| File name: | Android Fastbooot Reset Tool 2.0.exe |
| Full analysis: | https://app.any.run/tasks/b3810c1a-907a-4370-bc61-400932aed195 |
| Verdict: | Malicious activity |
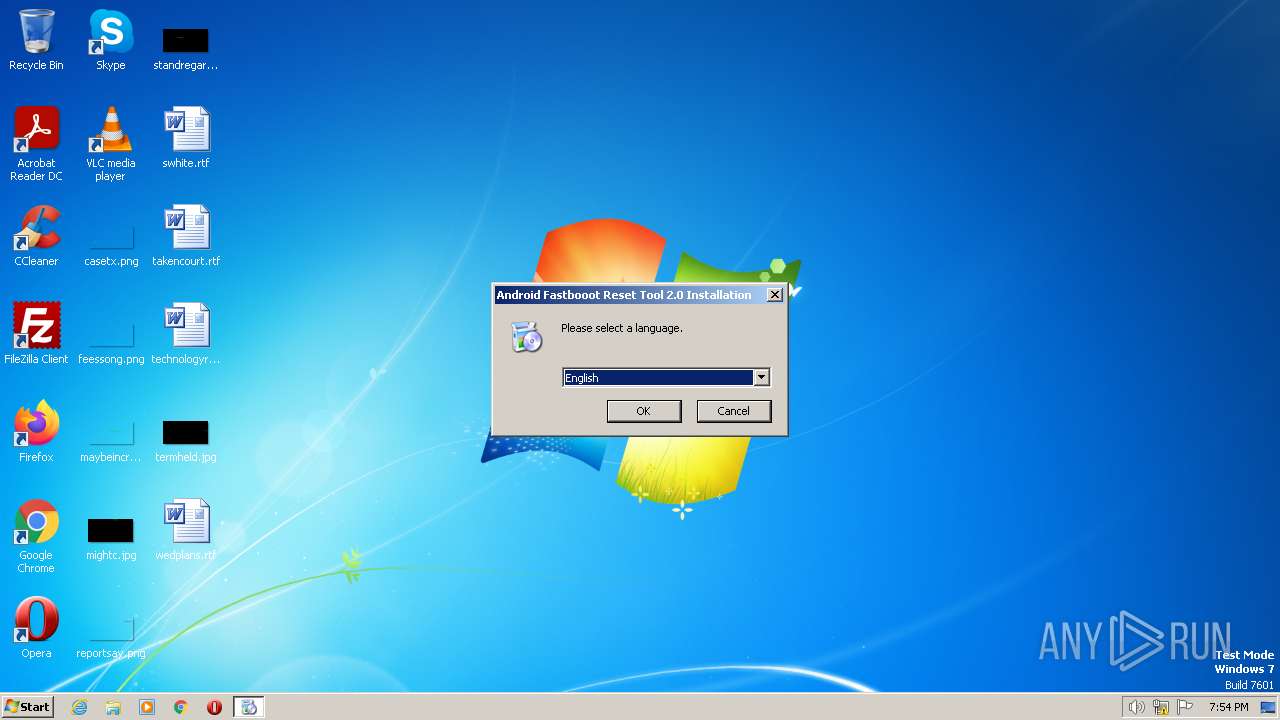
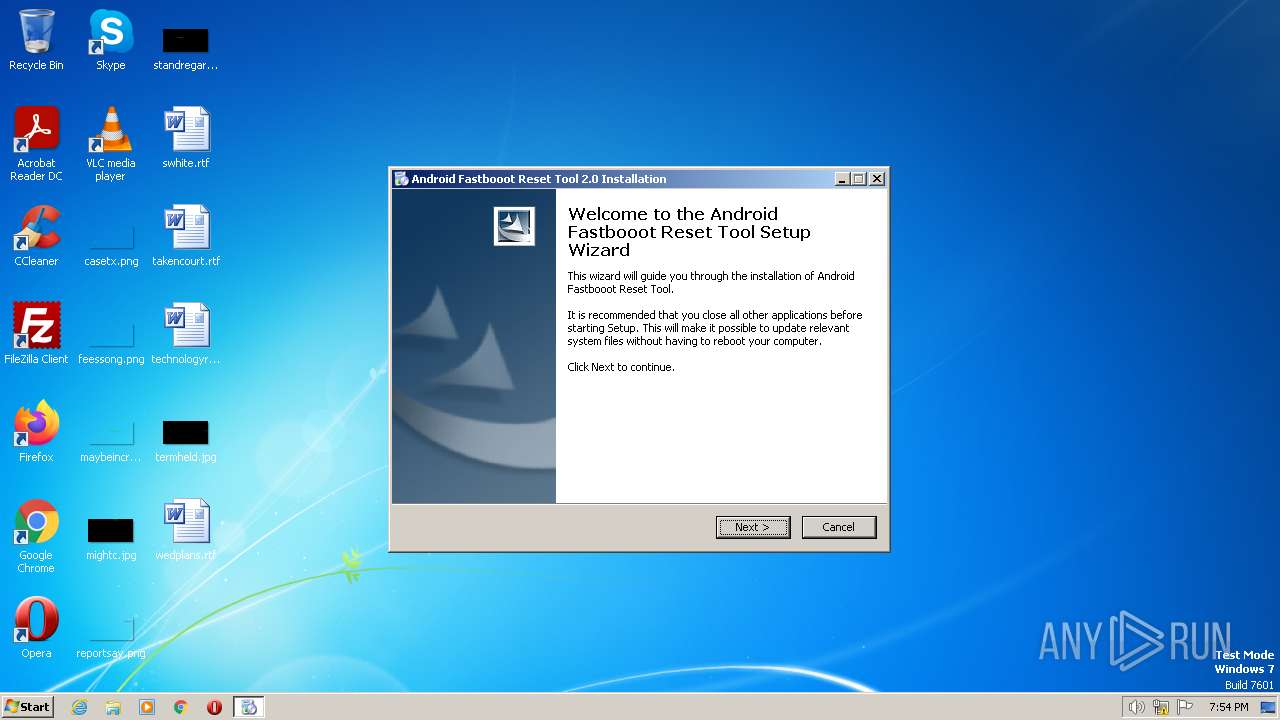
| Analysis date: | June 17, 2023, 18:54:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E5A2A3B9B0CB7B1DC714B94186F313AC |
| SHA1: | 9E3184288B5DCCFACA6ACB59834F2C528F4E4431 |
| SHA256: | D78850EE6DA97AA6A858419E6392387E5B8944A686E03D47995E7AAAAA12E448 |
| SSDEEP: | 24576:WAT8QE+kmQ0qGqSy5YOADwXHTI/ulFbvWkkbgmlJ:WAI+pqpn59XHEWDbvTAge |
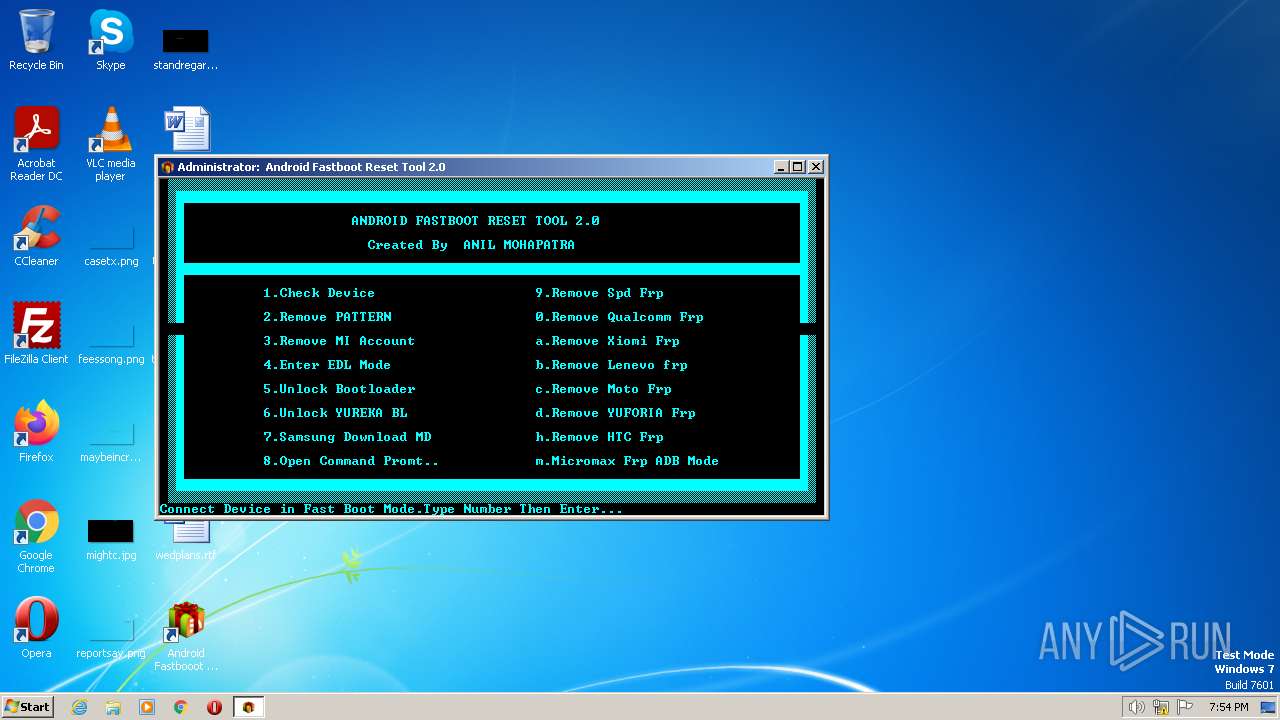
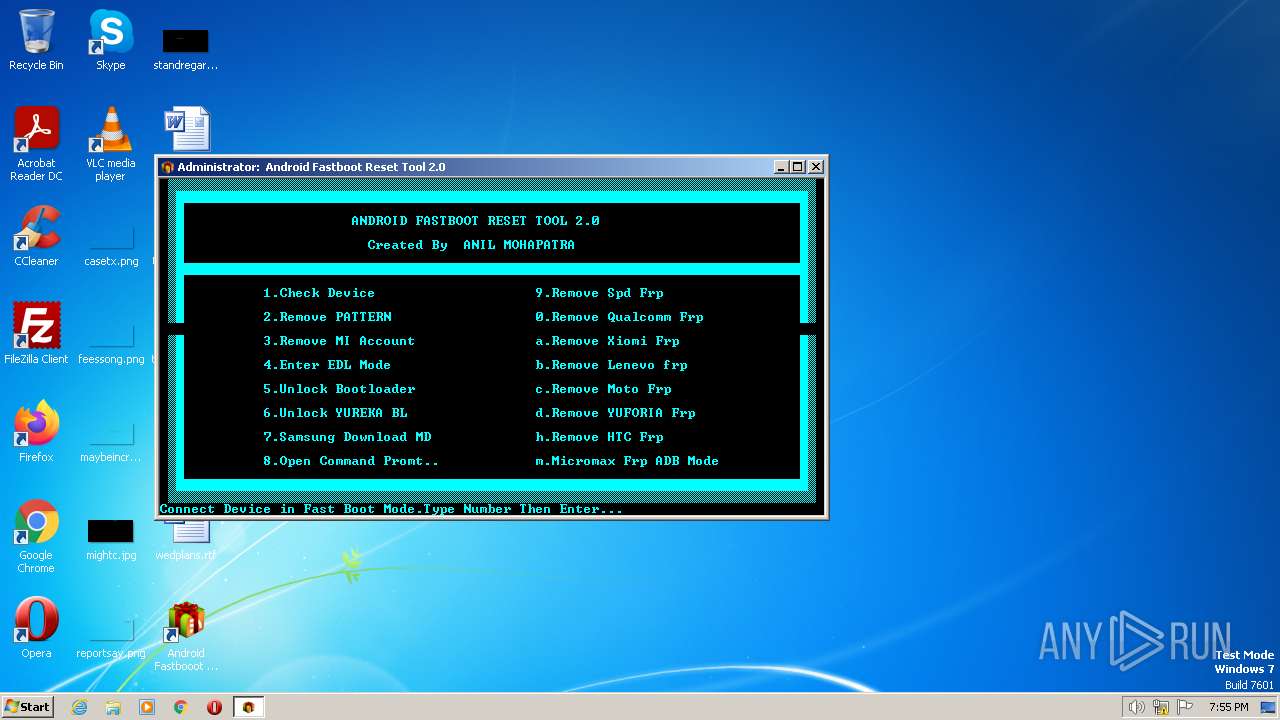
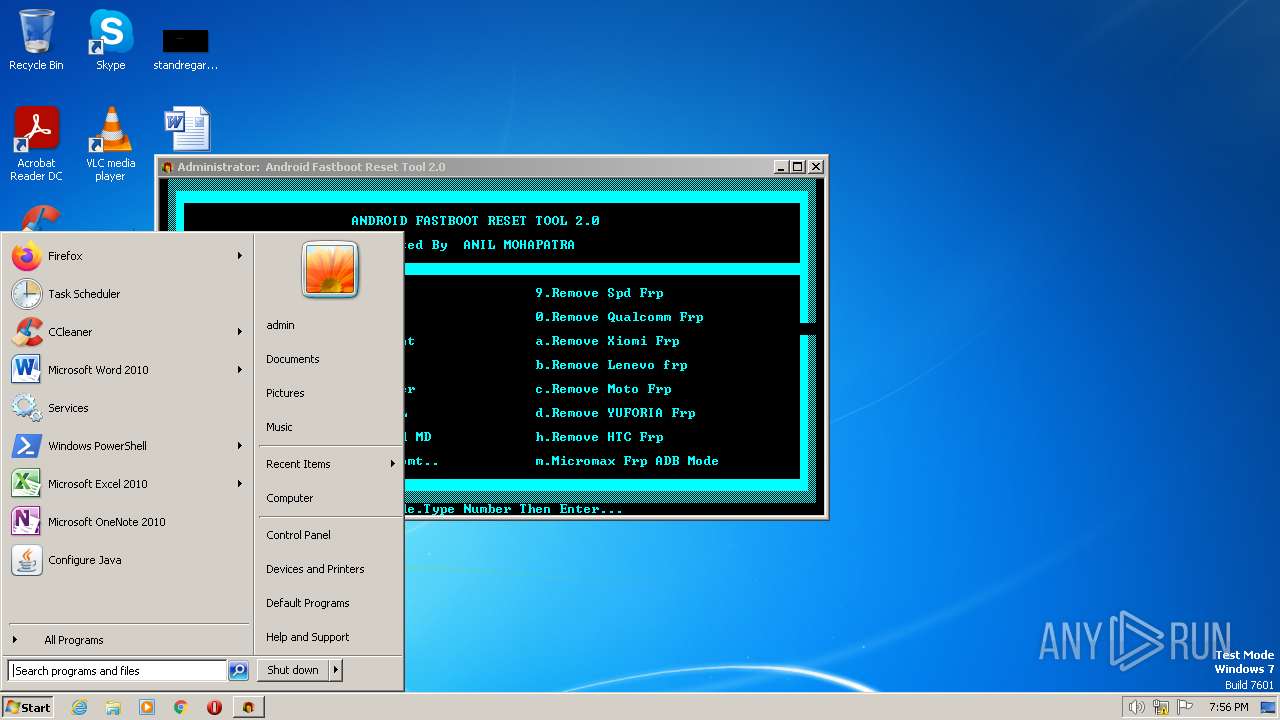
MALICIOUS
Application was dropped or rewritten from another process
- Android Fastbooot Reset Tool 2.0.exe (PID: 128)
- fastboot.exe (PID: 844)
Loads dropped or rewritten executable
- fastboot.exe (PID: 844)
SUSPICIOUS
Executing commands from a ".bat" file
- Android Fastbooot Reset Tool 2.0.exe (PID: 128)
Starts CMD.EXE for commands execution
- Android Fastbooot Reset Tool 2.0.exe (PID: 128)
Executable content was dropped or overwritten
- Android Fastbooot Reset Tool 2.0.exe (PID: 1352)
INFO
Reads the computer name
- Android Fastbooot Reset Tool 2.0.exe (PID: 1352)
- fastboot.exe (PID: 844)
Checks supported languages
- Android Fastbooot Reset Tool 2.0.exe (PID: 1352)
- Android Fastbooot Reset Tool 2.0.exe (PID: 128)
- mode.com (PID: 2448)
- fastboot.exe (PID: 844)
The process checks LSA protection
- Android Fastbooot Reset Tool 2.0.exe (PID: 1352)
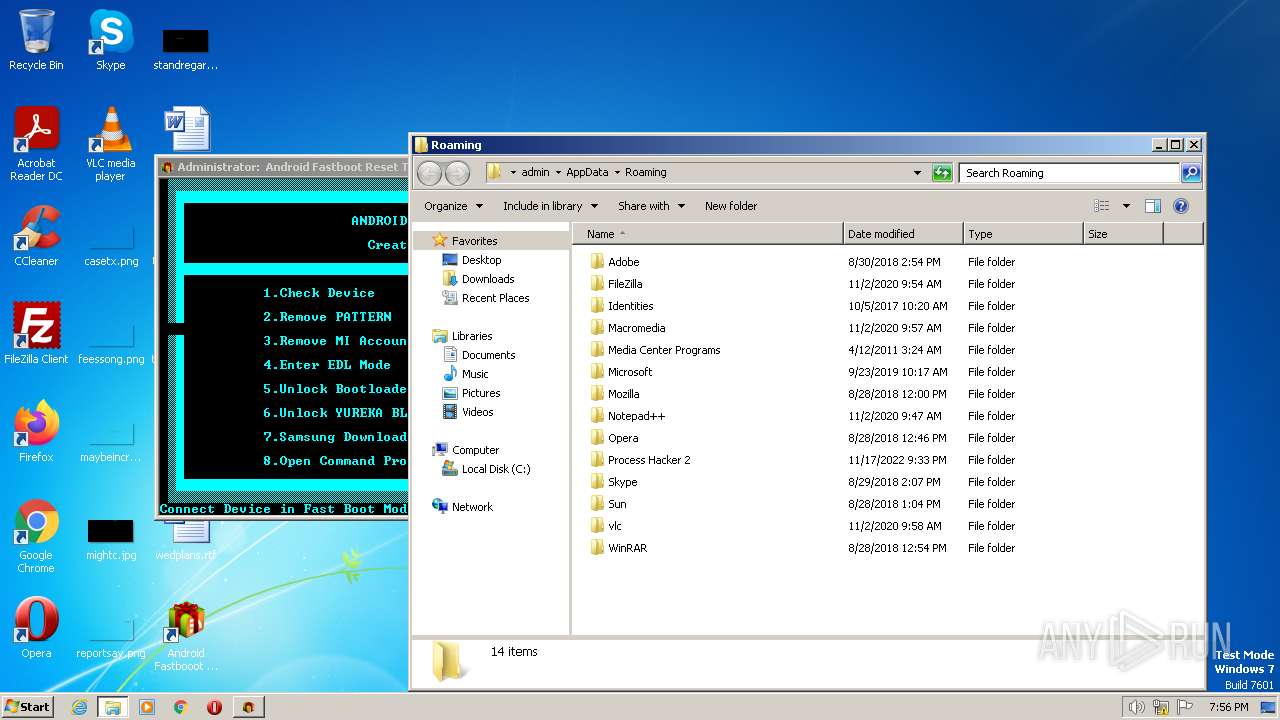
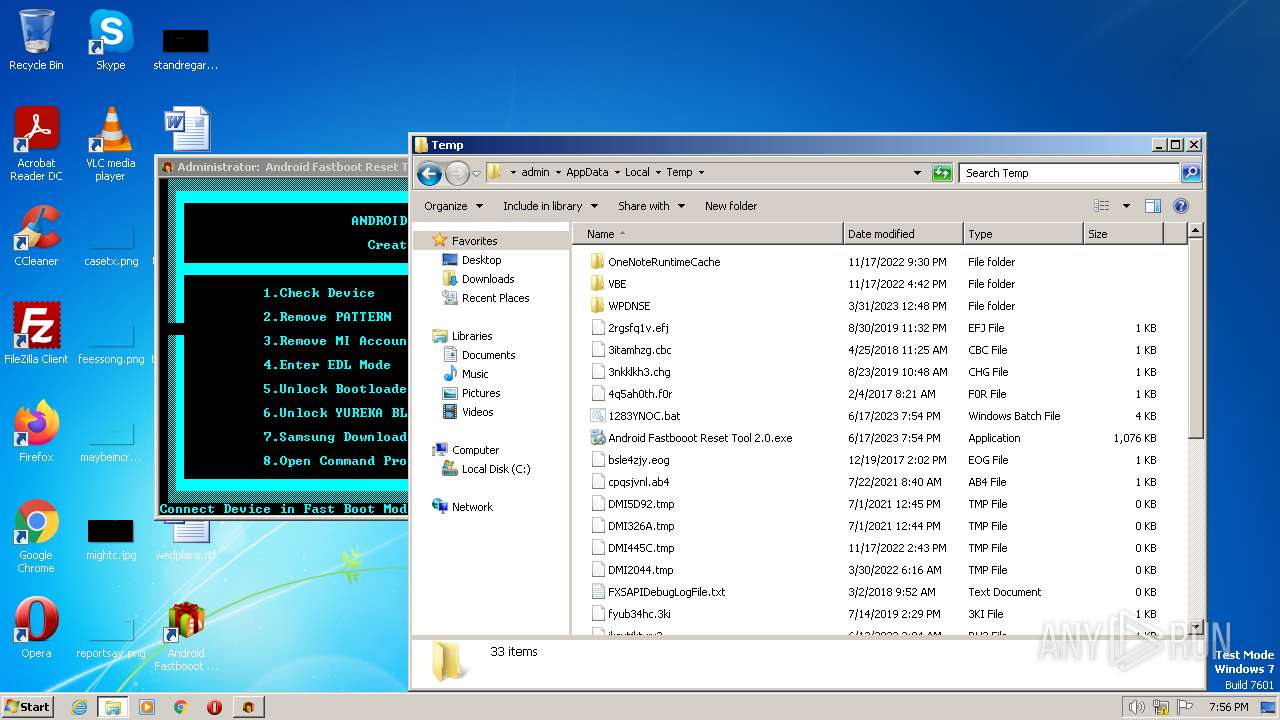
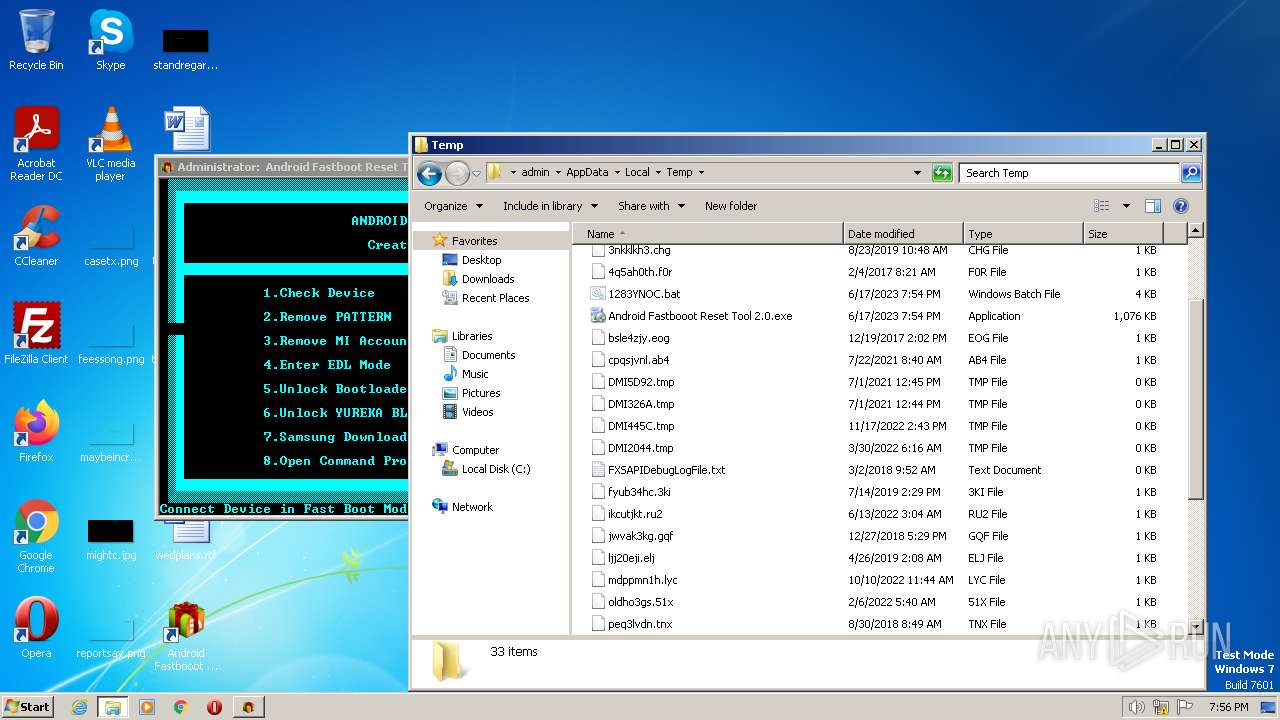
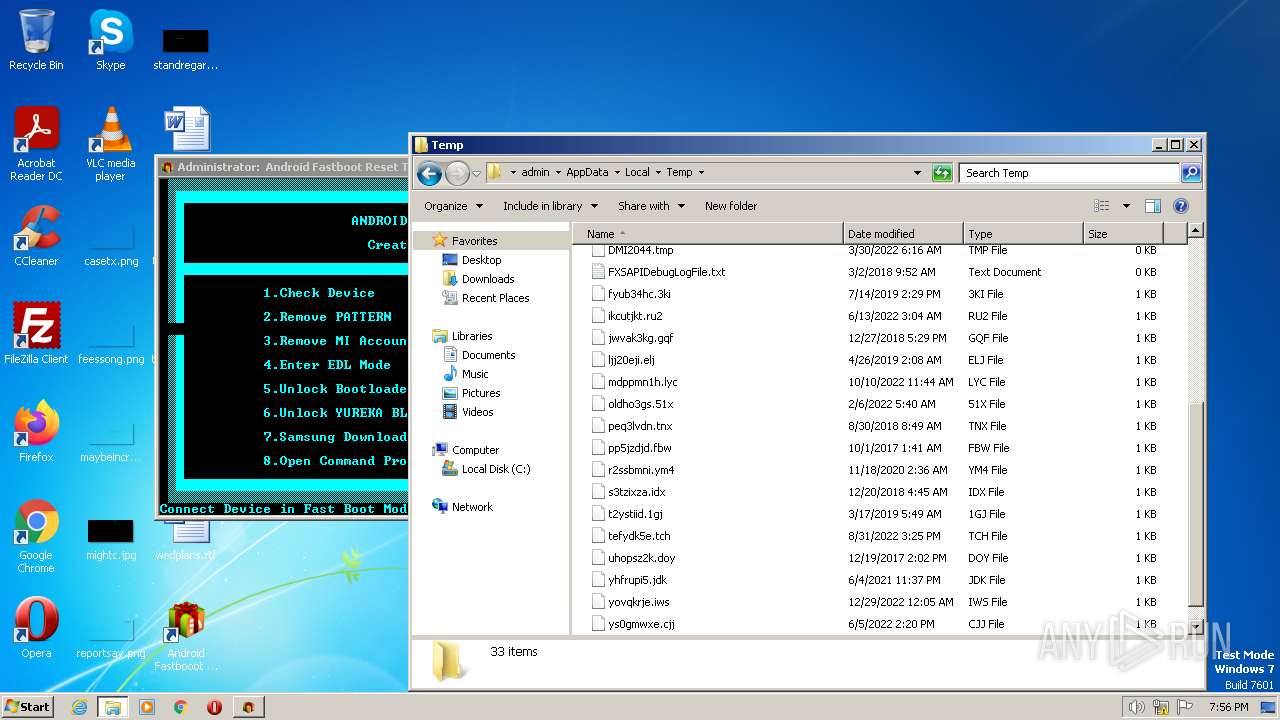
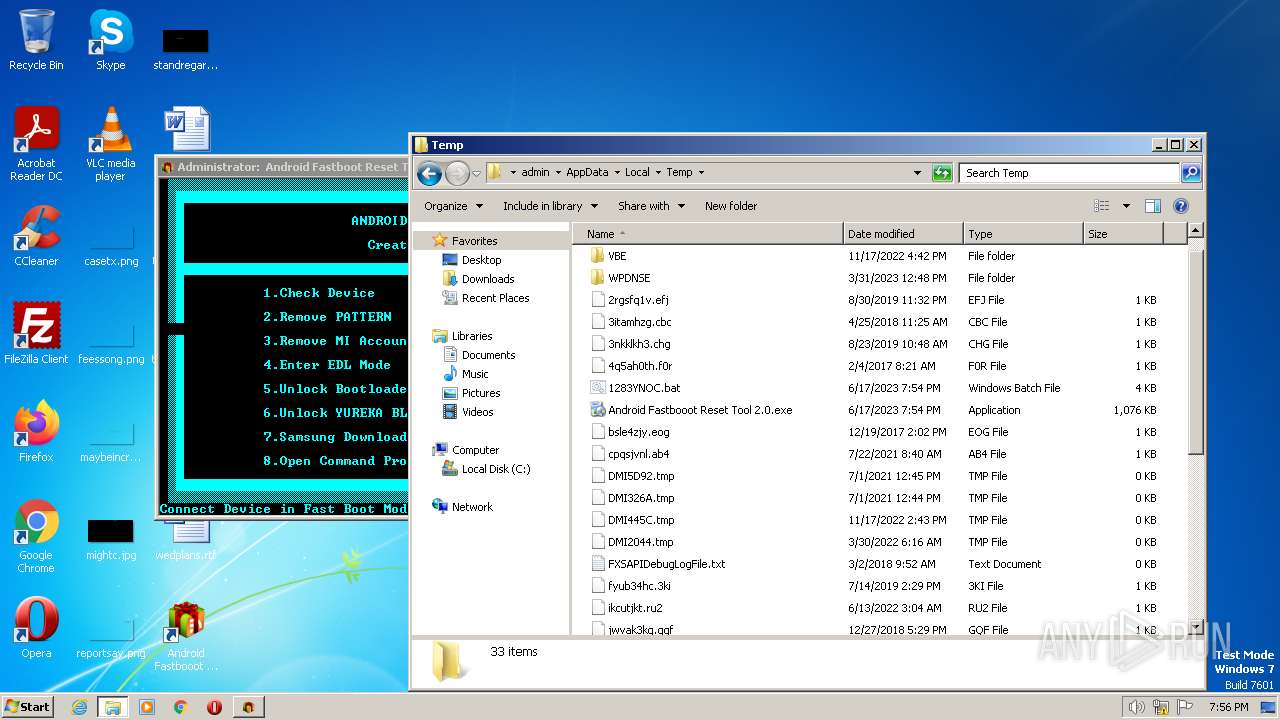
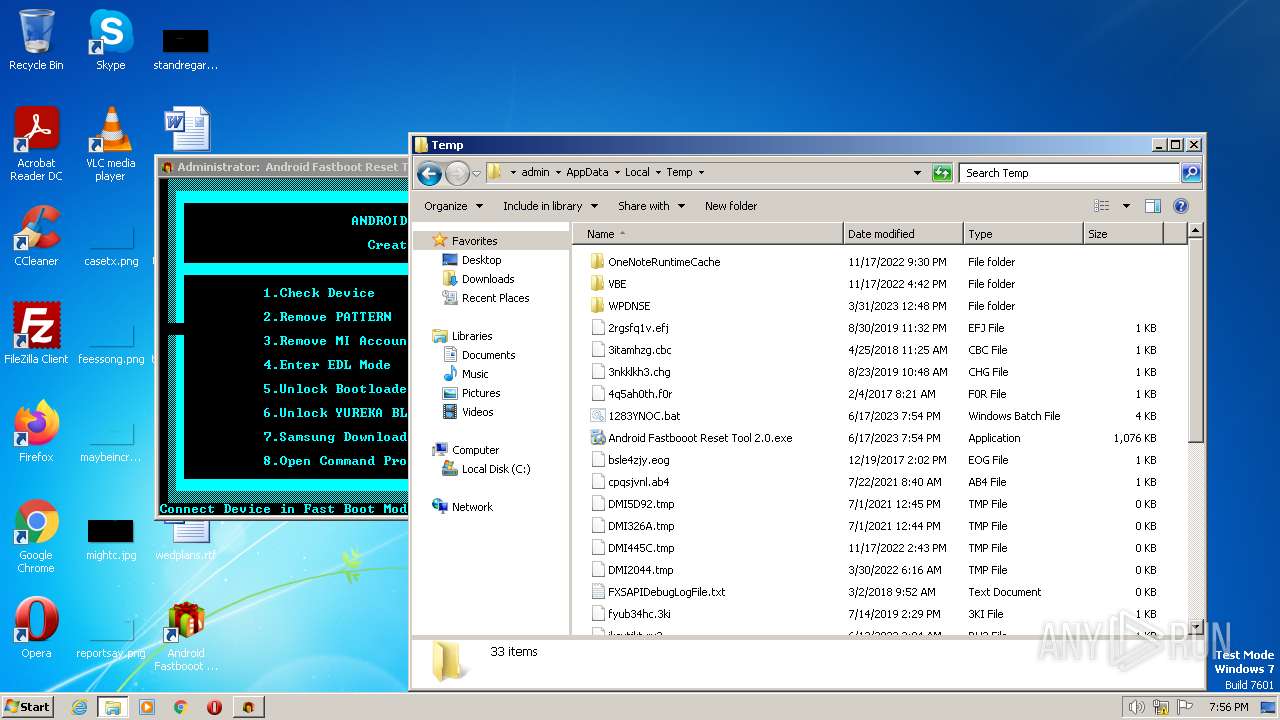
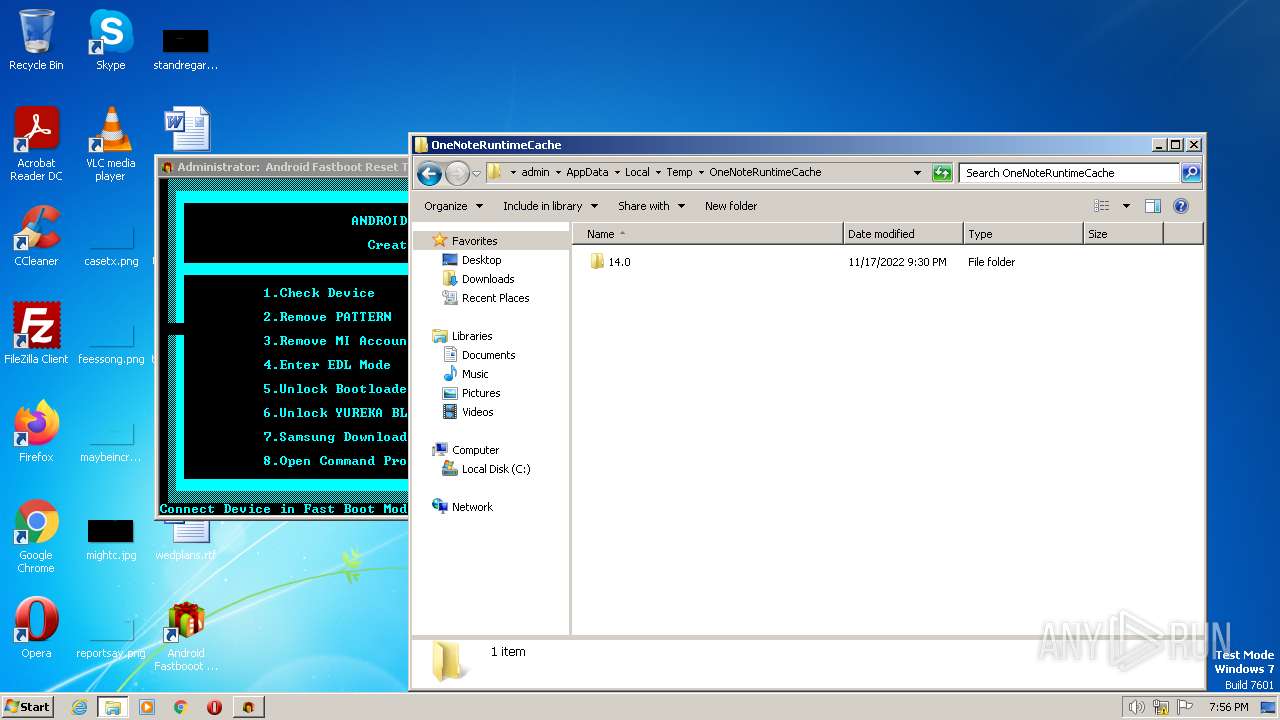
Create files in a temporary directory
- Android Fastbooot Reset Tool 2.0.exe (PID: 1352)
- Android Fastbooot Reset Tool 2.0.exe (PID: 128)
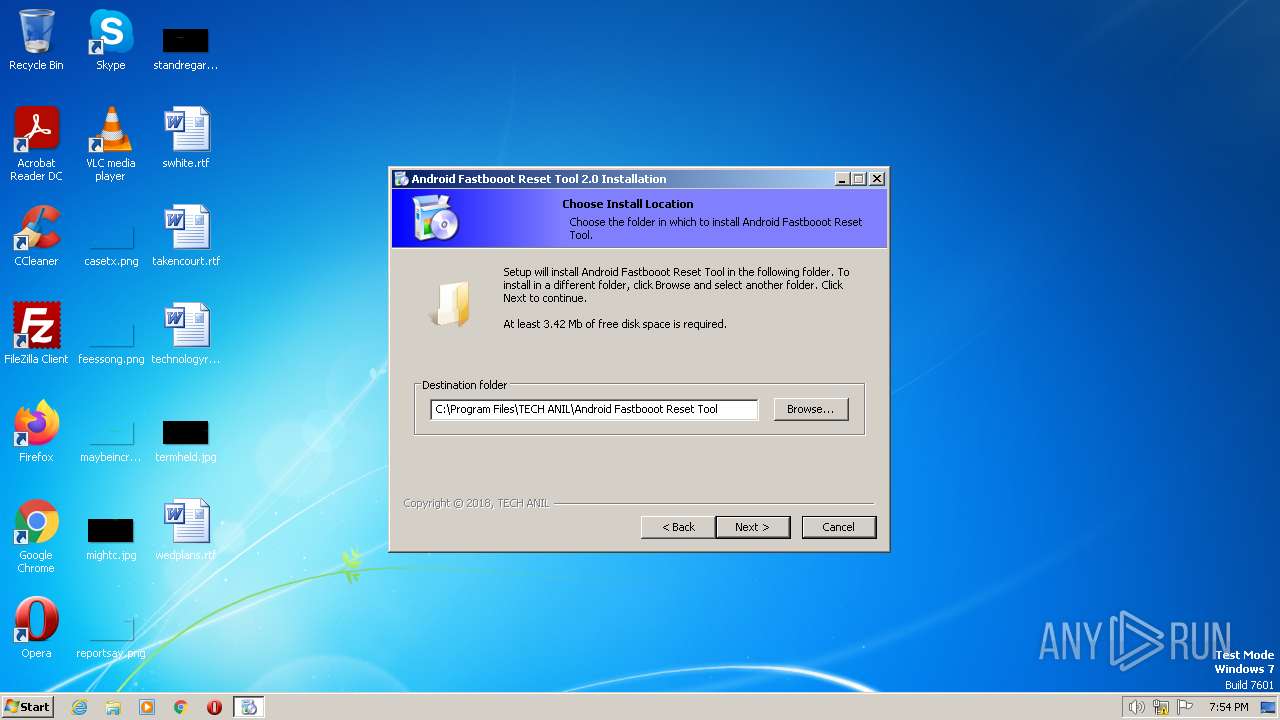
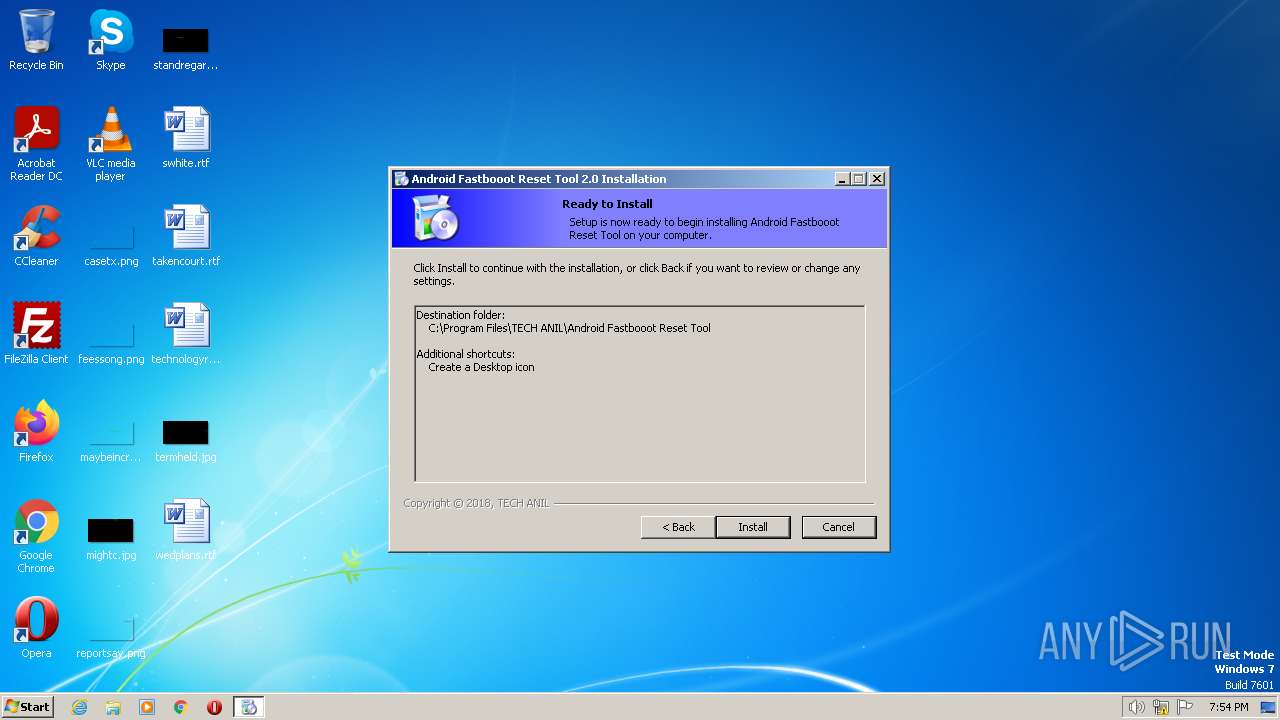
Creates files in the program directory
- Android Fastbooot Reset Tool 2.0.exe (PID: 1352)
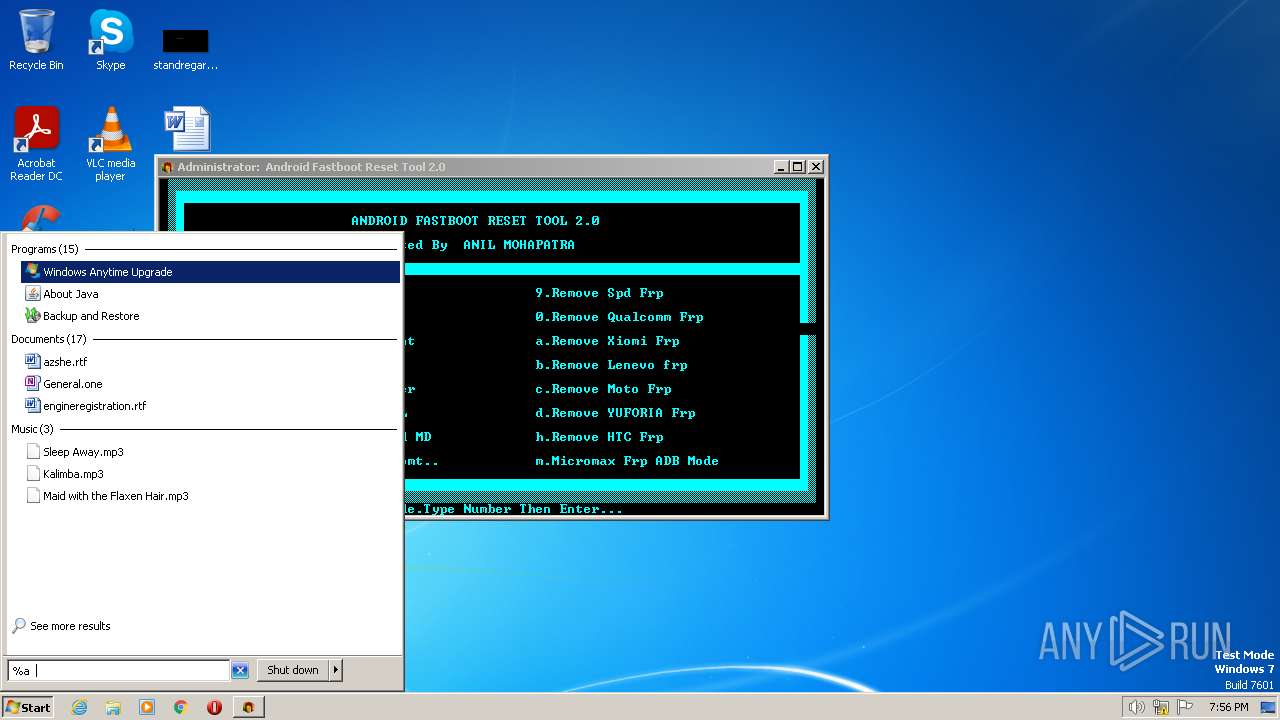
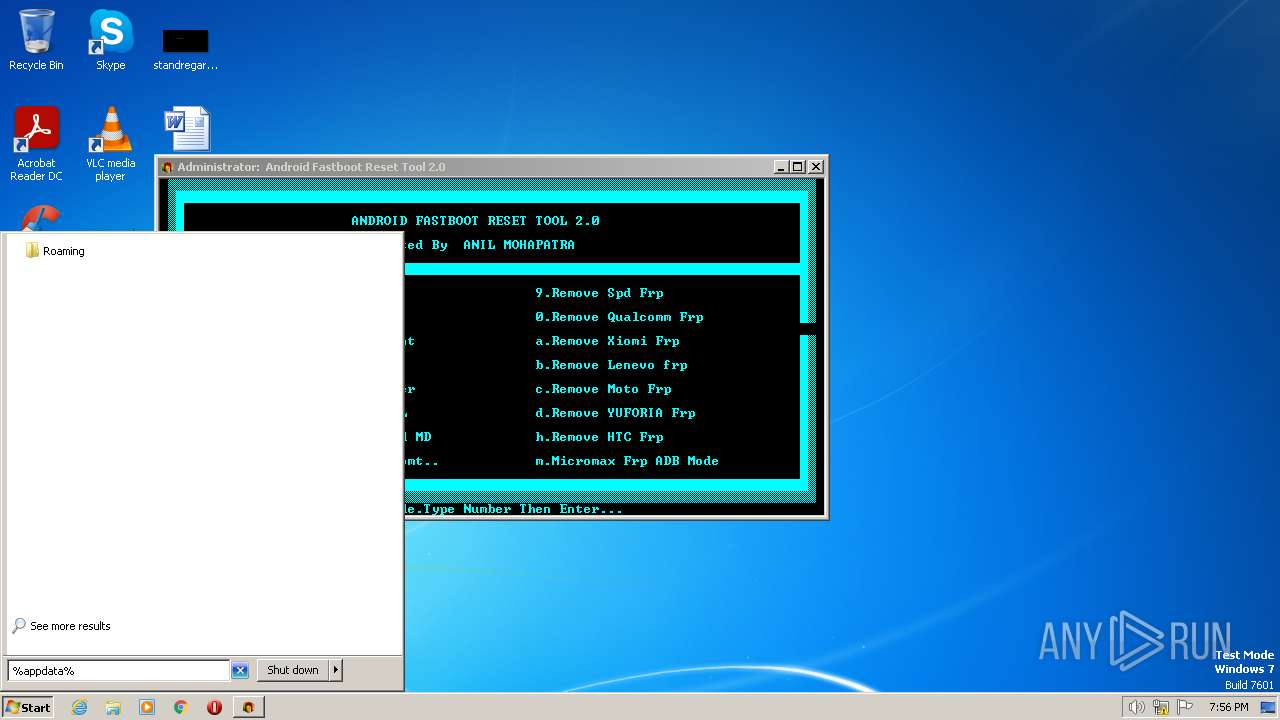
Manual execution by a user
- verclsid.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| LegalCopyright: | TECH ANIL |
|---|---|
| FileVersion: | 2.0 |
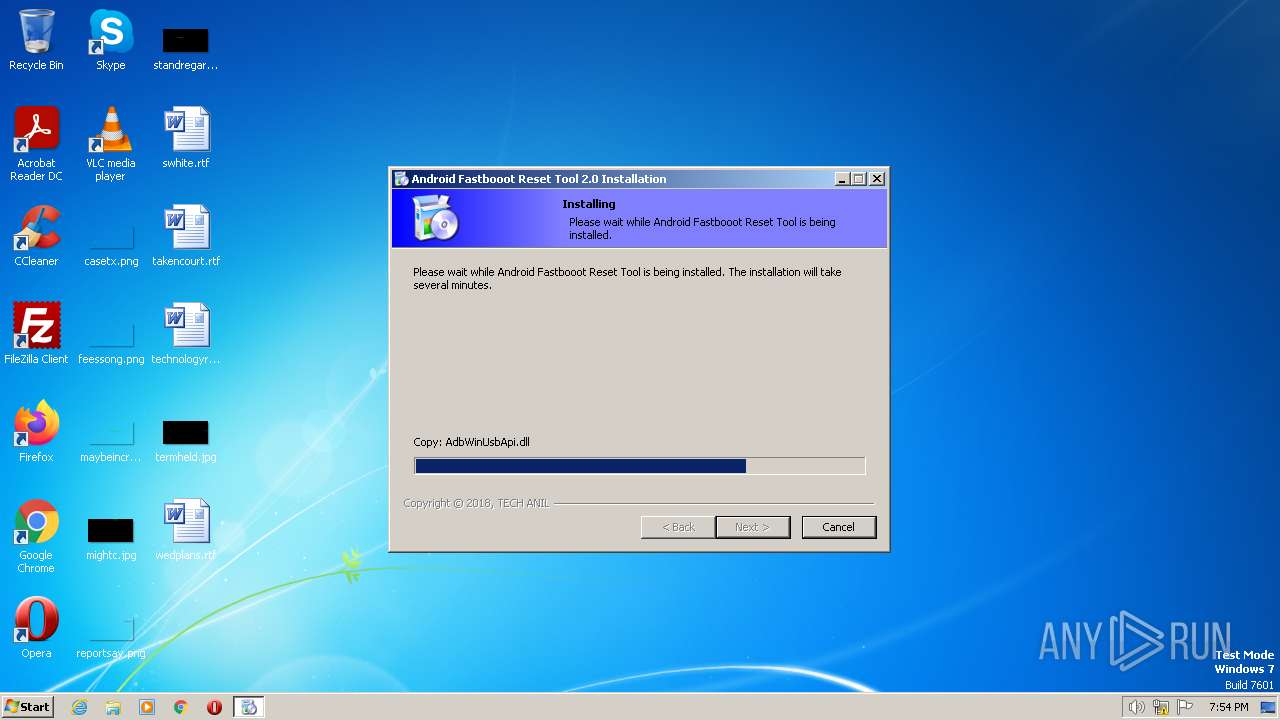
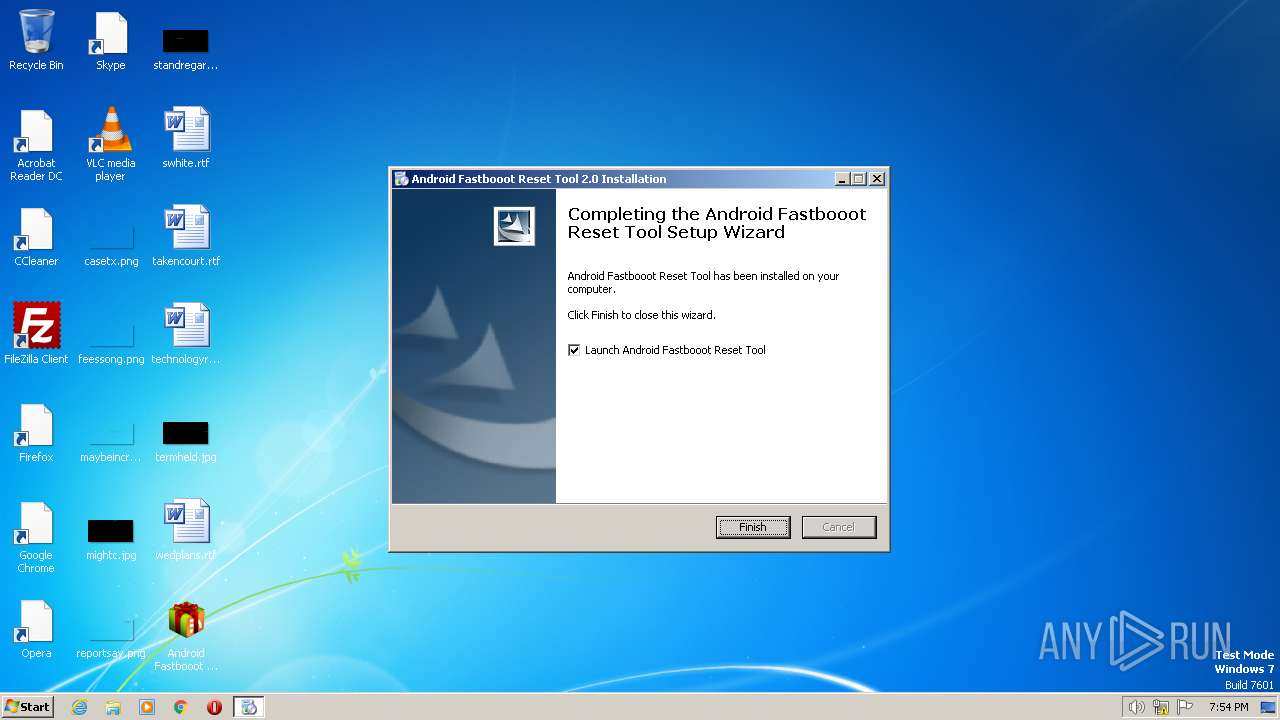
| FileDescription: | Android Fastbooot Reset Tool 2.0 Installation |
| CompanyName: | TECH ANIL |
| Comments: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 2.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x25468 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 49664 |
| CodeSize: | 148992 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | TECH ANIL |
| FileDescription: | Android Fastbooot Reset Tool 2.0 Installation |
| FileVersion: | 2.0 |
| LegalCopyright: | TECH ANIL |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x000062A8 | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.69003 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 4.48733 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 6.72637 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.93388 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 5.97766 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 5.62687 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
55 | 5.11342 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.81411 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
50
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\Android Fastbooot Reset Tool 2.0.exe" | C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\Android Fastbooot Reset Tool 2.0.exe | — | Android Fastbooot Reset Tool 2.0.exe | |||||||||||
User: admin Company: TECH ANIL Integrity Level: HIGH Exit code: 0 Version: 0. 0. 0. 0 Modules
| |||||||||||||||
| 844 | fastboot devices | C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\fastboot.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\AppData\Local\Temp\Android Fastbooot Reset Tool 2.0.exe" | C:\Users\admin\AppData\Local\Temp\Android Fastbooot Reset Tool 2.0.exe | — | explorer.exe | |||||||||||
User: admin Company: TECH ANIL Integrity Level: MEDIUM Description: Android Fastbooot Reset Tool 2.0 Installation Exit code: 3221226540 Version: 2.0 Modules
| |||||||||||||||
| 1348 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\System32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\Android Fastbooot Reset Tool 2.0.exe" | C:\Users\admin\AppData\Local\Temp\Android Fastbooot Reset Tool 2.0.exe | explorer.exe | ||||||||||||
User: admin Company: TECH ANIL Integrity Level: HIGH Description: Android Fastbooot Reset Tool 2.0 Installation Exit code: 0 Version: 2.0 Modules
| |||||||||||||||
| 2448 | mode con:cols=83 lines=28 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\1283YNOC.bat" "C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\Android Fastbooot Reset Tool 2.0.exe"" | C:\Windows\System32\cmd.exe | — | Android Fastbooot Reset Tool 2.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
382
Read events
381
Write events
1
Delete events
0
Modification events
| (PID) Process: | (1352) Android Fastbooot Reset Tool 2.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 102 | |||
Executable files
7
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Users\admin\AppData\Local\Temp\$inst\7.tmp | image | |
MD5:696641D2325E8B142B6C16D1183ACA43 | SHA256:4A56FFCE0E414F3495F70E9C2960837DF25423B0DBAFD21A073DBDBAA461BC90 | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\AdbWinUsbApi.dll | executable | |
MD5:A770AB787FA7B0AE49E9E280D3198C56 | SHA256:A2CD723104748252691F9F768964EA7181070D1AED6F68344AC49EF6DBAF68F0 | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Users\admin\AppData\Local\Temp\$inst\8.tmp | image | |
MD5:BAC172B887BC7D09DB5E14CE26A4943E | SHA256:AAA3BEE9EBD3640C05B8A70F22C9FBDB8EA0E61CA3762DB5A4583E94D46A5C79 | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Users\admin\AppData\Local\Temp\$inst\4.tmp | image | |
MD5:0D8DBE5CD39F3369265D93195E5C6449 | SHA256:FD17CA05FA0587FBF2D1AB722EBBF4A4B254F2EC0048E9CDAE20655F7DE06A39 | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | compressed | |
MD5:992033E30F40701D5AFC2533E25775EF | SHA256:26E4EB9436383DB01C0BA64416B26811F87E971975AA0564E61E793D6A6A5F1E | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\Uninstall.exe | executable | |
MD5:499CCC8D6D7C08E135A91928CCC2FD7A | SHA256:1FA5D83A5766556CF2FF16AD279E73CB40584746BD388E0A4E818A2CC06613D3 | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\fastboot.exe | executable | |
MD5:747E247B942E4D7AA84A55803368415F | SHA256:4495BAB473DD736BCA5A3EB4CD90157F9590185C2CD17FBB34F823AF8567B64B | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Users\admin\Desktop\Android Fastbooot Reset Tool 2.0.lnk | binary | |
MD5:70D3F9AA6A42A9788DCA0408C75E56B5 | SHA256:EC402E54489F8C8E5424F63AC2297E6641D96F781B0532AE5AC78C9668DD52B2 | |||
| 128 | Android Fastbooot Reset Tool 2.0.exe | C:\Users\admin\AppData\Local\Temp\1283YNOC.bat | text | |
MD5:4294888D83F4C01EB380405D09E9C243 | SHA256:D29F5B96C1673A8A3A37E11A9D1C2774B4570744E7BB4E8EF438D7D94C04C884 | |||
| 1352 | Android Fastbooot Reset Tool 2.0.exe | C:\Program Files\TECH ANIL\Android Fastbooot Reset Tool\Uninstall.ini | text | |
MD5:876C3F5FF64EE67337246D027F87542C | SHA256:A48F60C88078943C7AA756E397369CF26A51882D8693EFDBE722261051028440 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4004 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |