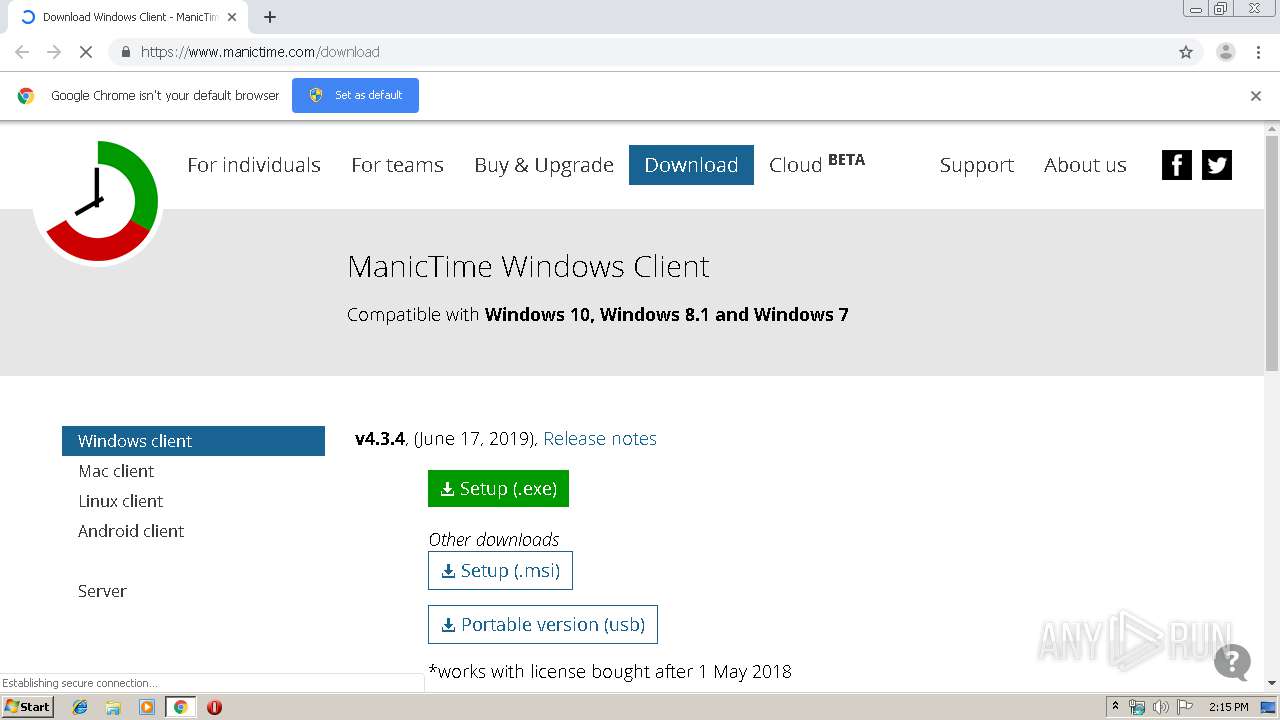
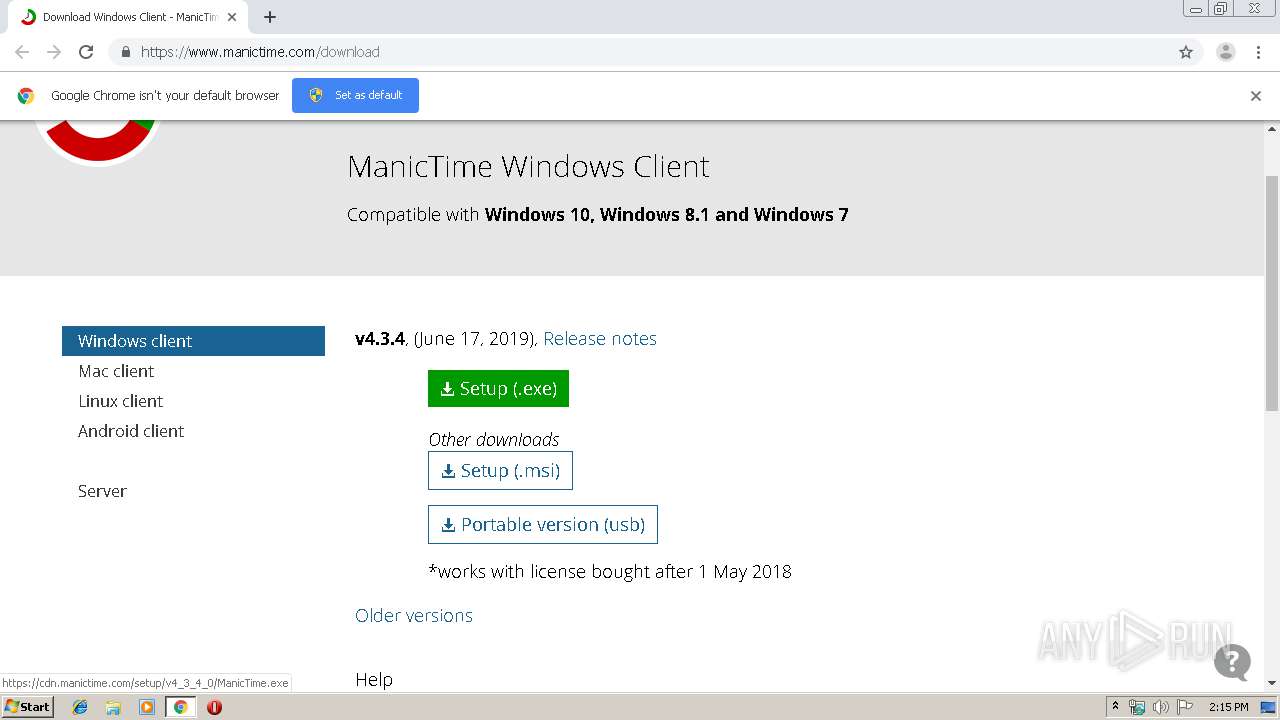
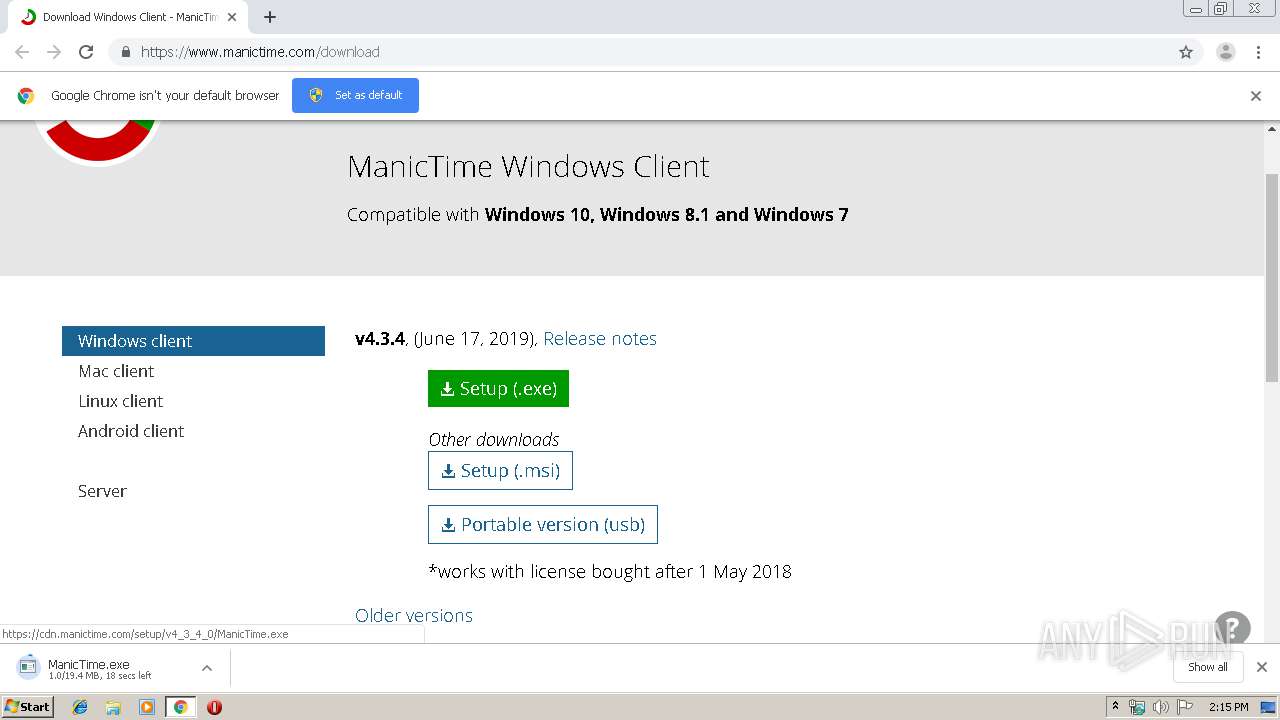
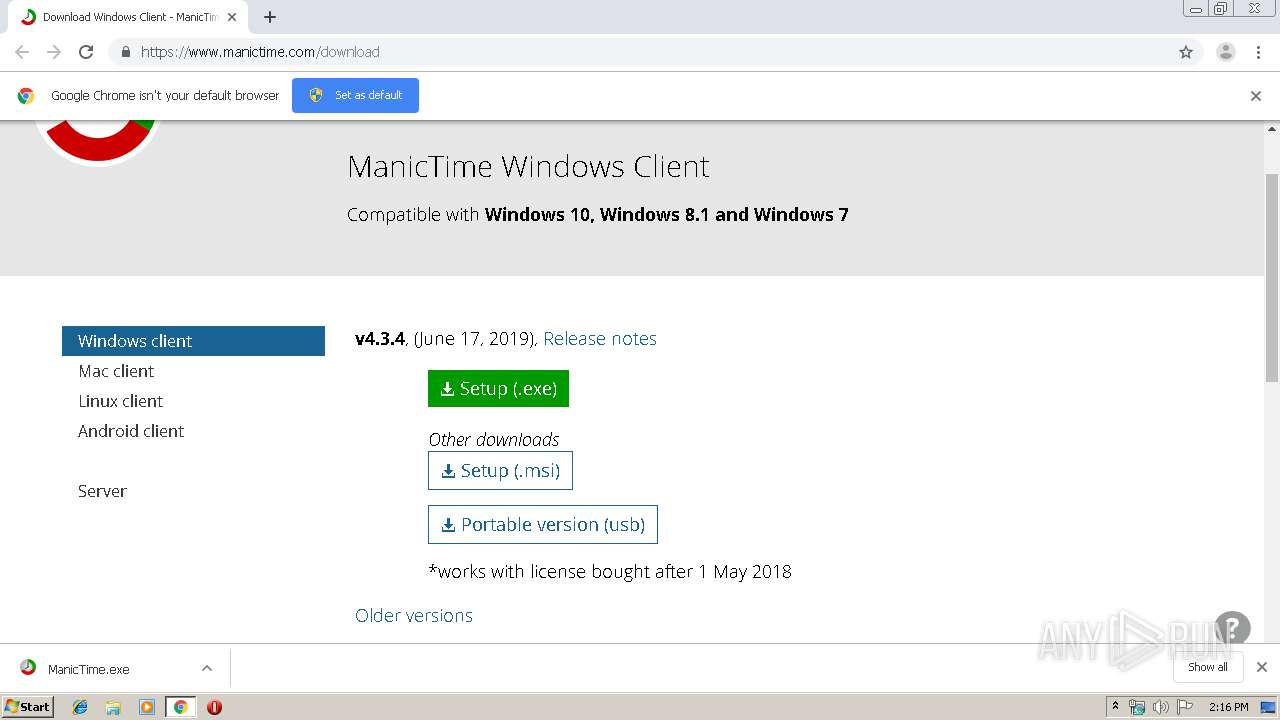
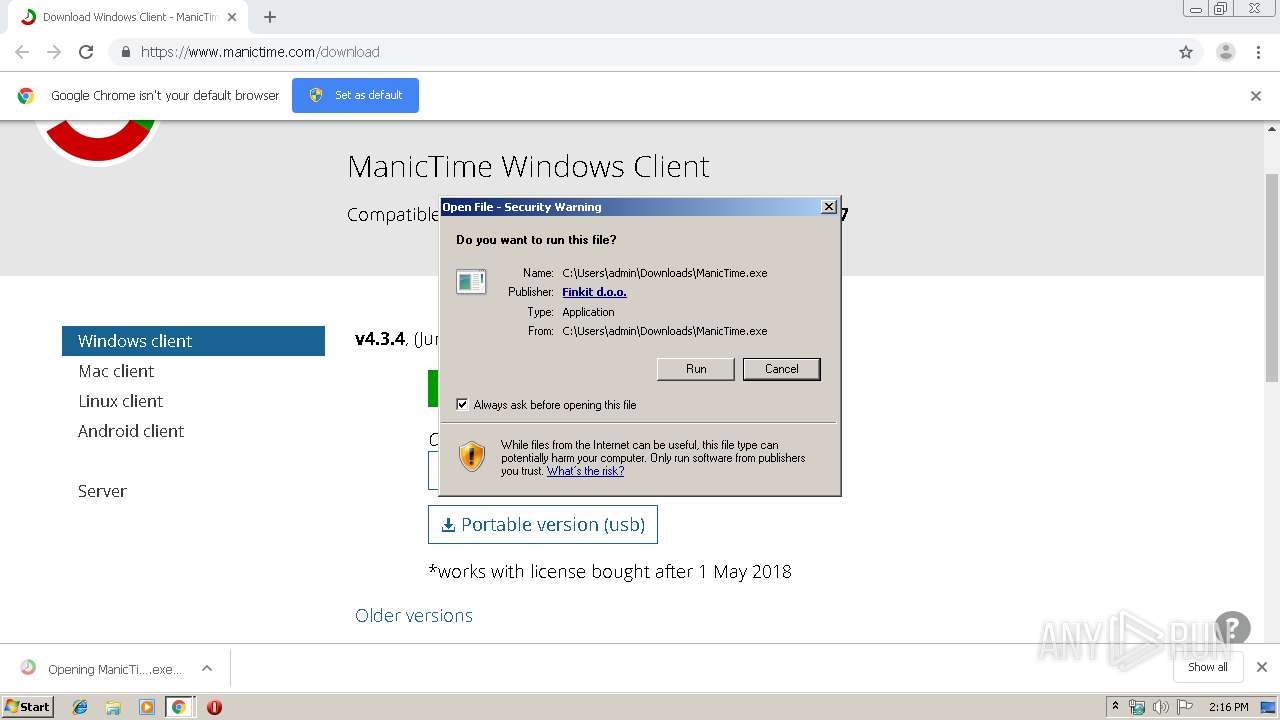
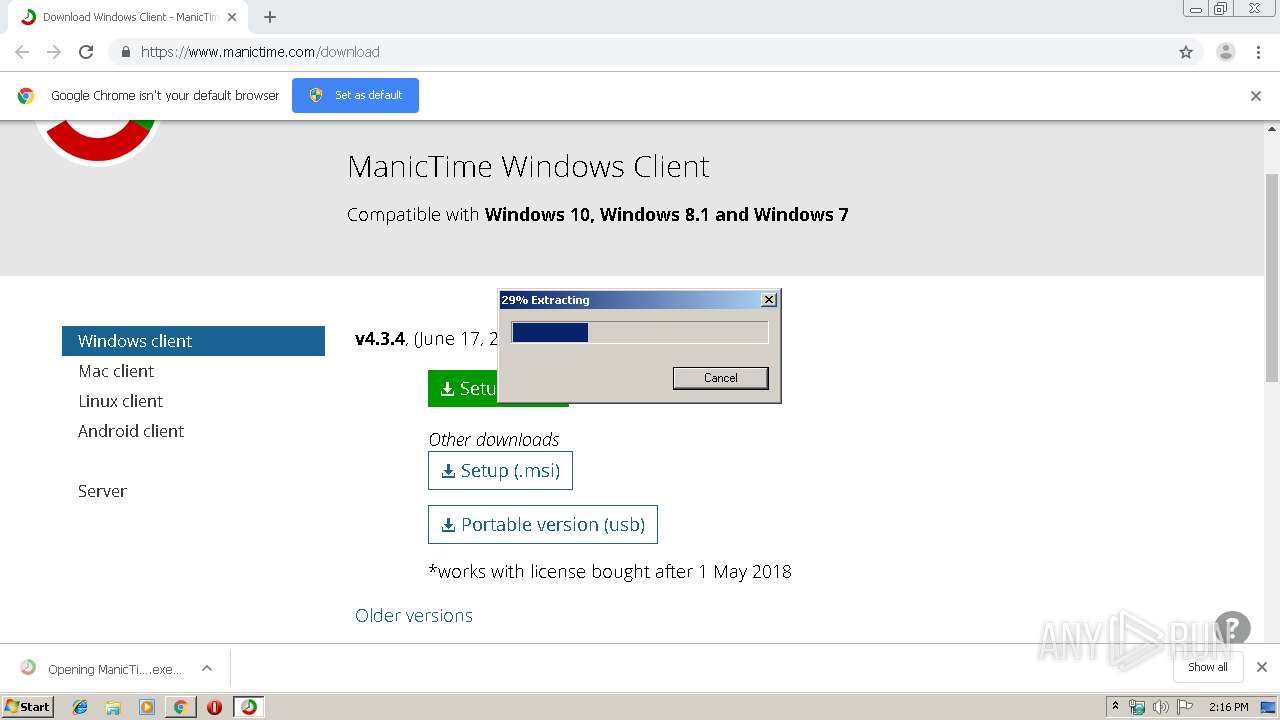
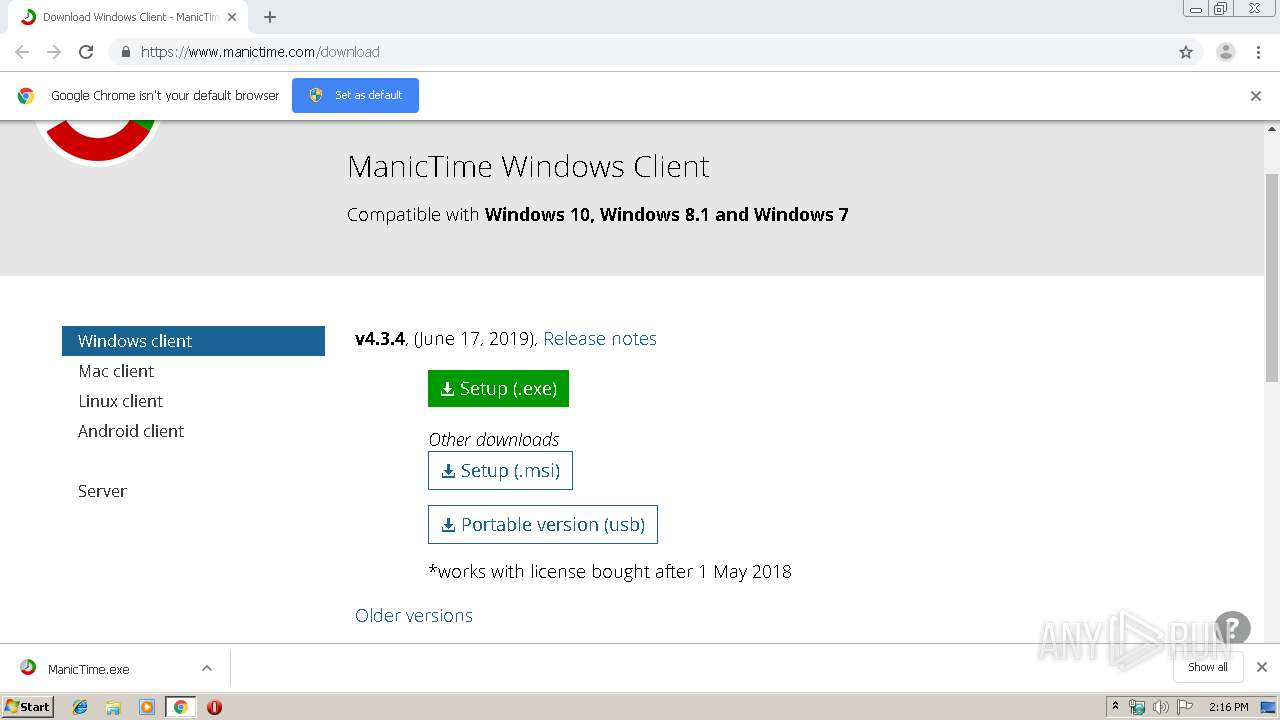
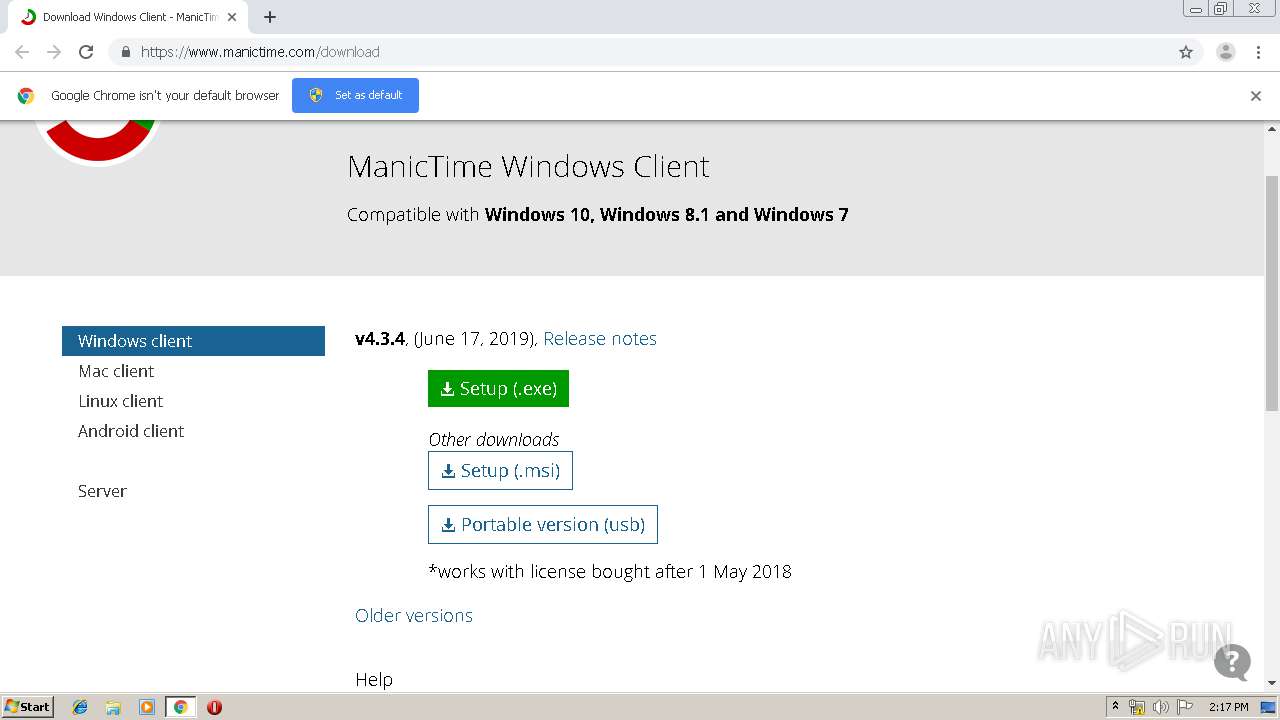
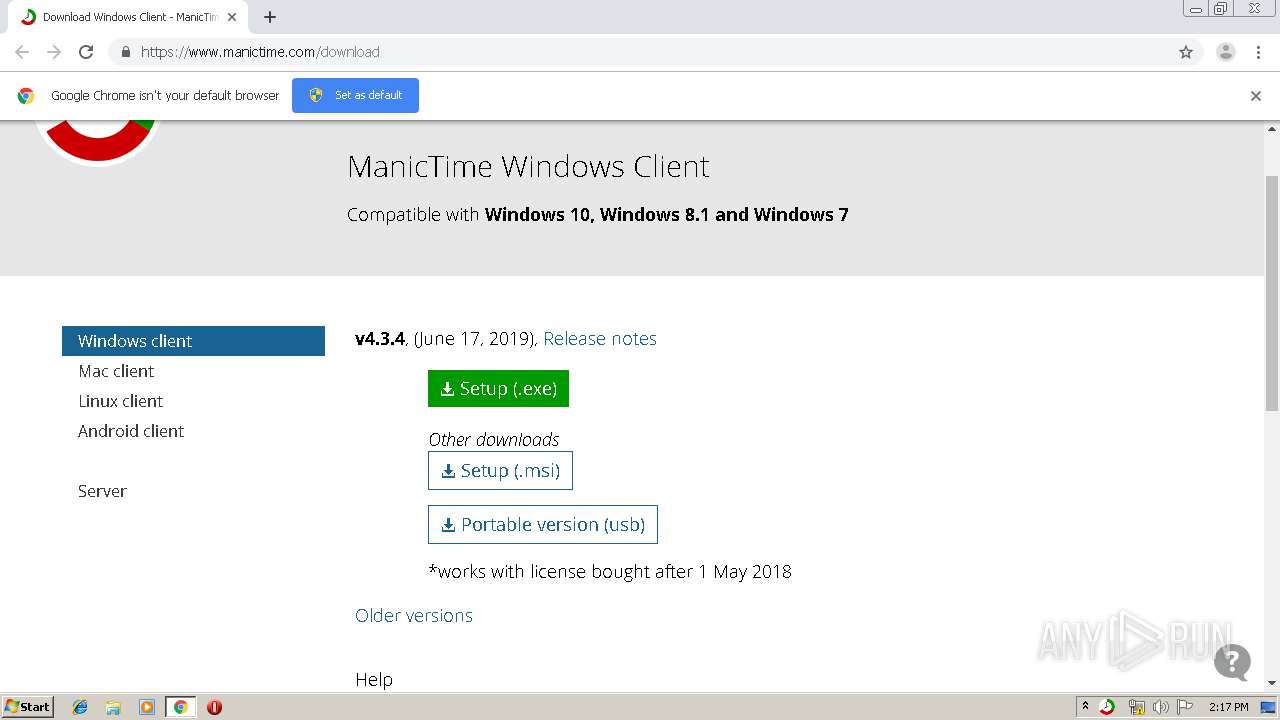
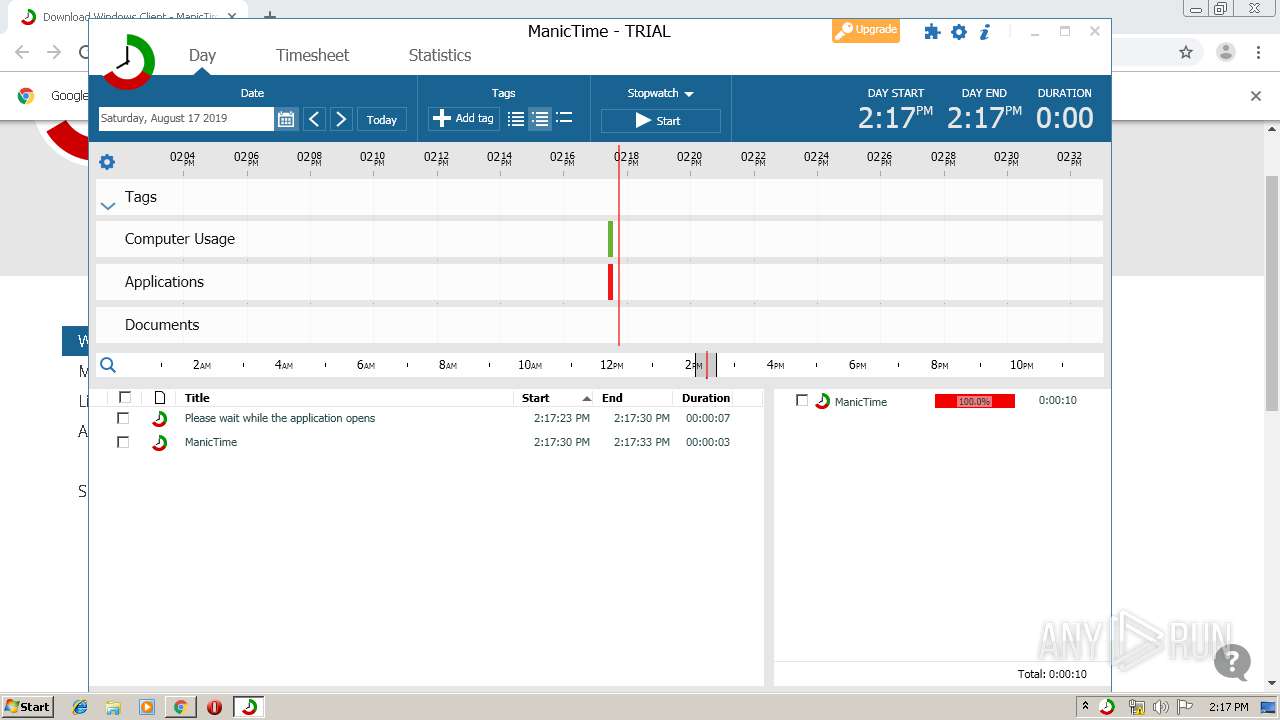
| URL: | https://www.manictime.com/download |
| Full analysis: | https://app.any.run/tasks/e1a39648-432f-46d9-8d62-92ccac55317d |
| Verdict: | Malicious activity |
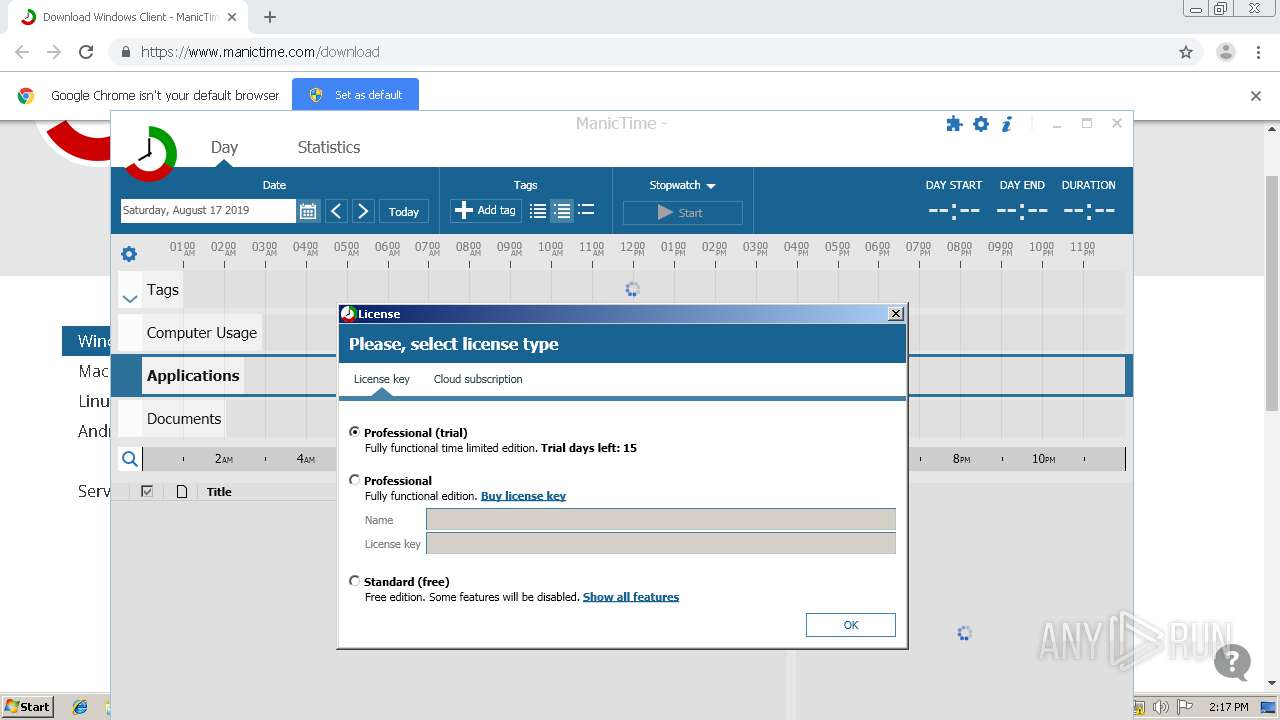
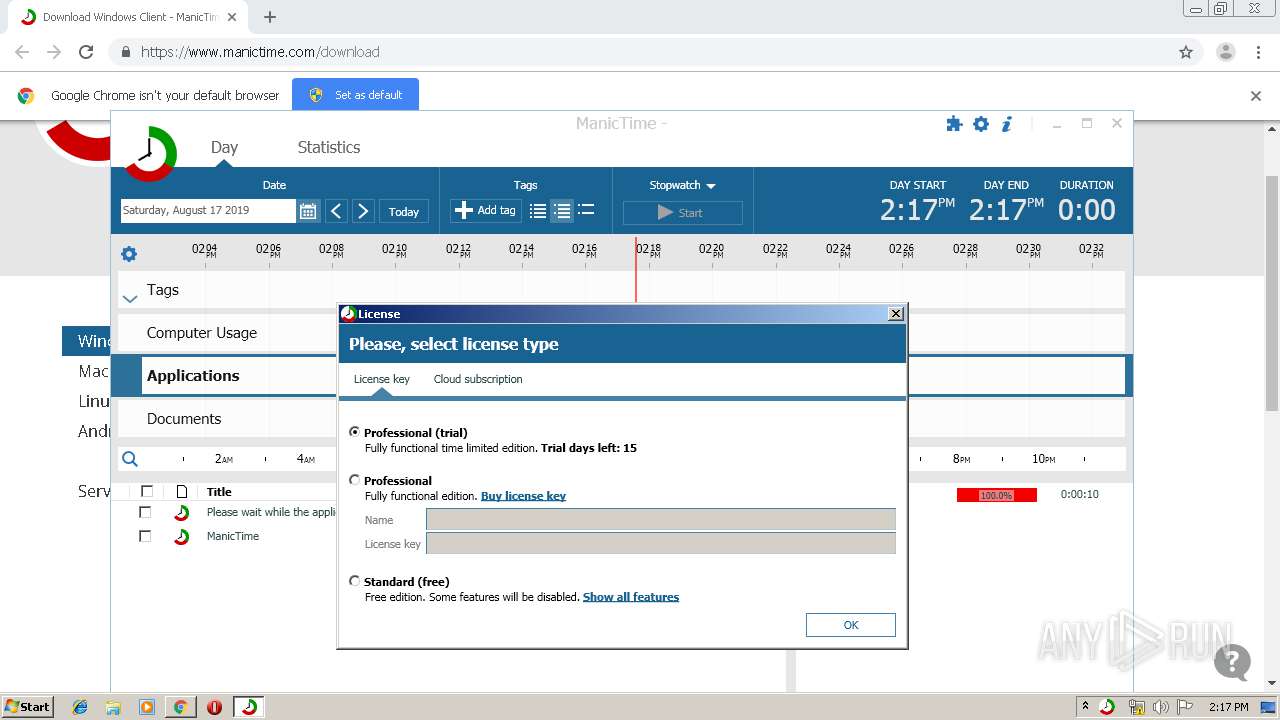
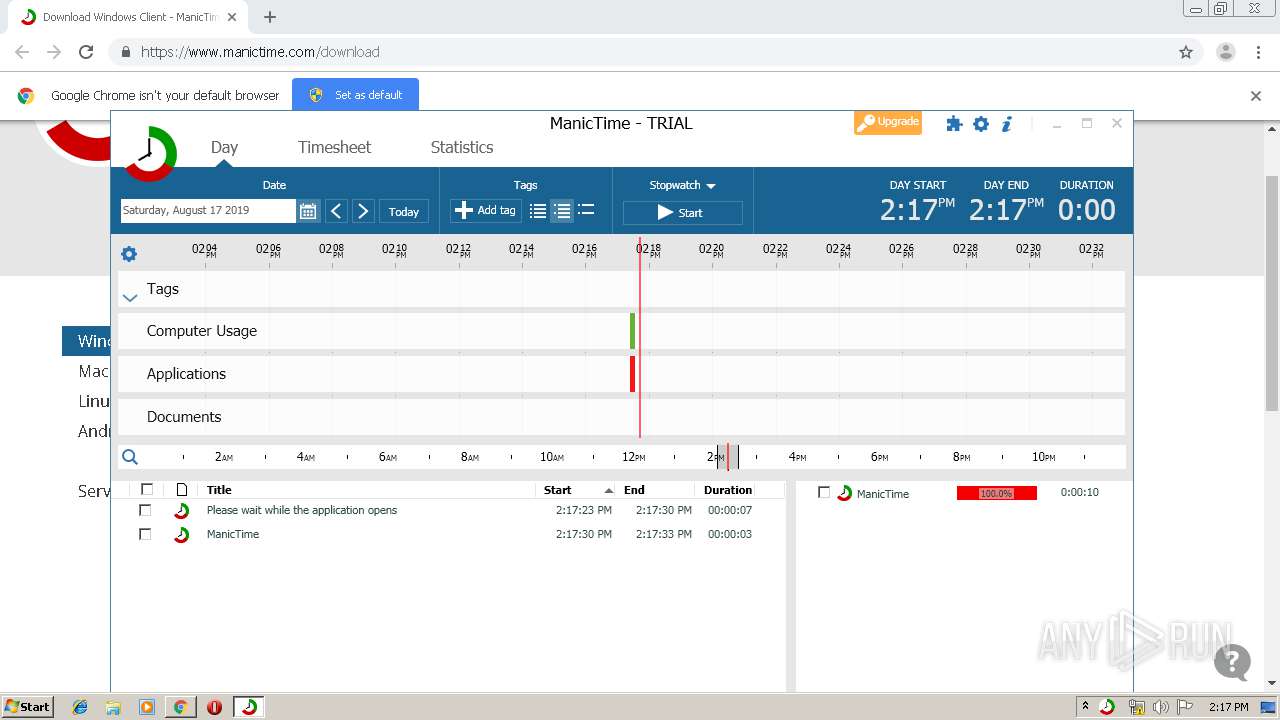
| Analysis date: | August 17, 2019, 13:15:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 725E610E389960C660E140E216AE4732 |
| SHA1: | F077CB48B161F40F8E0A967EC8465175948C55E0 |
| SHA256: | D74D04D2186C3C2E7A452A38770FF245DEC2C879E612C71045F2A3D9FA77EEB7 |
| SSDEEP: | 3:N8DSLmGRJwKM:2OLmGz/M |
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 3444)
- rundll32.exe (PID: 2668)
- rundll32.exe (PID: 4056)
- rundll32.exe (PID: 3964)
- rundll32.exe (PID: 3148)
- rundll32.exe (PID: 1648)
- rundll32.exe (PID: 3536)
- mscorsvw.exe (PID: 3100)
- mscorsvw.exe (PID: 1216)
- mscorsvw.exe (PID: 1348)
- mscorsvw.exe (PID: 3276)
- mscorsvw.exe (PID: 4056)
- ManicTime.exe (PID: 1856)
- mscorsvw.exe (PID: 3436)
- ManicTimeClient.exe (PID: 548)
- mscorsvw.exe (PID: 1264)
- mscorsvw.exe (PID: 3348)
- mscorsvw.exe (PID: 3880)
- mscorsvw.exe (PID: 3364)
- mscorsvw.exe (PID: 3040)
- mscorsvw.exe (PID: 2528)
- mscorsvw.exe (PID: 2476)
- mscorsvw.exe (PID: 3408)
- mscorsvw.exe (PID: 1744)
- mscorsvw.exe (PID: 3212)
- mscorsvw.exe (PID: 776)
- mscorsvw.exe (PID: 3596)
- mscorsvw.exe (PID: 3088)
- mscorsvw.exe (PID: 2404)
- mscorsvw.exe (PID: 1816)
- mscorsvw.exe (PID: 3488)
- mscorsvw.exe (PID: 2324)
- mscorsvw.exe (PID: 2552)
- mscorsvw.exe (PID: 2932)
- mscorsvw.exe (PID: 4004)
- mscorsvw.exe (PID: 2640)
- mscorsvw.exe (PID: 3252)
- mscorsvw.exe (PID: 876)
- mscorsvw.exe (PID: 2688)
- mscorsvw.exe (PID: 3008)
- mscorsvw.exe (PID: 2692)
- mscorsvw.exe (PID: 2204)
- mscorsvw.exe (PID: 2304)
- mscorsvw.exe (PID: 3544)
- mscorsvw.exe (PID: 2252)
- mscorsvw.exe (PID: 704)
- mscorsvw.exe (PID: 1396)
- mscorsvw.exe (PID: 1728)
- mscorsvw.exe (PID: 1080)
- mscorsvw.exe (PID: 2584)
- mscorsvw.exe (PID: 3792)
- mscorsvw.exe (PID: 1796)
- mscorsvw.exe (PID: 3652)
- mscorsvw.exe (PID: 3088)
- mscorsvw.exe (PID: 1440)
- mscorsvw.exe (PID: 3584)
- mscorsvw.exe (PID: 1628)
- mscorsvw.exe (PID: 3092)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 2868)
- mscorsvw.exe (PID: 4032)
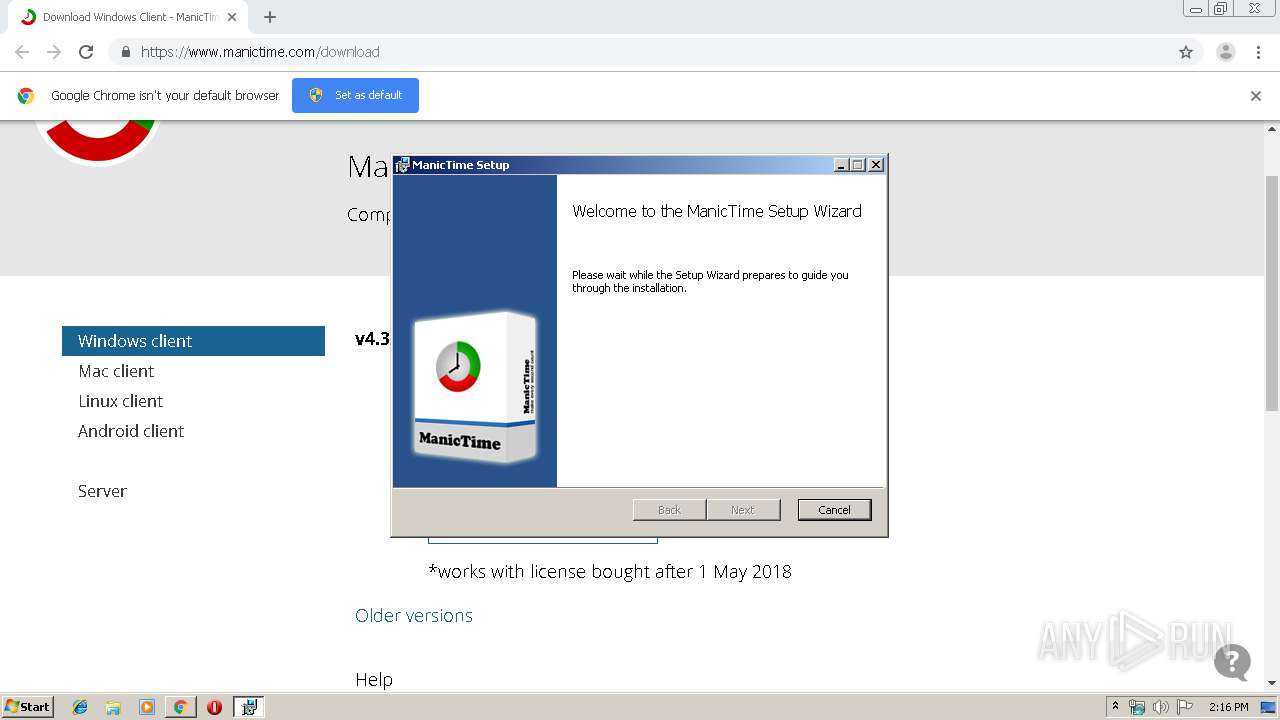
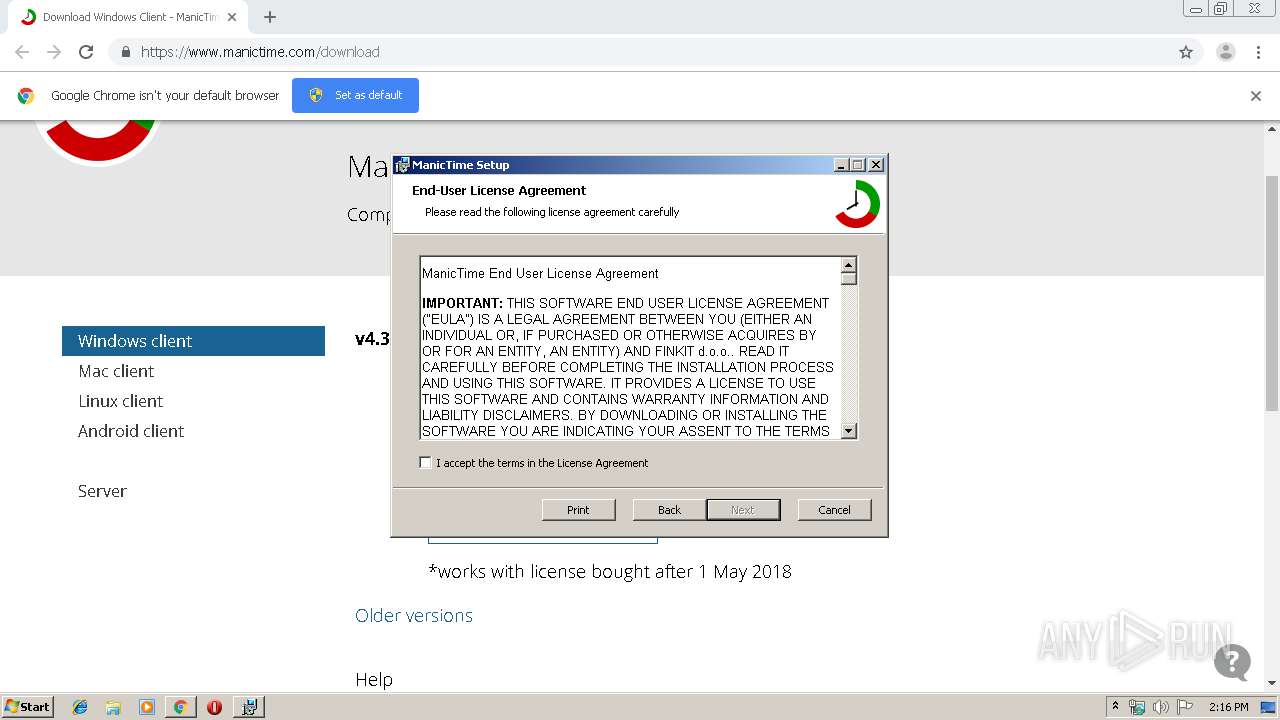
Application was dropped or rewritten from another process
- ManicTime.exe (PID: 2892)
- setup.exe (PID: 4036)
- ManicTime.exe (PID: 1856)
- ManicTimeClient.exe (PID: 548)
Loads the Task Scheduler COM API
- ngen.exe (PID: 2360)
- ngen.exe (PID: 3072)
- ngen.exe (PID: 2548)
- ngen.exe (PID: 2604)
- ngen.exe (PID: 2152)
- ngen.exe (PID: 3964)
- ngen.exe (PID: 2520)
- ngen.exe (PID: 3644)
- ngen.exe (PID: 2592)
- ngen.exe (PID: 3784)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 3048)
- ngen.exe (PID: 2800)
- ngen.exe (PID: 364)
- ngen.exe (PID: 2312)
- ngen.exe (PID: 3756)
- ngen.exe (PID: 2216)
- ngen.exe (PID: 408)
- ngen.exe (PID: 2244)
- ngen.exe (PID: 2460)
- ngen.exe (PID: 3572)
- ngen.exe (PID: 2180)
- ngen.exe (PID: 560)
- ngen.exe (PID: 3380)
- ngen.exe (PID: 1000)
- ngen.exe (PID: 1492)
- ngen.exe (PID: 3160)
- ngen.exe (PID: 2352)
- ngen.exe (PID: 2888)
- ngen.exe (PID: 2452)
- ngen.exe (PID: 3744)
- ngen.exe (PID: 3336)
- ngen.exe (PID: 3540)
- ngen.exe (PID: 2596)
- ngen.exe (PID: 3380)
- ngen.exe (PID: 2712)
- ngen.exe (PID: 304)
- ngen.exe (PID: 2208)
- ngen.exe (PID: 3628)
- ngen.exe (PID: 3180)
- ngen.exe (PID: 3636)
- ngen.exe (PID: 2332)
- ngen.exe (PID: 2548)
- ngen.exe (PID: 2556)
- ngen.exe (PID: 3644)
- ngen.exe (PID: 2428)
- ngen.exe (PID: 408)
- ngen.exe (PID: 3232)
- ngen.exe (PID: 2364)
- ngen.exe (PID: 780)
- ngen.exe (PID: 3540)
- ngen.exe (PID: 2420)
- ngen.exe (PID: 2616)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 1644)
- ngen.exe (PID: 1968)
- ngen.exe (PID: 3868)
- ngen.exe (PID: 2908)
- ngen.exe (PID: 2076)
- ngen.exe (PID: 1520)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 2416)
- ngen.exe (PID: 3972)
- ngen.exe (PID: 3876)
- ngen.exe (PID: 3676)
- ngen.exe (PID: 1784)
- ngen.exe (PID: 3760)
- ngen.exe (PID: 3296)
- ngen.exe (PID: 3920)
- ngen.exe (PID: 3868)
- ngen.exe (PID: 2884)
- ngen.exe (PID: 360)
- ngen.exe (PID: 564)
- ngen.exe (PID: 2952)
- ngen.exe (PID: 3180)
- ngen.exe (PID: 2064)
- ngen.exe (PID: 1812)
- ngen.exe (PID: 2364)
- ngen.exe (PID: 3000)
- ngen.exe (PID: 3896)
- ngen.exe (PID: 2592)
- ngen.exe (PID: 2888)
- ngen.exe (PID: 2976)
- ngen.exe (PID: 1156)
- ngen.exe (PID: 872)
- ngen.exe (PID: 3400)
- ngen.exe (PID: 916)
- ngen.exe (PID: 2520)
- ngen.exe (PID: 2852)
- ngen.exe (PID: 2716)
- ngen.exe (PID: 2404)
- ngen.exe (PID: 3596)
- ngen.exe (PID: 3096)
- ngen.exe (PID: 1812)
- ngen.exe (PID: 1304)
- ngen.exe (PID: 2992)
- ngen.exe (PID: 2532)
- ngen.exe (PID: 1428)
- ngen.exe (PID: 3932)
- ngen.exe (PID: 3852)
- ngen.exe (PID: 1032)
- ngen.exe (PID: 3196)
- ngen.exe (PID: 3336)
- ngen.exe (PID: 3136)
- ngen.exe (PID: 1632)
- ngen.exe (PID: 3220)
- ngen.exe (PID: 2512)
- ngen.exe (PID: 560)
- ngen.exe (PID: 2960)
- ngen.exe (PID: 3760)
- ngen.exe (PID: 1188)
- ngen.exe (PID: 3204)
- ngen.exe (PID: 1968)
- ngen.exe (PID: 3660)
- ngen.exe (PID: 1440)
- ngen.exe (PID: 2716)
- ngen.exe (PID: 316)
- ngen.exe (PID: 2604)
- ngen.exe (PID: 3824)
- ngen.exe (PID: 2628)
- ngen.exe (PID: 2420)
- ngen.exe (PID: 2484)
- ngen.exe (PID: 1720)
- ngen.exe (PID: 3100)
- ngen.exe (PID: 2056)
- ngen.exe (PID: 3136)
- ngen.exe (PID: 1736)
- ngen.exe (PID: 888)
- ngen.exe (PID: 3316)
- ngen.exe (PID: 3312)
- ngen.exe (PID: 4088)
- ngen.exe (PID: 3888)
- ngen.exe (PID: 2304)
- ngen.exe (PID: 564)
- ngen.exe (PID: 2412)
- ngen.exe (PID: 3632)
- ngen.exe (PID: 2952)
- ngen.exe (PID: 3484)
- ngen.exe (PID: 1520)
- ngen.exe (PID: 4000)
- ngen.exe (PID: 3320)
- ngen.exe (PID: 996)
- ngen.exe (PID: 3232)
- ngen.exe (PID: 3284)
- ngen.exe (PID: 1484)
- ngen.exe (PID: 2760)
- ngen.exe (PID: 2396)
- ngen.exe (PID: 3676)
- ngen.exe (PID: 3680)
- ngen.exe (PID: 2936)
- ngen.exe (PID: 3104)
- ngen.exe (PID: 3584)
- ngen.exe (PID: 3904)
- ngen.exe (PID: 3012)
- ngen.exe (PID: 1304)
- ngen.exe (PID: 3604)
- ngen.exe (PID: 1264)
- ngen.exe (PID: 2660)
- ngen.exe (PID: 552)
- ngen.exe (PID: 2672)
- ngen.exe (PID: 3912)
- ngen.exe (PID: 3296)
- ngen.exe (PID: 2508)
- ngen.exe (PID: 2428)
Changes the autorun value in the registry
- ManicTime.exe (PID: 1856)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2900)
- ManicTime.exe (PID: 2892)
- msiexec.exe (PID: 2988)
- chrome.exe (PID: 2376)
- rundll32.exe (PID: 1648)
- msiexec.exe (PID: 2876)
- ManicTime.exe (PID: 1856)
- mscorsvw.exe (PID: 1216)
- mscorsvw.exe (PID: 1348)
- mscorsvw.exe (PID: 1264)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 3092)
- ManicTimeClient.exe (PID: 548)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 4076)
- MsiExec.exe (PID: 4012)
- MsiExec.exe (PID: 3432)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2900)
Creates files in the user directory
- msiexec.exe (PID: 2876)
Creates files in the Windows directory
- ngen.exe (PID: 2548)
- ngen.exe (PID: 2360)
- ngen.exe (PID: 3072)
- ngen.exe (PID: 2604)
- ngen.exe (PID: 2152)
- ngen.exe (PID: 3644)
- ngen.exe (PID: 2520)
- ngen.exe (PID: 3784)
- ngen.exe (PID: 3964)
- ngen.exe (PID: 2592)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 2312)
- ngen.exe (PID: 3048)
- ngen.exe (PID: 2800)
- ngen.exe (PID: 3756)
- ngen.exe (PID: 2216)
- ngen.exe (PID: 408)
- ngen.exe (PID: 364)
- ngen.exe (PID: 2460)
- ngen.exe (PID: 3572)
- ngen.exe (PID: 2244)
- ngen.exe (PID: 560)
- ngen.exe (PID: 3380)
- ngen.exe (PID: 1492)
- ngen.exe (PID: 2452)
- ngen.exe (PID: 2180)
- ngen.exe (PID: 3160)
- ngen.exe (PID: 1000)
- ngen.exe (PID: 2352)
- ngen.exe (PID: 3744)
- ngen.exe (PID: 3336)
- ngen.exe (PID: 3540)
- ngen.exe (PID: 2596)
- ngen.exe (PID: 2888)
- ngen.exe (PID: 3380)
- ngen.exe (PID: 2712)
- ngen.exe (PID: 2208)
- ngen.exe (PID: 304)
- ngen.exe (PID: 3628)
- ngen.exe (PID: 3180)
- ngen.exe (PID: 2332)
- ngen.exe (PID: 3636)
- ngen.exe (PID: 2548)
- ngen.exe (PID: 2556)
- ngen.exe (PID: 2420)
- ngen.exe (PID: 2428)
- ngen.exe (PID: 408)
- ngen.exe (PID: 3232)
- ngen.exe (PID: 780)
- ngen.exe (PID: 3644)
- ngen.exe (PID: 2364)
- ngen.exe (PID: 3540)
- ngen.exe (PID: 1644)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 1968)
- ngen.exe (PID: 3868)
- ngen.exe (PID: 2076)
- ngen.exe (PID: 2908)
- ngen.exe (PID: 1520)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 2616)
- ngen.exe (PID: 3676)
- ngen.exe (PID: 3868)
- ngen.exe (PID: 3972)
- ngen.exe (PID: 2884)
- ngen.exe (PID: 3760)
- ngen.exe (PID: 3920)
- ngen.exe (PID: 2416)
- ngen.exe (PID: 3876)
- ngen.exe (PID: 1784)
- ngen.exe (PID: 1812)
- ngen.exe (PID: 564)
- ngen.exe (PID: 2952)
- ngen.exe (PID: 3180)
- ngen.exe (PID: 2364)
- ngen.exe (PID: 2064)
- ngen.exe (PID: 1156)
- ngen.exe (PID: 3296)
- ngen.exe (PID: 360)
- ngen.exe (PID: 3896)
- ngen.exe (PID: 3400)
- ngen.exe (PID: 2592)
- ngen.exe (PID: 2888)
- ngen.exe (PID: 872)
- ngen.exe (PID: 3000)
- ngen.exe (PID: 2976)
- ngen.exe (PID: 3096)
- ngen.exe (PID: 2520)
- ngen.exe (PID: 1812)
- ngen.exe (PID: 1304)
- ngen.exe (PID: 2852)
- ngen.exe (PID: 2716)
- ngen.exe (PID: 2404)
- ngen.exe (PID: 3596)
- ngen.exe (PID: 916)
- ngen.exe (PID: 3336)
- ngen.exe (PID: 2992)
- ngen.exe (PID: 3136)
- ngen.exe (PID: 1428)
- ngen.exe (PID: 2532)
- ngen.exe (PID: 3932)
- ngen.exe (PID: 3852)
- ngen.exe (PID: 1032)
- ngen.exe (PID: 3196)
- ngen.exe (PID: 1632)
- ngen.exe (PID: 2512)
- ngen.exe (PID: 3220)
- ngen.exe (PID: 560)
- ngen.exe (PID: 3760)
- ngen.exe (PID: 1188)
- ngen.exe (PID: 3204)
- ngen.exe (PID: 3660)
- ngen.exe (PID: 2716)
- ngen.exe (PID: 2604)
- ngen.exe (PID: 316)
- ngen.exe (PID: 3824)
- ngen.exe (PID: 2628)
- ngen.exe (PID: 1968)
- ngen.exe (PID: 1440)
- ngen.exe (PID: 2420)
- ngen.exe (PID: 2484)
- ngen.exe (PID: 1720)
- ngen.exe (PID: 2056)
- ngen.exe (PID: 3136)
- ngen.exe (PID: 1736)
- ngen.exe (PID: 888)
- ngen.exe (PID: 3632)
- ngen.exe (PID: 3316)
- ngen.exe (PID: 3312)
- ngen.exe (PID: 3888)
- ngen.exe (PID: 4088)
- ngen.exe (PID: 564)
- ngen.exe (PID: 2304)
- ngen.exe (PID: 1484)
- ngen.exe (PID: 3100)
- ngen.exe (PID: 2412)
- ngen.exe (PID: 2960)
- ngen.exe (PID: 2760)
- ngen.exe (PID: 1520)
- ngen.exe (PID: 3484)
- ngen.exe (PID: 4000)
- ngen.exe (PID: 2952)
- ngen.exe (PID: 996)
- ngen.exe (PID: 3320)
- ngen.exe (PID: 3284)
- ngen.exe (PID: 3232)
- ngen.exe (PID: 1304)
- ngen.exe (PID: 3680)
- ngen.exe (PID: 3012)
- ngen.exe (PID: 3676)
- ngen.exe (PID: 2396)
- ngen.exe (PID: 3584)
- ngen.exe (PID: 2936)
- ngen.exe (PID: 3104)
- ngen.exe (PID: 2508)
- ngen.exe (PID: 3904)
- ngen.exe (PID: 3604)
- ngen.exe (PID: 2428)
- ngen.exe (PID: 1264)
- ngen.exe (PID: 2660)
- ngen.exe (PID: 3912)
- ngen.exe (PID: 2672)
- ngen.exe (PID: 3296)
- ngen.exe (PID: 552)
- mscorsvw.exe (PID: 1216)
- mscorsvw.exe (PID: 1348)
- mscorsvw.exe (PID: 4056)
- mscorsvw.exe (PID: 3348)
- mscorsvw.exe (PID: 1264)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 3092)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 3880)
- mscorsvw.exe (PID: 3040)
- mscorsvw.exe (PID: 2528)
- mscorsvw.exe (PID: 3364)
- mscorsvw.exe (PID: 3584)
- mscorsvw.exe (PID: 3088)
- mscorsvw.exe (PID: 2476)
- mscorsvw.exe (PID: 3408)
- mscorsvw.exe (PID: 1744)
- mscorsvw.exe (PID: 776)
- mscorsvw.exe (PID: 3596)
- mscorsvw.exe (PID: 2404)
- mscorsvw.exe (PID: 1816)
- mscorsvw.exe (PID: 2640)
- mscorsvw.exe (PID: 3212)
- mscorsvw.exe (PID: 2552)
- mscorsvw.exe (PID: 2252)
- mscorsvw.exe (PID: 2688)
- mscorsvw.exe (PID: 3252)
- mscorsvw.exe (PID: 876)
- mscorsvw.exe (PID: 1080)
- mscorsvw.exe (PID: 3792)
- mscorsvw.exe (PID: 1796)
- mscorsvw.exe (PID: 2304)
Removes files from Windows directory
- mscorsvw.exe (PID: 1216)
- mscorsvw.exe (PID: 1348)
- mscorsvw.exe (PID: 1264)
- mscorsvw.exe (PID: 4056)
- mscorsvw.exe (PID: 3348)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 3584)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 3880)
- mscorsvw.exe (PID: 3040)
- mscorsvw.exe (PID: 2528)
- mscorsvw.exe (PID: 3364)
- mscorsvw.exe (PID: 3092)
- mscorsvw.exe (PID: 776)
- mscorsvw.exe (PID: 2476)
- mscorsvw.exe (PID: 3596)
- mscorsvw.exe (PID: 3408)
- mscorsvw.exe (PID: 1744)
- mscorsvw.exe (PID: 3088)
- mscorsvw.exe (PID: 2404)
- mscorsvw.exe (PID: 1816)
- mscorsvw.exe (PID: 2552)
- mscorsvw.exe (PID: 2640)
- mscorsvw.exe (PID: 3212)
- mscorsvw.exe (PID: 876)
- mscorsvw.exe (PID: 3252)
- mscorsvw.exe (PID: 2688)
- mscorsvw.exe (PID: 2252)
- mscorsvw.exe (PID: 1080)
- mscorsvw.exe (PID: 3792)
- mscorsvw.exe (PID: 1796)
- mscorsvw.exe (PID: 2304)
Creates files in the program directory
- mscorsvw.exe (PID: 3276)
- ManicTime.exe (PID: 1856)
- mscorsvw.exe (PID: 2584)
Reads Environment values
- ManicTimeClient.exe (PID: 548)
INFO
Application launched itself
- chrome.exe (PID: 2900)
- msiexec.exe (PID: 2876)
Reads settings of System Certificates
- chrome.exe (PID: 2900)
- ManicTime.exe (PID: 1856)
Reads Internet Cache Settings
- chrome.exe (PID: 2900)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4076)
- MsiExec.exe (PID: 4012)
- MsiExec.exe (PID: 3432)
Changes settings of System certificates
- chrome.exe (PID: 2900)
Creates a software uninstall entry
- msiexec.exe (PID: 2876)
Creates files in the program directory
- msiexec.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
474
Monitored processes
253
Malicious processes
61
Suspicious processes
170
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\Microsoft.IdentityModel.Logging.dll" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 316 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\Plugins\Packages\ManicTime.DocumentTracker.Opera\Lib\Plugins.Common.dll" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,4119292633824799482,11289299140632425670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8525902836849934535 --mojo-platform-channel-handle=3840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 360 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\System.Runtime.InteropServices.RuntimeInformation.dll" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 364 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\ManicTimeProcessMonitor.exe" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 408 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\ManicTimeClient.exe" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 408 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\System.Diagnostics.Tracing.dll" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
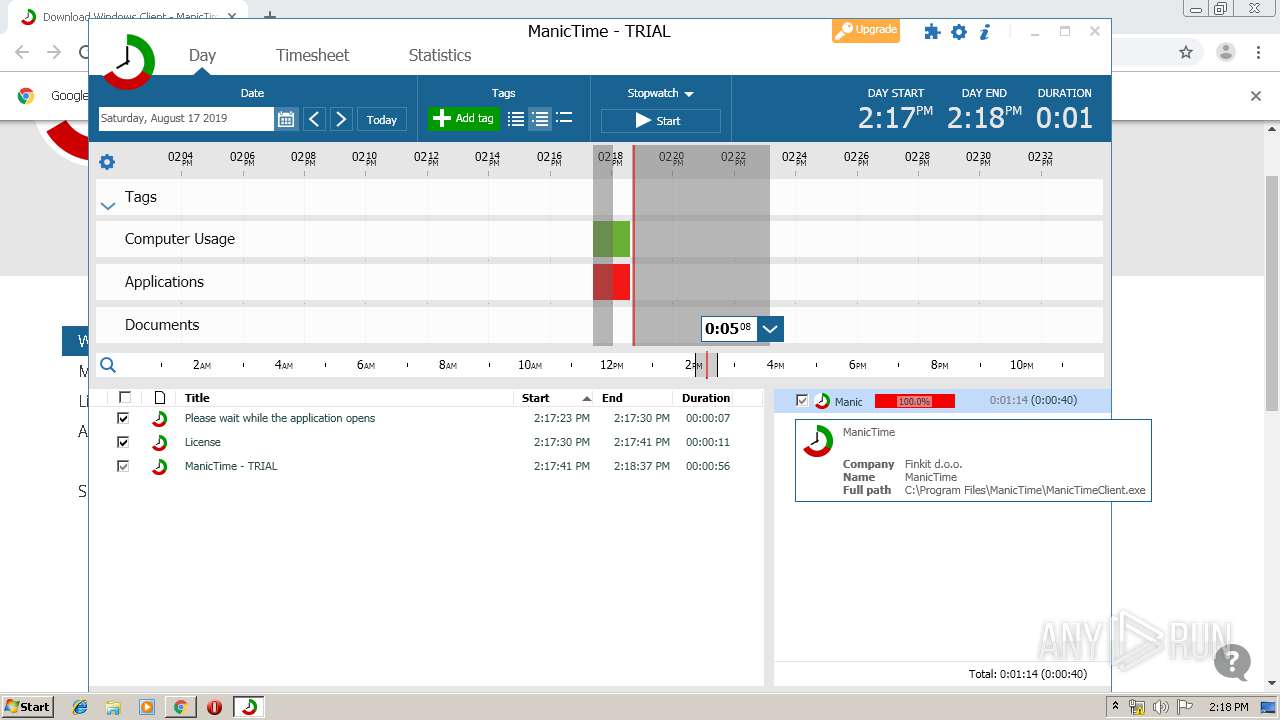
| 548 | "C:\Program Files\ManicTime\ManicTimeClient.exe" /minimized /messageKey:"b04a36a9-05cd-48f1-9c6c-0a26154d8075" | C:\Program Files\ManicTime\ManicTimeClient.exe | ManicTime.exe | ||||||||||||
User: admin Company: Finkit d.o.o. Integrity Level: MEDIUM Description: ManicTime Client Exit code: 0 Version: 4.3.4.0 Modules
| |||||||||||||||
| 552 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\Plugins\Packages\ManicTime.ScreenshotStorage.LocalDisk\Lib\Shared.ScreenshotStorage.LocalDisk.dll" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 560 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\ManicTime\SQLitePCLRaw.core.dll" /queue:1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
6 701
Read events
3 026
Write events
3 637
Delete events
38
Modification events
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2900-13210521324054125 |
Value: 259 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
364
Suspicious files
32
Text files
647
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\138e1924-9954-4af1-af8f-7d15e44c86c3.tmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169e67.TMP | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169eb5.TMP | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF16a01d.TMP | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
31
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2376 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
1856 | ManicTime.exe | GET | 200 | 168.62.48.183:80 | http://services.manictime.com/Versions/GetLatestVersionNumber?currentVersion=4.3.4.0&license=AA%2BR%2BZiuC3j9EkGxRKlOacRlXZeTCMO26lrX6YTmKMjKwbvrqZ8%2FkitM16%2FiM0Y2nlOBDg%3D%3D&operatingSystemVersion=6.1.7601.65536&platform=X86&dotNetVersions=2.0.50727.5420%2C2%3B3.0.30729.5420%2C2%3B3.5.30729.5420%2C1%3BClient%3A4.7.03062%2C0%3BFull%3A4.7.03062%2C0%3BClient%3A4.0.0.0%2C0&systemCulture=en-US&includeMessage=False | US | text | 164 b | suspicious |
2376 | chrome.exe | GET | 200 | 173.194.150.139:80 | http://r5---sn-f5f7ln7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.217.54&mm=28&mn=sn-f5f7ln7s&ms=nvh&mt=1566046984&mv=u&mvi=4&pl=21&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2376 | chrome.exe | 216.58.207.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 168.62.48.183:443 | www.manictime.com | Microsoft Corporation | US | whitelisted |
2376 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 104.17.31.92:443 | widget.uservoice.com | Cloudflare Inc | US | shared |
2376 | chrome.exe | 216.58.208.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2376 | chrome.exe | 74.125.133.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.manictime.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
widget.uservoice.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |
www.google.pl |
| whitelisted |