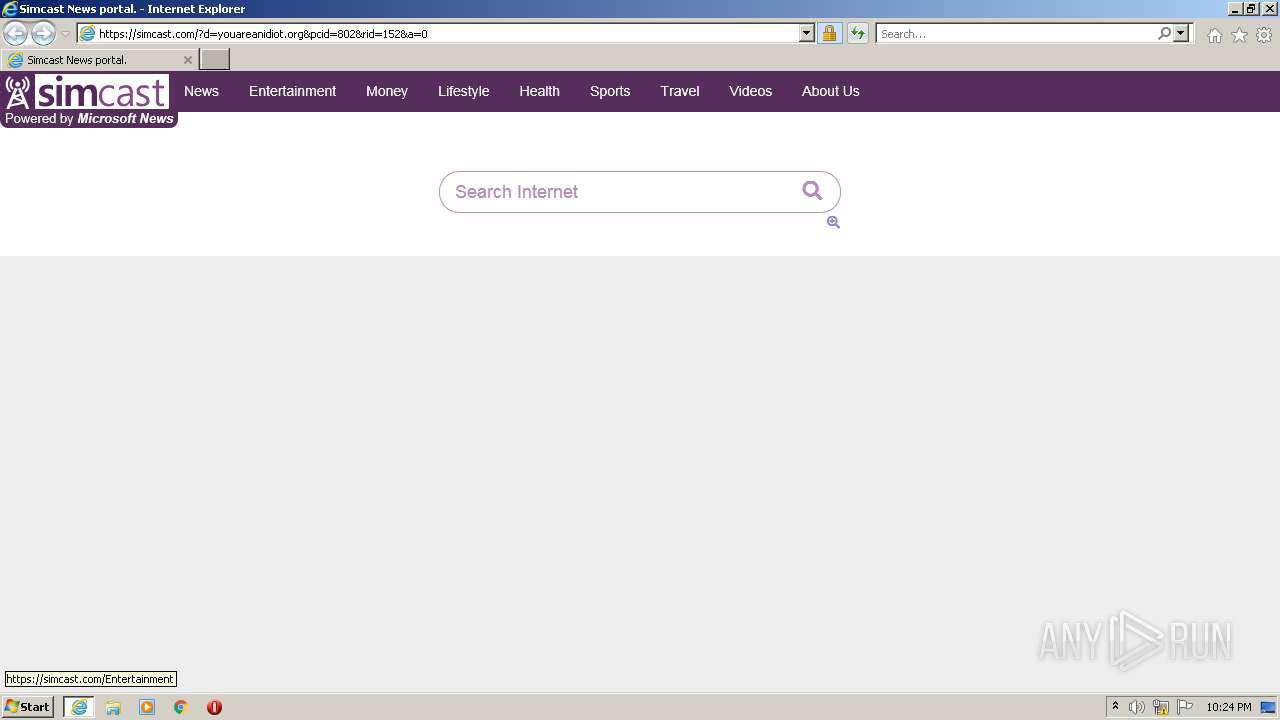
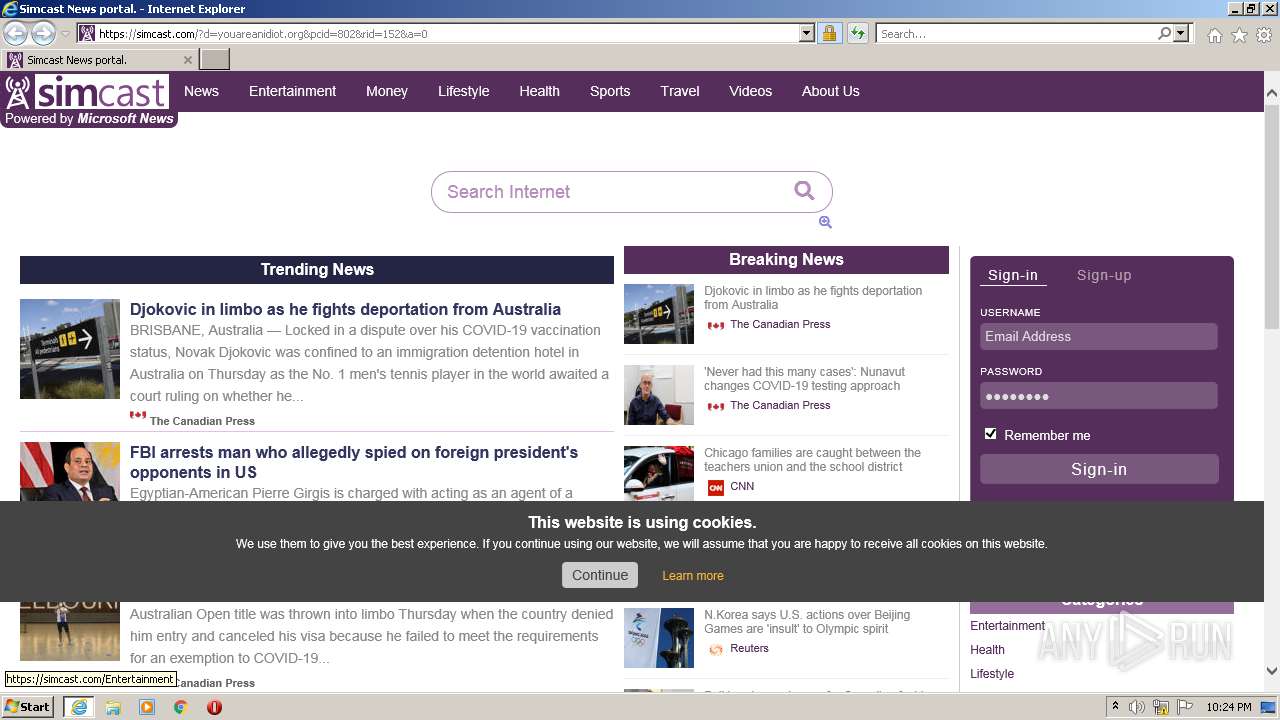
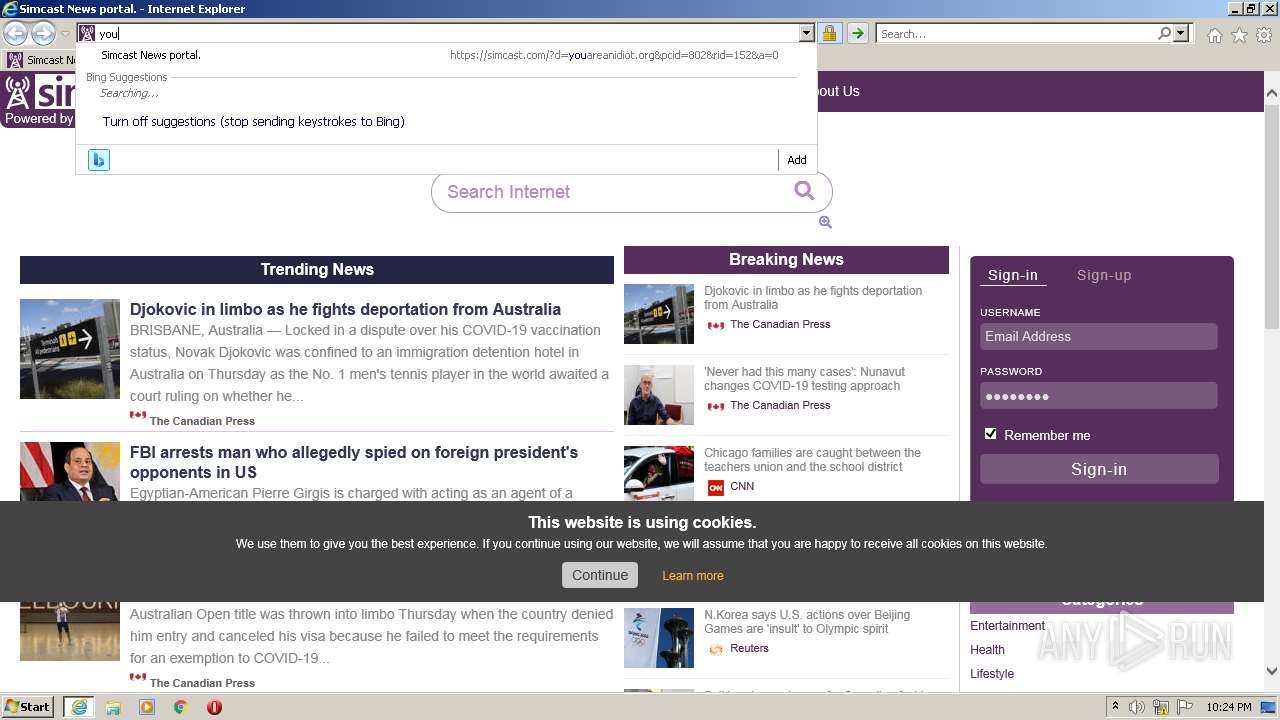
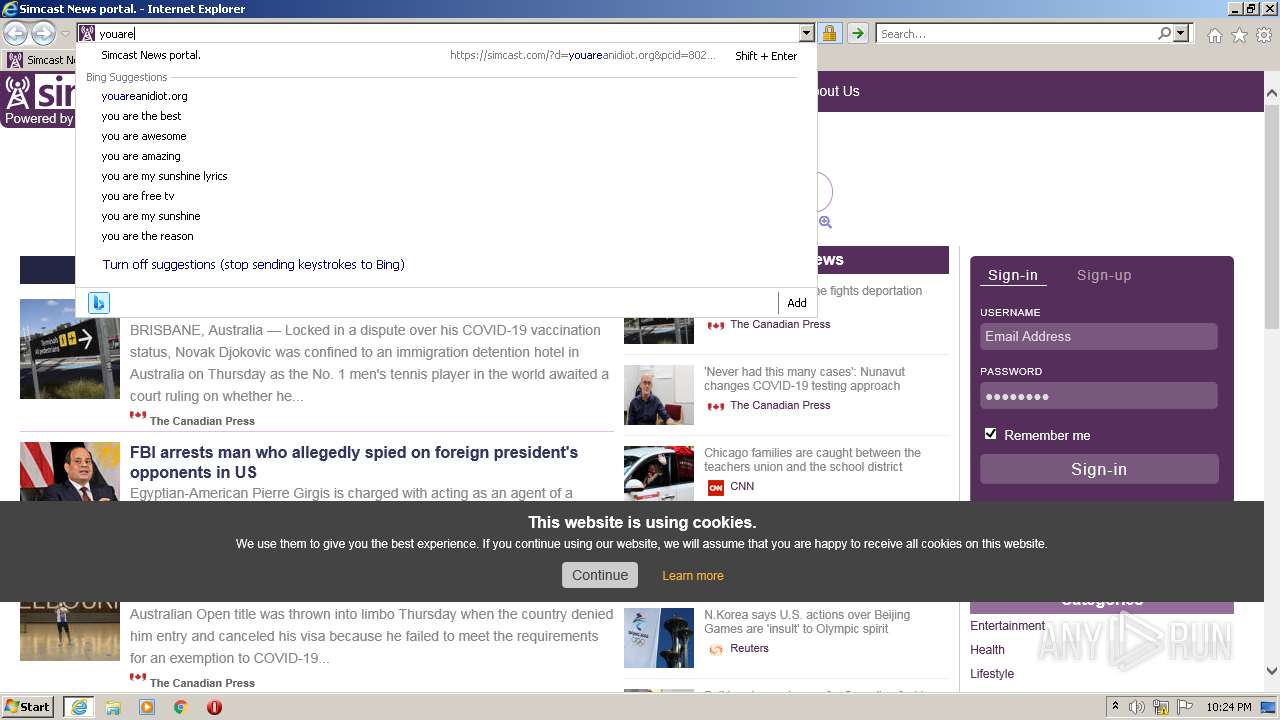
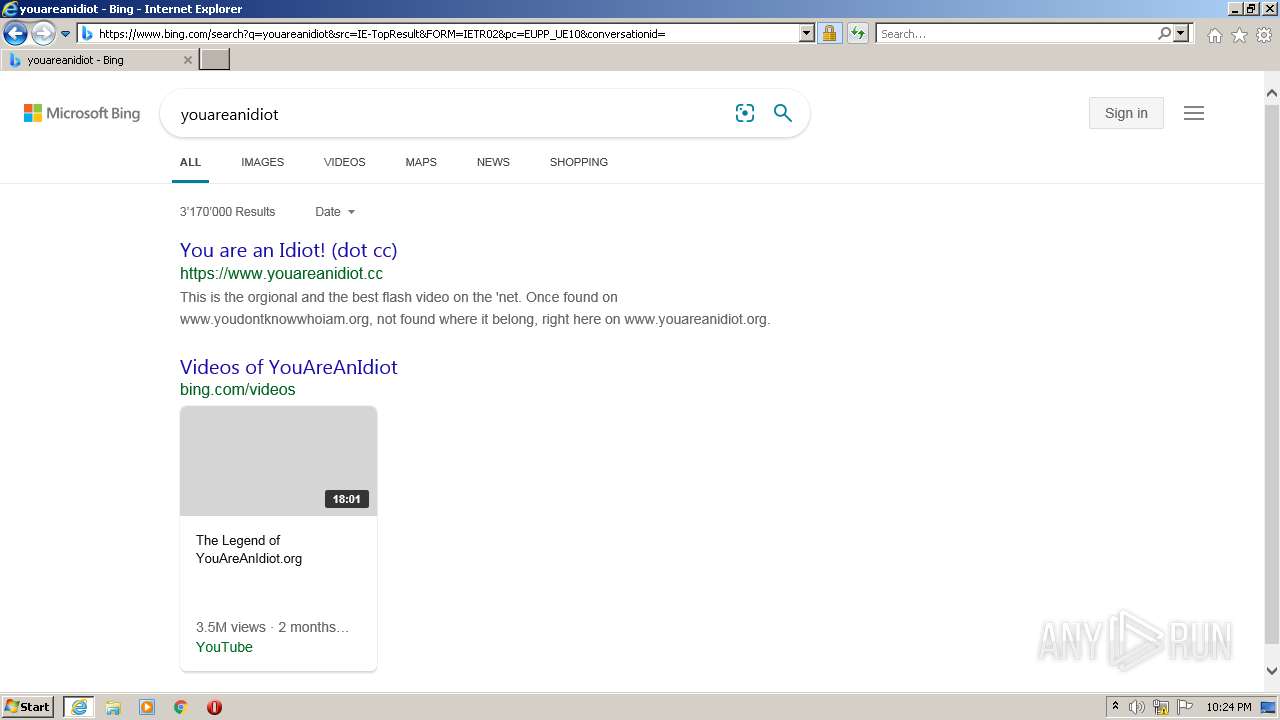
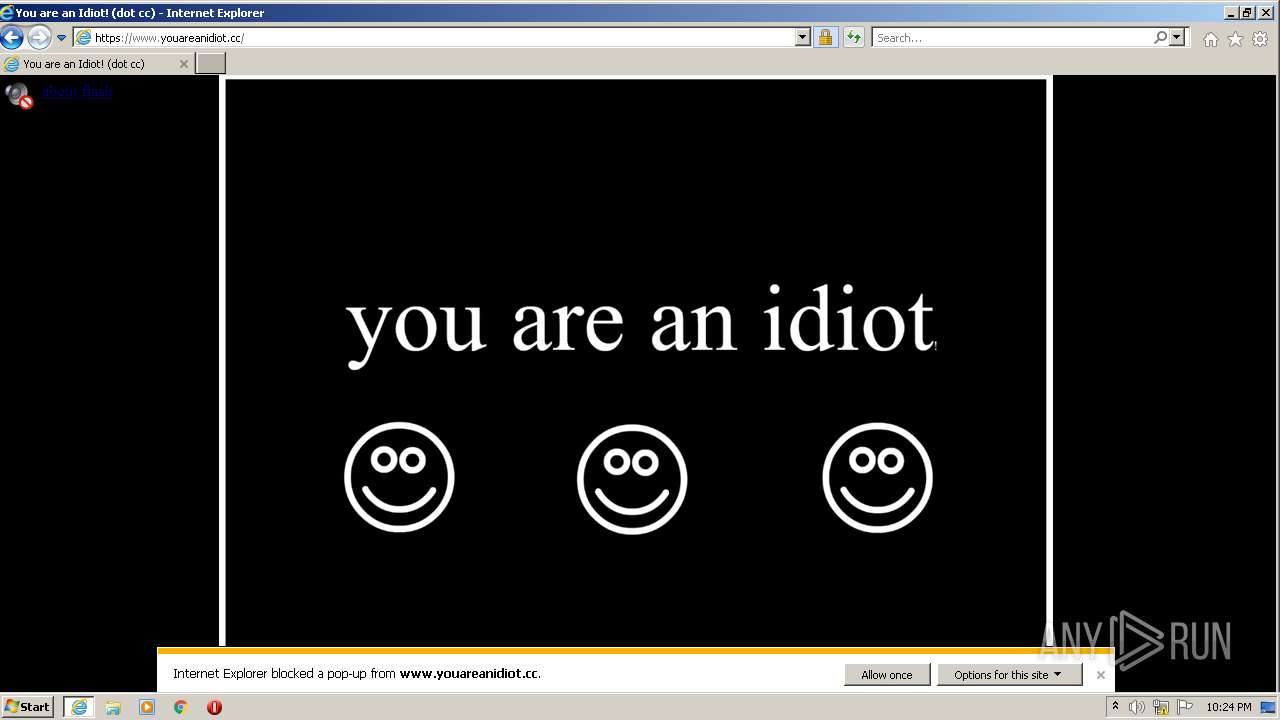
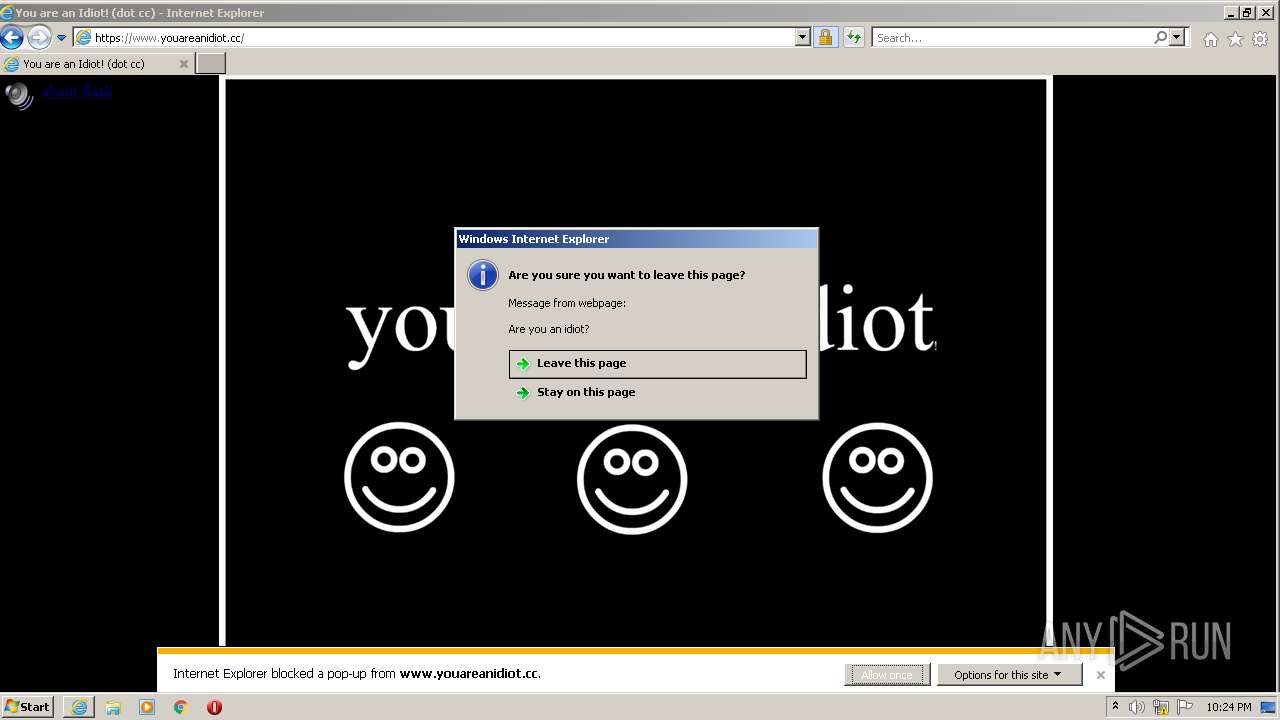
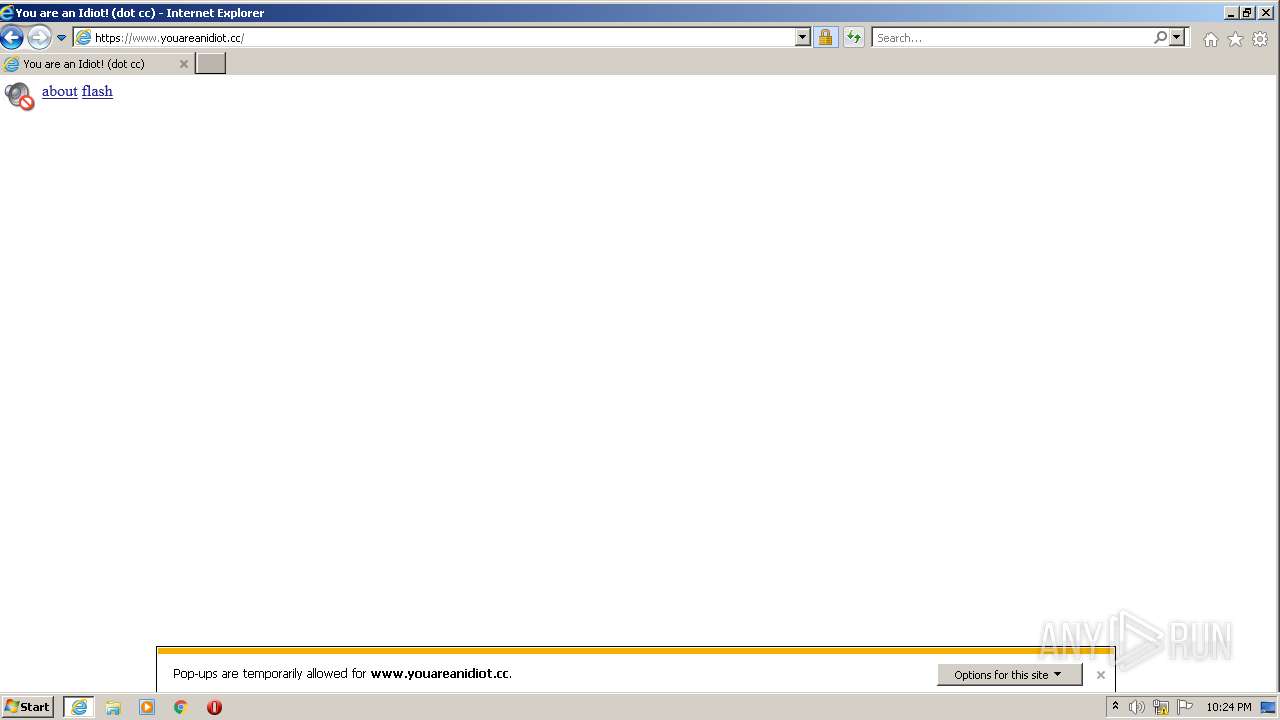
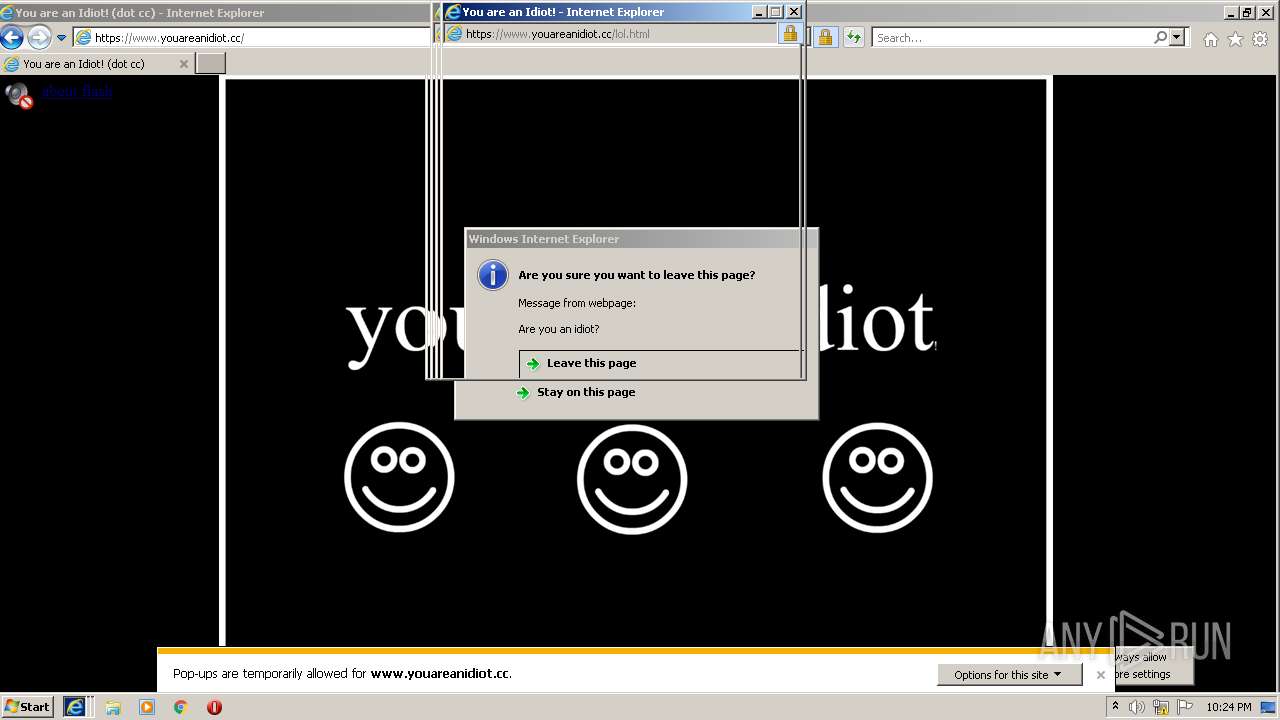
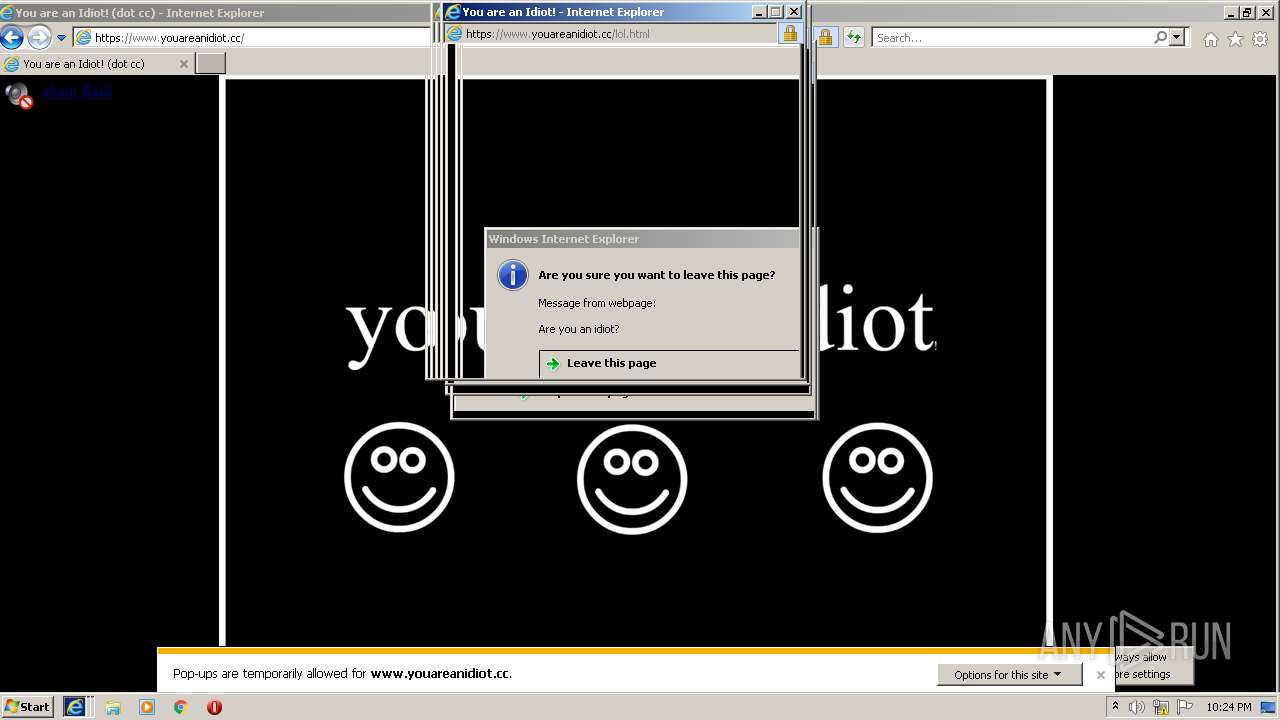
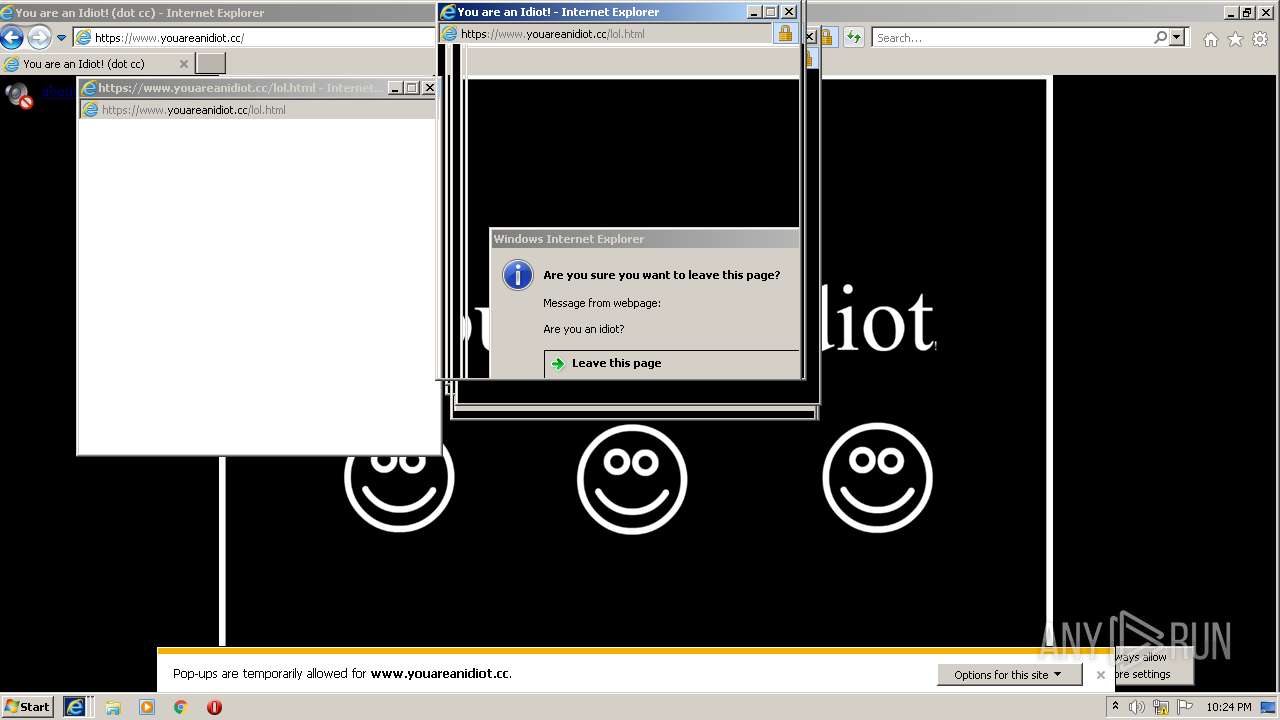
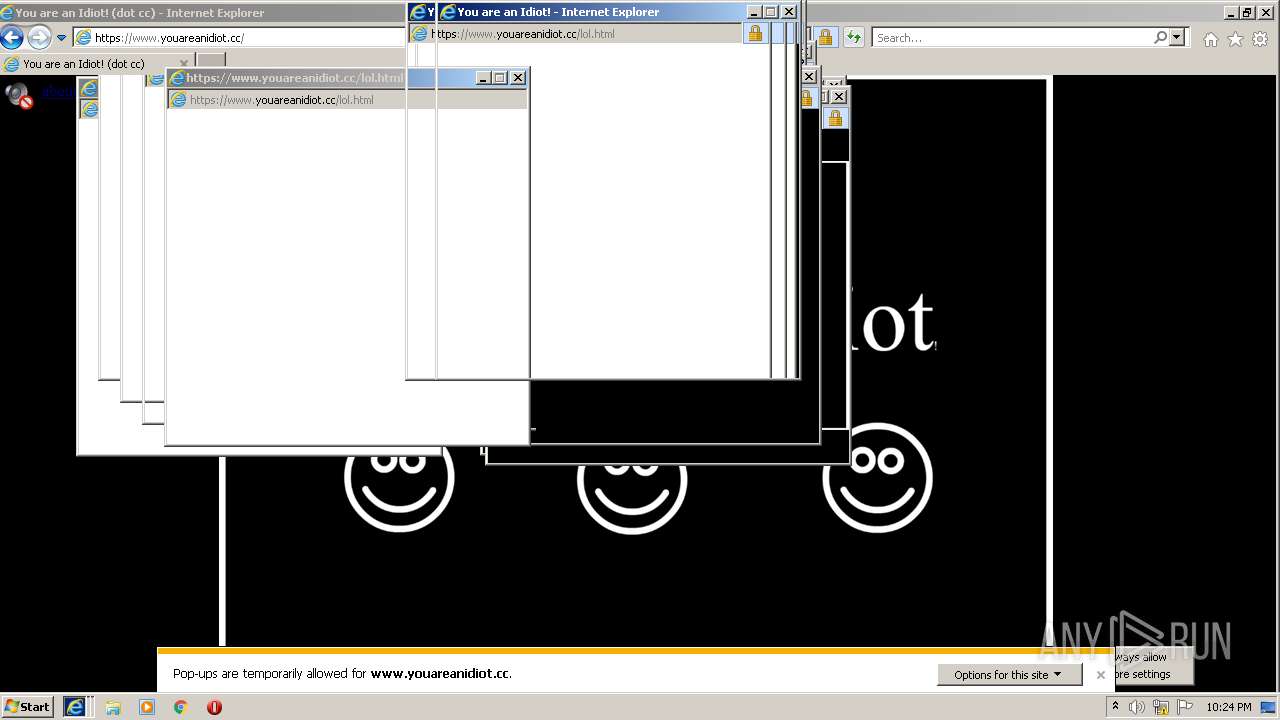
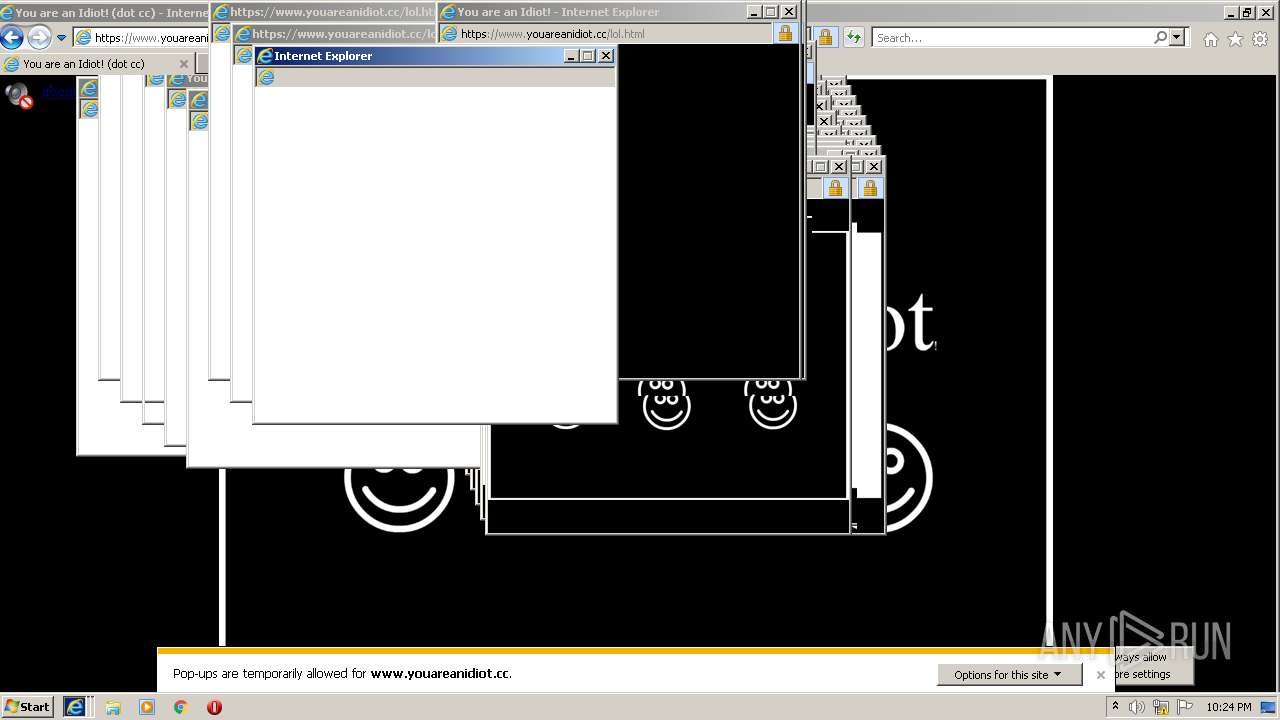
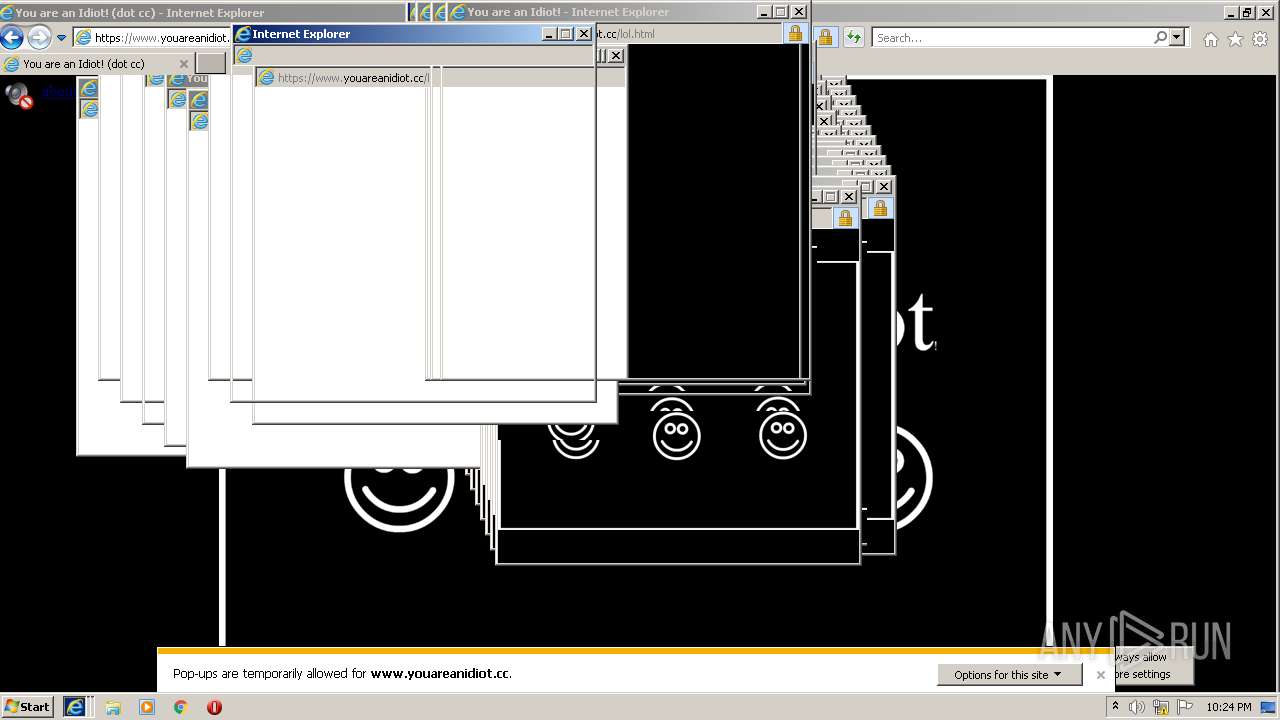
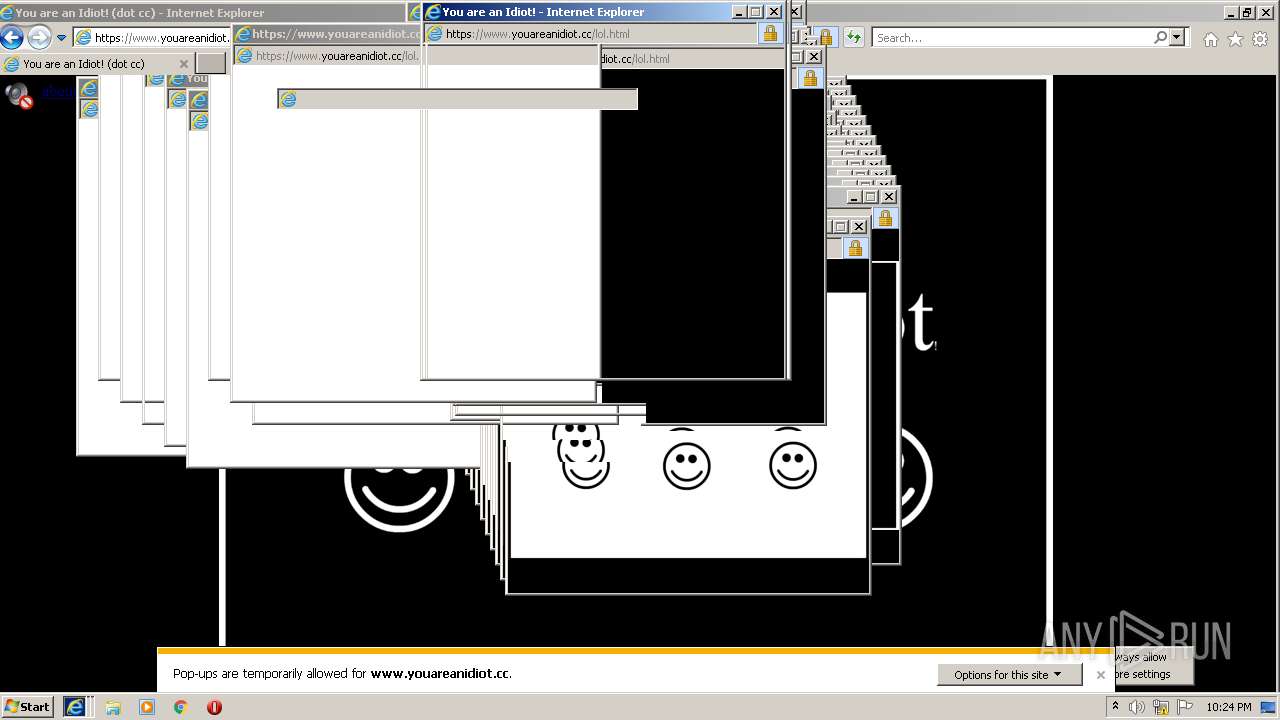
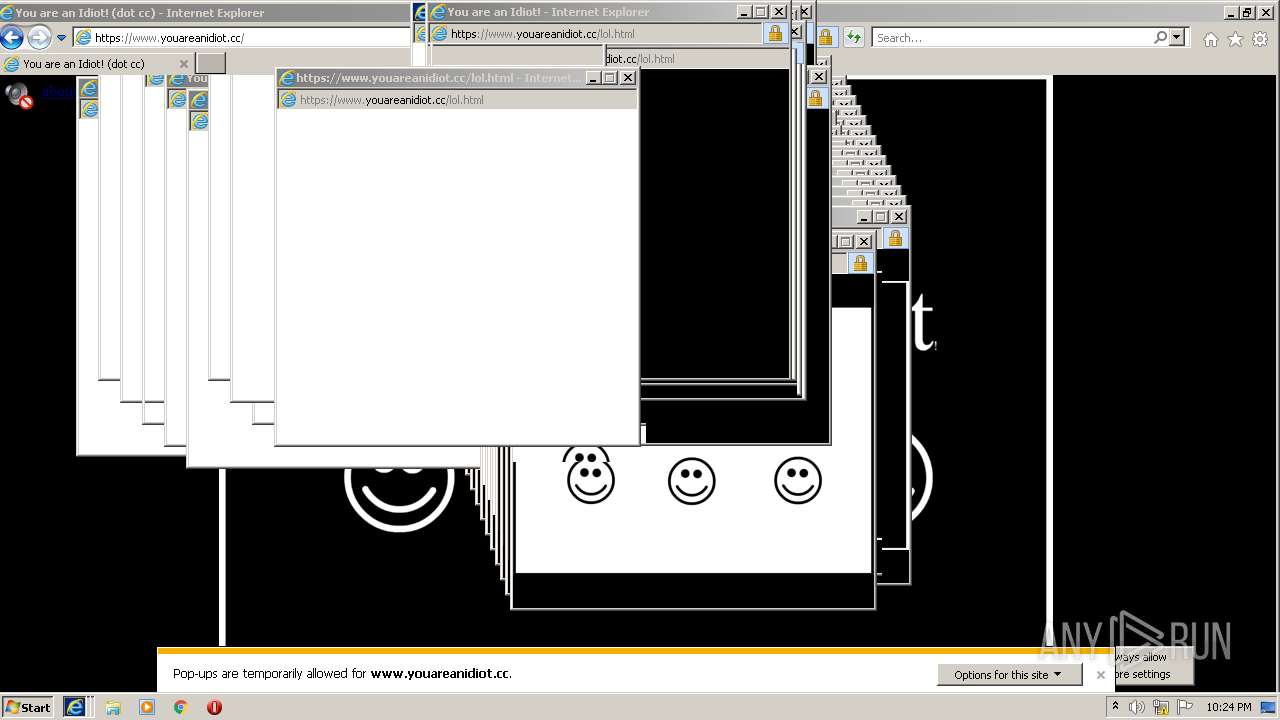
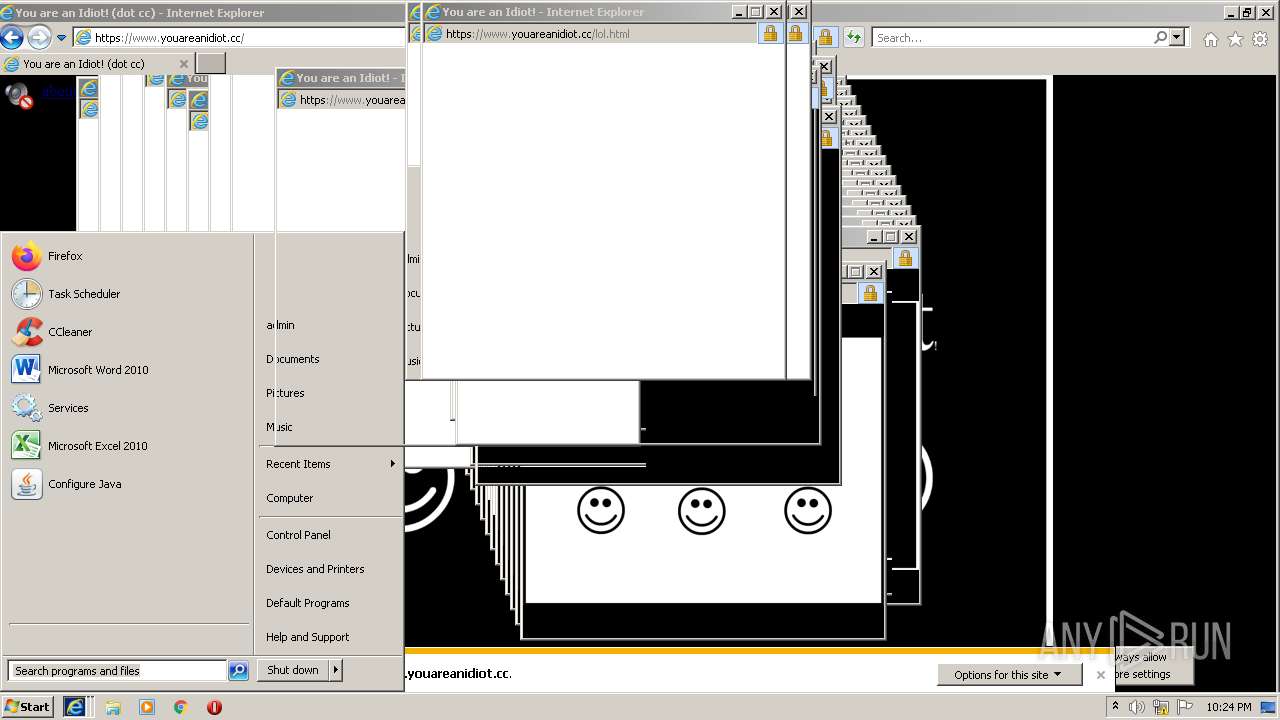
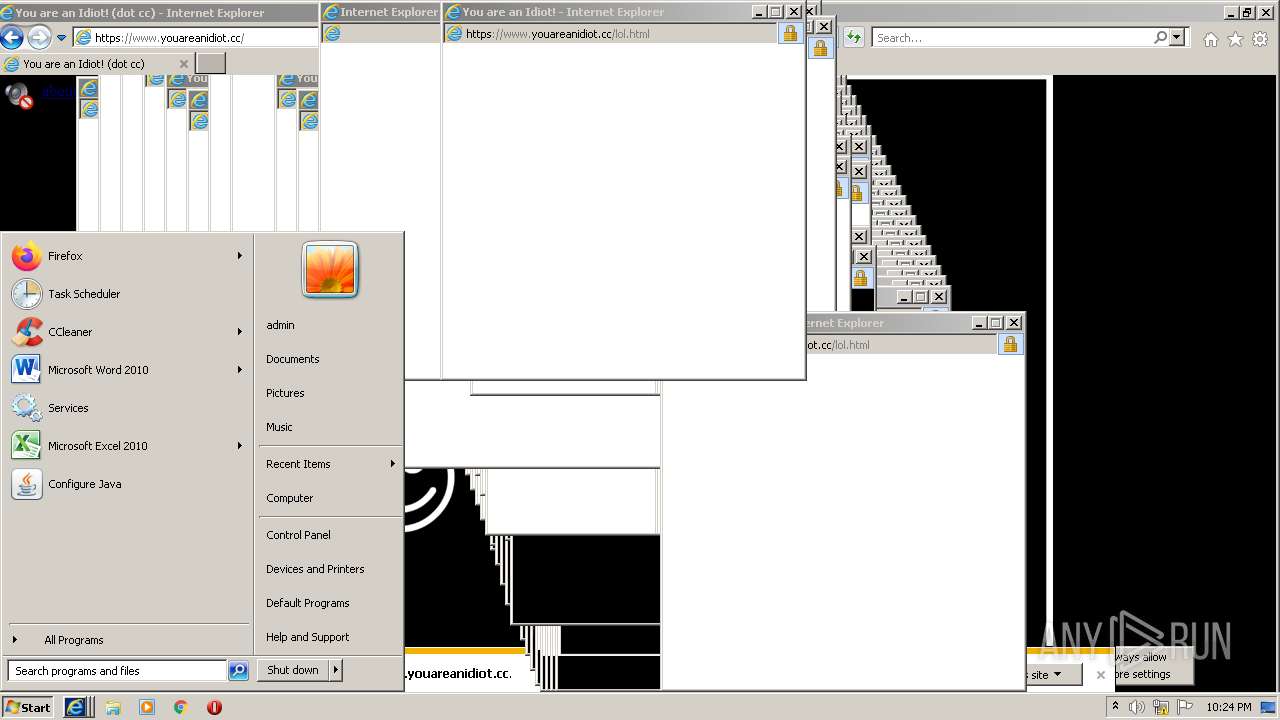
| URL: | http://youareanidiot.org |
| Full analysis: | https://app.any.run/tasks/6ef08f94-1894-4dae-849a-d82c3e9d2dfc |
| Verdict: | Malicious activity |
| Analysis date: | January 06, 2022, 22:23:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C9ED886B8FD89B13CF03D2DACFDC7E53 |
| SHA1: | E718AFBBD71EED14FA5A97618AD1305C47C94599 |
| SHA256: | D775BEA71BEE756FED8D035A60310844BD1C224DB470BC9272F10C8ABA1333A4 |
| SSDEEP: | 3:N1KHGpQKS:CT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3760)
- iexplore.exe (PID: 2916)
INFO
Reads the computer name
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3760)
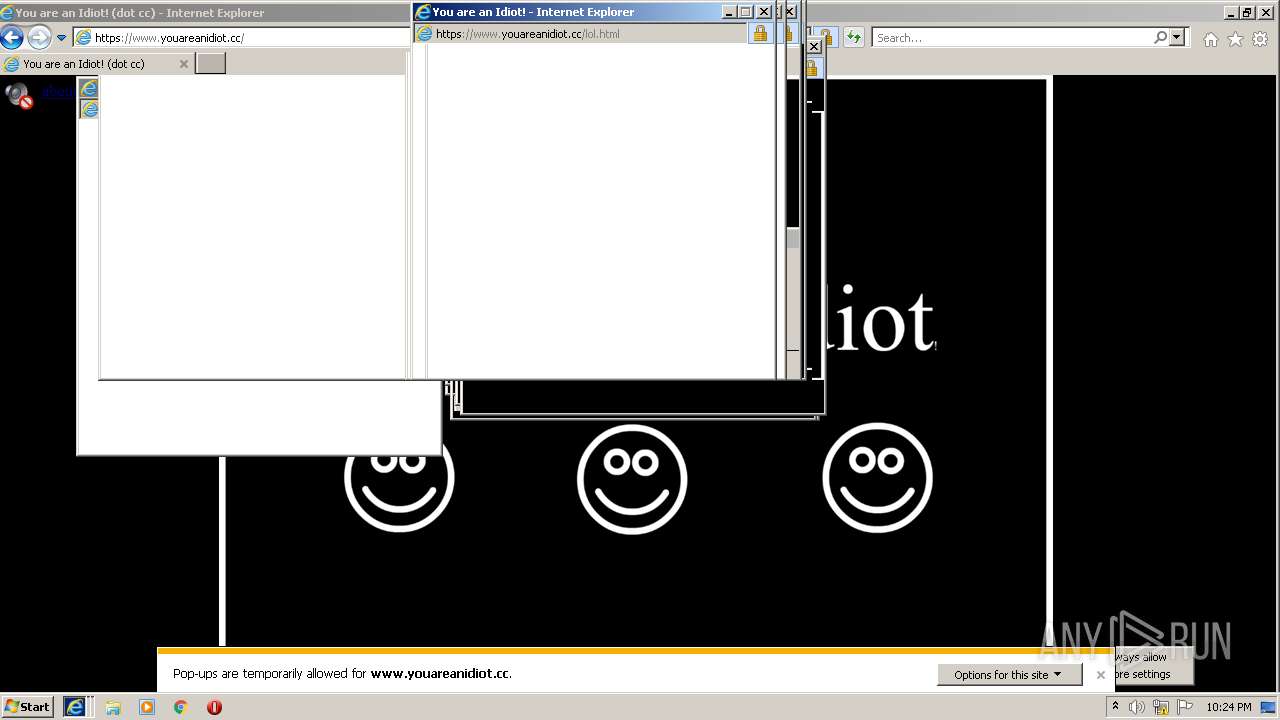
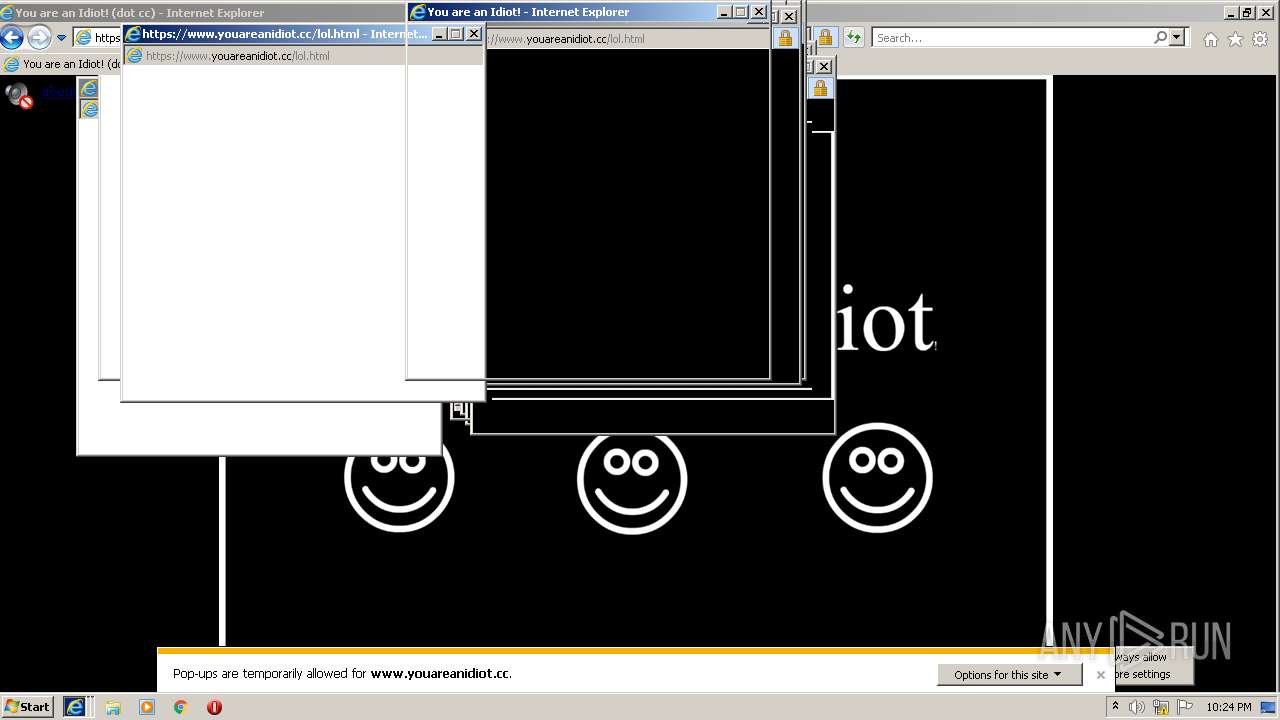
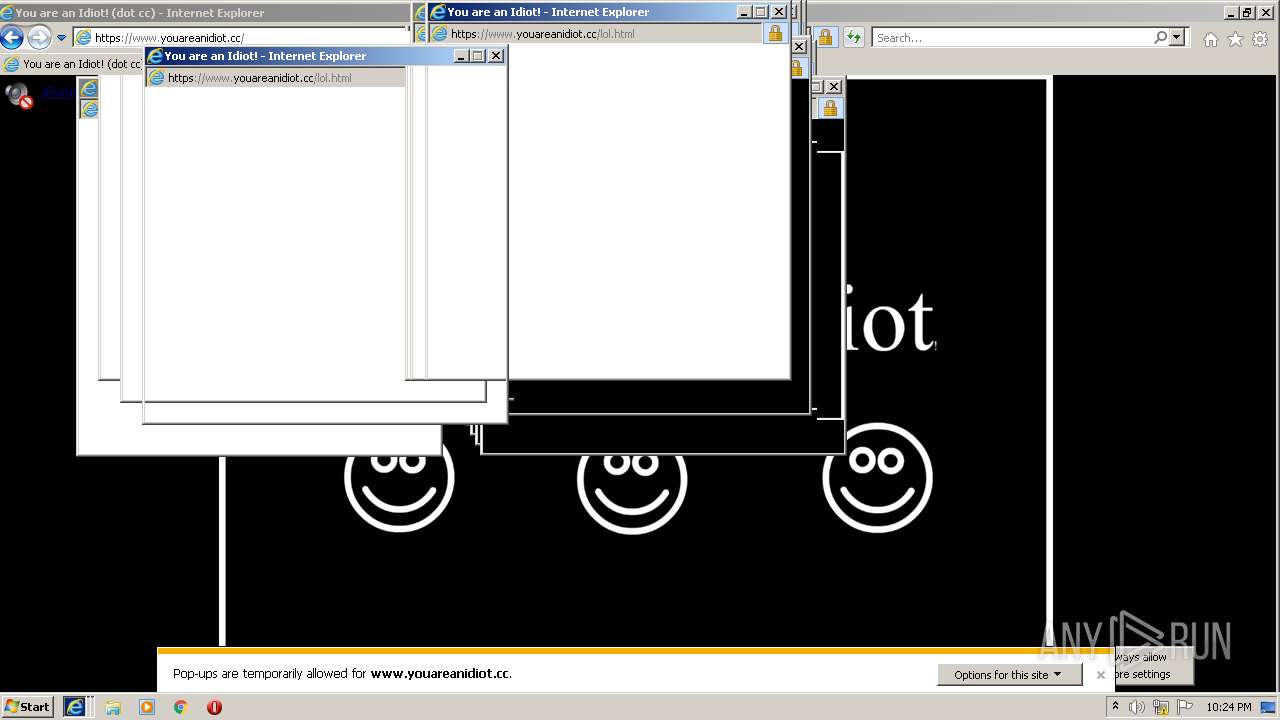
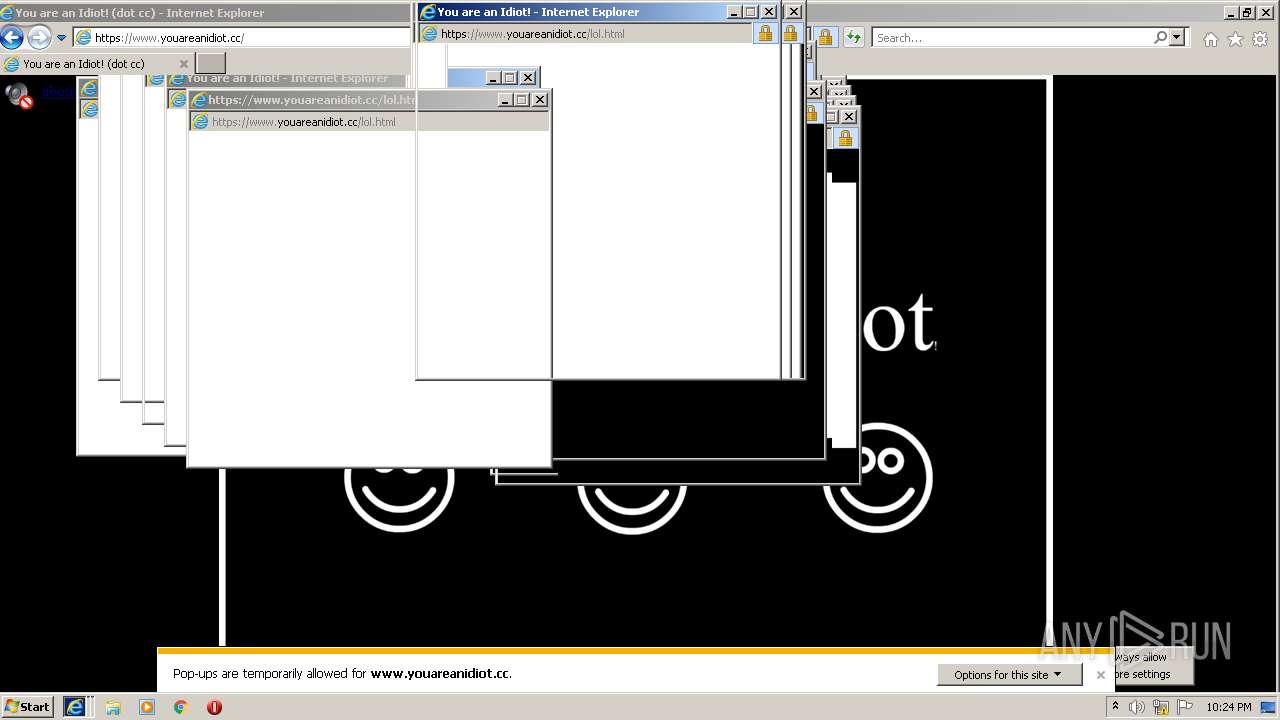
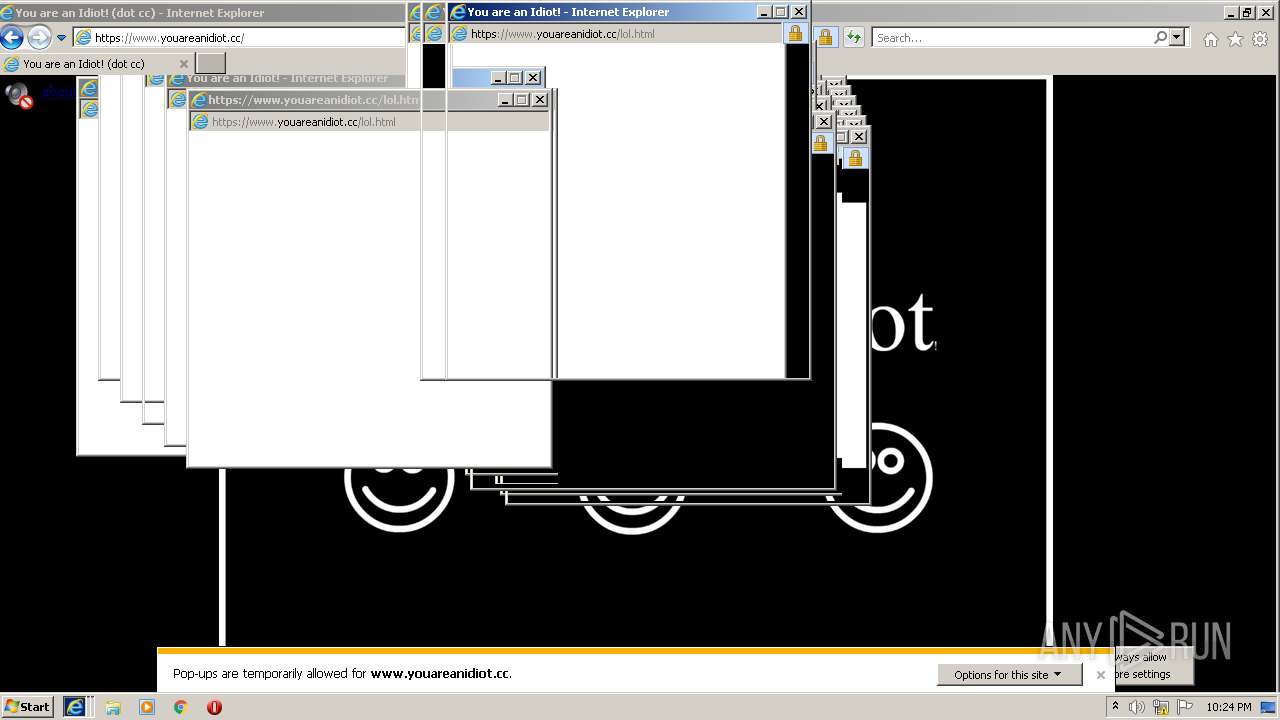
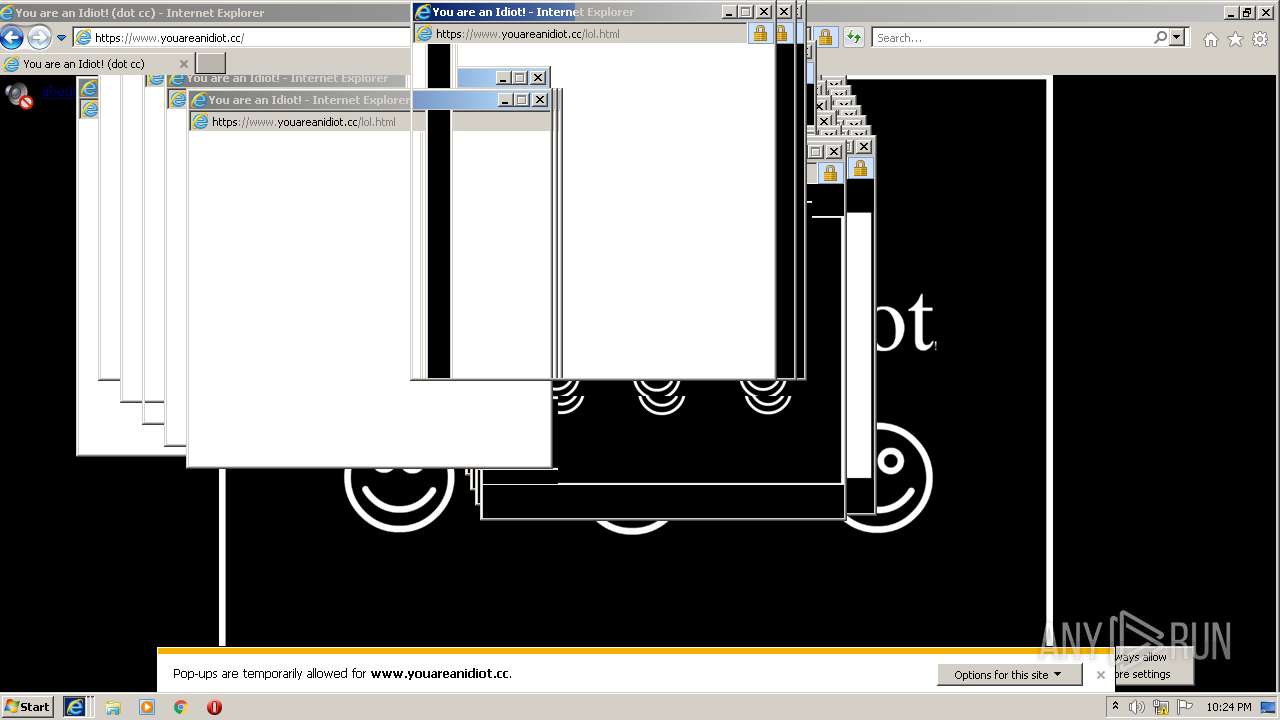
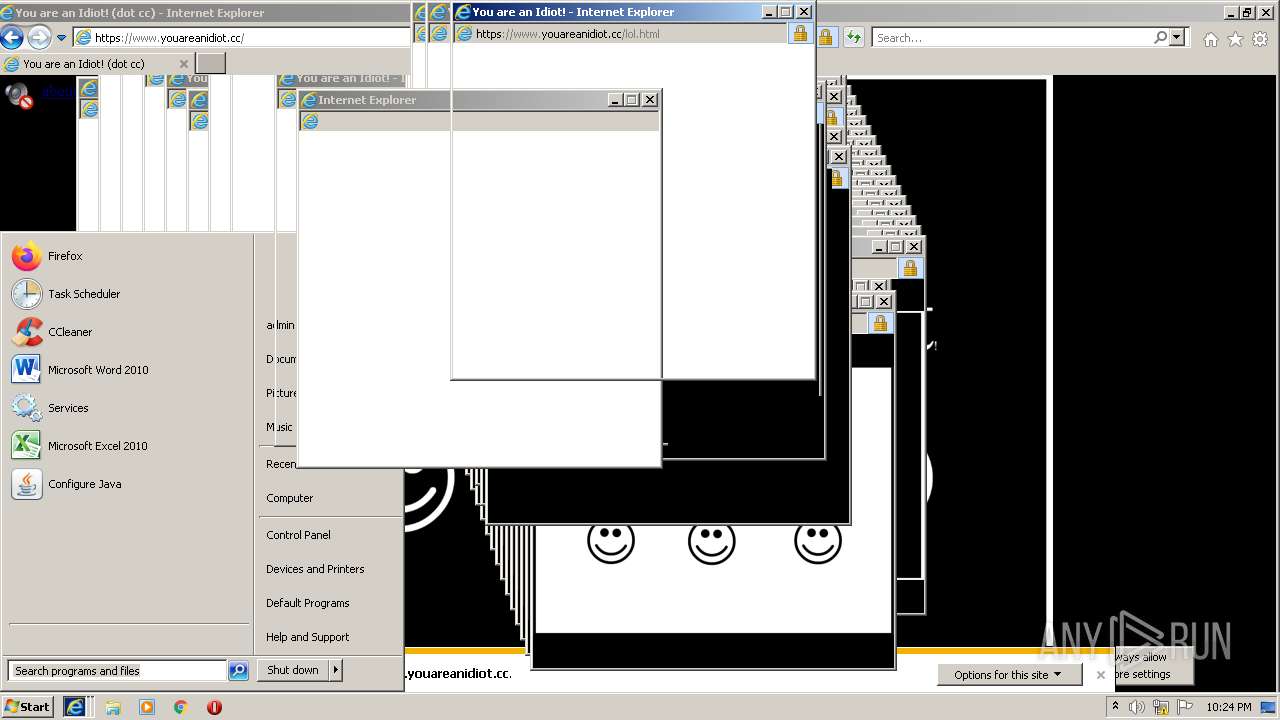
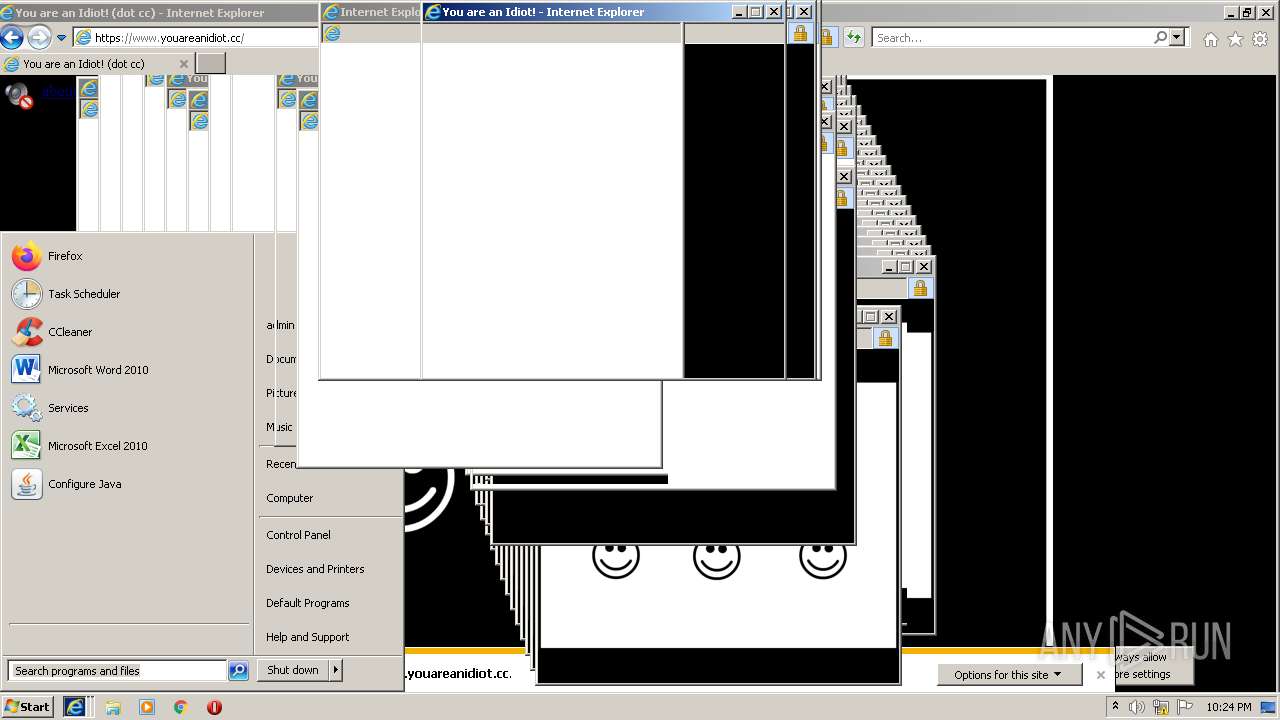
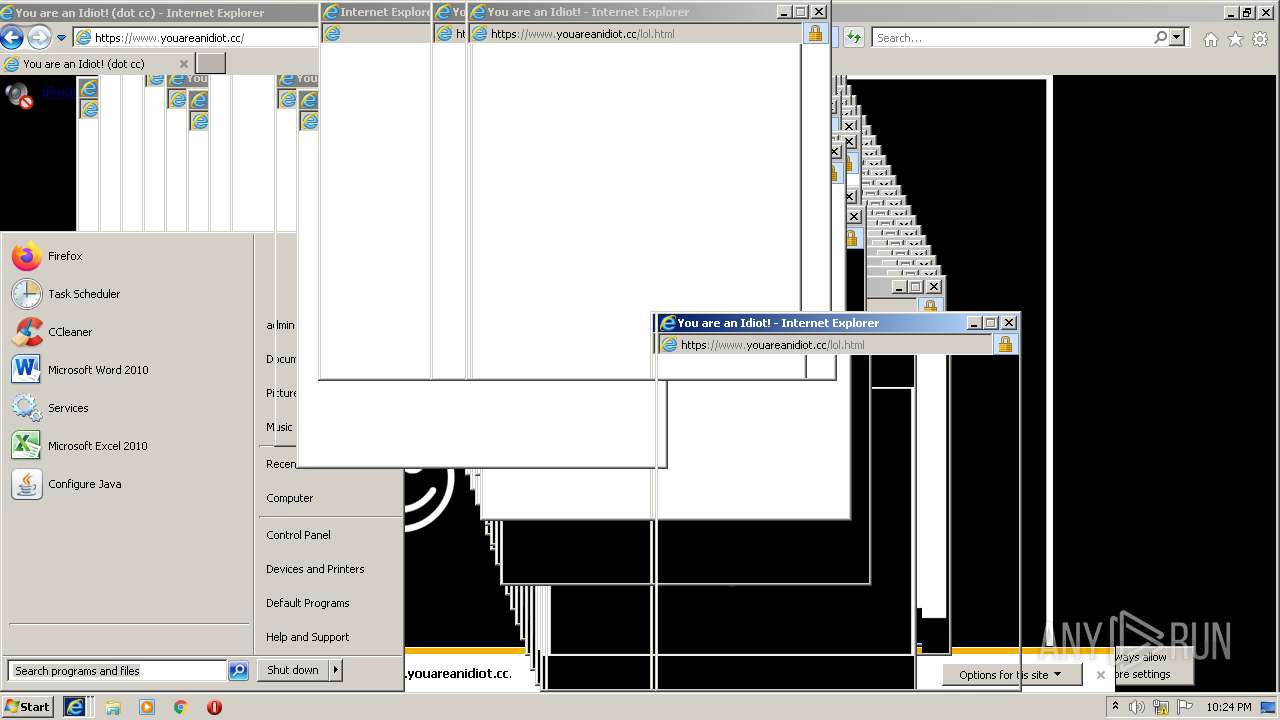
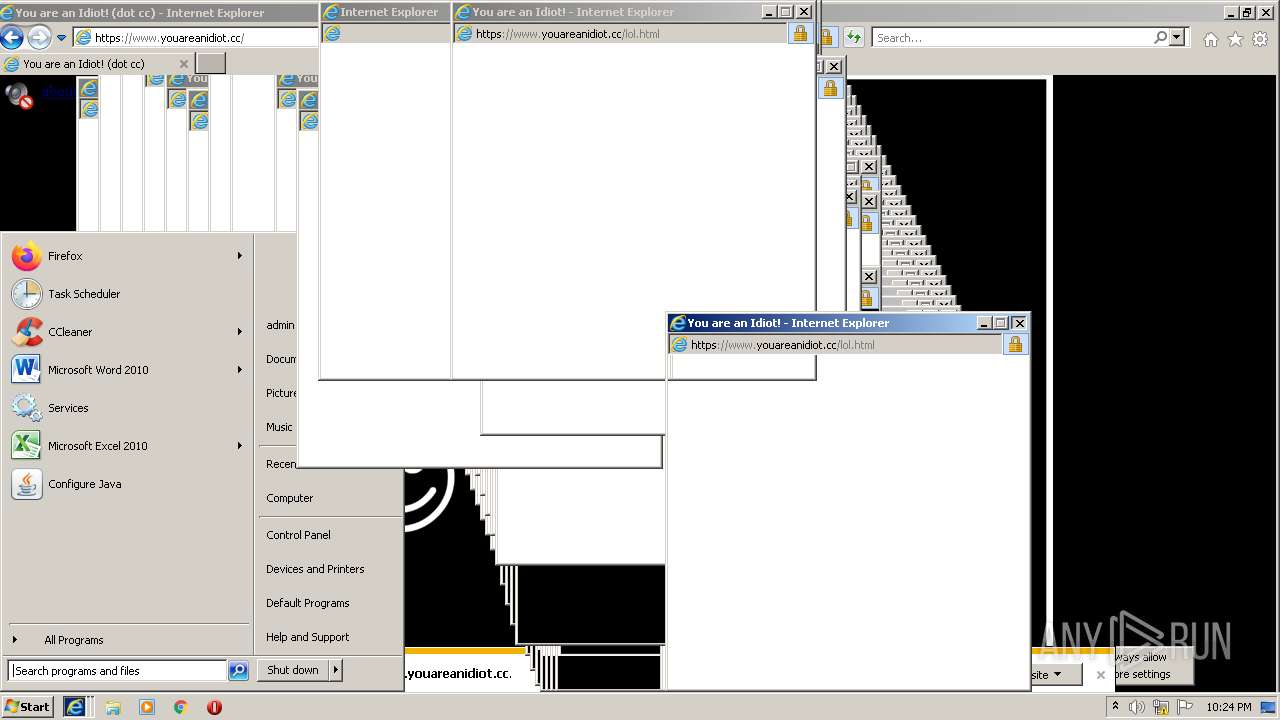
Application launched itself
- iexplore.exe (PID: 2916)
Checks supported languages
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3760)
Changes internet zones settings
- iexplore.exe (PID: 2916)
Checks Windows Trust Settings
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3760)
Changes settings of System certificates
- iexplore.exe (PID: 2916)
Reads settings of System Certificates
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3760)
Reads the date of Windows installation
- iexplore.exe (PID: 2916)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2916)
Creates files in the user directory
- iexplore.exe (PID: 3760)
- iexplore.exe (PID: 2916)
Reads internet explorer settings
- iexplore.exe (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2916 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://youareanidiot.org" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3760 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2916 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
39 218
Read events
38 460
Write events
754
Delete events
4
Modification events
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 374122544 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30933836 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 674280669 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30933836 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
56
Text files
181
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\72SSBRVM.htm | html | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\bouncy[1].htm | html | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\30D802E0E248FEE17AAF4A62594CC75A | binary | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F190623702881C0A562BABDD77A9E591 | der | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U9R27NMU.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
180
DNS requests
61
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3760 | iexplore.exe | GET | 200 | 69.16.231.150:80 | http://youareanidiot.org/page/bouncy.php?&bpae=GbhOt6smolx797uvwVmZ5NfFFjcJ7dclc3EJtpi%2BxFPG6KIf9ejbu8BmCqcw3pgCkJ0F6TGNUhPnRi44mDbnIjNrTTIOvx9OhOm6%2F7N7HQ2FT21mPrV%2F3CL66zK3lAdzT41cKnwD3WaSDFsqahfH33uyEUknaj51ow%2B63UhJ023gK0aLw9xJfU8i0nG0o76MInqPu6xXP33uSZHSCAdlsI9OpiFQMILIPagp9dZ%2FWtp4Zb%2F%2BbvqL0fD5jxbmjov2lT1SNJAX5eNVfKnYZmaJ1XoepY%2BQ7cKKK%2Bb8d7svc0M5fCzTJkRGdFsTkhG1wBZod8oC4fXU2ivT%2FhZATZIaqPY7U%2FLUosi2LrQirMf2jqHEW4FKlVWjzwRPnWvysFuuiAqkru7dL4XFzHmarpVj&redirectType=js&inIframe=false&inPopUp=false | US | html | 709 b | malicious |
3760 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCW9uAi6kHj8JQ1KgyADe1h | US | der | 472 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZ2fjZwSXF%2BwoAAAABJfz9 | US | der | 472 b | whitelisted |
— | — | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECHMNwkPtKJCCgAAAAEl%2FQo%3D | US | der | 471 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECECDO7PFgn2GFn0KraxqRs6A%3D | US | der | 471 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3760 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
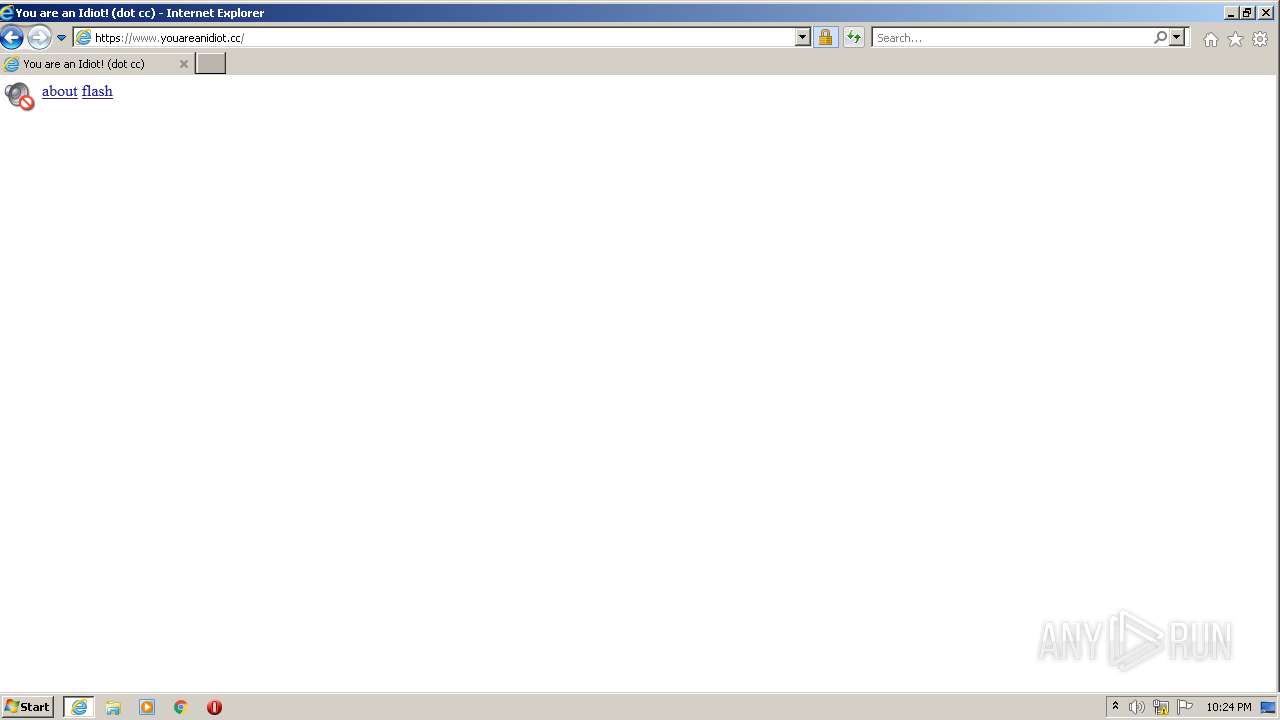
3760 | iexplore.exe | GET | 200 | 69.16.231.150:80 | http://youareanidiot.org/ | US | html | 1.88 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3760 | iexplore.exe | 69.16.231.150:80 | youareanidiot.org | Liquid Web, L.L.C | US | malicious |
3760 | iexplore.exe | 45.79.244.12:443 | simcast.com | Linode, LLC | US | malicious |
3760 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3760 | iexplore.exe | 91.199.212.52:80 | crt.sectigo.com | Comodo CA Ltd | GB | suspicious |
— | — | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
3760 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2916 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2916 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3760 | iexplore.exe | 69.16.175.42:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
3760 | iexplore.exe | 45.79.200.29:443 | parking2.parklogic.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
youareanidiot.org |
| unknown |
simcast.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crt.sectigo.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3760 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |