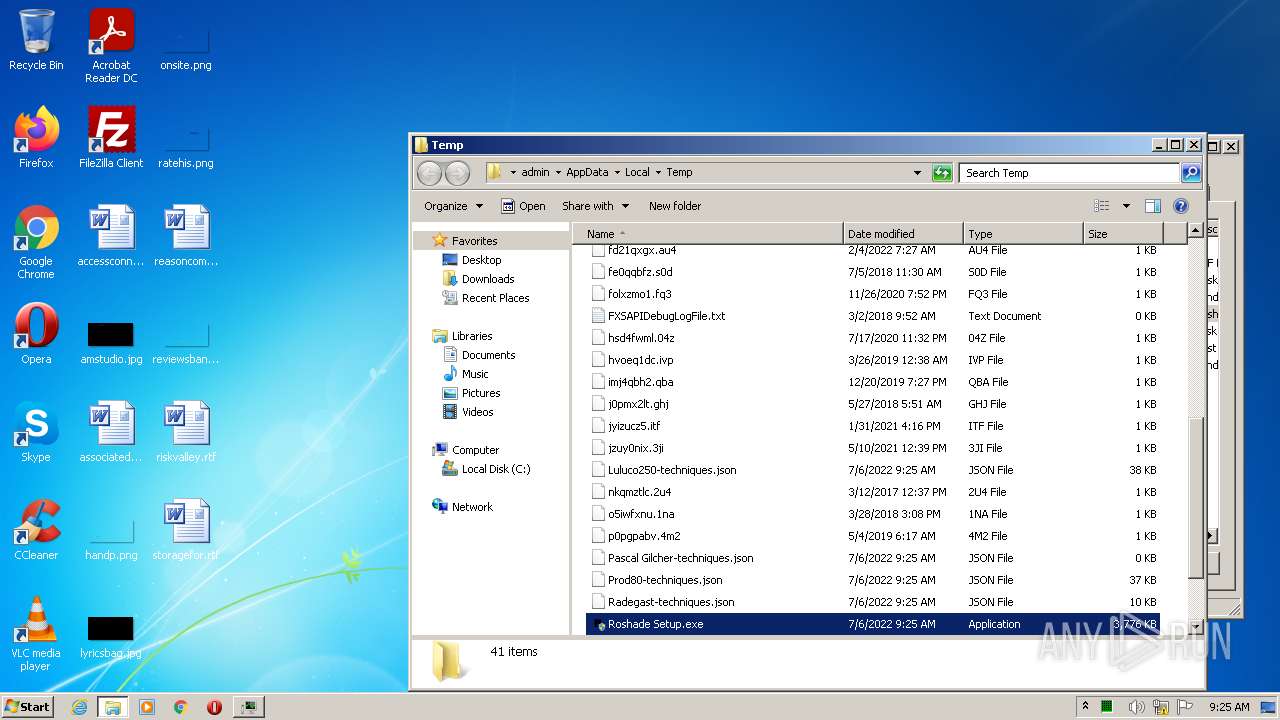
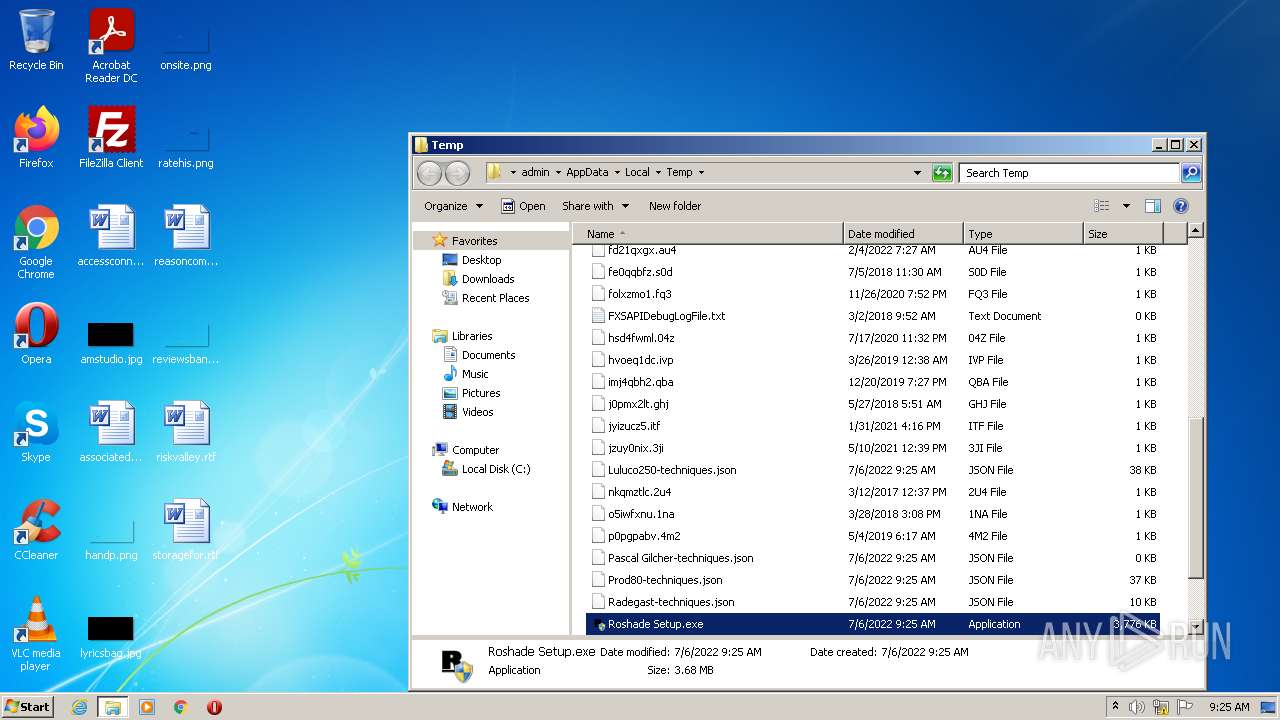
| File name: | Roshade Setup.exe |
| Full analysis: | https://app.any.run/tasks/593620f0-2937-458f-afd1-fe186a698c4d |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2022, 08:25:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 110FDC5182BC502F2BA2776BC9890CA3 |
| SHA1: | 941B5091254D189FEB32327C2DD025E9A418F7AB |
| SHA256: | D753C505EC1C38CB314688ECF4832EB00F5E03E26BC10A6D7120CFC187CC7590 |
| SSDEEP: | 98304:twOp4LXrzA77Oz40TCvy6/Y6UrUi1U5wCRuKk7:tRpUXr877gCq6/Y6Urve5wCUV7 |
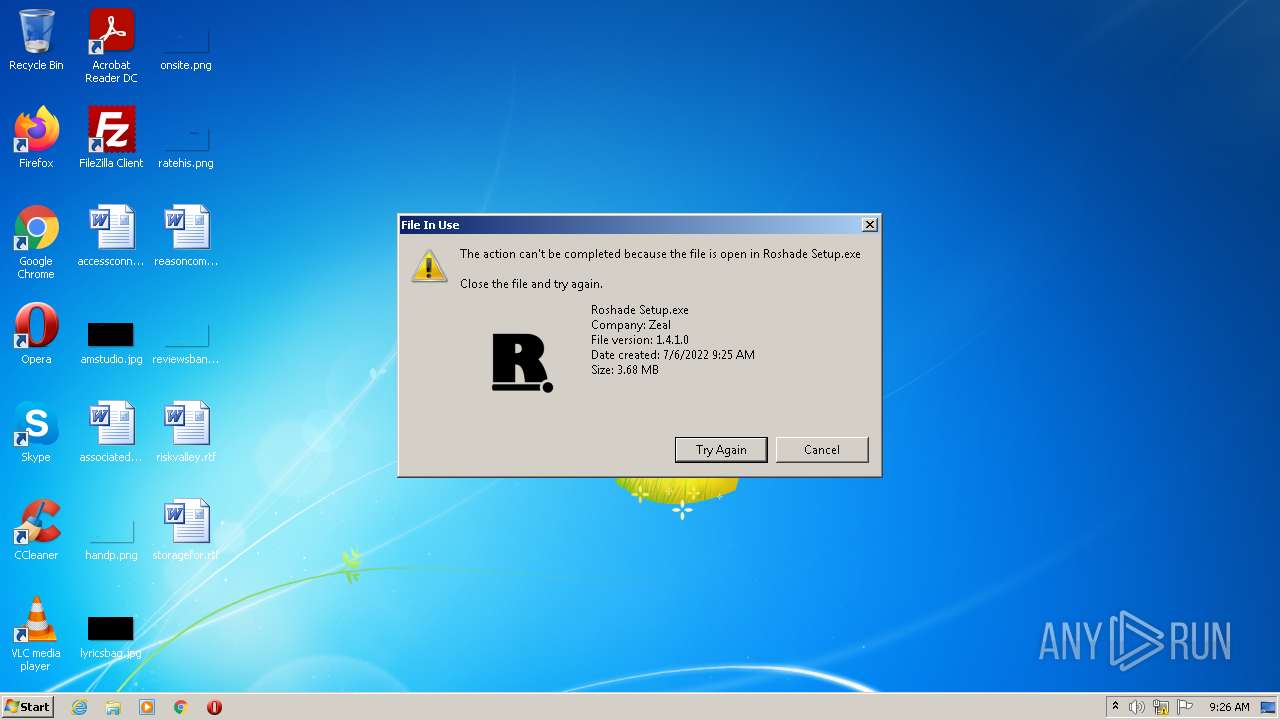
MALICIOUS
Loads dropped or rewritten executable
- Roshade Setup.exe (PID: 3680)
Application was dropped or rewritten from another process
- RobloxPlayerLauncher.exe (PID: 560)
- RobloxPlayerLauncher.exe (PID: 956)
Drops executable file immediately after starts
- Roshade Setup.exe (PID: 3680)
- RobloxPlayerLauncher.exe (PID: 560)
SUSPICIOUS
Reads the computer name
- Roshade Setup.exe (PID: 3680)
- RobloxPlayerLauncher.exe (PID: 956)
- RobloxPlayerLauncher.exe (PID: 560)
Checks supported languages
- RobloxPlayerLauncher.exe (PID: 560)
- Roshade Setup.exe (PID: 3680)
- RobloxPlayerLauncher.exe (PID: 956)
Drops a file with a compile date too recent
- Roshade Setup.exe (PID: 3680)
- RobloxPlayerLauncher.exe (PID: 560)
Executable content was dropped or overwritten
- Roshade Setup.exe (PID: 3680)
- RobloxPlayerLauncher.exe (PID: 560)
Creates files in the user directory
- Roshade Setup.exe (PID: 3680)
- RobloxPlayerLauncher.exe (PID: 560)
Application launched itself
- RobloxPlayerLauncher.exe (PID: 560)
Changes default file association
- RobloxPlayerLauncher.exe (PID: 560)
Creates a directory in Program Files
- RobloxPlayerLauncher.exe (PID: 560)
Creates files in the program directory
- RobloxPlayerLauncher.exe (PID: 560)
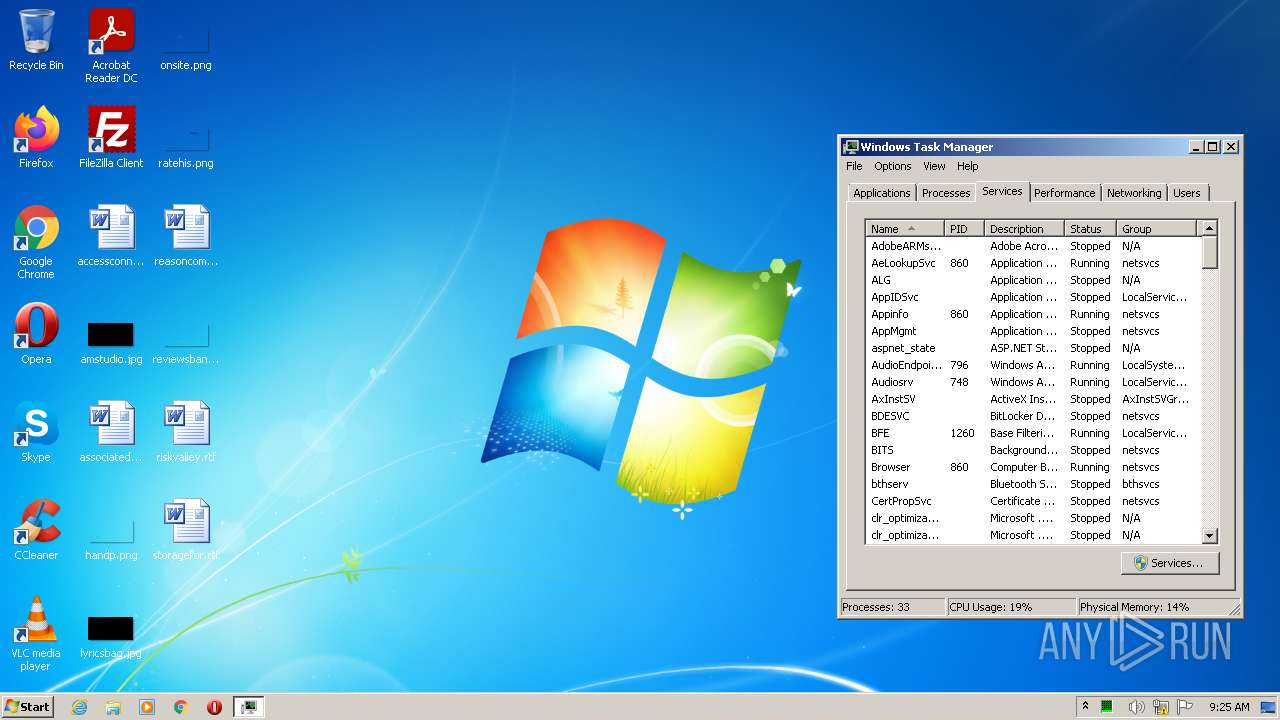
INFO
Checks supported languages
- taskmgr.exe (PID: 1240)
Manual execution by user
- taskmgr.exe (PID: 1240)
Reads the computer name
- taskmgr.exe (PID: 1240)
Dropped object may contain Bitcoin addresses
- Roshade Setup.exe (PID: 3680)
- RobloxPlayerLauncher.exe (PID: 560)
Reads settings of System Certificates
- RobloxPlayerLauncher.exe (PID: 560)
- RobloxPlayerLauncher.exe (PID: 956)
Checks Windows Trust Settings
- RobloxPlayerLauncher.exe (PID: 560)
- RobloxPlayerLauncher.exe (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 1.4.1 |
|---|---|
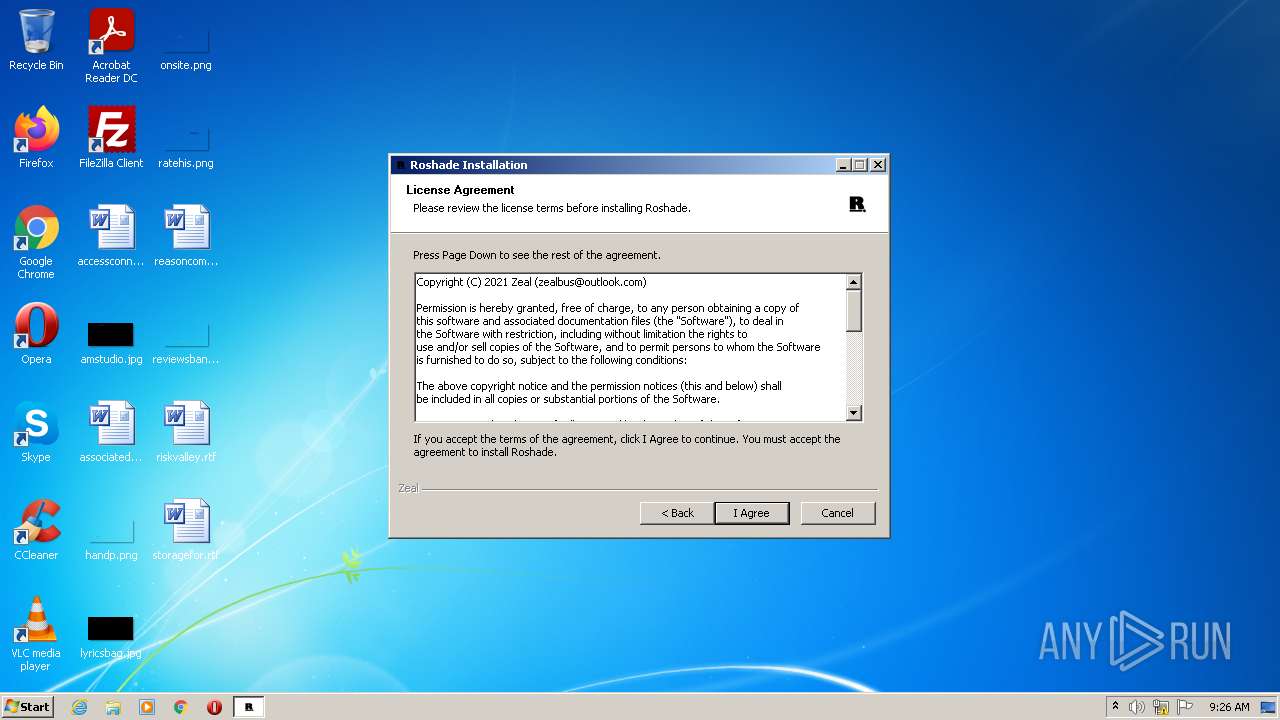
| ProductName: | Roshade |
| LegalCopyright: | Copyright (C) 2021 Zeal |
| FileVersion: | 1.4.1 |
| CompanyName: | Zeal |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.4.1.0 |
| FileVersionNumber: | 1.4.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x352d |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 186880 |
| CodeSize: | 27136 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2021:09:25 23:57:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2021 21:57:46 |
| Detected languages: |
|
| CompanyName: | Zeal |
| FileVersion: | 1.4.1 |
| LegalCopyright: | Copyright (C) 2021 Zeal |
| ProductName: | Roshade |
| ProductVersion: | 1.4.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Sep-2021 21:57:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006897 | 0x00006A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4584 |
.rdata | 0x00008000 | 0x000014A6 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02411 |
.data | 0x0000A000 | 0x0002B018 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.15458 |
.ndata | 0x00036000 | 0x00039000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006F000 | 0x0001A4A8 | 0x0001A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.10388 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28834 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.566893 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 0.616259 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 0.663673 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 7.71207 | 2381 | UNKNOWN | English - United States | RT_ICON |
6 | 0.846009 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.79908 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.67285 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
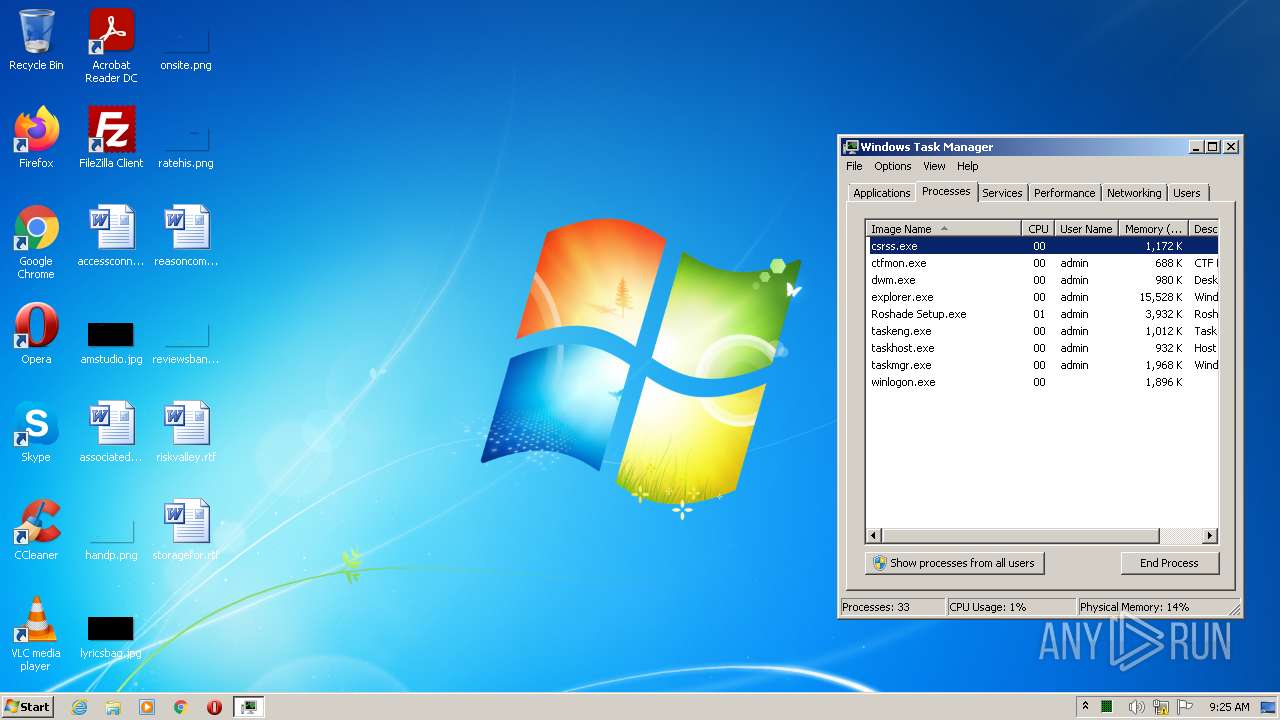
Total processes
43
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\RobloxPlayerLauncher.exe | Roshade Setup.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: HIGH Description: Roblox Exit code: 0 Version: 1, 6, 0, 5330256 Modules
| |||||||||||||||
| 956 | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\RobloxPlayerLauncher.exe --crashpad --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --metrics-dir=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --url=https://upload.crashes.rbxinfra.com/post --annotation=RobloxChannel=production --annotation=RobloxGitHash=a10cfe01197e4d64bb3a4e8972a9e0c902fdfcea --annotation=UploadAttachmentKiloByteLimit=100 --annotation=UploadPercentage=100 --annotation=format=minidump --annotation=token=a2440b0bfdada85f34d79b43839f2b49ea6bba474bd7d126e844bc119271a1c3 --initial-client-data=0x5ac,0x5b0,0x5b4,0x588,0x5bc,0x1310418,0x1310428,0x1310438 | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\RobloxPlayerLauncher.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: HIGH Description: Roblox Exit code: 0 Version: 1, 6, 0, 5330256 Modules
| |||||||||||||||
| 1240 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Users\admin\AppData\Local\Temp\Roshade Setup.exe" | C:\Users\admin\AppData\Local\Temp\Roshade Setup.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Zeal Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.4.1 Modules
| |||||||||||||||
| 3680 | "C:\Users\admin\AppData\Local\Temp\Roshade Setup.exe" | C:\Users\admin\AppData\Local\Temp\Roshade Setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: Zeal Integrity Level: HIGH Exit code: 0 Version: 1.4.1 Modules
| |||||||||||||||
Total events
10 875
Read events
10 783
Write events
91
Delete events
1
Modification events
| (PID) Process: | (1240) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (1240) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000004503000086000000DD0400006C0200000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (560) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
14
Suspicious files
44
Text files
24
Unknown types
7
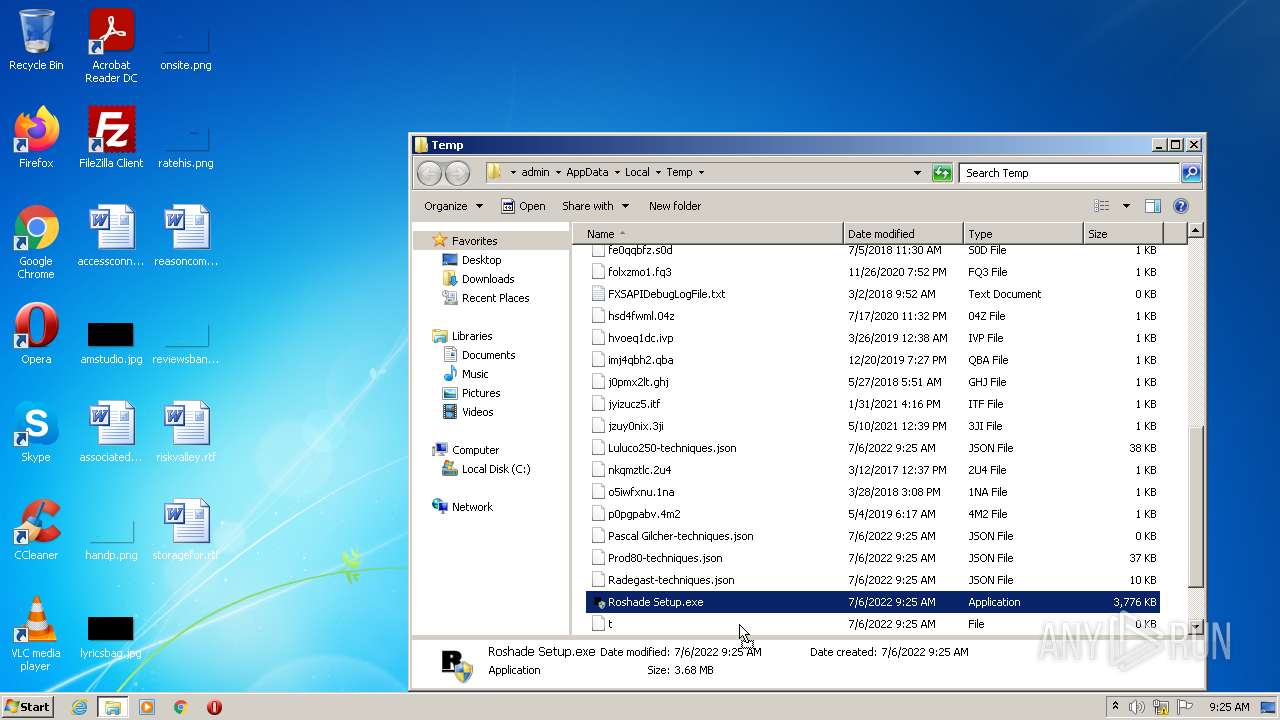
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
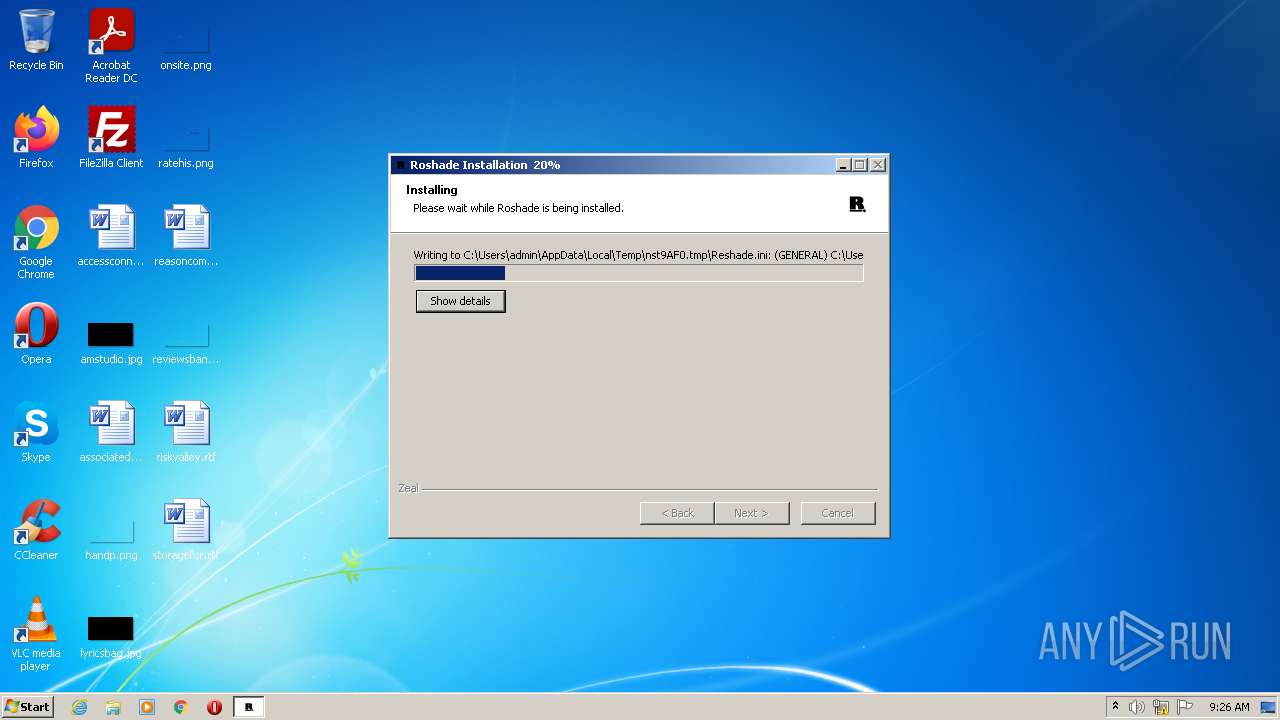
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\Shaders.ini | ini | |
MD5:71AE6E9DA7D71BBD8DBC0DAF46F2BEF9 | SHA256:BDBB1DFAA6FA5ABF5286E5EBFF355877D45E3AC2648805587341313DCB18B819 | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\Reshade.ini | ini | |
MD5:FE1379E6645F0E00E0722FDBB5EC97EC | SHA256:6F056D33A3E7EF8675B8BFA852A38F5C17AE3E0C6483B529EDC1C9592E4682FE | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\LogEx.dll | executable | |
MD5:1C440EC84001C94327082ACA9BDBD0D1 | SHA256:F6D21EF2FA853B922C94D66D3ABD9277AD71BC1BE73A8D8418BC06635925A343 | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\Pascal Gilcher-techniques.json | ini | |
MD5:1D7A2528939FC5B2B3DBD0FEB0A29E60 | SHA256:44F5385470C6F52F9B1C57DEA922F46C84EB27A5422DFAF59734AC3874286FA4 | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\Daodan317081-techniques.json | ini | |
MD5:E5EA4CBD810E21FBD9AB92FB30F5A407 | SHA256:93854F74F0072C07B416837F7F3BB97FA6C787F43A5E671176B672DC8101E76F | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\Prod80-techniques.json | ini | |
MD5:15DDCE7A5BA03974649D8FD5E0178662 | SHA256:95C1F1D93BAA604561154091ED8E27B1D85AB2CF0C637A37610475D31DE153DB | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\titprog.dll | executable | |
MD5:6D821A7565CAF442FC3F394B31F760C6 | SHA256:C14B1E0280B2DF7727A396EED3A84F9B2C444A3DA5F6C4F5C41A4845B9D402EC | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\Luluco250-techniques.json | ini | |
MD5:F558D8687FC2AD51DE5A5317EF4CFF92 | SHA256:35C96B40CE04F5D3AEF9467A50EEDE3C91F90851A173708AB8F09B13F990E6F6 | |||
| 3680 | Roshade Setup.exe | C:\Users\admin\AppData\Local\Temp\nst9AF0.tmp\RobloxPlayerLauncher.exe | executable | |
MD5:E3F7B7057A43E527523FBF5CA8EBF267 | SHA256:B1CDCB4F6040EDE8E7C359ADF507B1578D5CFBEC74639032511F39D0EEBF5226 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
39
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
560 | RobloxPlayerLauncher.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
560 | RobloxPlayerLauncher.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
560 | RobloxPlayerLauncher.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
560 | RobloxPlayerLauncher.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
560 | RobloxPlayerLauncher.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?04e26d14ade10164 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | Roshade Setup.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3680 | Roshade Setup.exe | 140.82.121.10:443 | codeload.github.com | — | US | suspicious |
3680 | Roshade Setup.exe | 92.123.224.216:443 | setup.rbxcdn.com | Akamai International B.V. | — | unknown |
560 | RobloxPlayerLauncher.exe | 104.89.4.140:443 | clientsettingscdn.roblox.com | Akamai Technologies, Inc. | NL | unknown |
560 | RobloxPlayerLauncher.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
560 | RobloxPlayerLauncher.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
956 | RobloxPlayerLauncher.exe | 104.89.4.140:443 | clientsettingscdn.roblox.com | Akamai Technologies, Inc. | NL | unknown |
560 | RobloxPlayerLauncher.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
560 | RobloxPlayerLauncher.exe | 92.123.224.208:443 | setup.rbxcdn.com | Akamai International B.V. | — | suspicious |
3680 | Roshade Setup.exe | 140.82.121.5:443 | api.github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.github.com |
| whitelisted |
www.roblox.com |
| whitelisted |
setup.rbxcdn.com |
| whitelisted |
github.com |
| malicious |
codeload.github.com |
| whitelisted |
clientsettingscdn.roblox.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ephemeralcounters.api.roblox.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |