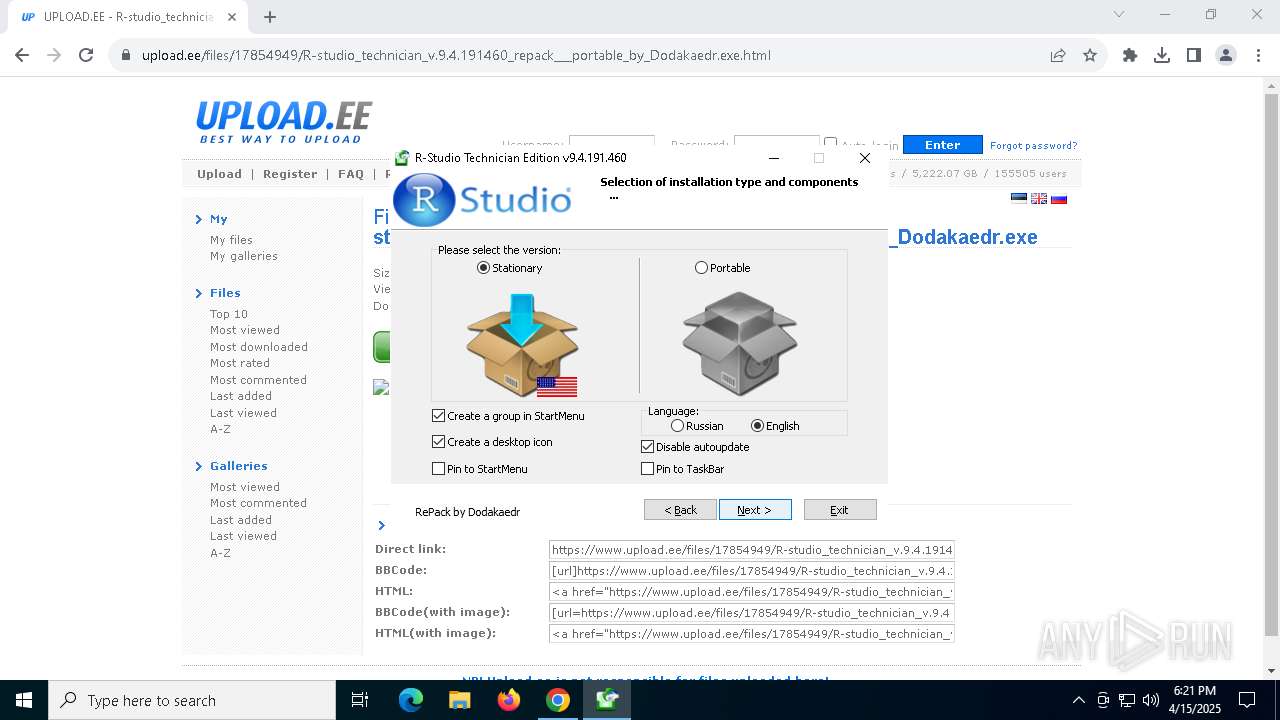
MALICIOUS
Executing a file with an untrusted certificate
- RStudio.exe (PID: 8144)
- RStudio.exe (PID: 728)
- RStudio.exe (PID: 7196)
SUSPICIOUS
Reads the Windows owner or organization settings
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
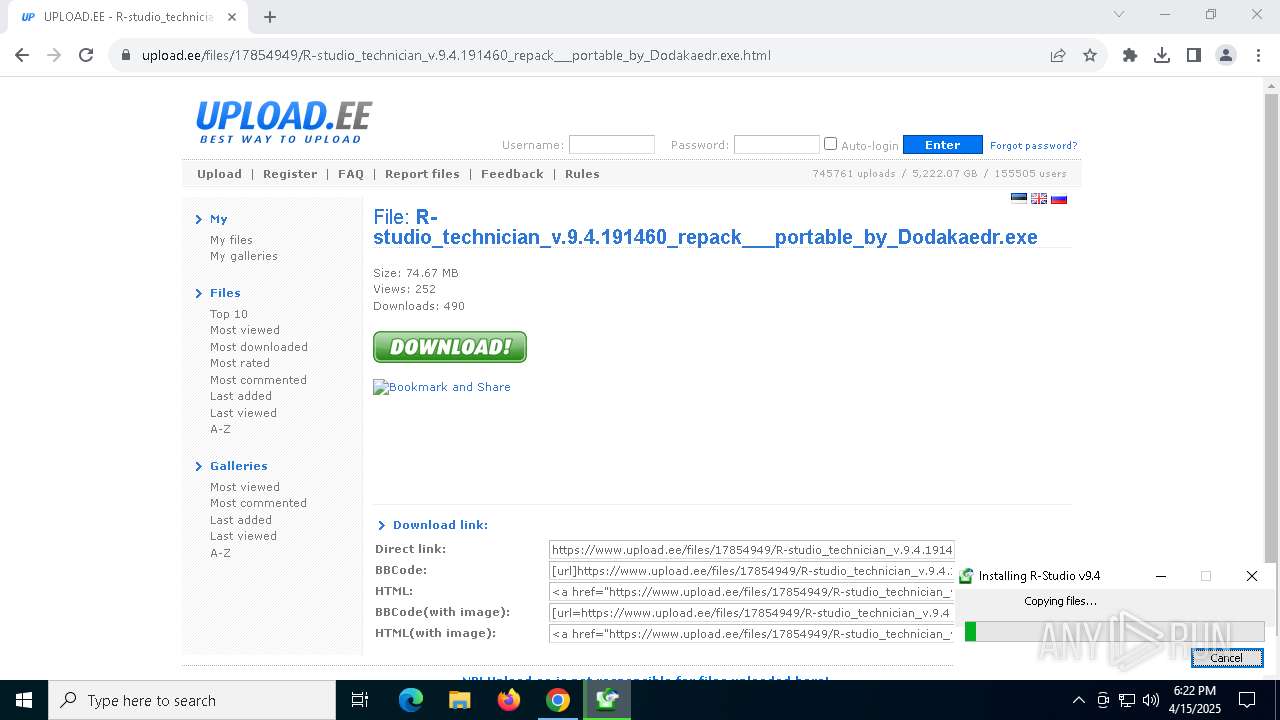
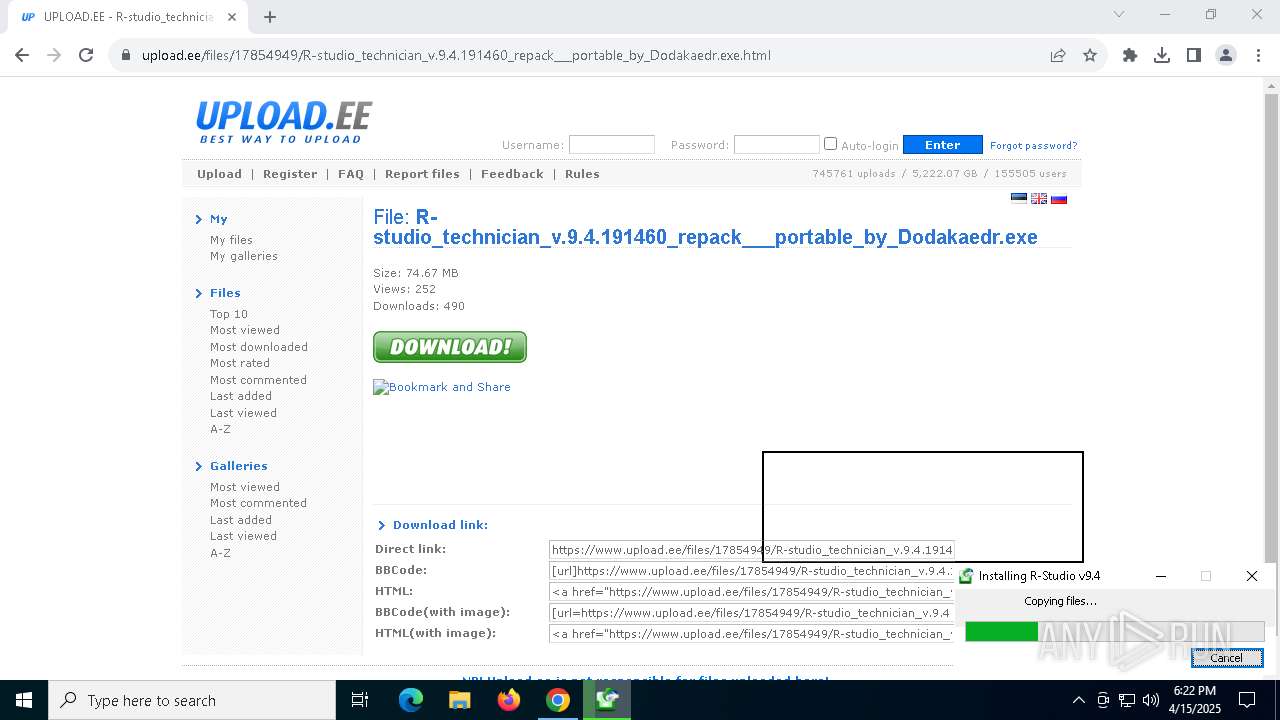
Executable content was dropped or overwritten
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe (PID: 1052)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Process drops legitimate windows executable
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
There is functionality for taking screenshot (YARA)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Drops a system driver (possible attempt to evade defenses)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
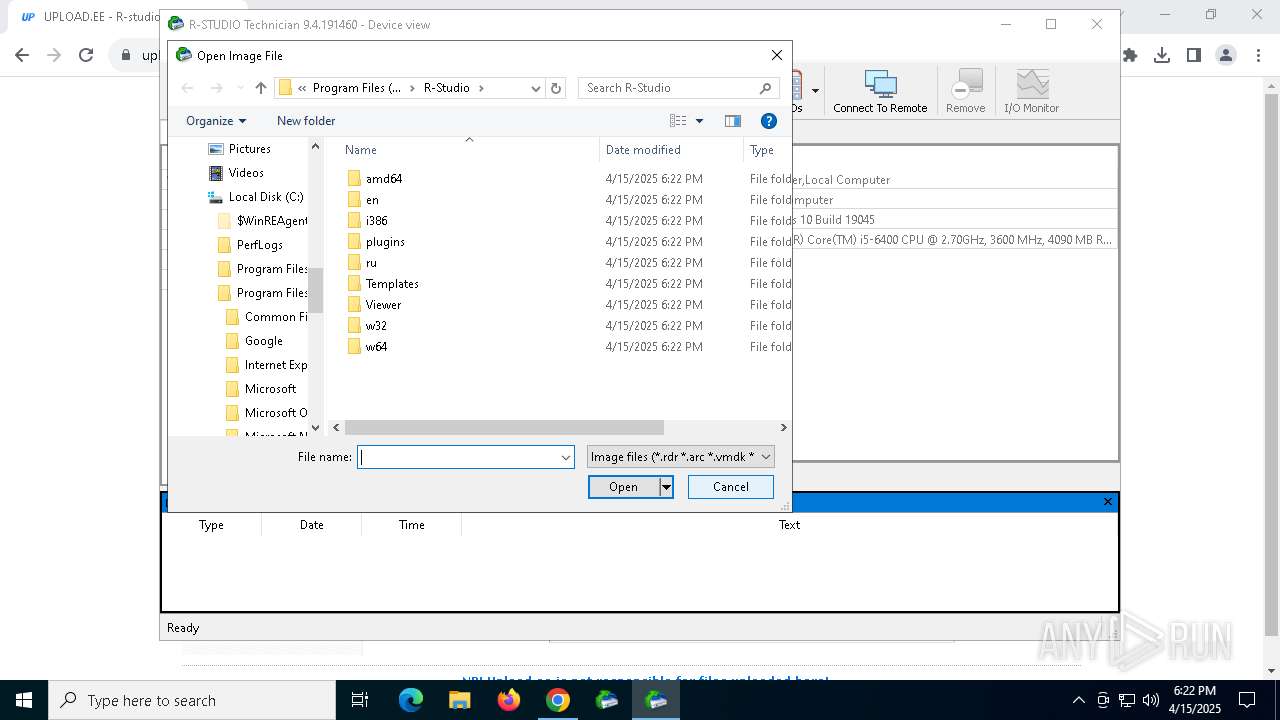
Searches for installed software
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Detected use of alternative data streams (AltDS)
