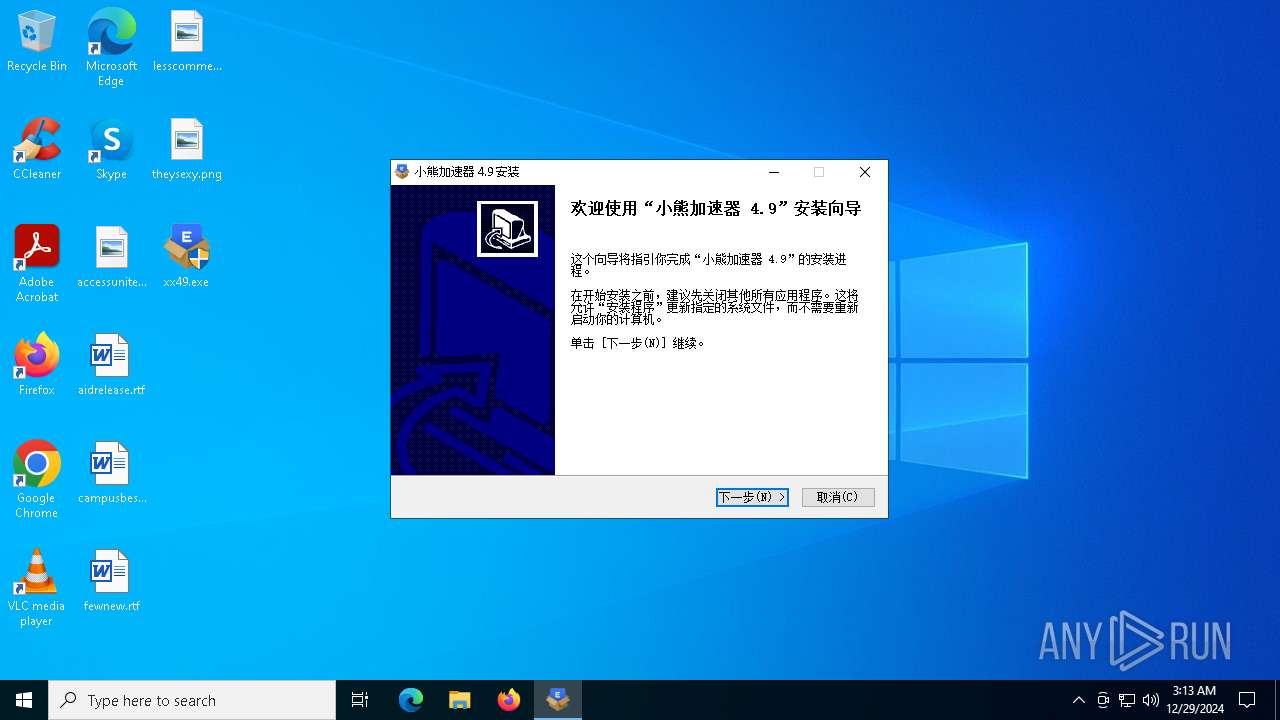
| File name: | xx49.exe |
| Full analysis: | https://app.any.run/tasks/86c5dc8a-800c-41a5-a9ff-6a54f283504c |
| Verdict: | Malicious activity |
| Analysis date: | December 29, 2024, 03:13:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | AF8D0E077886E2F8A8E6DEA5AA0716D6 |
| SHA1: | 2CA4FC379F465F34BD762D9818C3DA7936AB746C |
| SHA256: | D7529EC476213BFC2A5B9792BB189969345AD498E6721F7752C6DC5B71332A2E |
| SSDEEP: | 98304:goaWSEZHeYlpHjcUNtyMYGC5SCq0YJ0Y5JzNL91E/uzZCQDVL6FF1gNmt8QO2ME3:z3HGMJAIz37wc02Jh8xh0G |
MALICIOUS
No malicious indicators.SUSPICIOUS
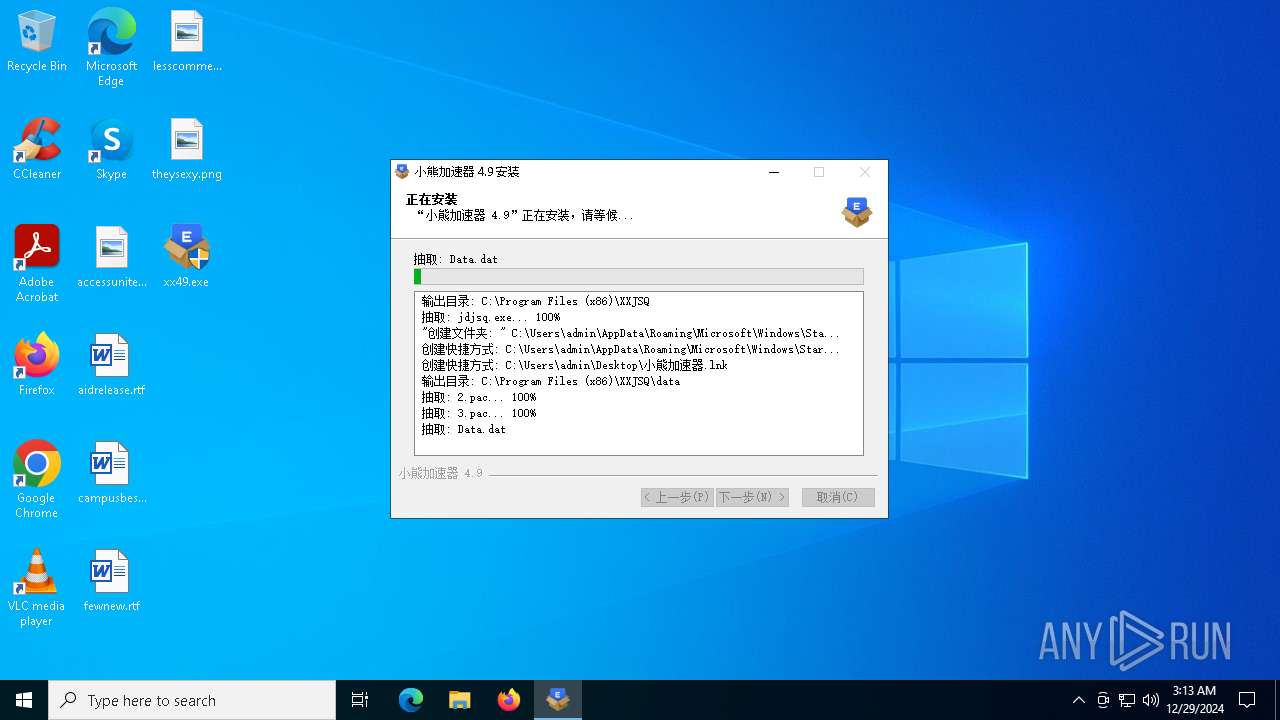
Executable content was dropped or overwritten
- xx49.exe (PID: 6516)
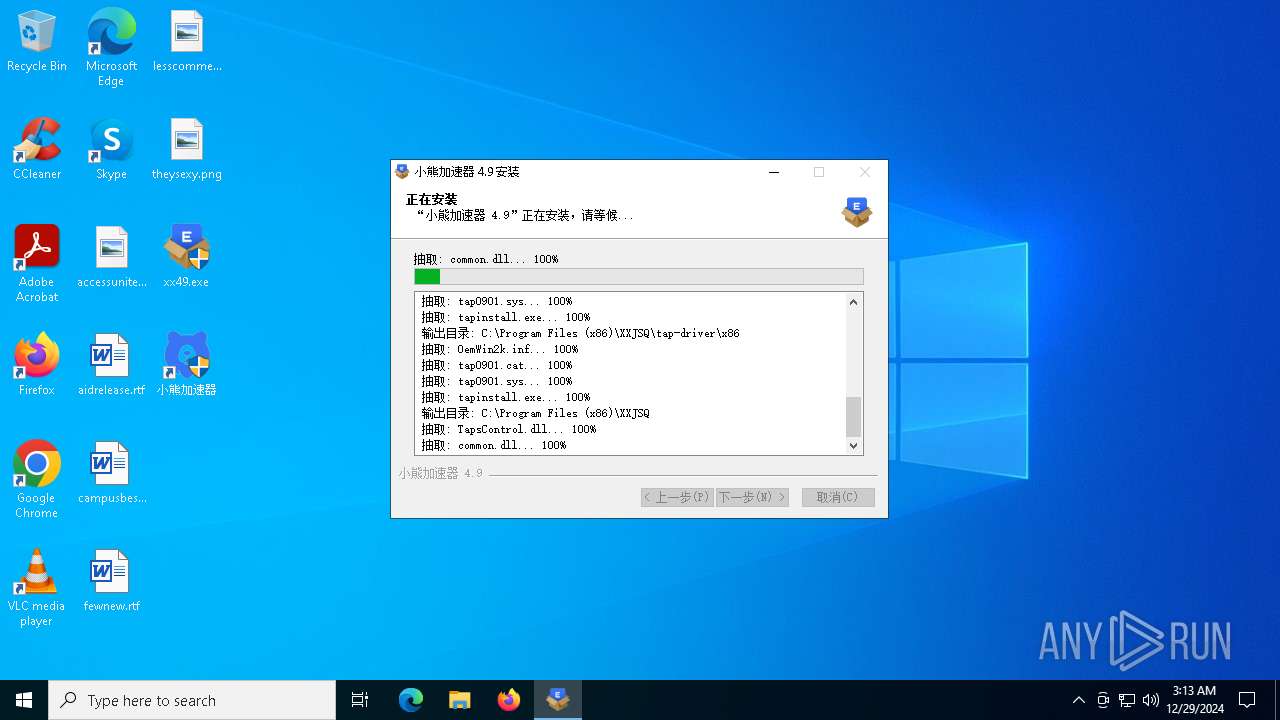
Drops a system driver (possible attempt to evade defenses)
- xx49.exe (PID: 6516)
Adds/modifies Windows certificates
- jdjsq.exe (PID: 6932)
The process creates files with name similar to system file names
- xx49.exe (PID: 6516)
Creates a software uninstall entry
- xx49.exe (PID: 6516)
Process drops legitimate windows executable (CertUtil.exe)
- xx49.exe (PID: 6516)
INFO
Checks supported languages
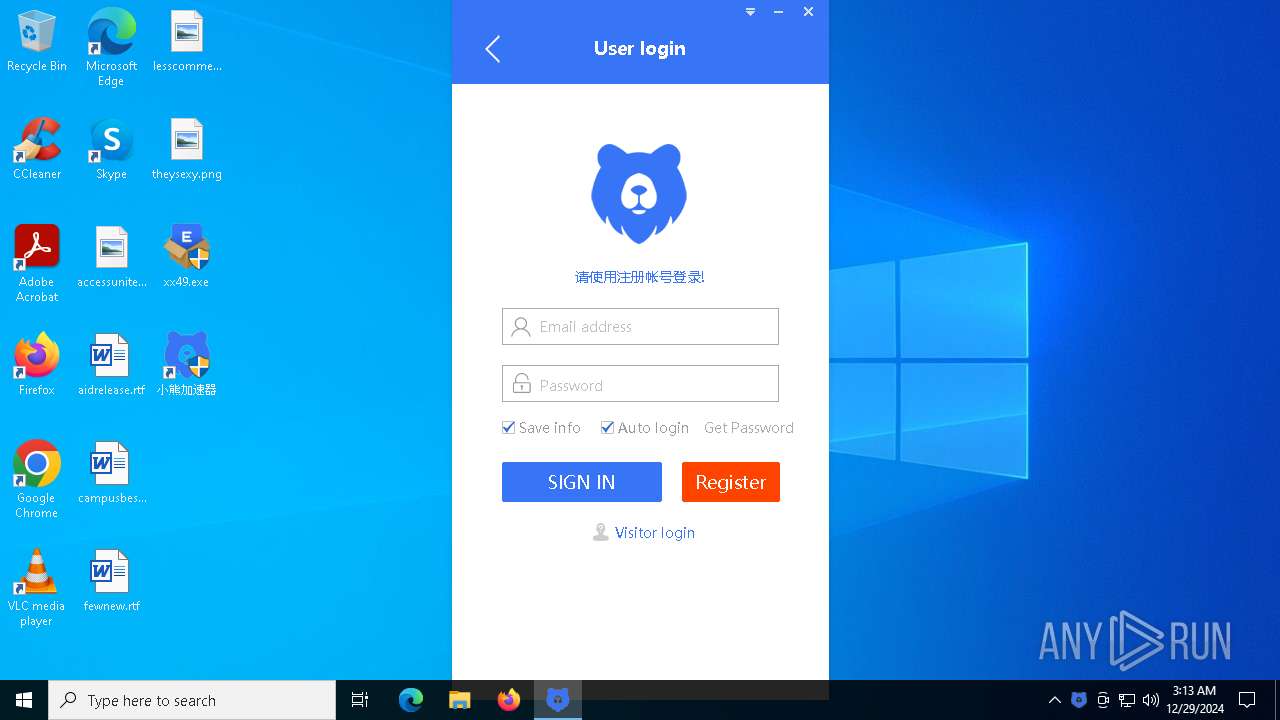
- xx49.exe (PID: 6516)
- jdjsq.exe (PID: 6932)
Create files in a temporary directory
- xx49.exe (PID: 6516)
The sample compiled with chinese language support
- xx49.exe (PID: 6516)
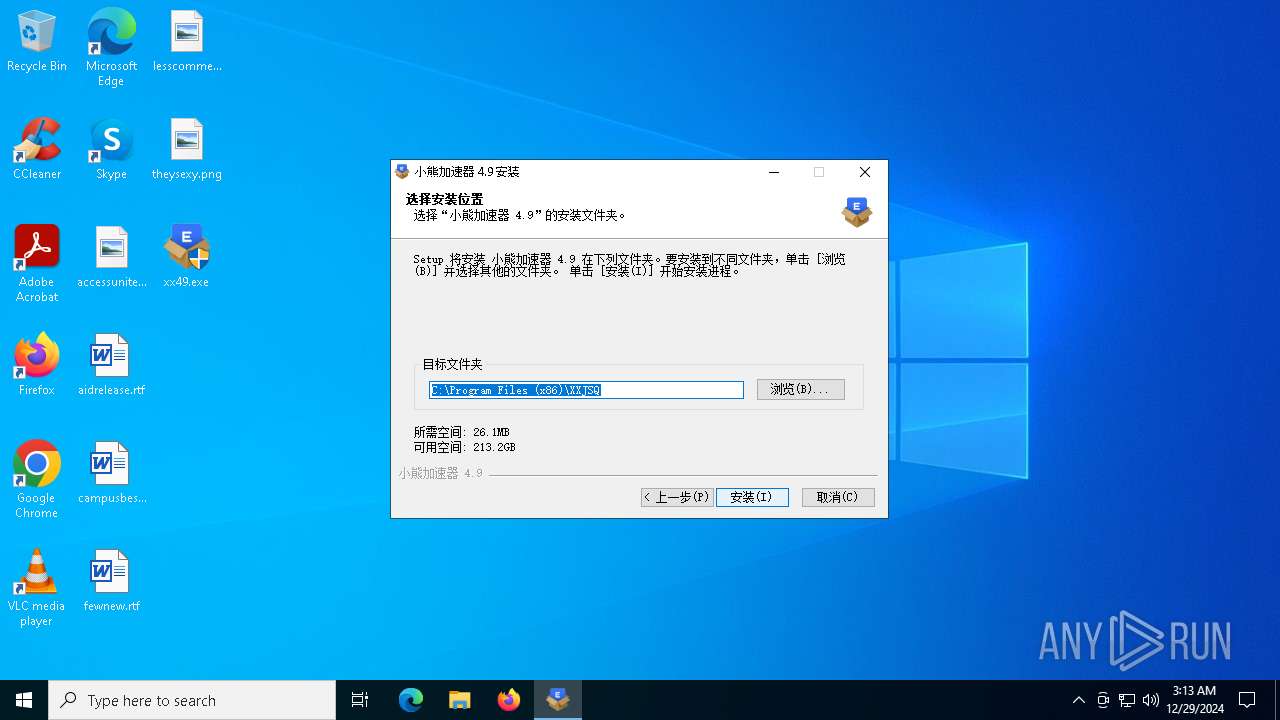
Creates files in the program directory
- xx49.exe (PID: 6516)
- jdjsq.exe (PID: 6932)
Creates files or folders in the user directory
- xx49.exe (PID: 6516)
- jdjsq.exe (PID: 6932)
The sample compiled with english language support
- xx49.exe (PID: 6516)
Reads the software policy settings
- jdjsq.exe (PID: 6932)
Reads the machine GUID from the registry
- jdjsq.exe (PID: 6932)
Reads the computer name
- jdjsq.exe (PID: 6932)
- xx49.exe (PID: 6516)
Application based on Golang
- jdjsq.exe (PID: 6932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:20:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 489984 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
128
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6364 | "C:\Users\admin\Desktop\xx49.exe" | C:\Users\admin\Desktop\xx49.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6516 | "C:\Users\admin\Desktop\xx49.exe" | C:\Users\admin\Desktop\xx49.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6932 | "C:\Program Files (x86)\XXJSQ\jdjsq.exe" | C:\Program Files (x86)\XXJSQ\jdjsq.exe | xx49.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: jdJsq Version: 4, 9, 0, 0 Modules
| |||||||||||||||
Total events
4 474
Read events
4 463
Write events
9
Delete events
2
Modification events
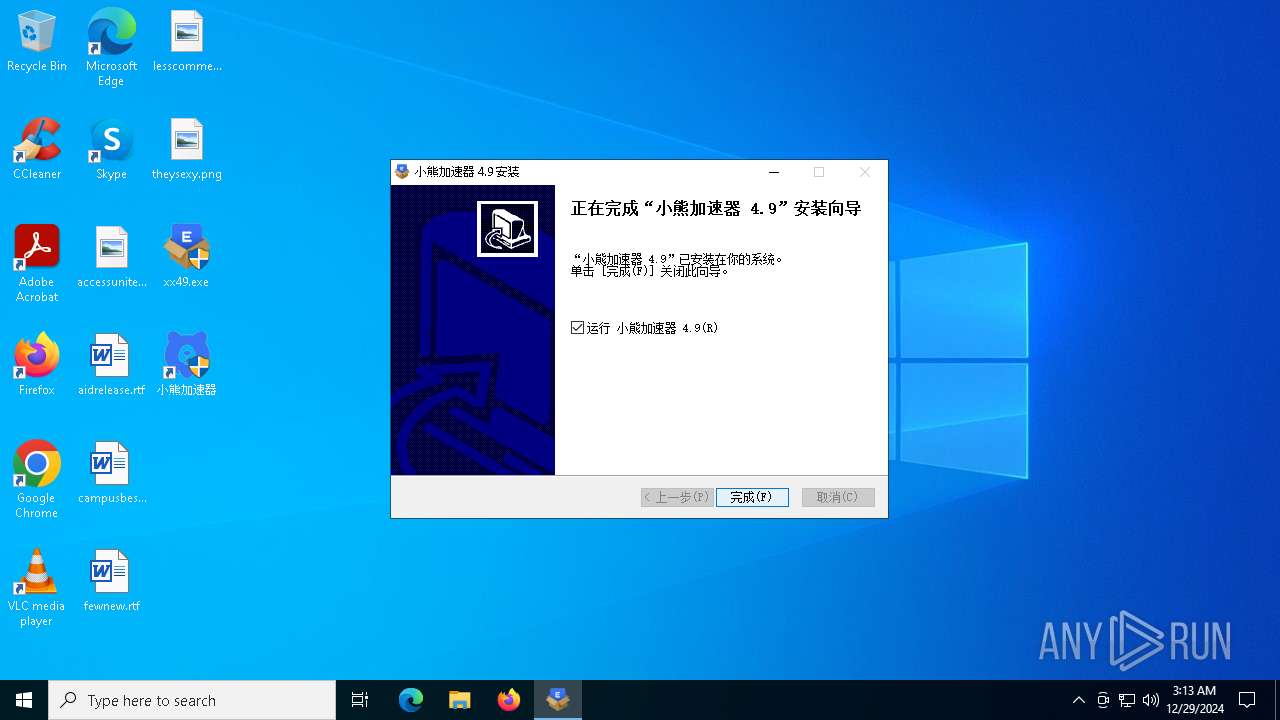
| (PID) Process: | (6516) xx49.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\小熊加速器 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\XXJSQ\uninst.exe | |||
| (PID) Process: | (6516) xx49.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\小熊加速器 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\XXJSQ\jdjsq.exe | |||
| (PID) Process: | (6516) xx49.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\小熊加速器 |
| Operation: | write | Name: | DisplayVersion |
Value: 4.9 | |||
| (PID) Process: | (6516) xx49.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\小熊加速器 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.xxjsqa.com/ | |||
| (PID) Process: | (6516) xx49.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\小熊加速器 |
| Operation: | write | Name: | Publisher |
Value: xxjsq, Inc. | |||
| (PID) Process: | (6516) xx49.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\小熊加速器 |
| Operation: | write | Name: | NSIS:Language |
Value: 2052 | |||
| (PID) Process: | (6516) xx49.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\小熊加速器 |
| Operation: | write | Name: | DisplayName |
Value: 小熊加速器 4.9 | |||
| (PID) Process: | (6932) jdjsq.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 1F24C630CDA418EF2069FFAD4FDD5F463A1B69AA |
Value: | |||
| (PID) Process: | (6932) jdjsq.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\1F24C630CDA418EF2069FFAD4FDD5F463A1B69AA |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000009FAD3B1C021E8ABA177438810CA2BC087F000000010000000C000000300A06082B060105050703031400000001000000140000003DE629489BEA07CA21444A26DE6EDED283D09F59090000000100000034000000303206082B0601050507030206082B0601050507030306082B0601050507030406082B0601050507030106082B06010505070308530000000100000040000000303E301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00F0000000100000030000000F019C7BA12795DACD6EF1A767657DEB8E41060A2AD1A6C66900A6EC16870FC06EECBAFFDD3E2C986659578E7E85E535A0300000001000000140000001F24C630CDA418EF2069FFAD4FDD5F463A1B69AA190000000100000010000000E3087C0C81F60A2A2B466B8A3E70CCE80B000000010000003800000047006C006F00620061006C005300690067006E002000450043004300200052006F006F00740020004300410020002D002000520035000000620000000100000020000000179FBC148A3DD00FD24EA13458CC43BFA7F59C8182D783A513F6EBEC100C89241D0000000100000010000000B647DD2A9CCADEE75E8905E256CC6B147E00000001000000080000000080C82B6886D7012000000001000000220200003082021E308201A4A0030201020211605949E0262EBB55F90A778A71F94AD86C300A06082A8648CE3D040303305031243022060355040B131B476C6F62616C5369676E2045434320526F6F74204341202D20523531133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3132313131333030303030305A170D3338303131393033313430375A305031243022060355040B131B476C6F62616C5369676E2045434320526F6F74204341202D20523531133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E3076301006072A8648CE3D020106052B810400220362000447450E96FB7D5DBFE939D121F89F0BB6D57B1E923A48591CF062312DC07A28FE1AA75CB3B6CC97E745D458FAD1776D43A2C08765340A1F7ADDEB3C33A1C59D4DA46F4195387FC91E84EBD19E49928794870C3A854A669F9D59934D976106864AA3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604143DE629489BEA07CA21444A26DE6EDED283D09F59300A06082A8648CE3D0403030368003065023100E56912C96EDBC631BA0941E197F8FBFD9AE27D12C9ED7C64D3CB05258B56D9A0E75E5D4E0B839C5B7629A00926216A62023071D2B58F5CEA3BE1780985A875923BC85CFD48EF0D7422A808E26EC549CEC70CBCA76169F1F73BE12ACBF92BF3669037 | |||
| (PID) Process: | (6932) jdjsq.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\1F24C630CDA418EF2069FFAD4FDD5F463A1B69AA |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000800100007E00000001000000080000000080C82B6886D7011D0000000100000010000000B647DD2A9CCADEE75E8905E256CC6B14620000000100000020000000179FBC148A3DD00FD24EA13458CC43BFA7F59C8182D783A513F6EBEC100C89240B000000010000003800000047006C006F00620061006C005300690067006E002000450043004300200052006F006F00740020004300410020002D002000520035000000190000000100000010000000E3087C0C81F60A2A2B466B8A3E70CCE80300000001000000140000001F24C630CDA418EF2069FFAD4FDD5F463A1B69AA0F0000000100000030000000F019C7BA12795DACD6EF1A767657DEB8E41060A2AD1A6C66900A6EC16870FC06EECBAFFDD3E2C986659578E7E85E535A530000000100000040000000303E301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030206082B0601050507030306082B0601050507030406082B0601050507030106082B060105050703081400000001000000140000003DE629489BEA07CA21444A26DE6EDED283D09F597F000000010000000C000000300A06082B060105050703030400000001000000100000009FAD3B1C021E8ABA177438810CA2BC082000000001000000220200003082021E308201A4A0030201020211605949E0262EBB55F90A778A71F94AD86C300A06082A8648CE3D040303305031243022060355040B131B476C6F62616C5369676E2045434320526F6F74204341202D20523531133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3132313131333030303030305A170D3338303131393033313430375A305031243022060355040B131B476C6F62616C5369676E2045434320526F6F74204341202D20523531133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E3076301006072A8648CE3D020106052B810400220362000447450E96FB7D5DBFE939D121F89F0BB6D57B1E923A48591CF062312DC07A28FE1AA75CB3B6CC97E745D458FAD1776D43A2C08765340A1F7ADDEB3C33A1C59D4DA46F4195387FC91E84EBD19E49928794870C3A854A669F9D59934D976106864AA3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604143DE629489BEA07CA21444A26DE6EDED283D09F59300A06082A8648CE3D0403030368003065023100E56912C96EDBC631BA0941E197F8FBFD9AE27D12C9ED7C64D3CB05258B56D9A0E75E5D4E0B839C5B7629A00926216A62023071D2B58F5CEA3BE1780985A875923BC85CFD48EF0D7422A808E26EC549CEC70CBCA76169F1F73BE12ACBF92BF3669037 | |||
Executable files
18
Suspicious files
11
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6516 | xx49.exe | C:\Users\admin\AppData\Local\Temp\nsx5C8C.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\libiconv2.dll | executable | |
MD5:331F570AA7C20BC93DEB7B237B21CC9C | SHA256:3EC2D1A924EF6F19F2DB45E48B9CF4B74A904AF5720100E3DA02182EEE3BCF02 | |||
| 6516 | xx49.exe | C:\Users\admin\AppData\Local\Temp\nsx5C8C.tmp\ioSpecial.ini | text | |
MD5:6F98FCDA445825382121E480A64AE24C | SHA256:689A67B30946CBE12DCE92D17207EC0488E850A806BE608E6FB174F853F86B57 | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\data\3.pac | text | |
MD5:588BF059B17CC2A8DA2E49D3F9F6D657 | SHA256:EE8985011115DBDDDBCFA9B316EAB3DDFF334239EDEA570A0CF334EFACFA2187 | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\libeay32.dll | executable | |
MD5:B1929368409321770B26AD8C9BE4494A | SHA256:CA30581A0E281717CB80512642F37D55DF63EBDDE1265861B68887965F00016A | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\data\2.pac | text | |
MD5:E5483AE7DE8EC7289A14E07C896FDCDA | SHA256:1230067D339968A937F816730BD75A093CEC262B0A9831CD4609AE9E4FCBC4EB | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\tap-driver\ik.cert.pem | text | |
MD5:63F97DF7E625BACDB86C2A8E4D15C7CD | SHA256:93F6A7AE07C46DCDE710D024B0C64DD37728129B83ACEC9252CFDA7732F2DE41 | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\tap-driver\cacert.pem | text | |
MD5:5726B0C3F8178094B08EE544E92619BD | SHA256:B7B41BD3B74B7AFDD8AD6D84E77236AA9D2FBDCDC3445E7A7ED4721E1E1F3C55 | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\libintl3.dll | executable | |
MD5:D202BAA425176287017FFE1FB5D1B77C | SHA256:F48CE1866602B114E653C876334B771107559ACF1C685373D2305034613958F0 | |||
| 6516 | xx49.exe | C:\Program Files (x86)\XXJSQ\LibDui.dll | executable | |
MD5:A2FB323163C028F9C50929E07F9EEEAD | SHA256:3E07E52B4E4038971ACEF8D3102EC378B36E9967CEA199E5B6961438F601D533 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
40
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7112 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5916 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7112 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1488 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1488 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dns.alidns.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6932 | jdjsq.exe | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |