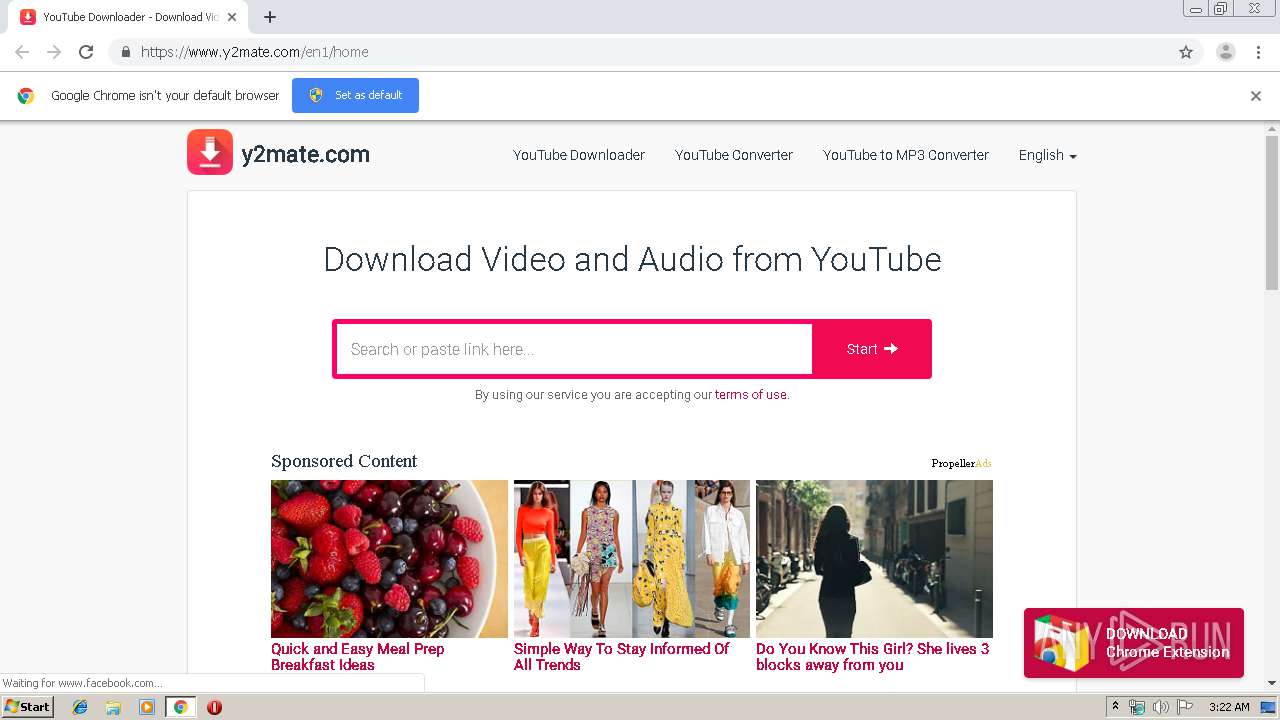
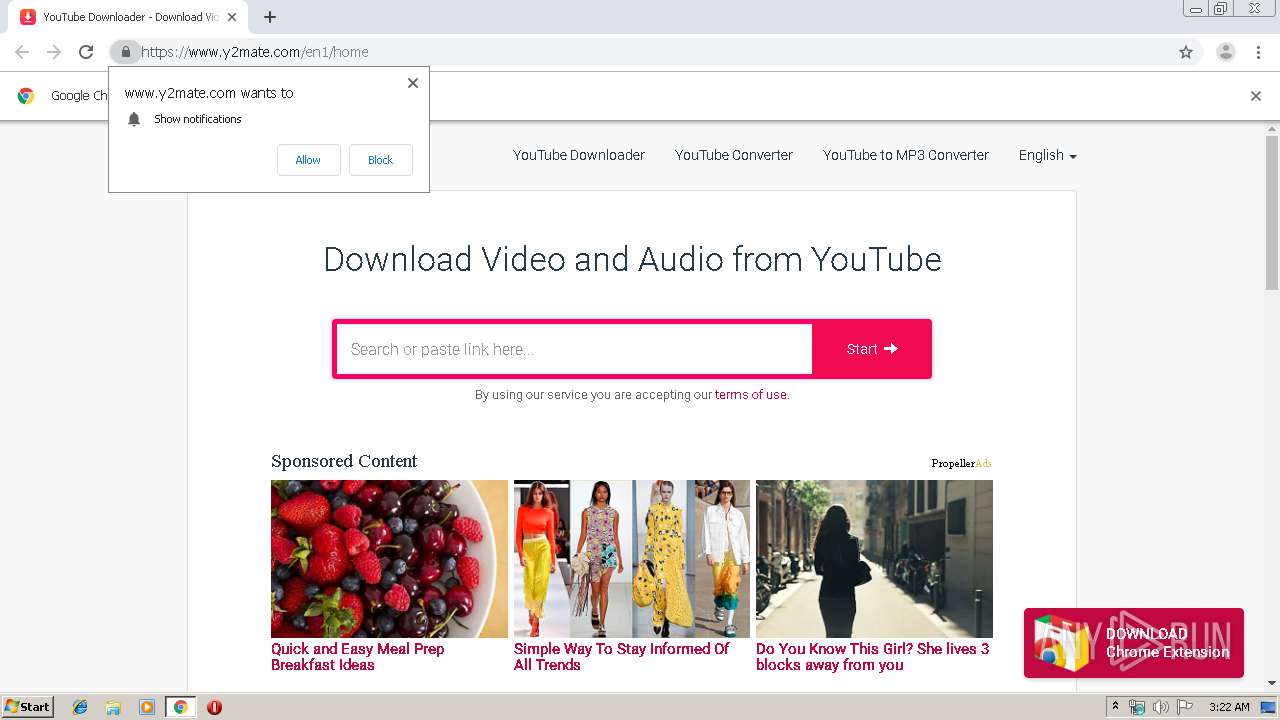
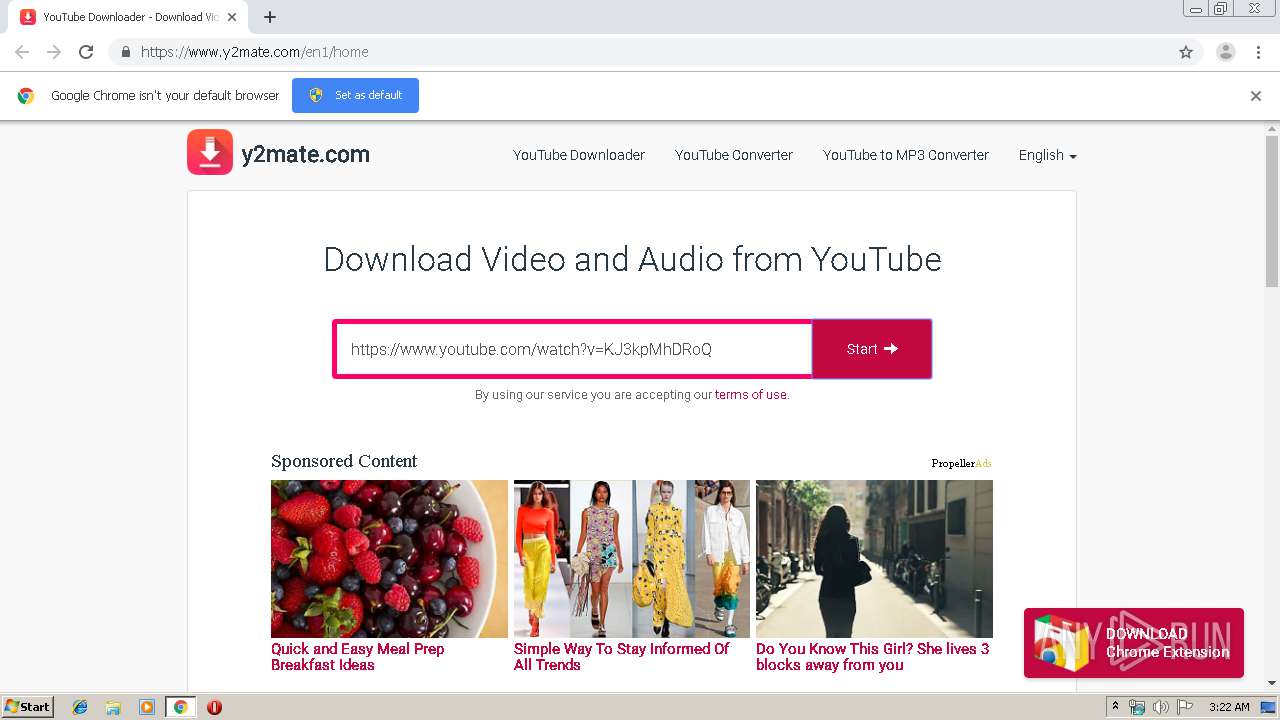
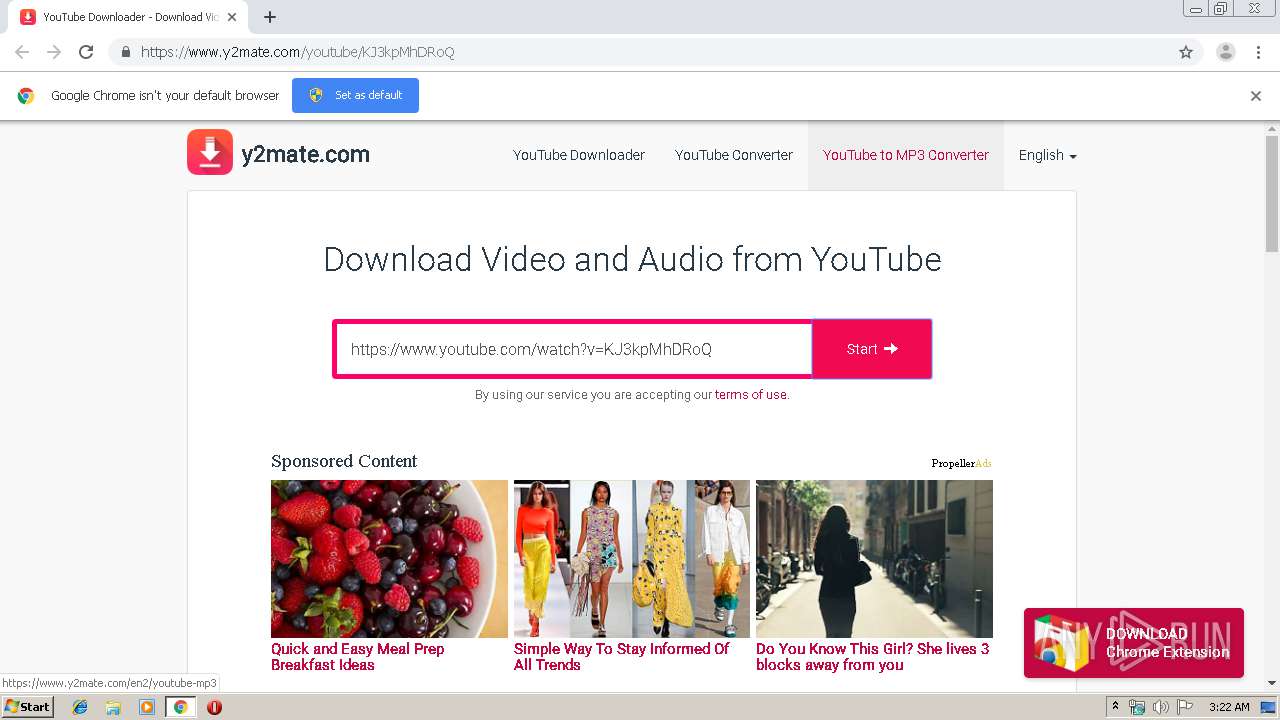
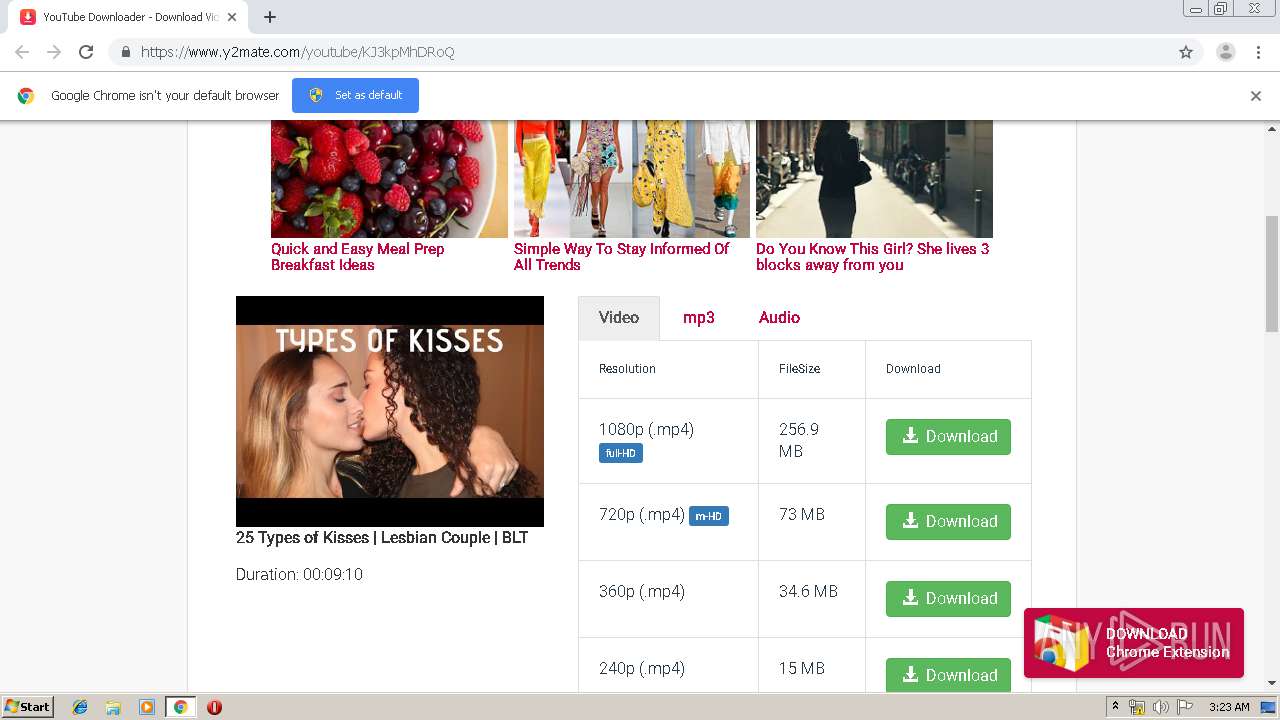
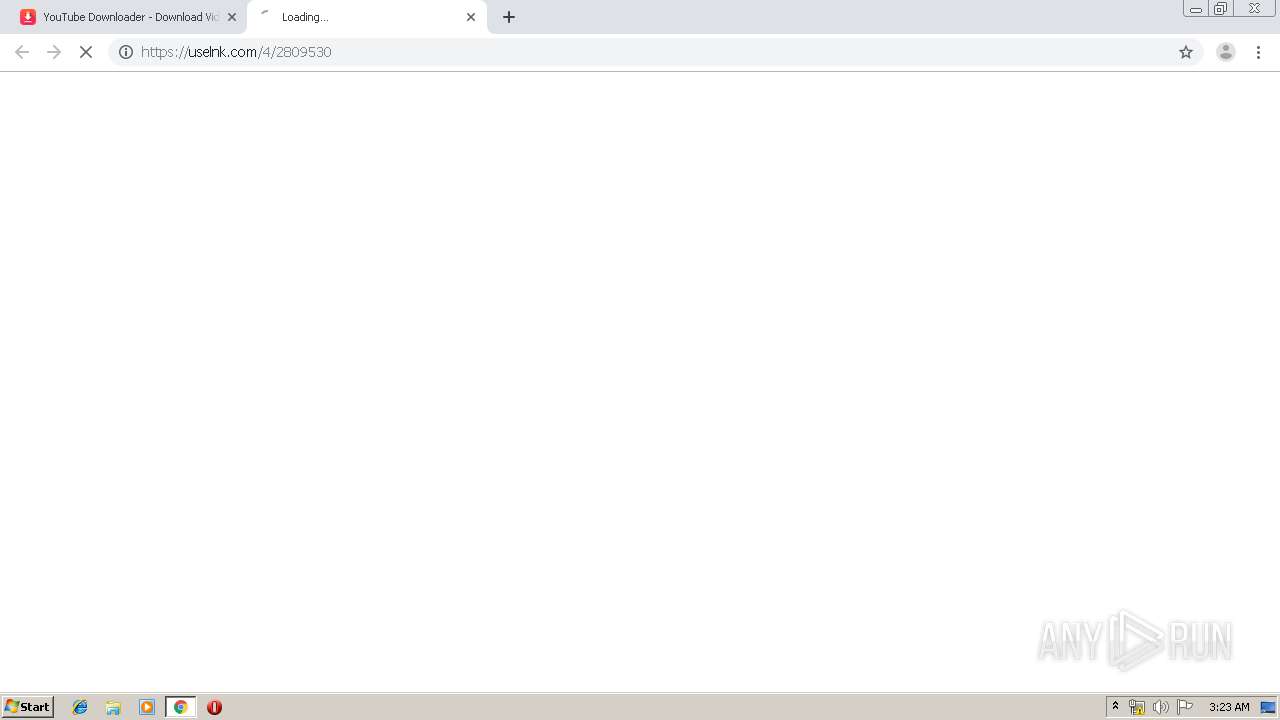
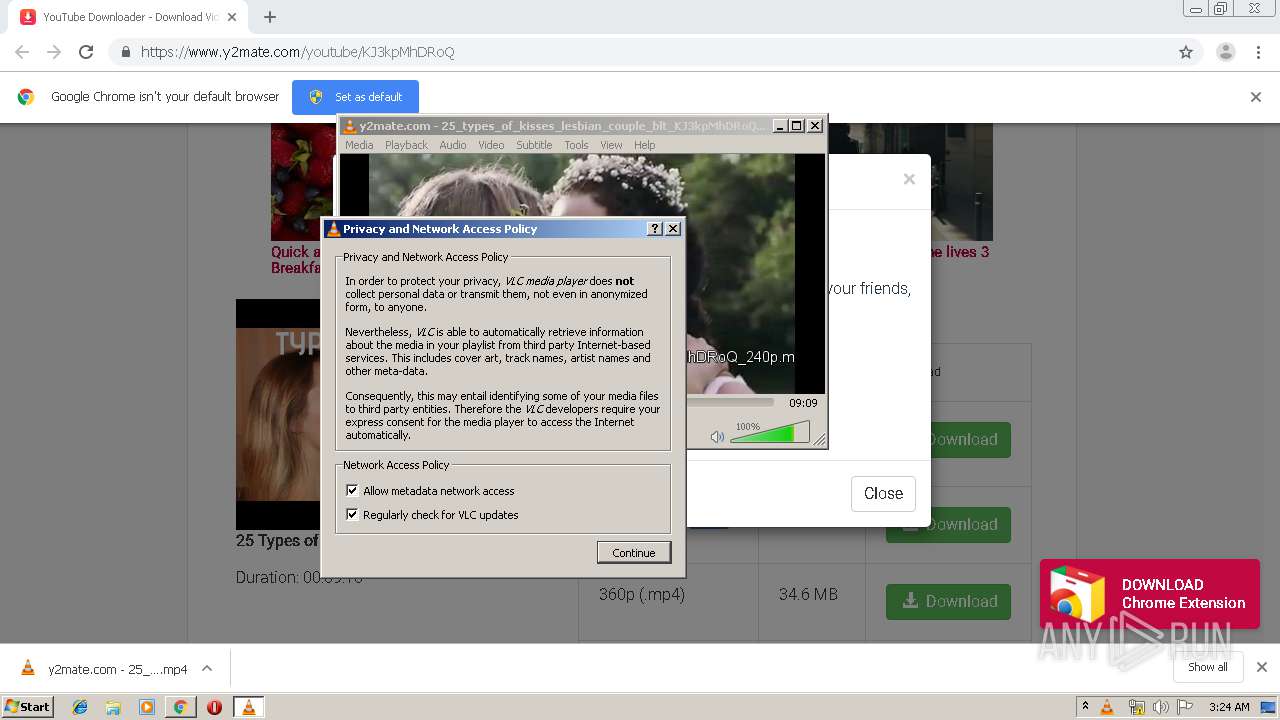
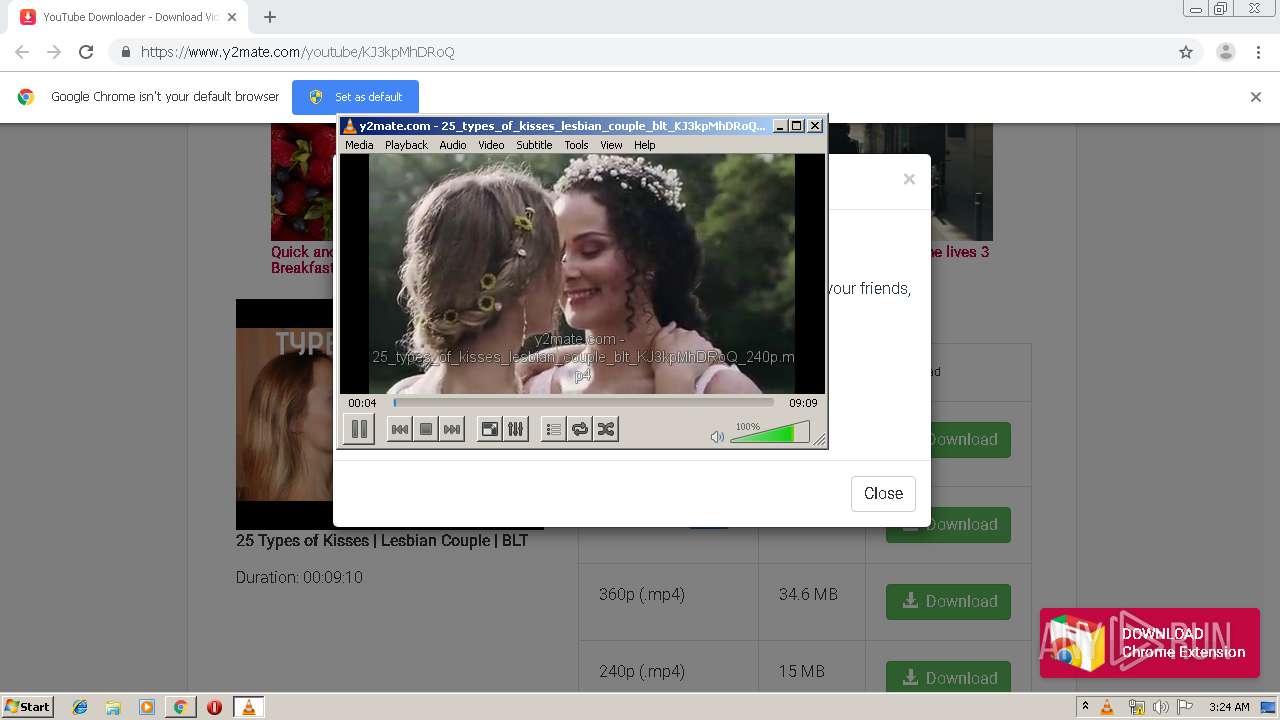
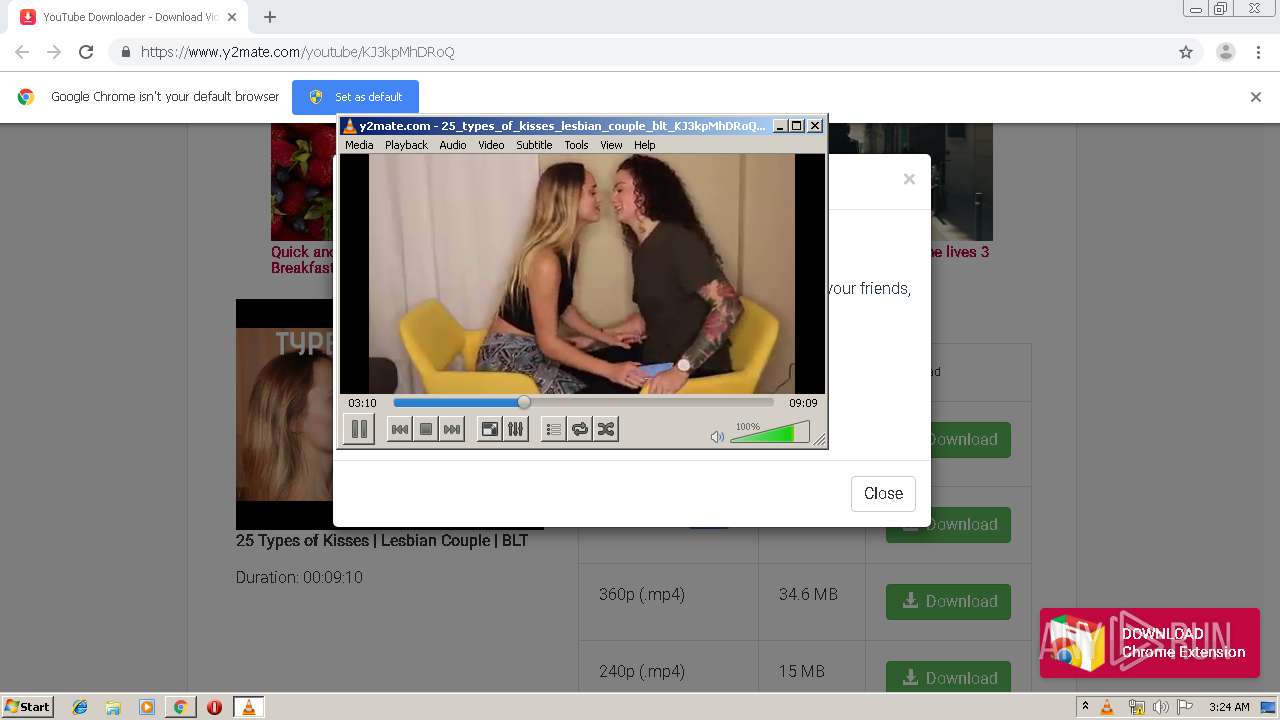
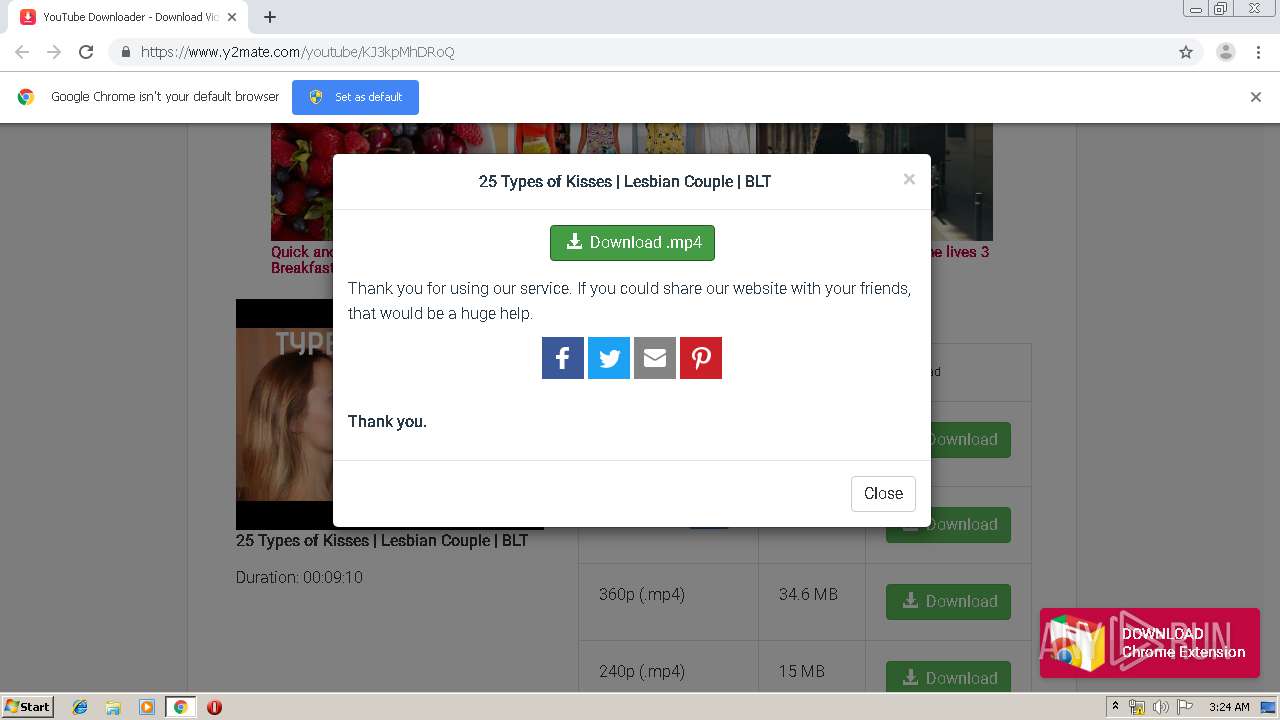
| URL: | https://www.y2mate.com/ |
| Full analysis: | https://app.any.run/tasks/05cc1f95-662f-49cb-9c0b-8f42d92b519a |
| Verdict: | No threats detected |
| Analysis date: | November 26, 2019, 03:22:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D508AB244123F564D8155092C21D6748 |
| SHA1: | AA6B63478F69C88E54656325E1592857B574C26A |
| SHA256: | D77D26C84248E5FC912DA7EF5E56E60895F9F2AAEDCD4DAC44A4EE50FA5C36FA |
| SSDEEP: | 3:N8DSLMW:2OLP |
MALICIOUS
No malicious indicators.SUSPICIOUS
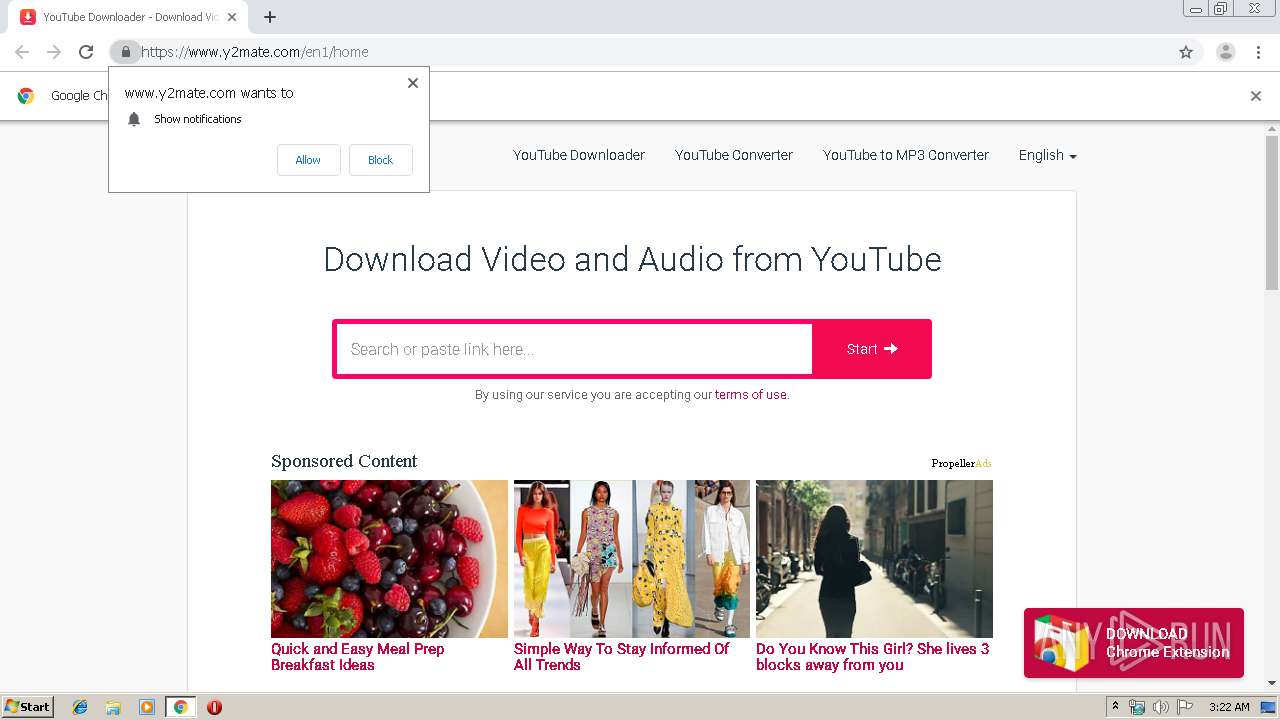
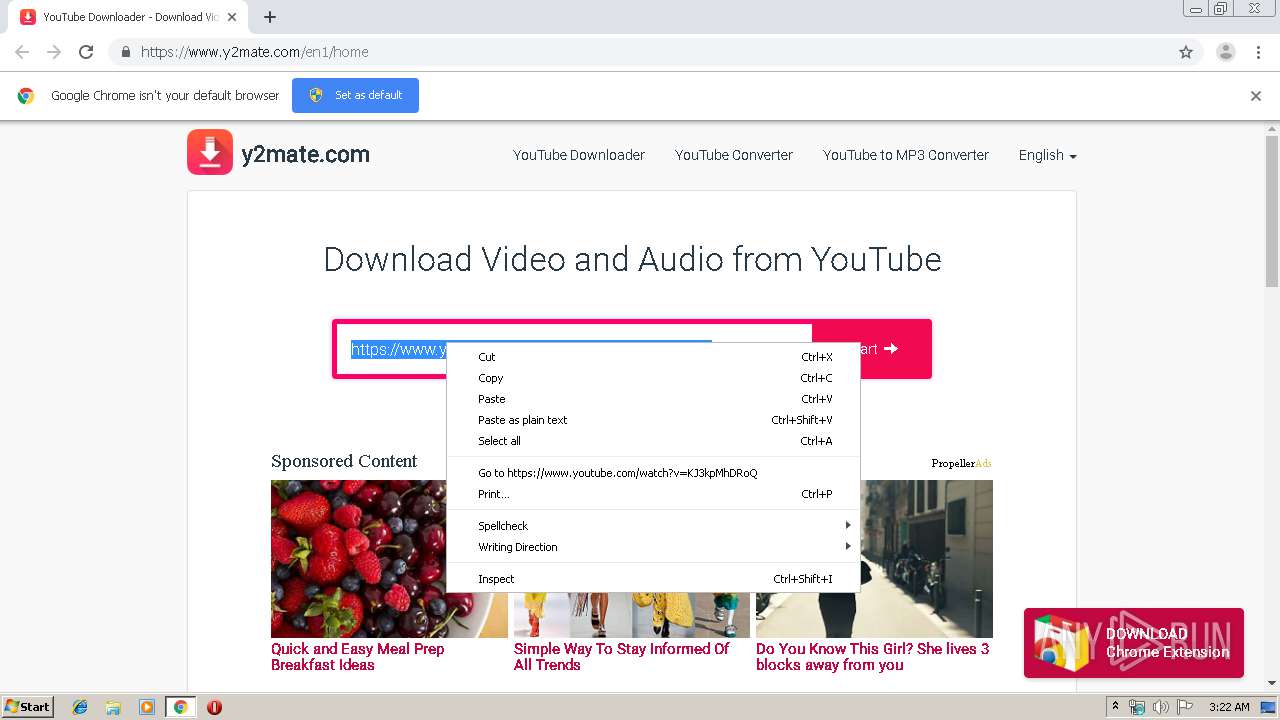
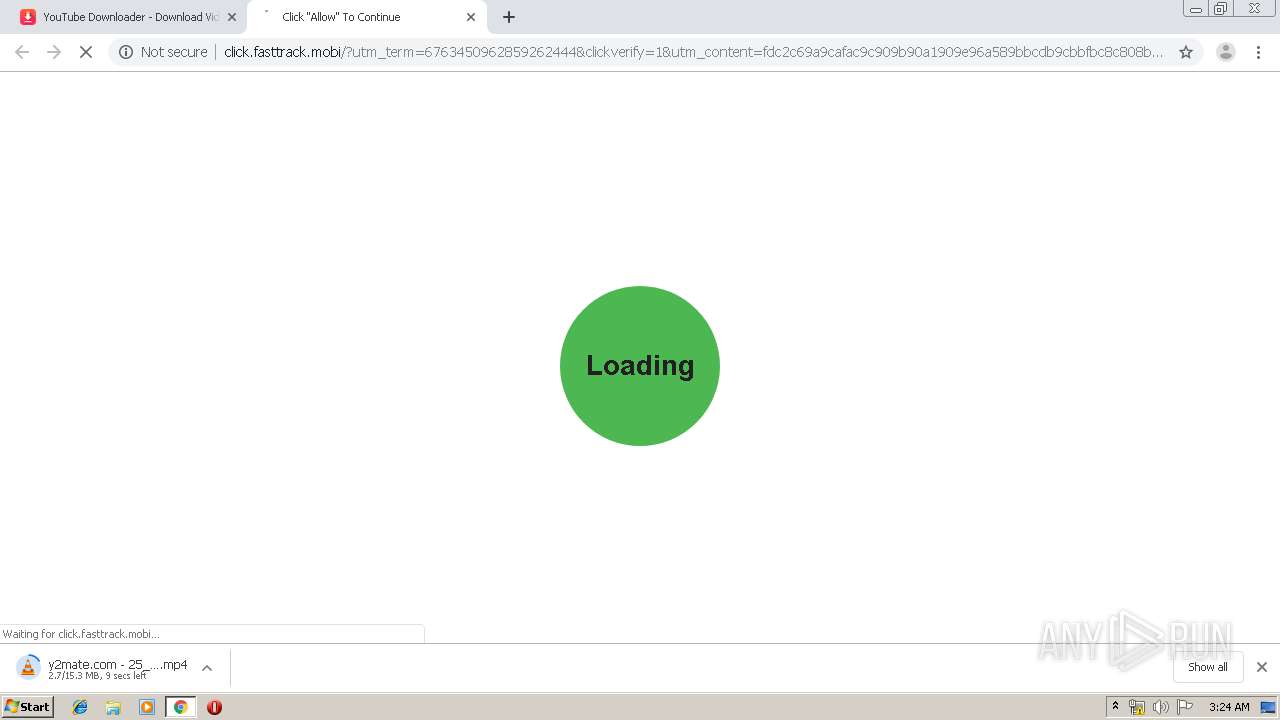
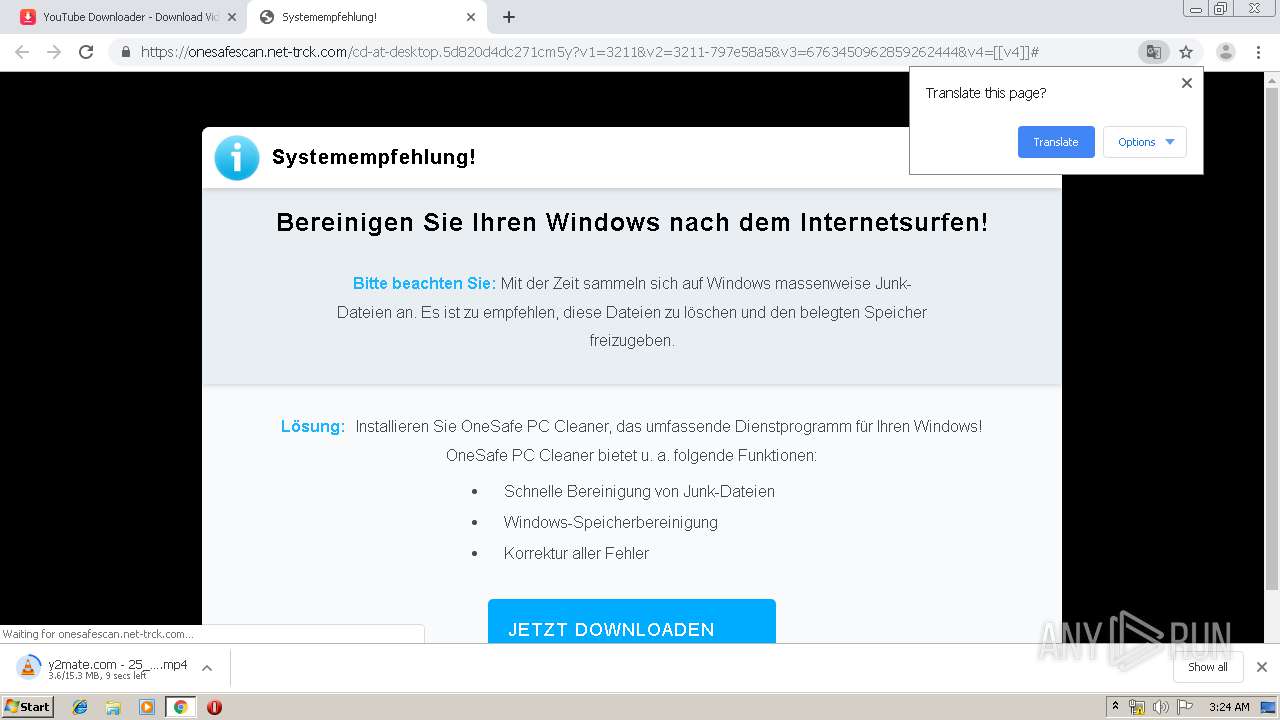
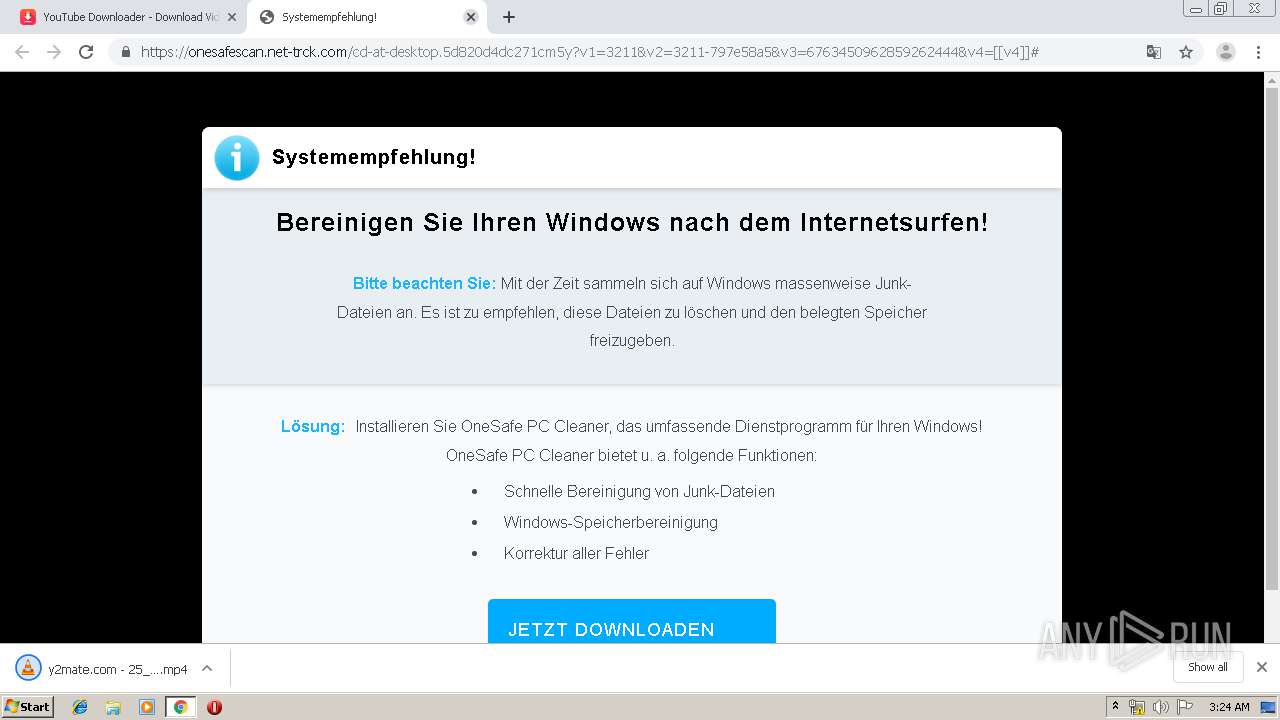
Modifies files in Chrome extension folder
- chrome.exe (PID: 1524)
Creates files in the user directory
- vlc.exe (PID: 3428)
INFO
Reads the hosts file
- chrome.exe (PID: 1524)
- chrome.exe (PID: 3900)
Application launched itself
- chrome.exe (PID: 1524)
Reads Internet Cache Settings
- chrome.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5757731747209472717 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7168422047115605131 --mojo-platform-channel-handle=3980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4993240592105741469 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14280915974088957968 --mojo-platform-channel-handle=4016 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.y2mate.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3912380471050523170 --mojo-platform-channel-handle=4188 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1712 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10161064504047735999 --mojo-platform-channel-handle=4428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1740227724635361268 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11970269098717372898,14581026622855114933,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1650462241747536591 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 335
Read events
1 220
Write events
110
Delete events
5
Modification events
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1524-13219212139483000 |
Value: 259 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
Executable files
0
Suspicious files
98
Text files
278
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d77e1c97-c36c-4bf1-b9c9-840c2376a3fd.tmp | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39ab00.TMP | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39aad1.TMP | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39aa92.TMP | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
71
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3900 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 529 b | whitelisted |
3900 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 534 b | whitelisted |
3900 | chrome.exe | GET | 200 | 88.99.167.139:80 | http://dl102.y2mate.com/?file=M3R4SUNiN3JsOHJ6WWQ2a3NQS1Y5ZGlxVlZIOCtyaDJ6ZW91M2dBbUVwUkRvTElrM3Zlekp0cHdJcUljejRPakgrRlgraXZJZmRXME1nT2RpYk1NRVhpUjJ0NFppekQrek54MENkay9Xd2FzM2VDcW1qUkptUWJoZG9XSVI1NVBZbUp2dGtKbWxuUzF3ZUdBL0VmZTV6ai9nVlRSWVNVZXQzVUlNdmlidk5RYWdGYmZkdWZod0s4S3F4bVU2NGxhMytPaXVBVGx3YnMvdHVOMlVWRmtmNVZpMjViaDROdm05a3dKclpFNDZFS1ZsckR5Vm81N0ViWEtQelI4TnljSC9jYmZBVXBHbW10UG9EL3dwLzl5b0RKYkp1Wnc4SEs5Ni9mOWJ6S2RJNU9qR01YVGZycnY5WmM9 | DE | m4v | 15.2 Mb | unknown |
3900 | chrome.exe | GET | 200 | 198.143.165.222:80 | http://click.fasttrack.mobi/?utm_term=6763450962859262444&clickverify=1&utm_content=fdc2c69a9cafac9c909b90a1909e96a589bbcdb9cbbfbc8c808b80b1838f83b5ba8bbabd8e8fbd8d8283ece0e8e3f7e6fbebfdb4eeedf5f0f3e1e991a797d3fa858c848ccea6828ecce3d2d5e6d5d0e5fafb8c8b8b9afcfdc3f3c1c3cec7f4c2f8fbc8c9ceda | US | html | 2.39 Kb | suspicious |
3900 | chrome.exe | GET | 302 | 198.143.165.222:80 | http://click.fasttrack.mobi/proc.php?523b1504787fb05eb84edcf96f783f629a5d0420 | US | compressed | 2.39 Kb | suspicious |
3900 | chrome.exe | GET | 200 | 198.143.165.222:80 | http://click.fasttrack.mobi/?utm_medium=472188563ab9676486bef3c504098037241dda55&utm_campaign=TB&1=87&cid=4cb2cci3zsck2vr94e | US | html | 1.25 Kb | suspicious |
3900 | chrome.exe | GET | 200 | 185.180.12.140:80 | http://r1---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1574738483&mv=m&mvi=0&pl=24&shardbypass=yes | AT | crx | 862 Kb | whitelisted |
3900 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
3900 | chrome.exe | GET | 200 | 185.180.12.141:80 | http://r2---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1574738483&mv=m&mvi=1&pl=24&shardbypass=yes | AT | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3900 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 104.23.132.73:443 | www.y2mate.com | Cloudflare Inc | US | shared |
3900 | chrome.exe | 104.17.65.4:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
3900 | chrome.exe | 216.58.207.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 23.210.248.44:443 | m.addthis.com | Akamai International B.V. | NL | whitelisted |
3900 | chrome.exe | 172.217.23.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3900 | chrome.exe | 172.217.21.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 172.217.16.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.y2mate.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
content-cdn.y2mate.com |
| unknown |
ajax.cloudflare.com |
| whitelisted |
www.google.com |
| malicious |
getbootstrap.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
m.addthis.com |
| shared |
fonts.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
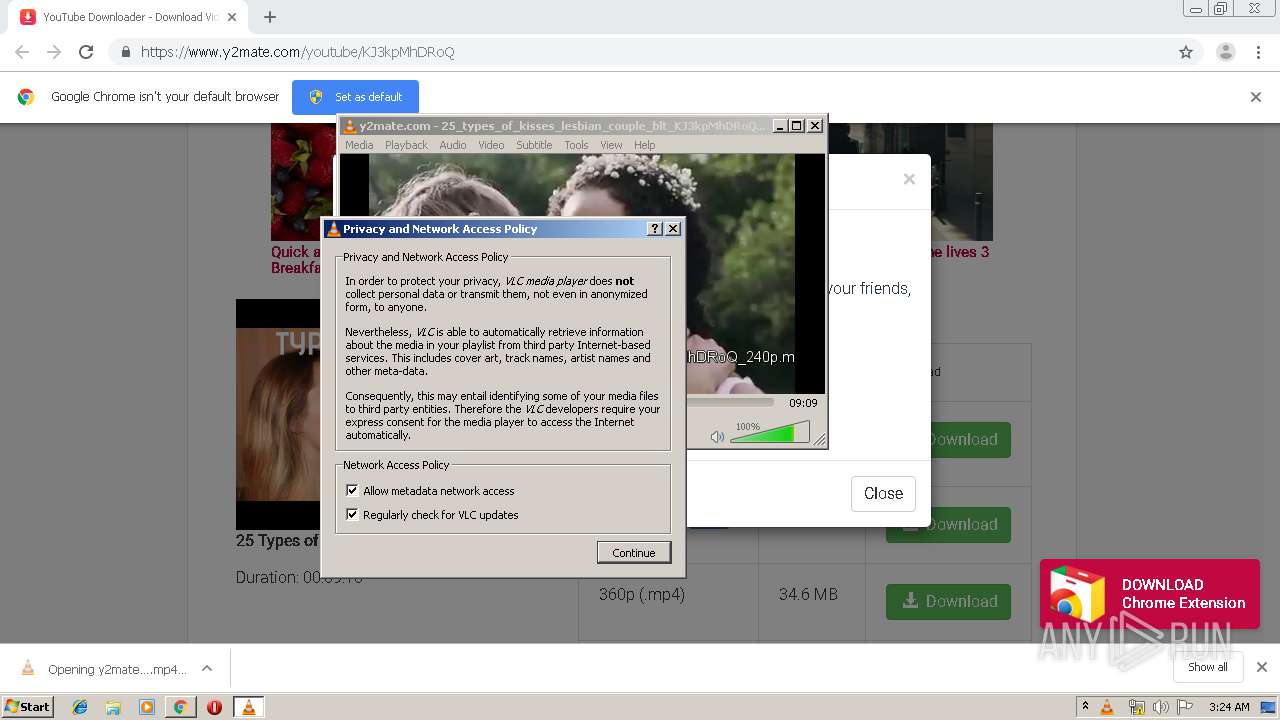
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | direct3d vout display error: Could not read adapter capabilities. (hr=0x8876086A)
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|
vlc.exe | freetype spu text error: Breaking unbreakable line
|