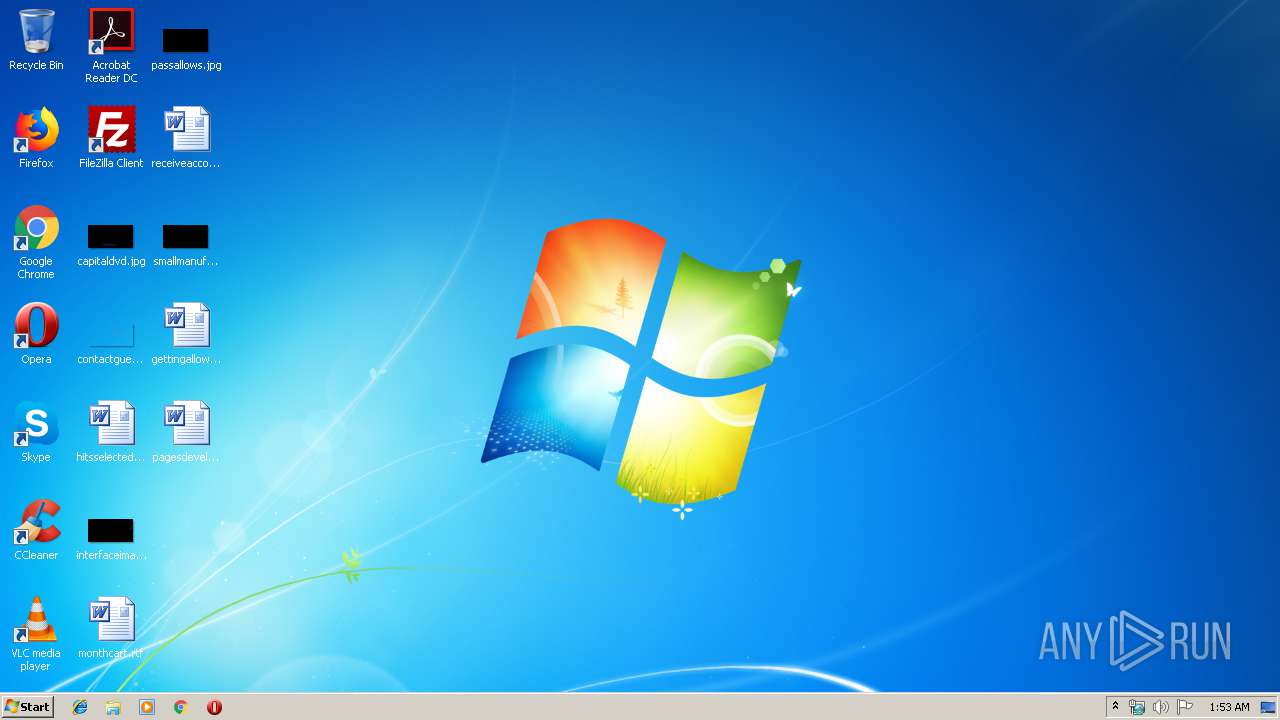
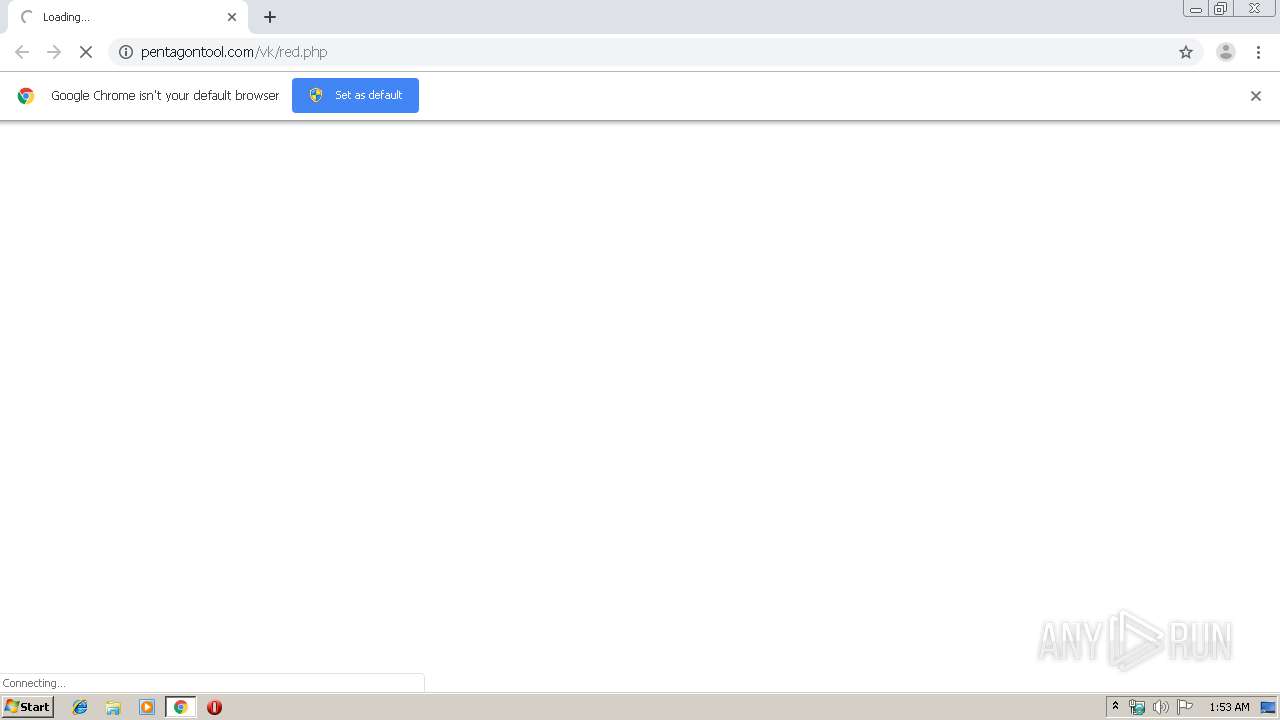
| URL: | http://pentagontool.com/vk/red.php |
| Full analysis: | https://app.any.run/tasks/6dc43d8c-b9d0-43d0-a93f-c63dd52954b8 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 01:52:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 648E0938923FD9ECB91B1BEE9F899CD3 |
| SHA1: | B4776B8041B0FD90BD9C7B66280ED3ED67543102 |
| SHA256: | D736863CE554119C01CBF6506910309DDFC0E436B44B2B6CF3F0C4345AF677A3 |
| SSDEEP: | 3:N1KOAL6KKsIYVNV:CO/KKsPV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1016)
INFO
Reads the hosts file
- chrome.exe (PID: 4064)
- chrome.exe (PID: 1016)
Reads settings of System Certificates
- chrome.exe (PID: 4064)
Application launched itself
- chrome.exe (PID: 1016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12971427313284419302 --mojo-platform-channel-handle=4552 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7040251934531131839 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6557437674915663556 --mojo-platform-channel-handle=3712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4995215972282010408 --mojo-platform-channel-handle=4496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://pentagontool.com/vk/red.php" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18342907571943183950 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15161040119102706757 --mojo-platform-channel-handle=3692 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1756 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2260058583844593395 --mojo-platform-channel-handle=3812 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11325401914529428105 --mojo-platform-channel-handle=4456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
640
Read events
524
Write events
110
Delete events
6
Modification events
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1016-13223785988880500 |
Value: 259 | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1016) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
27
Text files
338
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0e0bddc7-a074-4f95-a58f-0fdce1868c44.tmp | — | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39ac57.TMP | text | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39ac96.TMP | text | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39ac29.TMP | text | |
MD5:— | SHA256:— | |||
| 1016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39ac29.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
36
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
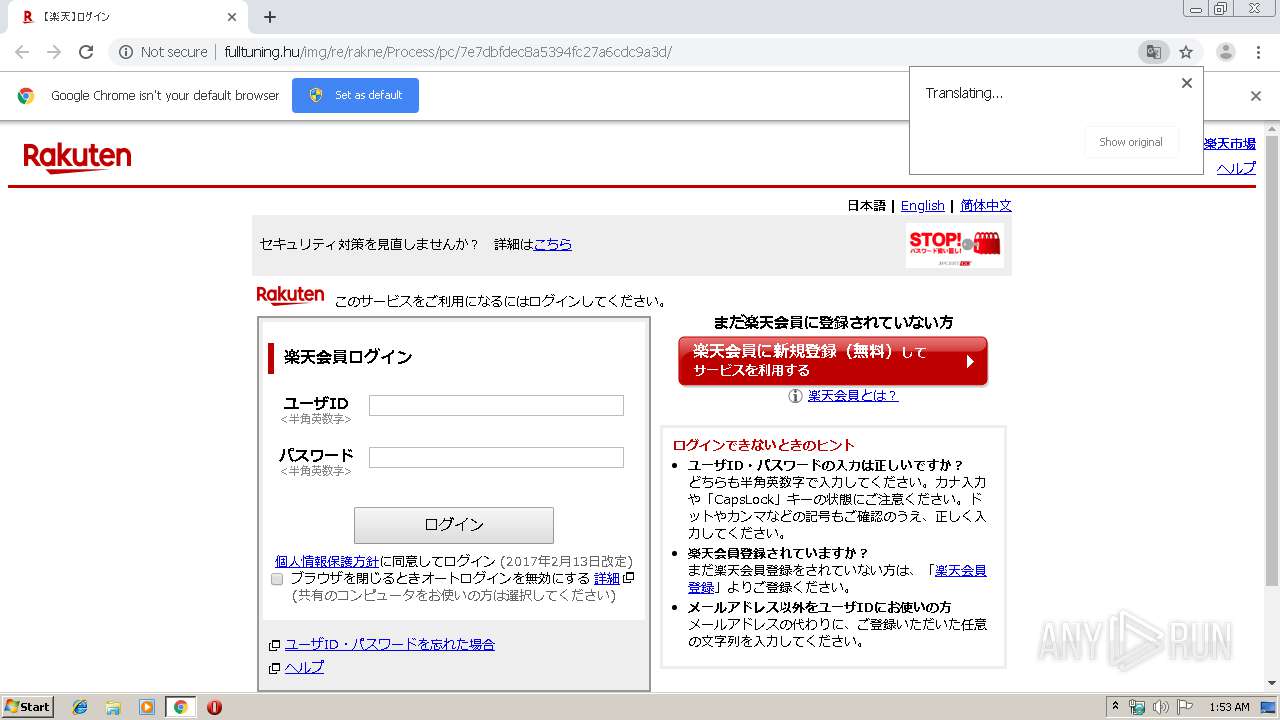
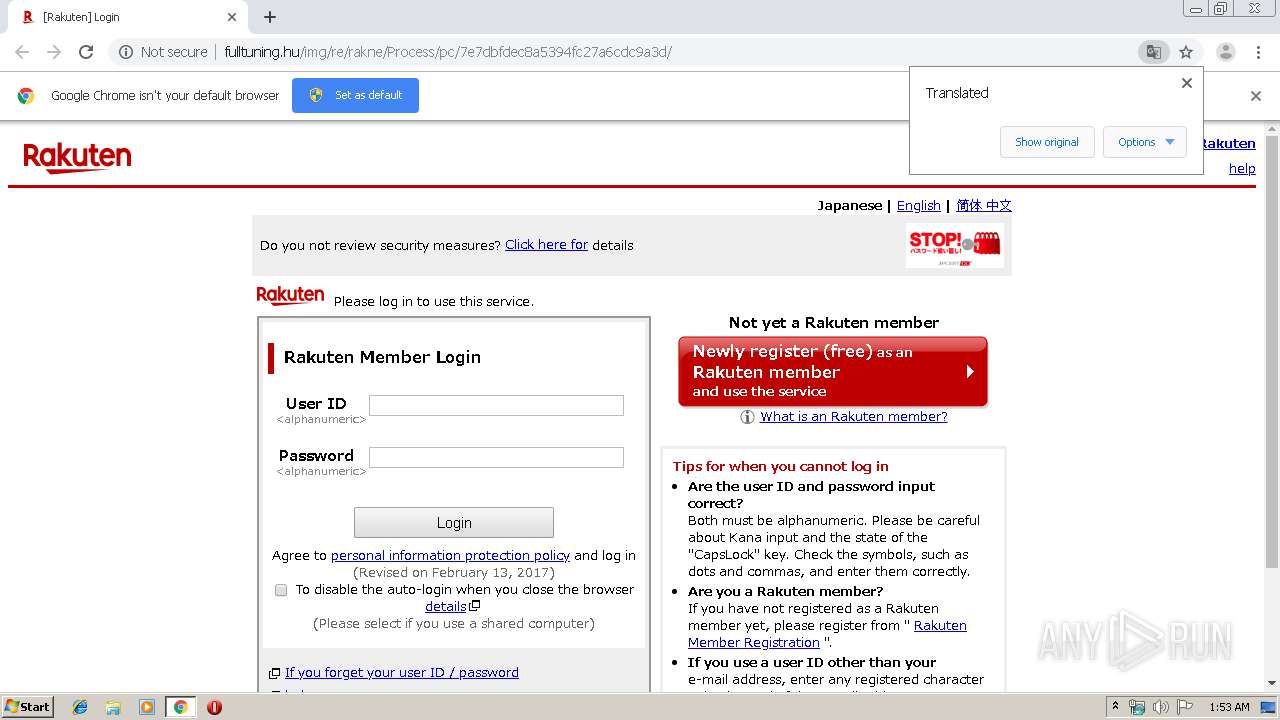
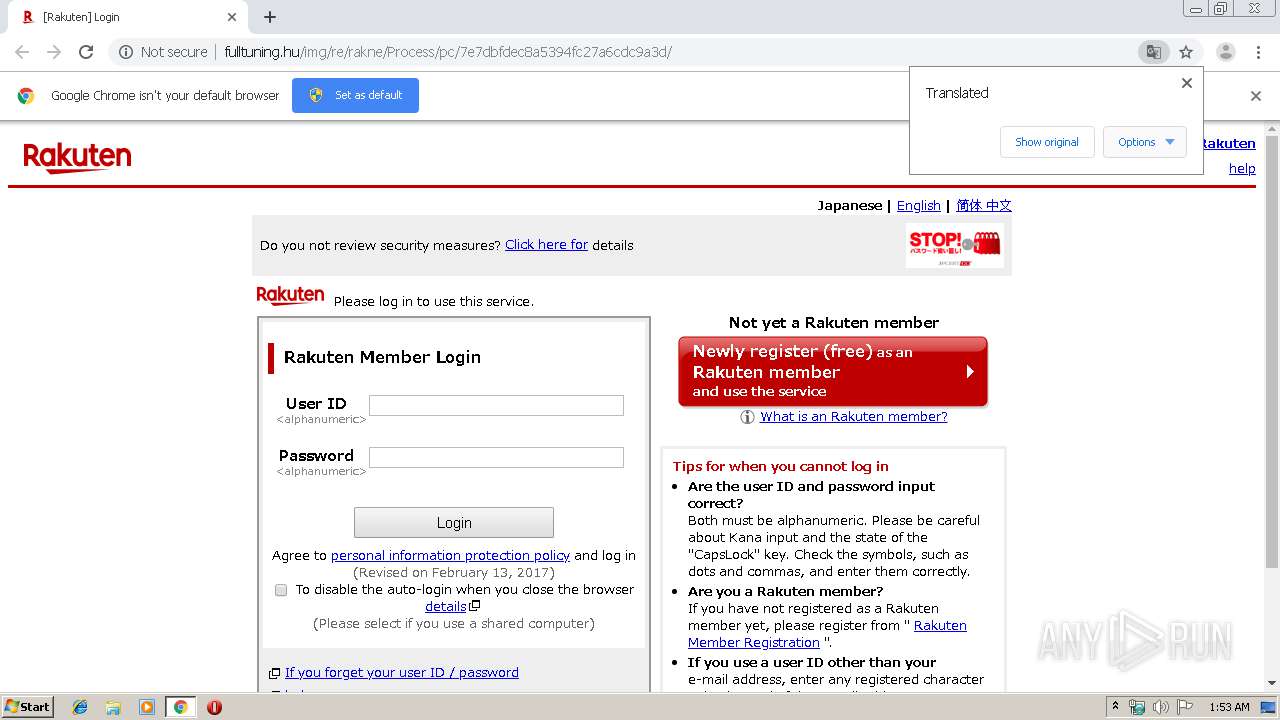
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/css/challenger.css | HU | text | 625 b | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/js/tls_alert.js | HU | html | 1.06 Kb | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/js/id.js | HU | text | 256 b | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/js/challenger.js | HU | text | 373 b | suspicious |
4064 | chrome.exe | GET | 200 | 2.21.38.77:80 | http://www.rakuten.co.jp/com/rat/plugin/external/ral-iframe-rakuten.co.jp.html?o-id=http%3A%2F%2Ffulltuning.hu | FR | html | 1.82 Kb | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/js/tls12.js | HU | text | 29 b | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/images/info.gif | HU | image | 360 b | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/images/bg_btn_red_top.gif | HU | image | 1.84 Kb | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/images/bg_btn_red_btm.gif | HU | image | 442 b | suspicious |
4064 | chrome.exe | GET | 200 | 193.91.64.2:80 | http://fulltuning.hu/img/re/rakne/Process/pc/7e7dbfdec8a5394fc27a6cdc9a3d/static/js/hint.js | HU | text | 1.13 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4064 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 45.40.157.86:80 | pentagontool.com | GoDaddy.com, LLC | US | unknown |
4064 | chrome.exe | 193.91.64.2:80 | fulltuning.hu | Invitech Megoldasok Zrt. | HU | suspicious |
4064 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 52.232.41.74:443 | challenger.api.global.rakuten.com | Microsoft Corporation | NL | unknown |
4064 | chrome.exe | 23.77.211.108:443 | static.id.rakuten.co.jp | Akamai International B.V. | NL | unknown |
4064 | chrome.exe | 2.21.38.77:80 | www.rakuten.co.jp | GTT Communications Inc. | FR | unknown |
4064 | chrome.exe | 95.140.236.22:80 | image.rakuten.co.jp | Limelight Networks, Inc. | GB | unknown |
4064 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 172.217.16.202:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pentagontool.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fulltuning.hu |
| suspicious |
www.google.com |
| malicious |
static.id.rakuten.co.jp |
| unknown |
challenger.api.global.rakuten.com |
| unknown |
image.rakuten.co.jp |
| whitelisted |
www.rakuten.co.jp |
| suspicious |
r.r10s.jp |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4064 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |