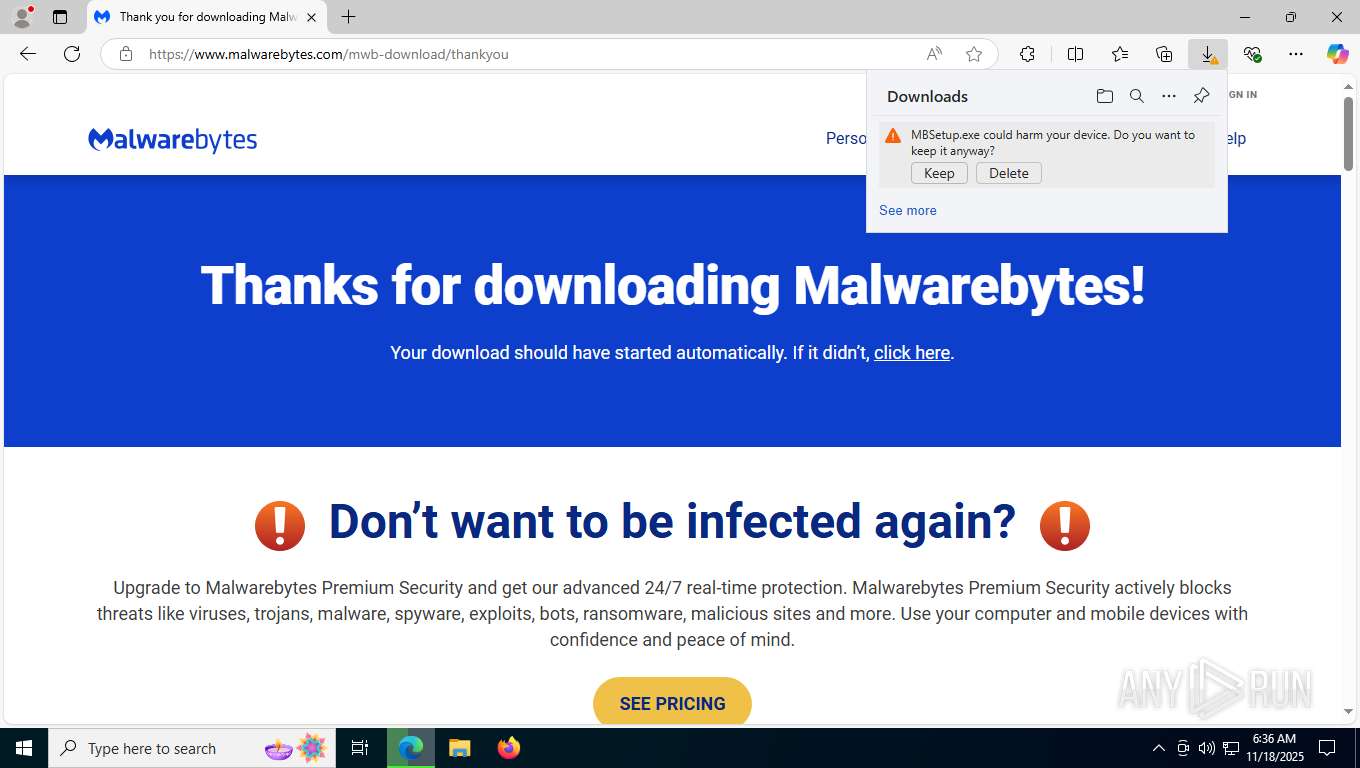
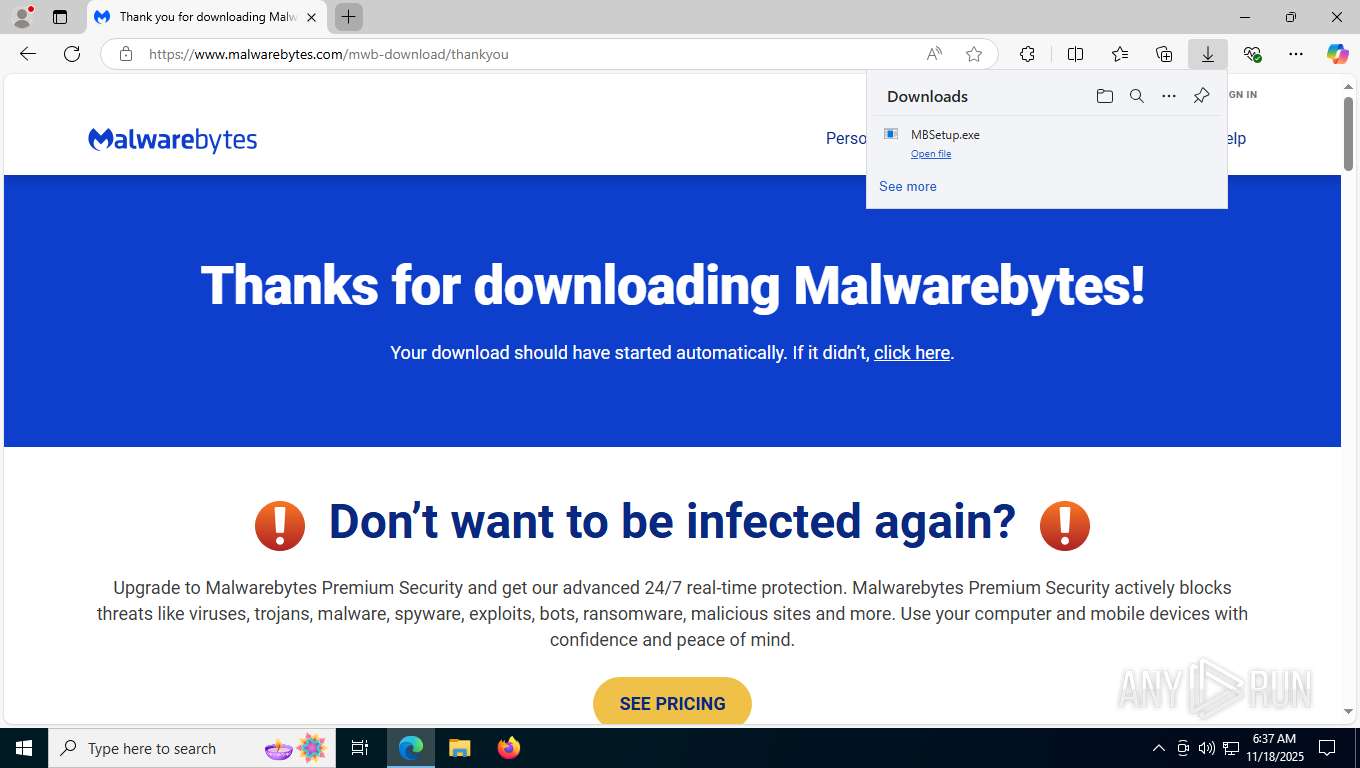
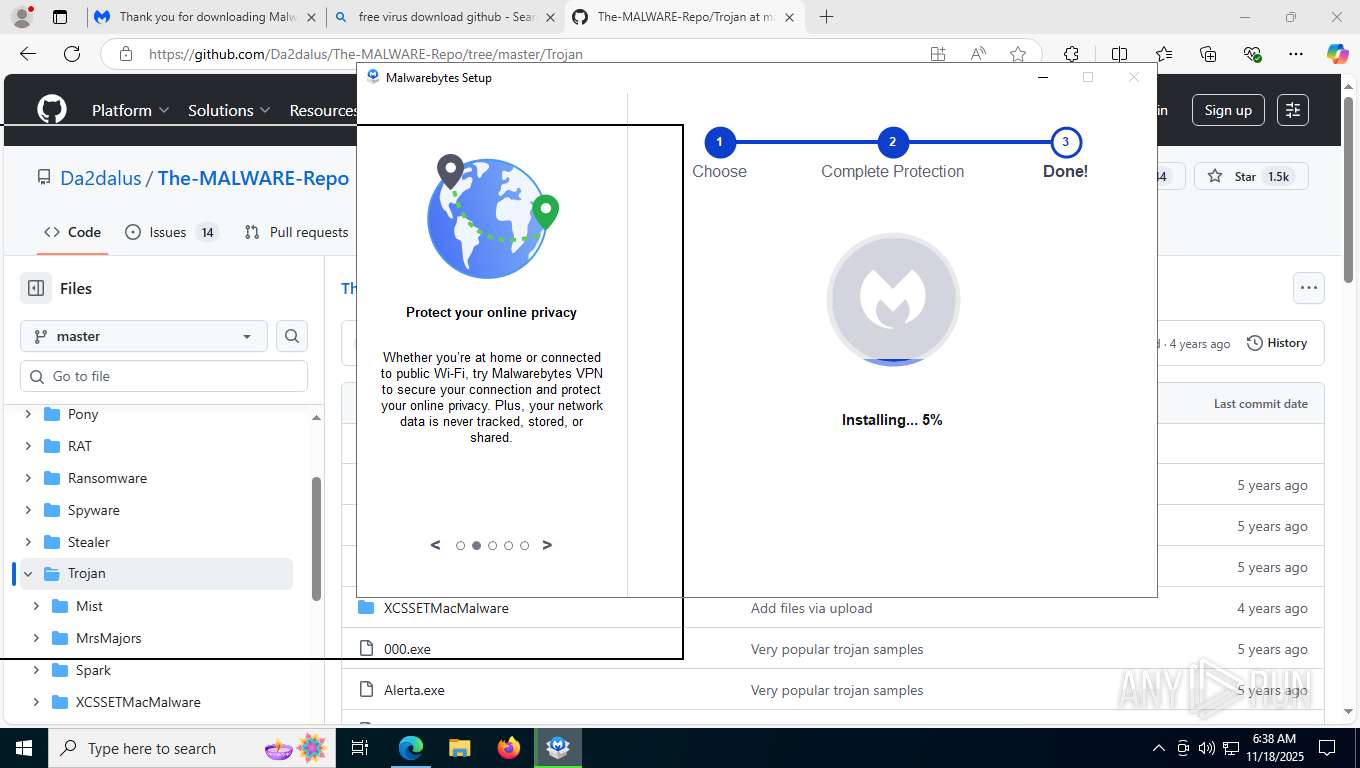
| URL: | malwarebytes.com |
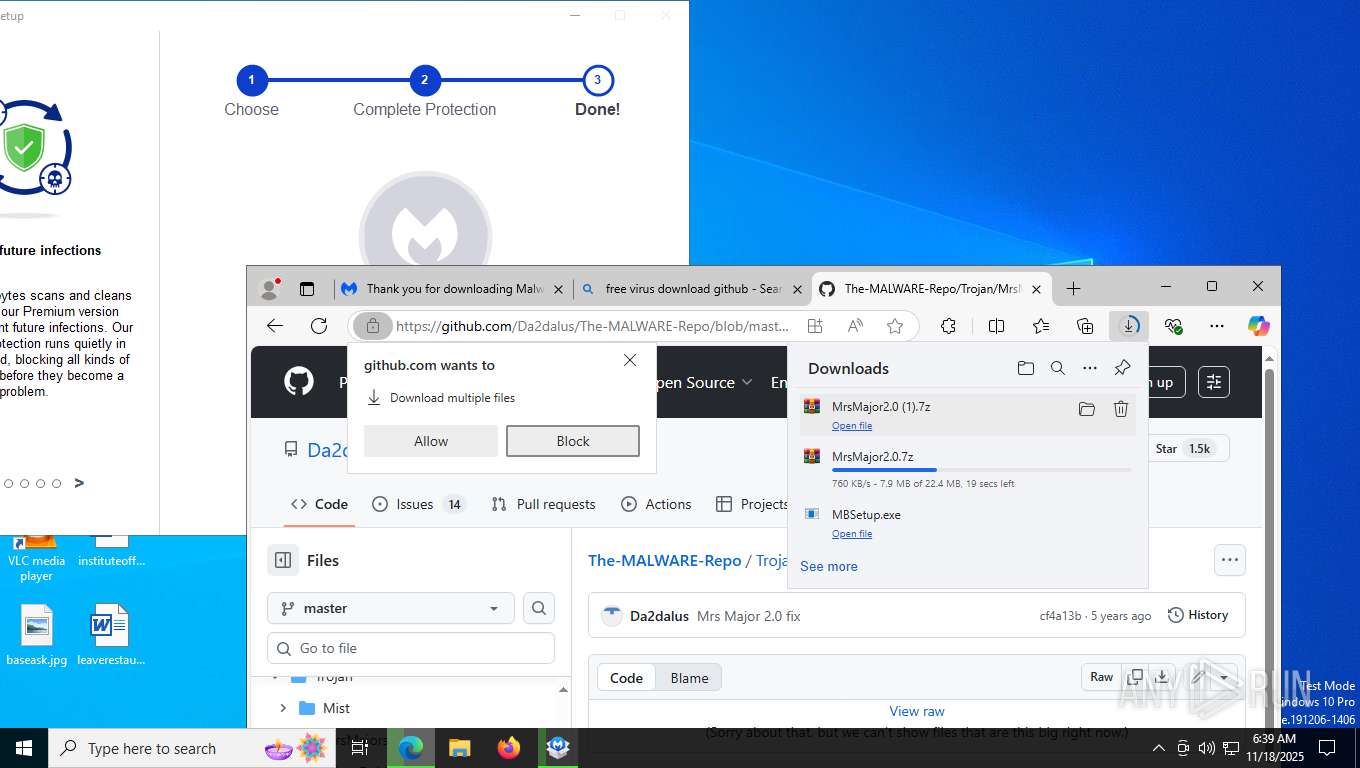
| Full analysis: | https://app.any.run/tasks/56367a78-391c-4d08-8c44-2f1f30dcaf33 |
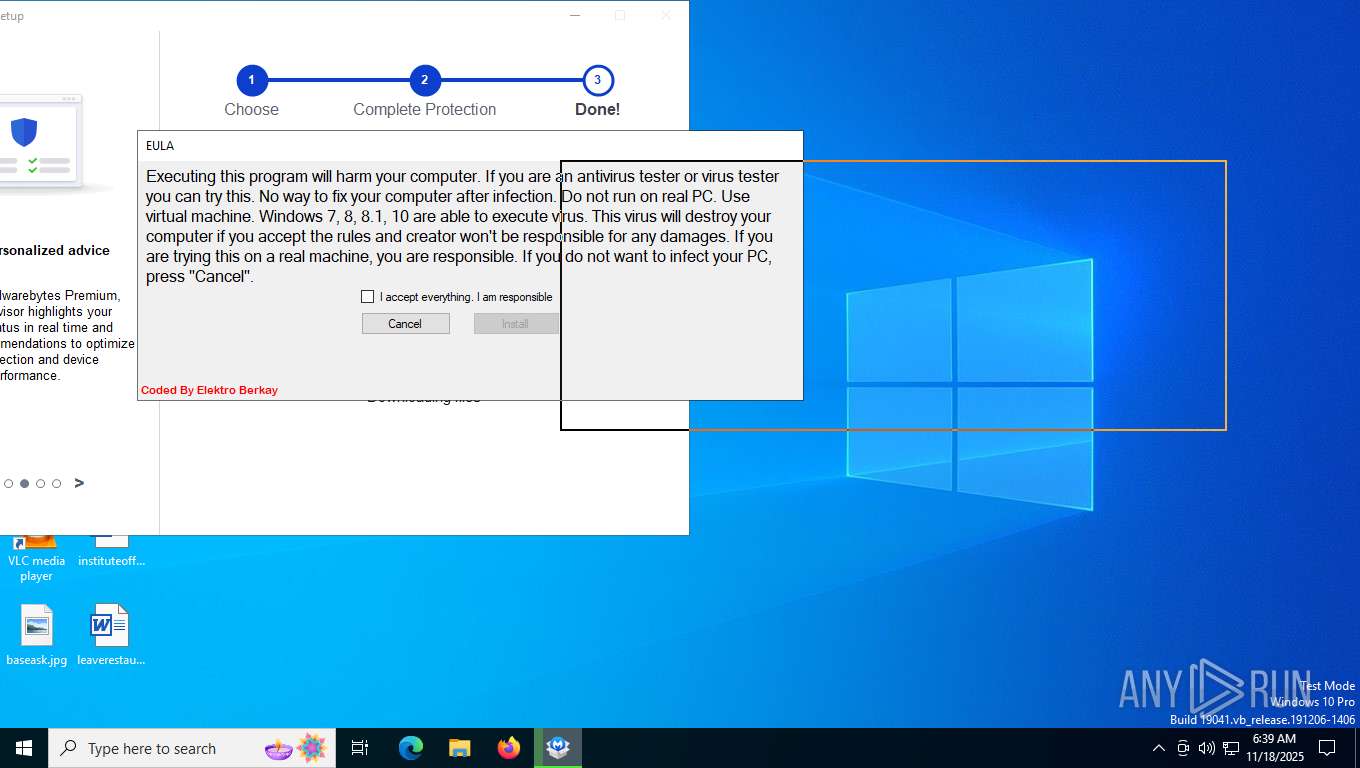
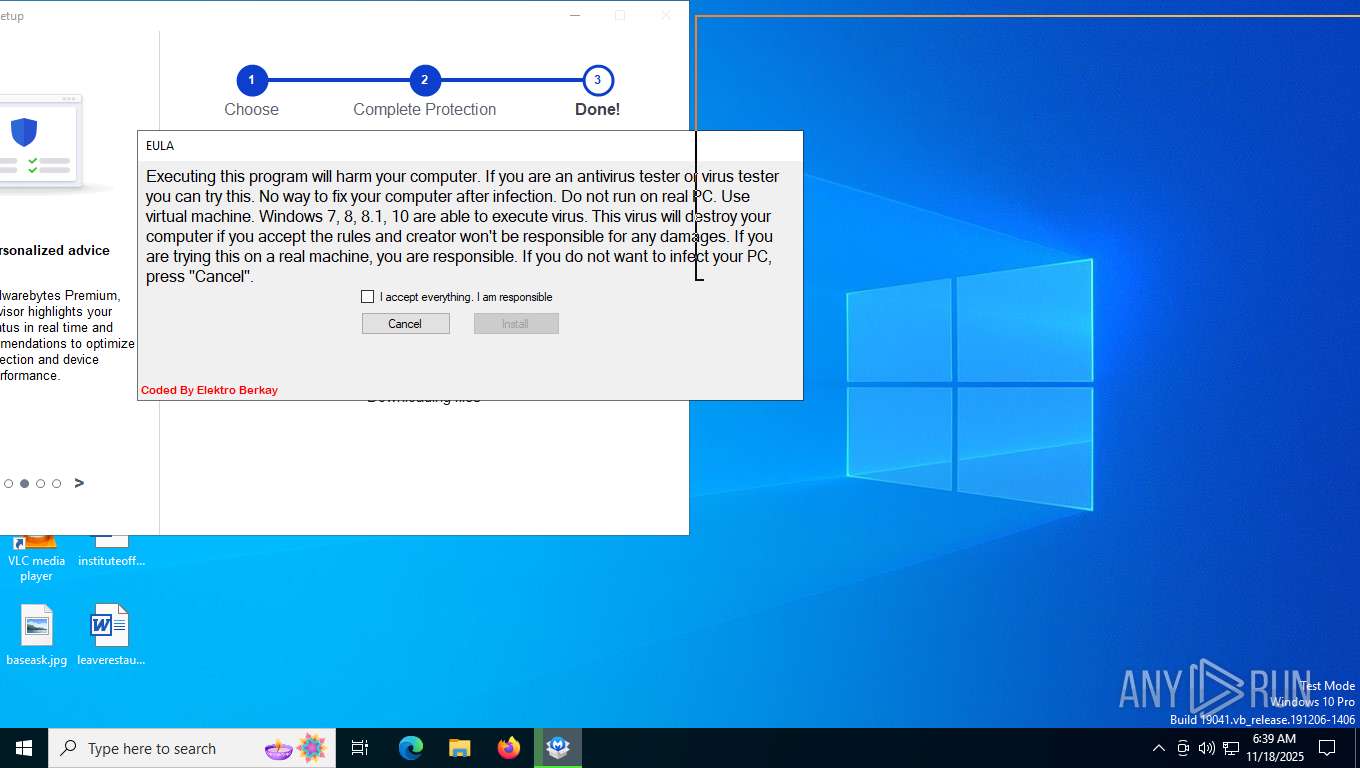
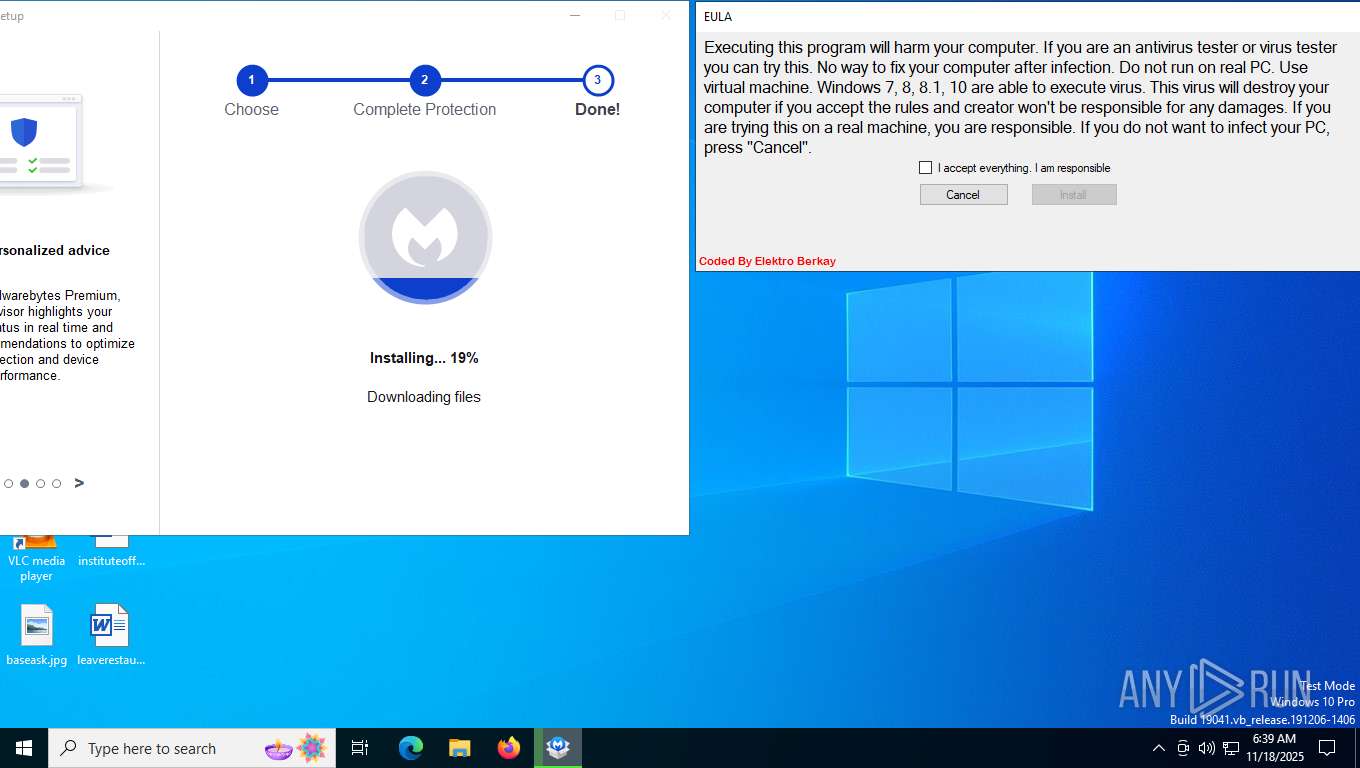
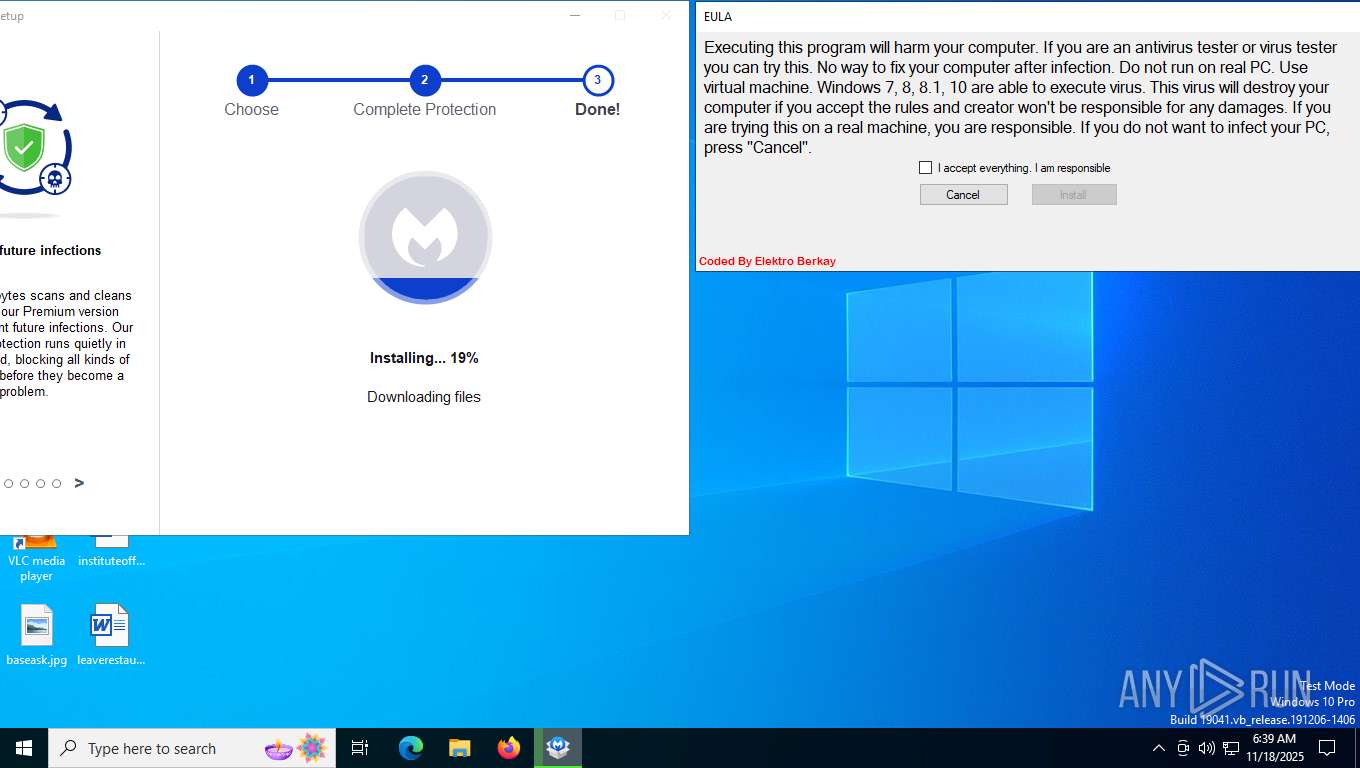
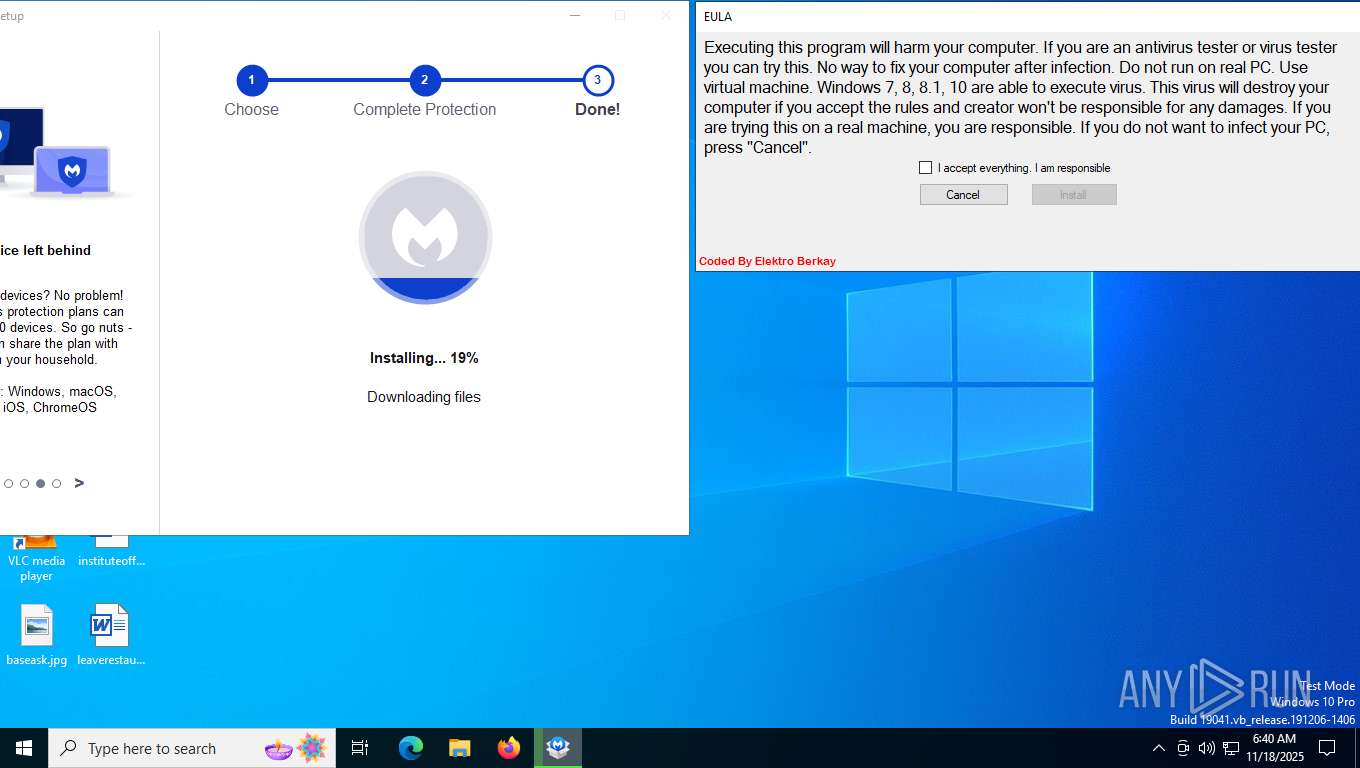
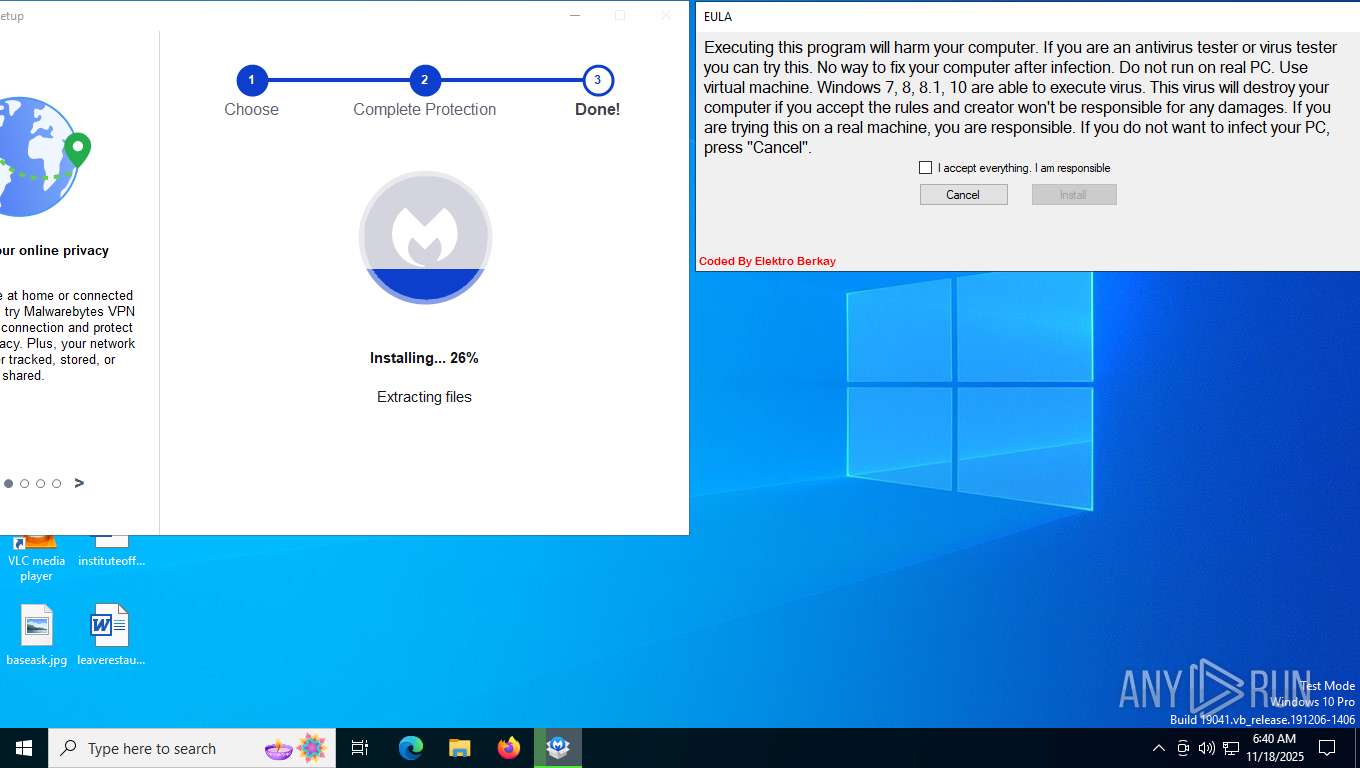
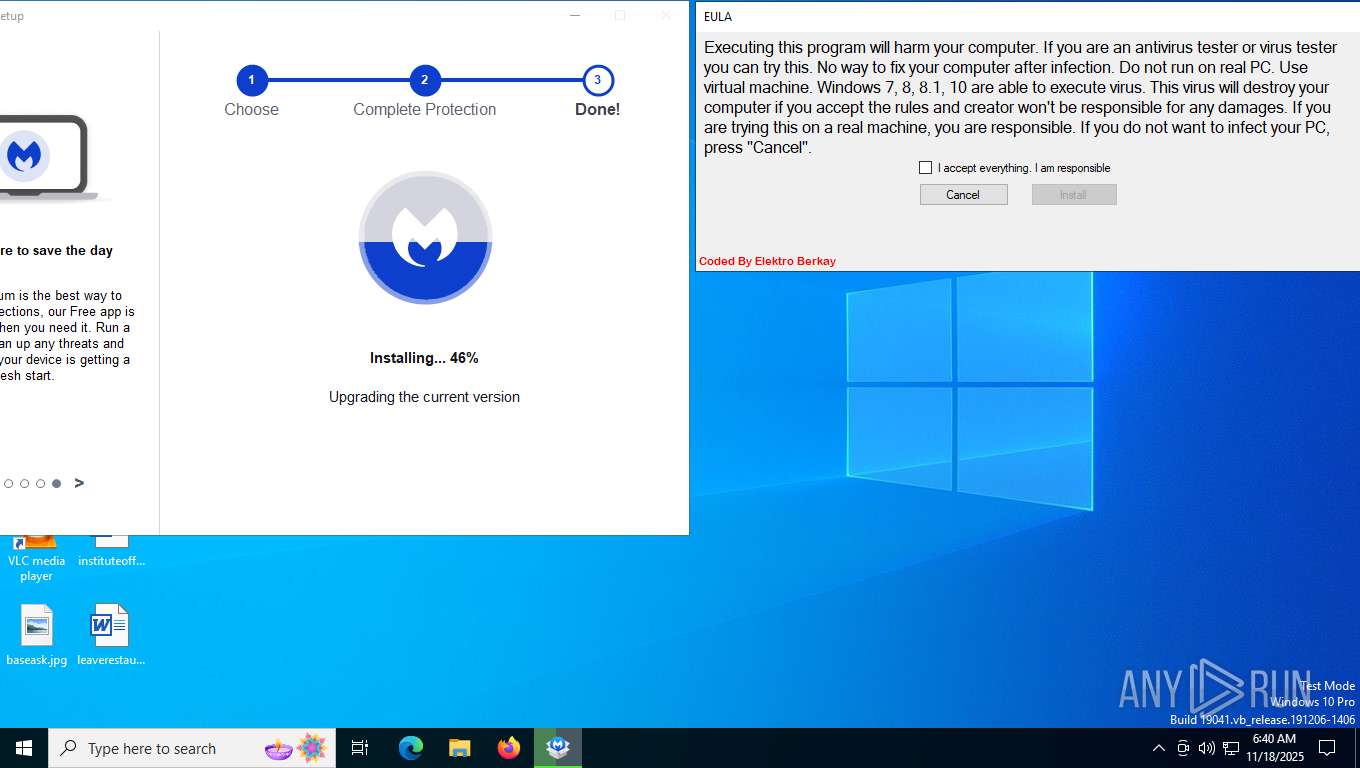
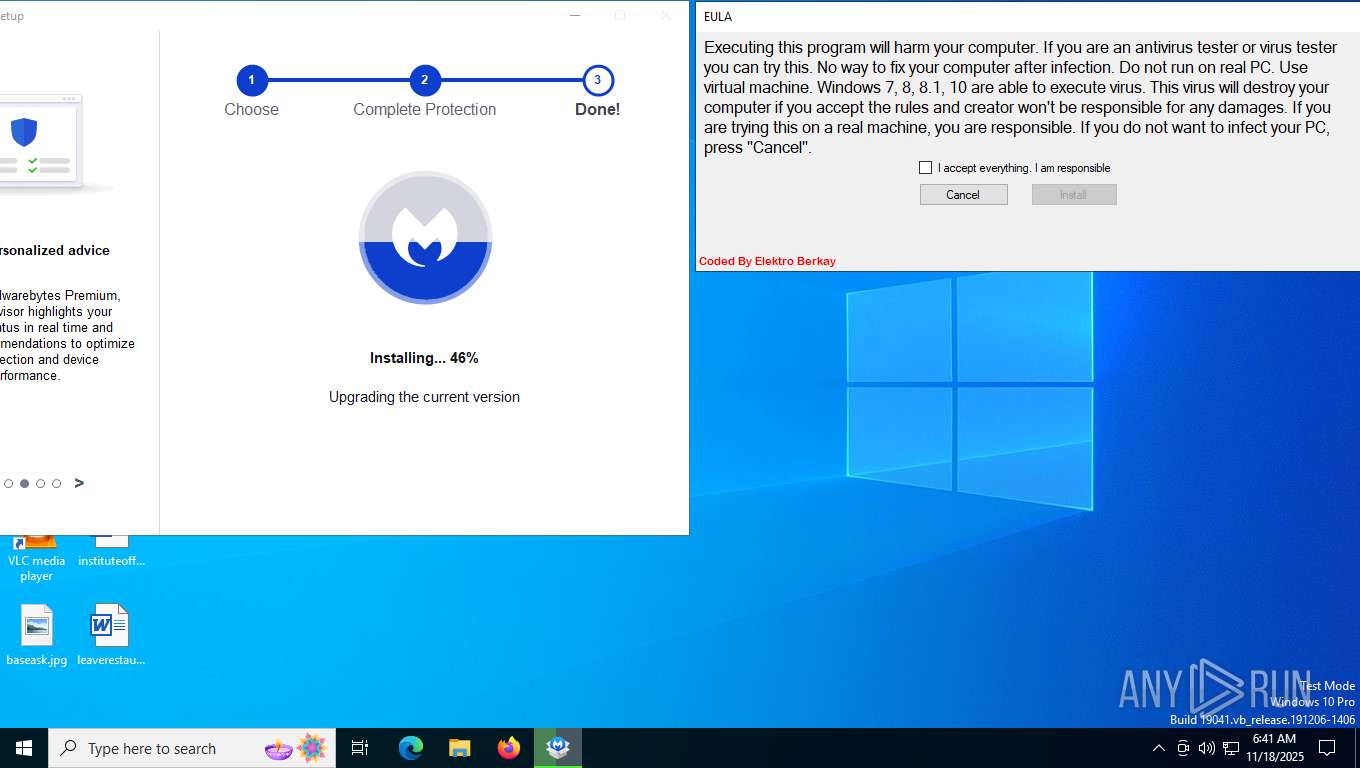
| Verdict: | Malicious activity |
| Analysis date: | November 18, 2025, 06:36:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E2F0354CD055EE727D5359CEB3EC59AD |
| SHA1: | FF3668206CE68588D7C3D7F3995EFD8A238CC85F |
| SHA256: | D739C20D5AA5273EB3FE7E0F0BED66B2E7D2CF707ECFD44942865E1E86697452 |
| SSDEEP: | 3:5c+ZzyT:pGT |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2220)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 2220)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2220)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 2220)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 2220)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 2220)
SUSPICIOUS
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 6748)
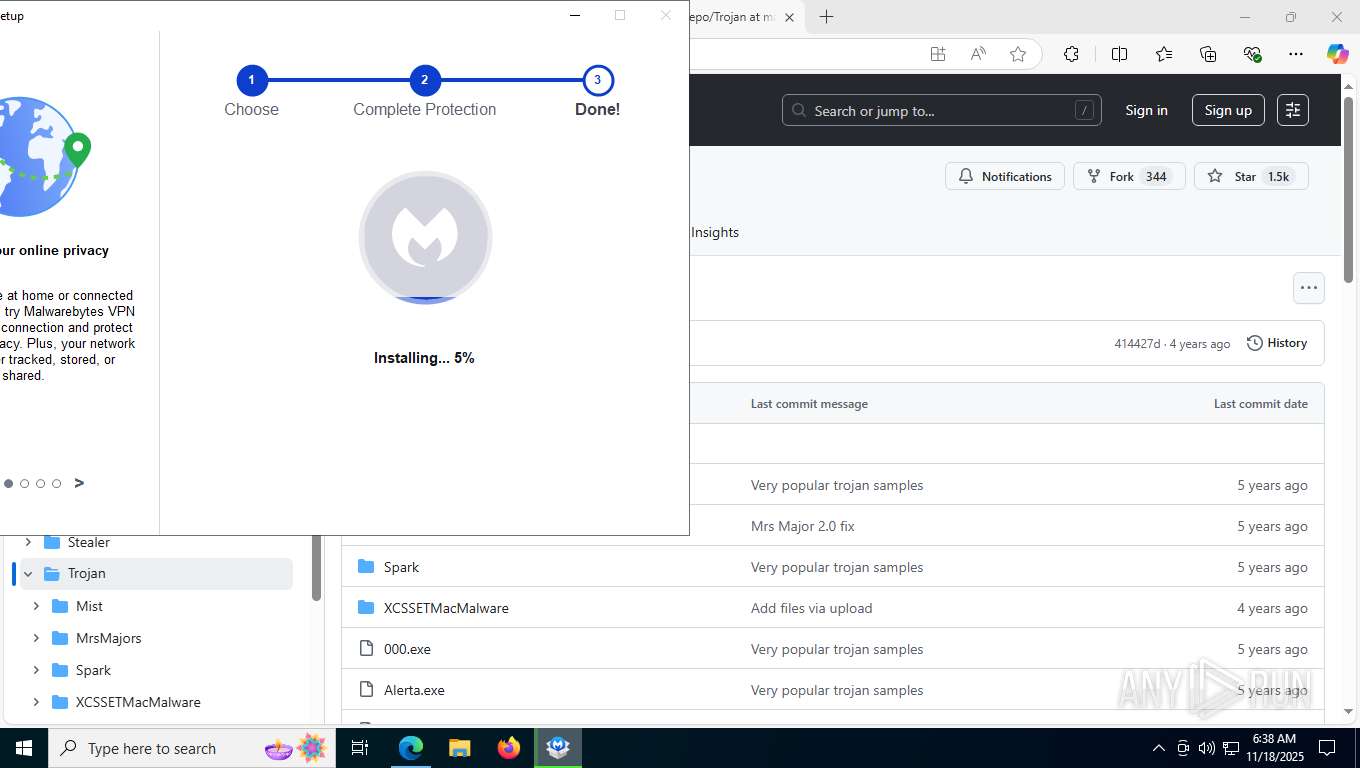
Searches for installed software
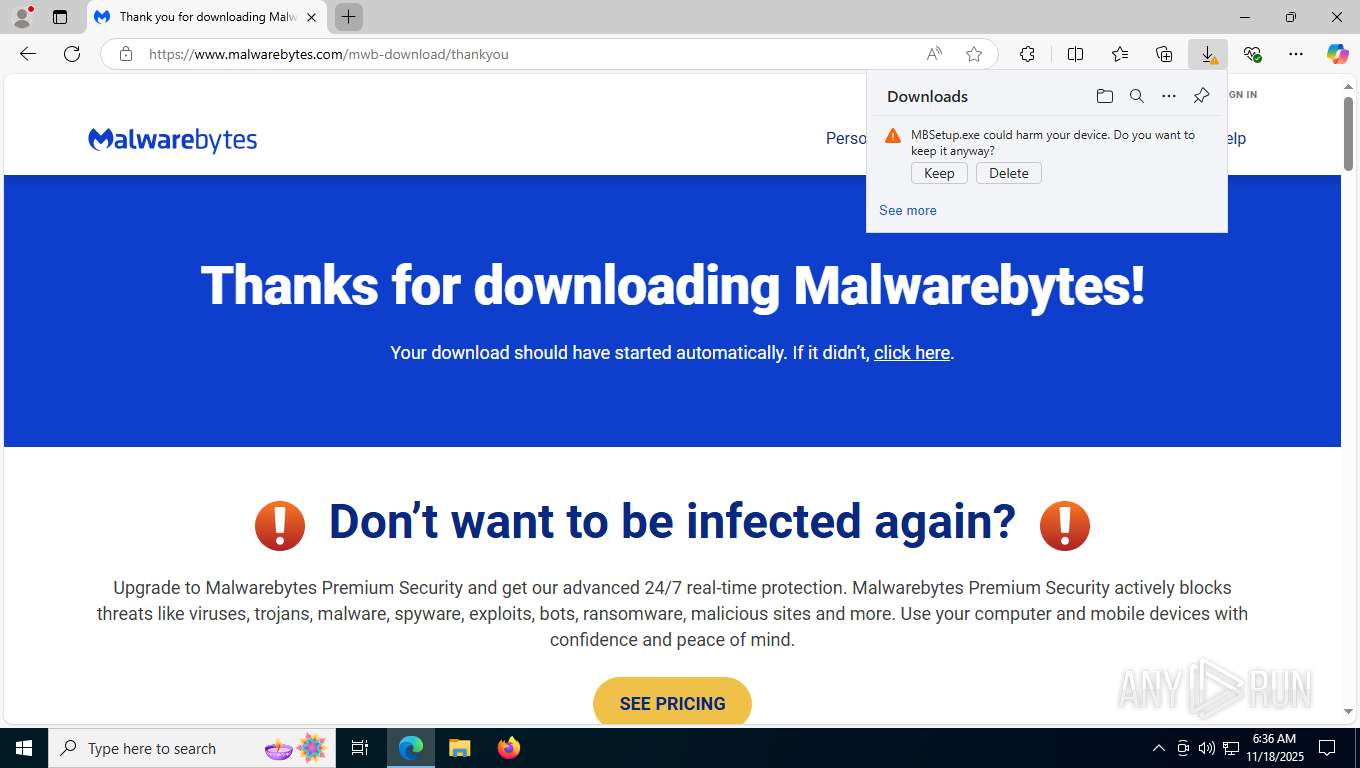
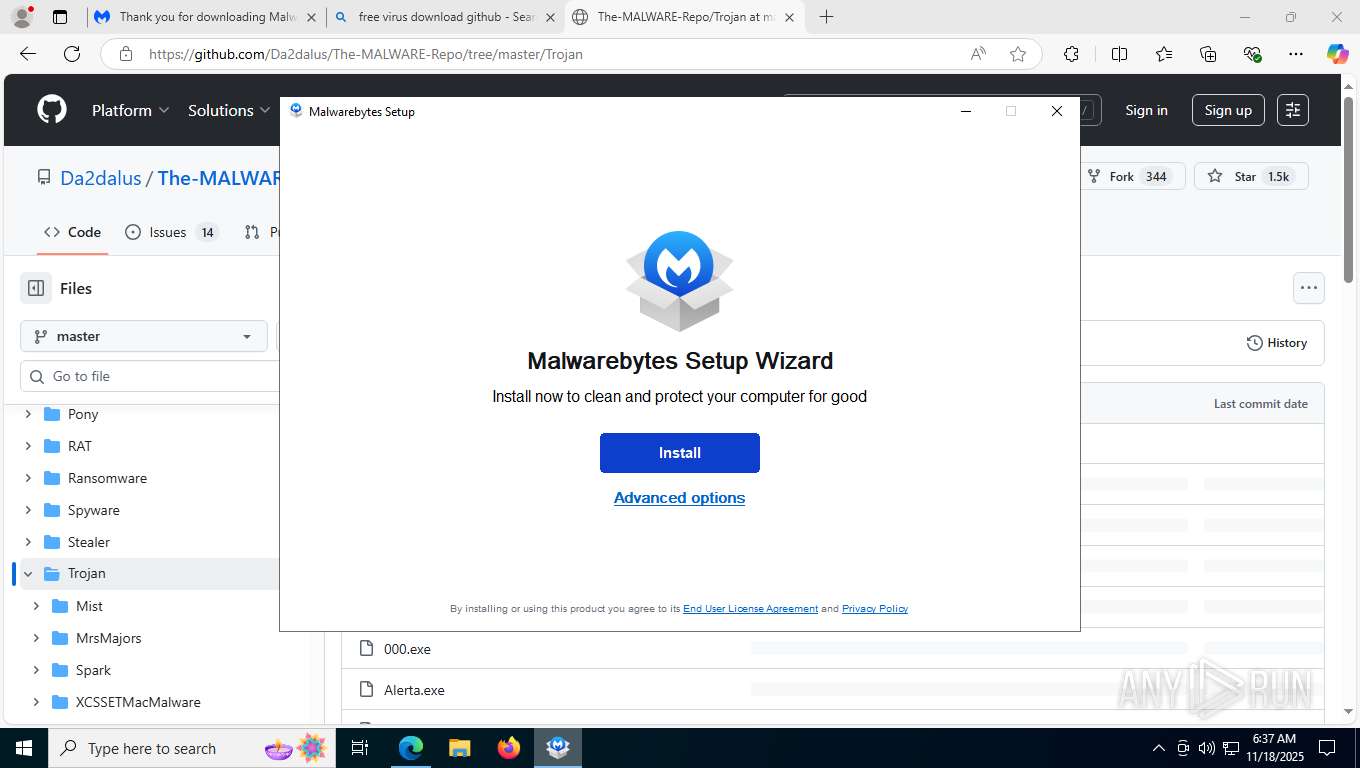
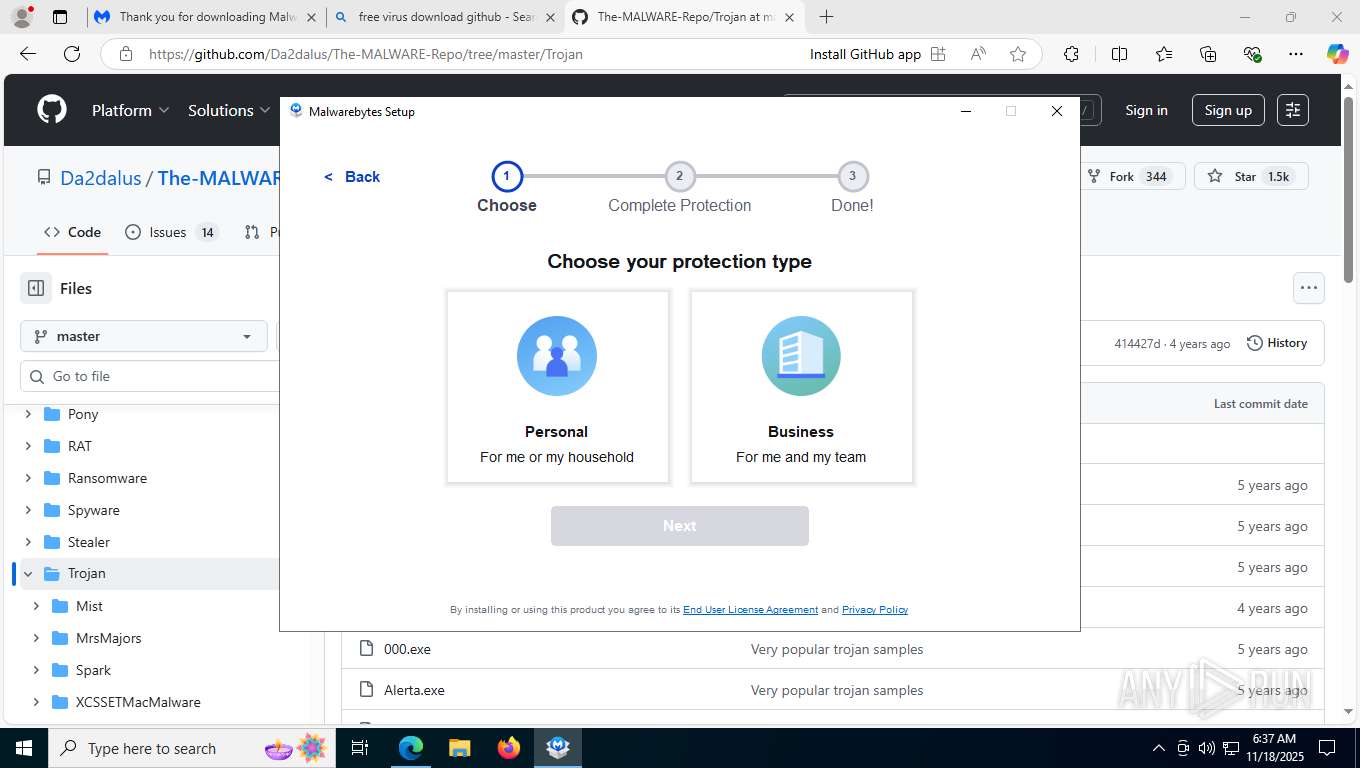
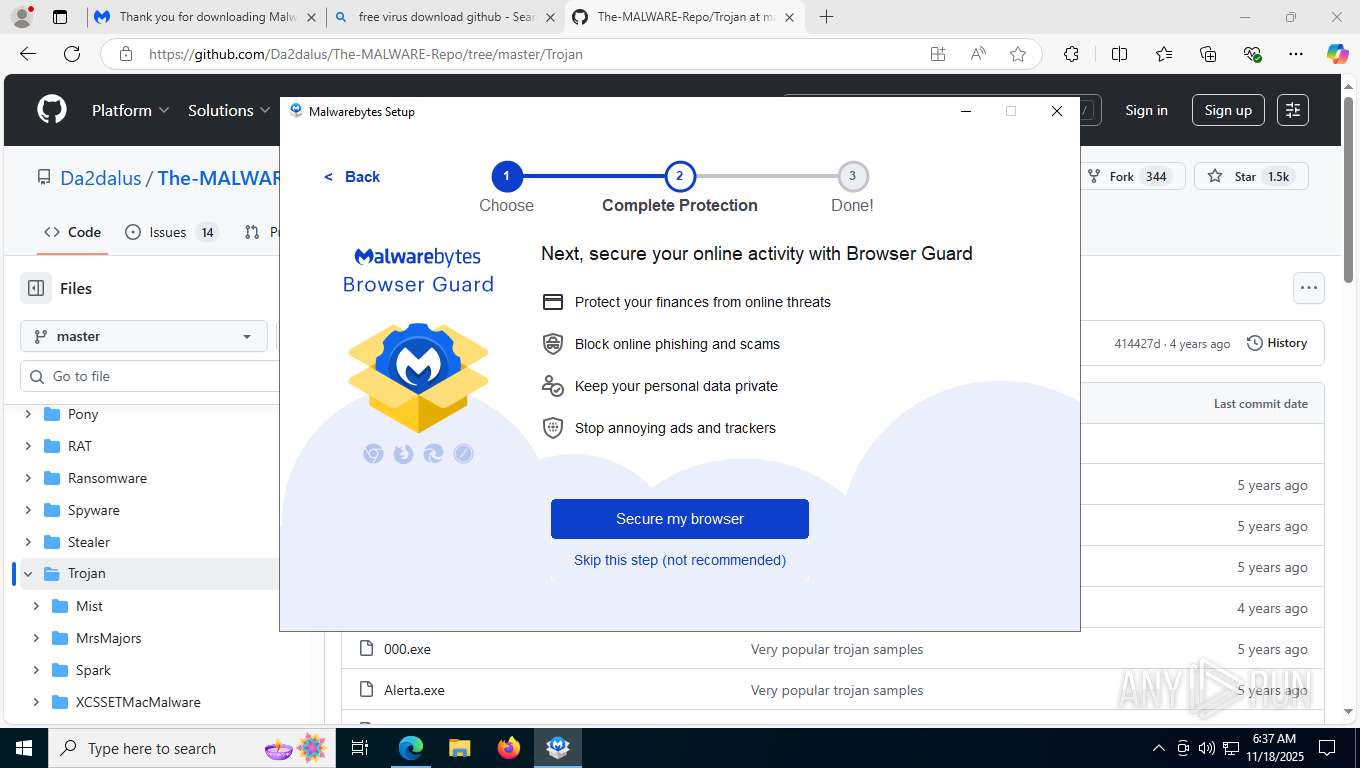
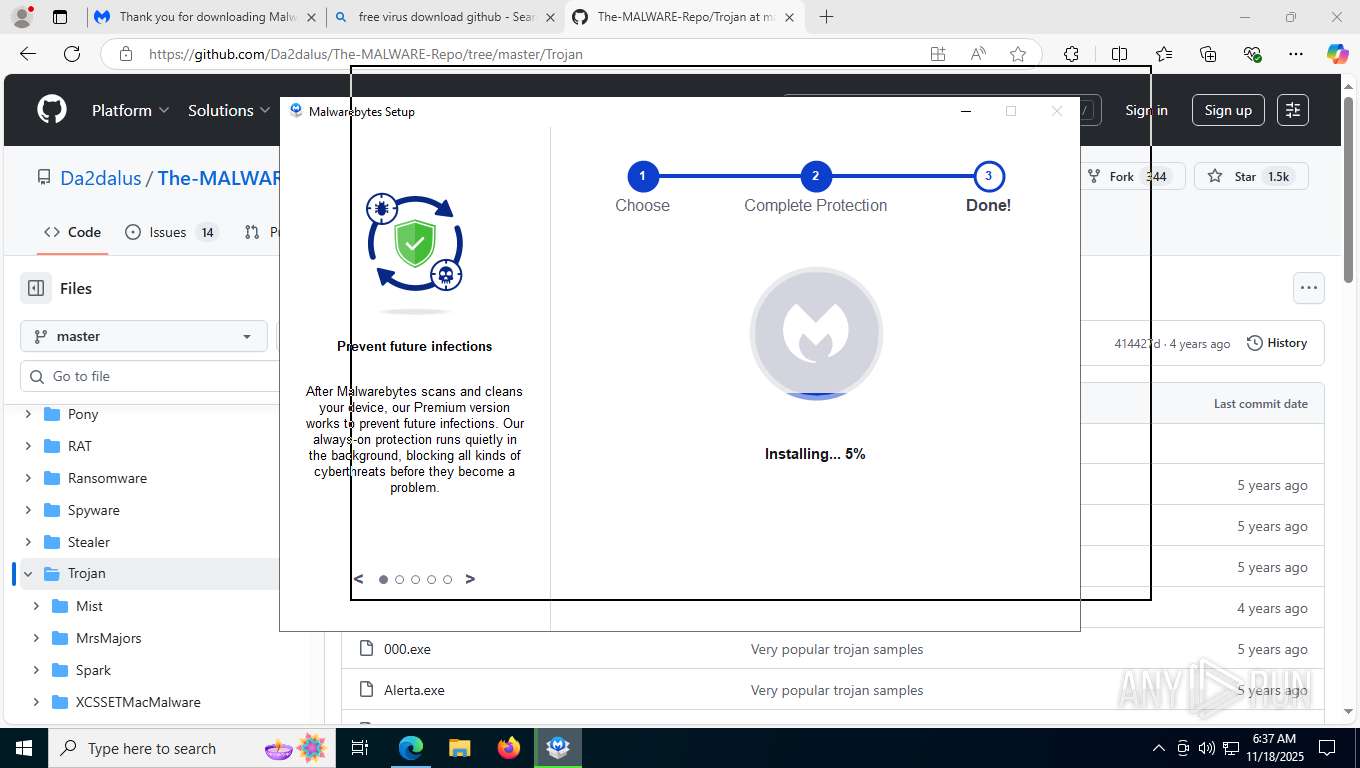
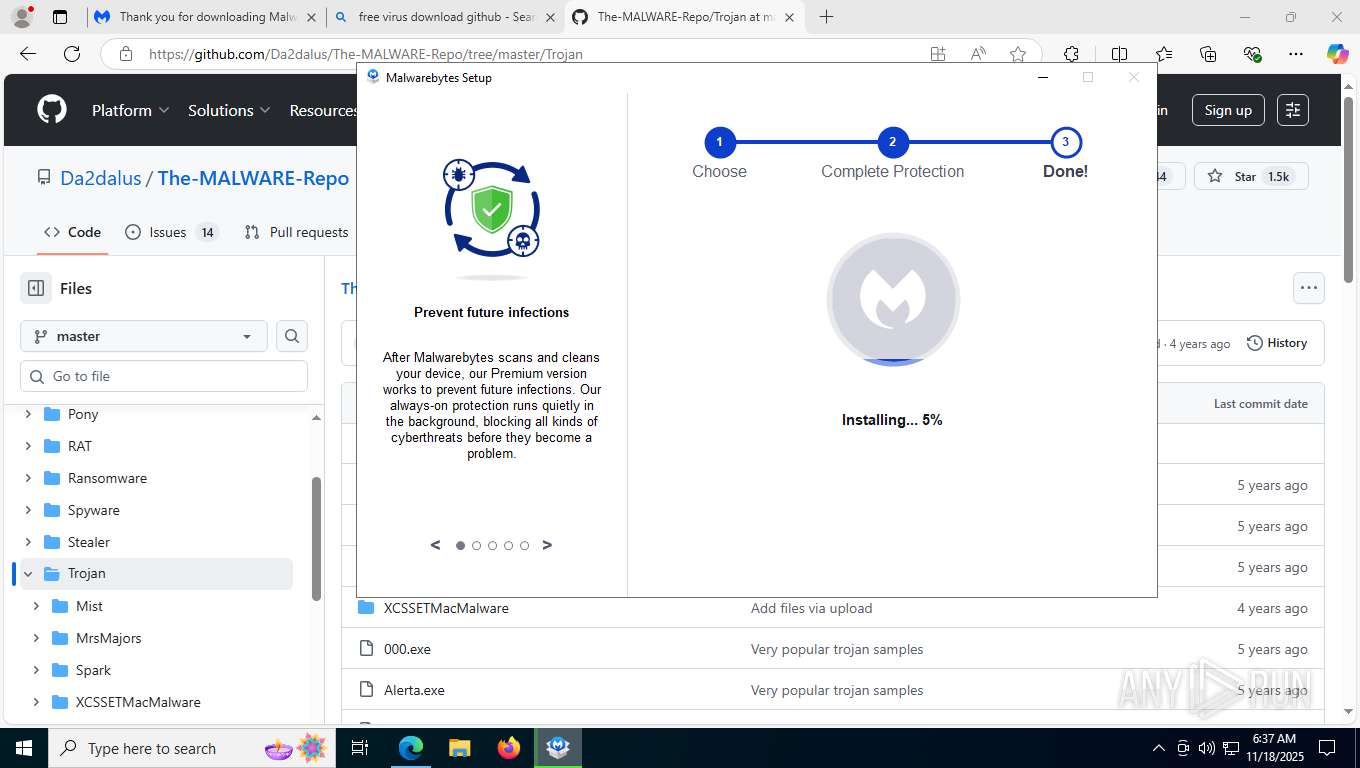
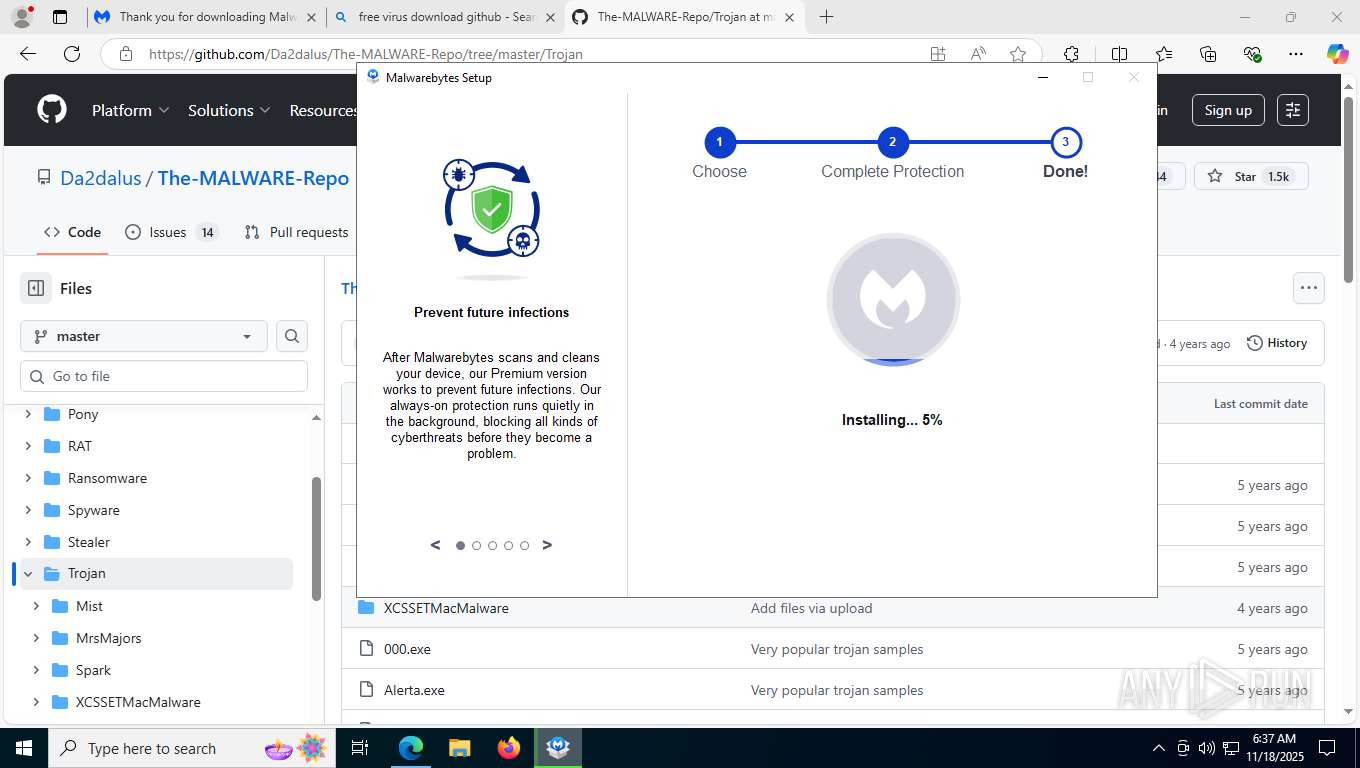
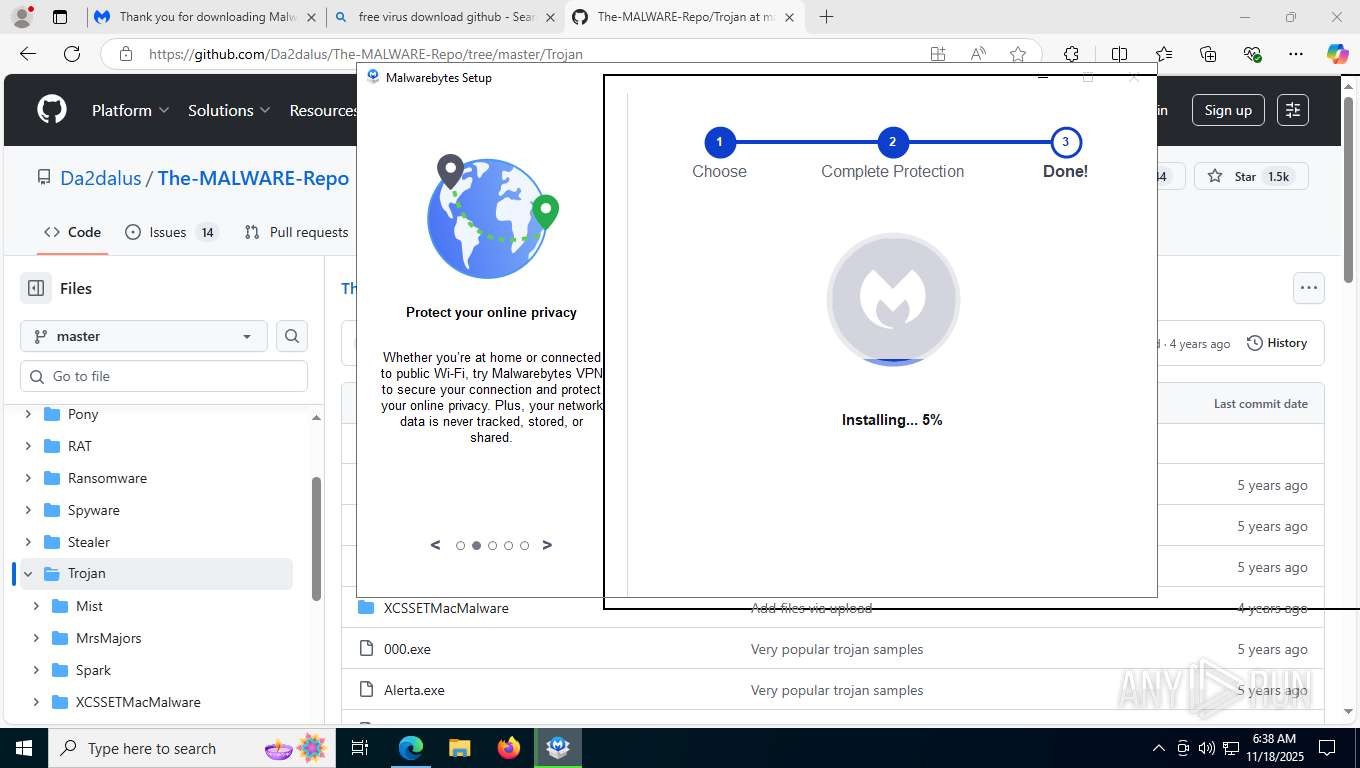
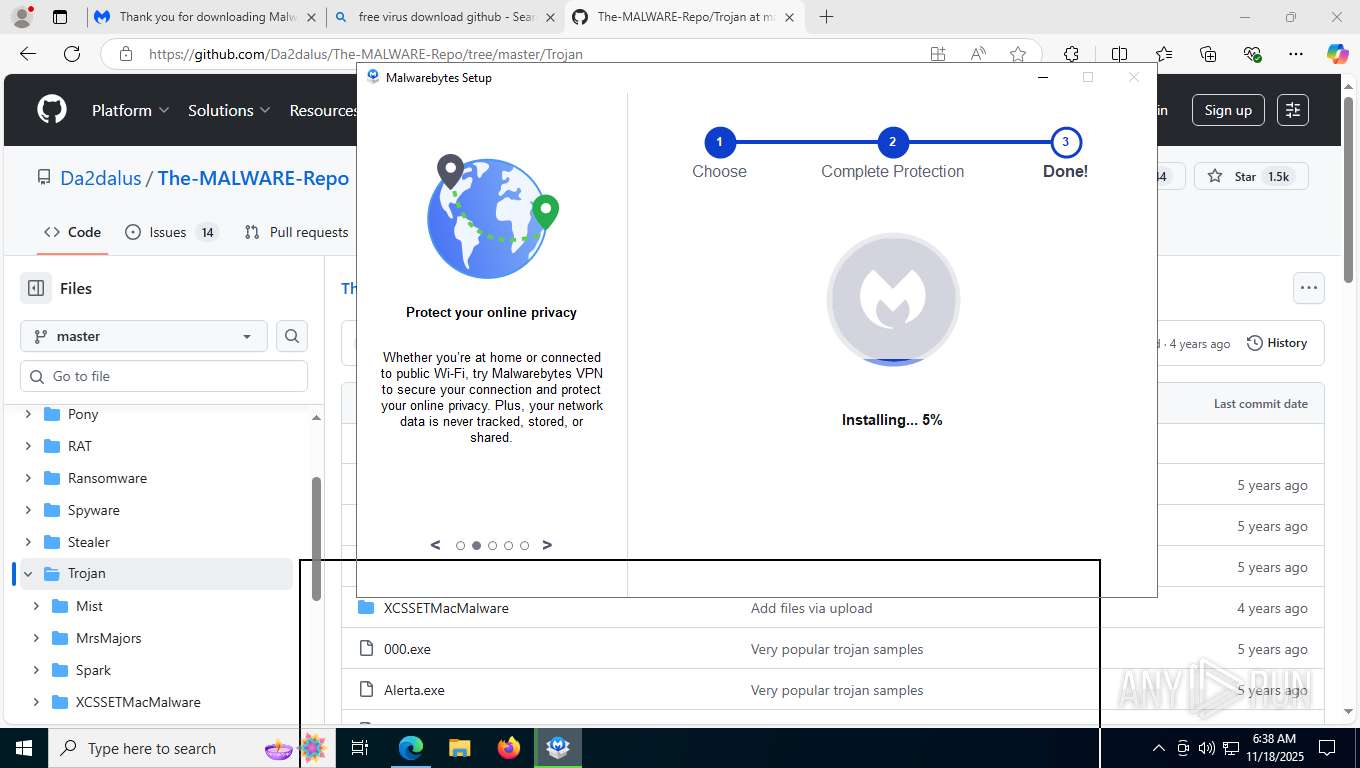
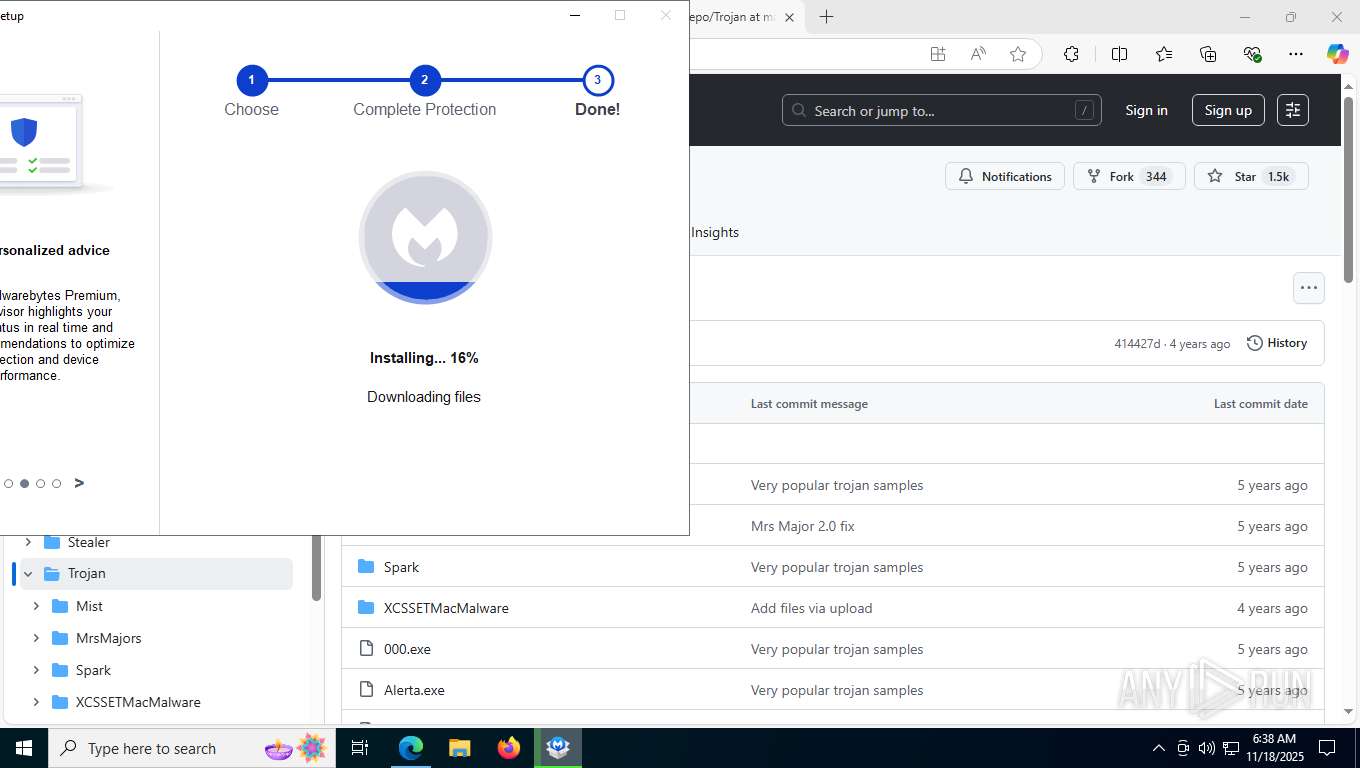
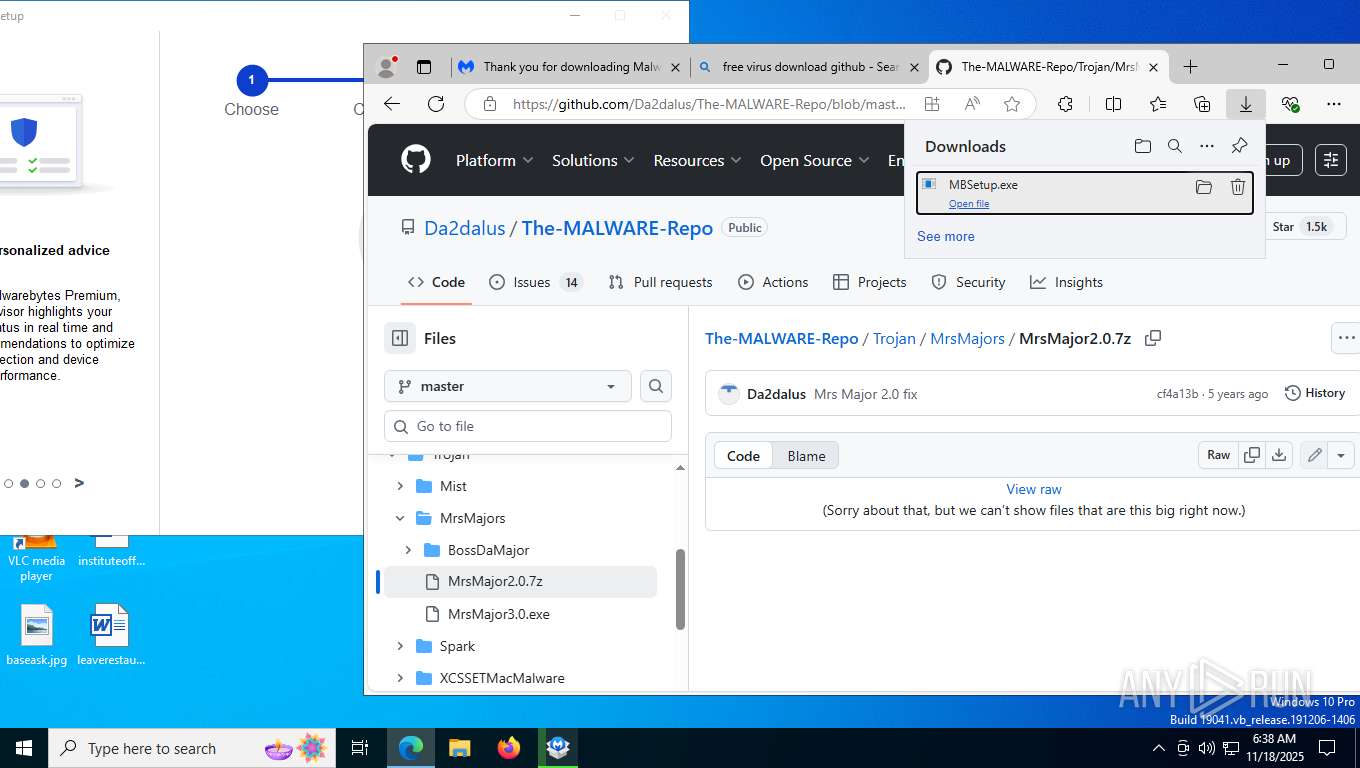
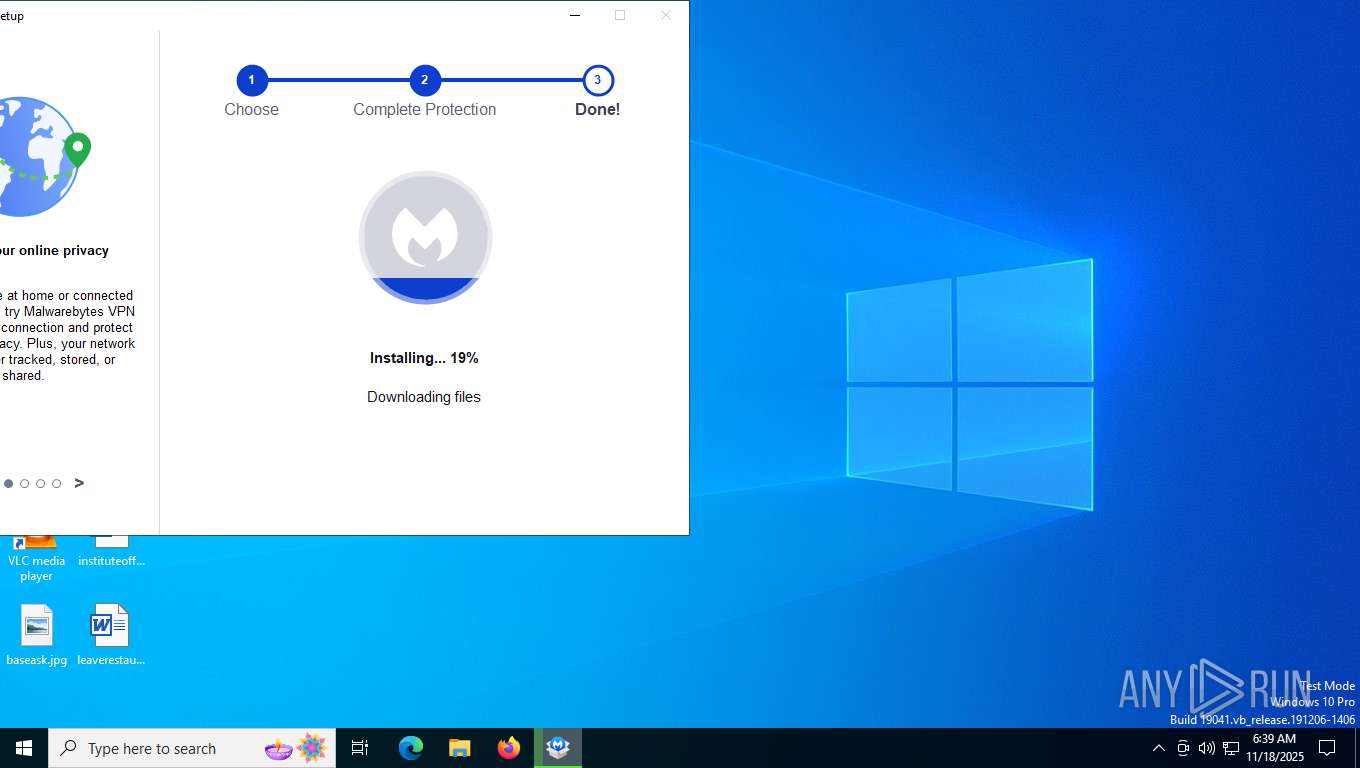
- MBSetup.exe (PID: 5776)
- MBSetup.exe (PID: 7220)
- MBAMInstallerService.exe (PID: 2124)
Reads the BIOS version
- MBSetup.exe (PID: 5776)
Creates files in the driver directory
- MBSetup.exe (PID: 5776)
The process verifies whether the antivirus software is installed
- MBSetup.exe (PID: 5776)
- MBAMInstallerService.exe (PID: 2124)
Executable content was dropped or overwritten
- MBSetup.exe (PID: 5776)
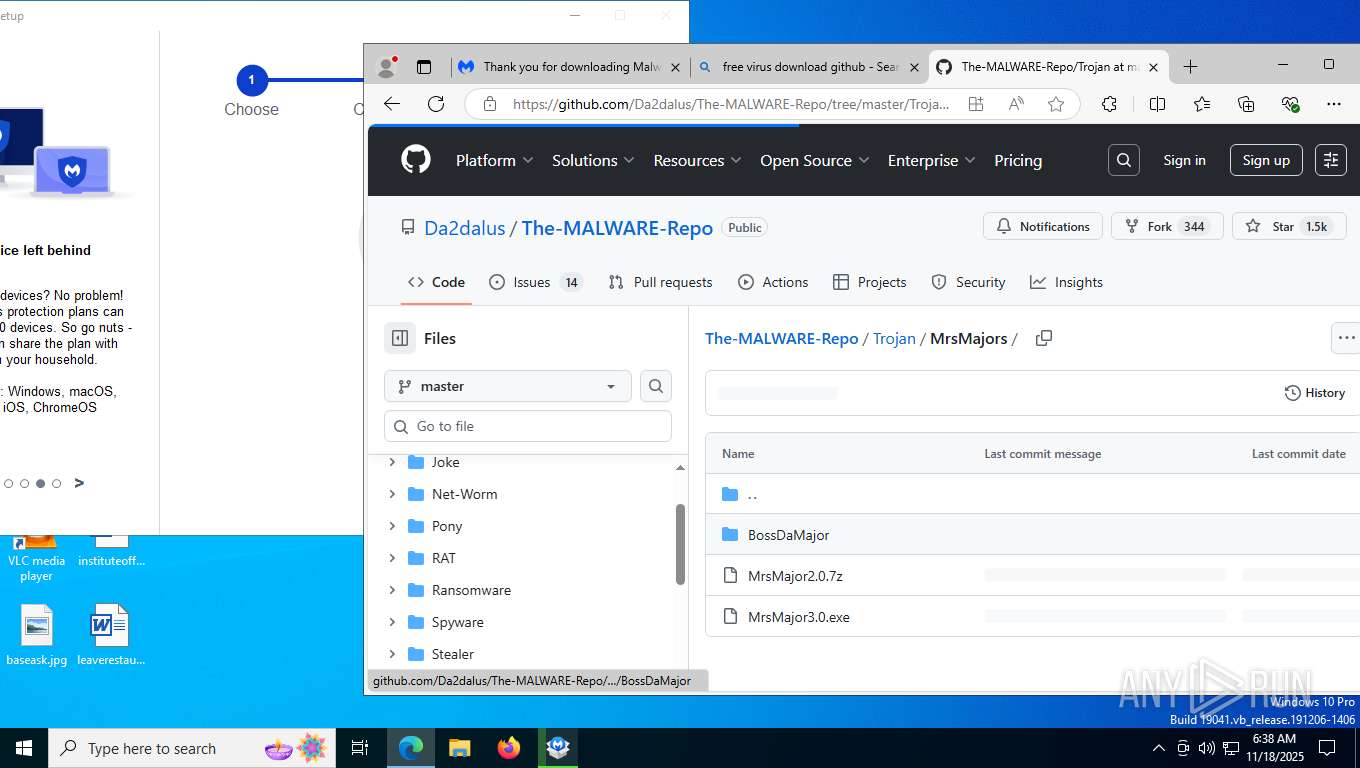
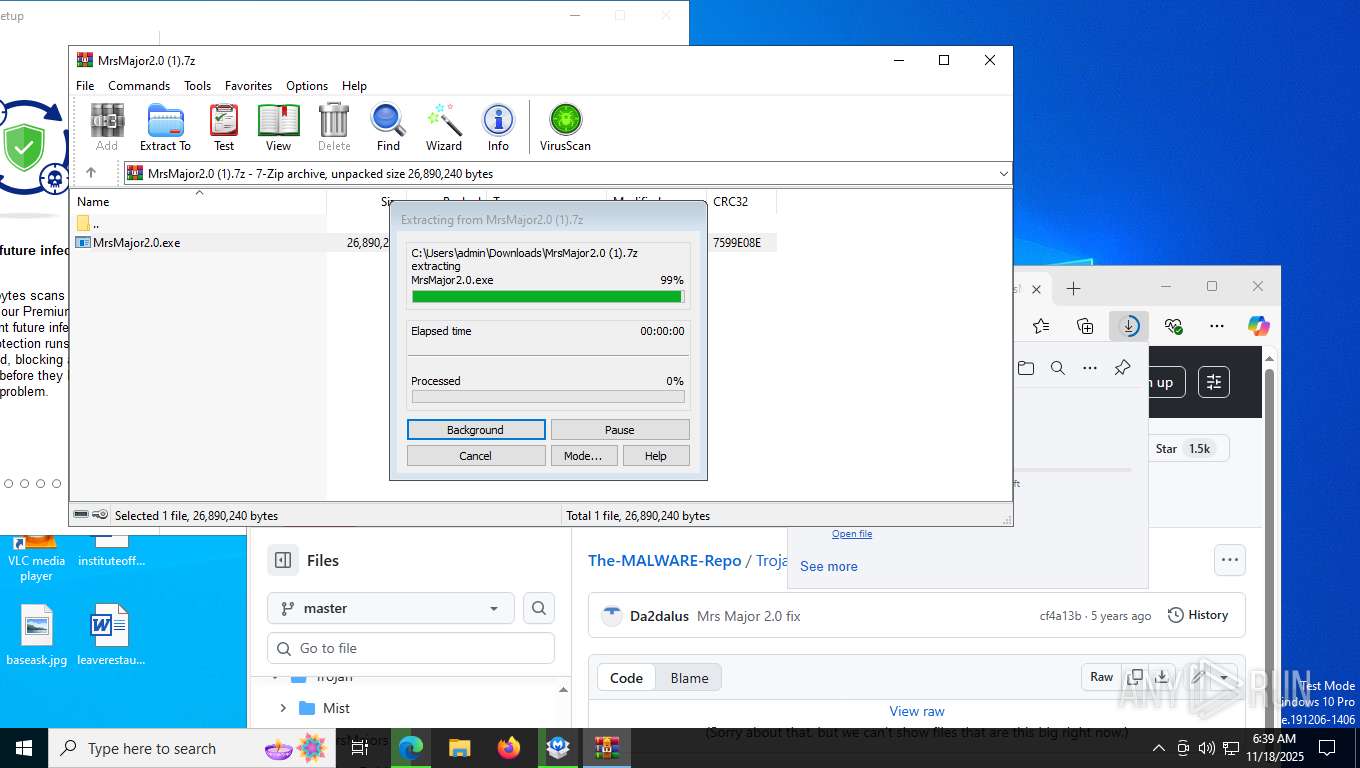
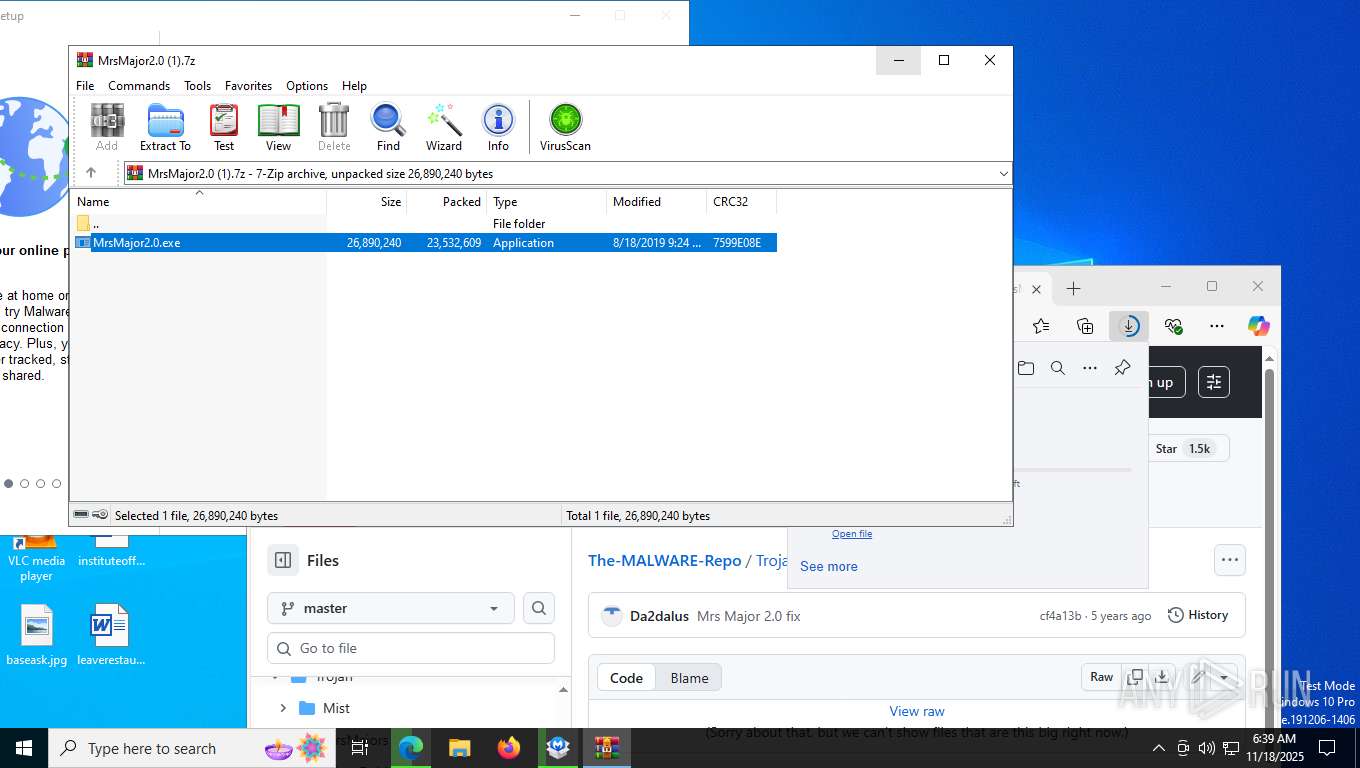
- MrsMajor2.0.exe (PID: 8120)
- wscript.exe (PID: 2220)
- MBAMInstallerService.exe (PID: 2124)
Executes as Windows Service
- MBAMInstallerService.exe (PID: 2124)
Non windows owned service launched
- MBAMInstallerService.exe (PID: 2124)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6428)
- MrsMajor2.0.exe (PID: 8120)
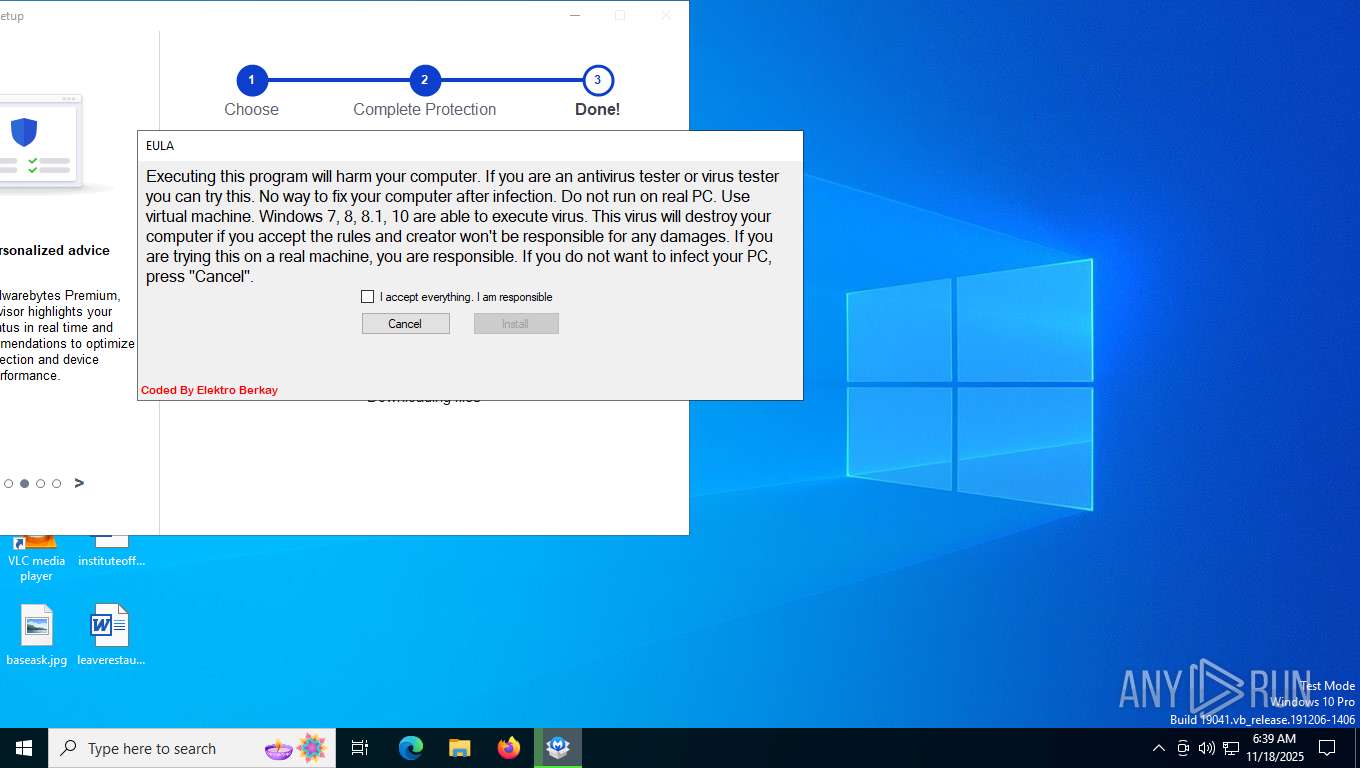
The process executes VB scripts
- MrsMajor2.0.exe (PID: 8120)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2220)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2220)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2220)
The executable file from the user directory is run by the CMD process
- eula32.exe (PID: 1788)
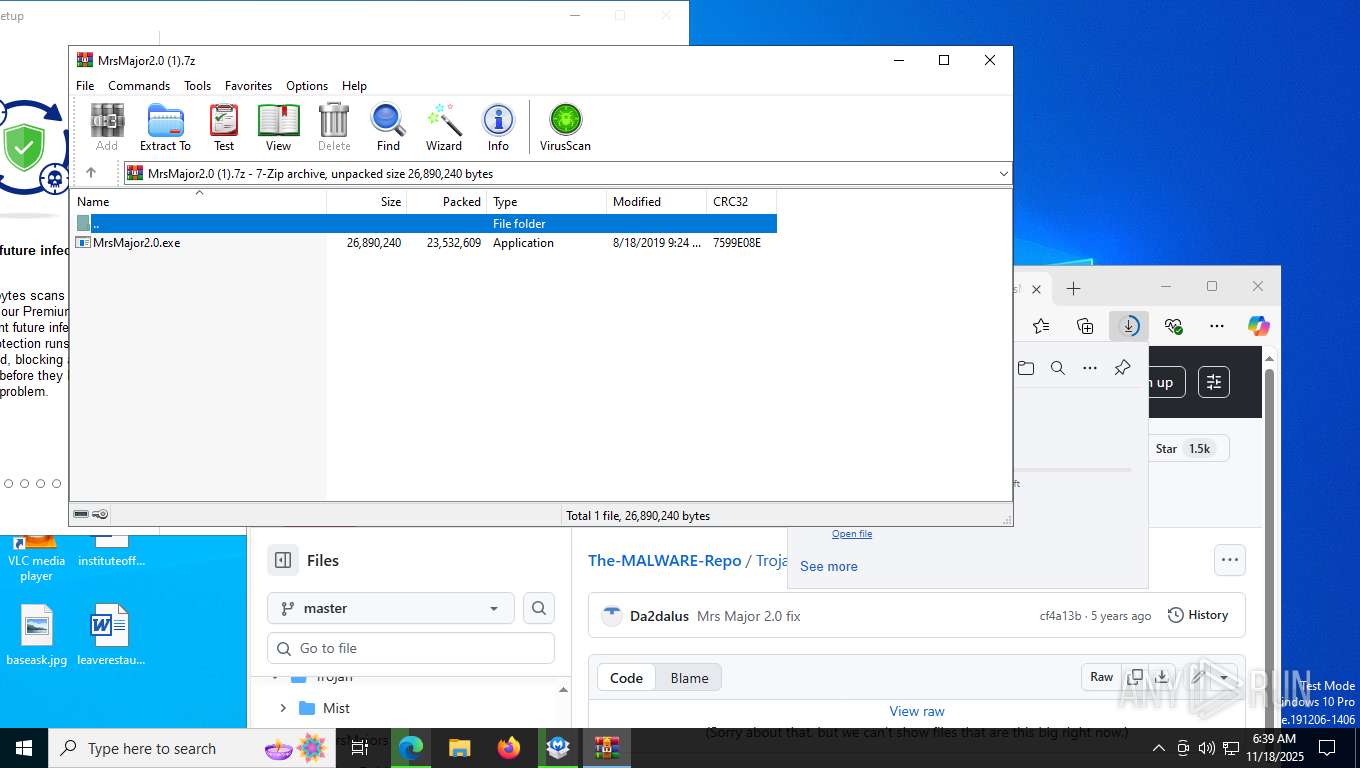
Drops 7-zip archiver for unpacking
- MBAMInstallerService.exe (PID: 2124)
There is functionality for taking screenshot (YARA)
- MrsMajor2.0.exe (PID: 8120)
Process drops legitimate windows executable
- MBAMInstallerService.exe (PID: 2124)
The process creates files with name similar to system file names
- MBAMInstallerService.exe (PID: 2124)
Drops a system driver (possible attempt to evade defenses)
- MBAMInstallerService.exe (PID: 2124)
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 6748)
The process drops C-runtime libraries
- MBAMInstallerService.exe (PID: 2124)
INFO
Application launched itself
- msedge.exe (PID: 7404)
- firefox.exe (PID: 6724)
Checks supported languages
- default-browser-agent.exe (PID: 6748)
- MBSetup.exe (PID: 5776)
- MBAMInstallerService.exe (PID: 2124)
- MBSetup.exe (PID: 7220)
- identity_helper.exe (PID: 7180)
- MrsMajor2.0.exe (PID: 8120)
- eula32.exe (PID: 1788)
- identity_helper.exe (PID: 5236)
Executable content was dropped or overwritten
- msedge.exe (PID: 7748)
- msedge.exe (PID: 7404)
- WinRAR.exe (PID: 6428)
The sample compiled with english language support
- msedge.exe (PID: 7748)
- msedge.exe (PID: 7404)
- MBSetup.exe (PID: 5776)
- WinRAR.exe (PID: 6428)
- MBAMInstallerService.exe (PID: 2124)
Create files in a temporary directory
- MBSetup.exe (PID: 5776)
- MrsMajor2.0.exe (PID: 8120)
- wscript.exe (PID: 2220)
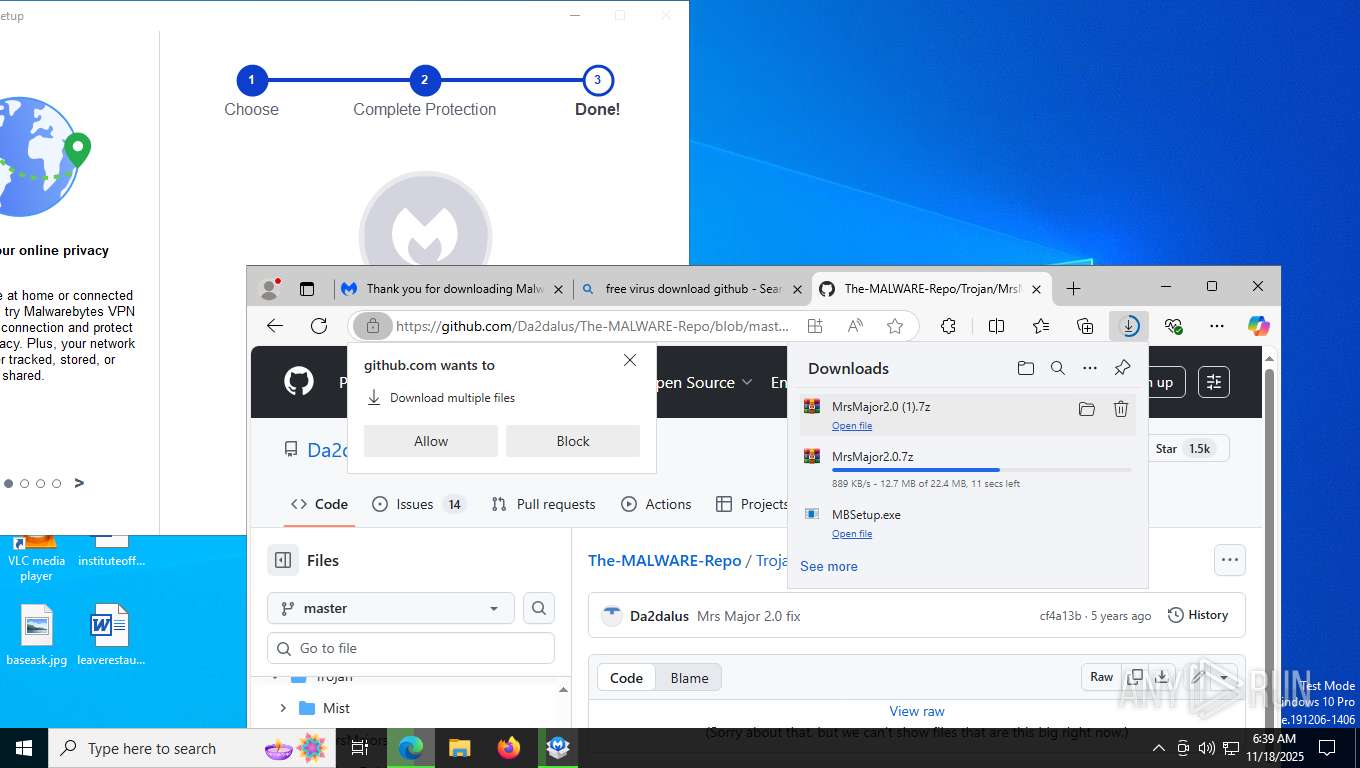
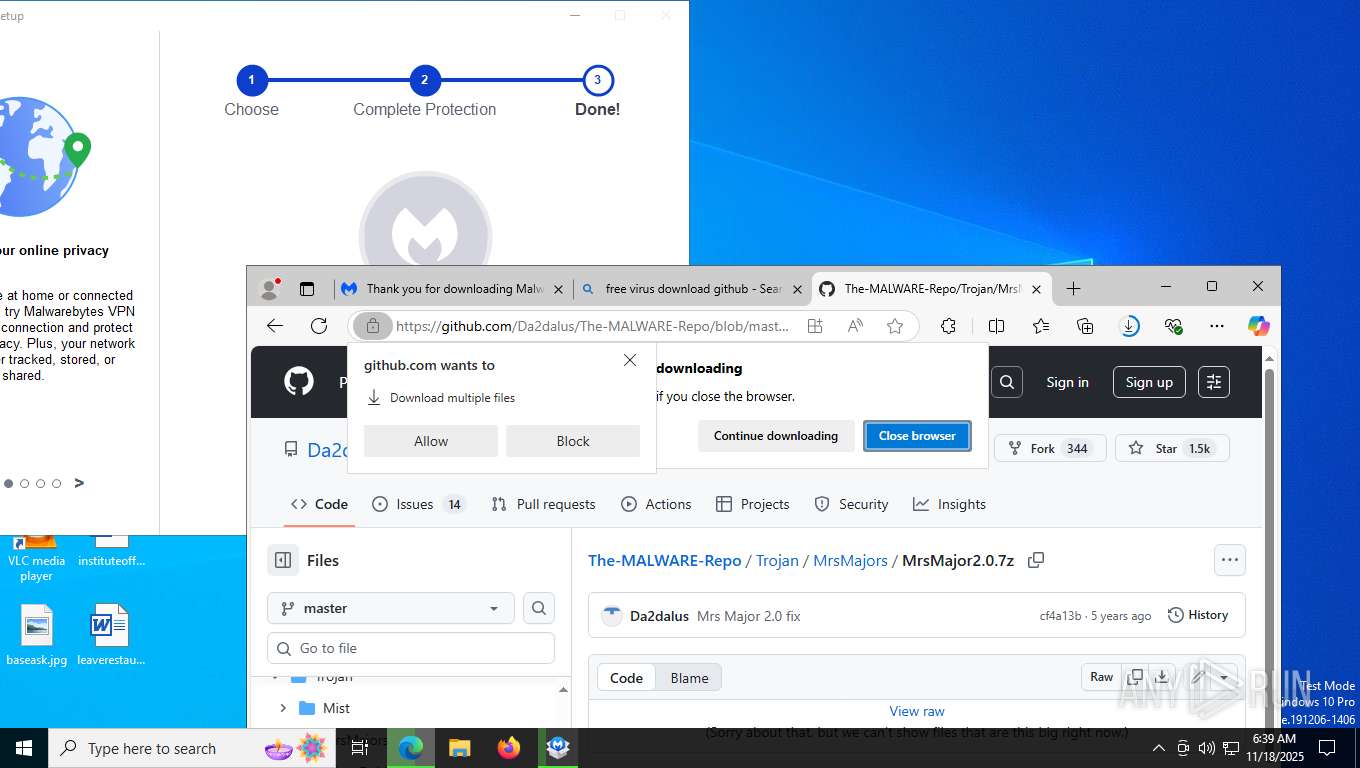
Launching a file from the Downloads directory
- msedge.exe (PID: 7404)
Reads the machine GUID from the registry
- MBSetup.exe (PID: 5776)
- eula32.exe (PID: 1788)
Reads the computer name
- MBSetup.exe (PID: 5776)
- MBSetup.exe (PID: 7220)
- MBAMInstallerService.exe (PID: 2124)
- identity_helper.exe (PID: 7180)
- MrsMajor2.0.exe (PID: 8120)
- eula32.exe (PID: 1788)
- identity_helper.exe (PID: 5236)
Reads the software policy settings
- MBSetup.exe (PID: 5776)
- slui.exe (PID: 7564)
- MBAMInstallerService.exe (PID: 2124)
Creates files in the program directory
- MBSetup.exe (PID: 5776)
- MBAMInstallerService.exe (PID: 2124)
- wscript.exe (PID: 2220)
Checks proxy server information
- MBSetup.exe (PID: 5776)
- slui.exe (PID: 7564)
Reads Environment values
- identity_helper.exe (PID: 7180)
- identity_helper.exe (PID: 5236)
Reads security settings of Internet Explorer
- wscript.exe (PID: 2220)
Process checks computer location settings
- MrsMajor2.0.exe (PID: 8120)
The sample compiled with spanish language support
- MBAMInstallerService.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
211
Monitored processes
58
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6408,i,2917793203392811719,15411342061270660378,262144 --variations-seed-version --mojo-platform-channel-handle=7780 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=25 --always-read-main-dll --field-trial-handle=1308,i,2917793203392811719,15411342061270660378,262144 --variations-seed-version --mojo-platform-channel-handle=7148 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1788 | eula32.exe | C:\Users\admin\AppData\Local\Temp\eula32.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Description: eula32 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=27 --always-read-main-dll --field-trial-handle=8168,i,2917793203392811719,15411342061270660378,262144 --variations-seed-version --mojo-platform-channel-handle=4388 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1940 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=35 --always-read-main-dll --field-trial-handle=8660,i,2917793203392811719,15411342061270660378,262144 --variations-seed-version --mojo-platform-channel-handle=8428 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5828,i,2917793203392811719,15411342061270660378,262144 --variations-seed-version --mojo-platform-channel-handle=6092 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMInstallerService.exe" | C:\Program Files\Malwarebytes\Anti-Malware\MBAMInstallerService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Installer Service Version: 5.1.0.211 Modules
| |||||||||||||||
| 2220 | "C:\WINDOWS\sysnative\wscript.exe" C:\Users\admin\AppData\Local\Temp\A841.tmp\A842.vbs | C:\Windows\System32\wscript.exe | MrsMajor2.0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2436 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6428.8546\MrsMajor2.0.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6428.8546\MrsMajor2.0.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6792,i,2917793203392811719,15411342061270660378,262144 --variations-seed-version --mojo-platform-channel-handle=6692 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
13 241
Read events
13 148
Write events
92
Delete events
1
Modification events
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Malwarebytes |
| Operation: | write | Name: | id |
Value: 62f6d07962ed4411b76e550190bbe50f | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Malwarebytes |
| Operation: | write | Name: | id |
Value: 62f6d07962ed4411b76e550190bbe50f | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\mbamtestkey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MBAMInstallerService\Parameters |
| Operation: | write | Name: | UserName |
Value: admin | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MBAMInstallerService\Parameters |
| Operation: | write | Name: | ProductCode |
Value: MBAM-C | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MBAMInstallerService\Parameters |
| Operation: | write | Name: | ProductBuild |
Value: consumer | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MBAMInstallerService\Parameters |
| Operation: | write | Name: | ProgramDirectory |
Value: C:\Program Files\Malwarebytes\Anti-Malware | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MBAMInstallerService\Parameters |
| Operation: | write | Name: | LocalAppDataDir |
Value: C:\Users\admin\AppData\Local | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MBAMInstallerService\Parameters |
| Operation: | write | Name: | Channel |
Value: release | |||
| (PID) Process: | (5776) MBSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MBAMInstallerService\Parameters |
| Operation: | write | Name: | Installer |
Value: C:\Users\admin\Downloads\MBSetup.exe | |||
Executable files
1 147
Suspicious files
966
Text files
217
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF161f73.TMP | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF161f83.TMP | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF161f83.TMP | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF161f83.TMP | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF161f83.TMP | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
246
DNS requests
272
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5732 | svchost.exe | GET | 200 | 184.31.68.248:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2408 | svchost.exe | GET | 200 | 23.44.201.218:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7748 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:QYeoEVFRGEUs5wF08BrRth3pVkiooyLwRyDmaW3Hfos&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 23.44.201.218:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1664 | SIHClient.exe | GET | 200 | 23.56.210.93:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
1664 | SIHClient.exe | GET | 200 | 23.56.210.93:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1664 | SIHClient.exe | GET | 200 | 23.56.210.93:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
1664 | SIHClient.exe | GET | 200 | 23.44.201.218:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
1664 | SIHClient.exe | GET | 200 | 23.56.210.93:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
1664 | SIHClient.exe | GET | 200 | 23.56.210.93:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2408 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5732 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5732 | svchost.exe | 184.31.68.248:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 23.44.201.218:80 | crl.microsoft.com | AKAMAI-AS | US | whitelisted |
2408 | svchost.exe | 23.44.201.218:80 | crl.microsoft.com | AKAMAI-AS | US | whitelisted |
7748 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7748 | msedge.exe | 192.0.66.233:443 | malwarebytes.com | AUTOMATTIC | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
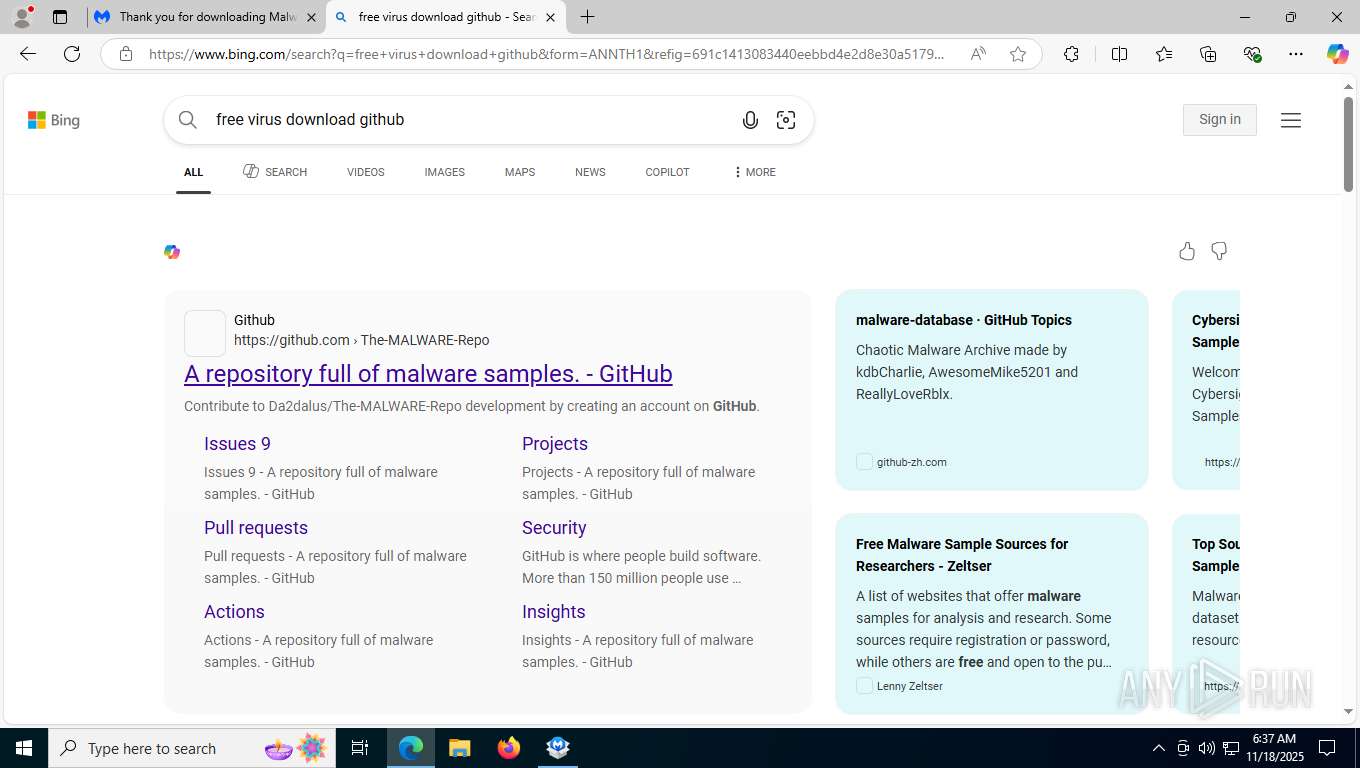
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
malwarebytes.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | Potentially Bad Traffic | ET INFO Executable served from Amazon S3 |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO Packed Executable Download |
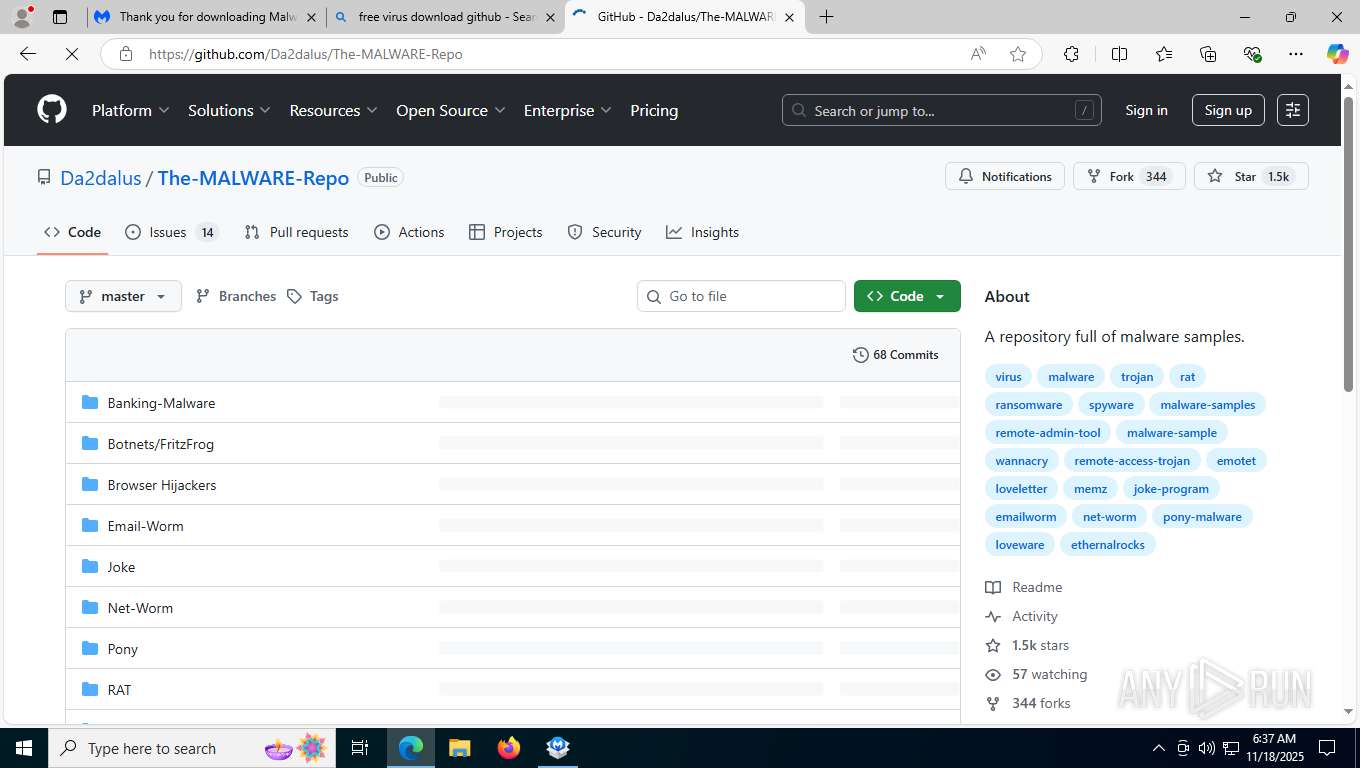
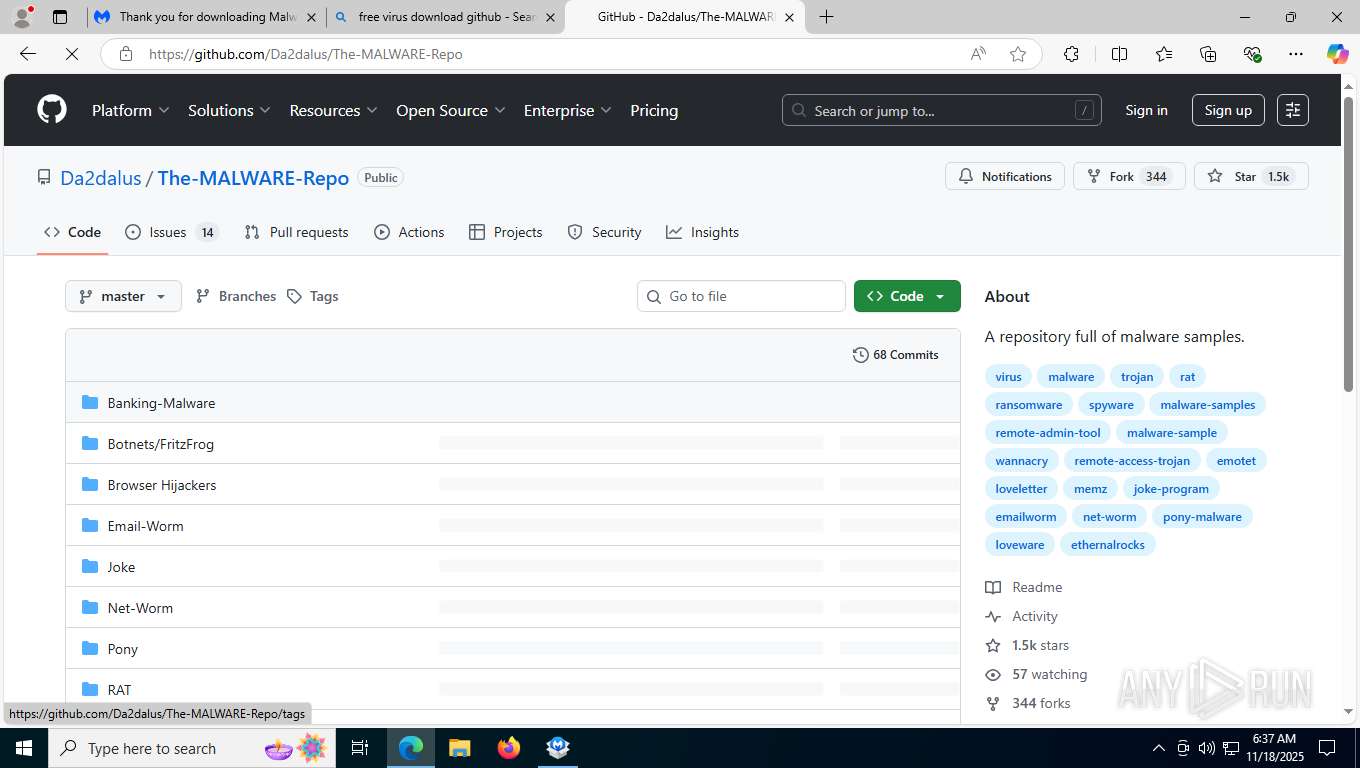
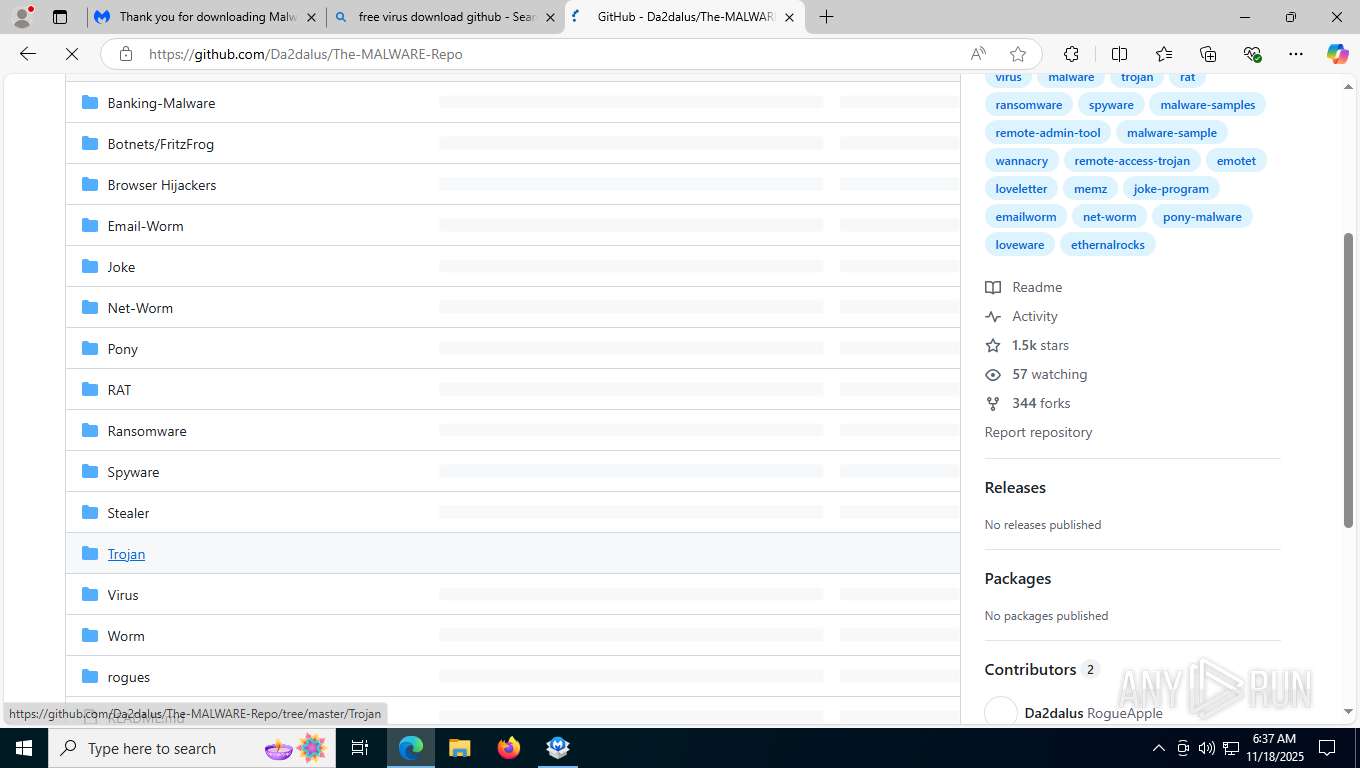
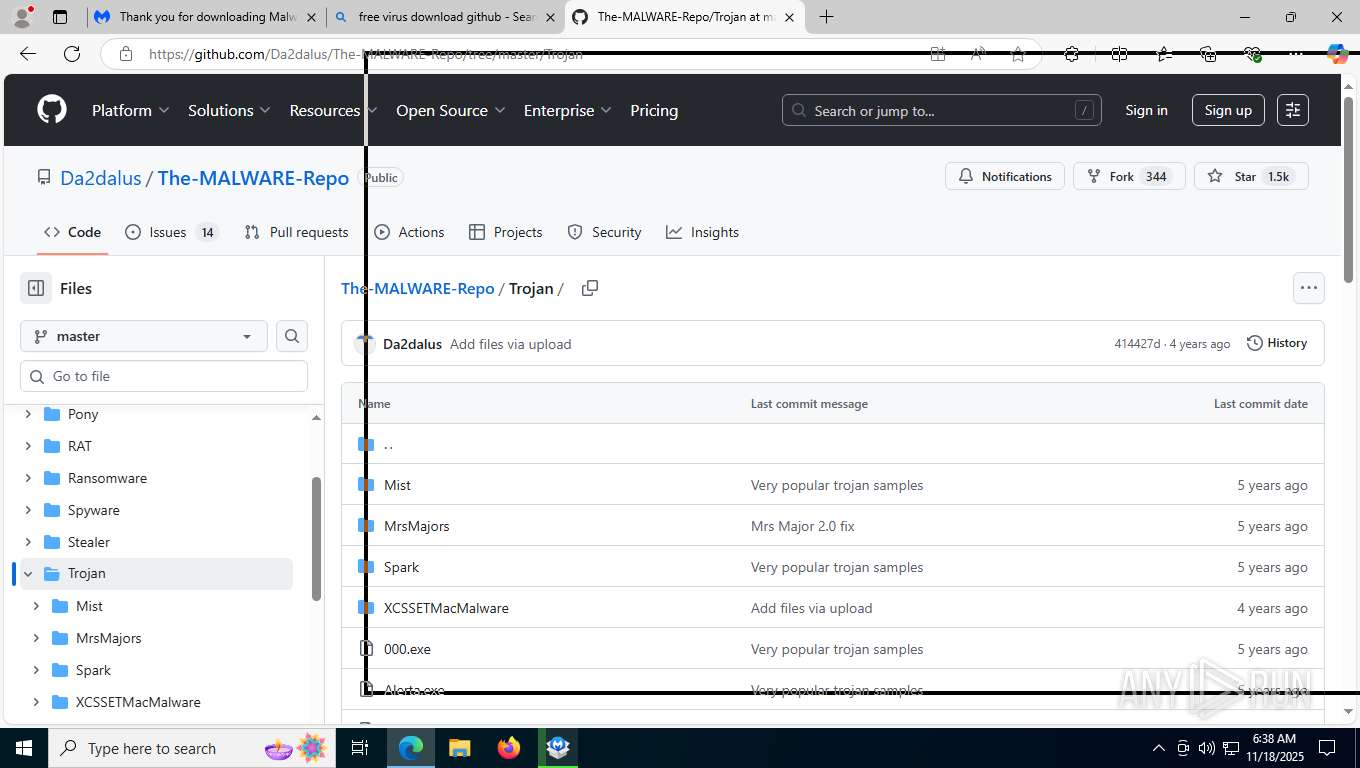
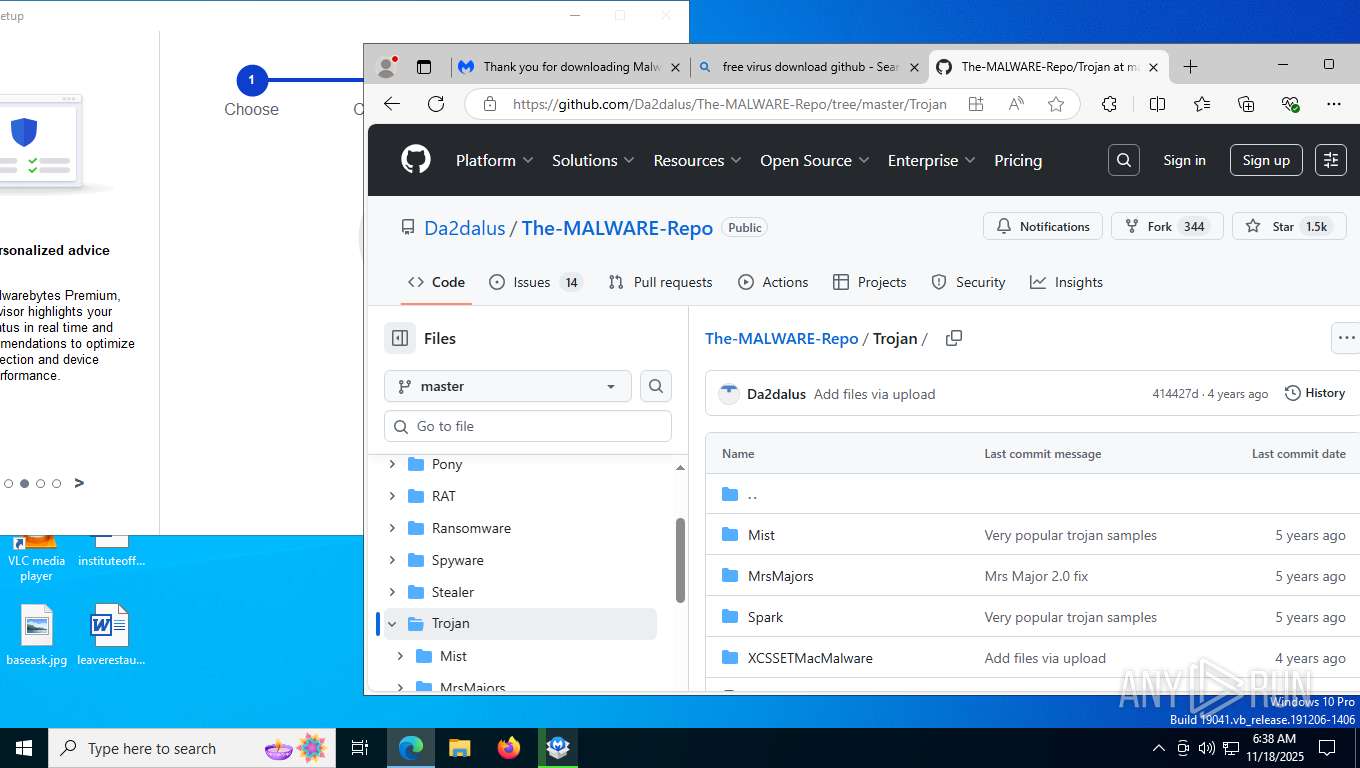
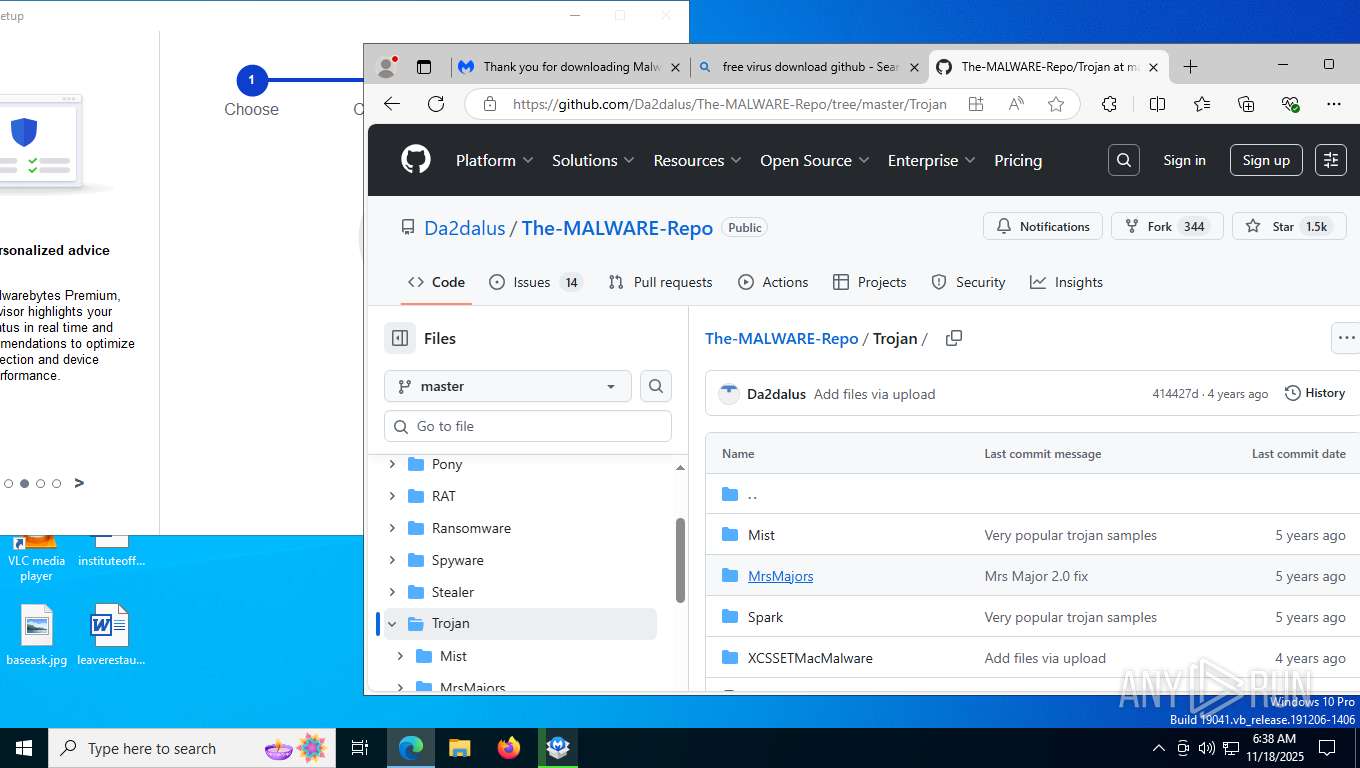
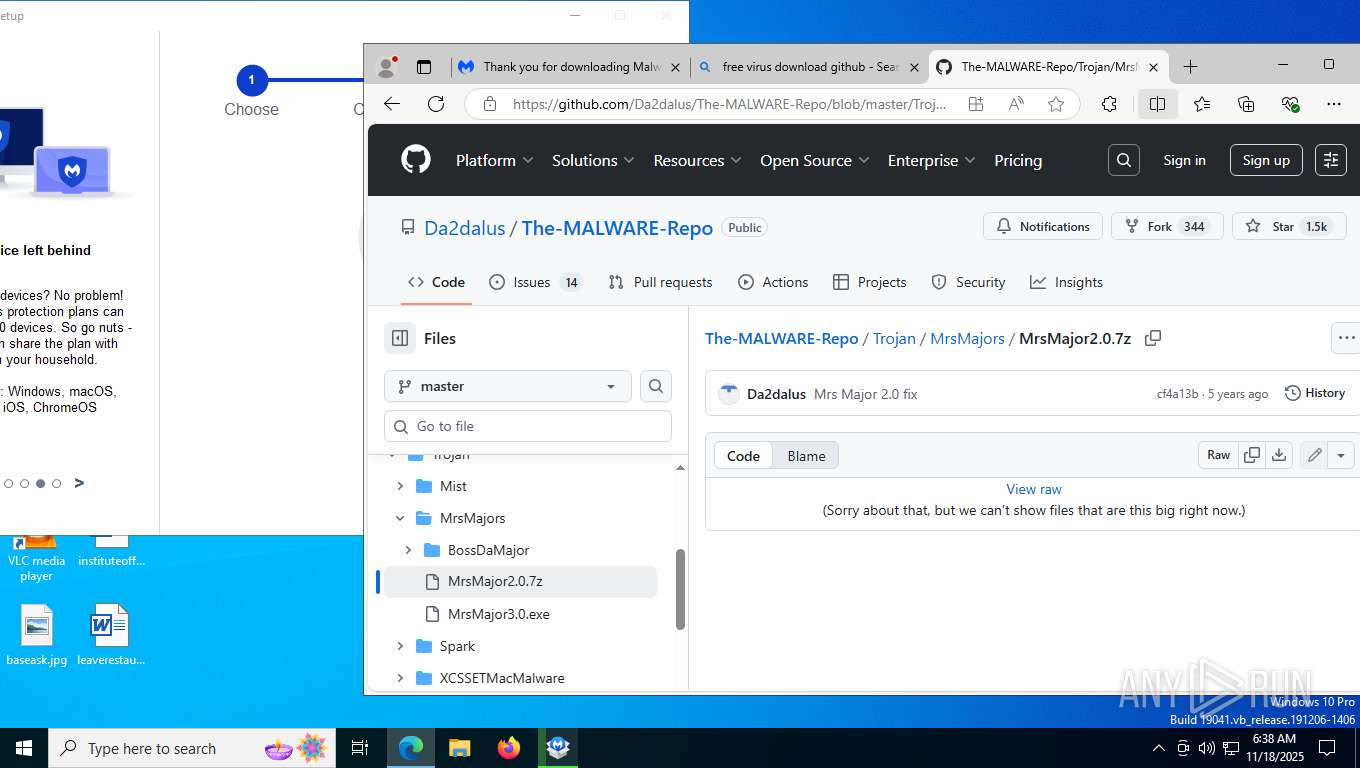
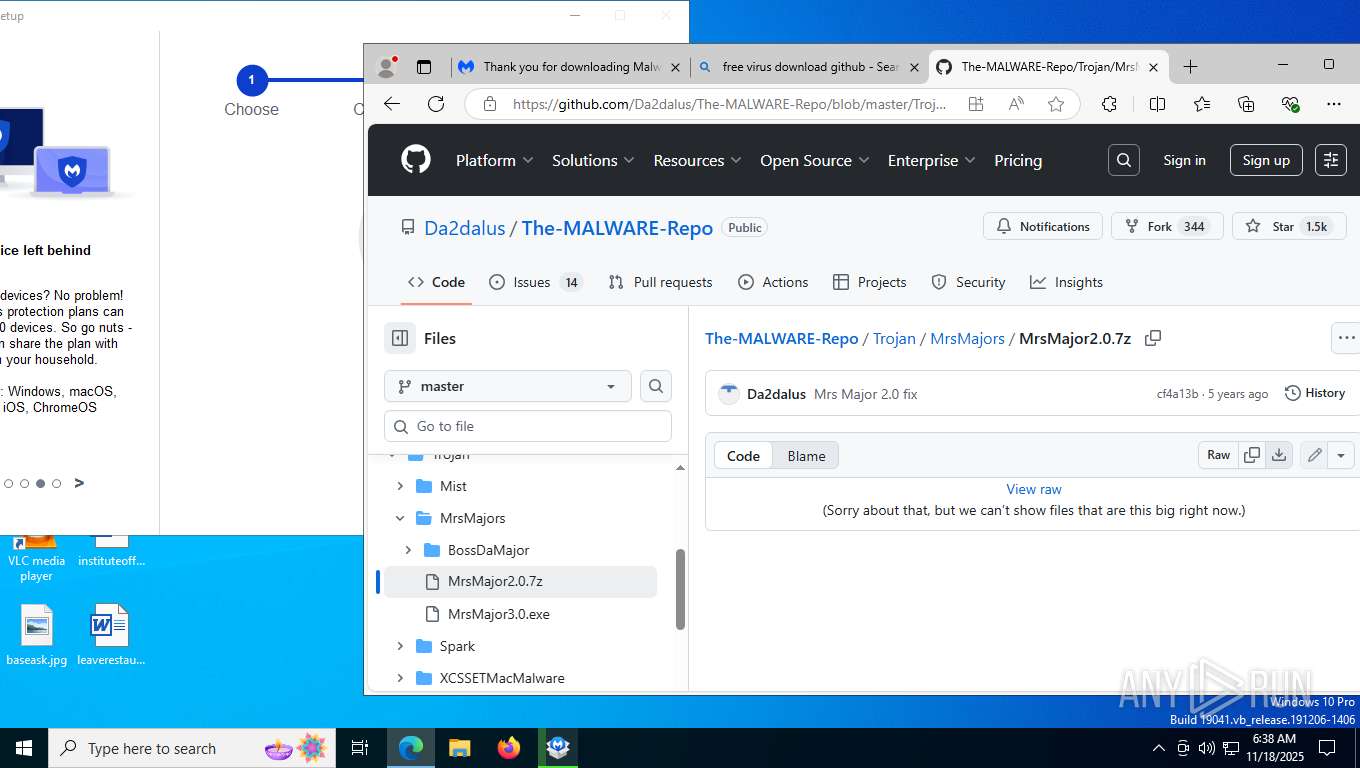
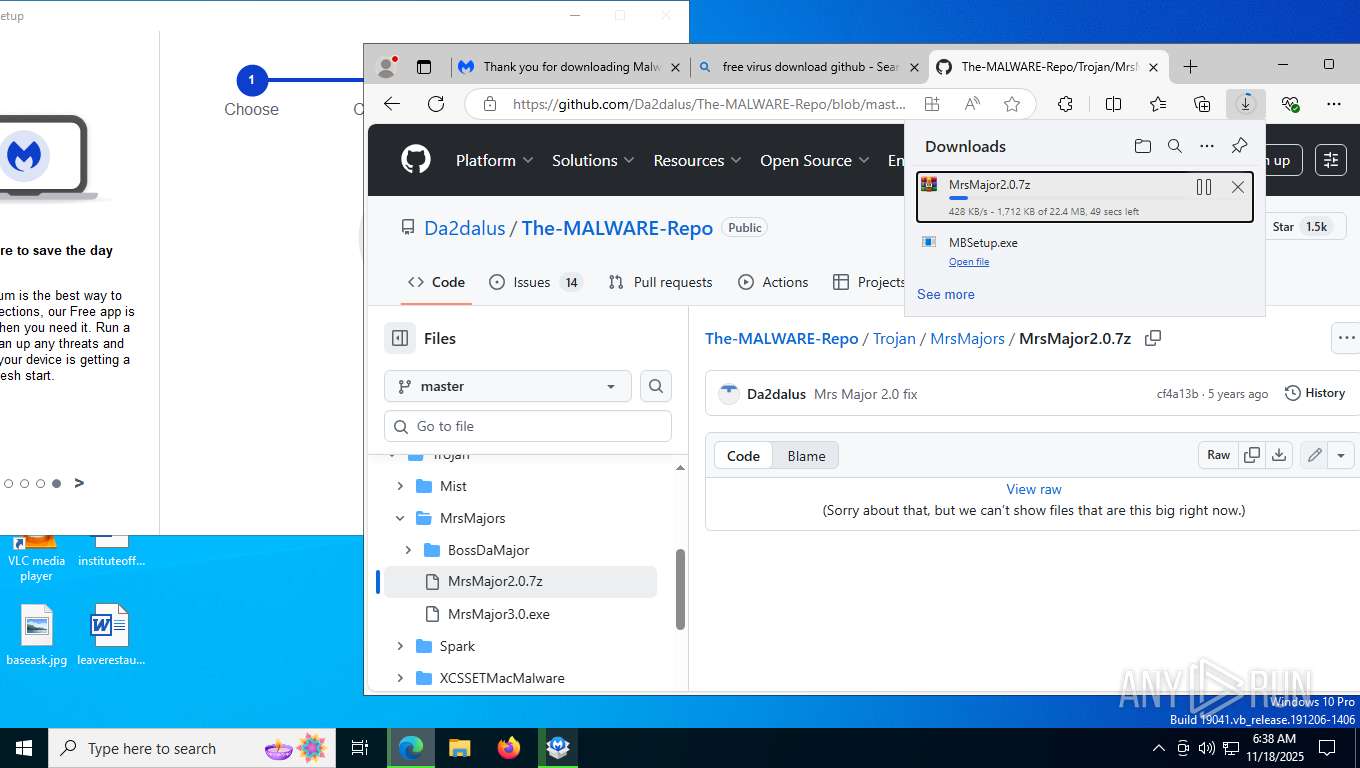
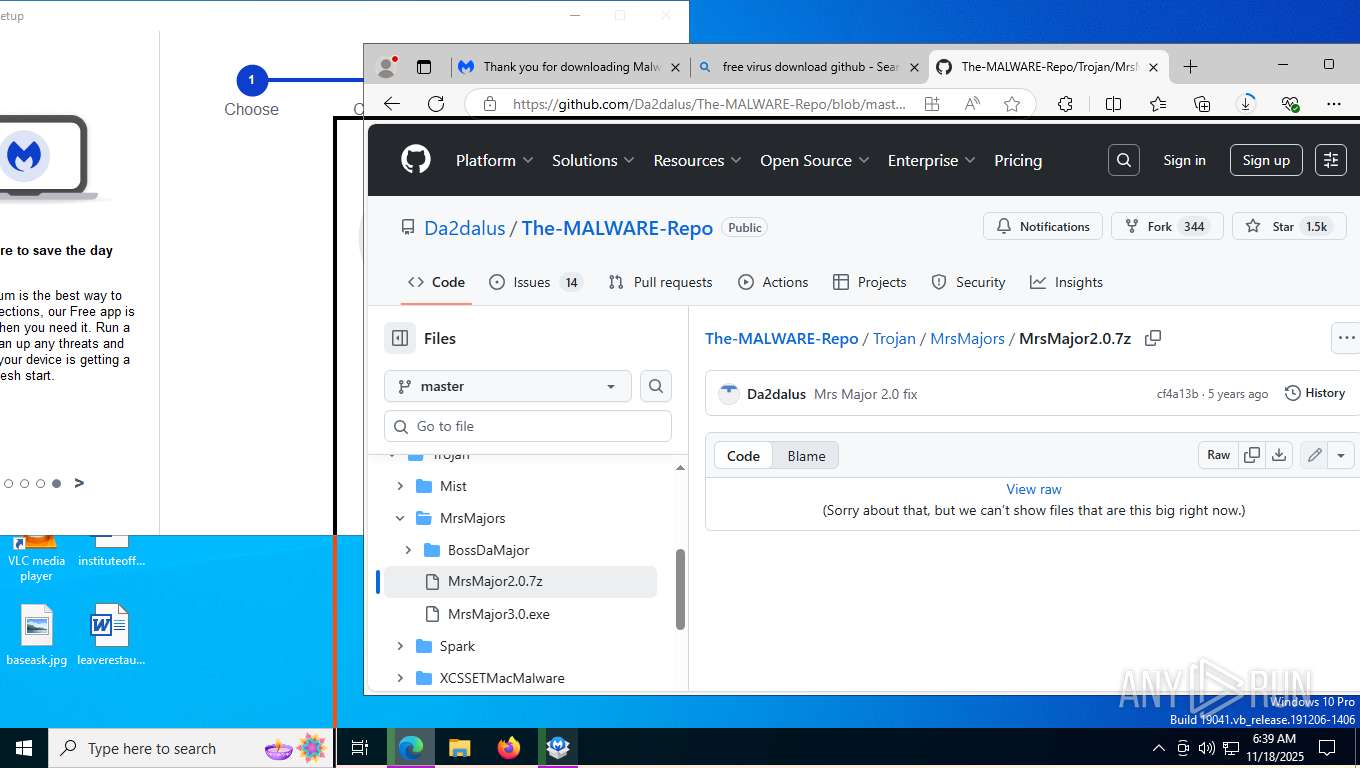
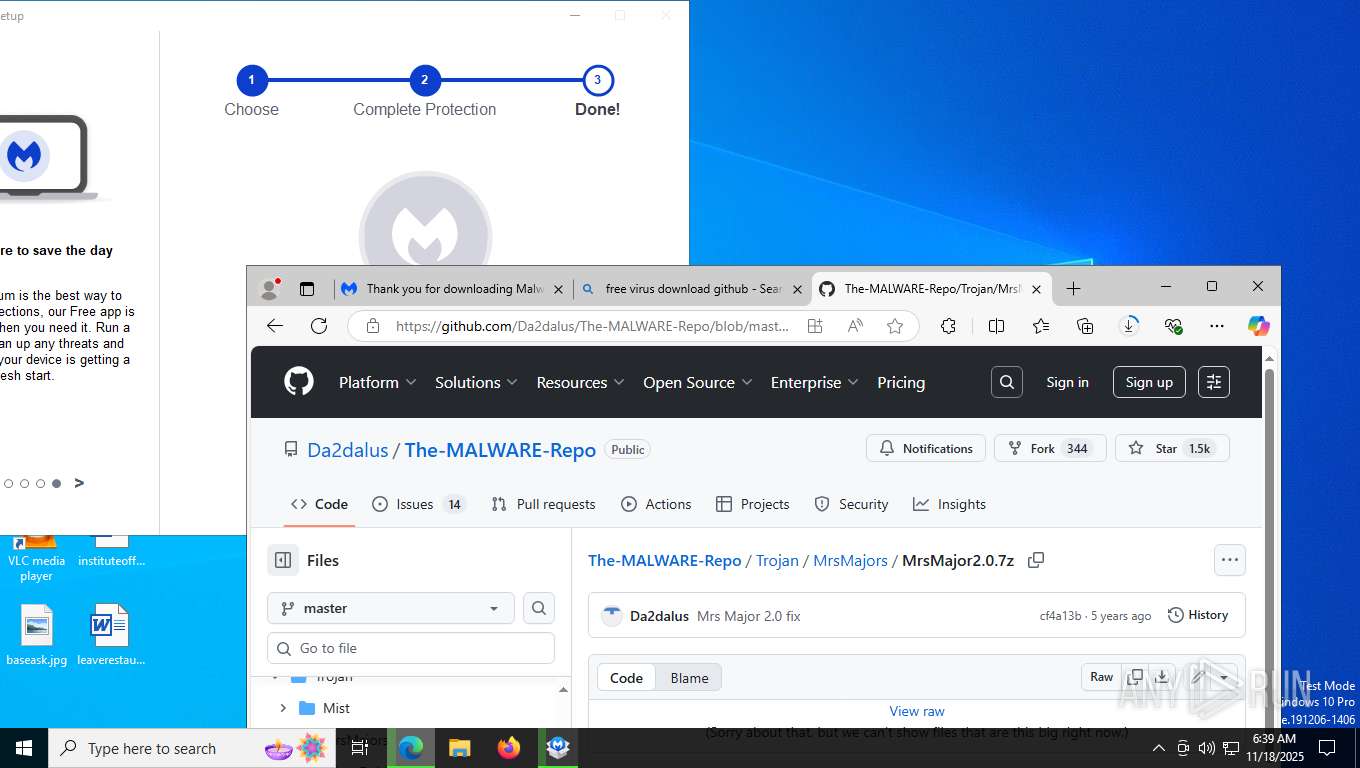
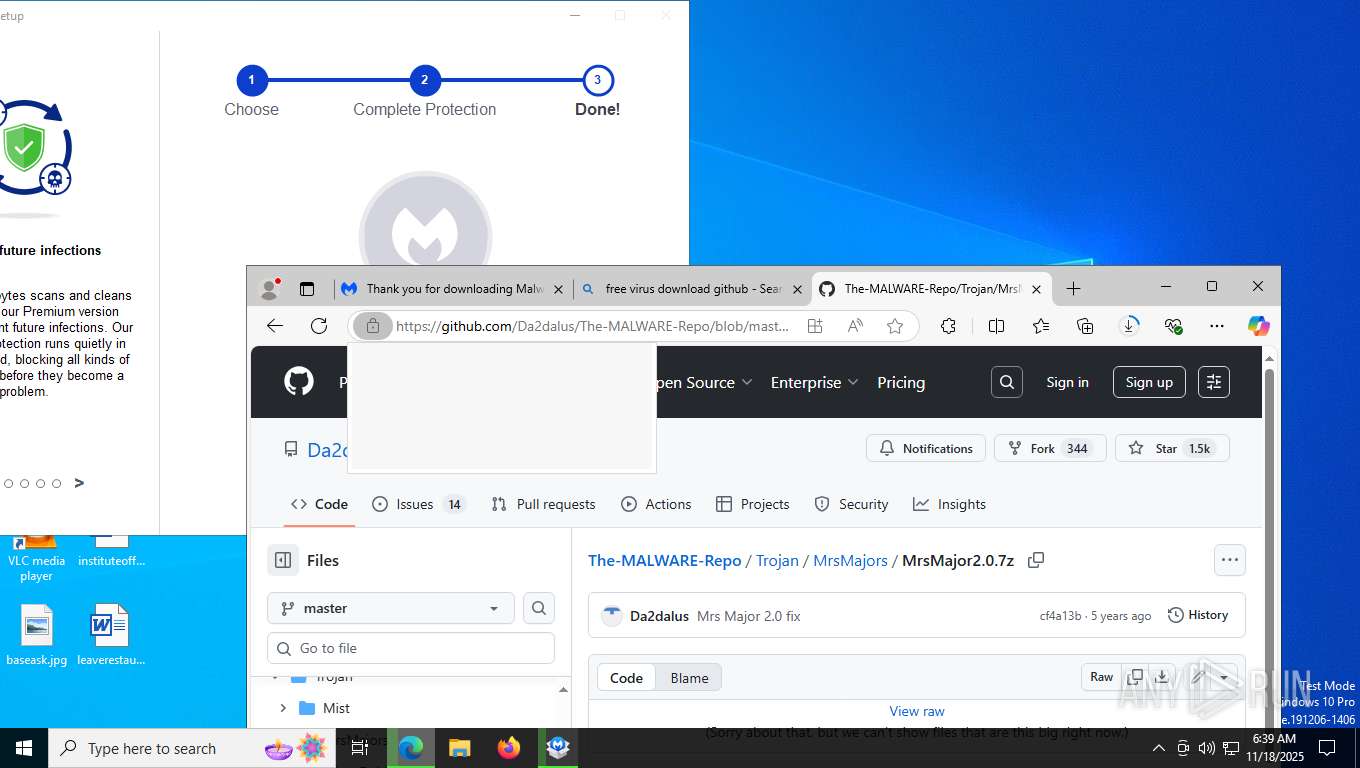
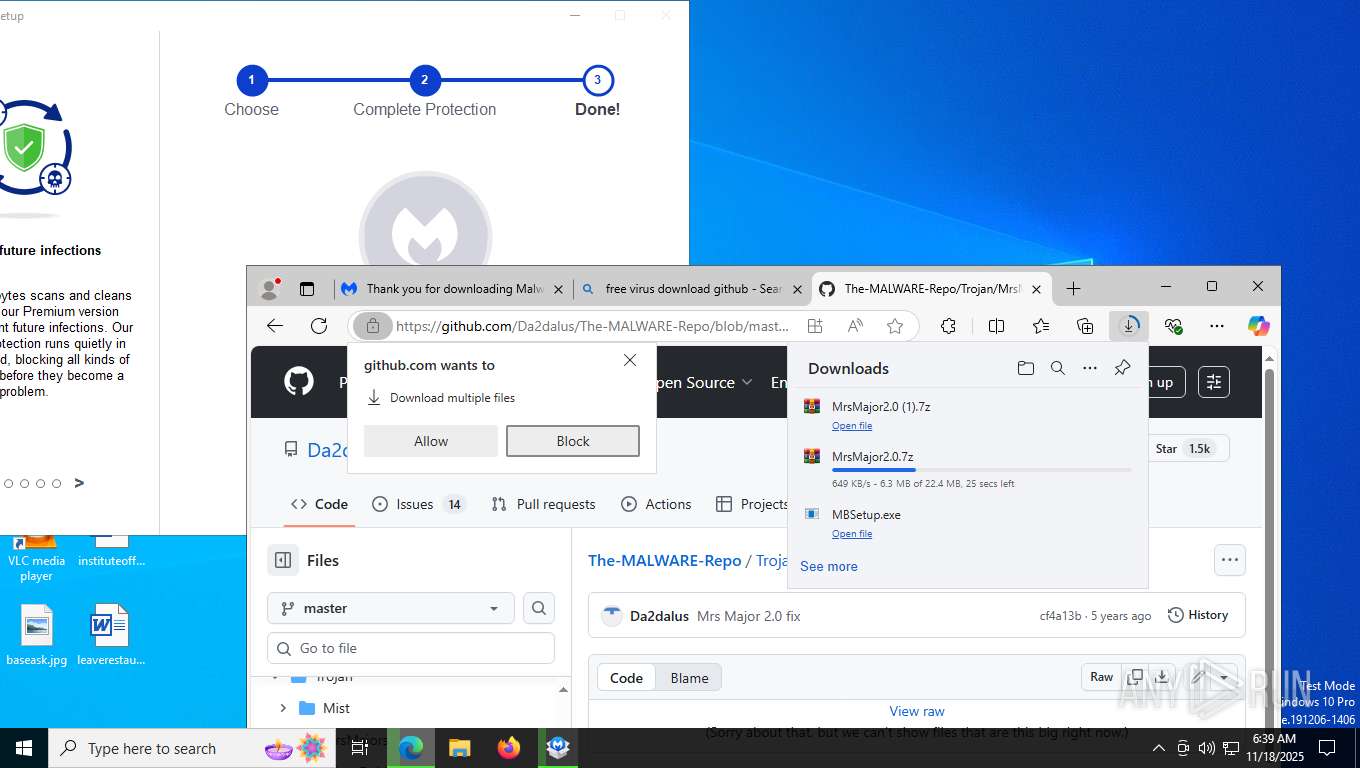
7748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |