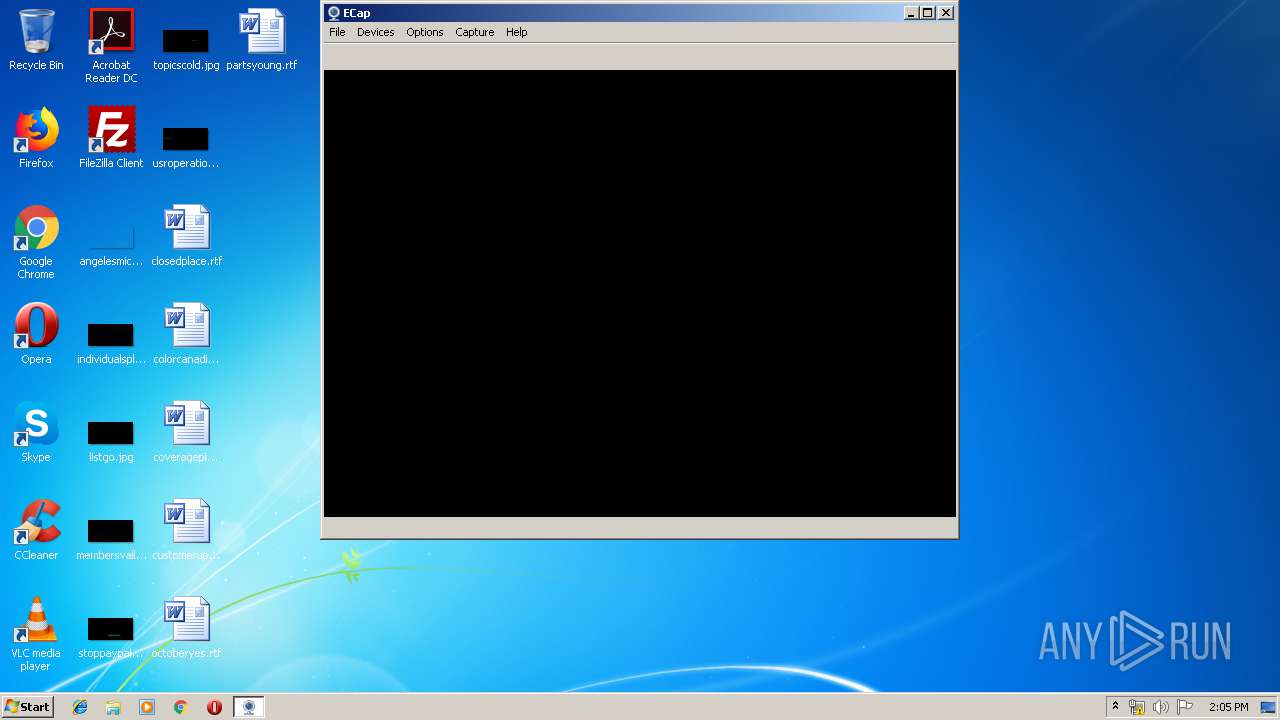
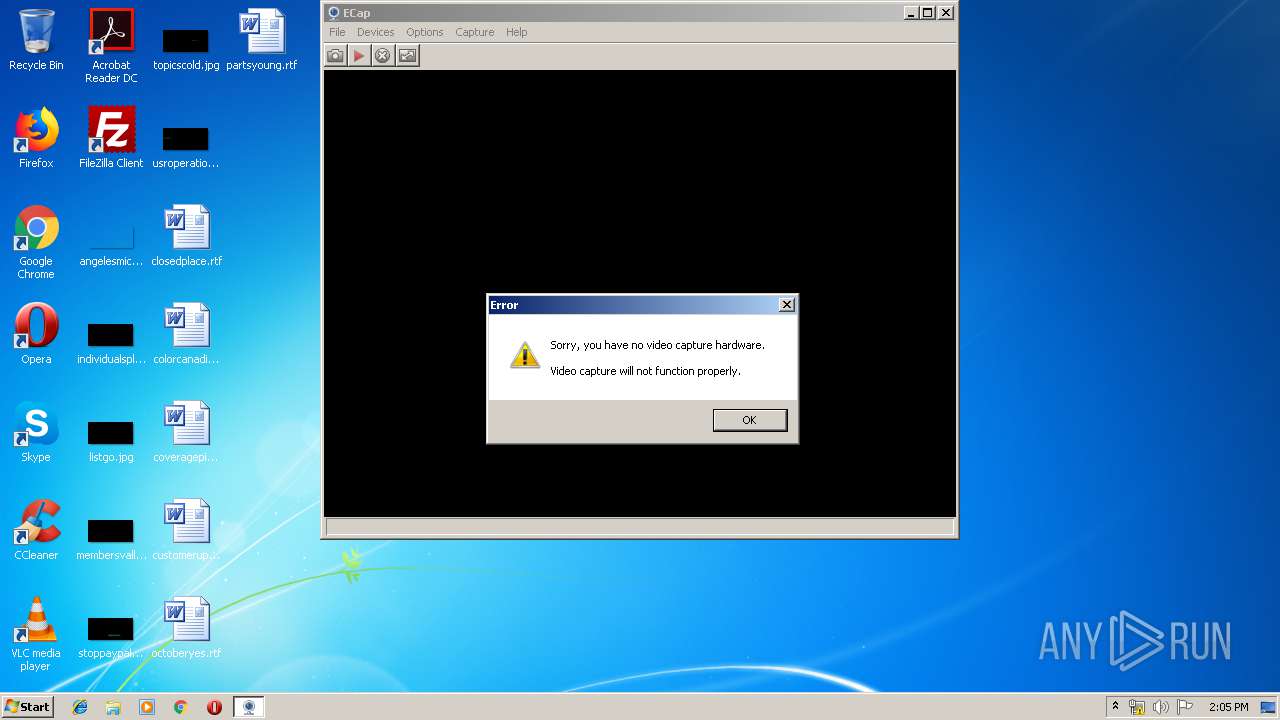
| File name: | ECap (2).exe |
| Full analysis: | https://app.any.run/tasks/c8d9427c-1aa5-4b5b-bc67-73e3c27a8d85 |
| Verdict: | No threats detected |
| Analysis date: | June 27, 2019, 13:05:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 6E58BCF863E57F4D5E31E3C68308720A |
| SHA1: | 55A292C9CE668A48C134DBD9A19A29459060B5A5 |
| SHA256: | D78110158C735F607B7B929D2CCB0137987A4614C6279E12C90EA7C93C36297C |
| SSDEEP: | 6144:in5X2e+8eG04k+pd9UzQhFHSW80UXyGyc:45F10tYbIQhFHTSf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- ECap (2).exe (PID: 3192)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:09:05 06:54:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 172032 |
| InitializedDataSize: | 102400 |
| UninitializedDataSize: | 499712 |
| EntryPoint: | 0xa4450 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.1.4 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x30003f |
| FileFlags: | Pre-release, Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comment: | ECap |
| Comments: | - |
| FileDescription: | Capture Application |
| FileVersion: | 1.014 |
| InternalName: | ECap.exe |
| LegalTrademarks: | - |
| OLESelfRegister: | AM20 |
| OriginalFileName: | ECap.exe |
| ProductName: | ECap |
| ProductVersion: | 1.014 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Sep-2002 04:54:49 |
| Detected languages: |
|
| Comment: | ECap |
| Comments: | - |
| FileDescription: | Capture Application |
| FileVersion: | 1.014 |
| InternalName: | ECap.exe |
| LegalTrademarks: | - |
| OLESelfRegister: | AM20 |
| OriginalFilename: | ECap.exe |
| ProductName: | ECap |
| ProductVersion: | 1.014 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Sep-2002 04:54:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0007A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0007B000 | 0x0002A000 | 0x00029800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93358 |
.rsrc | 0x000A5000 | 0x00020000 | 0x0001FC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.32111 |
gwzsqpv | 0x000C5000 | 0x00001000 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86333 | 643 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.67175 | 1018 | UNKNOWN | English - United States | RT_STRING |
3 | 7.65955 | 858 | UNKNOWN | English - United States | RT_STRING |
4 | 7.41537 | 434 | UNKNOWN | English - United States | RT_STRING |
5 | 5.27761 | 44 | UNKNOWN | English - United States | RT_STRING |
6 | 0 | 306 | UNKNOWN | English - United States | RT_DIALOG |
7 | 7.41313 | 448 | UNKNOWN | Chinese - Taiwan | RT_STRING |
8 | 7.45702 | 436 | UNKNOWN | Chinese - Taiwan | RT_STRING |
9 | 7.48862 | 482 | UNKNOWN | Chinese - Taiwan | RT_STRING |
10 | 6.66827 | 174 | UNKNOWN | Chinese - Taiwan | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSACM32.dll |
OLEAUT32.dll |
OLEPRO32.DLL |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3192 | "C:\Users\admin\AppData\Local\Temp\ECap (2).exe" | C:\Users\admin\AppData\Local\Temp\ECap (2).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Capture Application Exit code: 0 Version: 1.014 Modules
| |||||||||||||||
Total events
29
Read events
20
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | FriendlyName |
Value: Microphone (Realtek AC'97 Audio | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | CLSID |
Value: {E30629D2-27E5-11CE-875D-00608CB78066} | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | FilterData |
Value: 02000000000020000000000000000000 | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | WaveInId |
Value: 0 | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | ClassManagerFlags |
Value: 2 | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Line In (Realtek AC'97 Audio) |
| Operation: | write | Name: | FriendlyName |
Value: Line In (Realtek AC'97 Audio) | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Line In (Realtek AC'97 Audio) |
| Operation: | write | Name: | CLSID |
Value: {E30629D2-27E5-11CE-875D-00608CB78066} | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Line In (Realtek AC'97 Audio) |
| Operation: | write | Name: | FilterData |
Value: 02000000000020000000000000000000 | |||
| (PID) Process: | (3192) ECap (2).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Line In (Realtek AC'97 Audio) |
| Operation: | write | Name: | WaveInId |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | ECap (2).exe | C:\ProgramData\Temp\GenePccMon.ini | text | |
MD5:E5D6E8557F3004E9AB2AFD26075FF775 | SHA256:80843DA68C4AF134658372D1A156CD155603EC4EE281DC074EBFB1CFECCB588F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
ECap (2).exe |
Ini Path=[ |
ECap (2).exe | C:\ProgramData\Temp\ECap (2).ini |
ECap (2).exe | ]
|