- RStudio64.exe (PID: 4560)
Creates file in the systems drive root
- RStudio64.exe (PID: 4560)
Reads security settings of Internet Explorer
- RStudio64.exe (PID: 4560)
The process drops C-runtime libraries
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 7320)
Application launched itself
- chrome.exe (PID: 7320)
Create files in a temporary directory
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe (PID: 1052)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Reads the computer name
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
- RStudio64.exe (PID: 4560)
- RStudio64.exe (PID: 4208)
The sample compiled with english language support
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Checks supported languages
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe (PID: 1052)
- RStudio.exe (PID: 8144)
- RStudio64.exe (PID: 4560)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
- RStudio64.exe (PID: 4208)
- RStudio.exe (PID: 728)
Detects InnoSetup installer (YARA)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe (PID: 1052)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Compiled with Borland Delphi (YARA)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe (PID: 1052)
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
The sample compiled with russian language support
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
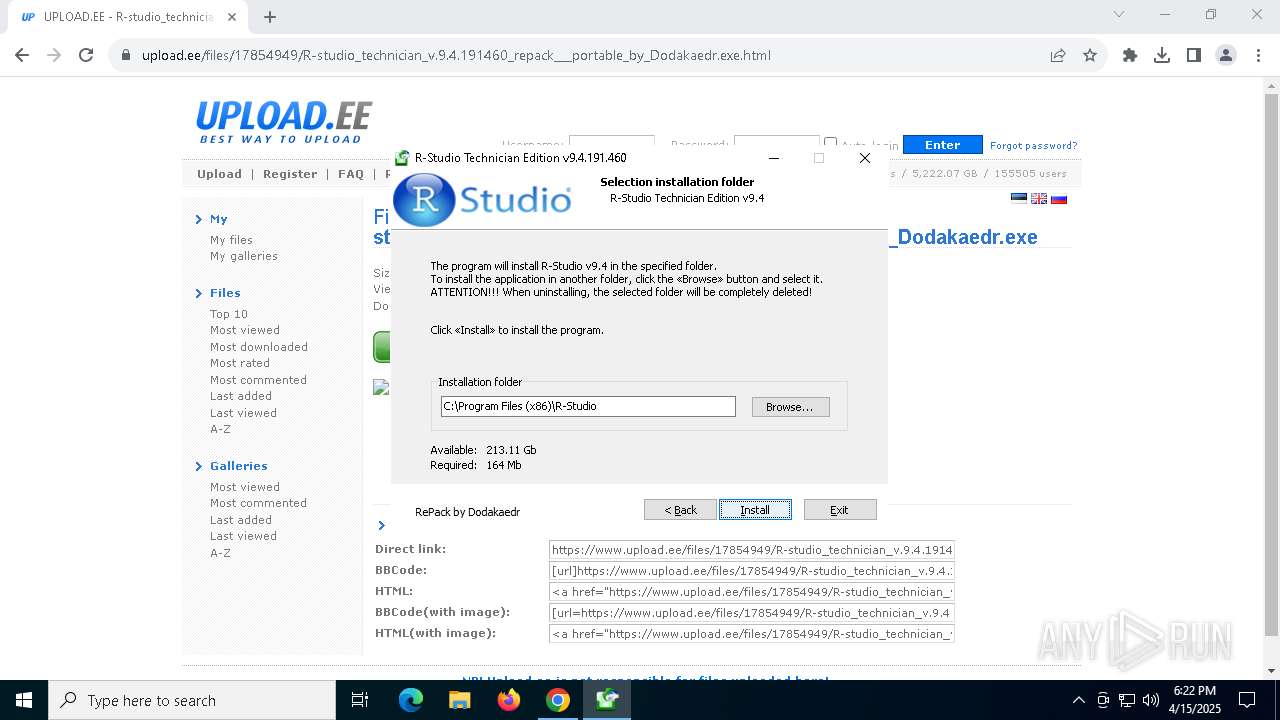
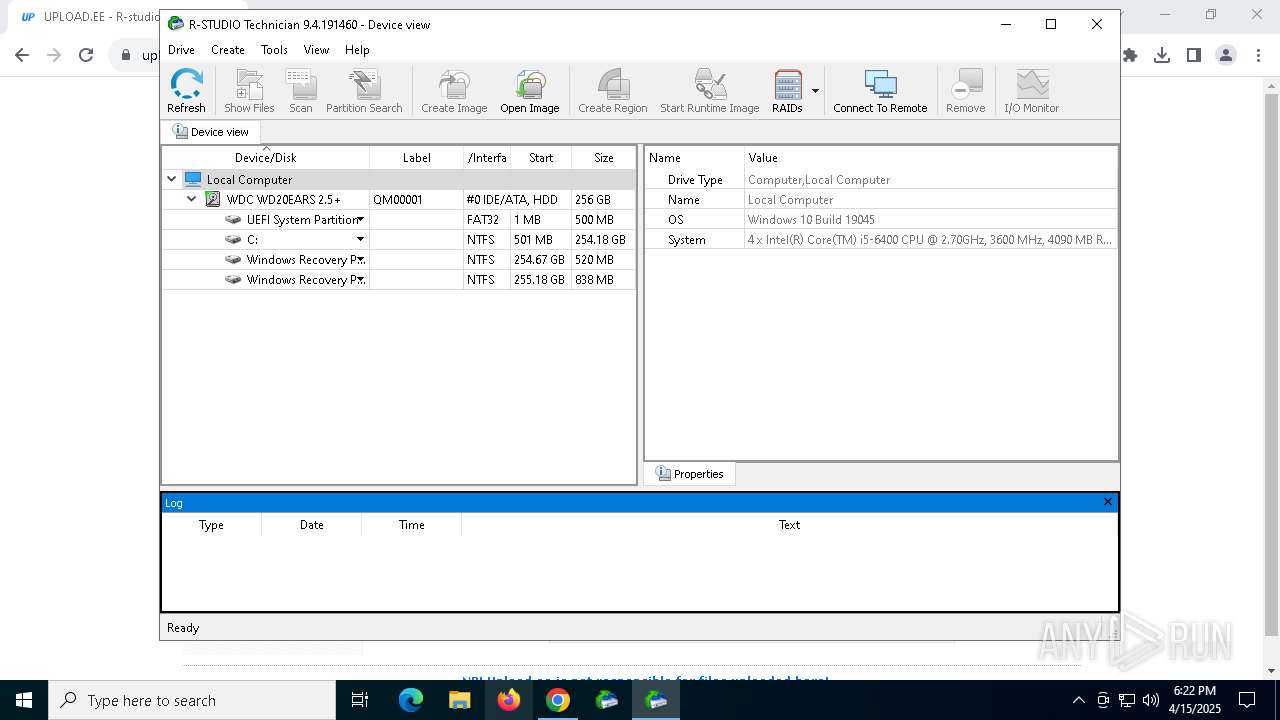
Creates files in the program directory
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Reads the software policy settings
- slui.exe (PID: 1616)
- slui.exe (PID: 4696)
Creates a software uninstall entry
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
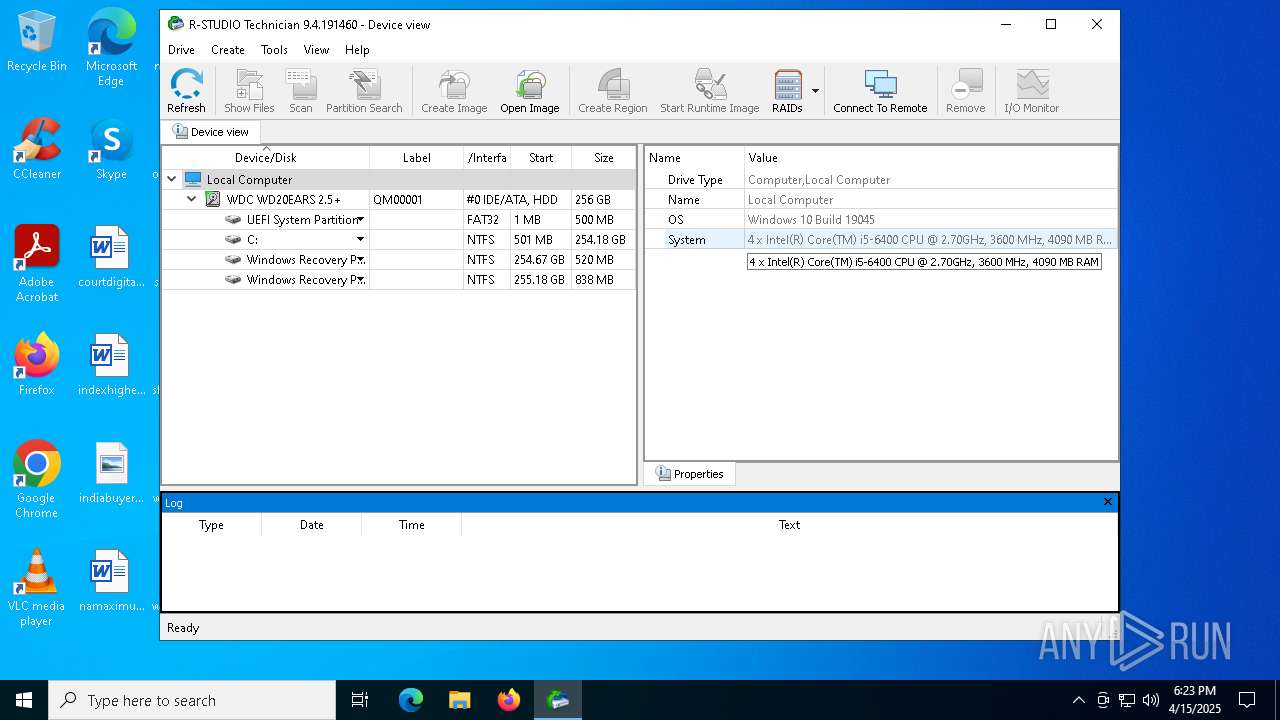
Reads CPU info
- RStudio64.exe (PID: 4560)
- RStudio64.exe (PID: 4208)
Process checks computer location settings
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
Reads Environment values
- RStudio64.exe (PID: 4560)
- RStudio64.exe (PID: 4208)
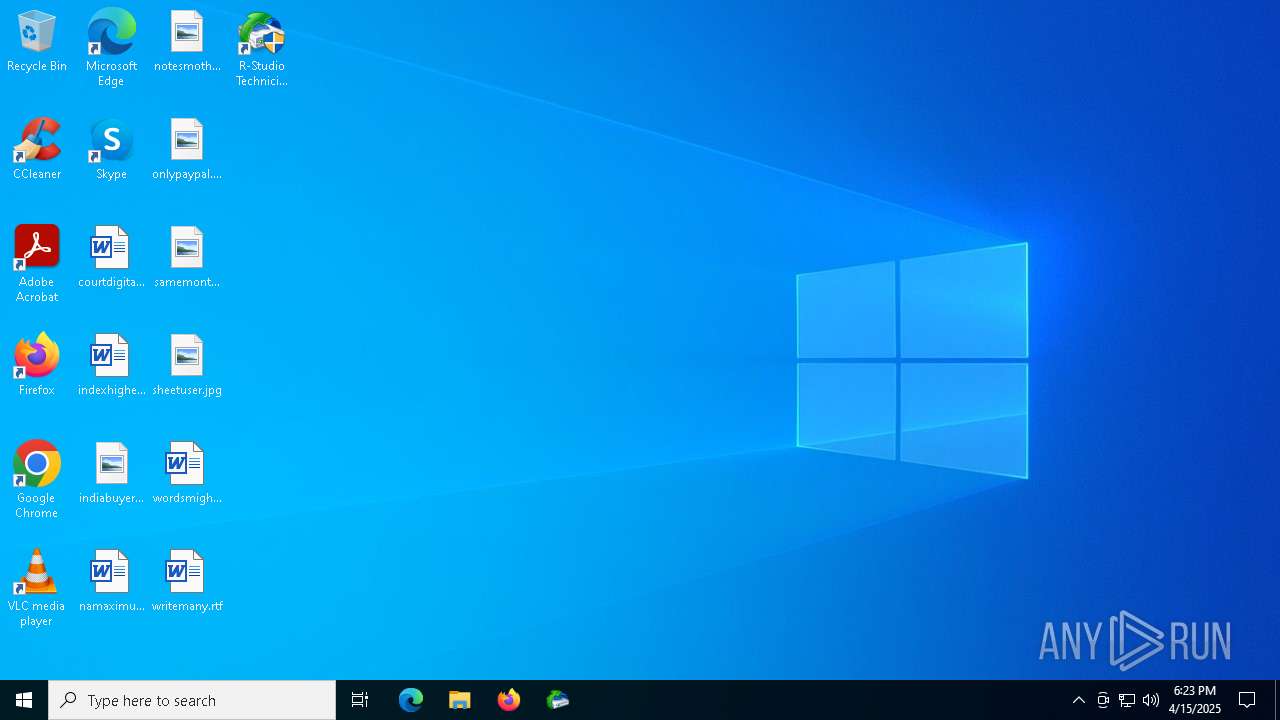
Creates files or folders in the user directory
- R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.tmp (PID: 6068)
- RStudio64.exe (PID: 4560)
Checks proxy server information
- slui.exe (PID: 4696)
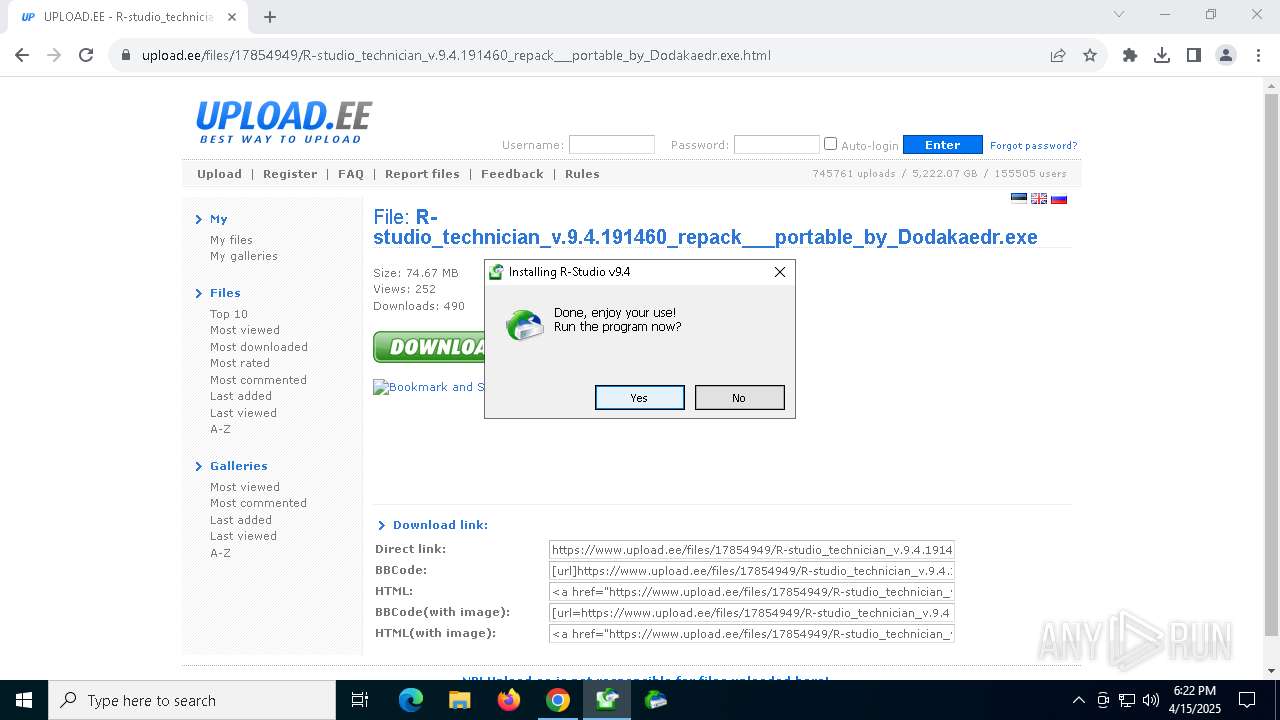
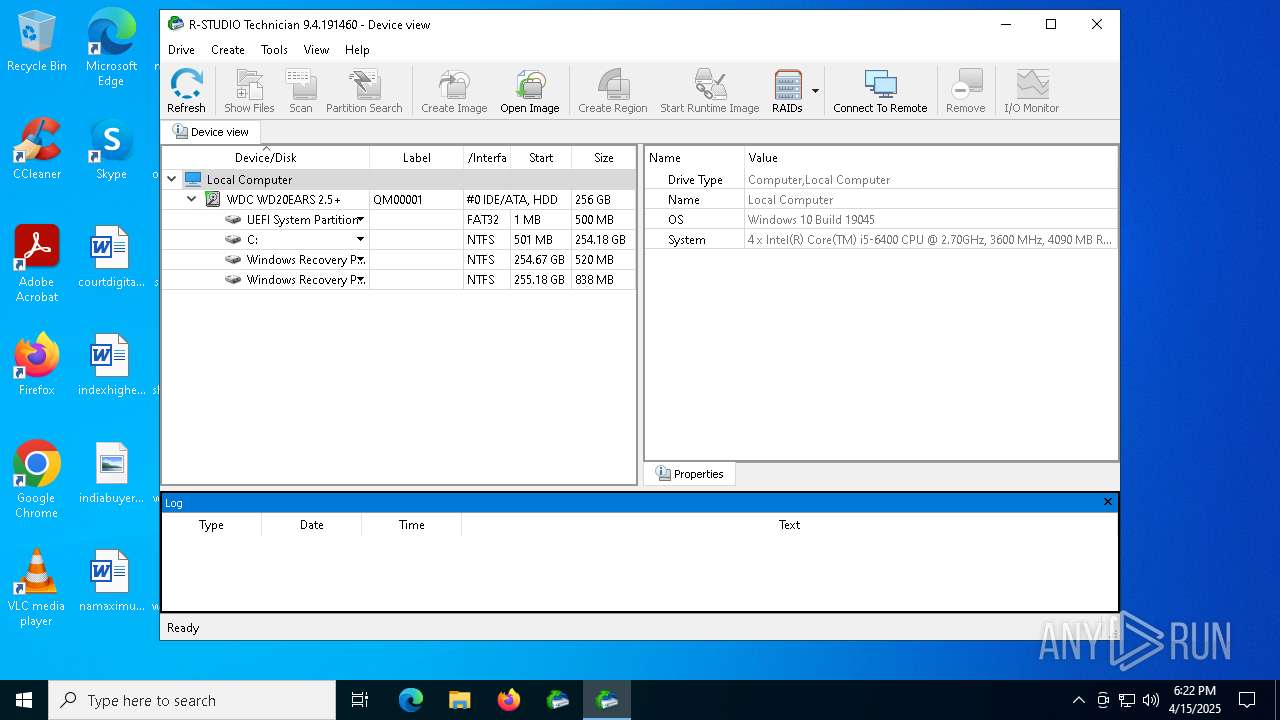
Manual execution by a user
- RStudio.exe (PID: 728)
- RStudio.exe (PID: 7196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
37
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=4844 --field-trial-handle=1784,i,3478325334598744237,3504209311846150365,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
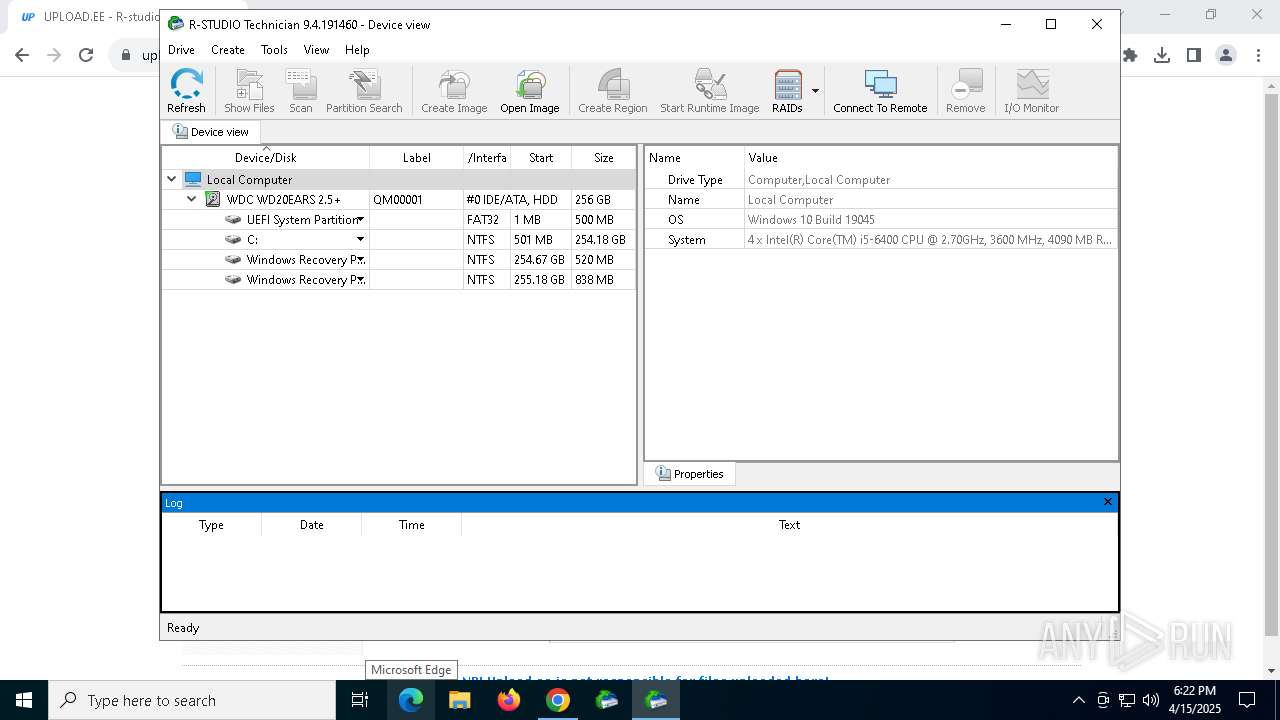
| 728 | "C:\Program Files (x86)\R-Studio\RStudio.exe" | C:\Program Files (x86)\R-Studio\RStudio.exe | explorer.exe | ||||||||||||
User: admin Company: R-Tools Technology Inc. Integrity Level: HIGH Description: R-Studio Exit code: 0 Version: 9, 4, 191, 460 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=5888 --field-trial-handle=1784,i,3478325334598744237,3504209311846150365,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5416 --field-trial-handle=1784,i,3478325334598744237,3504209311846150365,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\Downloads\R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe" | C:\Users\admin\Downloads\R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe | chrome.exe | ||||||||||||
User: admin Company: R-Tools Technology Inc (RePack by Dodakaedr) Integrity Level: HIGH Description: R-Studio Technician Edition Exit code: 0 Version: 9.4.191.460 Modules
| |||||||||||||||
| 1616 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=4844 --field-trial-handle=1784,i,3478325334598744237,3504209311846150365,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3316 --field-trial-handle=1784,i,3478325334598744237,3504209311846150365,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4108 | "C:\Users\admin\Downloads\R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe" | C:\Users\admin\Downloads\R-studio_technician_v.9.4.191460_repack___portable_by_Dodakaedr.exe | — | chrome.exe | |||||||||||
User: admin Company: R-Tools Technology Inc (RePack by Dodakaedr) Integrity Level: MEDIUM Description: R-Studio Technician Edition Exit code: 3221226540 Version: 9.4.191.460 Modules
| |||||||||||||||
| 4208 | "C:\Program Files (x86)\R-Studio\RStudio64.exe" | C:\Program Files (x86)\R-Studio\RStudio64.exe | — | RStudio.exe | |||||||||||
User: admin Company: R-Tools Technology Inc. Integrity Level: HIGH Description: R-Studio Exit code: 0 Version: 9, 4, 191, 460 Modules
| |||||||||||||||
Total events
10 718
Read events
10 486
Write events
124
Delete events
108
Modification events
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7696) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000473EEE2233AEDB01 | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | ahfgeienlihckogmohjhadlkjgocpleb |
Value: 3B08F722C14555E595AF269F140EE426CE8DEBAD90D03EE9FF33B95CB34233F6 | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | bjbddleefiddlmdfdfbgodgacjjldihj |
Value: 5CFE6AD362B9AABBD07085580BC6C063CF1C79A0B22ECB6BCBA21EECA68BA07F | |||
| (PID) Process: | (7320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | mhjfbmdgcfjbbpaeojofohoefgiehjai |
Value: F6EE482B70E472BD0FE04C8E130D7E2A0D87334BDC8F199AD874C100863BC5BE | |||
Executable files
155
Suspicious files
378
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10be02.TMP | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10be02.TMP | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10bdf3.TMP | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10be02.TMP | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10be12.TMP | — | |
MD5:— | SHA256:— | |||
| 7320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
97
DNS requests
131
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5304 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
6476 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
6476 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
5304 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aduqmobp6ks75n7ttnnffvuarmea_20250330.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250330.743742949.14_all_ENUS500000_fqd3hluhdynjr3tbfczv7voxsu.crx3 | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7320 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7540 | chrome.exe | 57.129.39.102:443 | www.upload.ee | — | FR | whitelisted |
7540 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.upload.ee |
| shared |
accounts.google.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
du0pud0sdlmzf.cloudfront.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7540 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |