| File name: | dvrsetup.exe |
| Full analysis: | https://app.any.run/tasks/34076b61-1f09-4430-82fd-84bb7f919abe |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2024, 06:58:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 05174740EC8B6F5277D1A06F75B61EB1 |
| SHA1: | D18D9D12662D97C3B8656EC23BD78A96E2F800F8 |
| SHA256: | D74EE6AF7D39E53BD0183A5002E4F3AFF5C3DDAA46F2F6A0BB608FF6F5986180 |
| SSDEEP: | 24576:Z2ZQe6fKakTa+zE6FEbH1aqtAjFKu2y9QyA8Qm4wABBUL8u7EFo4BPDkvL+saLnn:ZYQtKakTawE6FEbH1aqtSFKu2y2yA8QV |
MALICIOUS
Runs injected code in another process
- rundll32.exe (PID: 5544)
Application was injected by another process
- svchost.exe (PID: 1316)
SUSPICIOUS
Process drops legitimate windows executable
- dvrsetup.tmp (PID: 5124)
Reads security settings of Internet Explorer
- dvrsetup.tmp (PID: 7140)
- dvrsetup.tmp (PID: 5124)
- rk_setup.tmp (PID: 6968)
- installer.exe (PID: 4060)
- rlvknlg.exe (PID: 6512)
- rlvknlg.exe (PID: 2400)
Checks Windows Trust Settings
- dvrsetup.tmp (PID: 5124)
- rlvknlg.exe (PID: 6512)
- rlvknlg.exe (PID: 2400)
Executable content was dropped or overwritten
- dvrsetup.exe (PID: 5548)
- dvrsetup.exe (PID: 6188)
- rk_setup.exe (PID: 872)
- dvrsetup.tmp (PID: 5124)
- rk_setup.tmp (PID: 6968)
- installer.exe (PID: 4060)
- rlvknlg.exe (PID: 6512)
Reads the Windows owner or organization settings
- dvrsetup.tmp (PID: 5124)
- rk_setup.tmp (PID: 6968)
Reads the date of Windows installation
- rk_setup.tmp (PID: 6968)
- dvrsetup.tmp (PID: 7140)
The process verifies whether the antivirus software is installed
- dvrsetup.tmp (PID: 5124)
Creates a software uninstall entry
- rlvknlg.exe (PID: 6512)
- rlservice.exe (PID: 7144)
- rlvknlg.exe (PID: 2400)
Searches for installed software
- rlservice.exe (PID: 7144)
- rlvknlg.exe (PID: 6512)
- rundll32.exe (PID: 5544)
- svchost.exe (PID: 1316)
- reg.exe (PID: 2228)
- rlvknlg.exe (PID: 2400)
- installer.exe (PID: 4060)
Adds/modifies Windows certificates
- rlvknlg.exe (PID: 6512)
- rlservice.exe (PID: 7144)
Executes as Windows Service
- rlservice.exe (PID: 7144)
Uses RUNDLL32.EXE to load library
- rlservice.exe (PID: 7144)
INFO
Checks supported languages
- dvrsetup.exe (PID: 6188)
- dvrsetup.tmp (PID: 7140)
- dvrsetup.exe (PID: 5548)
- dvrsetup.tmp (PID: 5124)
- rk_setup.tmp (PID: 6968)
- rk_setup.exe (PID: 872)
- installer.exe (PID: 4060)
- rlvknlg.exe (PID: 6512)
- rlservice.exe (PID: 7144)
- rlvknlg.exe (PID: 2400)
Process checks computer location settings
- dvrsetup.tmp (PID: 7140)
- rk_setup.tmp (PID: 6968)
Create files in a temporary directory
- dvrsetup.exe (PID: 5548)
- dvrsetup.tmp (PID: 5124)
- dvrsetup.exe (PID: 6188)
- rk_setup.exe (PID: 872)
- rk_setup.tmp (PID: 6968)
- installer.exe (PID: 4060)
Reads the computer name
- dvrsetup.tmp (PID: 7140)
- dvrsetup.tmp (PID: 5124)
- rk_setup.tmp (PID: 6968)
- installer.exe (PID: 4060)
- rlvknlg.exe (PID: 6512)
- rlservice.exe (PID: 7144)
- rlvknlg.exe (PID: 2400)
Reads the machine GUID from the registry
- dvrsetup.tmp (PID: 5124)
- rk_setup.tmp (PID: 6968)
- rlvknlg.exe (PID: 6512)
- rlservice.exe (PID: 7144)
- rlvknlg.exe (PID: 2400)
Reads the software policy settings
- dvrsetup.tmp (PID: 5124)
- rlvknlg.exe (PID: 6512)
- rlservice.exe (PID: 7144)
- rlvknlg.exe (PID: 2400)
Checks proxy server information
- dvrsetup.tmp (PID: 5124)
- rlvknlg.exe (PID: 6512)
- rlvknlg.exe (PID: 2400)
Creates files or folders in the user directory
- dvrsetup.tmp (PID: 5124)
- installer.exe (PID: 4060)
- rlvknlg.exe (PID: 6512)
- rlvknlg.exe (PID: 2400)
The process uses the downloaded file
- rk_setup.tmp (PID: 6968)
Reads Environment values
- rlvknlg.exe (PID: 6512)
- rlvknlg.exe (PID: 2400)
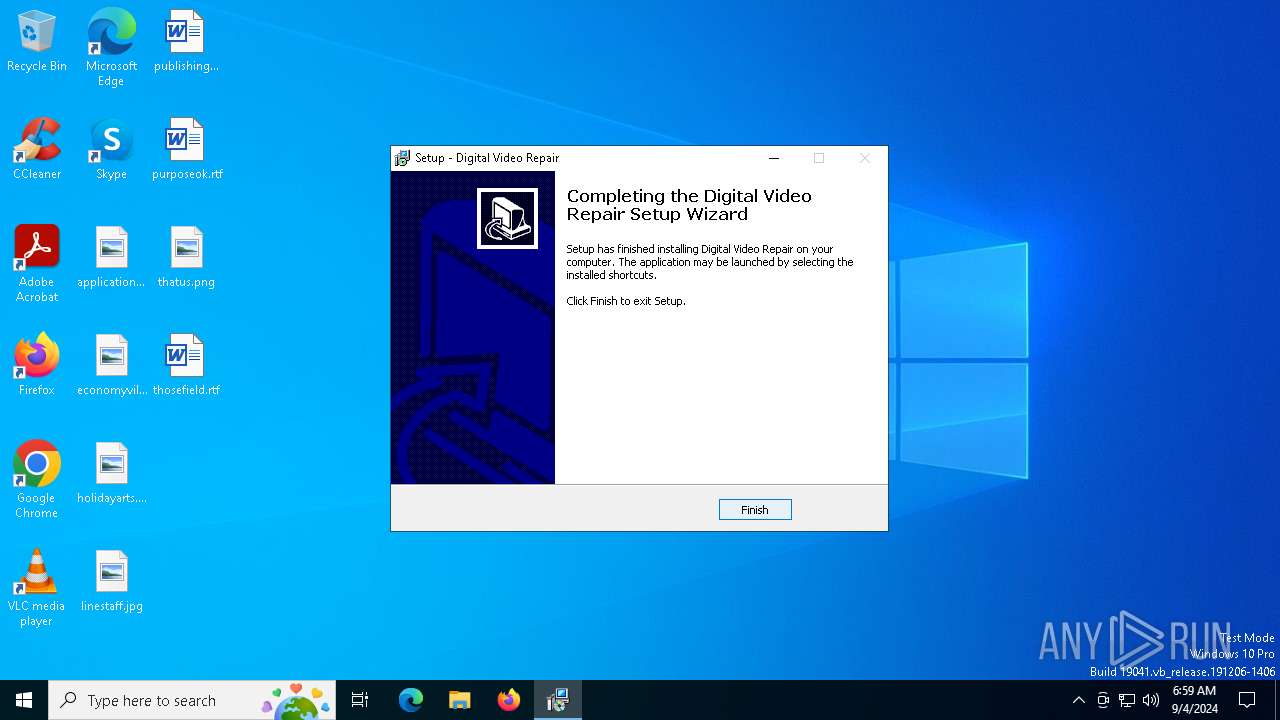
Creates a software uninstall entry
- dvrsetup.tmp (PID: 5124)
- installer.exe (PID: 4060)
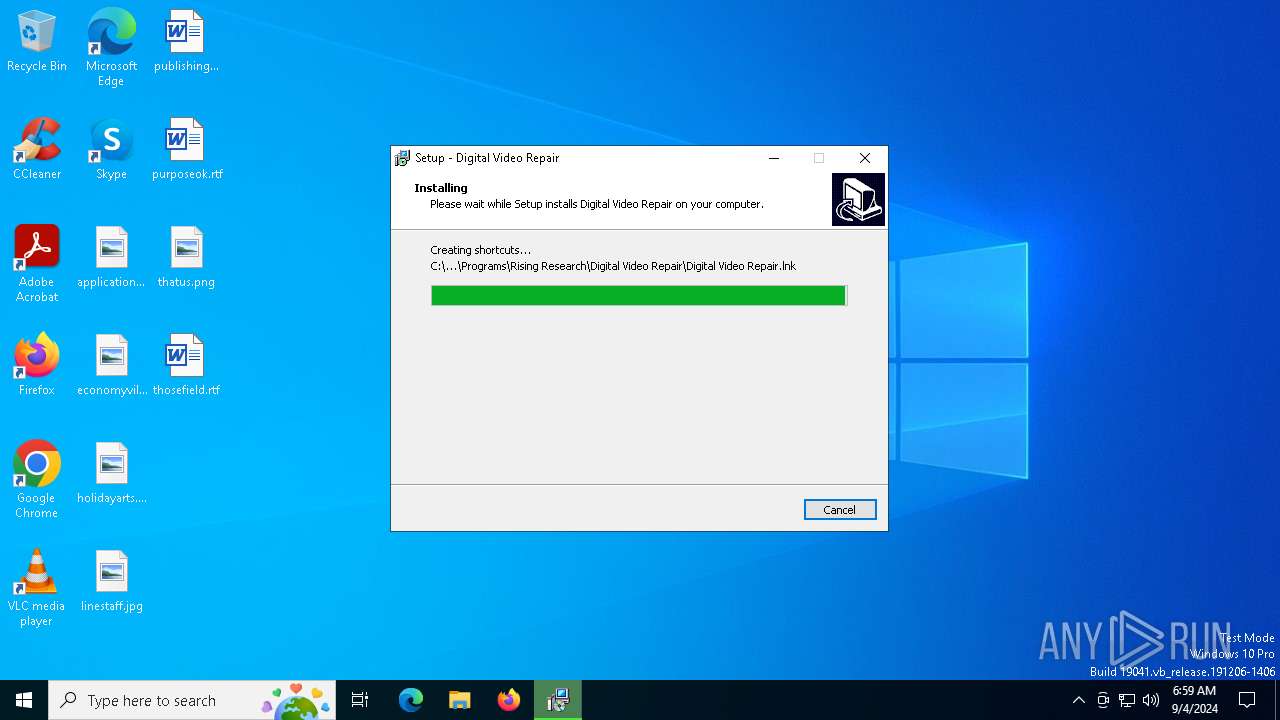
Creates files in the program directory
- installer.exe (PID: 4060)
- dvrsetup.tmp (PID: 5124)
- rlvknlg.exe (PID: 6512)
- rlservice.exe (PID: 7144)
- reg.exe (PID: 2228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:15 08:22:50+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
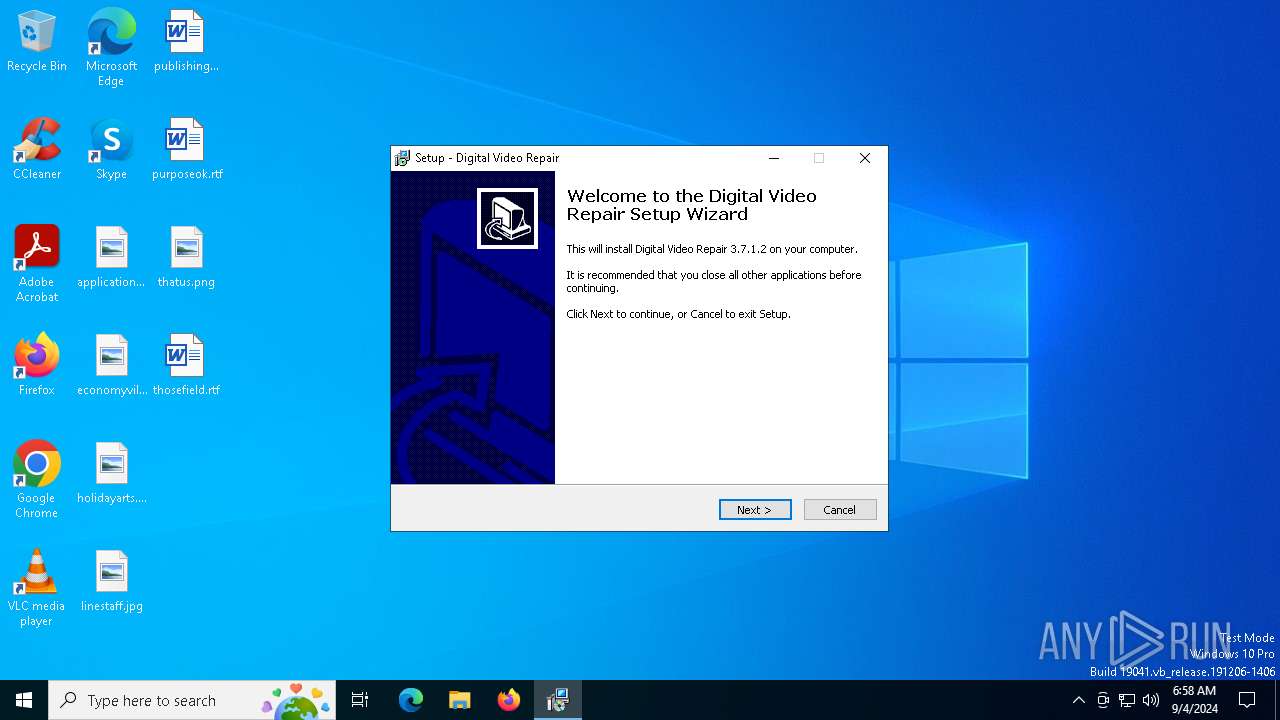
| FileVersionNumber: | 3.7.1.2 |
| ProductVersionNumber: | 3.7.1.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
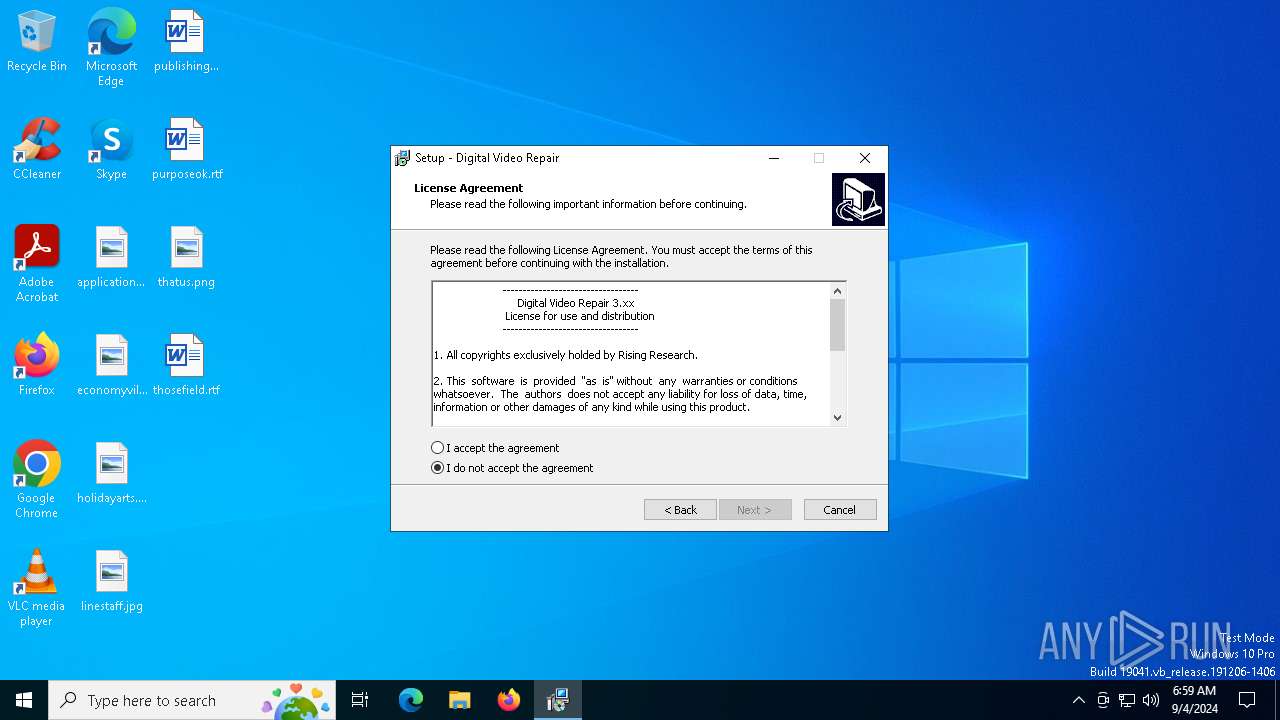
| Comments: | This installation was built with Inno Setup. |
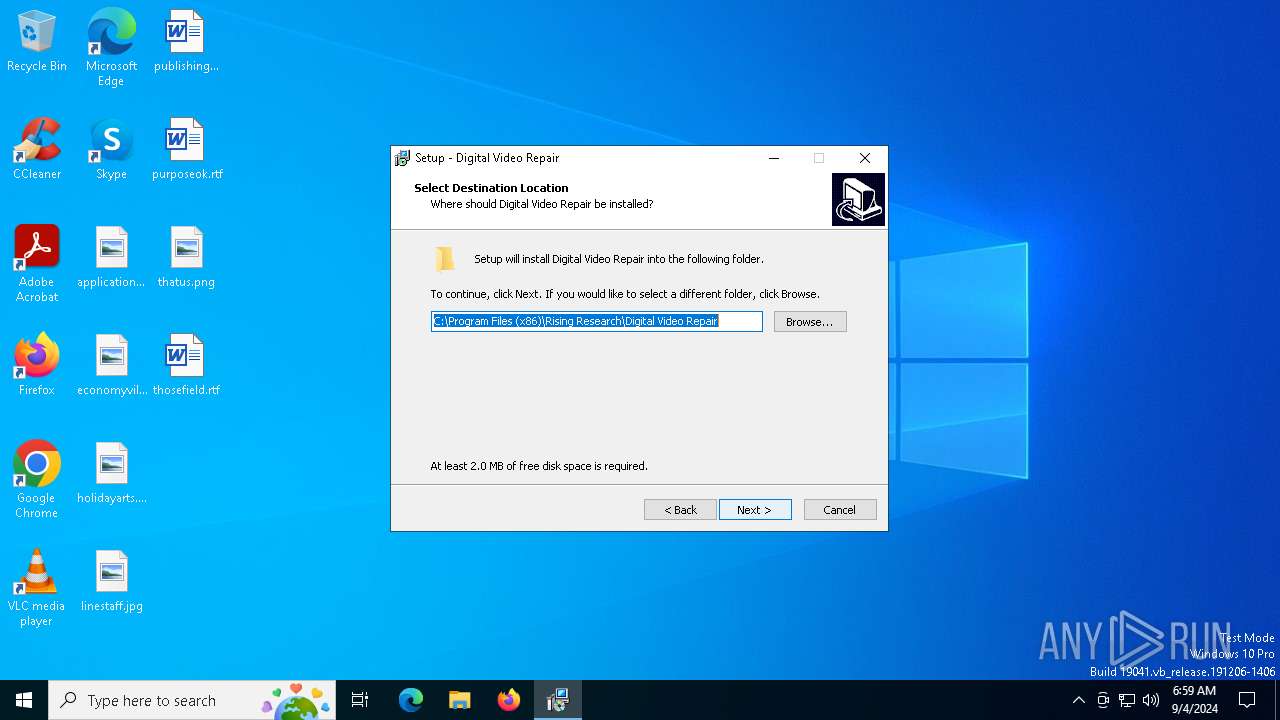
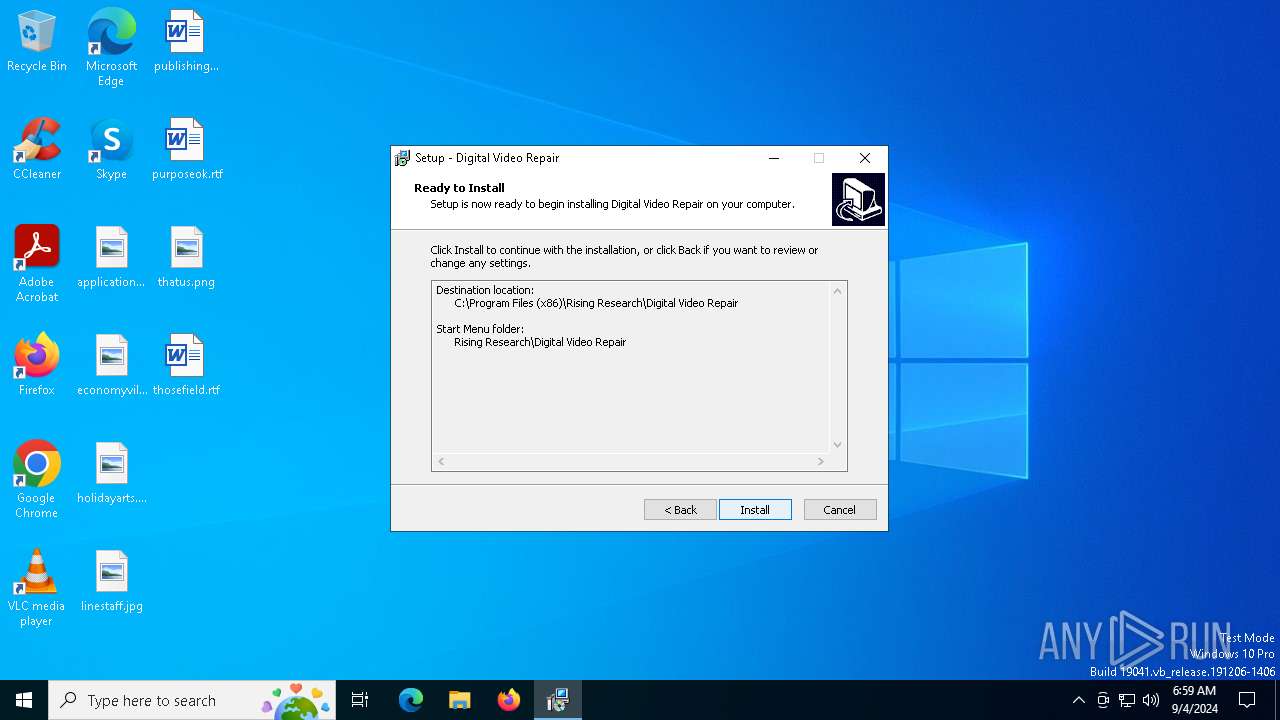
| CompanyName: | Rising Research |
| FileDescription: | Digital Video Repair Setup |
| FileVersion: | 3.7.1.2 |
| LegalCopyright: | (c) Rising Research |
| ProductName: | Digital Video Repair |
| ProductVersion: | 3.7.1.2 |
Total processes
141
Monitored processes
14
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
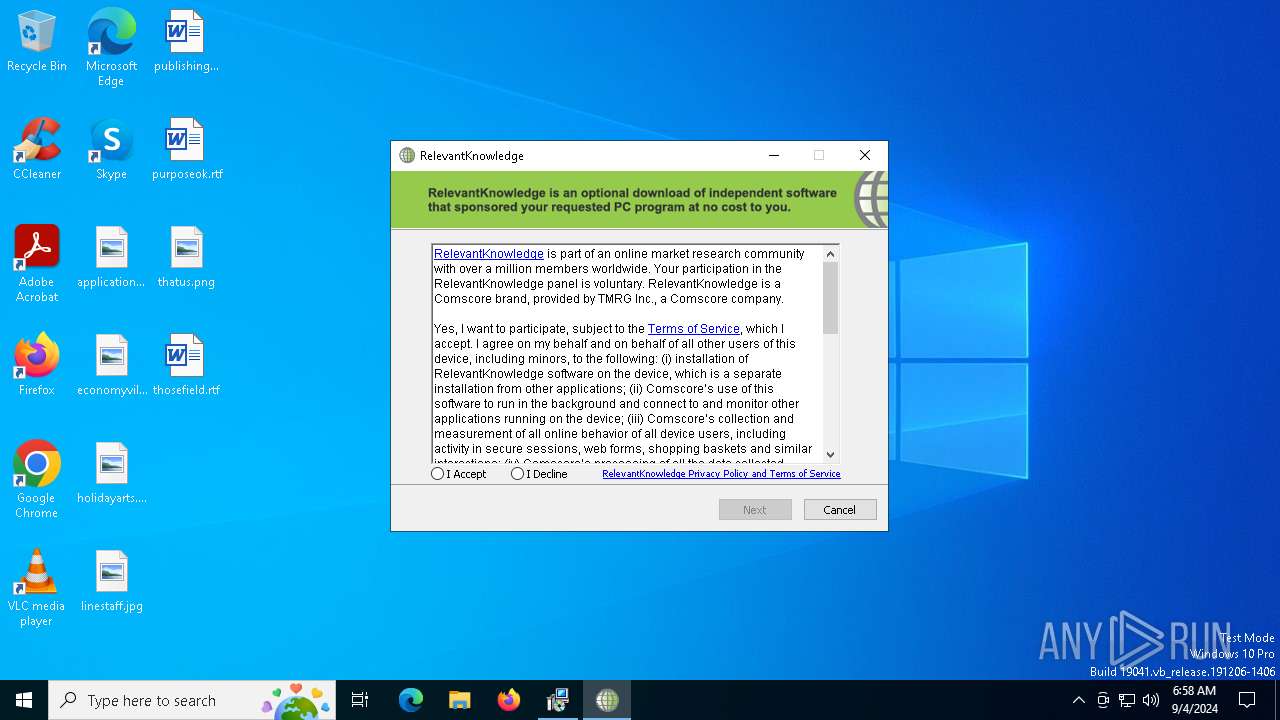
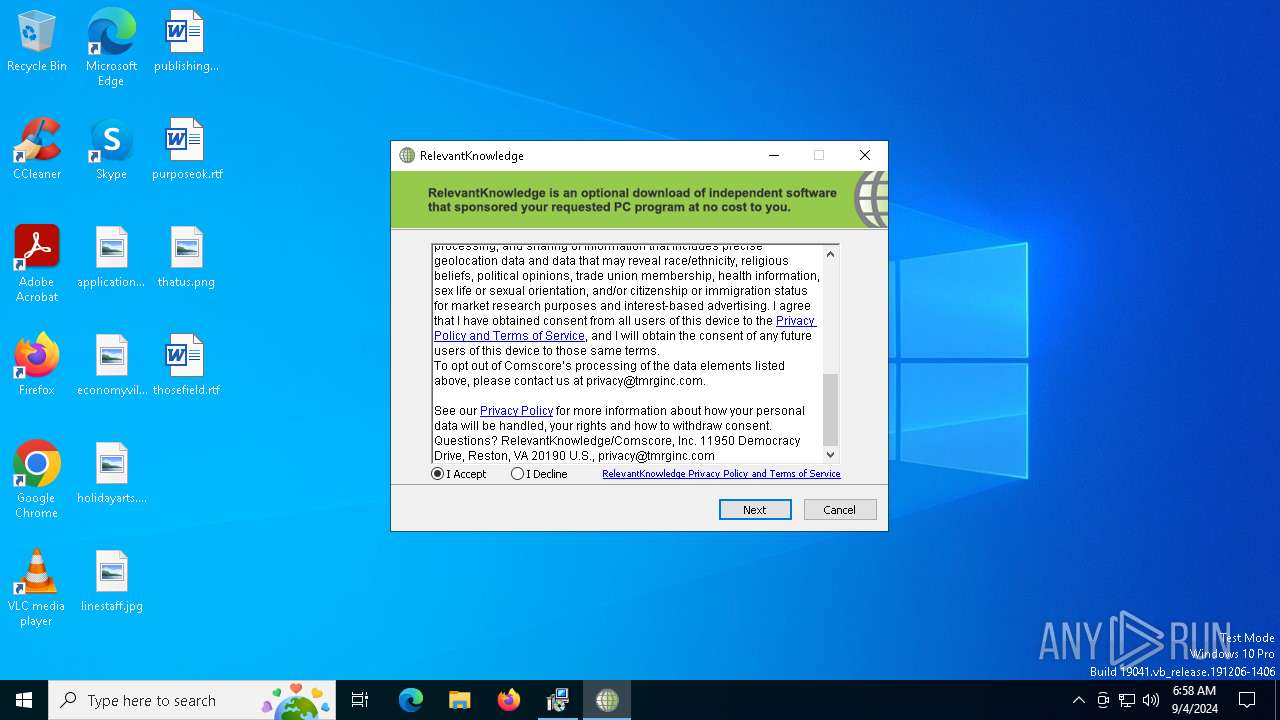
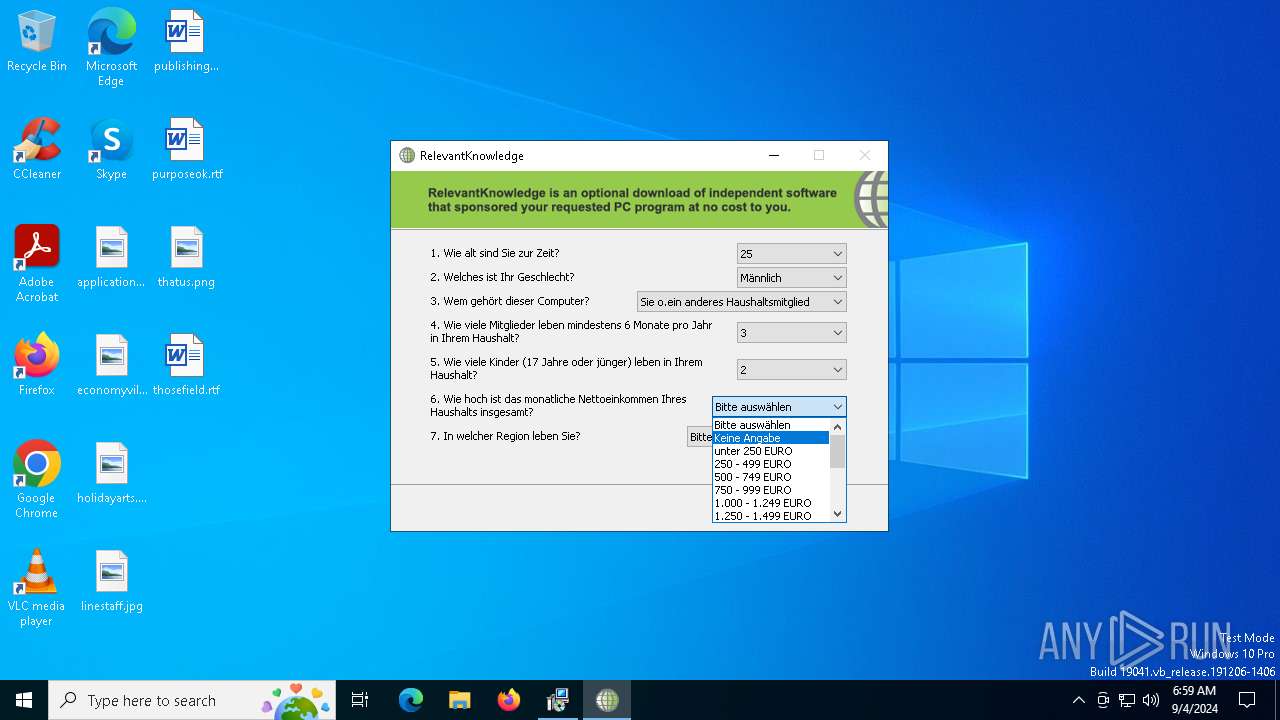
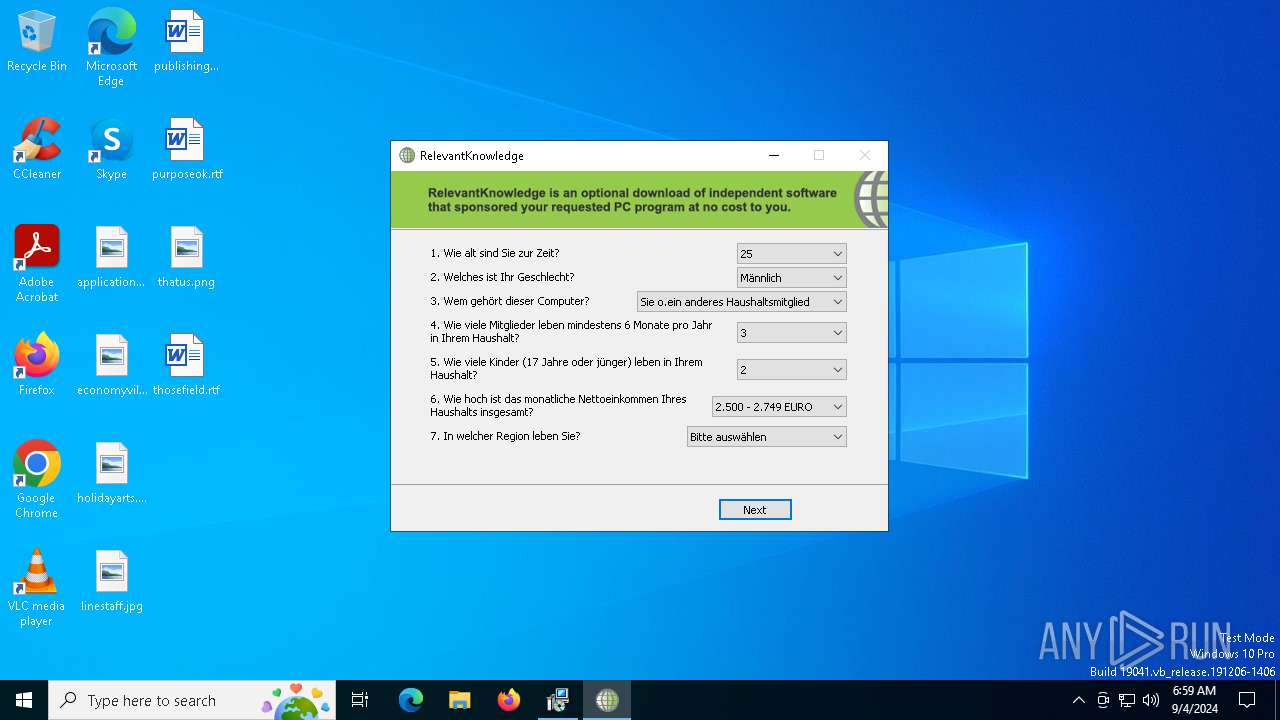
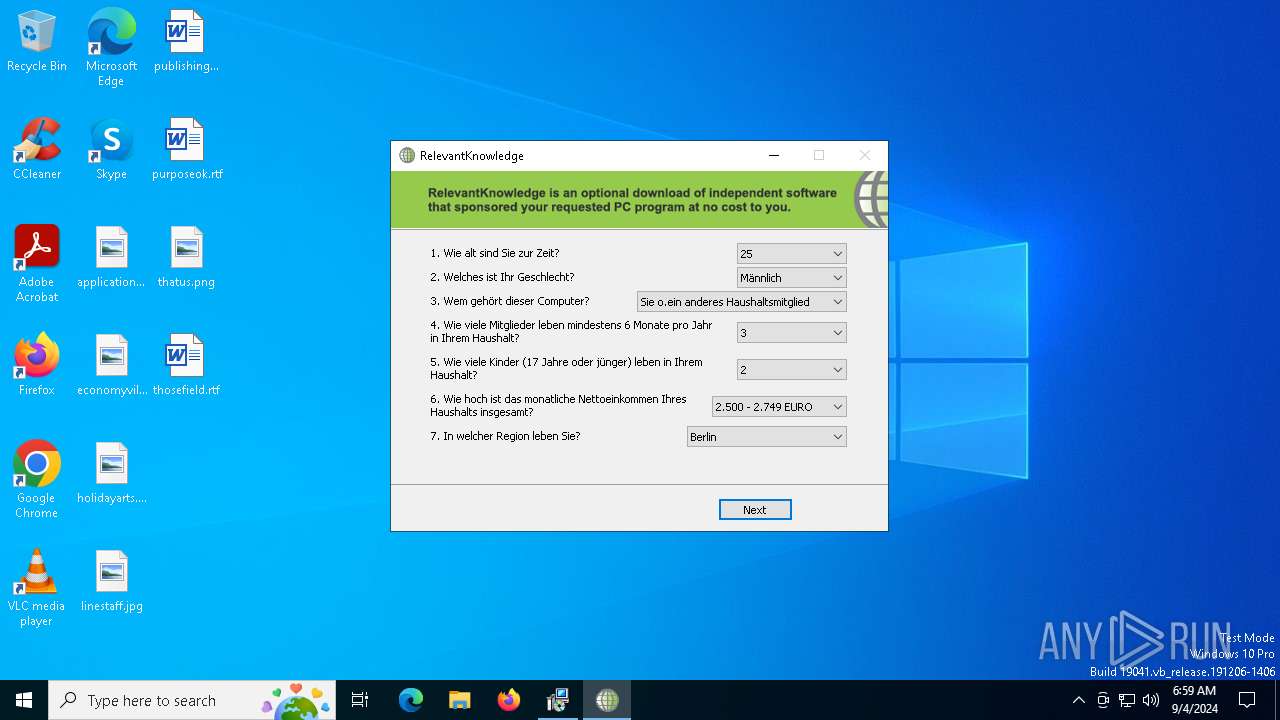
| 872 | "C:\Users\admin\AppData\Local\Temp\is-P35MI.tmp\rk_setup.exe" -c: 3032 -lang: 1 -tpi: IDP_DigitalVideoRepairRKK2 | C:\Users\admin\AppData\Local\Temp\is-P35MI.tmp\rk_setup.exe | dvrsetup.tmp | ||||||||||||
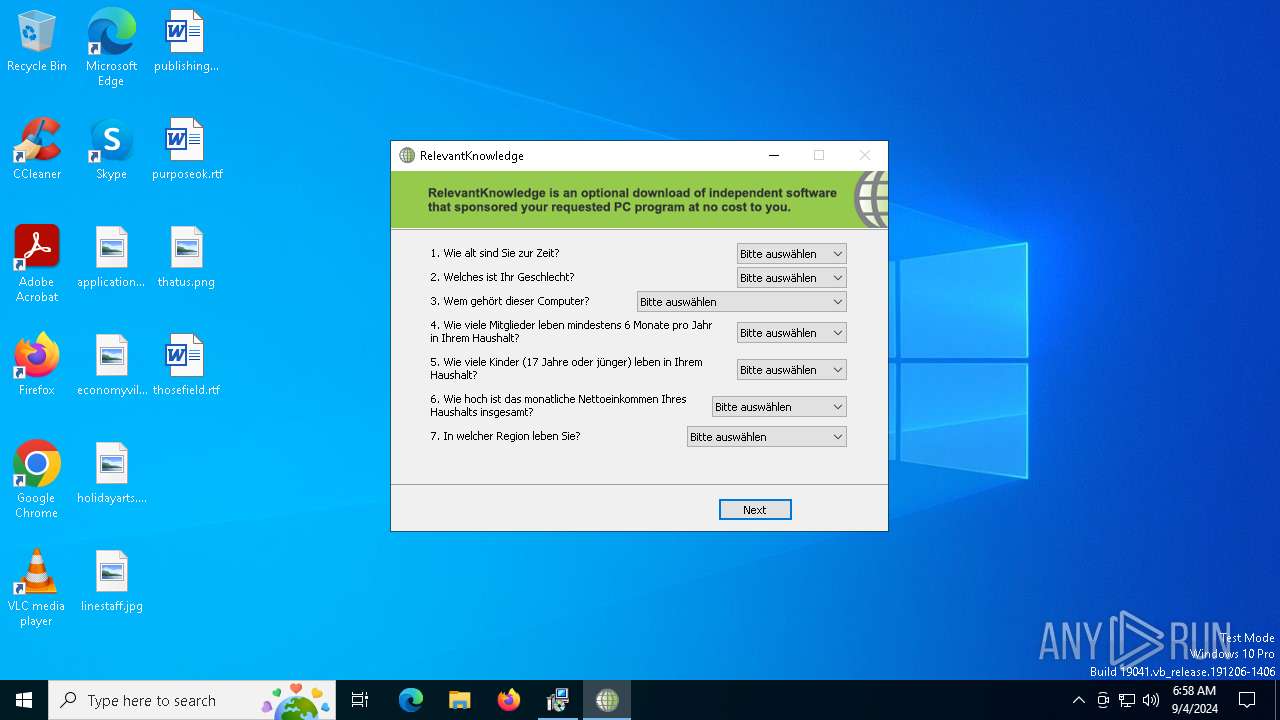
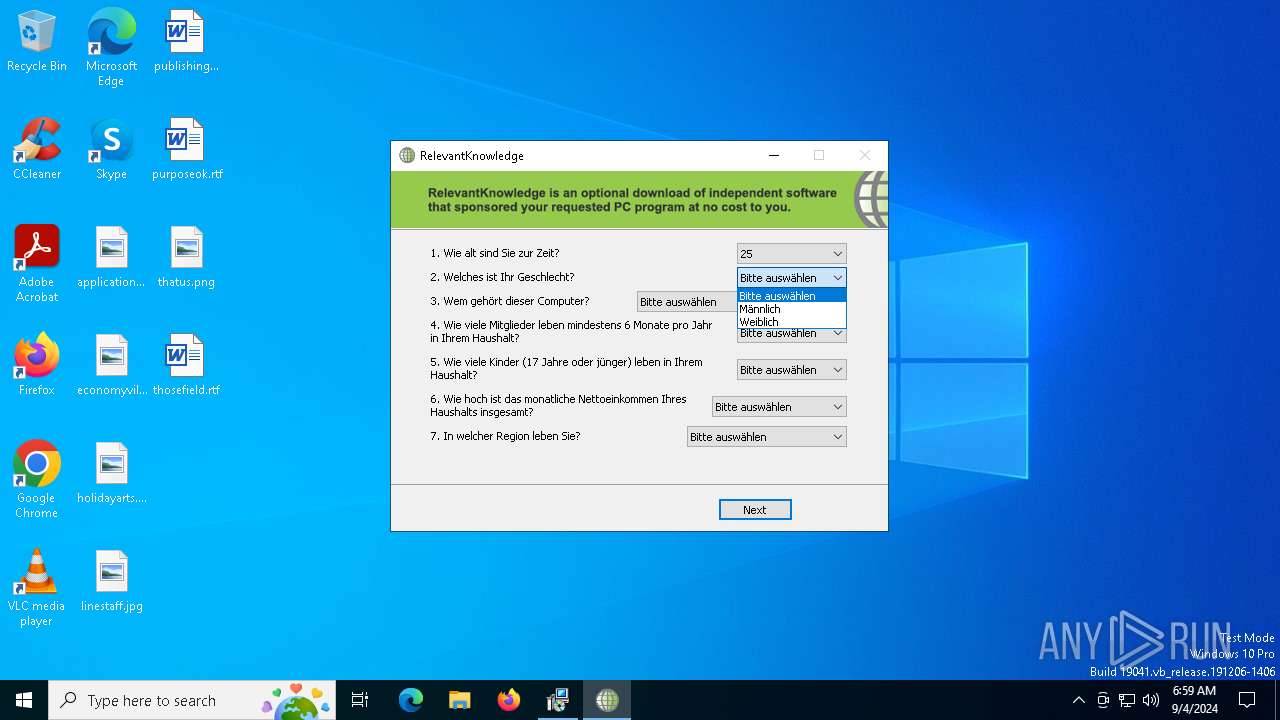
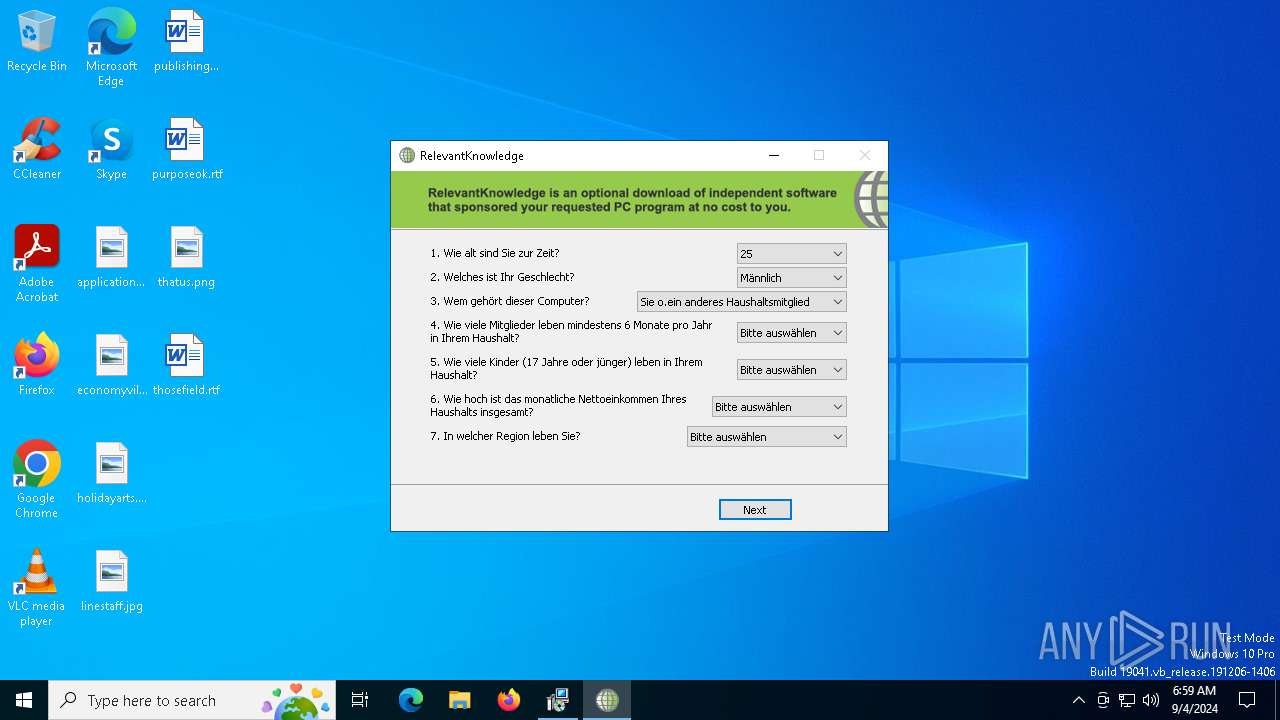
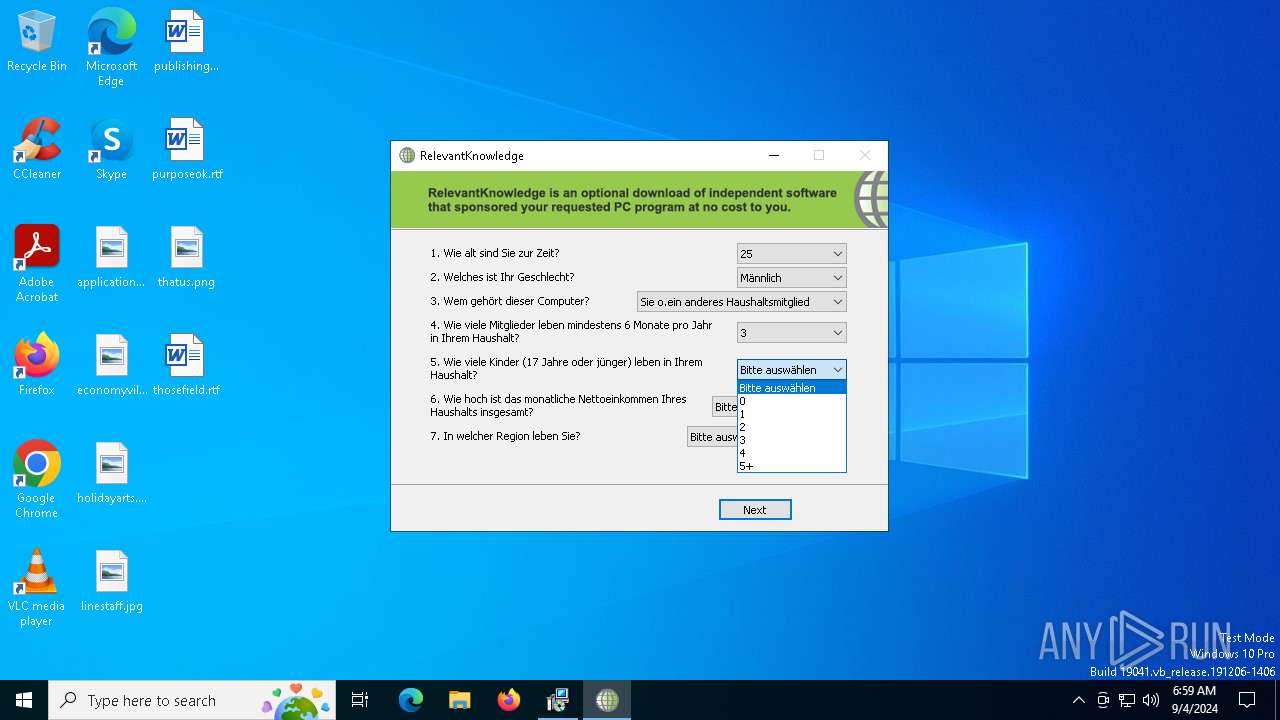
User: admin Company: TMRG Integrity Level: HIGH Description: RelevantKnowledge Setup Setup Exit code: 9 Version: 1.1.0 Modules
| |||||||||||||||
| 1316 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s Schedule | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | reg.exe EXPORT "HKLM\Software\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{d08d9f98-1c78-4704-87e6-368b0023d831}" C:\PROGRA~2\RELEVA~1\RData.reg /y | C:\Windows\SysWOW64\reg.exe | — | rlservice.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2400 | "c:\program files (x86)\relevantknowledge\rlvknlg.exe" -boot | C:\Program Files (x86)\RelevantKnowledge\rlvknlg.exe | rlservice.exe | ||||||||||||
User: admin Company: TMRG, Inc. Integrity Level: MEDIUM Description: Relevant-Knowledge Version: 1.3.340.310 (Build 340.310) Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Local\Temp\is-2DLCM.tmp\installer.exe" -c:3032 -t:IDP_DigitalVideoRepairRKK2 | C:\Users\admin\AppData\Local\Temp\is-2DLCM.tmp\installer.exe | rk_setup.tmp | ||||||||||||
User: admin Company: TMRG, INC. Integrity Level: HIGH Description: Relevant-Knowledge Installer Exit code: 0 Version: 1.0.8.1 (Build 1) Modules
| |||||||||||||||
| 5124 | "C:\Users\admin\AppData\Local\Temp\is-DMDJG.tmp\dvrsetup.tmp" /SL5="$704DA,429571,119296,C:\Users\admin\AppData\Local\Temp\dvrsetup.exe" /SPAWNWND=$80322 /NOTIFYWND=$D01E4 | C:\Users\admin\AppData\Local\Temp\is-DMDJG.tmp\dvrsetup.tmp | dvrsetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 5244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | C:\WINDOWS\system32\rundll32.exe C:\WINDOWS\system32\rlls64.dll,UpdateProcess 1316 | C:\Windows\System32\rundll32.exe | — | rlservice.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "C:\Users\admin\AppData\Local\Temp\dvrsetup.exe" /SPAWNWND=$80322 /NOTIFYWND=$D01E4 | C:\Users\admin\AppData\Local\Temp\dvrsetup.exe | dvrsetup.tmp | ||||||||||||
User: admin Company: Rising Research Integrity Level: HIGH Description: Digital Video Repair Setup Exit code: 0 Version: 3.7.1.2 Modules
| |||||||||||||||
| 6188 | "C:\Users\admin\AppData\Local\Temp\dvrsetup.exe" | C:\Users\admin\AppData\Local\Temp\dvrsetup.exe | explorer.exe | ||||||||||||
User: admin Company: Rising Research Integrity Level: MEDIUM Description: Digital Video Repair Setup Exit code: 0 Version: 3.7.1.2 Modules
| |||||||||||||||
Total events
29 500
Read events
29 301
Write events
158
Delete events
41
Modification events
| (PID) Process: | (1316) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{C2AF3602-9179-4BAE-85B3-74A4EF5CF51F} |
| Operation: | write | Name: | DynamicInfo |
Value: 03000000BDCB09F80A59DA0126BE59E097FEDA01000000000000000051658CE297FEDA01 | |||
| (PID) Process: | (1316) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{4671B5C1-A383-4428-A45A-8D348E4CB873} |
| Operation: | write | Name: | DynamicInfo |
Value: 030000009F7DFD23AAB7D8014A1549E097FEDA0100000000000000009772D0E397FEDA01 | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 04140000CA80BDE297FEDA01 | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: BC7F3BC6B970A45C59365BD2B717FDB6E0520ACCC5B89D54B97B7854B5C6D60D | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Rising Research\Digital Video Repair |
| Operation: | write | Name: | Language |
Value: 0 | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5124) dvrsetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
35
Suspicious files
21
Text files
25
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6188 | dvrsetup.exe | C:\Users\admin\AppData\Local\Temp\is-542SM.tmp\dvrsetup.tmp | executable | |
MD5:6A96BEF4679E16A54B4090E74664DCCA | SHA256:CB095356DDCFCBACE96C6252FB73A267ED011C15FF206A7A9302007BAA68A783 | |||
| 5124 | dvrsetup.tmp | C:\Users\admin\AppData\Local\Temp\is-P35MI.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 5124 | dvrsetup.tmp | C:\Users\admin\AppData\Local\Temp\is-P35MI.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 4060 | installer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\rkfC[1].bin | — | |
MD5:— | SHA256:— | |||
| 4060 | installer.exe | C:\Users\admin\AppData\Local\Temp\osi592F.tmp | — | |
MD5:— | SHA256:— | |||
| 6968 | rk_setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2DLCM.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 5124 | dvrsetup.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | der | |
MD5:0E9B5D4346A2CE2A3FB31D9CEF97313D | SHA256:216E4AB5D4243D93615A59FF2342573D10A4424B968D52D2D84A787DCAE80661 | |||
| 5124 | dvrsetup.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F53EB4E574DE32C870452087D92DBEBB_6D263F6DDB7D7C531B75FF66E0A31295 | der | |
MD5:3F4B6FE58AE2A7D5744EF986F9BEAC75 | SHA256:560F956859B13500C2A425C30CF0C9E88074DF824DD179F21ABB1F74458245CC | |||
| 6968 | rk_setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2DLCM.tmp\banner.bmp | image | |
MD5:B57BA367D98A2FD2B8450ADC87D4B6D4 | SHA256:F7533CE87599698B009FE67826BEA2BB3BF1280EEEABC3AE28F29CF8A1D31F46 | |||
| 5548 | dvrsetup.exe | C:\Users\admin\AppData\Local\Temp\is-DMDJG.tmp\dvrsetup.tmp | executable | |
MD5:6A96BEF4679E16A54B4090E74664DCCA | SHA256:CB095356DDCFCBACE96C6252FB73A267ED011C15FF206A7A9302007BAA68A783 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
36
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5124 | dvrsetup.tmp | GET | 200 | 18.245.65.219:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEAlP7jAS3v%2Bl2J82Ok5qEvI%3D | unknown | — | — | whitelisted |
2096 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2096 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5124 | dvrsetup.tmp | GET | 200 | 18.245.39.64:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | unknown | — | — | unknown |
6512 | rlvknlg.exe | HEAD | 200 | 165.193.78.245:80 | http://www.relevantknowledge.com/Tile.aspx | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7080 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6776 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5124 | dvrsetup.tmp | 13.32.121.51:443 | dpd.securestudies.com | AMAZON-02 | US | whitelisted |
5124 | dvrsetup.tmp | 18.245.39.64:80 | ocsp.rootca1.amazontrust.com | — | US | shared |
5124 | dvrsetup.tmp | 18.245.65.219:80 | ocsp.r2m02.amazontrust.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
dpd.securestudies.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.r2m02.amazontrust.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |