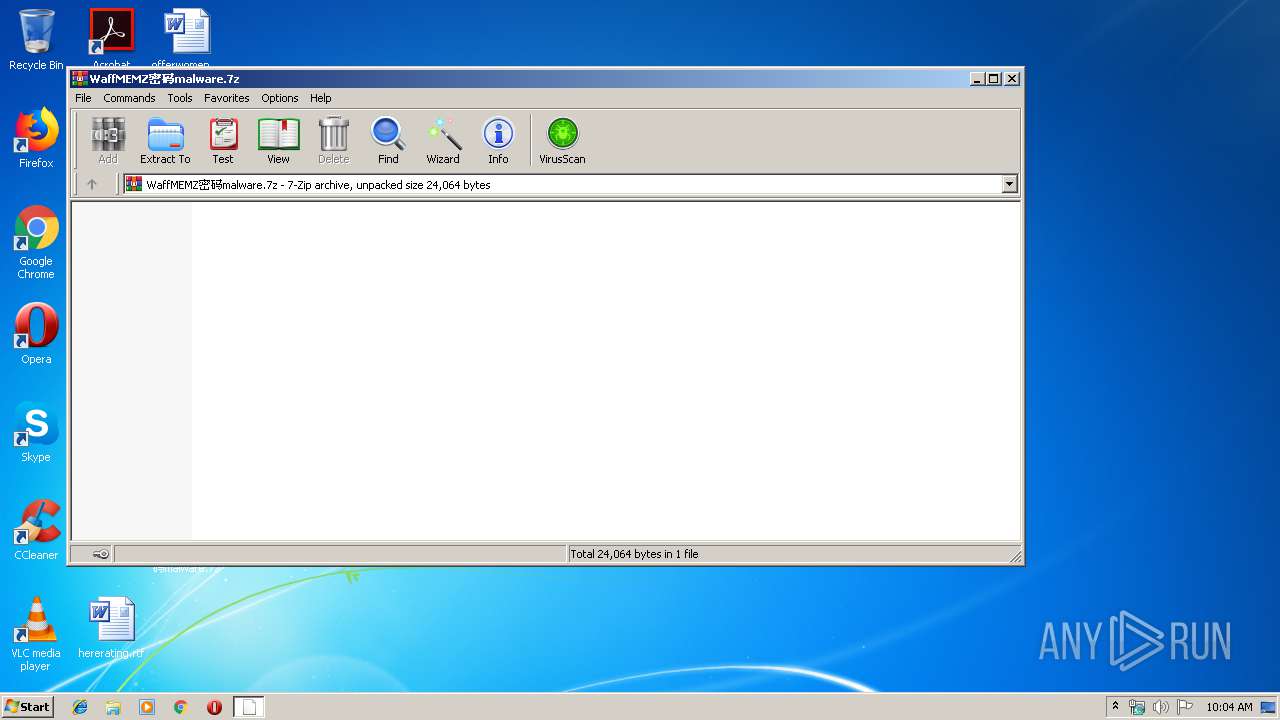
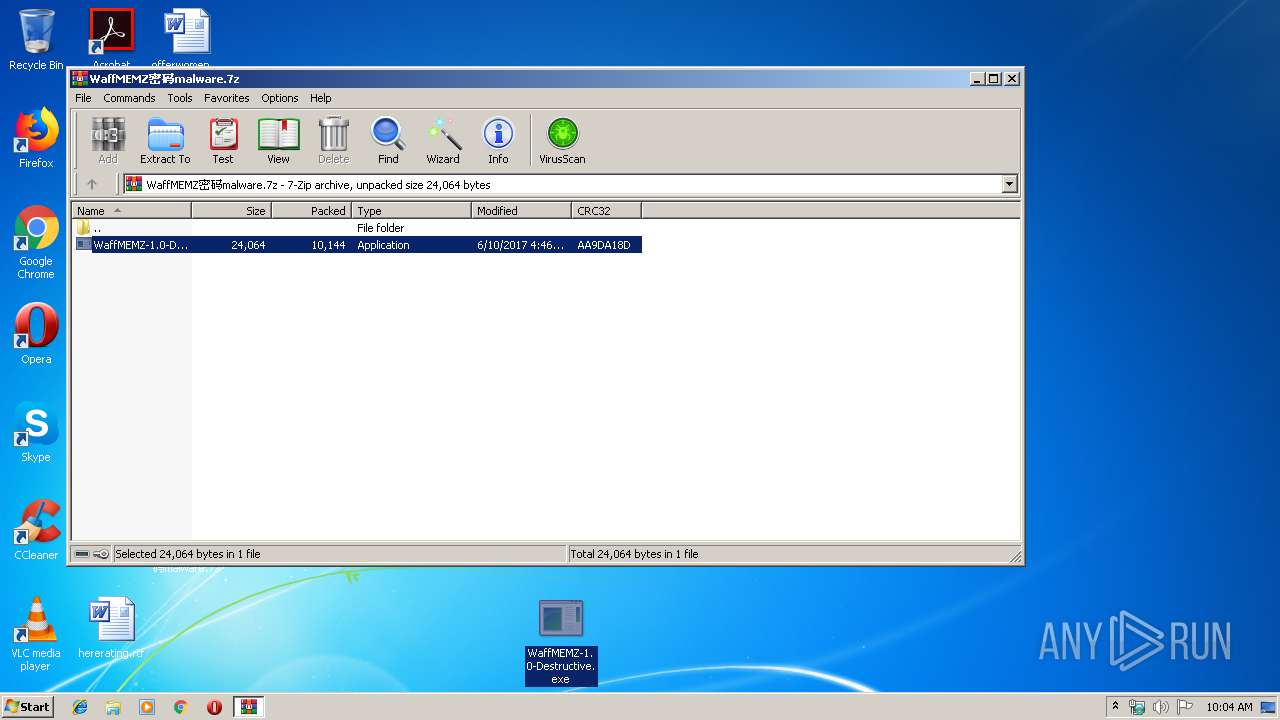
| File name: | WaffMEMZ密码malware.7z |
| Full analysis: | https://app.any.run/tasks/603f582c-00da-4440-8de4-25651af1e978 |
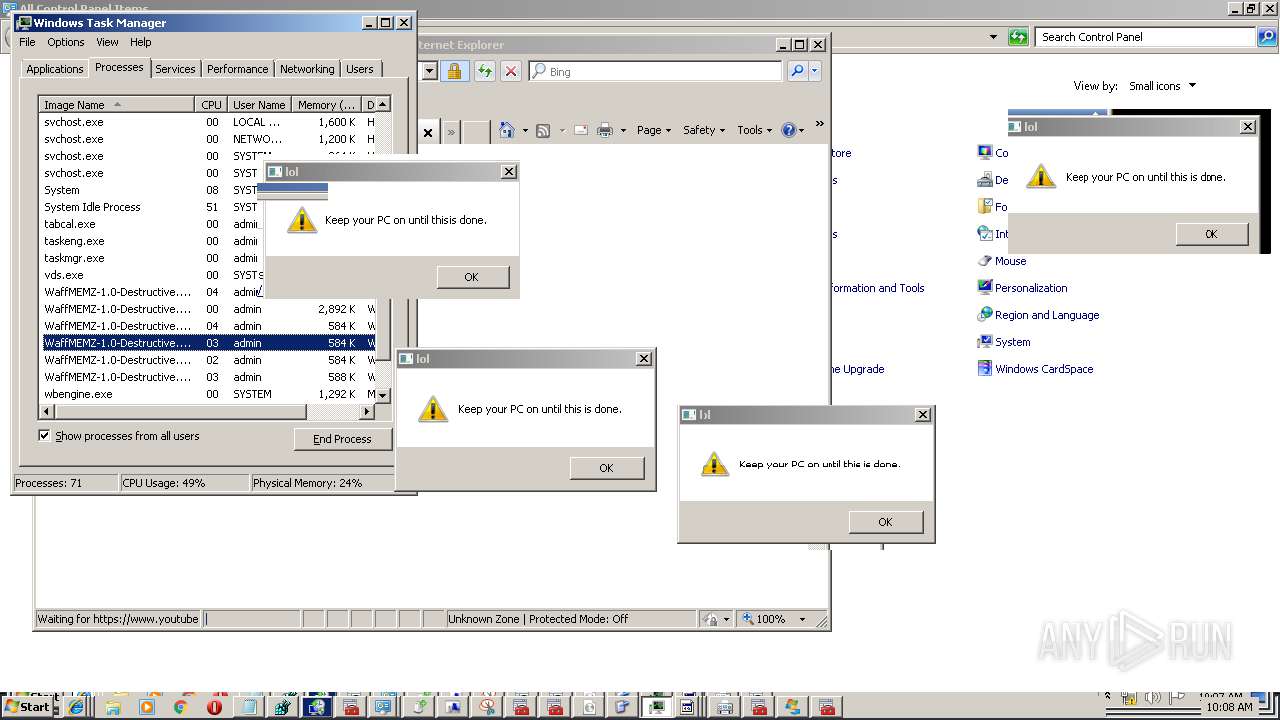
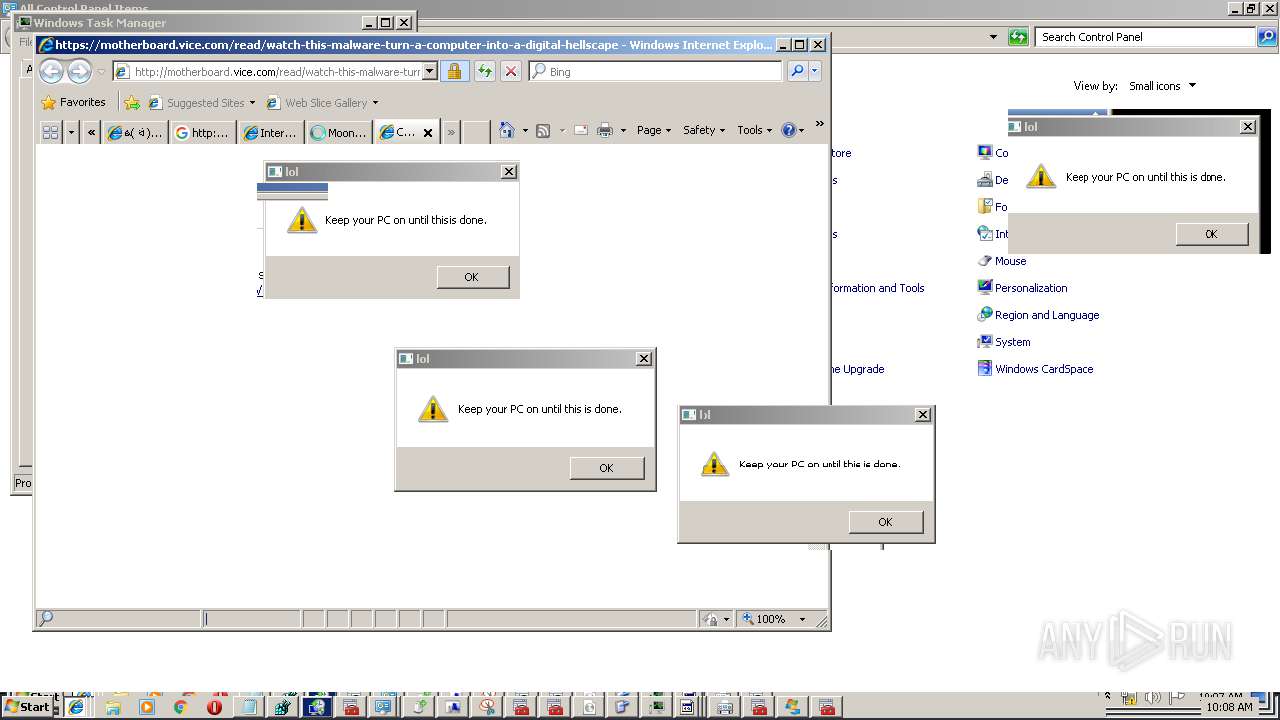
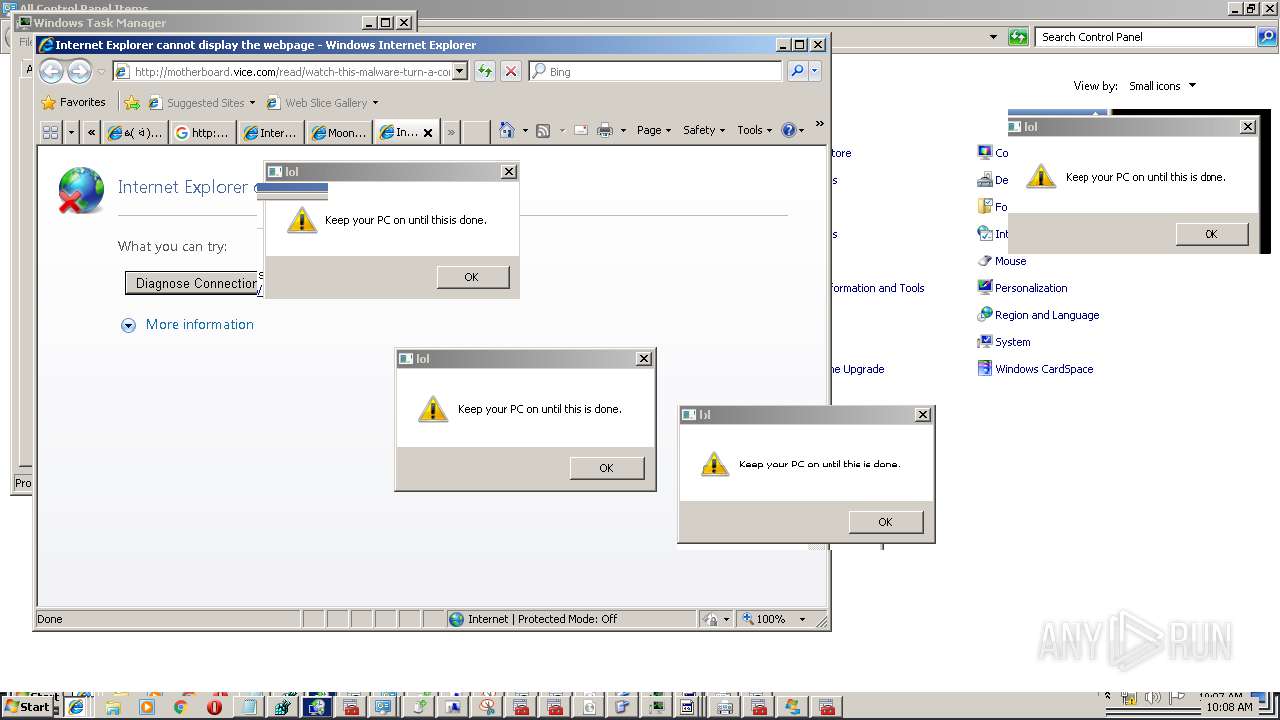
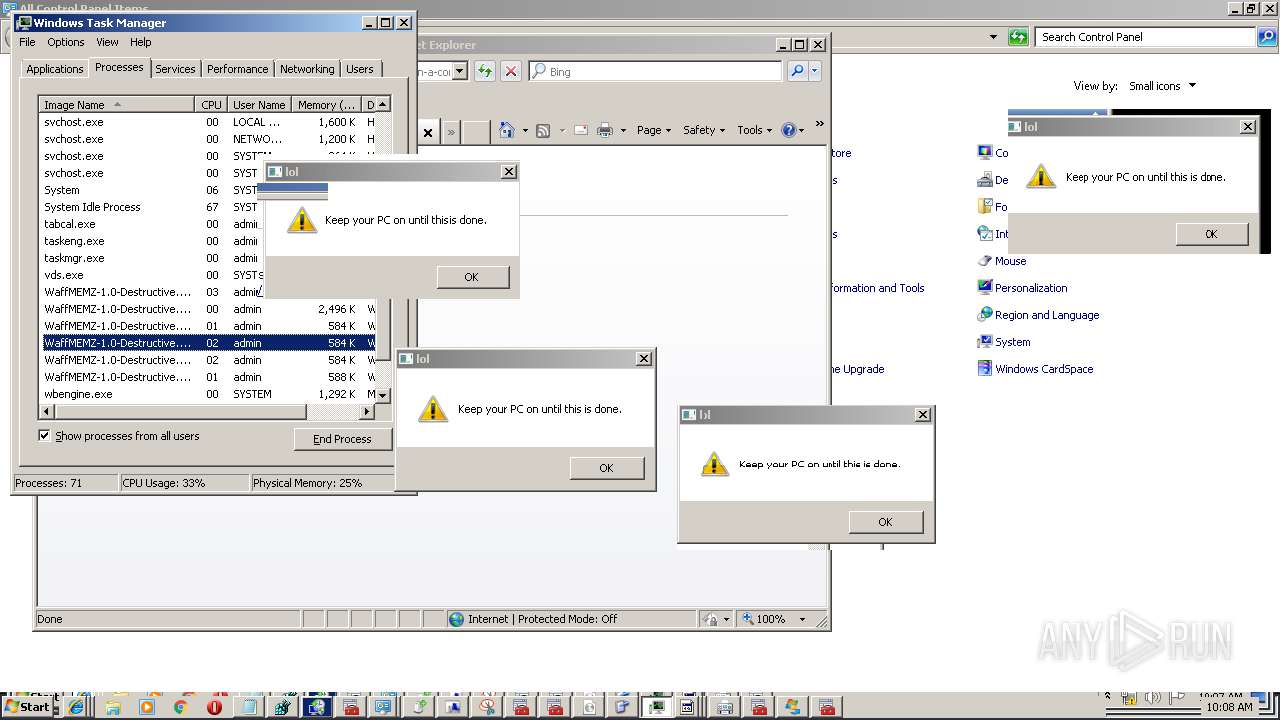
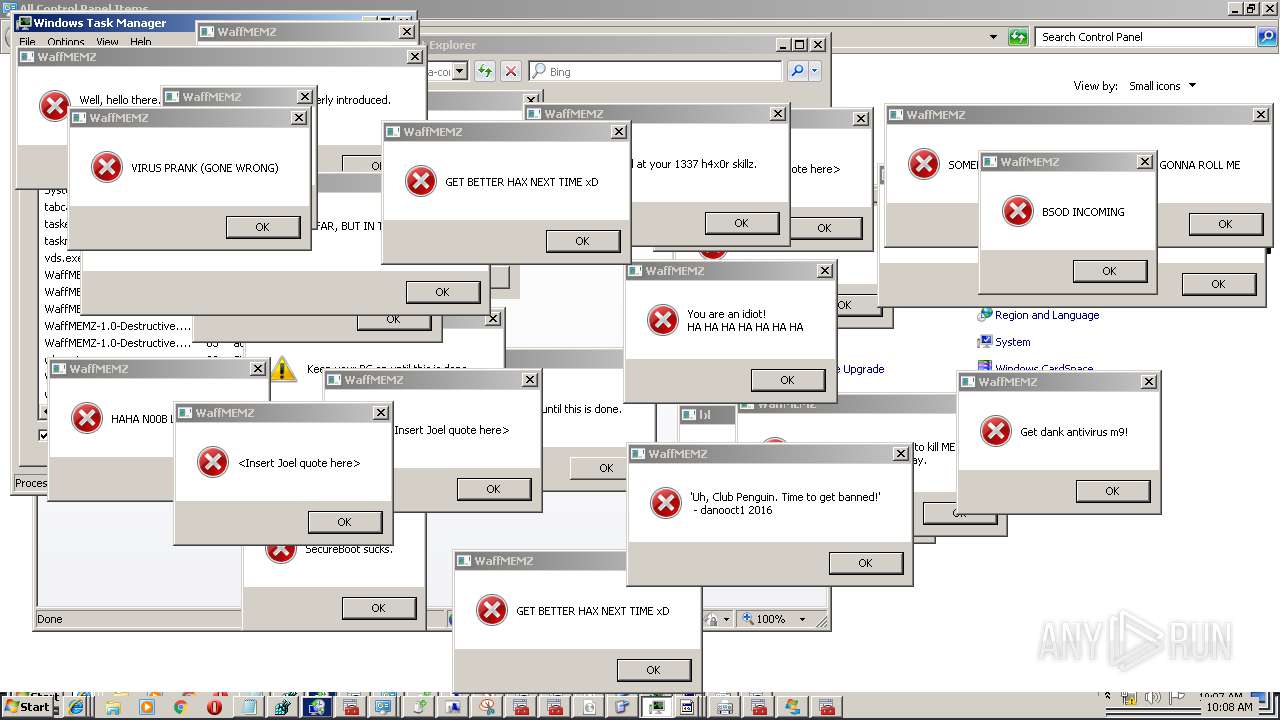
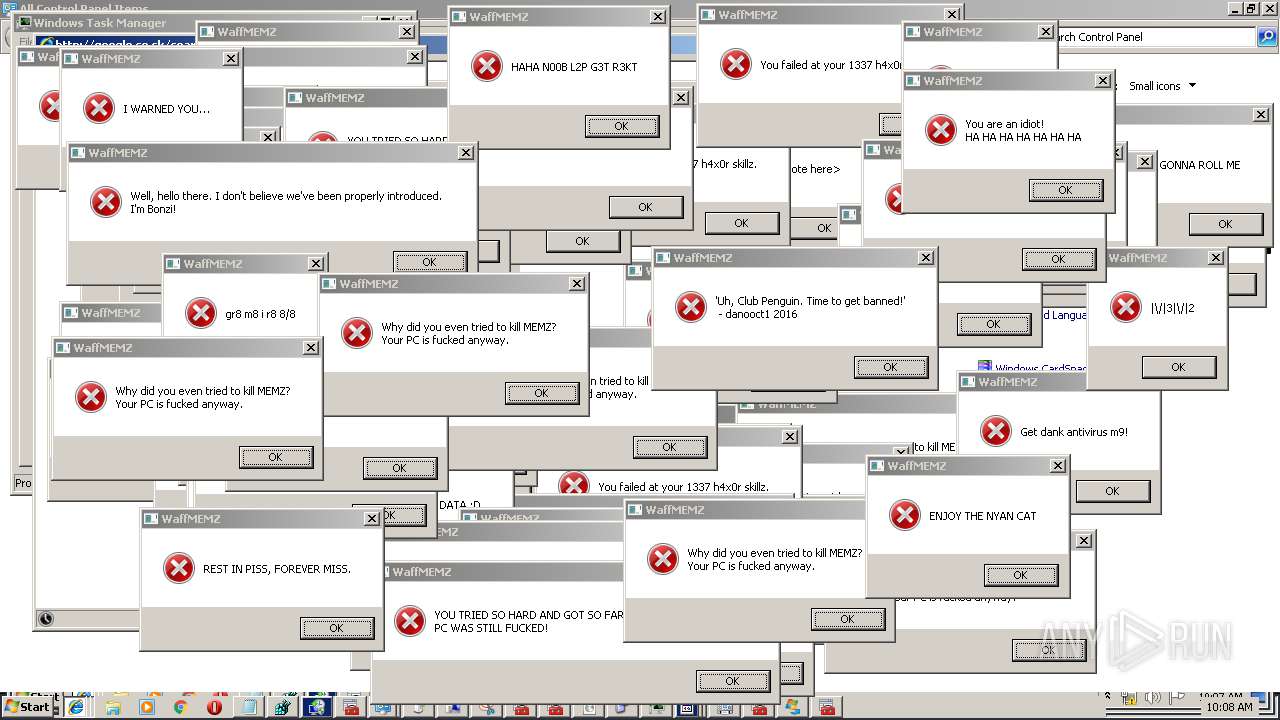
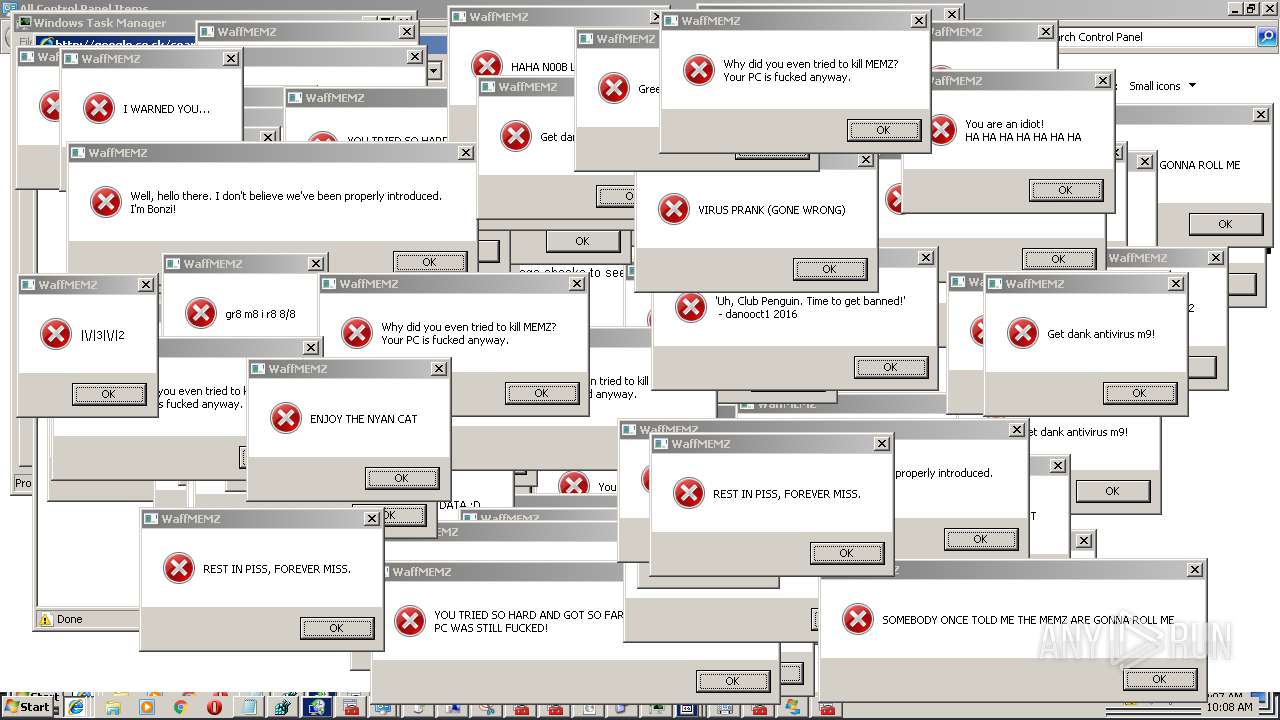
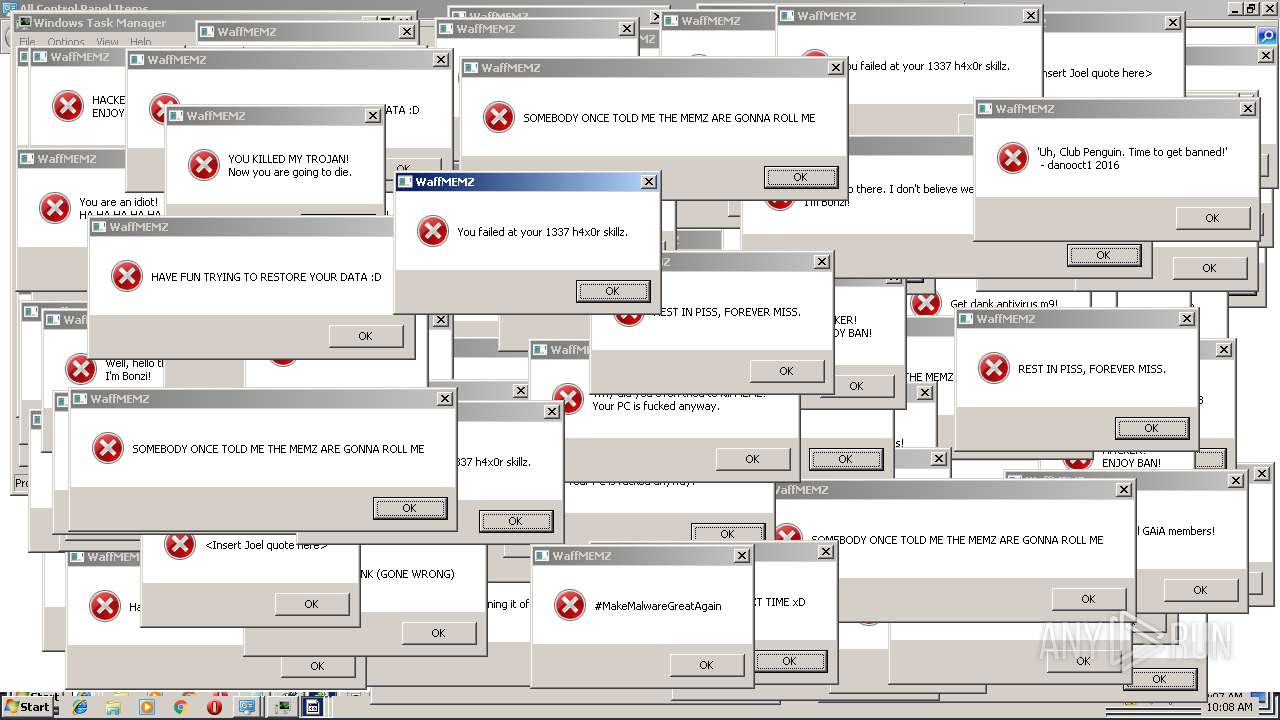
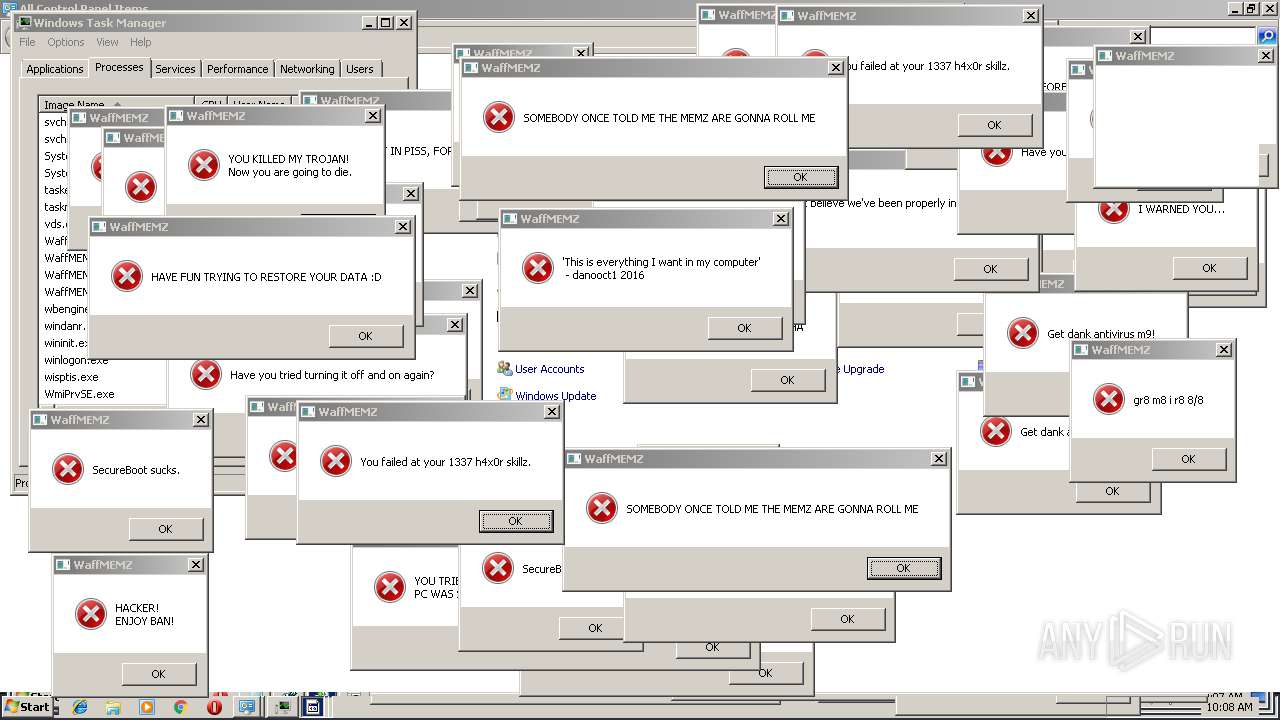
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 09:03:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 527D8596B05F8A5EA645A2327BC083FE |
| SHA1: | 985960A519CAC4977C849D34FDA06D016FA75F95 |
| SHA256: | D76514431F556A3B5BCFF9D9222C94FF97ED4139B157D8C73966A18607A8C86F |
| SSDEEP: | 192:MAgxv8STCX5EuBlt/xHRsjgHMclxkbatifgAzS01AgI3T6dmVXFN+Ic/uf1:e9CXdBD/xhMmxm3fgx0YmdmVXFN+D/ud |
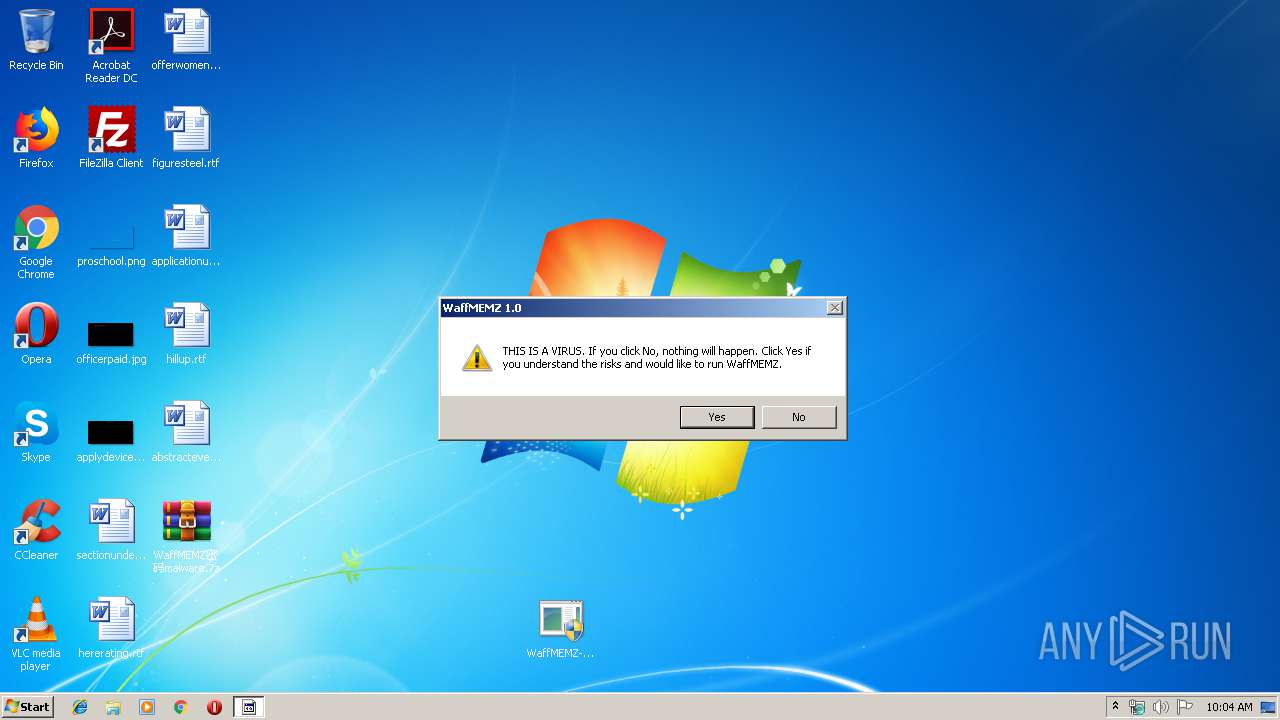
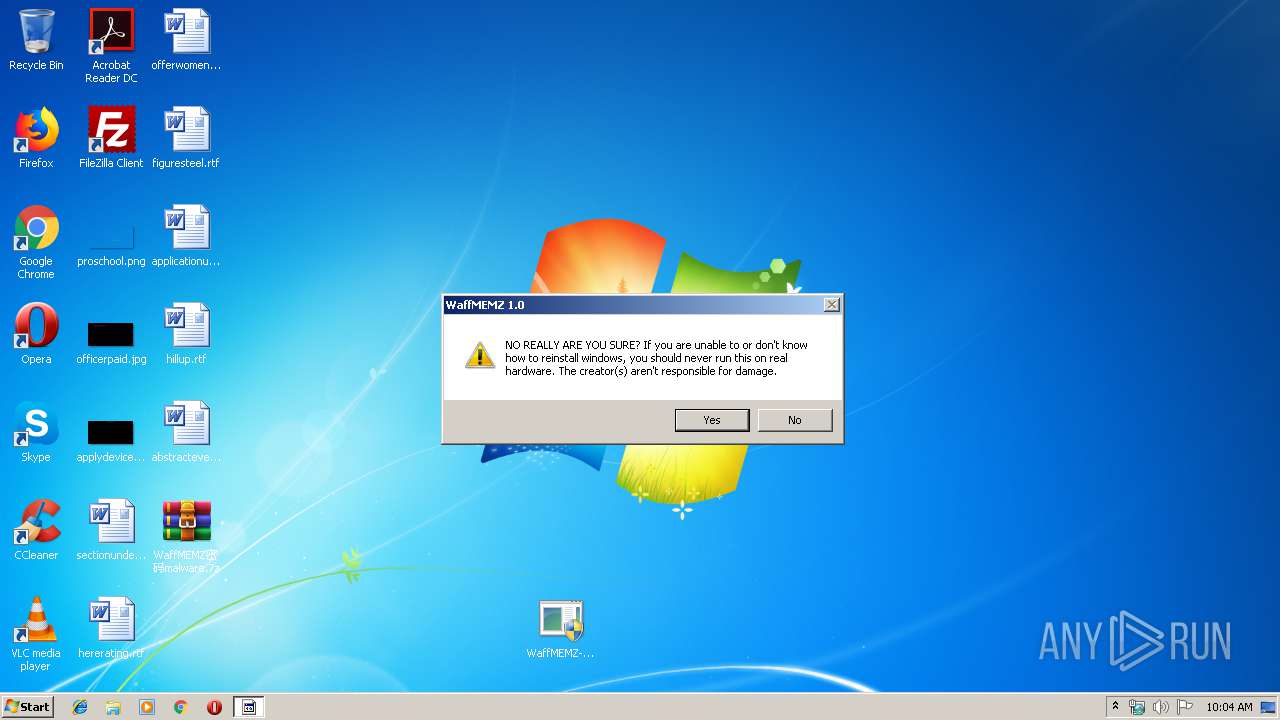
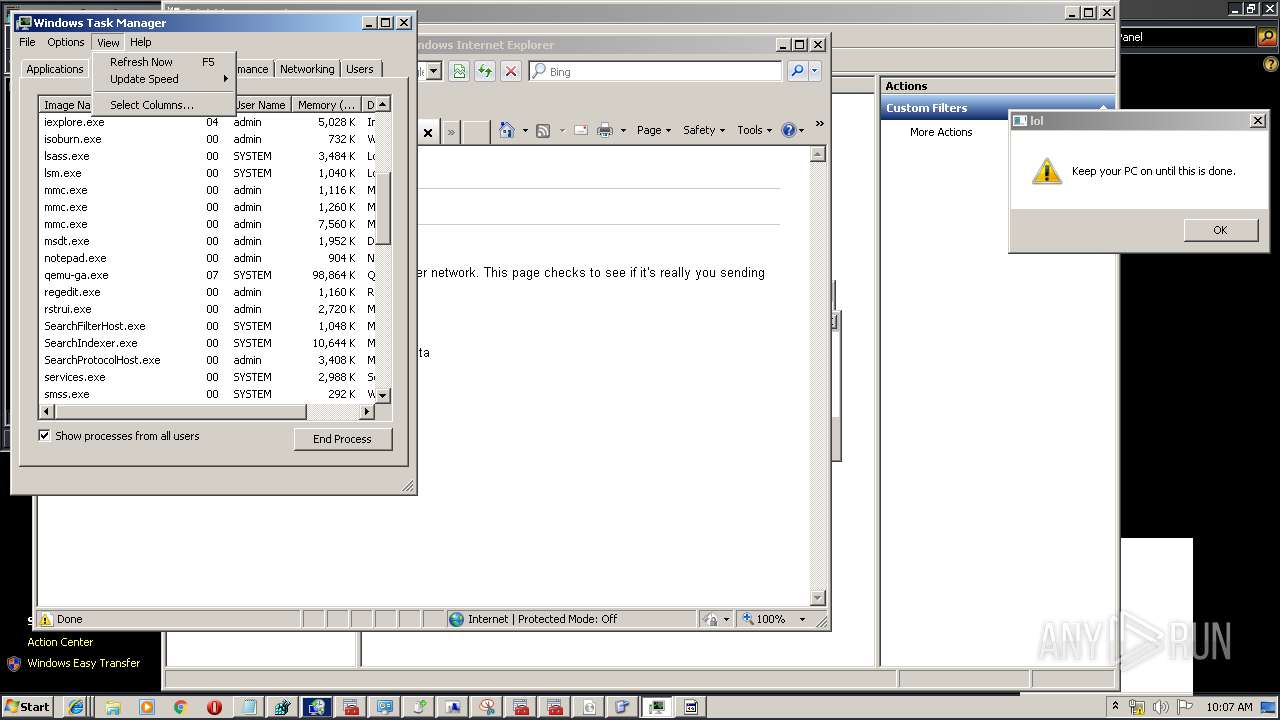
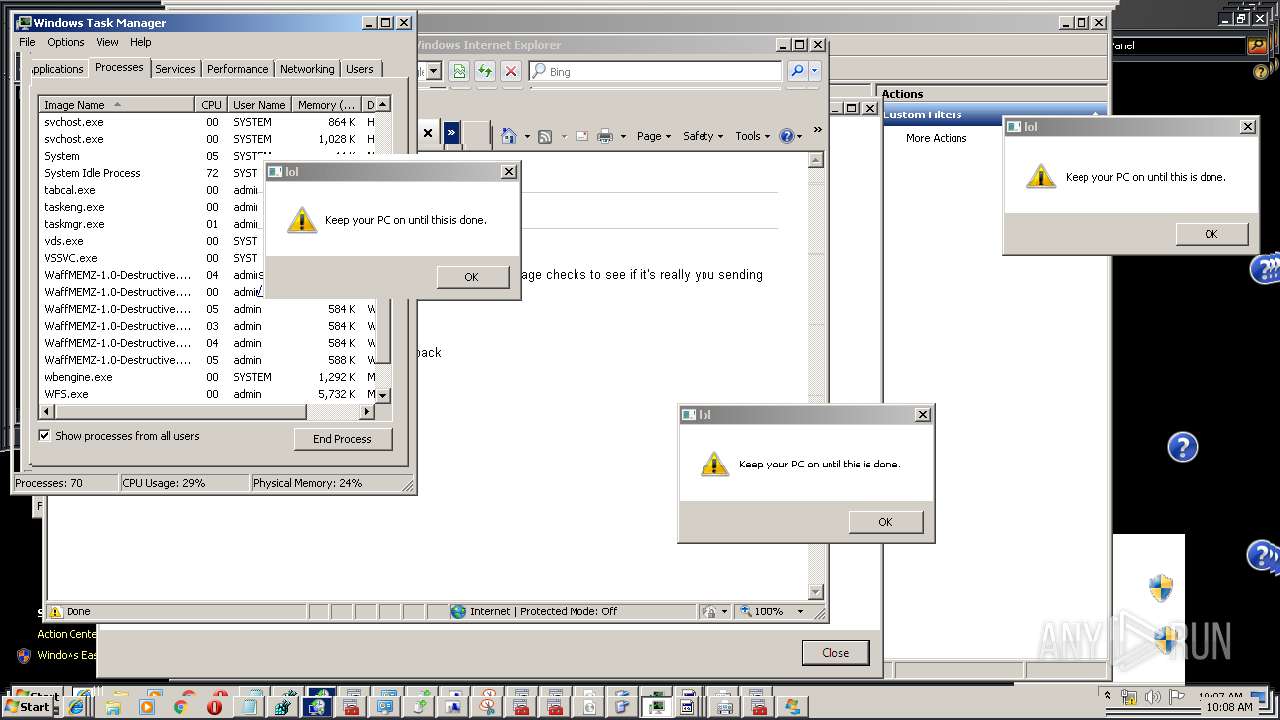
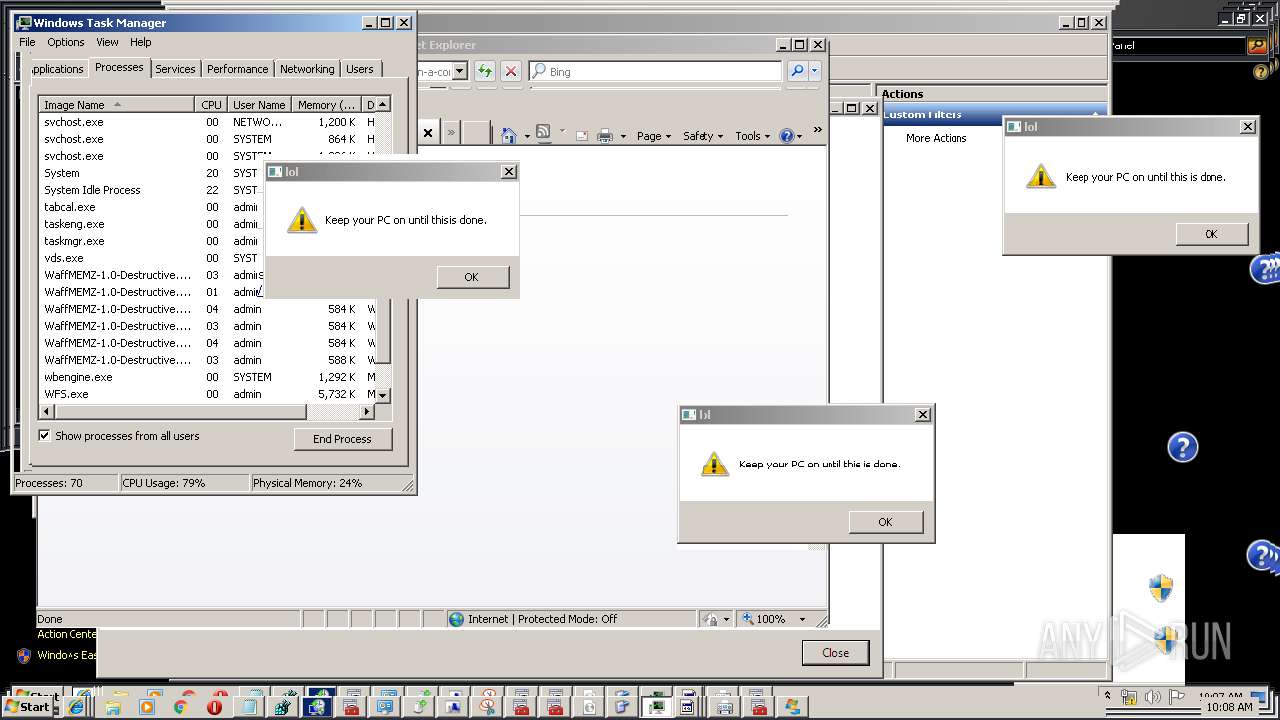
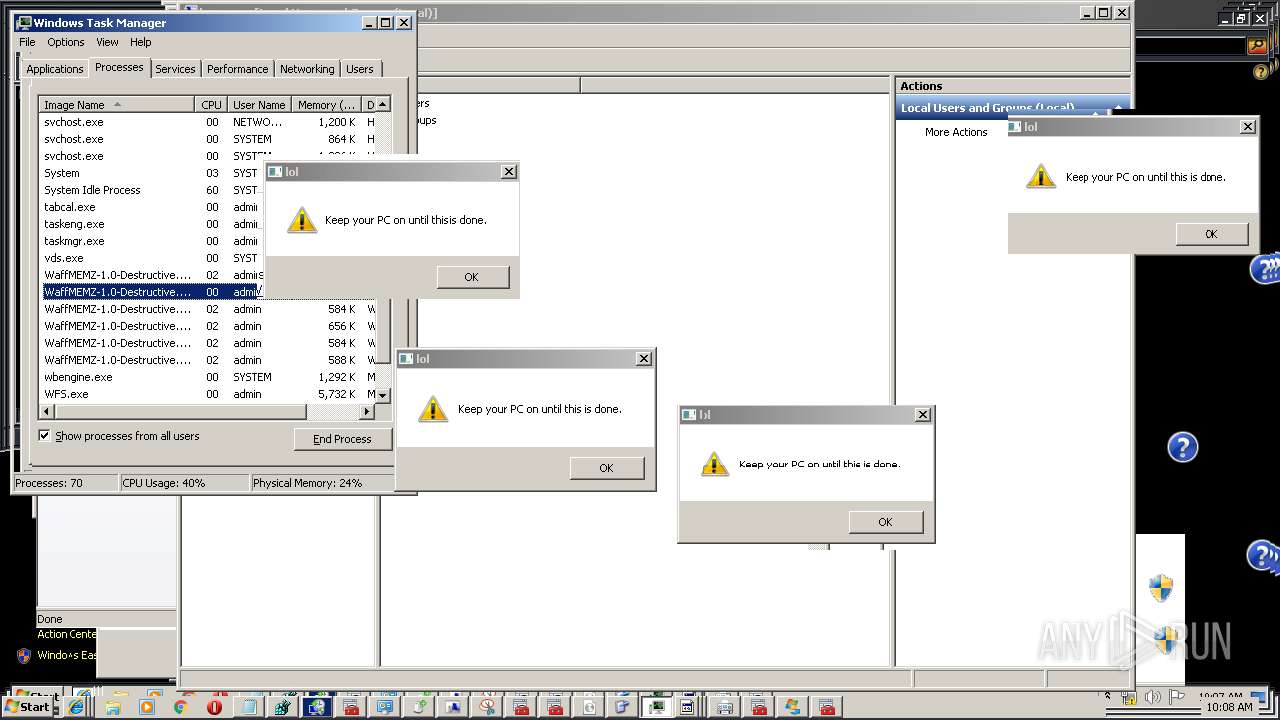
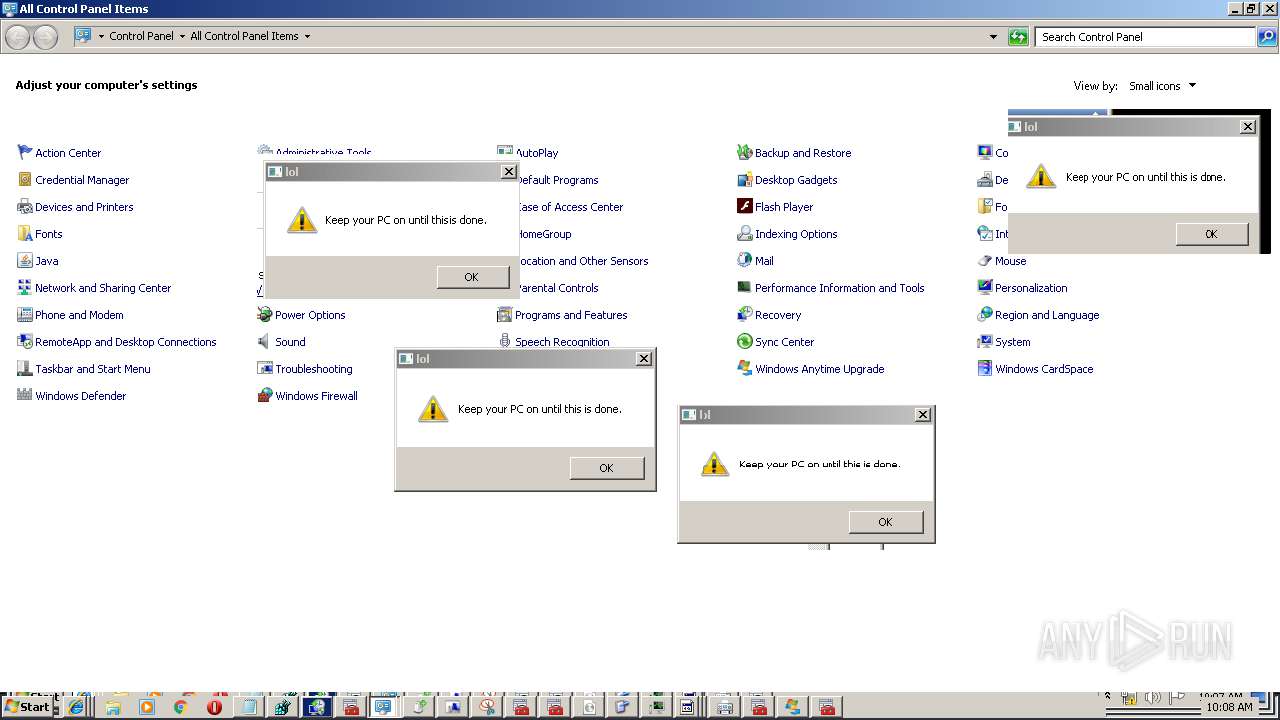
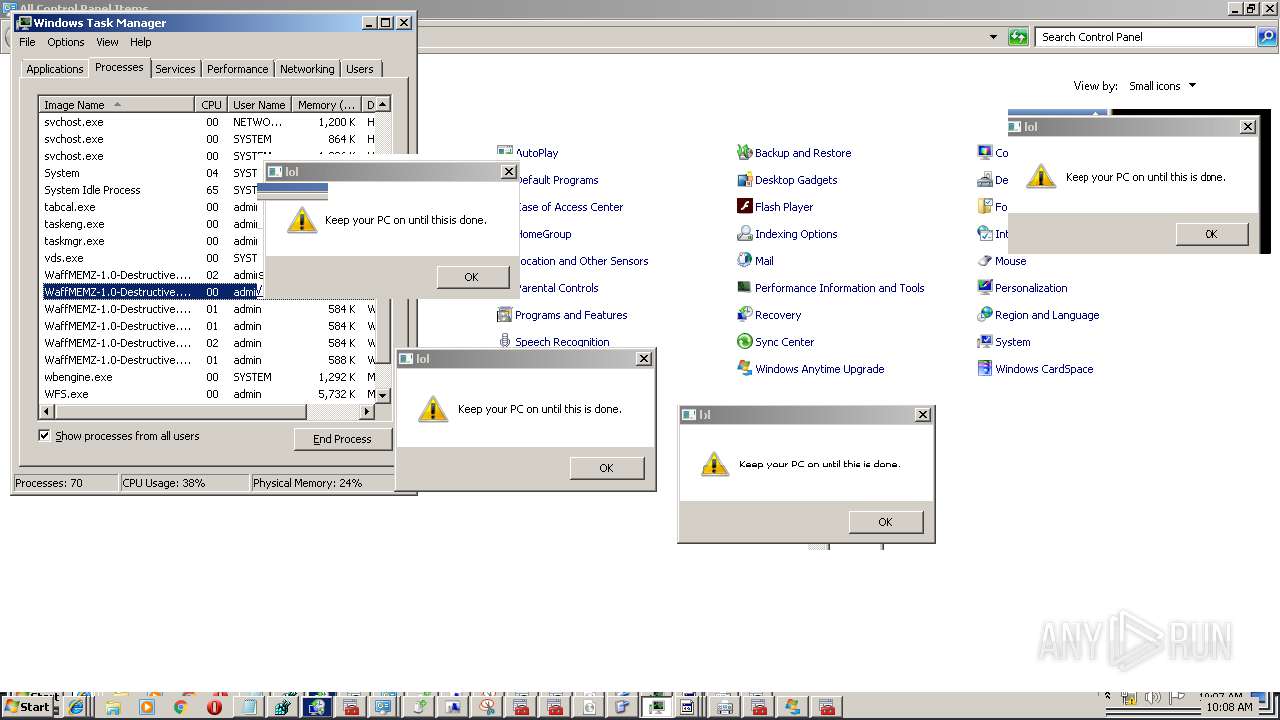
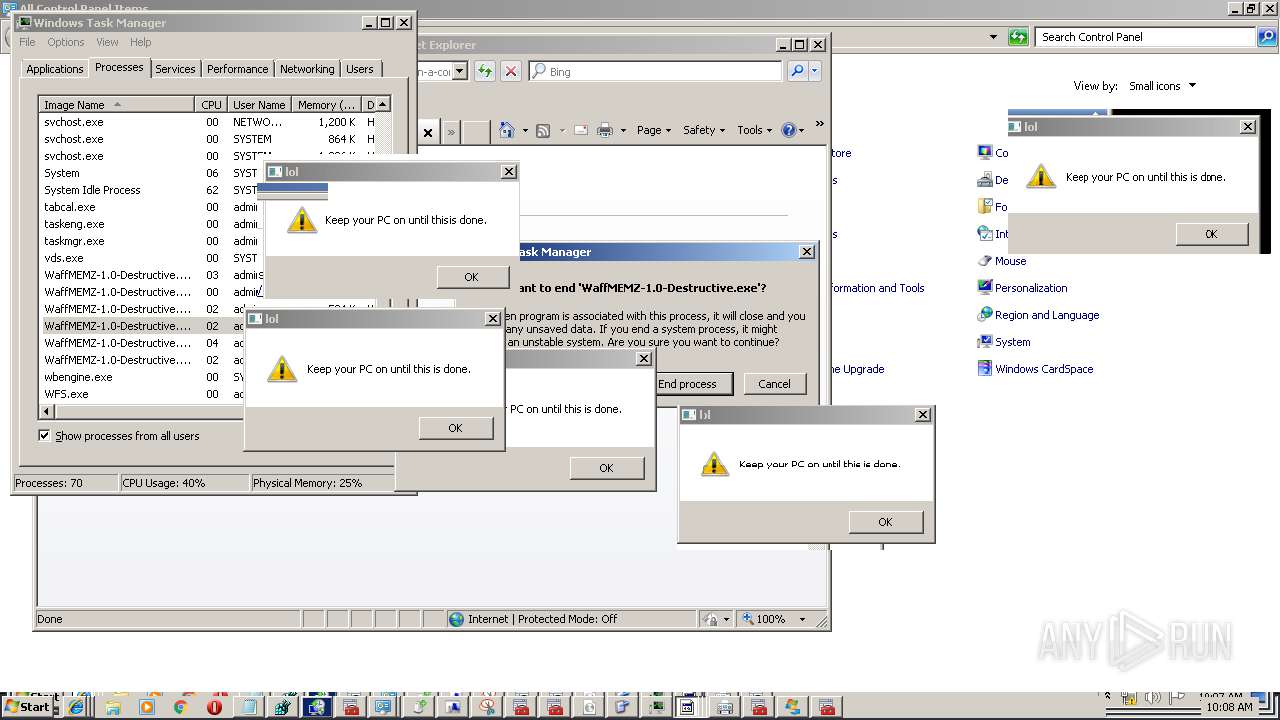
MALICIOUS
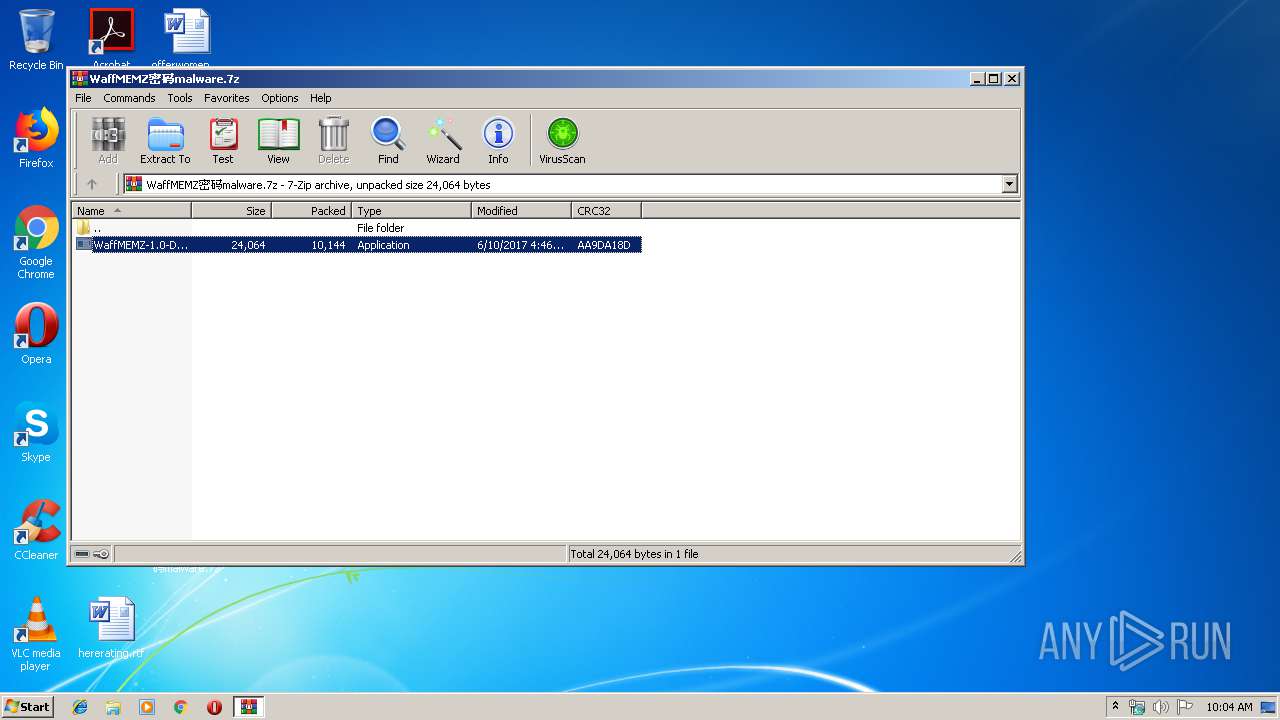
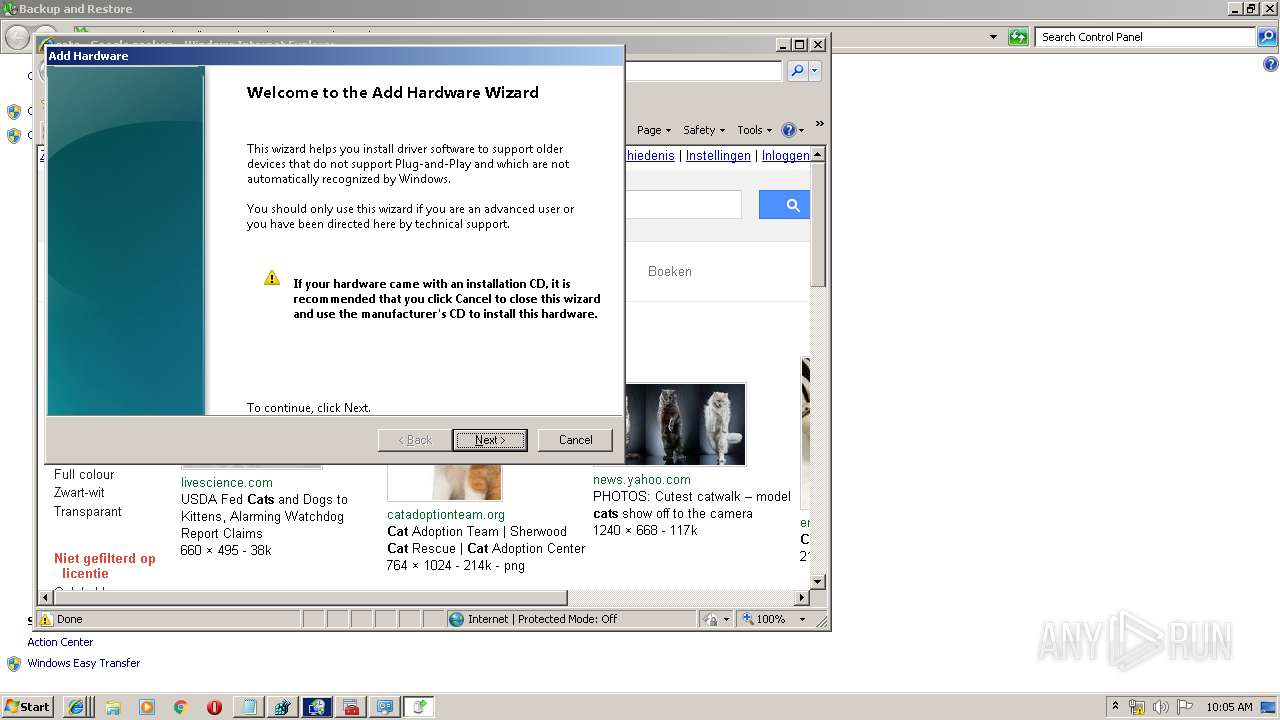
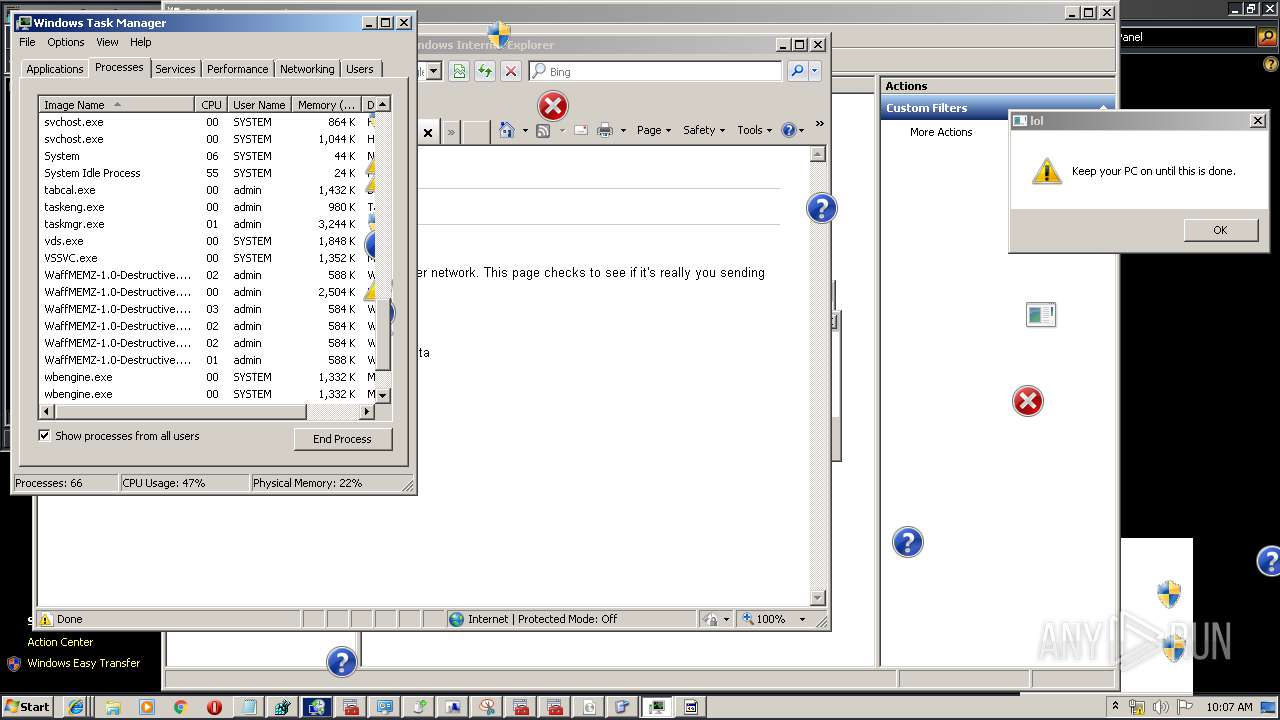
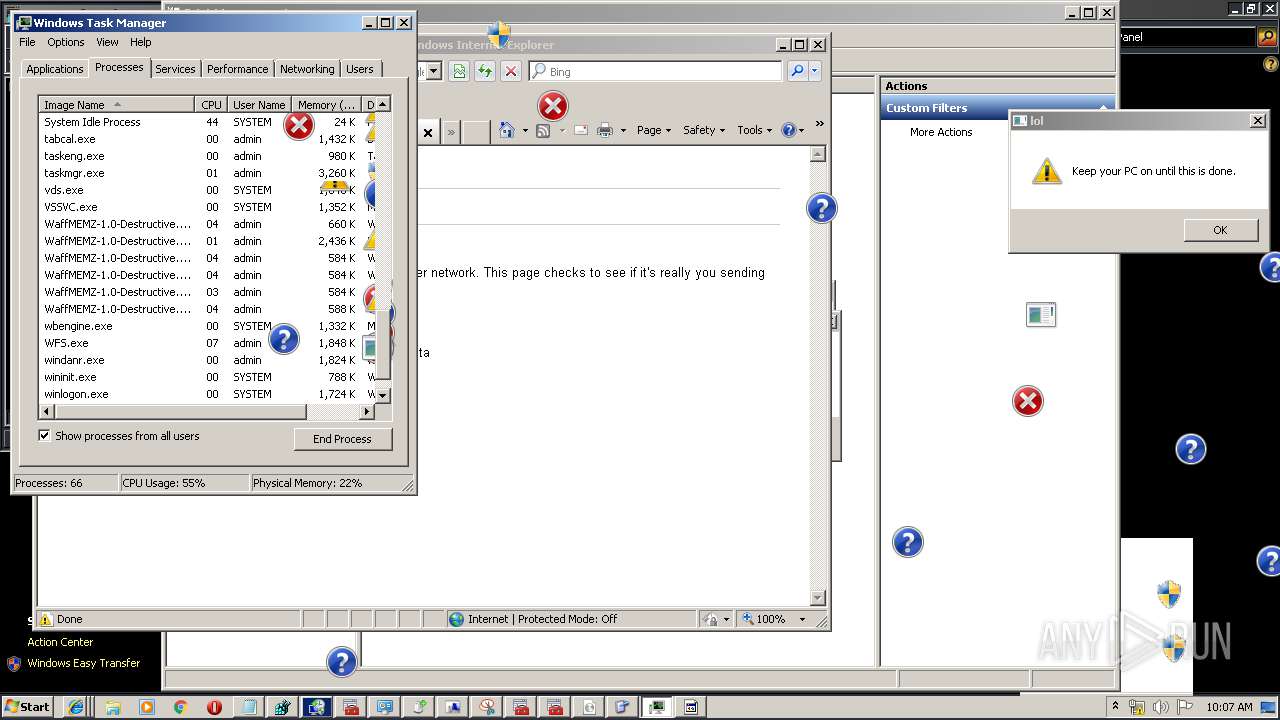
Application was dropped or rewritten from another process
- WaffMEMZ-1.0-Destructive.exe (PID: 3560)
- WaffMEMZ-1.0-Destructive.exe (PID: 3200)
- WaffMEMZ-1.0-Destructive.exe (PID: 2836)
- WaffMEMZ-1.0-Destructive.exe (PID: 2892)
- WaffMEMZ-1.0-Destructive.exe (PID: 3680)
- WaffMEMZ-1.0-Destructive.exe (PID: 2452)
- WaffMEMZ-1.0-Destructive.exe (PID: 4052)
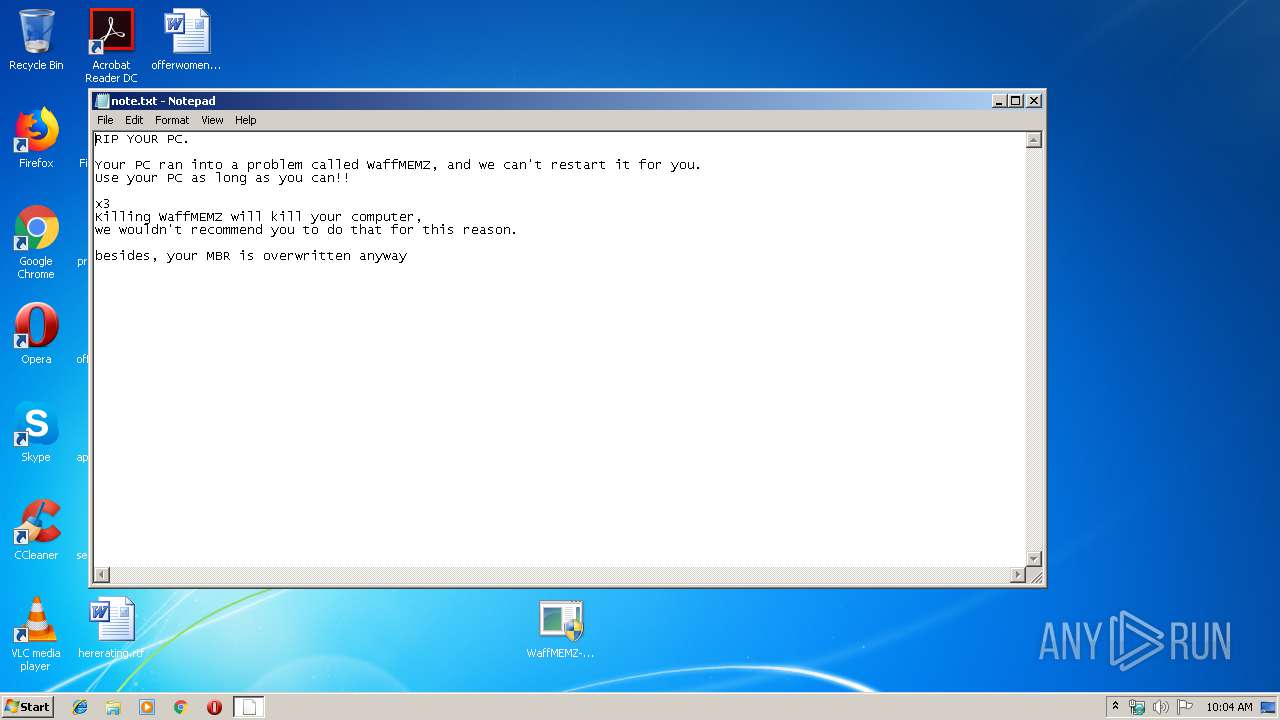
Low-level write access rights to disk partition
- WaffMEMZ-1.0-Destructive.exe (PID: 2836)
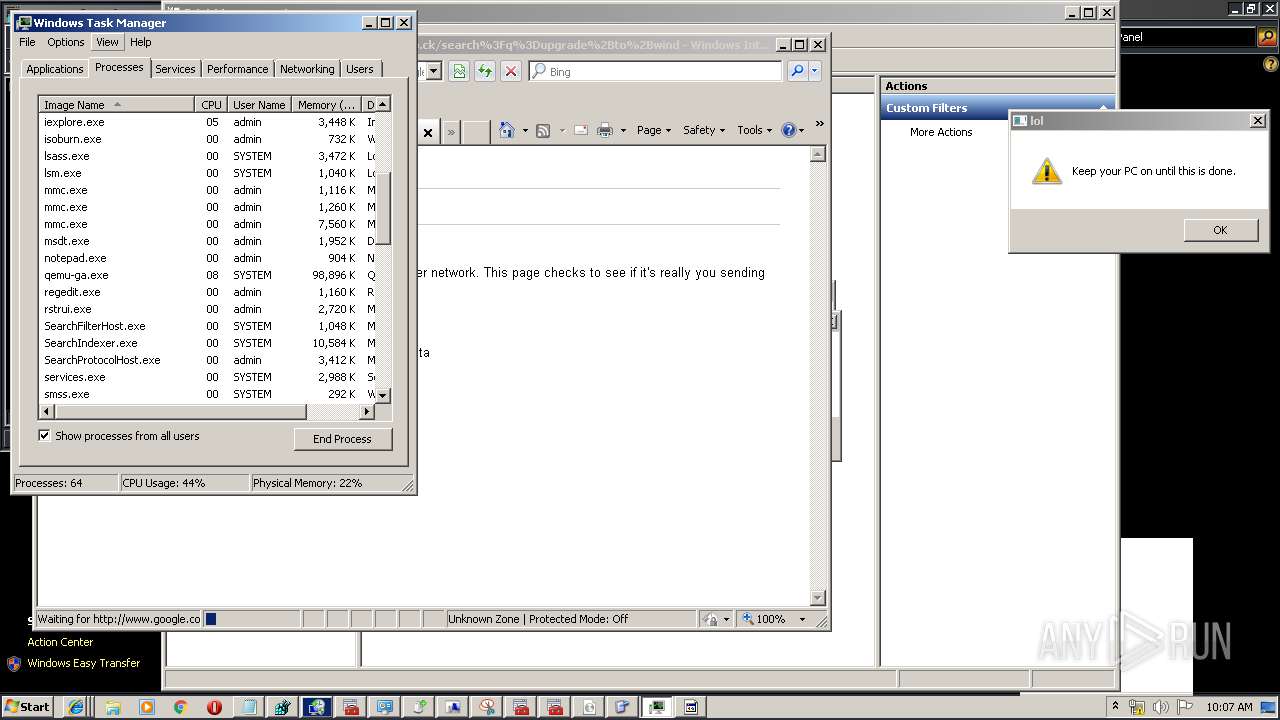
Runs injected code in another process
- rstrui.exe (PID: 3056)
Application was injected by another process
- SearchIndexer.exe (PID: 332)
- svchost.exe (PID: 1044)
- svchost.exe (PID: 852)
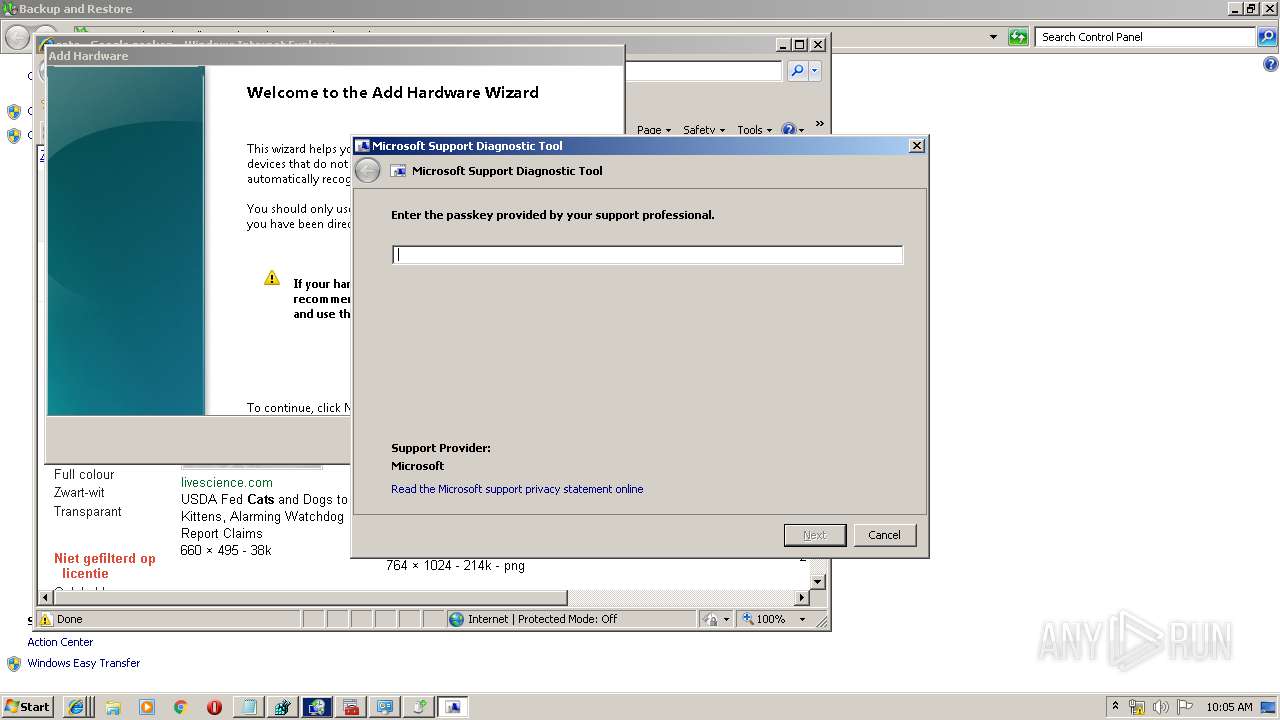
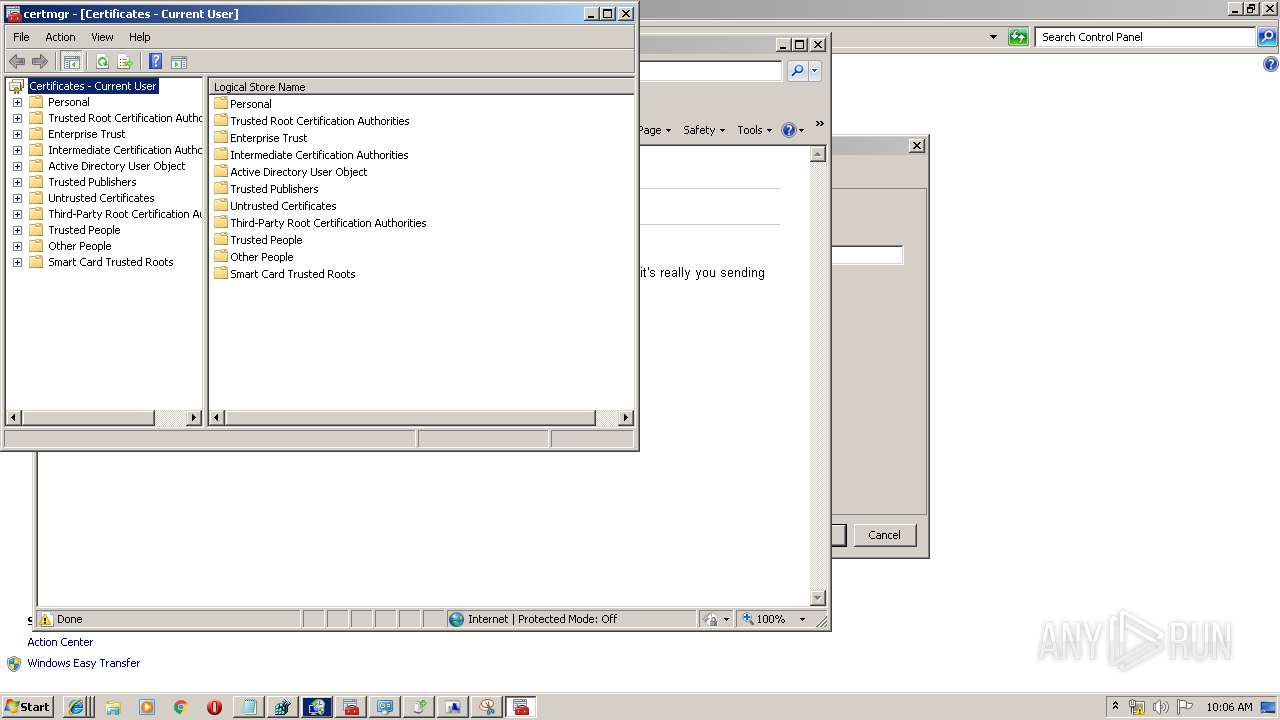
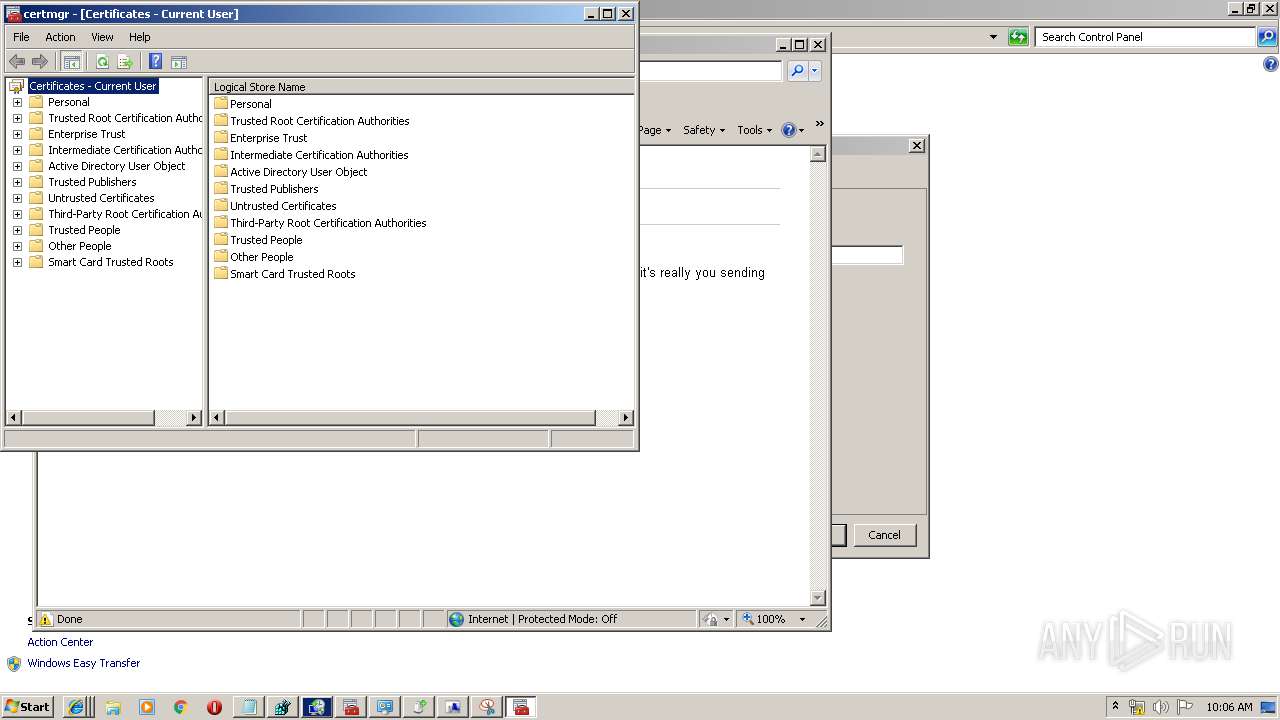
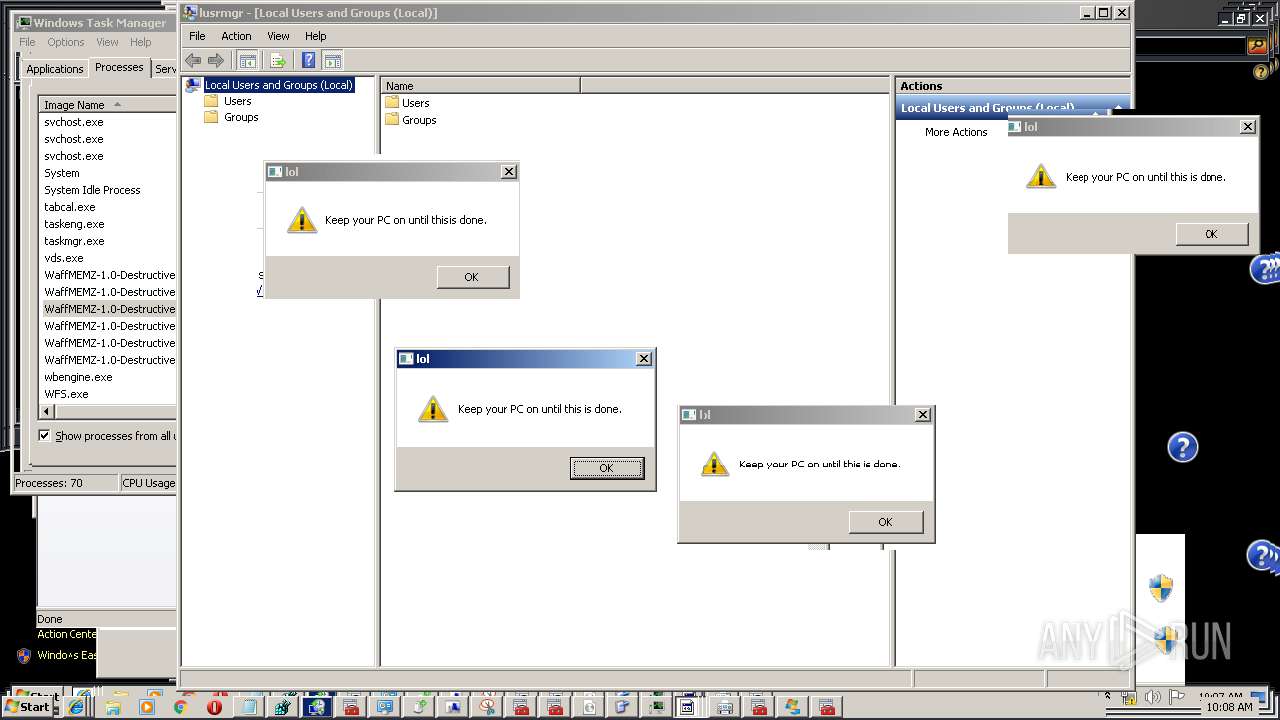
Changes settings of System certificates
- svchost.exe (PID: 1044)
SUSPICIOUS
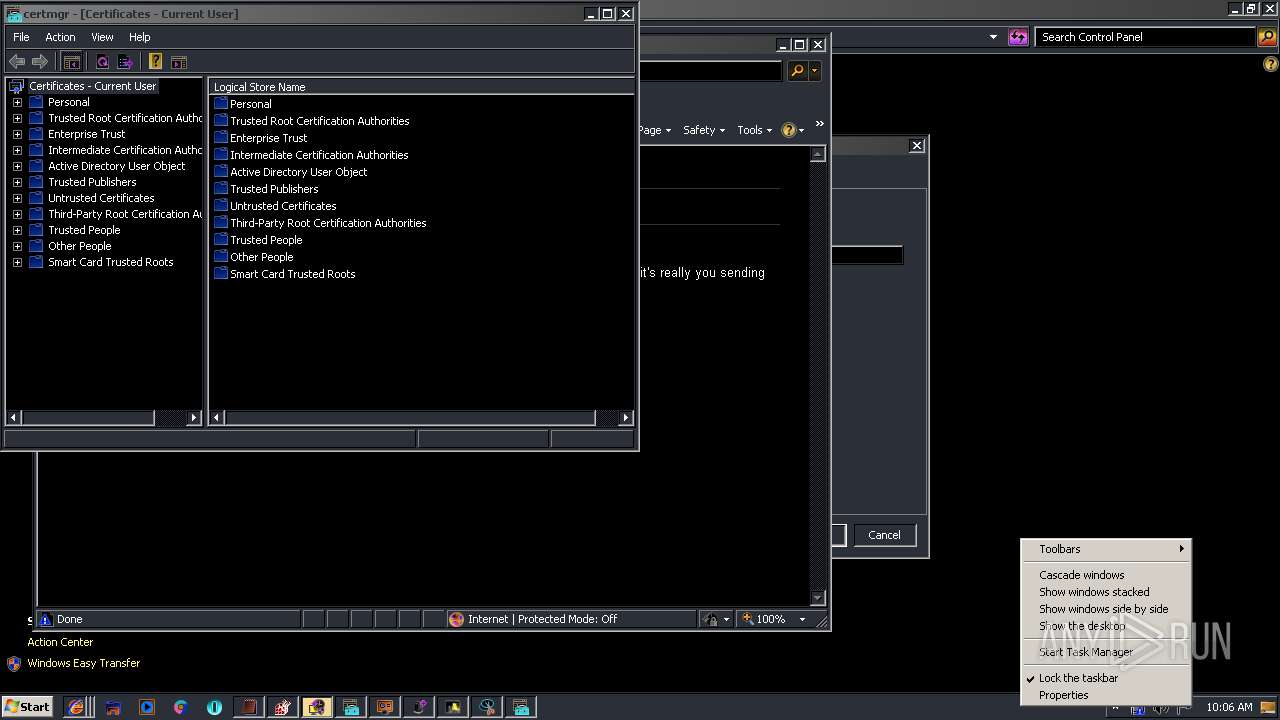
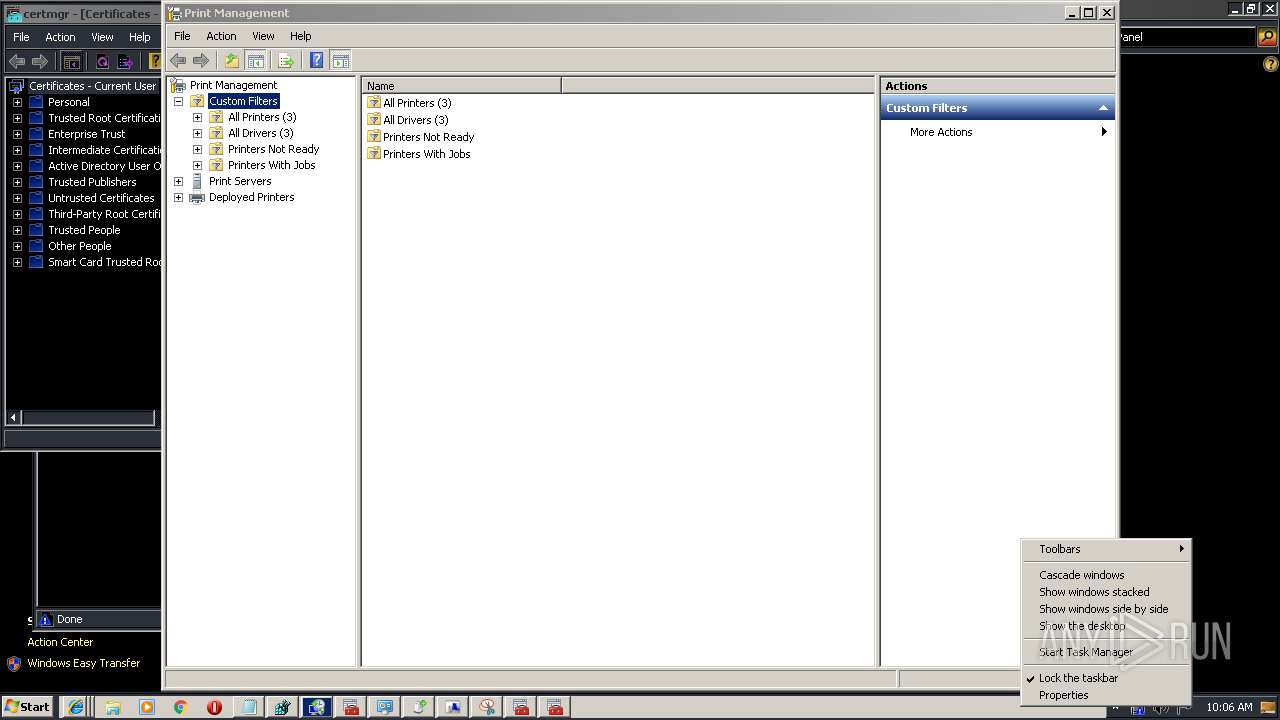
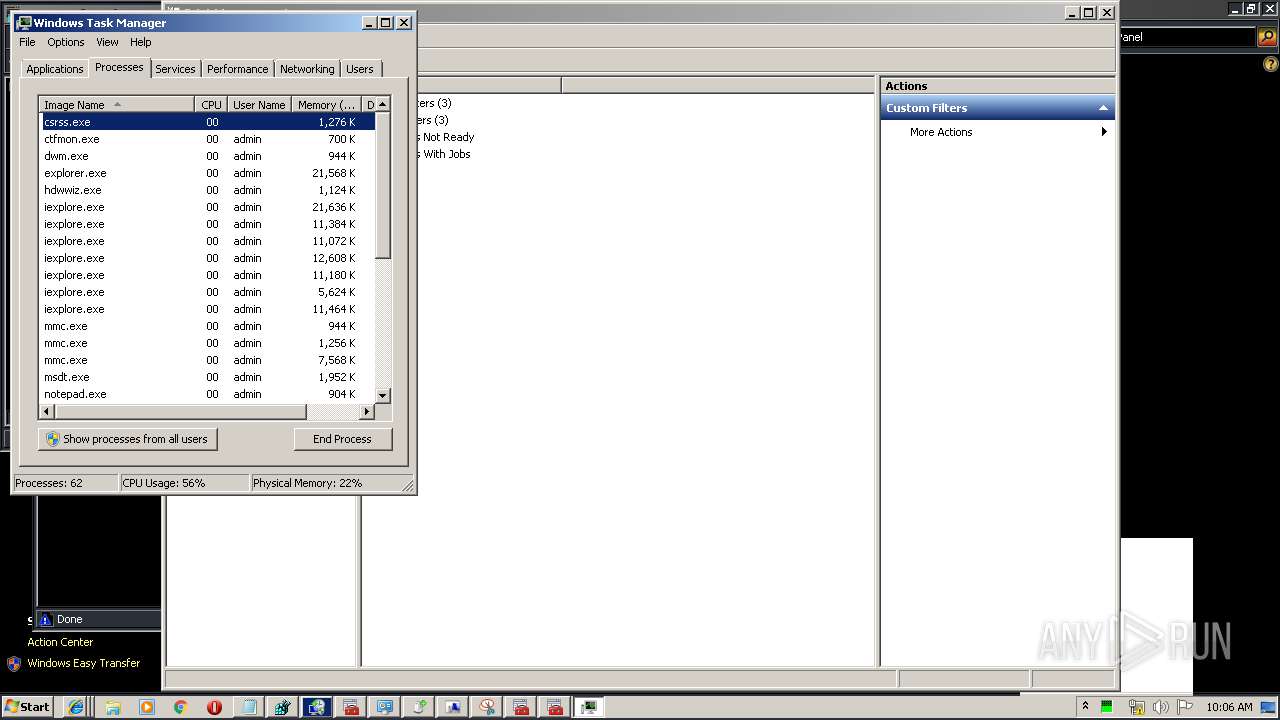
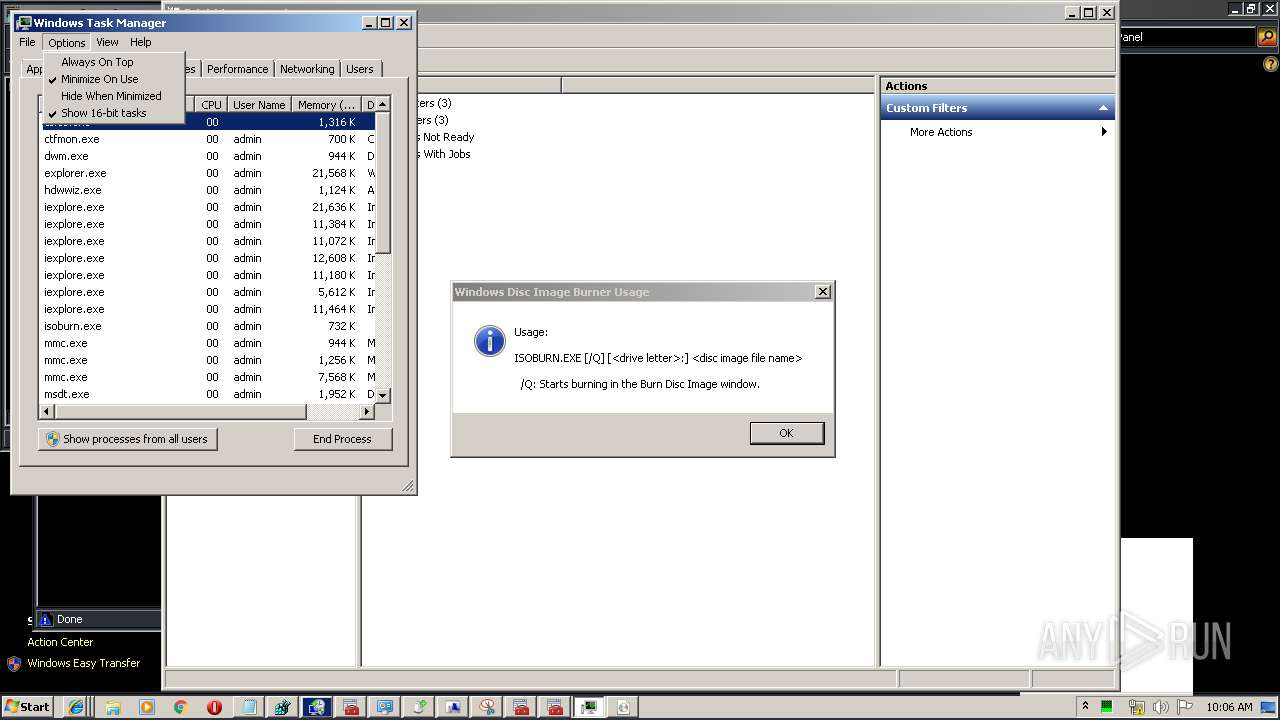
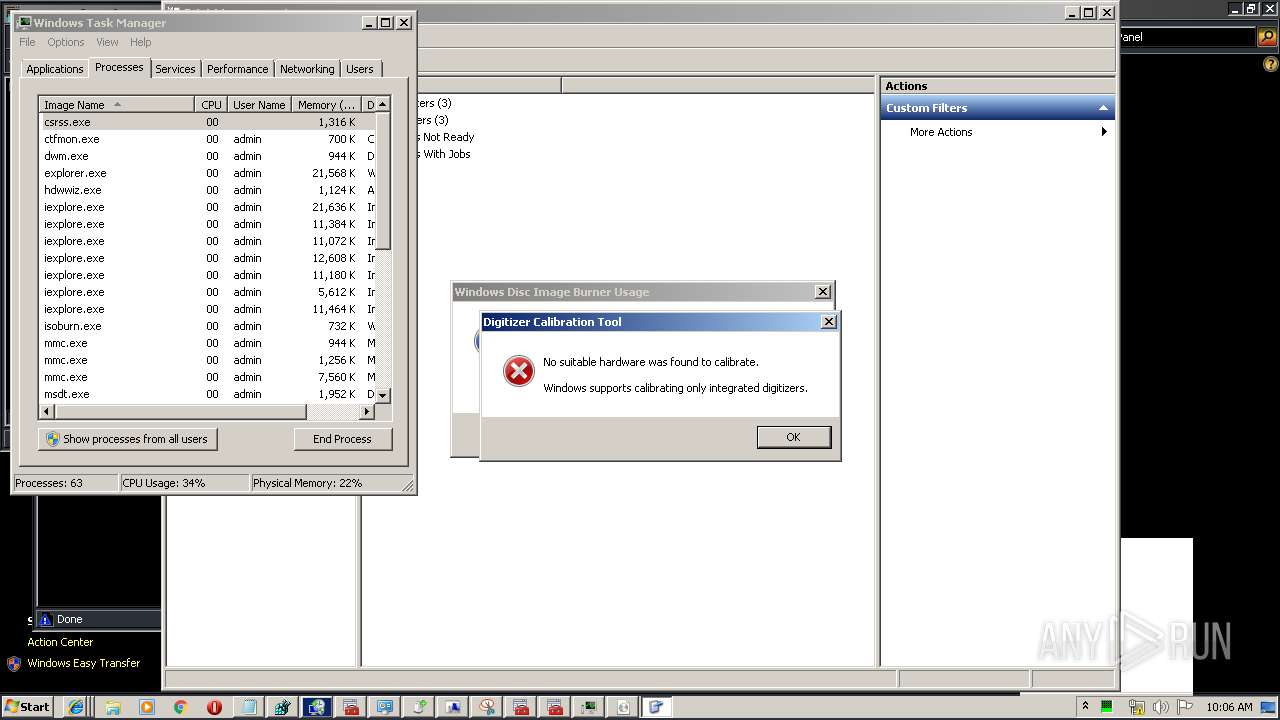
Application launched itself
- WaffMEMZ-1.0-Destructive.exe (PID: 3560)
- taskmgr.exe (PID: 3700)
Low-level read access rights to disk partition
- WaffMEMZ-1.0-Destructive.exe (PID: 2836)
- wbengine.exe (PID: 3996)
- vds.exe (PID: 2584)
Creates files in the user directory
- WaffMEMZ-1.0-Destructive.exe (PID: 2836)
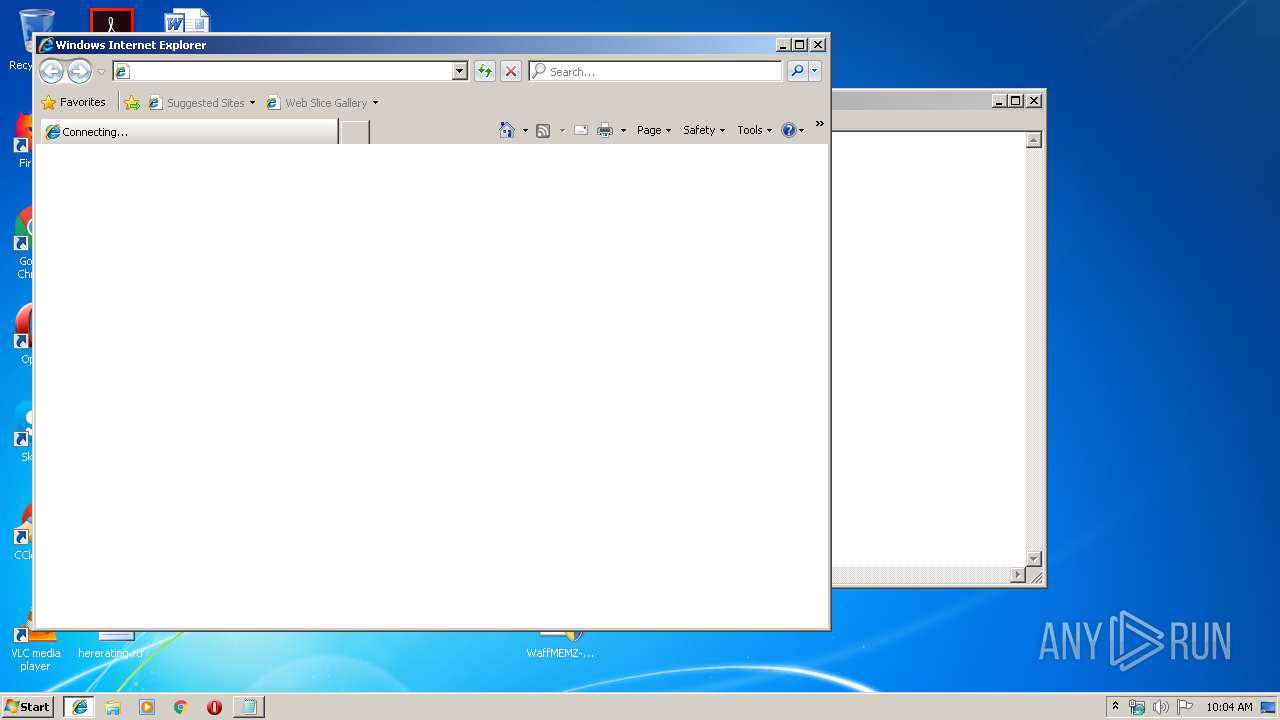
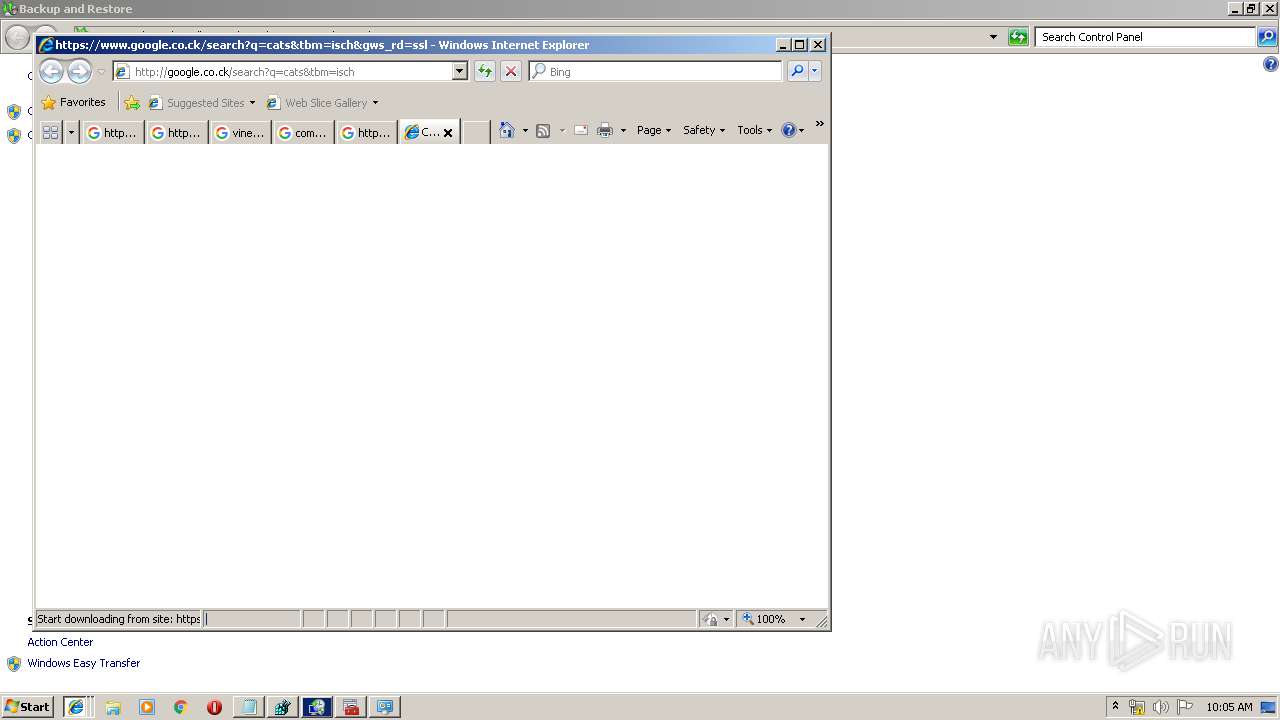
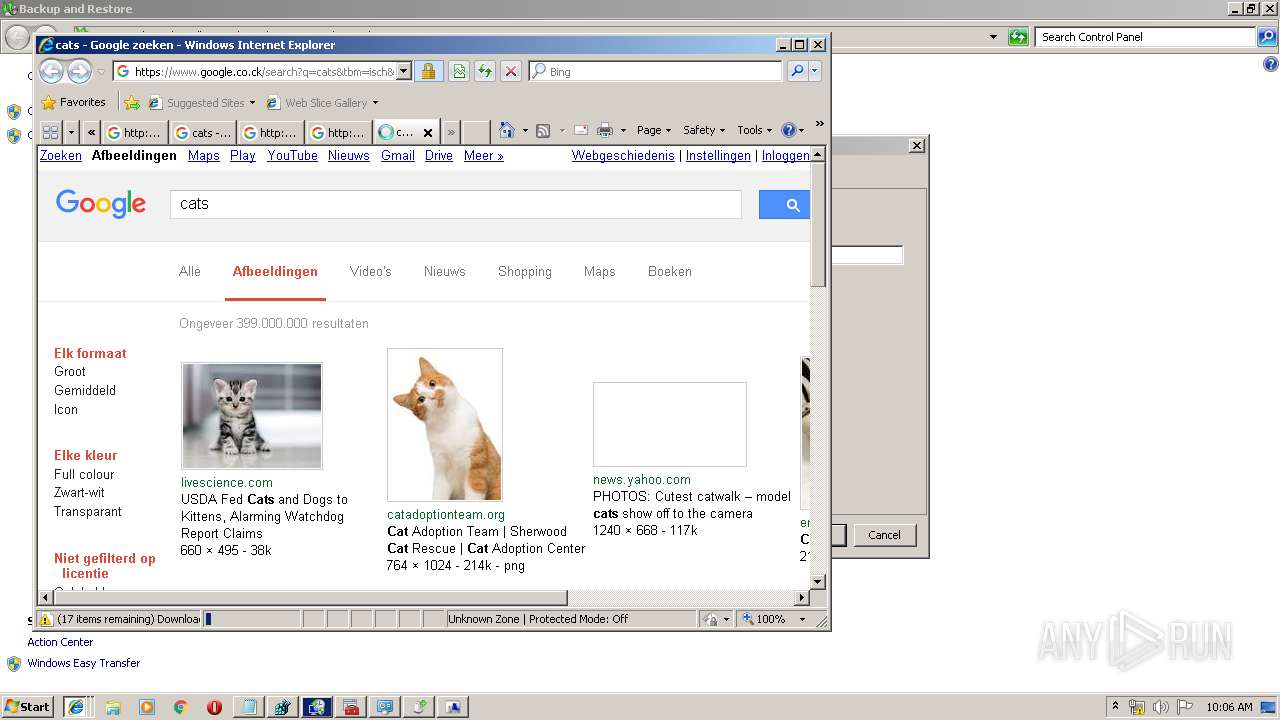
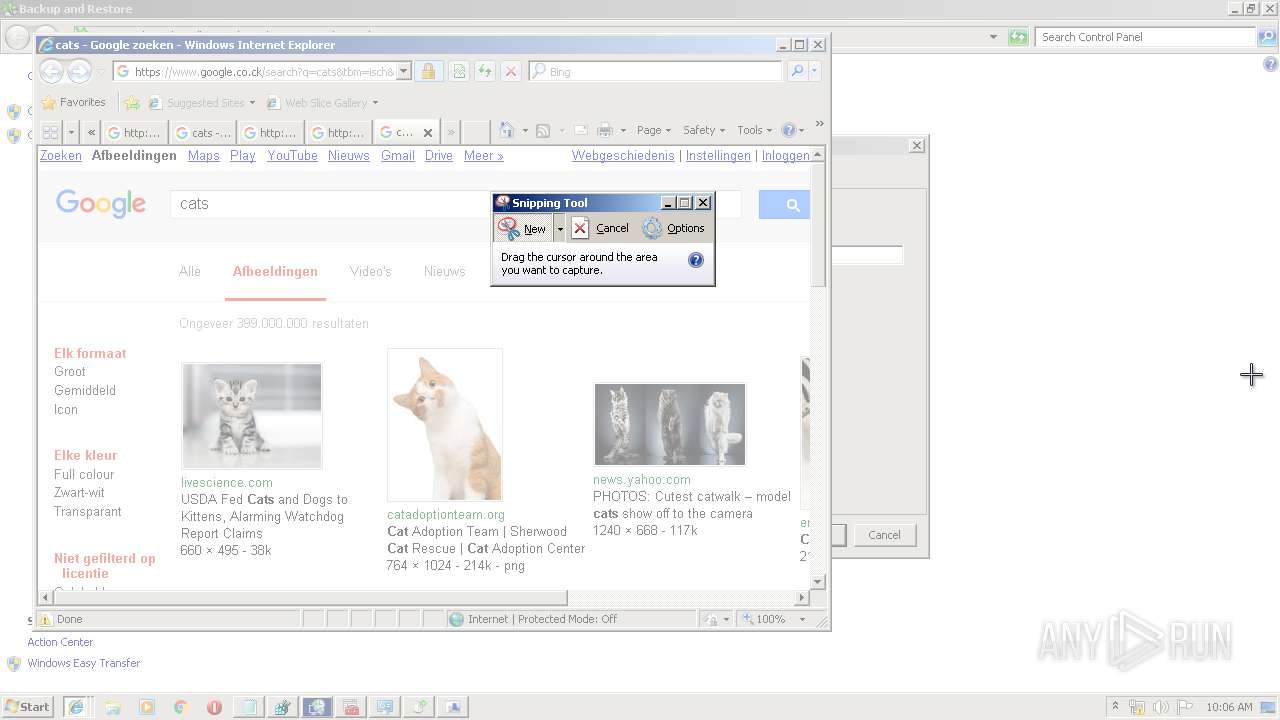
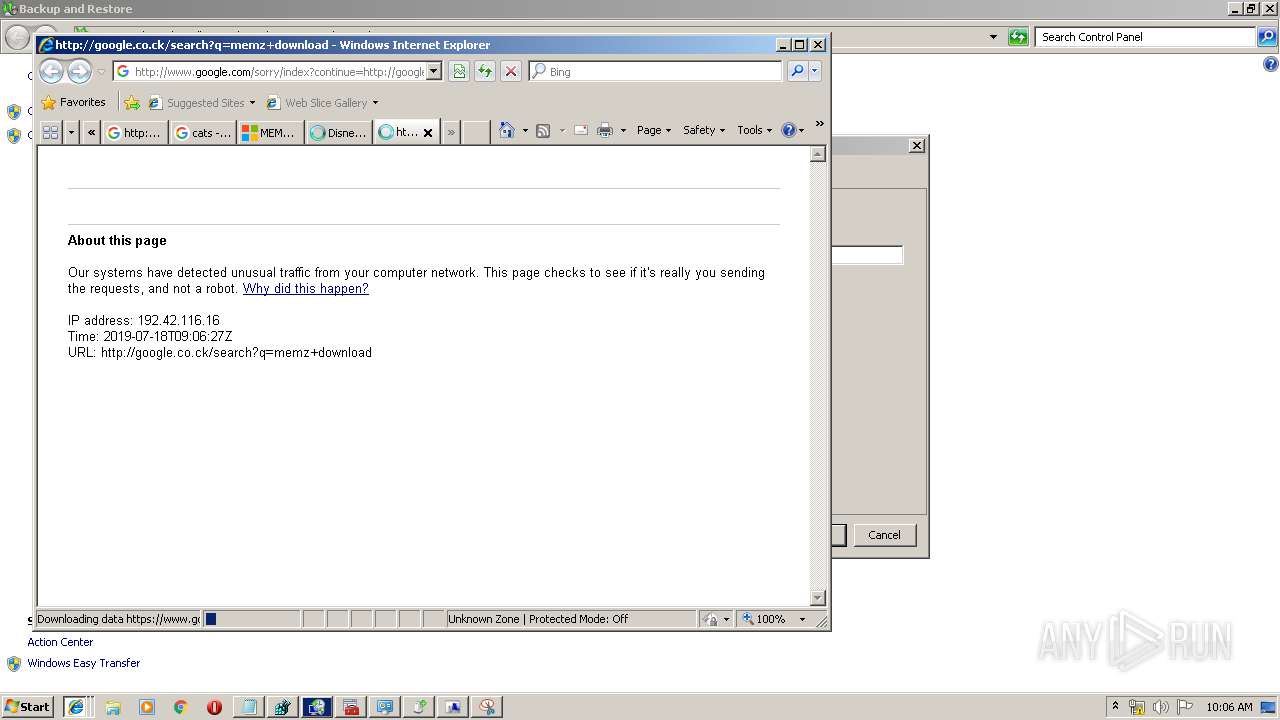
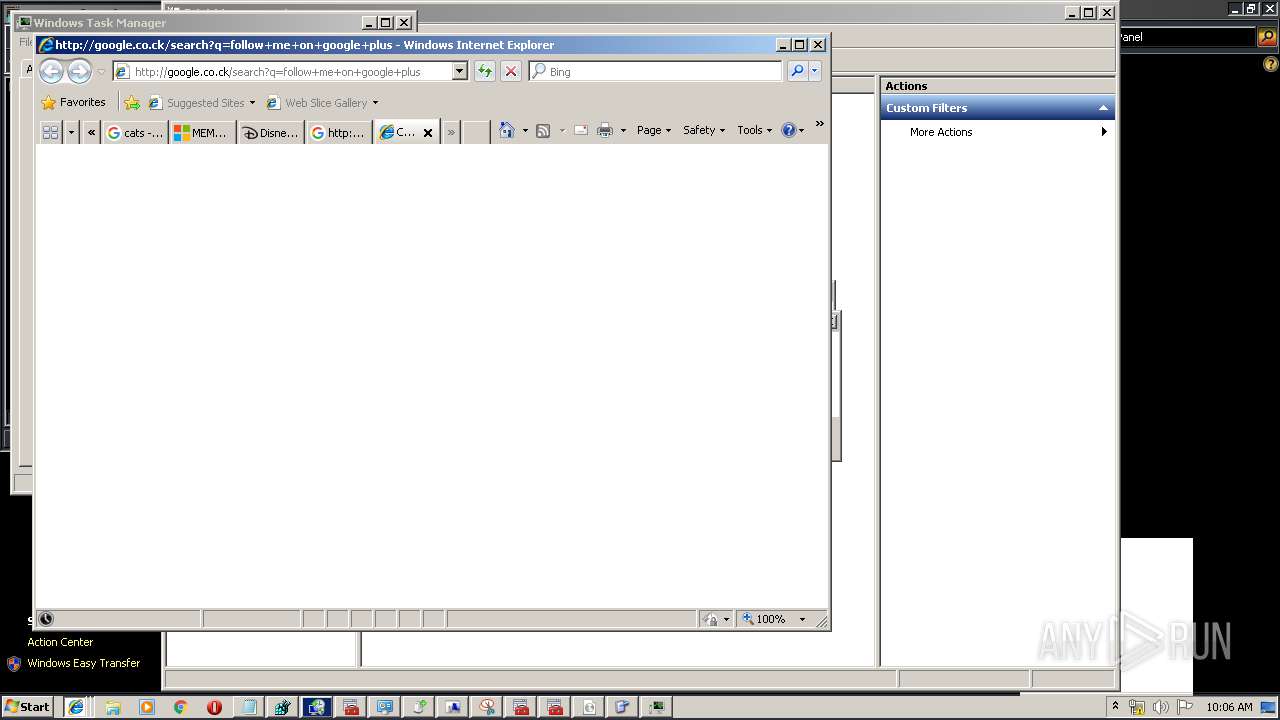
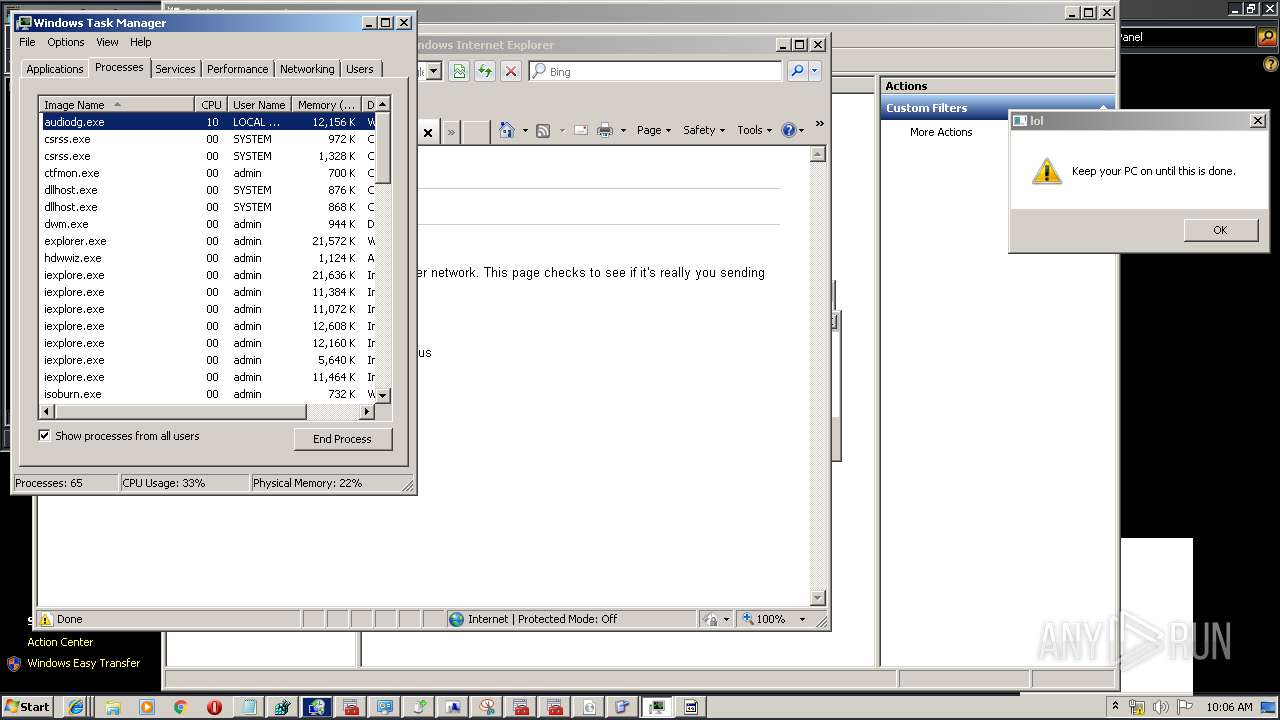
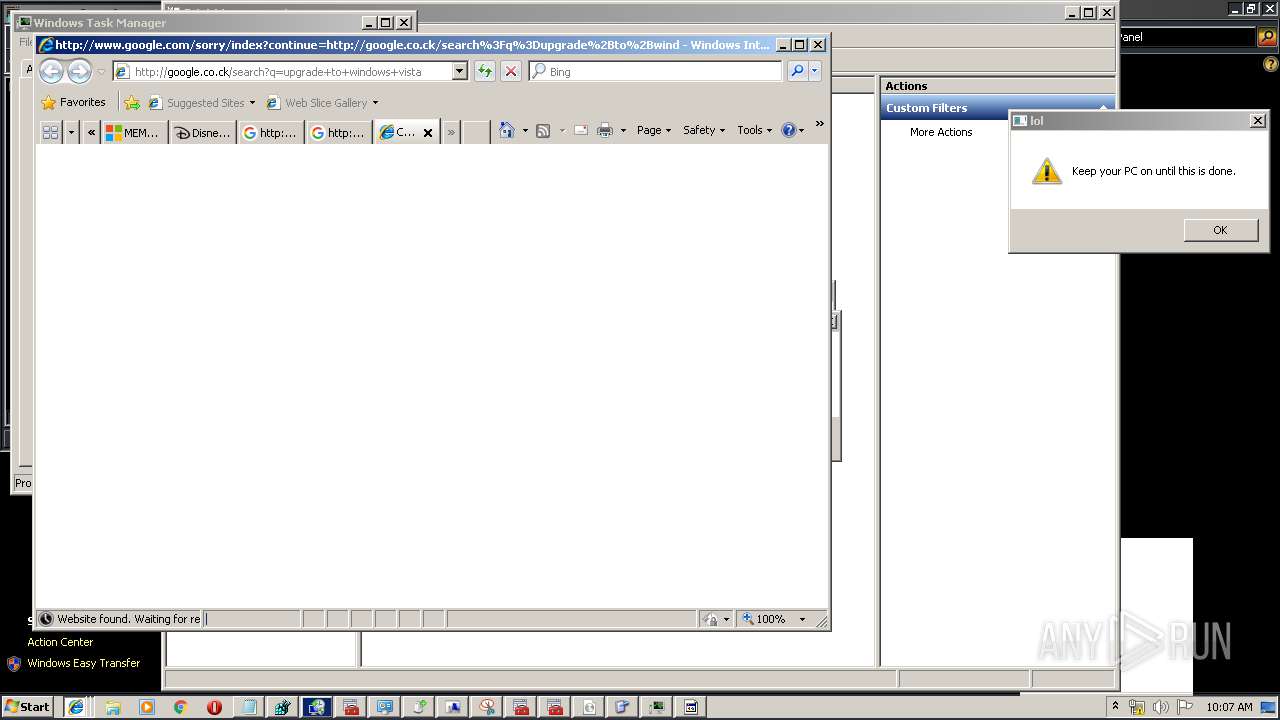
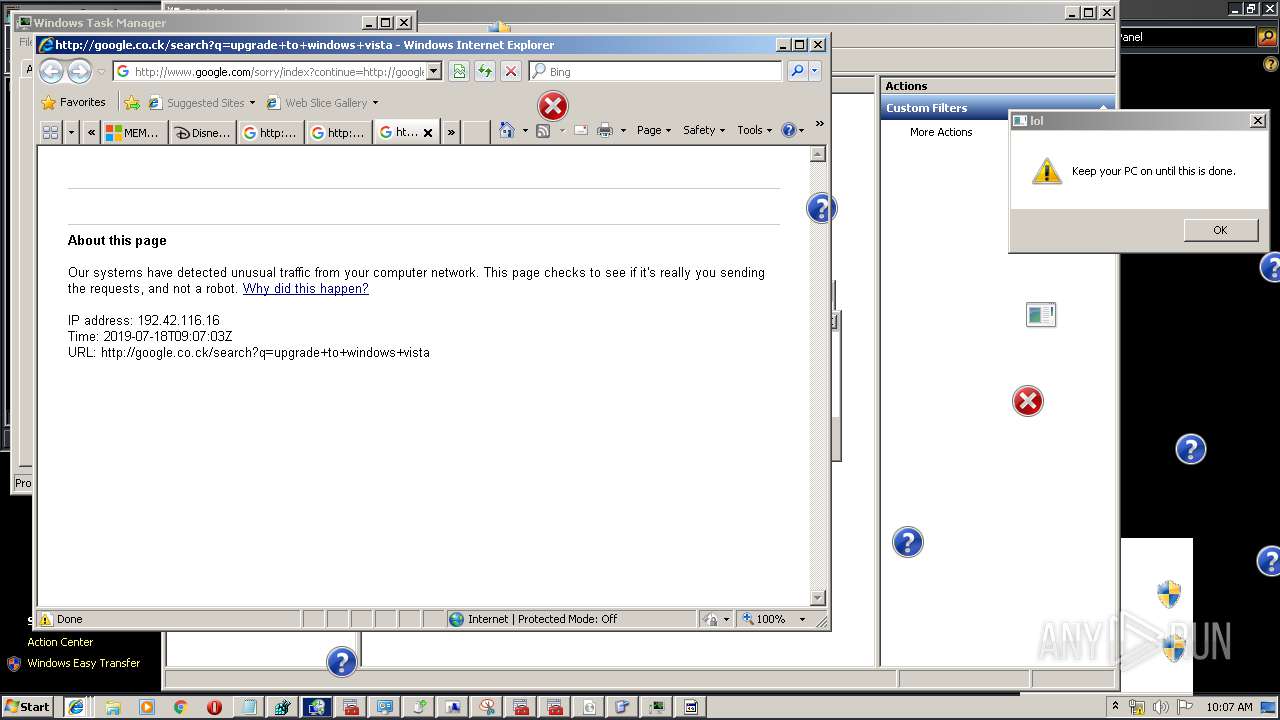
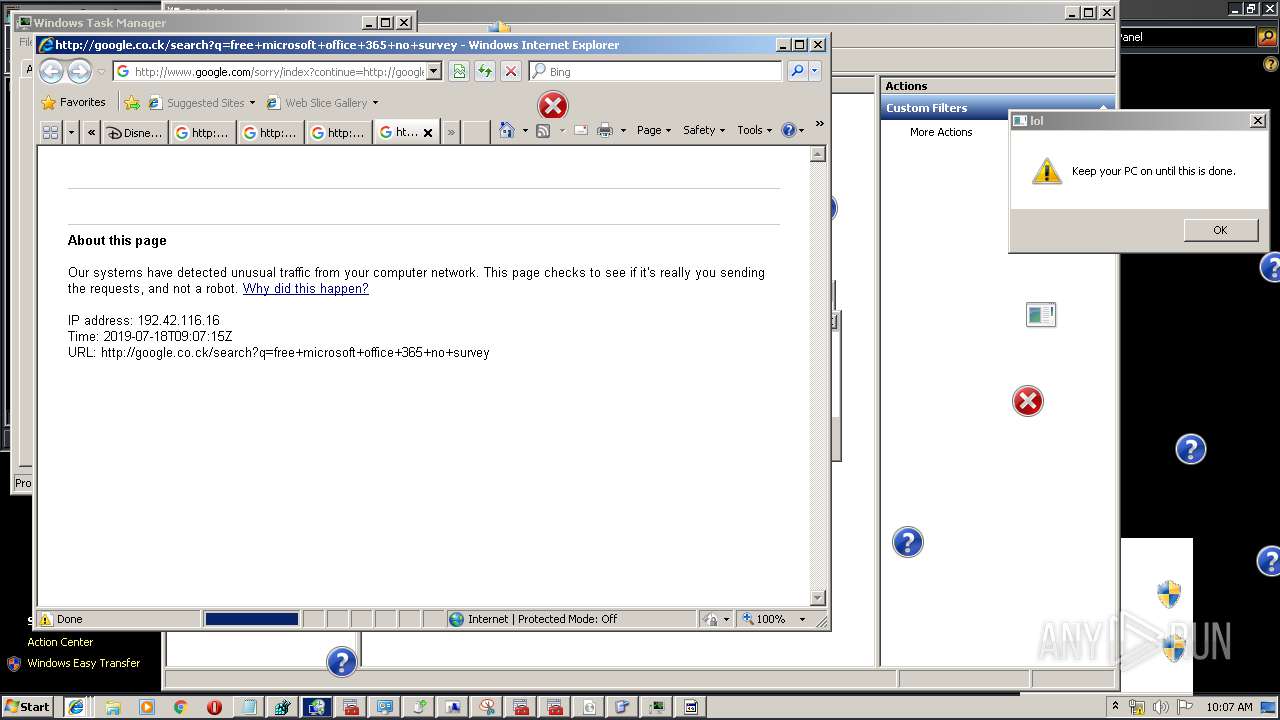
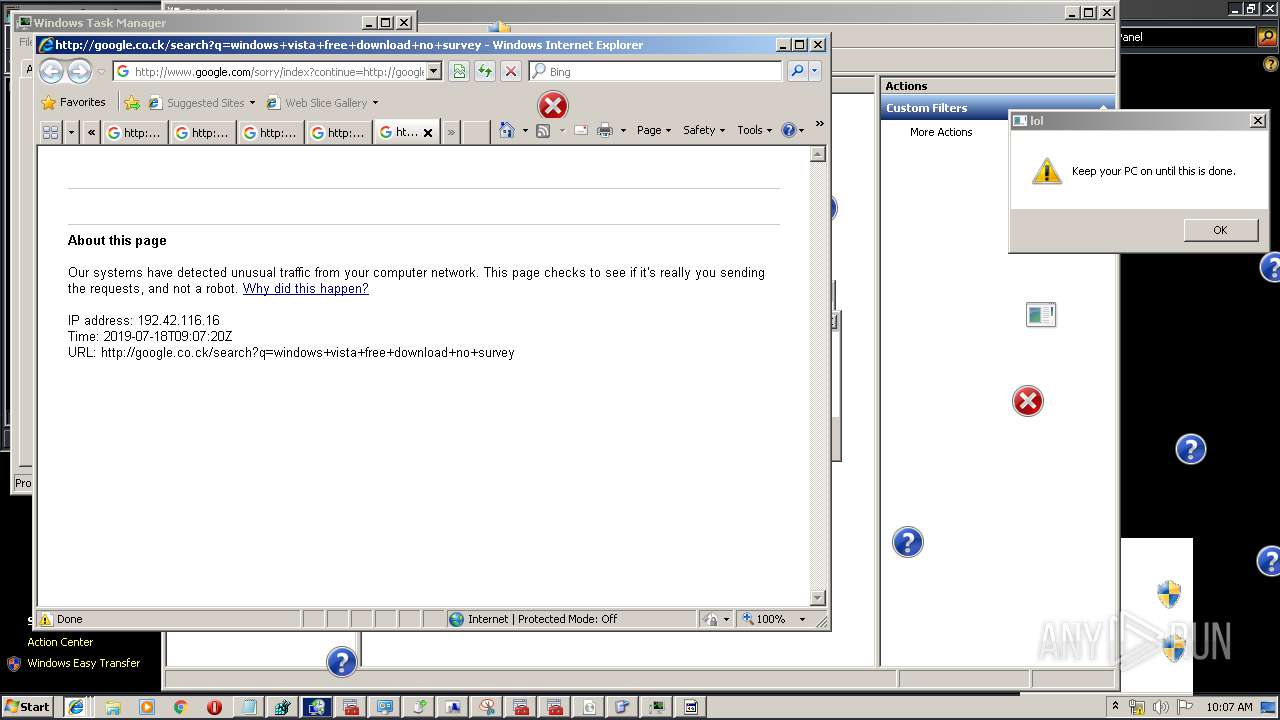
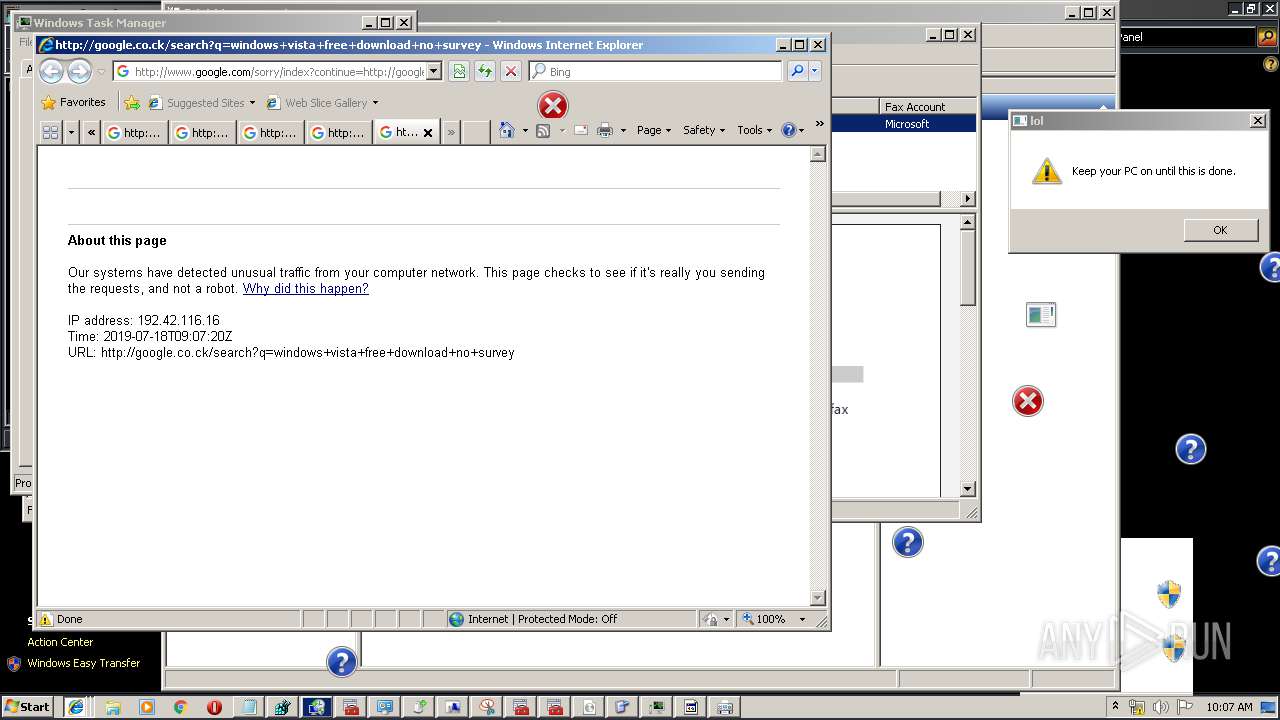
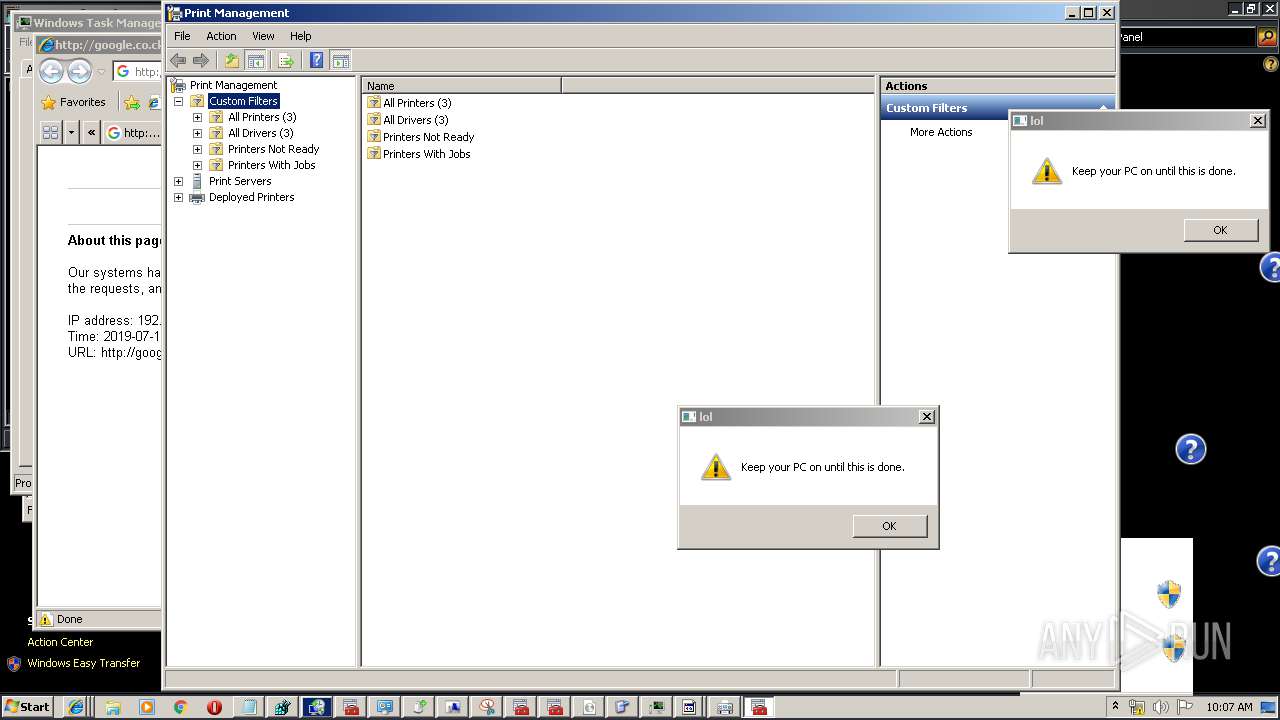
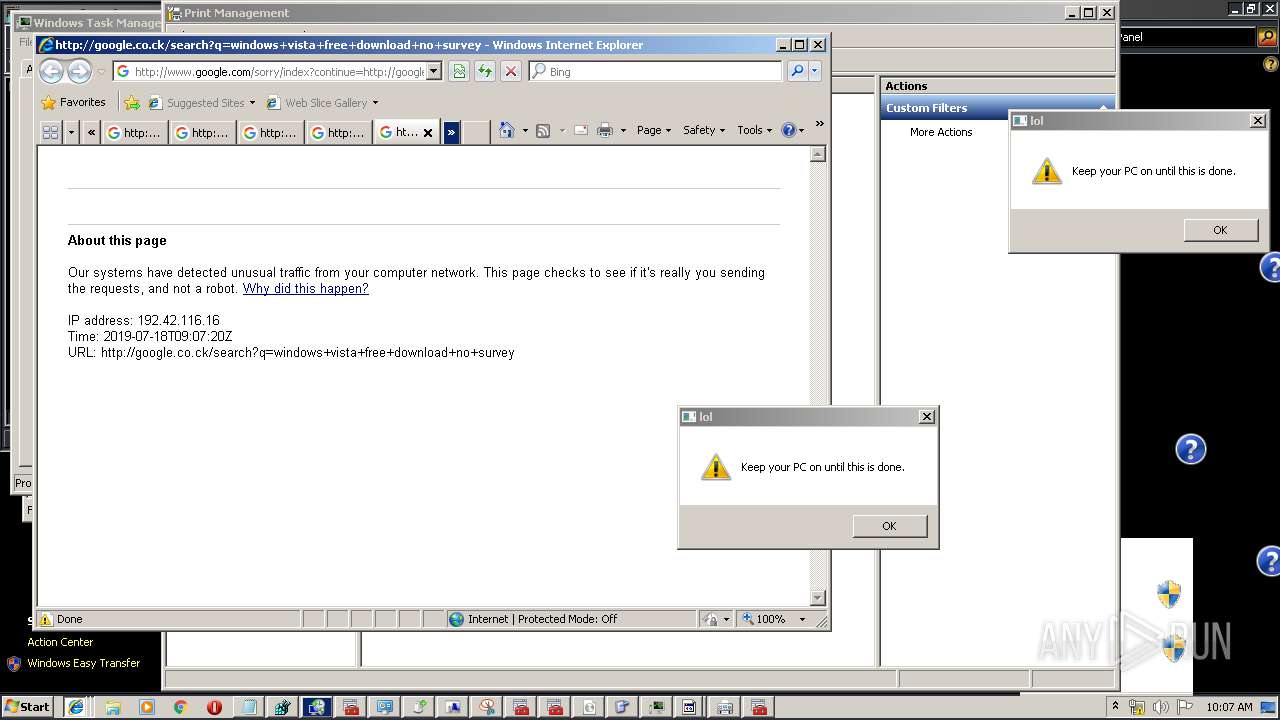
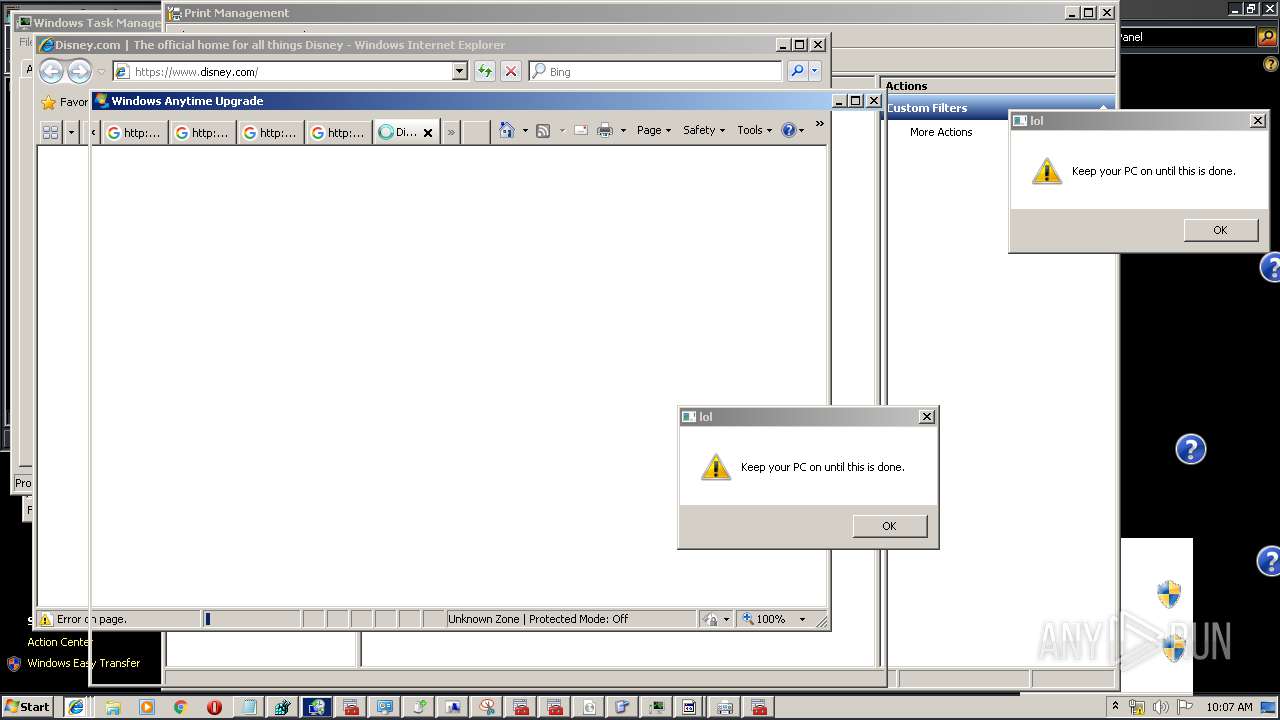
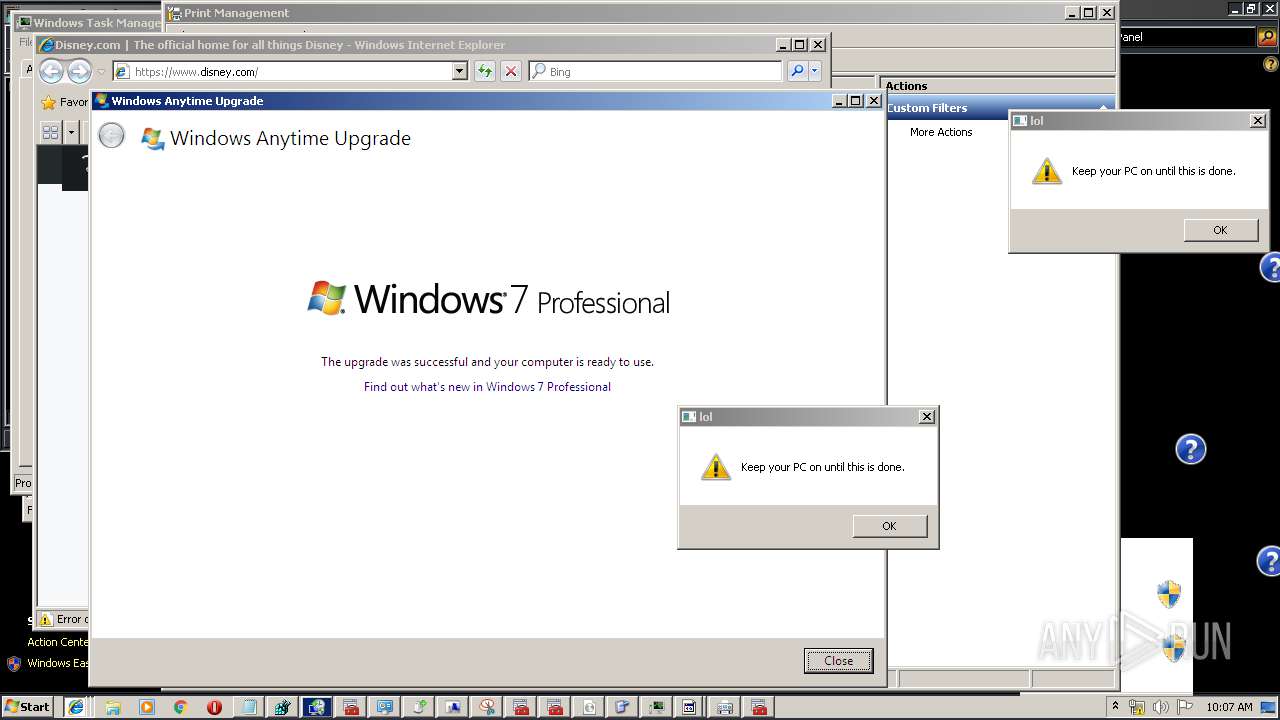
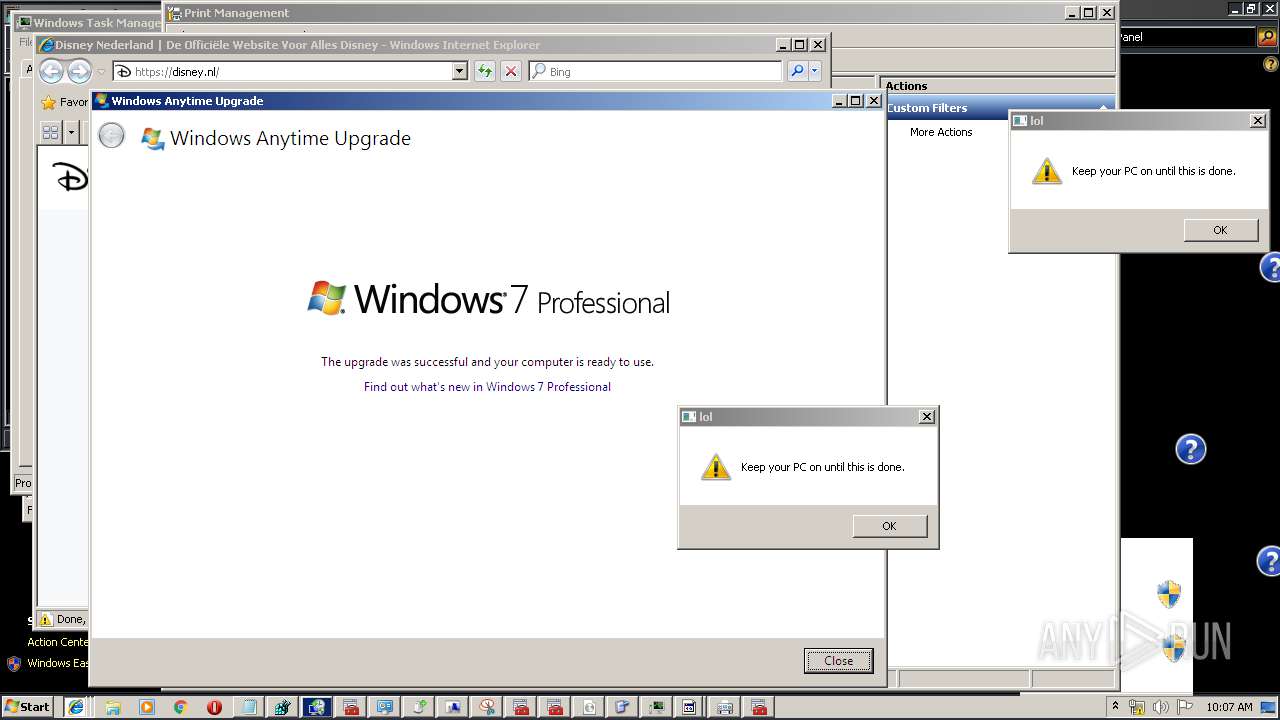
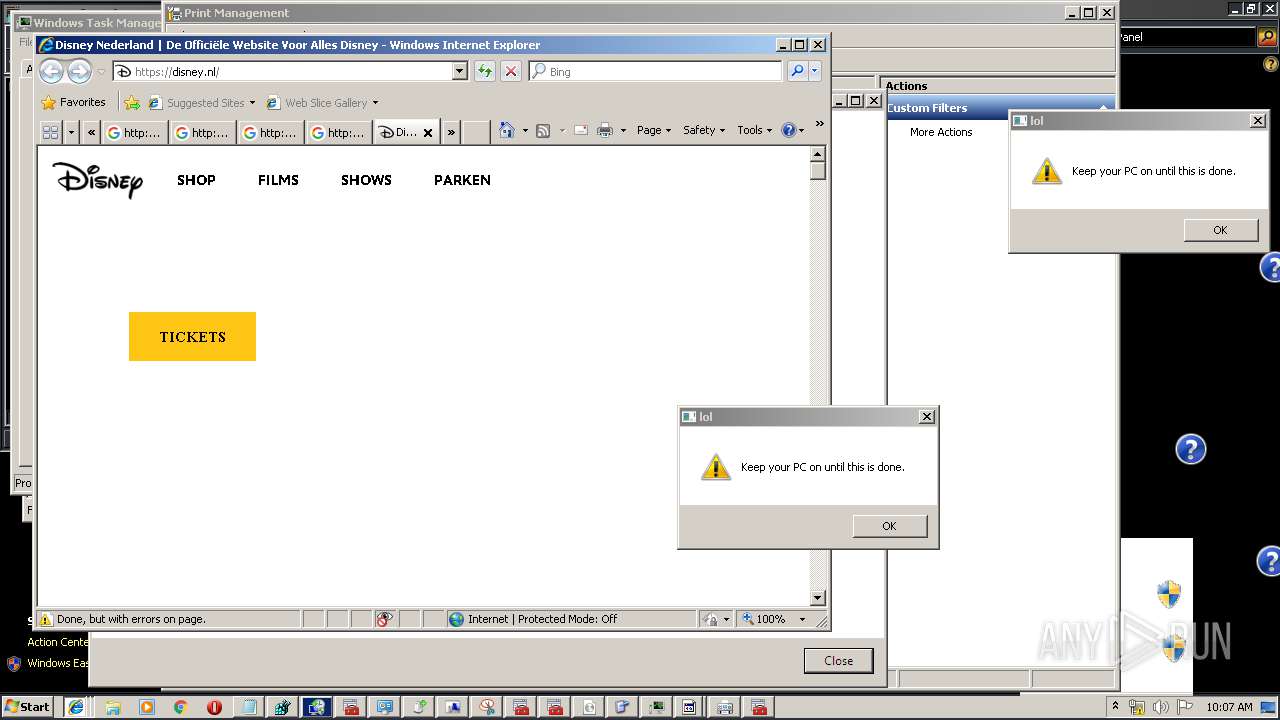
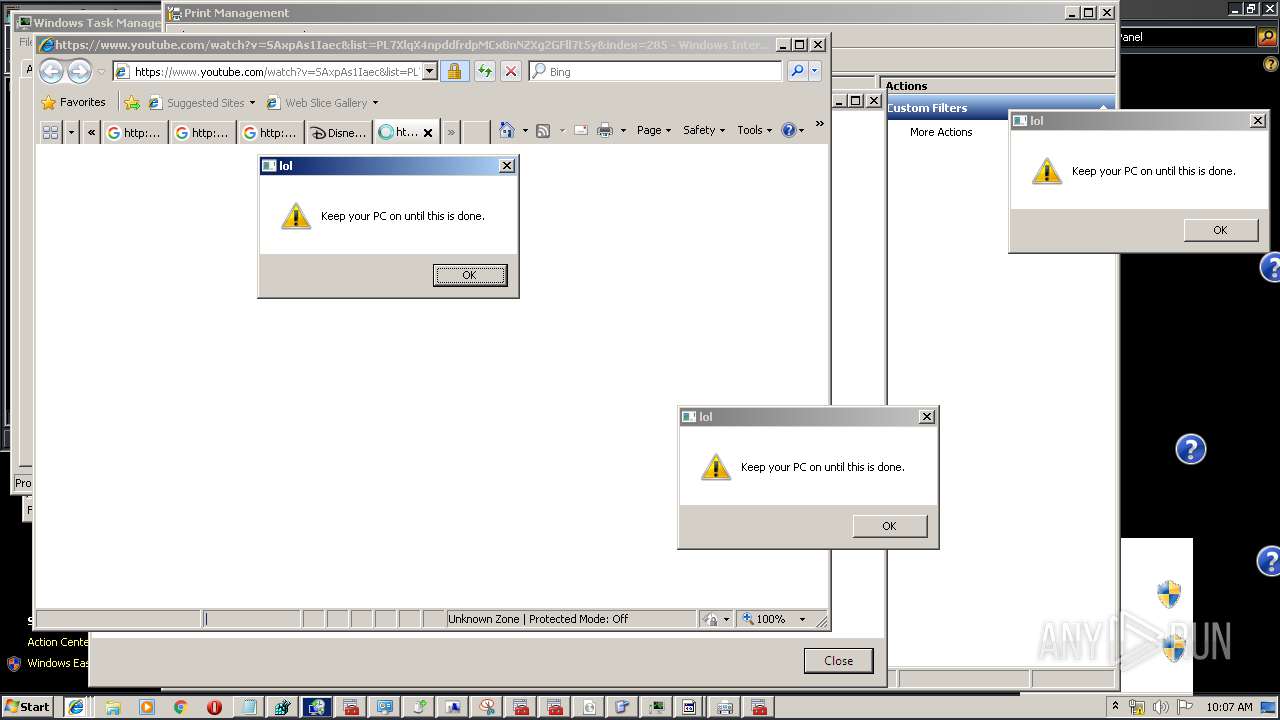
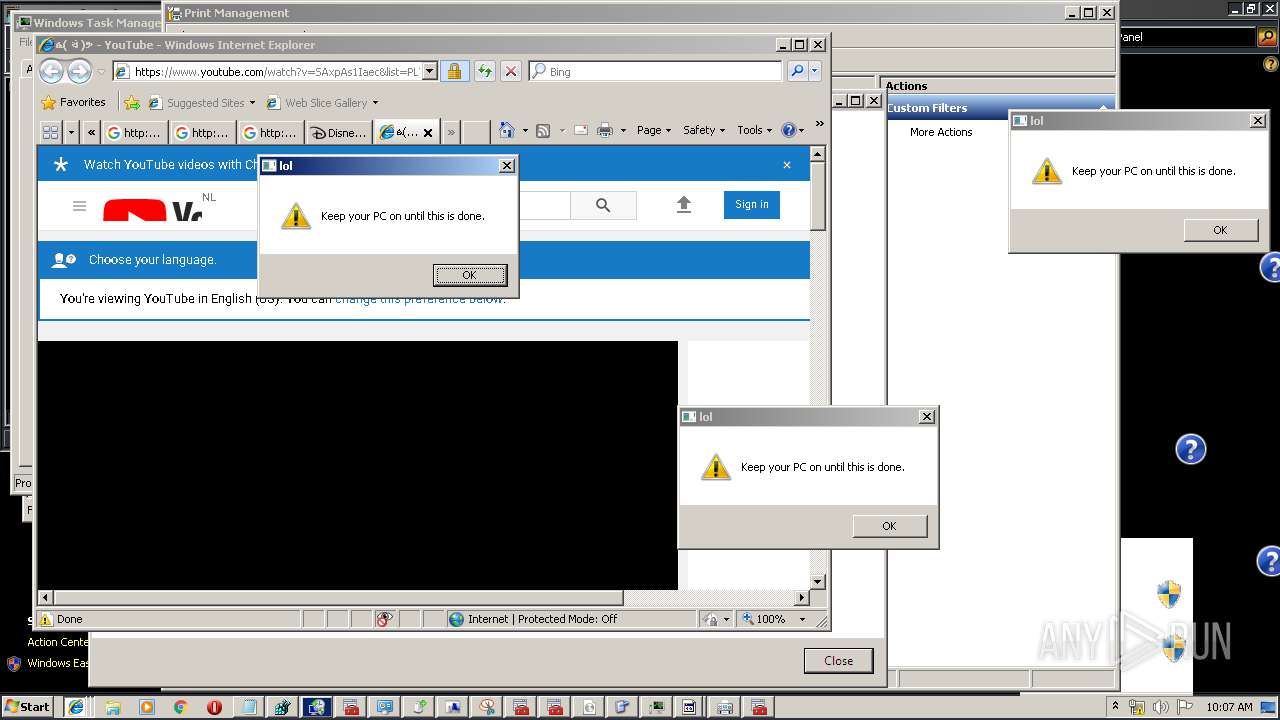
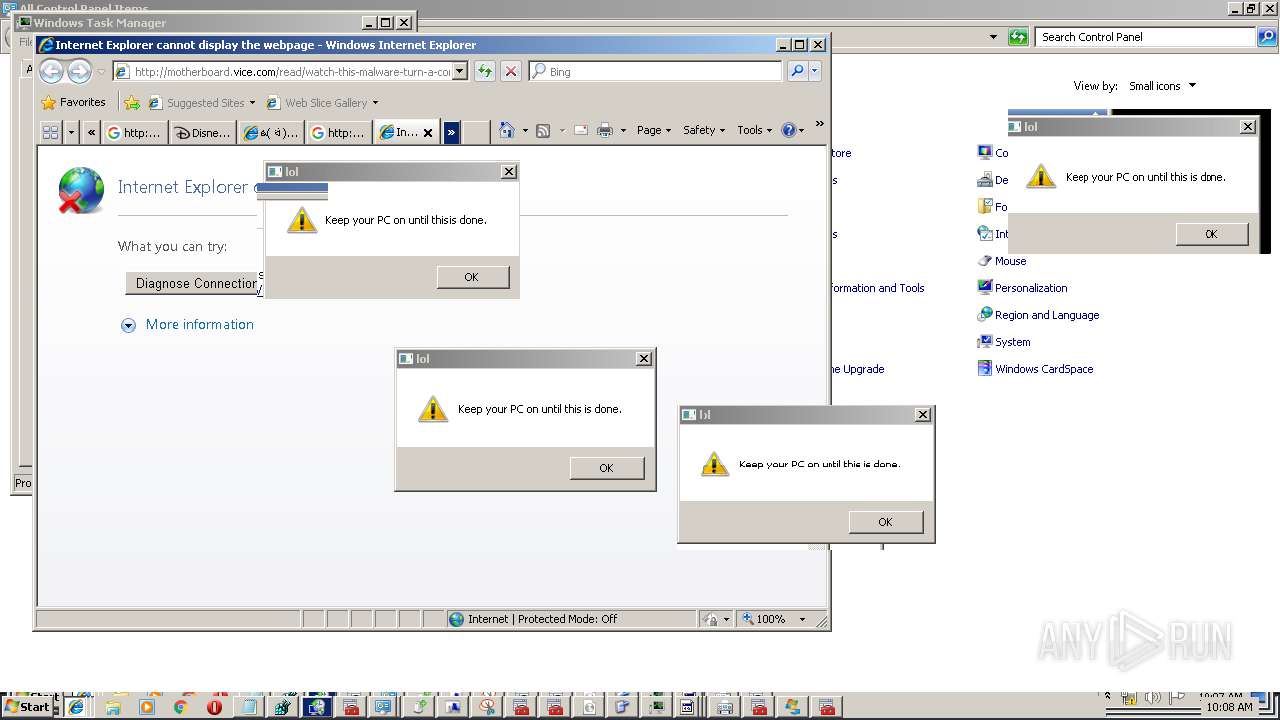
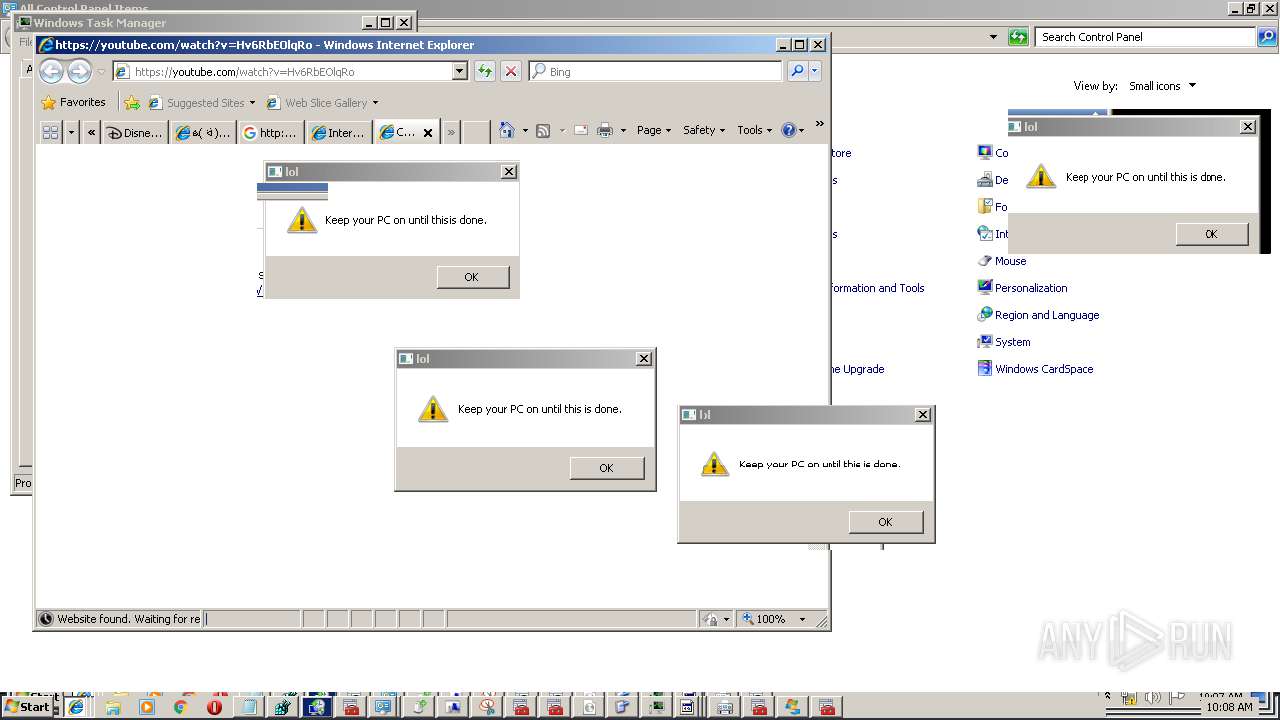
Starts Internet Explorer
- WaffMEMZ-1.0-Destructive.exe (PID: 2836)
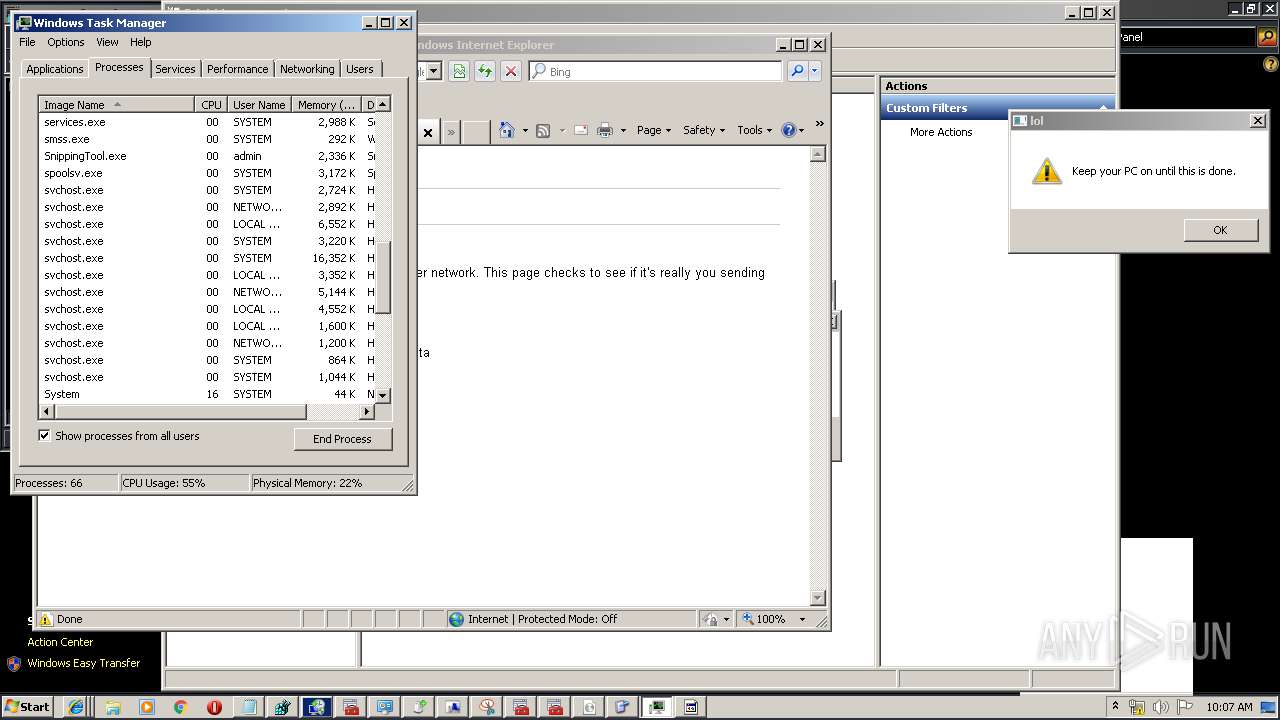
Executed as Windows Service
- wbengine.exe (PID: 3996)
- vssvc.exe (PID: 2260)
- vds.exe (PID: 2584)
- fxssvc.exe (PID: 5440)
Creates files in the program directory
- SearchIndexer.exe (PID: 332)
- fxssvc.exe (PID: 5440)
Creates files in the Windows directory
- rstrui.exe (PID: 3056)
- fxssvc.exe (PID: 5440)
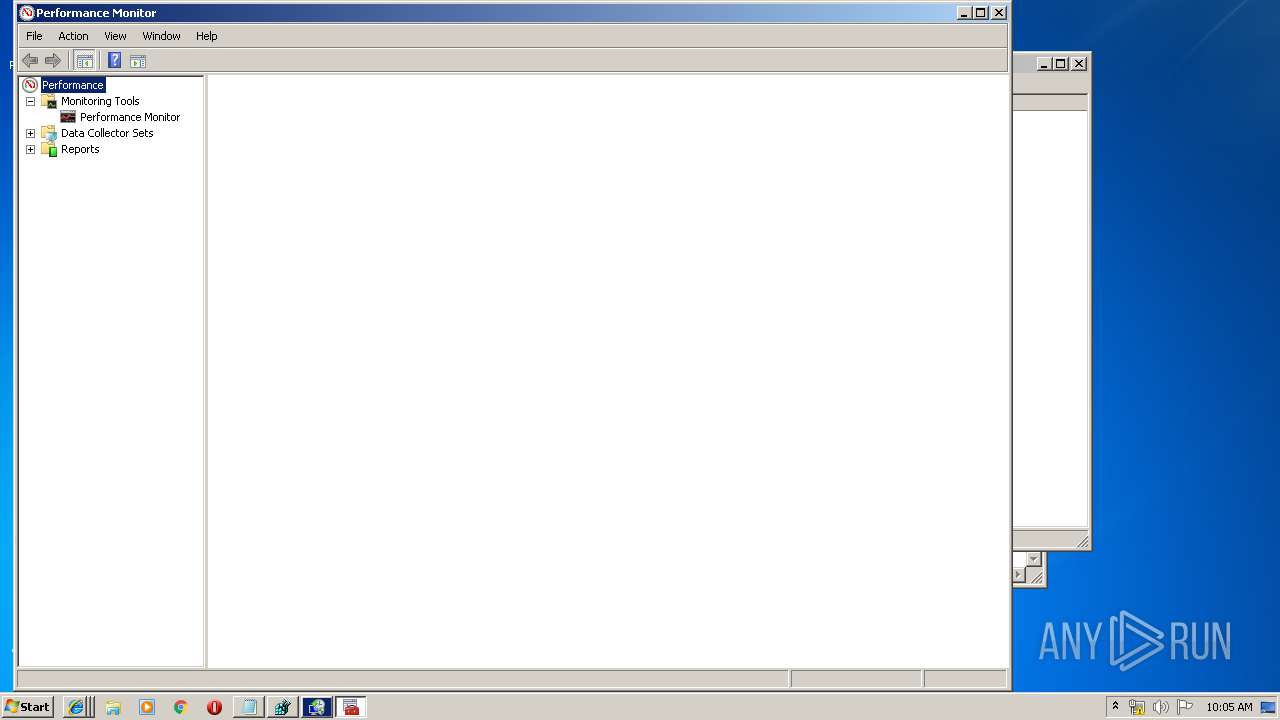
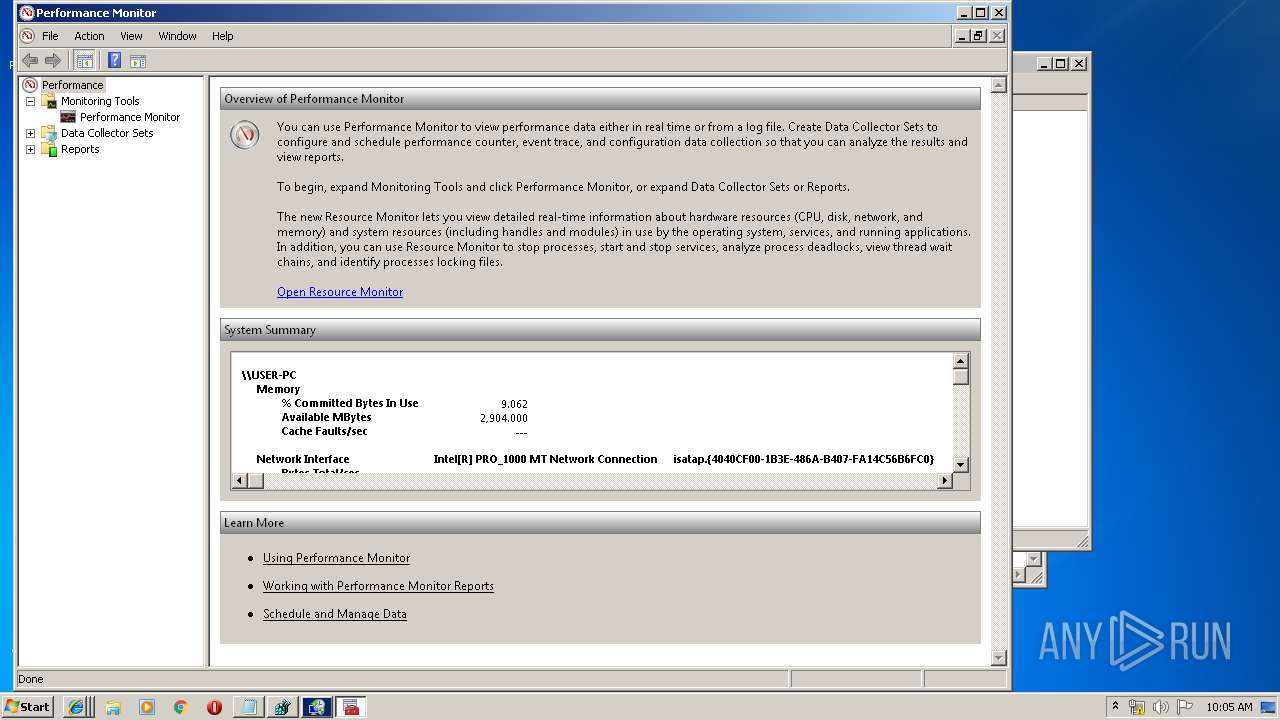
Reads internet explorer settings
- mmc.exe (PID: 3328)
Adds / modifies Windows certificates
- svchost.exe (PID: 1044)
Writes to a desktop.ini file (may be used to cloak folders)
- WFS.exe (PID: 4820)
Executed via COM
- vdsldr.exe (PID: 2236)
INFO
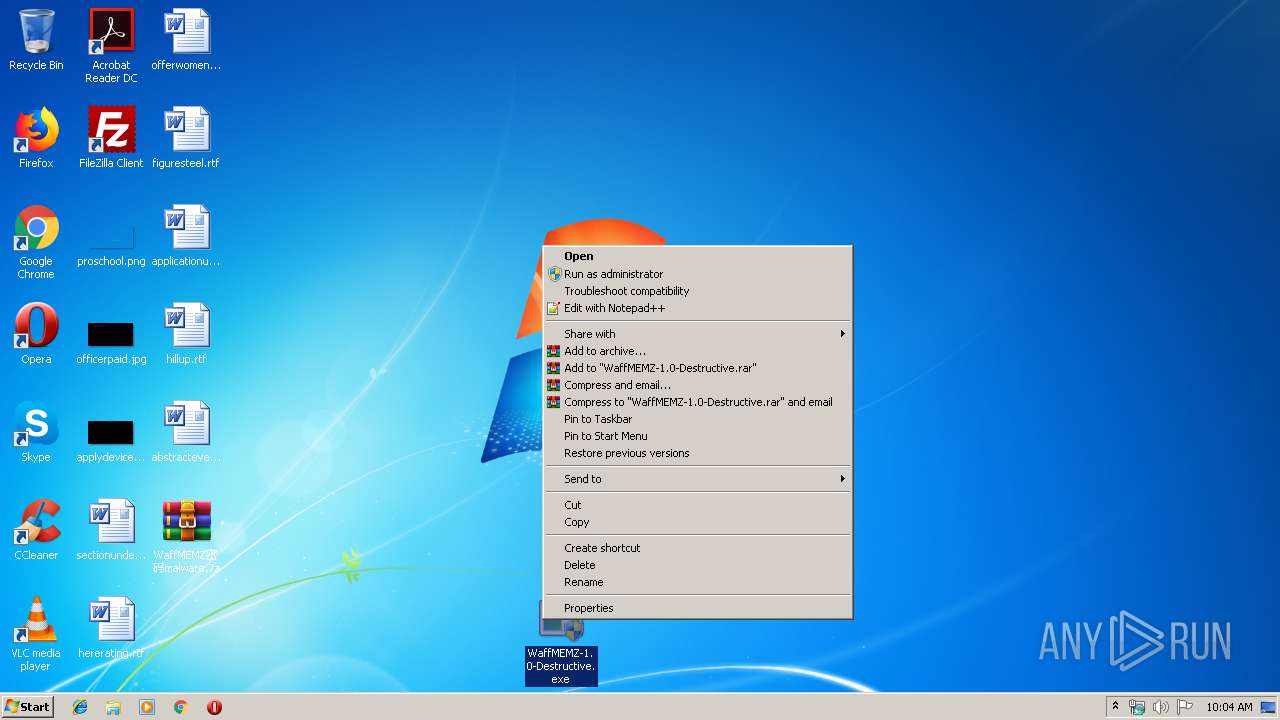
Manual execution by user
- WaffMEMZ-1.0-Destructive.exe (PID: 3560)
- taskmgr.exe (PID: 3700)
Creates files in the user directory
- iexplore.exe (PID: 3468)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 2320)
- iexplore.exe (PID: 2980)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 3480)
- iexplore.exe (PID: 5500)
- iexplore.exe (PID: 1608)
- iexplore.exe (PID: 5880)
Reads internet explorer settings
- iexplore.exe (PID: 3468)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 2320)
- iexplore.exe (PID: 2980)
- iexplore.exe (PID: 1608)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 5880)
- iexplore.exe (PID: 5500)
- iexplore.exe (PID: 3416)
Application launched itself
- iexplore.exe (PID: 3480)
Reads Internet Cache Settings
- iexplore.exe (PID: 2320)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 2980)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 3480)
- iexplore.exe (PID: 3468)
- iexplore.exe (PID: 1608)
- iexplore.exe (PID: 5880)
- iexplore.exe (PID: 3416)
Changes internet zones settings
- iexplore.exe (PID: 3480)
Reads settings of System Certificates
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 2980)
- svchost.exe (PID: 1044)
- iexplore.exe (PID: 1608)
- iexplore.exe (PID: 3480)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 1608)
Changes settings of System certificates
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 1608)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 1608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
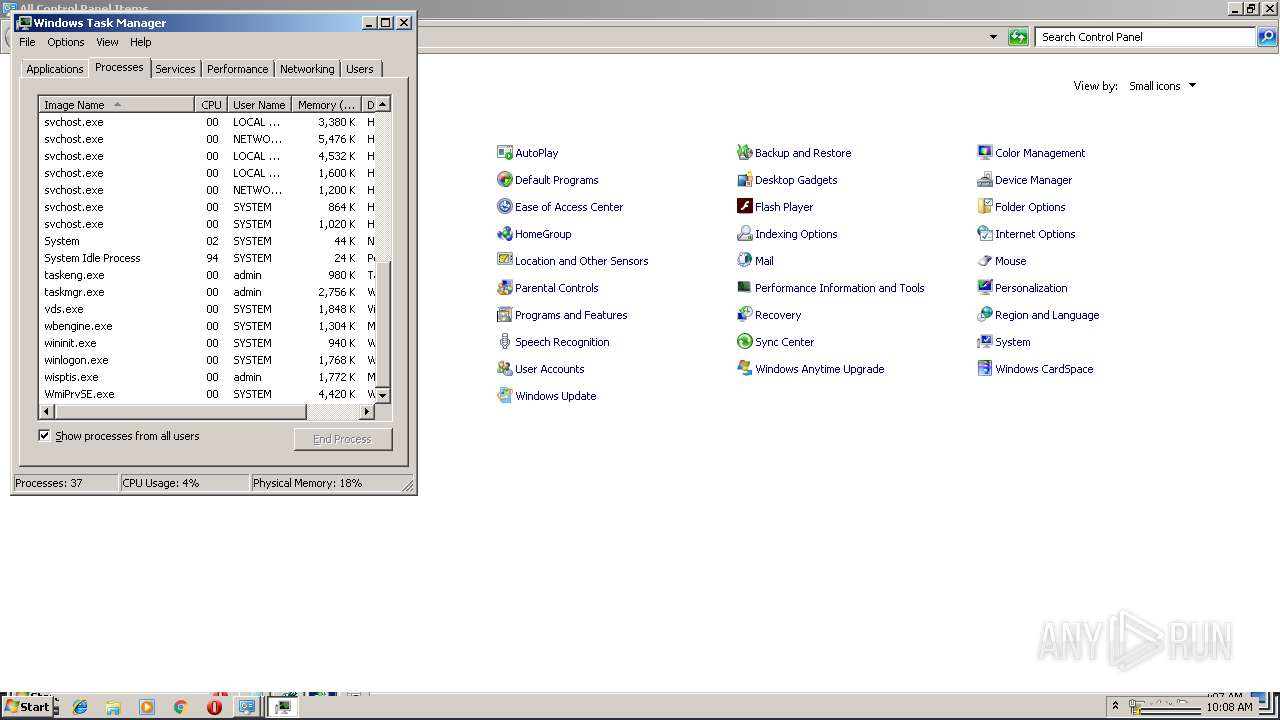
Total processes
114
Monitored processes
67
Malicious processes
5
Suspicious processes
1
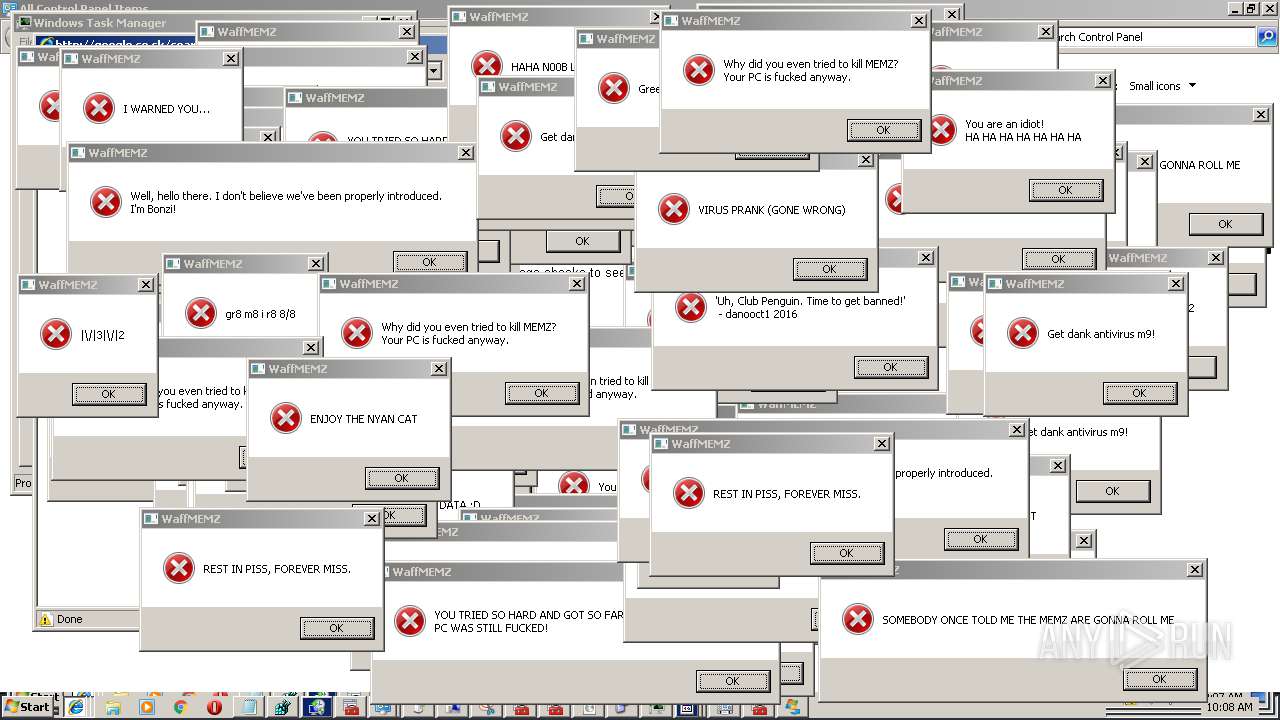
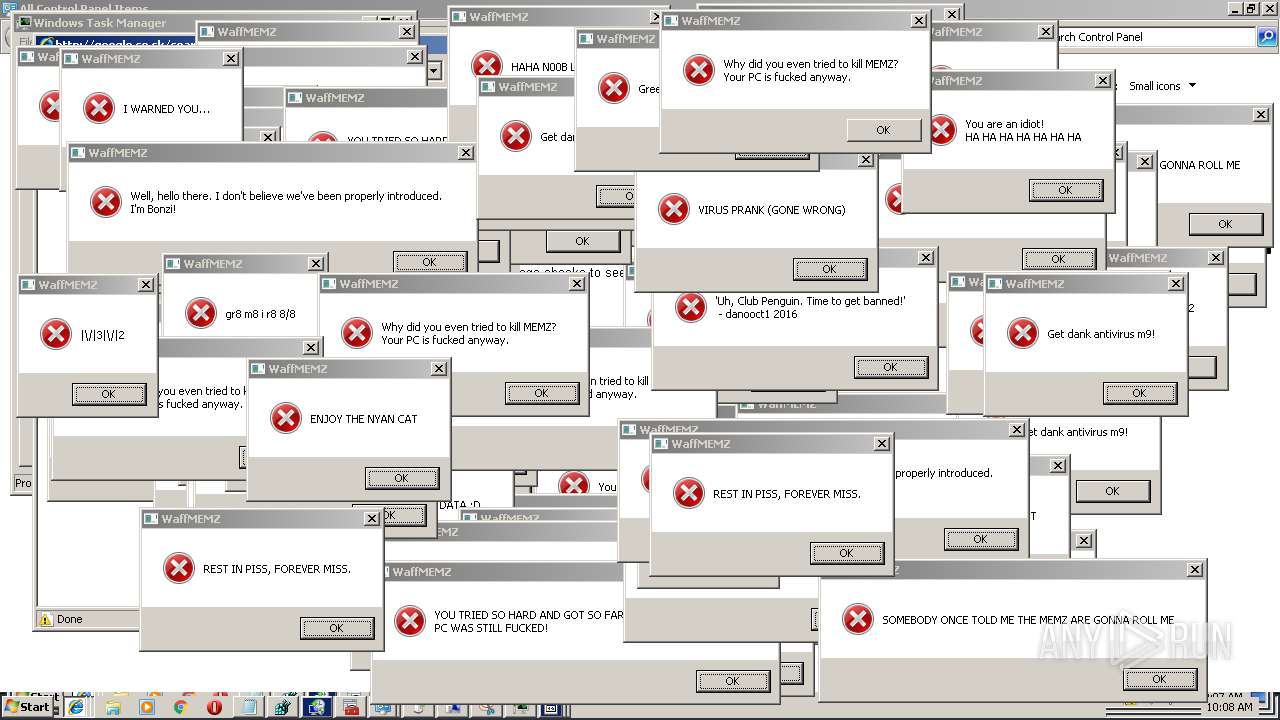
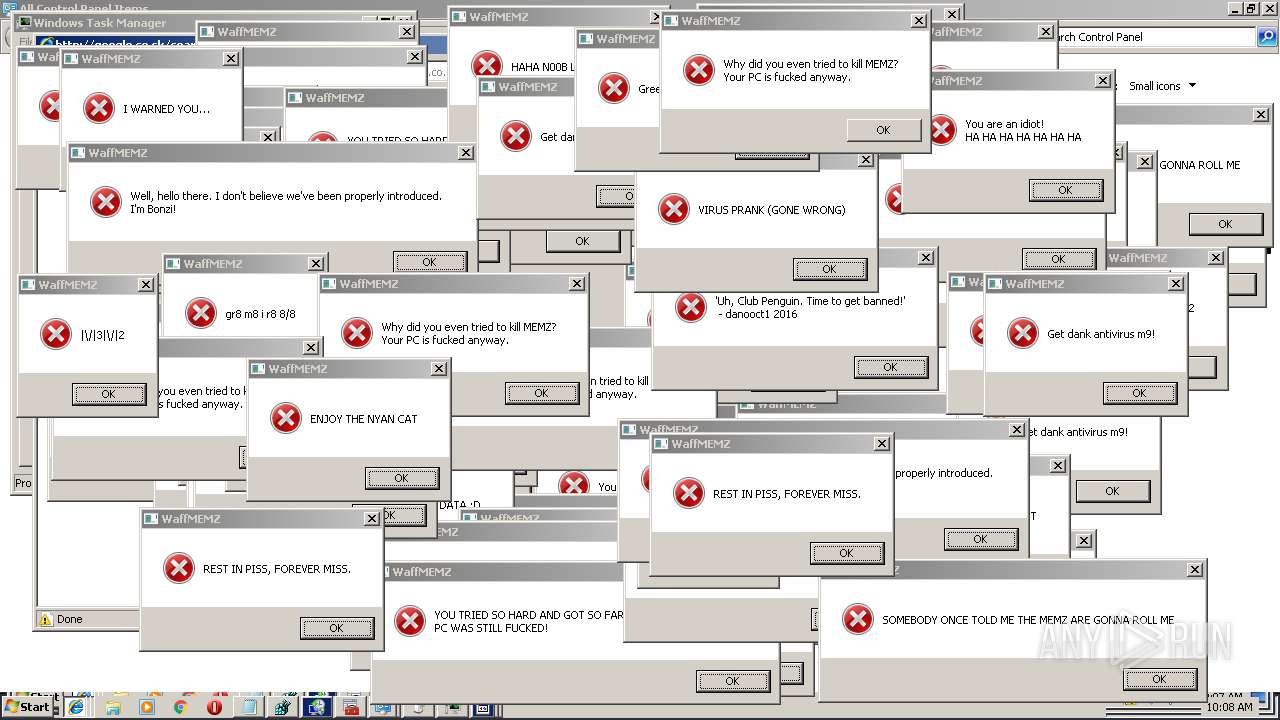
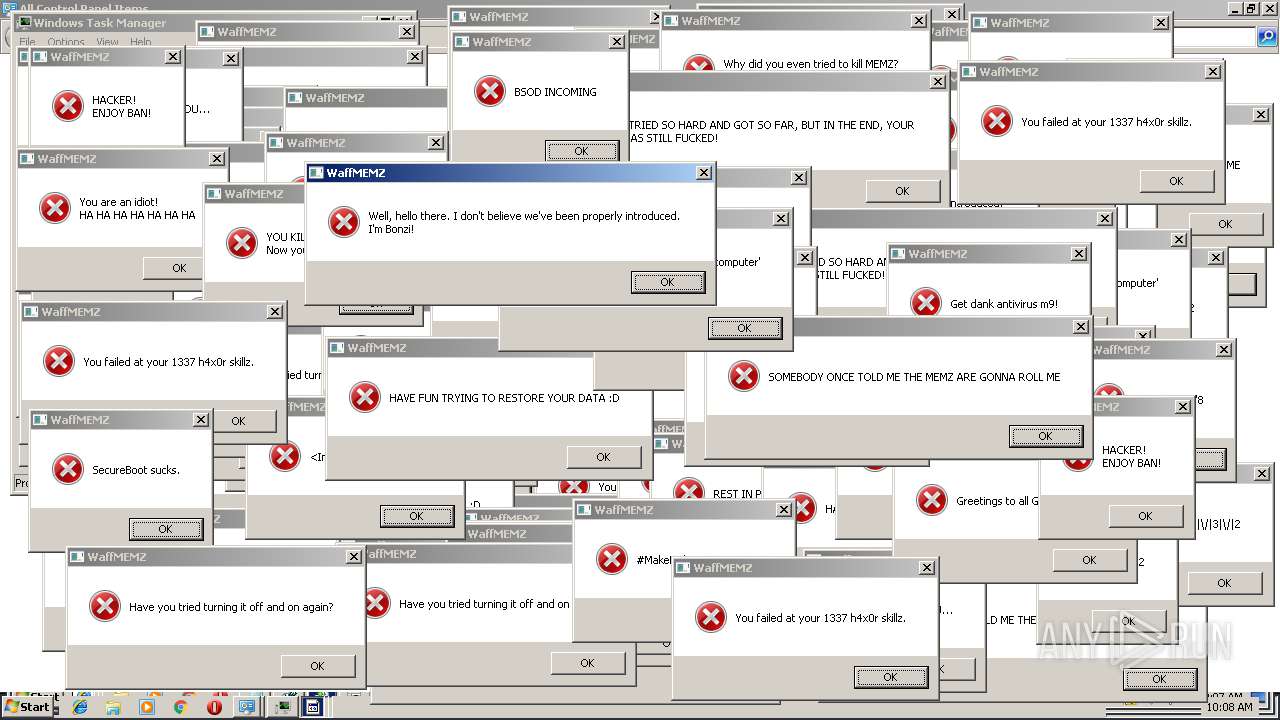
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\System32\SearchIndexer.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 672 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3480 CREDAT:145414 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 3221225794 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3480 CREDAT:1259521 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 3221225794 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3480 CREDAT:14381 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 3221225794 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | "C:\Windows\system32\mmc.exe" "C:\Windows\System32\certmgr.msc" | C:\Windows\system32\mmc.exe | — | WaffMEMZ-1.0-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3480 CREDAT:79879 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1073807364 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
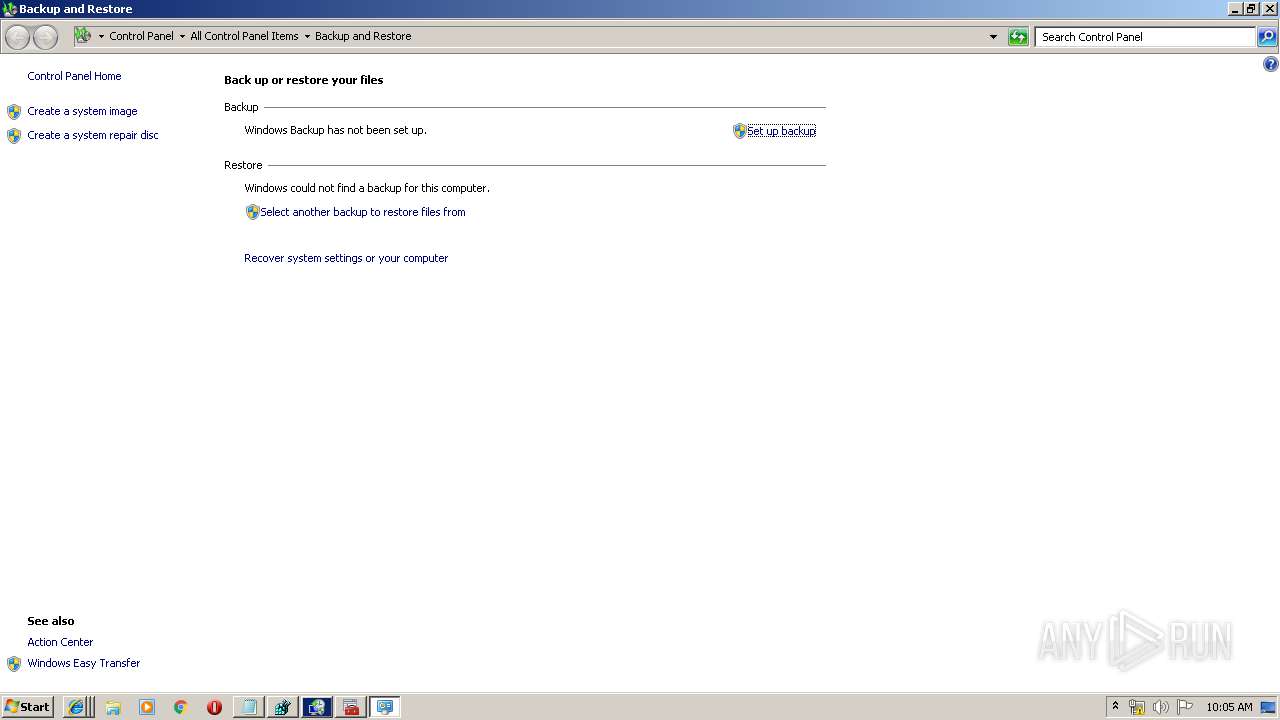
| 2168 | "C:\Windows\System32\sdclt.exe" | C:\Windows\System32\sdclt.exe | WaffMEMZ-1.0-Destructive.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows Backup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2236 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 552
Read events
4 573
Write events
977
Delete events
2
Modification events
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\WaffMEMZ密码malware.7z | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
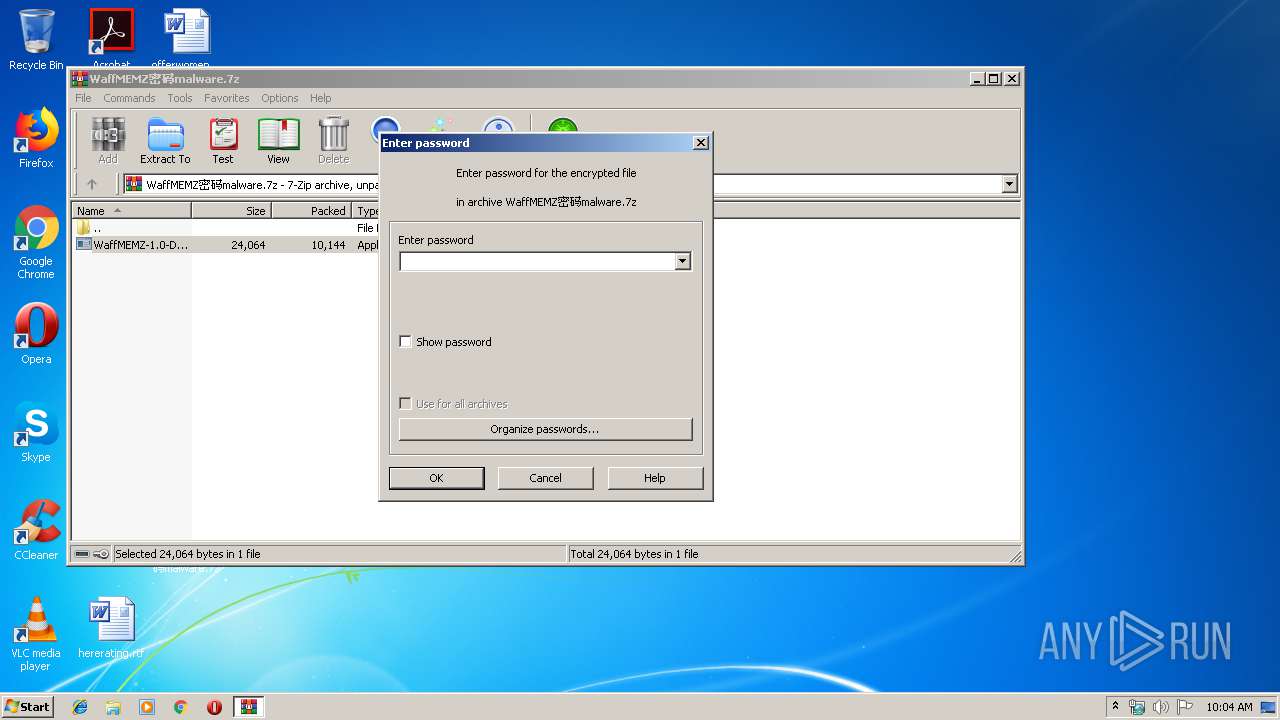
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
47
Text files
262
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3092.15389\WaffMEMZ-1.0-Destructive.exe | — | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2320 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google.co[1].txt | — | |
MD5:— | SHA256:— | |||
| 3984 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\api[1].js | text | |
MD5:— | SHA256:— | |||
| 2320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\search[1].htm | html | |
MD5:— | SHA256:— | |||
| 3468 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\api[1].js | text | |
MD5:— | SHA256:— | |||
| 2320 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google.co[4].txt | text | |
MD5:— | SHA256:— | |||
| 2320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\images[1].jpg | image | |
MD5:— | SHA256:— | |||
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
273
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
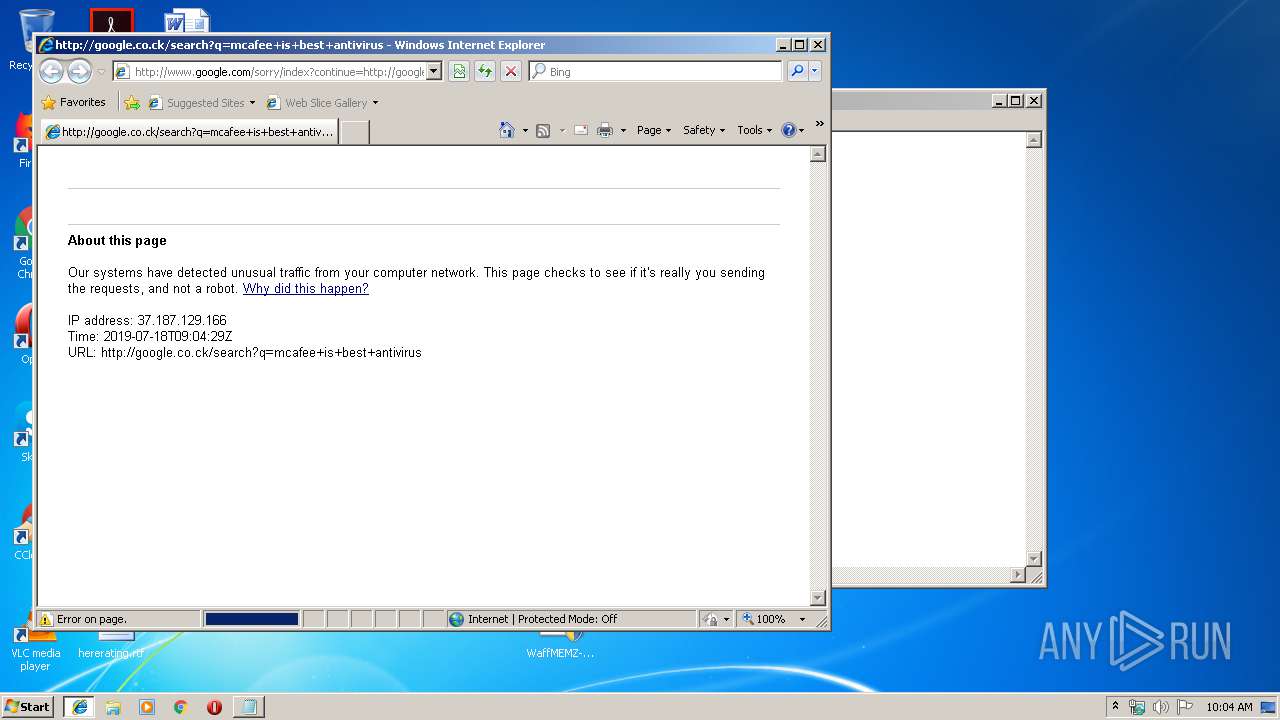
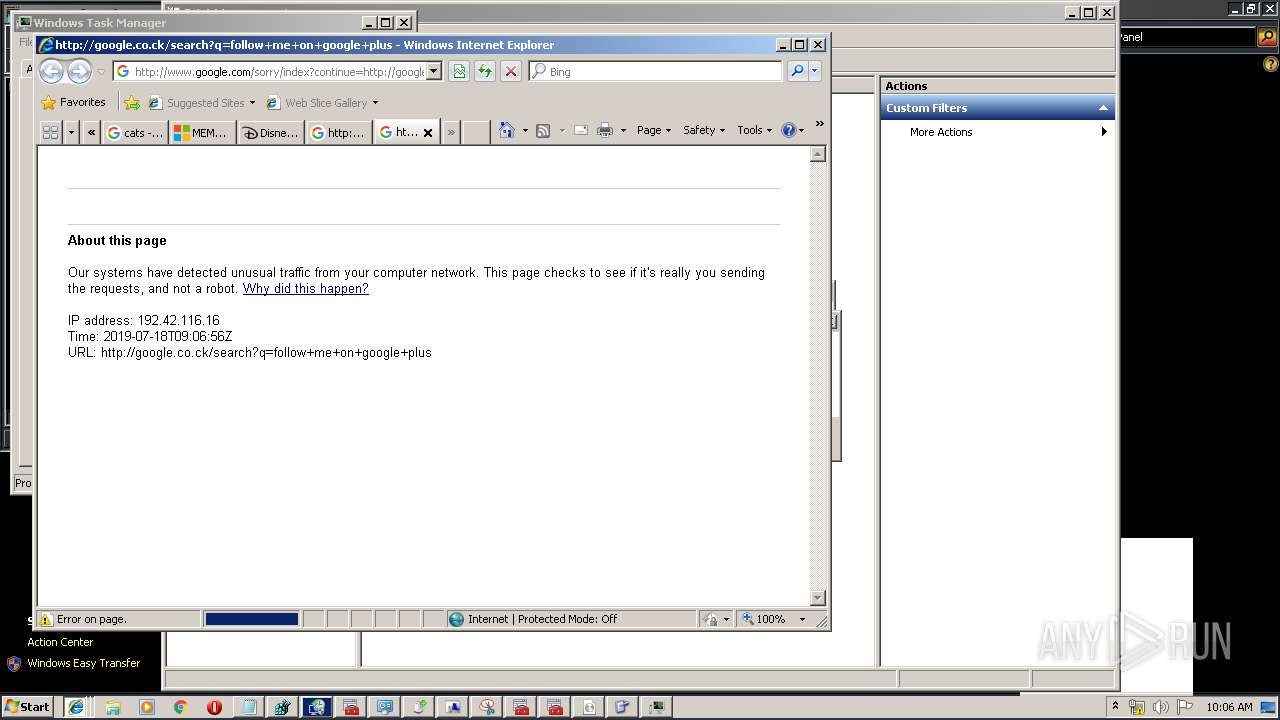
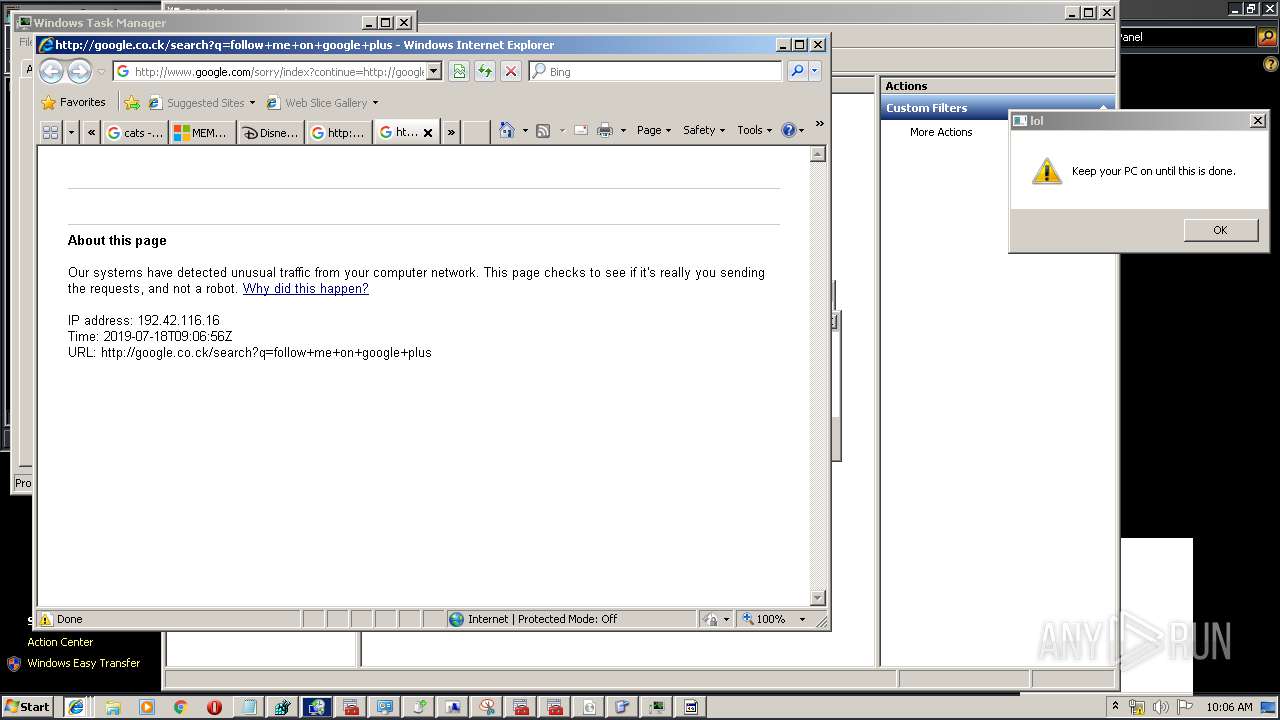
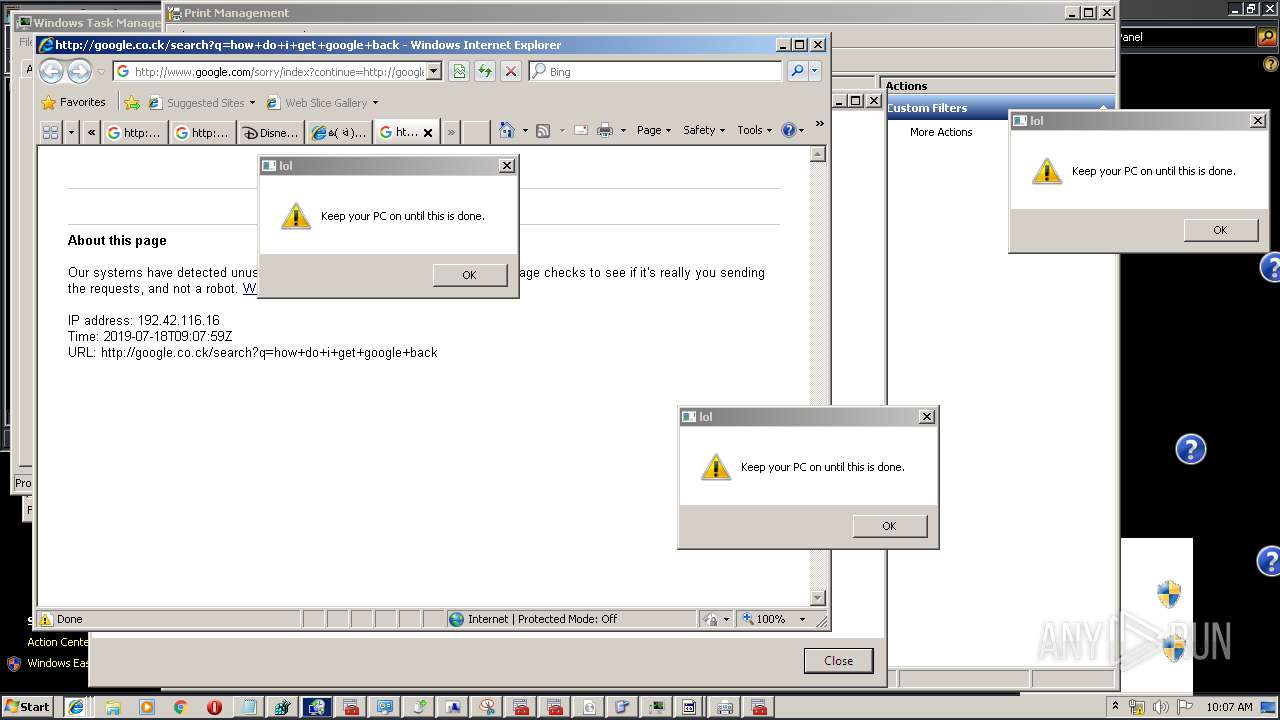
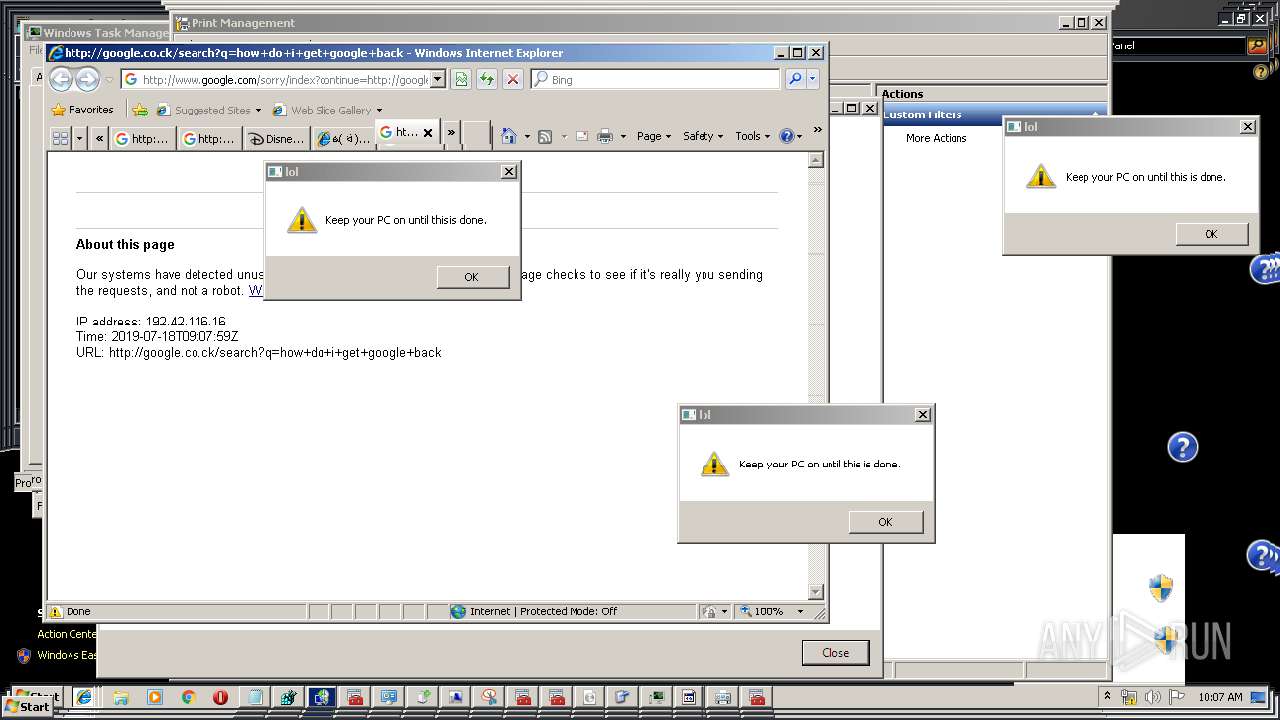
3468 | iexplore.exe | GET | 429 | 216.58.215.36:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Dmcafee%2Bis%2Bbest%2Bantivirus&q=EgQlu4GmGJzswOkFIhkA8aeDSzIBuwIMdIogkzdo72brobKQwM2BMgFy | US | html | 2.82 Kb | malicious |
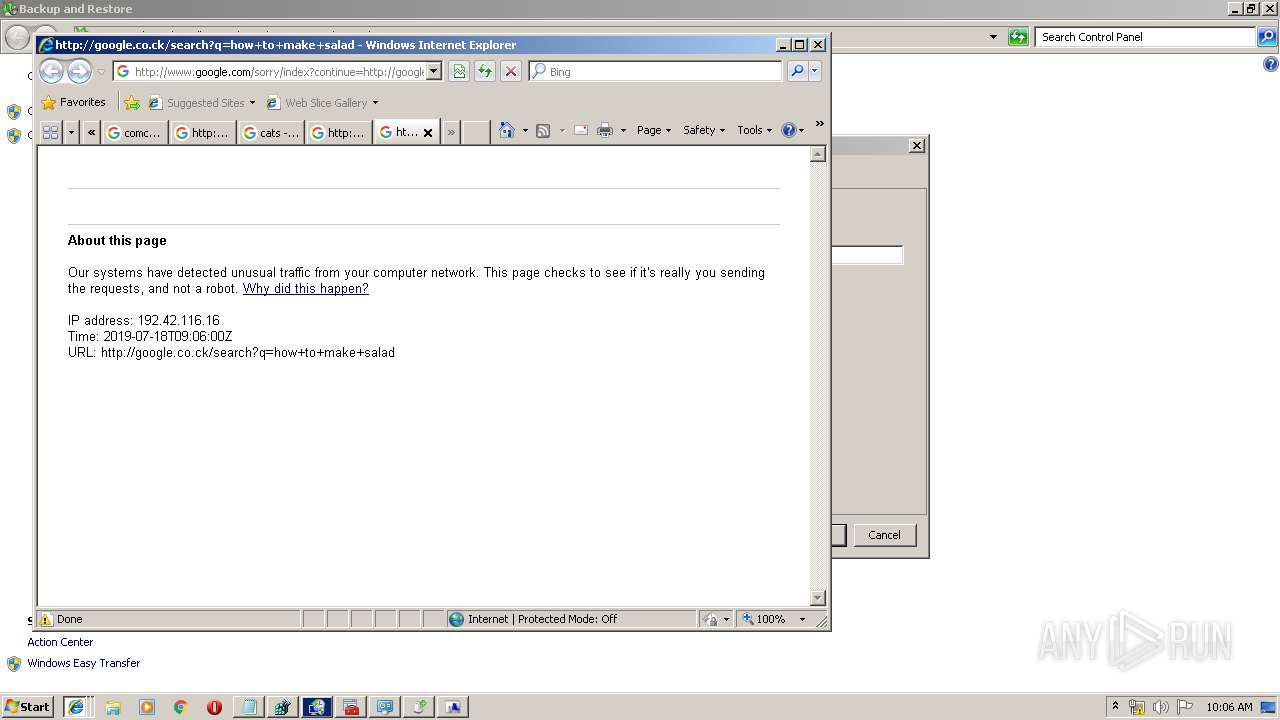
2996 | iexplore.exe | GET | 429 | 216.58.215.36:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Dhow%2Bto%2Bmake%2Bsalad&q=EgTAKnQQGPjswOkFIhkA8aeDS-xG1G5C3gYnQntr4wy1Cl0JRreAMgFy | US | html | 2.80 Kb | malicious |
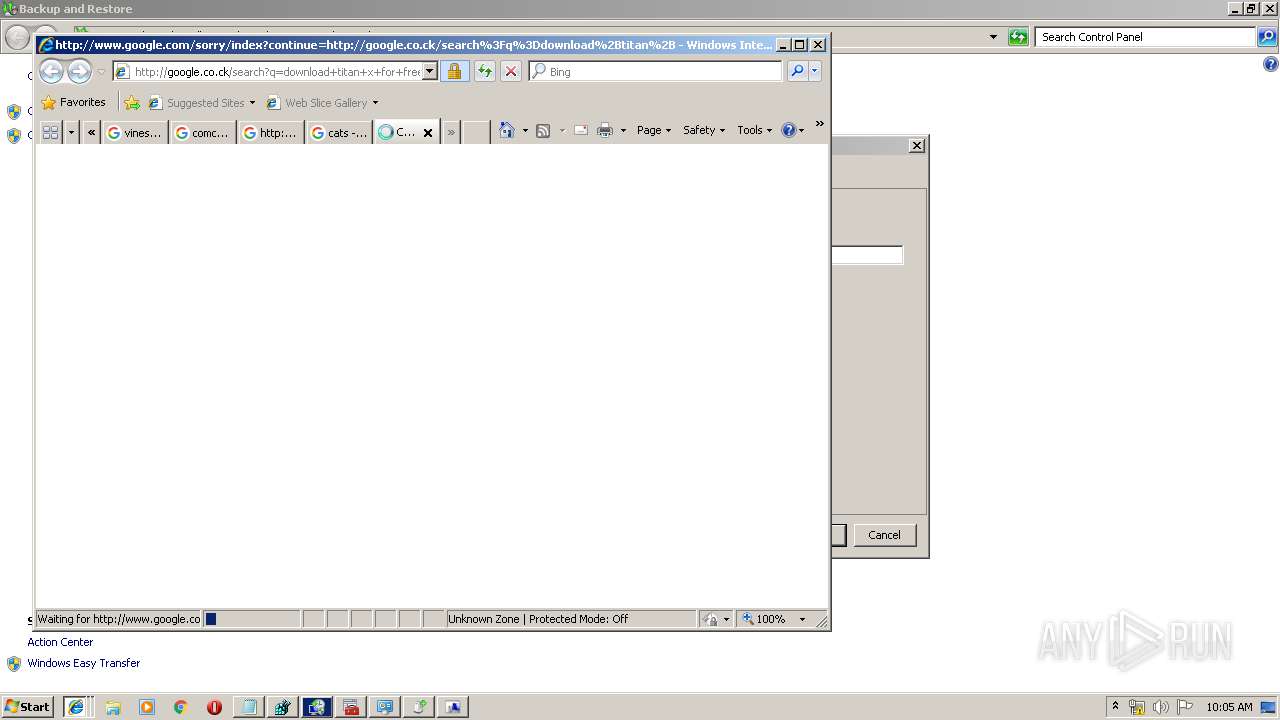
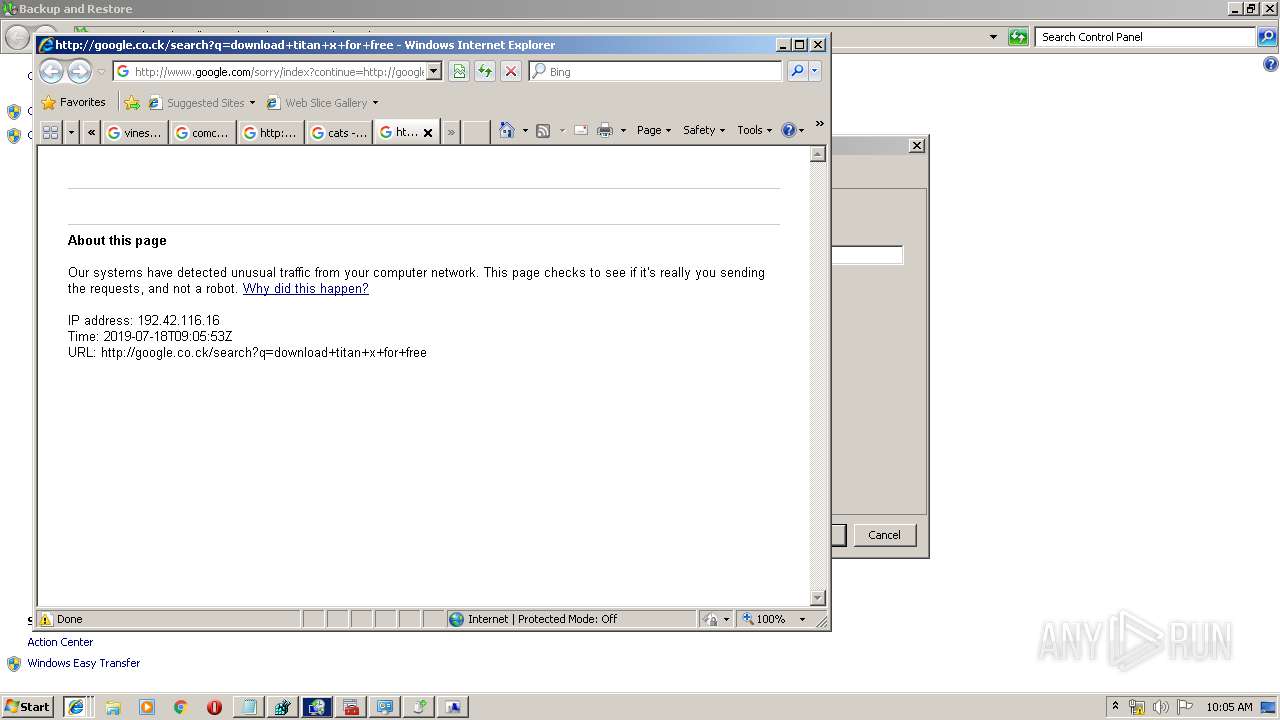
2320 | iexplore.exe | GET | 429 | 216.58.215.36:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Ddownload%2Btitan%2Bx%2Bfor%2Bfree&q=EgTAKnQQGPHswOkFIhkA8aeDS-BR4VmlvyEQ88dUe8boNMsKmyLpMgFy | US | html | 2.82 Kb | malicious |
3468 | iexplore.exe | GET | 302 | 216.58.213.164:80 | http://google.co.ck/search?q=mcafee+is+best+antivirus | US | html | 366 b | whitelisted |
2980 | iexplore.exe | GET | 429 | 216.58.215.36:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Dmicrosoft%2Brecommends&q=EgQlu4GmGMbswOkFIhkA8aeDS3D0EuWjXyyAGrmE84z2W6VojOtUMgFy | US | html | 1.76 Kb | malicious |
2320 | iexplore.exe | GET | 302 | 216.58.213.163:80 | http://www.google.co.ck/search?q=vinesauce&tbm=isch | US | html | 268 b | whitelisted |
2980 | iexplore.exe | GET | 302 | 216.58.213.164:80 | http://google.co.ck/search?q=microsoft+recommends | US | html | 358 b | whitelisted |
3468 | iexplore.exe | GET | 302 | 216.58.213.163:80 | http://www.google.co.ck/search?q=comcast&tbm=isch | US | html | 266 b | whitelisted |
3984 | iexplore.exe | GET | 302 | 216.58.213.163:80 | http://www.google.co.ck/search?q=cats&tbm=isch | US | html | 263 b | whitelisted |
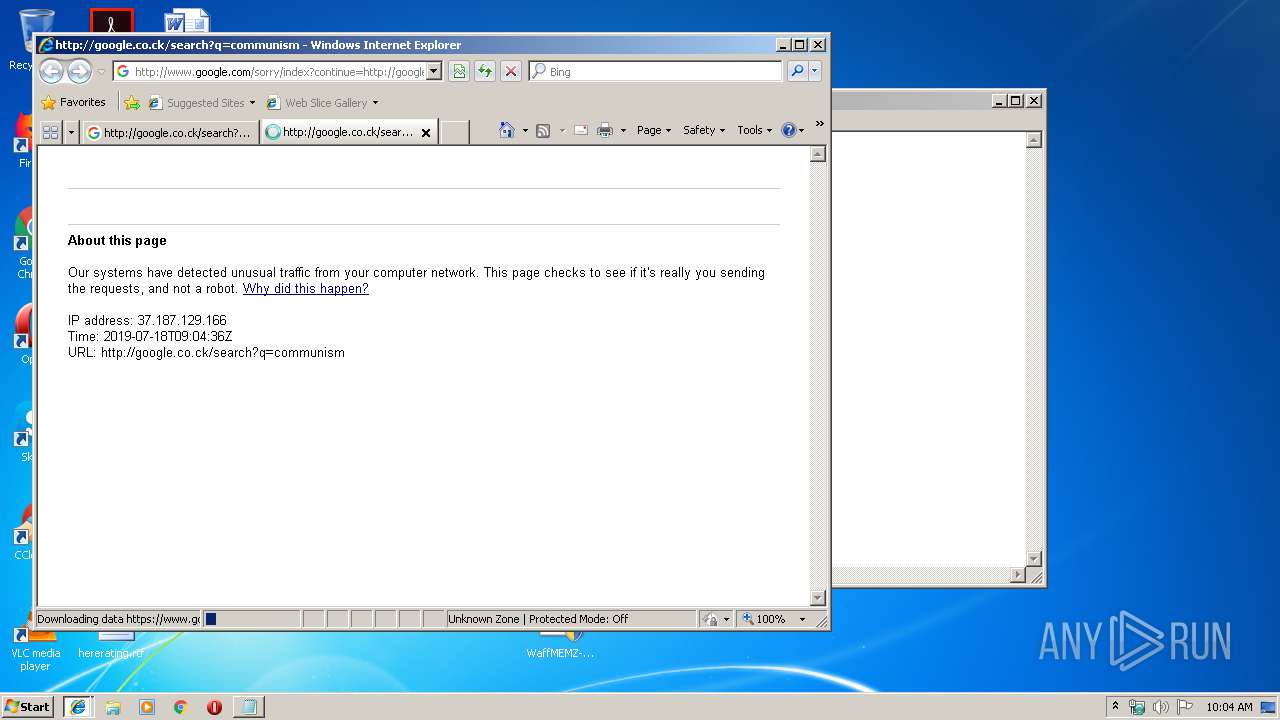
3984 | iexplore.exe | GET | 302 | 216.58.213.164:80 | http://google.co.ck/search?q=communism | US | html | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3468 | iexplore.exe | 216.58.213.164:80 | google.co.ck | Google Inc. | US | whitelisted |
3480 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3468 | iexplore.exe | 216.58.215.36:80 | www.google.com | Google Inc. | US | whitelisted |
3468 | iexplore.exe | 216.58.215.36:443 | www.google.com | Google Inc. | US | whitelisted |
3984 | iexplore.exe | 216.58.213.164:80 | google.co.ck | Google Inc. | US | whitelisted |
3468 | iexplore.exe | 216.58.201.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3984 | iexplore.exe | 216.58.215.36:80 | www.google.com | Google Inc. | US | whitelisted |
3984 | iexplore.exe | 216.58.215.36:443 | www.google.com | Google Inc. | US | whitelisted |
2320 | iexplore.exe | 216.58.213.164:80 | google.co.ck | Google Inc. | US | whitelisted |
3984 | iexplore.exe | 216.58.201.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.co.ck |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
www.google.co.ck |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
answers.microsoft.com |
| whitelisted |
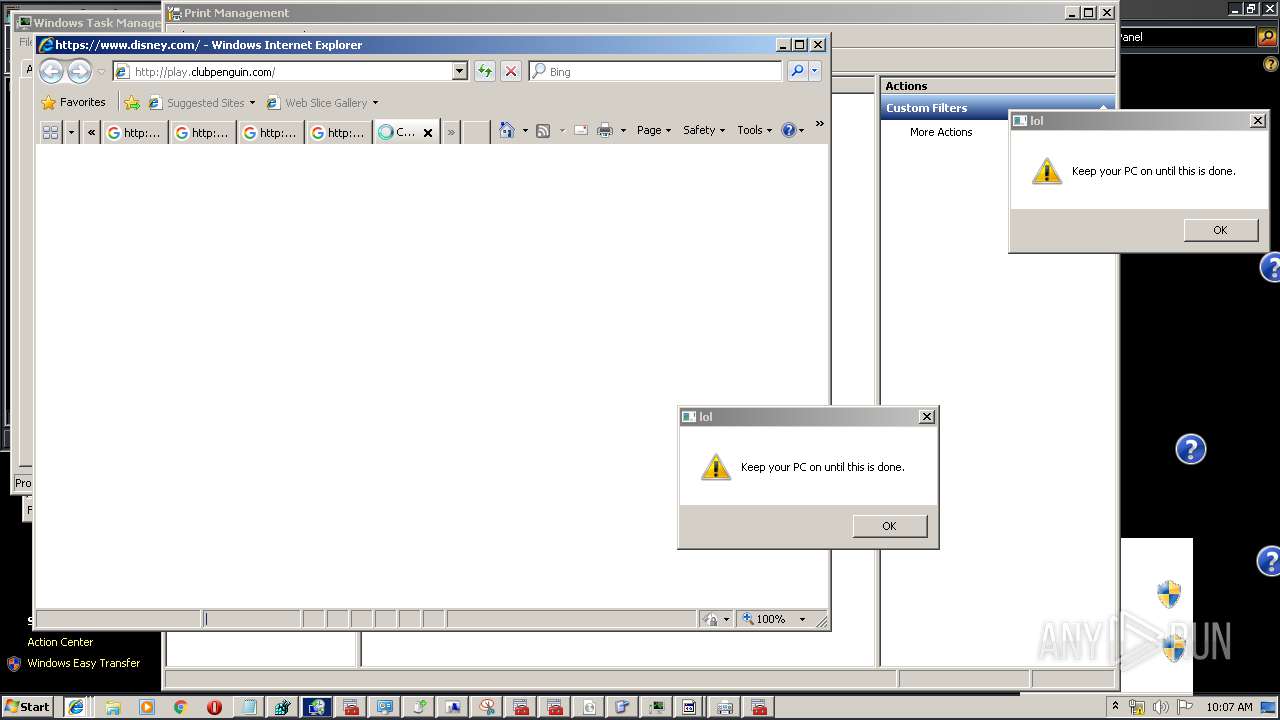
play.clubpenguin.com |
| whitelisted |
www.clubpenguinisland.com |
| whitelisted |
answersstaticfilecdn.azureedge.net |
| whitelisted |
Threats
Process | Message |
|---|---|
sdclt.exe | Invalid parameter passed to C runtime function.
|
sdclt.exe | Invalid parameter passed to C runtime function.
|