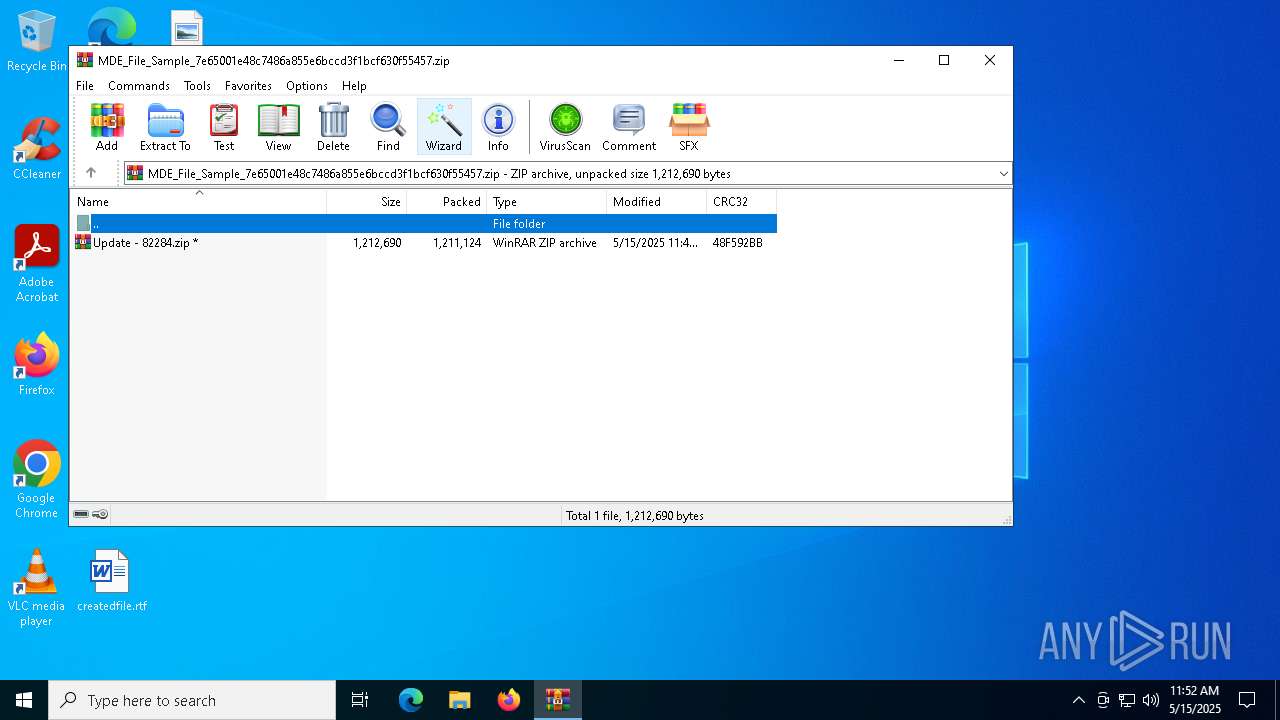
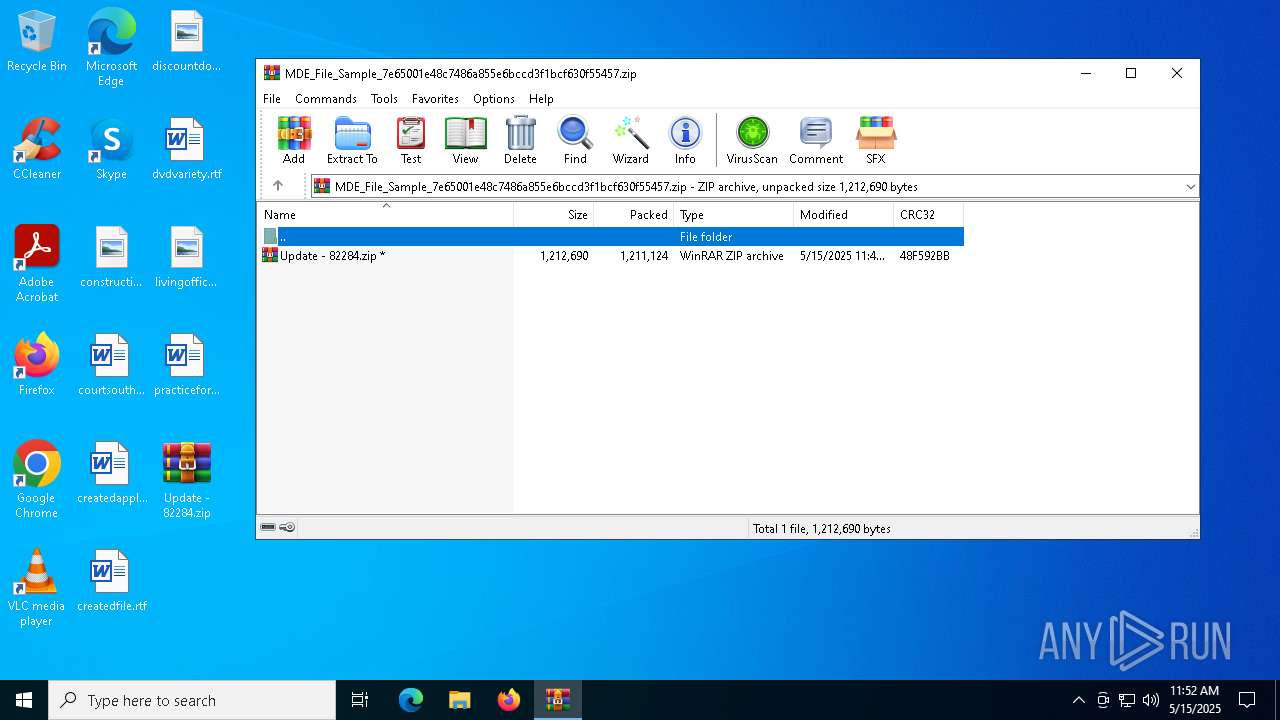
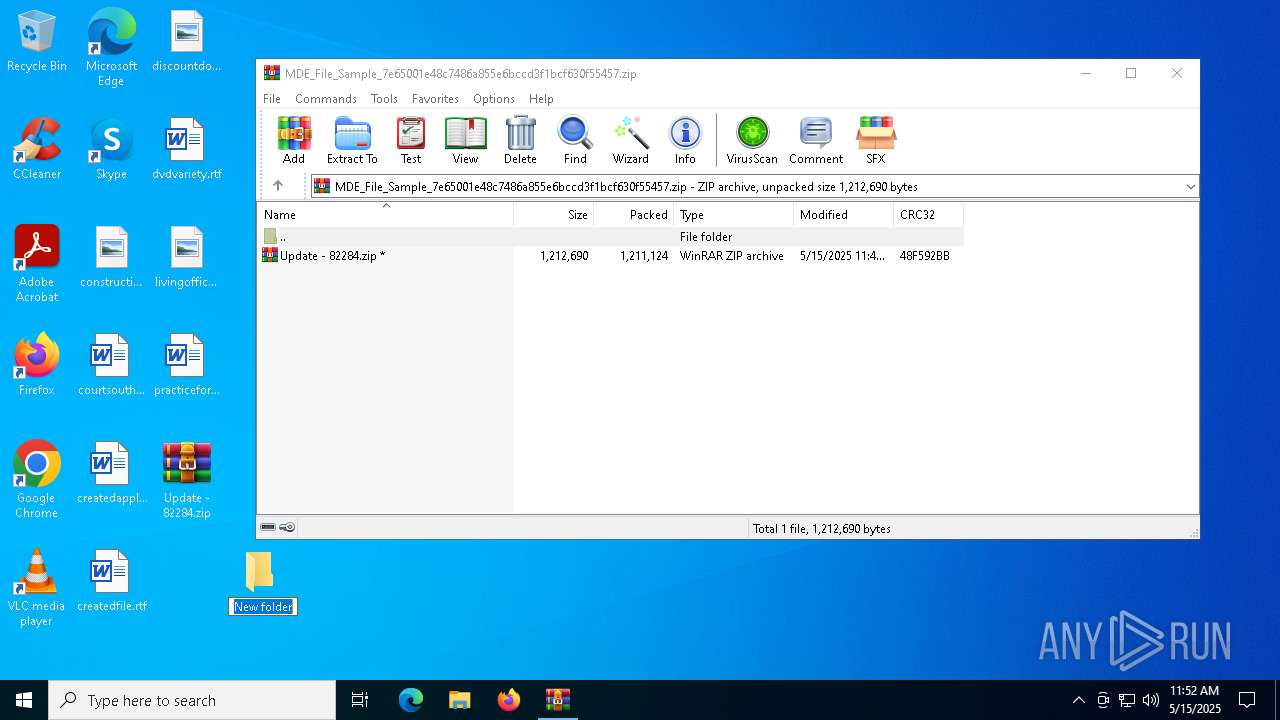
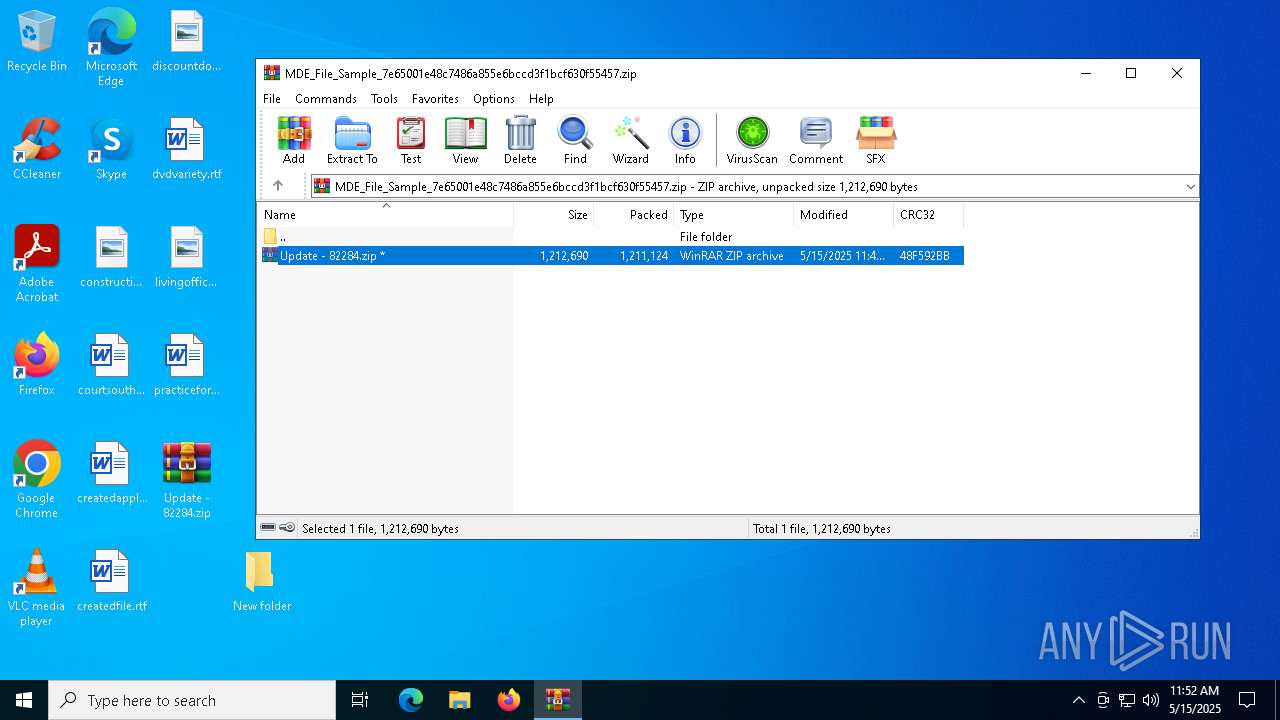
| File name: | MDE_File_Sample_7e65001e48c7486a855e6bccd3f1bcf630f55457.zip |
| Full analysis: | https://app.any.run/tasks/098859e7-6282-4d71-85cd-5fafdcf522f8 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 11:51:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
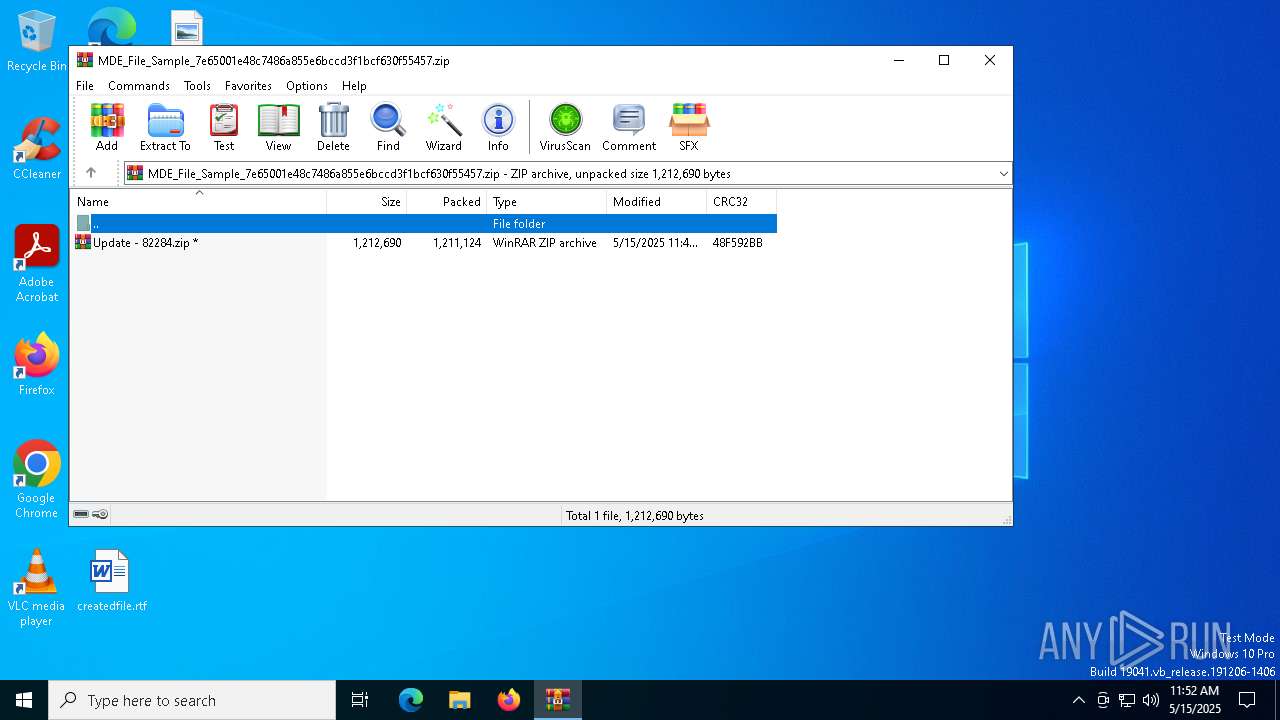
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 1771F5E8BF82EED457E5986343B9DC22 |
| SHA1: | D8E8FB5688F2D9EE3AAE4212CCE6FEF7EE0CA793 |
| SHA256: | D74082F0B431625918E0208102E371929970D158C2283262BFD2131815743615 |
| SSDEEP: | 49152:KwngtmnGUaWlUYsqY+2AmfI+Wf+I6llLjufoiYRycKLS/NTHnwf+A7pyazVYinNX:Kwng8GUWZQ2dM6loAiYRycKLSlTQf+QL |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 4024)
- wscript.exe (PID: 5640)
- wscript.exe (PID: 4812)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 4024)
- wscript.exe (PID: 5640)
- wscript.exe (PID: 4812)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 4024)
- wscript.exe (PID: 5640)
- wscript.exe (PID: 4812)
SUSPICIOUS
No suspicious indicators.INFO
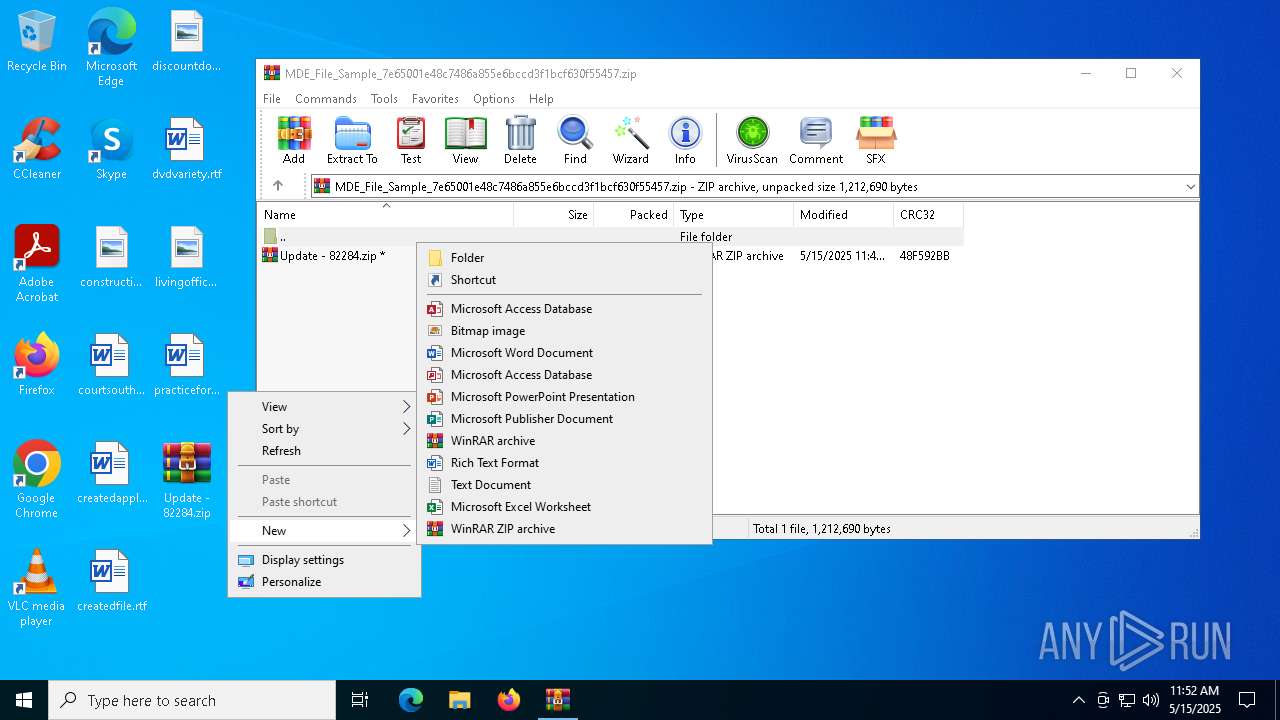
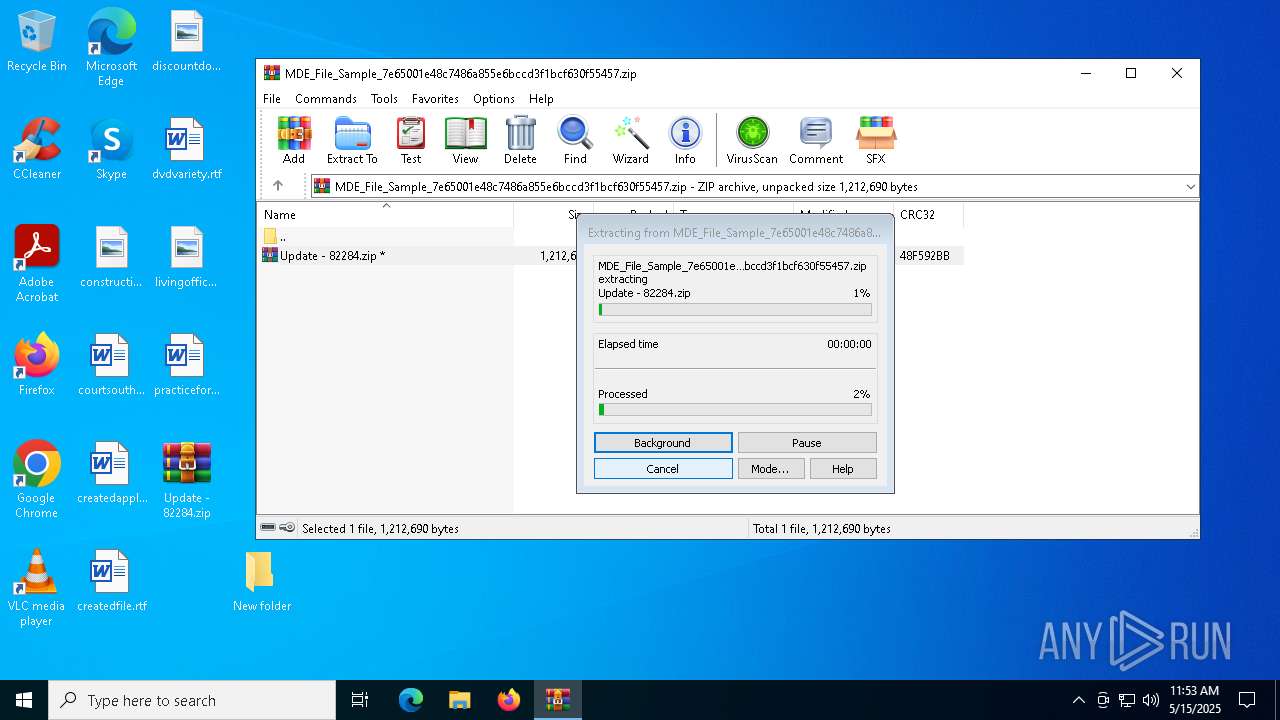
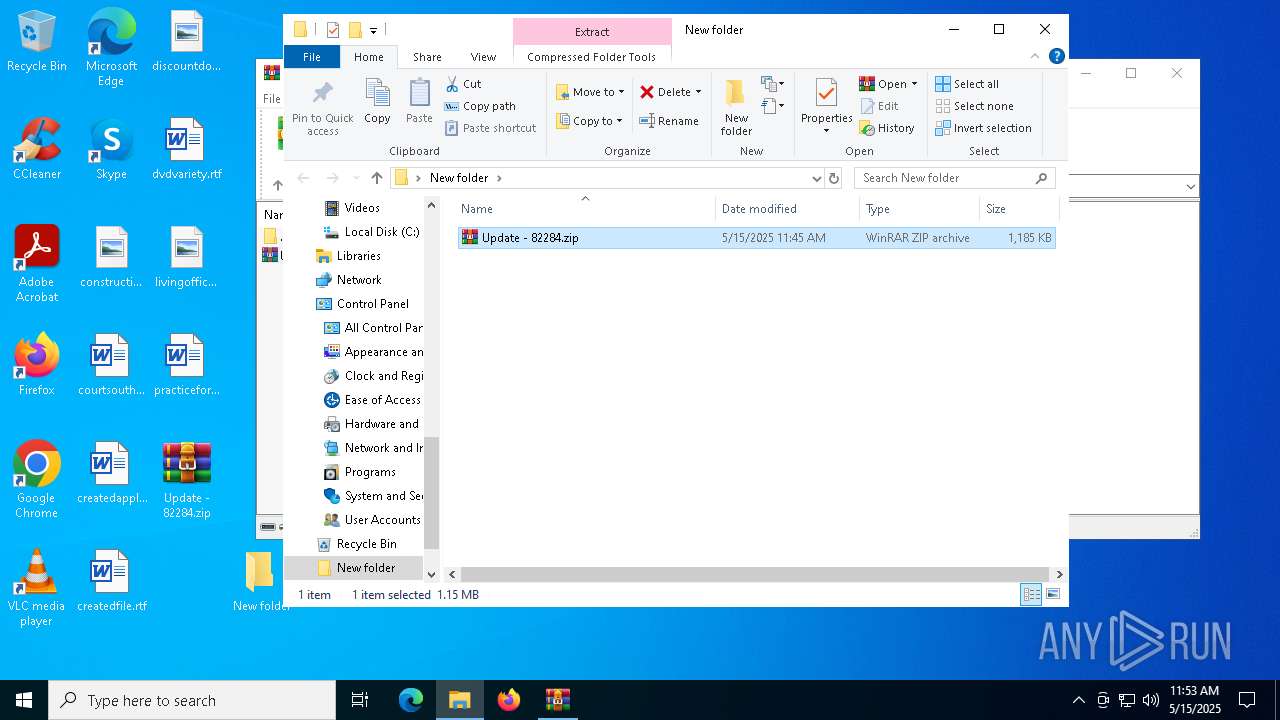
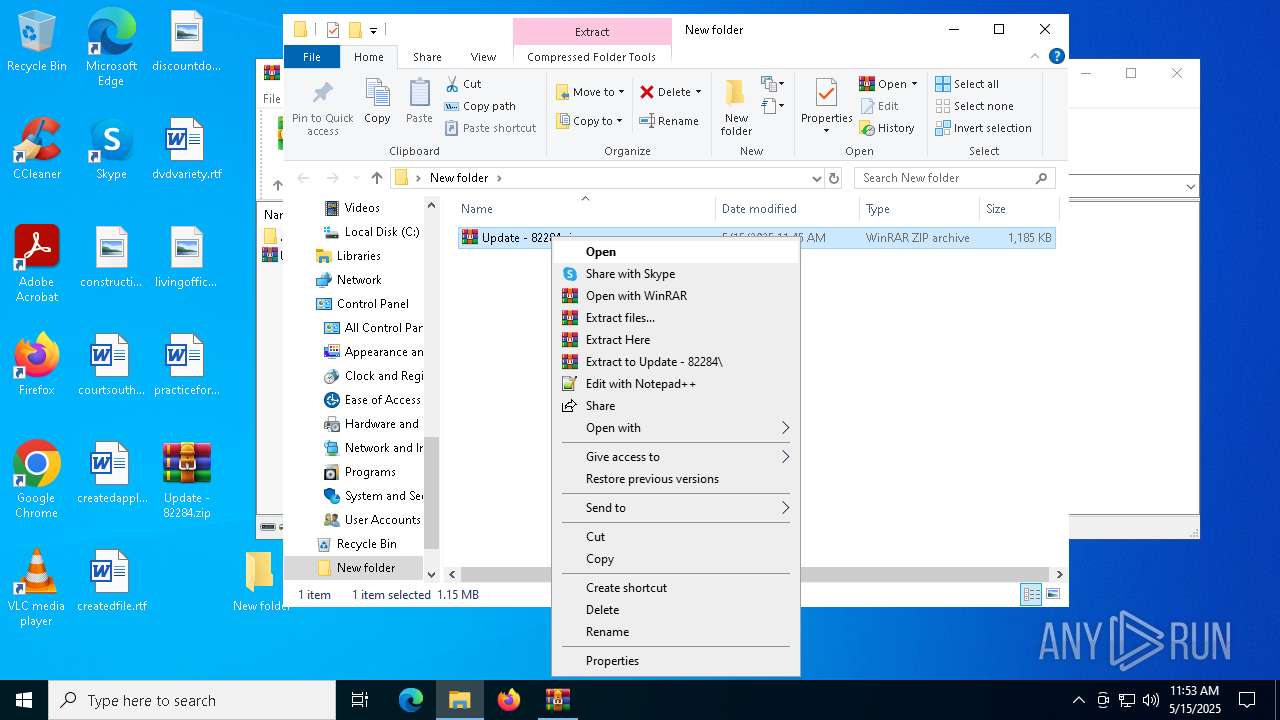
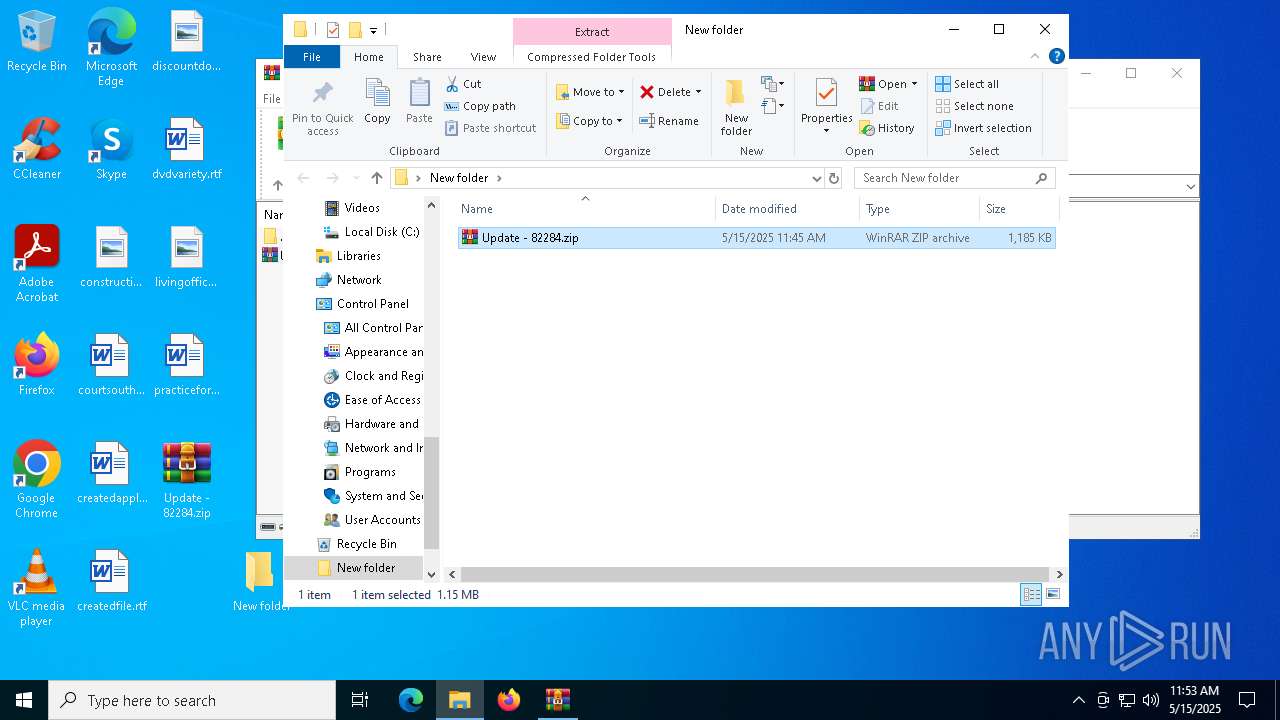
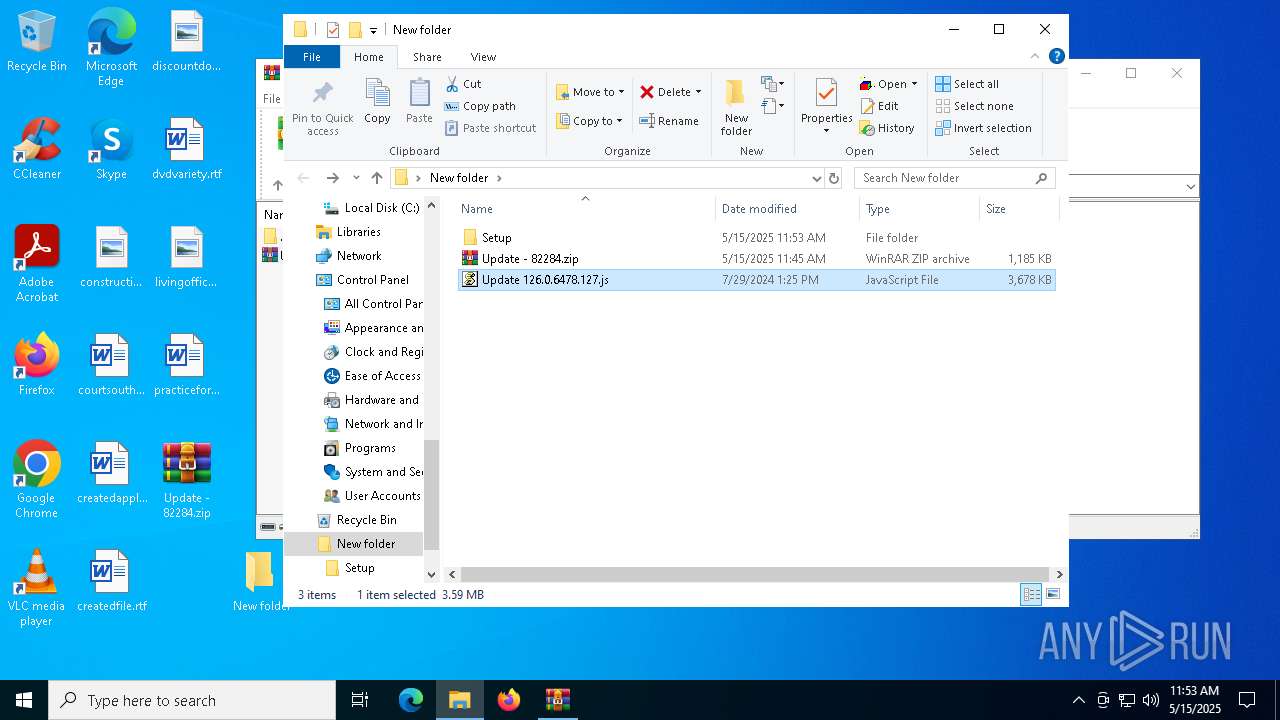
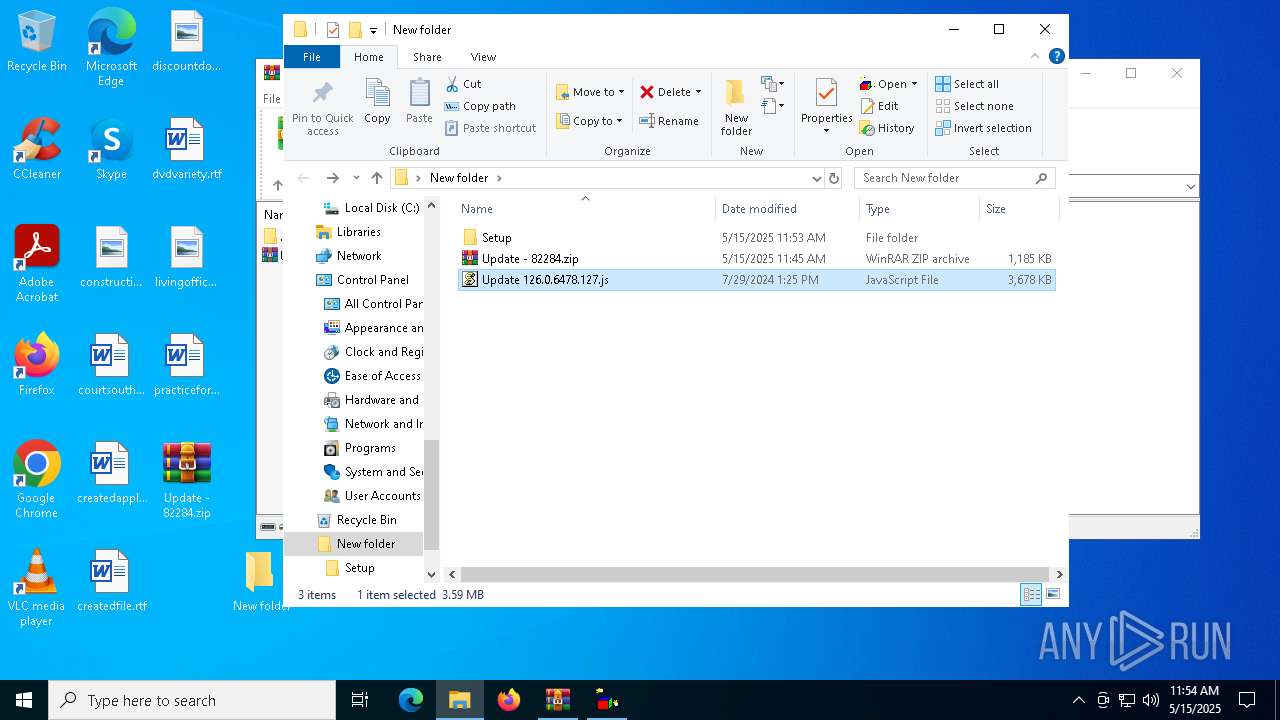
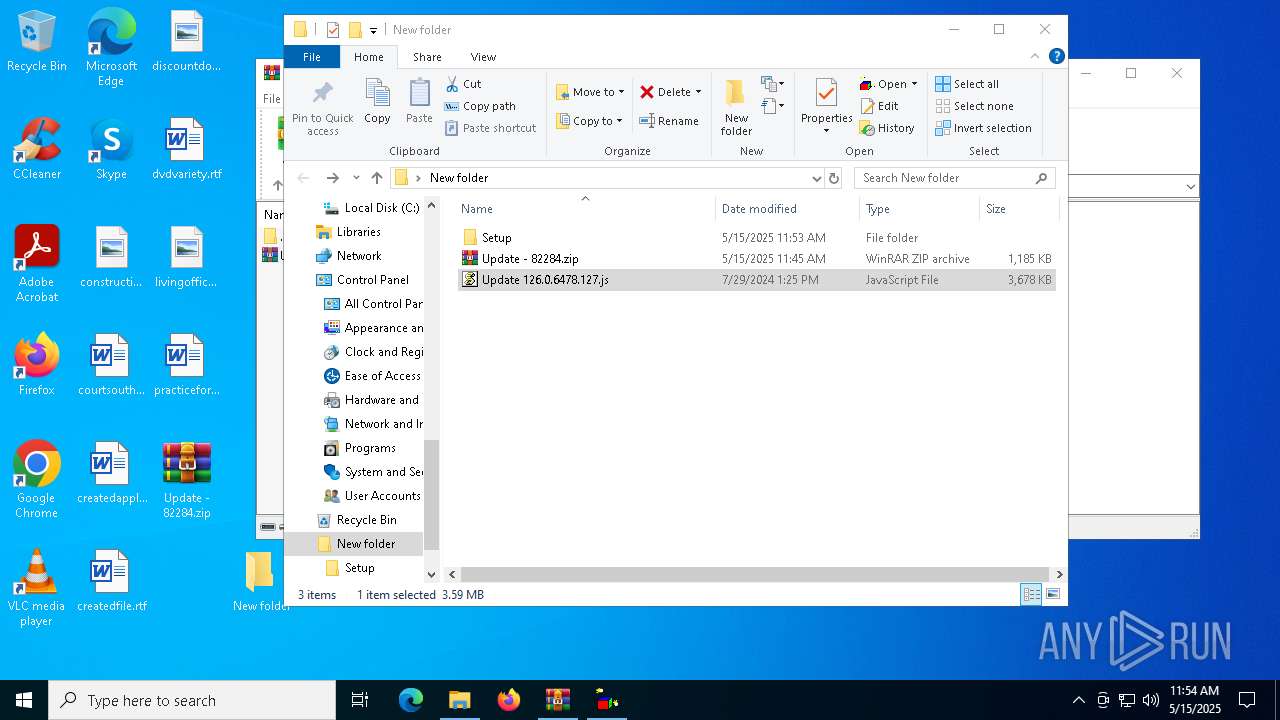
Manual execution by a user
- WinRAR.exe (PID: 7392)
- wscript.exe (PID: 4024)
- wscript.exe (PID: 5640)
- wscript.exe (PID: 4812)
Reads the software policy settings
- slui.exe (PID: 7564)
- slui.exe (PID: 7252)
Checks proxy server information
- wscript.exe (PID: 4024)
- wscript.exe (PID: 5640)
- slui.exe (PID: 7252)
- wscript.exe (PID: 4812)
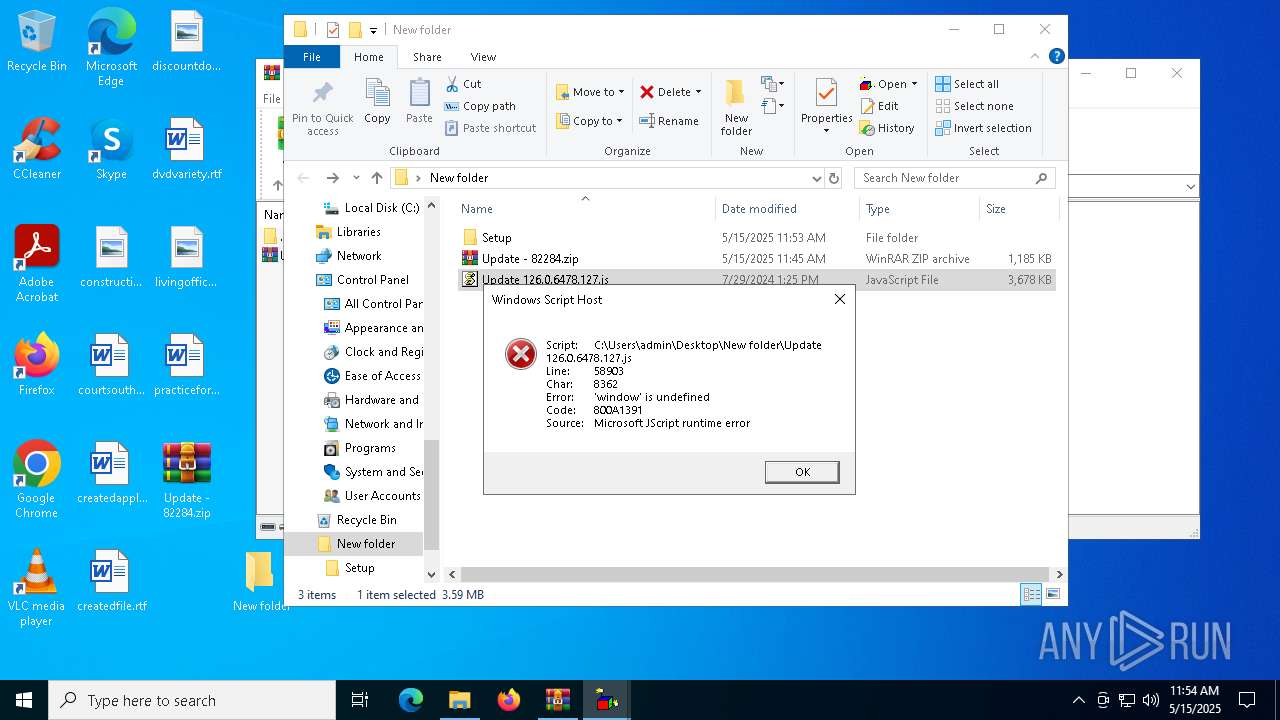
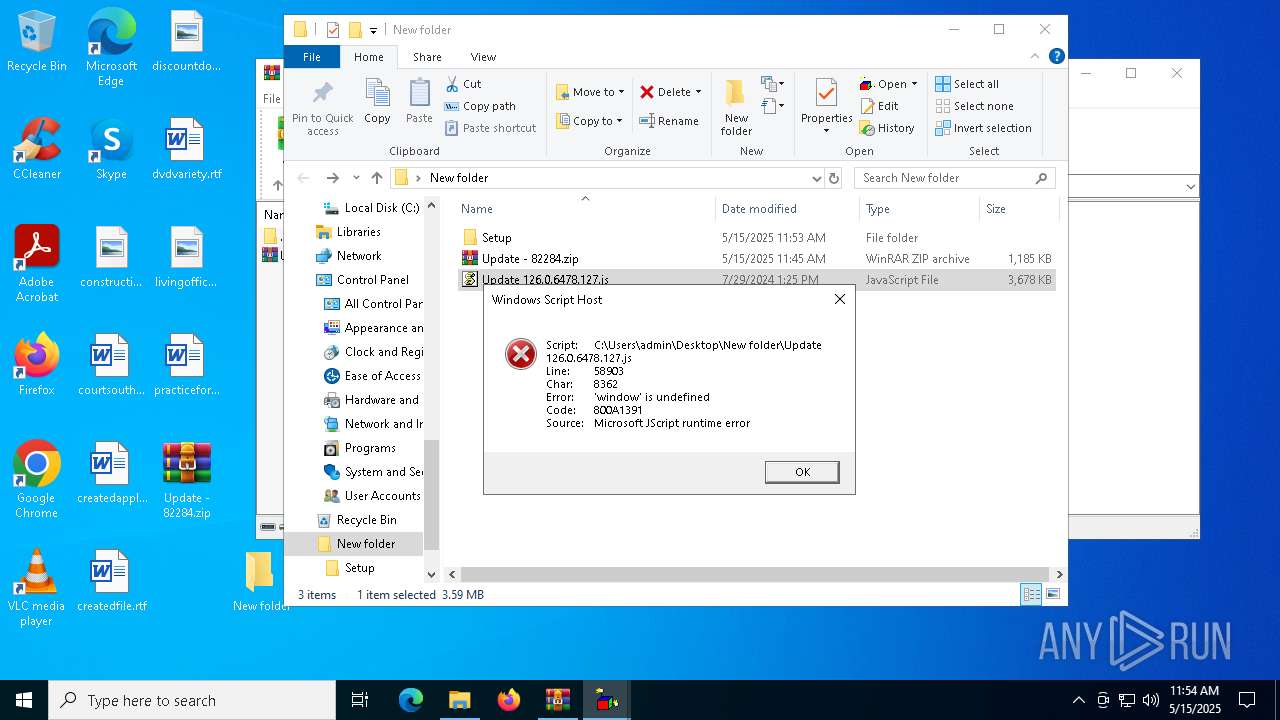
JScript runtime error (SCRIPT)
- wscript.exe (PID: 4024)
- wscript.exe (PID: 5640)
- wscript.exe (PID: 4812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
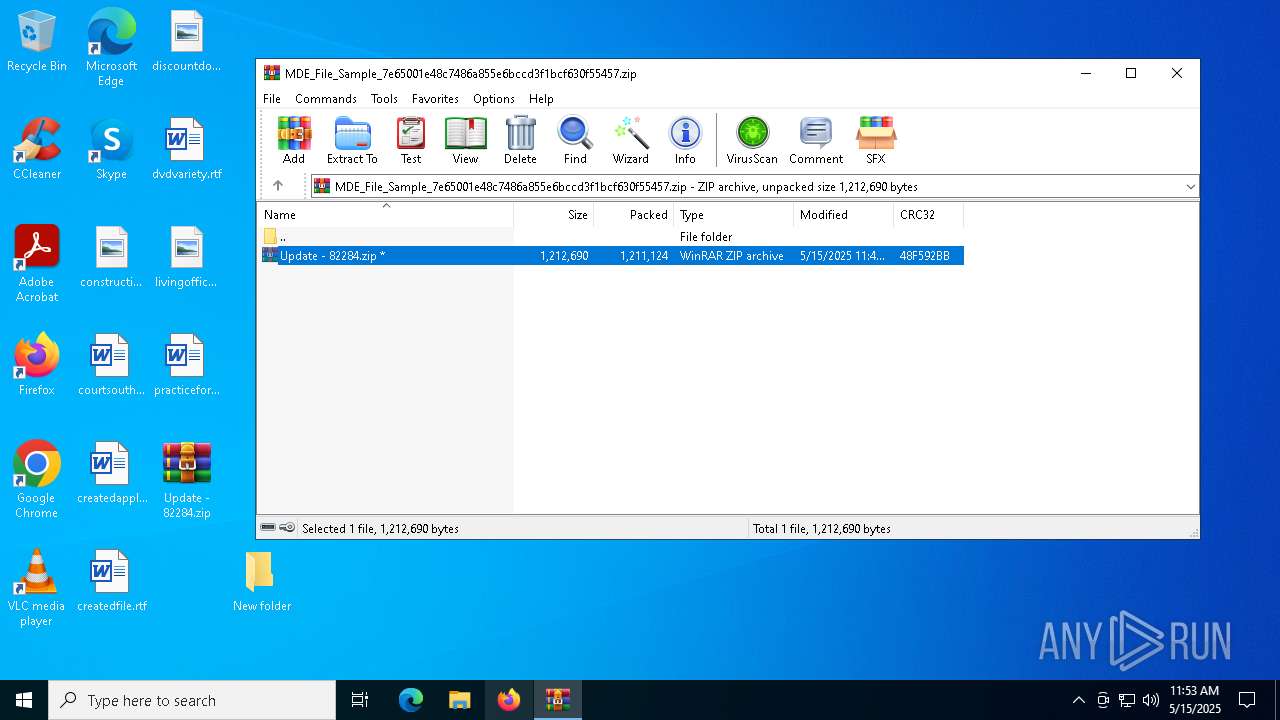
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:15 11:45:44 |
| ZipCRC: | 0x48f592bb |
| ZipCompressedSize: | 1211124 |
| ZipUncompressedSize: | 1212690 |
| ZipFileName: | Update - 82284.zip |
Total processes
138
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1760 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
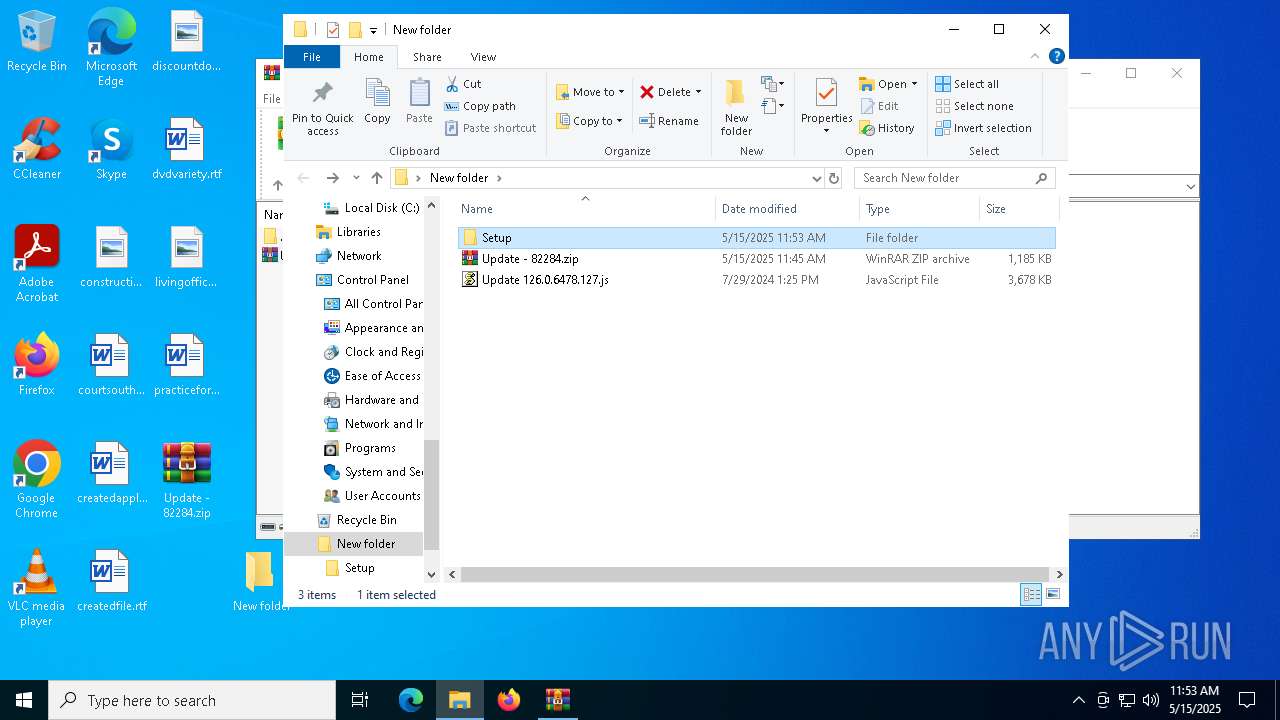
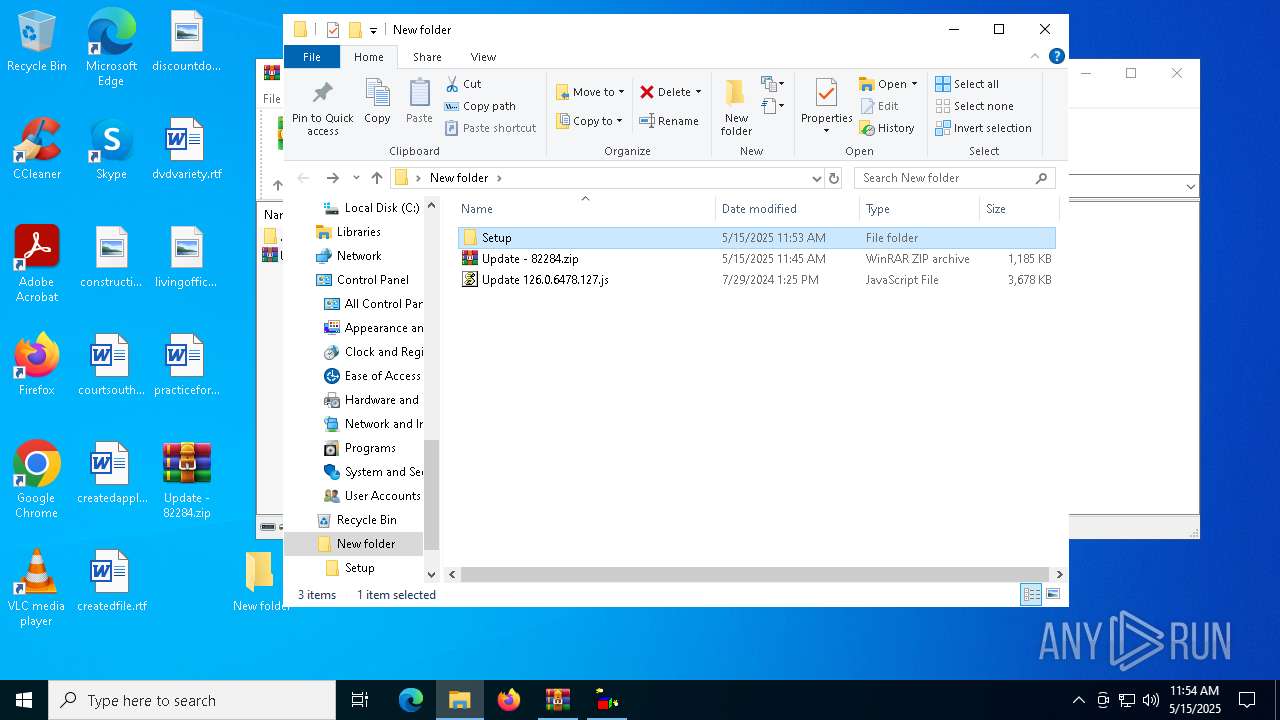
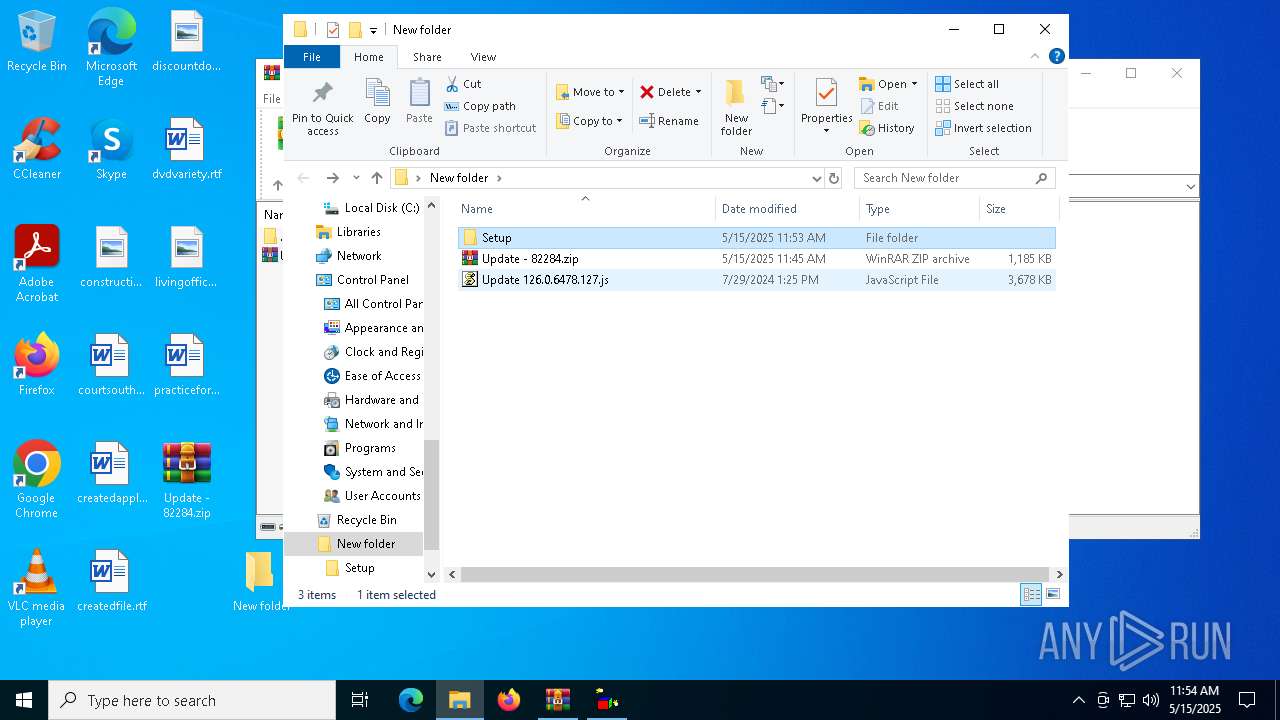
| 4024 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\New folder\Update 126.0.6478.127.js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4812 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\New folder\Update 126.0.6478.127.js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5640 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\New folder\Update 126.0.6478.127.js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7252 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
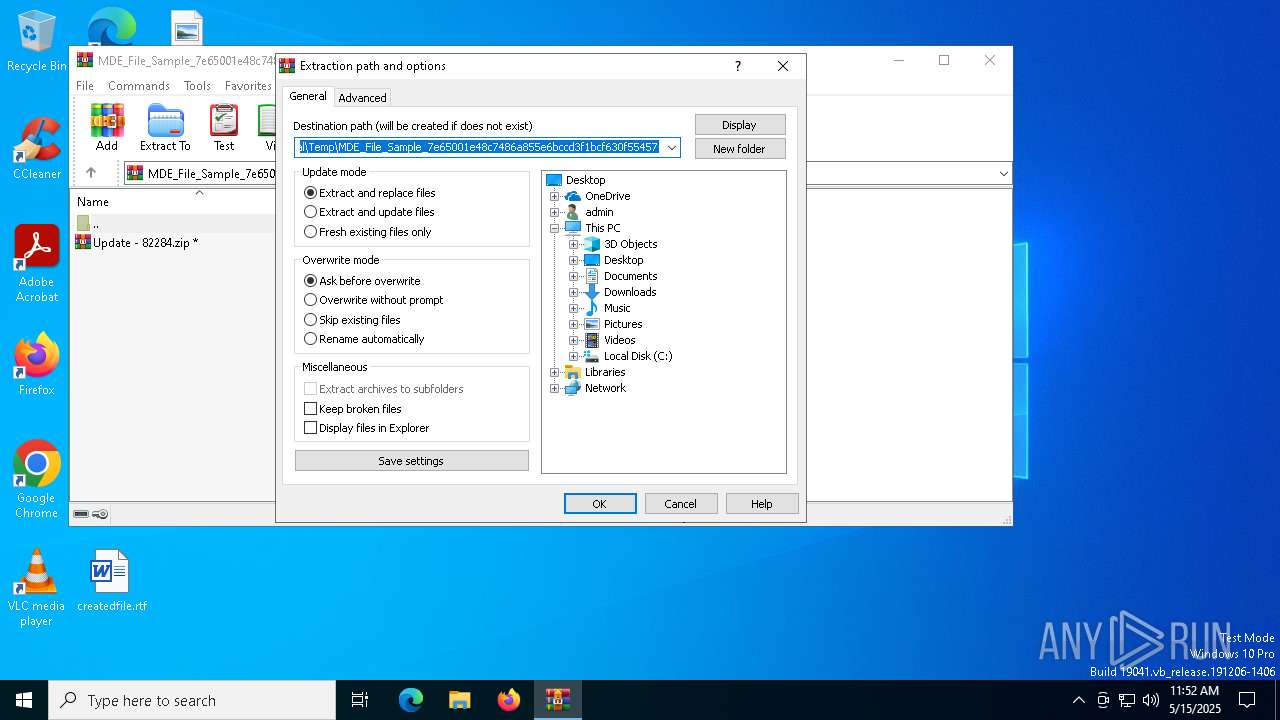
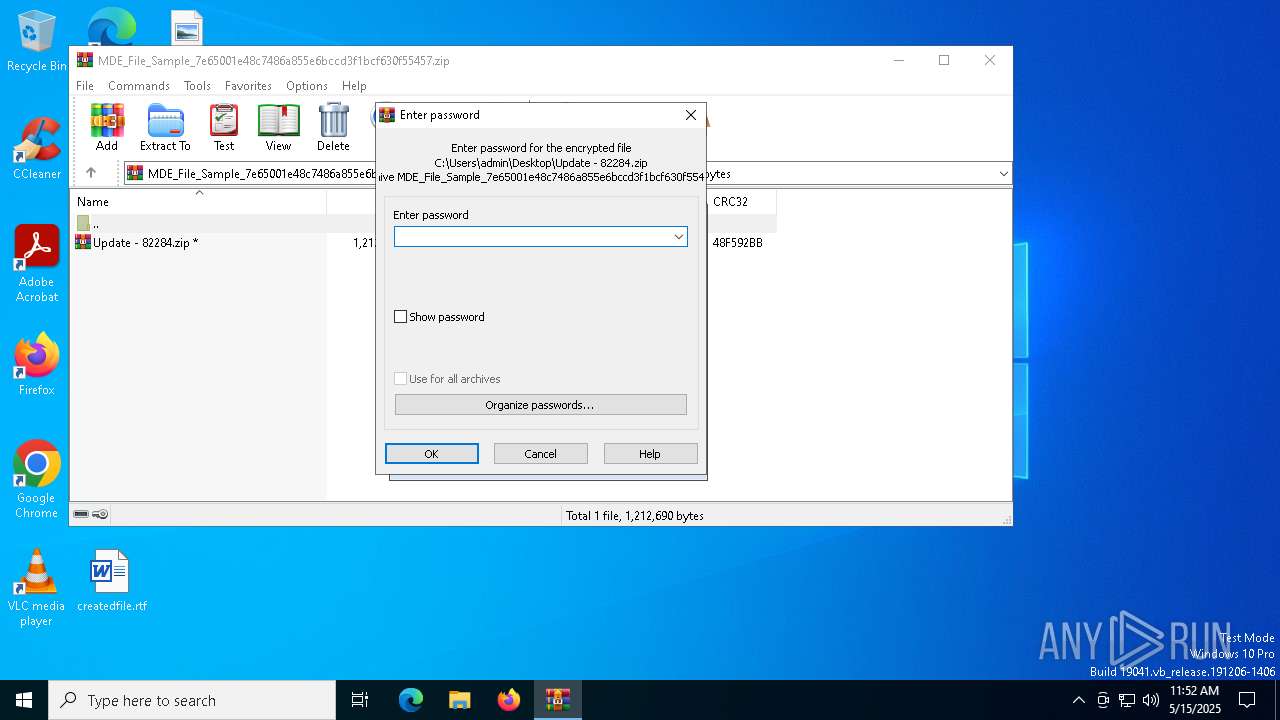
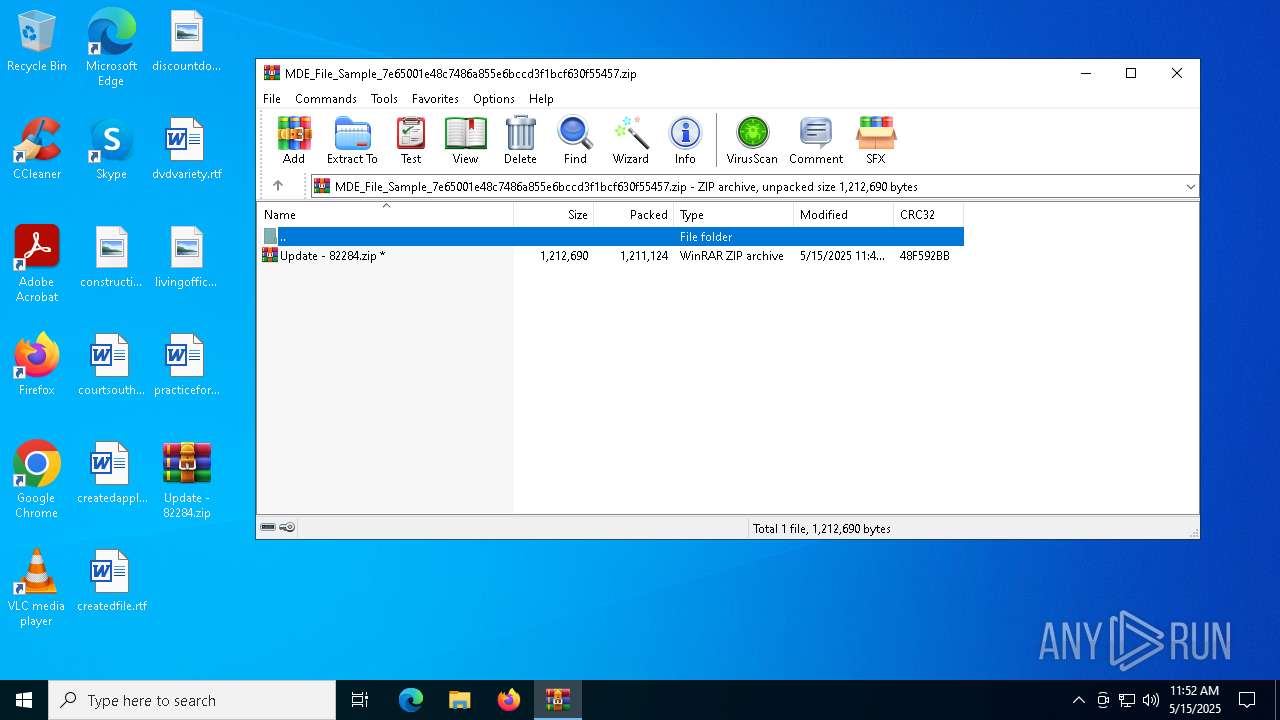
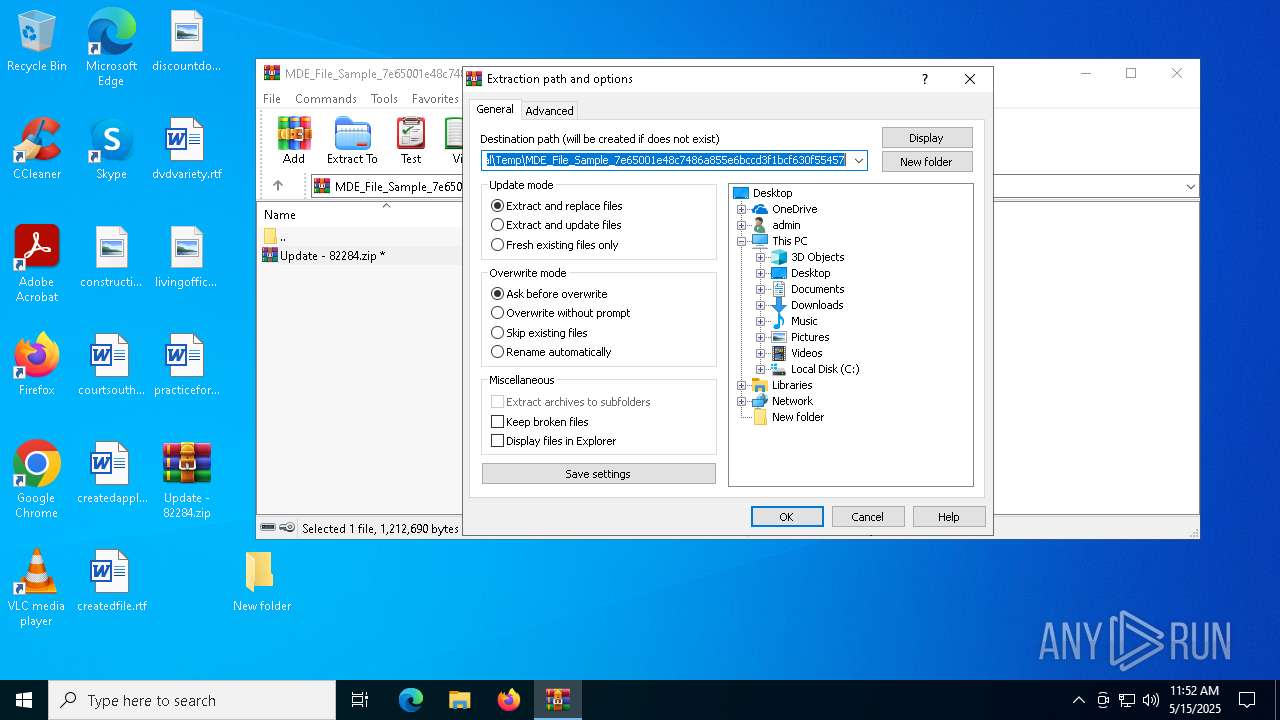
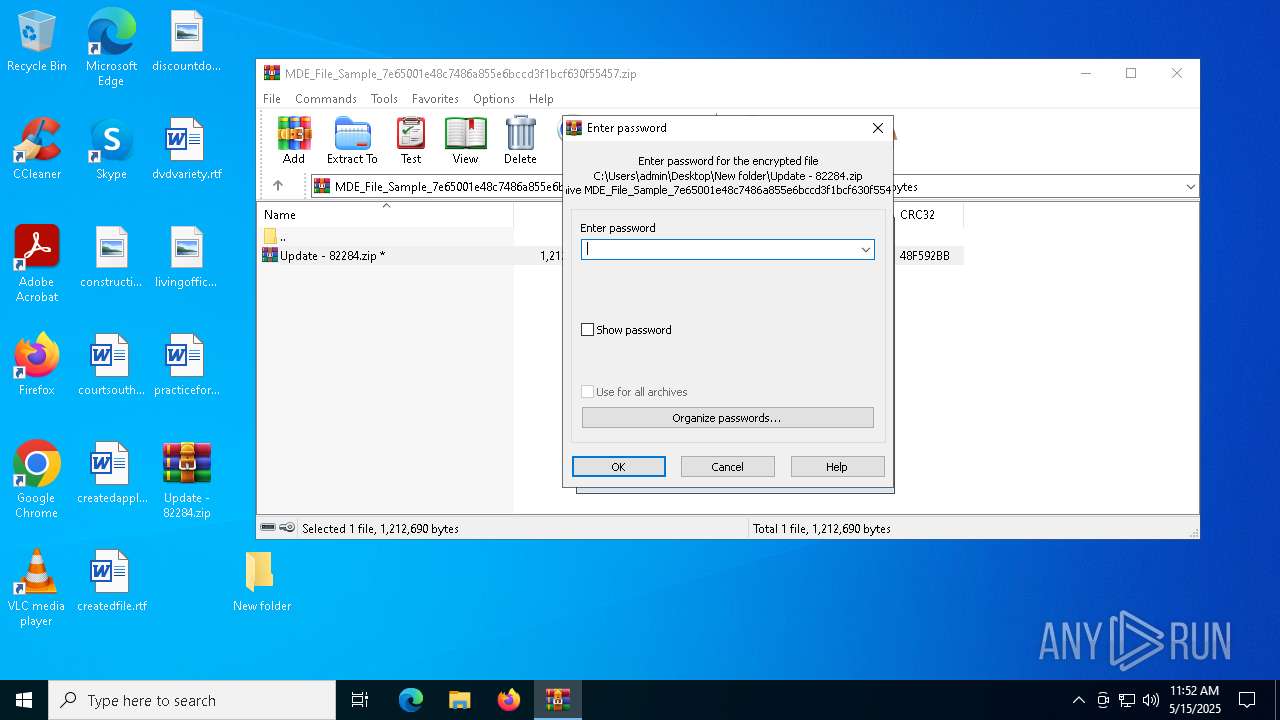
| 7392 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\New folder\Update - 82284.zip" "C:\Users\admin\Desktop\New folder\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7404 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\MDE_File_Sample_7e65001e48c7486a855e6bccd3f1bcf630f55457.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7532 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7564 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 421
Read events
5 365
Write events
31
Delete events
25
Modification events
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MDE_File_Sample_7e65001e48c7486a855e6bccd3f1bcf630f55457.zip | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
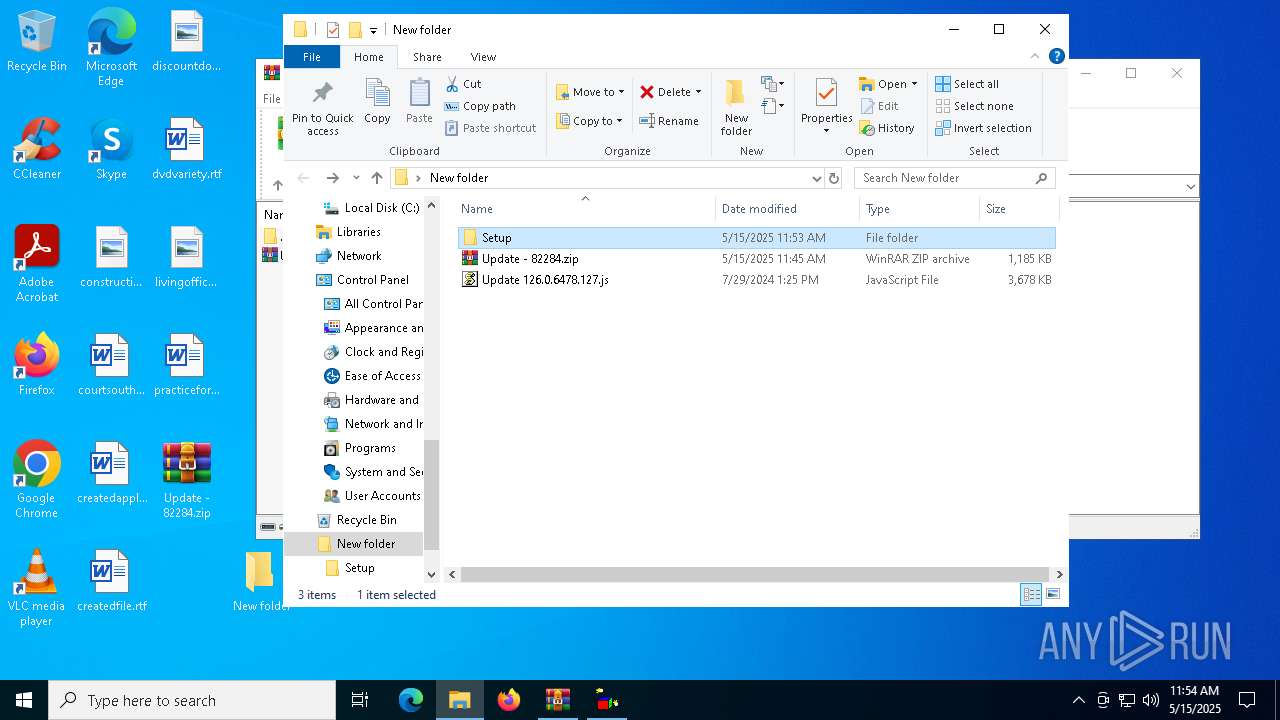
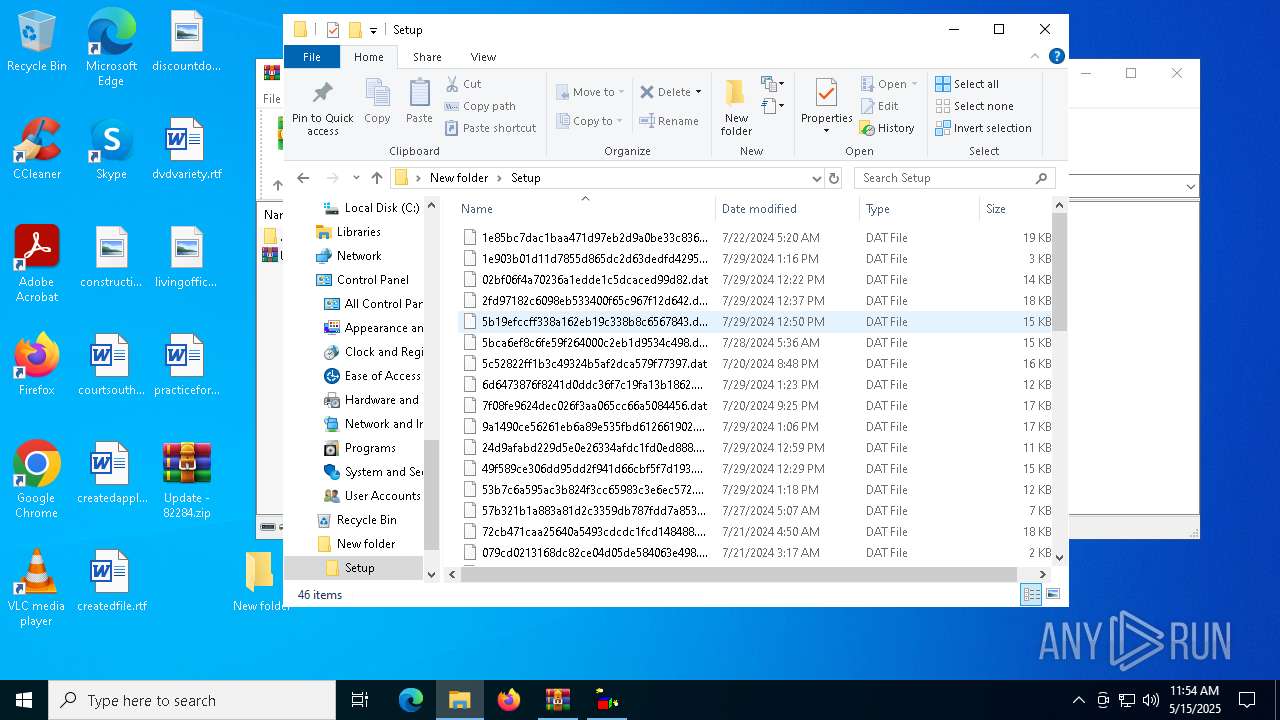
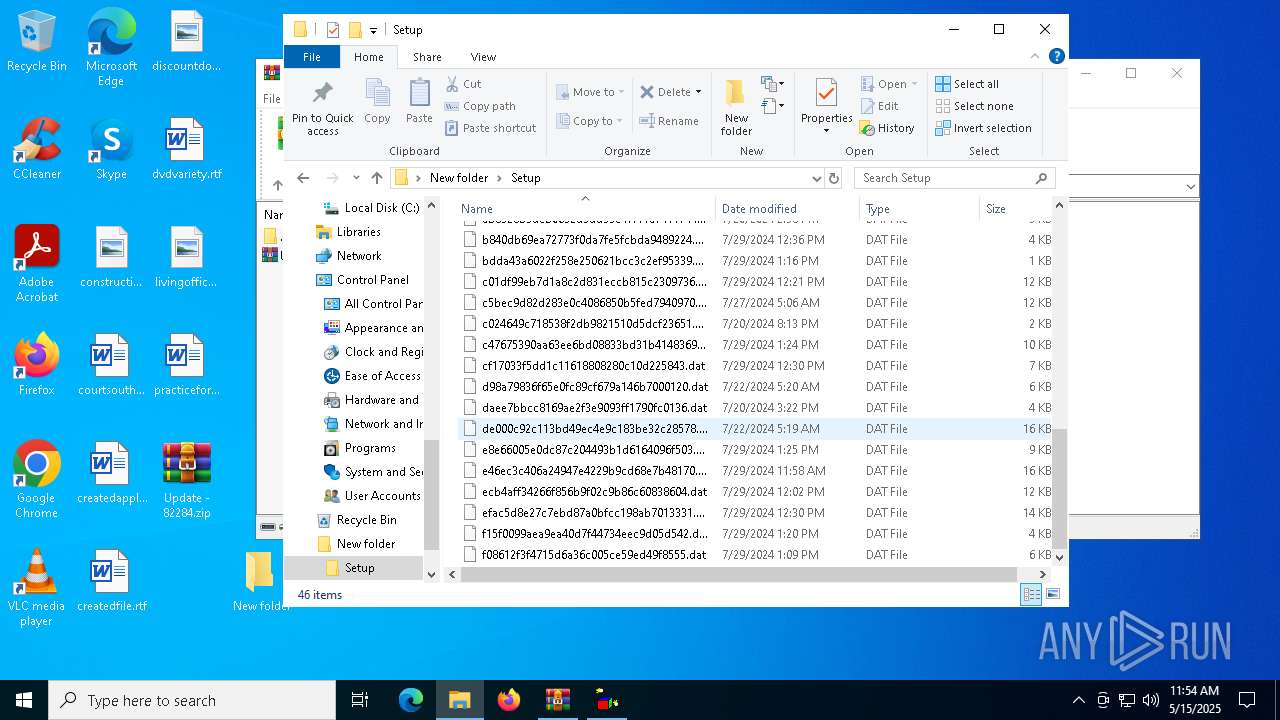
Executable files
0
Suspicious files
3
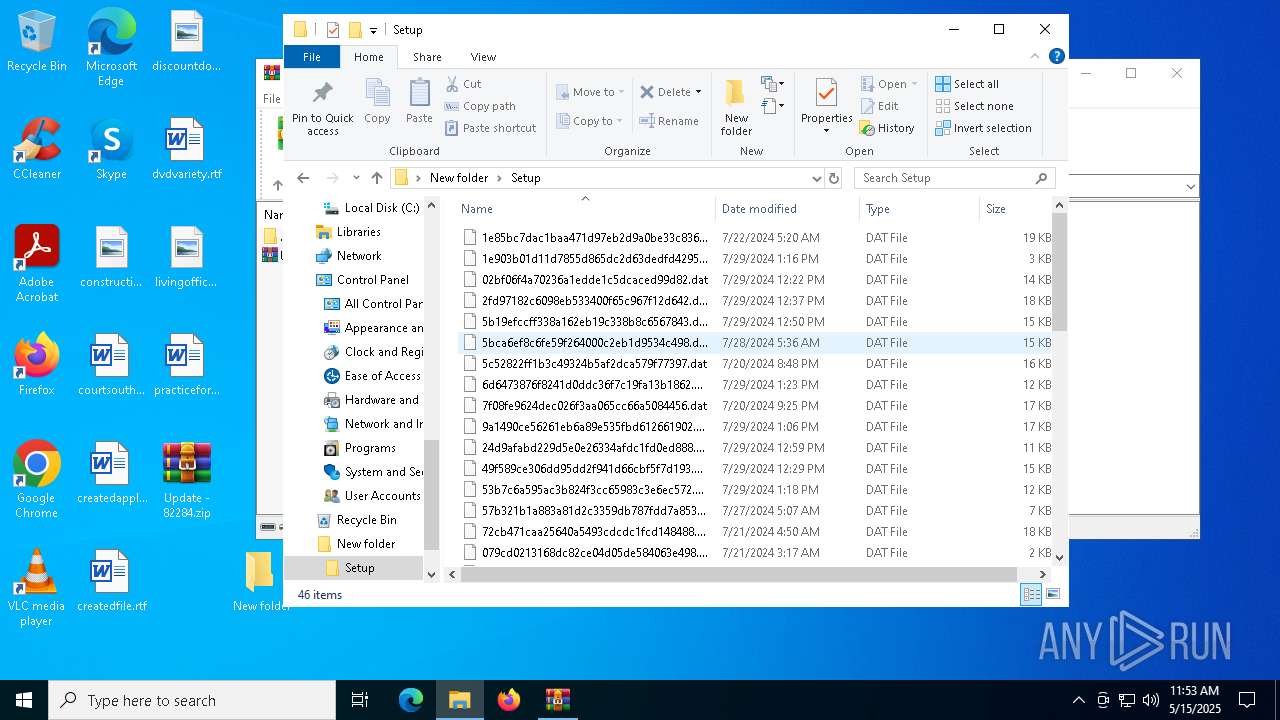
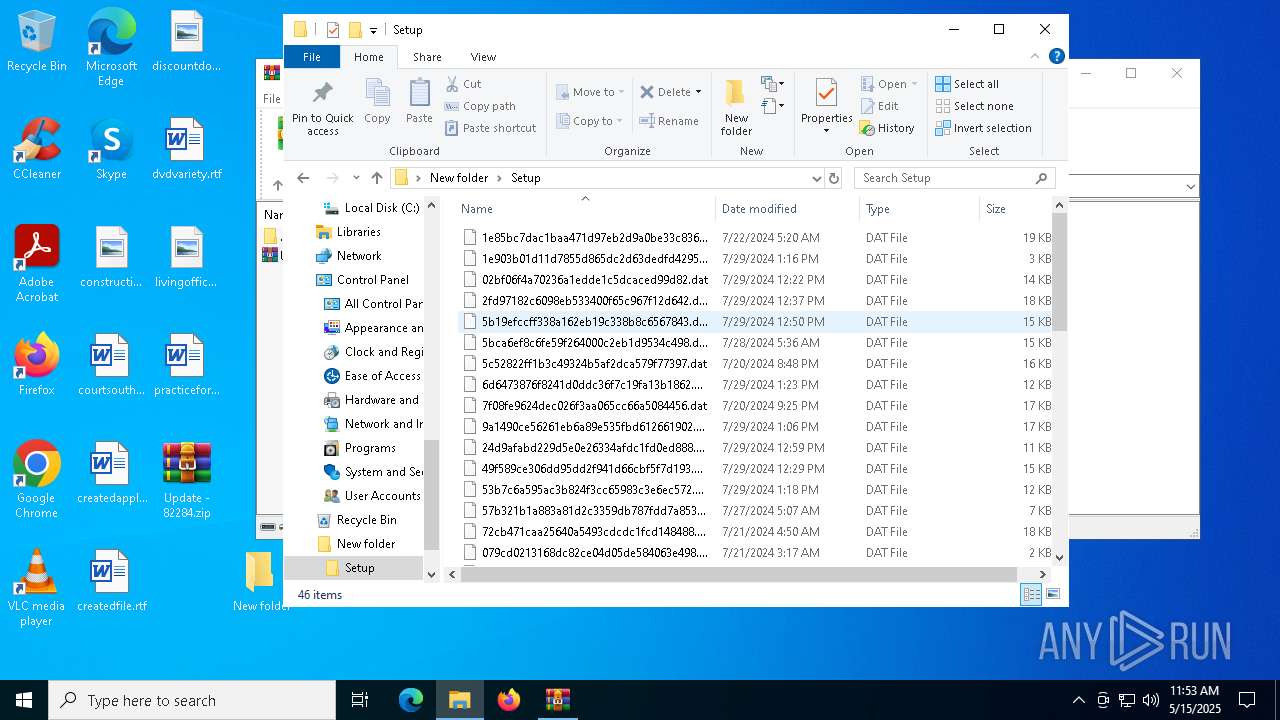
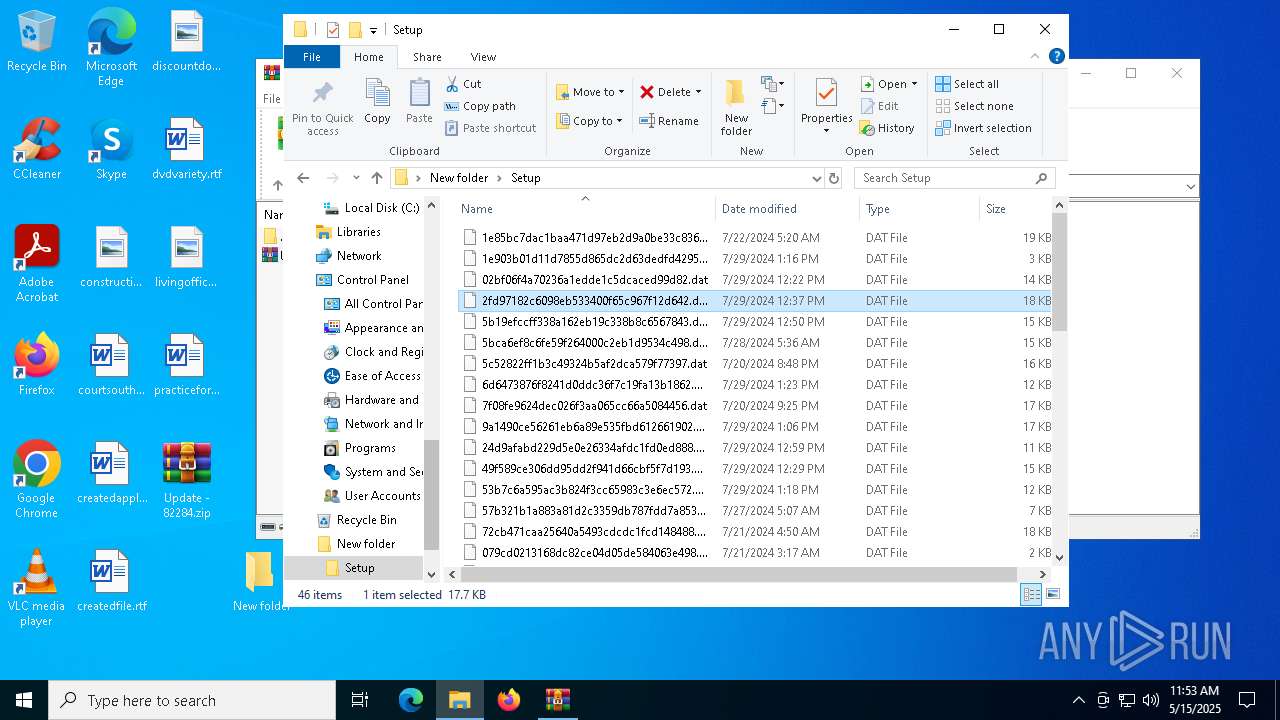
Text files
46
Unknown types
0
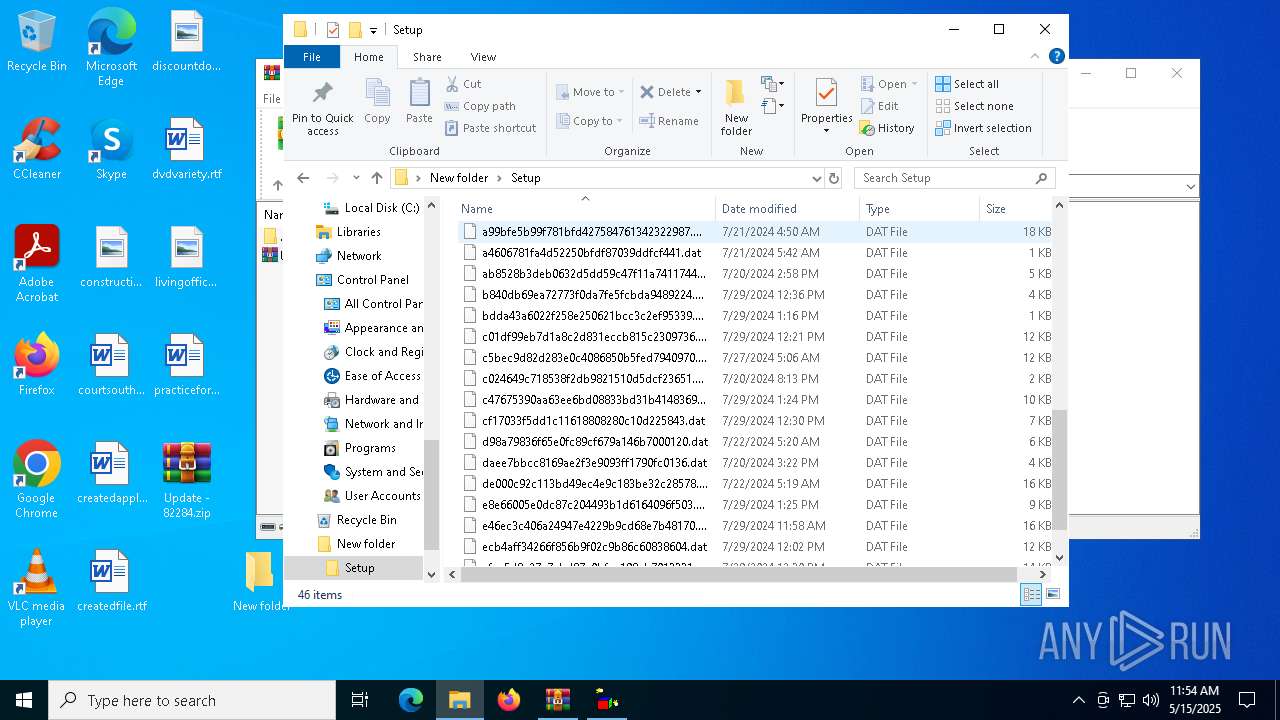
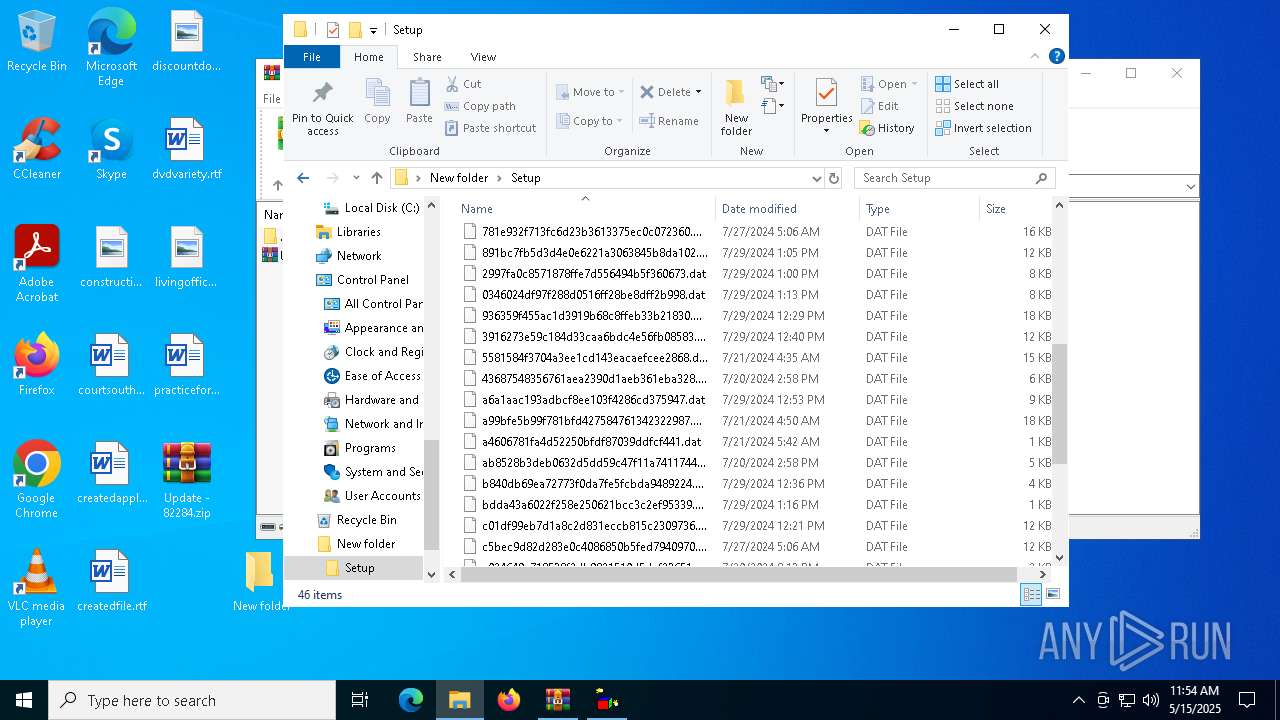
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Setup\daee7bbcc8169ae2f3e9093ff1790fc0136.dat | text | |
MD5:9D29A761208B48D25467353347FC6F3E | SHA256:7FBB3C36959187A94F8D1D2B1F7F30C3C9B55E5533BA0525B414E2D6C4307D80 | |||
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Setup\7f08fe9624dec026f3aa065cc66a5084456.dat | text | |
MD5:33FC4CB92B79609DDB0F77841A5DEF86 | SHA256:EFEF9FBBCB2CF0CEA4535A83290813E7F48E49902D39718EC37250816D9FB2BD | |||
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Setup\43687548356761aea2390d1aeb361eba328.dat | text | |
MD5:8ECDA677C05930FFA8AFC14EEF97535D | SHA256:D77F034F7B96764B07F1C116097B09FA2EE09362FF2978F084B3E5666FE96A64 | |||
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Setup\5c52822ff1b3c49324b5af2dca579f77397.dat | text | |
MD5:5D29358D3FF33E6B0AB5F691387EEEBB | SHA256:A28EC0229498A053D70AA64FA57ED43A262D6E445016C016A60FD291A2161C4C | |||
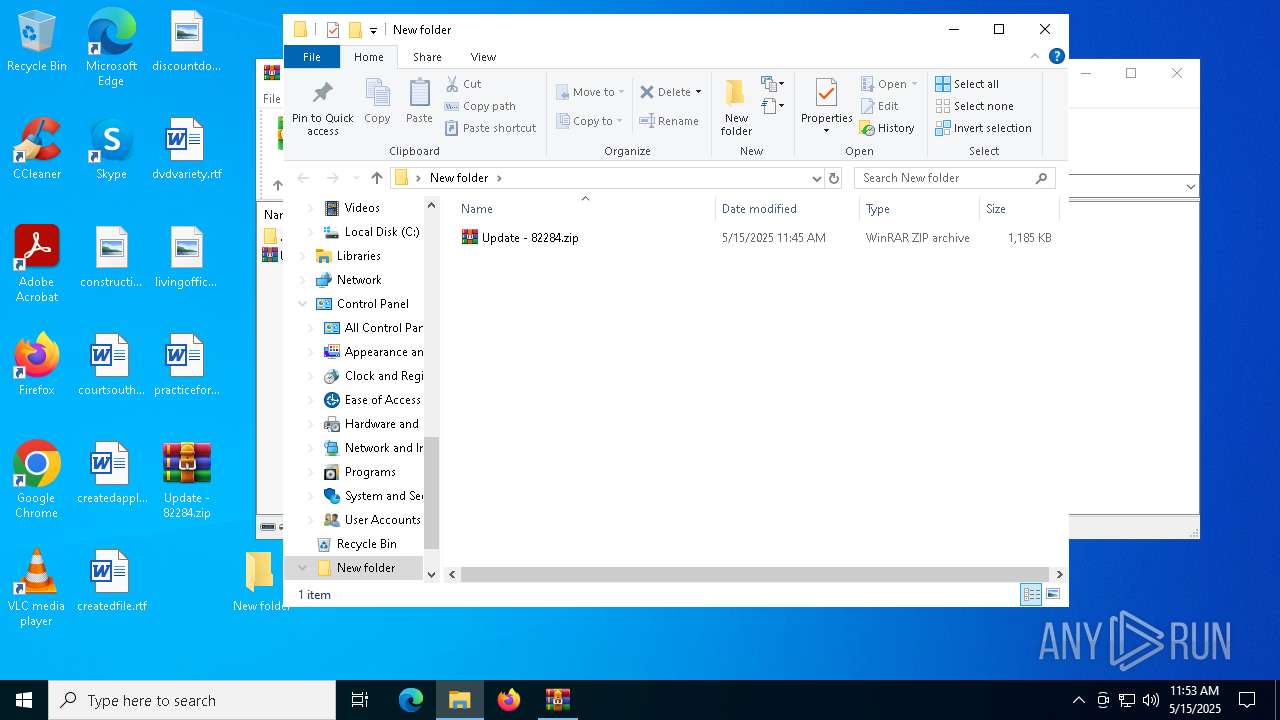
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Update 126.0.6478.127.js | binary | |
MD5:09BD6BE585AF8134BF5FF2AD0415E993 | SHA256:DA28130A1055E4E0A52A7B6A68685490054A8C34056DAC822988C2F7E3946D7E | |||
| 7404 | WinRAR.exe | C:\Users\admin\Desktop\Update - 82284.zip | compressed | |
MD5:17B3F0E81DA065A92E42F12A556DCF37 | SHA256:63643D686F891ED4A07AC5D74561342B3EEAABB8835243AAD1A97B43CD7C4506 | |||
| 7404 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Update - 82284.zip | compressed | |
MD5:17B3F0E81DA065A92E42F12A556DCF37 | SHA256:63643D686F891ED4A07AC5D74561342B3EEAABB8835243AAD1A97B43CD7C4506 | |||
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Setup\5581584f3704a3ee1cd143eacaefcee2868.dat | text | |
MD5:3B4BAC66CADCEC7E997BF71D1903F0AA | SHA256:C40779768CAF025C07CF430700DC36D96734398771A3FEC86F3650E921F05597 | |||
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Setup\ab8528b3deb0632d5dd59c47f11a7411744.dat | text | |
MD5:DD92355F32D05E628887030F8E104907 | SHA256:8C51E46036FA528ACBC37A36FDF25605D43F24479BBAAD5109C3AF976AD419D1 | |||
| 7392 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Setup\781e932f713fc6d23b3613375ec0c072360.dat | text | |
MD5:D91799A61B28EB822FE83CF9D8C29540 | SHA256:2AA6A3CA2E574EFCB2324875960F49042CCC9A68B54287D7510209CC706687D2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
26
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8088 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8088 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4024 | wscript.exe | GET | 200 | 175.110.113.177:80 | http://astronomicspace.com/cdn-vs/22per.php?9676 | unknown | — | — | unknown |
4812 | wscript.exe | GET | 200 | 175.110.113.177:80 | http://astronomicspace.com/cdn-vs/22per.php?9676 | unknown | — | — | unknown |
5640 | wscript.exe | GET | 200 | 175.110.113.177:80 | http://astronomicspace.com/cdn-vs/22per.php?9676 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |