| File name: | o.exe |
| Full analysis: | https://app.any.run/tasks/63a94883-bb43-406f-96e9-aed88a816fa1 |
| Verdict: | Malicious activity |
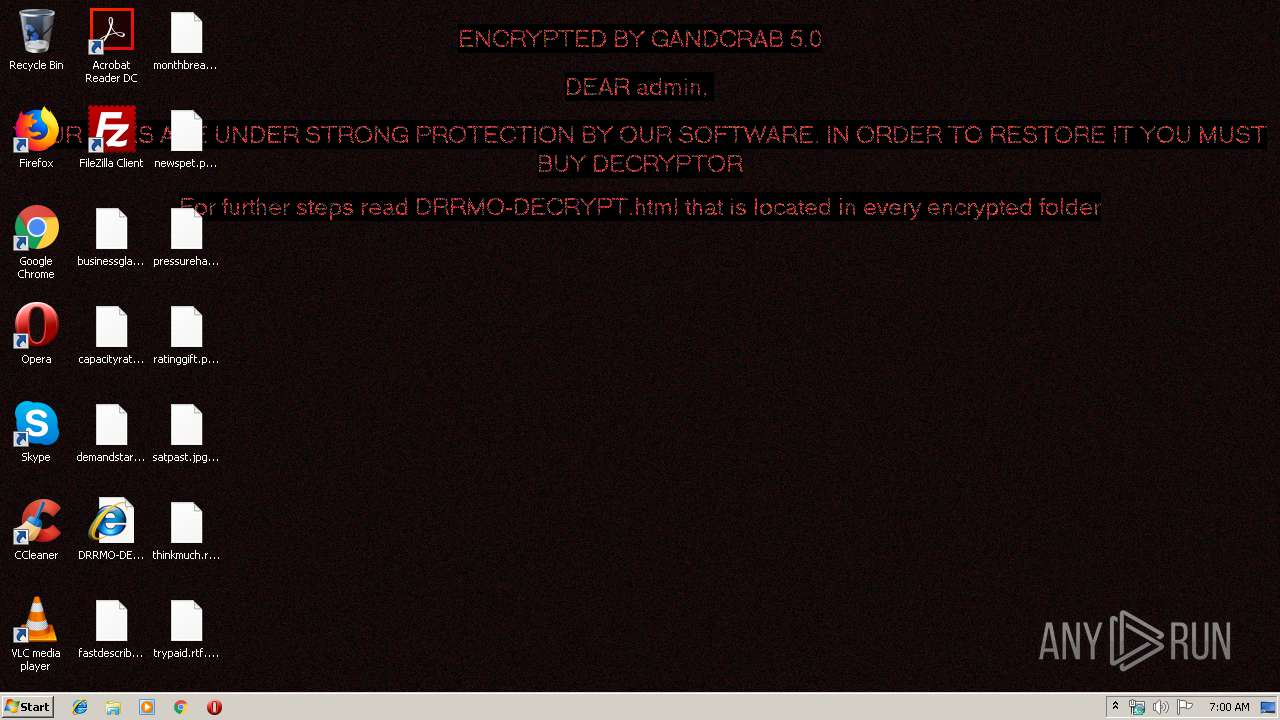
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | May 20, 2019, 05:59:57 |
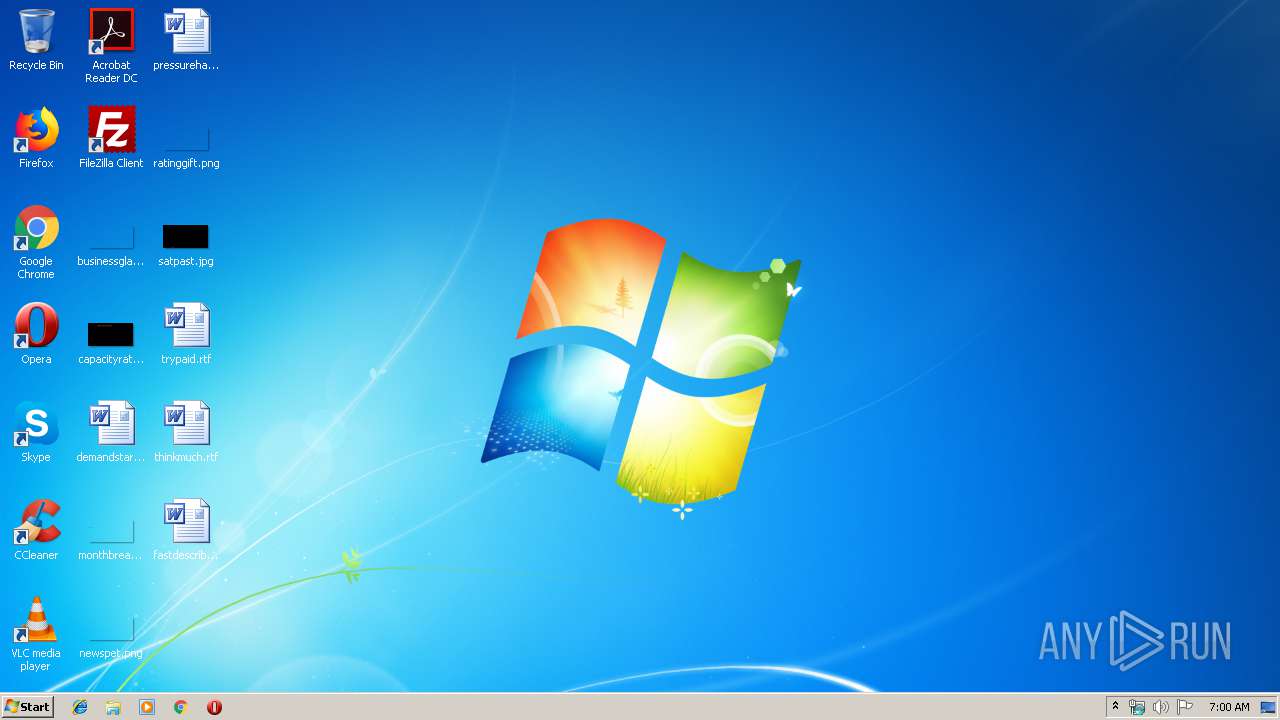
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 07FADB006486953439CE0092651FD7A6 |
| SHA1: | E42431D37561CC695DE03B85E8E99C9E31321742 |
| SHA256: | D77378DCC42B912E514D3BD4466CDDA050DDA9B57799A6C97F70E8489DD8C8D0 |
| SSDEEP: | 3072:Ealy19emgKe0QuYS3UmWuDTEltI3S/7IarDrjCgrQp0M7W:EaqxxDwx/7IS40MS |
MALICIOUS
GandCrab keys found
- o.exe (PID: 3108)
Actions looks like stealing of personal data
- o.exe (PID: 3108)
Connects to CnC server
- o.exe (PID: 3108)
Renames files like Ransomware
- o.exe (PID: 3108)
Writes file to Word startup folder
- o.exe (PID: 3108)
Deletes shadow copies
- o.exe (PID: 3108)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- o.exe (PID: 3108)
Creates files like Ransomware instruction
- o.exe (PID: 3108)
Creates files in the user directory
- o.exe (PID: 3108)
INFO
Dropped object may contain Bitcoin addresses
- o.exe (PID: 3108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:24 09:47:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 79360 |
| InitializedDataSize: | 114688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6314 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Sep-2018 07:47:02 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Sep-2018 07:47:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013474 | 0x00013600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57387 |
.rdata | 0x00015000 | 0x00006EE0 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.58949 |
.data | 0x0001C000 | 0x000138F4 | 0x00011C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.85604 |
.rsrc | 0x00030000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7015 |
.reloc | 0x00031000 | 0x000013B4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65085 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
XPSPRINT.DLL |
ole32.dll |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2920 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | o.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\o.exe" | C:\Users\admin\AppData\Local\Temp\o.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
120
Read events
89
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3108) o.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\o_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
272
Text files
205
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | o.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\DRRMO-DECRYPT.html | html | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\.oracle_jre_usage\DRRMO-DECRYPT.html | html | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DRRMO-DECRYPT.html | html | |
MD5:— | SHA256:— | |||
| 3108 | o.exe | C:\Users\admin\AppData\Roaming\DRRMO-DECRYPT.html | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
31
DNS requests
27
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3108 | o.exe | GET | — | 92.53.96.201:80 | http://perovaphoto.ru/ | RU | — | — | malicious |
3108 | o.exe | GET | — | 87.236.16.31:80 | http://asl-company.ru/ | RU | — | — | malicious |
3108 | o.exe | GET | — | 77.104.171.238:80 | http://www.fabbfoundation.gm/ | US | — | — | malicious |
3108 | o.exe | GET | — | 146.66.72.87:80 | http://www.perfectfunnelblueprint.com/ | US | — | — | malicious |
— | — | GET | 301 | 23.236.62.147:80 | http://dna-cp.com/ | US | — | — | whitelisted |
3108 | o.exe | GET | 301 | 213.186.33.3:80 | http://acbt.fr/ | FR | — | — | malicious |
3108 | o.exe | GET | 301 | 199.188.201.218:80 | http://www.poketeg.com/ | US | html | 227 b | malicious |
3108 | o.exe | GET | — | 178.238.37.162:80 | http://www.mimid.cz/ | CZ | — | — | malicious |
3108 | o.exe | POST | — | 87.236.16.31:80 | http://asl-company.ru/uploads/imgs/eska.jpg | RU | — | — | malicious |
3108 | o.exe | POST | — | 146.66.72.87:80 | http://www.perfectfunnelblueprint.com/wp-content/tmp/fudezuse.gif | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3108 | o.exe | 92.53.96.201:80 | perovaphoto.ru | TimeWeb Ltd. | RU | malicious |
3108 | o.exe | 199.188.201.218:443 | www.poketeg.com | Namecheap, Inc. | US | malicious |
3108 | o.exe | 87.236.16.31:80 | asl-company.ru | Beget Ltd | RU | malicious |
3108 | o.exe | 77.104.171.238:80 | www.fabbfoundation.gm | SoftLayer Technologies Inc. | US | malicious |
3108 | o.exe | 217.160.0.234:443 | www.billerimpex.com | 1&1 Internet SE | DE | malicious |
— | — | 217.70.184.50:80 | www.macartegrise.eu | GANDI SAS | FR | malicious |
— | — | 217.70.184.50:443 | www.macartegrise.eu | GANDI SAS | FR | malicious |
3108 | o.exe | 199.188.201.218:80 | www.poketeg.com | Namecheap, Inc. | US | malicious |
— | — | 213.186.33.3:80 | acbt.fr | OVH SAS | FR | malicious |
3108 | o.exe | 213.186.33.3:443 | acbt.fr | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.billerimpex.com |
| whitelisted |
www.macartegrise.eu |
| malicious |
www.poketeg.com |
| malicious |
perovaphoto.ru |
| malicious |
asl-company.ru |
| malicious |
www.fabbfoundation.gm |
| malicious |
www.perfectfunnelblueprint.com |
| unknown |
www.wash-wear.com |
| malicious |
pp-panda74.ru |
| malicious |
cevent.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3108 | o.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
3108 | o.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
3108 | o.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3108 | o.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
3108 | o.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
3108 | o.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3108 | o.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
3108 | o.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
3108 | o.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3108 | o.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |