| File name: | rufus-3.9p.exe |
| Full analysis: | https://app.any.run/tasks/21845941-ea6f-4be4-a3b9-0de2f286c918 |
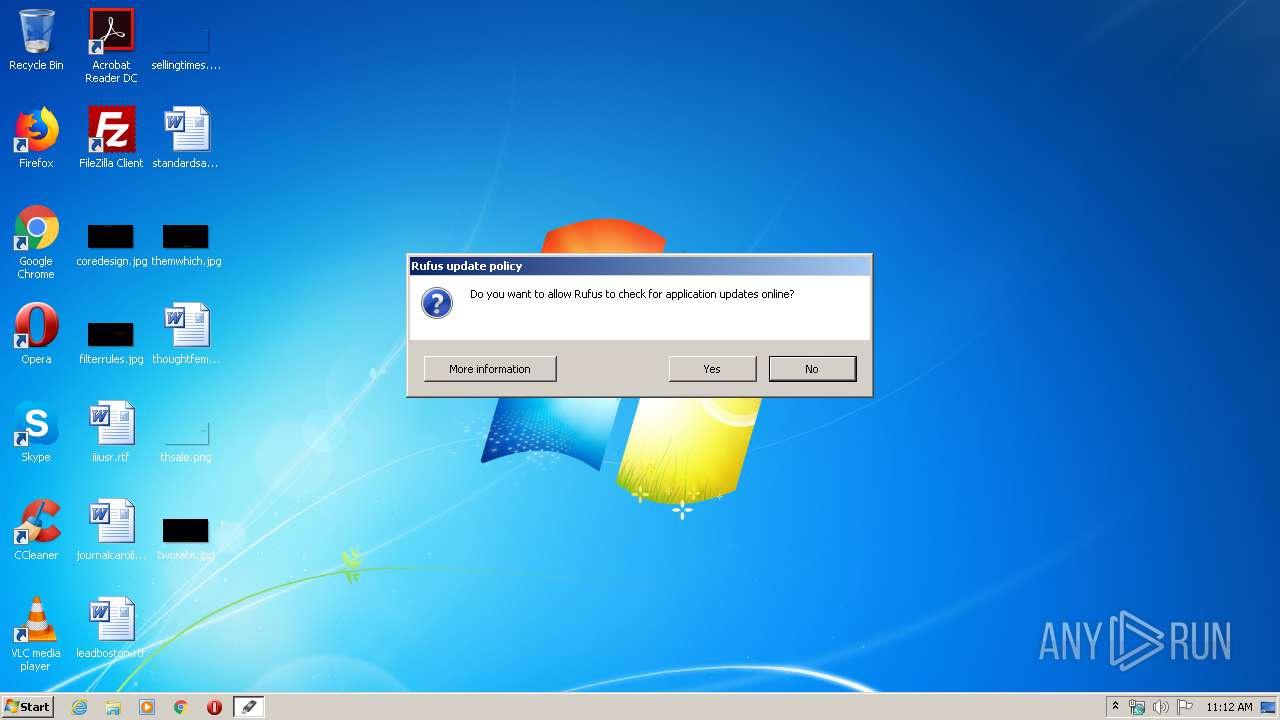
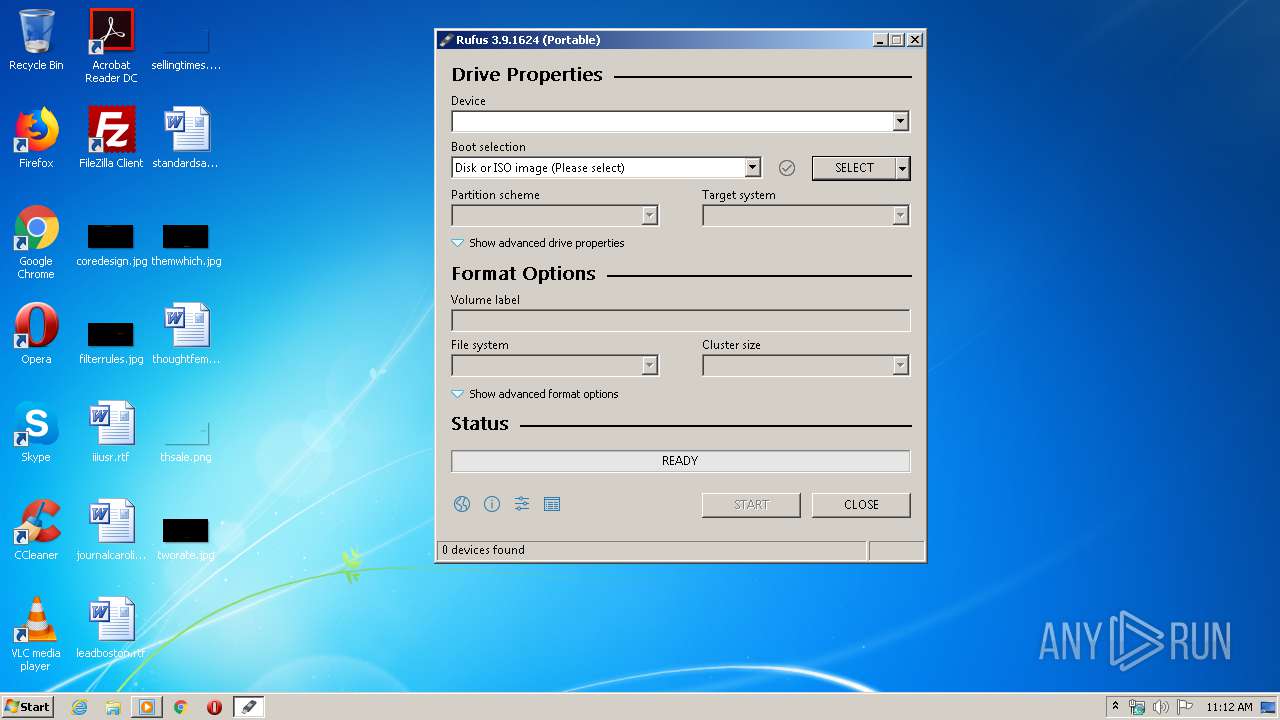
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2020, 10:12:06 |
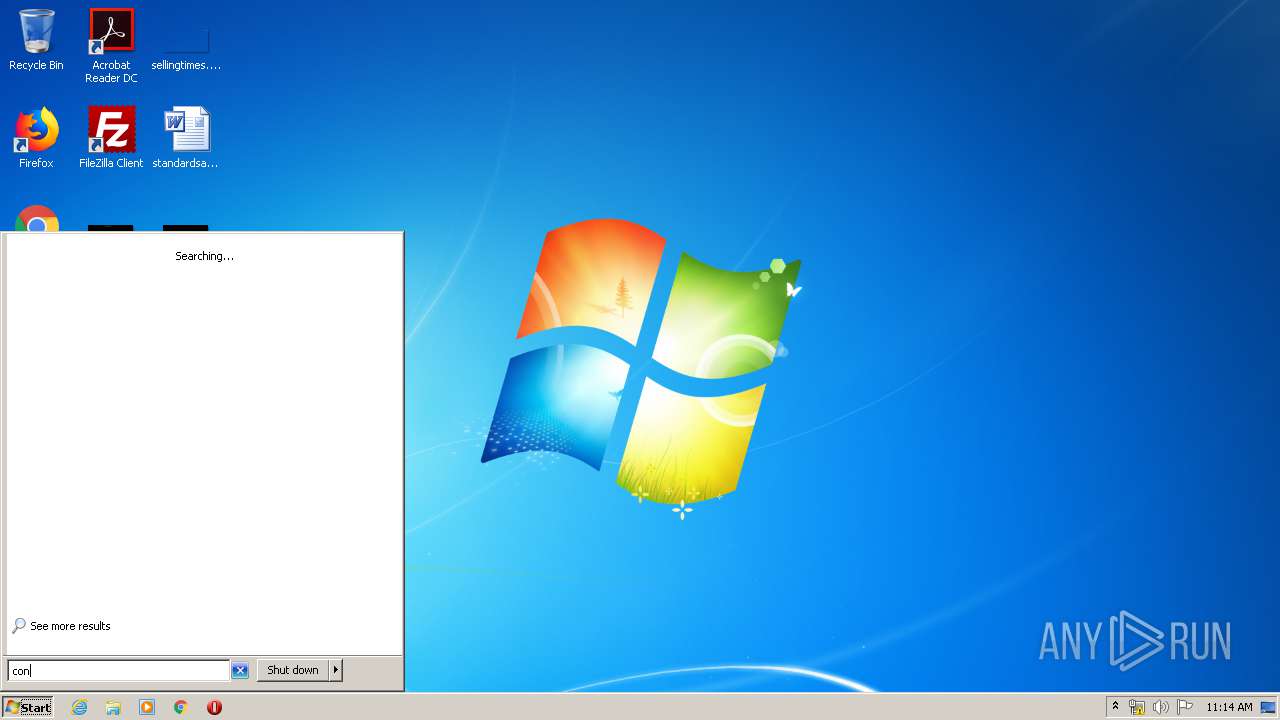
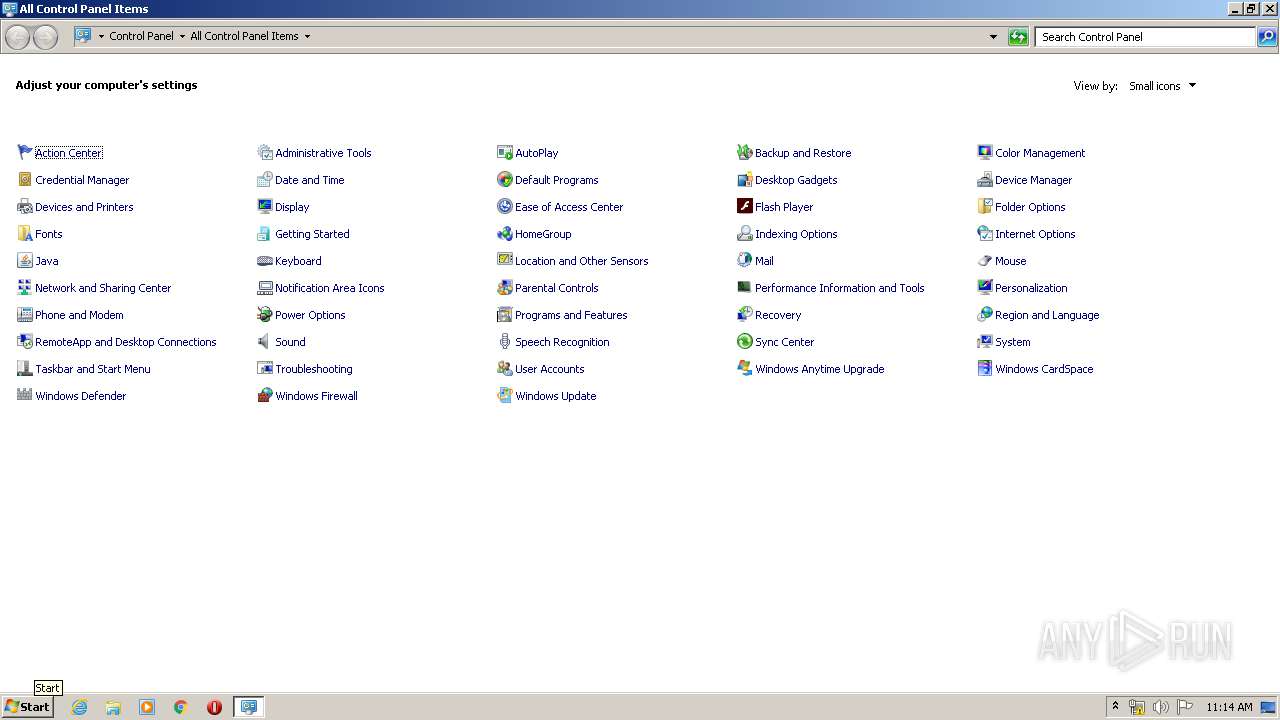
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | D8B30D4C4DBC07B11573481B58ADCD4B |
| SHA1: | 38D643DED3B34851884C0C55FBF7EA2BF5C52F9F |
| SHA256: | D761D571BB4DCF5164484F3B573FE1C420444C77176F14D52AE5909D02360C75 |
| SSDEEP: | 24576:ed0dkhseUYQ6WEtCSSIHNZOLCvMCYmqTb77/gtt4q9aM:edgkuenQ6W1HWNZ7vMSqTb7Li |
MALICIOUS
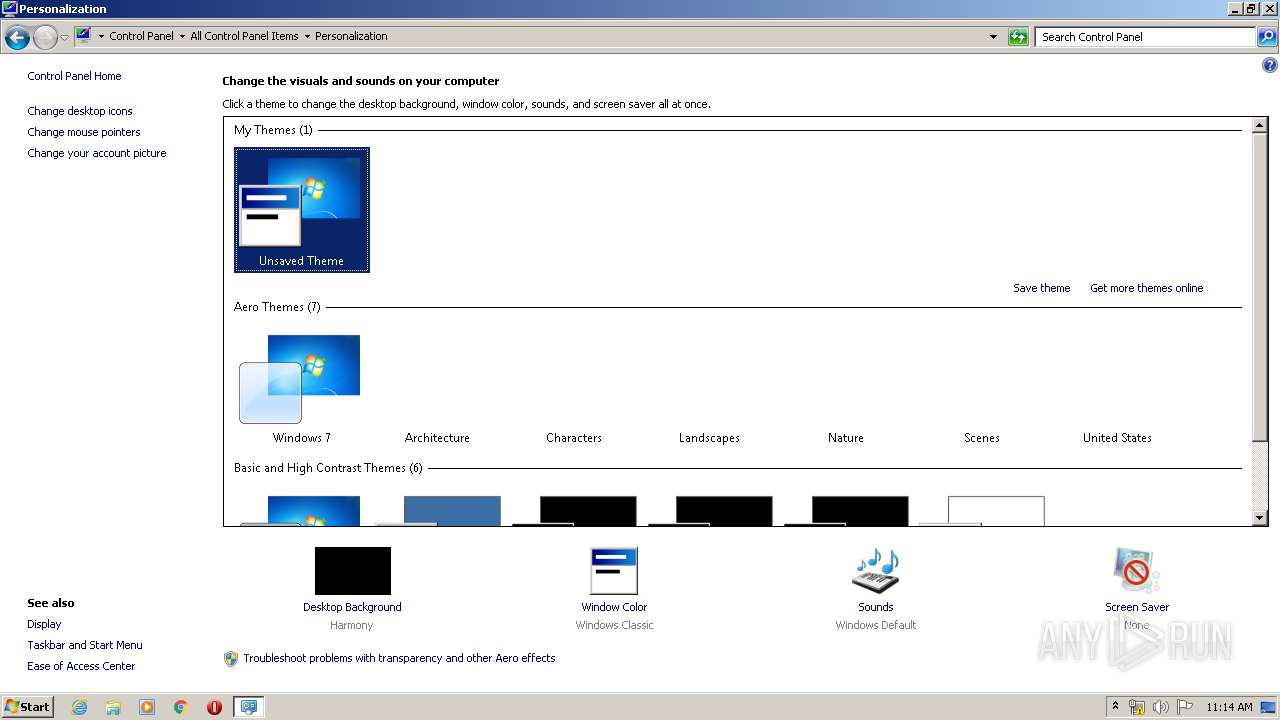
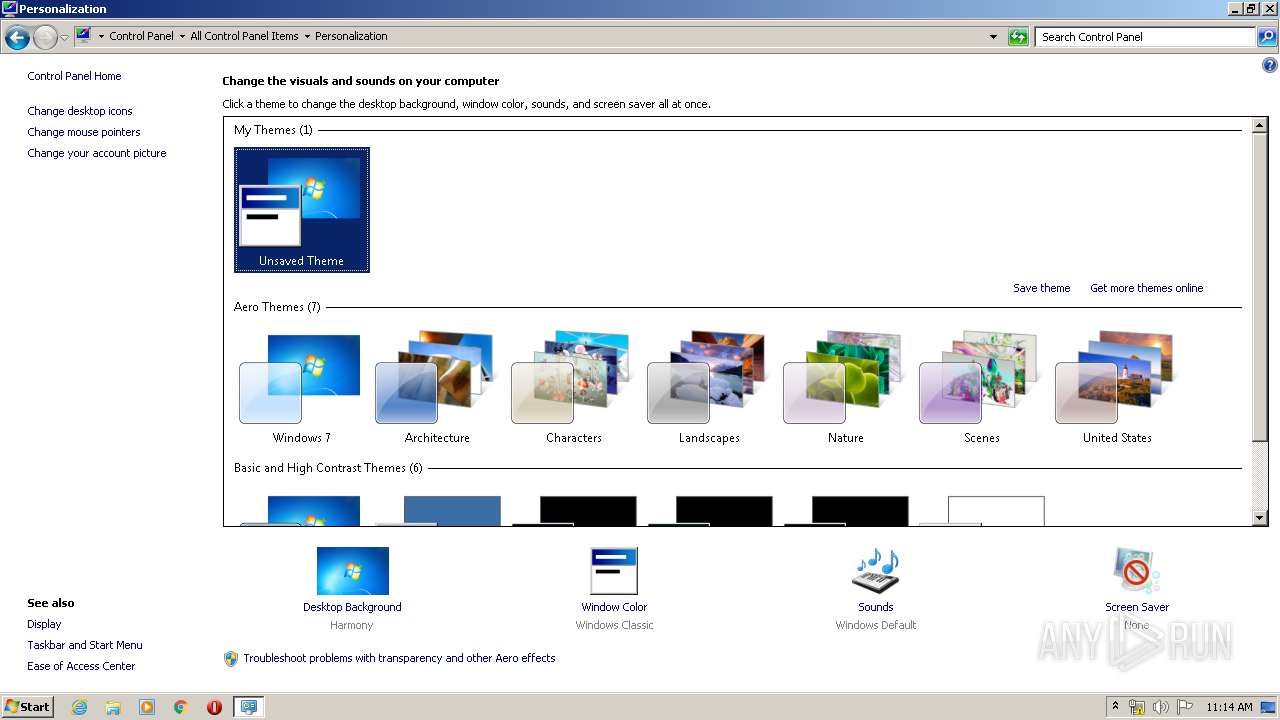
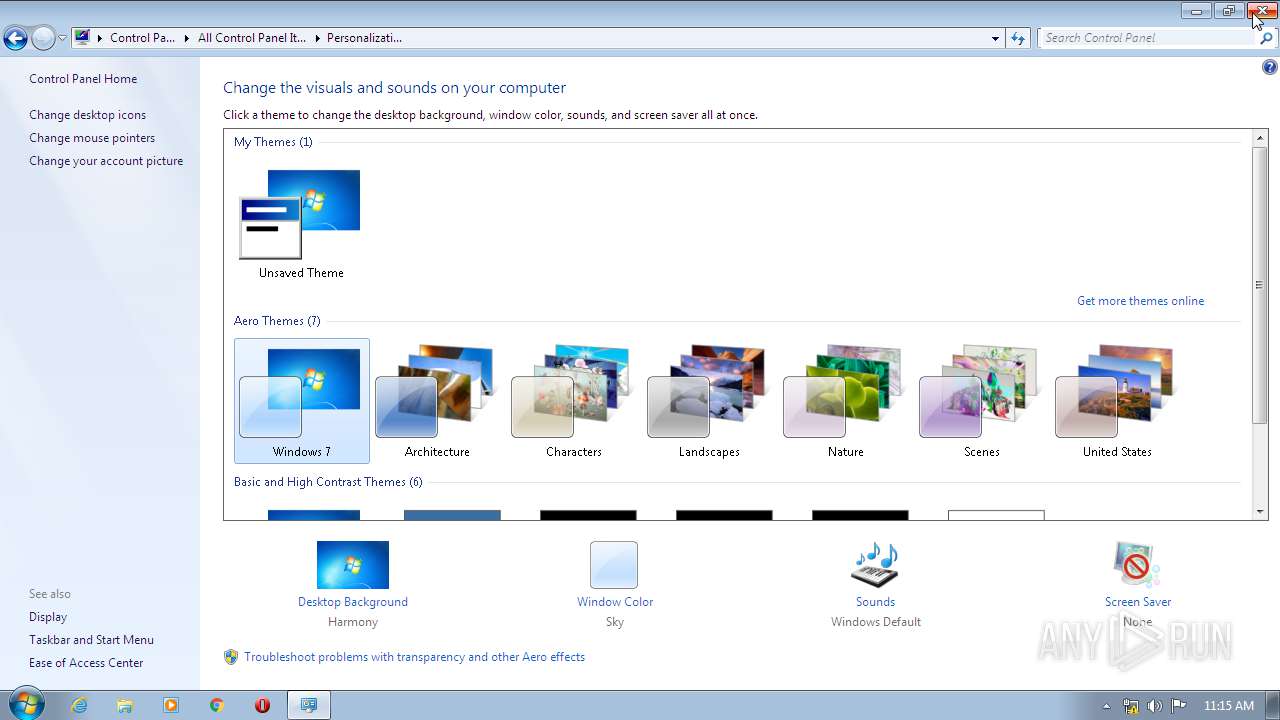
Changes Windows auto-update feature
- rufus-3.9p.exe (PID: 3580)
Disables Windows Defender
- rufus-3.9p.exe (PID: 3580)
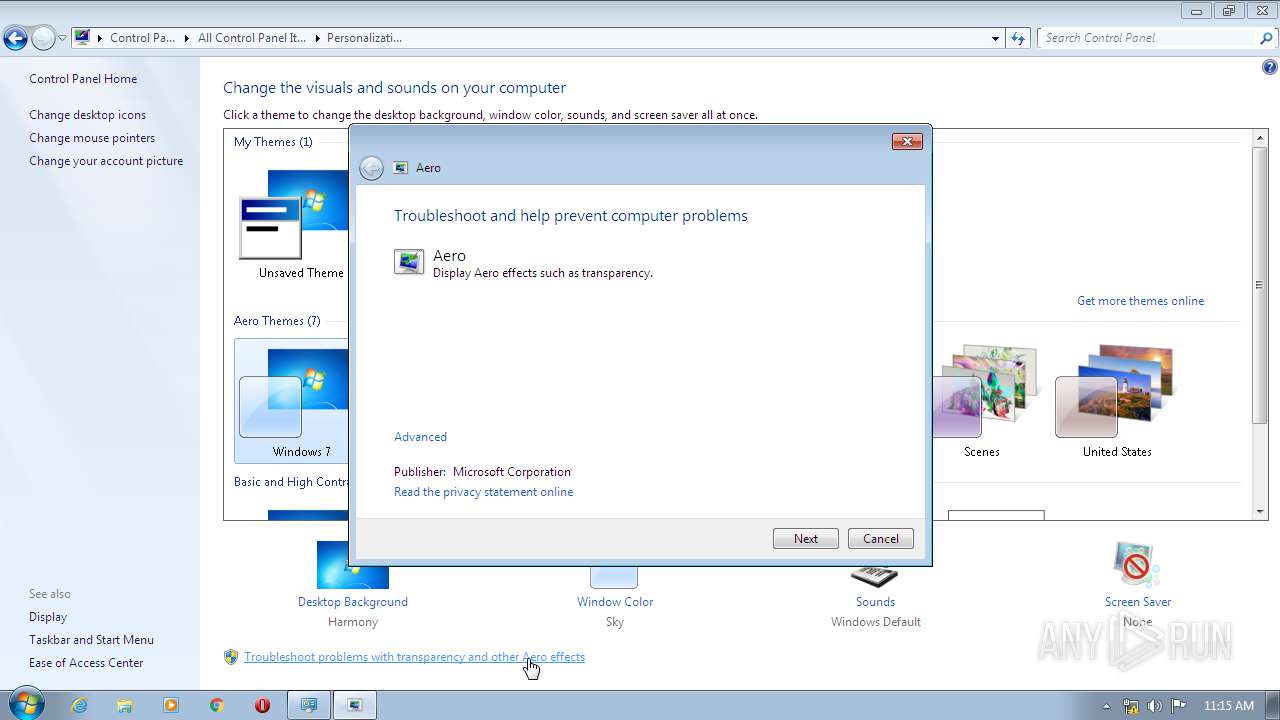
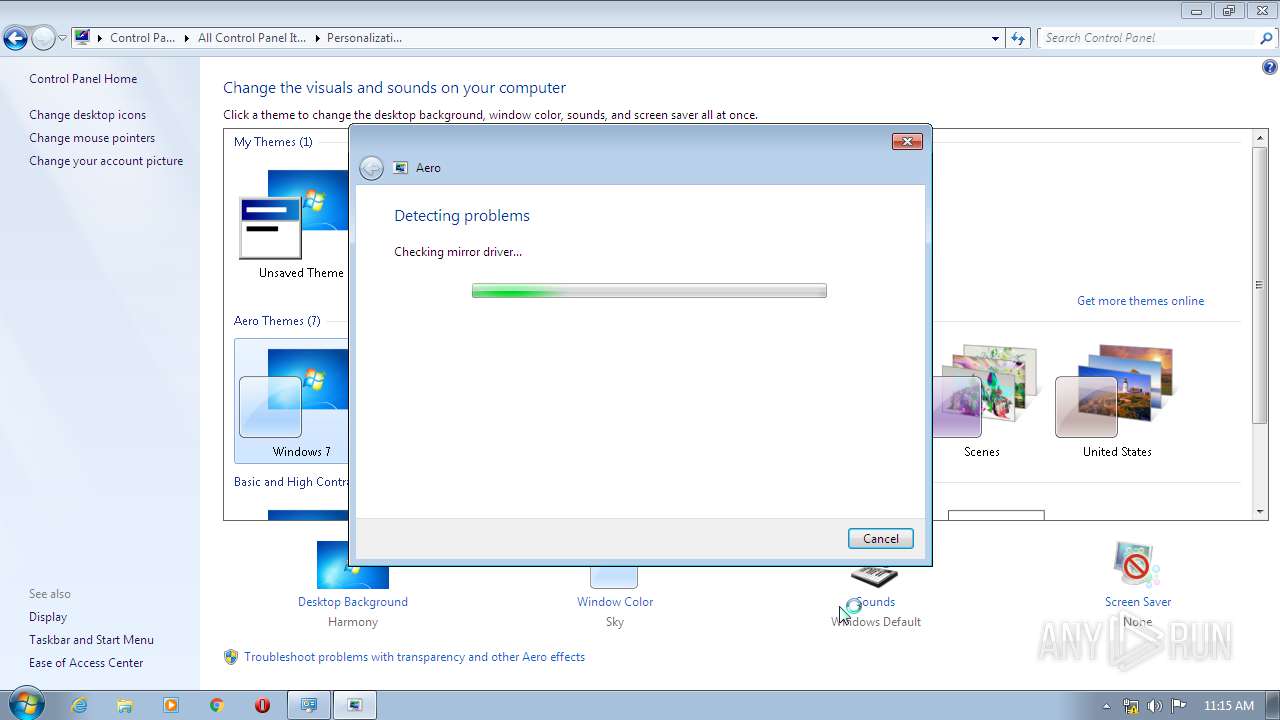
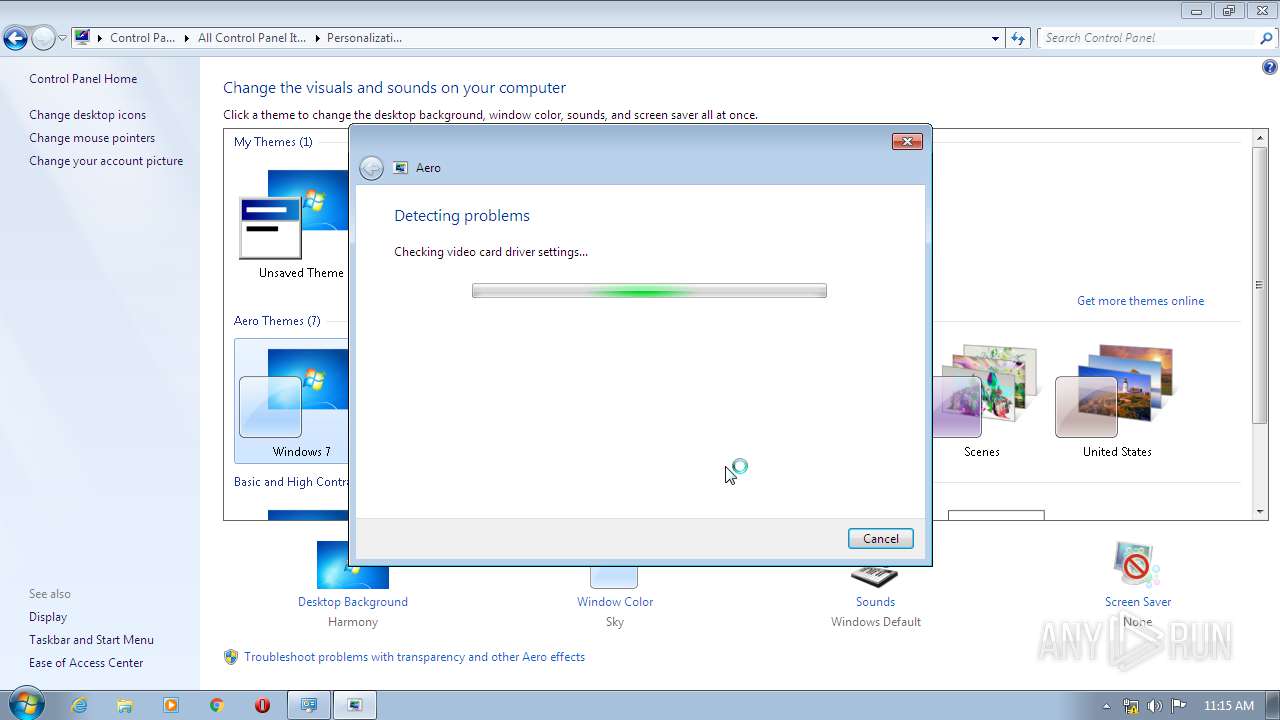
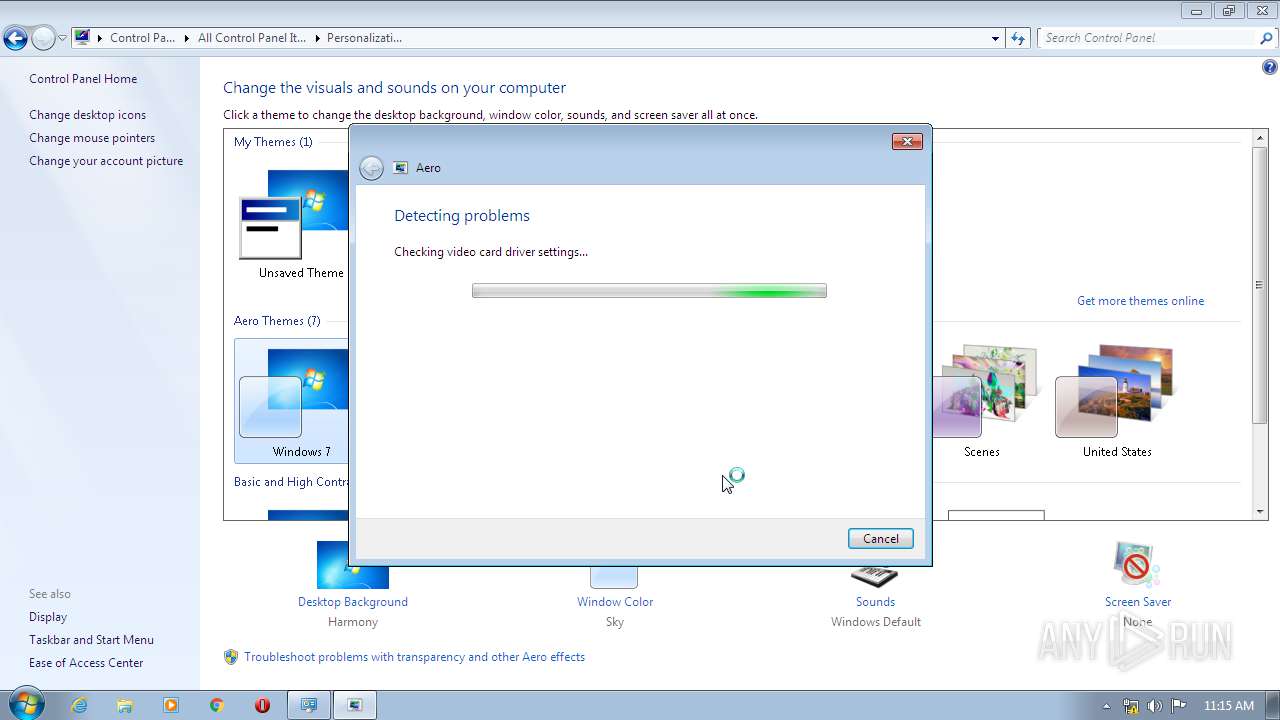
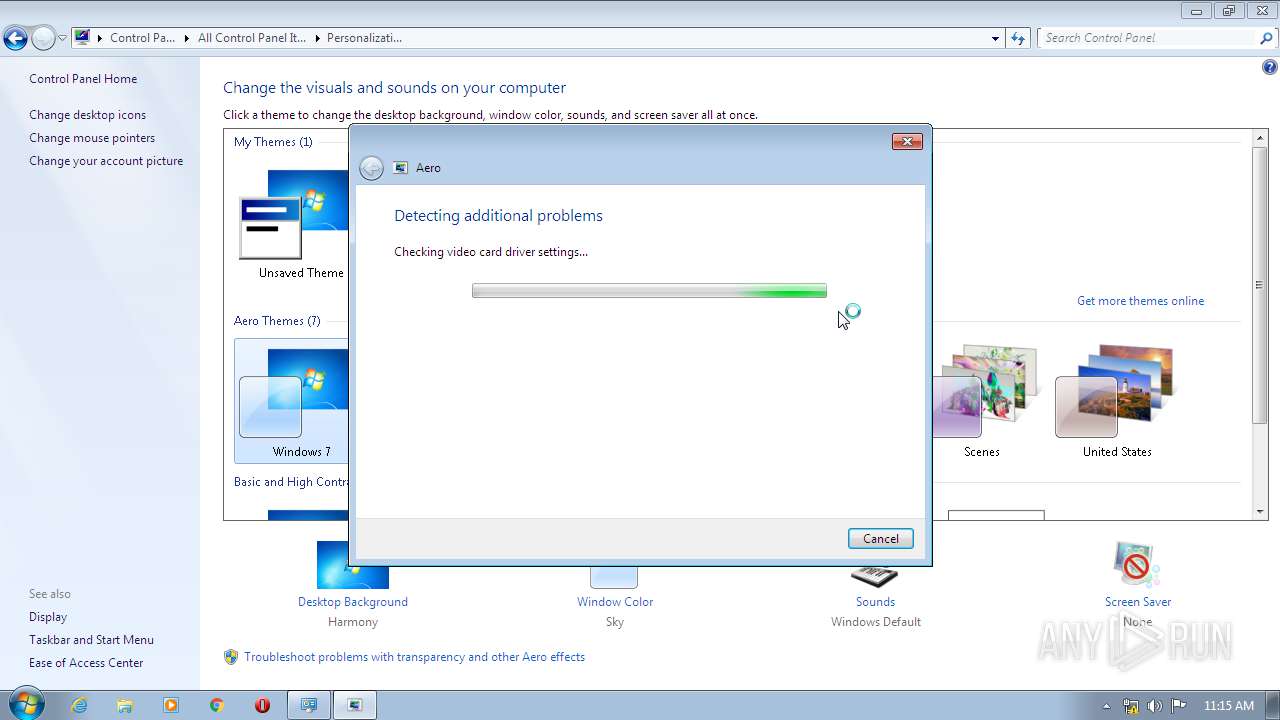
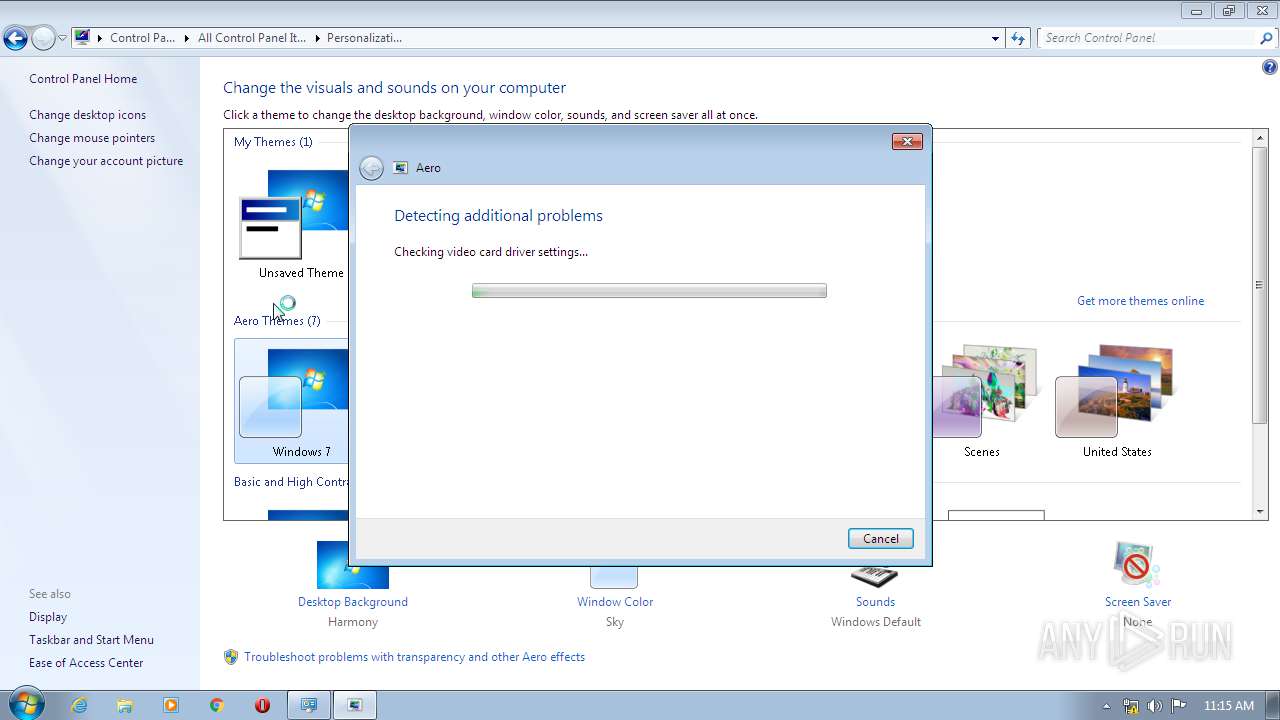
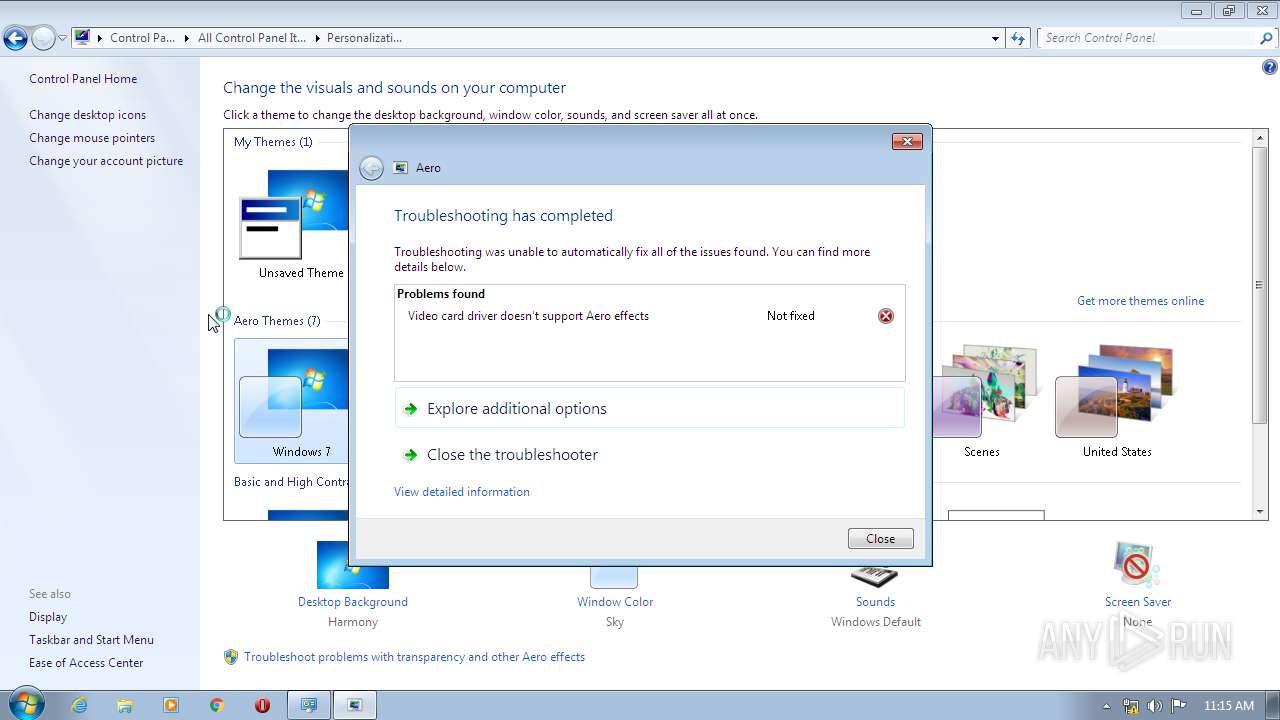
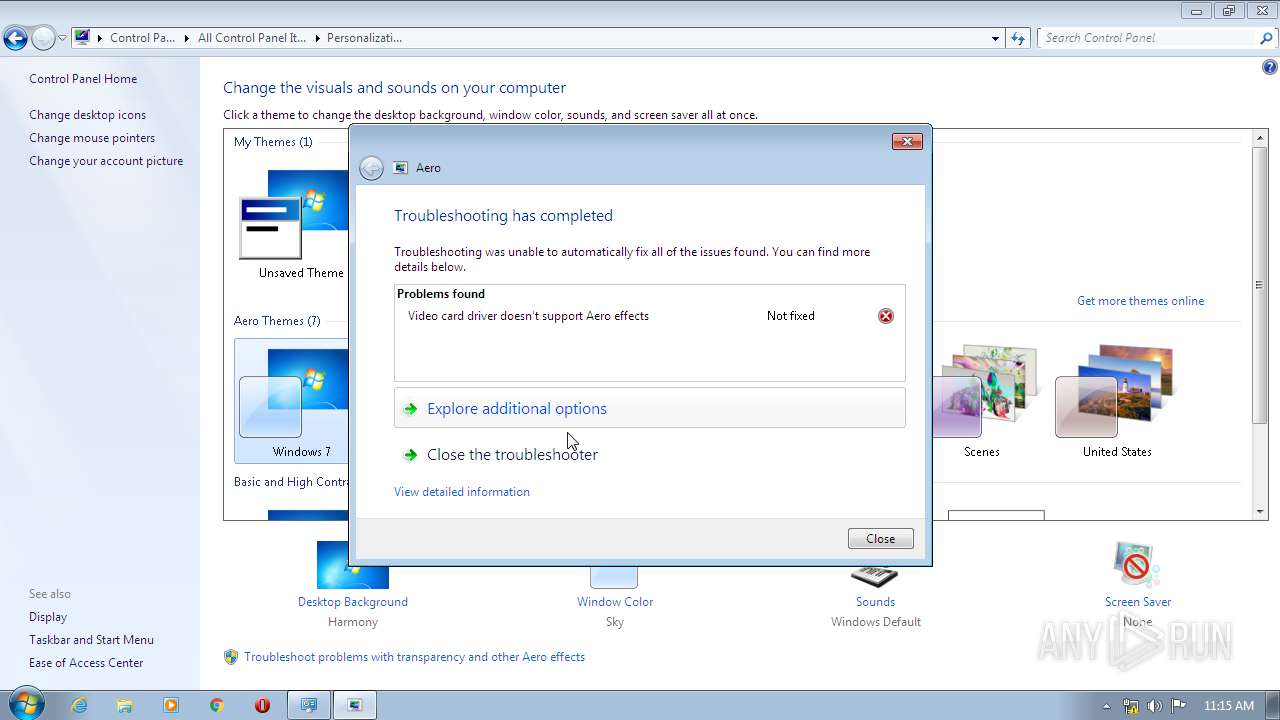
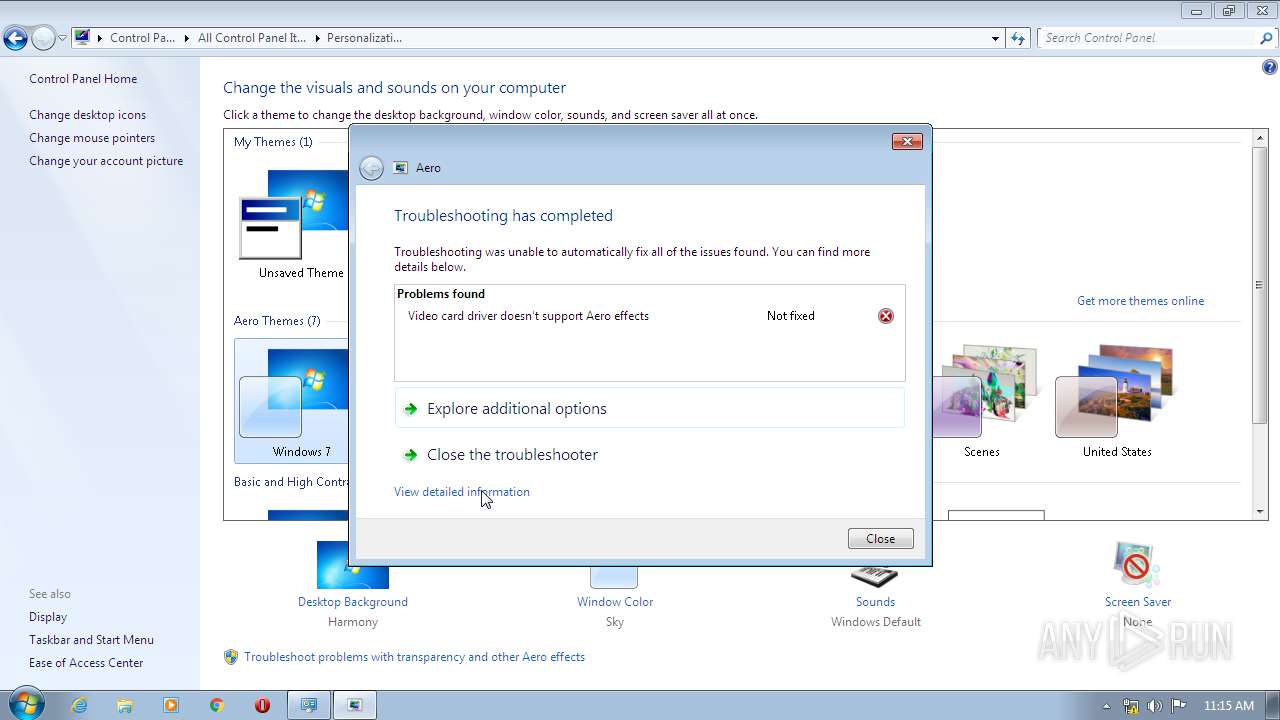
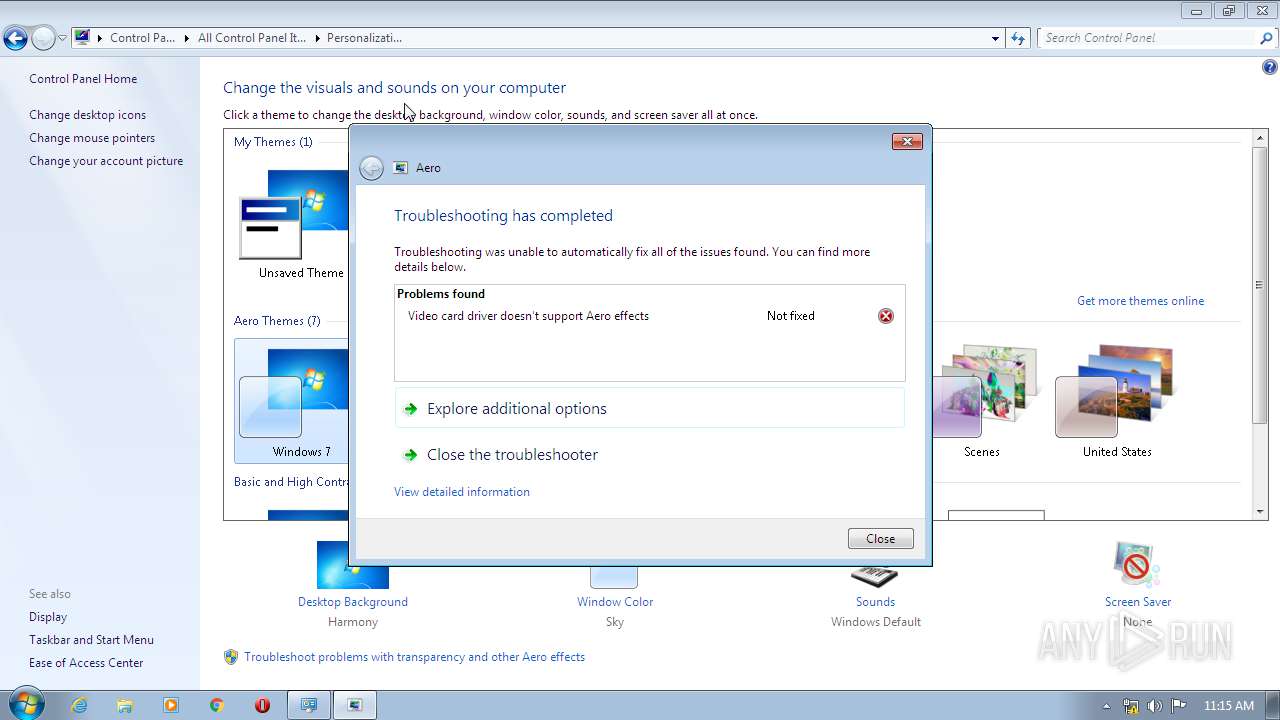
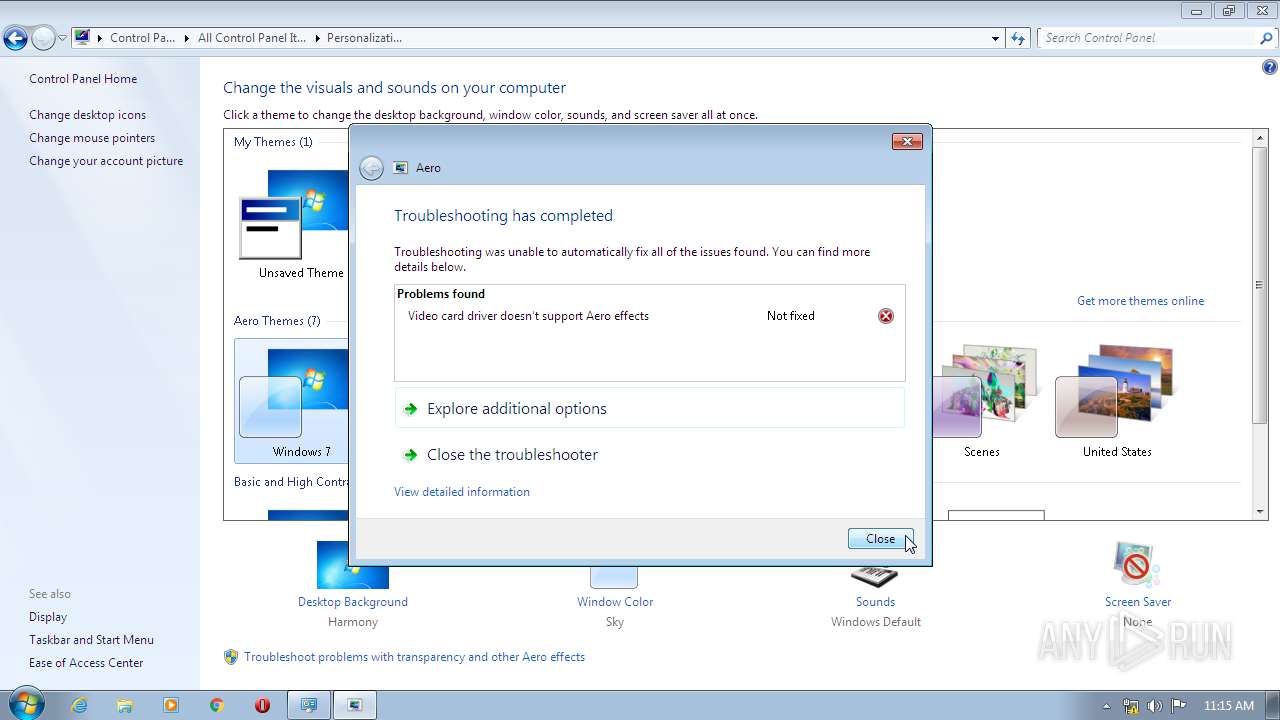
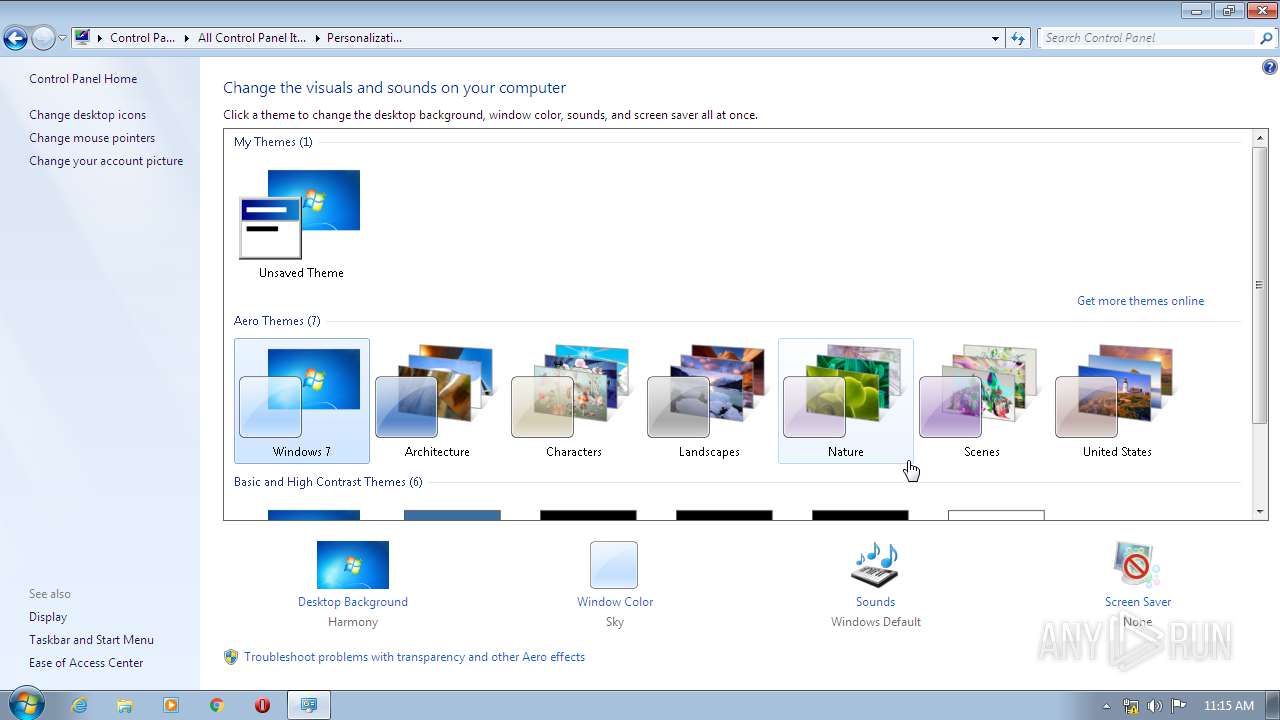
Starts Visual C# compiler
- sdiagnhost.exe (PID: 3840)
- sdiagnhost.exe (PID: 3592)
Changes the autorun value in the registry
- WinSat.exe (PID: 4032)
- WinSat.exe (PID: 3864)
- WinSat.exe (PID: 1900)
Changes settings of System certificates
- rufus-3.9p.exe (PID: 3580)
SUSPICIOUS
Reads Internet Cache Settings
- rufus-3.9p.exe (PID: 3580)
Application launched itself
- msdt.exe (PID: 4004)
Executable content was dropped or overwritten
- msdt.exe (PID: 3000)
Executed via COM
- sdiagnhost.exe (PID: 3840)
- sdiagnhost.exe (PID: 3592)
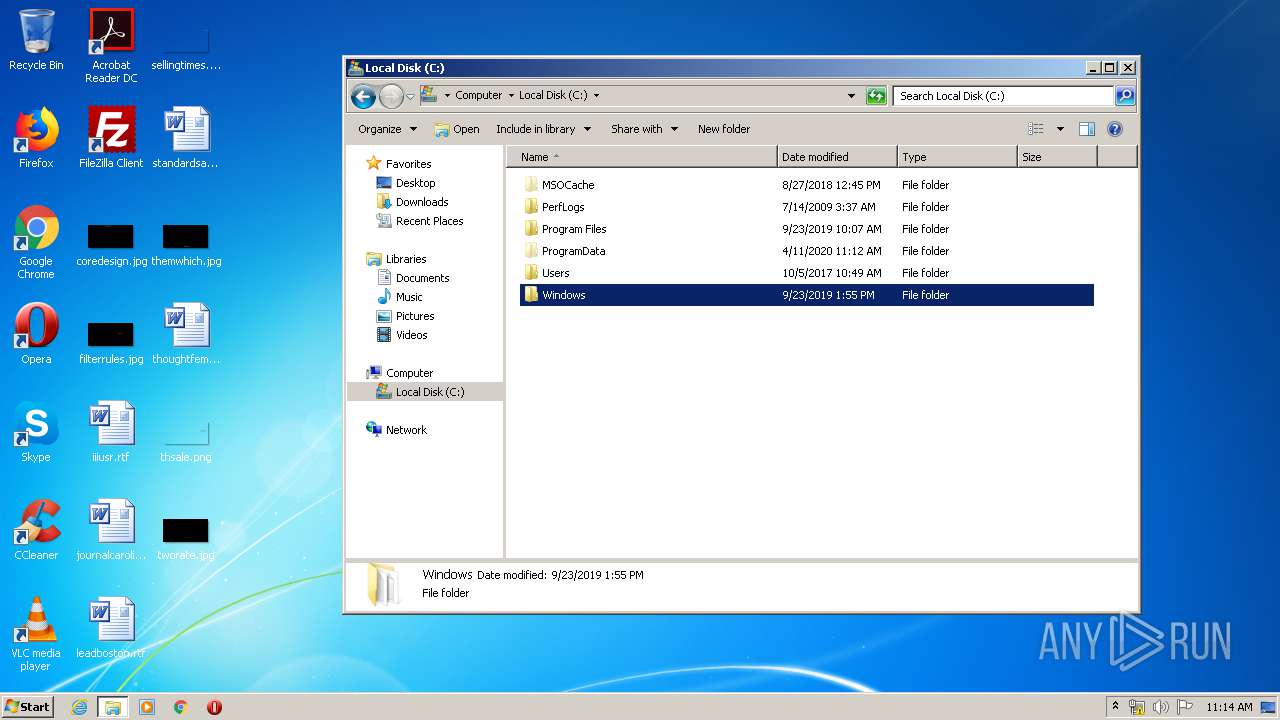
Creates files in the Windows directory
- msdt.exe (PID: 3000)
- WinSat.exe (PID: 3864)
- WinSat.exe (PID: 1900)
Low-level read access rights to disk partition
- WinSat.exe (PID: 3864)
- WinSat.exe (PID: 4032)
- WinSat.exe (PID: 1900)
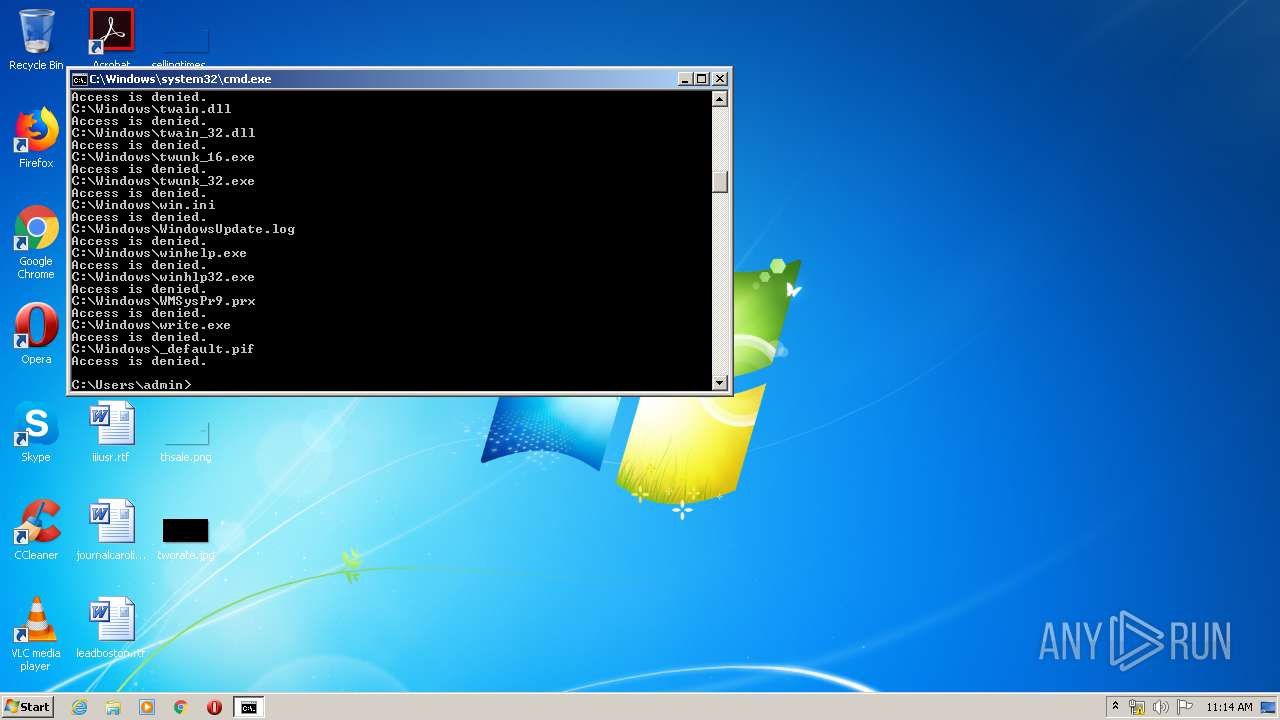
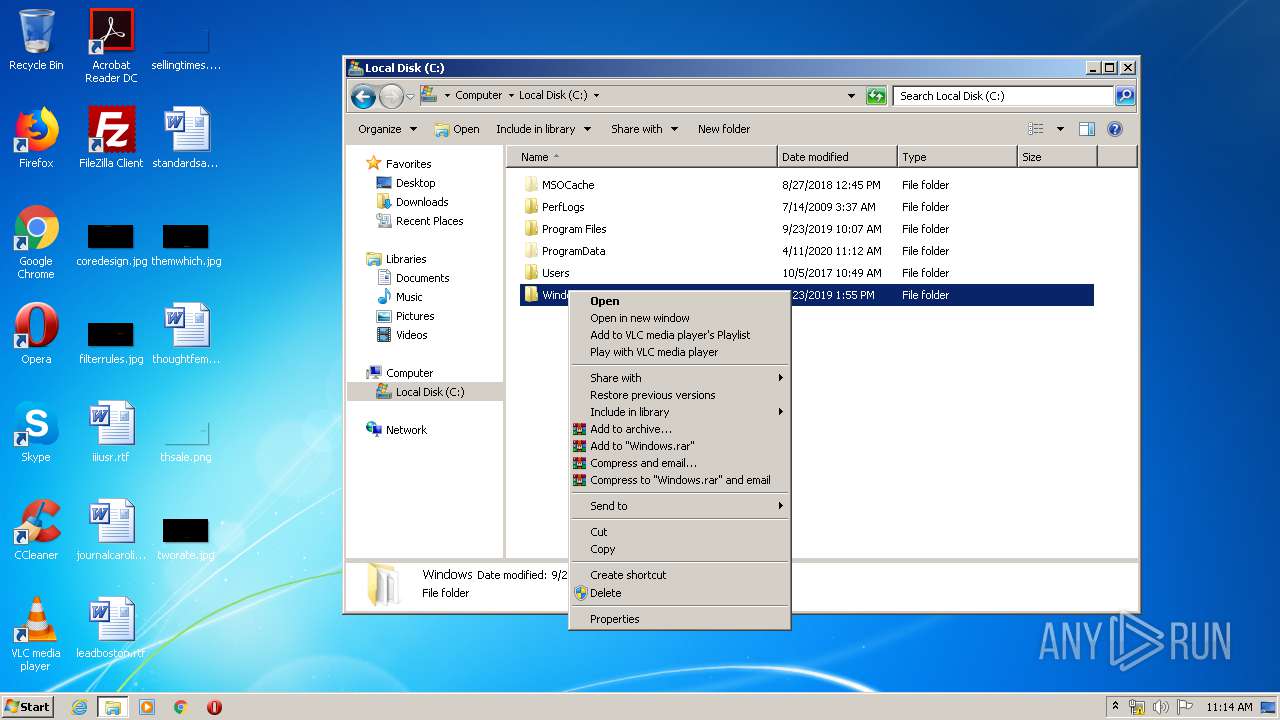
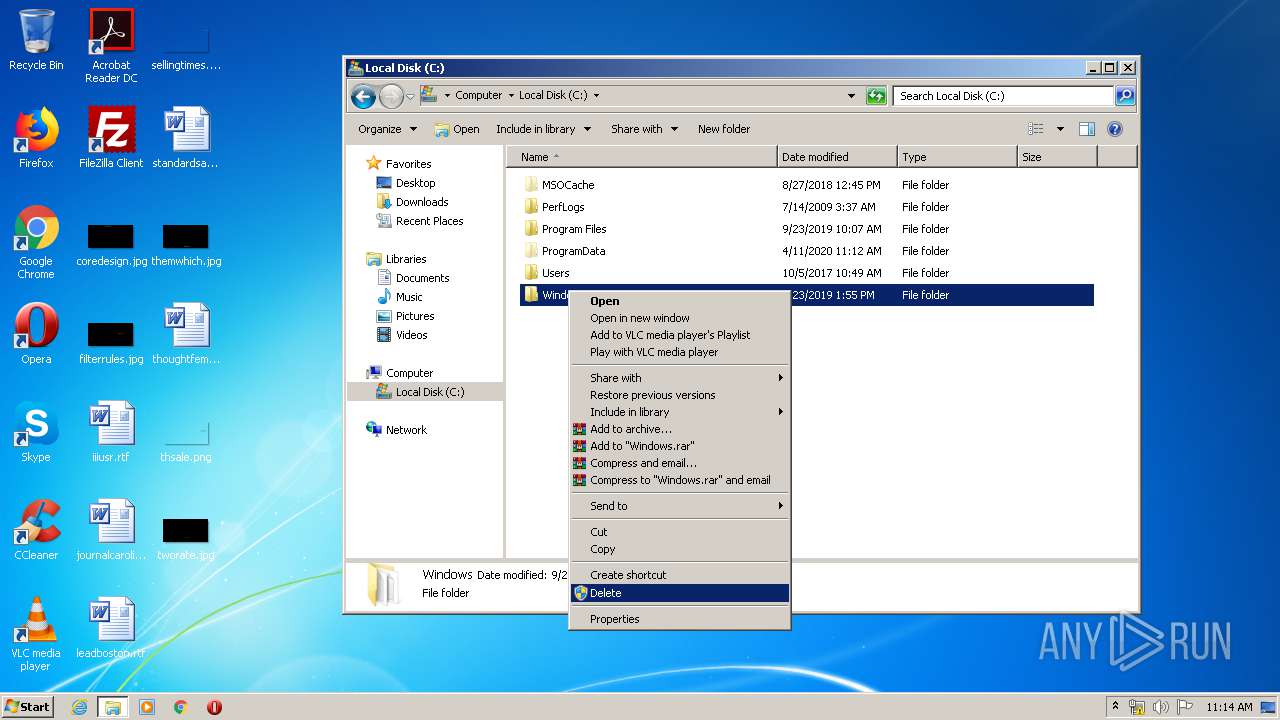
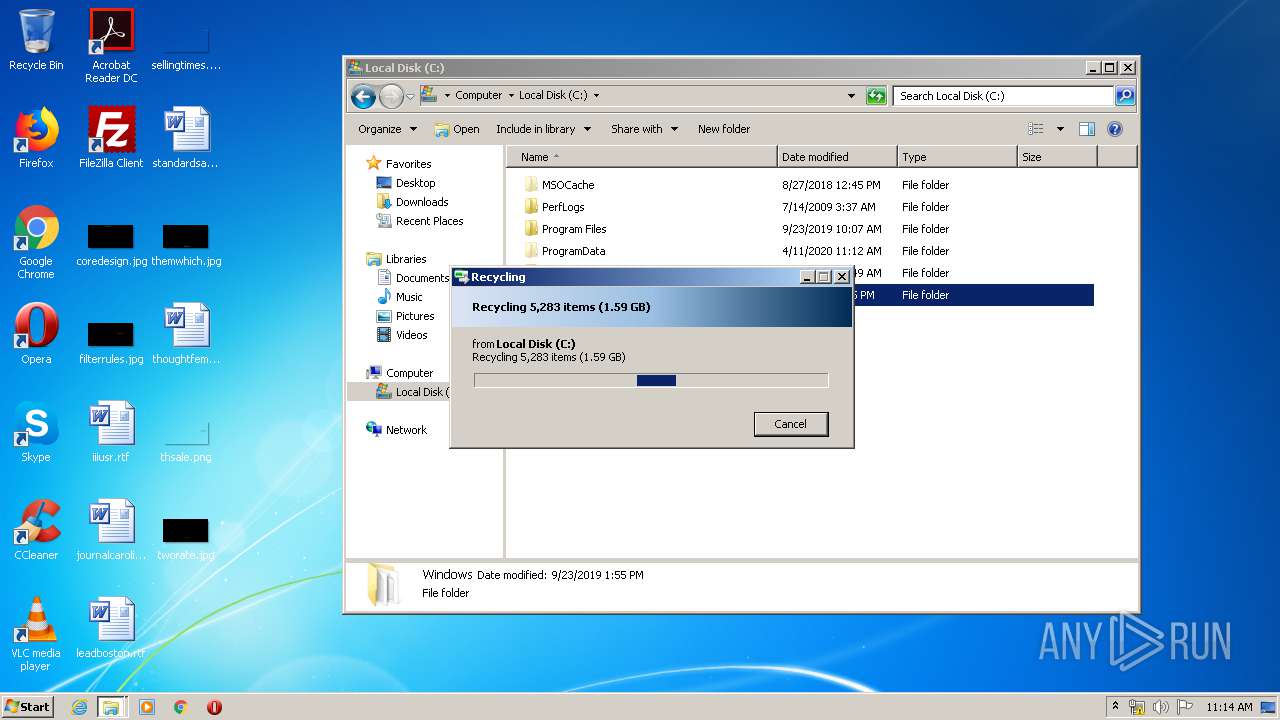
Removes files from Windows directory
- msdt.exe (PID: 3000)
Creates files in the program directory
- msdt.exe (PID: 3000)
Adds / modifies Windows certificates
- rufus-3.9p.exe (PID: 3580)
INFO
Creates files in the user directory
- opera.exe (PID: 1800)
Reads the hosts file
- chrome.exe (PID: 3440)
- chrome.exe (PID: 3820)
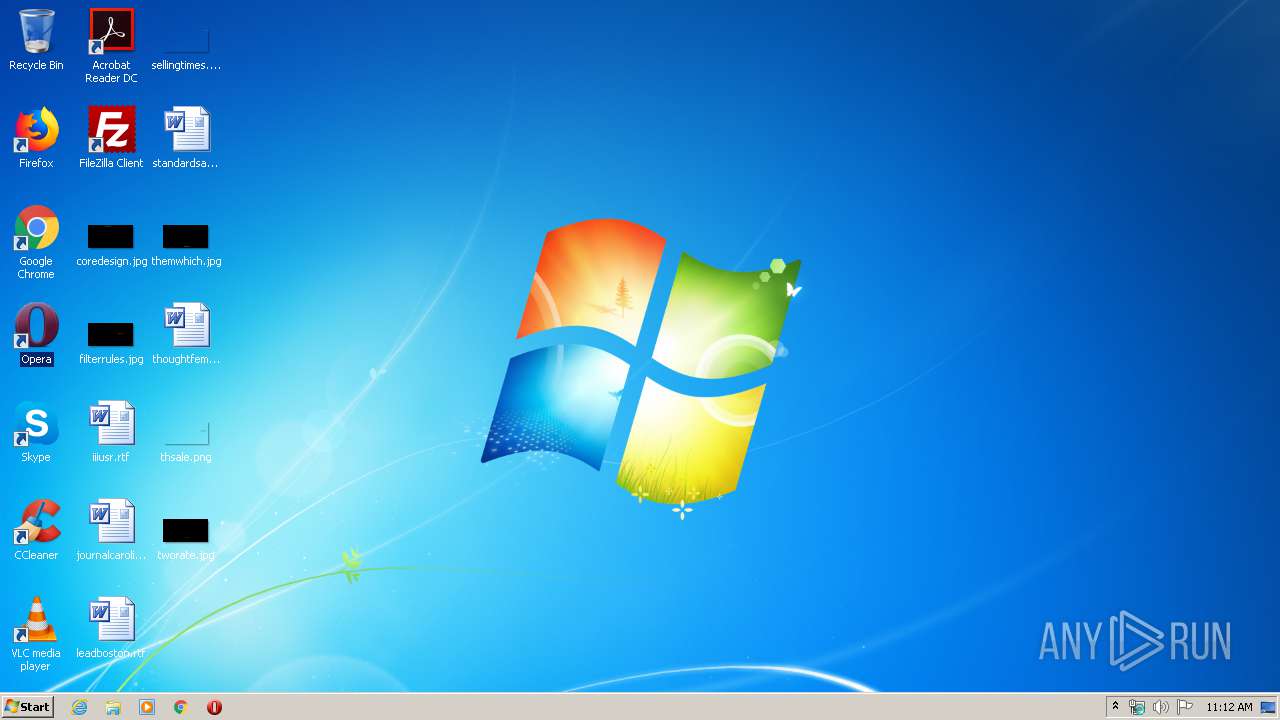
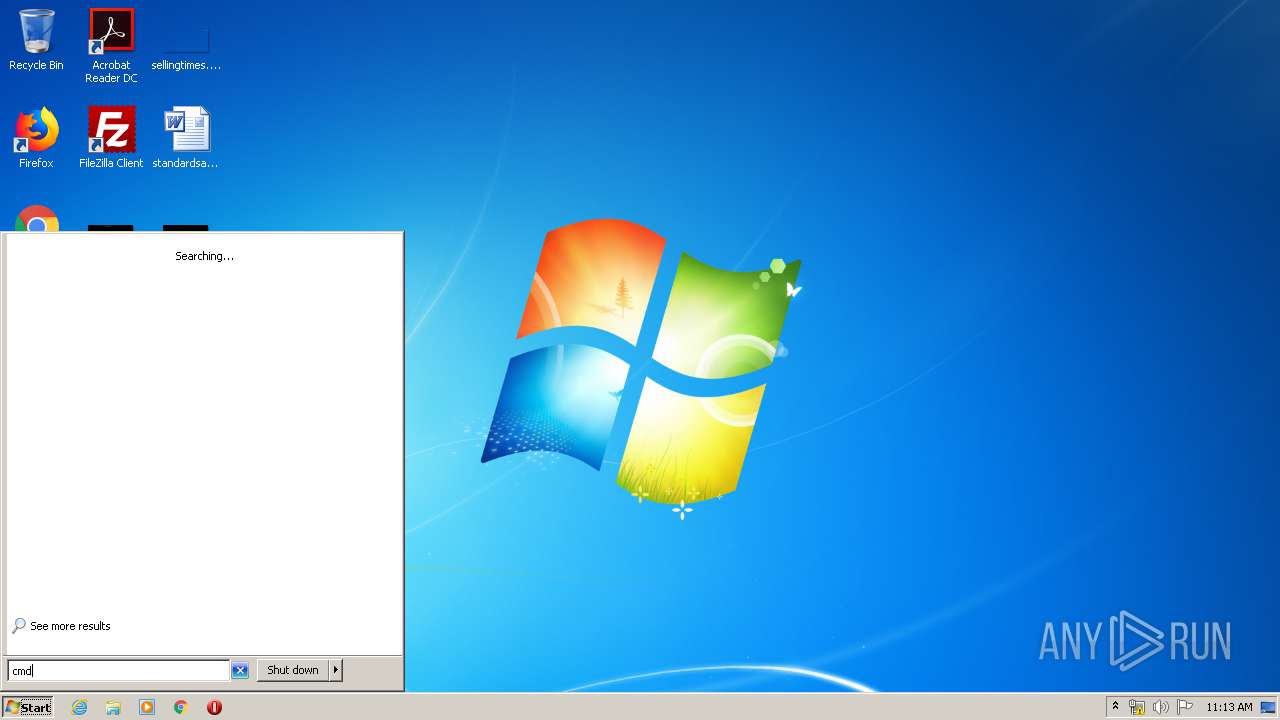
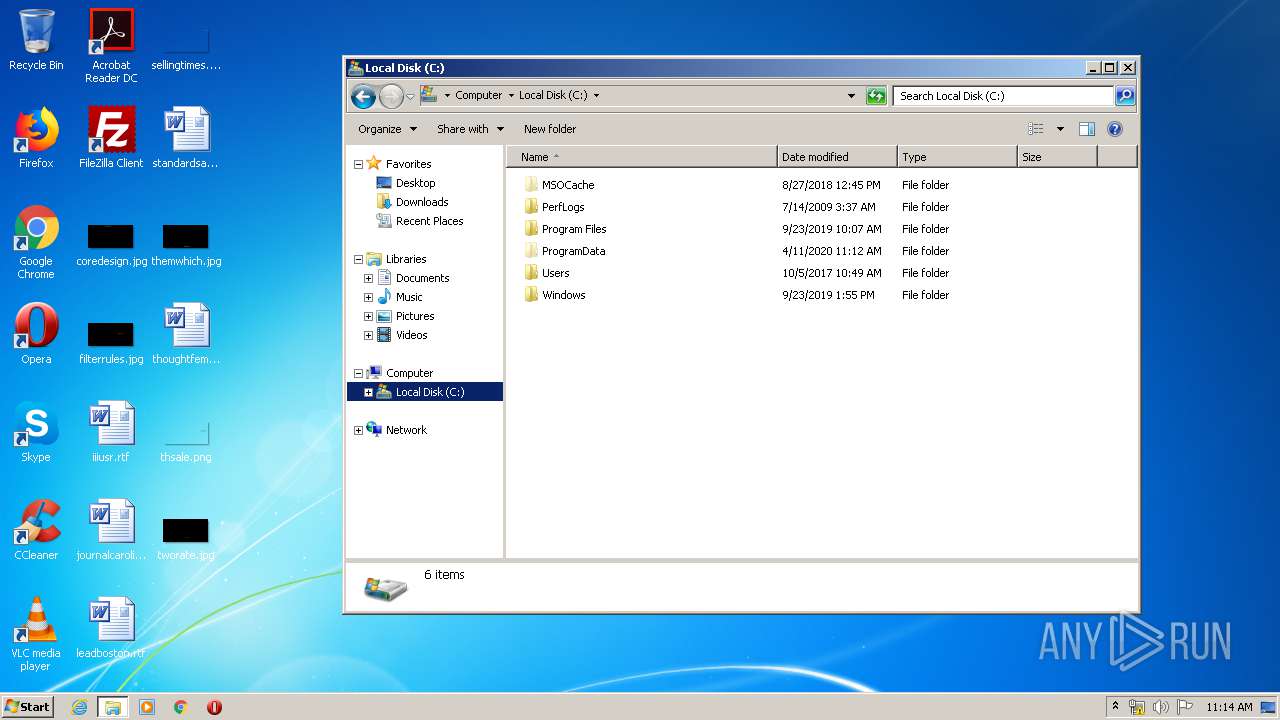
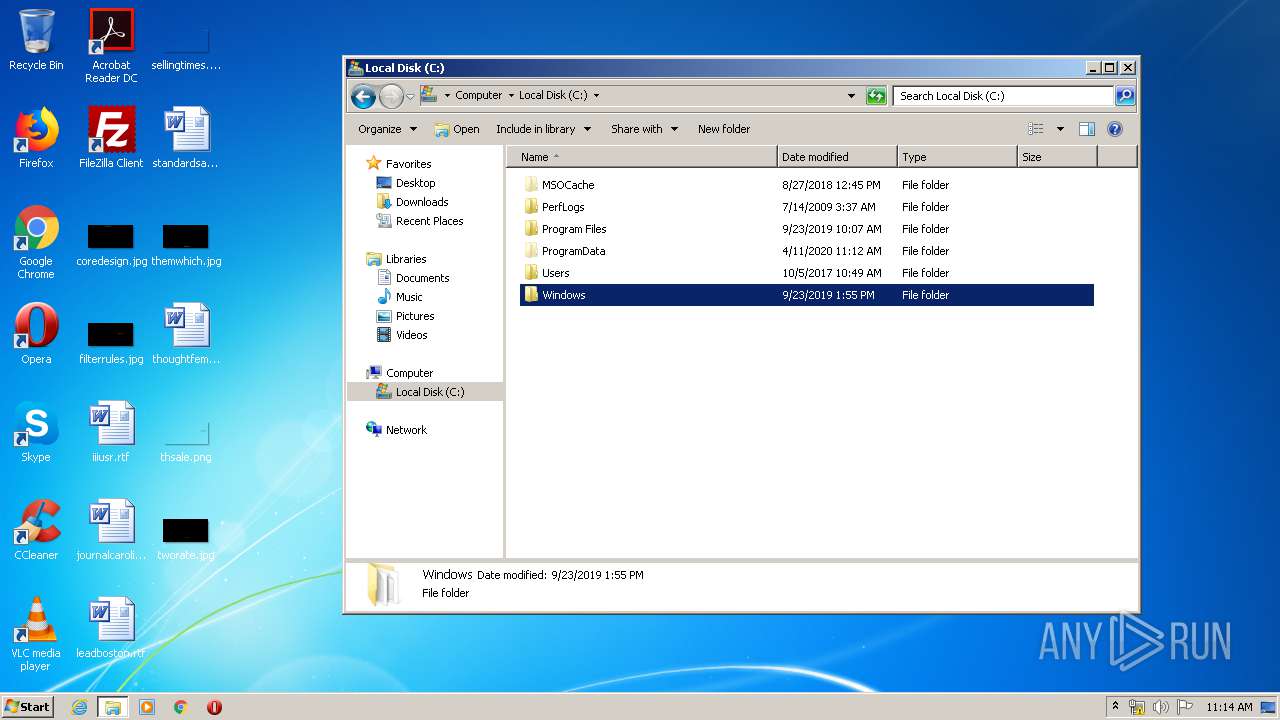
Manual execution by user
- opera.exe (PID: 1800)
- explorer.exe (PID: 1028)
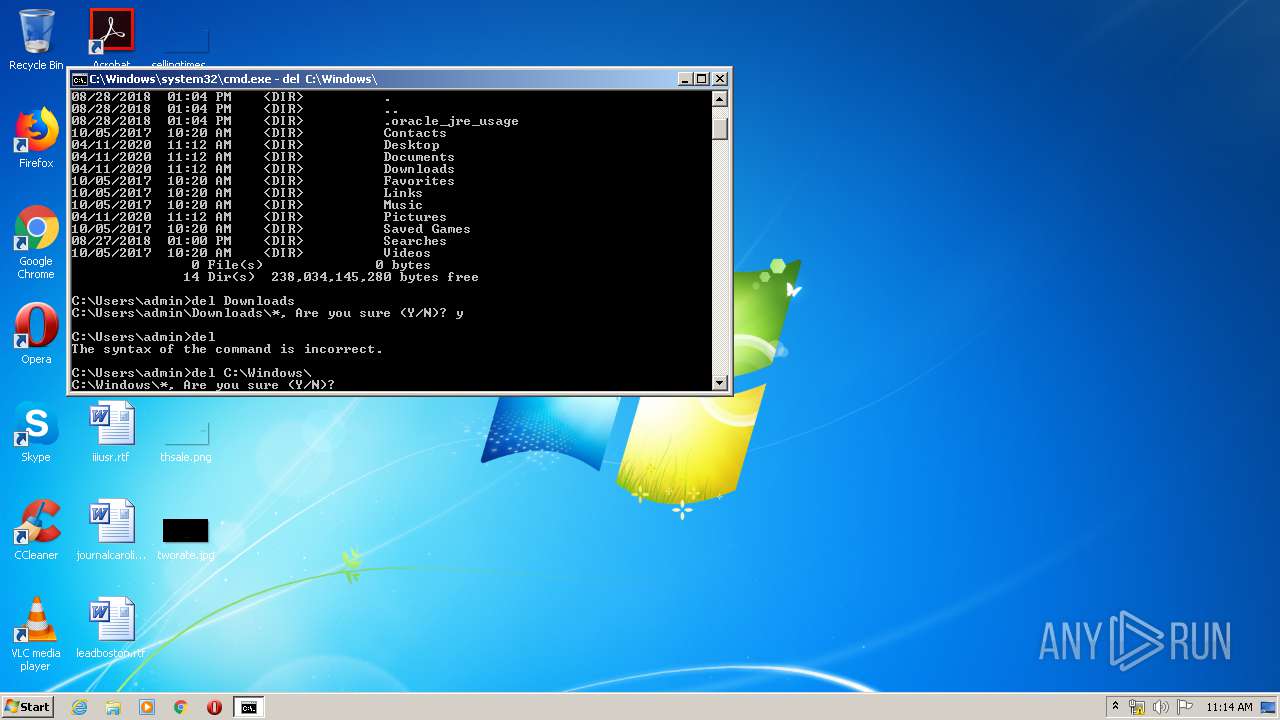
- cmd.exe (PID: 872)
- chrome.exe (PID: 3820)
- msdt.exe (PID: 4004)
Application launched itself
- chrome.exe (PID: 3820)
Reads settings of System Certificates
- rufus-3.9p.exe (PID: 3580)
- chrome.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.34 |
| CodeSize: | 1146880 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 2125824 |
| EntryPoint: | 0x31e5f0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.9.1624.0 |
| ProductVersionNumber: | 3.9.1624.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | https://rufus.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 3.9.1624 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2020 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/licenses/gpl-3.0.html |
| OriginalFileName: | rufus-3.9.exe |
| ProductName: | Rufus |
| ProductVersion: | 3.9.1624 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| TLS Callbacks: | 1 callback(s) detected. |
| Comments: | https://rufus.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 3.9.1624 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2020 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/licenses/gpl-3.0.html |
| OriginalFilename: | rufus-3.9.exe |
| ProductName: | Rufus |
| ProductVersion: | 3.9.1624 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00207000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00208000 | 0x00118000 | 0x00117200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99978 |
.rsrc | 0x00320000 | 0x0000B000 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9373 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17938 | 1895 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.68423 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.77127 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.98144 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.04318 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 7.93863 | 2398 | UNKNOWN | UNKNOWN | RT_DIALOG |
102 | 7.31034 | 316 | UNKNOWN | UNKNOWN | RT_DIALOG |
103 | 7.58795 | 470 | UNKNOWN | UNKNOWN | RT_DIALOG |
104 | 7.84457 | 1268 | UNKNOWN | UNKNOWN | RT_DIALOG |
105 | 6.86066 | 172 | UNKNOWN | UNKNOWN | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
COMDLG32.DLL |
CRYPT32.dll |
GDI32.dll |
KERNEL32.DLL |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
87
Monitored processes
34
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
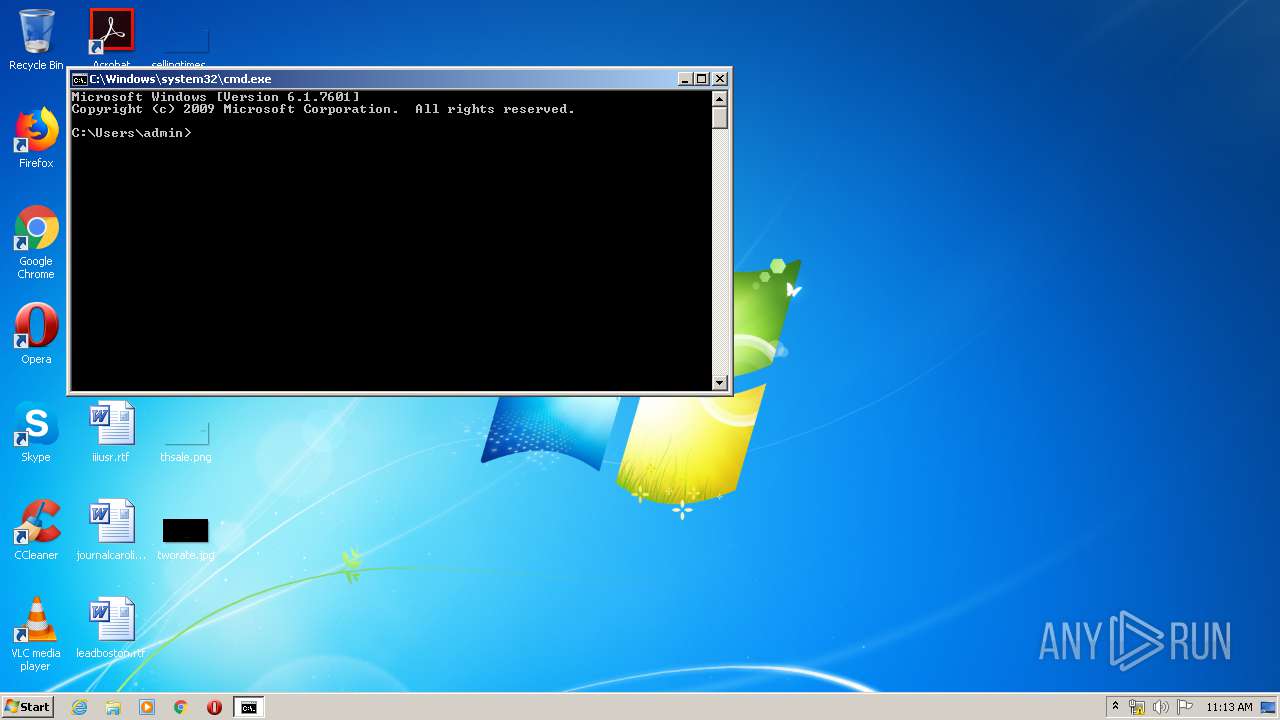
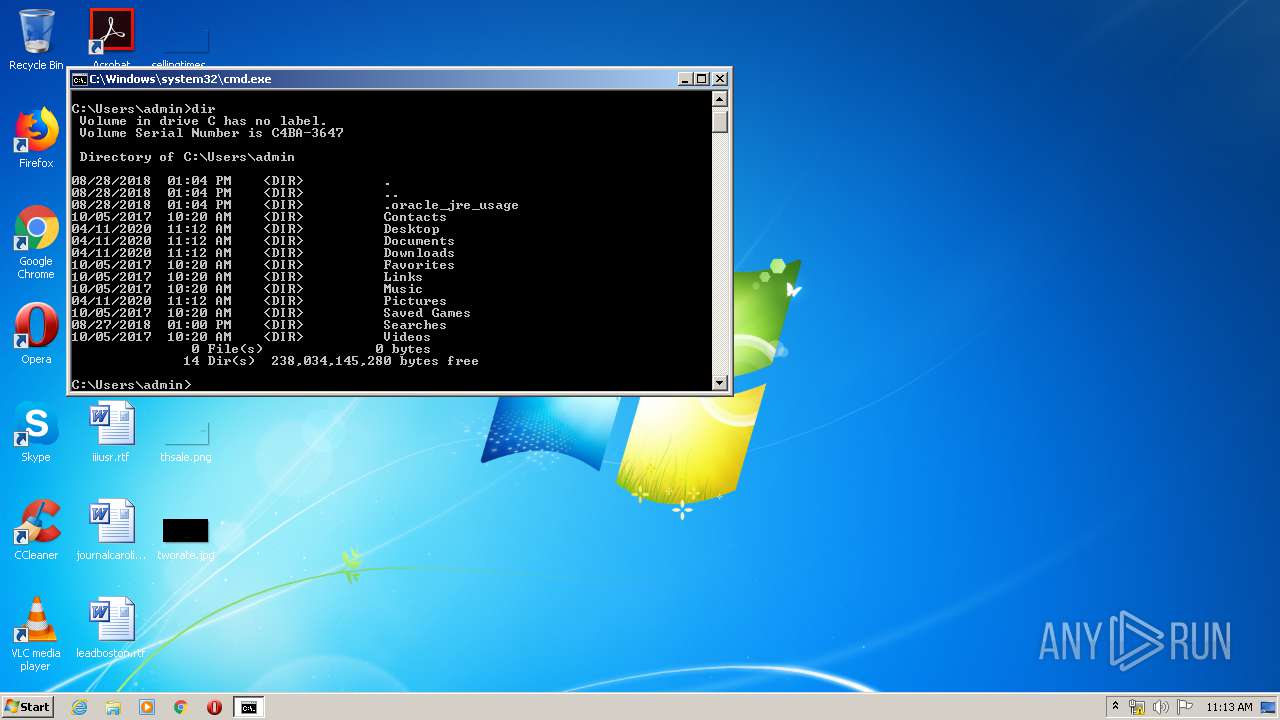
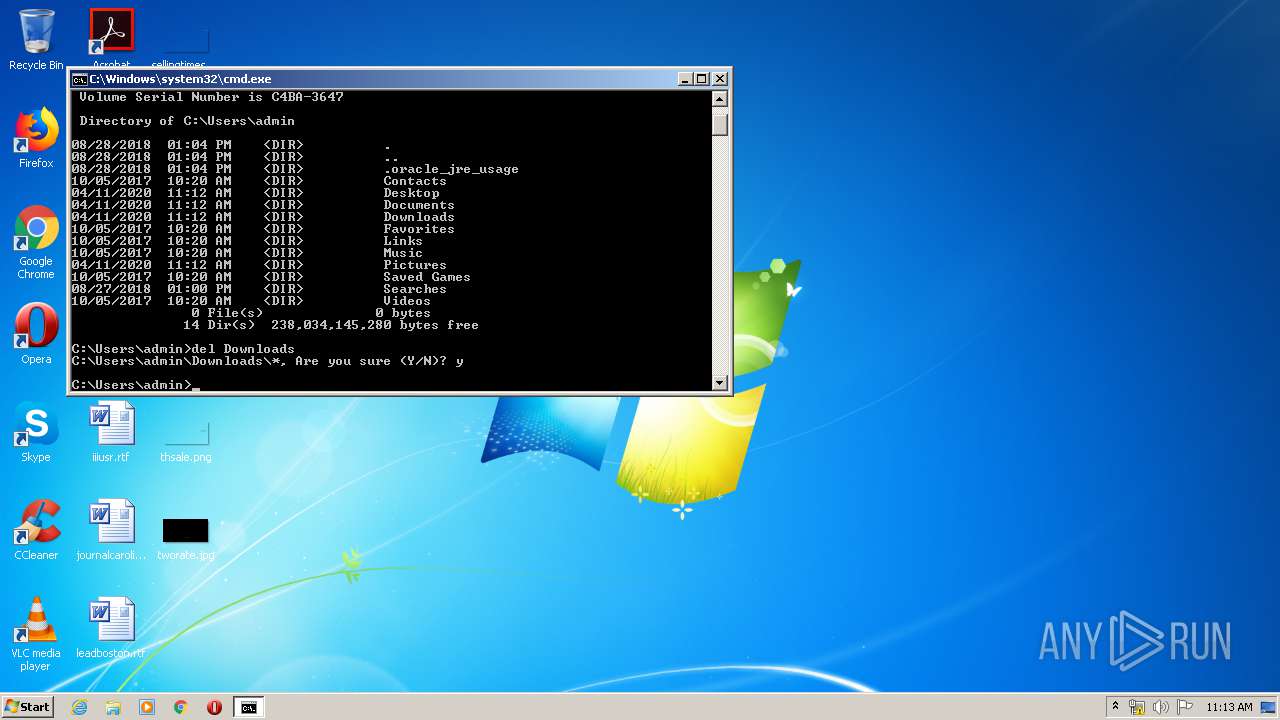
| 872 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1028 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,10654316406610964553,8618675141386048724,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11142889648978356379 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,10654316406610964553,8618675141386048724,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2634244060559358476 --mojo-platform-channel-handle=3408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,10654316406610964553,8618675141386048724,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8475245547899374813 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1564 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES83B1.tmp" "c:\Users\admin\AppData\Local\Temp\CSC83B0.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1900 | "C:\Windows\system32\WinSat.exe" features -xml features.xml | C:\Windows\system32\WinSat.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows System Assessment Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2112 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES847D.tmp" "c:\Users\admin\AppData\Local\Temp\CSC847C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
2 103
Read events
630
Write events
1 410
Delete events
63
Modification events
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | IncludeRecommendedUpdates |
Value: 0 | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | AutoInstallMinorUpdates |
Value: 0 | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}Machine\Software\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}Machine\Software\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}Machine\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoDriveTypeAutorun |
Value: 158 | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}User |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}Machine |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3580) rufus-3.9p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{E9B76602-D18B-403D-8532-DAFA7609D5CE}Machine\Software |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
8
Suspicious files
75
Text files
192
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | rufus-3.9p.exe | C:\Users\admin\AppData\Local\Temp\rufus.ini~ | — | |
MD5:— | SHA256:— | |||
| 3580 | rufus-3.9p.exe | C:\Users\admin\AppData\Local\Temp\Cab17B.tmp | — | |
MD5:— | SHA256:— | |||
| 3580 | rufus-3.9p.exe | C:\Users\admin\AppData\Local\Temp\Tar17C.tmp | — | |
MD5:— | SHA256:— | |||
| 3580 | rufus-3.9p.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Fido[1].ver | — | |
MD5:— | SHA256:— | |||
| 1800 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2A40.tmp | — | |
MD5:— | SHA256:— | |||
| 1800 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2A8F.tmp | — | |
MD5:— | SHA256:— | |||
| 3580 | rufus-3.9p.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:— | SHA256:— | |||
| 3580 | rufus-3.9p.exe | C:\Windows\System32\GroupPolicy\GPT.INI | text | |
MD5:— | SHA256:— | |||
| 3580 | rufus-3.9p.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C31B2498754E340573F1336DE607D619 | der | |
MD5:— | SHA256:— | |||
| 3580 | rufus-3.9p.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5887976EDAA817EEF5159B09F6FCD000_F64DCBBA399D666280C86776448D3B95 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
16
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3580 | rufus-3.9p.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
3580 | rufus-3.9p.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3580 | rufus-3.9p.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3580 | rufus-3.9p.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
3580 | rufus-3.9p.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuqL92L3tjkN67RNFF%2FEdvT6NEzAQUwBKyKHRoRmfpcCV0GgBFWwZ9XEQCEAgt9o7pxpMVvr9yB5s4EP0%3D | US | der | 471 b | whitelisted |
1800 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1800 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3440 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3440 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3440 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3440 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3580 | rufus-3.9p.exe | 140.82.118.3:443 | github.com | — | US | malicious |
3580 | rufus-3.9p.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3580 | rufus-3.9p.exe | 52.216.145.91:443 | github-production-release-asset-2e65be.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
3440 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3440 | chrome.exe | 172.217.18.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rufus.ie |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
github.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
github-production-release-asset-2e65be.s3.amazonaws.com |
| shared |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
Threats
Process | Message |
|---|---|
rufus-3.9p.exe | *** Rufus init ***
|
rufus-3.9p.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-3.9p.exe | localization: found locale 'ko-KR'
|
rufus-3.9p.exe | localization: found locale 'hu-HU'
|
rufus-3.9p.exe | localization: found locale 'nl-NL'
|
rufus-3.9p.exe | localization: found locale 'zh-CN'
|
rufus-3.9p.exe | localization: found locale 'en-US'
|
rufus-3.9p.exe | localization: found locale 'bg-BG'
|
rufus-3.9p.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-3.9p.exe | localization: found locale 'fr-FR'
|