| URL: | http://bit.ly/2qqAlYy |
| Full analysis: | https://app.any.run/tasks/af2d70cd-4ce8-4585-a909-6704a34835d0 |
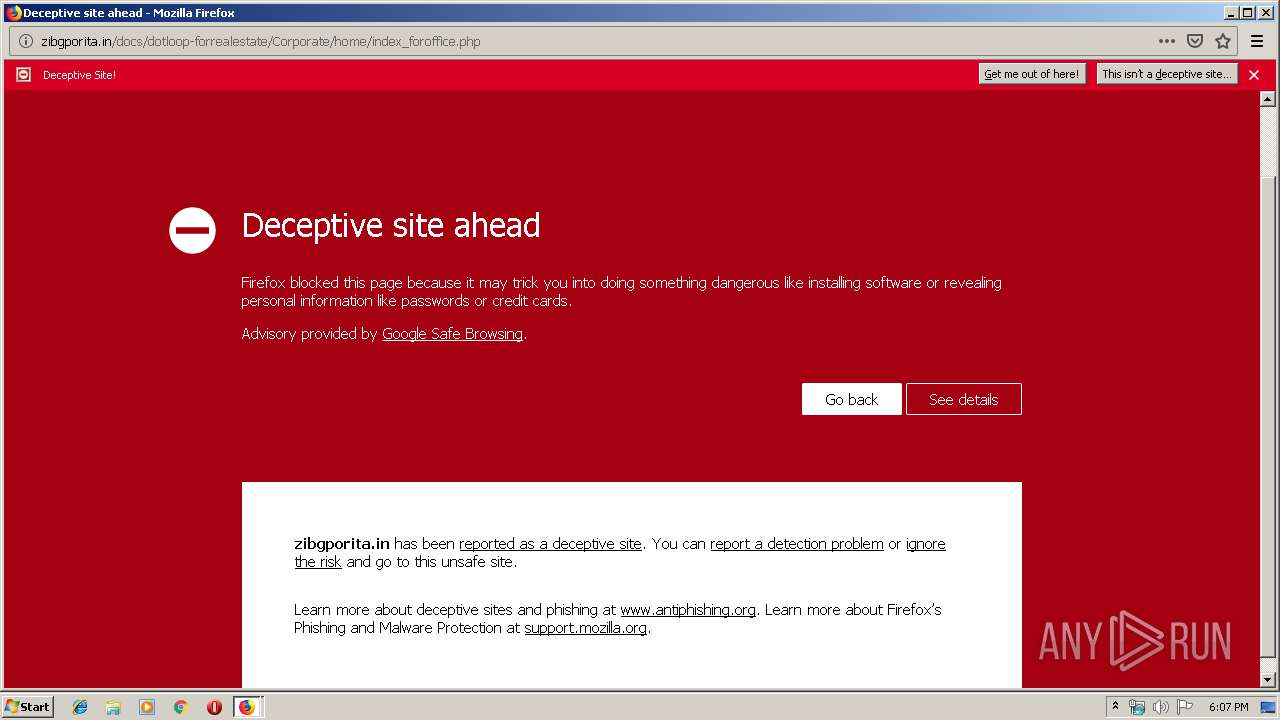
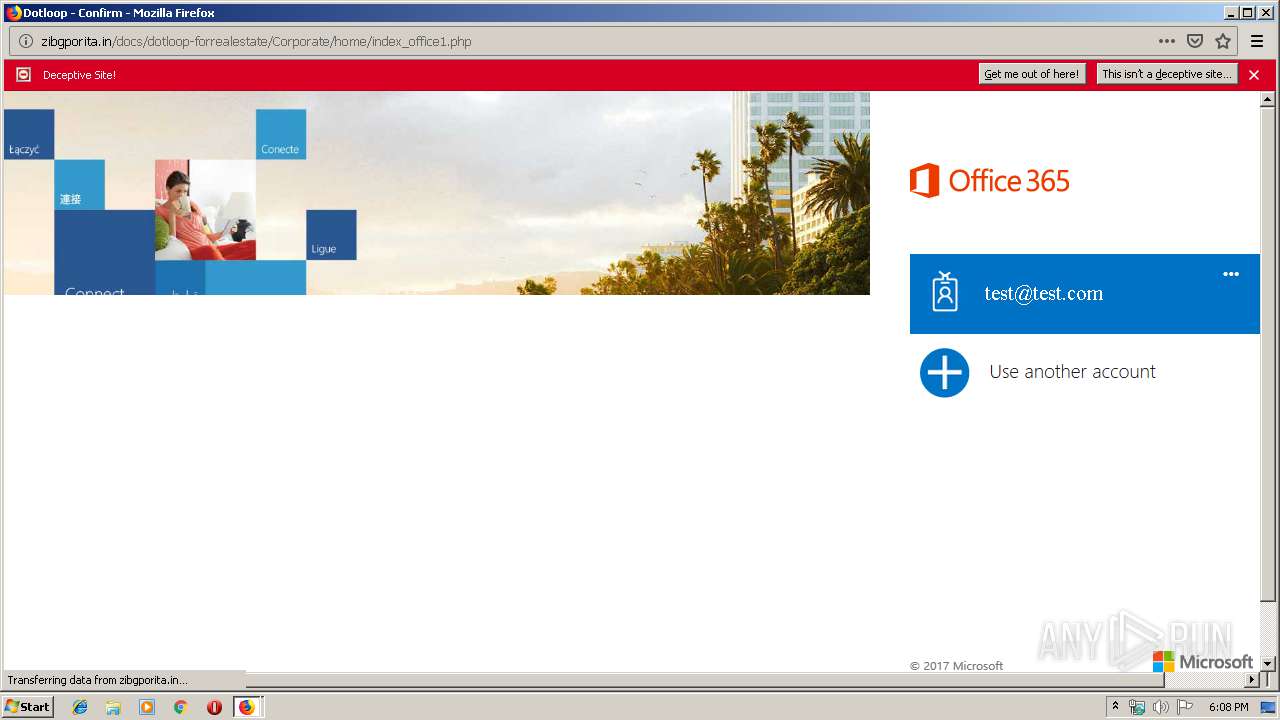
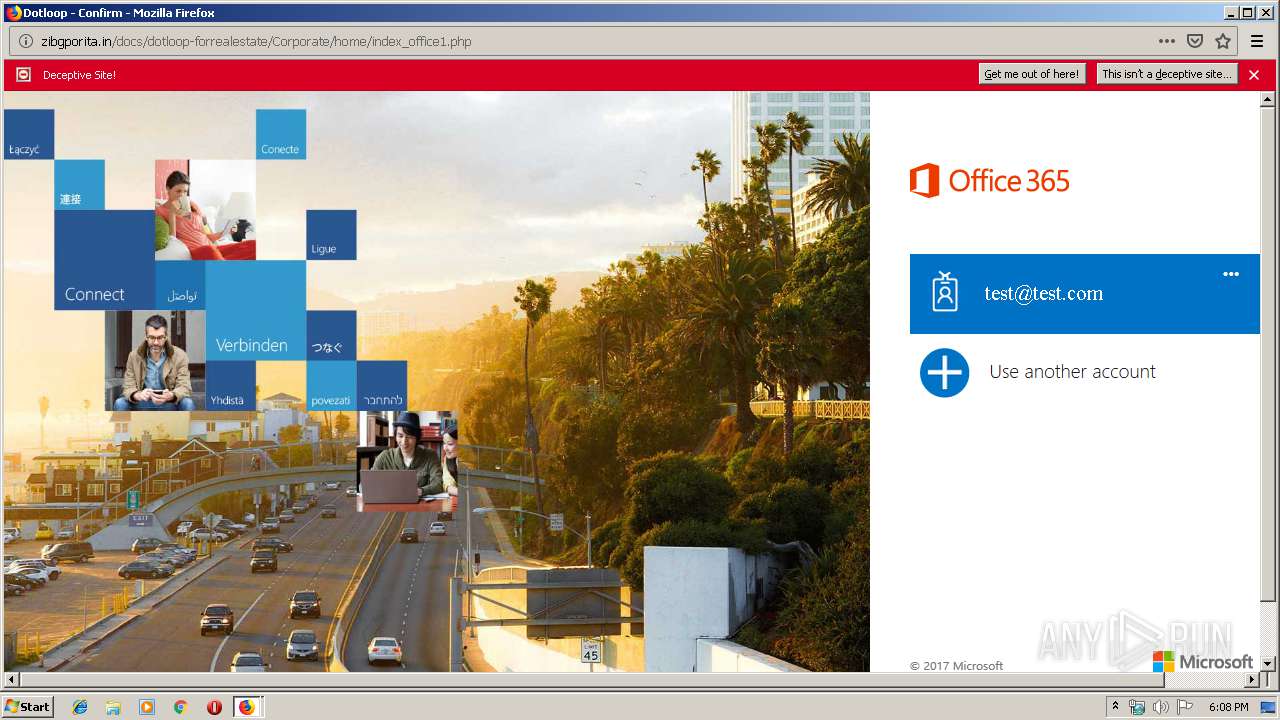
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 18:07:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F25DABA7BE4B48DA73912D70354E667E |
| SHA1: | 4376C453D4BBC0E29F6ABC9141D1FDCE3F5C6D32 |
| SHA256: | D761B413F94BBC7FCCCBCF2AA848B666A9E67A8EC097568AC2A1DDB29DDB7826 |
| SSDEEP: | 3:N1KcQ9TUoc:CcYw |
MALICIOUS
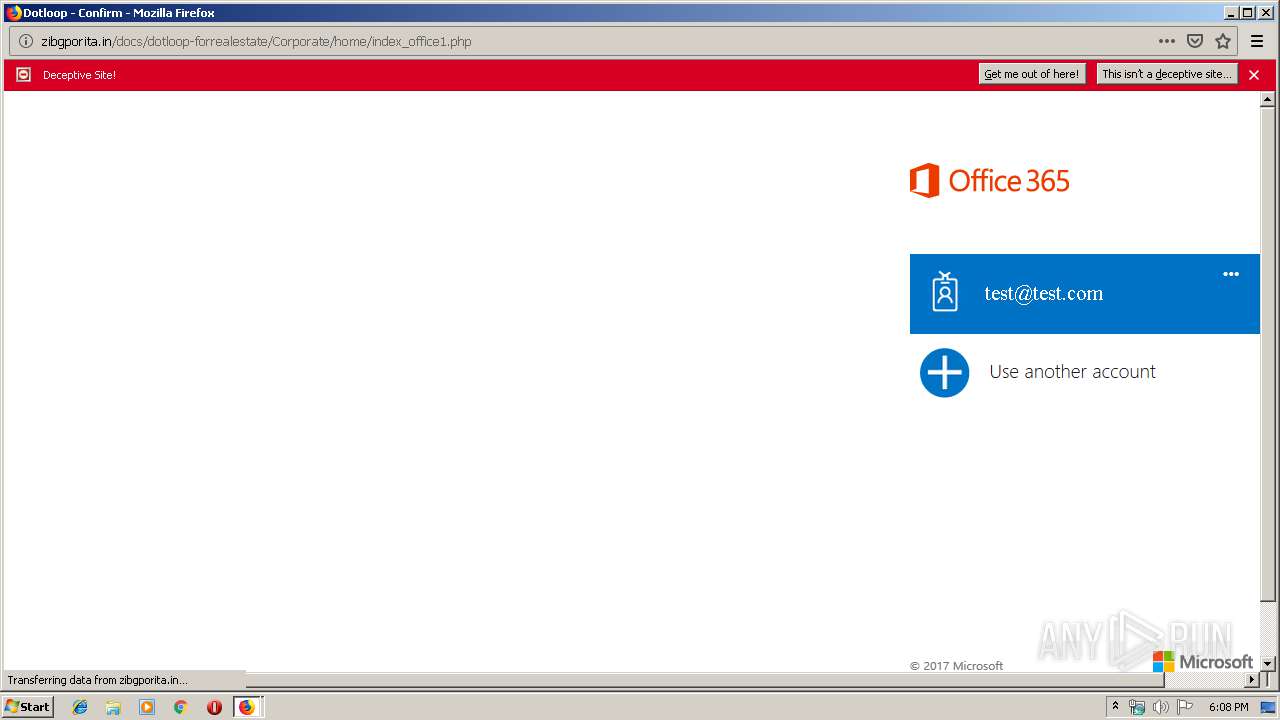
Loads Microsoft favicon from HTTP
- firefox.exe (PID: 3944)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 3944)
INFO
Creates files in the user directory
- firefox.exe (PID: 3944)
Reads CPU info
- firefox.exe (PID: 3944)
Application launched itself
- firefox.exe (PID: 2344)
- firefox.exe (PID: 3944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1316 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3944.20.177648051\1901539000" -childID 3 -isForBrowser -prefsHandle 3780 -prefMapHandle 3776 -prefsLen 7297 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3944 "\\.\pipe\gecko-crash-server-pipe.3944" 3792 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3944.3.818885202\1431381812" -childID 1 -isForBrowser -prefsHandle 1732 -prefMapHandle 1728 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3944 "\\.\pipe\gecko-crash-server-pipe.3944" 1640 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://bit.ly/2qqAlYy" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3944.13.1087627498\852165200" -childID 2 -isForBrowser -prefsHandle 2856 -prefMapHandle 2860 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3944 "\\.\pipe\gecko-crash-server-pipe.3944" 2872 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2988 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3944.0.948578205\2003081460" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3944 "\\.\pipe\gecko-crash-server-pipe.3944" 1176 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3944 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://bit.ly/2qqAlYy | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
571
Read events
566
Write events
5
Delete events
0
Modification events
| (PID) Process: | (3944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 7FD5411803000000 | |||
| (PID) Process: | (2344) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: A60F3F1803000000 | |||
| (PID) Process: | (3944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
68
Text files
35
Unknown types
57
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 3944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
40
DNS requests
85
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
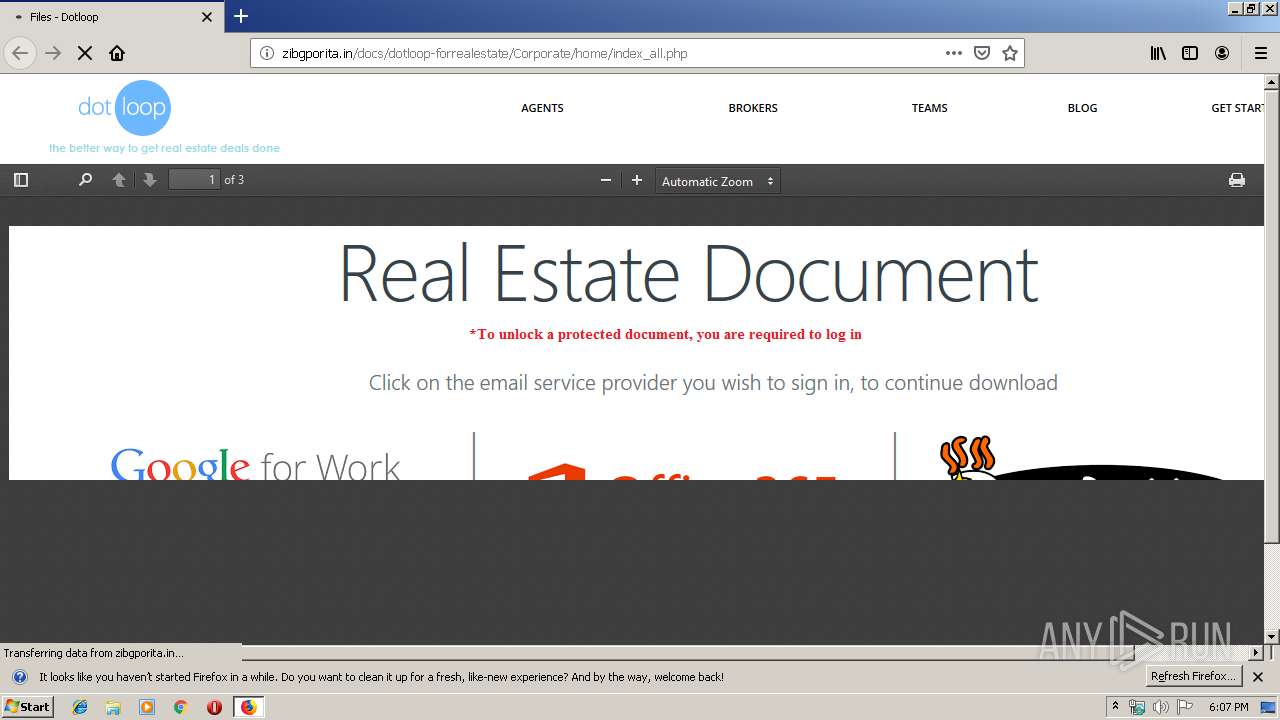
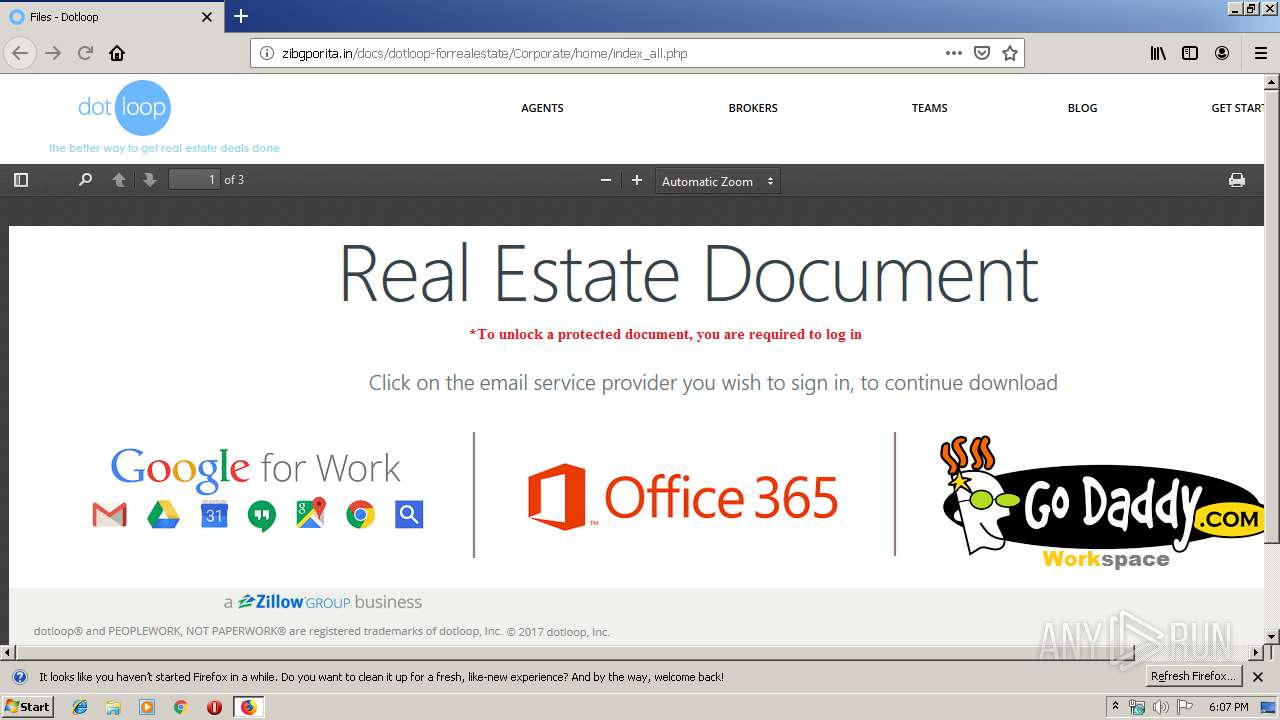
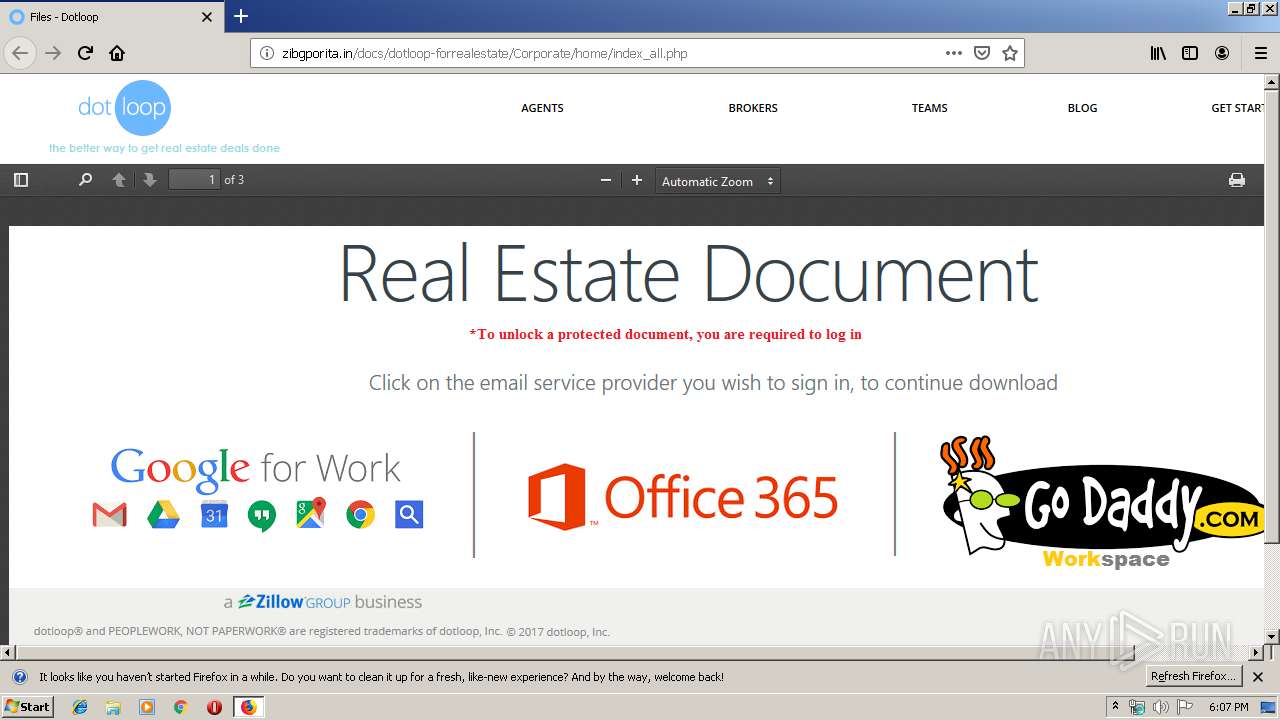
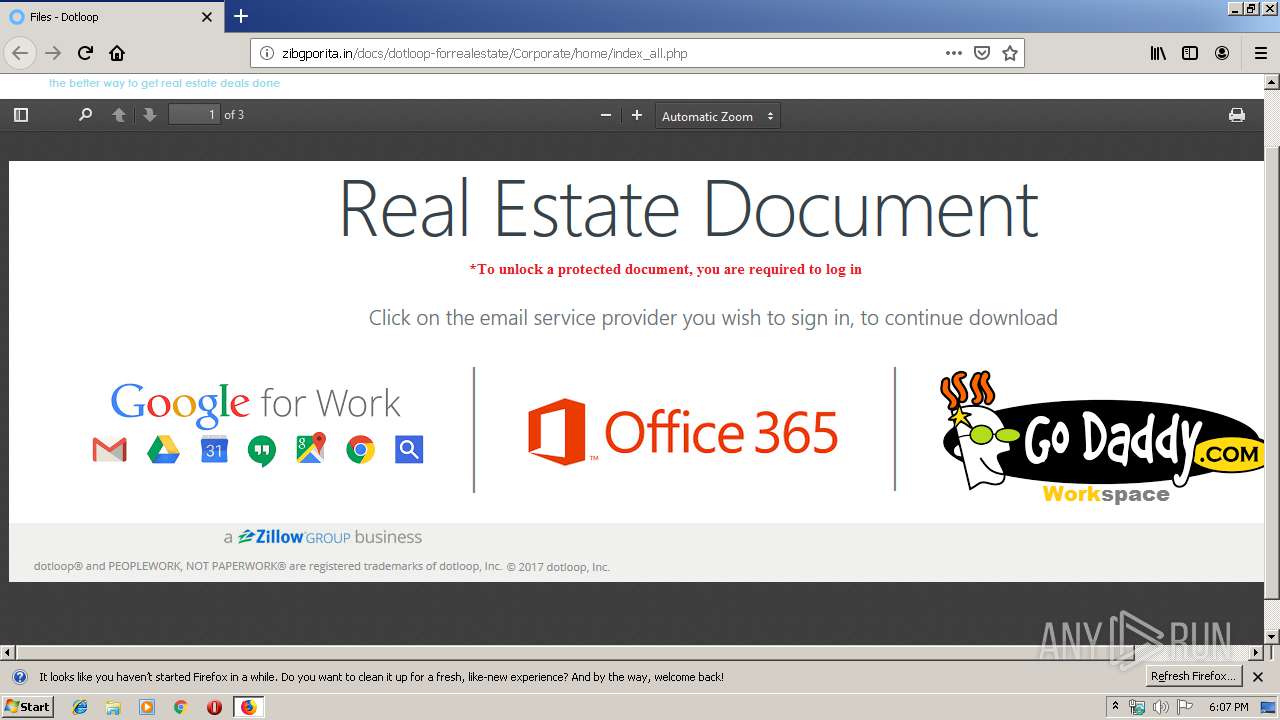
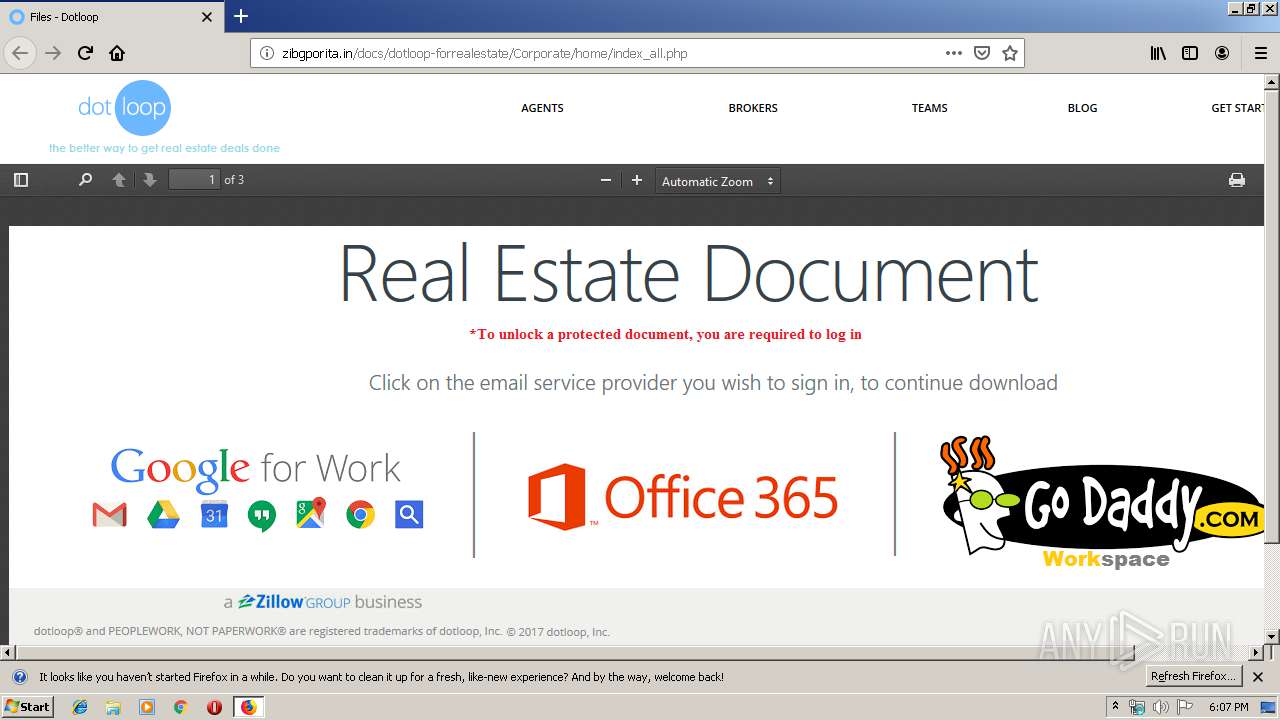
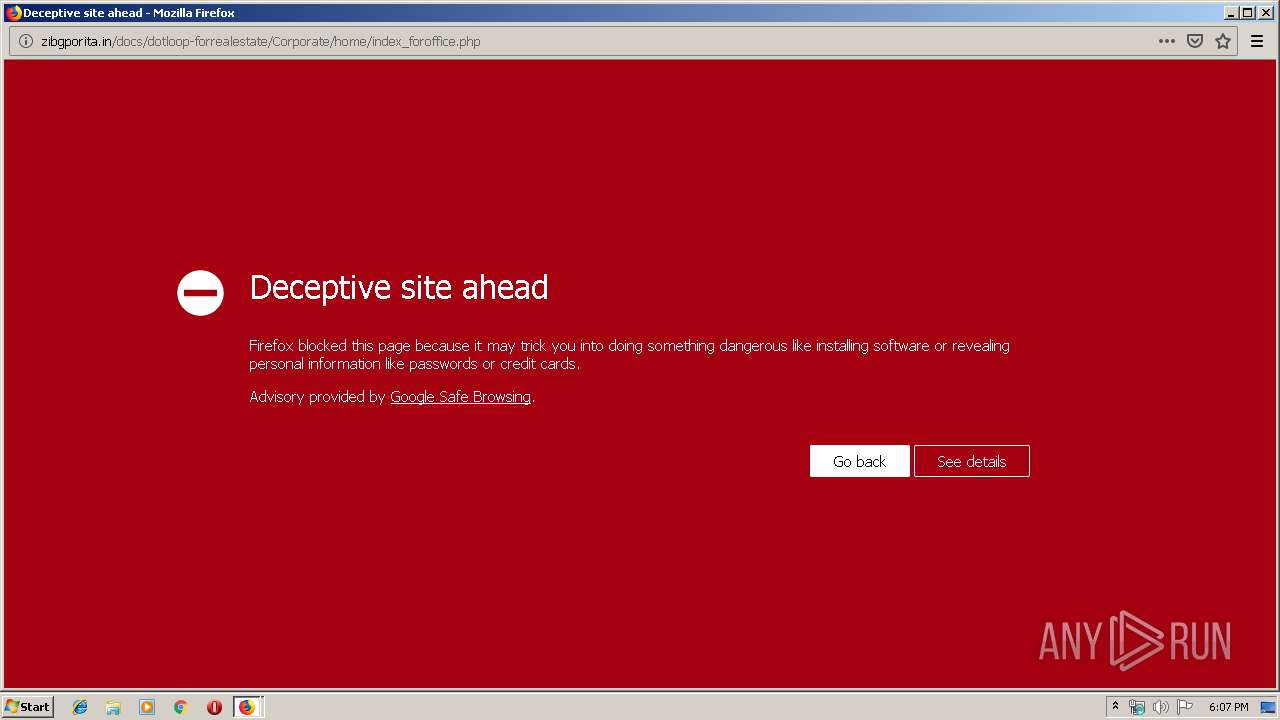
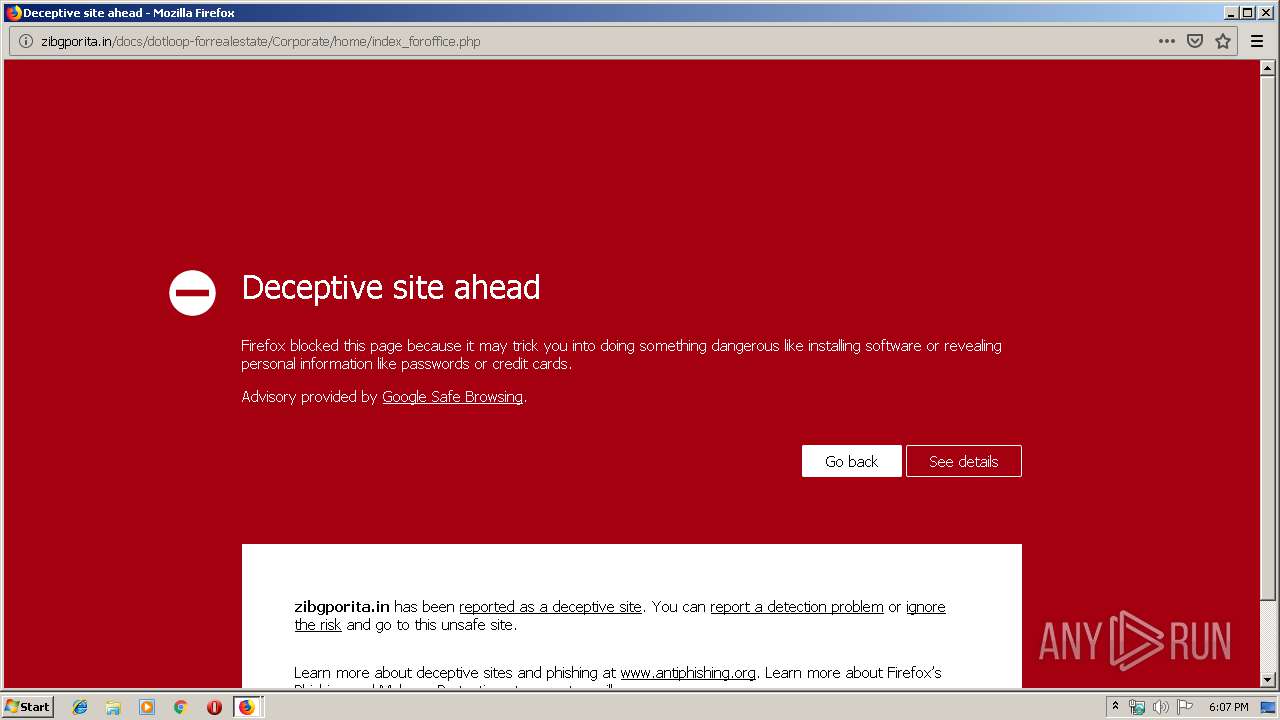
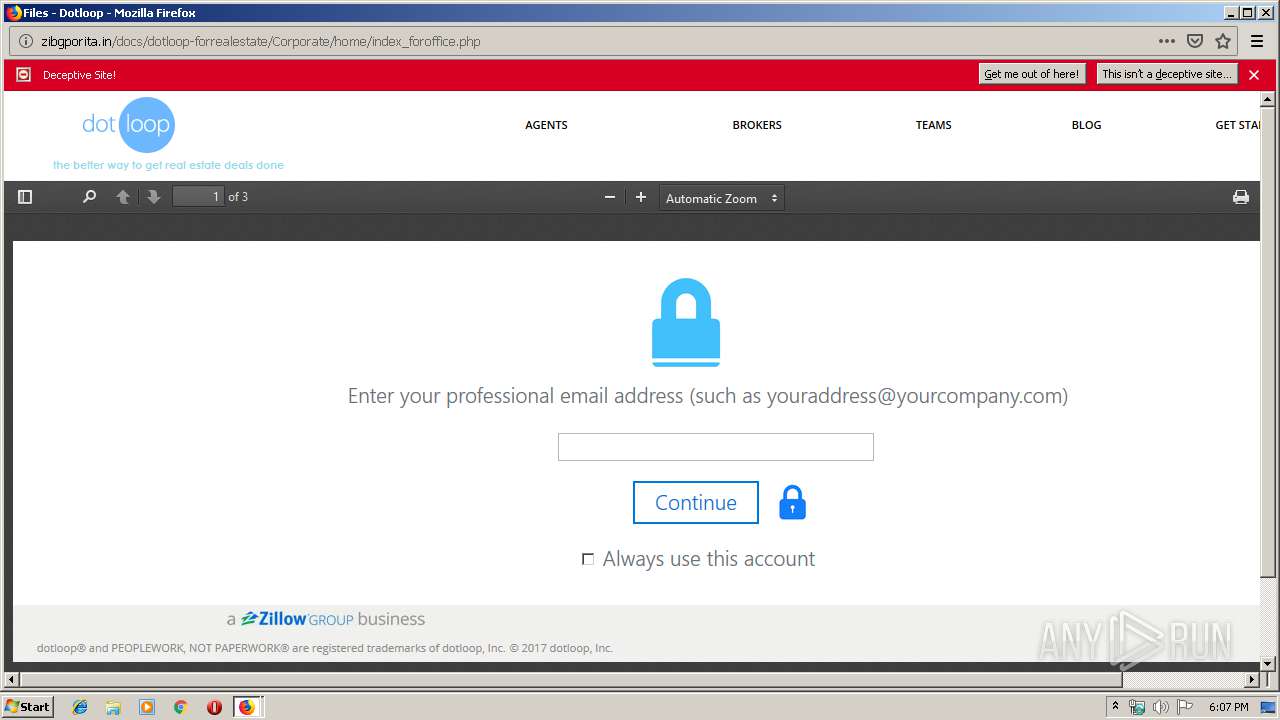
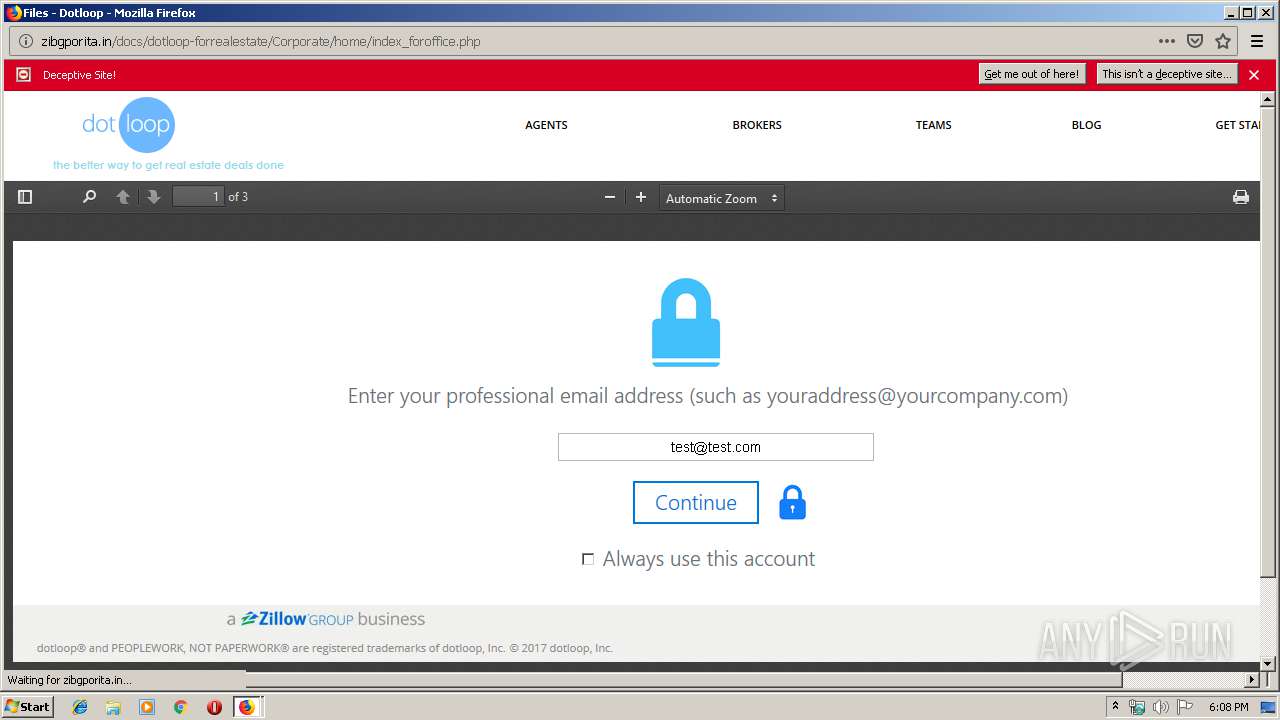
3944 | firefox.exe | GET | — | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/index_foroffice.php | AU | — | — | suspicious |
3944 | firefox.exe | GET | 301 | 67.199.248.10:80 | http://bit.ly/2qqAlYy | US | html | 149 b | shared |
3944 | firefox.exe | GET | 200 | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/ | AU | html | 2.07 Kb | suspicious |
3944 | firefox.exe | GET | 200 | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/images/ori2.png | AU | image | 20.7 Kb | suspicious |
3944 | firefox.exe | GET | 200 | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/images/bode_all.png | AU | image | 101 Kb | suspicious |
3944 | firefox.exe | GET | 200 | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/images/ori.png | AU | image | 20.7 Kb | suspicious |
3944 | firefox.exe | GET | 200 | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/images/bg.png | AU | image | 1.22 Kb | suspicious |
3944 | firefox.exe | GET | 200 | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/index_all.php | AU | html | 4.37 Kb | suspicious |
3944 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3944 | firefox.exe | GET | 200 | 13.211.155.51:80 | http://zibgporita.in/docs/dotloop-forrealestate/Corporate/home/images/load.gif | AU | image | 8.58 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3944 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3944 | firefox.exe | 54.186.225.209:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3944 | firefox.exe | 34.214.202.211:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
3944 | firefox.exe | 52.35.182.58:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3944 | firefox.exe | 13.211.155.51:80 | zibgporita.in | Amazon.com, Inc. | AU | suspicious |
3944 | firefox.exe | 13.35.253.99:443 | firefox.settings.services.mozilla.com | — | US | malicious |
3944 | firefox.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3944 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3944 | firefox.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3944 | firefox.exe | 13.35.253.55:443 | content-signature-2.cdn.mozilla.net | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
bit.ly |
| shared |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
zibgporita.in |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3944 | firefox.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Multi-Email Phishing Landing 2018-08-30 |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |